Wonders of the Digital Envelope Computational complexity based
Wonders of the Digital Envelope Computational complexity based cryptography Theoretical ideas behind e-commerce and the internet revolution
Lecture III - plan - Cryptography before computational complexity - The ambitions of modern cryptography - The assumptions of modern cryptography - The “digital envelope” and its power - Zero-knowledge proofs - Private communication - Oblivious computation
Cryptography before computational complexity Secret communication Assuming shared information which no one else has
What do we want to do?
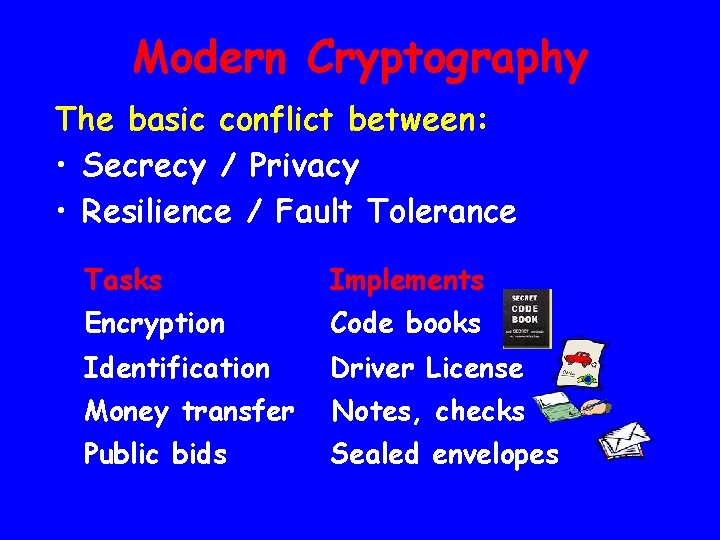
Modern Cryptography The basic conflict between: • Secrecy / Privacy • Resilience / Fault Tolerance Tasks Implements Encryption Code books Identification Driver License Money transfer Notes, checks Public bids Sealed envelopes
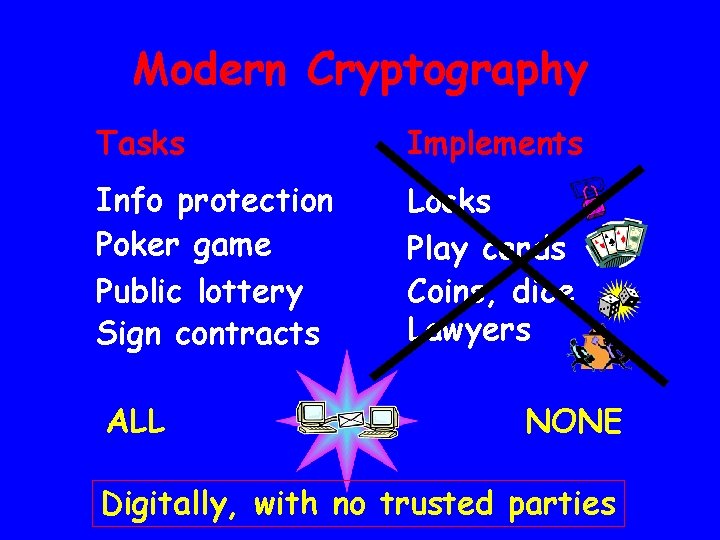
Modern Cryptography Tasks Implements Info protection Poker game Public lottery Sign contracts Locks Play cards Coins, dice Lawyers ALL NONE Digitally, with no trusted parties
What are we assuming?
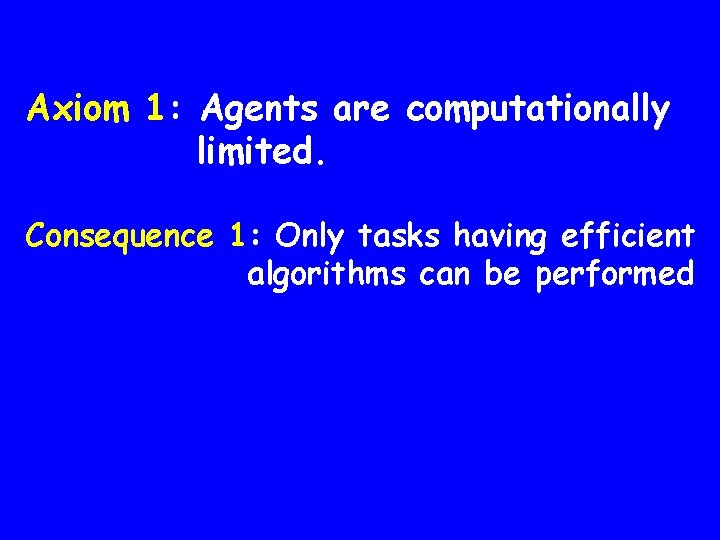
Axiom 1: Agents are computationally limited. Consequence 1: Only tasks having efficient algorithms can be performed
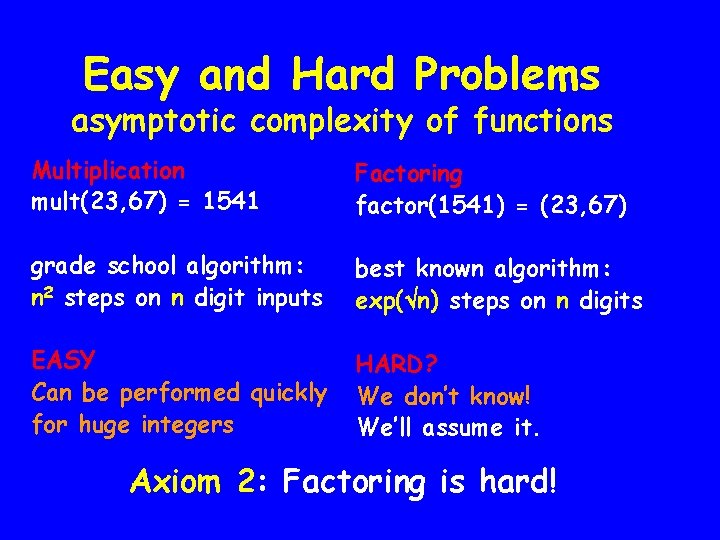
Easy and Hard Problems asymptotic complexity of functions Multiplication mult(23, 67) = 1541 Factoring factor(1541) = (23, 67) grade school algorithm: n 2 steps on n digit inputs best known algorithm: exp( n) steps on n digits EASY Can be performed quickly for huge integers HARD? We don’t know! We’ll assume it. Axiom 2: Factoring is hard!
