Stream Ciphers u Block ciphers generate ciphertext CiphertextKey
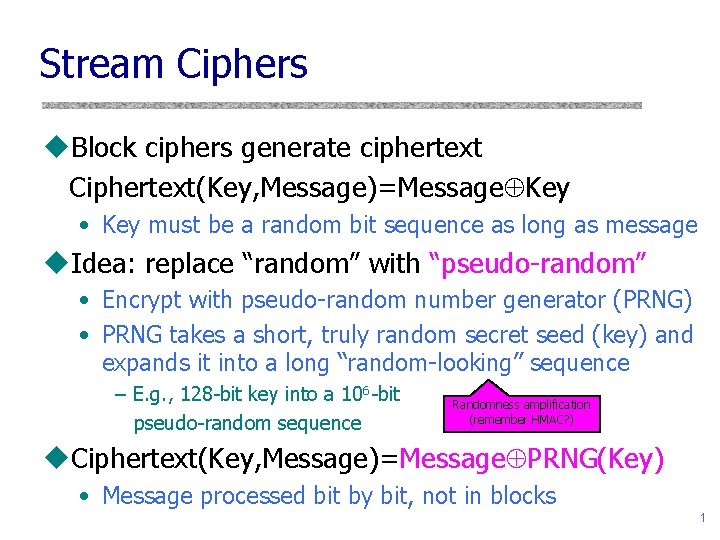
Stream Ciphers u. Block ciphers generate ciphertext Ciphertext(Key, Message)=Message Key • Key must be a random bit sequence as long as message u. Idea: replace “random” with “pseudo-random” • Encrypt with pseudo-random number generator (PRNG) • PRNG takes a short, truly random secret seed (key) and expands it into a long “random-looking” sequence – E. g. , 128 -bit key into a 106 -bit pseudo-random sequence Randomness amplification (remember HMAC? ) u. Ciphertext(Key, Message)=Message PRNG(Key) • Message processed bit by bit, not in blocks 1
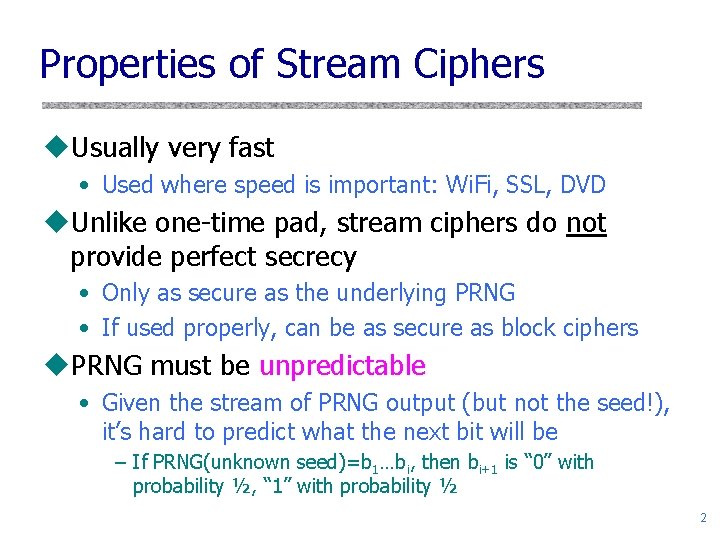
Properties of Stream Ciphers u. Usually very fast • Used where speed is important: Wi. Fi, SSL, DVD u. Unlike one-time pad, stream ciphers do not provide perfect secrecy • Only as secure as the underlying PRNG • If used properly, can be as secure as block ciphers u. PRNG must be unpredictable • Given the stream of PRNG output (but not the seed!), it’s hard to predict what the next bit will be – If PRNG(unknown seed)=b 1…bi, then bi+1 is “ 0” with probability ½, “ 1” with probability ½ 2
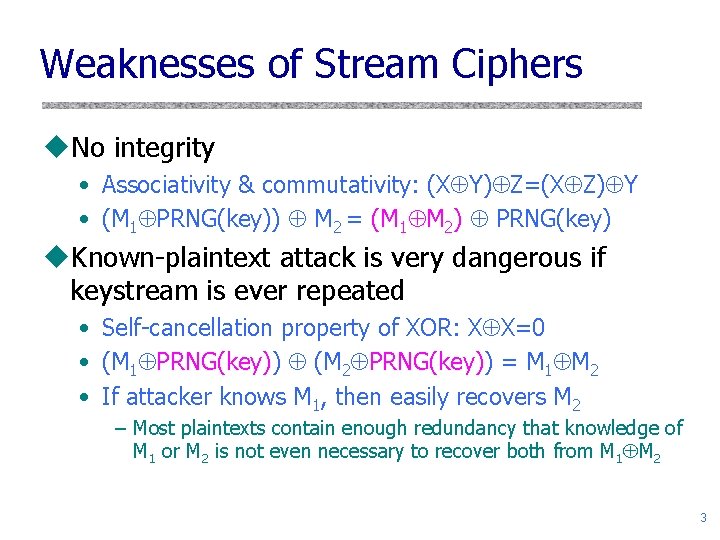
