Data Link Layer Two sublayer Medium access sublayer
Data Link Layer Two sublayer: – Medium access sublayer (MAC) – Logical link control (LLC) 1
Data Link Layer • LANs -- Referred to as: – Multiaccess channels – Random access channels • LANs Characterized by: – – Data rate of at least several Mbps Low error rates A diameter of not more than a few kilometers Complete ownership by a single organization 2
Networks Two types • Point-to-Point e. g. , WANs • Broadcast e. g. , Packet radio, Satellite LANs Note: In between LANs and WANs are MANs. 3
Channel Allocation in LANs and MANs • Static e. g. , FDM • Dynamic e. g. , Slotted time, Carrier sense Note: MANs use LANs Technology. 4
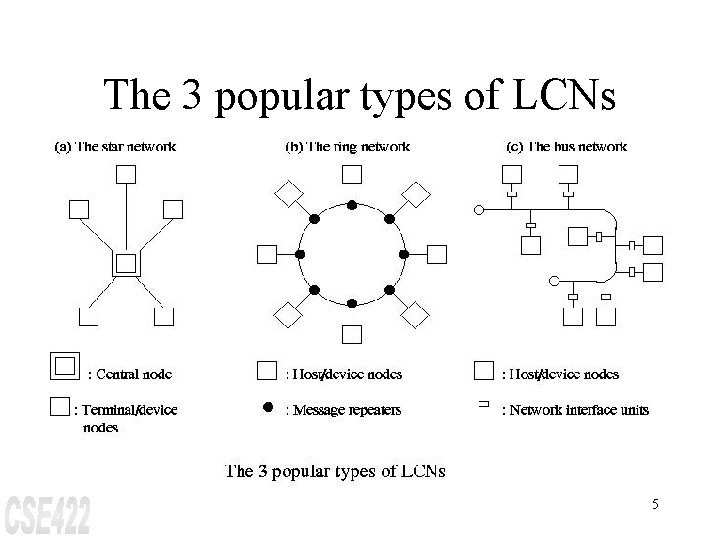
The 3 popular types of LCNs 5
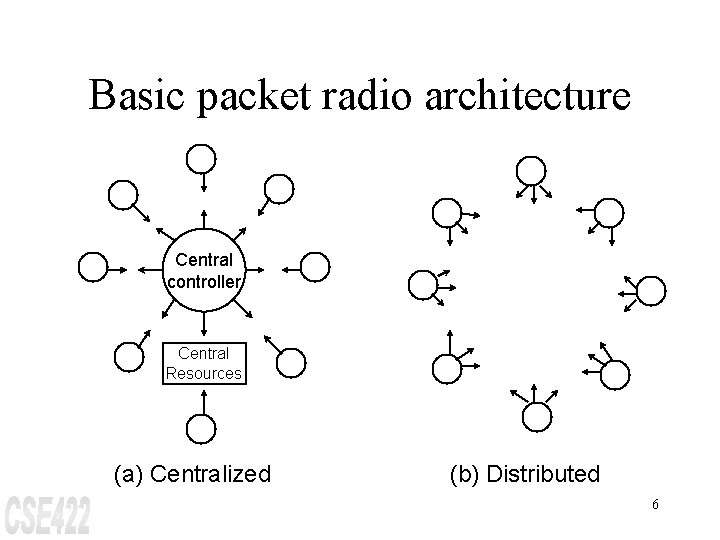
Basic packet radio architecture Central controller Central Resources (a) Centralized (b) Distributed 6
ALOHA A medium access control technique for multiple access transmission media. – Pure ALOHA -- a station transmits whenever it has data to send. Unacknowledged transmissions are repeated. Notation for analysis: – – S: Throughput of the network G: Total rate of data presented I: Total Rate of data generated by the stations (input load) D: Average delay between the time a packet is ready for transmission and the completion of successful transmission. 7
ALOHA (cont. ) Assumptions: 1. All packets are of constant length 2. The channel is noise-free 3. Packets do not queue at individual stations (i. e. , I=S) 4. G is Poisson distributed 8
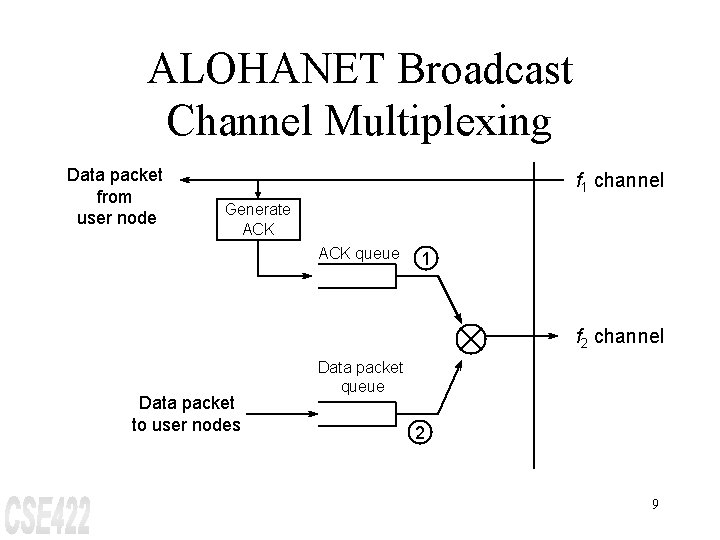
ALOHANET Broadcast Channel Multiplexing Data packet from user node f 1 channel Generate ACK queue 1 f 2 channel Data packet to user nodes Data packet queue 2 9
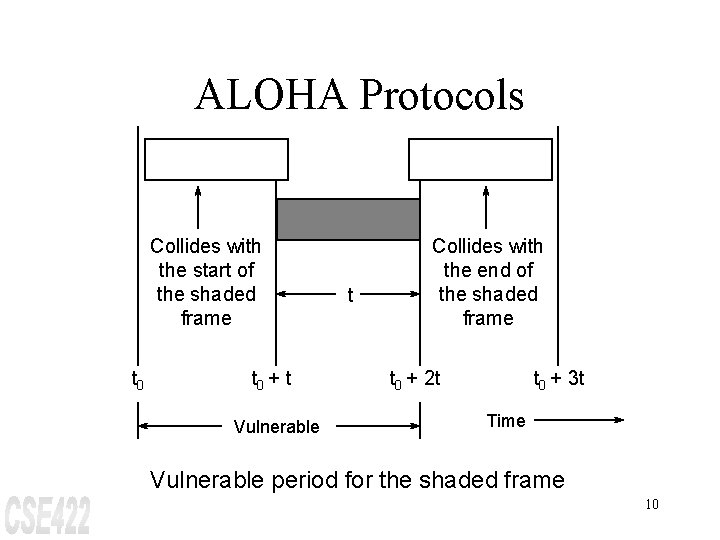
ALOHA Protocols Collides with the start of the shaded frame t 0 + t Vulnerable t Collides with the end of the shaded frame t 0 + 2 t t 0 + 3 t Time Vulnerable period for the shaded frame 10
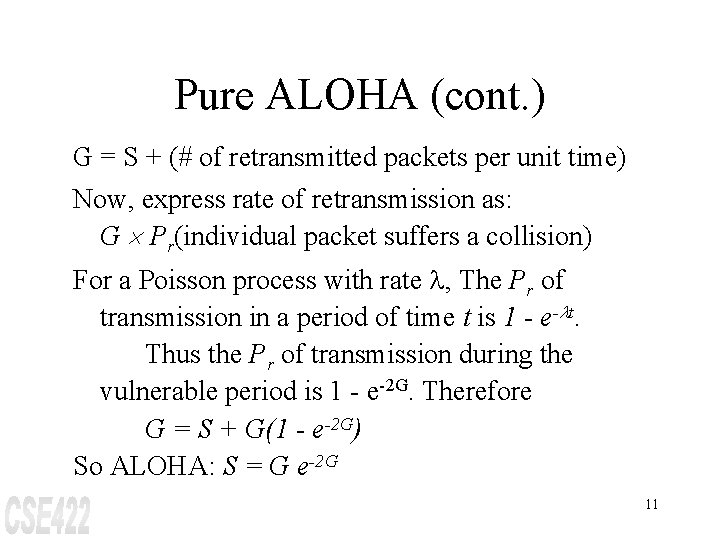
Pure ALOHA (cont. ) G = S + (# of retransmitted packets per unit time) Now, express rate of retransmission as: G ´ Pr(individual packet suffers a collision) For a Poisson process with rate l, The Pr of transmission in a period of time t is 1 - e-lt. Thus the Pr of transmission during the vulnerable period is 1 - e-2 G. Therefore G = S + G(1 - e-2 G) So ALOHA: S = G e-2 G 11
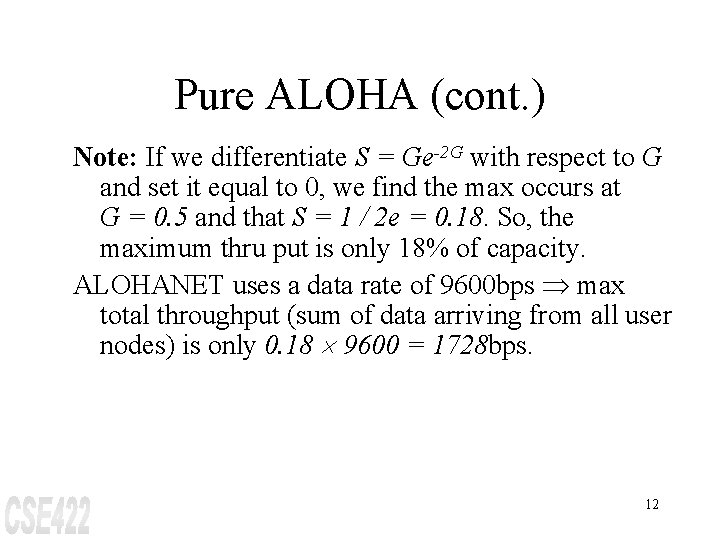
Pure ALOHA (cont. ) Note: If we differentiate S = Ge-2 G with respect to G and set it equal to 0, we find the max occurs at G = 0. 5 and that S = 1 / 2 e = 0. 18. So, the maximum thru put is only 18% of capacity. ALOHANET uses a data rate of 9600 bps Þ max total throughput (sum of data arriving from all user nodes) is only 0. 18 ´ 9600 = 1728 bps. 12
Slotted ALOHA Channel is organized into uniform slots whose size equals the packet transmission time. Transmission is permitted only to begin at a slot boundary. Note: Since the vulnerable period is now reduced in half, the Pr of transmission during this period is 1 - e-G; thus we have S-ALOHA: S = Ge-G Now, differentiating with respect to G, we have the max possible value for S is 1 / e = 0. 37 or 37%. 13
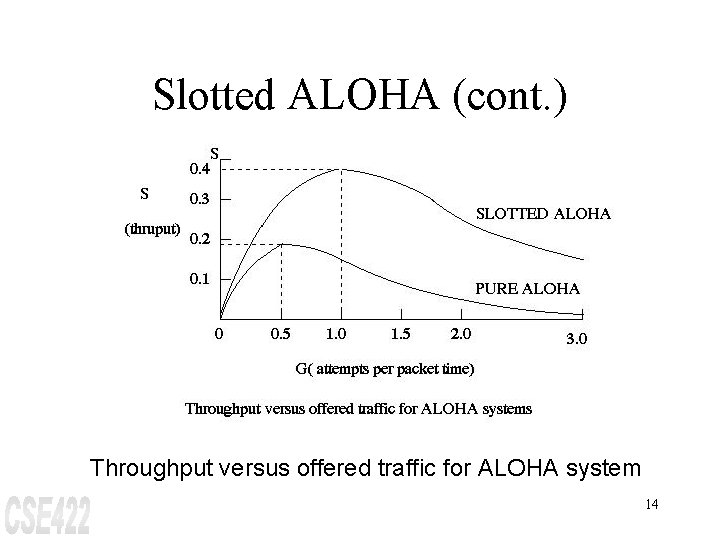
Slotted ALOHA (cont. ) Throughput versus offered traffic for ALOHA system 14