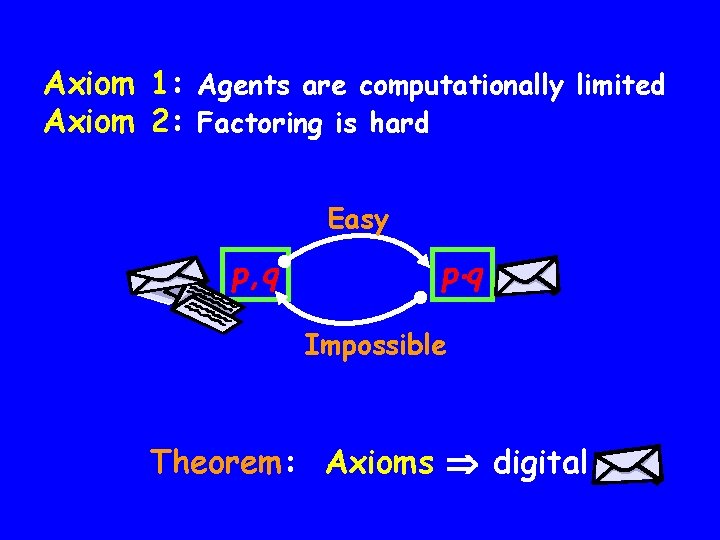
Axiom 1: Agents are computationally limited Axiom 2: Factoring is hard Easy p, q p q Impossible Theorem: Axioms digital
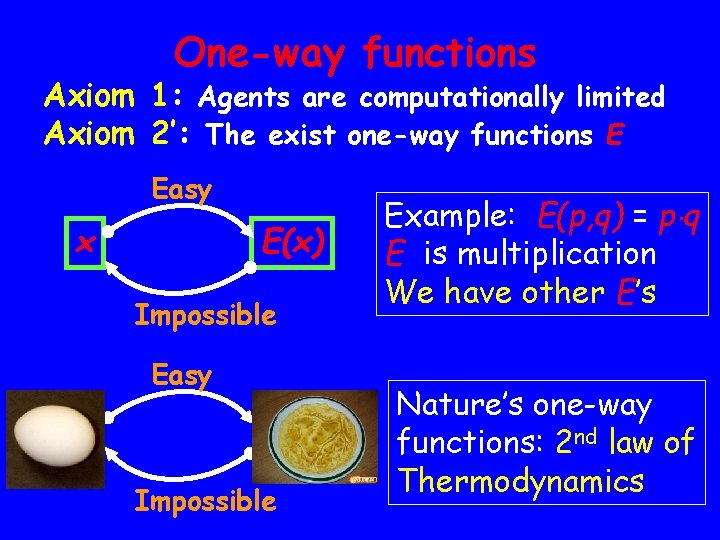
One-way functions Axiom 1: Agents are computationally limited Axiom 2’: The exist one-way functions E Easy x E(x) Impossible Easy Impossible Example: E(p, q) = p q E is multiplication We have other E’s Nature’s one-way functions: 2 nd law of Thermodynamics
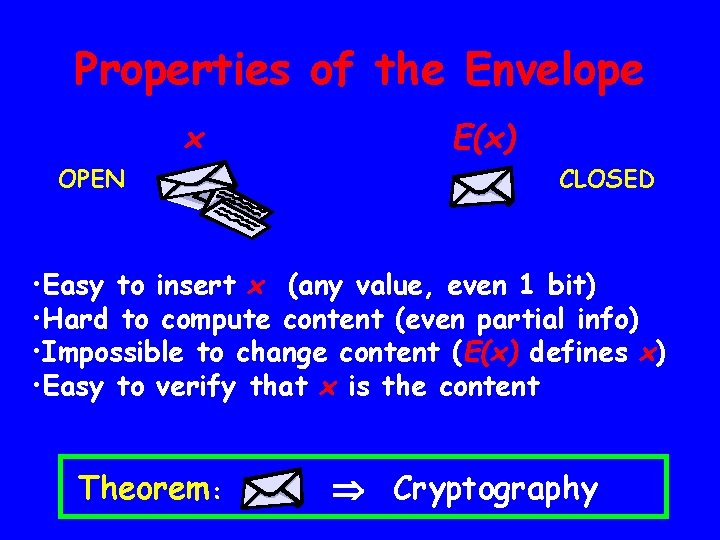
Properties of the Envelope x OPEN E(x) CLOSED • Easy to insert x (any value, even 1 bit) • Hard to compute content (even partial info) • Impossible to change content (E(x) defines x) • Easy to verify that x is the content Theorem: Cryptography
The power of the digital envelope Examples of increasing difficulty Mind games of the 1980’s – before Internet & E-commerce were imagined
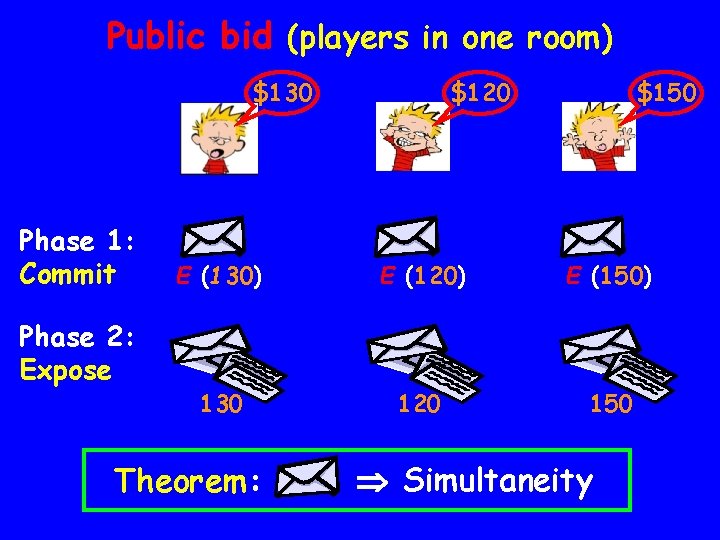
Public bid (players in one room) $130 Phase 1: Commit Phase 2: Expose $120 $150 E (130) E (120) E (150) 130 120 150 Theorem: Simultaneity
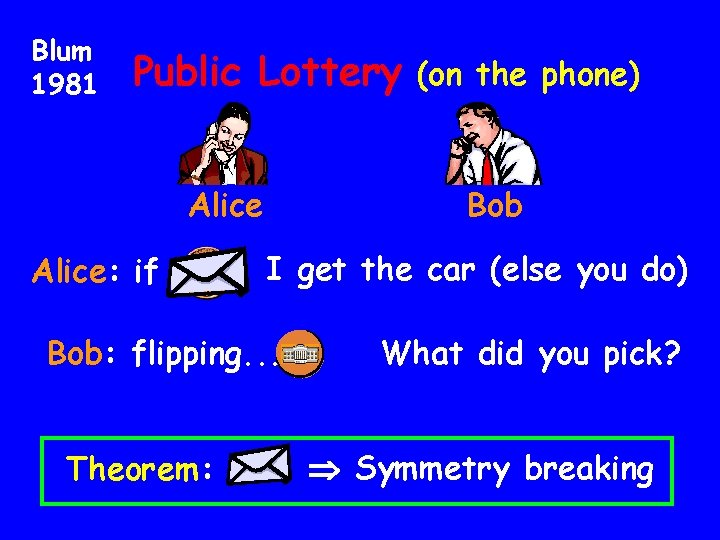
