Understanding ContentionBased Channels and Using Them for Defense
Understanding Contention-Based Channels and Using Them for Defense Casen Hunger Alex Dimakis Ankit Rawat Mikhail Kazdagli Mohit Tiwari Sriram Vishwanath HPCA 2015 The University of Texas at Austin
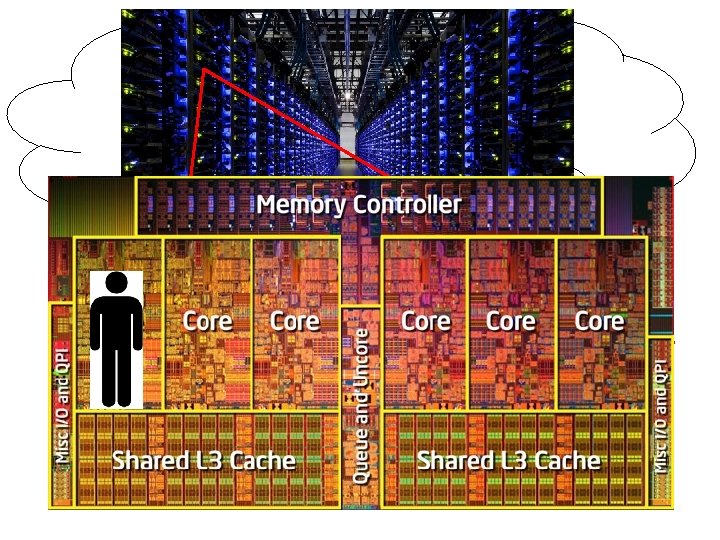
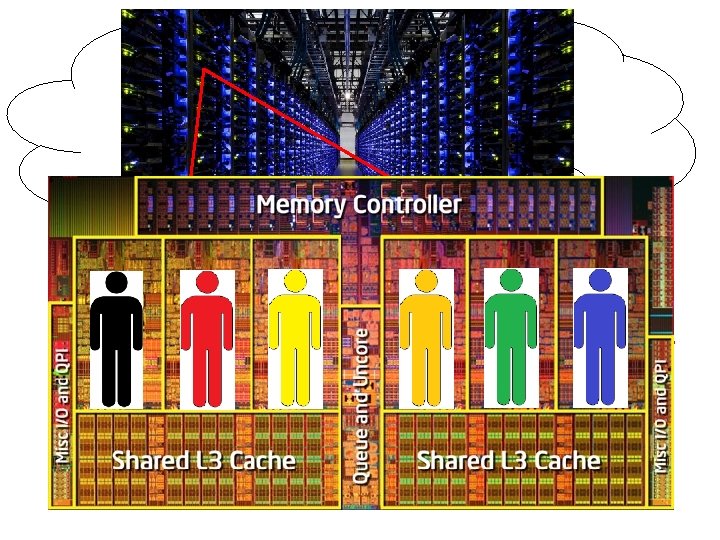
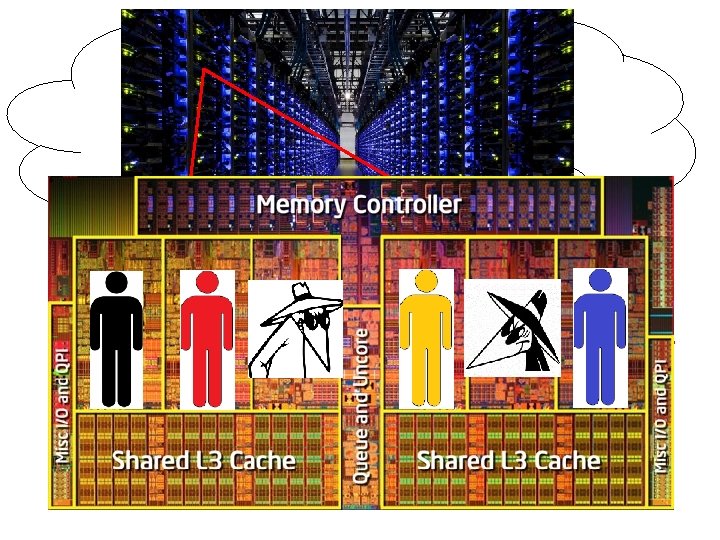
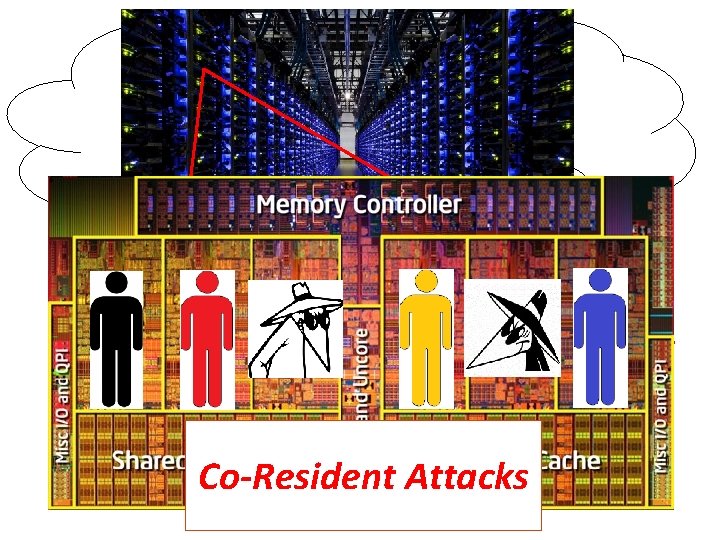
Co-Resident Attacks
Co-Residency On The Cloud? Are co-residency attacks even possible?
Co-Residency On The Cloud? Are co-residency attacks even possible?
Co-Residency On The Cloud? Are co-residency attacks even possible? - Attacker can force co-residency on EC 2
Co-Residency On The Cloud? Are co-residency attacks even possible? - Attacker can force co-residency on EC 2 - Attacker can verify co-residency
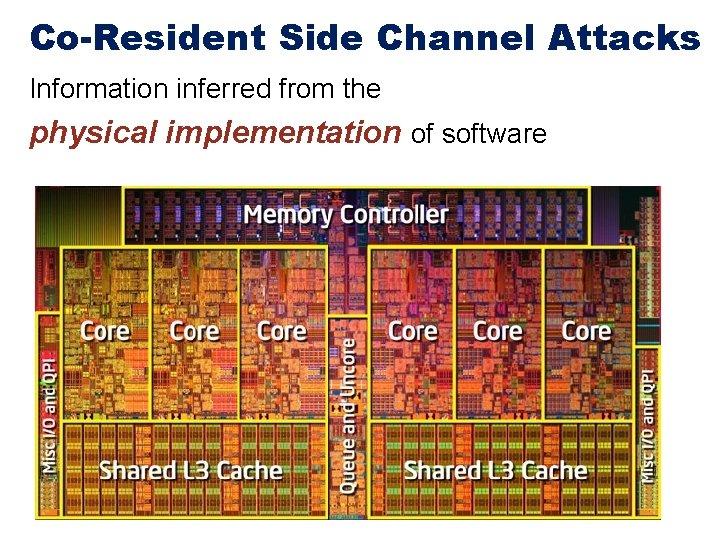
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software
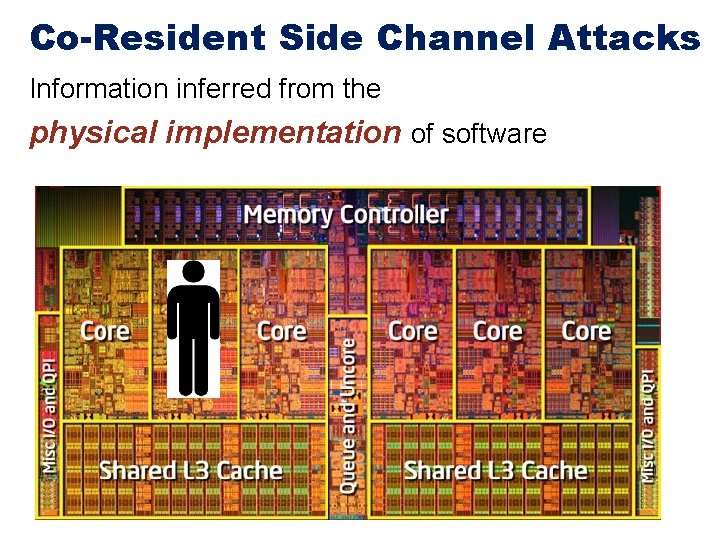
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software
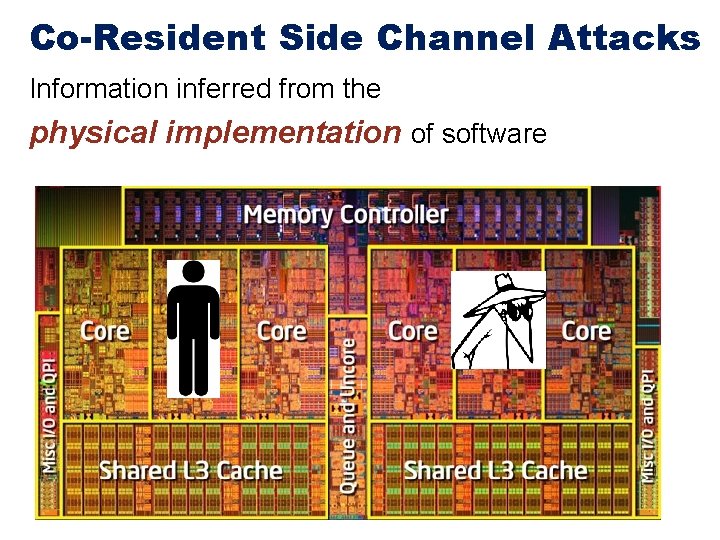
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software
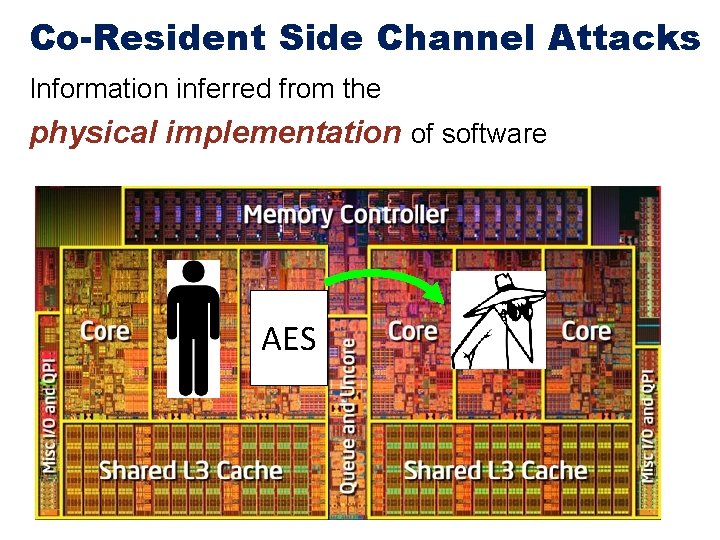
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software AES
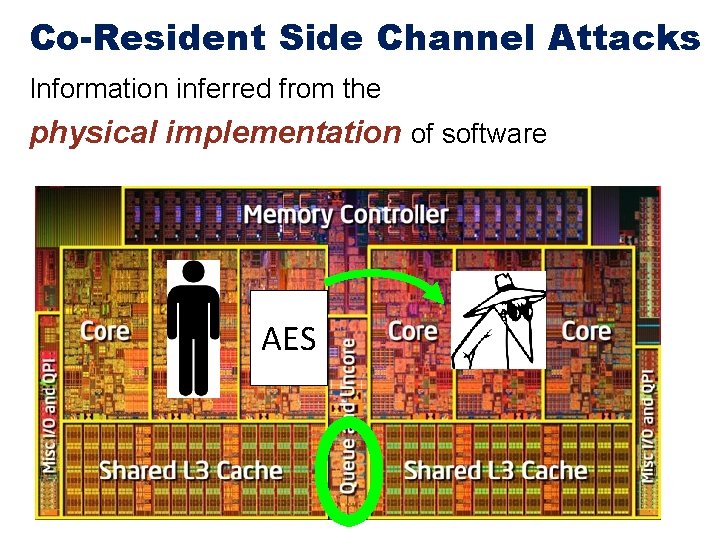
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software AES
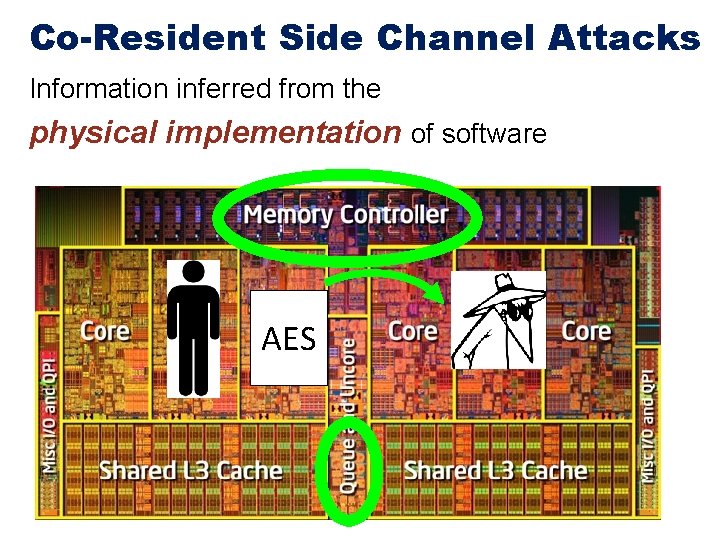
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software AES
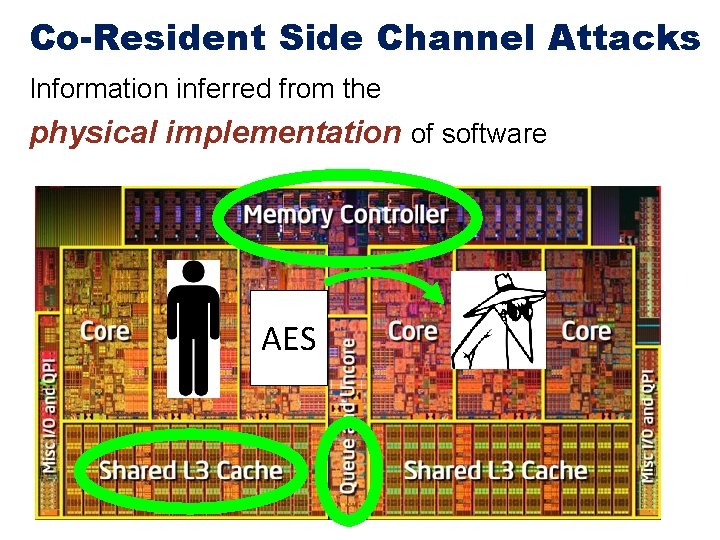
Co-Resident Side Channel Attacks Information inferred from the physical implementation of software AES
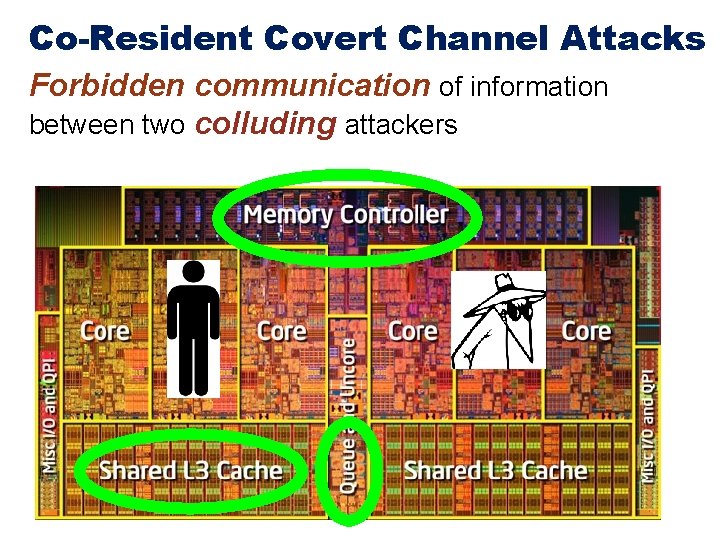
Co-Resident Covert Channel Attacks Forbidden communication of information between two colluding attackers
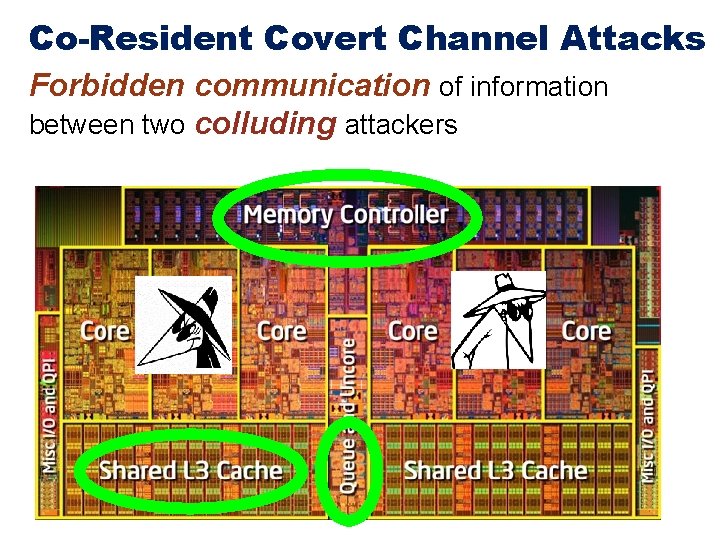
Co-Resident Covert Channel Attacks Forbidden communication of information between two colluding attackers
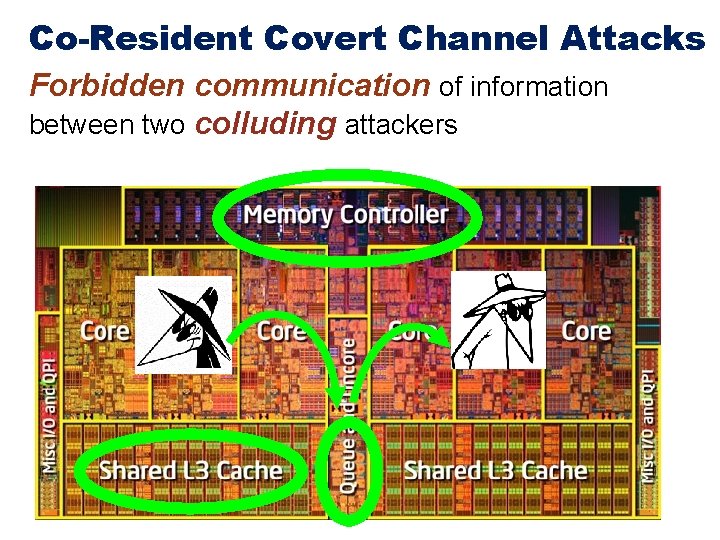
Co-Resident Covert Channel Attacks Forbidden communication of information between two colluding attackers
