IEEE 802 Protocols 100 base VG 100 VG
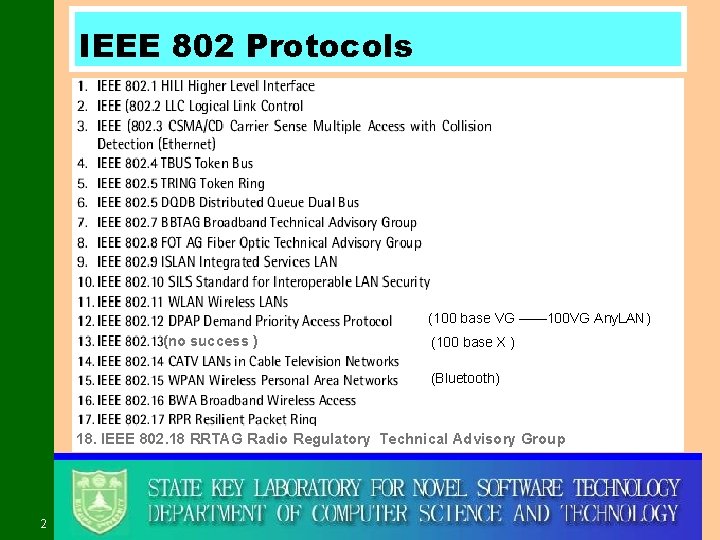
IEEE 802 Protocols (100 base VG —— 100 VG Any. LAN) (no success ) (100 base X ) (Bluetooth) 18. IEEE 802. 18 RRTAG Radio Regulatory Technical Advisory Group 2
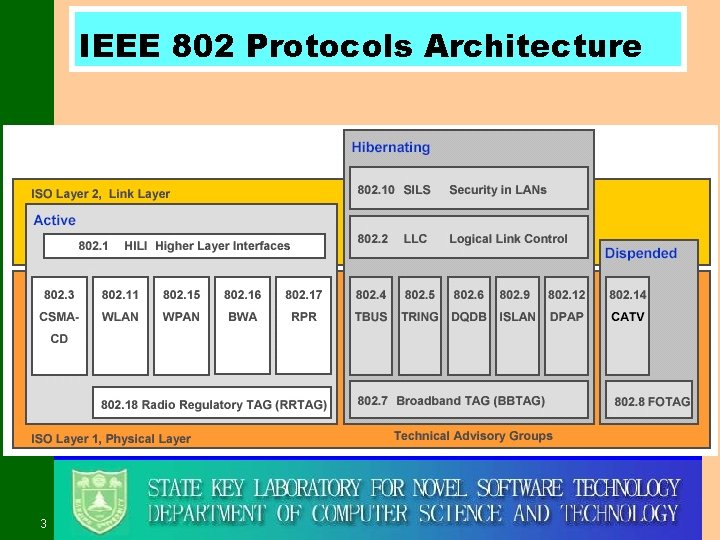
IEEE 802 Protocols Architecture 3
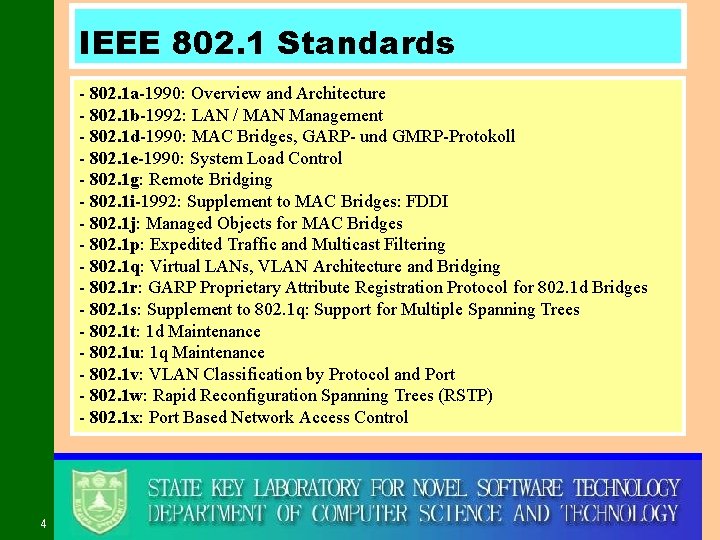
IEEE 802. 1 Standards - 802. 1 a-1990: Overview and Architecture - 802. 1 b-1992: LAN / MAN Management - 802. 1 d-1990: MAC Bridges, GARP- und GMRP-Protokoll - 802. 1 e-1990: System Load Control - 802. 1 g: Remote Bridging - 802. 1 i-1992: Supplement to MAC Bridges: FDDI - 802. 1 j: Managed Objects for MAC Bridges - 802. 1 p: Expedited Traffic and Multicast Filtering - 802. 1 q: Virtual LANs, VLAN Architecture and Bridging - 802. 1 r: GARP Proprietary Attribute Registration Protocol for 802. 1 d Bridges - 802. 1 s: Supplement to 802. 1 q: Support for Multiple Spanning Trees - 802. 1 t: 1 d Maintenance - 802. 1 u: 1 q Maintenance - 802. 1 v: VLAN Classification by Protocol and Port - 802. 1 w: Rapid Reconfiguration Spanning Trees (RSTP) - 802. 1 x: Port Based Network Access Control 4
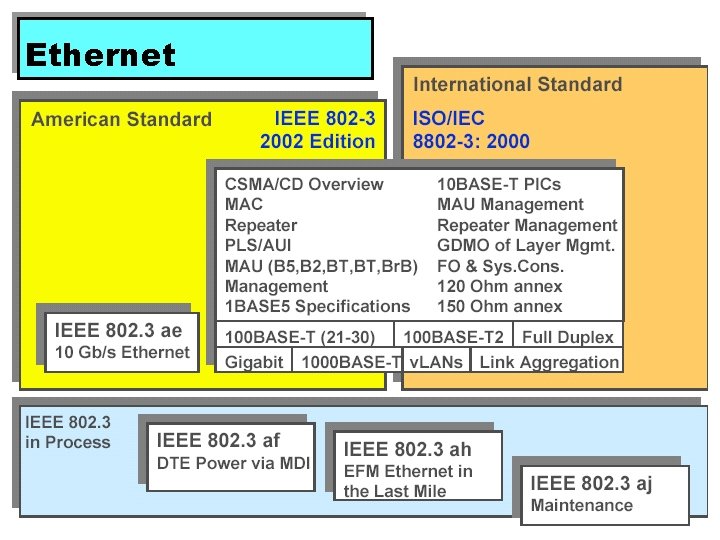
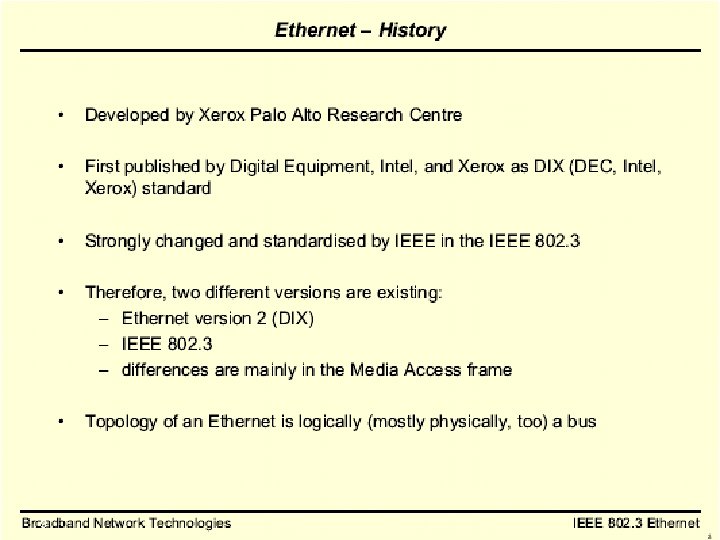
Ethernet 5
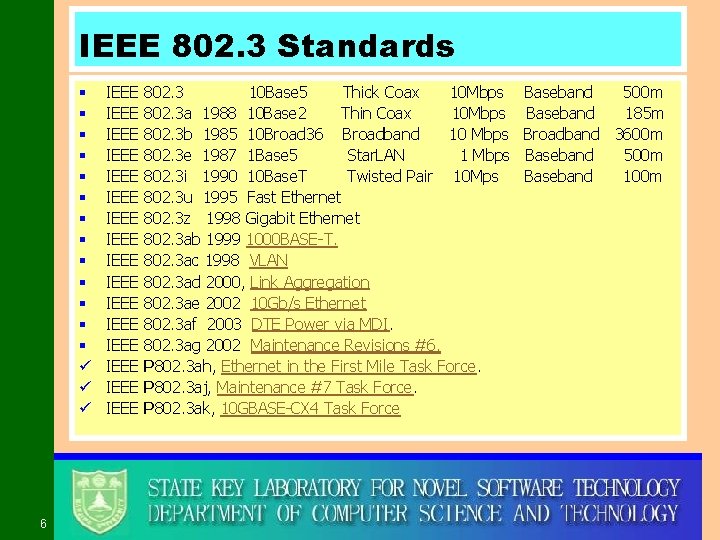
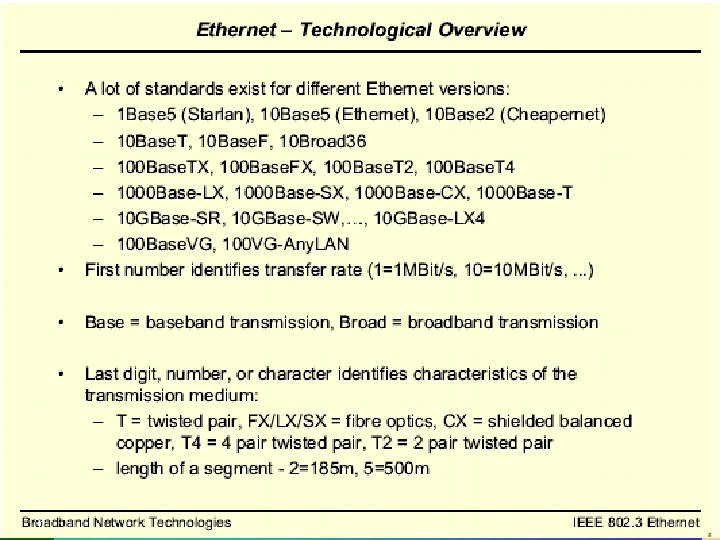
IEEE 802. 3 Standards § § § § ü ü ü 6 IEEE IEEE IEEE IEEE 802. 3 10 Base 5 Thick Coax 10 Mbps 802. 3 a 1988 10 Base 2 Thin Coax 10 Mbps 802. 3 b 1985 10 Broad 36 Broadband 10 Mbps 802. 3 e 1987 1 Base 5 Star. LAN 1 Mbps 802. 3 i 1990 10 Base. T Twisted Pair 10 Mps 802. 3 u 1995 Fast Ethernet 802. 3 z 1998 Gigabit Ethernet 802. 3 ab 1999 1000 BASE-T. 802. 3 ac 1998 VLAN 802. 3 ad 2000, Link Aggregation 802. 3 ae 2002 10 Gb/s Ethernet 802. 3 af 2003 DTE Power via MDI. 802. 3 ag 2002 Maintenance Revisions #6. P 802. 3 ah, Ethernet in the First Mile Task Force. P 802. 3 aj, Maintenance #7 Task Force. P 802. 3 ak, 10 GBASE-CX 4 Task Force Baseband 500 m Baseband 185 m Broadband 3600 m Baseband 500 m Baseband 100 m
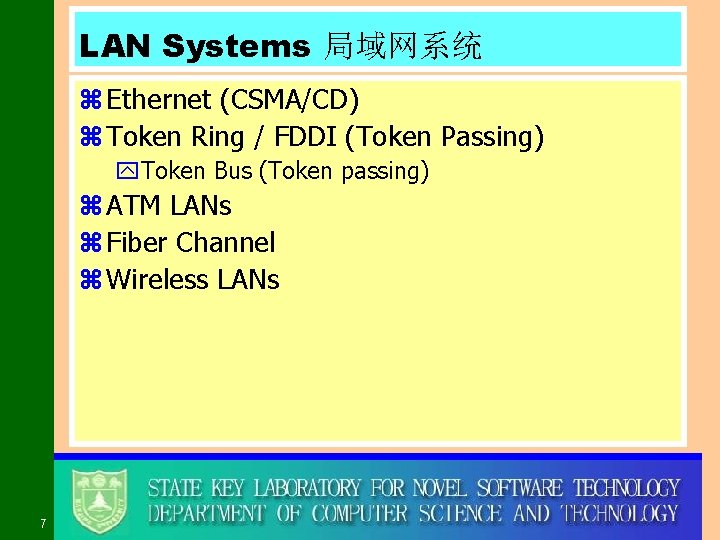
LAN Systems 局域网系统 z Ethernet (CSMA/CD) z Token Ring / FDDI (Token Passing) y. Token Bus (Token passing) z ATM LANs z Fiber Channel z Wireless LANs 7
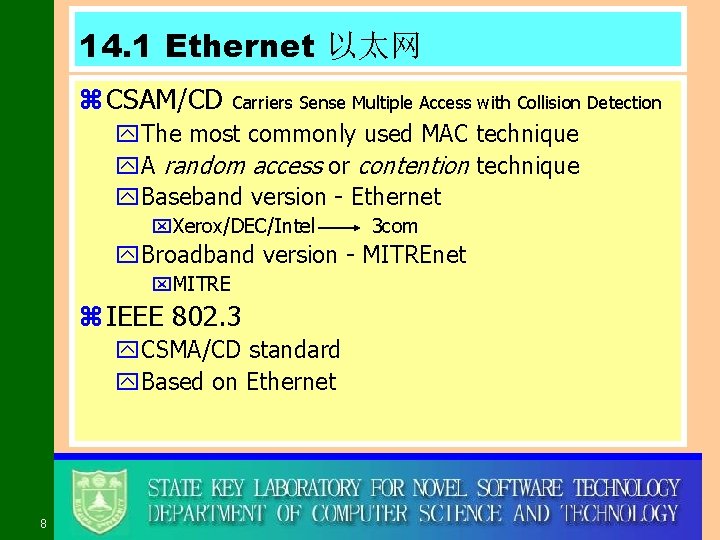
14. 1 Ethernet 以太网 z CSAM/CD Carriers Sense Multiple Access with Collision Detection y. The most commonly used MAC technique y. A random access or contention technique y. Baseband version - Ethernet x. Xerox/DEC/Intel 3 com y. Broadband version - MITREnet x. MITRE z IEEE 802. 3 y. CSMA/CD standard y. Based on Ethernet 8
9
10
11
12
13
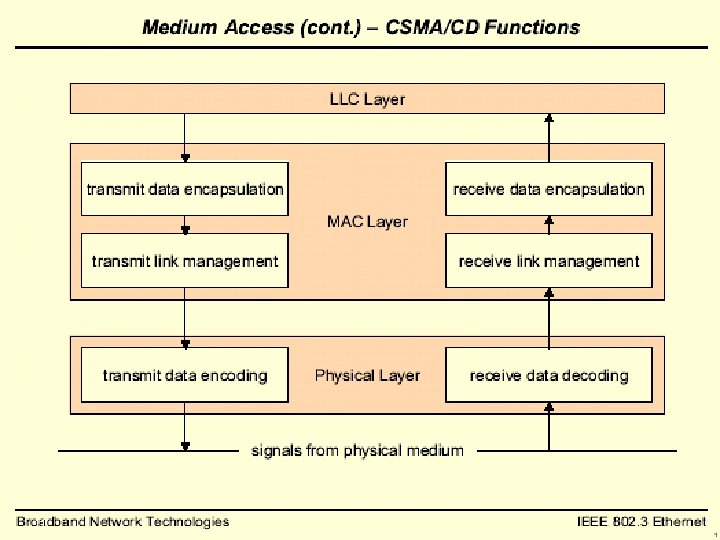
14. 1. 1 MAC protocol—CSMA/CD z IEEE 802. 3 z Random Access y Stations access medium randomly z Contention y. Stations content for time on medium z Precursors y. ALOHA Additive Link On-line HAwaii system xdeveloped for packet radio networks xby Hawaii University y. Slotted ALOHA y. CSMA 14
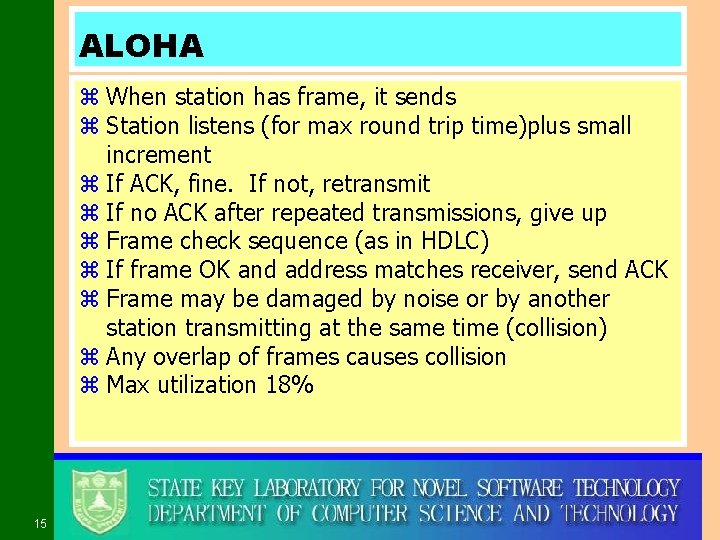
