Lecture 3 Block Ciphers and the Data Encryption
Lecture 3 Block Ciphers and the Data Encryption Standard 1
Outline • Ideal Block Cipher • The Feistel Structure for Block Ciphers • DES: The Data Encryption Standard 2
Symmetric Block Ciphers • The most commonly used symmetric encryption algorithm • Take a plaintext divided into a fixed-length (called ”block”) as input and produce the same size of ciphertext for each block as output. • The most important ones: – – Feistel Cipher Structure. Data Encryption Standard (DES) Triple DES (3 DES) Advanced Encryption Standard (AES) 3
Basic idea of modern block ciphers • From classical ciphers, we learn two techniques that may improve security: – Encrypt multiple letters at a time – Use multiple ciphertext alphabets (Polyalphabetic ciphers) • Combining these two techniques – encrypt eight (or more) letters at a time • called a block cipher – and use an extremely large number of ciphertext alphabets • will be called modes of operation 1
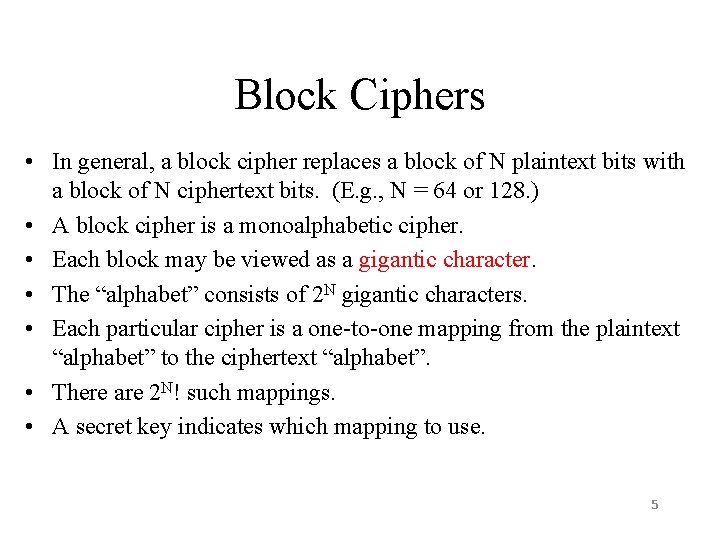
Block Ciphers • In general, a block cipher replaces a block of N plaintext bits with a block of N ciphertext bits. (E. g. , N = 64 or 128. ) • A block cipher is a monoalphabetic cipher. • Each block may be viewed as a gigantic character. • The “alphabet” consists of 2 N gigantic characters. • Each particular cipher is a one-to-one mapping from the plaintext “alphabet” to the ciphertext “alphabet”. • There are 2 N! such mappings. • A secret key indicates which mapping to use. 5
Ideal Block Cipher • An ideal block cipher would allow us to use any of these 2 N! mappings. – The key space would be extremely large. • But this would require a key of log 2(2 N!) bits. • If N = 64, log 2(2 N!) ≈ N x 2 N ≈ 1021 bits ≈ 1011 GB. • Infeasible! 6
Practical Block Ciphers • Modern block ciphers use a key of K bits to specify a random subset of 2 K mappings. • If K ≈ N, – 2 K is much smaller than 2 N! – But is still very large. • If the selection of the 2 K mappings is random, the resulting cipher will be a good approximation of the ideal block cipher. • Horst Feistel, in 1970 s, proposed a method to achieve this. 7
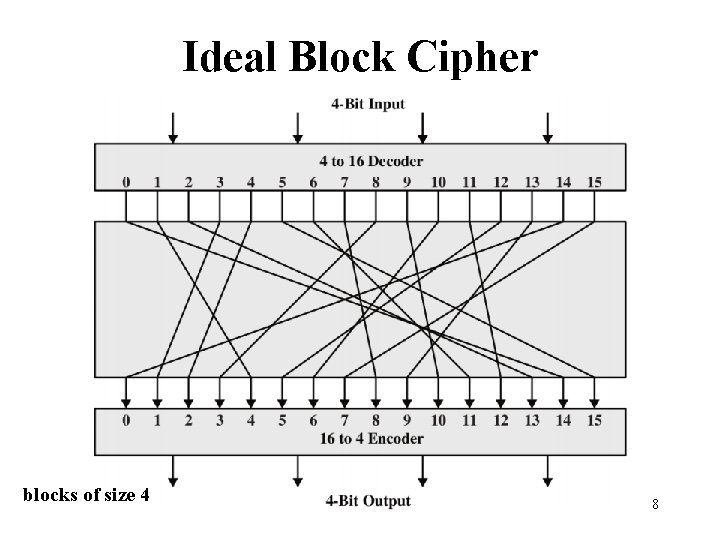
Ideal Block Cipher blocks of size 4 8
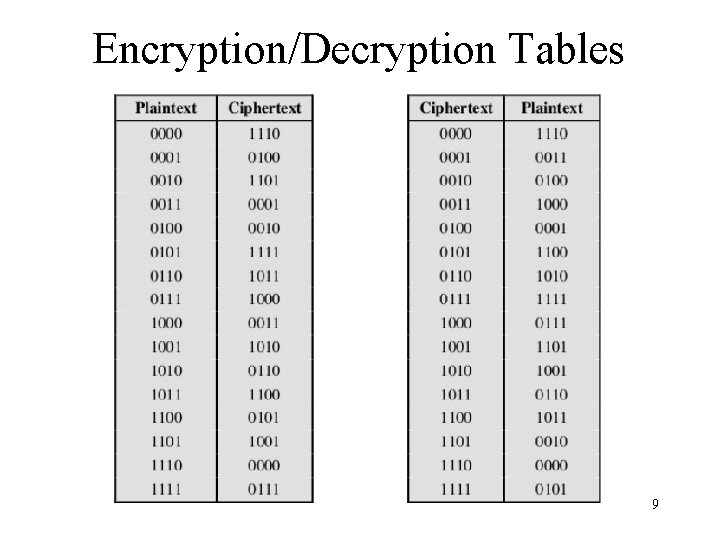
Encryption/Decryption Tables 9
Feistel Cipher Structure • Virtually all symmetric block encryption algorithms, including DES, have a structure first described by Horst Feistel of IBM in 1973 • The Feistel structure is a particular example of the more general structure used by all symmetric block ciphers. 10
Feistel Cipher Structure • Feistel proposed applying two or more simple ciphers in sequence so final result is cryptographically stronger than component ciphers • n-bit block length; k-bit key length; 2 k transformations • Feistel cipher alternates: substitutions, transpositions (permutations) • Applies concepts of diffusion and confusion • Applied in many ciphers today • Approach: – – – Plaintext split into halves Subkeys (or round keys) generated from key Round function, F, applied to right half Apply substitution on left half using XOR Apply permutation: interchange to halves 11
