Social Engineering The Art of Social Hacking Deff




- Slides: 59
Social Engineering The Art of Social Hacking Deff Arnaldy This Presentation belong to : 1. Christopher Stowe 2. Frederick Gallegos, CISA, CGFM, CDE
Introduction • What is Social Engineering? o Manipulate people into doing something, rather than by breaking in using technical means • Types of Social Engineering o Quid Pro Quo o Phishing o Baiting o Pretexting o Diversion Theft • Ways to prevent Social Engineering
What is Social Engineering? • Attacker uses human interaction to obtain or compromise information • Attacker my appear unassuming or respectable o Pretend to be a new employee, repair man, ect o May even offer credentials • By asking questions, the attacker may piece enough information together to infiltrate a companies network o May attempt to get information from many sources
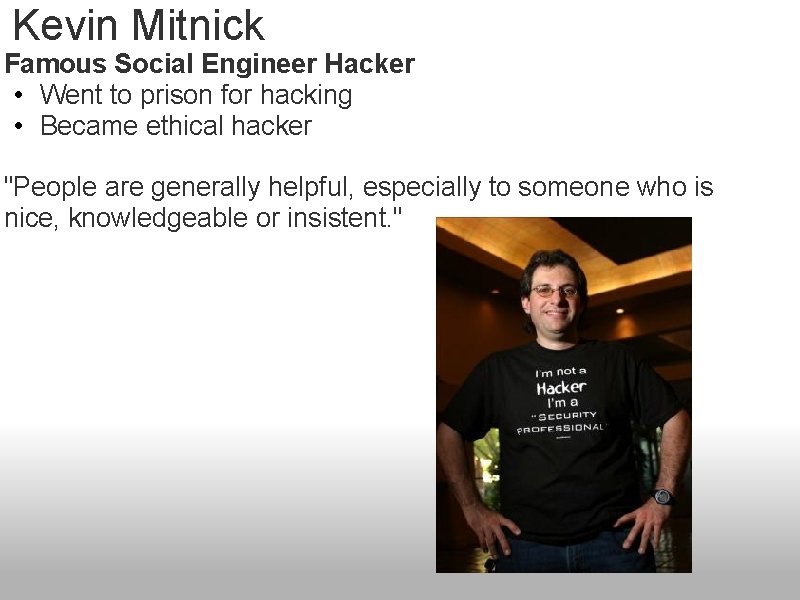
Kevin Mitnick Famous Social Engineer Hacker • Went to prison for hacking • Became ethical hacker "People are generally helpful, especially to someone who is nice, knowledgeable or insistent. "
Kevin Mitnick - Art of Deception: • "People inherently want to be helpful and therefore are easily duped" • "They assume a level of trust in order to avoid conflict" • "It's all about gaining access to information that people think is innocuous when it isn't" • Here a nice voice on the phone, we want to be helpful • Social engineering cannot be blocked by technology alone
Examples of Social Engineering • Kevin Mitnick talks his way into central Telco office o Tells guard he will get a new badge o Pretend to work there, give manager name from another branch o Fakes a phone conversation when caught • Free food at Mc. Donalds
Live Example • Convinced friend that I would help fix their computer • People inherently want to trust and will believe someone when they want to be helpful • Fixed minor problems on the computer and secretly installed remote control software • Now I have total access to their computer through ultravnc viewer
Types of Social Engineering • Quid Pro Quo o Something for something • Phishing o Fraudulently obtaining private information • Baiting o Real world trojan horse • Pretexting o Invented Scenario • Diversion Theft o A con
Quid Pro Quo • Something for Something o Call random numbers at a company, claiming to be from technical support. o Eventually, you will reach someone with a legitamite problem o Grateful you called them back, they will follow your instructions o The attacker will "help" the user, but will really have the victim type commands that will allow the attacker to install malware
Phishing • Fraudulently obtaining private information o Send an email that looks like it came from a legitimate business o Request verification of information and warn of some consequence if not provided o Usually contains link to a fraudulent web page that looks legitimate o User gives information to the social engineer § Ex: Ebay Scam
Phishing continued • Spear Fishing o Specific phishing § Ex: email that makes claims using your name • Vishing o Phone phishing o Rogue interactive voice system § Ex: call bank to verify information
Baiting • Real world Trojan horse o Uses physical media o Relies on greed/curiosity of victim o Attacker leaves a malware infected cd or usb drive in a location sure to be found o Attacker puts a legitimate or curious lable to gain interest o Ex: "Company Earnings 2009" left at company elevator § Curious employee/Good samaritan uses § User inserts media and unknowingly installs malware
Pretexting • Invented Scenario o Prior Research/Setup used to establish legitimacy § Give information that a user would normally not divulge o This technique is used to impersonate § Authority ect § Using prepared answers to victims questions § Other gathered information o Ex: Law Enforcement § Threat of alleged infraction to detain suspect and hold for questioning
Pretexting Real Example: • Signed up for Free Credit Report • Saw Unauthorized charge from another credit company o Called to dispute charged and was asked for Credit Card Number § They insisted it was useless without the security code o Asked for Social Security number • Talked to Fraud Department at my bank
Diversion Theft • A Con o Persuade deliver person that delivery is requested elsewhere - "Round the Corner" o When deliver is redirected, attacker pursuades delivery driver to unload delivery near address o Ex: Attacker parks security van outside a bank. Victims going to deposit money into a night safe are told that the night safe is out of order. Victims then give money to attacker to put in the fake security van o Most companies do not prepare employees for this type of attack