Weaknesses of Stream Ciphers u. No integrity • Associativity & commutativity: (X Y) Z=(X Z) Y • (M 1 PRNG(key)) M 2 = (M 1 M 2) PRNG(key) u. Known-plaintext attack is very dangerous if keystream is ever repeated • Self-cancellation property of XOR: X X=0 • (M 1 PRNG(key)) (M 2 PRNG(key)) = M 1 M 2 • If attacker knows M 1, then easily recovers M 2 – Most plaintexts contain enough redundancy that knowledge of M 1 or M 2 is not even necessary to recover both from M 1 M 2 3
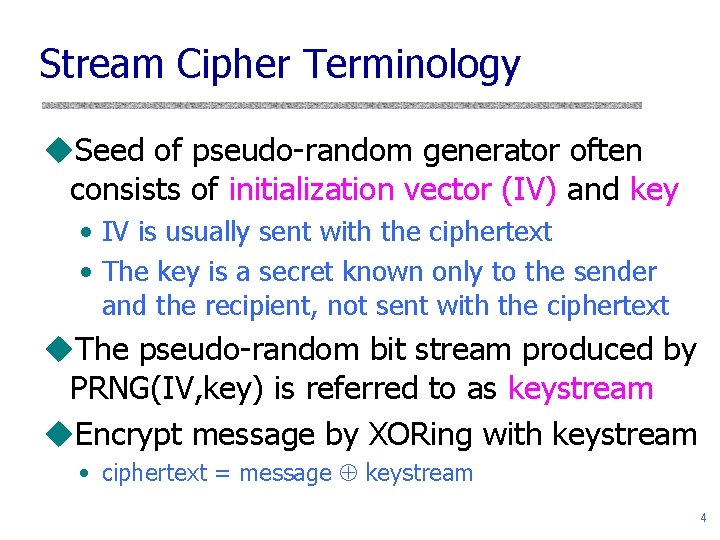
Stream Cipher Terminology u. Seed of pseudo-random generator often consists of initialization vector (IV) and key • IV is usually sent with the ciphertext • The key is a secret known only to the sender and the recipient, not sent with the ciphertext u. The pseudo-random bit stream produced by PRNG(IV, key) is referred to as keystream u. Encrypt message by XORing with keystream • ciphertext = message keystream 4
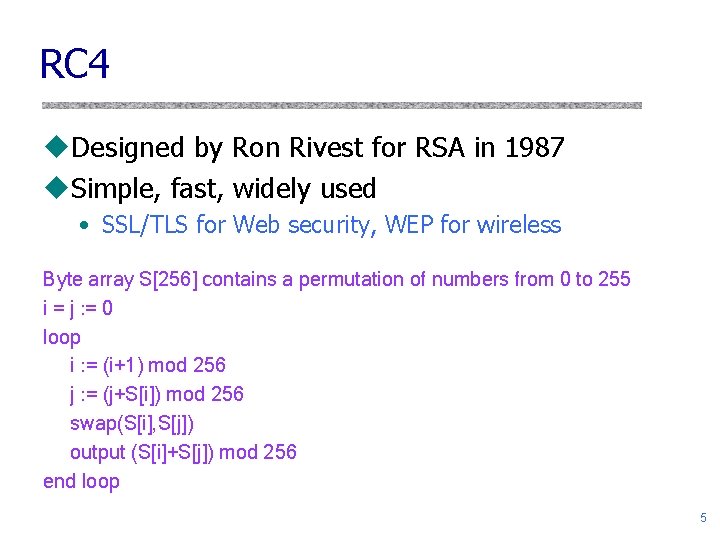
RC 4 u. Designed by Ron Rivest for RSA in 1987 u. Simple, fast, widely used • SSL/TLS for Web security, WEP for wireless Byte array S[256] contains a permutation of numbers from 0 to 255 i = j : = 0 loop i : = (i+1) mod 256 j : = (j+S[i]) mod 256 swap(S[i], S[j]) output (S[i]+S[j]) mod 256 end loop 5
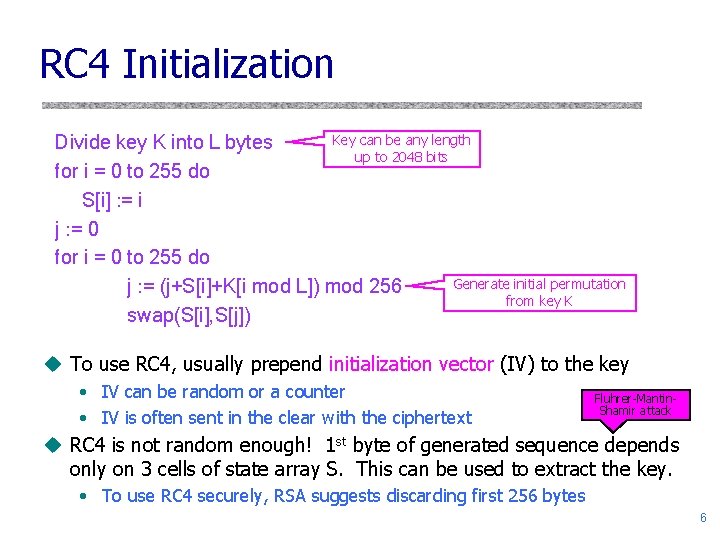