The Feistel Cipher Structure • • • Use the same basic algorithm for both encryption and decryption Input: a data block and a key Partition the data block into two halves L and R. Go through a number of rounds. In each round, – R does not change. – L goes through an operation that depends on R and a round key derived from the key. • A permutation is done by interchanging the two halves of the data, following the substitution 12
Simplified DES • • • Input (plaintext) block: 8 -bits Output (ciphertext) block: 8 -bits Key: 10 -bits Rounds: 2 Round keys generated using permutations and left shifts • Encryption: initial permutation, round function, switch halves • Decryption: Same as encryption, except round keys used in opposite order 13
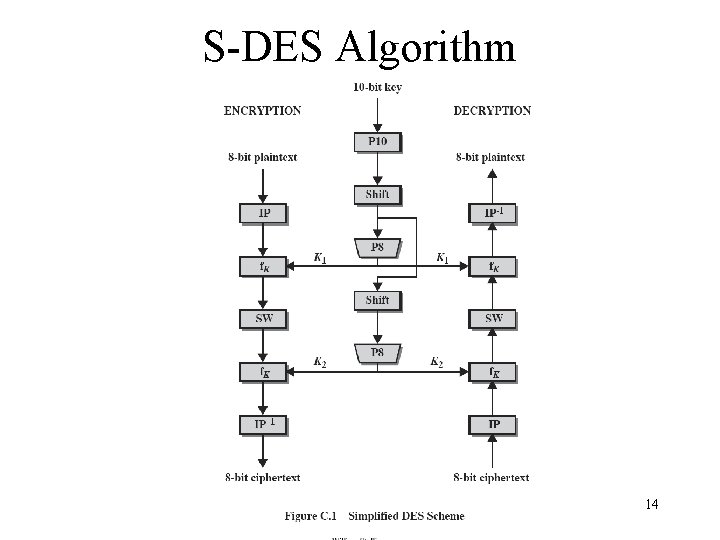
S-DES Algorithm 14
S-DES Operations • P 10 (permutate) Input : 1 2 3 4 5 6 7 8 9 10 Output: 3 5 2 7 4 10 1 9 8 6 • P 8 (select and permutate) Input : 1 2 3 4 5 6 7 8 9 10 Output: 6 3 7 4 8 5 10 9 • P 4 (permutate) Input : 1 2 3 4 Output: 2 4 3 1 15
S-DES Operations • EP (expand permutate) Input : 1 2 3 4 Output: 4 1 2 3 4 1 • IP (initial permutation) Input : 1 2 3 4 5 6 7 8 Output: 2 6 3 1 4 8 5 7 • IP 1 (inverse of IP) LS-1 (left shift 1 position) LS-2 (left shift 2 positions) 16
S-DES Example • Plaintext: 01110010 • Key: 1010000010 • Ciphertext: 0111 17
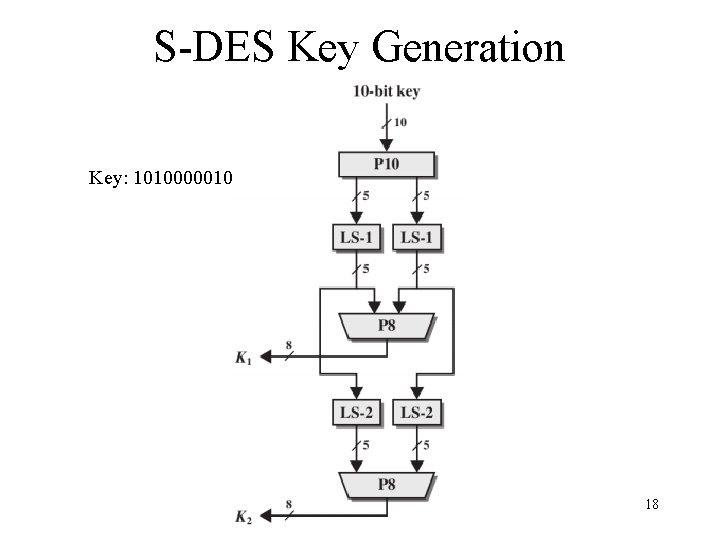
S-DES Key Generation Key: 1010000010 18
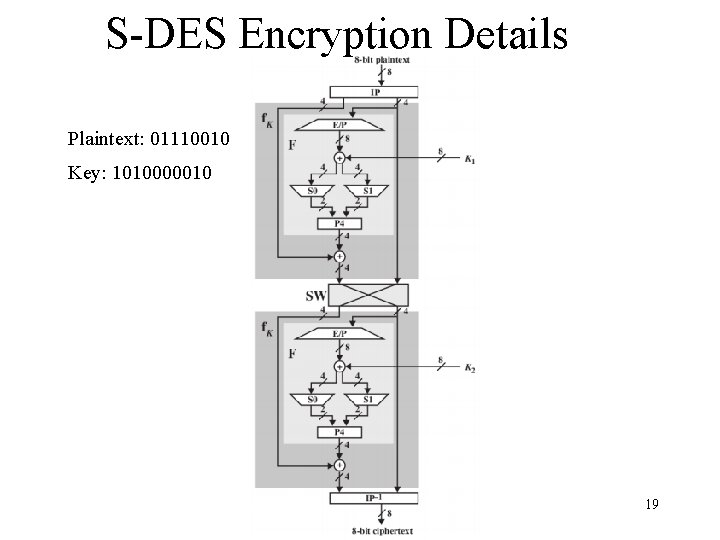
S-DES Encryption Details Plaintext: 01110010 Key: 1010000010 19
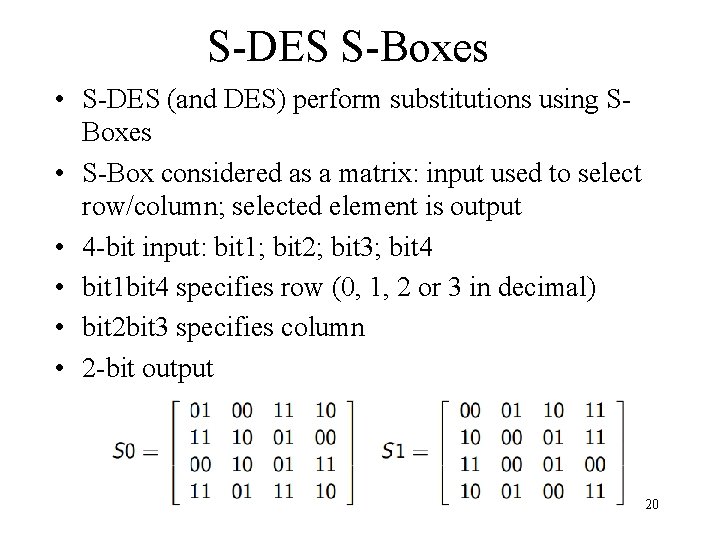
S-DES S-Boxes • S-DES (and DES) perform substitutions using SBoxes • S-Box considered as a matrix: input used to select row/column; selected element is output • 4 -bit input: bit 1; bit 2; bit 3; bit 4 • bit 1 bit 4 specifies row (0, 1, 2 or 3 in decimal) • bit 2 bit 3 specifies column • 2 -bit output 20
S-DES Summary • Educational encryption algorithm • S-DES expressed as functions: • Security of S-DES: – 10 -bit key, 1024 keys: brute force easy – If know plaintext and corresponding ciphertext, can we determine key? • Very hard 21
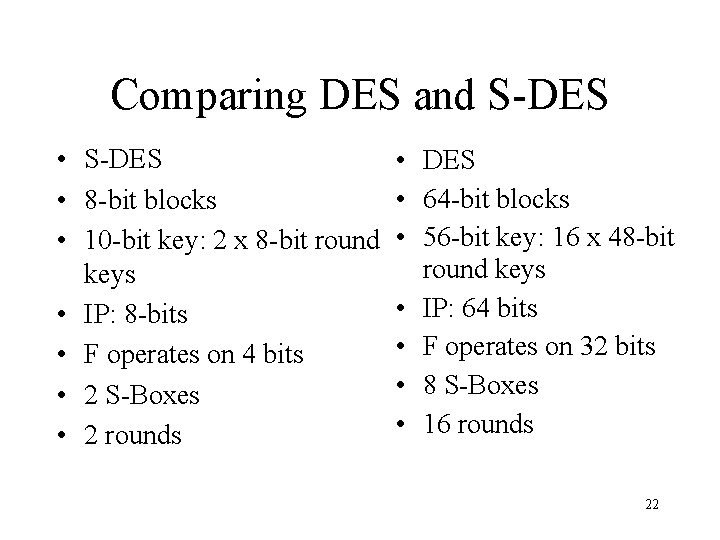
Comparing DES and S-DES • 8 -bit blocks • 10 -bit key: 2 x 8 -bit round keys • IP: 8 -bits • F operates on 4 bits • 2 S-Boxes • 2 rounds • DES • 64 -bit blocks • 56 -bit key: 16 x 48 -bit round keys • IP: 64 bits • F operates on 32 bits • 8 S-Boxes • 16 rounds 22
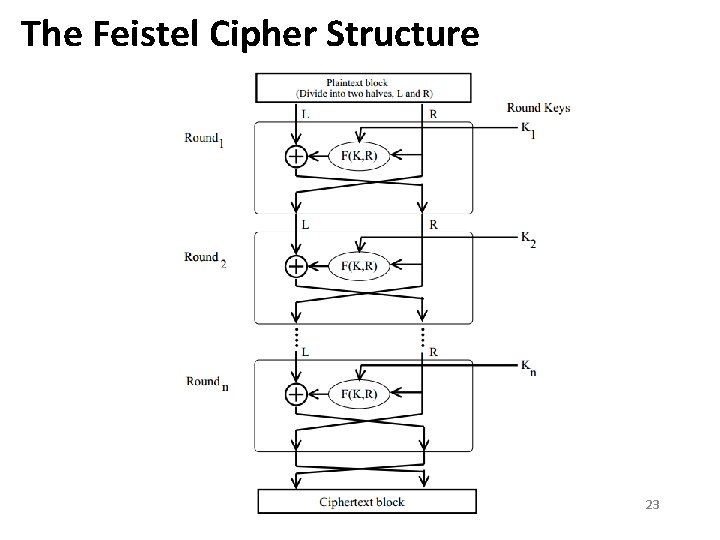
The Feistel Cipher Structure 23
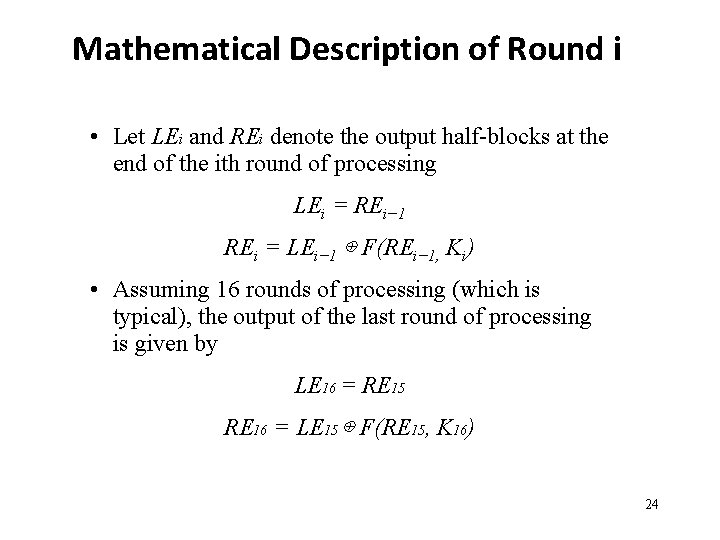
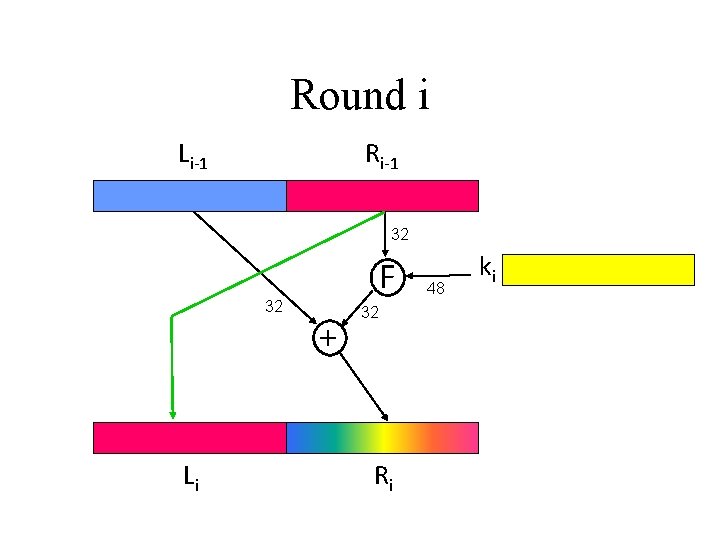
Mathematical Description of Round i • Let LEi and REi denote the output half-blocks at the end of the ith round of processing LEi = REi− 1 REi = LEi− 1 ⊕ F(REi− 1, Ki) • Assuming 16 rounds of processing (which is typical), the output of the last round of processing is given by LE 16 = RE 15 RE 16 = LE 15 ⊕ F(RE 15, K 16) 24
