Standards and Protocols Unit 6 Chapter 12 LAN
- Slides: 34
Standards and Protocols Unit 6, Chapter 12 LAN Installation & Operation
Objectives Describe the installation and operation of a LAN. Describe the necessary management criteria to deploy a LAN. Identify the factors that affect a LAN’s performance. Explain why LANs have distance limitations. List the major components of a home network. Describe the functions of a NOS. Describe the security implications when installing a wireless network.
LAN Selection Criteria Objectives Number of Workstations Type of Workstations Number of Concurrent Users Cost Constraints Security Wiring Availability Vendor Support & Training Expandability Other LANs Required network interfaces Type of Use Number of Printers Medium & Distance Speed Applications LAN Software & Hardware
LAN Cost Consideration Hardware Cost Software Cost Space for equipment Immediate Cost – LAN installation – Workstations – Servers – Printers – Bridges – Software Recurring Cost – operating cost – Hardware & software maintenance – training cost for LAN users and administrators
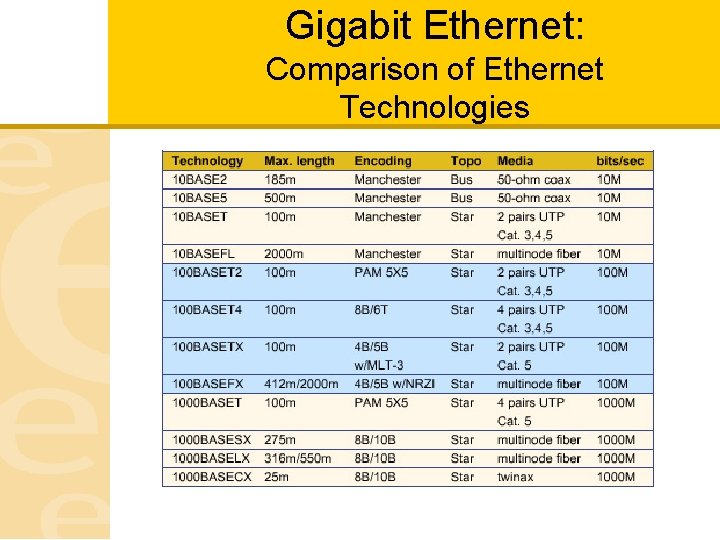
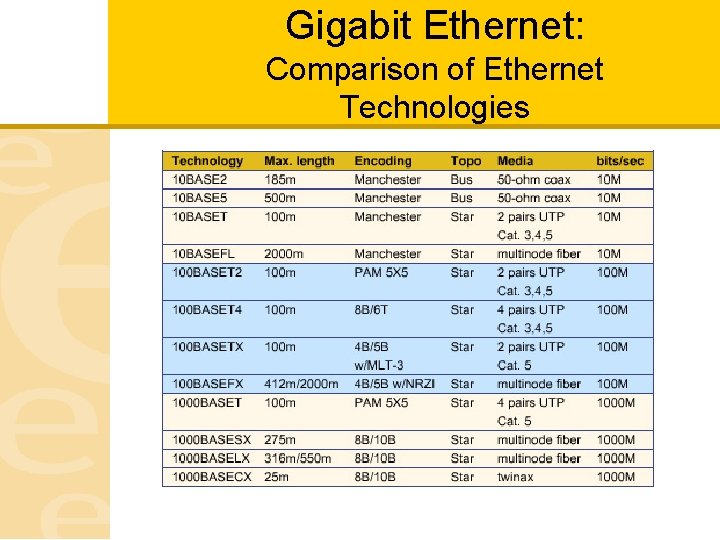
Gigabit Ethernet: Comparison of Ethernet Technologies
LAN Considerations Protocol: – CSM/CD, Token Ring Medium: – Coaxial cable and fiber optic cables are more noise-resistant mediums. – Error rates Speed: – Common LAN speeds for PC’s are 1, 2. 5, 4, 10, 16, 20 and 100 Mbps. – Trend is for higher speeds so can transmission greater volumes of data. Distance: – Distance in LAN is measured in wiring length. – Most microcomputer LANs range from few 100’s m to several 1000’s m Applications: – Application Program Interfaces (APIs) are used to interface with networks. – Some software is not LAN compatible.