Blum 1981 Public Lottery Alice: if Bob I get the car (else you do) Bob: flipping. . . Theorem: (on the phone) You lost! What did you pick? Symmetry breaking
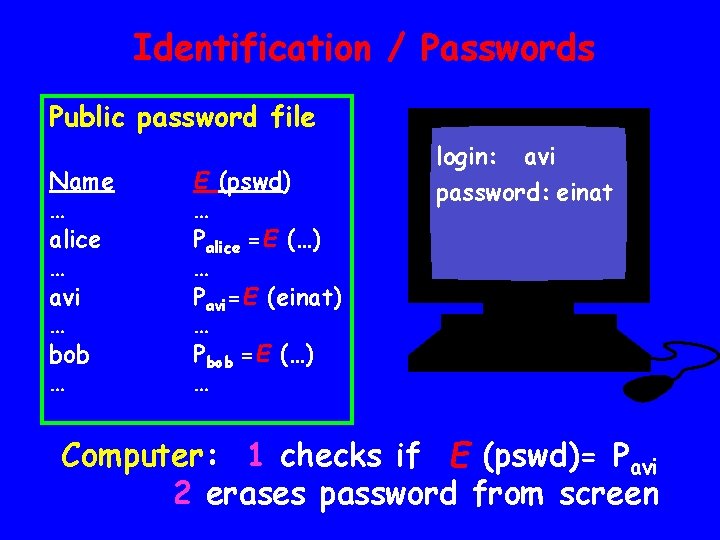
Identification / Passwords Public password file Name … alice … avi … bob … E (pswd) … Palice =E (…) … Pavi=E (einat) … Pbob =E (…) … login: avi password: einat Computer: 1 checks if E (pswd)= Pavi 2 erases password from screen
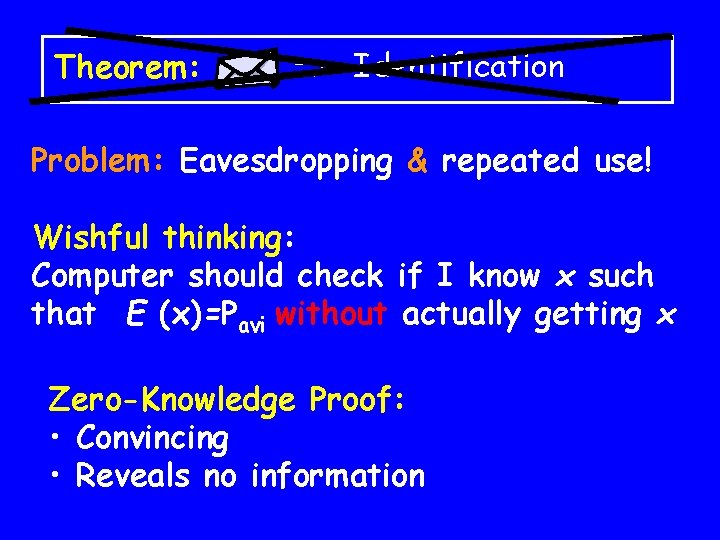
Theorem: Identification Problem: Eavesdropping & repeated use! Wishful thinking: Computer should check if I know x such that E (x)=Pavi without actually getting x Zero-Knowledge Proof: • Convincing • Reveals no information
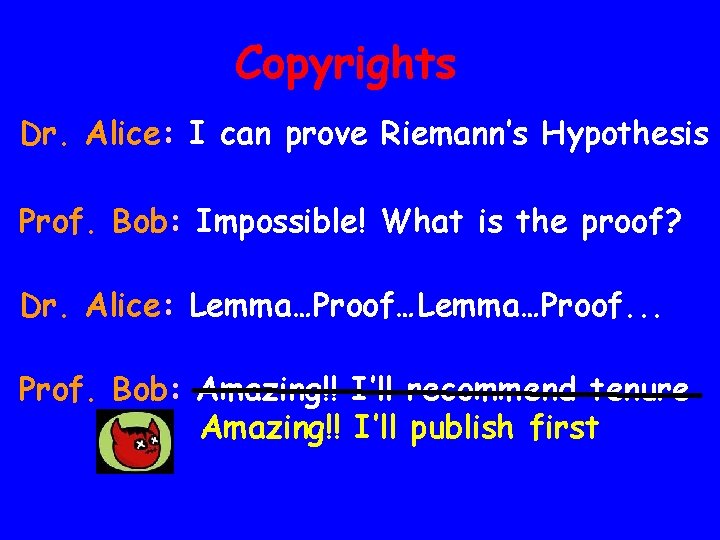
Copyrights Dr. Alice: I can prove Riemann’s Hypothesis Prof. Bob: Impossible! What is the proof? Dr. Alice: Lemma…Proof…Lemma…Proof. . . Prof. Bob: Amazing!! I’ll recommend tenure Amazing!! I’ll publish first
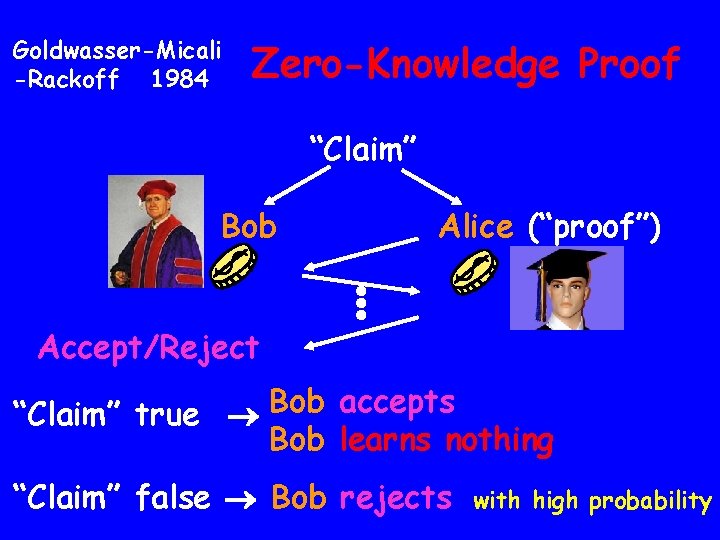