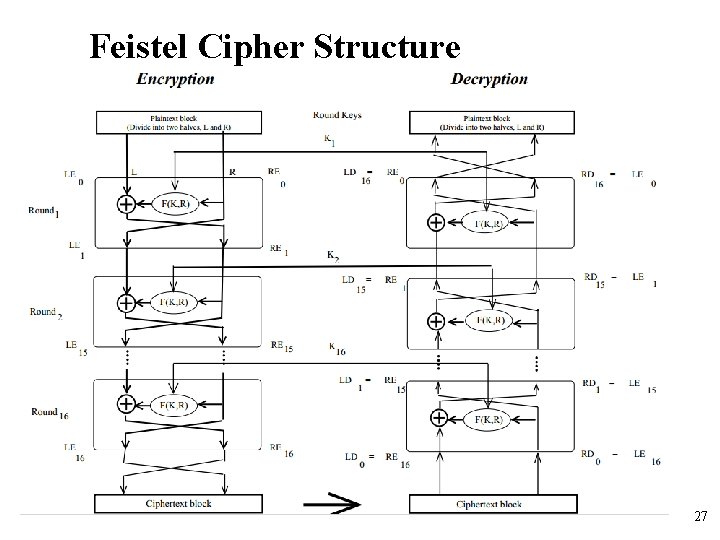
Feistel Cipher Structure • Decryption is the same process as the encryption process except the use of the ciphertext as input and the use of subkeys in reverse order(i. e. Kn 1 st, Kn-1 2 nd, and so on until k 1). • The realization of a Feistel Network depends on the choice of the following parameters and design features (see next slide): 25
Decryption in Ciphers Based on the Feistel Structure • The output of each round during decryption is the input to the corresponding round during encryption • let LDi and RDi denote the left half and the right half of the output of the ith round • The first decryption round LD 0 = RE 16 RD 0 = LE 16 • The first round of decryption is the same as the input to the last stage of the encryption round LD 1 = RE 15 RD 1 = LE 15 26
Feistel Cipher Structure 27
Feistel Cipher Structure • • Block size: larger block sizes mean greater security Key Size: larger key size means greater security Number of rounds: multiple rounds offer increasing security Subkey generation algorithm: greater complexity will lead to greater difficulty of cryptanalysis. • Round fuction : greater complexity means greater security • Fast software encryption/decryption: the speed of execution of the algorithm becomes a concern • Ease of analysis : leads ease of analysis for cryptanalytic vulnerability of the algorithm and a higher level of assurance 28
Data Encryption Standard (DES) • History of DES : LUCIFER – The first encryption algorithm in computer cryptography – Developed in 1971 as the result of a research project led by Horst Feistel, in IBM. – Sold to Lioyd’s of London for a cash-dispending system. – A block & product cipher operated in 64 -bit input block and 128 -bit key • A refined version of LUCIFER – Implemented on a single chip for a marketable commercial encryption product. – A reduced key size of 56 -bit. 29
DES: The Data Encryption Standard • Most widely used block cipher in the world. • Adopted by NIST in 1977. • Based on the Feistel cipher structure with 16 rounds of processing. • Block = 64 bits • Key = 56 bits 30
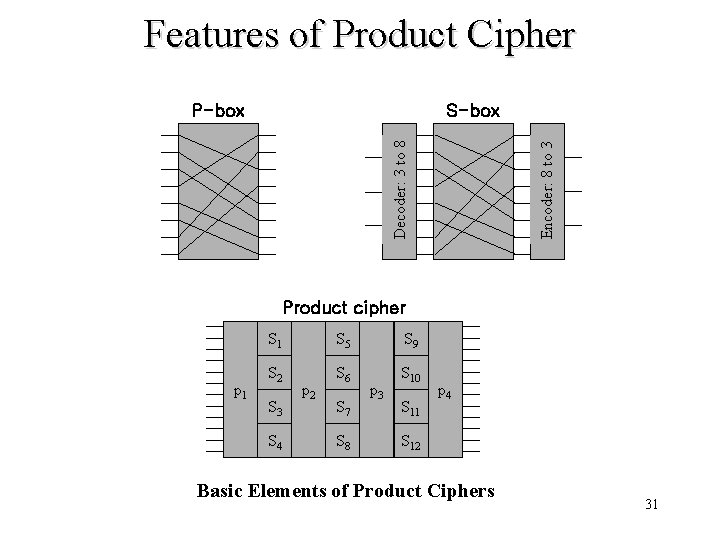
Features of Product Cipher S-box Encoder: 8 to 3 Decoder: 3 to 8 P-box Product cipher p 1 S 5 S 9 S 2 S 6 S 10 S 3 S 4 p 2 S 7 S 8 p 3 S 11 p 4 S 12 Basic Elements of Product Ciphers 31
Design Principles of DES • To achieve high degree of diffusion and confusion. • Diffusion: making each plaintext bit affect as many ciphertext bits as possible. • Confusion: making the relationship between the encryption key and the ciphertext as complex as possible. 1
DES Encryption • Two inputs to the encryption function – – • The 64 -bit plaintext to be encrypted The 56 -bit key Three phases for processing the plaintext 1. Rearrangement of the plaintext through an initial permutation to produce “permuted input” 2 -1 16 iterations of the same function, which consists of permutation and substitution functions with key 2 -2 Swap of left and right halves from output of the last iteration to produce “preoutput” 3. Inverse of the initial permutation on the preoutput to produce the “ 64 -bit ciphertext” 33