Delay (approx) Time interval from when a user is ready to transmit a packet until when it is successfully received by the central node. Simply the sum of queuing delay, propagation delay, and transmission time. Note: ALOHA has queueing delay = 0. So, we need to view queueing time in the context of above definition for delay. 15
Delay (approx) (cont. ) Expected # of transmissions per packet º G / S Þ Expected # of retransmissions per packet º G / S -1 G / S - 1 = e 2 G - 1 so D = (e 2 G - 1) d + a + 1, where d is the average delay for one retransmission ALOHA: D = (e 2 G - 1)(1 + 2 a + w + (K+1)/2) + a + 1 Note: Assume no collision for w 16
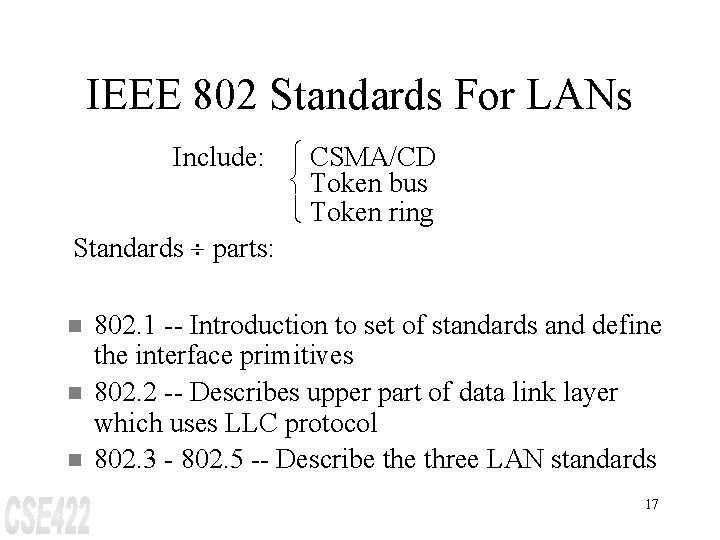
IEEE 802 Standards For LANs Include: ì CSMA/CD í Token bus î Token ring Standards ¸ parts: n n n 802. 1 -- Introduction to set of standards and define the interface primitives 802. 2 -- Describes upper part of data link layer which uses LLC protocol 802. 3 - 802. 5 -- Describe three LAN standards 17
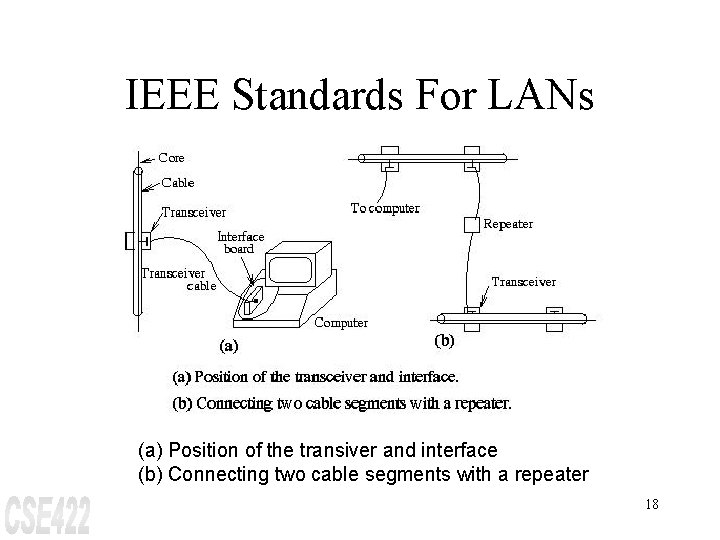
IEEE Standards For LANs (a) Position of the transiver and interface (b) Connecting two cable segments with a repeater 18
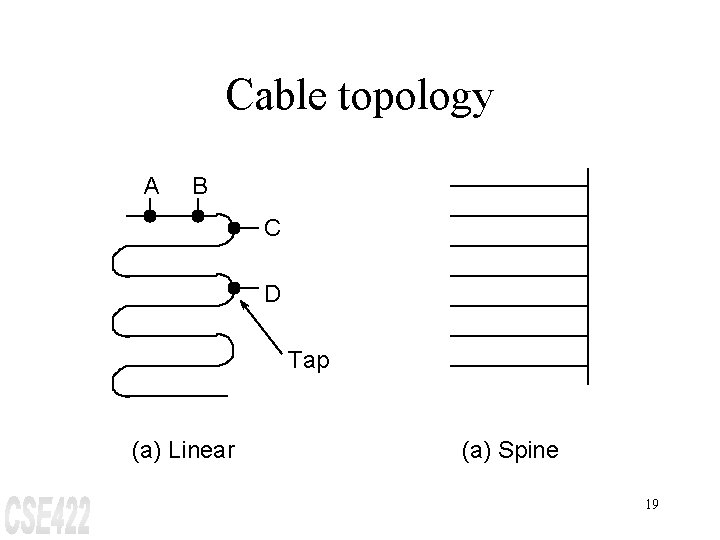
Cable topology A B C D Tap (a) Linear (a) Spine 19
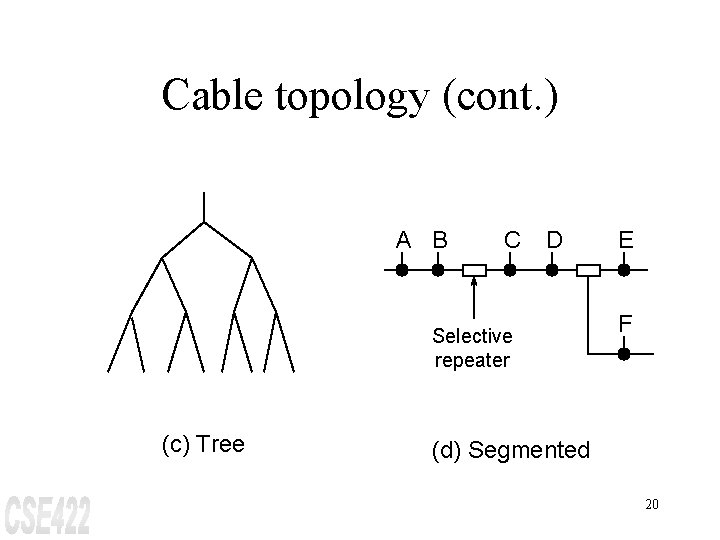
Cable topology (cont. ) A B C D Selective repeater (c) Tree E F (d) Segmented 20
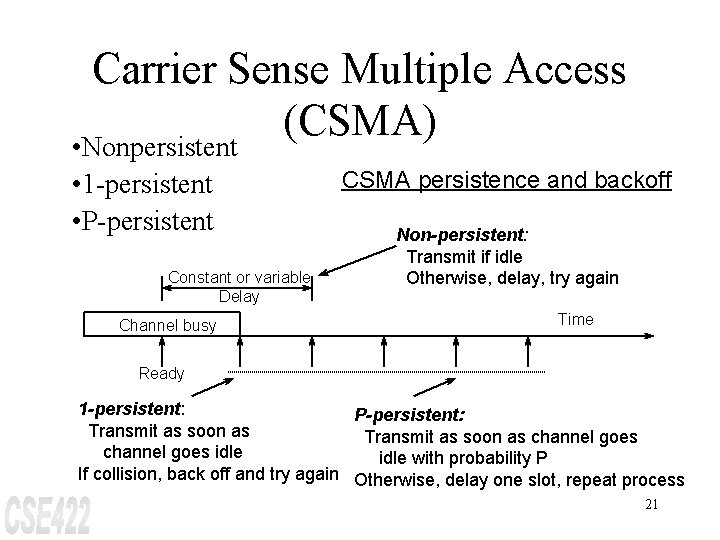
Carrier Sense Multiple Access (CSMA) • Nonpersistent • 1 -persistent • P-persistent Constant or variable Delay Channel busy CSMA persistence and backoff Non-persistent: Transmit if idle Otherwise, delay, try again Time Ready 1 -persistent: P-persistent: Transmit as soon as channel goes idle with probability P If collision, back off and try again Otherwise, delay one slot, repeat process 21
CSMA/CD Physical Layer Current Standard Baseband coaxial cable (50 W) 500 M segments, 100 Taps/segment Maximum 4 repeaters in path 10 Mbps Similar to Ethernet 22
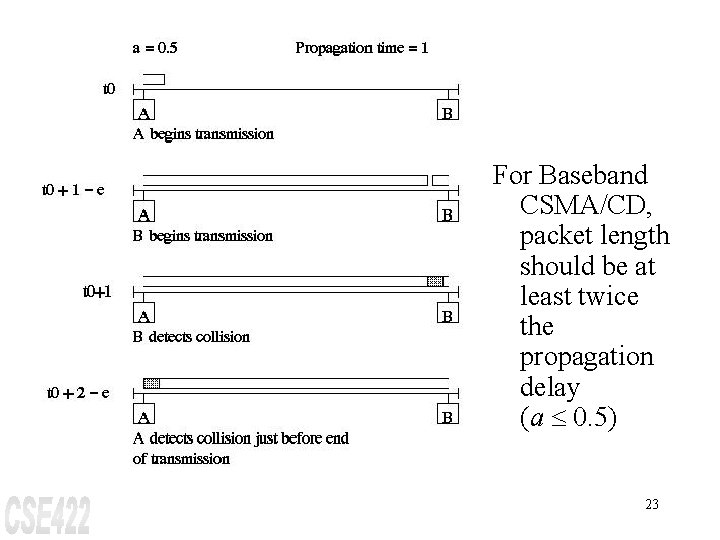
For Baseband CSMA/CD, packet length should be at least twice the propagation delay (a £ 0. 5) 23
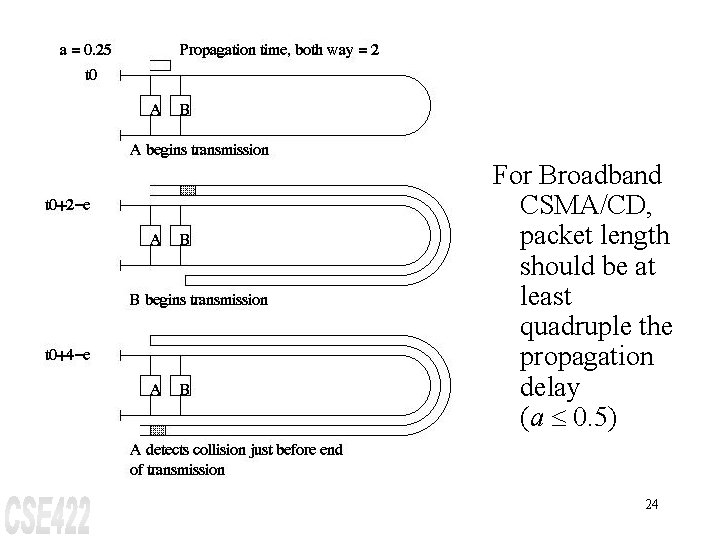
For Broadband CSMA/CD, packet length should be at least quadruple the propagation delay (a £ 0. 5) 24
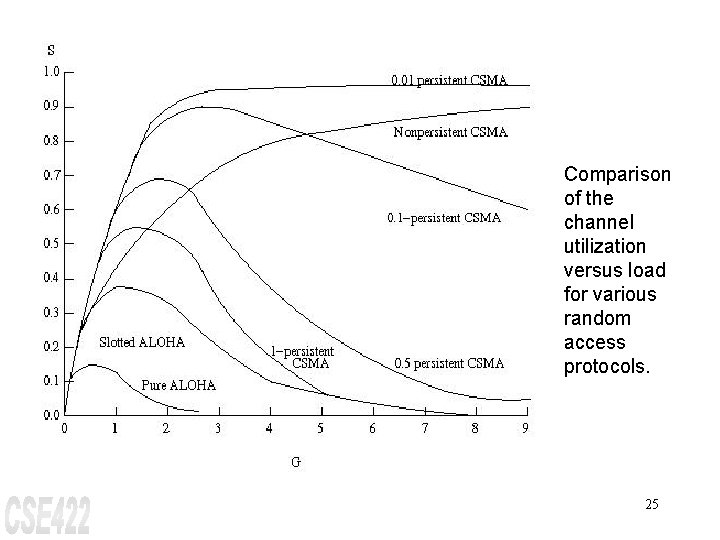
Comparison of the channel utilization versus load for various random access protocols. 25
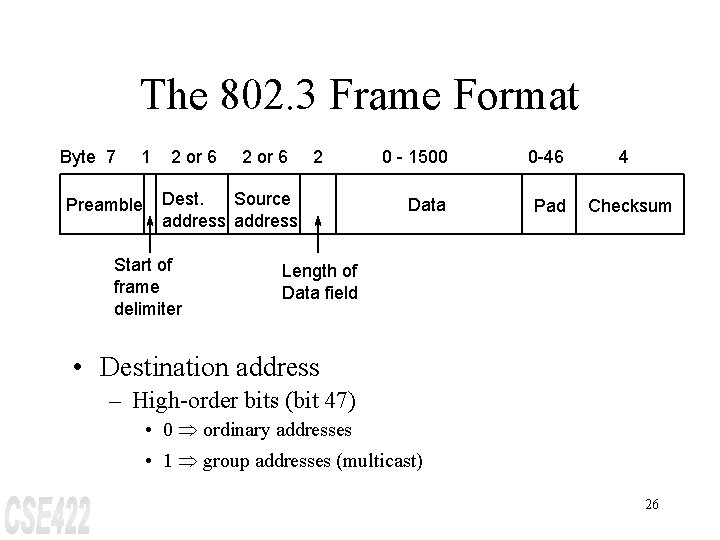
The 802. 3 Frame Format Byte 7 1 Preamble 2 or 6 2 Dest. Source address Start of frame delimiter 0 - 1500 0 -46 Data Pad 4 Checksum Length of Data field • Destination address – High-order bits (bit 47) • 0 Þ ordinary addresses • 1 Þ group addresses (multicast) 26
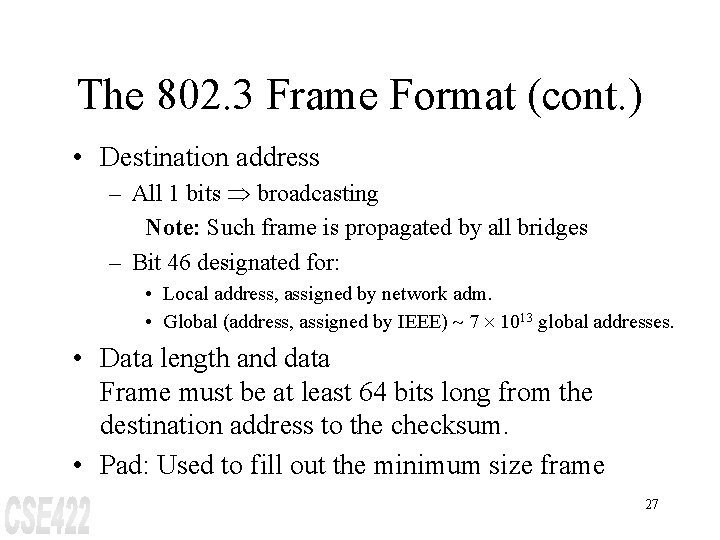
The 802. 3 Frame Format (cont. ) • Destination address – All 1 bits Þ broadcasting Note: Such frame is propagated by all bridges – Bit 46 designated for: • Local address, assigned by network adm. • Global (address, assigned by IEEE) ~ 7 ´ 1013 global addresses. • Data length and data Frame must be at least 64 bits long from the destination address to the checksum. • Pad: Used to fill out the minimum size frame 27
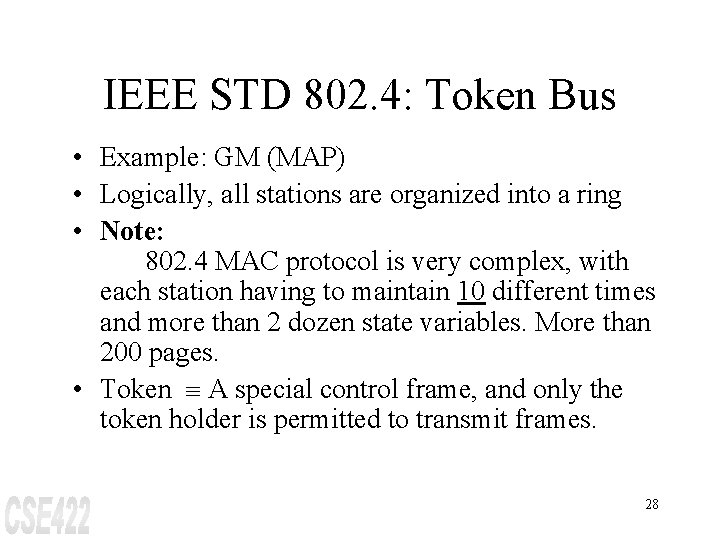