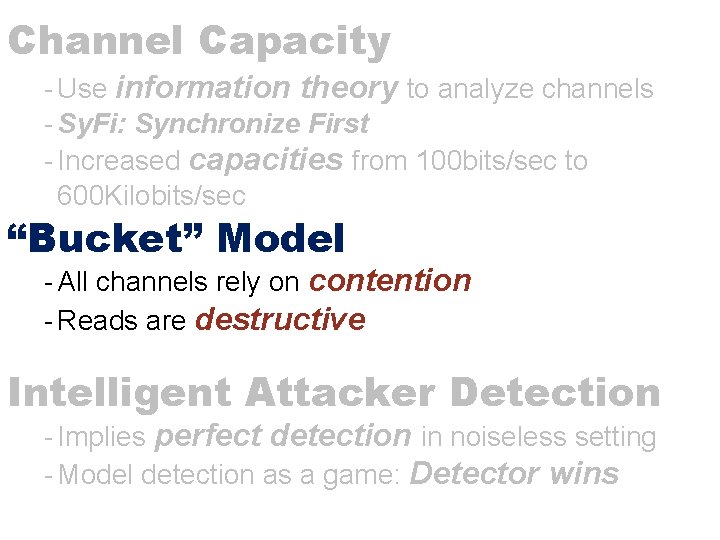
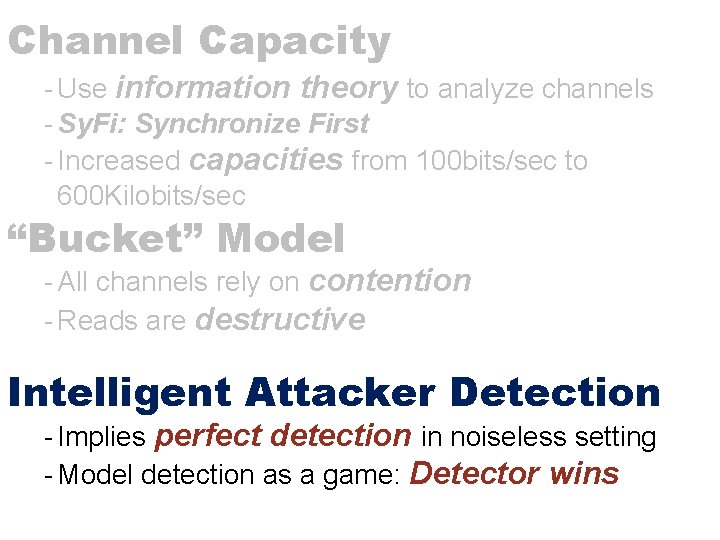
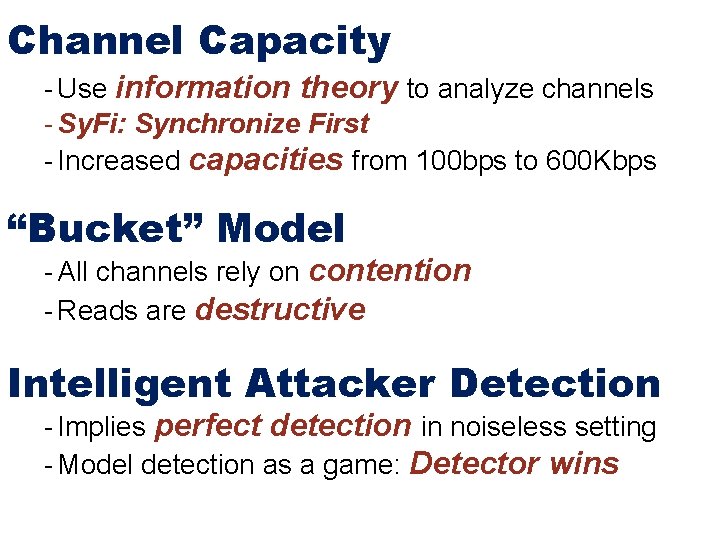
Channel Capacity
Channel Capacity - Use information theory to analyze channels
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting - Model detection as a game: Detector wins
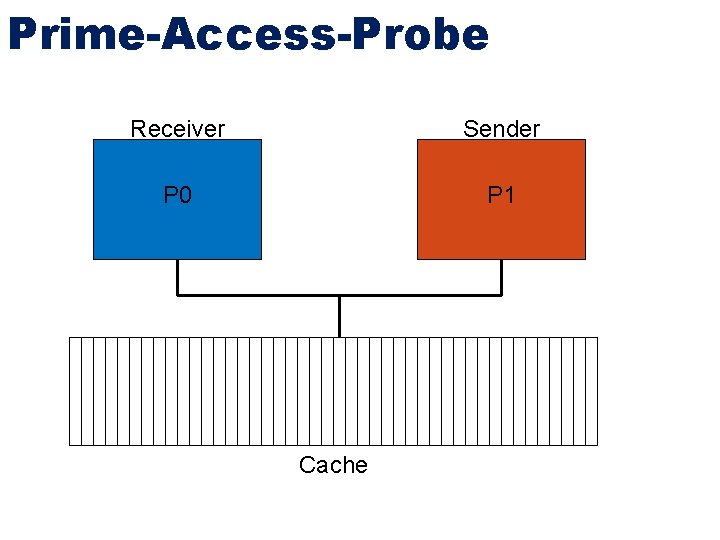
Prime-Access-Probe Receiver Sender P 0 P 1 Cache
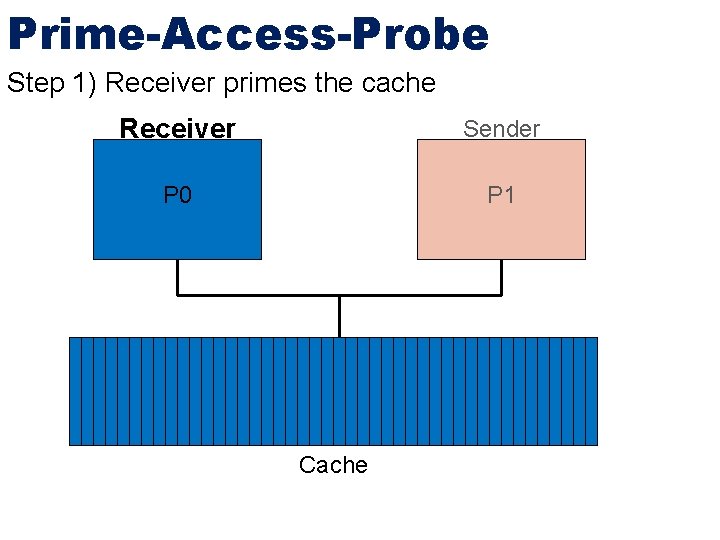
Prime-Access-Probe Step 1) Receiver primes the cache Receiver Sender P 0 P 1 Cache
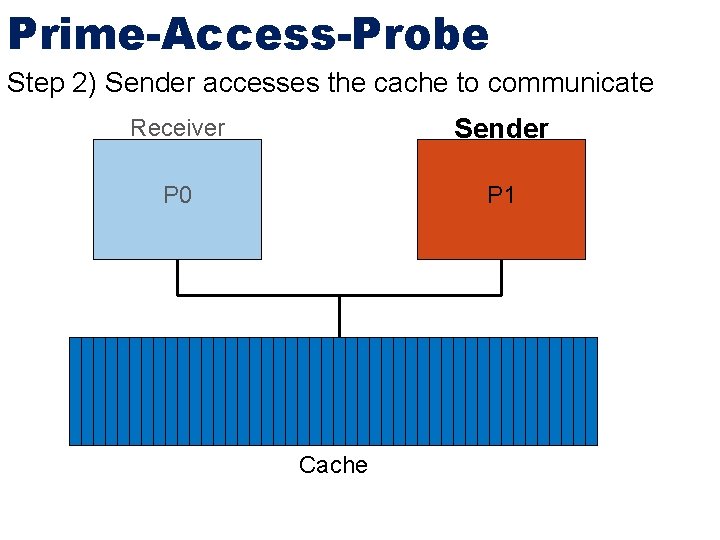
Prime-Access-Probe Step 2) Sender accesses the cache to communicate Receiver Sender P 0 P 1 Cache
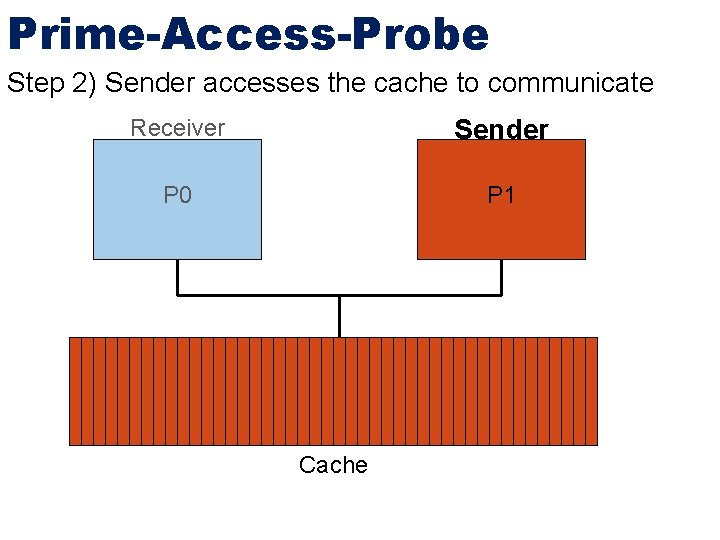
Prime-Access-Probe Step 2) Sender accesses the cache to communicate Receiver Sender P 0 P 1 Cache
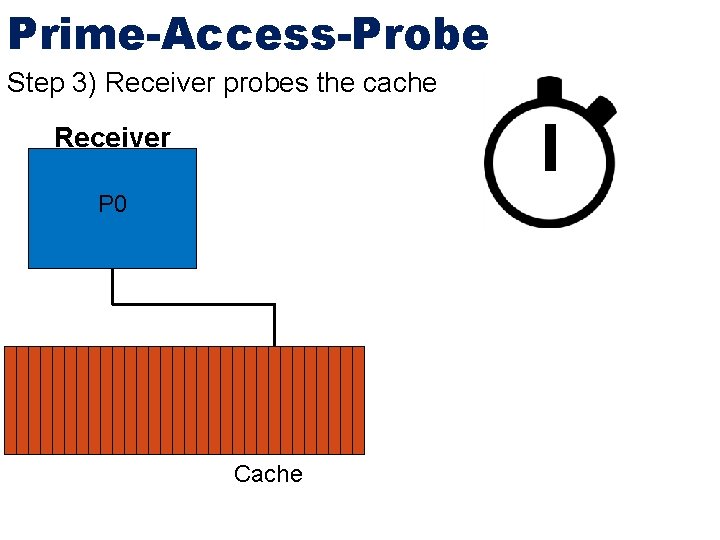
Prime-Access-Probe Step 3) Receiver probes the cache Receiver P 0 Cache
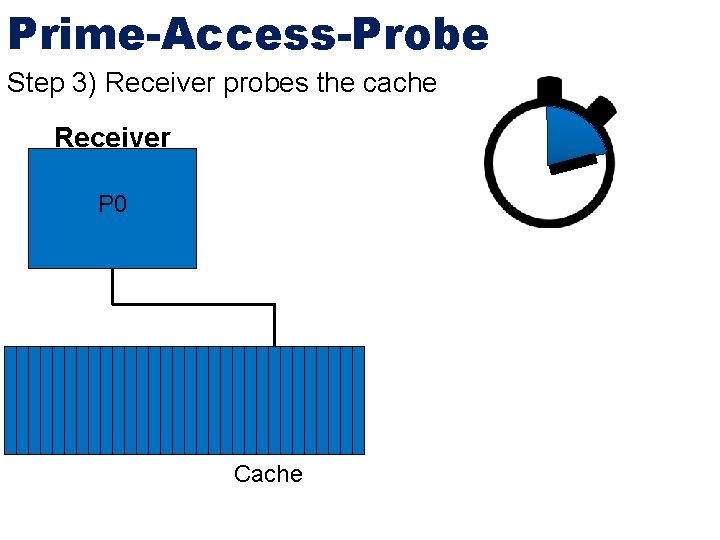
Prime-Access-Probe Step 3) Receiver probes the cache Receiver P 0 Cache
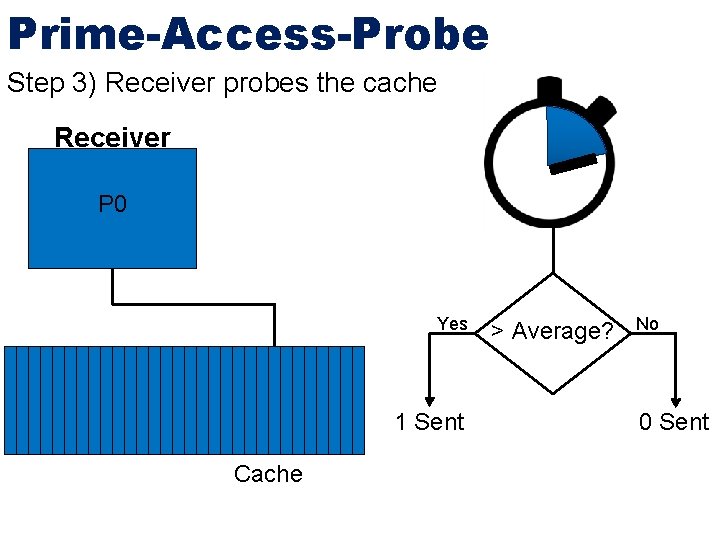
Prime-Access-Probe Step 3) Receiver probes the cache Receiver P 0 Yes 1 Sent Cache > Average? No 0 Sent
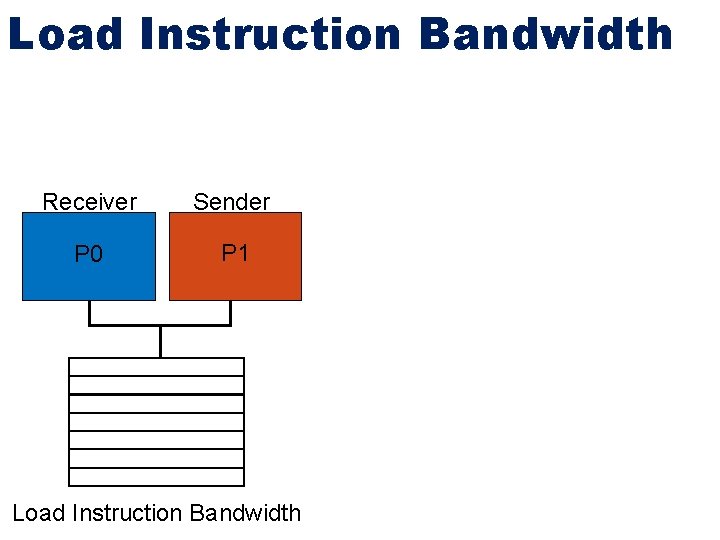
Load Instruction Bandwidth Receiver Sender P 0 P 1 Load Instruction Bandwidth
Load Instruction Bandwidth - Receiver executes as many loads as possible in a given time period Receiver Sender P 0 P 1 Load Instruction Bandwidth
Load Instruction Bandwidth - Receiver executes as many loads as possible in a given time period - Probe performance counter values for loads executed Receiver Sender P 0 P 1 Load Instruction Bandwidth
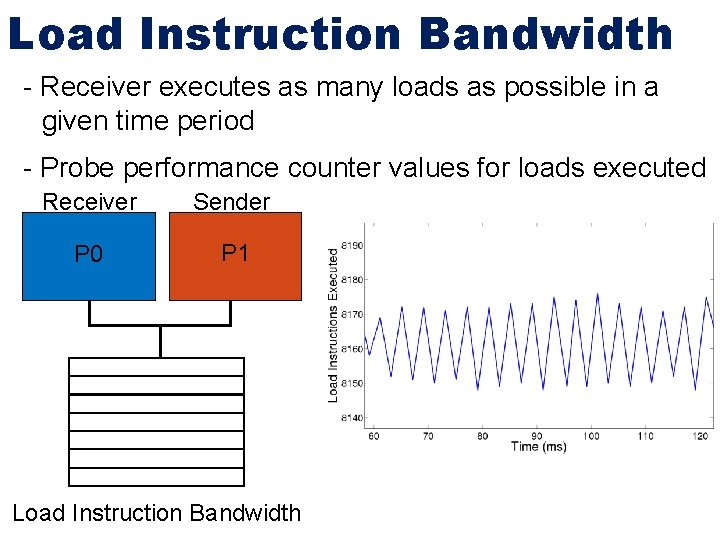
Load Instruction Bandwidth - Receiver executes as many loads as possible in a given time period - Probe performance counter values for loads executed Receiver Sender P 0 P 1 Load Instruction Bandwidth
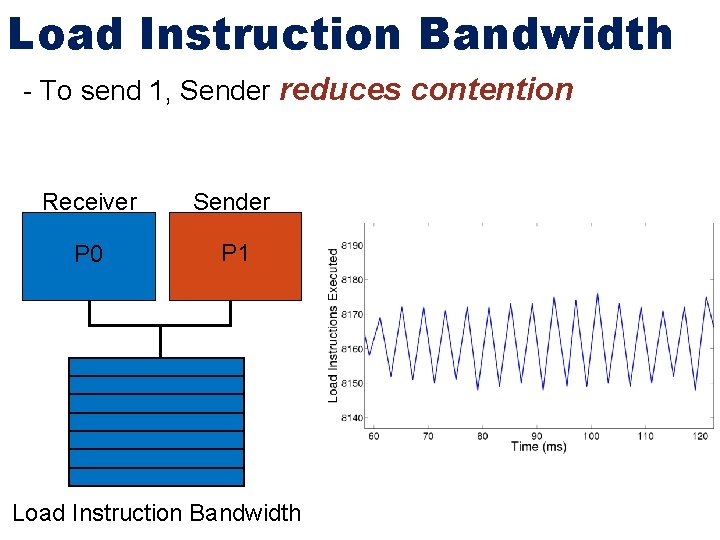
Load Instruction Bandwidth - To send 1, Sender reduces contention Receiver Sender P 0 P 1 Load Instruction Bandwidth
