Ethics of Ethical Hacking Source Grey Hat Hacking
- Slides: 41
Ethics of Ethical Hacking Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 1
Ethics of Ethical Hacking • Role of Ethical hacking in Today’s World • Vulnerability Assessments versus Penetration testing • How Hacking tools are used by security professionals • General steps of hackers and security professionals • Ethical issues between a white hat and a black hat hacker Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 2
Motivation • Why do militaries all over the world study their enemy’s tactics. Tools, strategies, technologies? • The more you know what the enemy is up to, the better idea you have as to what protection mechanisms you need to put into place to defend yourself. Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 3
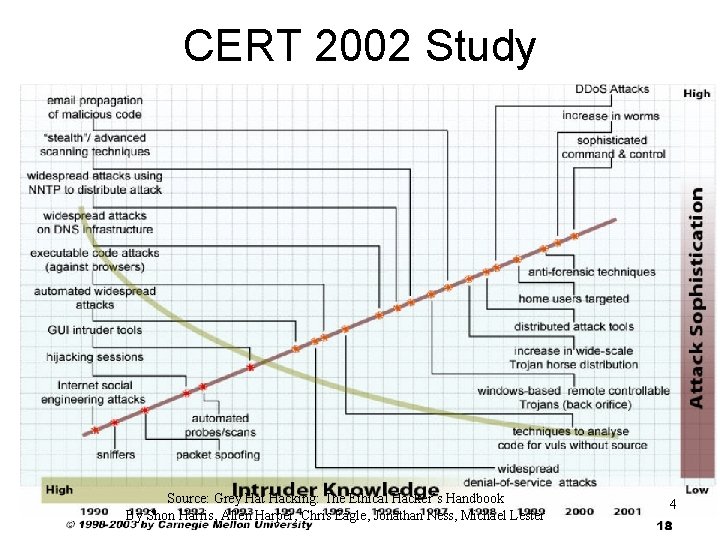
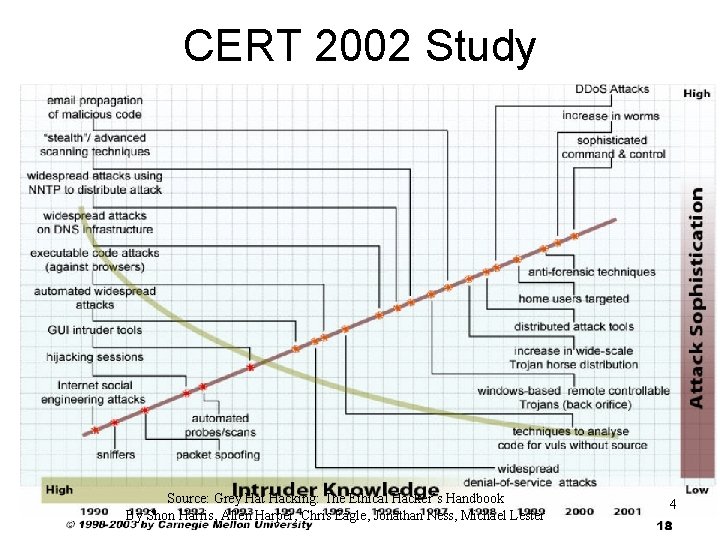
CERT 2002 Study Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 4
Vulnerability Assessment versus Penetration Testing • Vulnerability assessment uses a network scanner to probe the parts and services on a range of IP addresses and also looks at operating system, application software versions, patch levels, etc. • Penetration testing tests the vulnerabilities to determine actual threat and risk of the vulnerability. Try to break into the system. Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 5
Controversy of Hacking Books and Classes • Malicious attackers use the same toolset as used by security professionals. • What we are really doing in part is security professional tool set education Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 6
What is Network Security? • Security is much larger than just packets, firewalls, and hackers. Security includes: – – – Policies and procedures Liabilities and laws Human behavior patterns Corporate security programs and implementation Technical aspects- firewalls, intrusion detection systems, proxies, encryption, antivirus software, hacks, cracks, and attacks • Understanding hacking tools and how attacks are carried out is only one piece of the puzzle. Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 7
Common Steps for Attackers • Reconnaissance – Intelligent work of obtaining information either actively or passively – Examples: • Passively: Sniffing Traffic, eaves dropping • Actively: Obtaining data from American Registry for Internet Numbers (ARIN), whois databases, web sites, social engineering Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 8
Common Steps for Attackers • Scanning – Identifying systems that are running and services that are active on them – Examples: Ping sweeps and port scans Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 9
Common Steps for Attackers • Gaining Access – Exploiting identified vulnerabilities to gain unauthorized access – Examples: Exploiting a buffer overflow or brute forcing a password and logging onto a system Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 10
