Chapter 2 Block Ciphers and the Data Encryption
Chapter -2 Block Ciphers and the Data Encryption Standard Cryptography Techniques (CNET-326)
Block vs Stream Ciphers Ø Block ciphers process messages in blocks, each of which is then encrypted/decrypted. Ø like a substitution on very big characters l 64 -bits or more Ø Stream ciphers process messages a bit or byte at a time when encrypted/decrypted.
Block Cipher Principles Most symmetric block ciphers are based on a Feistel Cipher Structure Ø needed since must be able to decrypt ciphertext to recover messages efficiently Ø block ciphers look like an extremely large substitution Ø would need table of 264 entries for a 64 -bit block Ø instead create from smaller building blocks Ø using idea of a product cipher Ø
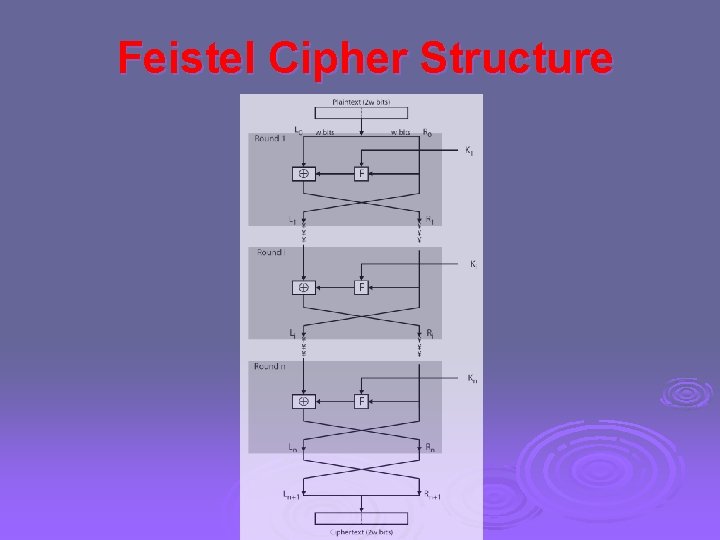
Feistel Cipher Structure
Feistel Cipher Design Elements Ø block size Ø key size Ø number of rounds Ø subkey generation algorithm Ø round function Ø fast software en/decryption Ø ease of analysis
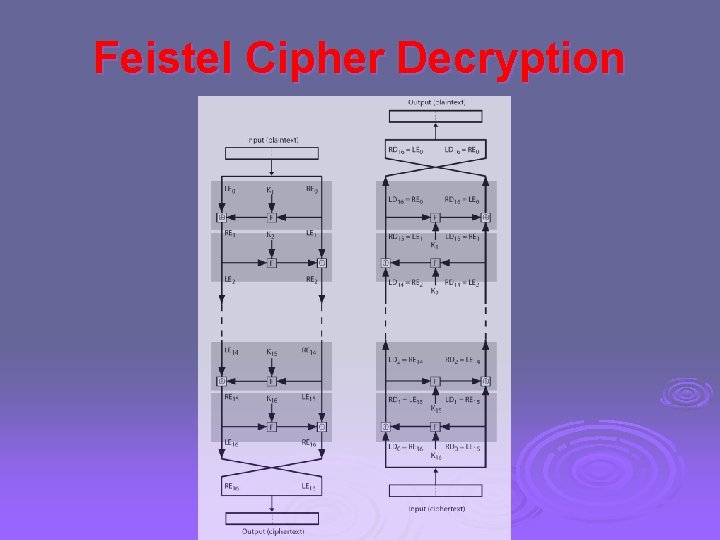
Feistel Cipher Decryption
Data Encryption Standard (DES) Ø Most widely used block cipher in world Ø adopted in 1977 by NBS (now NIST) l as FIPS PUB 46. Ø Encrypts 64 -bit data using 56 -bit key Ø Has widespread use Ø Has been considerable controversy over its security
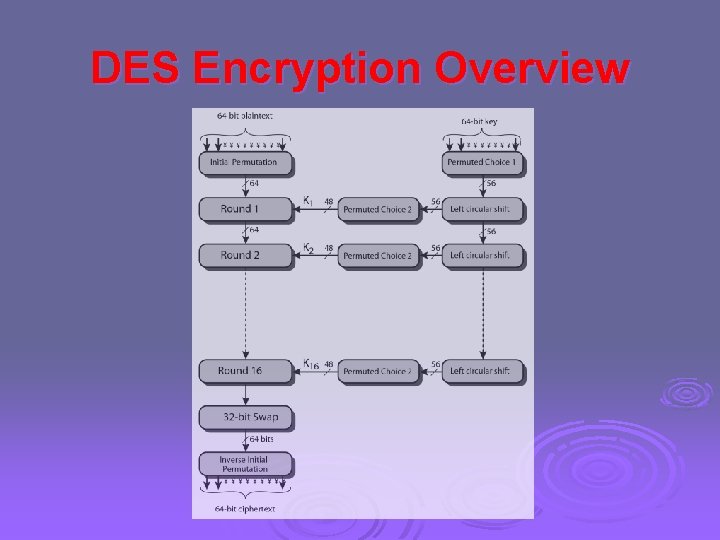
DES Encryption Overview
Initial Permutation IP Ø first step of the data computation Ø IP reorders the input data bits Ø even bits to LH half, odd bits to RH half Ø quite regular in structure (easy in h/w) Ø example: IP(675 a 6967 5 e 5 a 6 b 5 a) = (ffb 2194 d 004 df 6 fb)
DES Round Structure Ø uses two 32 -bit L & R halves Ø as for any Feistel cipher can describe as: Li = Ri– 1 Ri = Li– 1 F(Ri– 1, Ki) Ø F takes 32 -bit R half and 48 -bit subkey: l l expands R to 48 -bits using perm E adds to subkey using XOR passes through 8 S-boxes to get 32 -bit result finally permutes using 32 -bit perm P
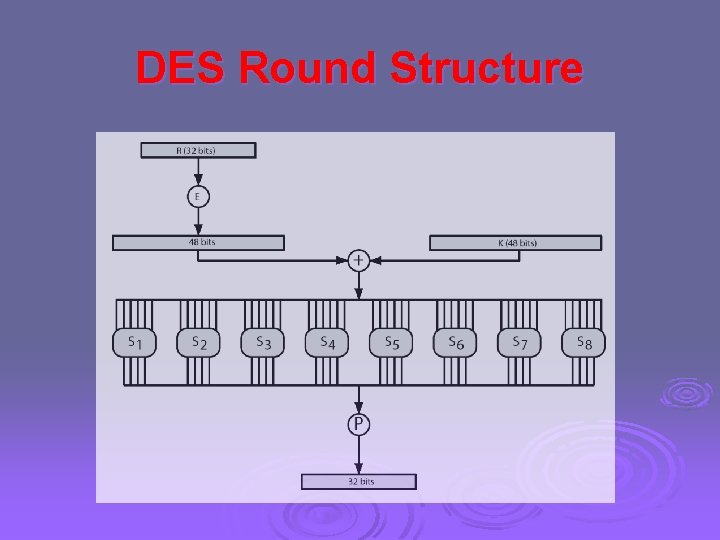
DES Round Structure
DES Decryption decrypt must unwind steps of data computation Ø with Feistel design, do encryption steps again using subkeys in reverse order (SK 16 … SK 1) Ø l l l IP undoes final FP step of encryption 1 st round with SK 16 undoes 16 th encrypt round …. 16 th round with SK 1 undoes 1 st encrypt round then final FP undoes initial encryption IP thus recovering original data value
- Slides: 12