RC 4 Initialization Key can be any length Divide key K into L bytes up to 2048 bits for i = 0 to 255 do S[i] : = i j : = 0 for i = 0 to 255 do Generate initial permutation j : = (j+S[i]+K[i mod L]) mod 256 from key K swap(S[i], S[j]) u To use RC 4, usually prepend initialization vector (IV) to the key • IV can be random or a counter • IV is often sent in the clear with the ciphertext Fluhrer-Mantin. Shamir attack u RC 4 is not random enough! 1 st byte of generated sequence depends only on 3 cells of state array S. This can be used to extract the key. • To use RC 4 securely, RSA suggests discarding first 256 bytes 6
Modes of Operation ublock ciphers encrypt fixed size blocks ueg. DES encrypts 64 -bit blocks, with 56 -bit key uneed way to use in practise, given usually have arbitrary amount of information to encrypt ufour were defined for DES in ANSI standard ANSI X 3. 106 -1983 Modes of Use usubsequently now have 5 for DES and AES uhave block and stream modes 7
Electronic Codebook Book (ECB) umessage is broken into independent blocks which are encrypted ueach block is a value which is substituted, like a codebook, hence name ueach block is encoded independently of the other blocks Ci = DESK 1 (Pi) uuses: secure transmission of single values 8
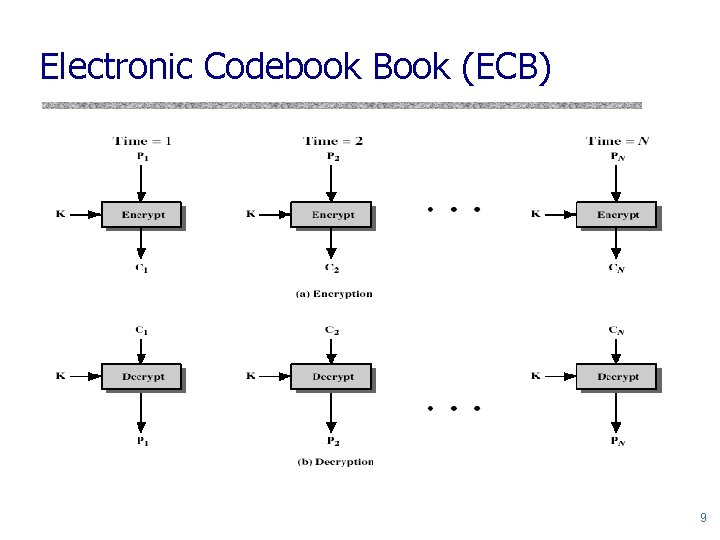
Electronic Codebook Book (ECB) 9
Advantages and Limitations of ECB urepetitions in message may show in ciphertext • if aligned with message block • particularly with data such graphics • or with messages that change very little, which become a code-book analysis problem uweakness due to encrypted message blocks being independent umain use is sending a few blocks of data 10
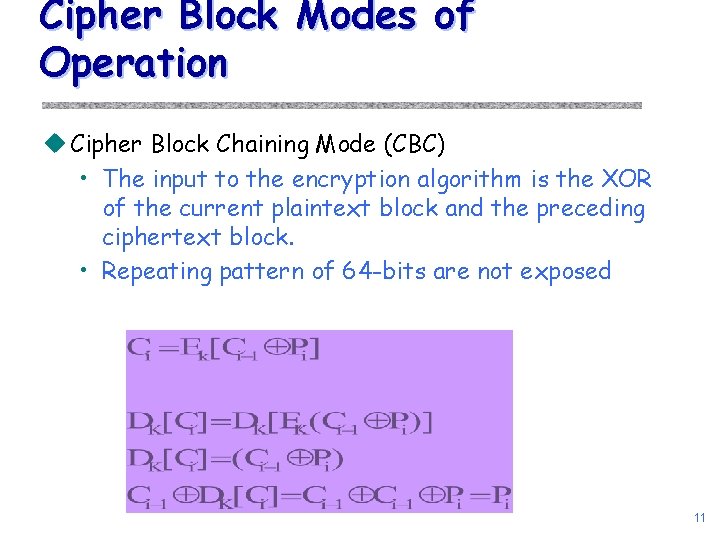
Cipher Block Modes of Operation u Cipher Block Chaining Mode (CBC) • The input to the encryption algorithm is the XOR of the current plaintext block and the preceding ciphertext block. • Repeating pattern of 64 -bits are not exposed 11
Cipher Feed. Back (CFB) umessage is treated as a stream of bits uadded to the output of the block cipher uresult is feed back for next stage (hence name) ustandard allows any number of bit (1, 8 or 64 or whatever) to be feed back • denoted CFB-1, CFB-8, CFB-64 etc uis most efficient to use all 64 bits (CFB-64) Ci = Pi XOR DESK 1(Ci-1) C-1 = IV uuses: stream data encryption, authentication 12
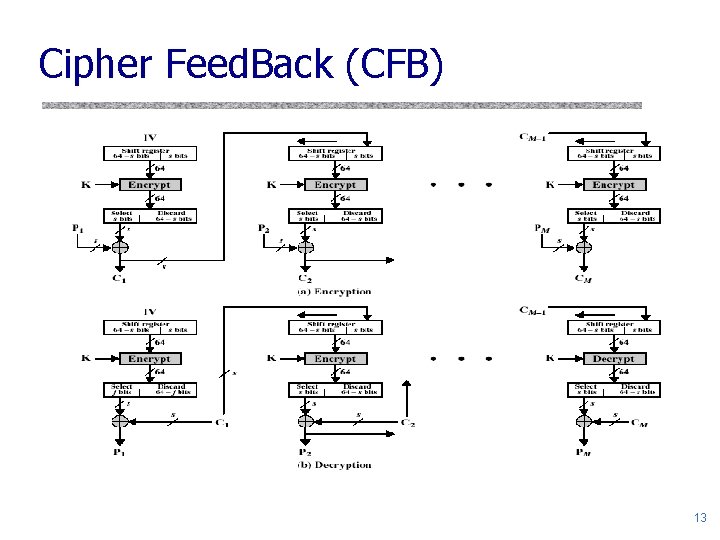
Cipher Feed. Back (CFB) 13