Common Steps for Attackers • Maintaining Access – Uploading malicious software to ensure reentry is possible – Example: Installing a backdoor on a system Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 11
Common Steps for Attackers • Covering Tracks – Carrying out activities to hide one’s malicious activities – Example: Deleting or modifying data in a system and its application logs Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 12
Where do Attackers get the Most Traction? • Flaws within software code is the root of the problem of successful attacks and exploits • Security does not like complexity • The more complex software gets, the harder it is to properly predict how it will react in all possible scenarios thus making it much harder to secure • Windows XP is approximately 40 million lines of code • Linux is approximately 2 million lines of code • Estimate in industry: 5 to 10 bugs per 1, 000 lines of code => windows XP has approximately 200, 000 bugs • With object-oriented language applications and operating systems using each other’s code, DLLs are installed and shared, many applications communicate with each other => Operating Systems cannot control this flow and provide protection against possible compromises Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 13
Majority of Successful Attacks Occur Because: • Software vendors do not integrate security into the design and specification phases • Programmers have not been properly taught how to code securely • Vendors are not being held liable for faulty code • Consumers are not willing to pay more for properly developed and tested code Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 14
Novice versus Advanced • Novice ethical hacker will use tools/techniques developed by others • A more advanced ethical hacker will not only depend upon other people’s tools but will have the skill set and understanding to develop their own tools/techniques Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 15
Ethical Hacking and the Legal System • Outline: – Laws dealing with computer crimes and what they address – Malware and insider threats companies face today – Civil versus criminal approaches in the court system – Federal versus state laws and their use in prosecution • See www. cyberspacelaw. org Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 16
USA Laws • 18 USC 1029: Fraud and related activity in connection with access devices • 18 USC 1030: Fraud and related activity in connection with computers • 18 USC 1326: Communication lines, stations, or systems • 18 USC 2510: Wire and electronic communications interception and interception of oral communications • 18 USC 2701: Stored wire and electronic communications and transactional records access Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 17
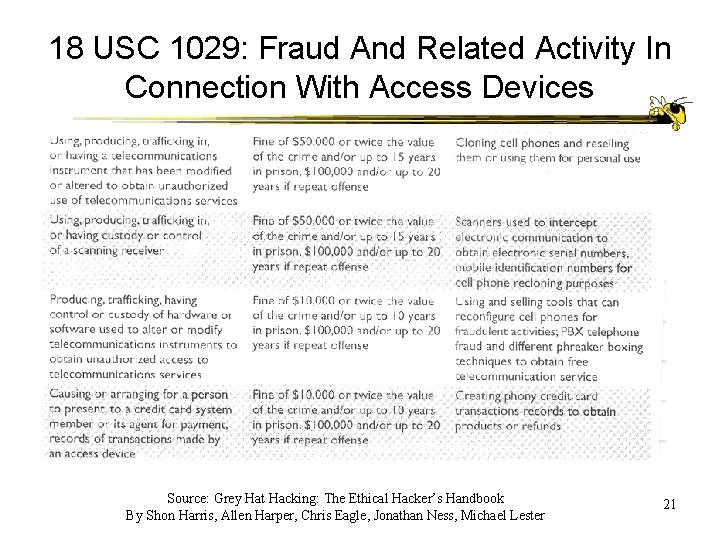