Weakest Link? • No matter how strong your: o Firewalls o Intrusion Detection Systems o Cryptography o Anti-virus software • You are the weakest link in computer security! o People are more vulnerable than computers • "The weakest link in the security chain is the human element" -Kevin Mitnick
Ways to Prevent Social Engineering Training • User Awareness o User knows that giving out certain information is bad • Military requires Cyber Transportation to hold o Top Secret Security Clearance o Security Plus Certification • Policies o Employees are not allowed to divulge private information o Prevents employees from being socially pressured or tricked
Ways to Prevent Social Engineering Cont. . • 3 rd Party test - Ethical Hacker o Have a third party come to your company and attempted to hack into your network o 3 rd party will attempt to glean information from employees using social engineering o Helps detect problems people have with security • Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about internal information • Do not provide personal information, information about the company(such as internal network) unless authority of person is verified
General Saftey • Before transmitting personal information over the internet, check the connection is secure and check the url is correct • If unsure if an email message is legitimate, contact the person or company by another means to verify • Be paranoid and aware when interacting with anything that needs protected o The smallest information could compromise what you're protecting
Social Engineering: A Test of Your Common Sense By Frederick Gallegos, CISA, CGFM, CDE Computer Info Systems Dept
Social Engineering • Monday morning, 6 am; the electric rooster is telling you it's time to start a new work week. A shower, some coffee, and you're in the car and off. On the way to work you're thinking of all you need to accomplished this week. • Then, on top of that there's the recent merger between your company and a competitor. One of your associates told you, you better be on your toes because rumors of layoff's are floating around.
Social Engineering • You arrive at the office and stop by the restroom to make sure you look your best. You straighten your tie, and turn to head to your cube when you notice, sitting on the back of the sink, is a CD-ROM. Someone must have left this behind by accident. You pick it up and notice there is a label on it. The label reads "2005 Financials & Layoff's". You get a sinking feeling in your stomach and hurry to your desk. It looks like your associate has good reasons for concern, and you're about to find out for your self.
And so • The Game Is In Play: People Are The Easiest Target You make it to your desk and insert the CD-ROM. You find several files on the CD, including a spreadsheet which you quickly open. The spreadsheet contains a list of employee names, start dates, salaries, and a note field that says "Release" or "Retain". You quickly search for your name but cannot find it. In fact, many of the names don't seem familiar. Why would they, this is pretty large company, you don't know everyone. Since your name is not on the list you feel a bit of relief. It's time to turn this over to your boss. Your boss thanks you and you head back to your desk.
Let's Take A Step Back In Time • The CD you found in the restroom, it was not left there by accident. It was strategically placed there by me, or one of Security Consulting employees. • You see, a firm has been hired to perform a Network Security Assessment on your company. • In reality, they have been contracted to hack into your company from the Internet and have been authorized to utilize social engineering techniques.
Bingo - Gotcha • The spreadsheet you opened was not the only thing executing on your computer. • The moment you open that file you caused a script to execute which installed a few files on your computer. • Those files were designed to call home and make a connection to one of our servers on the Internet. Once the connection was made the software on the Security firms servers responded by pushing (or downloading) several software tools to your computer. • Tools designed to give the team complete control of your computer. Now they have a platform, inside your company's network, where they can continue to hack the network. And, they can do it from inside without even being there.
This is what we call a 180 degree attack. • • • Meaning, the security consulting team did not have to defeat the security measures of your company's firewall from the Internet. You took care of that for us. Many organizations give their employees unfettered access (or impose limited control) to the Internet. Given this fact, the security firm devised a method for attacking the network from within with the explicit purpose of gaining control of a computer on the private network. All we had to do is get someone inside to do it for us.