IEEE STD 802. 4: Token Bus • Example: GM (MAP) • Logically, all stations are organized into a ring • Note: 802. 4 MAC protocol is very complex, with each station having to maintain 10 different times and more than 2 dozen state variables. More than 200 pages. • Token º A special control frame, and only the token holder is permitted to transmit frames. 28
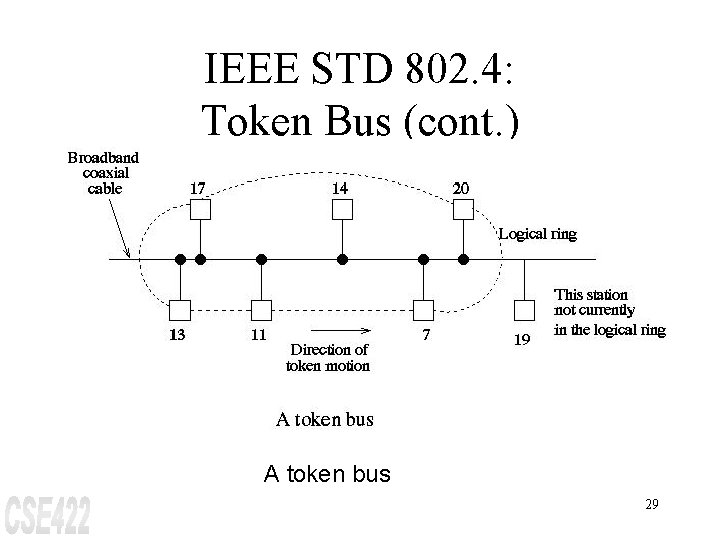
IEEE STD 802. 4: Token Bus (cont. ) A token bus 29
Token Bus MAC Sublayer Protocol • Stations are inserted into ring in order of station address, from highest to lowest. • Token passing is also done from high to low addresses. • Four priority classes: (0, 2, 4, 6) for traffic, with 0 the lowest and 6 the highest. When the token comes into the station, it passes to priority 6 substation, which may begin transmitting frames, if it has any. When it is done, (or when its timer expires), the token is passed to the priority 4 substations, etc. 30
Token Bus Priority Scheme 31
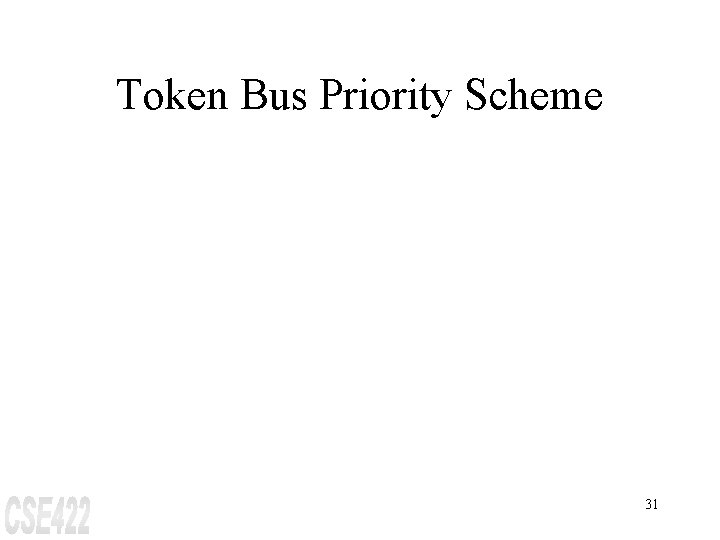
Ring Maintenance Frame control field Name 00000001 00000010 00000011 00000100 Claim_token Solicit_successor_1 Solicit_successor_2 Who_follows Resolve_contention 00001000 00001100 Token Set_successor Meaning Claim token during initialization Allows stations to enter the ring Recover from lost token Used when multiple stations want to enter the ring Pass the token Allows stations to leave the ring The token bus control frames 32
Logical Ring Maintenance Adding a station • Each station's interface must maintain address of predecessor and successor stations. • Periodically, the token holder solicits bids from stations not currently in the ring and wish to join. • Resolve contention -- token holder runs an arbitration algorithm when 2 or more stations bid to enter. All station interfaces maintain 2 random bits which are used to delay all bids by 0, 1, 2, or 3 slot times. 33
Logical Ring Maintenance (cont. ) Deleting a station • A station, X, with successor S, and predecessor P, leaves the ring by sending P a set_successor frame. Initialization • Special case of adding new station. When first station comes on line, it notices that there is no traffic for a certain time period. Then it sends a claim_token frame, and later solicit bids from stations to join. 34
Failure (Stations) If a station tries to pass the token to a failed station, it listens to see if the station either transmits a frame or passes the token. If it does neither, the token is passed a second time. If that also fails, the station transmits a who_follows, specifying the address of its successor. If this fails, the station sends a solicit_successor_2 frame, etc. 35
Failure (Stations) (cont. ) Token failure • Use the ring initialization algorithm. Each station has a timer that is reset whenever a frame appears on the network. When timer hits a threshold value, the station issues a claim_token. Multiple tokens • If a station holding the token notices a transmission from another station, it discards its token. 36
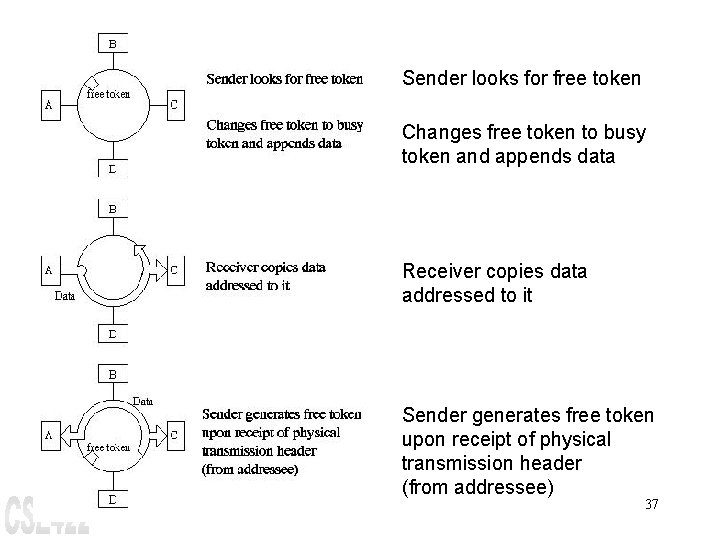
Sender looks for free token Changes free token to busy token and appends data Receiver copies data addressed to it Sender generates free token upon receipt of physical transmission header (from addressee) 37
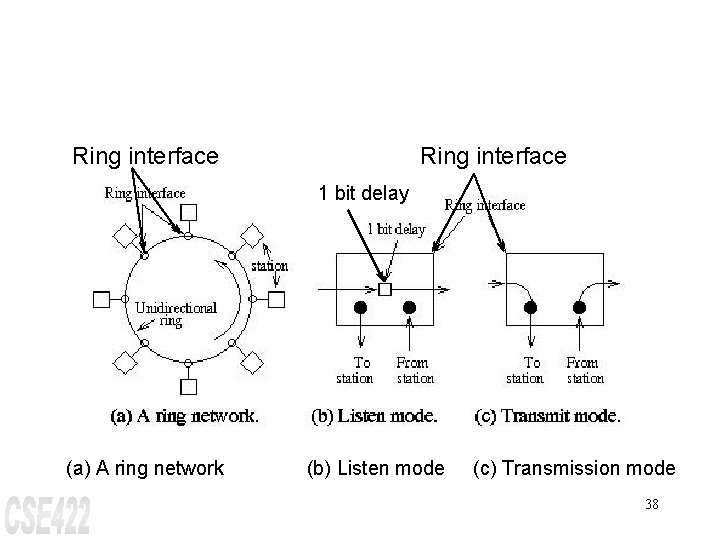
Ring interface 1 bit delay (a) A ring network (b) Listen mode (c) Transmission mode 38
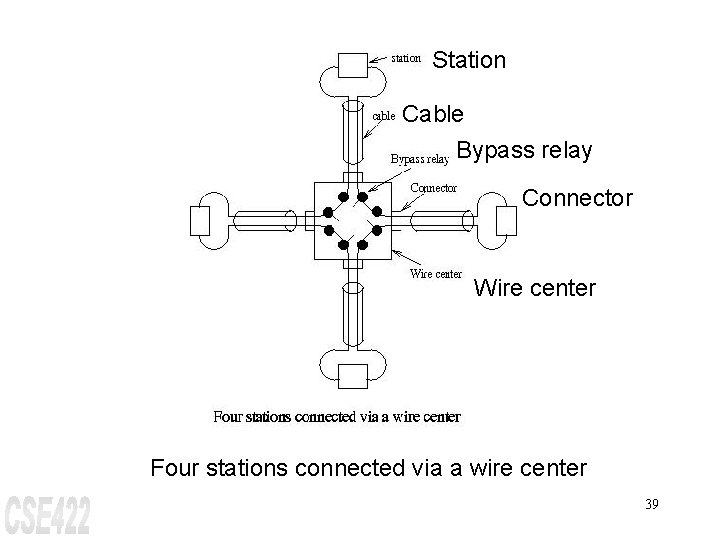