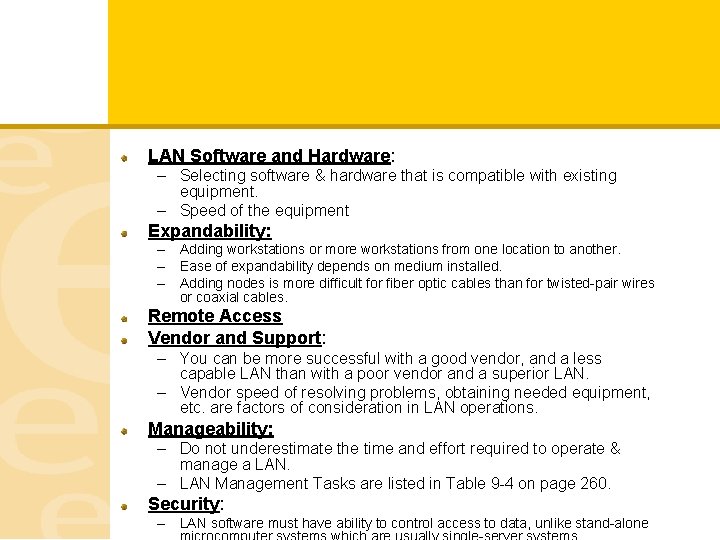
LAN Software and Hardware: – Selecting software & hardware that is compatible with existing equipment. – Speed of the equipment Expandability: – Adding workstations or more workstations from one location to another. – Ease of expandability depends on medium installed. – Adding nodes is more difficult for fiber optic cables than for twisted-pair wires or coaxial cables. Remote Access Vendor and Support: – You can be more successful with a good vendor, and a less capable LAN than with a poor vendor and a superior LAN. – Vendor speed of resolving problems, obtaining needed equipment, etc. are factors of consideration in LAN operations. Manageability: – Do not underestimate the time and effort required to operate & manage a LAN. – LAN Management Tasks are listed in Table 9 -4 on page 260. Security: – LAN software must have ability to control access to data, unlike stand-alone
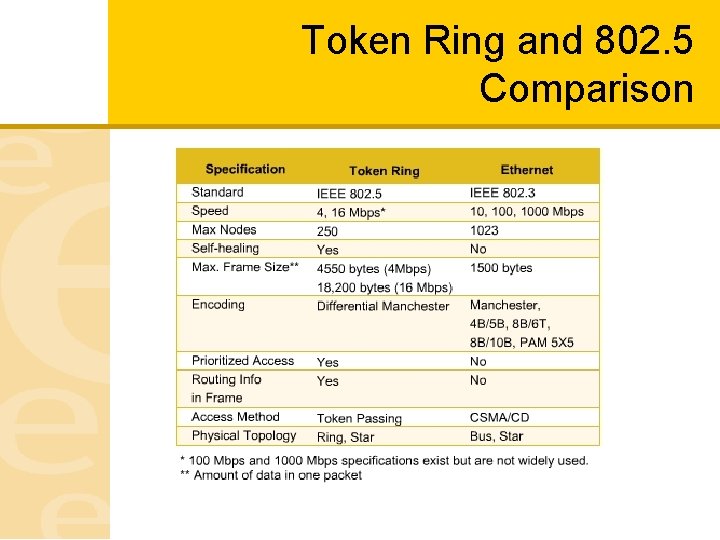
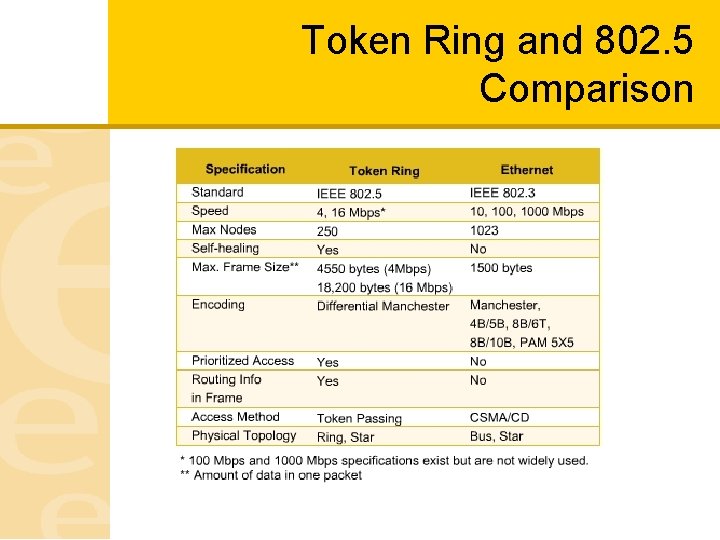
Token Ring and 802. 5 Comparison
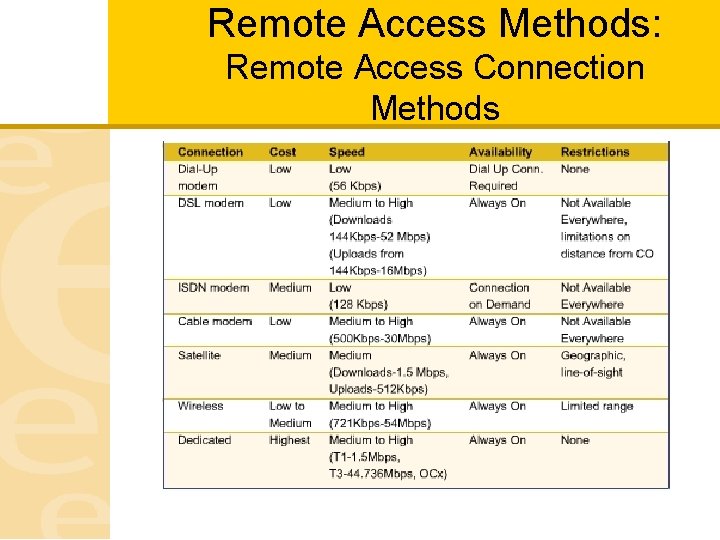
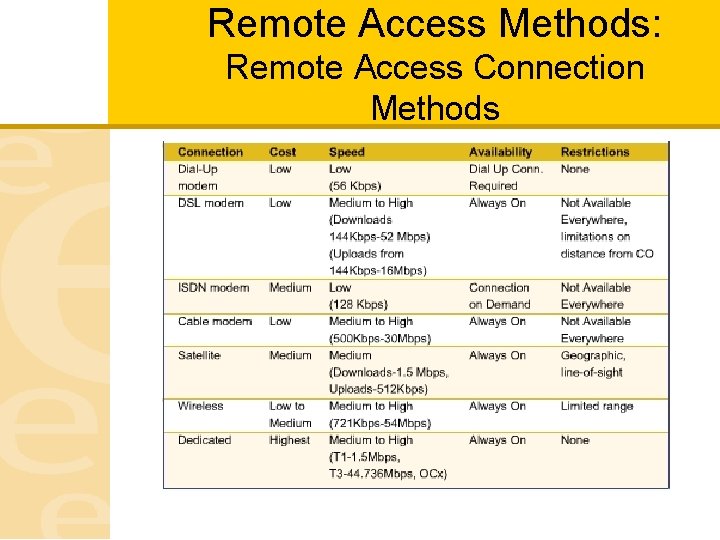
Remote Access Methods: Remote Access Connection Methods
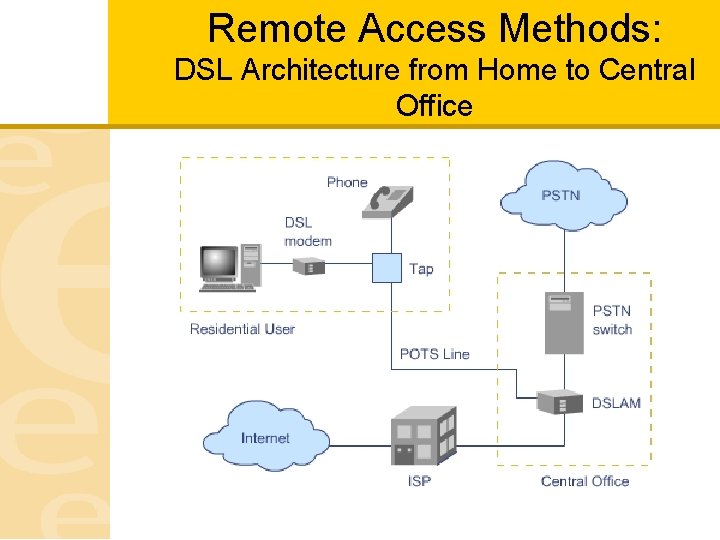
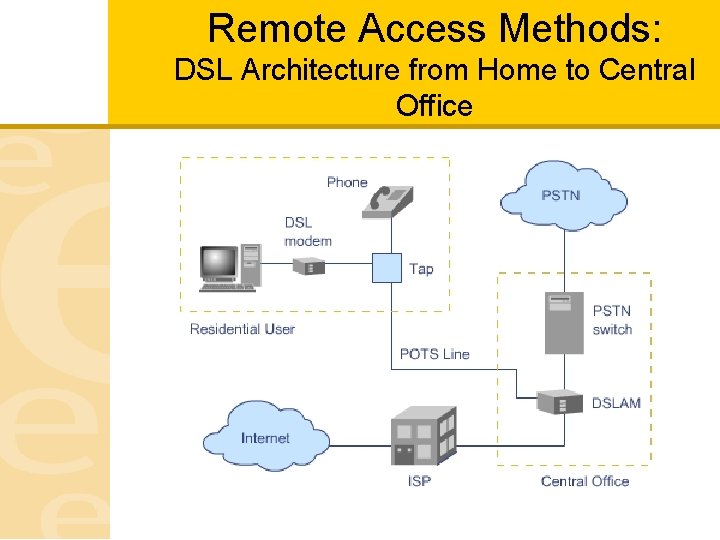
Remote Access Methods: DSL Architecture from Home to Central Office
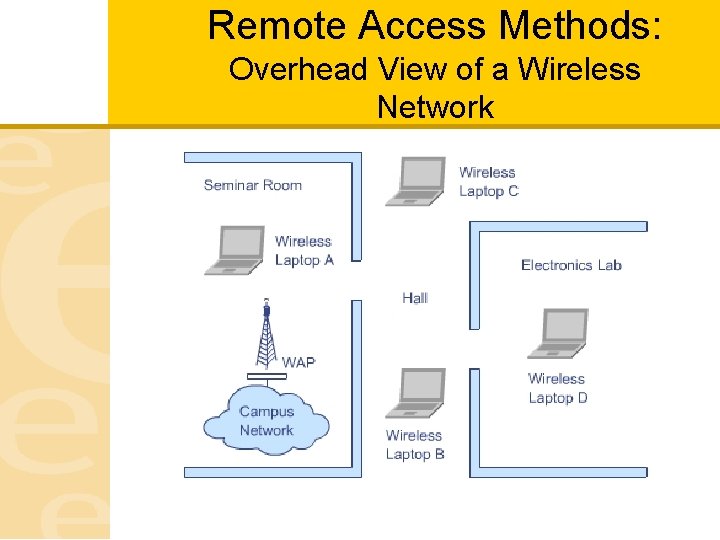
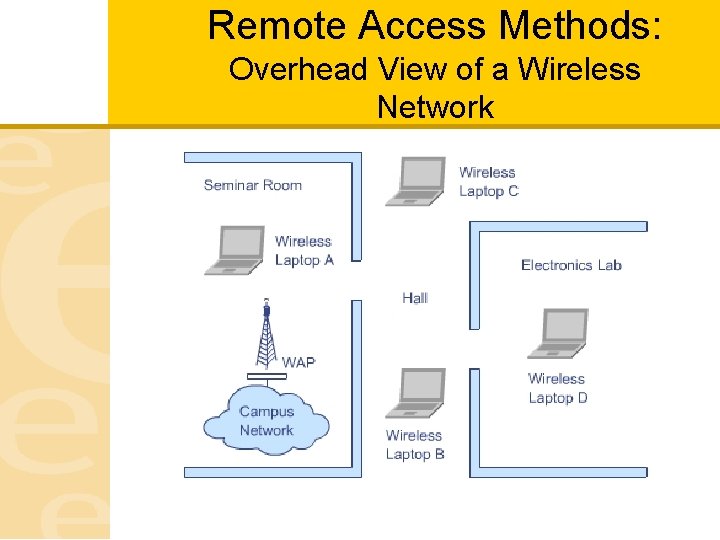
Remote Access Methods: Overhead View of a Wireless Network
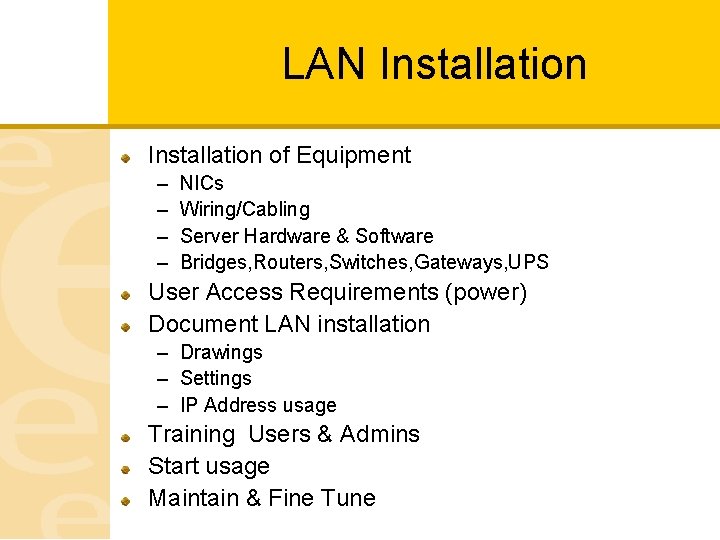
LAN Installation of Equipment – – NICs Wiring/Cabling Server Hardware & Software Bridges, Routers, Switches, Gateways, UPS User Access Requirements (power) Document LAN installation – Drawings – Settings – IP Address usage Training Users & Admins Start usage Maintain & Fine Tune
