5 Basics of Hacking Ethical hacking is the
5 -Basics of Hacking Ethical hacking is the science of testing computers and network for security vulnerabilities and plugging the holes found before the unauthorized people get a chance to exploit them. Or It is identifying weakness in computer systems and/or computer networks and coming up with countermeasures that protect the weaknesses.
• The intent of ethical hacking is to discover vulnerabilities from a malicious attacker’s viewpoint to better secure systems. • It’s on going security improvements. • Ethical hacking is also known as penetration testing, Intrusion testing, Red teaming.
Social engineering cycle: Social engineering is the art of exploiting the human elements to gain access to unauthorized resources. Or Social engineering is defined as the exploitation of the trusting nature of human beings to gain information for malicious purposes. Social engineering cycle is 1. Gather information. 2. Plan attack 3. Acquire tools 4. Attack 5. Use acquired knowledge
Hackers A Hacker is a person who finds and exploits the weakness in computer systems and/or networks to gain access. Hackers are problem solvers. They extract the problem and sorting out a solution. An ethical hacker is a security professional who applies their hacking skills for defensive purposes on behalf of the owners of information systems.
How hackers beget ethical hackers Hacker is word that has two 2 meaning: 1. Hacker is a someone who likes to tamper with software or electronic systems. Hackers enjoy exploring and learning how computer systems operate. They love discovering new ways to work electronically. 2. Hacker has taken on a new meaning- someone who maliciously breaks into systems for personal gain. Technically , these criminals are crackers(criminal hackers). Crackers break into systems with malicious intent.
1. 2. 3. 4. Ethical hacking versus auditing It involves comparing a company’s security policies to what’s actually taking place. Security audits are usually based on checklists In many cases, it might not be very technical. The intent of security auditing is to validate that security controls exist using a risk based approach.
1. 2. 3. 4. Rules abide by ethical hackers: Get written permission from the owner before hacking. Protect the privacy of the organization. Transparently report. Inform hardware and software vendors of the identified weaknesses.
Classification of hackers according to their intent 1. Ethical hacker(white hat) 2. Cracker(black hat) 3. Gray hat 4. Script kiddies : non-skilled person who gain access using already made tools 5. Hacktivist : who hacks by sending social, religious and political messages. 6. phreaker
How to become a qualified ethical hacker Step 0: read the hacking Step 1: learn to program in C. Step 2: Learn More than one programming language. Step 3: Learn UNIX. Step 4: L Step 5: Learn Networking concepts. Step 6: start reading simple some tutorials about hacking. Step 7: Learn cryptography. Step 8: Experiment A lot.
Some of the things you may need to keep in mind when doing experiments. a. Keept a backup before any experiments. b. Start small and have check points. c. Know when to stop. d. Document your progress. e. Keep improvising f. Automate repetitive tasks. Step 9: Read some good books from experts.
Step 10: participate in hacking challenges. Apart from that, there are some websites listed below that regularly offer hacking challenges online. Hackquest. de Page on hacktissite. org www. trythis. One. com www. hackchallenge. net Hacking-lab. com Step 11: Go Next Level: write vulnerability. Step 12: contribute to open source security projects Step 13: continue Learning and Keep Listening to security talks.
Legality of ethical hacking: Ethical hacking is legal if the hacker abides the rules. The International council of E-commerce(EC -Council) provides a certification program that tests individuals’ skill. Those who pass the examination are awarded with certificates. The certificates are supposed to be renewed.
Understanding the need to hack your own system 1. To catch a thief, think like a thief. 2. Building the foundation for ethical hacking. a. Hack your system in a non-destructive fashion. b. Enumerate vulnerabilities and if necessary, prove to upper management that vulnerabilities exist. c. Apply results to remove vulnerabilities and better secure your systems.
Understanding the dangers your system face Systems are generally under fire from hackers around the world. There are some well-known attacks. 1. Nontechnical attack 2. Network infrastructure attacks 3. Operating system attacks 4. Application and other specialized attacks.
Nontechnical attacks Hackers break into buildings, computer rooms or other areas containing critical information or property. Network infrastructure attacks 1. Connecting into a network through a rogue modem attached to a computer behind a firewall. 2. Exploiting weakness in network transport mechanisms such as TCP/IP and Net. BIOS. 3. Flooding a network with too many requests, creating a Denial of Service(Do. S) for legitimate requests.