Station Cable Bypass relay Connector Wire center Four stations connected via a wire center 39
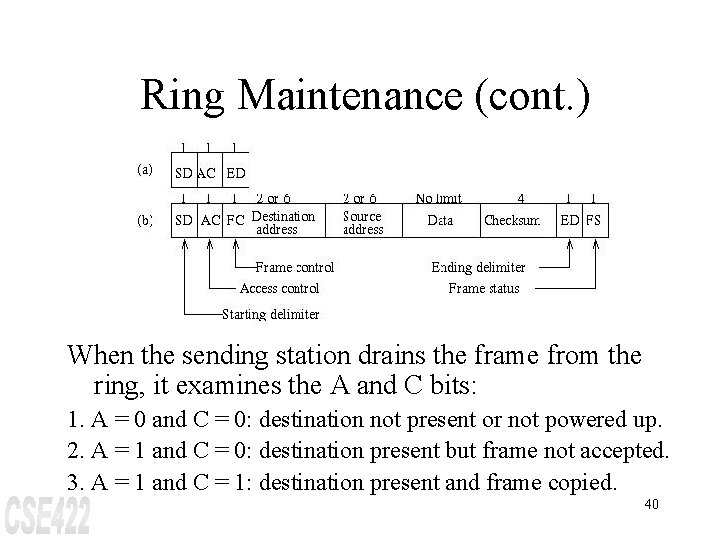
Ring Maintenance (cont. ) When the sending station drains the frame from the ring, it examines the A and C bits: 1. A = 0 and C = 0: destination not present or not powered up. 2. A = 1 and C = 0: destination present but frame not accepted. 3. A = 1 and C = 1: destination present and frame copied. 40
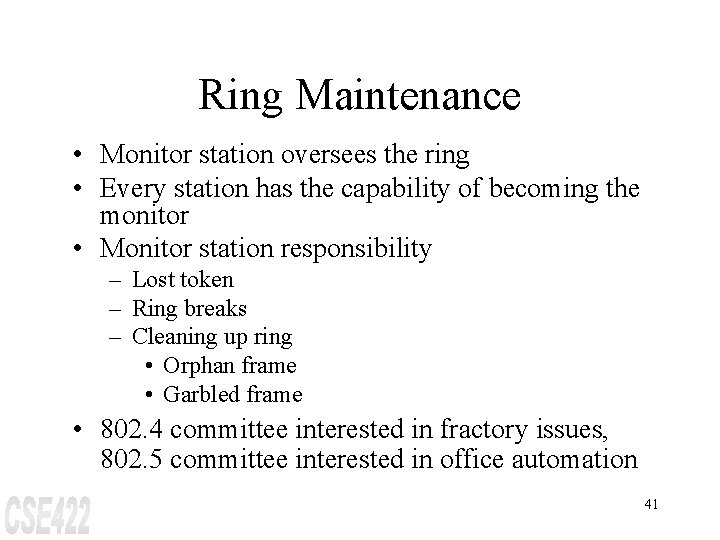
Ring Maintenance • Monitor station oversees the ring • Every station has the capability of becoming the monitor • Monitor station responsibility – Lost token – Ring breaks – Cleaning up ring • Orphan frame • Garbled frame • 802. 4 committee interested in fractory issues, 802. 5 committee interested in office automation 41
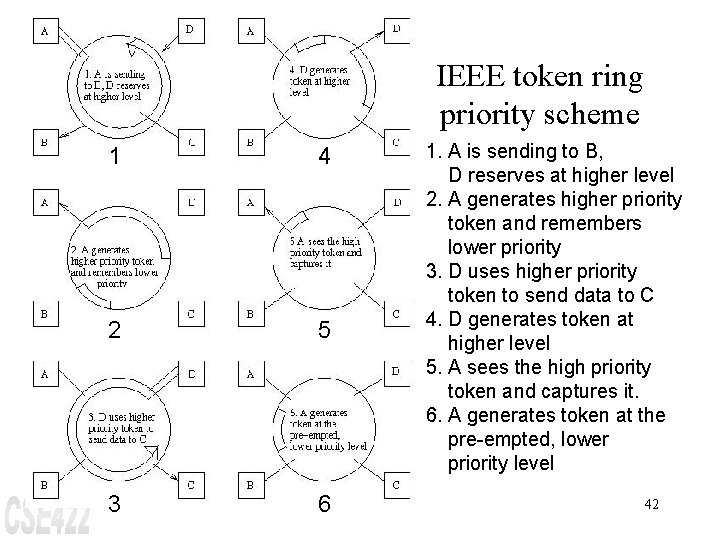
IEEE token ring priority scheme 1 4 2 5 3 6 1. A is sending to B, D reserves at higher level 2. A generates higher priority token and remembers lower priority 3. D uses higher priority token to send data to C 4. D generates token at higher level 5. A sees the high priority token and captures it. 6. A generates token at the pre-empted, lower priority level 42
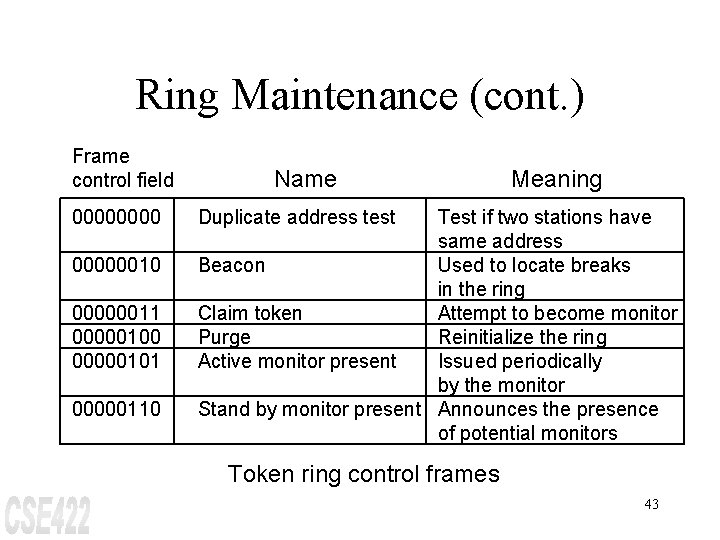
Ring Maintenance (cont. ) Frame control field 00000010 00000011 00000100 00000101 00000110 Name Meaning Duplicate address test Test if two stations have same address Beacon Used to locate breaks in the ring Claim token Attempt to become monitor Purge Reinitialize the ring Active monitor present Issued periodically by the monitor Stand by monitor present Announces the presence of potential monitors Token ring control frames 43
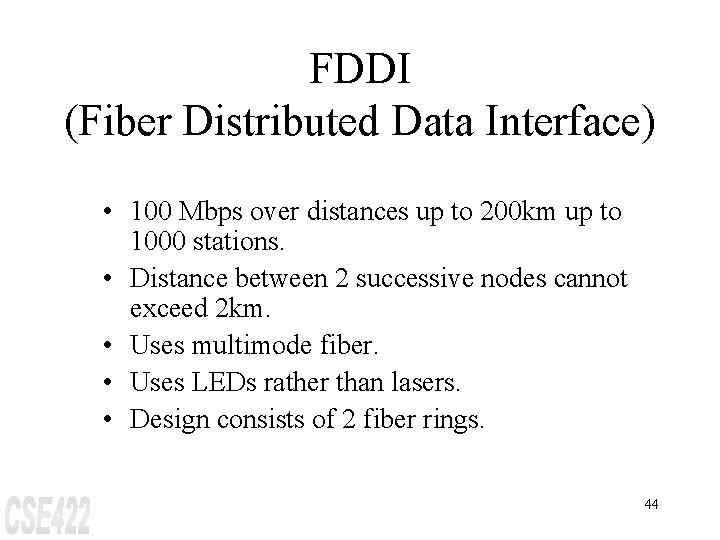
FDDI (Fiber Distributed Data Interface) • 100 Mbps over distances up to 200 km up to 1000 stations. • Distance between 2 successive nodes cannot exceed 2 km. • Uses multimode fiber. • Uses LEDs rather than lasers. • Design consists of 2 fiber rings. 44
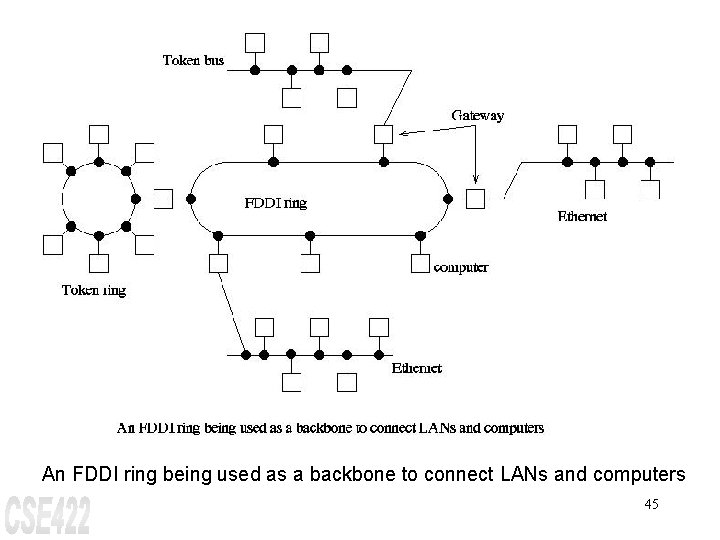
An FDDI ring being used as a backbone to connect LANs and computers 45
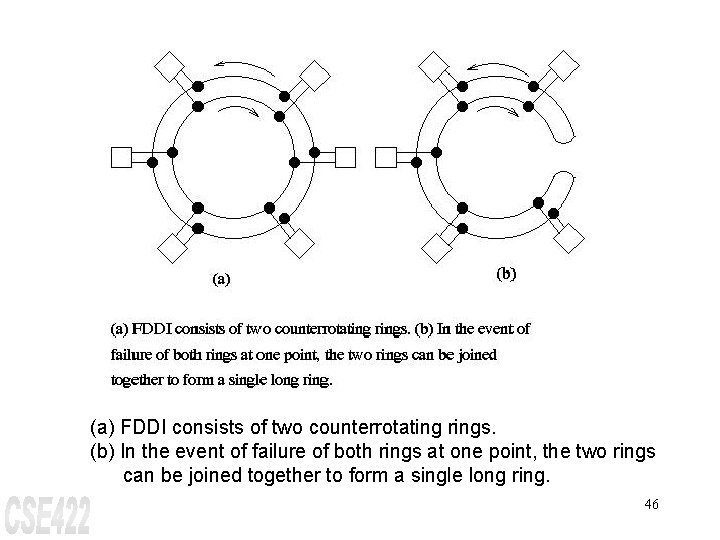
(a) FDDI consists of two counterrotating rings. (b) In the event of failure of both rings at one point, the two rings can be joined together to form a single long ring. 46
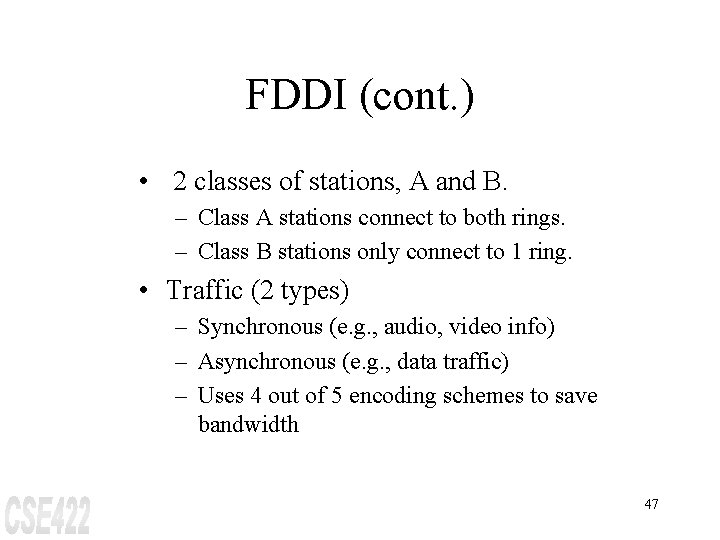
FDDI (cont. ) • 2 classes of stations, A and B. – Class A stations connect to both rings. – Class B stations only connect to 1 ring. • Traffic (2 types) – Synchronous (e. g. , audio, video info) – Asynchronous (e. g. , data traffic) – Uses 4 out of 5 encoding schemes to save bandwidth 47
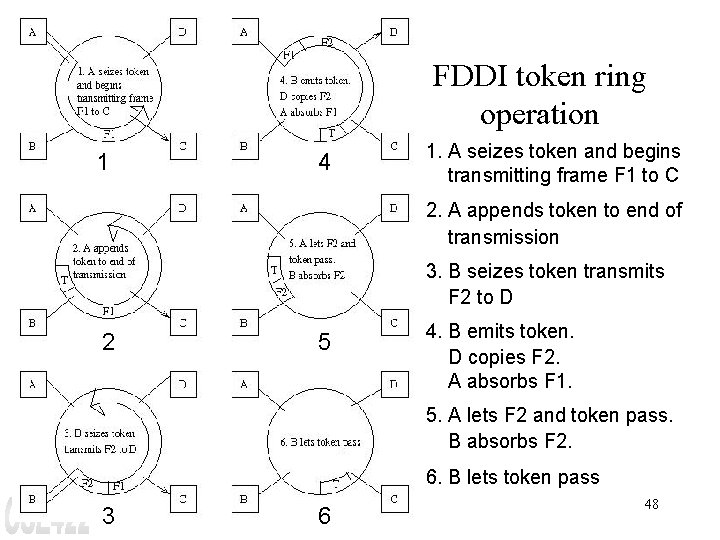
FDDI token ring operation 1 4 1. A seizes token and begins transmitting frame F 1 to C 2. A appends token to end of transmission 3. B seizes token transmits F 2 to D 2 5 4. B emits token. D copies F 2. A absorbs F 1. 5. A lets F 2 and token pass. B absorbs F 2. 6. B lets token pass 3 6 48
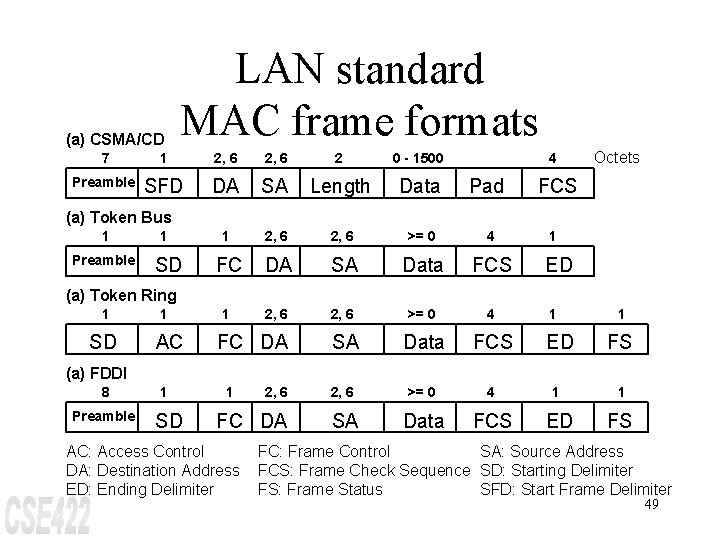
(a) CSMA/CD LAN standard MAC frame formats 4 Octets 7 1 2, 6 2 0 - 1500 Preamble SFD DA SA Length Data Pad 1 2, 6 >= 0 4 FC DA SA Data FCS 1 2, 6 >= 0 4 SA Data FCS ED FS 2, 6 >= 0 4 1 1 SA Data FCS ED FS FCS (a) Token Bus 1 Preamble 1 SD 1 ED (a) Token Ring 1 SD 1 AC FC DA 1 1 (a) FDDI 8 Preamble 1 SD 1 2, 6 FC DA AC: Access Control DA: Destination Address ED: Ending Delimiter FC: Frame Control SA: Source Address FCS: Frame Check Sequence SD: Starting Delimiter FS: Frame Status SFD: Start Frame Delimiter 49
