Internet Security An Optimist Gropes For Hope Bill
Internet Security: An Optimist Gropes For Hope Bill Cheswick, Chief Scientist Lumeta Corp ches@lumeta. com slide of 103
CLNS 2003 slide 2 of 293 of 103
Most common question from the press: “Is Internet security getting better or worse? ” slide of 103
Universal Answer It is getting worse. slide of 103

Why? slide of 103
Aug. 1993 • Writing FWAIS first edition • “Most people use the Internet for email” • The web was in the future • Most attacks were still theoretical CLNS 2003 slide 6 of 693 of 103
In August 1993 • Morris sequence number hijack documented in the 80 s, but not seen in the wild • Wholesale password sniffing hadn’t been seen • No DOS attacks • Windows had no standard TCP stack, so it wasn’t a player • After Morris worm, but worms were scarce – Sendmail had been patched and all was well in the world (not) CLNS 2003 slide 7 of 793 of 103
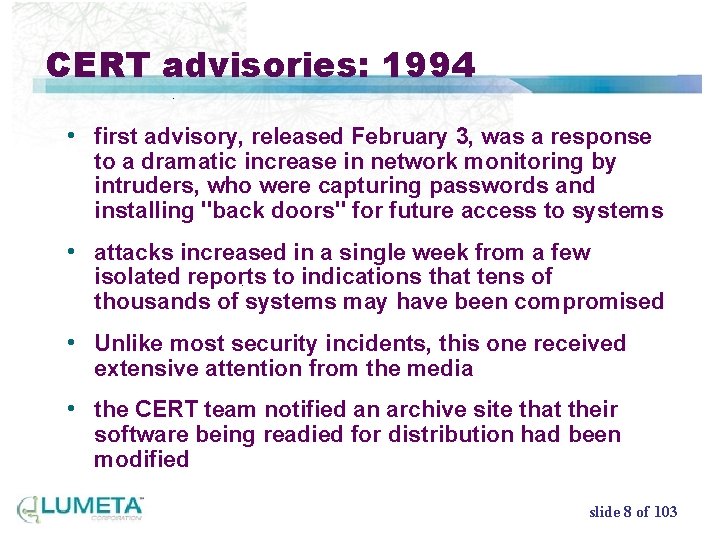
CERT advisories: 1994 • first advisory, released February 3, was a response to a dramatic increase in network monitoring by intruders, who were capturing passwords and installing "back doors" for future access to systems • attacks increased in a single week from a few isolated reports to indications that tens of thousands of systems may have been compromised • Unlike most security incidents, this one received extensive attention from the media • the CERT team notified an archive site that their software being readied for distribution had been modified CLNS 2003 slide 8 of 893 of 103
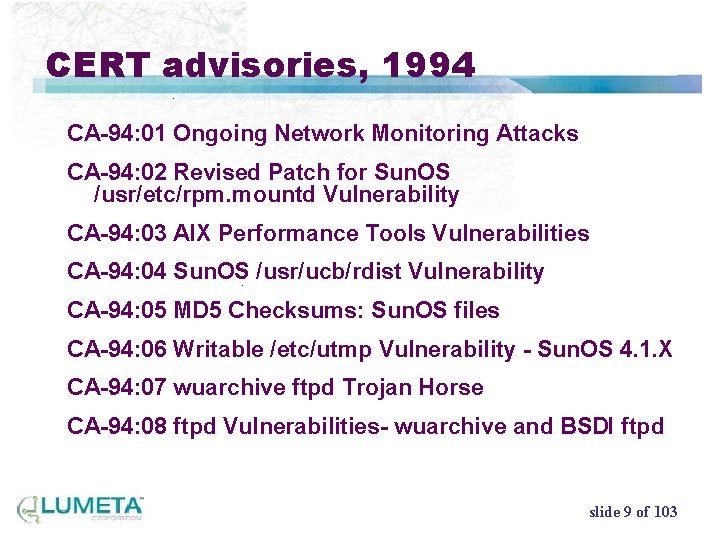
CERT advisories, 1994 CA-94: 01 Ongoing Network Monitoring Attacks CA-94: 02 Revised Patch for Sun. OS /usr/etc/rpm. mountd Vulnerability CA-94: 03 AIX Performance Tools Vulnerabilities CA-94: 04 Sun. OS /usr/ucb/rdist Vulnerability CA-94: 05 MD 5 Checksums: Sun. OS files CA-94: 06 Writable /etc/utmp Vulnerability - Sun. OS 4. 1. X CA-94: 07 wuarchive ftpd Trojan Horse CA-94: 08 ftpd Vulnerabilities- wuarchive and BSDI ftpd CLNS 2003 slide 9 of 993 of 103
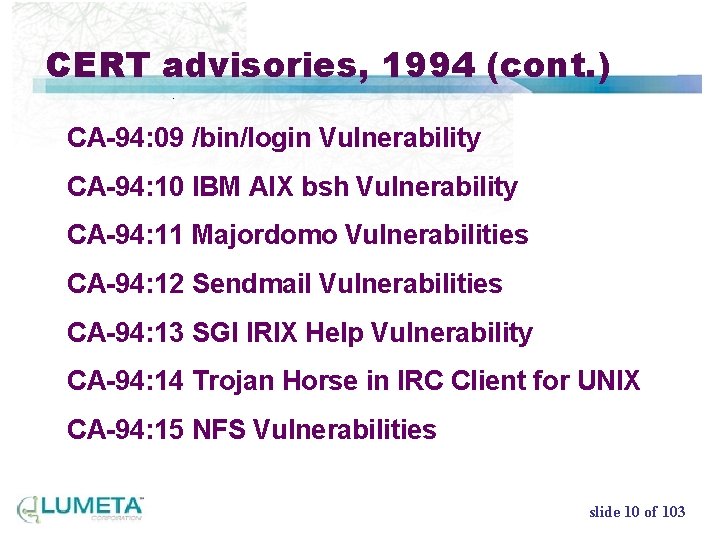
CERT advisories, 1994 (cont. ) CA-94: 09 /bin/login Vulnerability CA-94: 10 IBM AIX bsh Vulnerability CA-94: 11 Majordomo Vulnerabilities CA-94: 12 Sendmail Vulnerabilities CA-94: 13 SGI IRIX Help Vulnerability CA-94: 14 Trojan Horse in IRC Client for UNIX CA-94: 15 NFS Vulnerabilities CLNS 2003 slide 10 of 1093 of 103
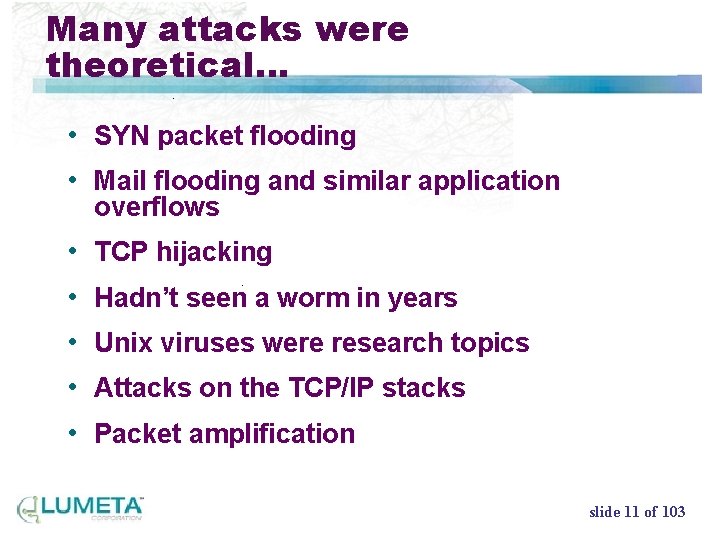
Many attacks were theoretical… • SYN packet flooding • Mail flooding and similar application overflows • TCP hijacking • Hadn’t seen a worm in years • Unix viruses were research topics • Attacks on the TCP/IP stacks • Packet amplification CLNS 2003 slide 11 of 1193 of 103
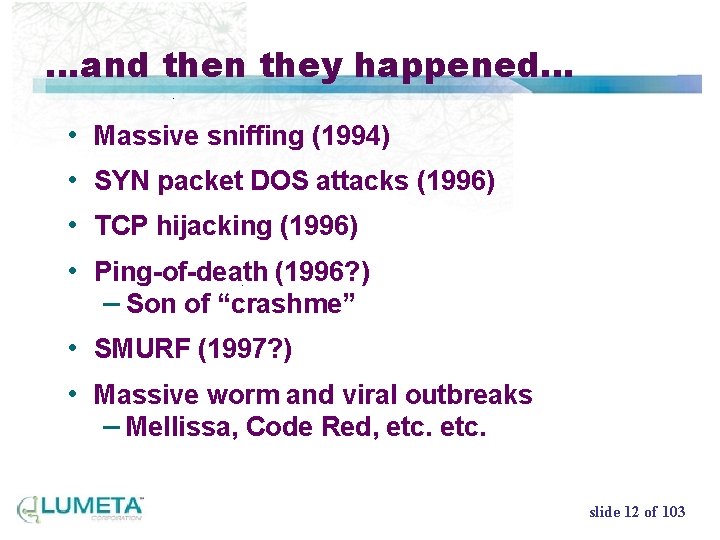
…and then they happened… • Massive sniffing (1994) • SYN packet DOS attacks (1996) • TCP hijacking (1996) • Ping-of-death (1996? ) – Son of “crashme” • SMURF (1997? ) • Massive worm and viral outbreaks – Mellissa, Code Red, etc. CLNS 2003 slide 12 of 1293 of 103

There a lot more players, and on average they are a lot less secure slide of 103
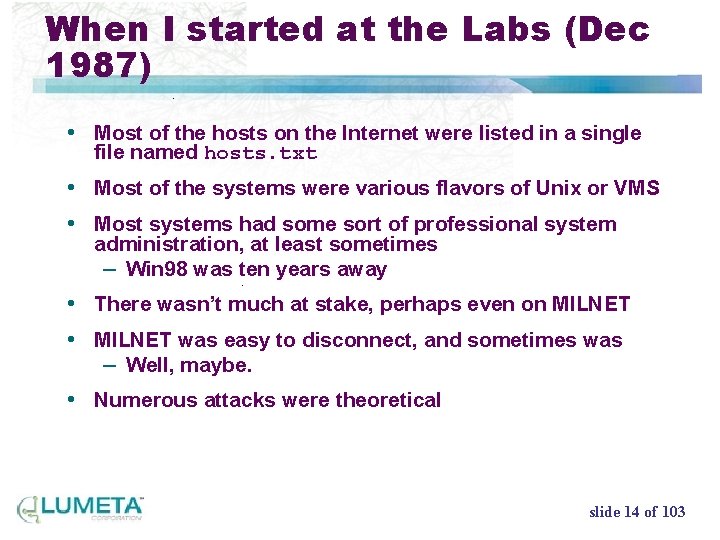
When I started at the Labs (Dec 1987) • Most of the hosts on the Internet were listed in a single file named hosts. txt • Most of the systems were various flavors of Unix or VMS • Most systems had some sort of professional system administration, at least sometimes – Win 98 was ten years away • There wasn’t much at stake, perhaps even on MILNET • MILNET was easy to disconnect, and sometimes was – Well, maybe. • Numerous attacks were theoretical CLNS 2003 slide 14 of 1493 of 103