18 USC 1029: Fraud And Related Activity In Connection With Access Devices • “Access Device Statute” • Access device – type of application or piece of hardware that is specifically created to generate access credentials (Passwords, Credit card numbers, long distance telephone service access codes, PINs, etc. ) for the purpose of unauthorized access • Tools that generate large volumes of credit card numbers are “credit master” and “credit wizard”. Trial and error used. Defense now is to have an additional 3 digit identifier in addition to 16 digit credit card number Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 18
Example “Access Device” Crime • 2003 Lowe’s Retail store • Three crackers circumvented a wireless network at a Lowe’s store in Michigan to gain entrance to central computer system in North Carolina • Installed programs in several retail stores networks across country to capture credit card numbers from customers making a purchase • Charges: conspiracy, wire fraud, computer fraud, unauthorized computer access, intentional transmission of computer code, attempted possession of unauthorized access devices Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 19
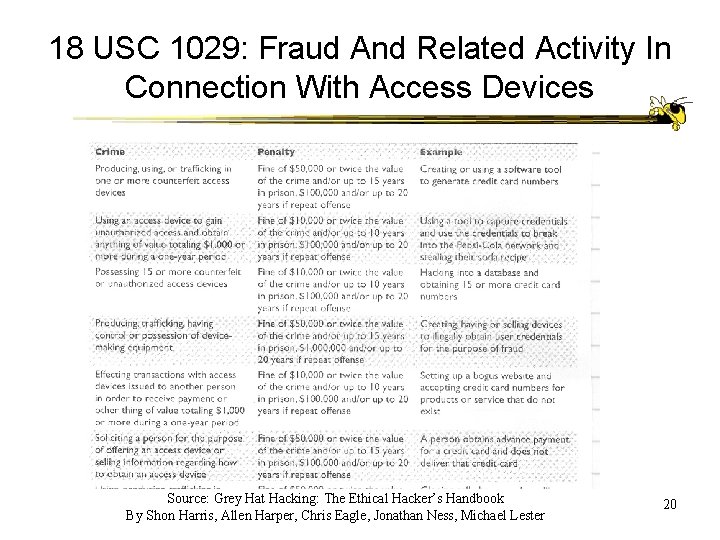
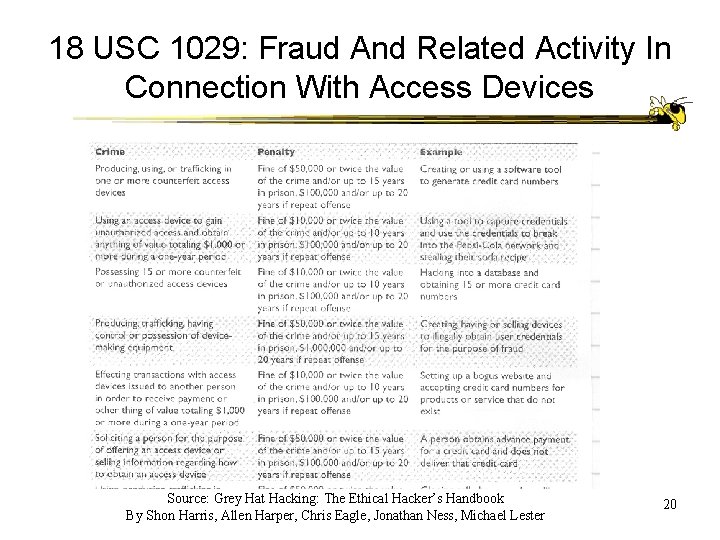
18 USC 1029: Fraud And Related Activity In Connection With Access Devices Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 20
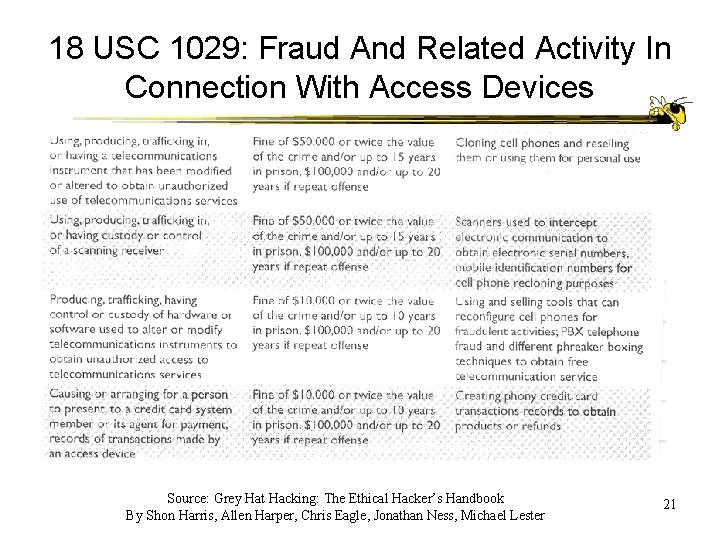
18 USC 1029: Fraud And Related Activity In Connection With Access Devices Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 21
18 USC 1030: Fraud And Related Activity In Connection With Computers • Computer Fraud and Abuse Act (CFAA) deals with unauthorized access to government and financial institution systems Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 22
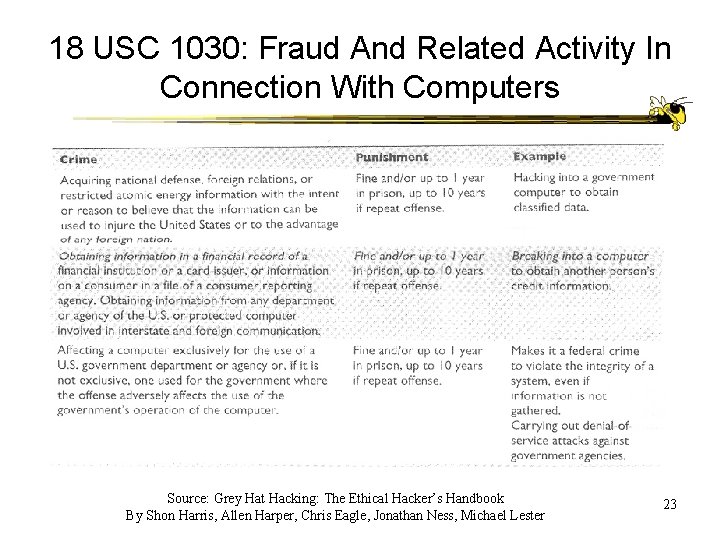
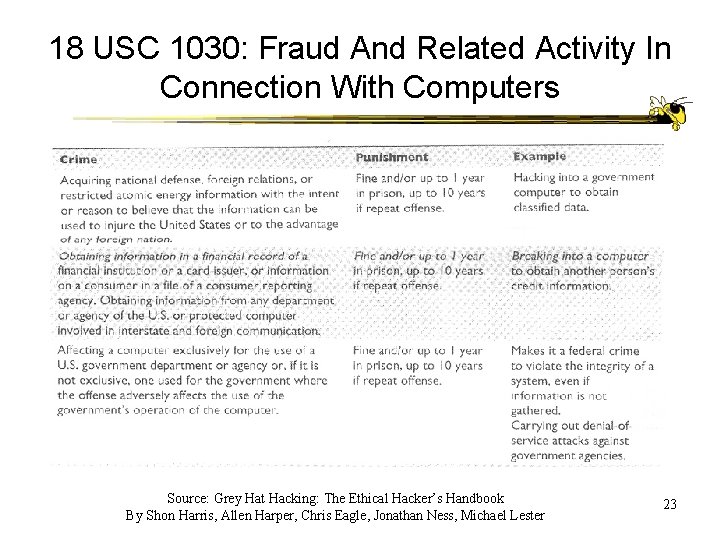
18 USC 1030: Fraud And Related Activity In Connection With Computers Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 23
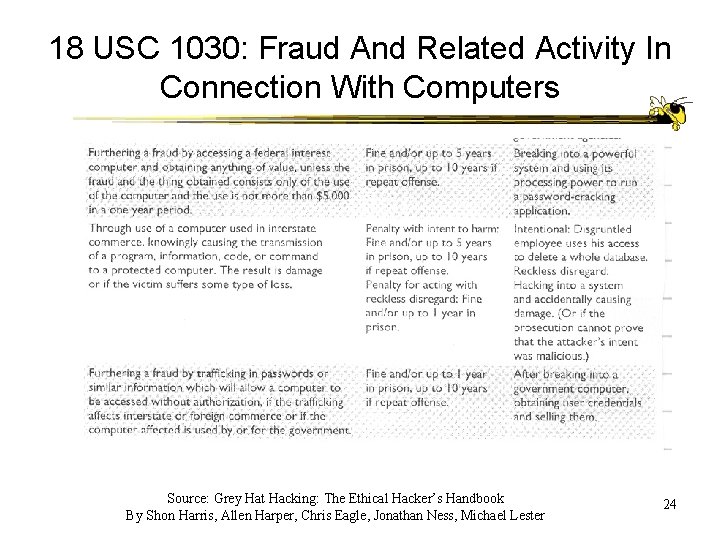
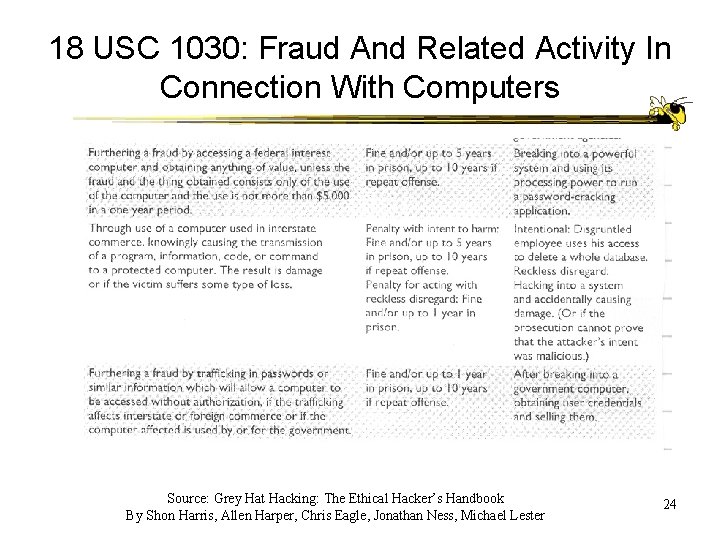
18 USC 1030: Fraud And Related Activity In Connection With Computers Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 24
18 USC 1030: Fraud And Related Activity In Connection With Computers • “Protected Computer” – computer used by US government, financial institutions, and any system used in interstate or foreign commerce or communications => this means all computers not just government computers • FBI given responsibility for cases with national security, financial institutions, organized crime. • Secret Service – crimes pertaining to treasury department and any other crime not covered by FBI jurisdiction including “critical infrastructure” • Computer Fraud and Abuse states if someone accesses a computer in an unauthorized manner or exceeds one’s access rights, they can be found guilty of a federal crime • Example: several Cisco employees exceeded their system rights and issued themselves almost 8 million shares of Cisco stock Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 25