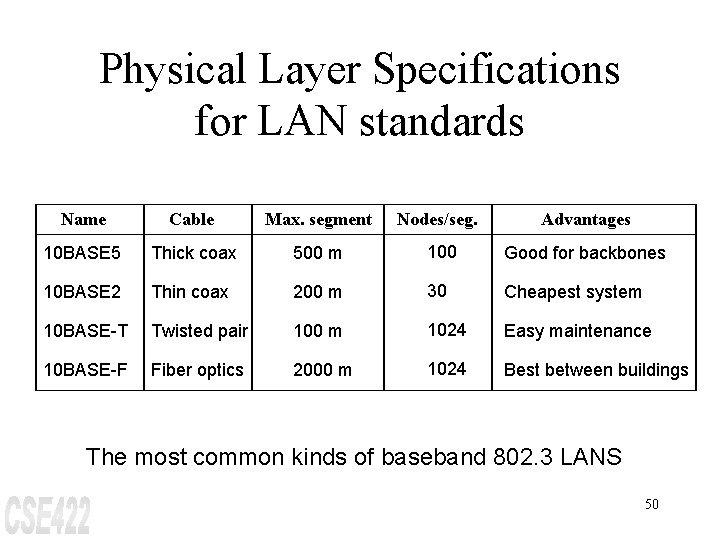
Physical Layer Specifications for LAN standards Name Cable Max. segment Nodes/seg. Advantages 10 BASE 5 Thick coax 500 m 100 Good for backbones 10 BASE 2 Thin coax 200 m 30 Cheapest system 10 BASE-T Twisted pair 100 m 1024 Easy maintenance 10 BASE-F Fiber optics 2000 m 1024 Best between buildings The most common kinds of baseband 802. 3 LANS 50
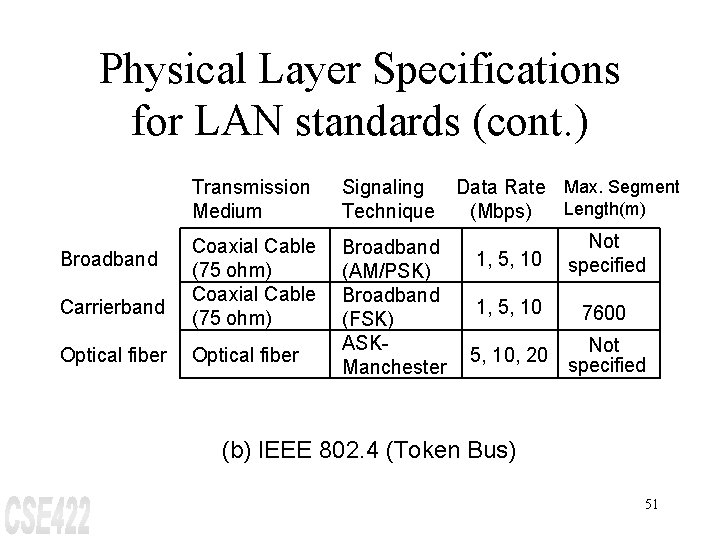
Physical Layer Specifications for LAN standards (cont. ) Transmission Medium Broadband Carrierband Optical fiber Coaxial Cable (75 ohm) Optical fiber Signaling Technique Data Rate Max. Segment Length(m) (Mbps) Not Broadband 1, 5, 10 specified (AM/PSK) Broadband 1, 5, 10 7600 (FSK) ASKNot 5, 10, 20 specified Manchester (b) IEEE 802. 4 (Token Bus) 51
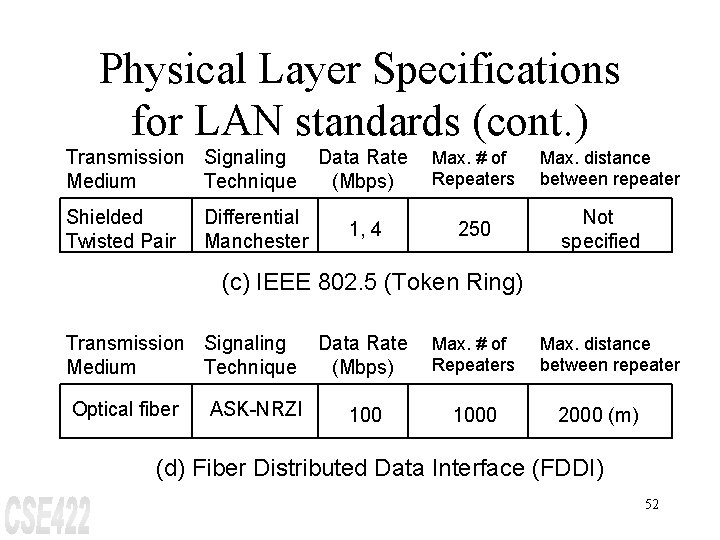
Physical Layer Specifications for LAN standards (cont. ) Transmission Signaling Medium Technique Shielded Twisted Pair Differential Manchester Data Rate (Mbps) Max. # of Repeaters 1, 4 250 Max. distance between repeater Not specified (c) IEEE 802. 5 (Token Ring) Transmission Signaling Medium Technique Optical fiber ASK-NRZI Data Rate (Mbps) Max. # of Repeaters 1000 Max. distance between repeater 2000 (m) (d) Fiber Distributed Data Interface (FDDI) 52
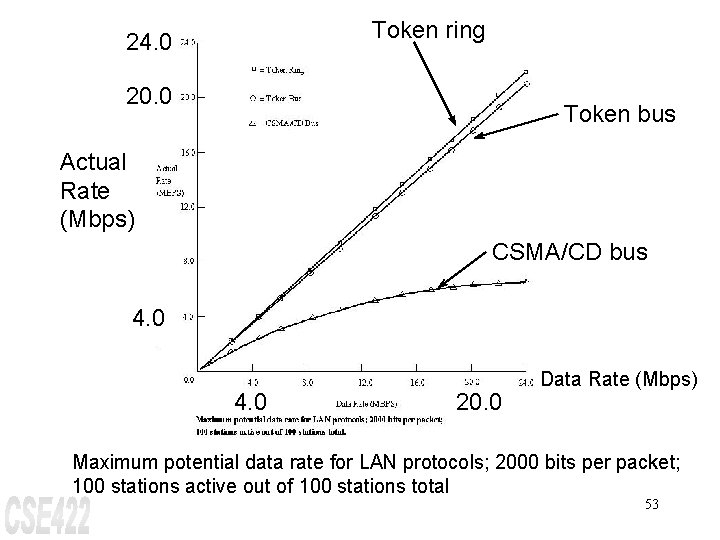
Token ring 24. 0 20. 0 Token bus Actual Rate (Mbps) CSMA/CD bus 4. 0 20. 0 Data Rate (Mbps) Maximum potential data rate for LAN protocols; 2000 bits per packet; 100 stations active out of 100 stations total 53
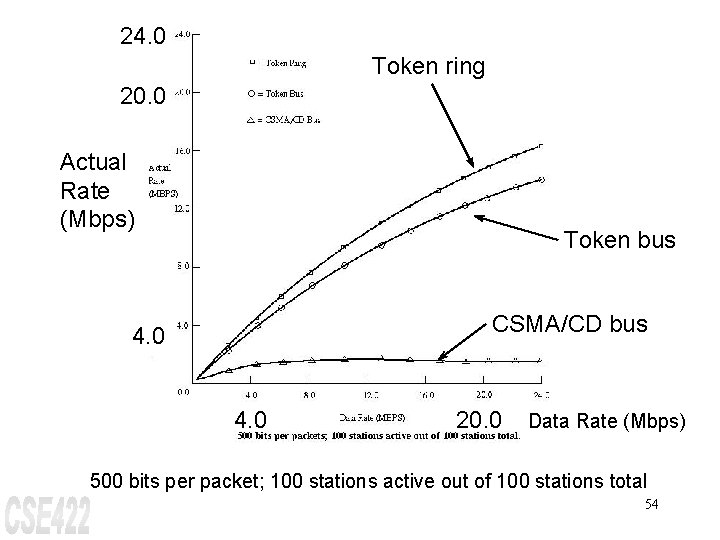
24. 0 Token ring 20. 0 Actual Rate (Mbps) Token bus CSMA/CD bus 4. 0 20. 0 Data Rate (Mbps) 500 bits per packet; 100 stations active out of 100 stations total 54
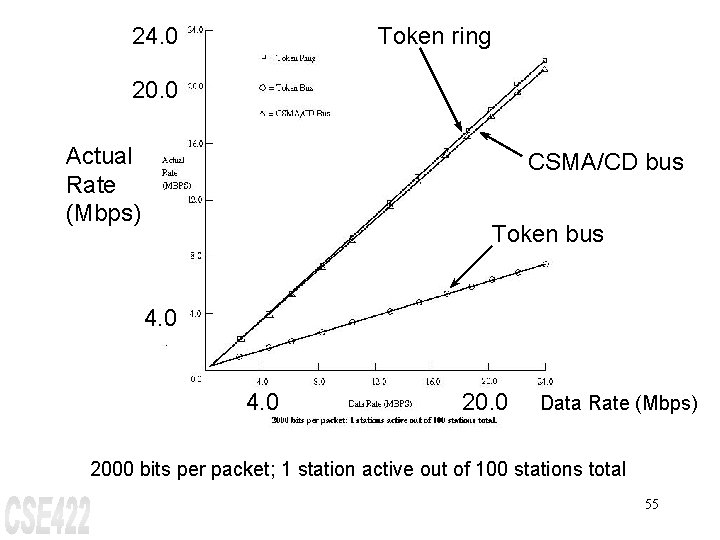
24. 0 Token ring 20. 0 Actual Rate (Mbps) CSMA/CD bus Token bus 4. 0 20. 0 Data Rate (Mbps) 2000 bits per packet; 1 station active out of 100 stations total 55
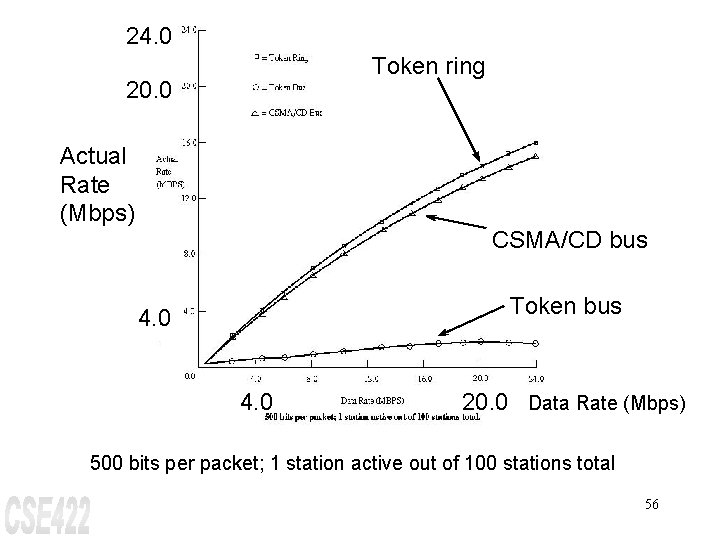
24. 0 Token ring 20. 0 Actual Rate (Mbps) CSMA/CD bus Token bus 4. 0 20. 0 Data Rate (Mbps) 500 bits per packet; 1 station active out of 100 stations total 56
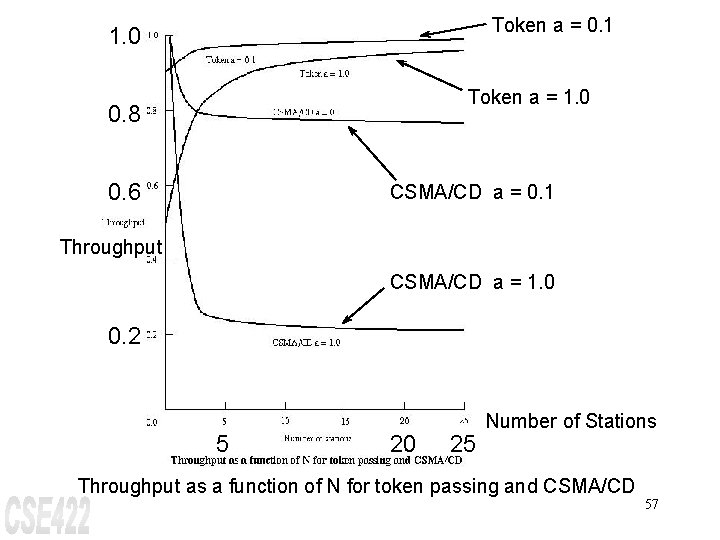
Token a = 0. 1 1. 0 Token a = 1. 0 0. 8 0. 6 CSMA/CD a = 0. 1 Throughput CSMA/CD a = 1. 0 0. 2 5 20 25 Number of Stations Throughput as a function of N for token passing and CSMA/CD 57
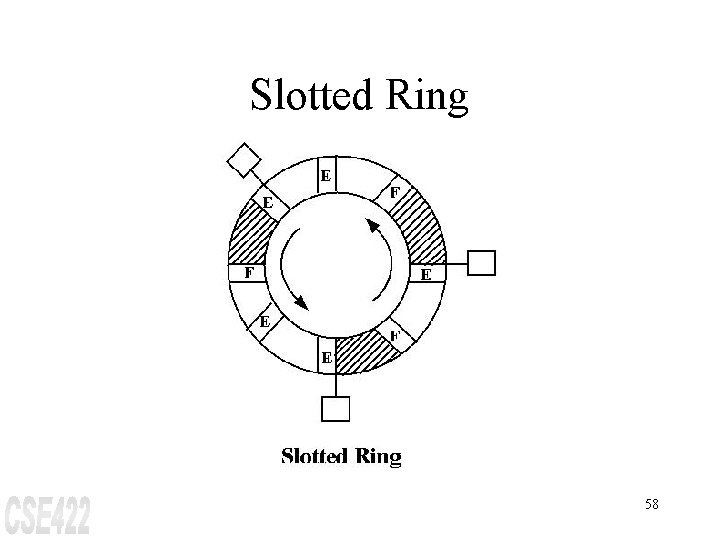
Slotted Ring 58
Medium Access Control Protocols in Wireless Networks • CSMA • 802. 11
MAC Protocols: Issues in Wireless Networks • • • Hidden Terminal Problem Reliability Collision avoidance Congestion control Fairness Energy efficiency
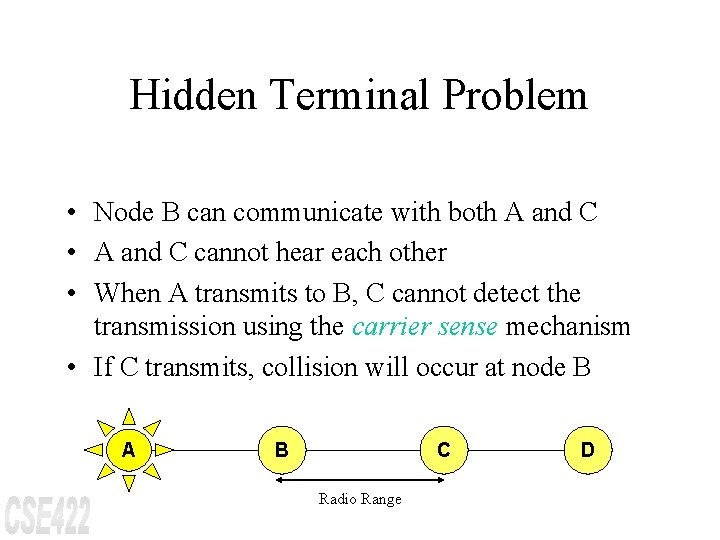
Hidden Terminal Problem • Node B can communicate with both A and C • A and C cannot hear each other • When A transmits to B, C cannot detect the transmission using the carrier sense mechanism • If C transmits, collision will occur at node B A B C Radio Range D
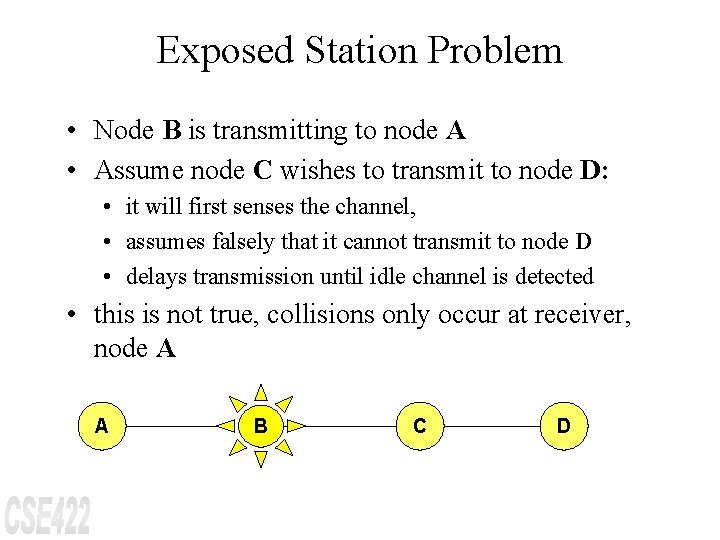