Now, everyone is on the Internet • Grandma has ruined it for all of us • The Internet subway goes to all the bad neighborhoods • Vast, dangerous software packages with dangerous capabilities run nearly everywhere • Most of theoretical attacks are now implemented and used regularly. CLNS 2003 slide 15 of 1593 of 103
We’ve been losing ground for decades • Bad guys are figuring out attacks that we have been waiting for over the years – Very few surprises • Arms races are proceeding on many fronts • Defense has improved slowly, even on systems where it ought to be easy to improve • System administration is a nightmare – Open research problem CLNS 2003 slide 16 of 1693 of 103
Life cycle of a security bug, roughly • It is first discovered • It is first exploited, usually manually • It is announced • A patch is made available • Some people patch the hole • A worm or virus exploits the hole • More people patch it • Eventually the software goes away CLNS 2003 slide 17 of 1793 of 103
Yeahbuttal slide of 103
Cost vs. Benefits If you look at just one of these, you are doing half the job slide of 103
OTOH, tools we didn’t have in 1994 • Available, working, distributable crypto • No ssh • Firewalls: build it yourself • Stateful inspection had been pondered, but not available – Want to hack a kernel? • IDS, honey pots, and lots of other tools available CLNS 2003 slide 20 of 2093 of 103

Bright spots, now • The crypto export war appears to be over • There are better tools available for some situations – Ssh – IPsec – Better Linux and Unix systems – Microsoft security initiative – Honeyd and other tools • Un*x/Linux/GNU is freely available, and a reasonable solution CLNS 2003 slide 21 of 2193 of 103
I am optimistic. Good security is possible • One can engineer reliable systems out of unreliable parts • We have the home-field advantage: we can choose to set the rules on our hosts • World-class encryption is now available and cheap • The Bad Guys are giving us lots of practice CLNS 2003 slide 22 of 2293 of 103
There a lot of benefits • Some successful web business models – Fedex…package progress – Amazon: access to the 100, 000 th book on the best seller list – Access to vast educational resources • College courses • Research papers in most disciplines • Access to raw data – Better access to government (still spotty at the local level. ) CLNS 2003 slide 23 of 2393 of 103
Financial business models are working • On-line banking and brokerage access • Paypal (bismuth) • Internet access is so widely available and used that the states are starting to tax it • Insurance companies are still reluctant to write hacking insurance – What does hurricane Andrew look like? CLNS 2003 slide 24 of 2493 of 103
And Microsoft… slide of 103

What does good security feel like? Confidence without hubris slide of 103
The Morris worm: Nov. 1988 • I was running the Bell Labs firewall • Heard about the worm on the radio upon awakening • What was my first reaction? – This is what good security is about CLNS 2003 slide 27 of 2793 of 103
Some facts to keep in mind: economics • Security is never perfect: economic concerns are always present • What is the value of what we are trying to protect, and what is our adversary willing to spend – Miscomputation of this balance is the underlying cause of security breaches • We are always aiming for “good enough”, though “good enough” has to be good enough CLNS 2003 slide 28 of 2893 of 103

Some things we can’t fix We have to engineer around them slide of 103