ALOHA z When station has frame, it sends z Station listens (for max round trip time)plus small increment z If ACK, fine. If not, retransmit z If no ACK after repeated transmissions, give up z Frame check sequence (as in HDLC) z If frame OK and address matches receiver, send ACK z Frame may be damaged by noise or by another station transmitting at the same time (collision) z Any overlap of frames causes collision z Max utilization 18% 15
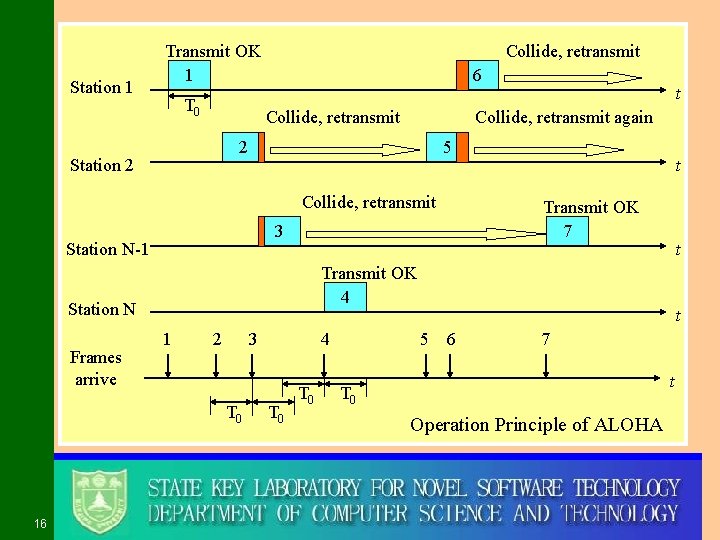
Station 1 Transmit OK 1 T 0 Collide, retransmit 6 Collide, retransmit again 2 Station 2 5 Collide, retransmit t Transmit OK 4 Station N 1 2 3 T 0 16 t Transmit OK 7 3 Station N-1 Frames arrive t 4 T 0 t 5 6 7 t T 0 Operation Principle of ALOHA
Slotted ALOHA z Time in uniform slots equal to frame transmission time z Need central clock (or other sync mechanism) z Transmission begins at slot boundary z Frames either miss or overlap totally z Max utilization 37% 17
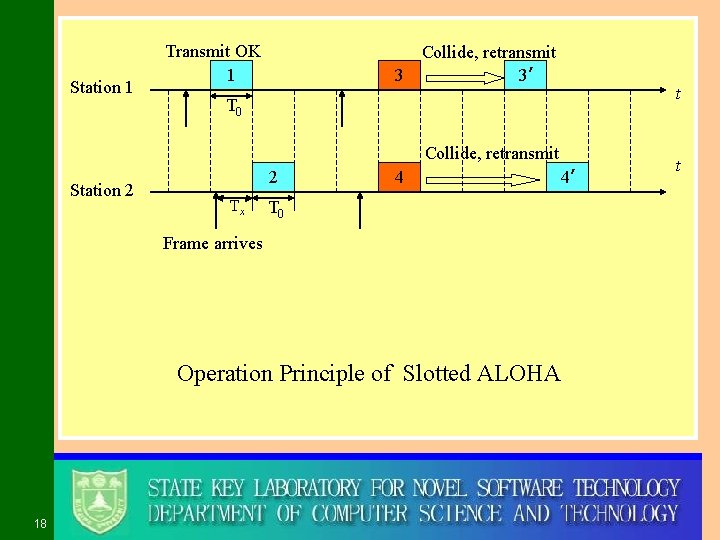
Station 1 Transmit OK 1 3 Collide, retransmit 3’ t T 0 Collide, retransmit Station 2 2 Tx 4 4’ T 0 Frame arrives Operation Principle of Slotted ALOHA 18 t
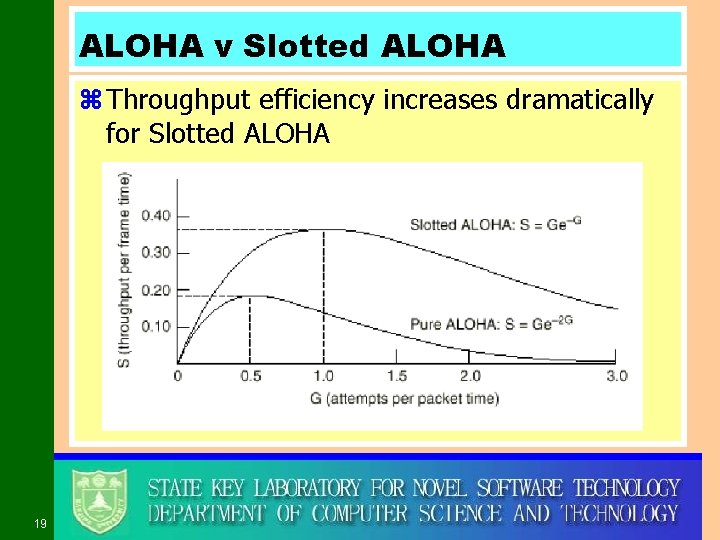
ALOHA v Slotted ALOHA z Throughput efficiency increases dramatically for Slotted ALOHA 19
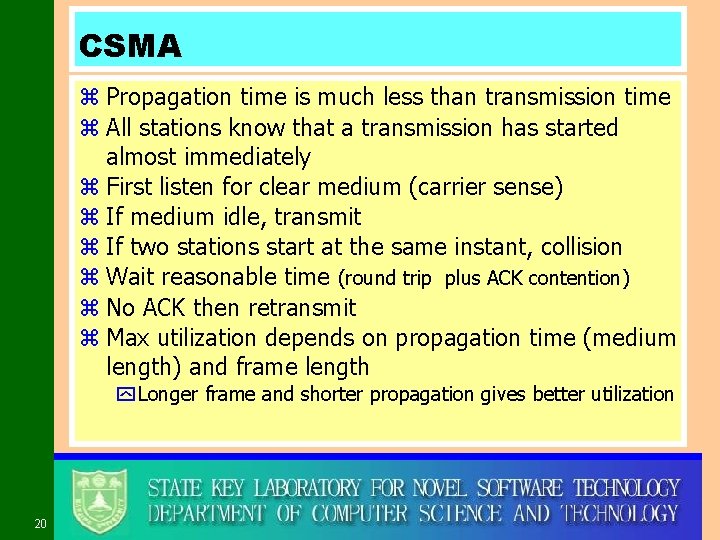
CSMA z Propagation time is much less than transmission time z All stations know that a transmission has started almost immediately z First listen for clear medium (carrier sense) z If medium idle, transmit z If two stations start at the same instant, collision z Wait reasonable time (round trip plus ACK contention) z No ACK then retransmit z Max utilization depends on propagation time (medium length) and frame length y Longer frame and shorter propagation gives better utilization 20
Strategies of Carriers Sense z ALOHA z Non-persistent CSMA z p-persistent CSMA z 1 -persistent CSMA 21
If Busy? (1 -persistent CSMA) z If medium is idle, transmit z If busy, listen for idle then transmit immediately z If two stations are waiting, collision 22
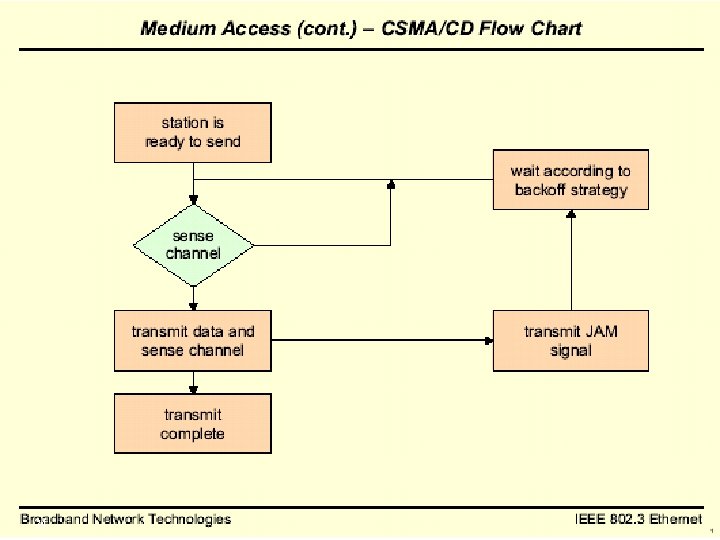
CSMA/CD z With CSMA, collision occupies medium for duration of transmission z Stations listen whilst transmitting z If medium idle, transmit z If busy, listen for idle, then transmit z If collision detected, jam then cease transmission z After jam, wait random time then start again y. Binary exponential back off 23
24
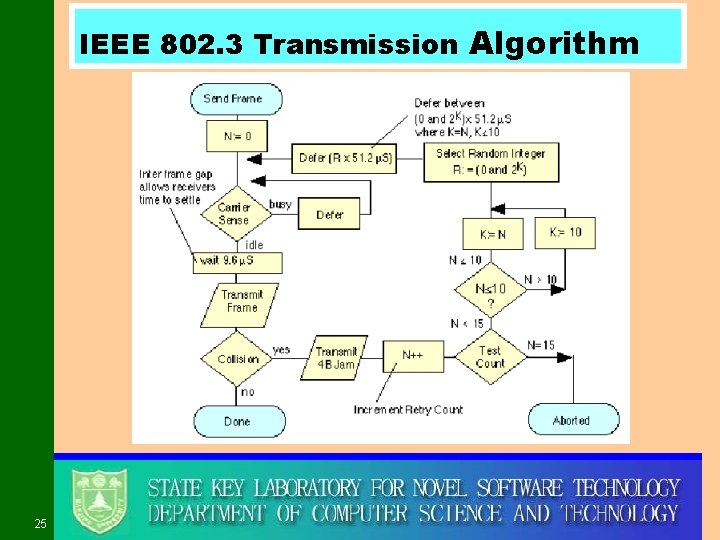
IEEE 802. 3 Transmission Algorithm 25
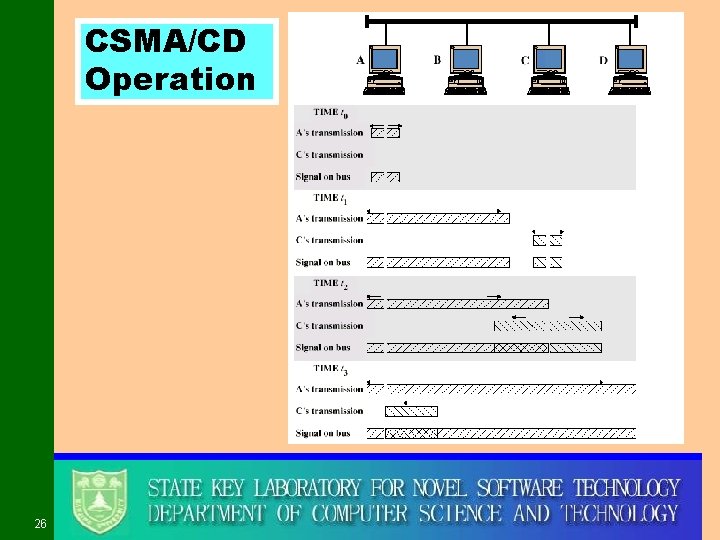
CSMA/CD Operation 26
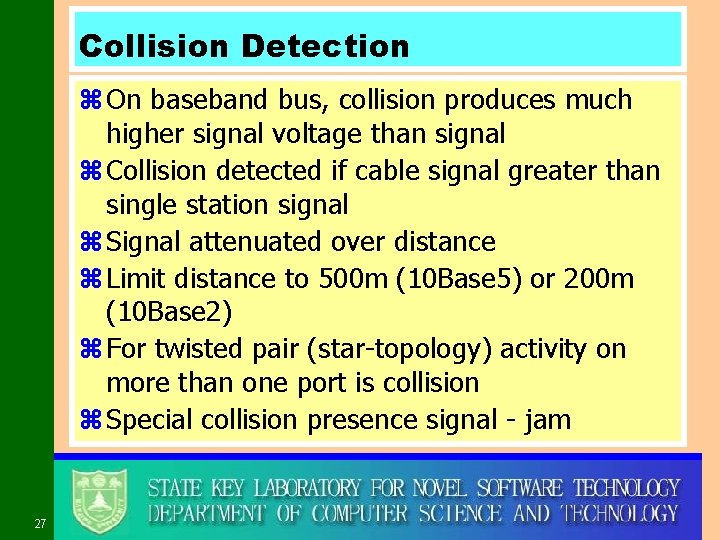
Collision Detection z On baseband bus, collision produces much higher signal voltage than signal z Collision detected if cable signal greater than single station signal z Signal attenuated over distance z Limit distance to 500 m (10 Base 5) or 200 m (10 Base 2) z For twisted pair (star-topology) activity on more than one port is collision z Special collision presence signal - jam 27
28
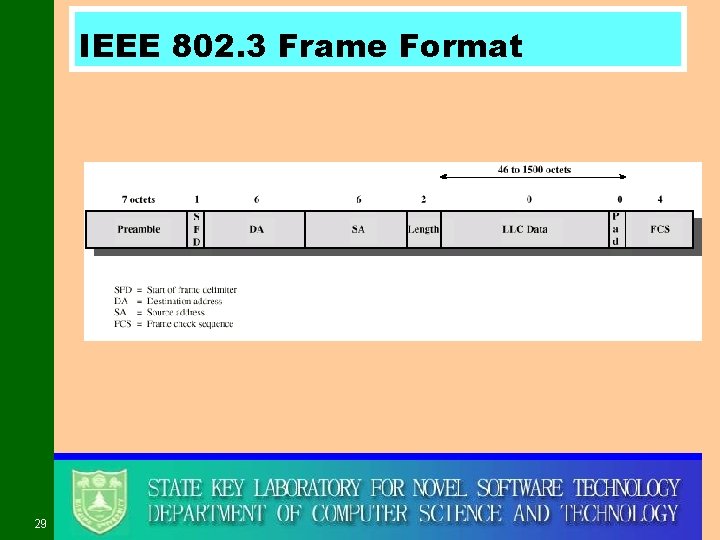
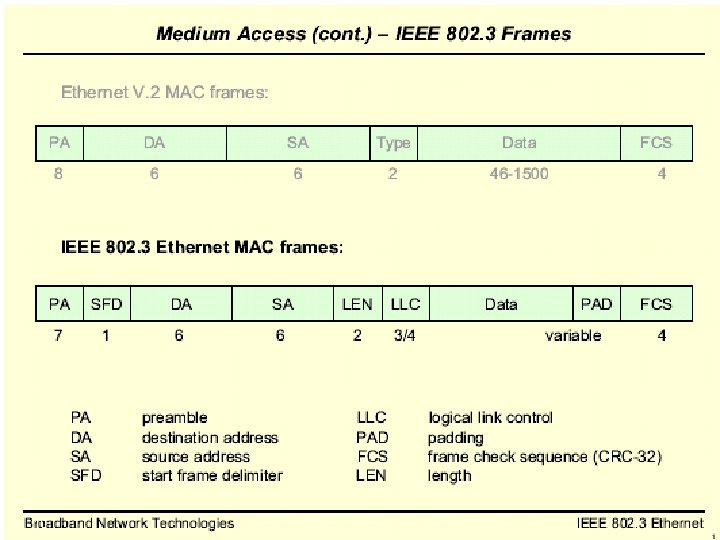
IEEE 802. 3 Frame Format 29
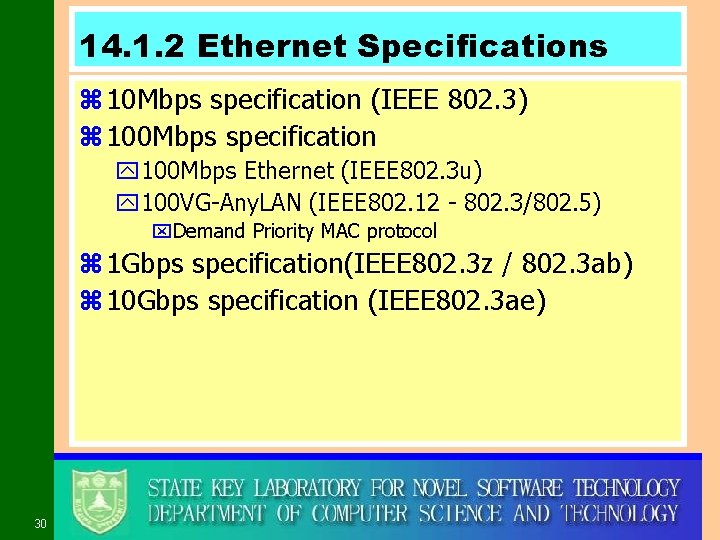
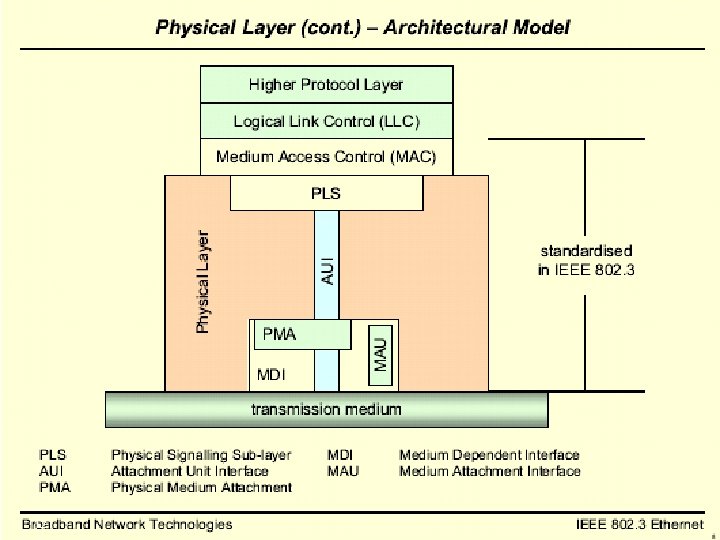
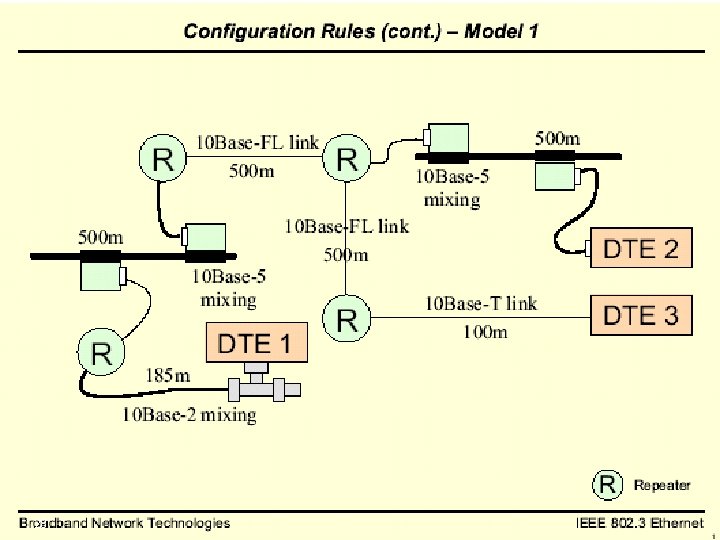