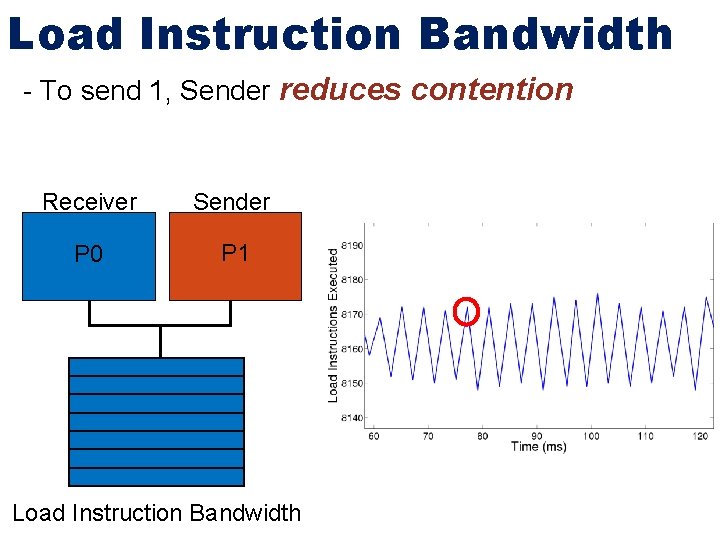
Load Instruction Bandwidth - To send 1, Sender reduces contention Receiver Sender P 0 P 1 Load Instruction Bandwidth
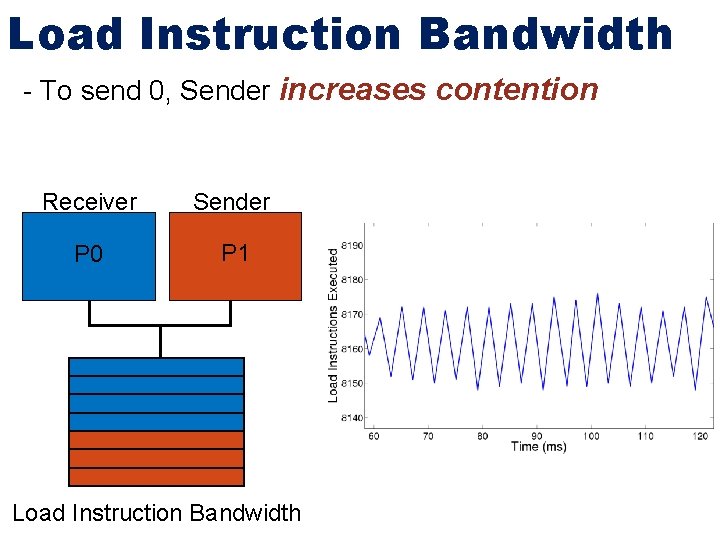
Load Instruction Bandwidth - To send 0, Sender increases contention Receiver Sender P 0 P 1 Load Instruction Bandwidth
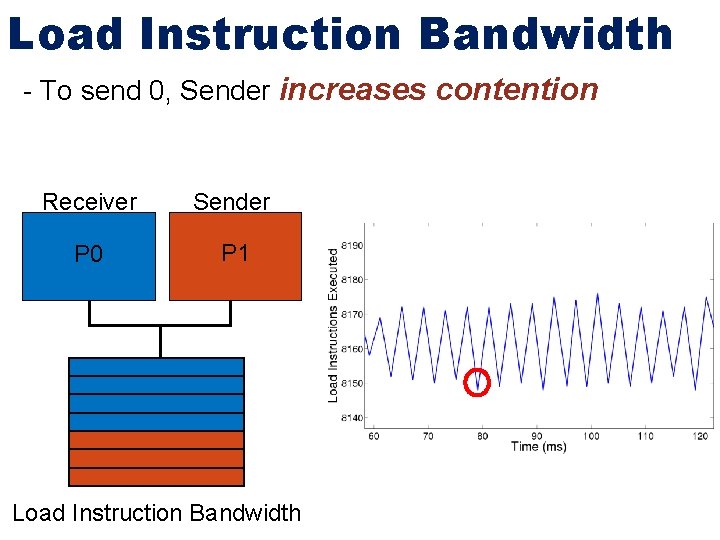
Load Instruction Bandwidth - To send 0, Sender increases contention Receiver Sender P 0 P 1 Load Instruction Bandwidth
Additional Channels - L 1, L 2, L 3 Cache Access Driven L 3 (Set Specific) Branch History Table Memory Bus
Additional Channels - L 1, L 2, L 3 Cache Access Driven L 3 (Set Specific) Branch History Table Memory Bus Load/Store Bandwidth AES Encryption Unit
![Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4] Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4]](http://slidetodoc.com/presentation_image/2128293fd27af2622edaae1983649476/image-50.jpg)
Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4] [1] Inaudible Sound as a Covert Channel in Mobile Devices USENIX `14 [2] Reverse Engineering Microprocessor Content Using Electromagnetic Radiation [3] Temperature-based covert channel in FPGA systems Re. Co. Soc `11 [4] Characteristics CLACK: A Network Covert Channel Based on Partial Acknowledgment Encoding ICC `09
![Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4] Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4]](http://slidetodoc.com/presentation_image/2128293fd27af2622edaae1983649476/image-51.jpg)
Non-Contention Channels - Sound [1] EM Radiation [2] Temperature [3] Network Packet Characteristics [4] [1] Inaudible Sound as a Covert Channel in Mobile Devices USENIX `14 [2] Reverse Engineering Microprocessor Content Using Electromagnetic Radiation [3] Temperature-based covert channel in FPGA systems Re. Co. Soc `11 [4] Characteristics CLACK: A Network Covert Channel Based on Partial Acknowledgment Encoding ICC `09
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting - Model detection as a game: Detector wins