Exposed Station Problem • Node B is transmitting to node A • Assume node C wishes to transmit to node D: • it will first senses the channel, • assumes falsely that it cannot transmit to node D • delays transmission until idle channel is detected • this is not true, collisions only occur at receiver, node A A B C D
![MACA Solution for Hidden Terminal/Exposed Station Problem [Karn 90] • When node A wants MACA Solution for Hidden Terminal/Exposed Station Problem [Karn 90] • When node A wants](http://slidetodoc.com/presentation_image_h2/4026982e59f3d5a4b0bcd22ed4bffd03/image-63.jpg)
MACA Solution for Hidden Terminal/Exposed Station Problem [Karn 90] • When node A wants to send a packet to node B, node A first sends a Request-to-Send (RTS) to B. • On receiving RTS, node B responds by sending Clear-to. Send (CTS), provided node A is able to receive the packet • When a node (such as C) overhears a CTS, it keeps quiet for the duration of the transfer – Transfer duration is included in both RTS and CTS. Range of A’s Transmitter C A RTS B D C E A CTS E Range of B’s Transmitter B D
Reliability • Wireless links are prone to errors. High packet loss rate detrimental to transport-layer performance. • Mechanisms needed to reduce packet loss rate experienced by upper layers A B C D
A Simple Solution to Improve Reliability • When node B receives a data packet from node A, node B sends an Acknowledgement (Ack). This approach adopted in many protocols [Bharghavan 94, IEEE 802. 11] • If node A fails to receive an Ack, it will retransmit the packet A B C D
IEEE 802. 11 Wireless MAC • Distributed and centralized MAC components – Distributed Coordination Function (DCF) – Point Coordination Function (PCF) • DCF suitable for multi-hop ad hoc networking
IEEE 802. 11 DCF • Uses RTS-CTS exchange to avoid hidden terminal problem – Any node overhearing a CTS cannot transmit for the duration of the transfer • Uses ACK to achieve reliability • Any node receiving the RTS cannot transmit for the duration of the transfer – To prevent collision with ACK when it arrives at the sender – When B is sending data to C, node A will keep quiet A B C D
Congestion Avoidance: IEEE 802. 1 DCF • When transmitting a packet, choose a backoff interval in the range [0, cw] – cw is contention window • Count down the backoff interval when medium is idle – Count-down is suspended if medium becomes busy • When backoff interval reaches 0, transmit RTS
Congestion Avoidance • The time spent counting down backoff intervals is a part of MAC overhead • Choosing a large cw leads to large backoff intervals and can result in larger overhead • Choosing a small cw leads to a larger number of collisions (when two nodes count down to 0 simultaneously)
GSM (Global System for Mobile Communications) Combination of ALOHA, TDM, FDM intertwined in complex ways • • Has a max of 200 full duplex channels per cell. Each channel has an uplink and a downlink Each frequency band has 200 k. Hz wide Uses 124 channels and supports 8 separate connections, using TDM • Note: Europe GSM is fully digital
CDMA (Code Division Multiple Access) Channel allocation scheme • Each station to transmit over the entire frequency spectrum all the time • Multiple simultaneous transmissions are separated using coding theory
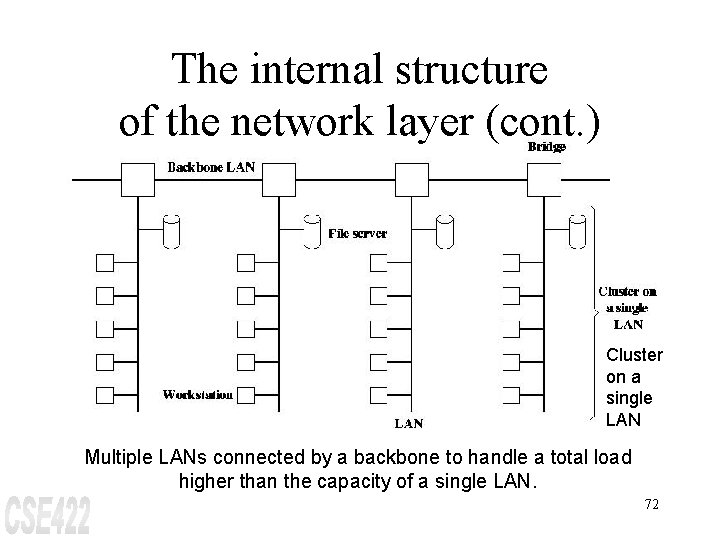
The internal structure of the network layer (cont. ) Cluster on a single LAN Multiple LANs connected by a backbone to handle a total load higher than the capacity of a single LAN. 72