Advantages and Limitations of CFB uappropriate when data arrives in bits/bytes umost common stream mode ulimitation is need to stall while do block encryption after every n-bits unote that the block cipher is used in encryption mode at both ends uerrors propagate for several blocks after the error 14
Location of Encryption Device u. Link encryption: • A lot of encryption devices • High level of security • Decrypts each packet at every switch u. End-to-end encryption • The source encrypts and the receiver decrypts • Payload encrypted • Header in the clear u. High Security: Both link and end-to-end encryption are needed (see Figure 2. 9) 15
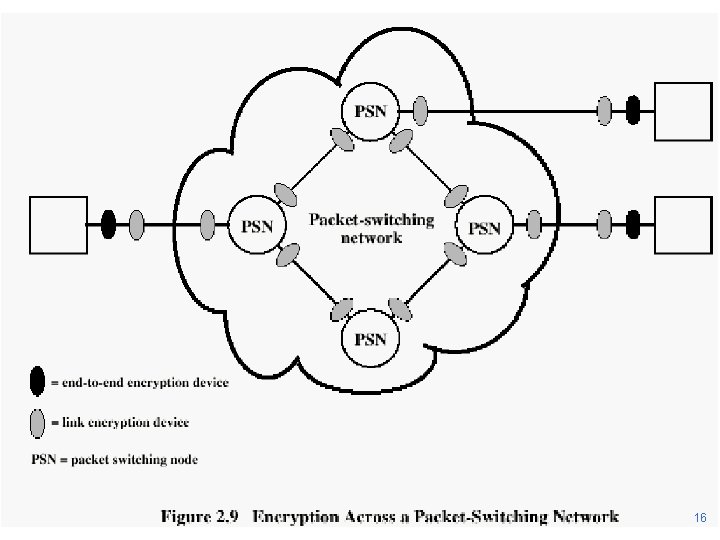
16
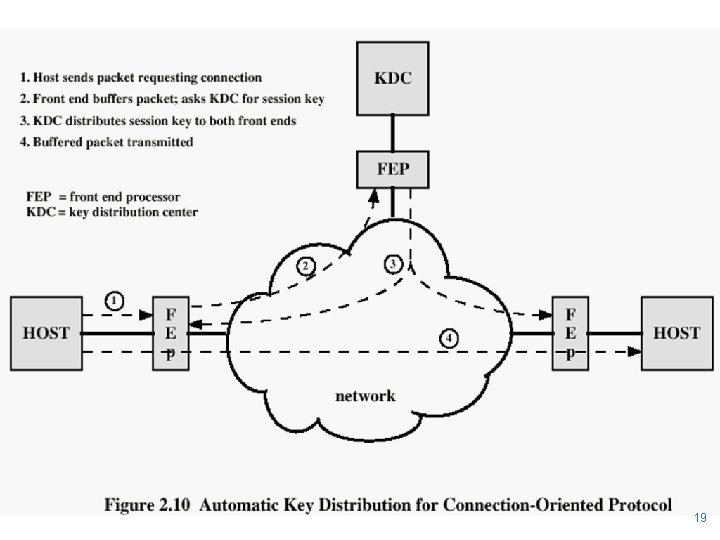
Key Distribution 1. 2. 3. 4. A key could be selected by A and physically delivered to B. A third party could select the key and physically deliver it to A and B. If A and B have previously used a key, one party could transmit the new key to the other, encrypted using the old key. If A and B each have an encrypted connection to a third party C, C could deliver a key on the encrypted links to A and B. 17
Key Distribution (See Figure 2. 10) u. Session key: • Data encrypted with a one-time session key. At the conclusion of the session the key is destroyed u. Permanent key: • Used between entities for the purpose of distributing session keys 18
19
- Slides: 19