Communication Issues
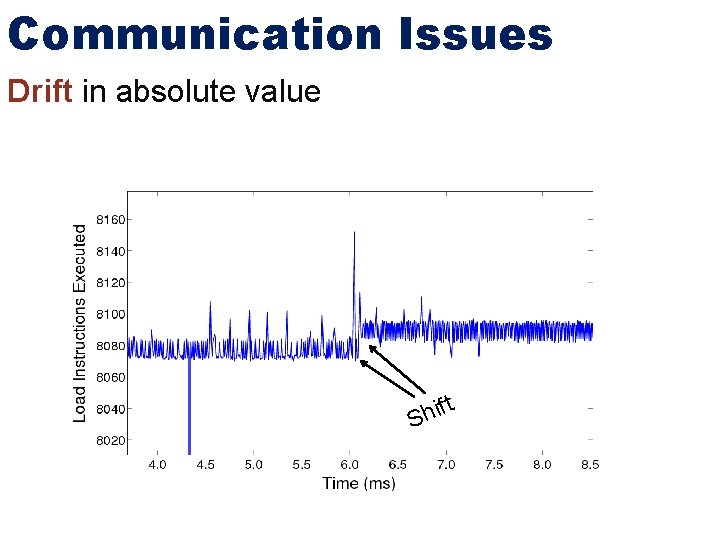
Communication Issues Drift in absolute value ft i h S
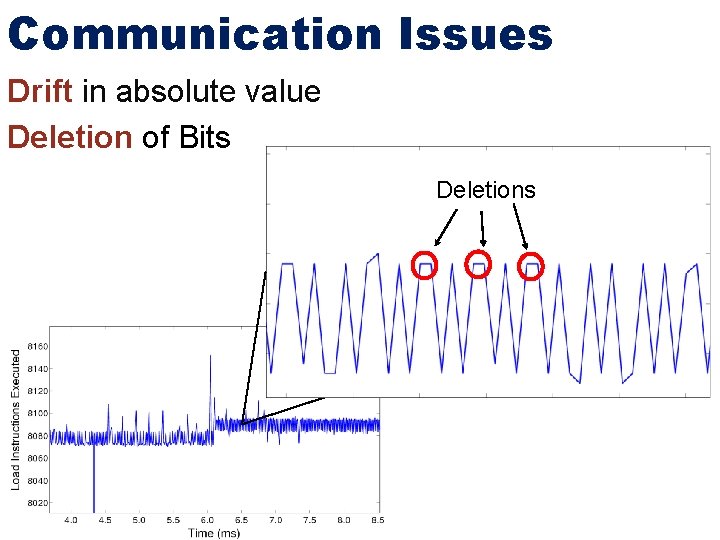
Communication Issues Drift in absolute value Deletion of Bits Deletions
Si. Fy: Offline Analysis
Si. Fy: Offline Analysis 1) Select starting time
Si. Fy: Offline Analysis 1) Select starting time 2) Select period length for each bit
Si. Fy: Offline Analysis 1) Select starting time 2) Select period length for each bit 3) Synchronize again after each bit
Si. Fy: Clock Alignment
Si. Fy: Clock Alignment Step One: Use Network Time Protocol
Si. Fy: Clock Alignment Step One: Use Network Time Protocol - Pass timestamps between both processes, taking into consideration round-trip time
Si. Fy: Clock Alignment Step One: Use Network Time Protocol - Pass timestamps between both processes, taking into consideration round-trip time RTT Clock Offset = t. S – t. R – RTT 2 t. S – Sender Timestamp t. R – Receiver Timestamp RTT – Round Trip Time
Si. Fy: Clock Alignment Step One: Use Network Time Protocol - Pass timestamps between both processes, taking into consideration round-trip time RTT Clock Offset = t. S – t. R – RTT 2 t. S – Sender Timestamp t. R – Receiver Timestamp RTT – Round Trip Time Step Two: Use covert communication for precise alignment
Si. Fy: Clock Alignment Step One: Use Network Time Protocol - Pass timestamps between both processes, taking into consideration round-trip time RTT Clock Offset = t. S – t. R – RTT 2 t. S – Sender Timestamp t. R – Receiver Timestamp RTT – Round Trip Time Step Two: Use covert communication for precise alignment - Repeatedly send predetermine message across channel
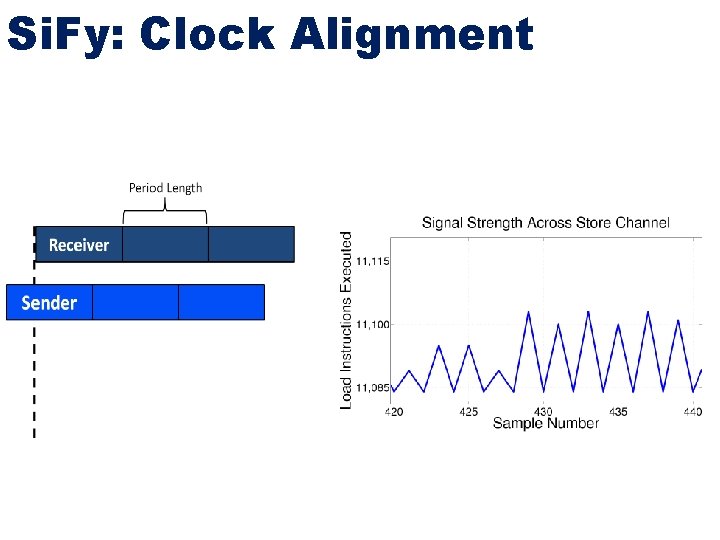
Si. Fy: Clock Alignment
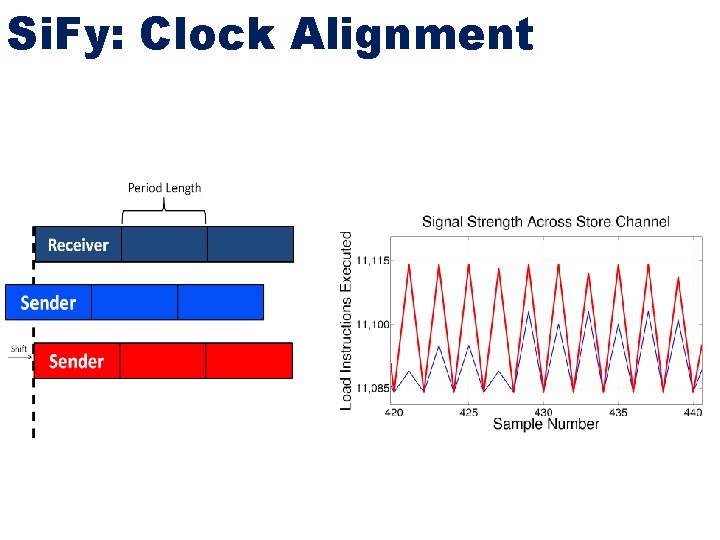
Si. Fy: Clock Alignment
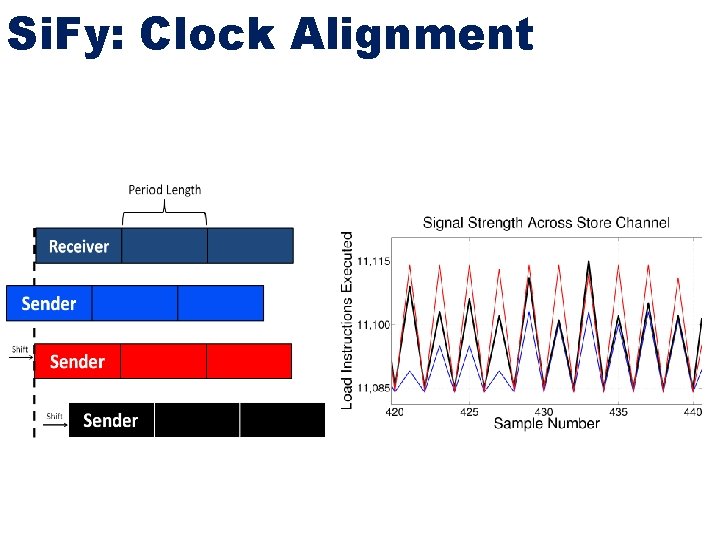
Si. Fy: Clock Alignment
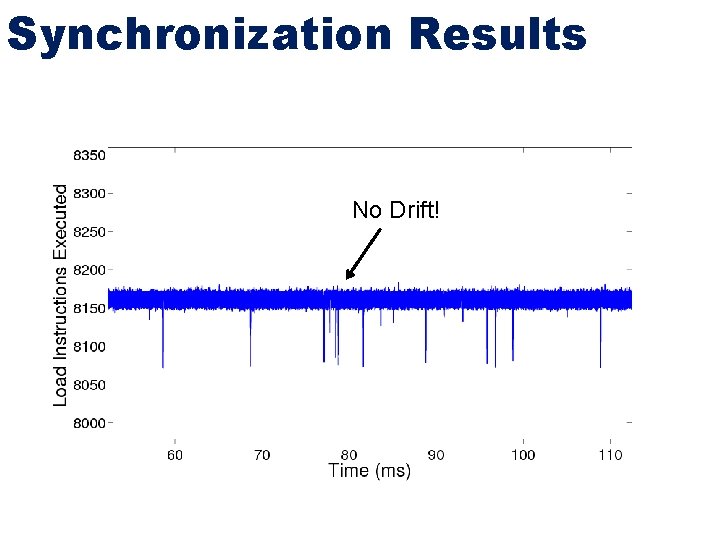
Synchronization Results No Drift!
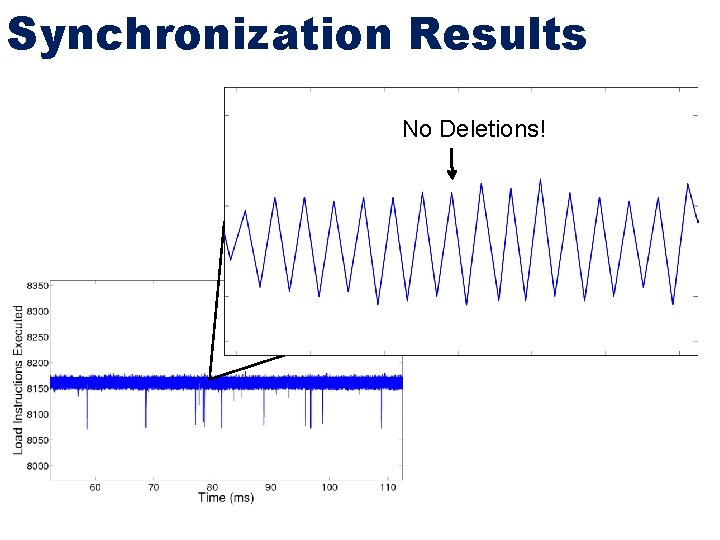
Synchronization Results No Deletions!