Goldwasser-Micali -Rackoff 1984 Zero-Knowledge Proof “Claim” Bob Alice (“proof”) Accept/Reject Bob accepts “Claim” true Bob learns nothing “Claim” false Bob rejects with high probability
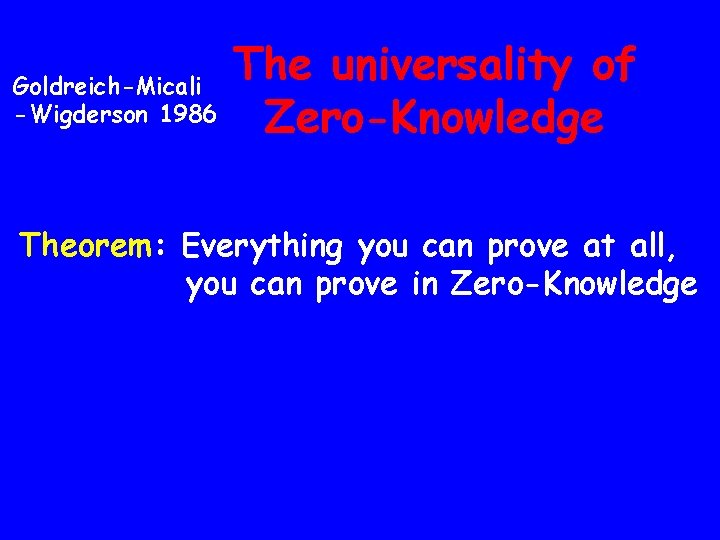
Goldreich-Micali -Wigderson 1986 The universality of Zero-Knowledge Theorem: Everything you can prove at all, you can prove in Zero-Knowledge
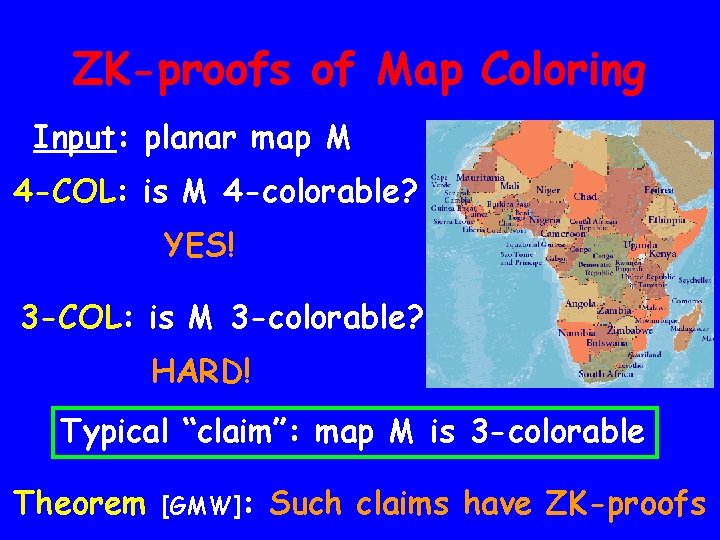
ZK-proofs of Map Coloring Input: planar map M 4 -COL: is M 4 -colorable? YES! 3 -COL: is M 3 -colorable? HARD! Typical “claim”: map M is 3 -colorable Theorem [GMW]: Such claims have ZK-proofs
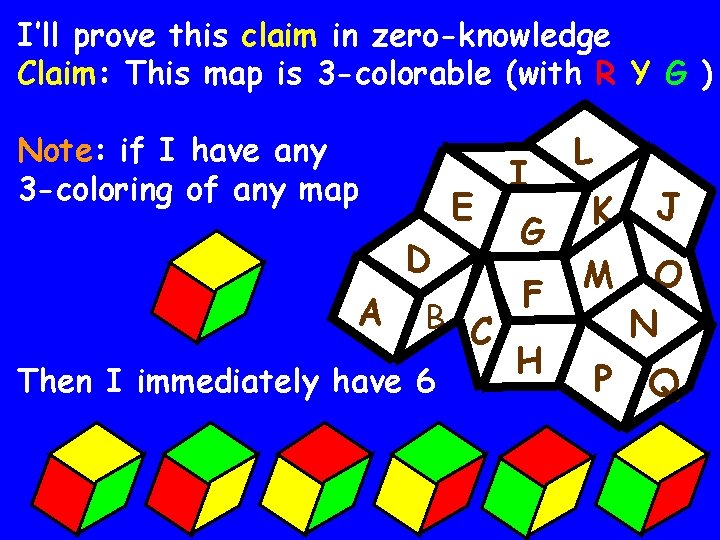
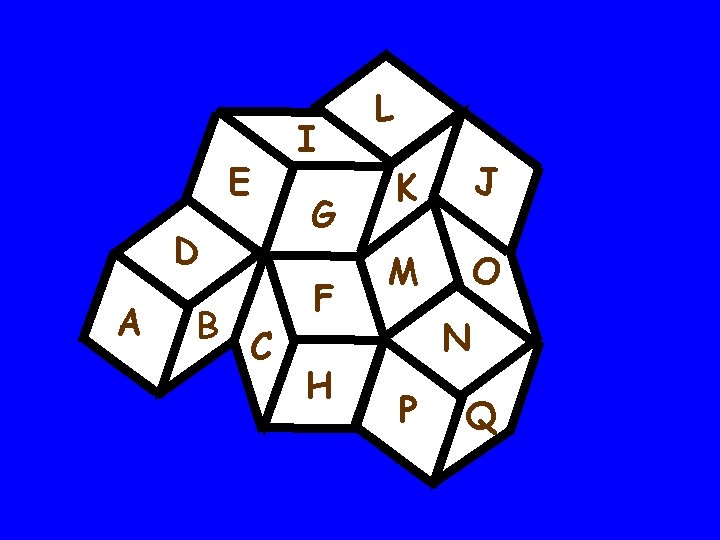
I’ll prove this claim in zero-knowledge Claim: This map is 3 -colorable (with R Y G ) Note: if I have any 3 -coloring of any map E D A I G F B C H Then I immediately have 6 L K J M O N P Q

Structure of proof: Repeat (until satisfied) - I hide a random one of my 6 colorings in digital envelopes A - You pick a pair of adjacent countries E D B C I G F H - I open this pair of envelopes Reject if RR, YY, GG or illegal color L K J M O N P Q
Zero-knowledge proof demo
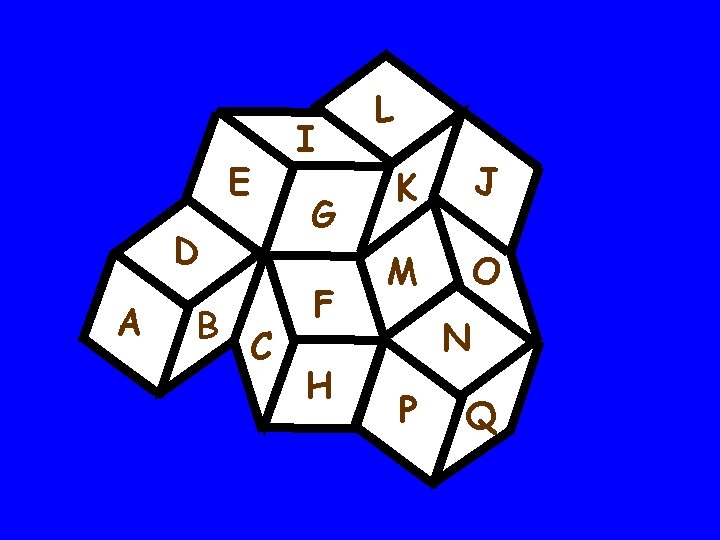