DES Encryption • Two phases of Key Generation 1. Permutation on the key input. 2. For each of the 16 iterations, - a subkey(Ki) is produced by the combination of left circular shift and permutation. - the permutation function is the same for each iteration - but, a different subkey is output because of the repeated shifting of the key bits 34
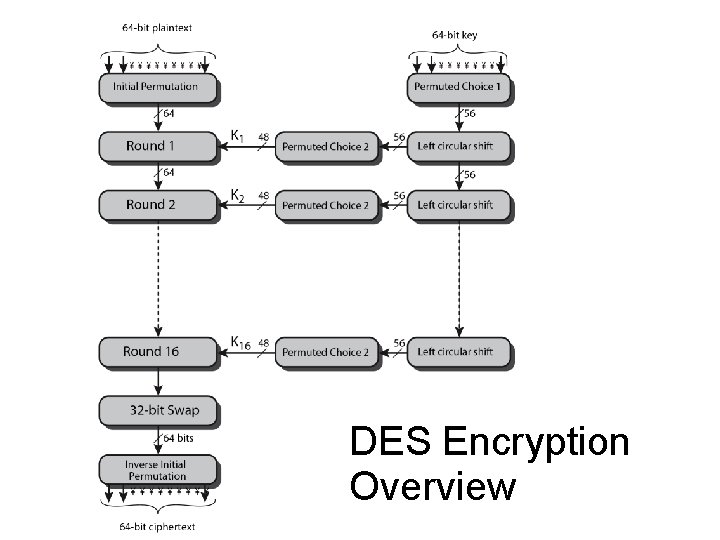
DES Encryption Overview
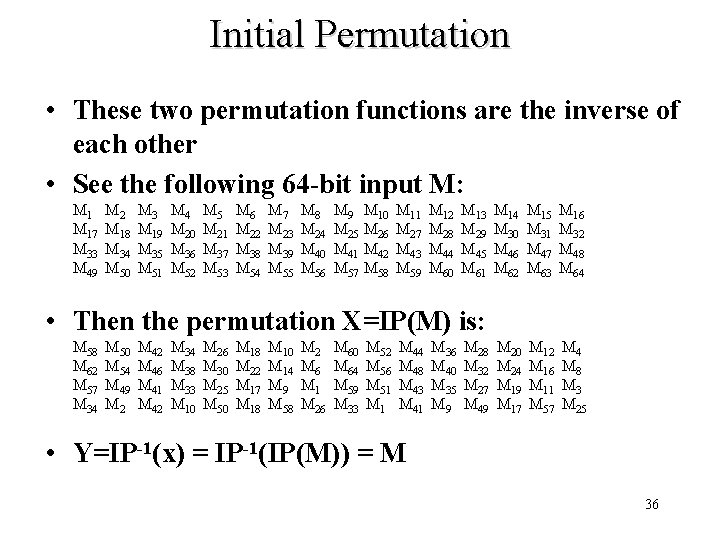
Initial Permutation • These two permutation functions are the inverse of each other • See the following 64 -bit input M: M 17 M 33 M 49 M 2 M 18 M 34 M 50 M 3 M 19 M 35 M 51 M 4 M 20 M 36 M 52 M 5 M 21 M 37 M 53 M 6 M 22 M 38 M 54 M 7 M 23 M 39 M 55 M 8 M 24 M 40 M 56 M 9 M 25 M 41 M 57 M 10 M 26 M 42 M 58 M 11 M 27 M 43 M 59 M 12 M 28 M 44 M 60 M 13 M 29 M 45 M 61 M 14 M 30 M 46 M 62 M 15 M 31 M 47 M 63 M 16 M 32 M 48 M 64 M 20 M 24 M 19 M 17 M 12 M 16 M 11 M 57 M 4 M 8 M 3 M 25 • Then the permutation X=IP(M) is: M 58 M 62 M 57 M 34 M 50 M 54 M 49 M 2 M 46 M 41 M 42 M 34 M 38 M 33 M 10 M 26 M 30 M 25 M 50 M 18 M 22 M 17 M 18 M 10 M 14 M 9 M 58 M 2 M 6 M 1 M 26 M 60 M 64 M 59 M 33 M 52 M 56 M 51 M 44 M 48 M 43 M 41 M 36 M 40 M 35 M 9 M 28 M 32 M 27 M 49 • Y=IP-1(x) = IP-1(IP(M)) = M 36
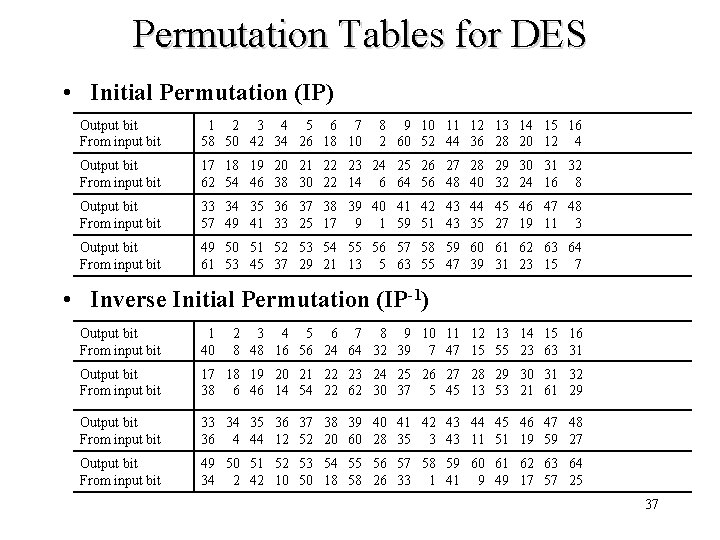
Permutation Tables for DES • Initial Permutation (IP) Output bit From input bit 1 2 3 4 5 6 7 58 50 42 34 26 18 10 8 9 10 11 12 13 14 15 16 2 60 52 44 36 28 20 12 4 Output bit From input bit 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 62 54 46 38 30 22 14 6 64 56 48 40 32 24 16 8 Output bit From input bit 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 57 49 41 33 25 17 9 1 59 51 43 35 27 19 11 3 Output bit From input bit 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 61 53 45 37 29 21 13 5 63 55 47 39 31 23 15 7 • Inverse Initial Permutation (IP-1) Output bit From input bit 1 40 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 8 48 16 56 24 64 32 39 7 47 15 55 23 63 31 Output bit From input bit 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 38 6 46 14 54 22 62 30 37 5 45 13 53 21 61 29 Output bit From input bit 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 36 4 44 12 52 20 60 28 35 3 43 11 51 19 59 27 Output bit From input bit 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 34 2 42 10 50 18 58 26 33 1 41 9 49 17 57 25 37
Round i Li-1 Ri-1 32 32 Li F + 32 Ri 48 ki
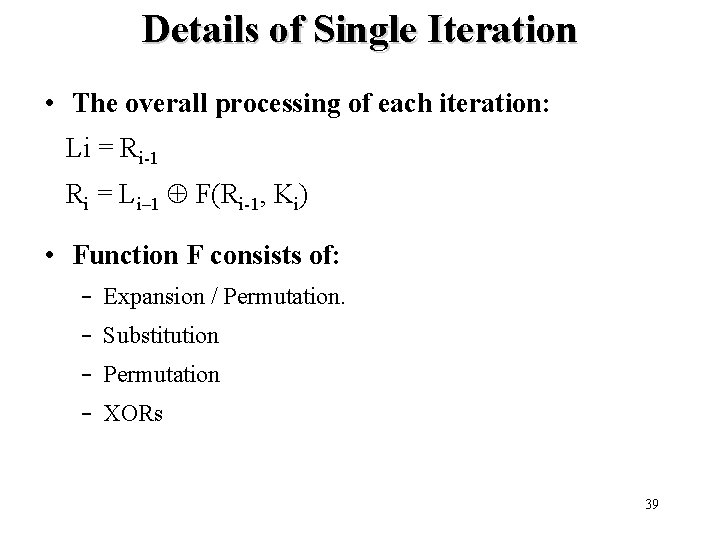
Details of Single Iteration • The overall processing of each iteration: Li = Ri-1 Ri = Li– 1 F(Ri-1, Ki) • Function F consists of: – Expansion / Permutation. – Substitution – Permutation – XORs 39
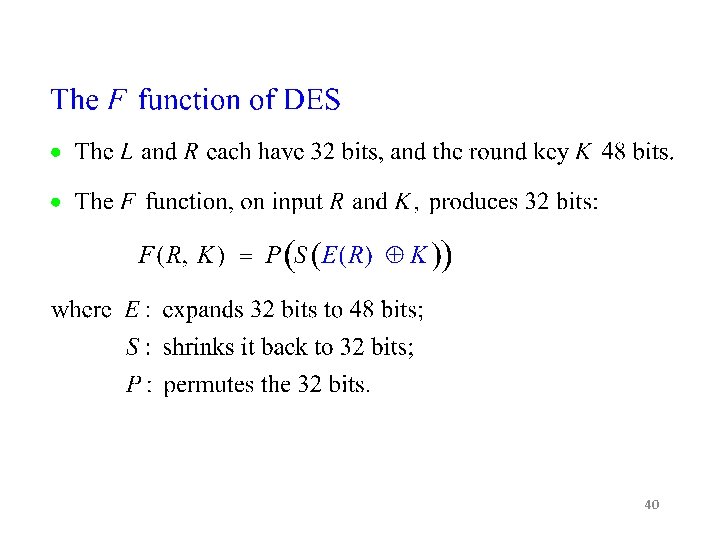
40
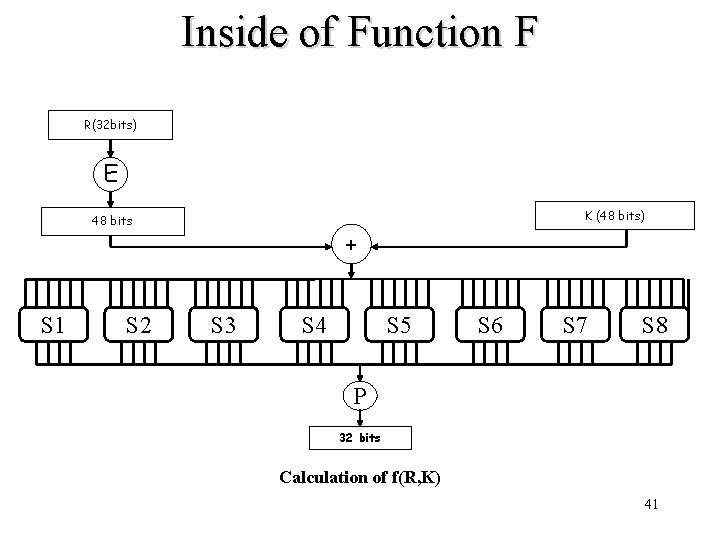
Inside of Function F R(32 bits) E K (48 bits) 48 bits S 1 S 2 + S 3 S 4 S 5 S 6 S 7 S 8 P 32 bits Calculation of f(R, K) 41