4. Installing a network analyzer on a network and capturing every packet that travels across it. 5. Piggybacking into a network through an insecure wireless configuration. Operating system attack 1. Exploiting specific protocol implementations 2. Attacking built-in authentication systems 3. Breaking file system security 4. Cracking passwords and encryption mechanism.
Application and other specialized attacks 1. HTTP & SMTP applications are frequently attacked because most firewalls and other security mechanism are configured to allow full access to these programs from the Internet. 2. Malicious software(Malware) includes viruses, worms, trojan horses and spyware. 3. Spam(junk email) is wreaking havoc on system availability and storage space. And it can carry malware.
What is penetration testing A penetration test, also known as a pen test, is a simulated cyber attack against your computer system to check for exploitable vulnerabilities. In the context of web application security, penetration testing is commonly used to augment a web application firewall (WAF). Pen testing can involve the attempted breaching of any number of application systems, (e. g. , application protocol interfaces (APIs), frontend/backend servers) to uncover vulnerabilities.
CASe- 4 : Take Travel Agent
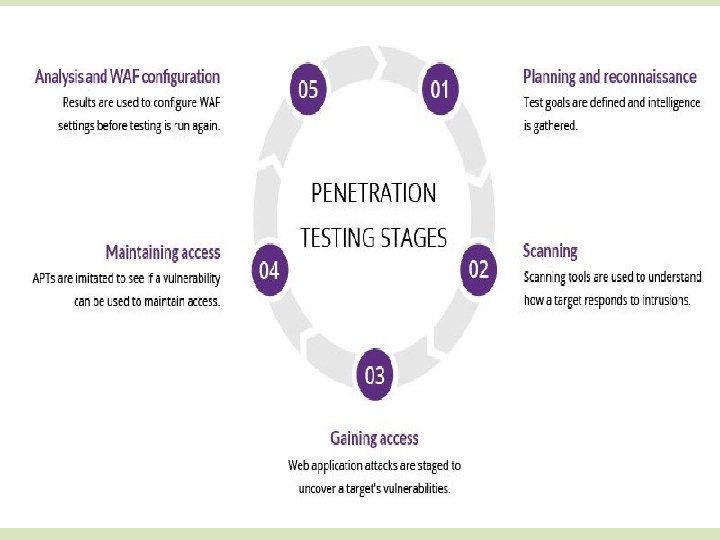
1. Planning and reconnaissance The first stage involves: Defining the scope and goals of a test, including the systems to be addressed and the testing methods to be used. Gathering intelligence (e. g. , network and domain names, mail server) to better understand how a target works and its potential vulnerabilities.
2. Scanning The next step is to understand how the target application will respond to various intrusion attempts. This is typically done using: Static analysis – Inspecting an application’s code to estimate the way it behaves while running. These tools can scan the entirety of the code in a single pass. Dynamic analysis – Inspecting an application’s code in a running state. This is a more practical way of scanning, as it provides a real-time view into an application’s performance.
3. Gaining Access This stage uses web application attacks, such as crosssite scripting, SQL injection and backdoors, to uncover a target’s vulnerabilities. Testers then try and exploit these vulnerabilities, typically by escalating privileges, stealing data, intercepting traffic, etc. , to understand the damage they can cause. 4. Maintaining access The goal of this stage is to see if the vulnerability can be used to achieve a persistent presence in the exploited system— long enough for a bad actor to gain in-depth access. The idea is to imitate advanced persistent threats, which often remain in a system for months in order to steal an organization’s most sensitive data.
5. Analysis The results of the penetration test are then compiled into a report detailing: Specific vulnerabilities that were exploited Sensitive data that was accessed The amount of time the pen tester was able to remain in the system undetected This information is analyzed by security personnel to help configure an enterprise’s WAF settings and other application security solutions to patch vulnerabilities and protect against future attacks.
1. 2. 3. 4. 5. 6. 7. Penetration testing Targeted testing External testing Internal testing Blind testing Double blind testing Black box testing White box testing
CASe- 4 : Take Travel Agent
CASe- 4 : Take Travel Agent
CASe- 4 : Take Travel Agent
CASe- 4 : Take Travel Agent
- Slides: 28