E D A B C I G F H L K J M O N P Q
E D A B C I G F H L K J M O N P Q
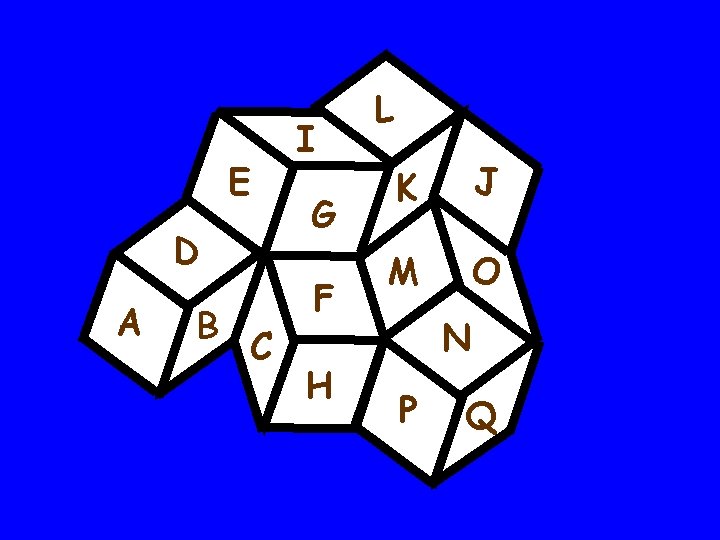
E D A B C I G F H L K J M O N P Q
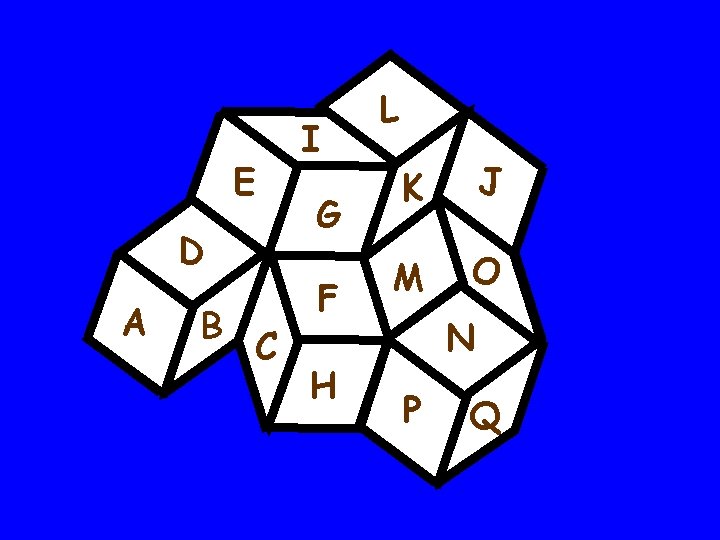
E D A B C I G F H L K J M O N P Q
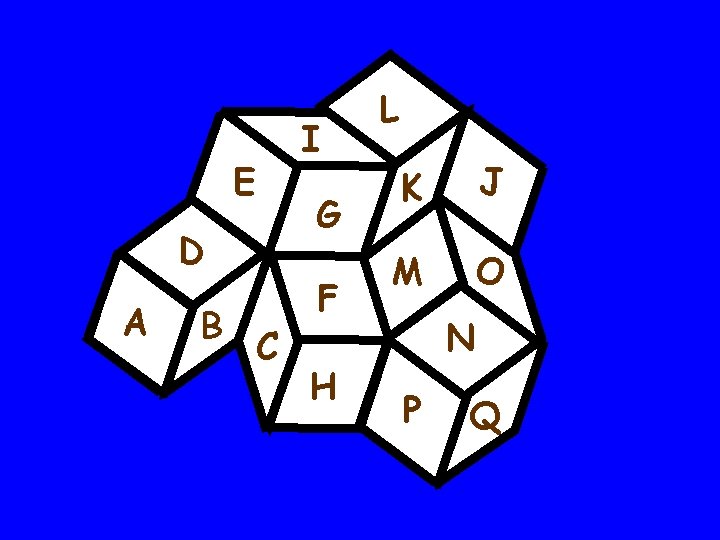
I E G D A B C F H L K J M O N P Q
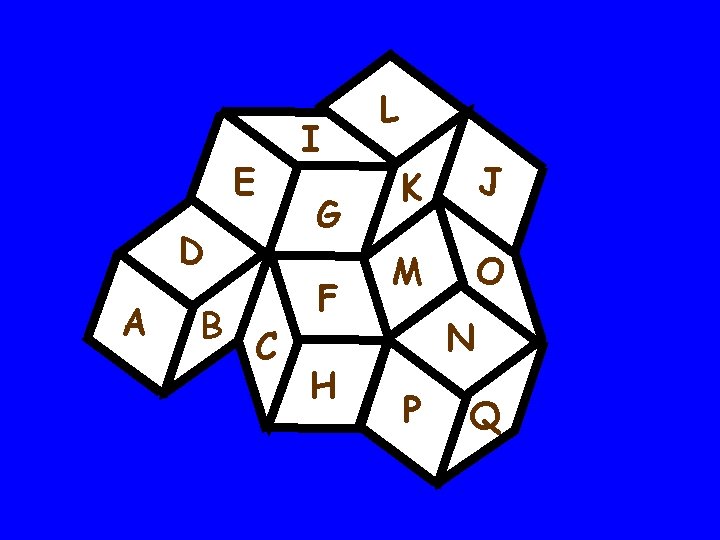
E D A B C I G F H L K J M O N P Q
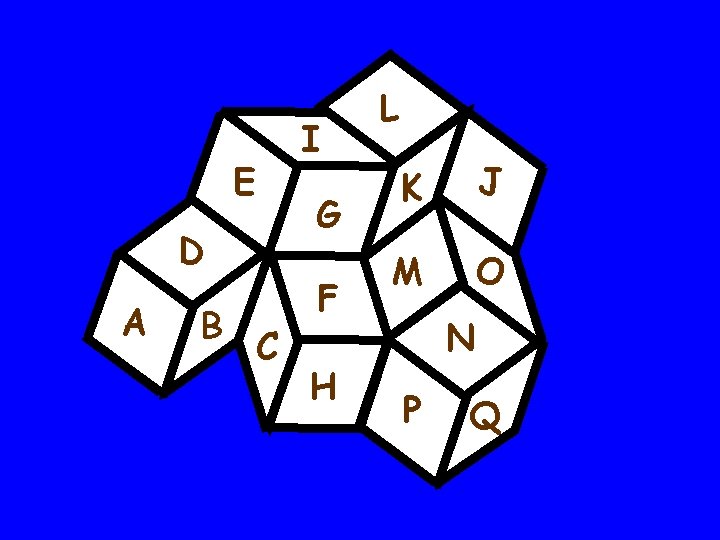
I E G D A B C F H L K J M O N P Q
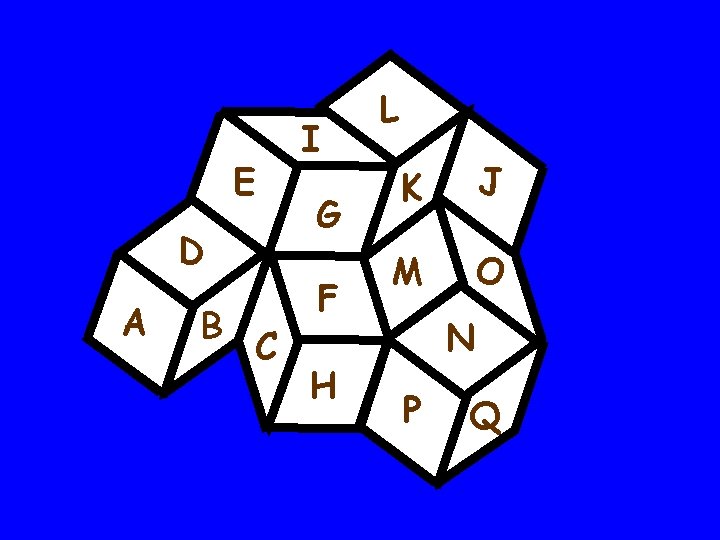
E D A B C I G F H L K J M O N P Q
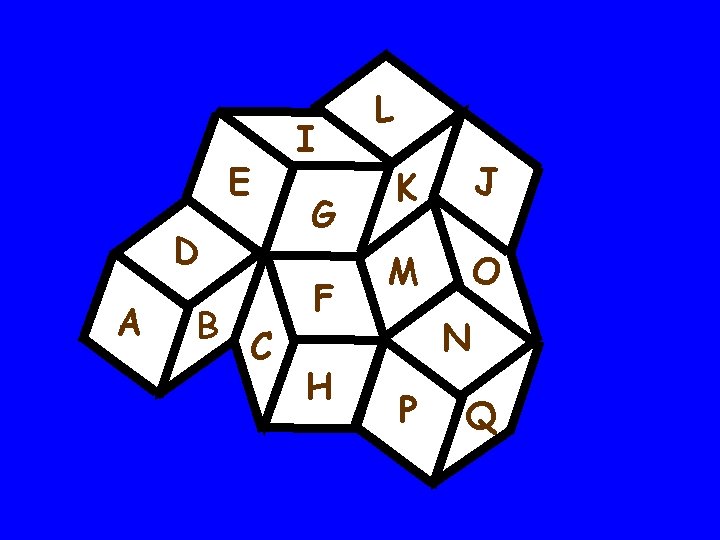
E D A B C I G F H L K J M O N P Q
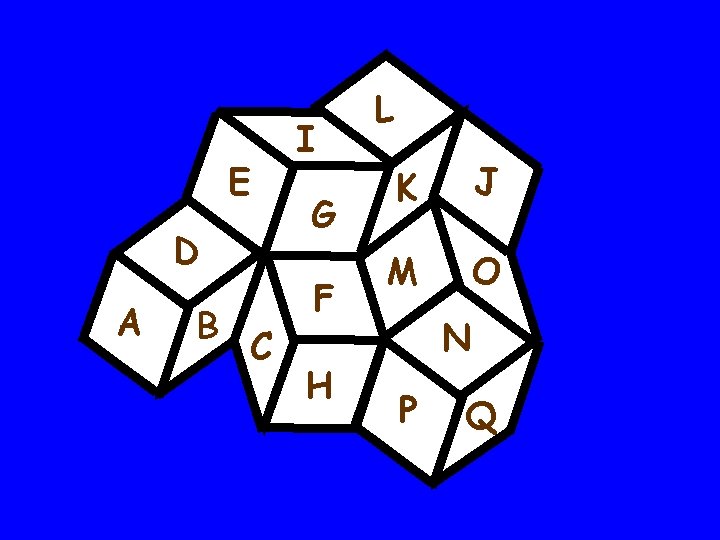
E D A B C I G F H L K J M O N P Q
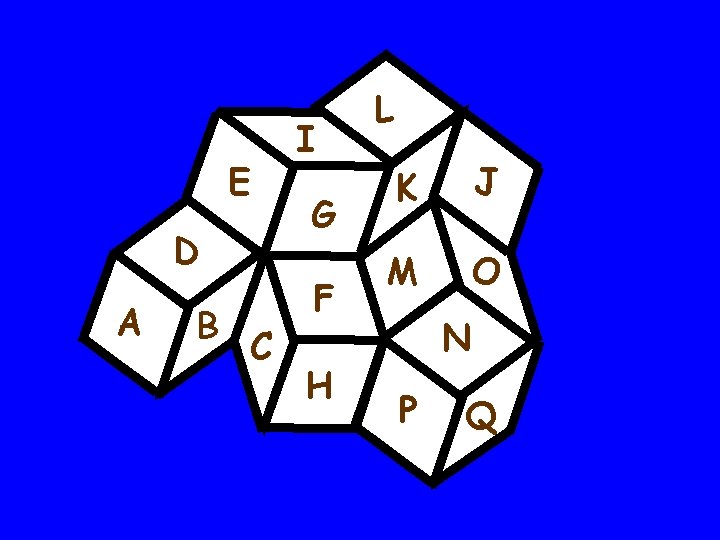
E D A B C I G F H L K J M O N P Q
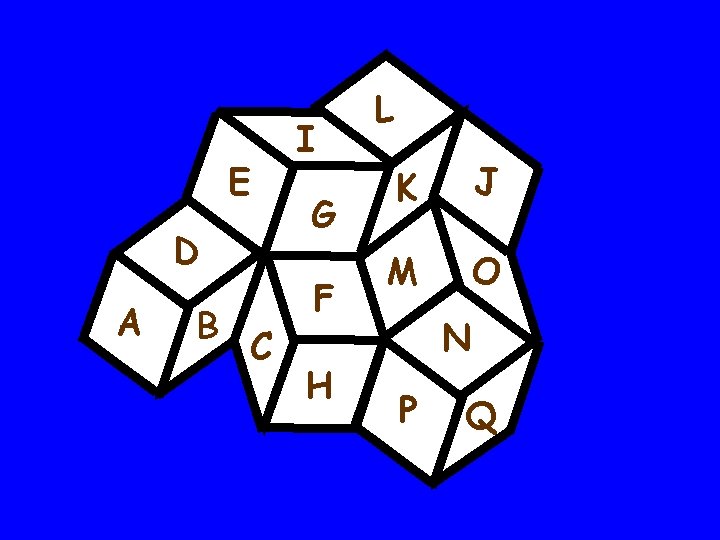
E D A B C I G F H L K J M O N P Q

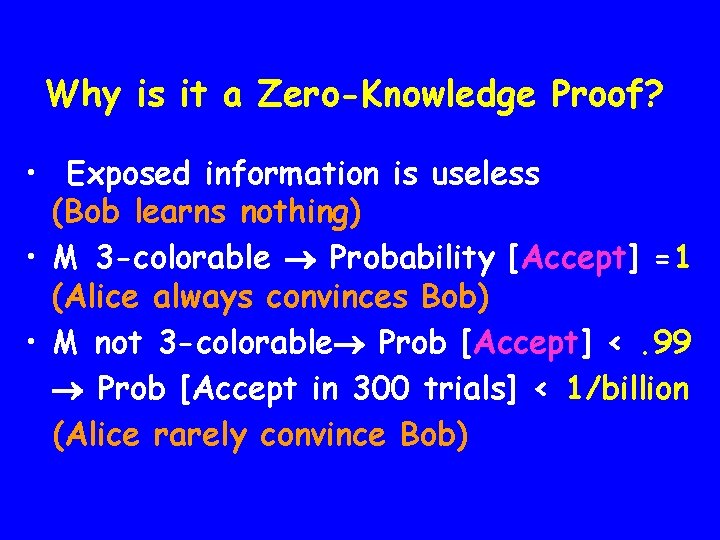
Why is it a Zero-Knowledge Proof? • Exposed information is useless (Bob learns nothing) • M 3 -colorable Probability [Accept] =1 (Alice always convinces Bob) • M not 3 -colorable Prob [Accept] <. 99 Prob [Accept in 300 trials] < 1/billion (Alice rarely convince Bob)