Calculating Capacity Easy to calculate bit flip probabilities after synchronization - Send 10, 000 bit sequence 20 times for each frequency tested
Calculating Capacity Easy to calculate bit flip probabilities after synchronization - Send 10, 000 bit sequence 20 times for each frequency tested Use Blahut-Arimoto - Maximize mutual information over all distributions
Calculating Capacity Easy to calculate bit flip probabilities after synchronization - Send 10, 000 bit sequence 20 times for each frequency tested Use Blahut-Arimoto - Maximize mutual information over all distributions Experimental Setup - Intel Quad-Core i 7 2600 3. 4 GHz - Ubuntu 12. 04 LTS - QEMU with KVM extensions - PAPI Performance Counter Library
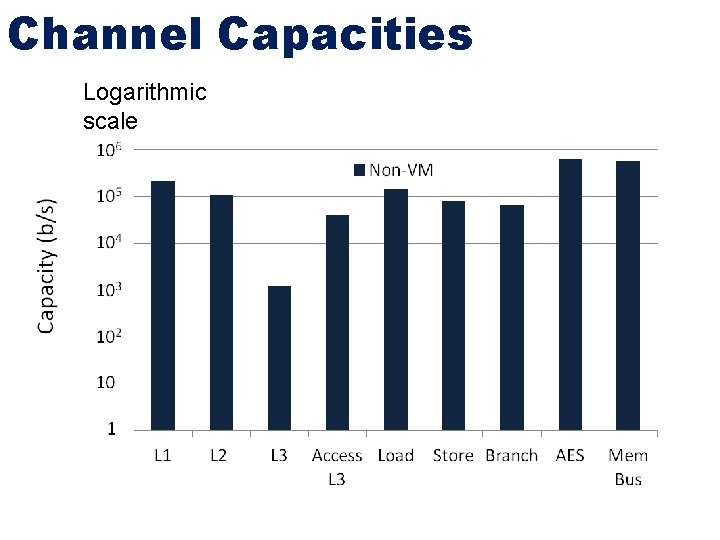
Channel Capacities Logarithmic scale
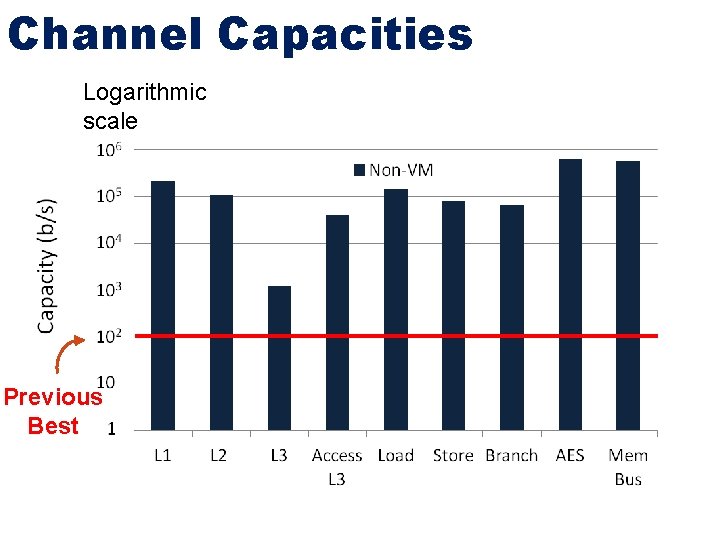
Channel Capacities Logarithmic scale Previous Best
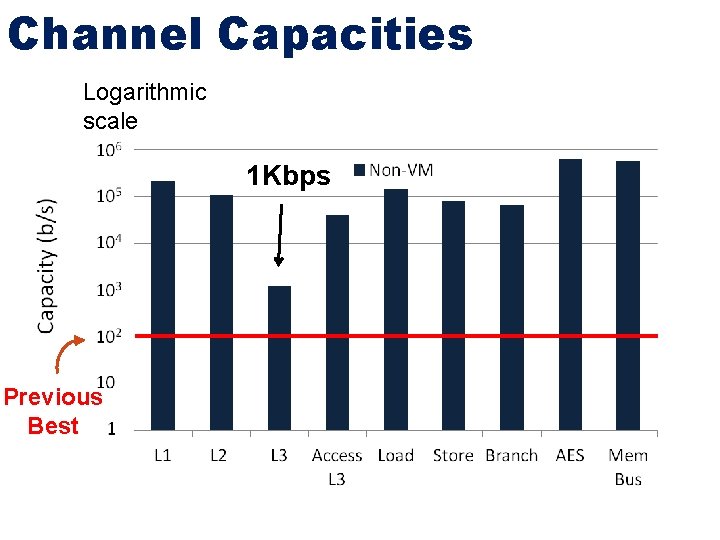
Channel Capacities Logarithmic scale 1 Kbps Previous Best
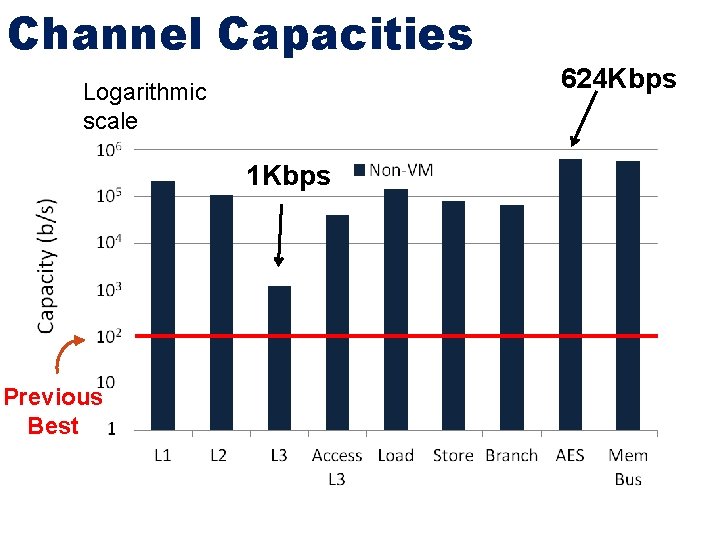
Channel Capacities Logarithmic scale 1 Kbps Previous Best 624 Kbps
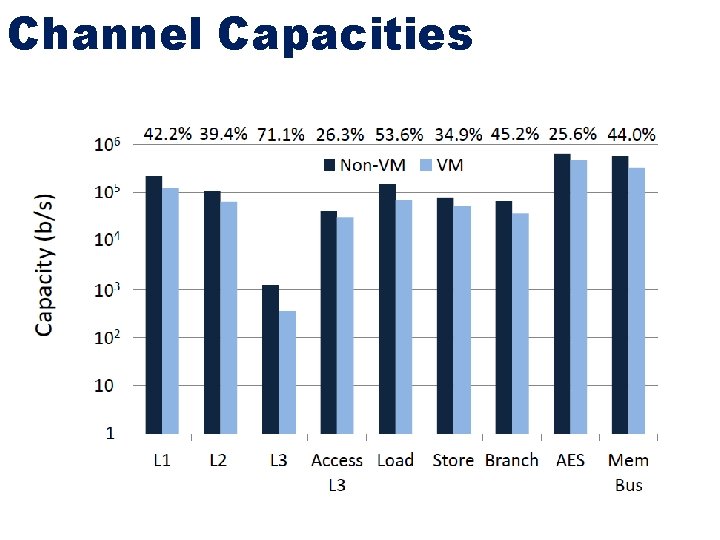
Channel Capacities
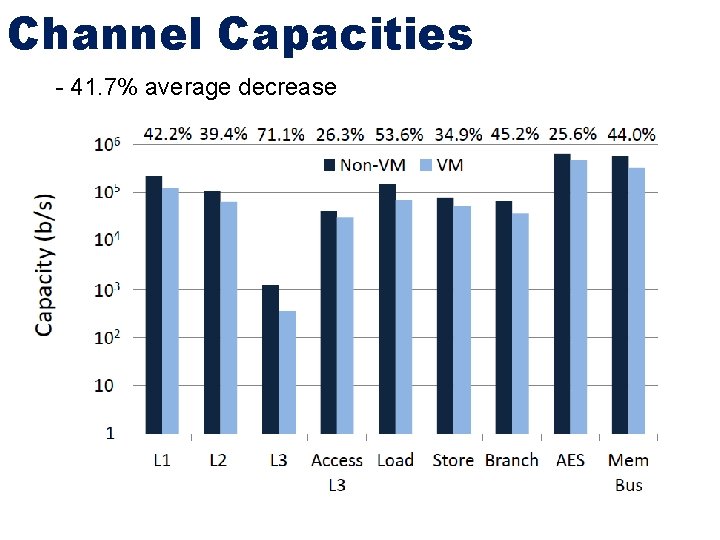
Channel Capacities - 41. 7% average decrease
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting - Model detection as a game: Detector wins
Bucket Model Alice Bob
Bucket Model Alice Bob