Welcome to Social Engineering • What would you have done if you found a CD with this type of information on it? • Yes it is people who are the weakest link in any security system and Social Engineering Exploits that ---

Phisher Site Basics • Thief sends e-mail to customer claiming to be a legitimate company which has lost the customer’s personal information • Customer reads e-mail and goes to fake website • Customer enters credit card or other personal information on website • Thief steals personal information
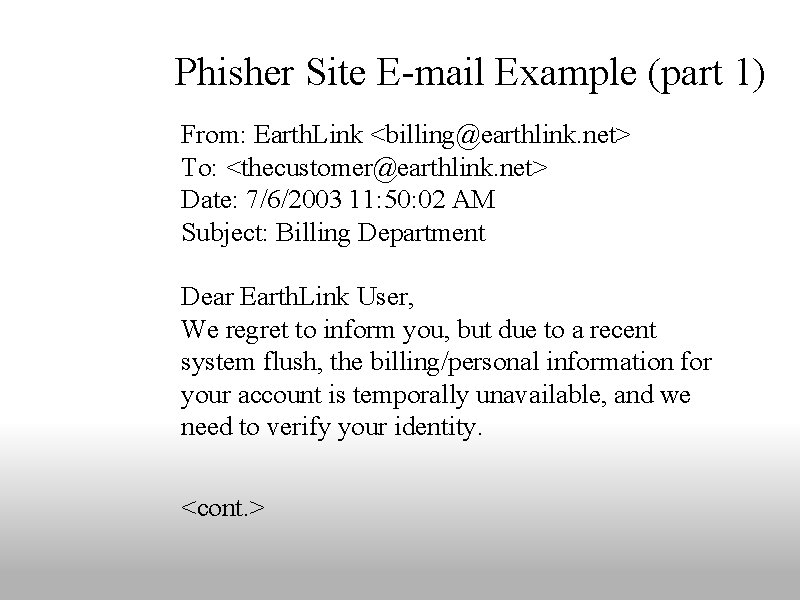
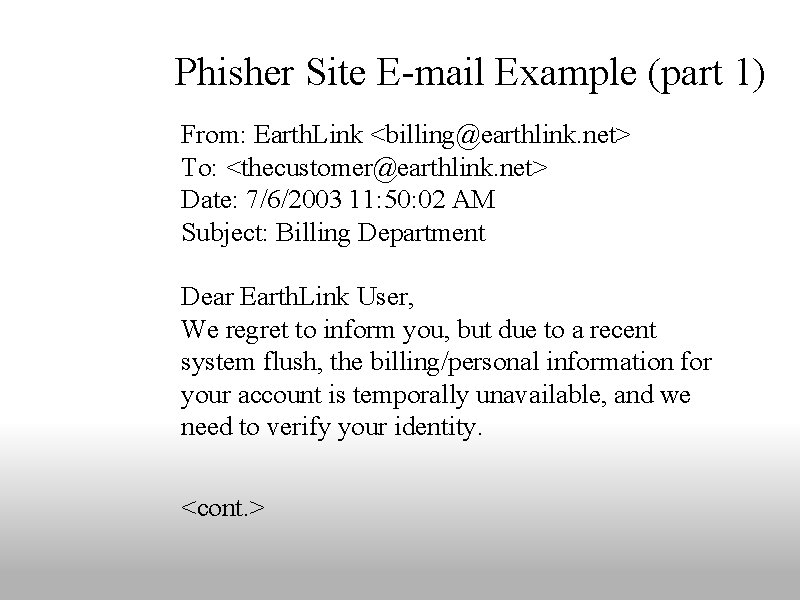