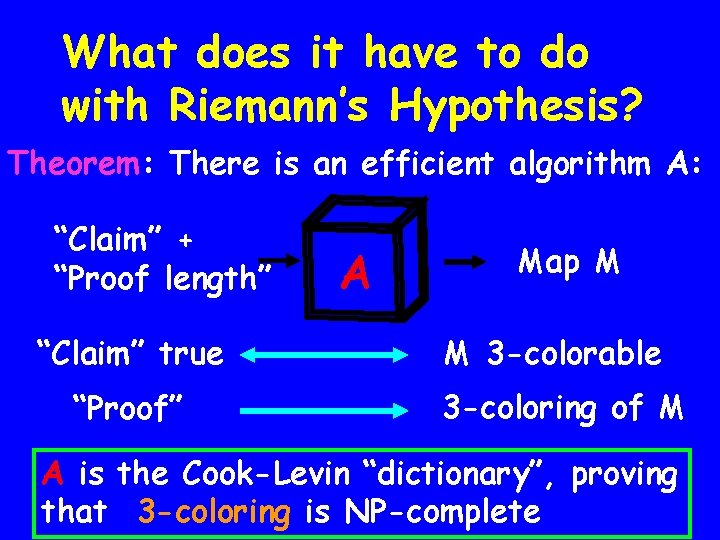
What does it have to do with Riemann’s Hypothesis? Theorem: There is an efficient algorithm A: “Claim” + “Proof length” “Claim” true “Proof” A Map M M 3 -colorable 3 -coloring of M A is the Cook-Levin “dictionary”, proving that 3 -coloring is NP-complete
![Theorem [GMW]: + short proof efficient ZK proof Theorem [GMW]: fault-tolerant protocols Theorem [GMW]: + short proof efficient ZK proof Theorem [GMW]: fault-tolerant protocols](http://slidetodoc.com/presentation_image/191755fa4f6a50e0759594bb7b43bead/image-40.jpg)
Theorem [GMW]: + short proof efficient ZK proof Theorem [GMW]: fault-tolerant protocols
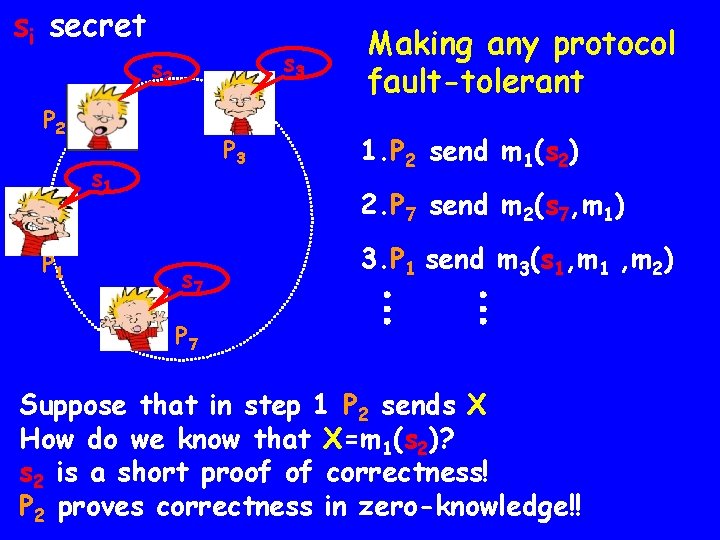
si secret s 3 s 2 P 3 s 1 P 1 Making any protocol fault-tolerant 1. P 2 send m 1(s 2) 2. P 7 send m 2(s 7, m 1) s 7 3. P 1 send m 3(s 1, m 1 , m 2) P 7 Suppose that in step 1 P 2 sends X How do we know that X=m 1(s 2)? s 2 is a short proof of correctness! P 2 proves correctness in zero-knowledge!!