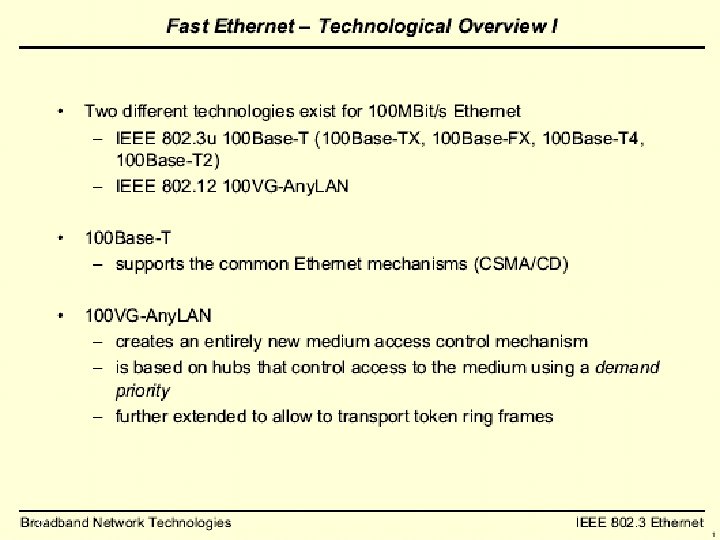
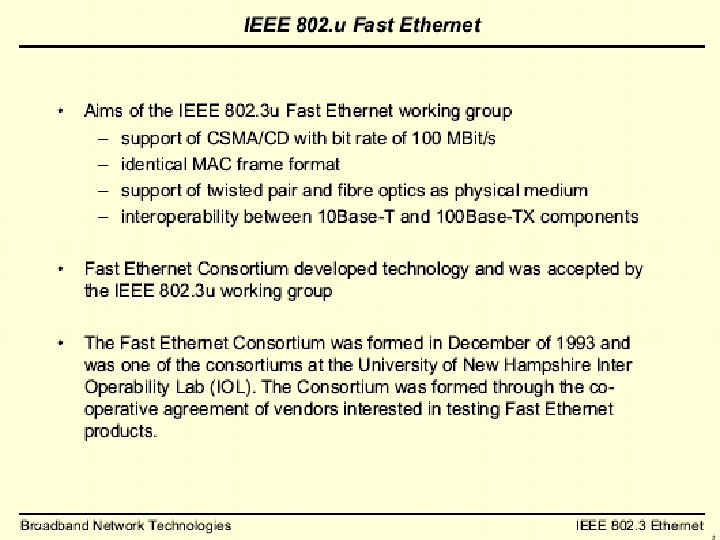
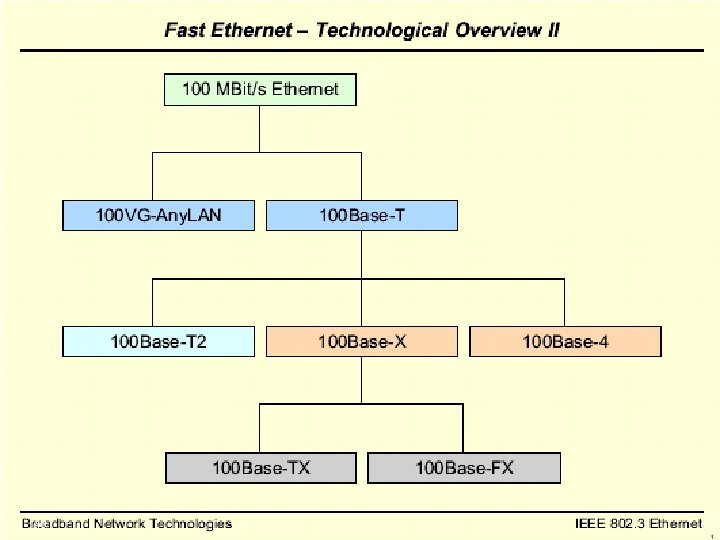
14. 1. 2 Ethernet Specifications z 10 Mbps specification (IEEE 802. 3) z 100 Mbps specification y 100 Mbps Ethernet (IEEE 802. 3 u) y 100 VG-Any. LAN (IEEE 802. 12 - 802. 3/802. 5) x. Demand Priority MAC protocol z 1 Gbps specification(IEEE 802. 3 z / 802. 3 ab) z 10 Gbps specification (IEEE 802. 3 ae) 30
31
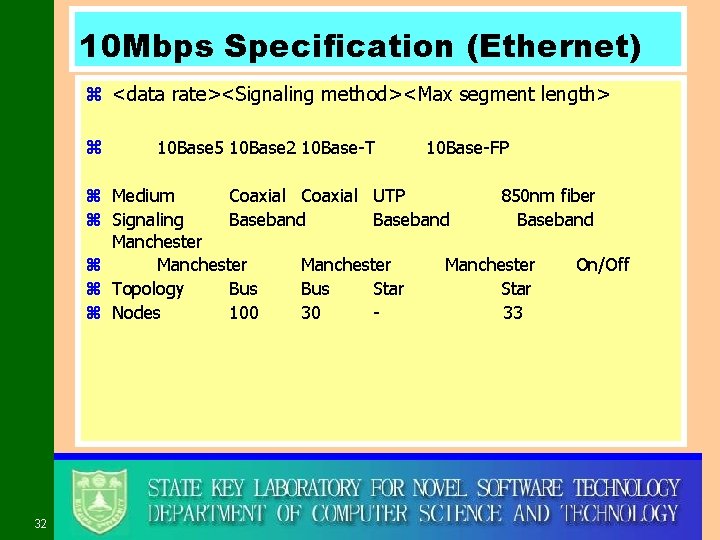
10 Mbps Specification (Ethernet) z <data rate><Signaling method><Max segment length> z 10 Base 5 10 Base 2 10 Base-T 10 Base-FP z Medium Coaxial UTP 850 nm fiber z Signaling Baseband Manchester z Manchester On/Off z Topology Bus Star z Nodes 100 30 33 32
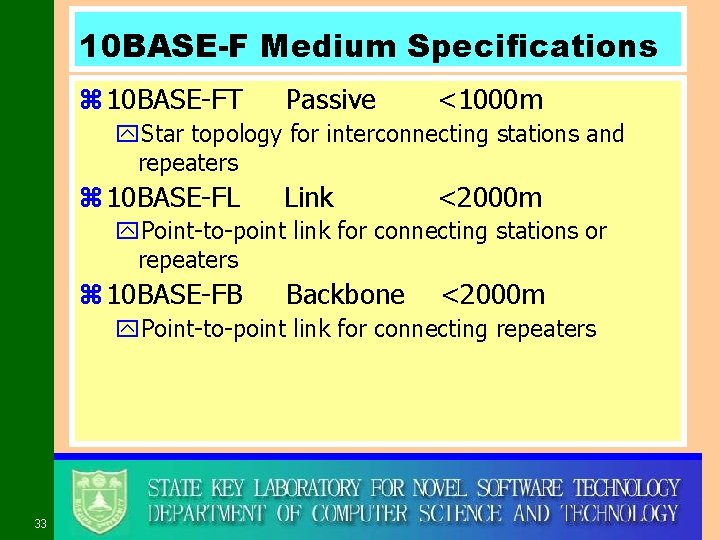
10 BASE-F Medium Specifications z 10 BASE-FT Passive <1000 m y. Star topology for interconnecting stations and repeaters z 10 BASE-FL Link <2000 m y. Point-to-point link for connecting stations or repeaters z 10 BASE-FB Backbone <2000 m y. Point-to-point link for connecting repeaters 33
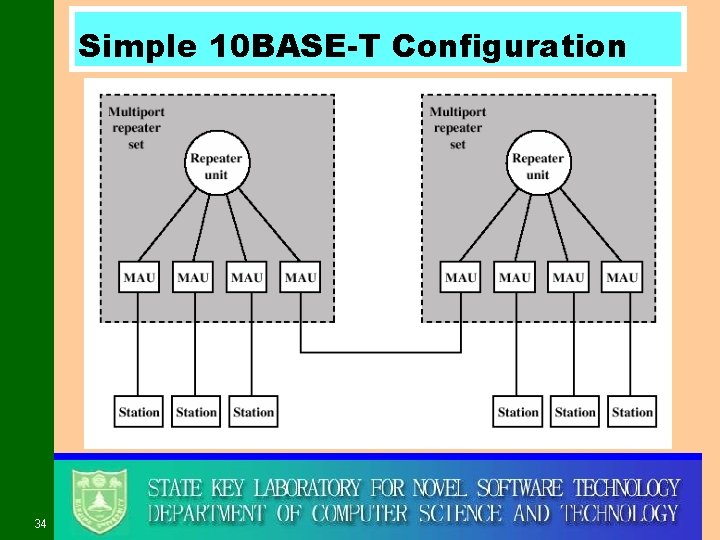
Simple 10 BASE-T Configuration 34
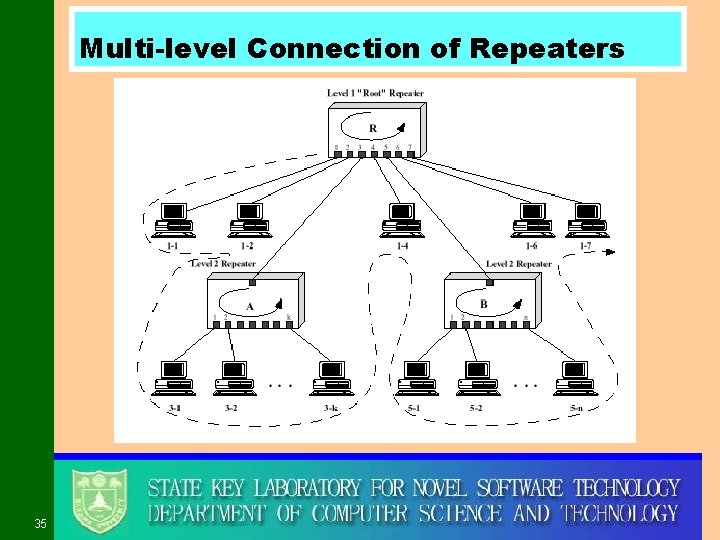
Multi-level Connection of Repeaters 35
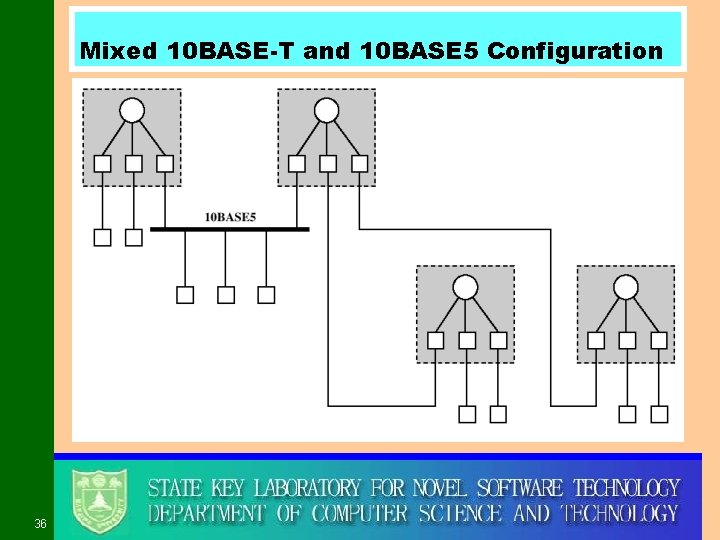
Mixed 10 BASE-T and 10 BASE 5 Configuration 36
37
38
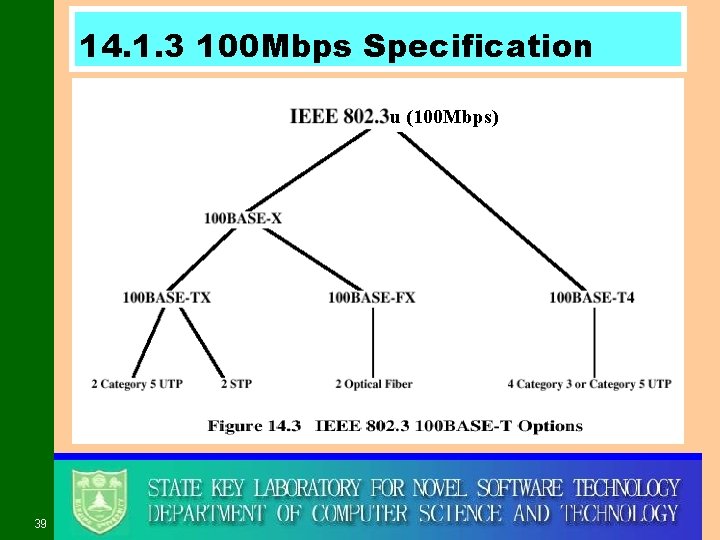
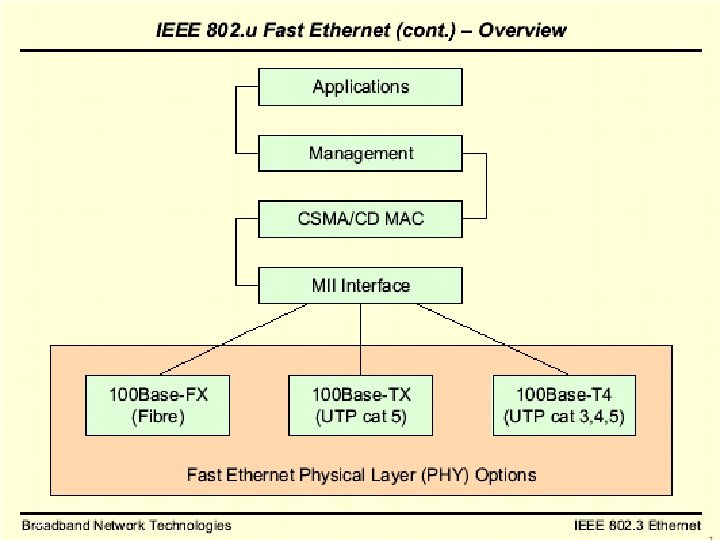
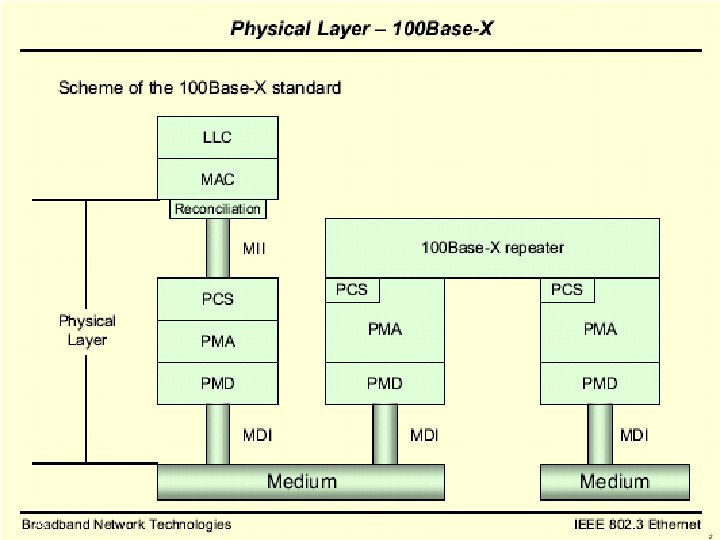
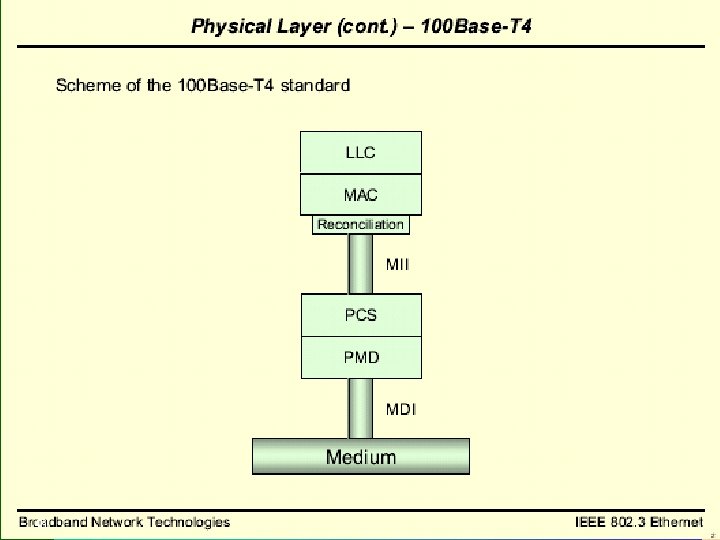
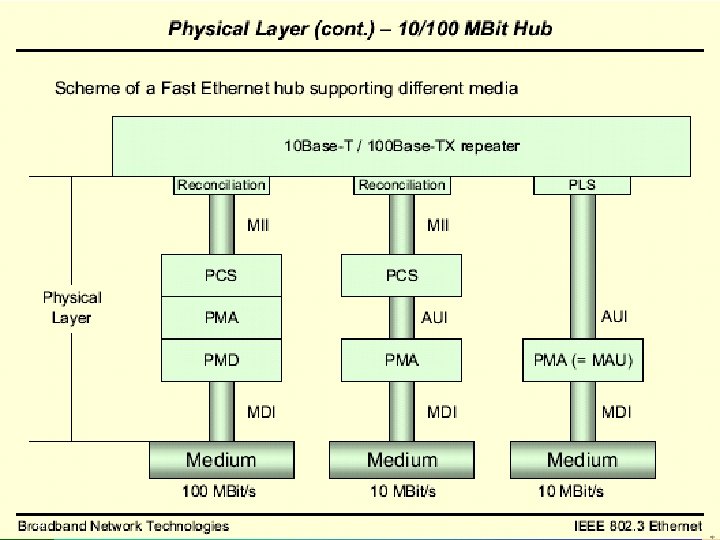
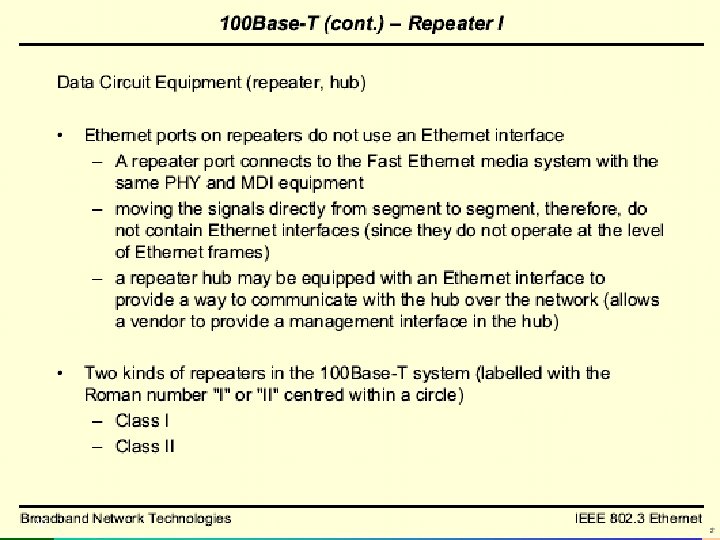
14. 1. 3 100 Mbps Specification u (100 Mbps) 39
40
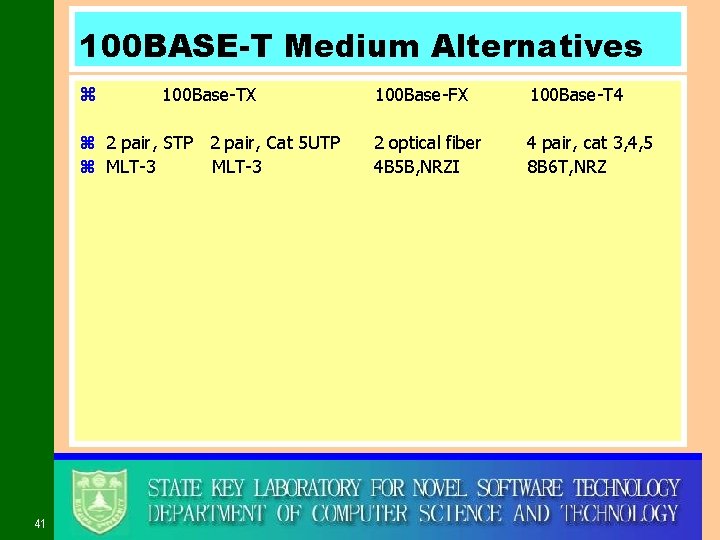
100 BASE-T Medium Alternatives z 100 Base-TX z 2 pair, STP 2 pair, Cat 5 UTP z MLT-3 41 100 Base-FX 100 Base-T 4 2 optical fiber 4 B 5 B, NRZI 4 pair, cat 3, 4, 5 8 B 6 T, NRZ
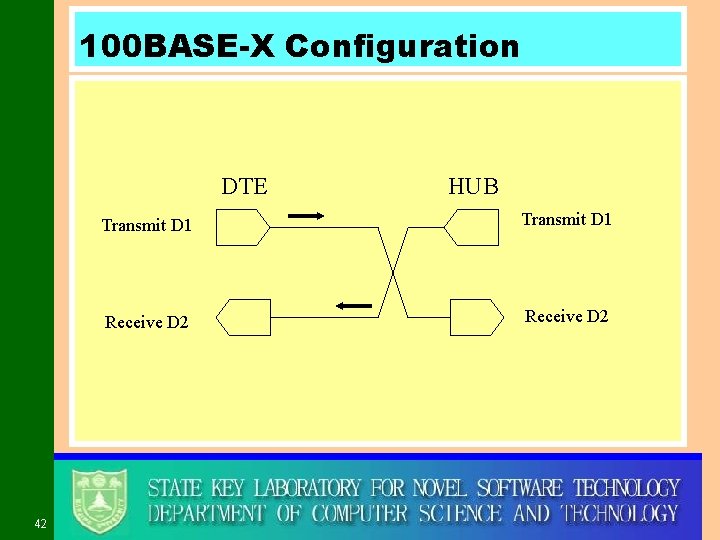
100 BASE-X Configuration DTE 42 HUB Transmit D 1 Receive D 2
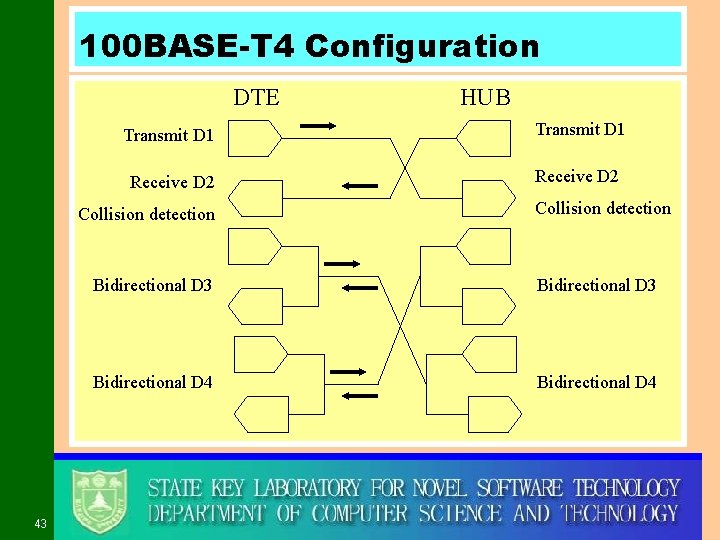
100 BASE-T 4 Configuration DTE Transmit D 1 Receive D 2 Collision detection 43 HUB Collision detection Bidirectional D 3 Bidirectional D 4
44
45
46
47
48
49
50
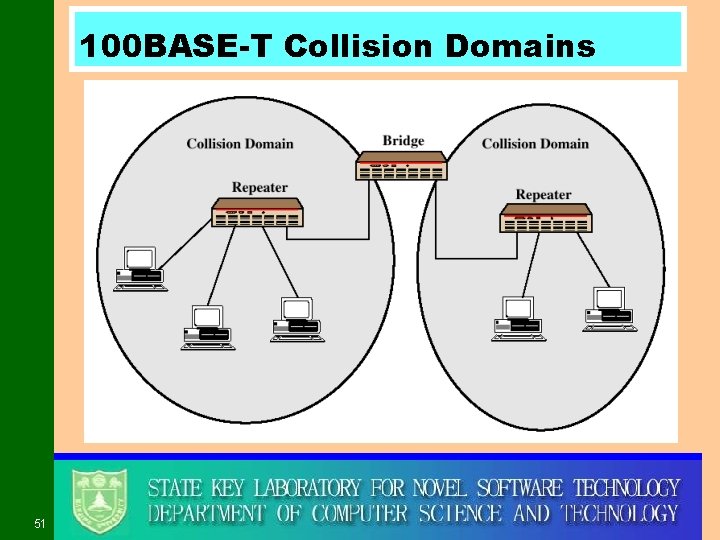
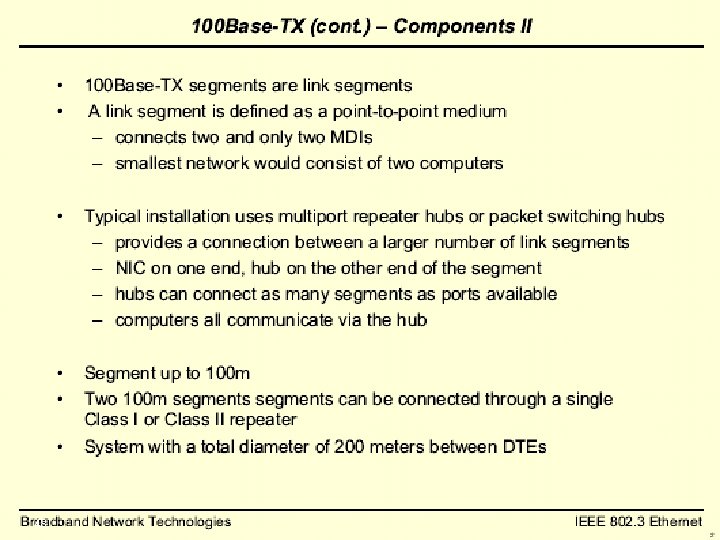
100 BASE-T Collision Domains 51
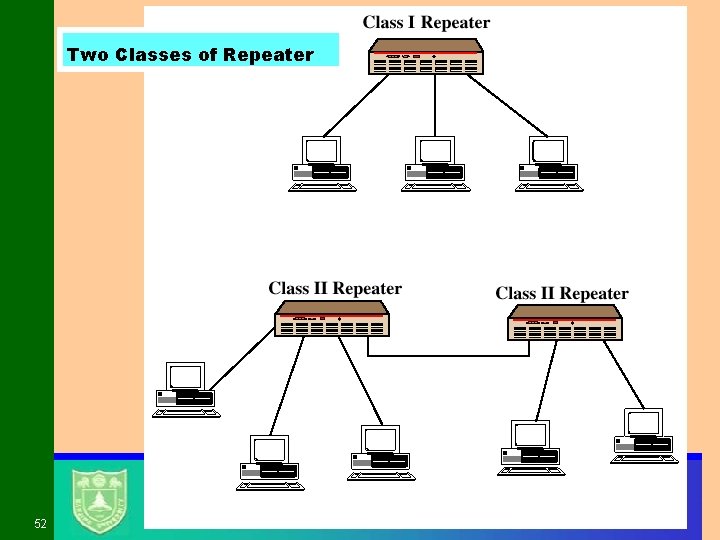
Two Classes of Repeater 52
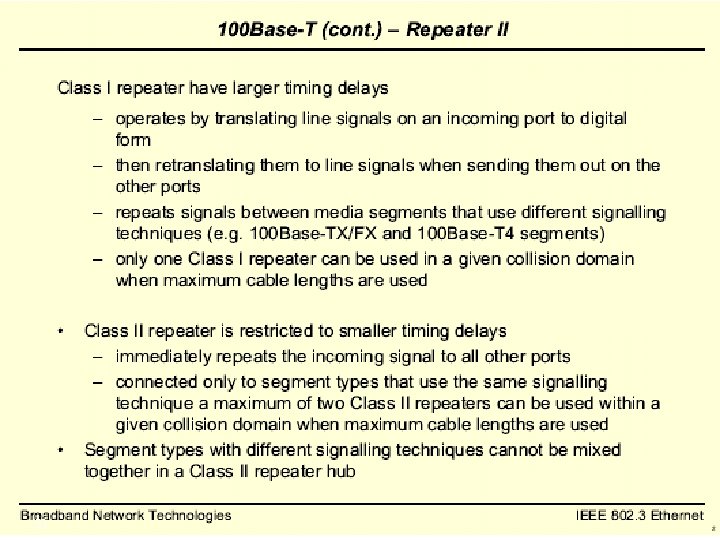
53
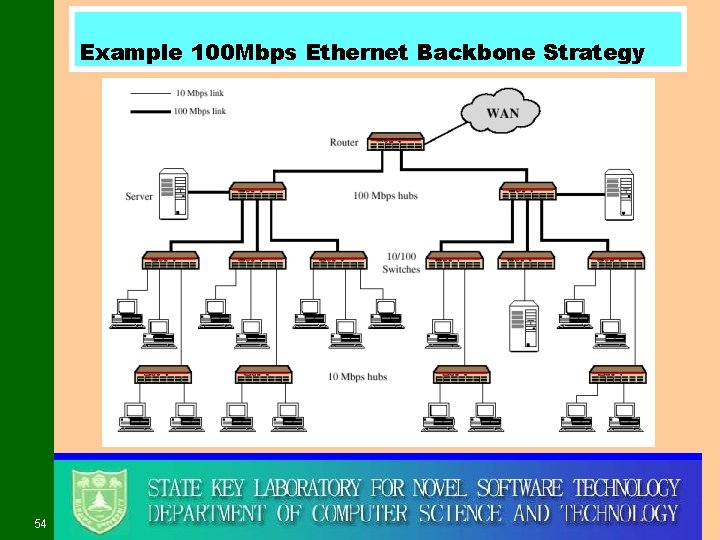
Example 100 Mbps Ethernet Backbone Strategy 54
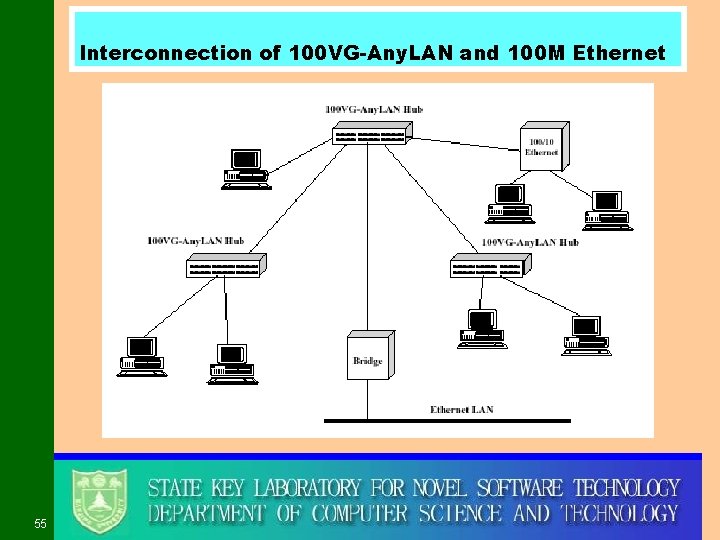
Interconnection of 100 VG-Any. LAN and 100 M Ethernet 55
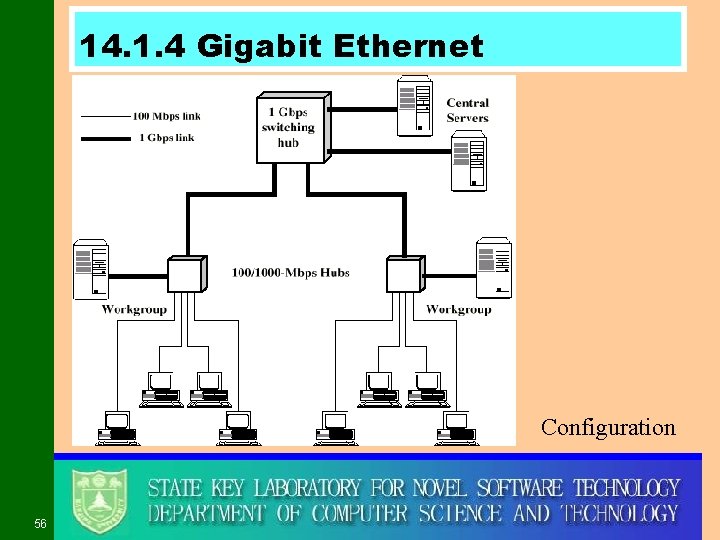
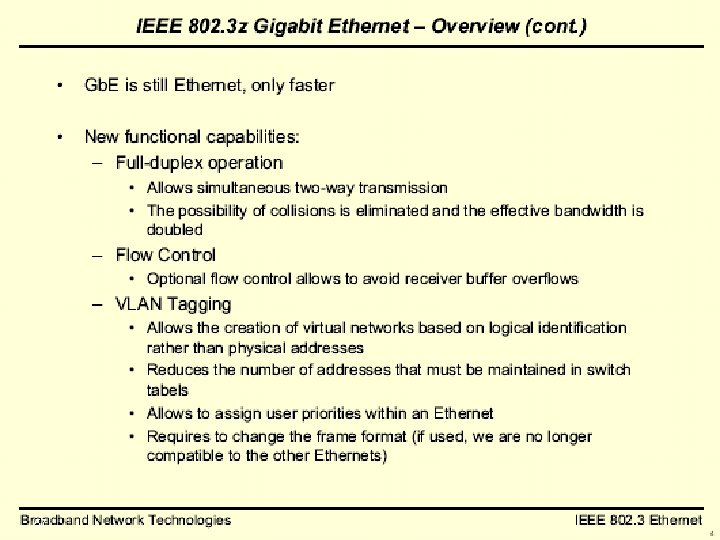
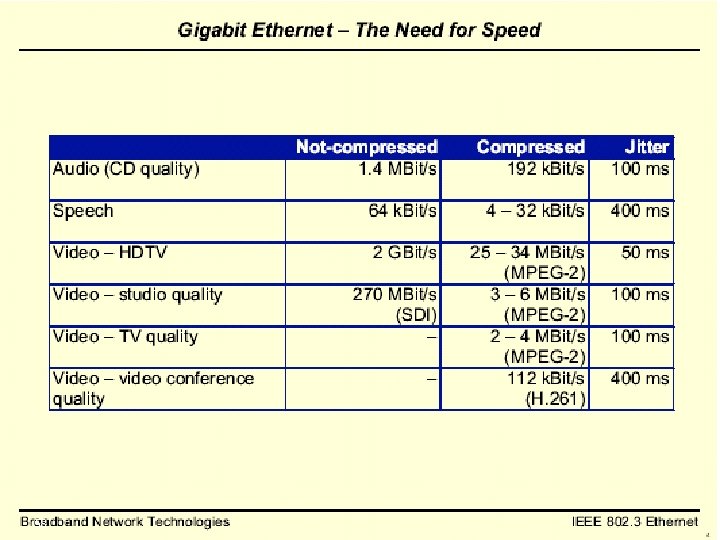
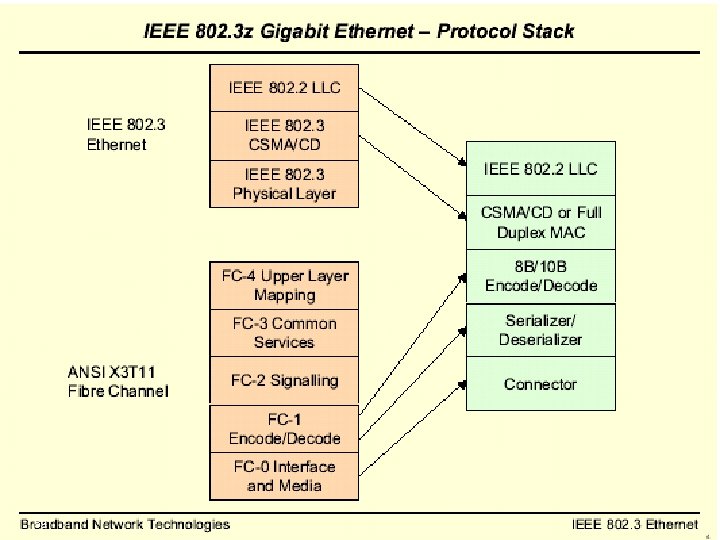
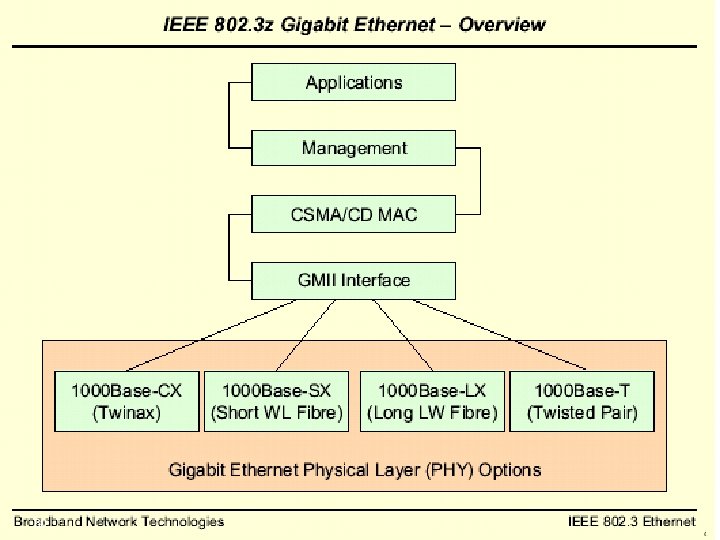
14. 1. 4 Gigabit Ethernet Configuration 56
57
58
59
60
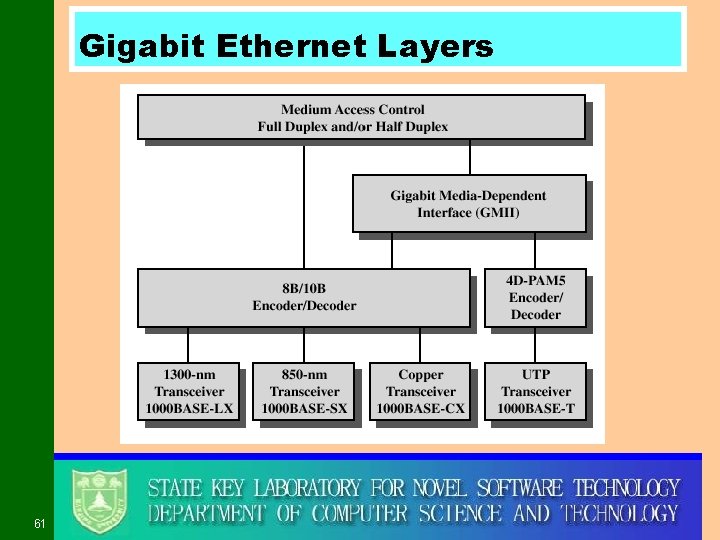
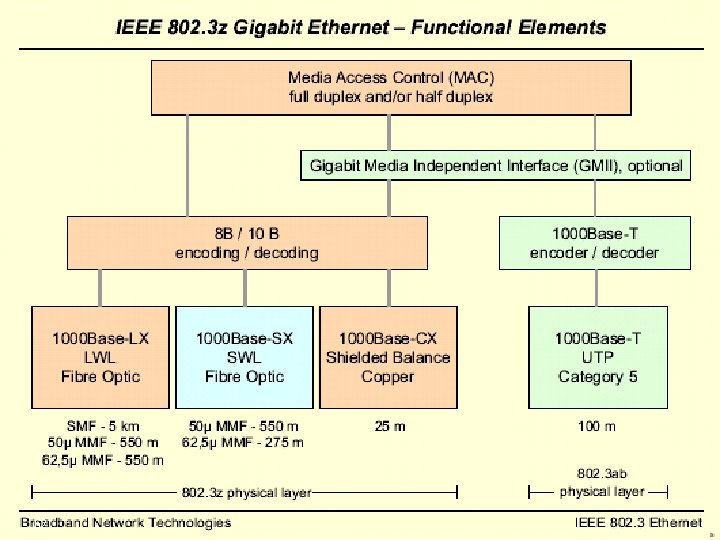
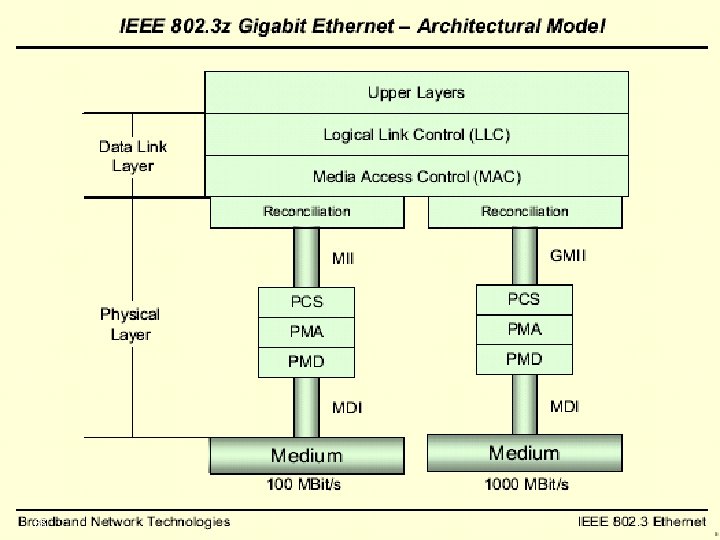
Gigabit Ethernet Layers 61
62
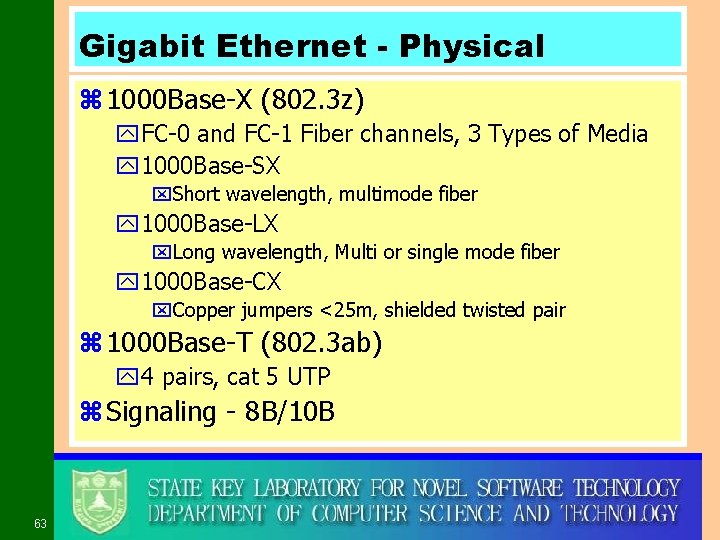
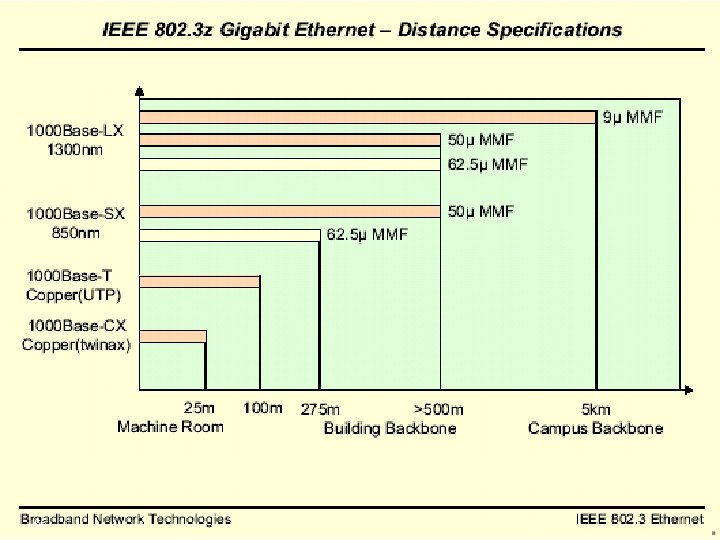