18 USC 1030: Fraud And Related Activity In Connection With Computers • Worms and Viruses • Computer Fraud and Abuse Act covers development and release of malware • Example: web-TV attack: hacker sent an email to web-TV subscribers that reset their internet dial in number for TV schedules to 911. • Max penalty is 10 years in prison and $250, 000 fine Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 26
18 USC Sections 2510 and 2701 • Wire and Electronic Communications Interception • Stored Wire and Electronic Communications and Transactional Records Access • Electronic Communication Privacy Act (ECPA) – Wiretap Act – Stored Communications Act Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 27
18 USC Sections 2510 and 2701 • Wiretap act states there cannot be any intentional “interception” of wire, oral or electronic communication in an illegal manner • Interception- lawyers asked what does this word mean? Only while being transmitted? What about stored? • Lawyers decided “intercept” only means when data is traveling, not when stored +> thus need for Stored Communications Act Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 28
18 USC Sections 2510 and 2701 • Application of Electronic Communication Privacy Act : – Some people did not like web cookies. These people argued cookies obtained by a company violated stored communications act because it is info stored on your hard drive. Different websites can be in joint marketing agreements and share browsing and buying habit information with each other – Also claimed this violated the wiretap law because the company intercepted the user’s communication to other sites – But Electronic Communication Privacy Act states if one of the parties of the communications authorizes these types of interceptions, then laws not broken Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 29
Digital Millennium Copyright Act (DMCA) • Does not allow one to tamper with and break an access control mechanism that are put into place to protect an item that is protected under the copyright law. • If item is not copyrighted but you have access control mechanism that someone breaks, DCMA does not apply! • There does not need to be any infringement upon the item that is protected by the copyright law for prosecution to take place • If someone reverse-engineers some type of control and does nothing with actual content, still can be prosecuted. Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 30
Cyber Security Enhancement Act of 2002 • July 2002 House of Representatives voted to put stricter laws into place. • If an attackers carries out a crime that could result in the bodily harm or death of another, can get life in prison • Act also allows service providers to report suspicious behavior and not risk consumer litigation. Allows serve providers to work with law officials • Reports are exempt from freedom of information act Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 31