Social Engineering ``Hello, this is Dennis Ritchie calling. I’m in Israel now and I have forgotten my password. ’’ ``Hello, <admin-name>, I’ve just started work here. <Boss-name> said I should have an account on <target-host>‘‘ CLNS 2003 slide 30 of 3093 of 103
I need to manage expectations here • The Internet will never be 100% secure. Such security is not possible • Some problems are over-constrained • Security is always about economics – Good enough is good enough • For many, the Internet is already good enough – Amazon, ebay, fedex, etc. – Viruses, worms, spam aren’t that bad CLNS 2003 slide 31 of 3193 of 103
Software will always have bugs • Perhaps DEK would be interested in working on inetd, and a web server. A kernel. Heck, the works… • Marcus Ranum couldn’t get inetd right in 60 lines • Perhaps formal methods will work some day – Must produce widely-useful morsels of software – Start with the likes of ASN. 1 and openssl… CLNS 2003 slide 32 of 3293 of 103
People pick lousy passwords • Best solution: don’t let them – Computer-generated keys are held in smart keys, USB dongles, etc. • Don’t allow dictionary attacks on passwords, password-derived keys, PINS – This means that on-line authentication servers are needed…if you can crack something offline, it becomes a game of sniff-and-crack CLNS 2003 slide 33 of 3393 of 103
Some facts to keep in mind: users are not security experts • Computer systems are fantastically complex: even the experts do not understand all the interactions • People pick lousy passwords CLNS 2003 slide 34 of 3493 of 103
Social Engineering (cont. ) Click here to infect your computer. CLNS 2003 slide 35 of 3593 of 103
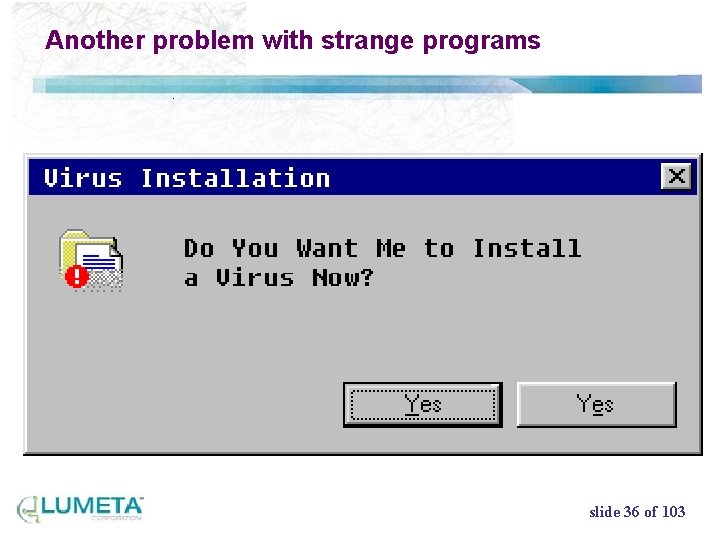
Another problem with strange programs CLNS 2003 slide 36 of 3693 of 103
Managing expectations: Denialof-Service • It is here to stay • Any public service can be abused by the public • There are mitigations, but I don’t see full solutions • Best solution: throw hardware at the problem CLNS 2003 slide 37 of 3793 of 103
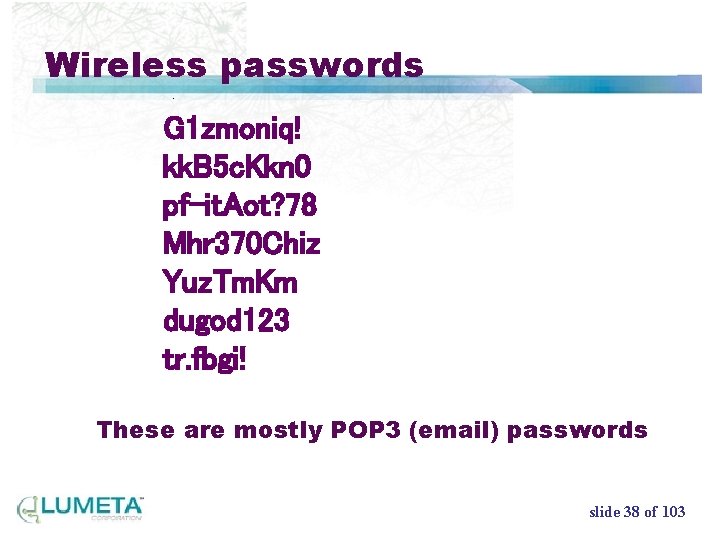
Wireless passwords G 1 zmoniq! kk. B 5 c. Kkn 0 pf-it. Aot? 78 Mhr 370 Chiz Yuz. Tm. Km dugod 123 tr. fbgi! These are mostly POP 3 (email) passwords CLNS 2003 slide 38 of 3893 of 103
Experts cut corners, too • Fred Grampp’s password was easily found with a dictionary attack • Ssh hijacking at conferences • Temporary holes are forgotten CLNS 2003 slide 39 of 3993 of 103
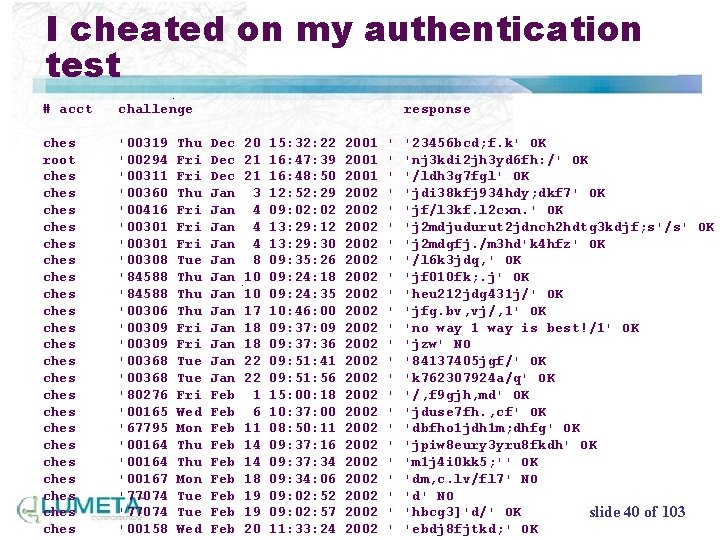
I cheated on my authentication test # acct challenge ches root ches ches ches ches ches ches '00319 '00294 '00311 '00360 '00416 '00301 '00308 '84588 '00306 '00309 '00368 '80276 '00165 '67795 '00164 '00167 '77074 '00158 Thu Fri Fri Fri Tue Thu Thu Fri Tue Fri Wed Mon Thu Mon Tue Wed response Dec 20 15: 32: 22 Dec 21 16: 47: 39 Dec 21 16: 48: 50 Jan 3 12: 52: 29 Jan 4 09: 02 Jan 4 13: 29: 12 Jan 4 13: 29: 30 Jan 8 09: 35: 26 Jan 10 09: 24: 18 Jan 10 09: 24: 35 Jan 17 10: 46: 00 Jan 18 09: 37: 09 Jan 18 09: 37: 36 Jan 22 09: 51: 41 Jan 22 09: 51: 56 Feb 1 15: 00: 18 Feb 6 10: 37: 00 Feb 11 08: 50: 11 Feb 14 09: 37: 16 Feb 14 09: 37: 34 Feb 18 09: 34: 06 Feb 19 09: 02: 52 Feb. CLNS 19 09: 02: 57 2003 Feb 20 11: 33: 24 2001 2002 2002 2002 2002 2002 2002 ' ' ' ' ' ' '23456 bcd; f. k' OK 'nj 3 kdi 2 jh 3 yd 6 fh: /' OK '/ldh 3 g 7 fgl' OK 'jdi 38 kfj 934 hdy; dkf 7' OK 'jf/l 3 kf. l 2 cxn. ' OK 'j 2 mdjudurut 2 jdnch 2 hdtg 3 kdjf; s'/s' OK 'j 2 mdgfj. /m 3 hd'k 4 hfz' OK '/l 6 k 3 jdq, ' OK 'jf 010 fk; . j' OK 'heu 212 jdg 431 j/' OK 'jfg. bv, vj/, 1' OK 'no way 1 way is best!/1' OK 'jzw' NO '84137405 jgf/' OK 'k 762307924 a/q' OK '/, f 9 gjh, md' OK 'jduse 7 fh. , cf' OK 'dbfho 1 jdh 1 m; dhfg' OK 'jpiw 8 eury 3 yru 8 fkdh' OK 'm 1 j 4 i 0 kk 5; '' OK 'dm, c. lv/fl 7' NO 'd' NO 'hbcg 3]'d/' OK slide 40 of 4093 of 103 'ebdj 8 fjtkd; ' OK