Gigabit Ethernet - Physical z 1000 Base-X (802. 3 z) y. FC-0 and FC-1 Fiber channels, 3 Types of Media y 1000 Base-SX x. Short wavelength, multimode fiber y 1000 Base-LX x. Long wavelength, Multi or single mode fiber y 1000 Base-CX x. Copper jumpers <25 m, shielded twisted pair z 1000 Base-T (802. 3 ab) y 4 pairs, cat 5 UTP z Signaling - 8 B/10 B 63
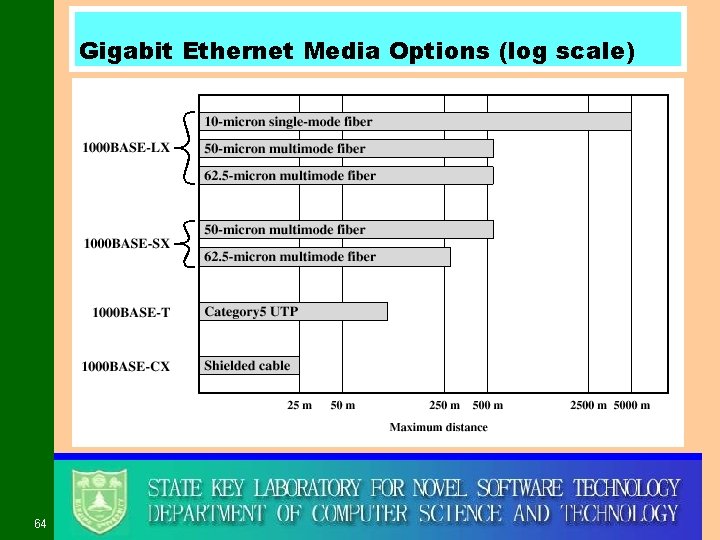
Gigabit Ethernet Media Options (log scale) 64
65
66
67
68
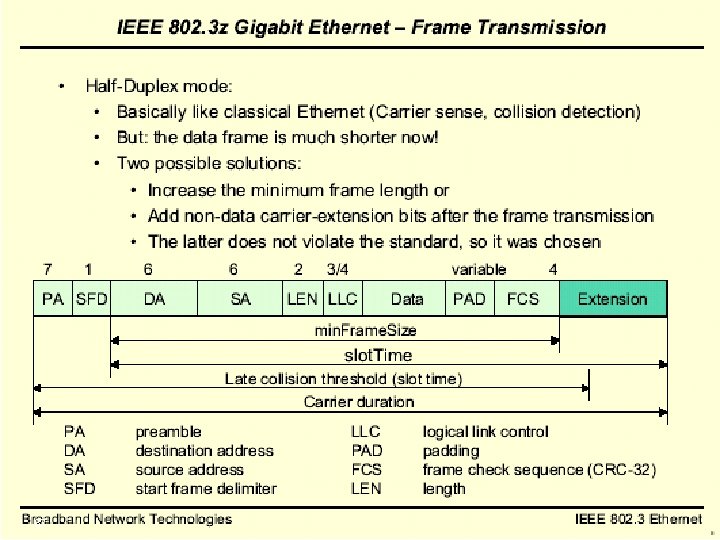
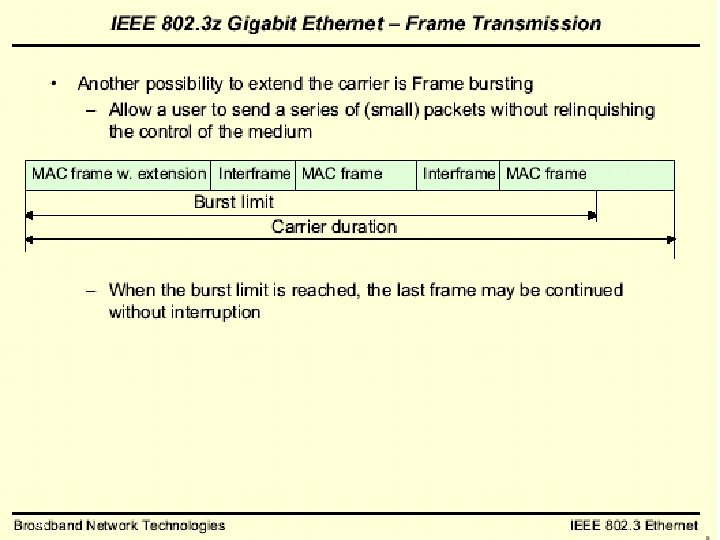
Gigabit Ethernet - Differences z Carrier extension y. At least 4096 bit-times long (512 for 10/100) z Frame bursting 69

14. 2 Token Ring and FDDI 71
14. 2. 1 Token Ring (802. 5) 令牌环 z MAC protocol y Small frame (token) circulates when idle y Station waits for token y Changes one bit in token to make it SOF for data frame y Append rest of data frame y Frame makes round trip and is absorbed by transmitting station y Station then inserts new token when transmission has finished and leading edge of returning frame arrives y Under light loads, some inefficiency y Under heavy loads, round robin 72
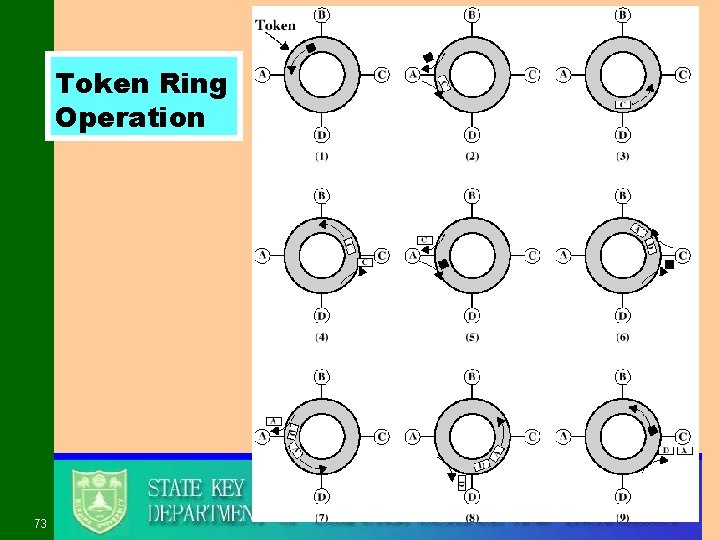
Token Ring Operation 73
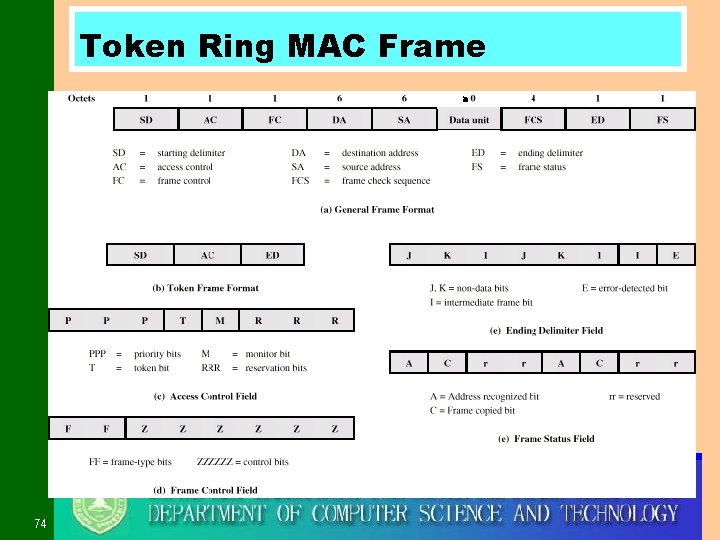
Token Ring MAC Frame 74
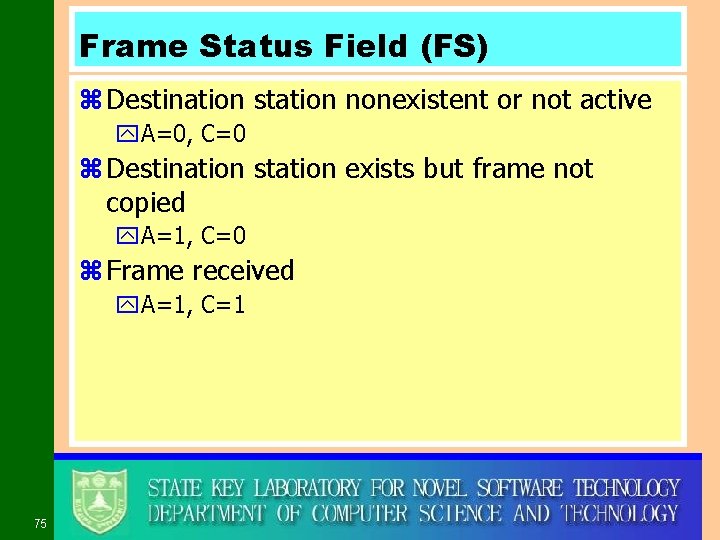
Frame Status Field (FS) z Destination station nonexistent or not active y. A=0, C=0 z Destination station exists but frame not copied y. A=1, C=0 z Frame received y. A=1, C=1 75
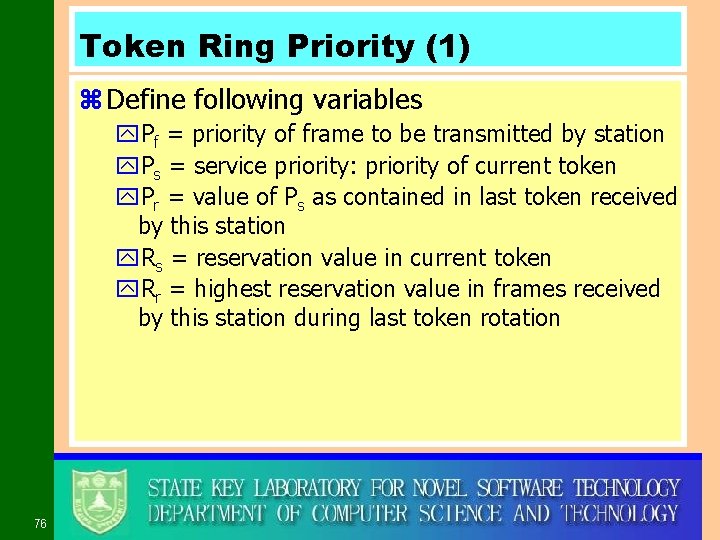
Token Ring Priority (1) z Define following variables y. Pf = priority of frame to be transmitted by station y. Ps = service priority: priority of current token y. Pr = value of Ps as contained in last token received by this station y. Rs = reservation value in current token y. Rr = highest reservation value in frames received by this station during last token rotation 76
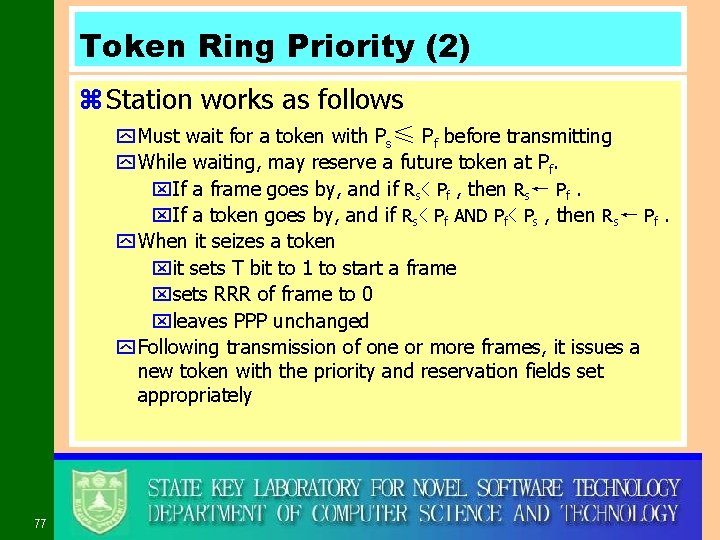
Token Ring Priority (2) z Station works as follows y Must wait for a token with Ps≤ Pf before transmitting y While waiting, may reserve a future token at Pf. x. If a frame goes by, and if Rs< Pf , then Rs← Pf. x. If a token goes by, and if Rs< Pf AND Pf< Ps , then Rs← Pf. y When it seizes a token xit sets T bit to 1 to start a frame xsets RRR of frame to 0 xleaves PPP unchanged y Following transmission of one or more frames, it issues a new token with the priority and reservation fields set appropriately 77
Token Ring Priority (3) z Each station maintains two stacks y Sx = store new values of token priority y Sr = store old values of token priority 78
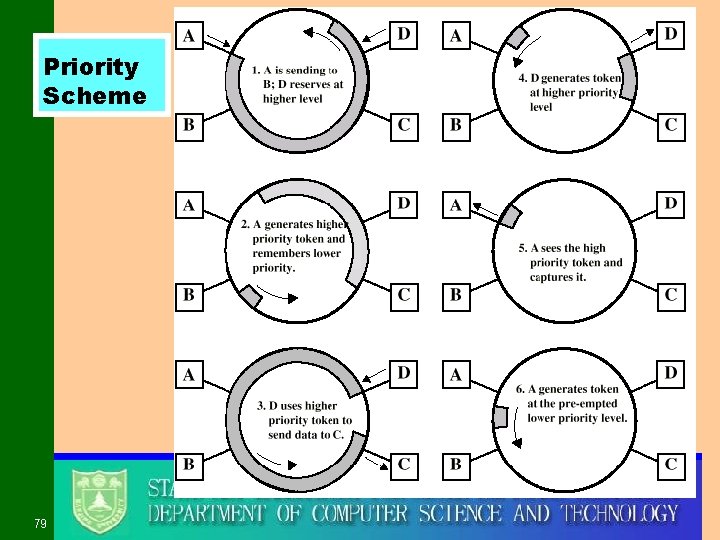
Priority Scheme 79
Early Token Release (ETR) z ETR allows a transmitting station to release a token as soon as it completes frame transmission, whether or not the frame header has returned to the station z One effect of ETR is that access delay for priority traffic may increase when the ring is heavily loaded with short frames z Stations that implement ETR are compatible and interoperable with those that do not 80
Dedicated Token Ring (DTR) z Central hub z Acts as switch z Full duplex point to point link z Concentrator acts as frame level repeater y. No token passing 81