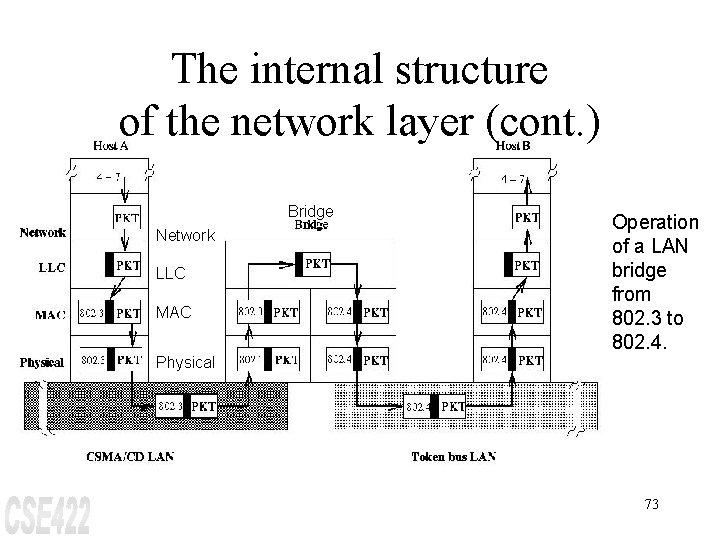
The internal structure of the network layer (cont. ) Bridge Network LLC MAC Physical Operation of a LAN bridge from 802. 3 to 802. 4. 73
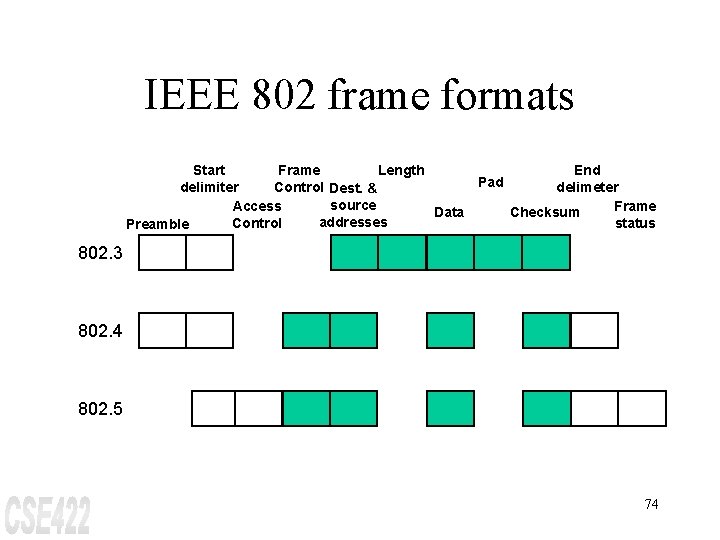
IEEE 802 frame formats Start Frame Length End Pad delimiter Control Dest. & delimeter source Access Frame Data Checksum addresses Control status Preamble 802. 3 802. 4 802. 5 74
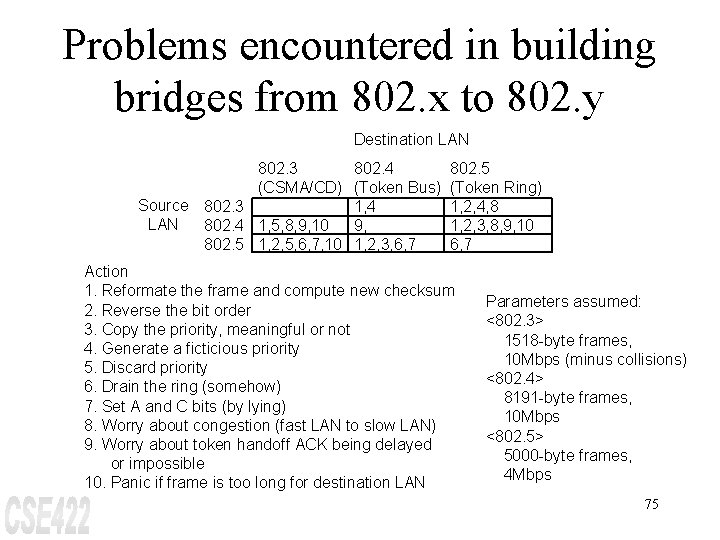
Problems encountered in building bridges from 802. x to 802. y Destination LAN 802. 3 802. 4 (CSMA/CD) (Token Bus) Source 802. 3 1, 4 LAN 802. 4 1, 5, 8, 9, 10 9, 802. 5 1, 2, 5, 6, 7, 10 1, 2, 3, 6, 7 802. 5 (Token Ring) 1, 2, 4, 8 1, 2, 3, 8, 9, 10 6, 7 Action 1. Reformate the frame and compute new checksum 2. Reverse the bit order 3. Copy the priority, meaningful or not 4. Generate a ficticious priority 5. Discard priority 6. Drain the ring (somehow) 7. Set A and C bits (by lying) 8. Worry about congestion (fast LAN to slow LAN) 9. Worry about token handoff ACK being delayed or impossible 10. Panic if frame is too long for destination LAN Parameters assumed: <802. 3> 1518 -byte frames, 10 Mbps (minus collisions) <802. 4> 8191 -byte frames, 10 Mbps <802. 5> 5000 -byte frames, 4 Mbps 75
Bridges From 802. x to 802. y Problems: • Different Frame Format Among LANs • Interconnected LANs Do Not Run at The Same Data Rate • LANs Have Different Max Frame Length • Value of Timers in The Higher Layer May Time Out too Early When Sending a Long Frame 76
Bridges From 802. x to 802. y (cont. ) 802. 3 --802. 3 Fairly straightforward. • If destination LAN is heavily loaded, then frames must be buffered; otherwise, they are discarded. 802. 4 --802. 3 Two problems: n priority bits in 802. 4 frames may request an ACK from the destination. What should the bridge do? 77
Bridges From 802. x to 802. y (cont. ) 802. 5 --802. 3 Similar problem as before: • 802. 5 has frame status byte with A and C bits which are set by the destination to tell sender whether the frame was copied. What should the bridge do? 802. 3 --802. 4 n What to put in the priority bits? Assuming enough delay has already, bridge may transmit all frames at highest priority. 78
Bridges From 802. x to 802. y (cont. ) 802. 4 --802. 4 • What to do with the temporary token handoff? 802. 5 --802. 4 n Same problem as before with the A and C bits. Note: priority bits are different in the two LANs. 802. 3 --802. 5 n Bridge must generate priority bits. 79
Bridges From 802. x to 802. y (cont. ) 802. 4 --802. 5 • Frames may be too long. • Token handoff problem. 802. 5 --802. 5 n What to do with the A and C bits? 80
• • • Transparent Bridges or Spanning Tree (802) There Should be No Hardware Changes Required, No Software Changes Required, etc. Just Plug in The Cable & Walk Away Each Bridge Has a Hash Table for Looking up Destination Addresses Initially, All Bridges Hash Tables Are Empty. Flooding is Used to Have Bridges Learn Destination Addresses To Handle Dynamic Topologies, The Arrival Time is Noted in Every Hash Table Entry Periodically, The Hash Table is Scanned & All Old Entries Are Purged 81
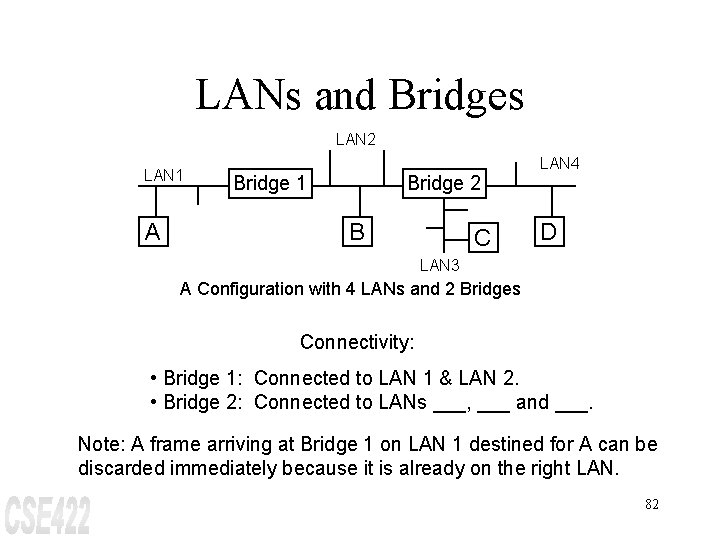