Georgia Institute of Technology • Computer and Network Usage Policy § Available for all students and faculty § http: //www. oit. gatech. edu/information_securi ty/policy/usage/ • Authorize users and uses • Privileges for individuals • User Responsibilities § Access to Facilities and Information ECE 4112 - Internetwork Security 32
GIT Computer and Network Usage Policy 4. 6. Attempts to circumvent security Users are prohibited from attempting to circumvent or subvert any system. s security measures. This section does not prohibit use of security tools by personnel authorized by OIT or their unit. 4. 6. 1. Decoding access control information Users are prohibited from using any computer program or device to intercept or decode passwords or similar access control information. 4. 6. 2. Denial of service Deliberate attempts to degrade the performance of a computer system or network or to deprive authorized personnel of resources or access to any Institute computer system or network are prohibited. 4. 6. 3. Harmful activities are prohibited. Examples include IP spoofing; creating and propagating viruses; port scanning; disrupting services; damaging files; or intentional destruction of or damage to equipment, software, or data. ECE 4112 - Internetwork Security 33
What if? • A Georgia Tech student uses their personal PC and the school’s network to do a port scan on a commercial web site. • A Georgia Tech student uses their personal PC and a commercial ISP to do a port scan on a commercial web site. • A Georgia Tech student sends a “spoofed mail” from the school account that appears to come from another user. • A Georgia Tech student uses a school computer and password guessing software to access and crack the administrator password. • A Georgia Tech student discovers that another user failed to log off when departing. The student uses the account to send an inflammatory email to the department chair. ECE 4112 - Internetwork Security 34
Proper and Ethical Disclosure • Outline: • Different points of view pertaining to vulnerability disclosure • Evolution and pitfalls of vulnerability discovery and reporting procedures • CERTs approach to work with ethical hacker and vendors • Full disclosure policy and how it differs between CERT and the Organization for Internet Safety (OIS) Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 35
Black hat versus Grey Hat • Ethical hackers must understand follow proper methods of disclosing vulnerabilities to software vendors • If an individual finds a vulnerability and exploits it or tells others how to attack => Black Hat • If a different person uncovers a vulnerability, does not illegally exploit it, tell others how to, and works with the vendor to fix it => Grey Hat Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 36