So Far. . . ü Fault Tolerance (we can force players to behave well!) ? Privacy/Secrecy (even when all players behave well)
Private communication Alice and Bob want to have a completely private conversation. They share no private information Many in this audience has already faced and solved this problem often!
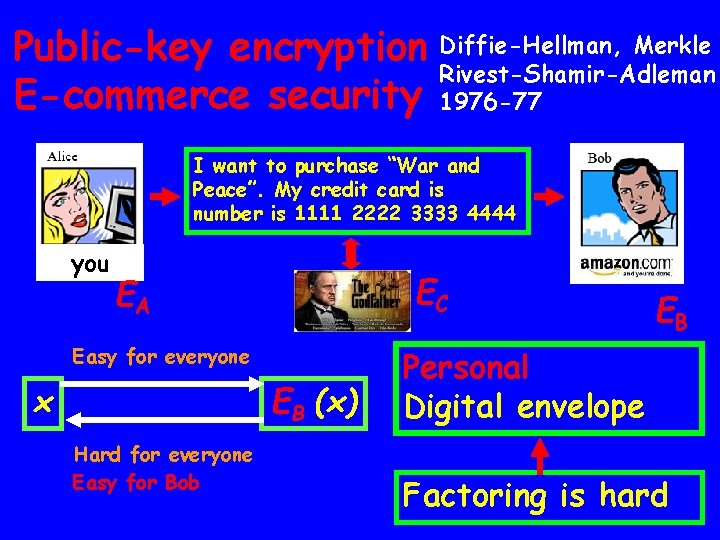
Public-key encryption Diffie-Hellman, Merkle Rivest-Shamir-Adleman E-commerce security 1976 -77 I want to purchase “War and Peace”. My credit card is number is 1111 2222 3333 4444 you EC EA Easy for everyone x EB (x) Hard for everyone Easy for Bob EB Personal Digital envelope Factoring is hard
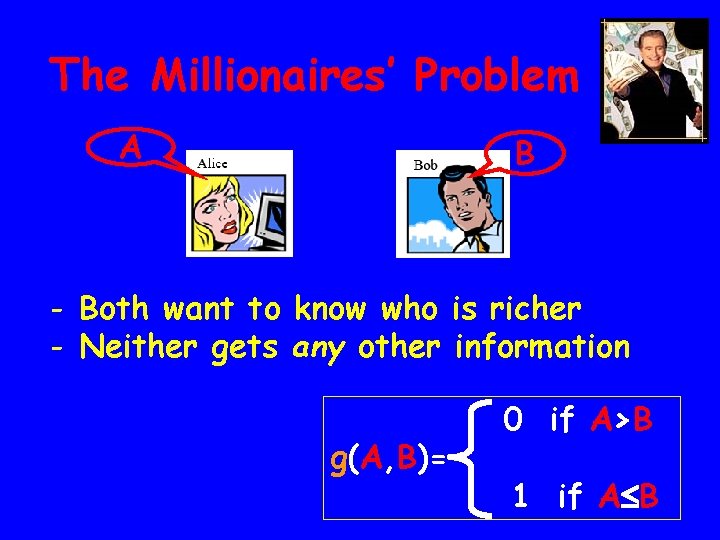
The Millionaires’ Problem A B - Both want to know who is richer - Neither gets any other information g(A, B)= 0 if A>B 1 if A B
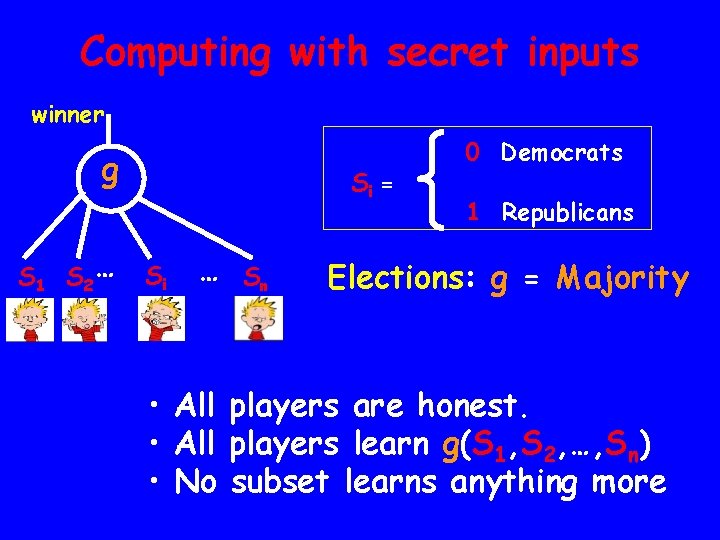
Computing with secret inputs winner g S 1 S 2 … Si = Si … Sn 0 Democrats 1 Republicans Elections: g = Majority • All players are honest. • All players learn g(S 1, S 2, …, Sn) • No subset learns anything more
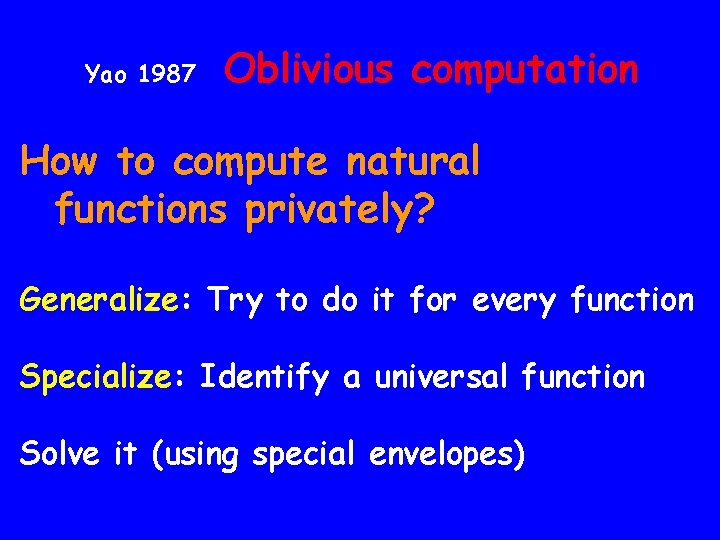