Phisher Site E-mail Example (part 1) From: Earth. Link <billing@earthlink. net> To: <thecustomer@earthlink. net> Date: 7/6/2003 11: 50: 02 AM Subject: Billing Department Dear Earth. Link User, We regret to inform you, but due to a recent system flush, the billing/personal information for your account is temporally unavailable, and we need to verify your identity. <cont. >
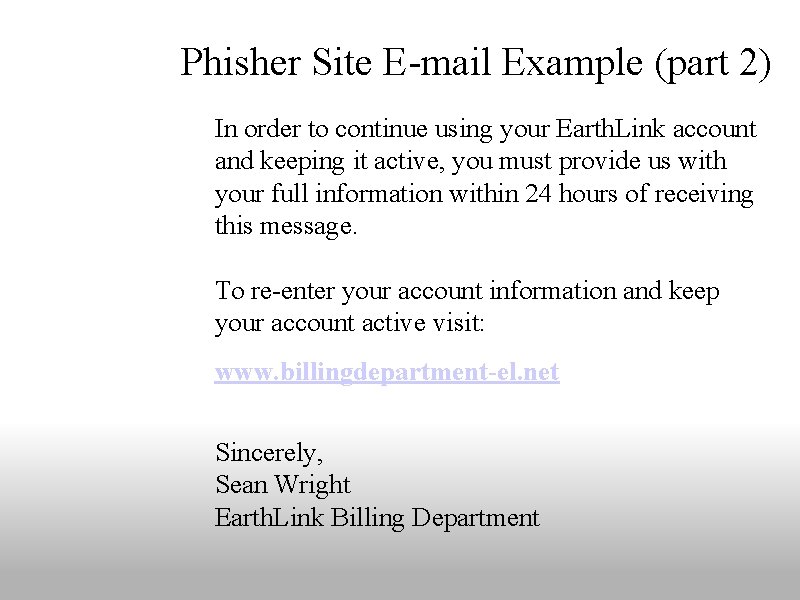
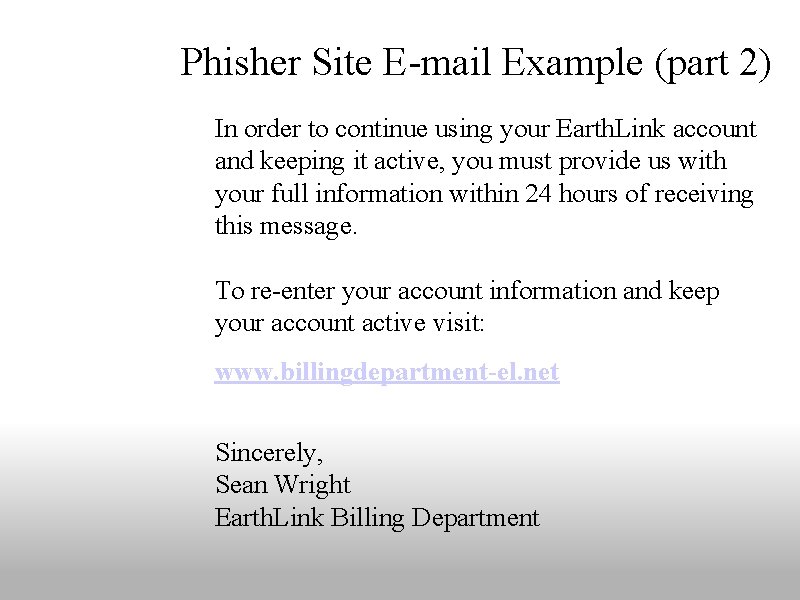
Phisher Site E-mail Example (part 2) In order to continue using your Earth. Link account and keeping it active, you must provide us with your full information within 24 hours of receiving this message. To re-enter your account information and keep your