Block Ciphers 1 Block Ciphers q Modern version
Block Ciphers 1
Block Ciphers q Modern version of a codebook cipher q In effect, a block cipher algorithm yields a huge number of codebooks o Specific codebook determined by key q It is OK to use same key for a while o Just like classic codebook o Initialization vector (IV) is like additive q Change Block Ciphers the key, get a new codebook 2
(Iterated) Block Cipher q Plaintext and ciphertext “units” are fixed sized blocks o Typical block sizes: 64 to 256 bits Ciphertext obtained from plaintext by iterating a round function q Input to round function consists of key and the output of previous round q Most are designed for software q Block Ciphers 3
Multiple Blocks How to encrypt multiple blocks? q A new key for each block? q o As bad as (or worse than) a one-time pad! Encrypt each block independently? q Make encryption depend on previous block(s), i. e. , “chain” the blocks together? q How to handle partial blocks? q Block Ciphers 4
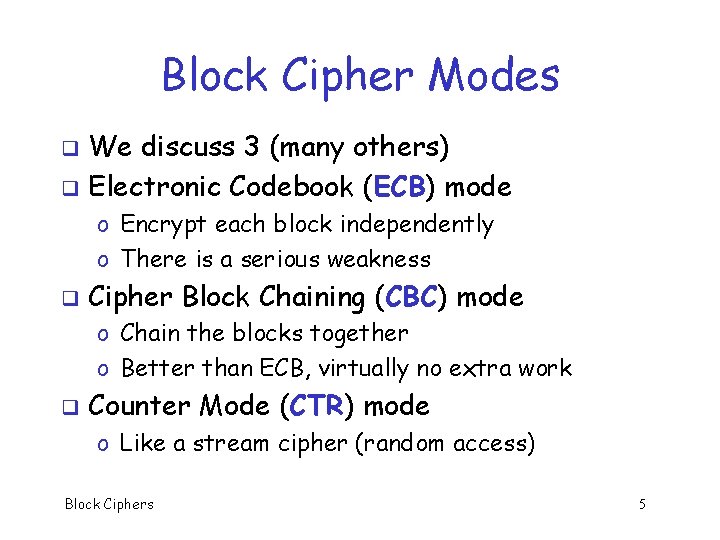
Block Cipher Modes We discuss 3 (many others) q Electronic Codebook (ECB) mode q o Encrypt each block independently o There is a serious weakness q Cipher Block Chaining (CBC) mode o Chain the blocks together o Better than ECB, virtually no extra work q Counter Mode (CTR) mode o Like a stream cipher (random access) Block Ciphers 5
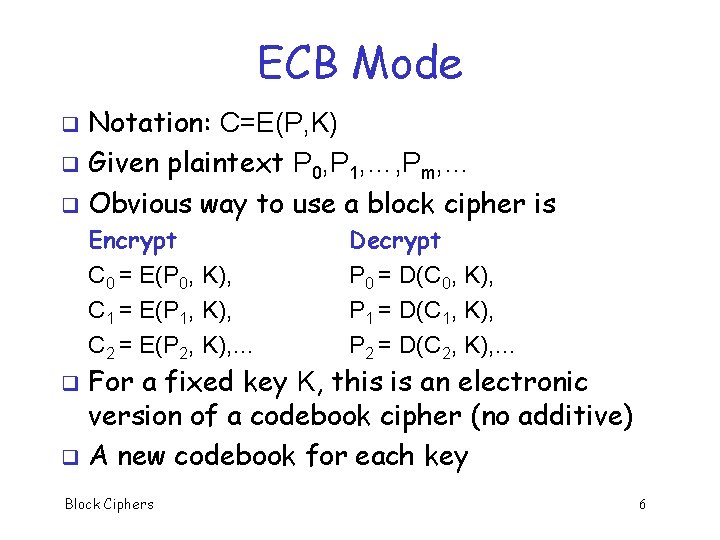
ECB Mode Notation: C=E(P, K) q Given plaintext P 0, P 1, …, Pm, … q Obvious way to use a block cipher is q Encrypt C 0 = E(P 0, K), C 1 = E(P 1, K), C 2 = E(P 2, K), … Decrypt P 0 = D(C 0, K), P 1 = D(C 1, K), P 2 = D(C 2, K), … For a fixed key K, this is an electronic version of a codebook cipher (no additive) q A new codebook for each key q Block Ciphers 6
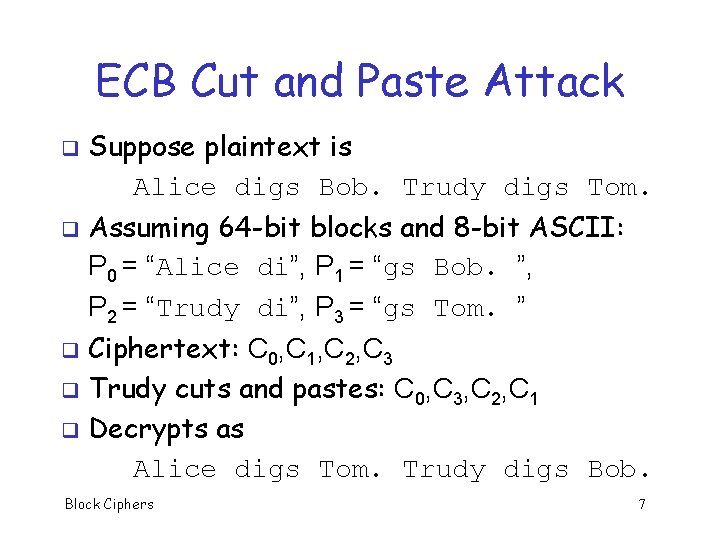
ECB Cut and Paste Attack q q Suppose plaintext is Alice digs Bob. Trudy digs Tom. Assuming 64 -bit blocks and 8 -bit ASCII: P 0 = “Alice di”, P 1 = “gs Bob. ”, P 2 = “Trudy di”, P 3 = “gs Tom. ” Ciphertext: C 0, C 1, C 2, C 3 q Trudy cuts and pastes: C 0, C 3, C 2, C 1 q Decrypts as Alice digs Tom. Trudy digs Bob. q Block Ciphers 7
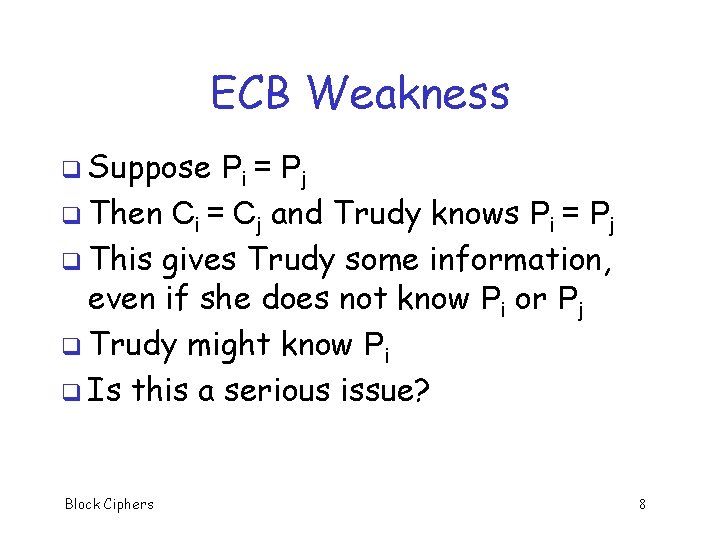
ECB Weakness q Suppose Pi = Pj q Then Ci = Cj and Trudy knows Pi = Pj q This gives Trudy some information, even if she does not know Pi or Pj q Trudy might know Pi q Is this a serious issue? Block Ciphers 8
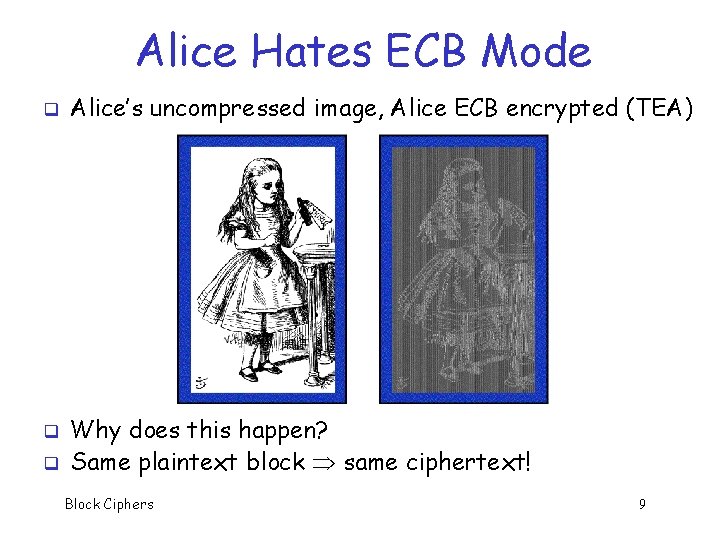
Alice Hates ECB Mode q q q Alice’s uncompressed image, Alice ECB encrypted (TEA) Why does this happen? Same plaintext block same ciphertext! Block Ciphers 9
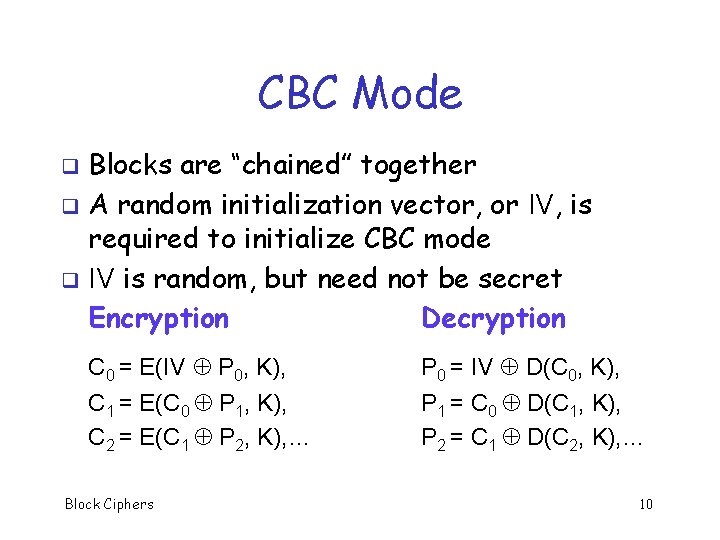
CBC Mode Blocks are “chained” together q A random initialization vector, or IV, is required to initialize CBC mode q IV is random, but need not be secret Encryption Decryption q C 0 = E(IV P 0, K), P 0 = IV D(C 0, K), C 1 = E(C 0 P 1, K), C 2 = E(C 1 P 2, K), … P 1 = C 0 D(C 1, K), P 2 = C 1 D(C 2, K), … Block Ciphers 10