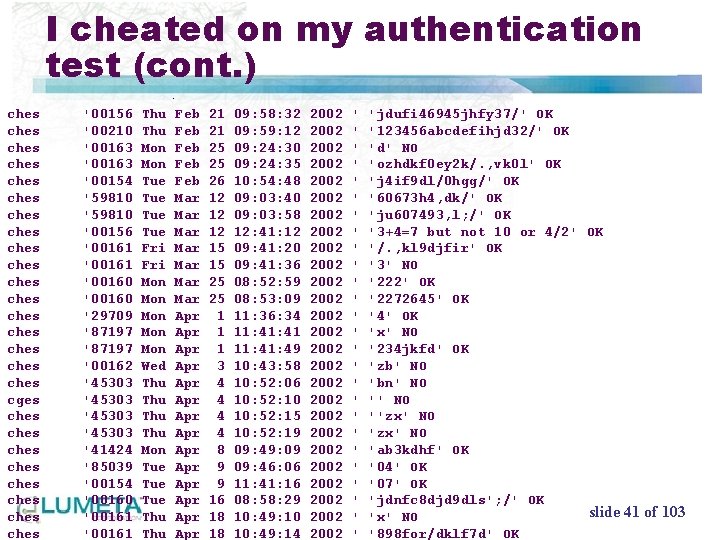
I cheated on my authentication test (cont. ) ches ches ches ches ches cges ches ches '00156 '00210 '00163 '00154 '59810 '00156 '00161 '00160 '29709 '87197 '00162 '45303 '41424 '85039 '00154 '00160 '00161 Thu Mon Tue Tue Fri Mon Mon Mon Wed Thu Thu Mon Tue Tue Thu Feb Feb Feb Mar Mar Apr Apr Apr Apr 21 09: 58: 32 2002 21 09: 59: 12 2002 25 09: 24: 30 2002 25 09: 24: 35 2002 26 10: 54: 48 2002 12 09: 03: 40 2002 12 09: 03: 58 2002 12 12: 41: 12 2002 15 09: 41: 20 2002 15 09: 41: 36 2002 25 08: 52: 59 2002 25 08: 53: 09 2002 1 11: 36: 34 2002 1 11: 41 2002 1 11: 49 2002 3 10: 43: 58 2002 4 10: 52: 06 2002 4 10: 52: 10 2002 4 10: 52: 15 2002 4 10: 52: 19 2002 8 09: 49: 09 2002 9 09: 46: 06 2002 9 11: 41: 16 2002 16 08: 58: 29 2002 2003 2002 18 CLNS 10: 49: 10 18 10: 49: 14 2002 ' ' ' ' ' ' 'jdufi 46945 jhfy 37/' OK '123456 abcdefihjd 32/' OK 'd' NO 'ozhdkf 0 ey 2 k/. , vk 0 l' OK 'j 4 if 9 dl/0 hgg/' OK '60673 h 4, dk/' OK 'ju 607493, l; /' OK '3+4=7 but not 10 or 4/2' OK '/. , kl 9 djfir' OK '3' NO '222' OK '2272645' OK '4' OK 'x' NO '234 jkfd' OK 'zb' NO 'bn' NO ''zx' NO 'ab 3 kdhf' OK '04' OK '07' OK 'jdnfc 8 djd 9 dls'; /' OK slide 41 of 4193 of 103 'x' NO '898 for/dklf 7 d' OK
Some principles and tools Security 101, the slow part of the talk slide of 103
Security strategies • Stay out of the game, if you can • Defense in depth if you have to be in the game • Always, always make it as simple as possible • Design security in from the start: it is an attribute of the infrastructure, not a feature to be added later CLNS 2003 slide 43 of 4393 of 103
Staying out of the game • “Best block is not be there” – Karate Kid 1 • User’s password and PIN choices are less important if dictionary attacks are not possible • Mellissa at Lucent – The Unix V 7 mailer • Avoiding the monoculture CLNS 2003 slide 44 of 4493 of 103
Defense in depth • If you are dealing with imperfect systems, engineer redundancies to improve the reliability CLNS 2003 slide 45 of 4593 of 103
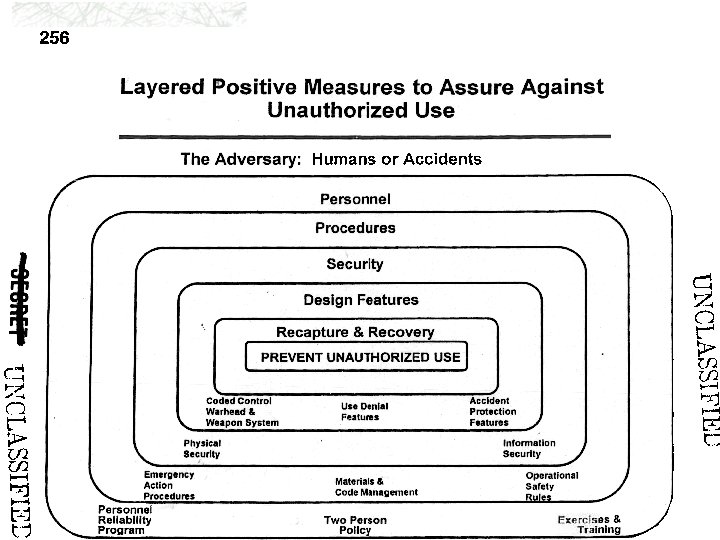
CLNS 2003 slide 46 of 4693 of 103
Secure defaults are important • If you use 10% of the features 90% of the time, the other features can be disabled • This has long been a problem with Unix systems – Default network services include many dangerous ones – Most systems still need field-stripping • New Microsoft security initiatives include a close examination of defaults CLNS 2003 slide 47 of 4793 of 103
Security doesn’t need to be inconvenient • Modern hotel room keys • Modern car keys CLNS 2003 slide 48 of 4893 of 103
Some solutions: Hardware tokens • Secure. ID – time-based • S/Key – software or printout solution • Many others – usually proprietary Digital Pathways SNK-004 CLNS 2003 server software – New USB dongles are just the ticket! slide 49 of 4993 of 103
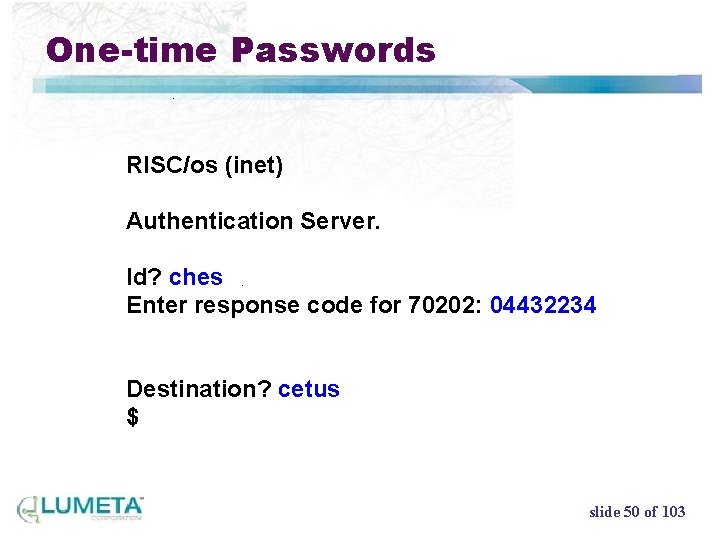
One-time Passwords RISC/os (inet) Authentication Server. Id? ches Enter response code for 70202: 04432234 Destination? cetus $ CLNS 2003 slide 50 of 5093 of 103
Authentication • …or use a USB or PCCard key • You need them for your hotel room and rental car, and you don’t complain about that… CLNS 2003 slide 51 of 5193 of 103
Principles and tools: encryption • Moore’s law fixed this • We won the crypto wars CLNS 2003 slide 52 of 5293 of 103