account active visit: www. billingdepartment-el. net Sincerely, Sean Wright Earth. Link Billing Department
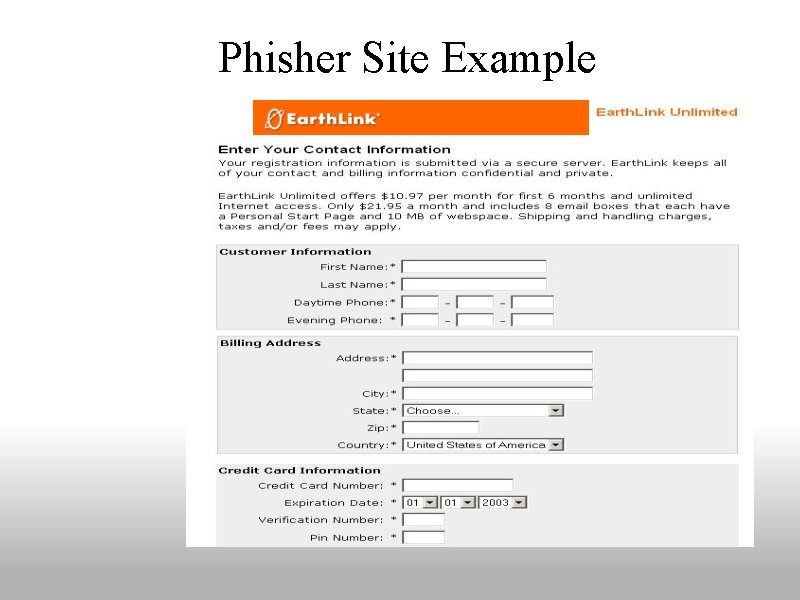
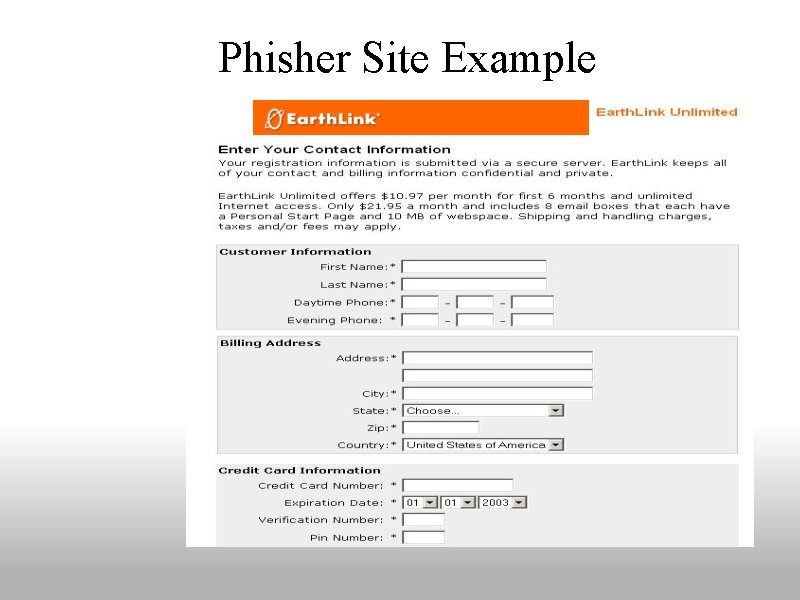
Phisher Site Example

The Real Earth. Link Web Site
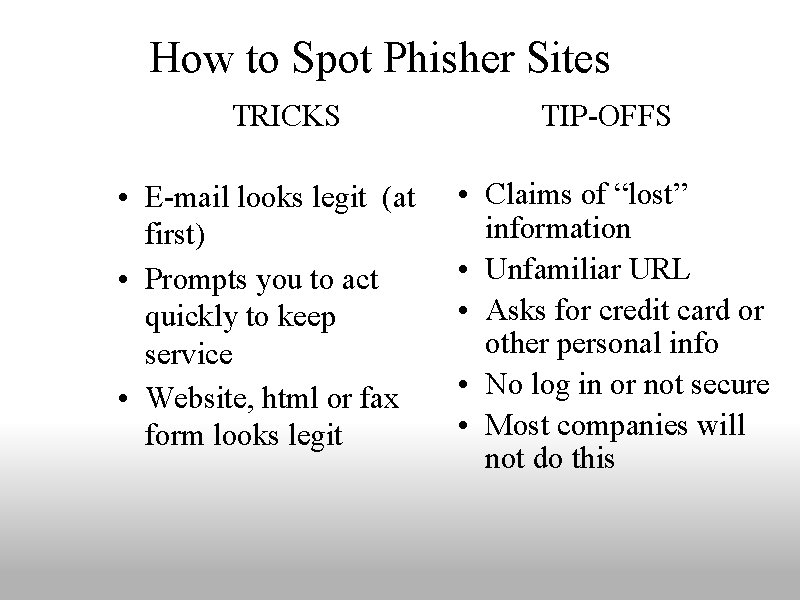
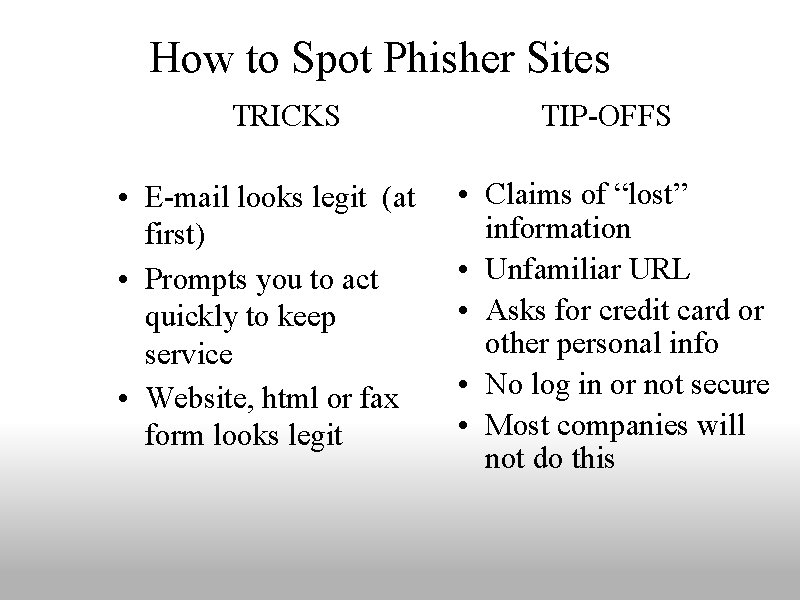
How to Spot Phisher Sites TRICKS • E-mail looks legit (at first) • Prompts you to act quickly to keep service • Website, html or fax form looks legit TIP-OFFS • Claims of “lost” information • Unfamiliar URL • Asks for credit card or other personal info • No log in or not secure • Most companies will not do this
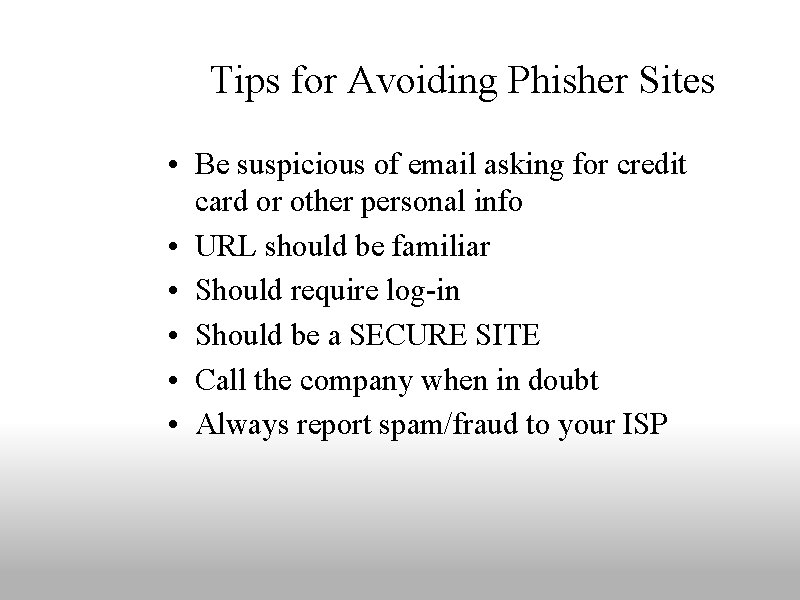