CBC Mode Identical plaintext blocks yield different ciphertext blocks q Cut and paste is still possible, but more complex (and will cause garbles) q If C 1 is garbled to, say, G then P 1 C 0 D(G, K), P 2 G D(C 2, K) q But P 3 = C 2 D(C 3, K), P 4 = C 3 D(C 4, K), … q Automatically recovers from errors! q Block Ciphers 11
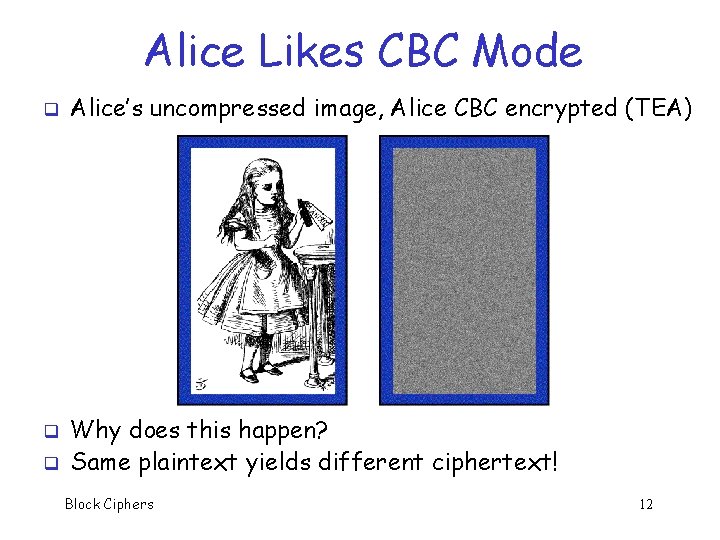
Alice Likes CBC Mode q q q Alice’s uncompressed image, Alice CBC encrypted (TEA) Why does this happen? Same plaintext yields different ciphertext! Block Ciphers 12
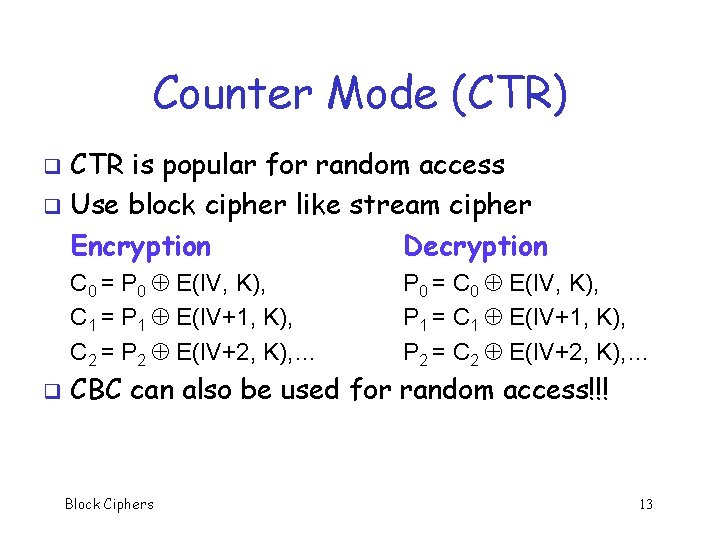
Counter Mode (CTR) CTR is popular for random access q Use block cipher like stream cipher Encryption Decryption q C 0 = P 0 E(IV, K), C 1 = P 1 E(IV+1, K), C 2 = P 2 E(IV+2, K), … q P 0 = C 0 E(IV, K), P 1 = C 1 E(IV+1, K), P 2 = C 2 E(IV+2, K), … CBC can also be used for random access!!! Block Ciphers 13
Integrity Block Ciphers 14
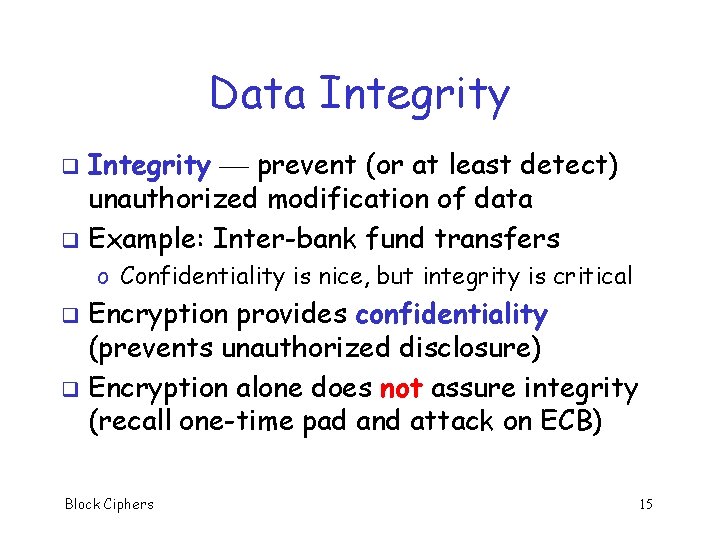