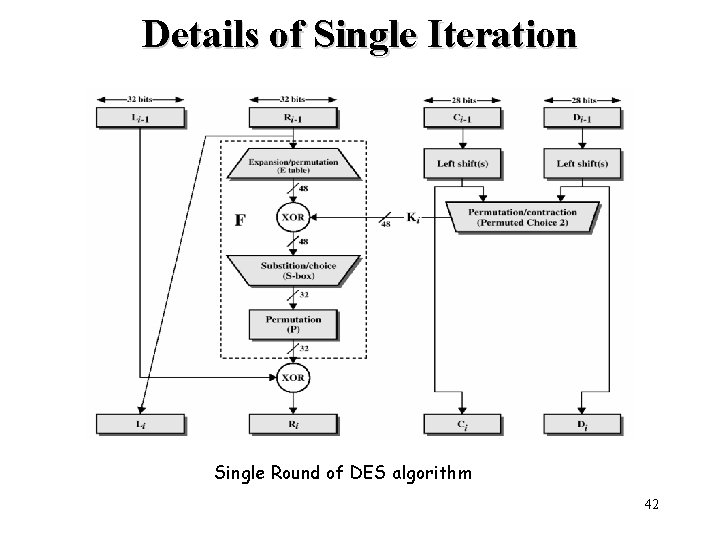
Details of Single Iteration Single Round of DES algorithm 42
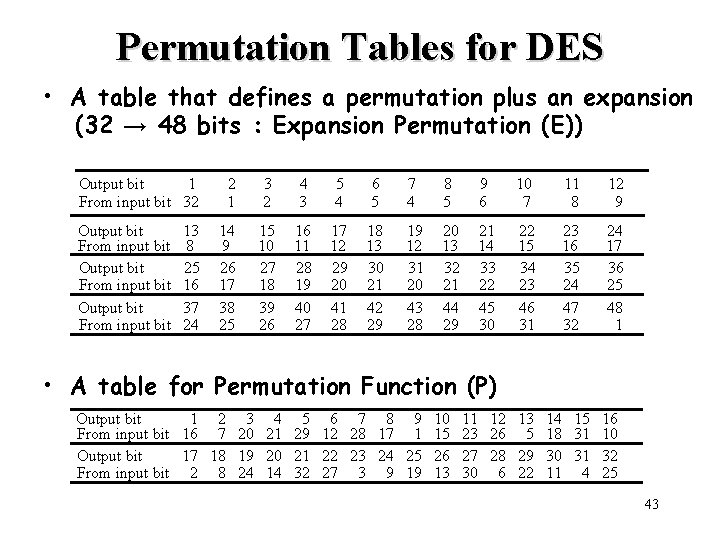
Permutation Tables for DES • A table that defines a permutation plus an expansion (32 → 48 bits : Expansion Permutation (E)) Output bit 1 From input bit 32 Output bit From input bit 13 8 25 16 37 24 2 1 3 2 4 3 5 4 6 5 7 4 8 5 9 6 10 7 11 8 12 9 14 9 26 17 38 25 15 10 27 18 39 26 16 11 28 19 40 27 17 12 29 20 41 28 18 13 30 21 42 29 19 12 31 20 43 28 20 13 32 21 44 29 21 14 33 22 45 30 22 15 34 23 46 31 23 16 35 24 47 32 24 17 36 25 48 1 • A table for Permutation Function (P) Output bit 1 2 3 4 5 6 7 8 9 From input bit 16 7 20 21 29 12 28 17 1 Output bit 17 18 19 20 21 22 23 24 25 From input bit 2 8 24 14 32 27 3 9 19 10 15 26 13 11 12 13 14 15 16 23 26 5 18 31 10 27 28 29 30 31 32 30 6 22 11 4 25 43
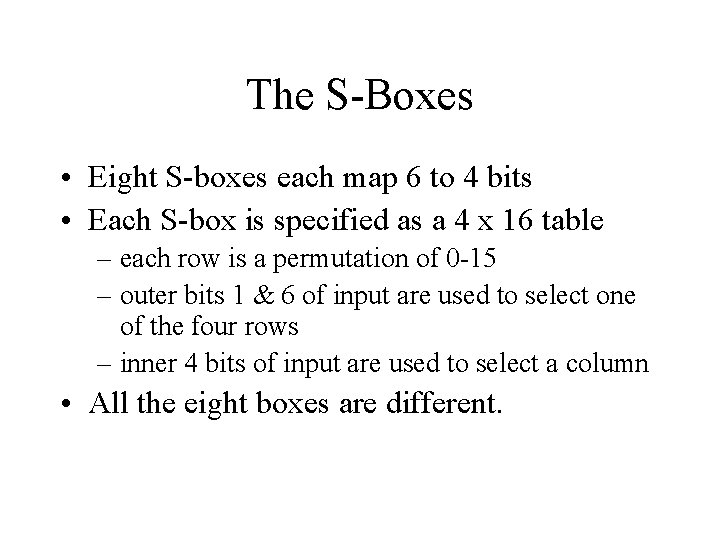
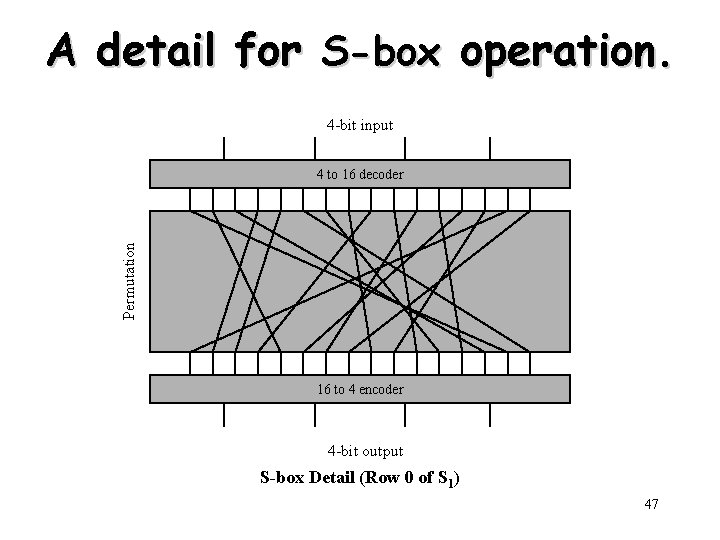
The S-Boxes • Eight S-boxes each map 6 to 4 bits • Each S-box is specified as a 4 x 16 table – each row is a permutation of 0 -15 – outer bits 1 & 6 of input are used to select one of the four rows – inner 4 bits of input are used to select a column • All the eight boxes are different.
Substitution • Transformation rule – The first & last bits of 6 -bit input select a particular row in the table for Si – The middle 4 -bit select a particular column. – The value crossed at the row & column is converted to its 4 bit output. • For example, given input 011010 for S 1, – Row 0 & column 13 select the value 9. – The output is 1001 45
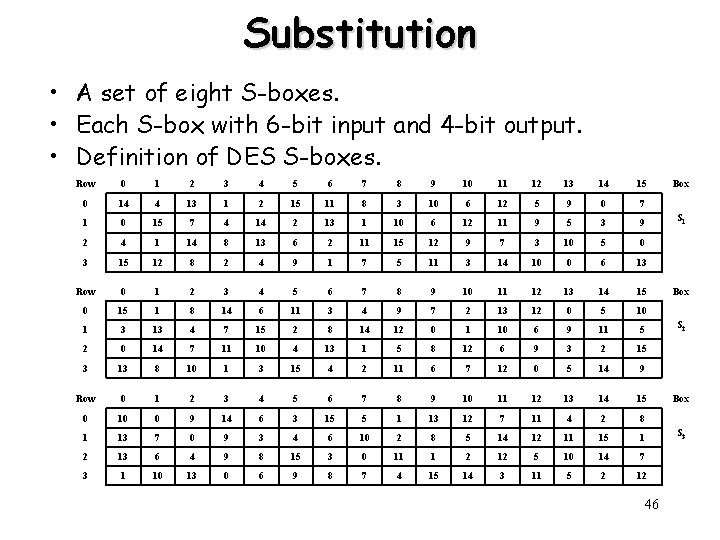
Substitution • A set of eight S-boxes. • Each S-box with 6 -bit input and 4 -bit output. • Definition of DES S-boxes. Row 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 0 14 4 13 1 2 15 11 8 3 10 6 12 5 9 0 7 1 0 15 7 4 14 2 13 1 10 6 12 11 9 5 3 9 2 4 1 14 8 13 6 2 11 15 12 9 7 3 10 5 0 3 15 12 8 2 4 9 1 7 5 11 3 14 10 0 6 13 Row 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 0 15 1 8 14 6 11 3 4 9 7 2 13 12 0 5 10 1 3 13 4 7 15 2 8 14 12 0 1 10 6 9 11 5 2 0 14 7 11 10 4 13 1 5 8 12 6 9 3 2 15 3 13 8 10 1 3 15 4 2 11 6 7 12 0 5 14 9 Row 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 0 10 0 9 14 6 3 15 5 1 13 12 7 11 4 2 8 1 13 7 0 9 3 4 6 10 2 8 5 14 12 11 15 1 2 13 6 4 9 8 15 3 0 11 1 2 12 5 10 14 7 3 1 10 13 0 6 9 8 7 4 15 14 3 11 5 2 12 46 Box S 1 Box S 2 Box S 3
A detail for S-box operation. 4 -bit input Permutation 4 to 16 decoder 16 to 4 encoder 4 -bit output S-box Detail (Row 0 of S 1) 47
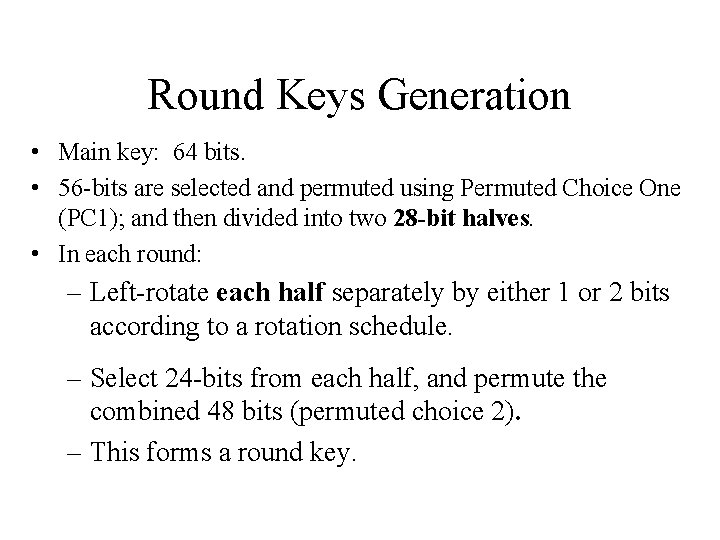
Round Keys Generation • Main key: 64 bits. • 56 -bits are selected and permuted using Permuted Choice One (PC 1); and then divided into two 28 -bit halves. • In each round: – Left-rotate each half separately by either 1 or 2 bits according to a rotation schedule. – Select 24 -bits from each half, and permute the combined 48 bits (permuted choice 2). – This forms a round key.