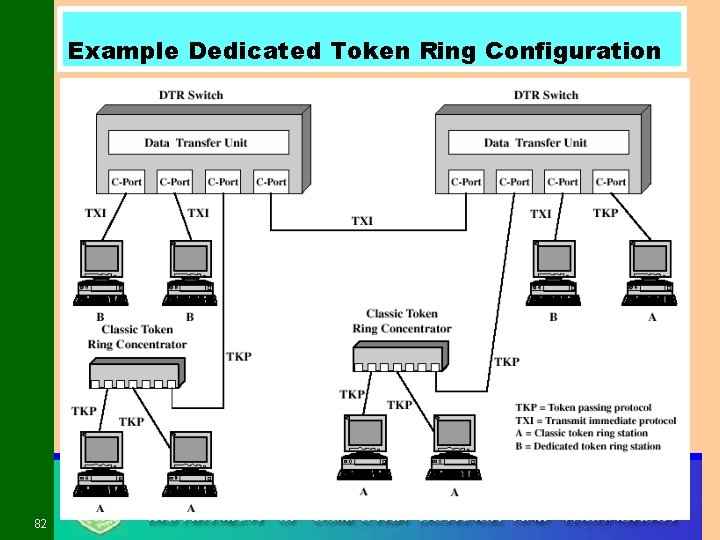
Example Dedicated Token Ring Configuration 82
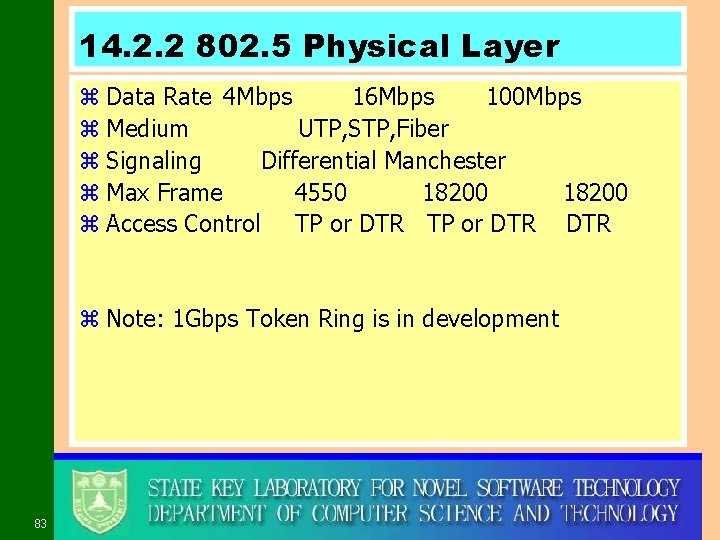
14. 2. 2 802. 5 Physical Layer z Data Rate 4 Mbps 16 Mbps 100 Mbps z Medium UTP, STP, Fiber z Signaling Differential Manchester z Max Frame 4550 18200 z Access Control TP or DTR DTR z Note: 1 Gbps Token Ring is in development 83
14. 2. 3 FDDI z 100 Mbps z LAN and MAN applications z Token Ring 84
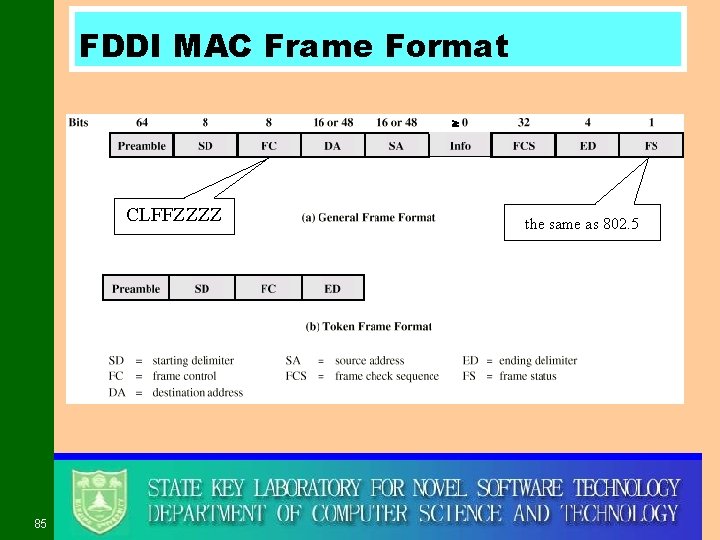
FDDI MAC Frame Format CLFFZZZZ 85 the same as 802. 5
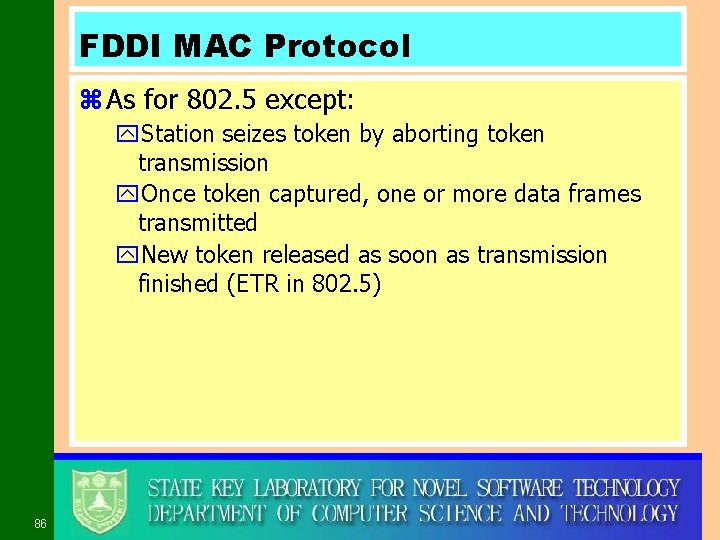
FDDI MAC Protocol z As for 802. 5 except: y. Station seizes token by aborting token transmission y. Once token captured, one or more data frames transmitted y. New token released as soon as transmission finished (ETR in 802. 5) 86
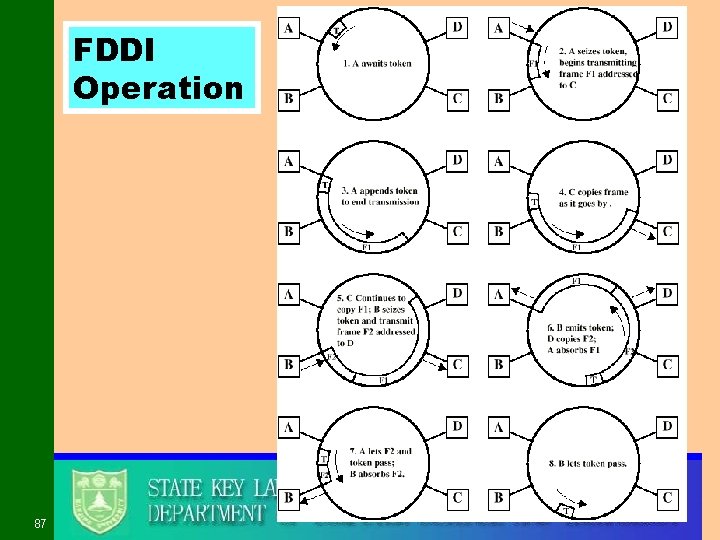
FDDI Operation 87
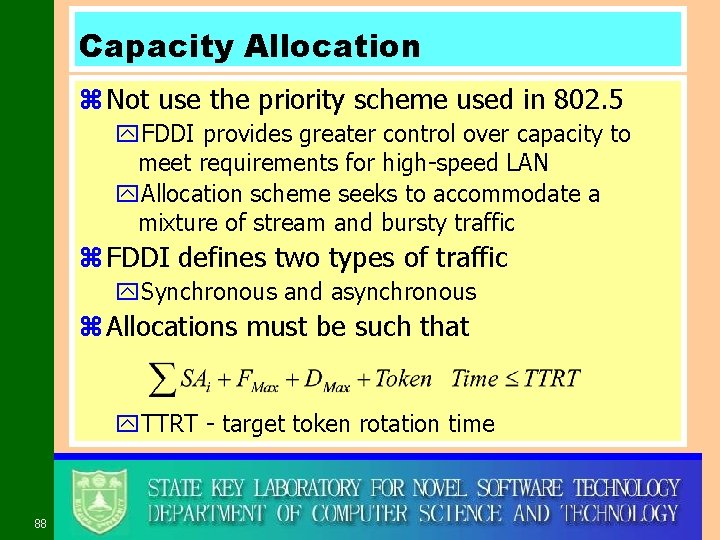
Capacity Allocation z Not use the priority scheme used in 802. 5 y. FDDI provides greater control over capacity to meet requirements for high-speed LAN y. Allocation scheme seeks to accommodate a mixture of stream and bursty traffic z FDDI defines two types of traffic y. Synchronous and asynchronous z Allocations must be such that y. TTRT - target token rotation time 88
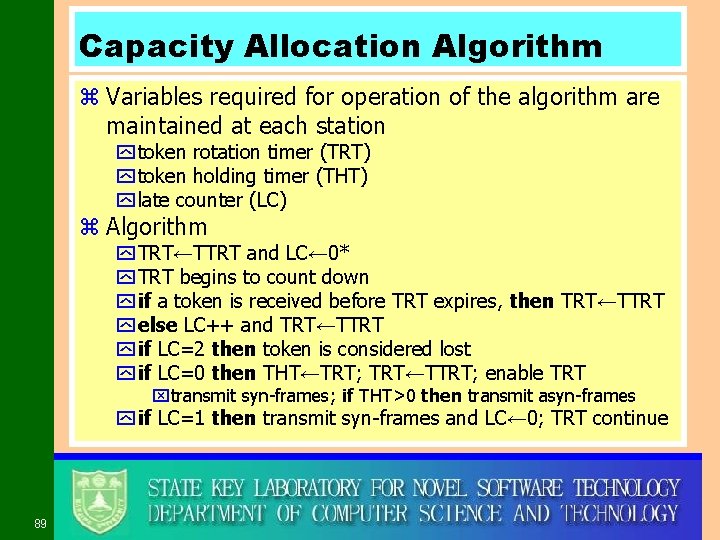
Capacity Allocation Algorithm z Variables required for operation of the algorithm are maintained at each station y token rotation timer (TRT) y token holding timer (THT) y late counter (LC) z Algorithm y TRT←TTRT and LC← 0* y TRT begins to count down y if a token is received before TRT expires, then TRT←TTRT y else LC++ and TRT←TTRT y if LC=2 then token is considered lost y if LC=0 then THT←TRT; TRT←TTRT; enable TRT xtransmit syn-frames; if THT>0 then transmit asyn-frames y if LC=1 then transmit syn-frames and LC← 0; TRT continue 89
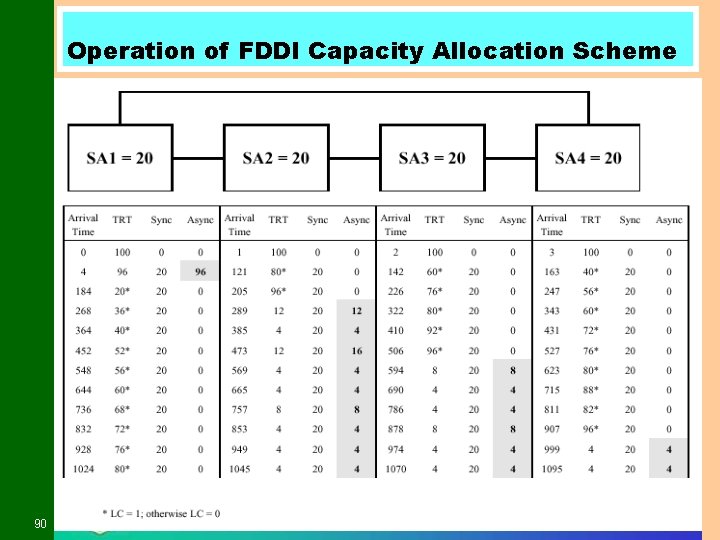
Operation of FDDI Capacity Allocation Scheme 90
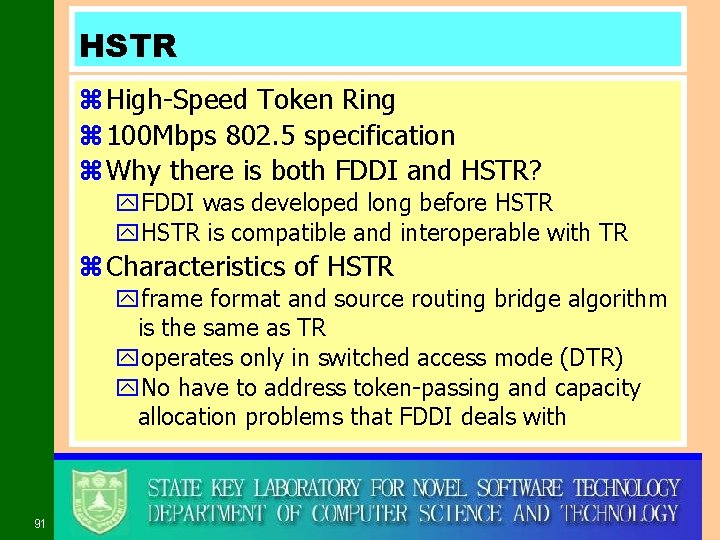
HSTR z High-Speed Token Ring z 100 Mbps 802. 5 specification z Why there is both FDDI and HSTR? y. FDDI was developed long before HSTR y. HSTR is compatible and interoperable with TR z Characteristics of HSTR yframe format and source routing bridge algorithm is the same as TR yoperates only in switched access mode (DTR) y. No have to address token-passing and capacity allocation problems that FDDI deals with 91
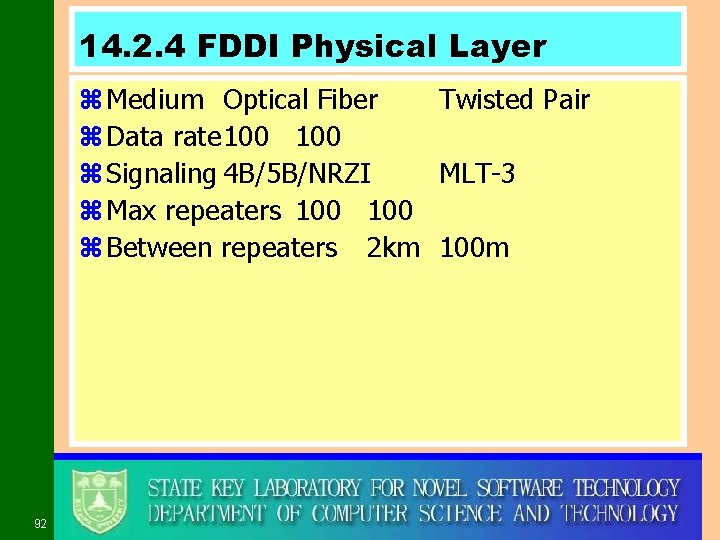
14. 2. 4 FDDI Physical Layer z Medium Optical Fiber Twisted Pair z Data rate 100 z Signaling 4 B/5 B/NRZI MLT-3 z Max repeaters 100 z Between repeaters 2 km 100 m 92
14. 3 ATM LANs z LAN Generations y. First x. CSMA/CD and token ring x. Terminal to host and client server x. Moderate data rates y. Second x. FDDI x. Backbone x. High performance workstations y. Third x. ATM x. Aggregate throughput and real time support for multimedia applications 93
Third Generation LANs z Support for multiple guaranteed classes of service y. Live video may need 2 Mbps y. File transfer can use background class z Scalable throughput y. Both aggregate and per host z Facilitate LAN/WAN internetworking 94