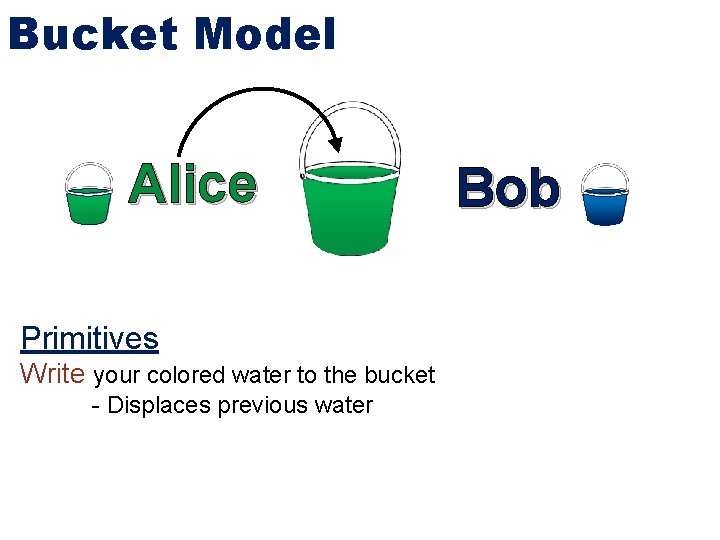
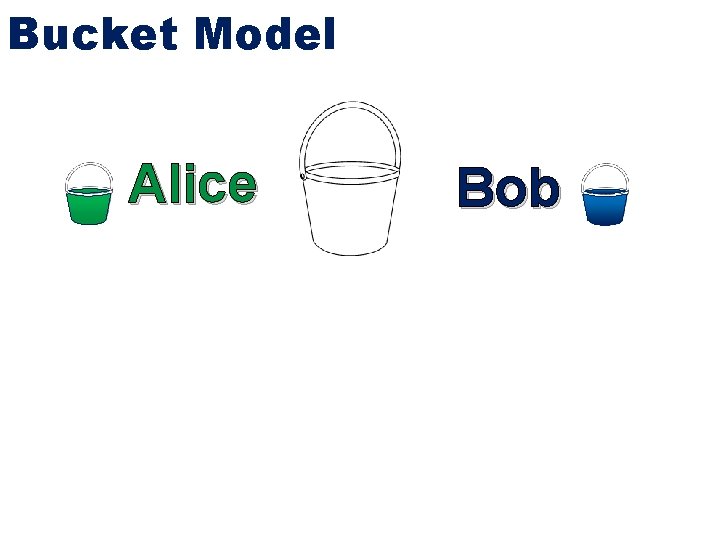
Bucket Model Alice Primitives Write your colored water to the bucket - Displaces previous water Bob
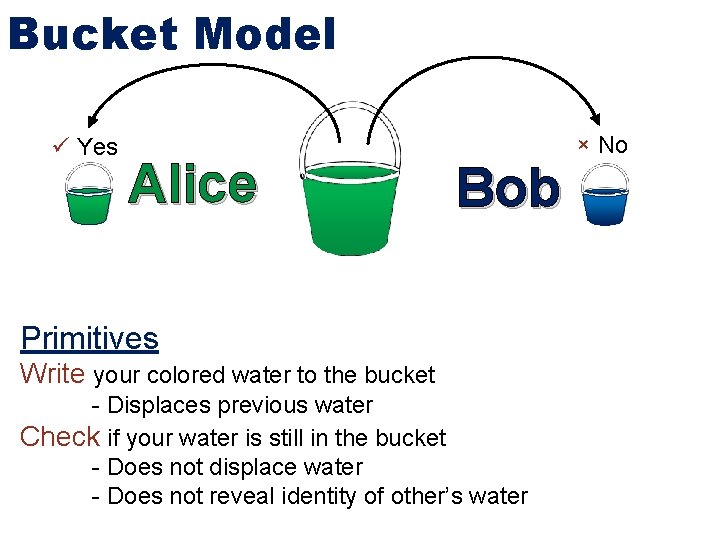
Bucket Model Yes Alice Bob Primitives Write your colored water to the bucket - Displaces previous water Check if your water is still in the bucket - Does not displace water - Does not reveal identity of other’s water × No
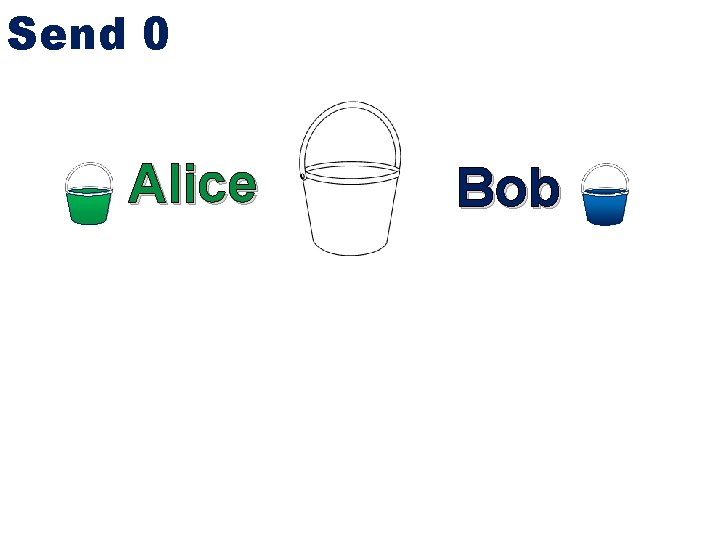
Send 0 Alice Bob
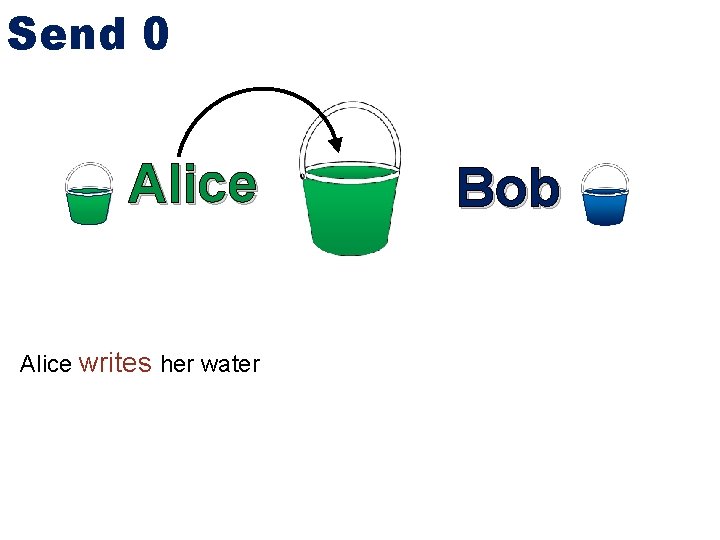
Send 0 Alice writes her water Bob
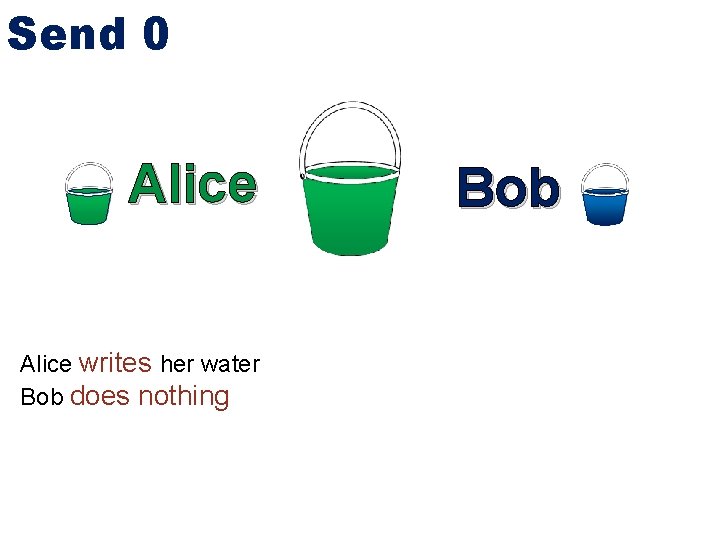
Send 0 Alice writes her water Bob does nothing Bob
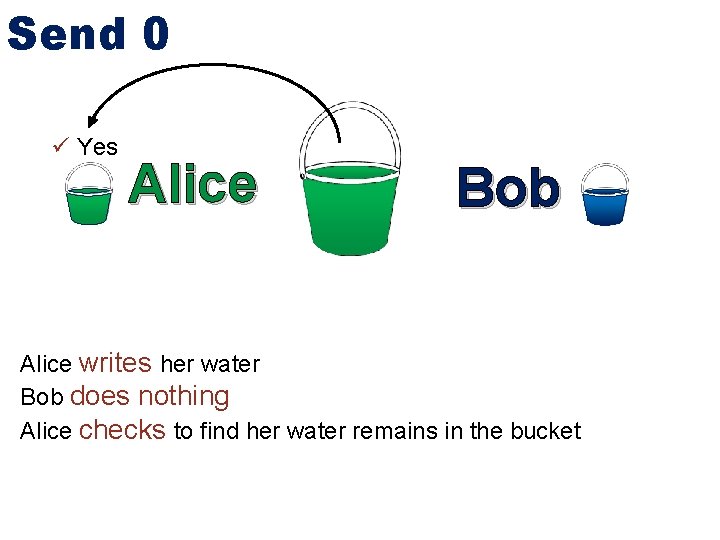
Send 0 Yes Alice Bob Alice writes her water Bob does nothing Alice checks to find her water remains in the bucket
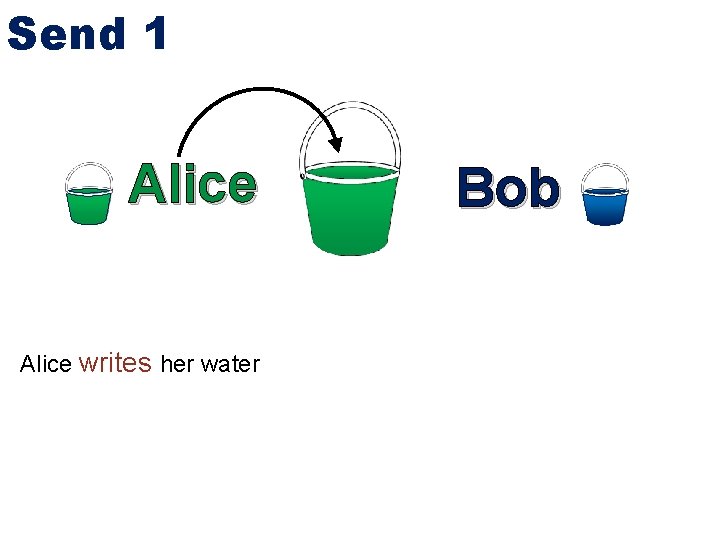
Send 1 Alice writes her water Bob
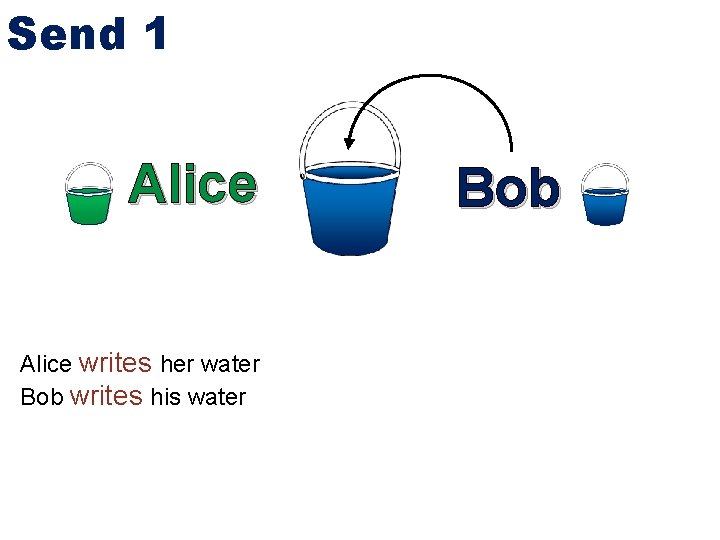
Send 1 Alice writes her water Bob writes his water Bob
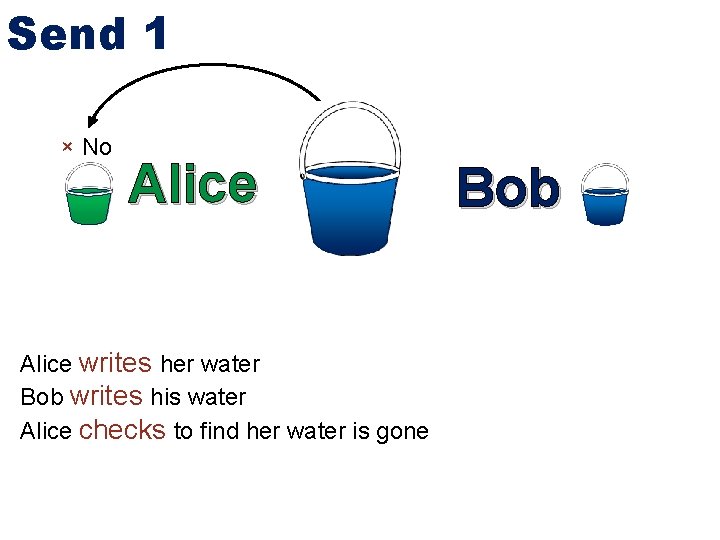
Send 1 × No Alice writes her water Bob writes his water Alice checks to find her water is gone Bob
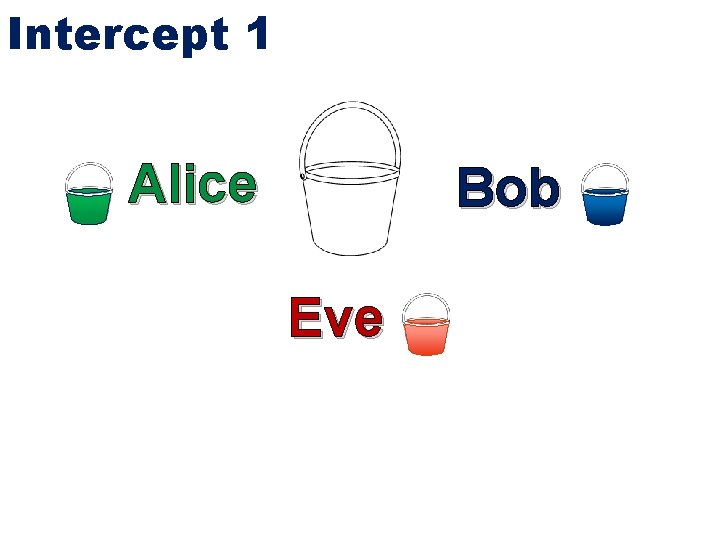
Intercept 1 Alice Bob Eve
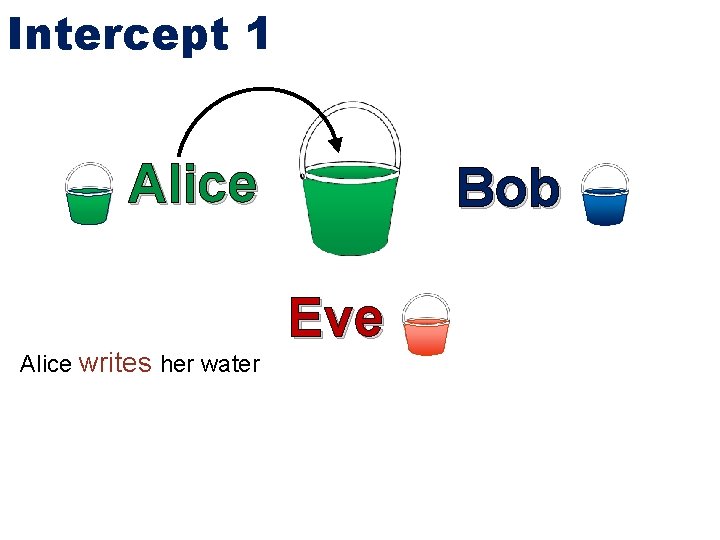
Intercept 1 Alice writes her water Bob Eve
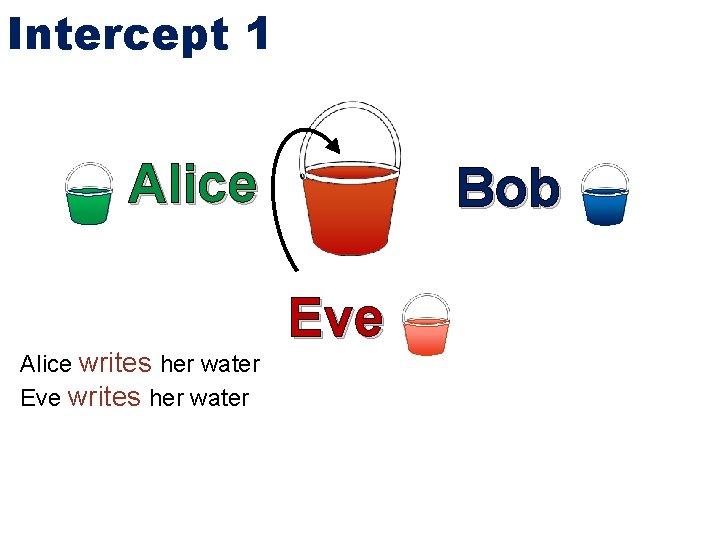
Intercept 1 Alice writes her water Eve writes her water Bob Eve