Tips for Avoiding Phisher Sites • Be suspicious of email asking for credit card or other personal info • URL should be familiar • Should require log-in • Should be a SECURE SITE • Call the company when in doubt • Always report spam/fraud to your ISP
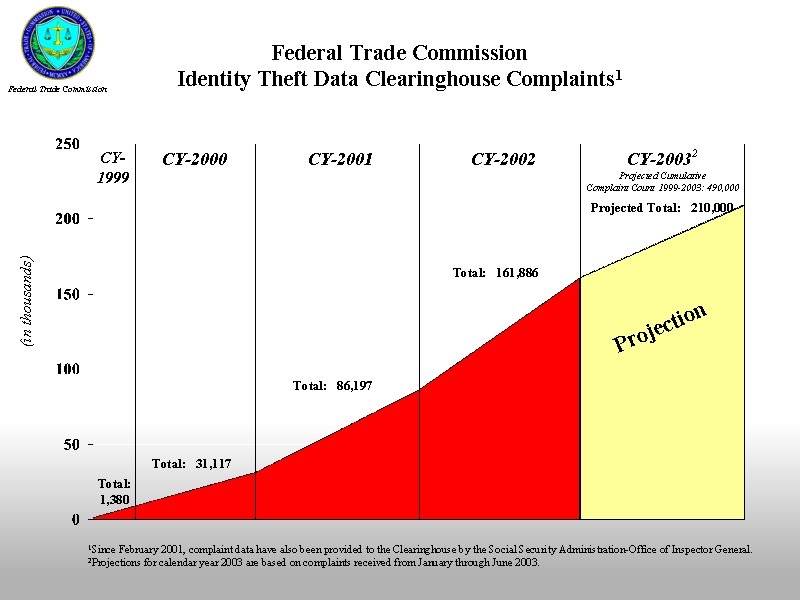
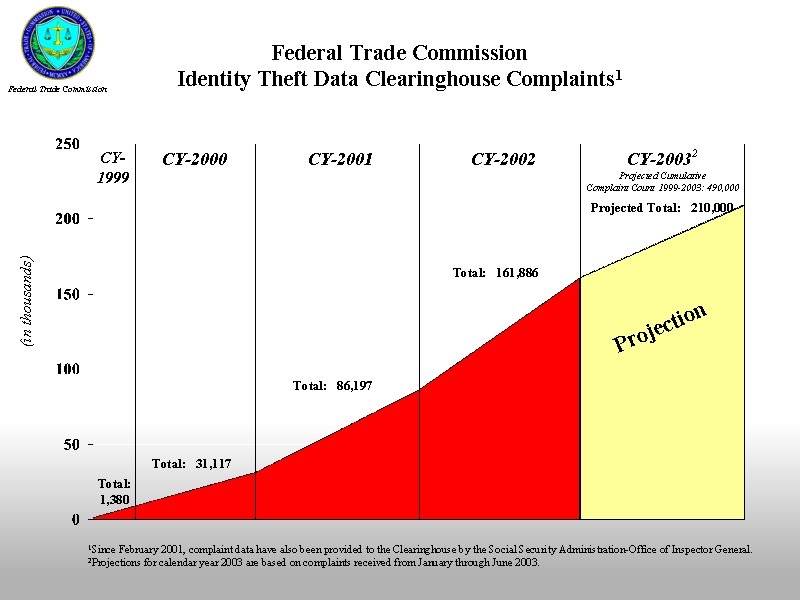
Federal Trade Commission Identity Theft Data Clearinghouse Complaints 1 Federal Trade Commission CY 1999 CY-2000 CY-2001 CY-2002 CY-20032 Projected Cumulative Complaint Count 1999 -2003: 490, 000 (in thousands) Projected Total: 210, 000 Total: 161, 886 n o i t jec Pro Total: 86, 197 Total: 31, 117 Total: 