Data Integrity prevent (or at least detect) unauthorized modification of data q Example: Inter-bank fund transfers q o Confidentiality is nice, but integrity is critical Encryption provides confidentiality (prevents unauthorized disclosure) q Encryption alone does not assure integrity (recall one-time pad and attack on ECB) q Block Ciphers 15
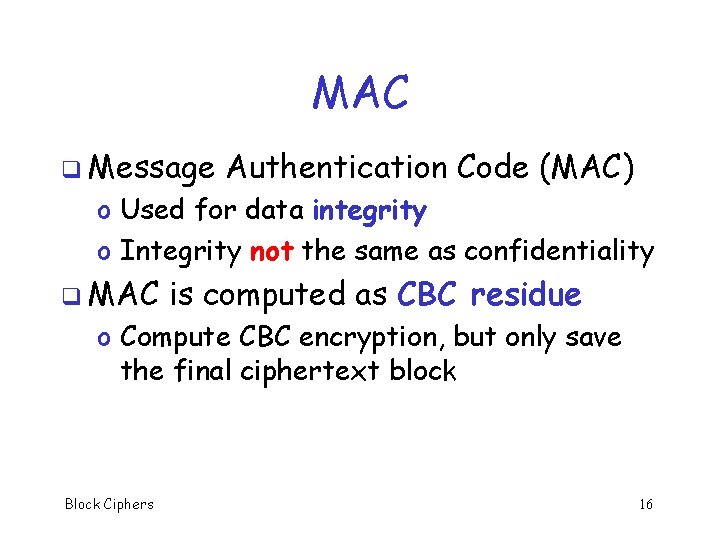
MAC q Message Authentication Code (MAC) o Used for data integrity o Integrity not the same as confidentiality q MAC is computed as CBC residue o Compute CBC encryption, but only save the final ciphertext block Block Ciphers 16
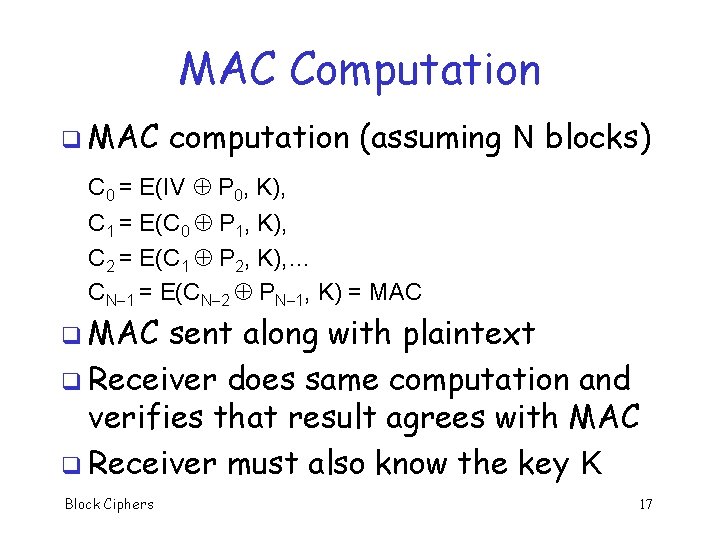
MAC Computation q MAC computation (assuming N blocks) C 0 = E(IV P 0, K), C 1 = E(C 0 P 1, K), C 2 = E(C 1 P 2, K), … CN 1 = E(CN 2 PN 1, K) = MAC q MAC sent along with plaintext q Receiver does same computation and verifies that result agrees with MAC q Receiver must also know the key K Block Ciphers 17
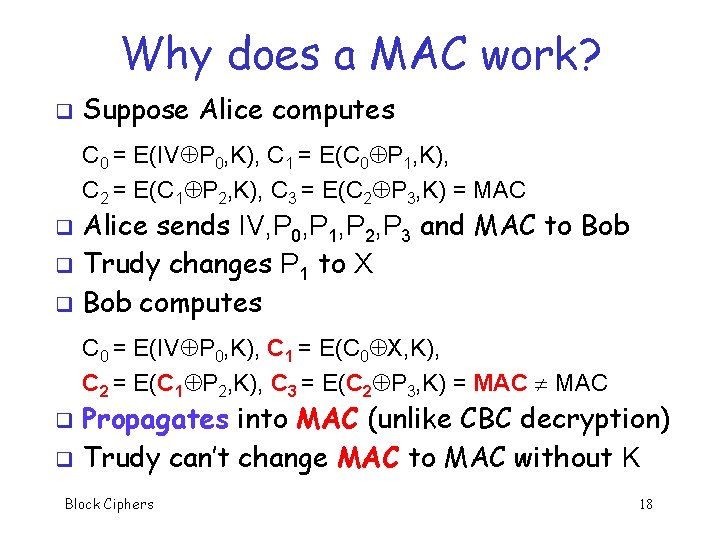