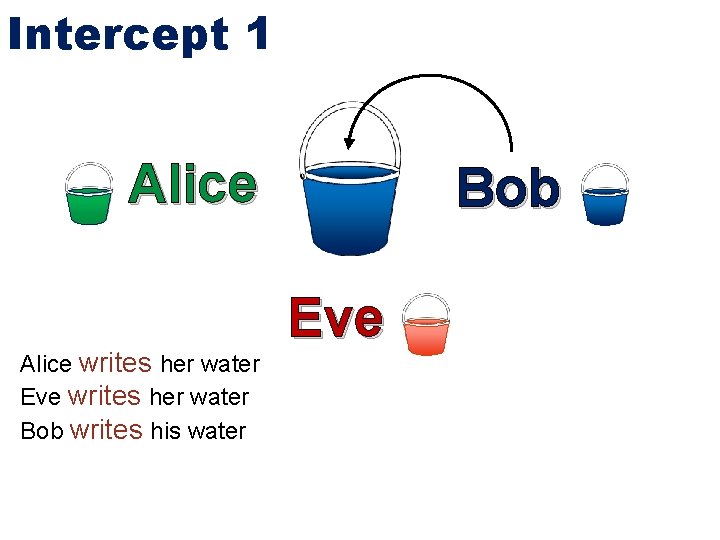
Intercept 1 Alice writes her water Eve writes her water Bob writes his water Bob Eve
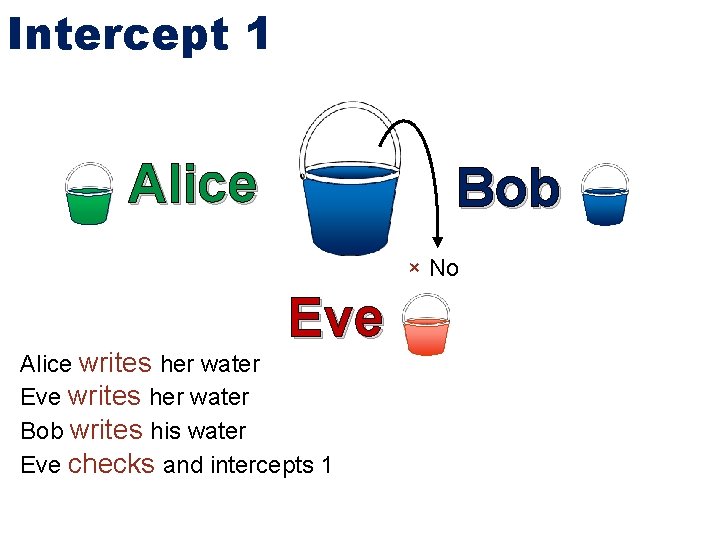
Intercept 1 Alice Bob × No Eve Alice writes her water Eve writes her water Bob writes his water Eve checks and intercepts 1
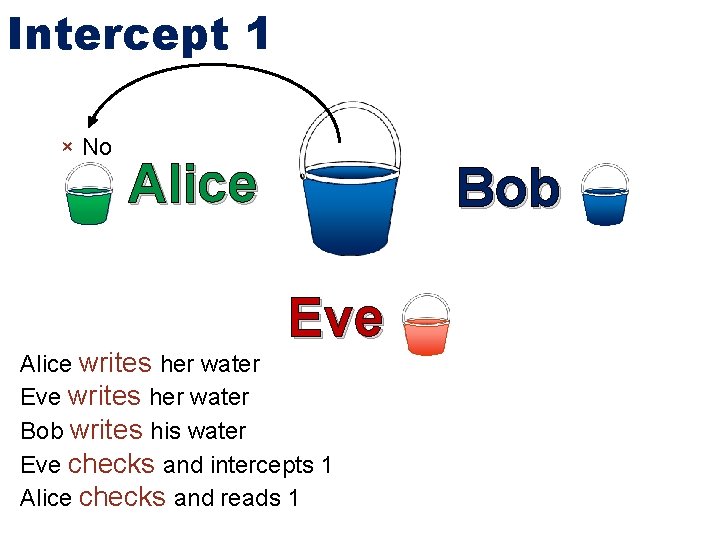
Intercept 1 × No Alice Bob Eve Alice writes her water Eve writes her water Bob writes his water Eve checks and intercepts 1 Alice checks and reads 1
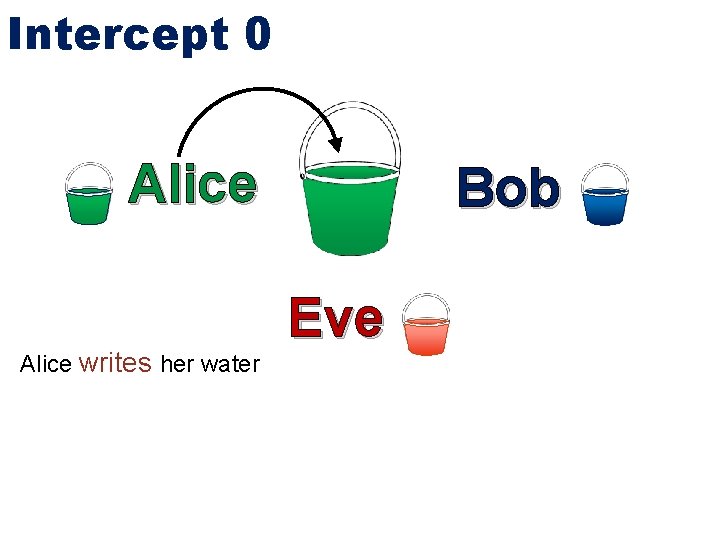
Intercept 0 Alice writes her water Bob Eve
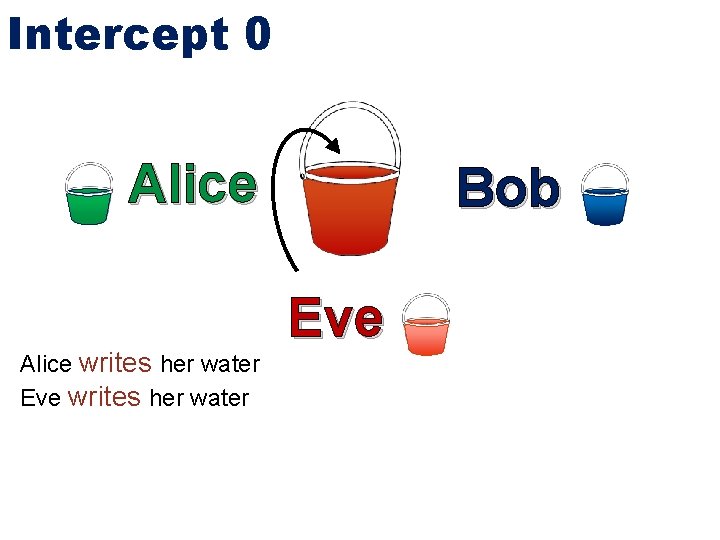
Intercept 0 Alice writes her water Eve writes her water Bob Eve
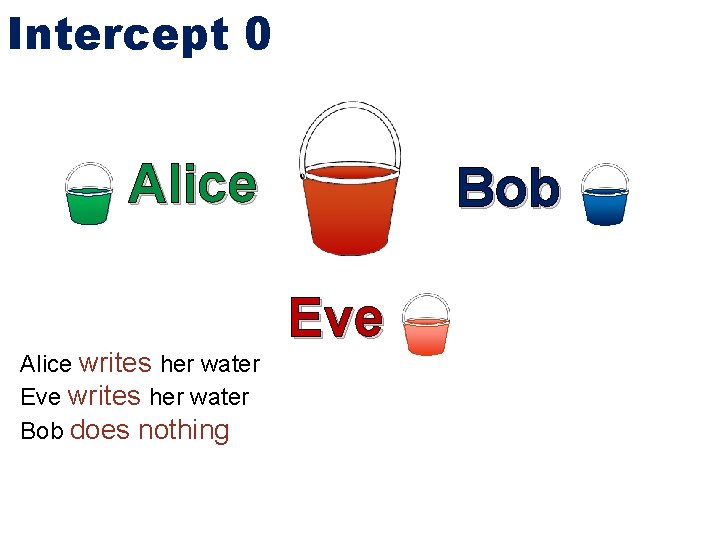
Intercept 0 Alice writes her water Eve writes her water Bob does nothing Bob Eve
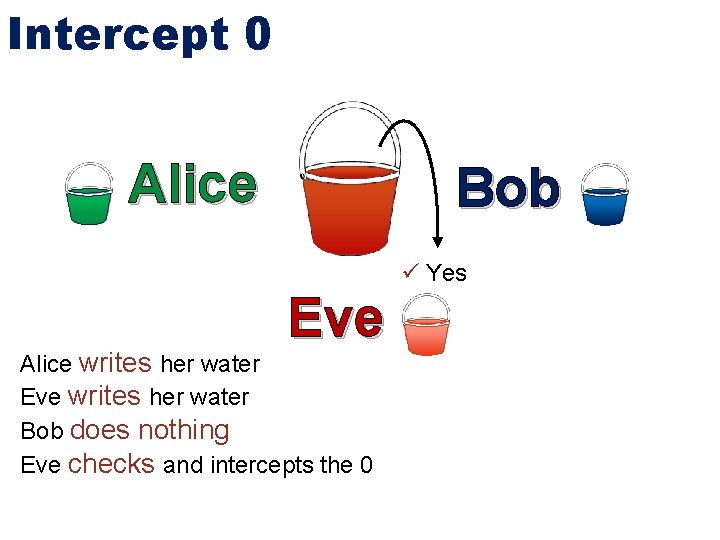
Intercept 0 Alice Bob Yes Eve Alice writes her water Eve writes her water Bob does nothing Eve checks and intercepts the 0
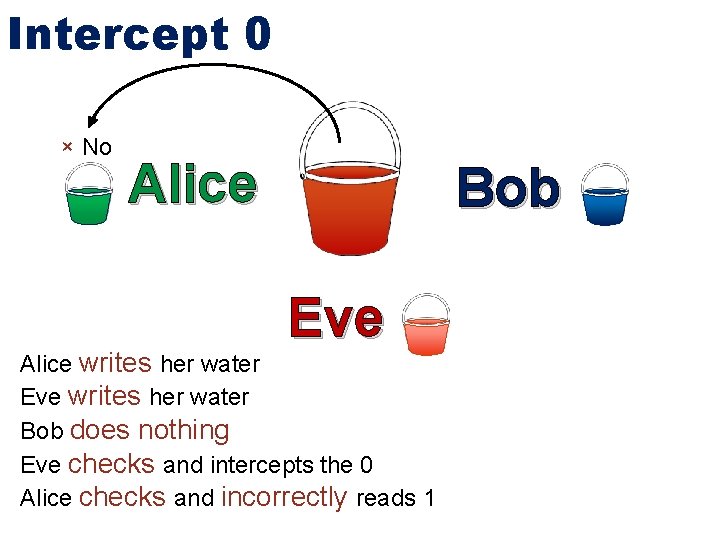
Intercept 0 × No Alice Bob Eve Alice writes her water Eve writes her water Bob does nothing Eve checks and intercepts the 0 Alice checks and incorrectly reads 1
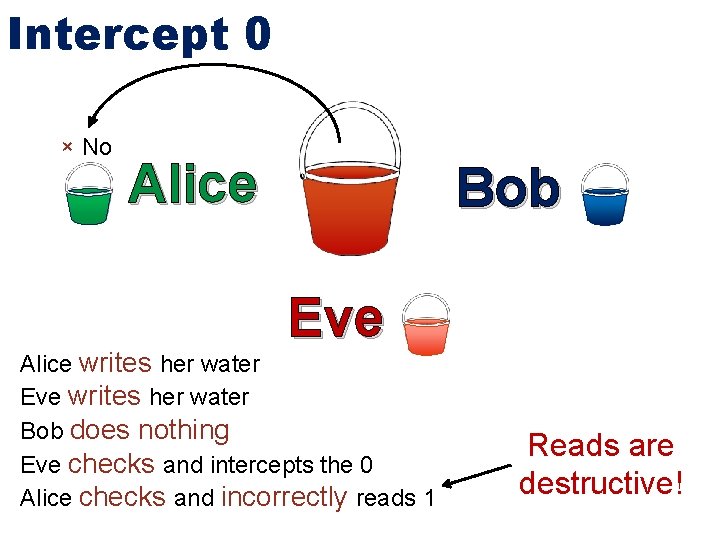
Intercept 0 × No Alice Bob Eve Alice writes her water Eve writes her water Bob does nothing Eve checks and intercepts the 0 Alice checks and incorrectly reads 1 Reads are destructive!