Network Management: Monitoring a Network Organization & management Physical Safeguards Documentation Change Control Hardware & Software Backup Access to Network Facilities Network Application Standards Network Performance Monitoring Disaster Planning & Recovery Network Time (NTP)
Disaster Recovery: Planning
LAN Software Workstation Software Considerations – APIs/Netbios Microsoft Server – – NT Windows Server 2000 Windows Server 2003 Windows Server 2008 UNIX (HP, Solaris, IBM) LINUX Novell
LAN Security should be built in from the starts Password rules (length & characters) Remote access consideration Encryption implementation Backups & restores, off-site storage Policies – User – Admins – Remote access
Home Networks Peer – to –Peer Ethernet Wireless Phone Line Networks – Multiple computers share one internet connection Power Line Networks
Home Networks Components Personal Computer Interconnect or Industry Standard Architecture – PC bus standards Personal Computer Memory Card Interface Adapter – Standard on laptops Wireless
Network Management Design & Implementation Develop the statement of requirements – Obtain concurrence Investigate Alternatives Network Design Select Equipment & Vendors Prepare for Implementation Cutover
Network Management Requirements & Alternatives Develop the statement of requirements – Ensure that the network engineer understands requirements – Work closely with management and users – Obtain concurrence Investigate Alternatives – Ask Questions , research methods to meet requirements