Yao 1987 Oblivious computation How to compute natural functions privately? Generalize: Try to do it for every function Specialize: Identify a universal function Solve it (using special envelopes)
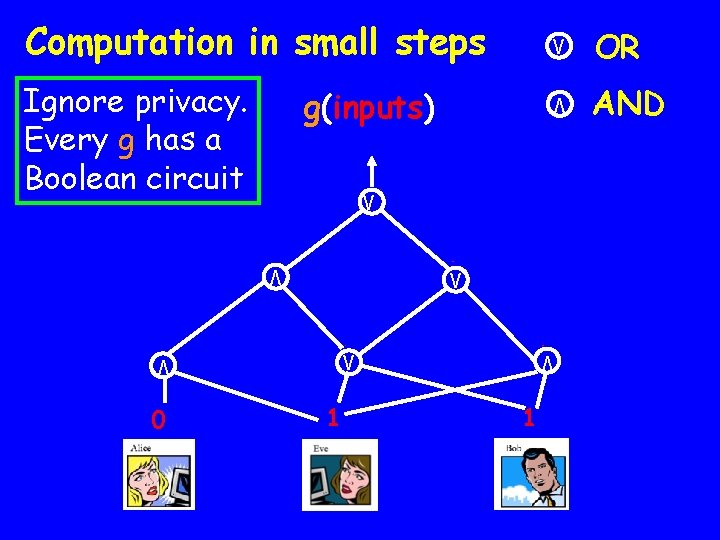
Ignore privacy. Every g has a Boolean circuit g(inputs) V 0 1 V V 0 0 1 V V 1 V 0 1 1 V OR V Computation in small steps AND
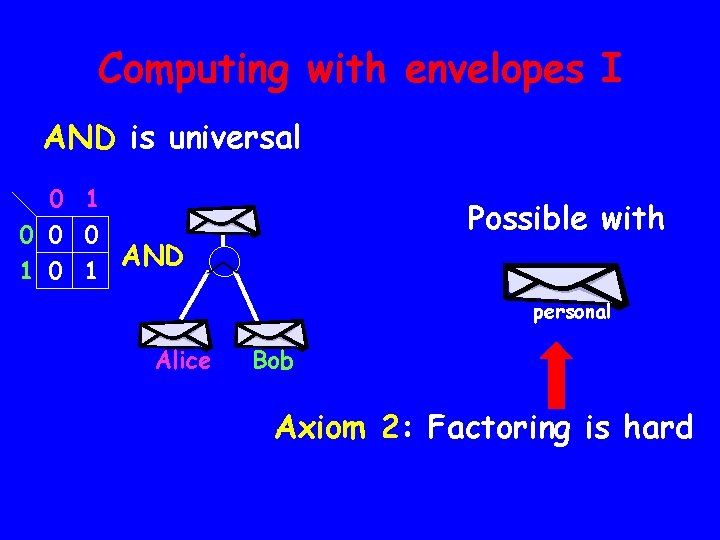
Computing with envelopes I AND is universal 0 1 0 0 0 AND 1 0 1 a Alice Possible with b Bob personal Axiom 2: Factoring is hard
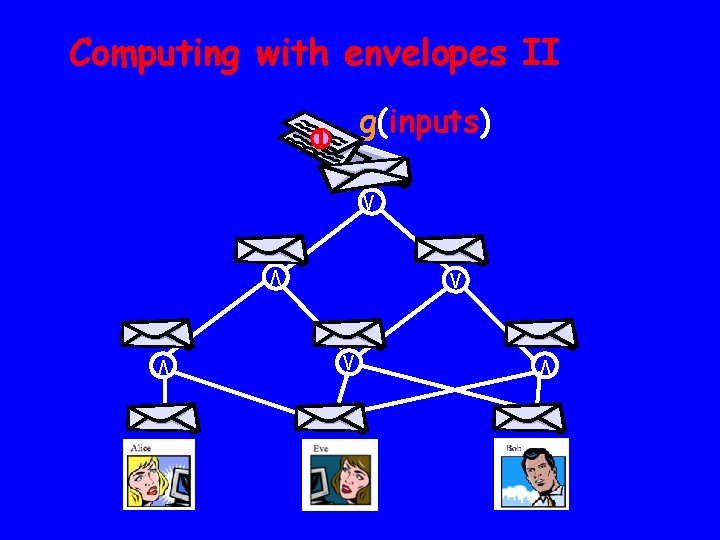
Computing with envelopes II g(inputs) 1 V 0 1 V V 0 0 1 V V 1 V 0 1 1
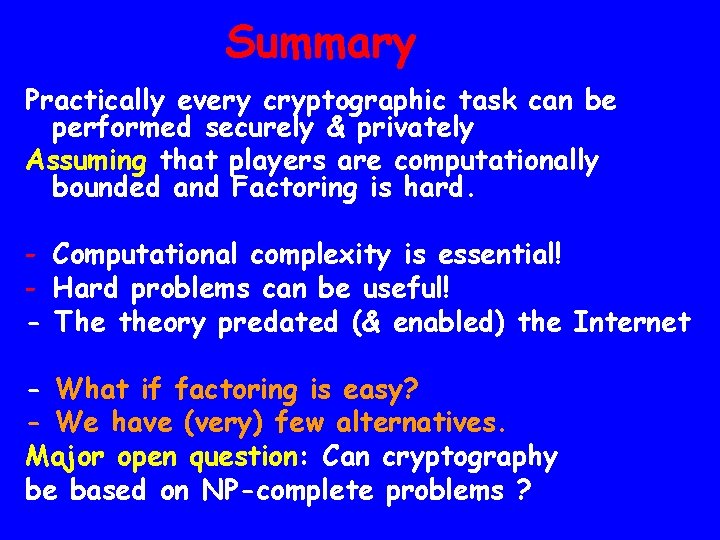
Summary Practically every cryptographic task can be performed securely & privately Assuming that players are computationally bounded and Factoring is hard. - Computational complexity is essential! - Hard problems can be useful! - The theory predated (& enabled) the Internet - What if factoring is easy? - We have (very) few alternatives. Major open question: Can cryptography be based on NP-complete problems ?
- Slides: 51