Possible Types of ATM LANs z Asynchronous Transfer Mode z Virtual paths and virtual channels z Preconfigured or switched z Gateway to ATM WAN z Backbone ATM switch y. Single ATM switch or local network of ATM switches z Workgroup ATM y. End systems connected directly to ATM switch z Mixed system 95
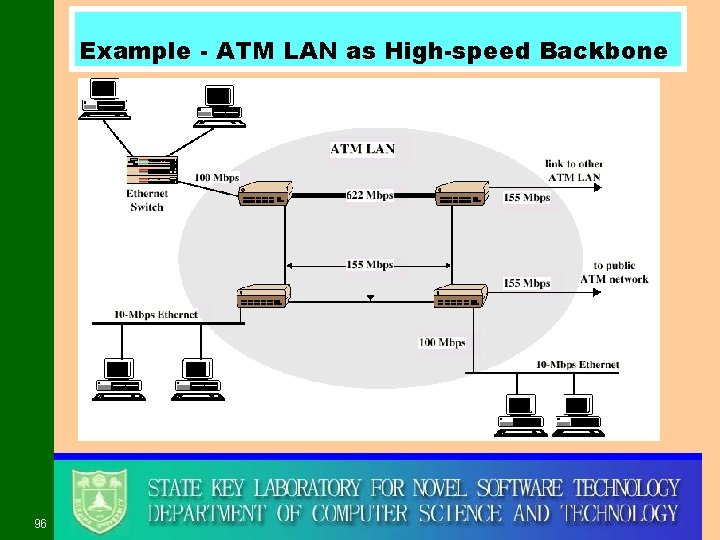
Example - ATM LAN as High-speed Backbone 96
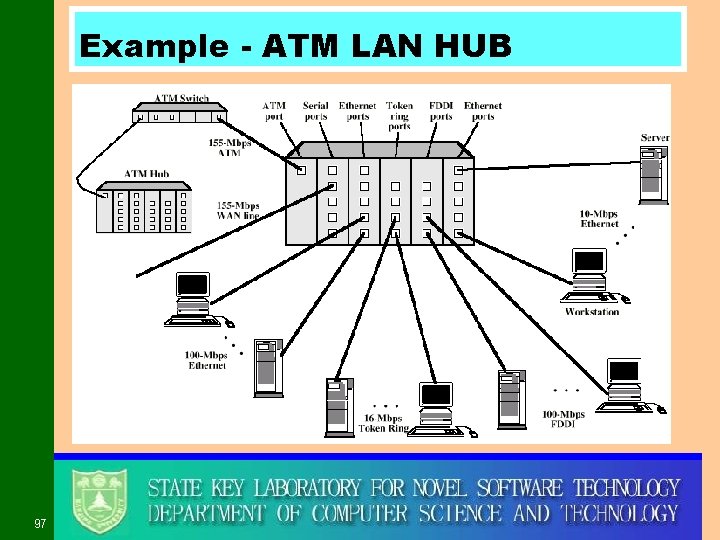
Example - ATM LAN HUB 97
Compatibility z Interaction between end system on ATM and end system on legacy LAN z Interaction between stations on legacy LANs of the same type z Interaction between stations on legacy LANs of different types 98
14. 4 Fiber Channel z Background y I/O channel x. Direct point to point or multipoint comms link x. Hardware based x. High Speed x. Very short distance x. User data moved from source buffer to destiation buffer y. Network connection x. Interconnected access points x. Software based protocol x. Flow control, error detection &recovery x. End systems connections 100
Design of Fiber Channel z Best of both technologies z Channel oriented y. Data type qualifiers for routing frame payload y. Link level constructs associated with I/O ops y. Protocol interface specifications to support existing I/O architectures xe. g. SCSI z Network oriented y. Full multiplexing between multiple destinations y. Peer to peer connectivity y. Internetworking to other connection technologies 101
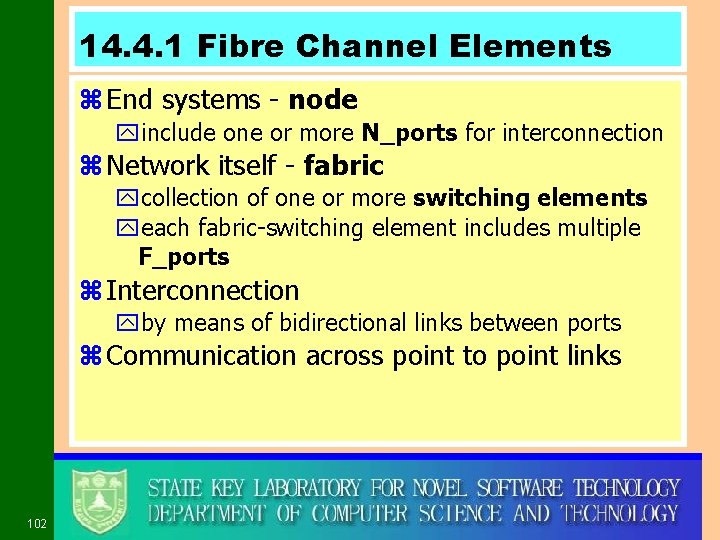
14. 4. 1 Fibre Channel Elements z End systems - node yinclude one or more N_ports for interconnection z Network itself - fabric ycollection of one or more switching elements yeach fabric-switching element includes multiple F_ports z Interconnection yby means of bidirectional links between ports z Communication across point to point links 102
Fibre Channel Port Types 103
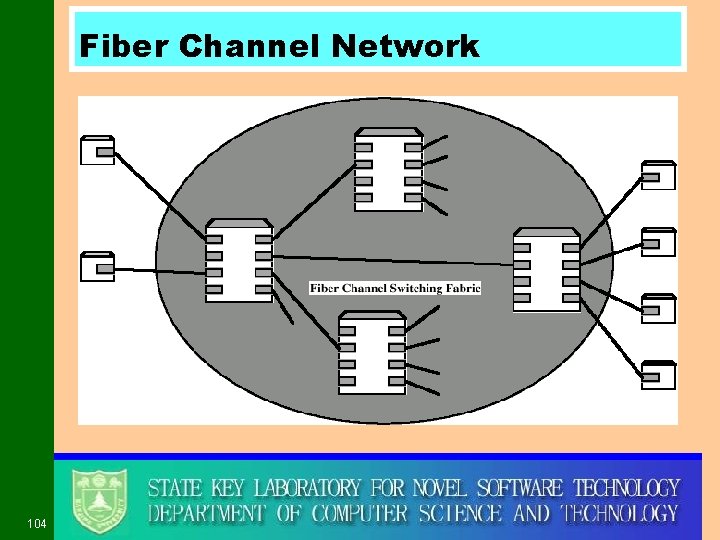
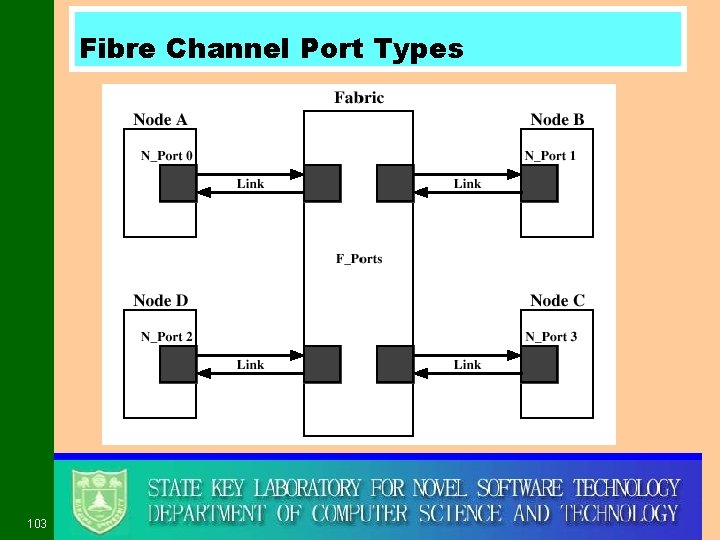
Fiber Channel Network 104
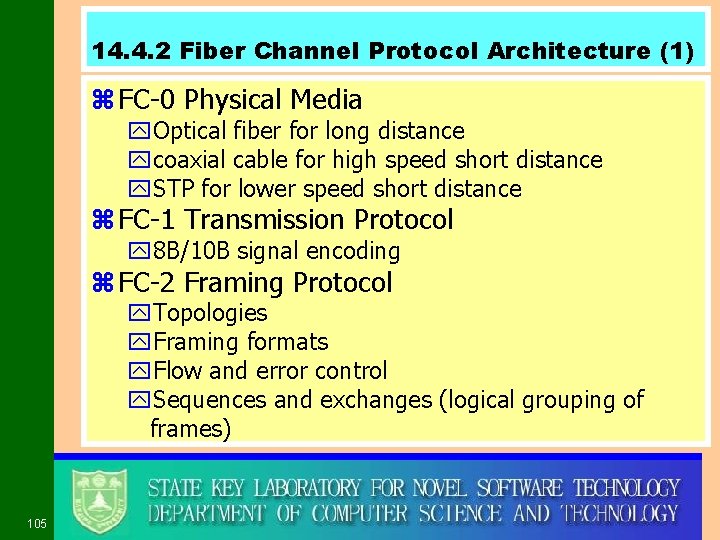
14. 4. 2 Fiber Channel Protocol Architecture (1) z FC-0 Physical Media y. Optical fiber for long distance ycoaxial cable for high speed short distance y. STP for lower speed short distance z FC-1 Transmission Protocol y 8 B/10 B signal encoding z FC-2 Framing Protocol y. Topologies y. Framing formats y. Flow and error control y. Sequences and exchanges (logical grouping of frames) 105
Fiber Channel Protocol Architecture(2) z FC-3 Common Services y. Including multicasting z FC-4 Mapping y. Mapping of channel and network services onto fiber channel xe. g. IEEE 802, ATM, IP, SCSI 106
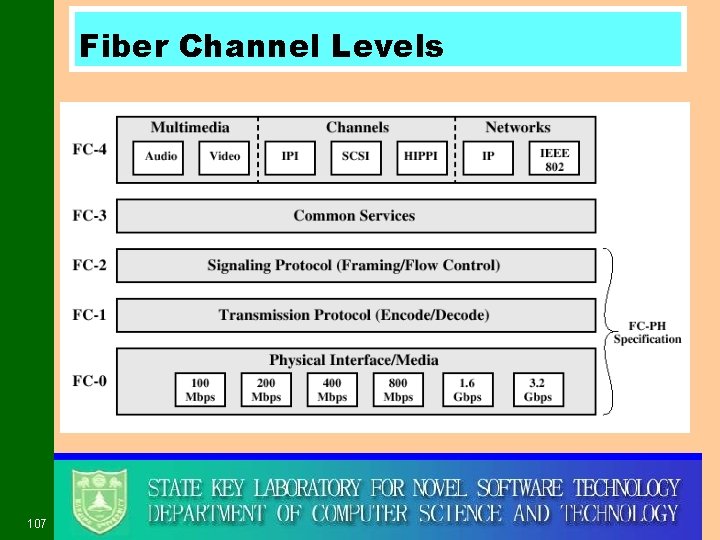
Fiber Channel Levels 107
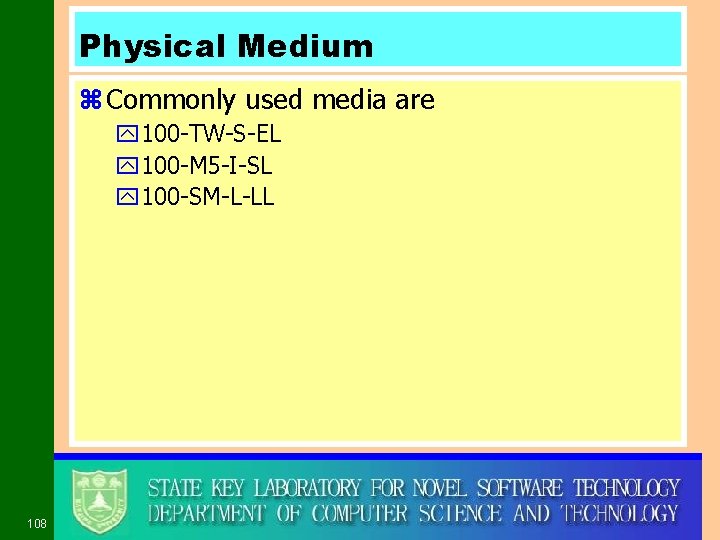
Physical Medium z Commonly used media are y 100 -TW-S-EL y 100 -M 5 -I-SL y 100 -SM-L-LL 108
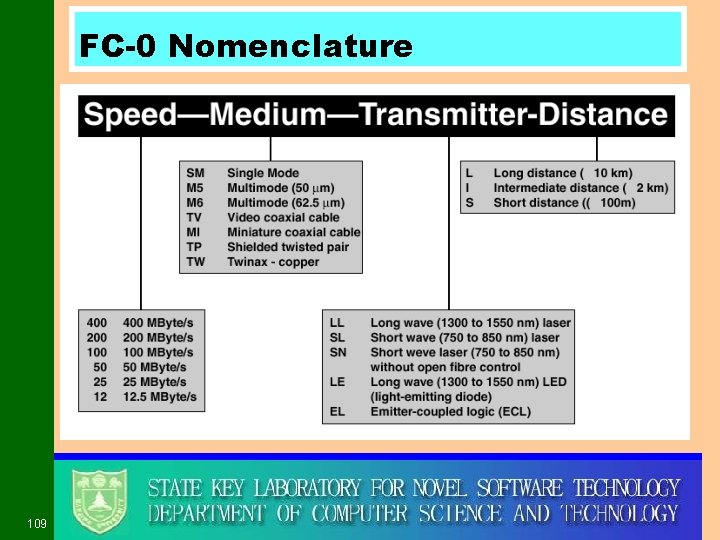
FC-0 Nomenclature 109
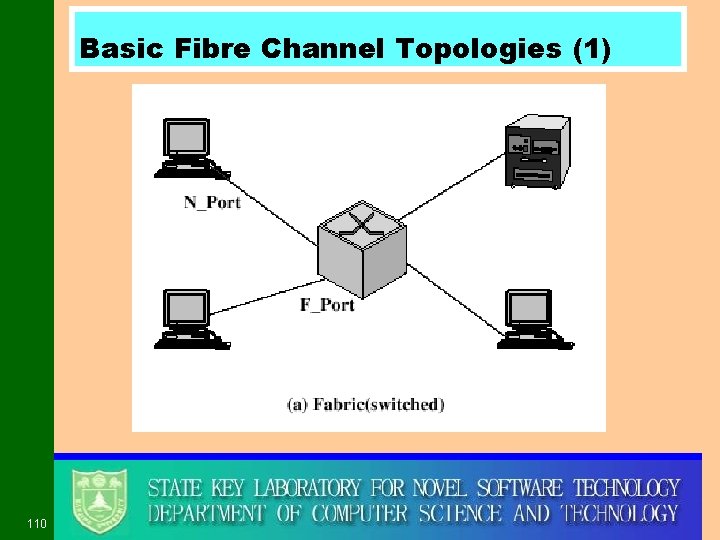
Basic Fibre Channel Topologies (1) 110
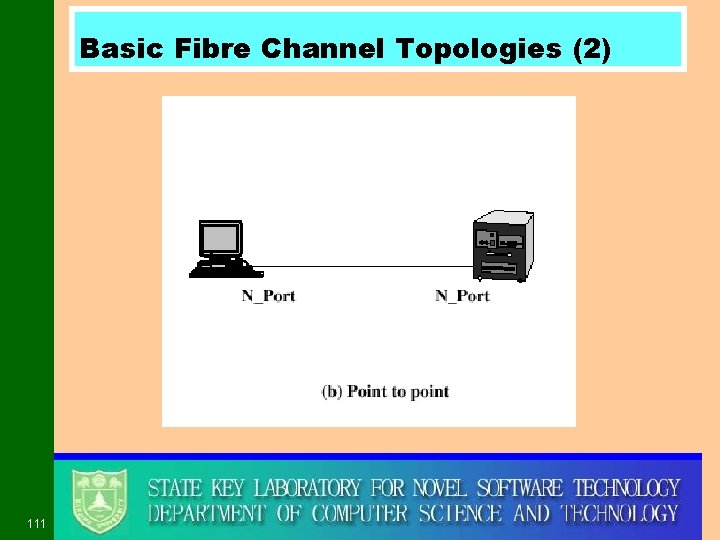
Basic Fibre Channel Topologies (2) 111
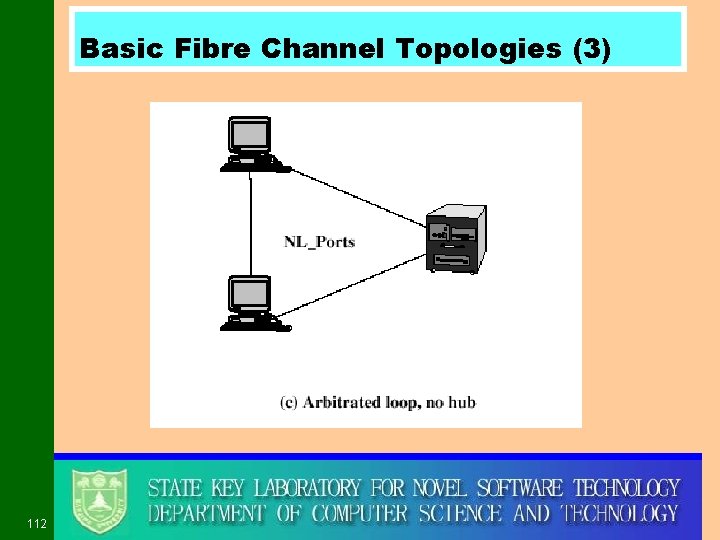