1, 380 1 Since February 2001, complaint data have also been provided to the Clearinghouse by the Social Security Administration-Office of Inspector General. for calendar year 2003 are based on complaints received from January through June 2003. 2 Projections
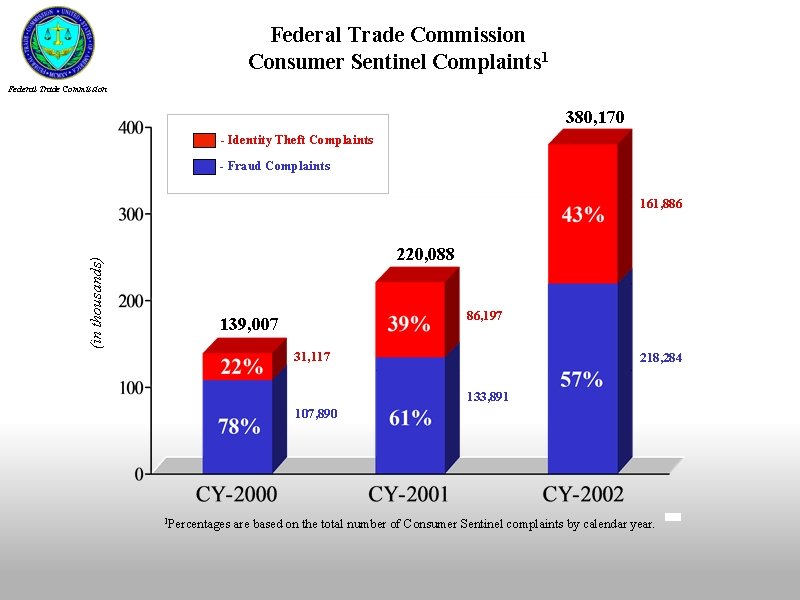
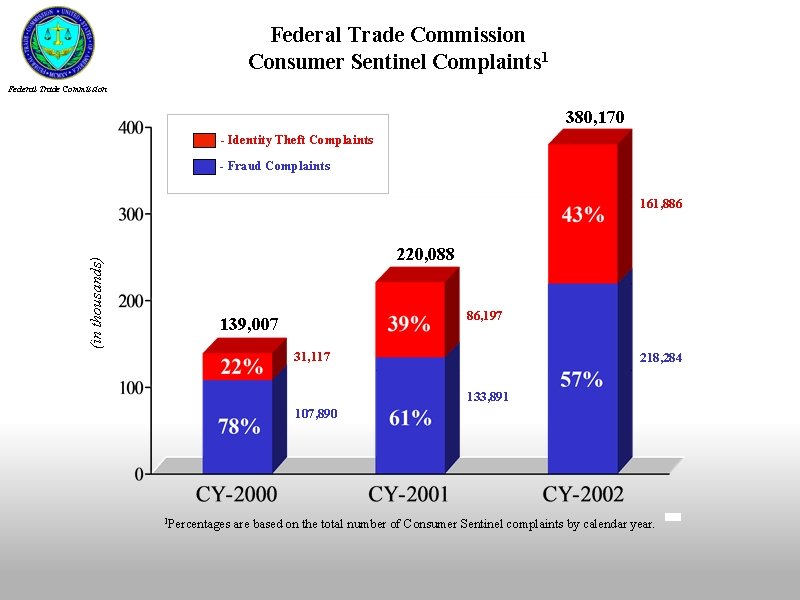
Federal Trade Commission Consumer Sentinel Complaints 1 Federal Trade Commission 380, 170 - Identity Theft Complaints - Fraud Complaints (in thousands) 161, 886 220, 088 86, 197 139, 007 31, 117 218, 284 133, 891 107, 890 1 Percentages are based on the total number of Consumer Sentinel complaints by calendar year.