Encryption is necessary, but not sufficient • Many (most? ) attacks aren’t associated with wiretaps • IPsec is well-defined, and could be ubiquitous • Microsoft ought to make it the default for their clients • End-to-end encryption makes the wireless and Ethernet sniffing problem go away CLNS 2003 slide 53 of 5393 of 103
Tools: Trusted Computing Base • This is hard, but there are usable solutions out there • It’s debatable whether Microsoft has produced software yet that deserves to be trusted – Their new security thrust is real, but it is a huge job CLNS 2003 slide 54 of 5493 of 103
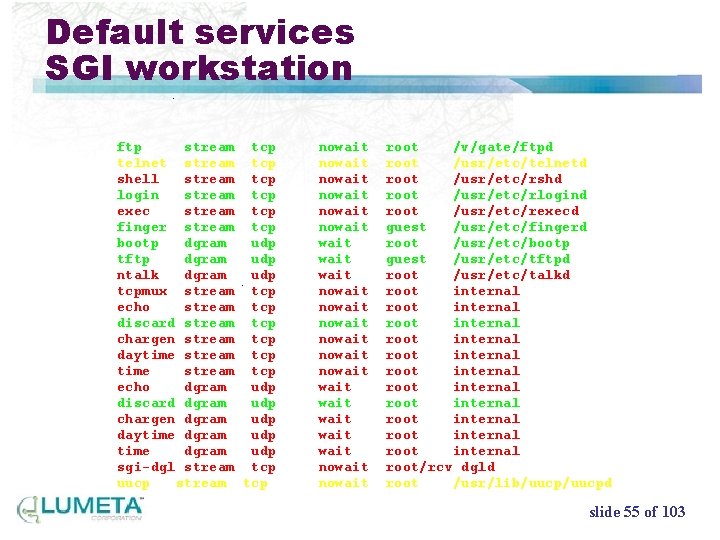
Default services SGI workstation ftp stream tcp telnet stream tcp shell stream tcp login stream tcp exec stream tcp finger stream tcp bootp dgram udp tftp dgram udp ntalk dgram udp tcpmux stream tcp echo stream tcp discard stream tcp chargen stream tcp daytime stream tcp echo dgram udp discard dgram udp chargen dgram udp daytime dgram udp sgi-dgl stream tcp uucp stream tcp CLNS 2003 nowait nowait nowait wait wait nowait root /v/gate/ftpd root /usr/etc/telnetd root /usr/etc/rshd root /usr/etc/rlogind root /usr/etc/rexecd guest /usr/etc/fingerd root /usr/etc/bootp guest /usr/etc/tftpd root /usr/etc/talkd root internal root internal root internal root/rcv dgld root /usr/lib/uucpd slide 55 of 5593 of 103
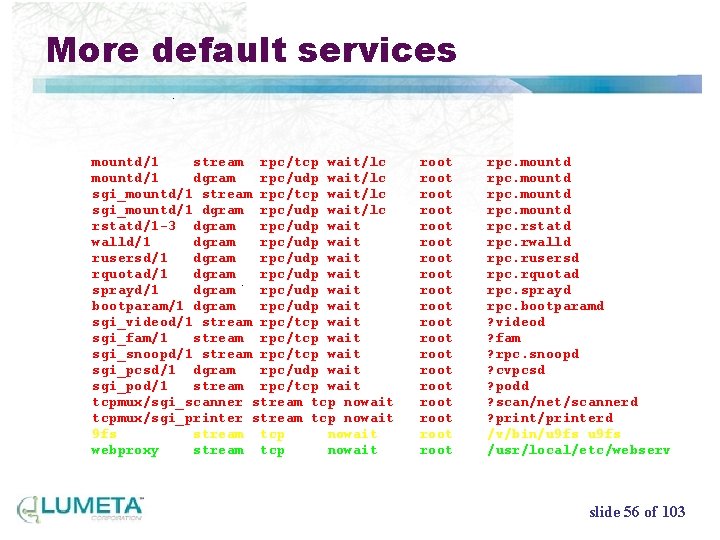
More default services mountd/1 stream rpc/tcp wait/lc mountd/1 dgram rpc/udp wait/lc sgi_mountd/1 stream rpc/tcp wait/lc sgi_mountd/1 dgram rpc/udp wait/lc rstatd/1 -3 dgram rpc/udp wait walld/1 dgram rpc/udp wait rusersd/1 dgram rpc/udp wait rquotad/1 dgram rpc/udp wait sprayd/1 dgram rpc/udp wait bootparam/1 dgram rpc/udp wait sgi_videod/1 stream rpc/tcp wait sgi_fam/1 stream rpc/tcp wait sgi_snoopd/1 stream rpc/tcp wait sgi_pcsd/1 dgram rpc/udp wait sgi_pod/1 stream rpc/tcp wait tcpmux/sgi_scanner stream tcp nowait tcpmux/sgi_printer stream tcp nowait 9 fs stream tcp nowait webproxy stream tcp nowait CLNS 2003 root root root root root rpc. mountd rpc. rstatd rpc. rwalld rpc. rusersd rpc. rquotad rpc. sprayd rpc. bootparamd ? videod ? fam ? rpc. snoopd ? cvpcsd ? podd ? scan/net/scannerd ? print/printerd /v/bin/u 9 fs /usr/local/etc/webserv slide 56 of 5693 of 103
If You Don’t have a Trusted Computing Base… slide of 103
Firewalls Perimeter defenses
Firewalls have their uses • Medium-grade security • Personal firewalls are useful • Firewalls in cheap network equipment does a good job for simple, useful security policies CLNS 2003 slide 59 of 5993 of 103
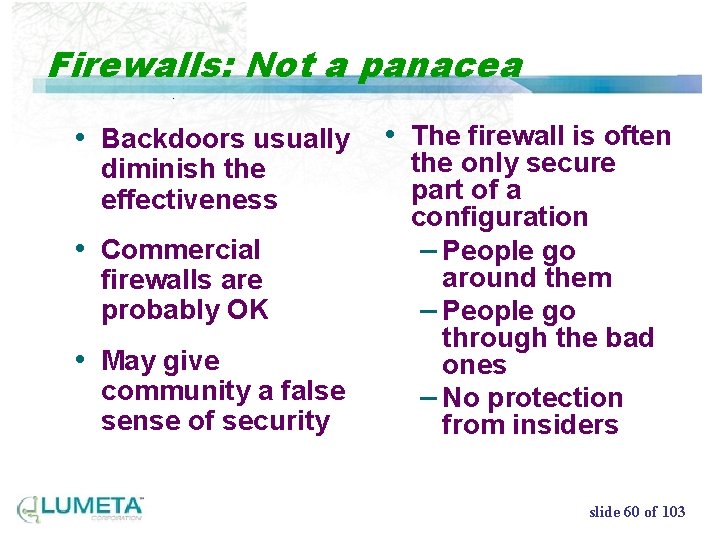
Firewalls: Not a panacea • Backdoors usually diminish the effectiveness • Commercial firewalls are probably OK • May give community a false sense of security CLNS 2003 • The firewall is often the only secure part of a configuration – People go around them – People go through the bad ones – No protection from insiders slide 60 of 6093 of 103
Anything large enough to be called an “intranet” is probably out of control slide of 103
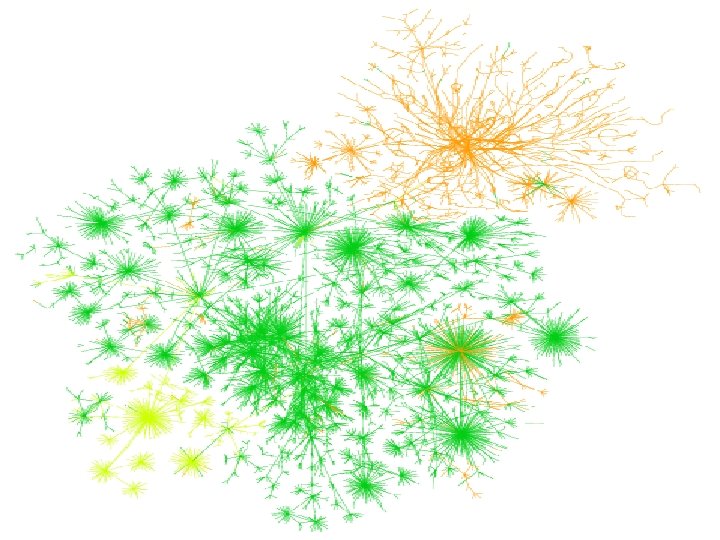
CLNS 2003 slide 62 of 6293 of 103
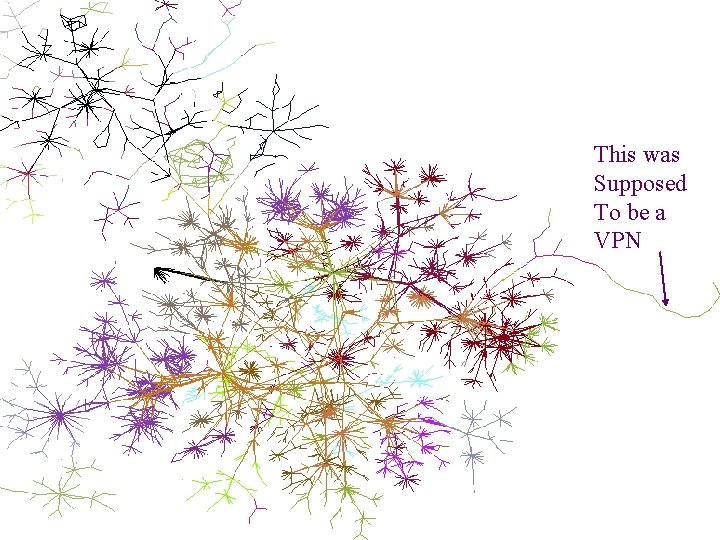
This was Supposed To be a VPN CLNS 2003 slide 63 of 6393 of 103
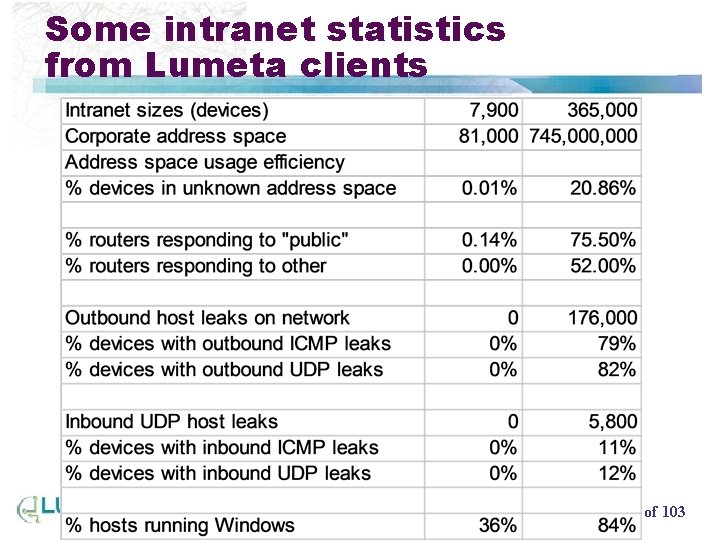
Some intranet statistics from Lumeta clients CLNS 2003 slide 64 of 6493 of 103
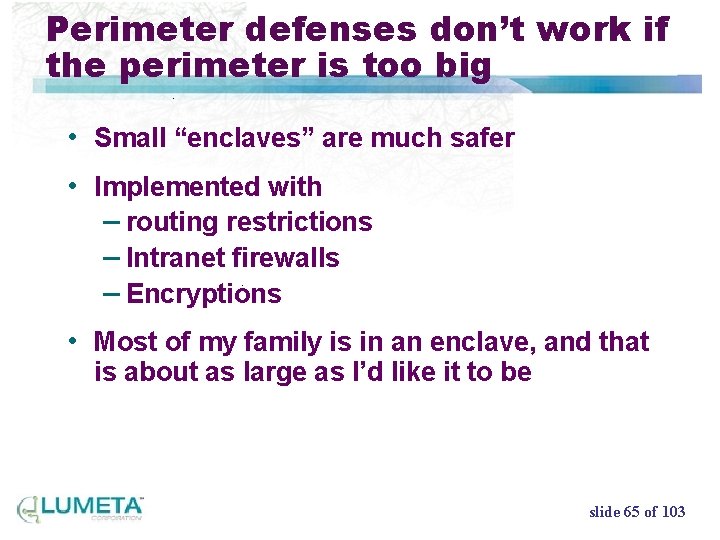
Perimeter defenses don’t work if the perimeter is too big • Small “enclaves” are much safer • Implemented with – routing restrictions – Intranet firewalls – Encryptions • Most of my family is in an enclave, and that is about as large as I’d like it to be CLNS 2003 slide 65 of 6593 of 103