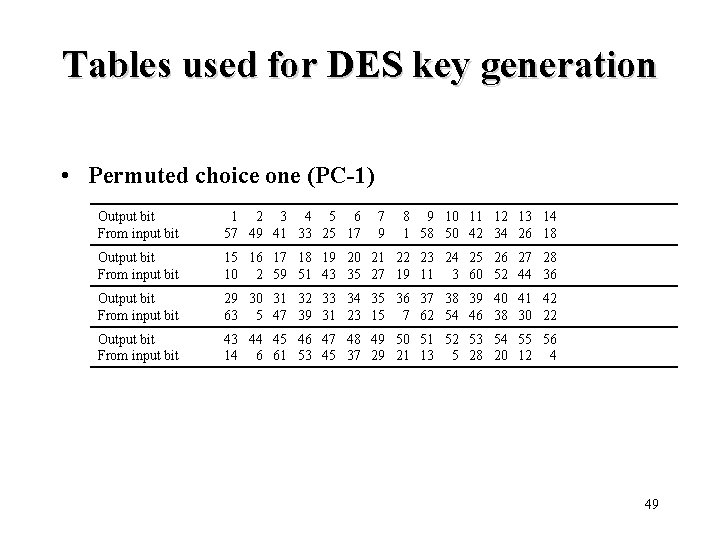
Tables used for DES key generation • Permuted choice one (PC-1) Output bit From input bit 1 2 3 4 5 6 57 49 41 33 25 17 7 9 8 9 10 11 12 13 14 1 58 50 42 34 26 18 Output bit From input bit 15 16 17 18 19 20 21 22 23 24 25 26 27 28 10 2 59 51 43 35 27 19 11 3 60 52 44 36 Output bit From input bit 29 30 31 32 33 34 35 36 37 38 39 40 41 42 63 5 47 39 31 23 15 7 62 54 46 38 30 22 Output bit From input bit 43 44 45 46 47 48 49 50 51 52 53 54 55 56 14 6 61 53 45 37 29 21 13 5 28 20 12 4 49
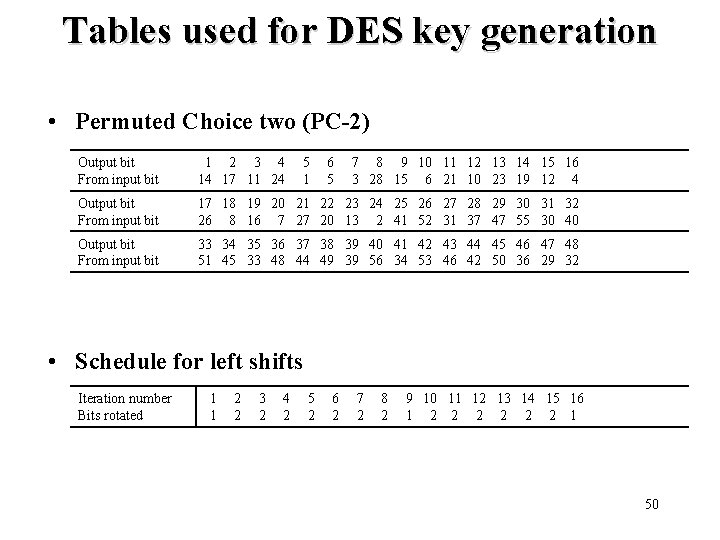
Tables used for DES key generation • Permuted Choice two (PC-2) Output bit From input bit 1 2 3 4 14 17 11 24 5 1 6 5 7 8 9 10 11 12 13 14 15 16 3 28 15 6 21 10 23 19 12 4 Output bit From input bit 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 26 8 16 7 27 20 13 2 41 52 31 37 47 55 30 40 Output bit From input bit 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 51 45 33 48 44 49 39 56 34 53 46 42 50 36 29 32 • Schedule for left shifts Iteration number Bits rotated 1 1 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 10 11 12 13 14 15 16 1 2 2 2 1 50
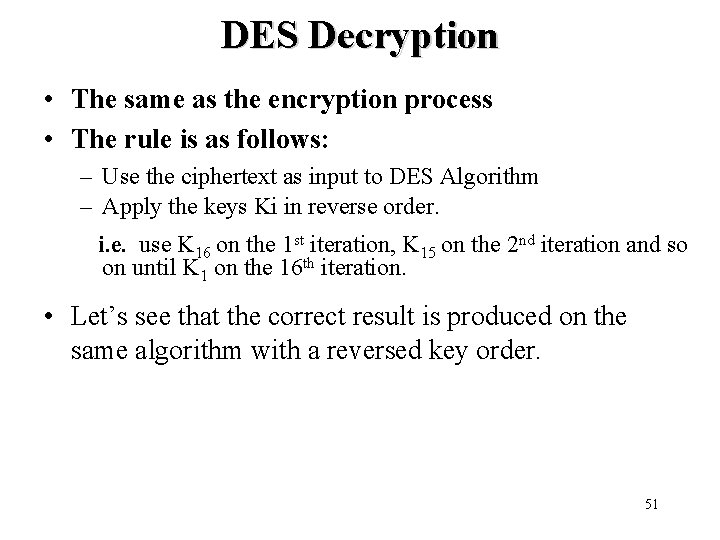
DES Decryption • The same as the encryption process • The rule is as follows: – Use the ciphertext as input to DES Algorithm – Apply the keys Ki in reverse order. i. e. use K 16 on the 1 st iteration, K 15 on the 2 nd iteration and so on until K 1 on the 16 th iteration. • Let’s see that the correct result is produced on the same algorithm with a reversed key order. 51
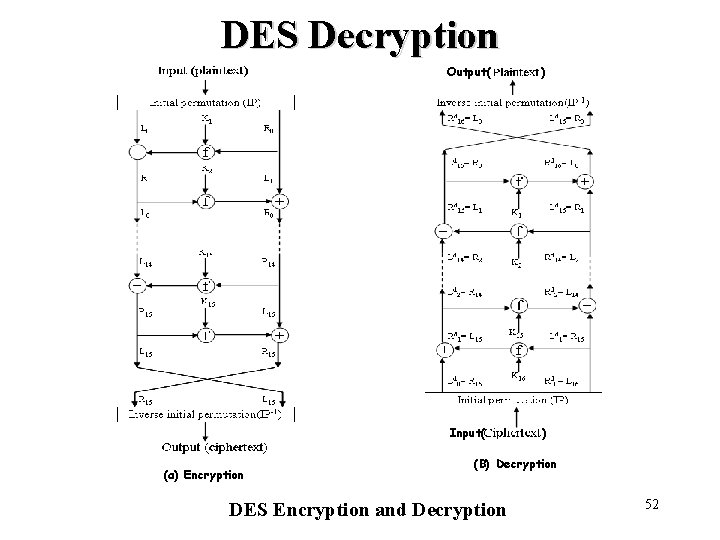
DES Decryption (a) Encryption Output( ) Input( ) (B) Decryption DES Encryption and Decryption 52
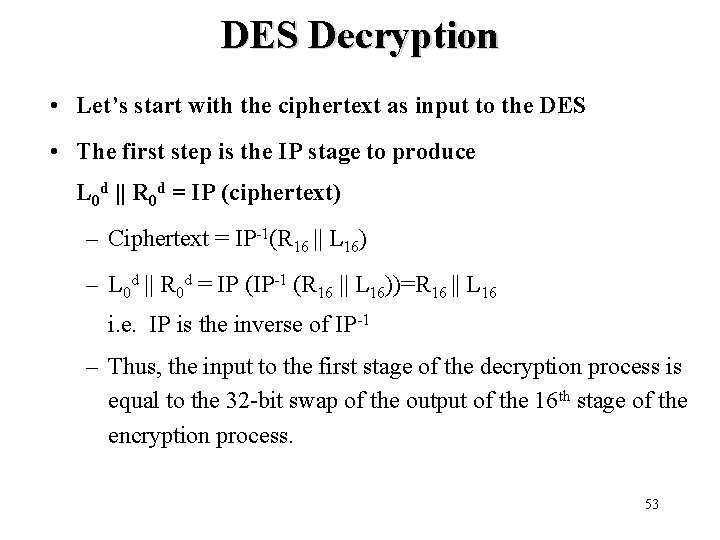
DES Decryption • Let’s start with the ciphertext as input to the DES • The first step is the IP stage to produce L 0 d || R 0 d = IP (ciphertext) – Ciphertext = IP-1(R 16 || L 16) – L 0 d || R 0 d = IP (IP-1 (R 16 || L 16))=R 16 || L 16 i. e. IP is the inverse of IP-1 – Thus, the input to the first stage of the decryption process is equal to the 32 -bit swap of the output of the 16 th stage of the encryption process. 53
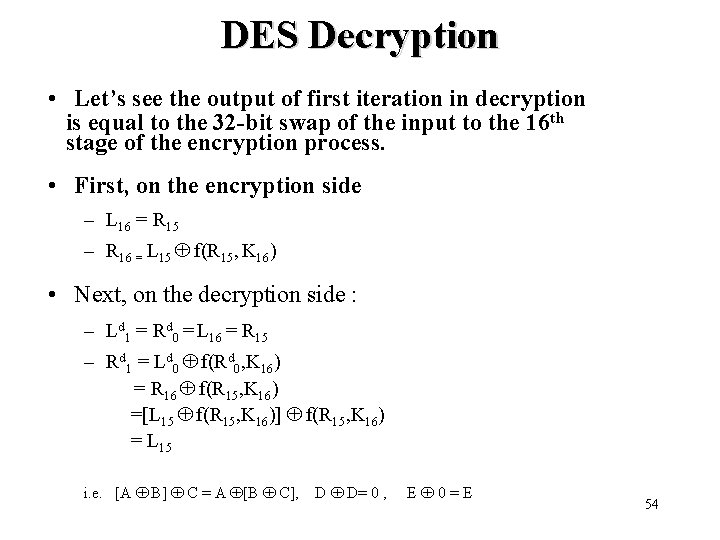
DES Decryption • Let’s see the output of first iteration in decryption is equal to the 32 -bit swap of the input to the 16 th stage of the encryption process. • First, on the encryption side – L 16 = R 15 – R 16 = L 15 f(R 15, K 16) • Next, on the decryption side : – Ld 1 = Rd 0 = L 16 = R 15 – Rd 1 = Ld 0 f(Rd 0, K 16) = R 16 f(R 15, K 16) =[L 15 f(R 15, K 16)] f(R 15, K 16) = L 15 i. e. [A B] C = A [B C], D D= 0 , E 0=E 54
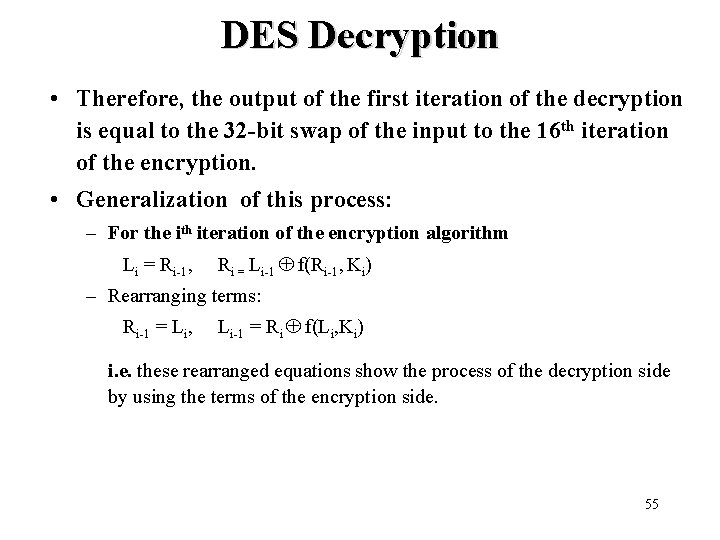