Why does a MAC work? q Suppose Alice computes C 0 = E(IV P 0, K), C 1 = E(C 0 P 1, K), C 2 = E(C 1 P 2, K), C 3 = E(C 2 P 3, K) = MAC Alice sends IV, P 0, P 1, P 2, P 3 and MAC to Bob q Trudy changes P 1 to X q Bob computes q C 0 = E(IV P 0, K), C 1 = E(C 0 X, K), C 2 = E(C 1 P 2, K), C 3 = E(C 2 P 3, K) = MAC Propagates into MAC (unlike CBC decryption) q Trudy can’t change MAC to MAC without K q Block Ciphers 18
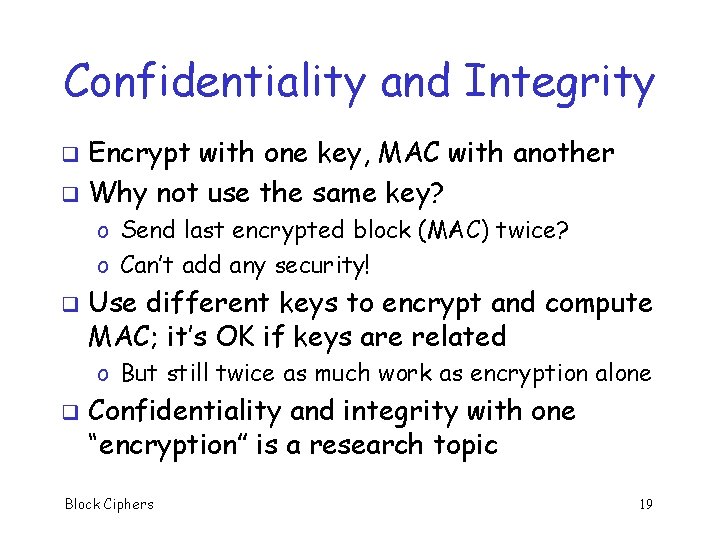
Confidentiality and Integrity Encrypt with one key, MAC with another q Why not use the same key? q o Send last encrypted block (MAC) twice? o Can’t add any security! q Use different keys to encrypt and compute MAC; it’s OK if keys are related o But still twice as much work as encryption alone q Confidentiality and integrity with one “encryption” is a research topic Block Ciphers 19
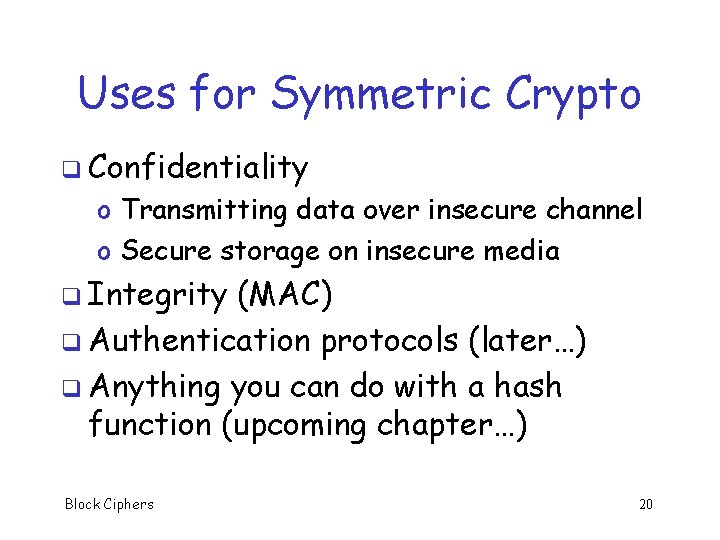
Uses for Symmetric Crypto q Confidentiality o Transmitting data over insecure channel o Secure storage on insecure media q Integrity (MAC) q Authentication protocols (later…) q Anything you can do with a hash function (upcoming chapter…) Block Ciphers 20