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bits/sec to 600 Kilobits/sec “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting - Model detection as a game: Detector wins
Detection Game Our Detector vs an attacker (Eve)
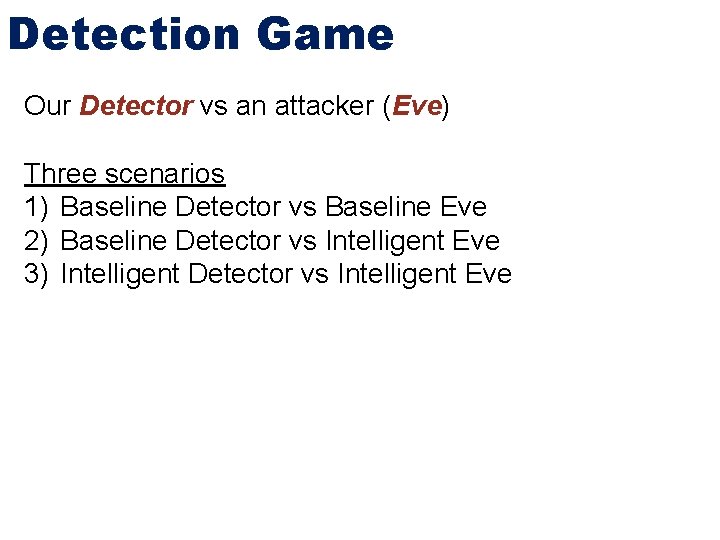
Detection Game Our Detector vs an attacker (Eve) Three scenarios 1) Baseline Detector vs Baseline Eve 2) Baseline Detector vs Intelligent Eve 3) Intelligent Detector vs Intelligent Eve
Detection Game Our Detector vs an attacker (Eve) Three scenarios 1) Baseline Detector vs Baseline Eve 2) Baseline Detector vs Intelligent Eve 3) Intelligent Detector vs Intelligent Eve Using load instruction bandwidth Apache httpd as victim
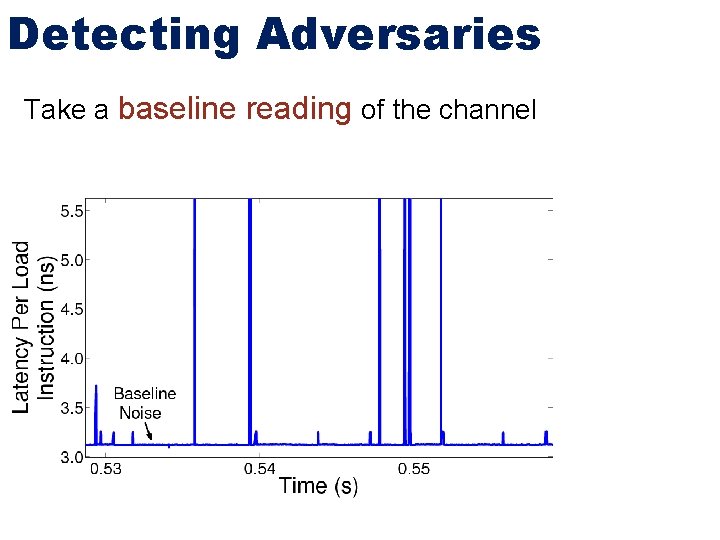
Detecting Adversaries Take a baseline reading of the channel
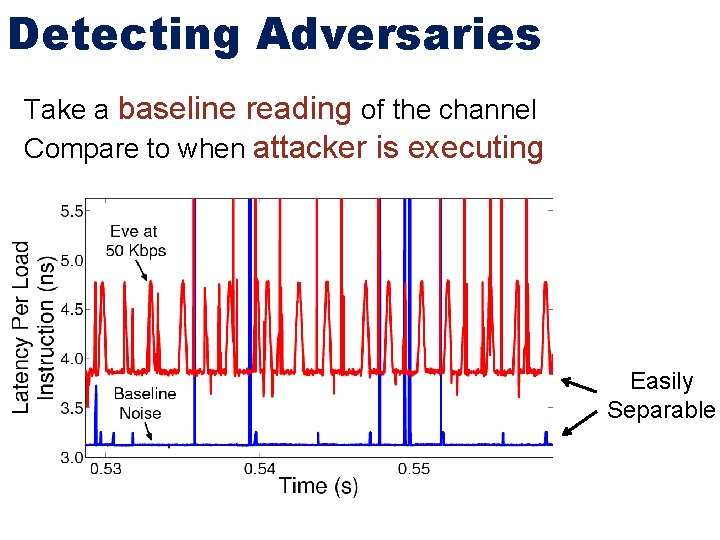
Detecting Adversaries Take a baseline reading of the channel Compare to when attacker is executing Easily Separable
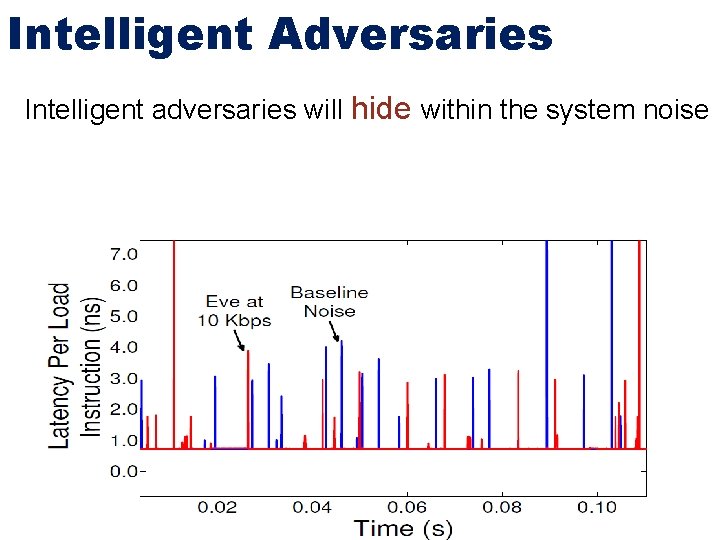
Intelligent Adversaries Intelligent adversaries will hide within the system noise
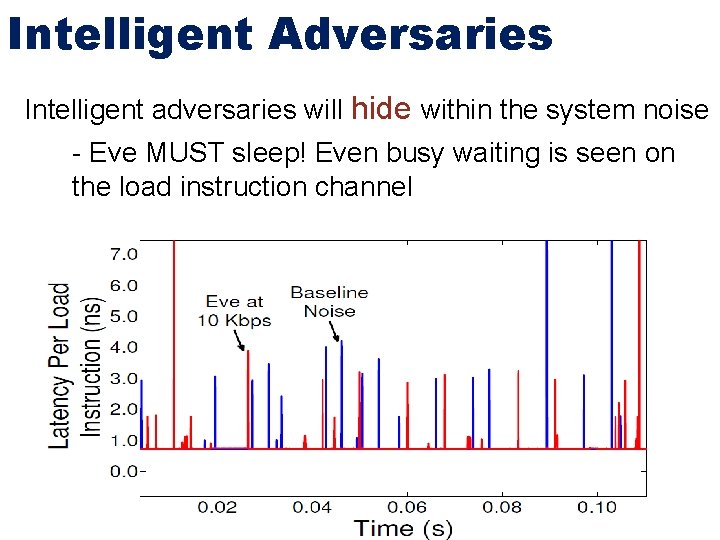
Intelligent Adversaries Intelligent adversaries will hide within the system noise - Eve MUST sleep! Even busy waiting is seen on the load instruction channel
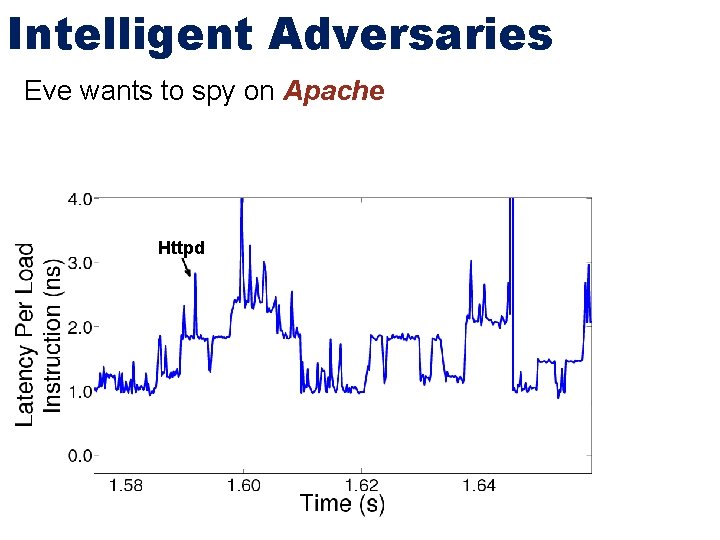
Intelligent Adversaries Eve wants to spy on Apache Httpd
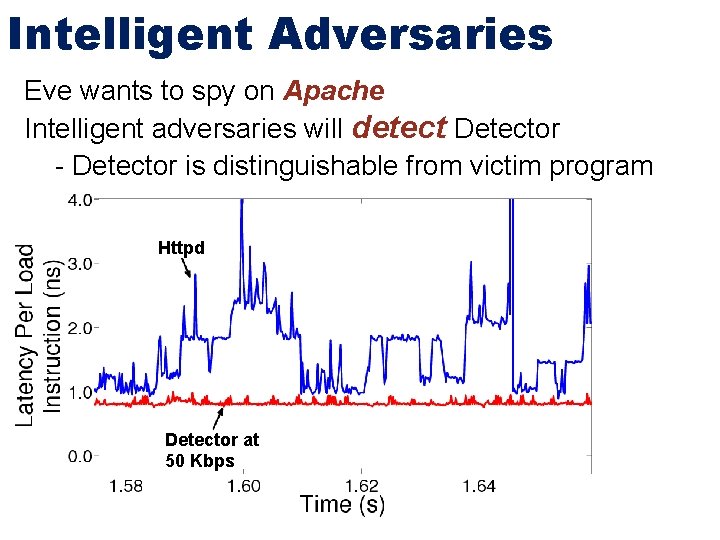
Intelligent Adversaries Eve wants to spy on Apache Intelligent adversaries will detect Detector - Detector is distinguishable from victim program Httpd Detector at 50 Kbps
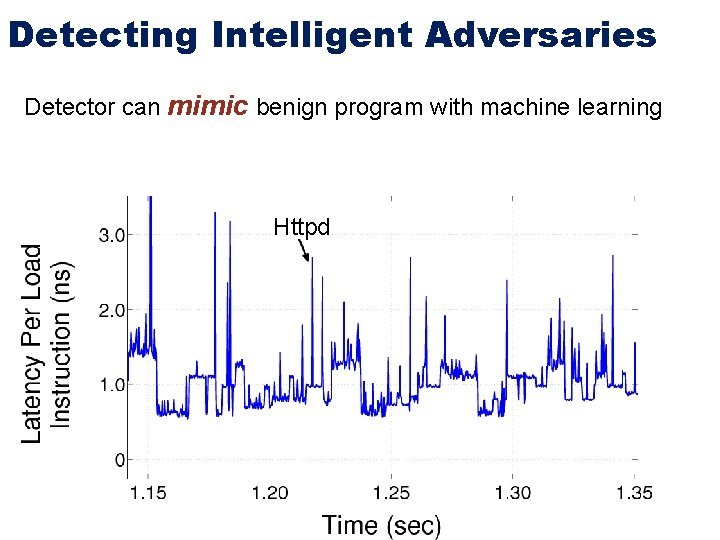
Detecting Intelligent Adversaries Detector can mimic benign program with machine learning Httpd
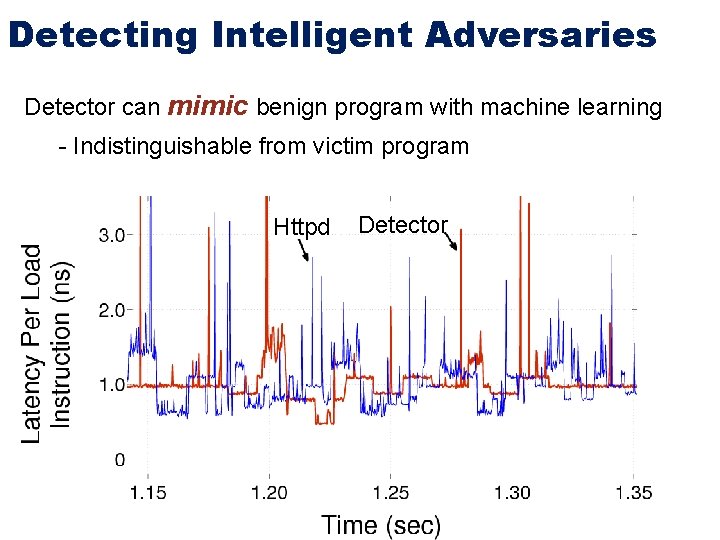
Detecting Intelligent Adversaries Detector can mimic benign program with machine learning - Indistinguishable from victim program Httpd Detector
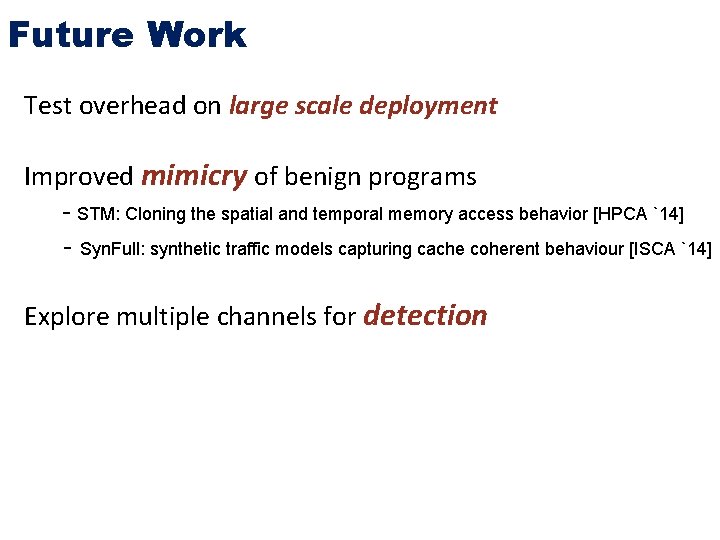
Future Work Test overhead on large scale deployment Improved mimicry of benign programs - STM: Cloning the spatial and temporal memory access behavior [HPCA `14] - Syn. Full: synthetic traffic models capturing cache coherent behaviour [ISCA `14] Explore multiple channels for detection
Channel Capacity - Use information theory to analyze channels - Sy. Fi: Synchronize First - Increased capacities from 100 bps to 600 Kbps “Bucket” Model - All channels rely on contention - Reads are destructive Intelligent Attacker Detection - Implies perfect detection in noiseless setting - Model detection as a game: Detector wins
Thank you! Questions?
- Slides: 118