Basic Fibre Channel Topologies (3) 112
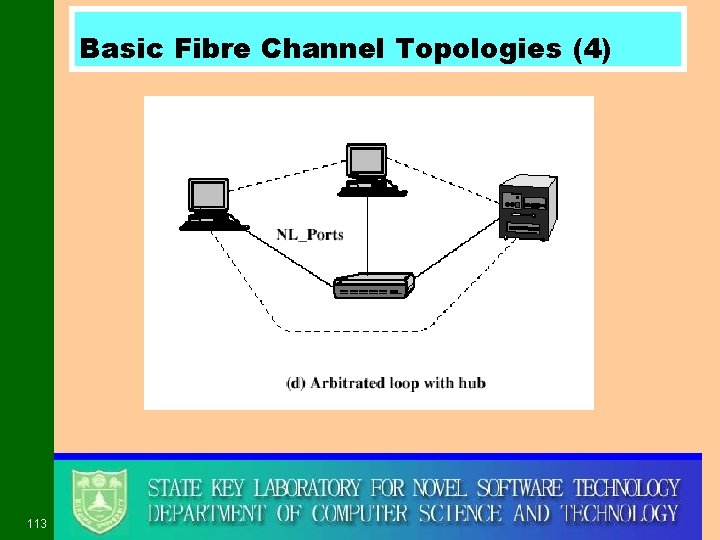
Basic Fibre Channel Topologies (4) 113
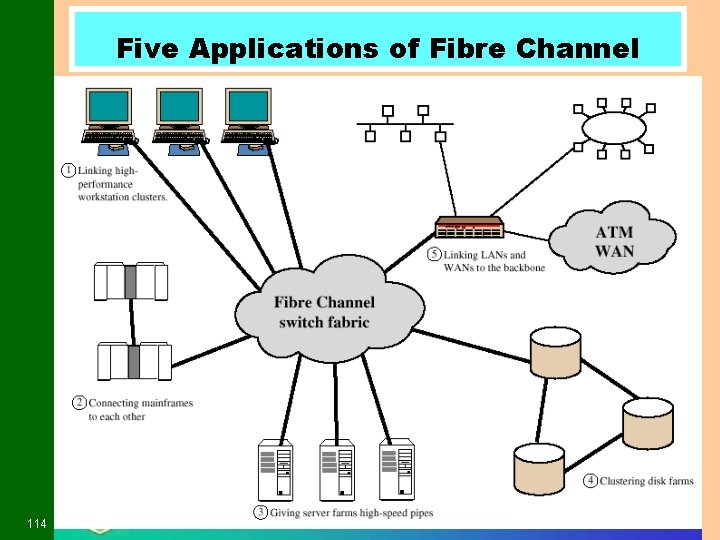
Five Applications of Fibre Channel 114
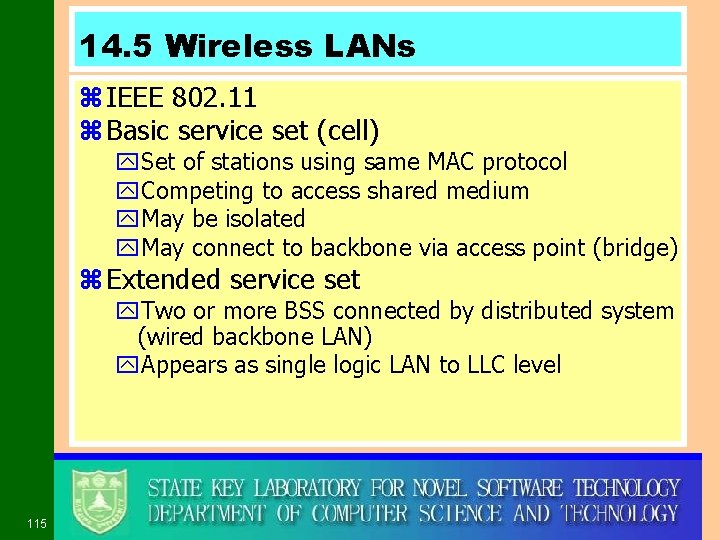
14. 5 Wireless LANs z IEEE 802. 11 z Basic service set (cell) y. Set of stations using same MAC protocol y. Competing to access shared medium y. May be isolated y. May connect to backbone via access point (bridge) z Extended service set y. Two or more BSS connected by distributed system (wired backbone LAN) y. Appears as single logic LAN to LLC level 115
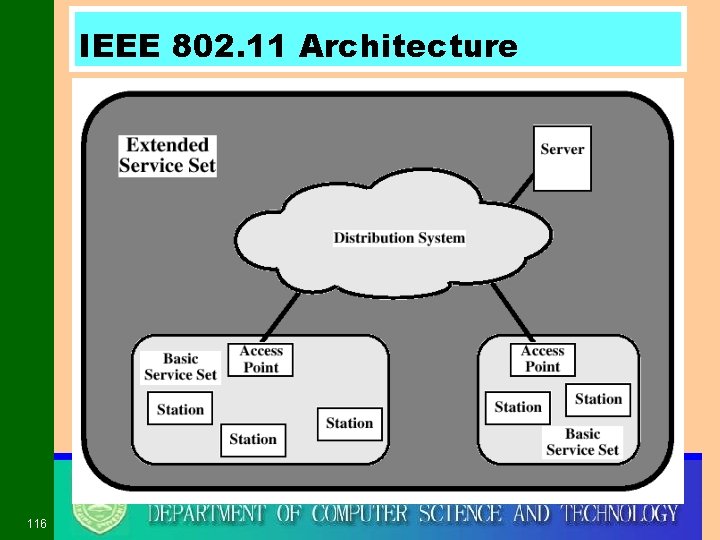
IEEE 802. 11 Architecture 116
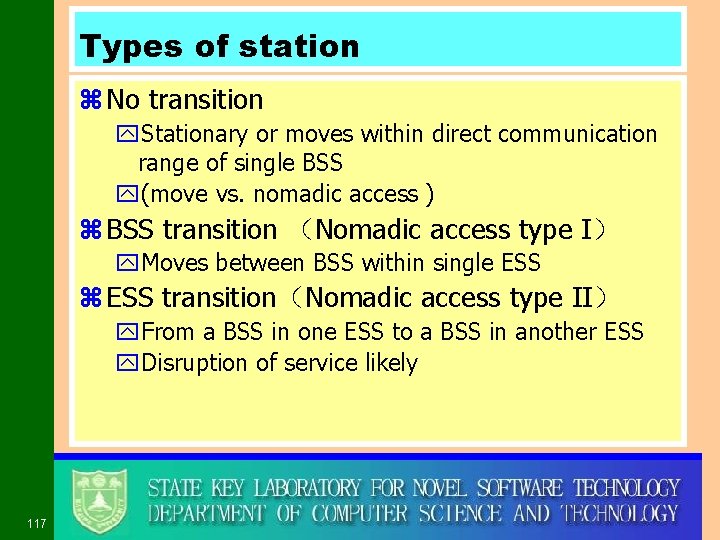
Types of station z No transition y. Stationary or moves within direct communication range of single BSS y(move vs. nomadic access ) z BSS transition (Nomadic access type I) y. Moves between BSS within single ESS z ESS transition(Nomadic access type II) y. From a BSS in one ESS to a BSS in another ESS y. Disruption of service likely 117
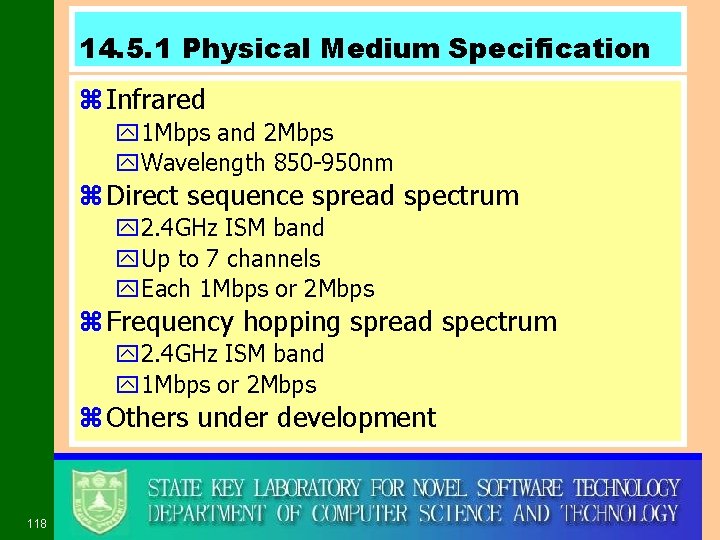
14. 5. 1 Physical Medium Specification z Infrared y 1 Mbps and 2 Mbps y. Wavelength 850 -950 nm z Direct sequence spread spectrum y 2. 4 GHz ISM band y. Up to 7 channels y. Each 1 Mbps or 2 Mbps z Frequency hopping spread spectrum y 2. 4 GHz ISM band y 1 Mbps or 2 Mbps z Others under development 118
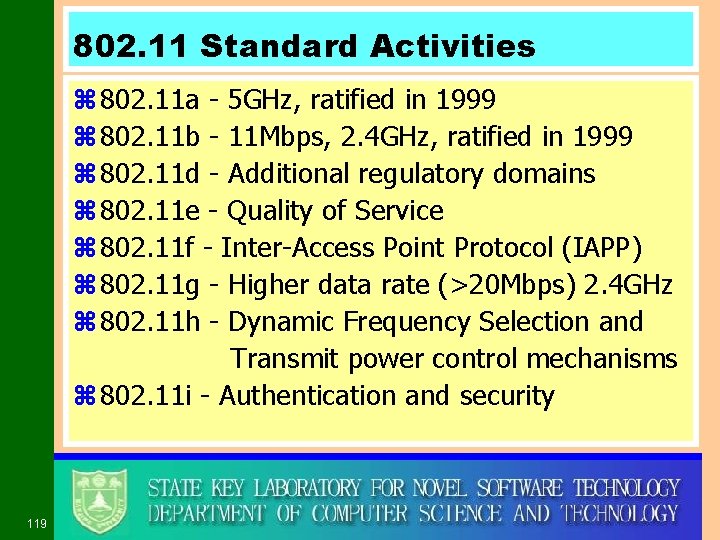
802. 11 Standard Activities z 802. 11 a - 5 GHz, ratified in 1999 z 802. 11 b - 11 Mbps, 2. 4 GHz, ratified in 1999 z 802. 11 d - Additional regulatory domains z 802. 11 e - Quality of Service z 802. 11 f - Inter-Access Point Protocol (IAPP) z 802. 11 g - Higher data rate (>20 Mbps) 2. 4 GHz z 802. 11 h - Dynamic Frequency Selection and Transmit power control mechanisms z 802. 11 i - Authentication and security 119
IEEE 802. 15 z Wireless Personal Area Networks y. Bluetooth y 2. 4 GHz 120
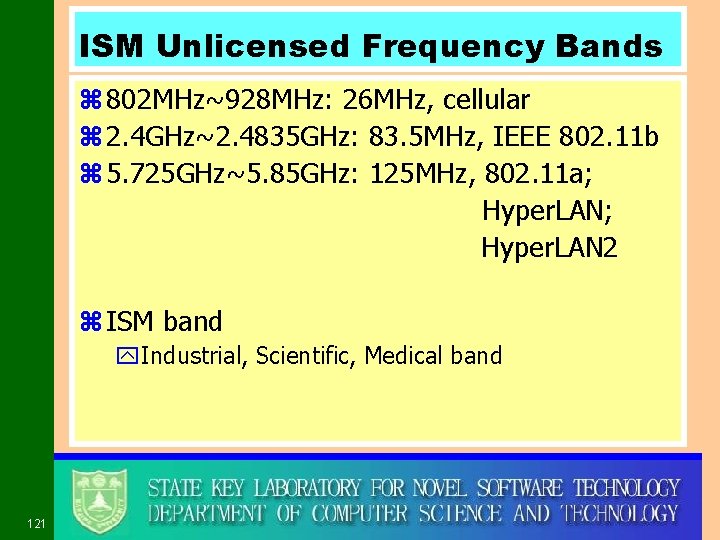
ISM Unlicensed Frequency Bands z 802 MHz~928 MHz: 26 MHz, cellular z 2. 4 GHz~2. 4835 GHz: 83. 5 MHz, IEEE 802. 11 b z 5. 725 GHz~5. 85 GHz: 125 MHz, 802. 11 a; Hyper. LAN 2 z ISM band y. Industrial, Scientific, Medical band 121
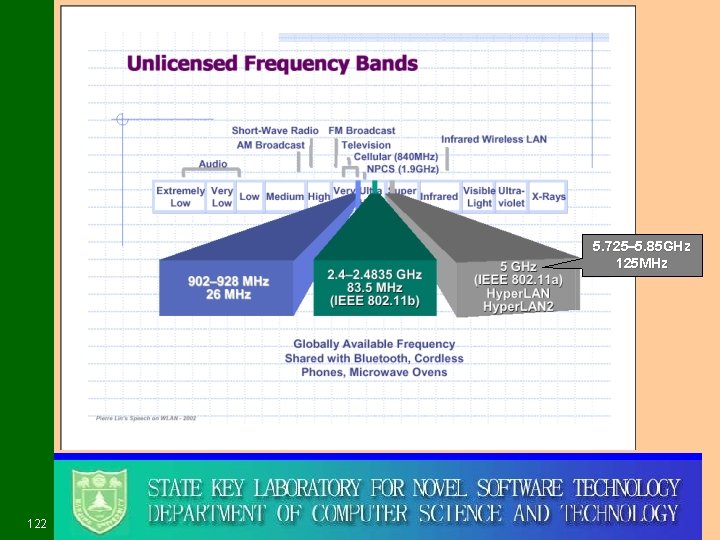
5. 725 -5. 85 GHz 125 MHz 122
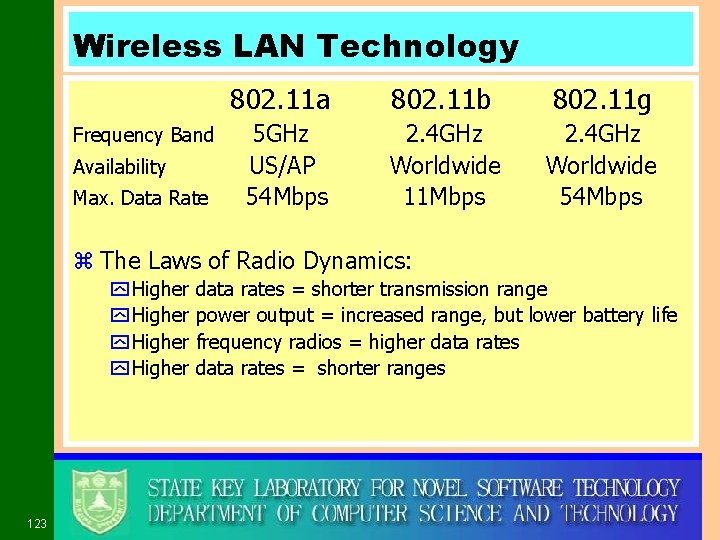
Wireless LAN Technology Frequency Band Availability Max. Data Rate 802. 11 a 802. 11 b 802. 11 g 5 GHz US/AP 54 Mbps 2. 4 GHz Worldwide 11 Mbps 2. 4 GHz Worldwide 54 Mbps z The Laws of Radio Dynamics: y Higher 123 data rates = shorter transmission range power output = increased range, but lower battery life frequency radios = higher data rates = shorter ranges
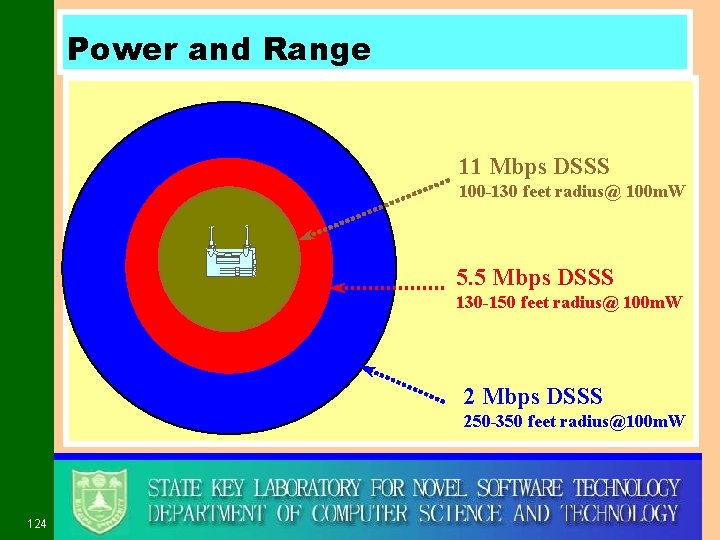
Power and Range 11 Mbps DSSS 100 -130 feet radius@ 100 m. W 5. 5 Mbps DSSS 130 -150 feet radius@ 100 m. W 2 Mbps DSSS 250 -350 feet radius@100 m. W 124
14. 5. 2 Medium Access Control z Distributed Foundation Wireless MAC (DFWMAC) z Distributed Coordination Function (DCF) y. CSMA y. No collision detection z Point Coordination Function (PCF) y. Polling of central master 125