Federal Trade Commission 1 -877 -FTC-HELP www. consumer. gov/sentinel 1 -877 -IDTHEFT www. consumer. gov/idtheft

And Another • The easiest way to break into any computer system is to use a valid username and password and the easiest way to get that information is to ask someone for it.
The Beginning • Like many hacking techniques, social engineering got its start in attacks against the telephone company. The hacker (or phone phreaks, as they used to be called) would dial-up an operator and by using the right jargon, convince him or her to make a connection or share some information that should not have been shared.
In Reality • social engineering is probably as old as speech, and goes back to the first lie. • It is still successful today because people are generally helpful, especially to someone who is nice, knowledgeable, and / or insistent. • No amount of technology can protect you against a social engineering attack.
So How Do You Protect Yourself from Yourself? • Recognizing an Attack – You can prepare your organization by teaching people how to recognize a possible social engineering attack. Do we have a Cyber Security & Ethics 101 Class? • Prevent a successful attack – You can prepare a defense against this form of social engineering by including instructions in your security policy for handling it.
So How Do You Protect Yourself from Yourself? • Create a response plan – Your response plan should include instructions on how to deal with inquiries relating to passwords or other classified information. • Implement and Monitor the response plan and continue to reinforce with Training
Target And Attack • The basic goals of social engineering are the same as hacking in general: to gain unauthorized access to systems or information in order to commit fraud, network intrusion, industrial espionage, identity theft, or simply to disrupt the system or network. • Typical targets include telephone companies and answering services, big-name corporations and financial institutions, military and government agencies, and hospitals. • The Internet boom had its share of industrial engineering attacks in start-ups as well, but attacks generally focus on larger entities.
And Another • One morning a few years back, a group of strangers walked into a large shipping firm and walked out with access to the firm’s entire corporate network. • How did they do it? By obtaining small amounts of access, bit by bit, from a number of different employees in that firm. First, they did research about the company for two days before even attempting to set foot on the premises.
And so on… • For example, they learned key employees’ names by calling HR. Next, they pretended to lose their key to the front door, and a man let them in. Then they "lost" their identity badges when entering the third floor secured area, smiled, and a friendly employee opened the door for them.
And so on… • The strangers knew the CFO was out of town, so they were able to enter his office and obtain financial data off his unlocked computer. • They dug through the corporate trash, finding all kinds of useful documents. • They asked a janitor for a garbage pail in which to place their contents and carried all of this data out of the building in their hands. • The strangers had studied the CFO's voice, so they were able to phone, pretending to be the CFO, in a rush, desperately in need of his network password. From there, they used regular technical hacking tools to gain superuser access into the system.
Common Techniques • • • Social Engineering by Phone Dumpster Diving On-line Social Engineering Persuasion Reverse Social Engineering And many more….
Defining The Term "Social Engineering" • In the world of computers and technology, social engineering is a technique used to obtain or attempt to obtain secure information by tricking an individual into revealing the information. • Social engineering is normally quite successful because most targets (or victims) want to trust people and provide as much help as possible. • Victims of social engineering typically have no idea they have been conned out of useful information or have been tricked into performing a particular task. • The prey is not just you but your children and elders as well
A Challenge to the CSU • This is the 21 st Century The Time of Cyber. Space • Why is their No Formal GE Requirement for Cyber. Security and Ethics which can not only be taught at the CSU level but the CC level as well? • Why don’t we extend this education to K-12 and Senior Centers as well?
Mt. SAC and Cal Poly Efforts • NSF Grant Project – Establishment of a Regional Information Systems Security Center (RISSC see http: //rissc. mtsac. edu/RISSC_NEW/default. asp ) • Cal Poly’s Participation in the Title V Grant and development of Network Security curriculum • Cal Poly Pomona’s Establishment of a Center for Information Assurance (see http: //www. bus. csupomona. edu/cfia. asp )
Please join US for • Information Assurance Symposium Building Information Assurance Capacity and Improving Infrastructure at Minority Serving Institutions December 8 - 10, 2005 Cal Poly Pomona 8: 30 a. m. - 5: 00 p. m.
Contribute to: • Information Sharing • Curriculum Development • Awareness, Knowledge and Development of initiatives to help others around us be better at practicing good security techniques • Our thanks to Educause, ISACA, ISSA, IIA and HTCIA for their support
Conclusion • What is Social Engineering? o Manipulate people into doing something, rather than by breaking in using technical means • Types of Social Engineering o Quid Pro Quo o Phishing o Baiting o Pretexting o Diversion Theft • Ways to prevent Social Engineering
Questions?
Social Engineering Clips Animation: http: //www. youtube. com/watch? v=Y 6 tb. UNj. L 0 No Live Action: http: //www. youtube. com/watch? v=8 TJ 4 XOv. Y 7 II&feature=relate d