DES Decryption • Therefore, the output of the first iteration of the decryption is equal to the 32 -bit swap of the input to the 16 th iteration of the encryption. • Generalization of this process: – For the ith iteration of the encryption algorithm Li = Ri-1, Ri = Li-1 f(Ri-1, Ki) – Rearranging terms: Ri-1 = Li, Li-1 = Ri f(Li, Ki) i. e. these rearranged equations show the process of the decryption side by using the terms of the encryption side. 55
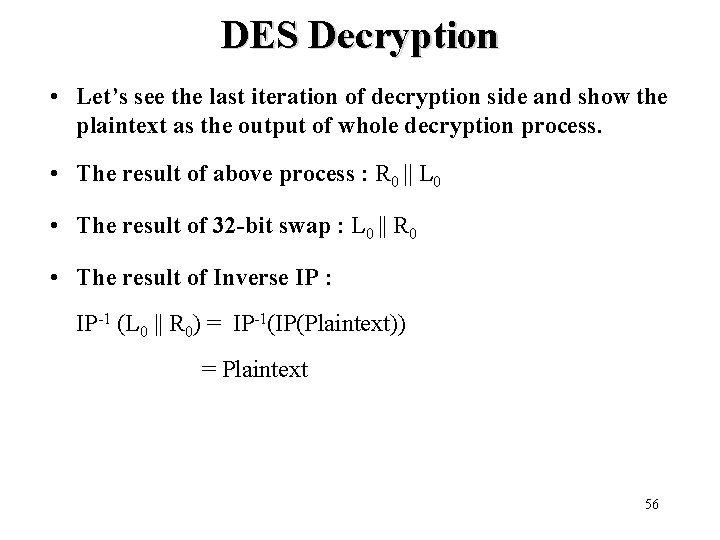
DES Decryption • Let’s see the last iteration of decryption side and show the plaintext as the output of whole decryption process. • The result of above process : R 0 || L 0 • The result of 32 -bit swap : L 0 || R 0 • The result of Inverse IP : IP-1 (L 0 || R 0) = IP-1(IP(Plaintext)) = Plaintext 56
Avalanche Effect • Avalanche effect: – A small change in the plaintext or in the key results in a significant change in the ciphertext. – an evidence of high degree of diffusion and confusion – a desirable property of any encryption algorithm • DES exhibits a strong avalanche effect – Changing 1 bit in the plaintext affects 34 bits in the ciphertext on average. – 1 -bit change in the key affects 35 bits in the ciphertext on average.
Avalanche Effect • Following examples show the number of bits that change in output when two different inputs are used, differing by 1 bit – Plaintext 1: 02468 aceeca 86420 Plaintext 2: 12468 aceeca 86420 Ciphertext difference: 32 bits – Key 1: 0 f 1571 c 947 d 9 e 859 Key 2: 1 f 1571 c 947 d 9 e 859 Ciphertext difference: 30 58
Attacks on DES • Brute-force key search – Needs only two plaintext-ciphertext samples – Trying 1 key per microsecond would take 1000+ years on average, due to the large key space size, 256 ≈ 7. 2× 1016. • Differential cryptanalysis – Possible to find a key with 247 plaintext-ciphertext samples – Known-plaintext attack • Liner cryptanalysis: – Possible to find a key with 243 plaintext-ciphertext samples – Known-plaintext attack 59
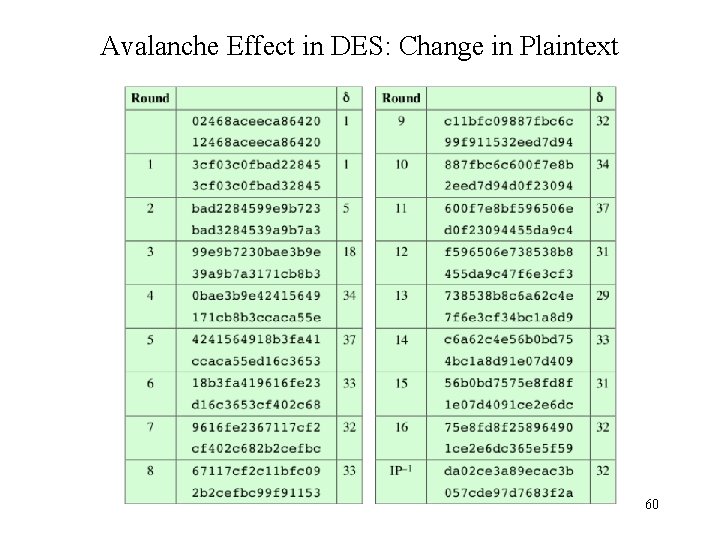
Avalanche Effect in DES: Change in Plaintext 60
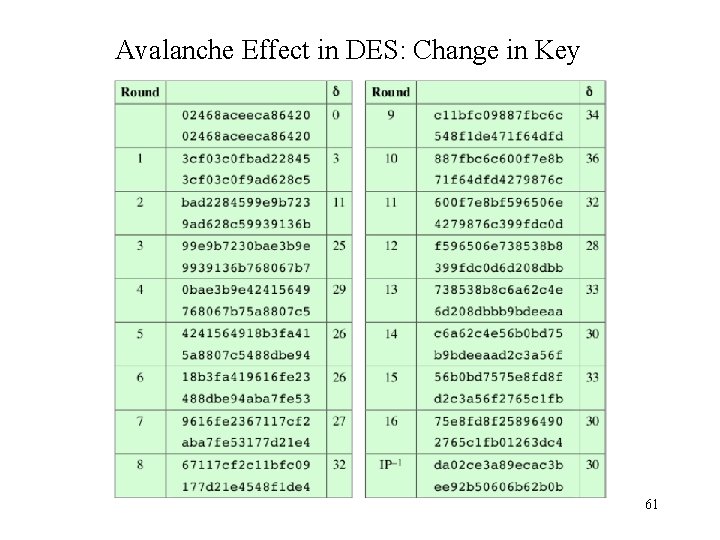
Avalanche Effect in DES: Change in Key 61
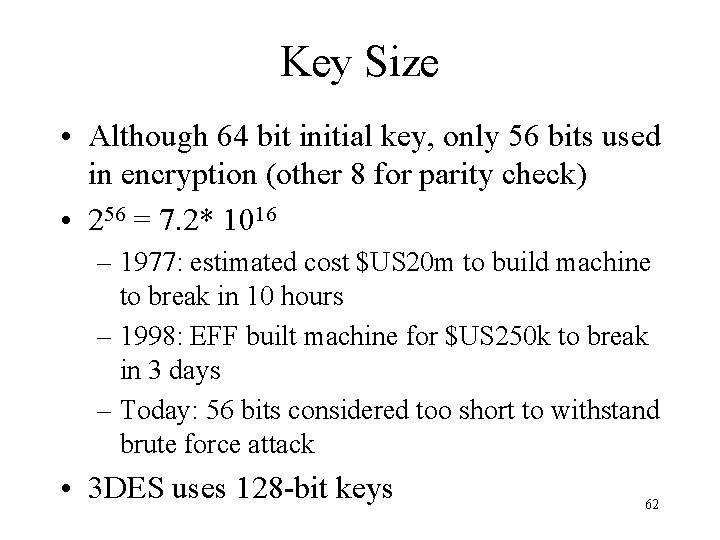
Key Size • Although 64 bit initial key, only 56 bits used in encryption (other 8 for parity check) • 256 = 7. 2* 1016 – 1977: estimated cost $US 20 m to build machine to break in 10 hours – 1998: EFF built machine for $US 250 k to break in 3 days – Today: 56 bits considered too short to withstand brute force attack • 3 DES uses 128 -bit keys 62
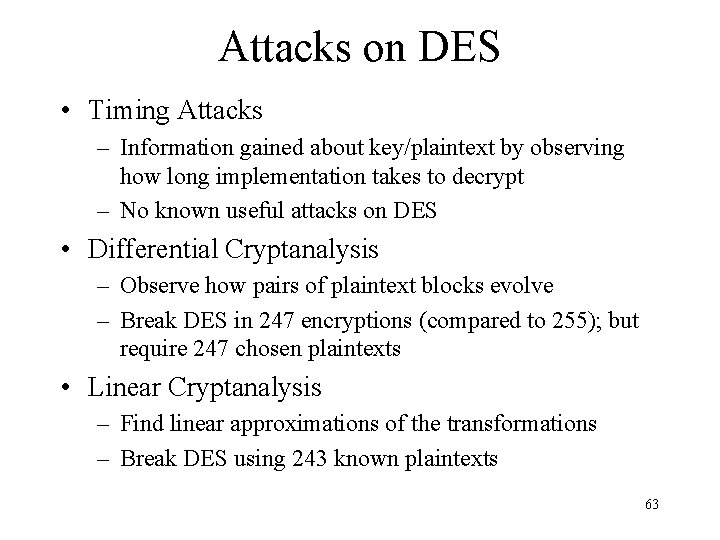
Attacks on DES • Timing Attacks – Information gained about key/plaintext by observing how long implementation takes to decrypt – No known useful attacks on DES • Differential Cryptanalysis – Observe how pairs of plaintext blocks evolve – Break DES in 247 encryptions (compared to 255); but require 247 chosen plaintexts • Linear Cryptanalysis – Find linear approximations of the transformations – Break DES using 243 known plaintexts 63