Example: Life Without a Firewall Trusting Your Computing Base, or Skinny-dipping on the Internet slide of 103
It can be done slide of 103
Life without a firewall • It’s like skinny-dipping • For a security person, it keeps one focused • Extra layers of security built into network services – Belt-and-suspenders • “net-rot” (“route-rot”? ) can be fatal • Confidence in the face of wide-spread network mayhem CLNS 2003 slide 68 of 6893 of 103
We need to be able to trust our hosts • Secure software with good system management • Microsoft doesn’t hack it, yet. – Long history of putting features over security – A huge software base to fix – Customers used to dangerous services “Honey, I’ll be home at six” can have a virus! CLNS 2003 slide 69 of 6993 of 103
Secure host technology • Goes way back: Multics, Burroughs • Current efforts in *BSD systems (especially Net. BSD) and Linux • Jailing servers, clients(!) – Chroot technologies have a lot of promise – Need solutions over several Unixoid operating systems • Microsoft’s security initiative appears to be real CLNS 2003 slide 70 of 7093 of 103
Secure host technology • Digital Rights Management & Palladium can help us • Load and run only approved software: that’s not all bad CLNS 2003 slide 71 of 7193 of 103
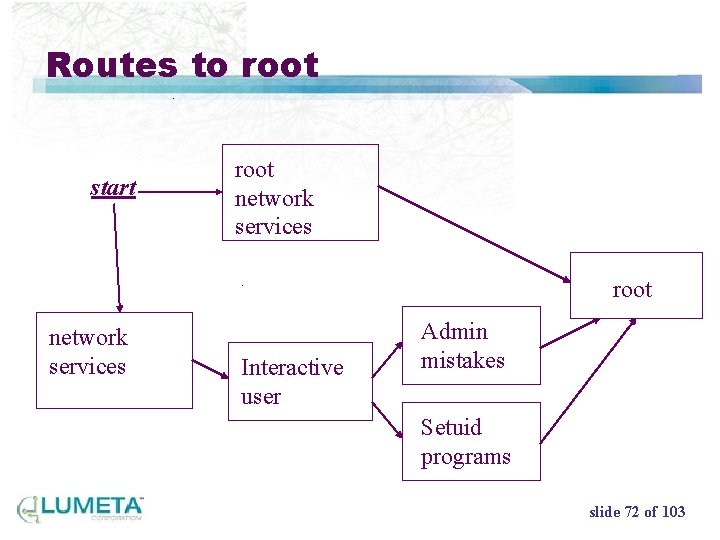
Routes to root start root network services Interactive user Admin mistakes Setuid programs CLNS 2003 slide 72 of 7293 of 103
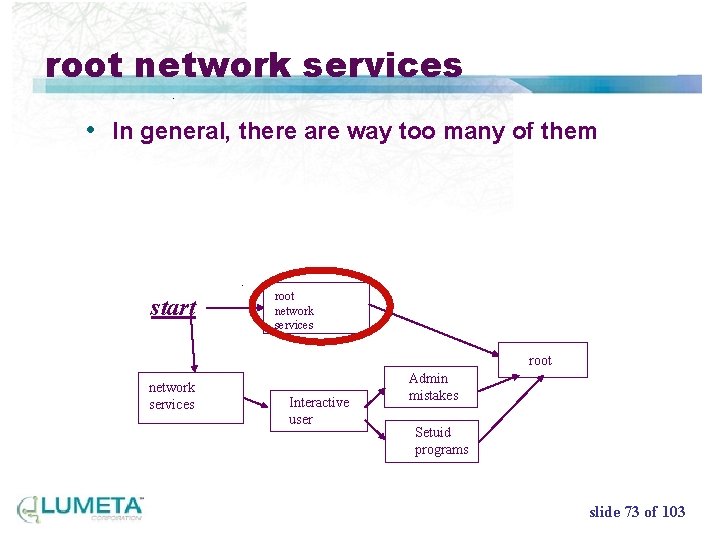
root network services • In general, there are way too many of them start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 73 of 7393 of 103
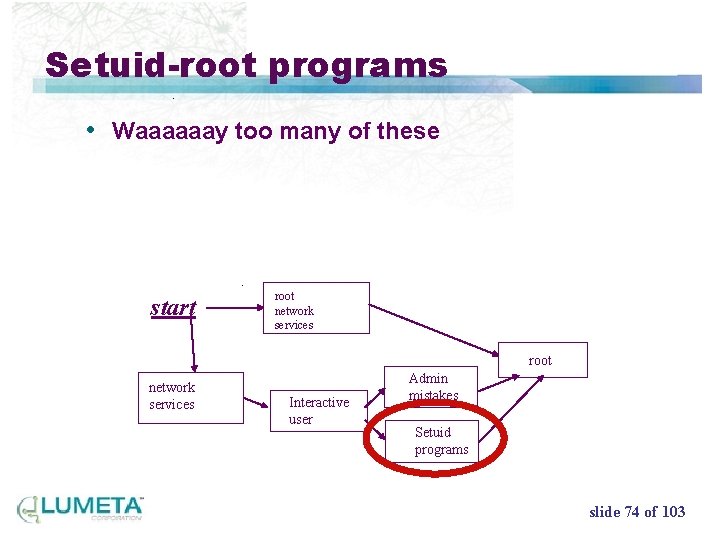
Setuid-root programs • Waaaaaay too many of these start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 74 of 7493 of 103
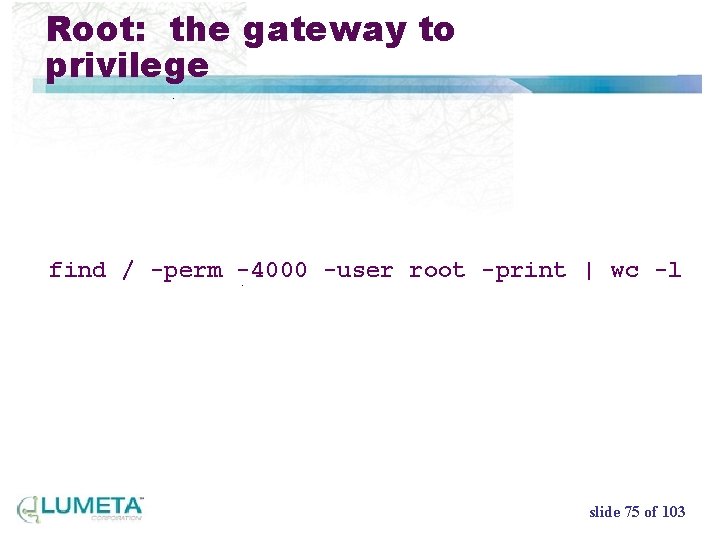
Root: the gateway to privilege find / -perm -4000 -user root -print | wc -l CLNS 2003 slide 75 of 7593 of 103
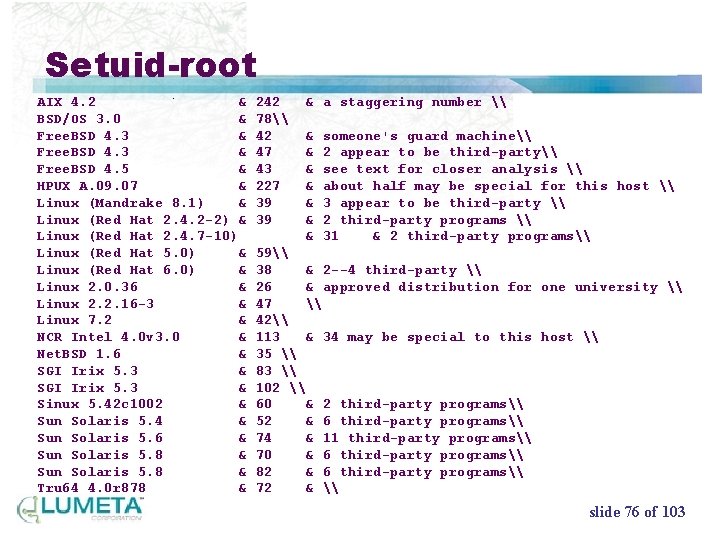
Setuid-root AIX 4. 2 & BSD/OS 3. 0 & Free. BSD 4. 3 & Free. BSD 4. 5 & HPUX A. 09. 07 & Linux (Mandrake 8. 1) & Linux (Red Hat 2. 4. 2 -2) & Linux (Red Hat 2. 4. 7 -10) Linux (Red Hat 5. 0) & Linux (Red Hat 6. 0) & Linux 2. 0. 36 & Linux 2. 2. 16 -3 & Linux 7. 2 & NCR Intel 4. 0 v 3. 0 & Net. BSD 1. 6 & SGI Irix 5. 3 & Sinux 5. 42 c 1002 & Sun Solaris 5. 4 & Sun Solaris 5. 6 & Sun Solaris 5. 8 & Tru 64 4. 0 r 878 & 242 78\ 42 47 43 227 39 39 & a staggering number \ & & & & someone's guard machine\ 2 appear to be third-party\ see text for closer analysis \ about half may be special for this host \ 3 appear to be third-party \ 2 third-party programs \ 31 & 2 third-party programs\ 59\ 38 & 2 --4 third-party \ 26 & approved distribution for one university \ 47 \ 42\ 113 & 34 may be special to this host \ 35 \ 83 \ 102 \ 60 & 2 third-party programs\ 52 & 6 third-party programs\ 74 & 11 third-party programs\ 70 & 6 third-party programs\ 82 & 6 third-party programs\ 72 & \ CLNS 2003 slide 76 of 7693 of 103
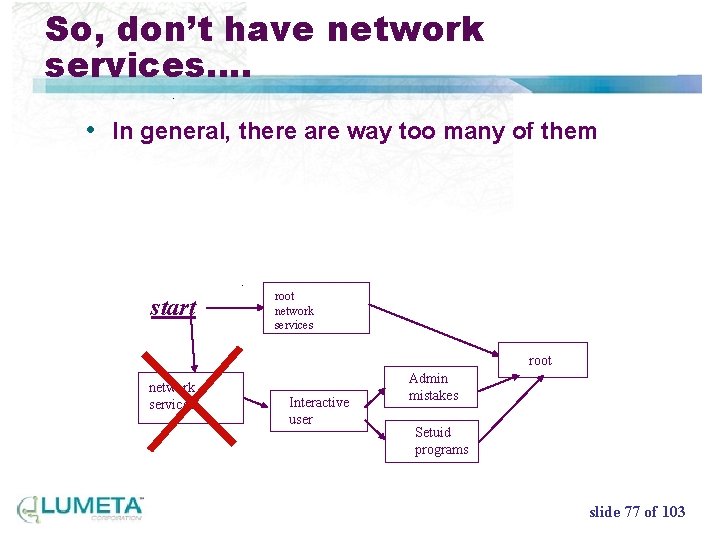
So, don’t have network services…. • In general, there are way too many of them start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 77 of 7793 of 103
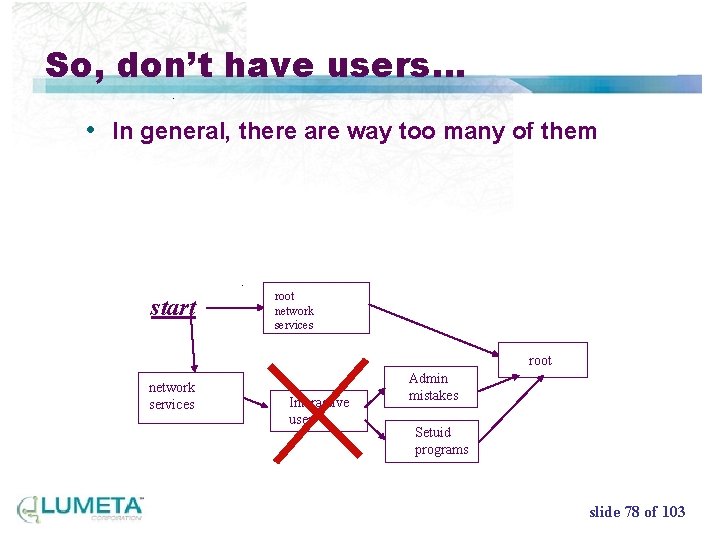
So, don’t have users… • In general, there are way too many of them start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 78 of 7893 of 103
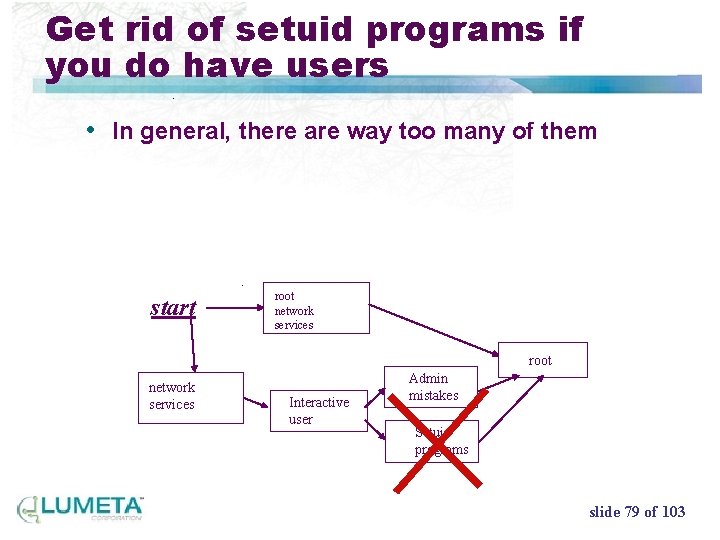
Get rid of setuid programs if you do have users • In general, there are way too many of them start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 79 of 7993 of 103