LANs and Bridges LAN 2 LAN 1 A Bridge 1 Bridge 2 B C LAN 4 D LAN 3 A Configuration with 4 LANs and 2 Bridges Connectivity: • Bridge 1: Connected to LAN 1 & LAN 2. • Bridge 2: Connected to LANs ___, ___ and ___. Note: A frame arriving at Bridge 1 on LAN 1 destined for A can be discarded immediately because it is already on the right LAN. 82
LANs and Bridges (cont. ) However, a frame arriving on LAN 1 destined for ___, or ___ must be forwarded. Hash Table (located inside bridge) ==> look up destination address. Example: Bridge 2's table would list A as belonging to ___. Note: Bridges learn destinations after the initial flooding. By looking at the source address, they can tell which machine is accessible on which LAN. 83
LANs and Bridges (cont. ) Example: If Bridge 1 sees a frame on LAN 2 coming from C, it knows that C must be reachable via ___, so it makes an entry in its hash table noting this. A subsequent frame addressed to C coming in on LAN 2 will be ______; whereas if this same frame comes in on LAN 1, it will be ______. Note: Whenever a frame that is already in the table arrives, its entry is updated with the current time. Periodically, a process in the bridge scans the hash table and purges all entries more than a few minutes old. 84
Routing Procedure For An Incoming Frame • If Destination & Source LANs Are The Same, Discard Frame • If Destination & Source LANs Are Different, Forward Frame • If The Destination LAN is Unknown, Use Flooding 85
Source Routing Bridges Note: CSMA/CD & Token Bus Chose Transparent Bridges. The Token Ring Group Chose Source Routing --- Assumes That The Sender of Each Frame Knows Whether or Not The Destination is on Its Own LAN The Frame Header Contains The Exact Path That Frame is To Follow: A Route is A Seq. of Bridge, LAN, . . . 86
Source Routing Bridges (cont. ) When sending a frame to a different LAN, the source machine sets the high order bit of the destination address to 1 to mark it. Also, it includes in the frame header the exact path that frame is to follow. A route is just a sequence of Bridges, LAN, Bridge, . . . Example: Route from A to C in previous figure: (B 1, L 2, B 2, L 3) B 1 --4 bits L 2 --12 bits 87
Source Routing Bridges (cont. ) This algorithm lends itself to three possible implementations: 1. Software: the bridge runs in promiscuous mode, copying all frames to its memory to see if they have the high-order destination bit set to 1. If so, the frame is inspected further, otherwise, it is not. 2. Hybrid: the bridge's LAN interface inspects the high-order destination bit and only gives its frames with the bit set. This interface is easy to build into hardware and greatly reduces the number of frames the bridge must inspect. 88
Source Routing Bridges (cont. ) 3. Hardware: the bridge's LAN interface not only checks the high-order destination bit, but it also scans the route to see if this bridge must do forwarding. Only frames that must actually be forwarded are given to the bridge. This implementation require the most complex hardware, but wastes no bridge CPU cycles because all irrelevant frames are screened out. 89
Discovering Routes: If destination address is unknown, the source issues a broadcast frame (copied by every bridge) asking where it is. When the reply comes back, the bridges record their identity in it, so that the sender can observe routes taken, and choose the best route. 90
- Slides: 90