Public Disclosure • Issue of public disclosure is controversial because consumer and software vendor view it differently • Many think security vulnerabilities should be disclosed as a matter of principal. Some consumer’s think the only way to get quick results from a large software vendor is to pressure it to fix the problem by threatening to make the information public. • Vendors think details of flaw will help hackers exploit the vulnerability. The release of information can hurt the reputation of the company • Several organizations have created policies, guidelines, and general suggestions on how to handle software vulnerability disclosures. Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 37
History of Disclosure • Mailing list Bugtraq – easy access to ways of exploiting vulnerabilities • In 2002 Atlanta’s Internet Security Systems (ISS) initiated its own disclosure policy. Vulnerability details would be released to paying subscribers one day after vendor notified Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 38
CERT Disclosure Policy • CERT coordination center CERT/CC federally funded research and development center focused on Internet security and related issues – Full disclosure will be announced to public within 45 days of being reported to CERT/CC – CERT/CC will notify vendor immediately so a solution may be found – Along with description of problem, CERT/CC will forward name of finder if desired – During 45 day period CERT/CC will update reporter on current status Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 39
Full Disclosure Policy (Rain Forest Puppy Policy) • Rain Forest Puppy is a Hacker with a long history of successfully and unsuccessfully working with vendors • Disclosure Policy: – – – Date of contact is when originator EMAILS the software vendor Software vendor must acknowledge the contact within 5 days Originator will assist vendor in reproducing problem Vendor status reports every 5 days Vendor will credit originator Originator and vendor make disclosure statements in conjunction Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 40
Organization for Internet Safety (OIS) • Group of founding companies @stake, Bindview corporation, the SCO group, Foundstone, Guardent, Internet Security Systems, Microsoft, Oracle, SGI, and Symantec • Policy: – Reduce the risk of software vulnerabilities by providing an improved method of identification, investigation, and resolution – Improve overall engineering quality of software by tightening security placed upon end product – Includes • Discovery, notification, validation, investigation (shared code products issues), findings (confirmation/disproof), resolution, time frame, release (patches, maintenance updates, future product versions) Source: Grey Hat Hacking: The Ethical Hacker’s Handbook By Shon Harris, Allen Harper, Chris Eagle, Jonathan Ness, Michael Lester 41