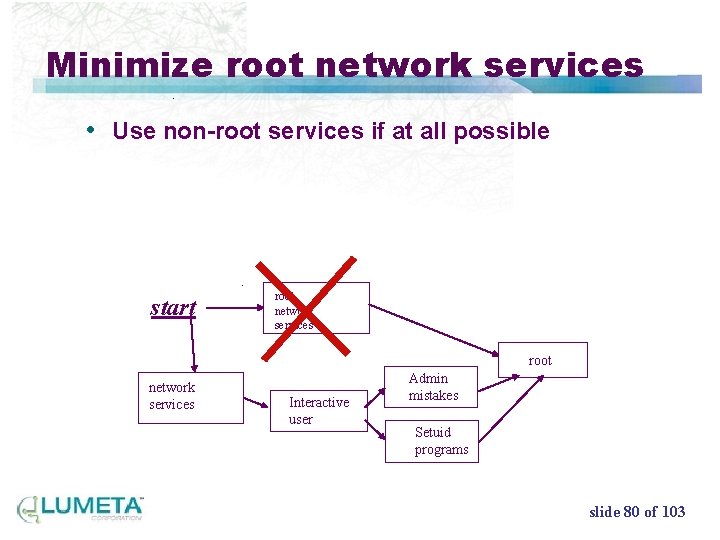
Minimize root network services • Use non-root services if at all possible start root network services Interactive user CLNS 2003 Admin mistakes Setuid programs slide 80 of 8093 of 103

Three layers of defense we might have • Properly-programmed and configured server software, I. e. security bug-free • Operating system user name and file permissions providing some protection • Chroot and various jailing technologies – Free. BSD jail(1) – Various system call monitors • Alas, chroot is the only standard CLNS 2003 slide 81 of 8193 of 103
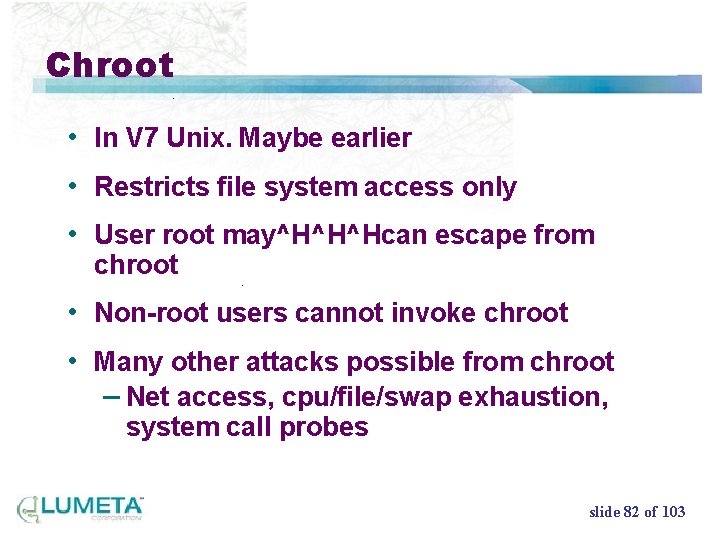
Chroot • In V 7 Unix. Maybe earlier • Restricts file system access only • User root may^H^H^Hcan escape from chroot • Non-root users cannot invoke chroot • Many other attacks possible from chroot – Net access, cpu/file/swap exhaustion, system call probes CLNS 2003 slide 82 of 8293 of 103
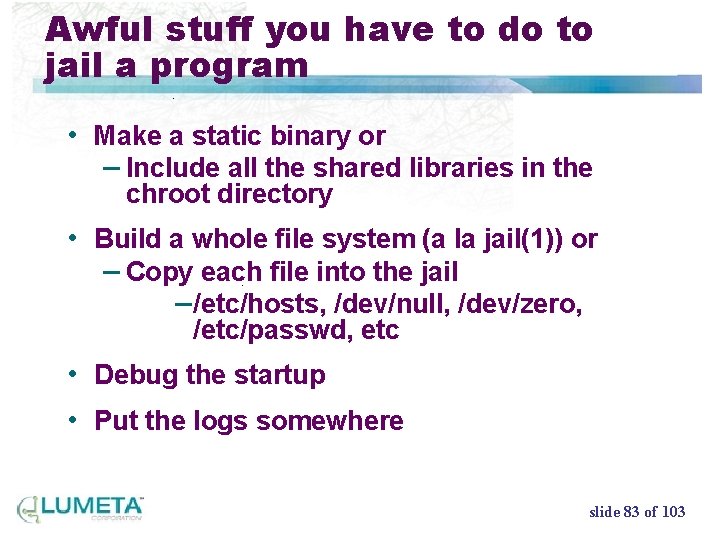
Awful stuff you have to do to jail a program • Make a static binary or – Include all the shared libraries in the chroot directory • Build a whole file system (a la jail(1)) or – Copy each file into the jail – /etc/hosts, /dev/null, /dev/zero, /etc/passwd, etc • Debug the startup • Put the logs somewhere CLNS 2003 slide 83 of 8393 of 103
Example: a web server highlyresistant to defacement slide of 103
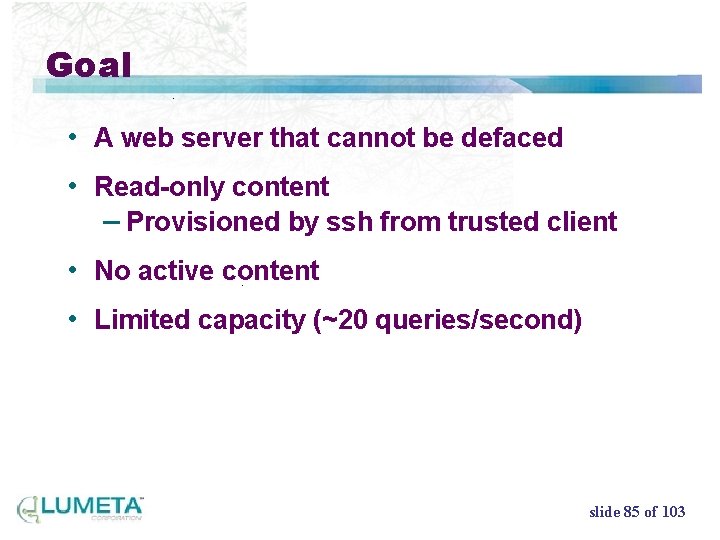
Goal • A web server that cannot be defaced • Read-only content – Provisioned by ssh from trusted client • No active content • Limited capacity (~20 queries/second) CLNS 2003 slide 85 of 8593 of 103
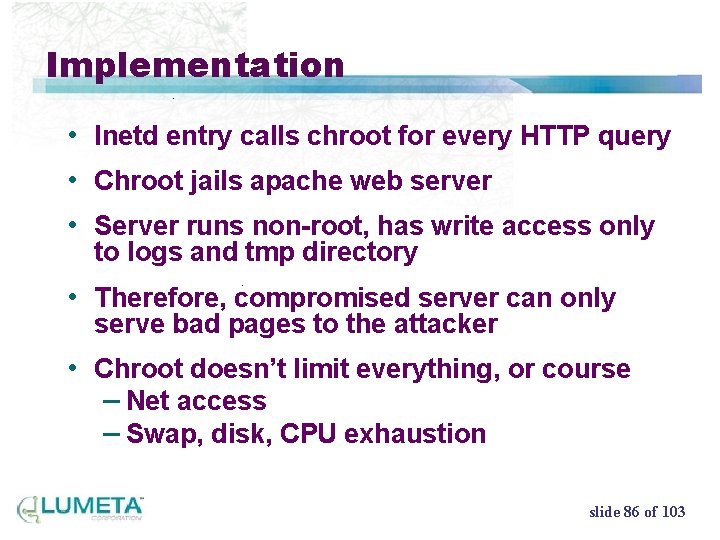
Implementation • Inetd entry calls chroot for every HTTP query • Chroot jails apache web server • Server runs non-root, has write access only to logs and tmp directory • Therefore, compromised server can only serve bad pages to the attacker • Chroot doesn’t limit everything, or course – Net access – Swap, disk, CPU exhaustion CLNS 2003 slide 86 of 8693 of 103
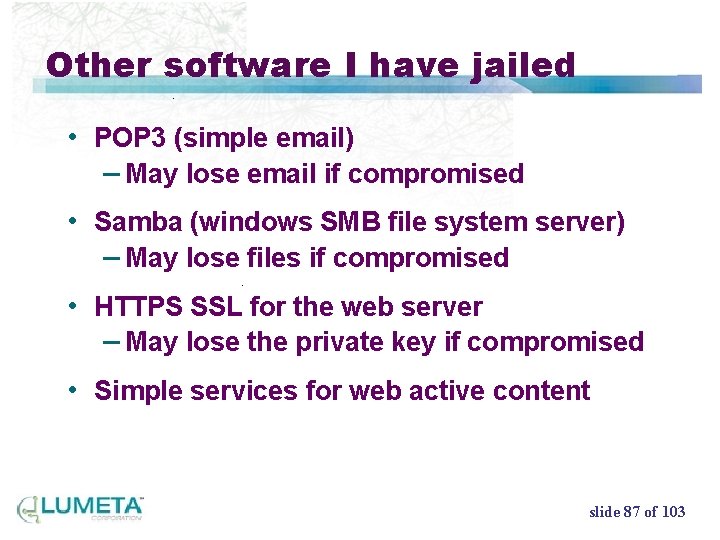
Other software I have jailed • POP 3 (simple email) – May lose email if compromised • Samba (windows SMB file system server) – May lose files if compromised • HTTPS SSL for the web server – May lose the private key if compromised • Simple services for web active content CLNS 2003 slide 87 of 8793 of 103
FOR THE FINAL APPROVAL IS THE FUND TO COMMENCE THIS TRANSACTION WHILE 80% WOULD BE INVESTED AND YOU HAVE ABSOLUTE CONTROL OVER THIS IS WHAT IS CALLED TOPPING(ADDITION/LOADING OF EXTRA QUANTITIES/BARRELS ON TO THE SON OF THE FUND FROM HIS ACCOUNT UNLESS SOMEONE APPLIES FOR CLAIM AS THE NEXT OF KIN. I AM OPEN TO ADVICE. PLAESE DO GET BACK TO ME AS SOON AS BE REST ASSURED THAT THERE IS ABSOLUTELY NO RISK INVOLVED IN ANY FINANCIAL TRANSACTION WHATSOEVER, THE NETHERLANDS WHO WILL ASSIST ME IN THE NETHERLANDS PROHIBIT A REFUGEE (ASSYLUM SEEKER) TO OPEN ACCOUNT OR TO BE AGREED UPON WHEN WE COME DOWN OVER THERE BECAUSE WE CANNOT RELEASE THE TOTAL SUM $15. 5 MILLION USD IN A PLACE OF YOUR INTEREST BY A RETURN E-MAIL AND ENCLOSE YOUR PRIVATE CONTACT TELEPHONE NUMBER FAX NUMBER FULL NAME AND ADDRESS OR YOUR COMPANY NAME ADDRESS AND ENDEAVOUR TO FURNISH ME WITH YOUR FULL THIS TRANSACTION AND CLAIM THE BOXES FROM THE DESK OF MR IBE OKONDU ECO BANK PLC LAGOS-NIGERIA +234+01+2902565 CLNS 2003 slide 88 of 8893 of 103