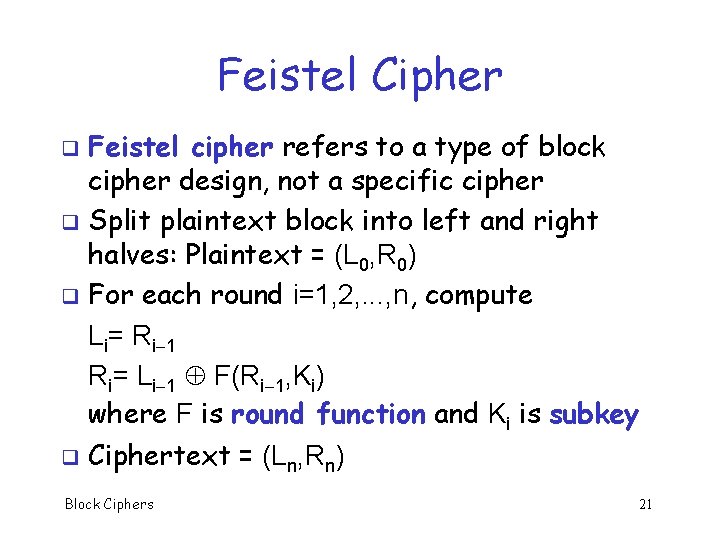
Feistel Cipher Feistel cipher refers to a type of block cipher design, not a specific cipher q Split plaintext block into left and right halves: Plaintext = (L 0, R 0) q For each round i=1, 2, . . . , n, compute Li= Ri 1 Ri= Li 1 F(Ri 1, Ki) where F is round function and Ki is subkey q q Ciphertext = (Ln, Rn) Block Ciphers 21
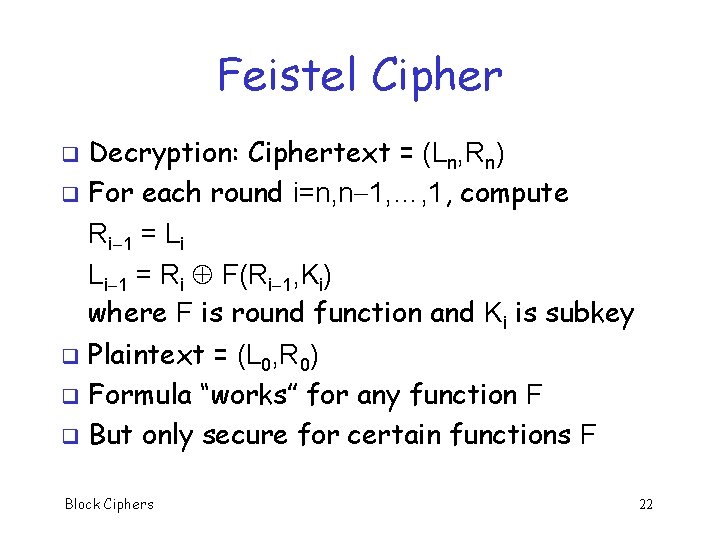
Feistel Cipher Decryption: Ciphertext = (Ln, Rn) q For each round i=n, n 1, …, 1, compute Ri 1 = Li Li 1 = Ri F(Ri 1, Ki) where F is round function and Ki is subkey q Plaintext = (L 0, R 0) q Formula “works” for any function F q But only secure for certain functions F q Block Ciphers 22
Conclusions q Block ciphers widely used today q Fast in software, very flexible, etc. q Not hard to design strong block cipher q Tricky to design fast and secure block cipher q Next: CMEA, Akelarre and FEAL Block Ciphers 23
- Slides: 23