Tackling Exposed Node Problem in IEEE 802 11
Tackling Exposed Node Problem in IEEE 802. 11 Mac Deepanshu Shukla (01329004) Guide: Dr. Sridhar Iyer
Wireless LAN w. Physical layer impact n Impact of Interference range w. Hidden Terminal Problem w. Exposed Node

Physical Layer w Medium n Communicate over a medium significantly less reliable than wired PHYs. Medium is a scarce commodity n Lack full connectivity w Transmission n Have time-varying and asymmetric propagation properties n Due to propagation limits, collision may not be ‘sensed’ by some nodes w Fix Range n Have Carrier sense threshold and Receive threshold n If packet below receive threshold, it is marked as in error and passed to MAC. n Packets below carrier sense threshold are ignored by PHY layer
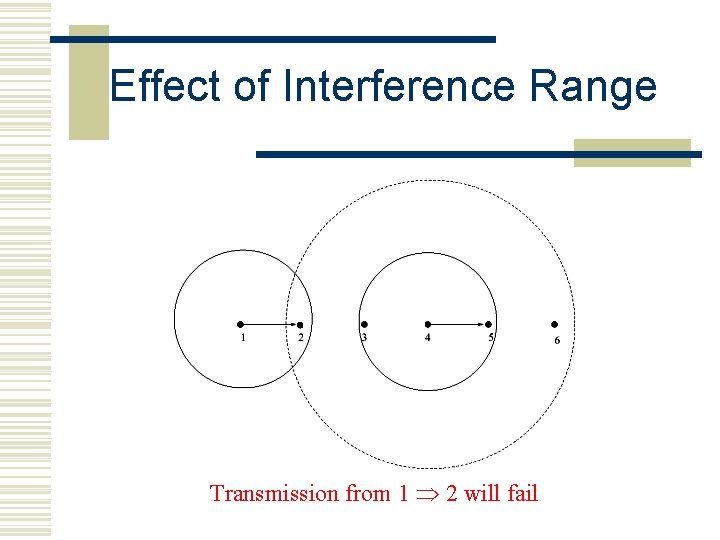
Effect of Interference Range Transmission from 1 2 will fail
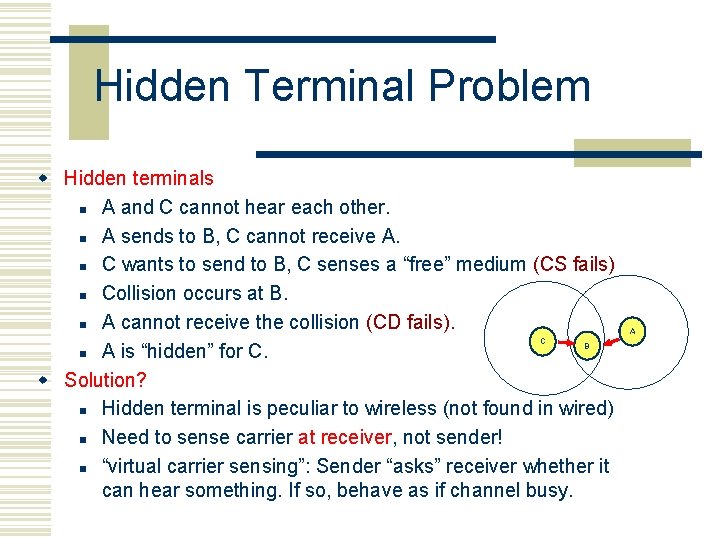
Hidden Terminal Problem w Hidden terminals n A and C cannot hear each other. n A sends to B, C cannot receive A. n C wants to send to B, C senses a “free” medium (CS fails) n Collision occurs at B. n A cannot receive the collision (CD fails). n A is “hidden” for C. w Solution? n Hidden terminal is peculiar to wireless (not found in wired) n Need to sense carrier at receiver, not sender! n “virtual carrier sensing”: Sender “asks” receiver whether it can hear something. If so, behave as if channel busy. C B A