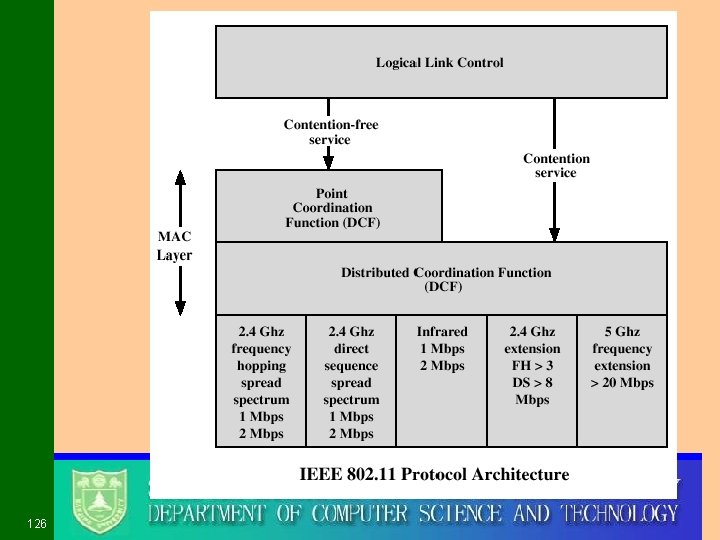
126
Distributed Coordination Function z DCF uses a simple CSMA algorithm y If a station has a MAC frame to transmit, then xlisten to medium x. If the medium is idle, then transmit xelse wait until the current transmission is complete z DCF does not include a collision detection function y not practical on a wireless network xthe dynamic range of signals on medium is very large, a transmitting station cannot effectively distinguish incoming weak signals from noise and the effects of its own transmission z DCF includes a set delays to ensure the smooth and fair functioning of this algorithm 127
CSMA Access Algorithm Using Delays z The set of Delays mounts to a priority scheme z Use a kind of IFS (Inter. Frame Space) z CSMA access rules y if medium is idle then xwaits to see if medium remains idle for a time equal to IFS xif idle then transmit immediately y if medium is busy then xdefers transmission and uses 1 -persistence y if current transmission is over then xdelays another IFS xif medium remains idle for this period then • uses a binary exponential backoff scheme • senses the medium again • if medium is still idle then transmit 128
IFS Types z SIFS - Short IFS ythe shortest IFS for all immediate response action z PIFS - Point coordination function IFS ymidlength IFS used by centralized controller in the PCF scheme when issuing polls z DIFS - Distributed coordination function IFS ythe longest IFS used as a minimum delay for asynchronous frames contending for access 129
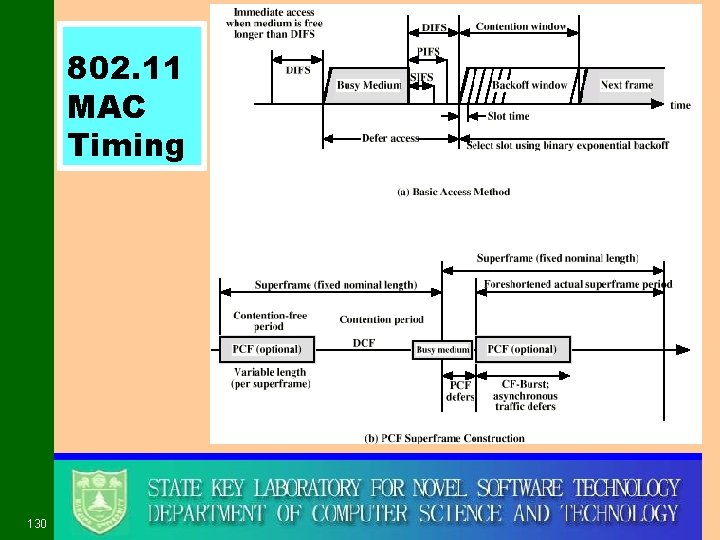
802. 11 MAC Timing 130
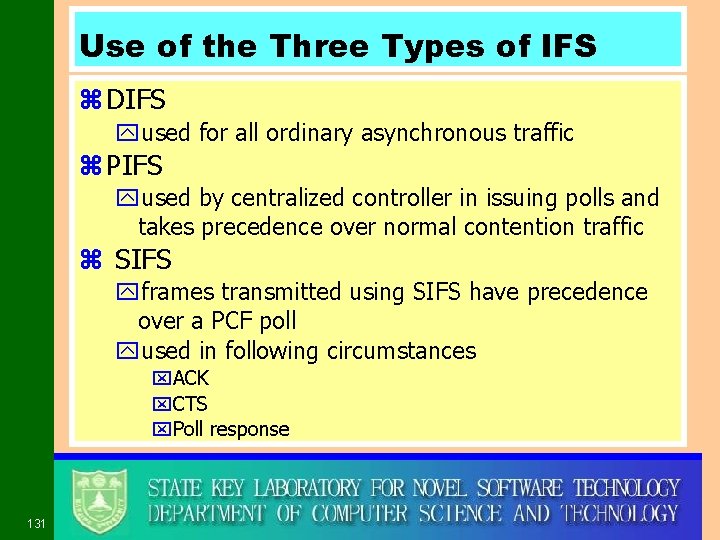
Use of the Three Types of IFS z DIFS yused for all ordinary asynchronous traffic z PIFS yused by centralized controller in issuing polls and takes precedence over normal contention traffic z SIFS yframes transmitted using SIFS have precedence over a PCF poll yused in following circumstances x. ACK x. CTS x. Poll response 131
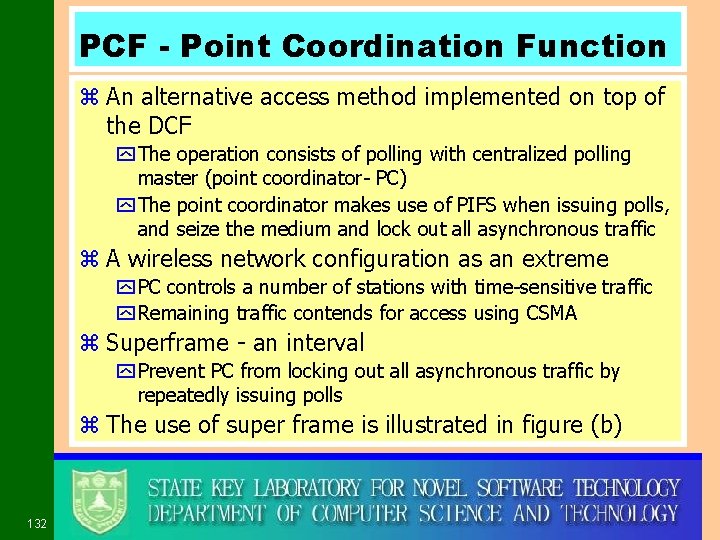
PCF - Point Coordination Function z An alternative access method implemented on top of the DCF y The operation consists of polling with centralized polling master (point coordinator- PC) y The point coordinator makes use of PIFS when issuing polls, and seize the medium and lock out all asynchronous traffic z A wireless network configuration as an extreme y PC controls a number of stations with time-sensitive traffic y Remaining traffic contends for access using CSMA z Superframe - an interval y Prevent PC from locking out all asynchronous traffic by repeatedly issuing polls z The use of super frame is illustrated in figure (b) 132
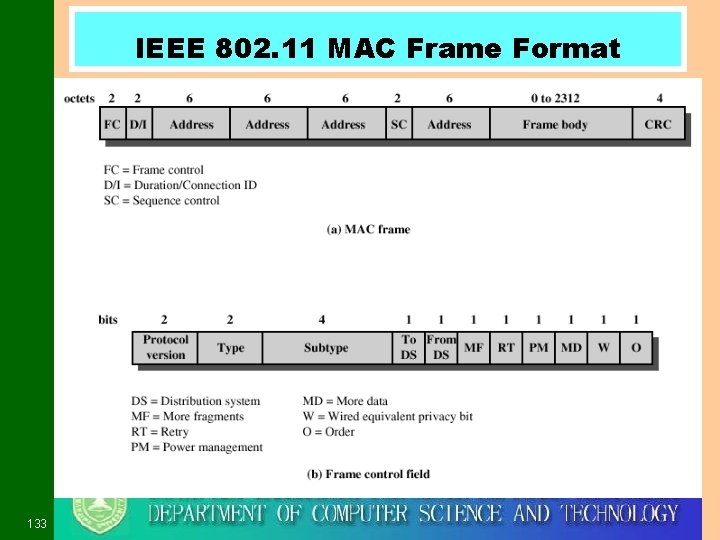
IEEE 802. 11 MAC Frame Format 133
Required Reading z Stallings, Data & Computer Communications, 6 e, Chapter 14 z Stallings, Local & Metropolitan Area Networks, 6 e, Chapter 7, 8, 9, 10 and 11 z Web sites on Ethernet, Token ring, FDDI, ATM etc. z Optional references y谢希仁,计机网络,第 3版,大连理 大学出版社, 第四章和第五章 y胡道元,计算机局域网,清华大学出版社,5. 3, 5. 4 和5. 6节 134
Exercises z Essential: 14. 7, 14. 10 z Optional: 14. 2 135
- Slides: 135