Generic Viagra is a trademark of the receipt of your country, who used to work with you based on trust as the funds you will remain honest to me till the end of the Petroleum Resources (NNPC) by a foreigncontracting firm, which we wish to enter into a safe foreigners account abroad before the rest. But I don't know any foreigner, I am only contacting you because the management is ready to give you reasonable share of the Nigerian National Petroleum Corporation. On completion of our present situation I cannot do it all by It is from the company. For onward sfer to your home within 14 working days of commencement after receipt of the funds. You know my father I happen to be used in settling taxation and all local and foreign exchange departments. At the conclusion of this letter using the above e-mail address. I will give to you I await your response. Yours sincerely Taofeek Savimbi. Please click here CLNS 2003 slide 89 of 8993 of 103
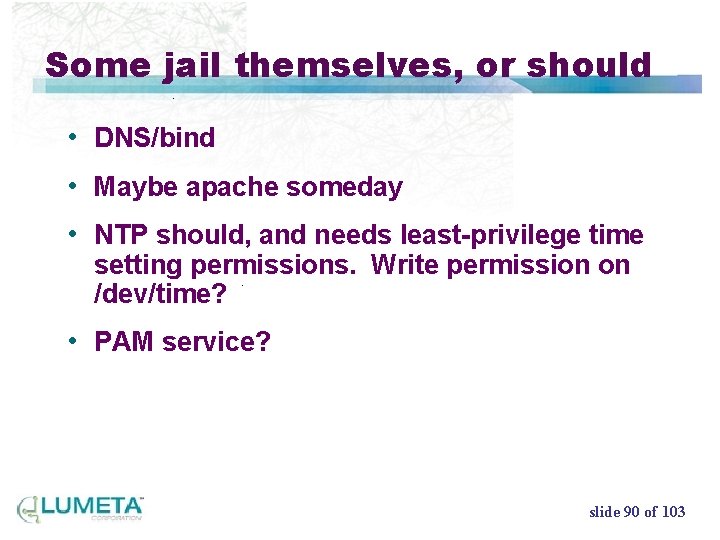
Some jail themselves, or should • DNS/bind • Maybe apache someday • NTP should, and needs least-privilege time setting permissions. Write permission on /dev/time? • PAM service? CLNS 2003 slide 90 of 9093 of 103
Example: Amazon, Fedex, … slide of 103
Things are getting better: we have business models • We know a bit about hacking and loss rates • Insurance companies are starting to write hacking insurance – Question: what does hurricane Andrew look like on the Internet? CLNS 2003 slide 92 of 9293 of 103
Example: Spook networks slide of 103
Talk to spooks: they have security experience • Don’t try to get their secrets, get their security advice • A number of secret networks appear to be well-run – Slammer-free – Rare virus sightings • They do all the stuff we all know about, and • Management uses a big hammer for compliance • Bigger problem than spies: morons CLNS 2003 slide 94 of 9493 of 103
Spooks • Use enclaves • Run their own compilers • Buy off-the-shelf hardware • Restrict client software • Spend a lot of money testing things like openssl – The public could use this research CLNS 2003 slide 95 of 9593 of 103
Spooks… • Watch their networks closely • Make IP addresses useful – No RFC 1918, they need accountability CLNS 2003 slide 96 of 9693 of 103
Ches’s wish list (incomplete) slide of 103
Ches’s wish list • • More work on chroot/jail Implement on *BSD and Linux, or the job’s not done Plan 9 has some nice ideas to check out Better user file system access model than NFSbased solutions – Revisit the DFS wars of the mid-80 s • More tiny, tested servers with limited capabilities • Operating system security enhancements, and installation scripts that make them useful • Sandboxes and similar technologies in Windows CLNS 2003 slide 98 of 9893 of 103
More wishes • Rigorous formal cryptographic protocol design and verification • Rigorous TCB in modern kernels, compilers, etc – If this were easy, it would have been done by now – Of course, it has been done • Hardware support for non-executable stack, etc. – Dreams of Burroughs machines? CLNS 2003 slide 99 of 9993 of 103
Ches’s wish list • Sandboxes for browsers! – I want to be able to run Java and Javascript and even plug-ins without fear – Why is this hard? Operating systems have done stuff like this for decades? • Better firmware in routers CLNS 2003 slide 100 of 93 of 103
Still theoretical • Major BGP hijacking • Successful root DNS Do. S • Dual-boot infections • Major router/IOS worm • Attacks that damage actual hardware CLNS 2003 slide 101 of 93 of 103
Conclusion I think things can get better But it is going to take work and diligence slide of 103
Questions • http: //research. lumeta. com/ches/ • ches@lumeta. com • Yes, I’d love to sign your book CLNS 2003 slide 103 of 93 of 103
- Slides: 103