Exposed Node Scenario
Exposed Terminal Problem w Exposed terminals n A starts sending to B. n S 1 senses carrier, finds medium in use and has to wait for A B to end. D is outside the range of A, therefore waiting is not necessary. n A and C are “exposed” terminals. w A->B and S 2 ->any. Node transmissions can be parallel; no collisions w NOT allowed under IEEE 802. 11 n Refer figure 3. 2
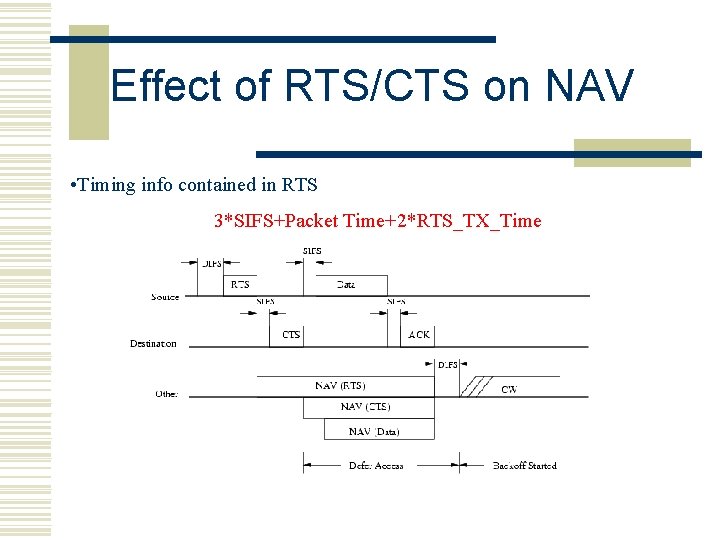
Effect of RTS/CTS on NAV • Timing info contained in RTS 3*SIFS+Packet Time+2*RTS_TX_Time

Proposed Solution w. Maintain neighborhood information w. Identify Exposed Node w. Process timing information w. Synchronize ACK w. Schedule DATA transmission

Identify Exposed Nodes w Node hears l RTS l corresponding DATA
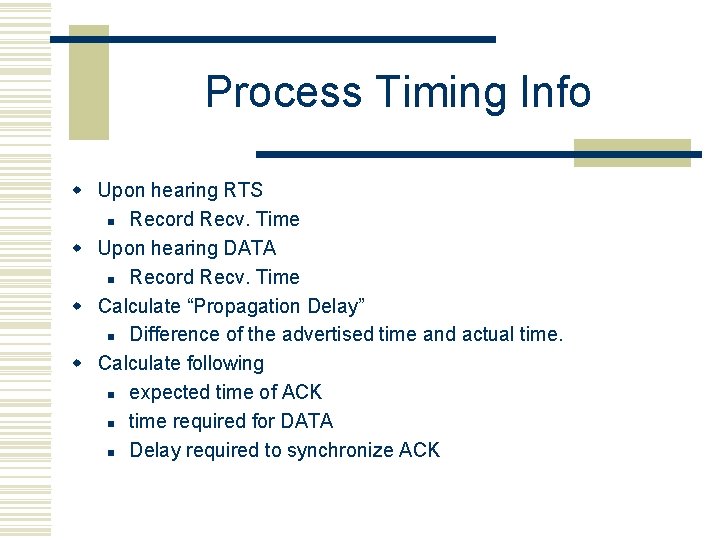
Process Timing Info w Upon hearing RTS n Record Recv. Time w Upon hearing DATA n Record Recv. Time w Calculate “Propagation Delay” n Difference of the advertised time and actual time. w Calculate following n expected time of ACK n time required for DATA n Delay required to synchronize ACK