Network Management Network Design & Selection of Vendors Network Design – – Modeling Simulation Star, Ring , fully meshed Expected Traffic Flow Select Equipment & Vendors – Use information obtained – Request for Proposals – Calculation of costs & benefits
Network Management Preparation for Implementation/Implementation Preparation for Implementation – Develop project plan – Obtain approval from management – Communication to users Implementation – Installation • Stress testing • Work Load Generators • Cable and wiring labeling – Training
Network Management Cutover Startup of new or upgraded network Testing each and every function – Use pre-defined test scripts Increased staffing to support cut over Changes made must be documented Post Installation Audit of implementation
Review Questions 1. The client software called Net. BIOS, which stands for Network Basic Input. Output Systems, operates at both layer 2 (the data link layer) and layer _______ (the session control layer) of the OSI model. a. 3 b. 4 c. 5 d. 7
Review Questions 2. More and more families are creating home networks to _______. a. avoid the high cost of ISPs b. share a high-speed Internet connection c. practice their networking skills d. ensure greater network security
Review Questions 3. One of the most important prerequisites for home networking is _______. a. thorough knowledge of networking b. an MSCE certification c. broadband cable access d. ease of installation
Review Questions 4. Which of the following is not a phase of network design as described in the text? a. developing the statement of requirements b. investigating alternatives c. network design d. implementation