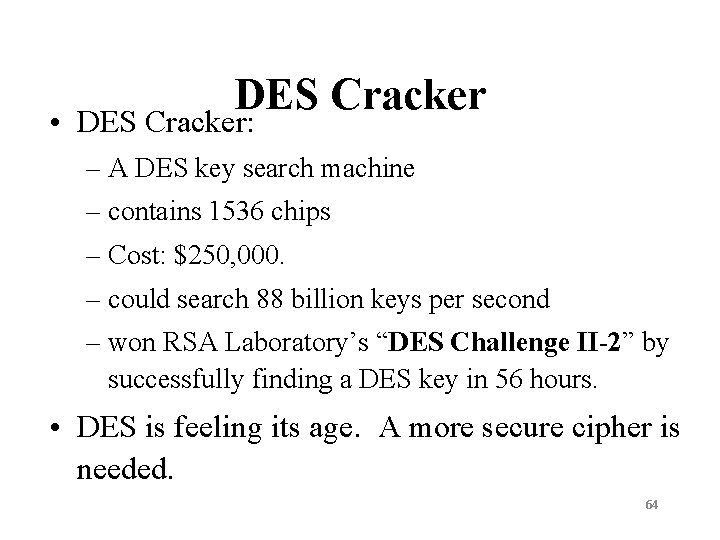
DES Cracker • DES Cracker: – A DES key search machine – contains 1536 chips – Cost: $250, 000. – could search 88 billion keys per second – won RSA Laboratory’s “DES Challenge II-2” by successfully finding a DES key in 56 hours. • DES is feeling its age. A more secure cipher is needed. 64
DES Algorithm Design • DES was designed in private; questions about the motivation of the design – S-Boxes provide non-linearity: important part of DES, generally considered to be secure – S-Boxes provide increased confusion – Permutation P chosen to increase diffusion 65
Multiple Encryption with DES • In 2001, NIST published the Advanced Encryption Standard (AES) to replace DES. • But users in commerce and finance are not ready to give up on DES. • As a temporary solution to DES’s security problem, one may encrypt a message (with DES) multiple times using multiple keys: – 2 DES is not much securer than the regular DES – So, 3 DES with either 2 or 3 keys is used – Triple DES (3 DES) with 2 keys: brute force 2112 – 3. Triple DES with 3 keys: brute force 2168 66
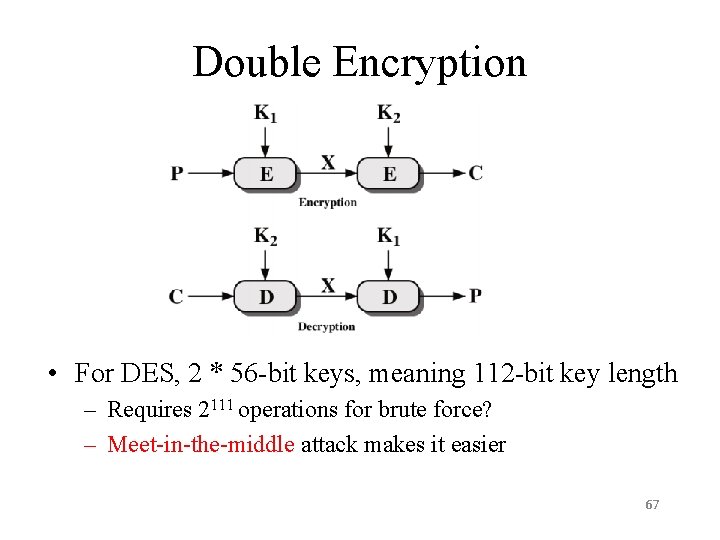
Double Encryption • For DES, 2 * 56 -bit keys, meaning 112 -bit key length – Requires 2111 operations for brute force? – Meet-in-the-middle attack makes it easier 67
Meet-in-the-Middle Attack on 2 DES • Double DES Encryption: C = E(K 2; E(K 1; P)) • Say X = E(K 1; P) = D(K 2; C) • Attacker knows two plaintext, ciphertext pairs (Pa; Ca) and (Pb; Cb) 1. Encrypt Pa using all 256 values of K 1 to get multiple values of X 2. Store results in table and sort by X 3. Decrypt Ca using al 256 values of K 2 4. As each decryption result produced, check against table 5. If match, check current K 1; K 2 on Cb. If Pb obtained, then accept the keys • With two known plaintext, ciphertext pairs, probability of successful attack is almost 1 – Encrypt/decrypt operations required: 256 (twice as many as single DES) 68
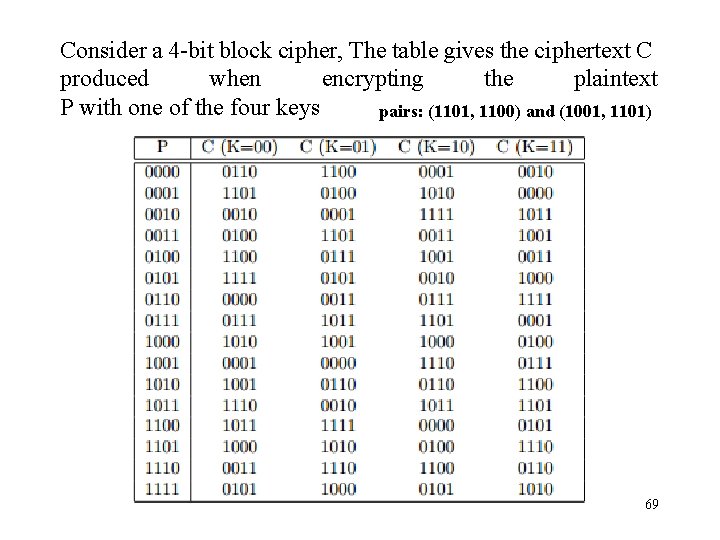
Consider a 4 -bit block cipher, The table gives the ciphertext C produced when encrypting the plaintext P with one of the four keys pairs: (1101, 1100) and (1001, 1101) 69
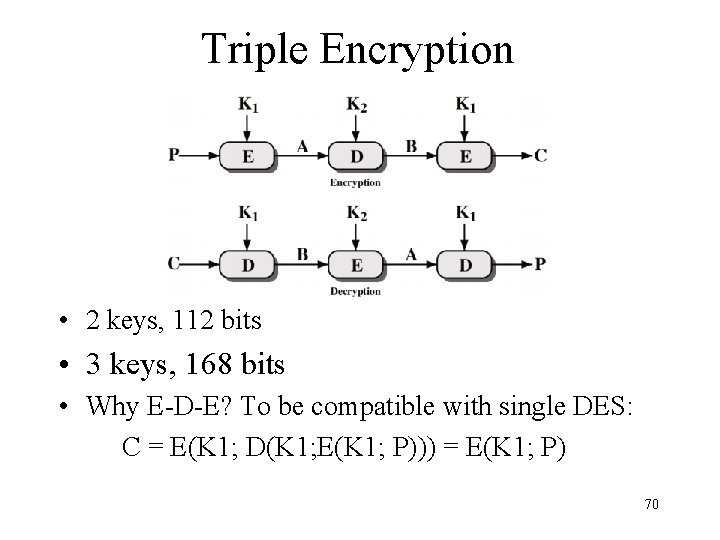
Triple Encryption • 2 keys, 112 bits • 3 keys, 168 bits • Why E-D-E? To be compatible with single DES: C = E(K 1; D(K 1; E(K 1; P))) = E(K 1; P) 70
Triple DES • Two attractions for its widespread use over the next few years: – Its 168 -bit key length to overcome the vulnerability to bruteforce attack – Use of DEA with a high level confidence as the underlying encryption algorithm in 3 DES • Drawbacks: – Relative sluggishness in software. – Use of a 64 -bit block size; a larger block size is required for both efficiency and security – So, 3 DES is not a reasonable candidate for long-term use. 71
- Slides: 71