Transmit DATA w Is Exposed Node? YES w Does network Layer has data? YES w Check the Size of DATA l Is it less than the ongoing data size? YES w Check the Destination of DATA l Is it Broadcast? NO l Addressed to already busy node? NO w Calculate the time of transmission of ACK (from RTS duration and propagation delay) w Schedule DATA packet transmission after the calculated delay

Modification to packets w RTS n Requires no change w CTS / ACK n IEEE 802. 11 CTS does not have TA (Transmitter's Address) n Added to maintain neighborhood information w DATA n Add “is. Exposed ”, 1 - bit flag n No such bit in IEEE 802. 11

Simulation Topologies 4 -6 -8 Node, single hop 5 Node, multi hop

Simulation Results Multi hop Scenario – 5 Nodes Single hop Scenario – 6 Nodes
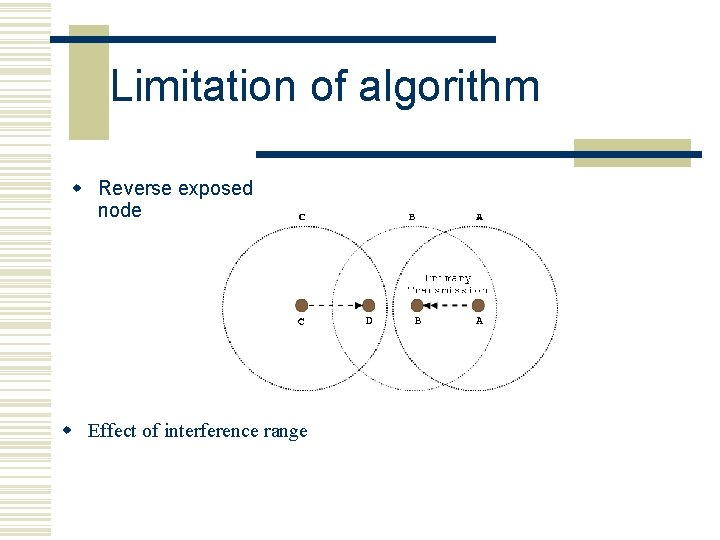
Limitation of algorithm w Reverse exposed node w Effect of interference range
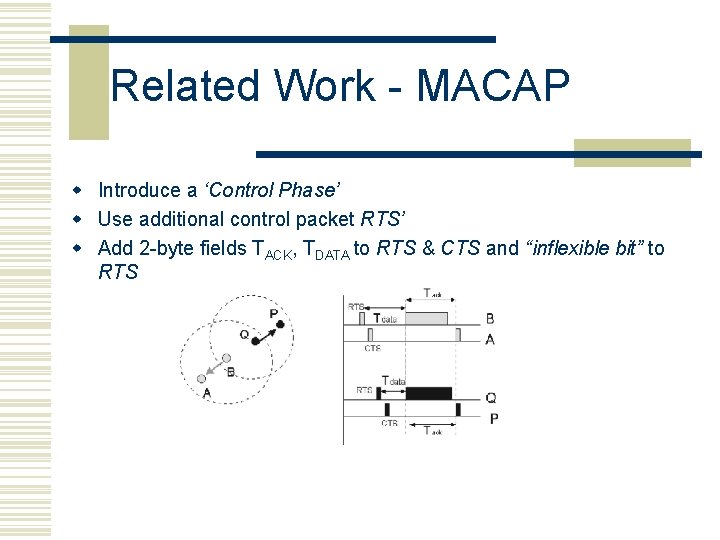
Related Work - MACAP w Introduce a ‘Control Phase’ w Use additional control packet RTS’ w Add 2 -byte fields TACK, TDATA to RTS & CTS and “inflexible bit” to RTS
Conclusion w Exposed nodes play a major role bandwidth underutilization, especially in case of multi hop scenario, as shown by the performance increase. w The Medium lays down various constraints and coming up with optimum PHY layer parameters is important. w The increase in performance is substantial to further investigate this problem in case of “Reverse Exposed” nodes

Thank you.
- Slides: 19