Review Questions 5. Management approval of a technical project is normally required _____. a. at the beginning of the project b. at the end of most phases of the network design process c. after the network is installed and they can see how it is operating d. only under exceptional circumstances
Review Questions 6. IPsec is used in which of the following? a. SPOOLing b. VPNs c. MVS d. PDNA
Review Questions 7. Attenuation is ________. a. the increase of signal strength by a factor of ten b. only an issue on digital circuits c. the weakening of a signal over a distance d. only an issue on circuits provided by ATT
Review Questions 8. Which of the following statements is true? a. Network cabling is often more expensive than the cost of the labor necessary to install it. b. It is best to install cabling with just enough capacity to meet today’s requirements. c. Cabling does not need to be labeled because it can easily be traced. d. all of the above e. none of the above
Review Questions 9. Internetwork designers must ______ a. deal with multiple organizations b. consider the high speed backbone that will carry traffic between networks. c. understand how routers, switches, and bridges work. d. consider traffic prioritization issues. e. All of the above.
Review Questions 10. Which of the following routing techniques are used in WANs? a. dynamic routing b. distributed routing c. static routing d. All of the above
Homework Due Next Week – Review: • • – Chapter 12, pp. 318 -344 Chapter 18, pp. 521 -531 Read: • • – Chapter 13, pp. 350 -371 Chapter 14, pp. 378 -411 Complete: • • Multiple Choice Questions 1 -7 on pp. 373 -374 Multiple Choice Questions 1 -10 on pp. 412 -414