OneWay Hacking Futility of Firewalls in Web Hacking
One-Way Hacking: Futility of Firewalls in Web Hacking JD Glaser, Saumil Shah Foundstone Inc.
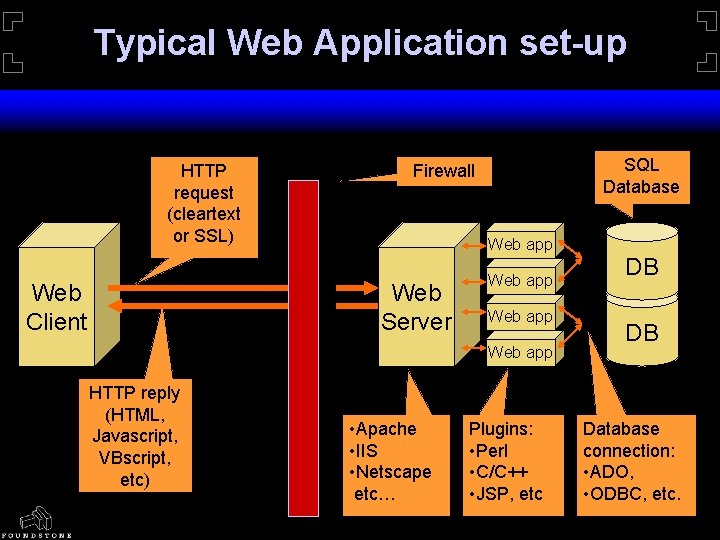
Typical Web Application set-up HTTP request (cleartext or SSL) Web Client SQL Database Firewall Web app Web Server Web app HTTP reply (HTML, Javascript, VBscript, etc) • Apache • IIS • Netscape etc… Plugins: • Perl • C/C++ • JSP, etc DB DB Database connection: • ADO, • ODBC, etc.
Traditional Hacking…Limitations • Modern network architectures are getting more robust and secure. • Firewalls being used in almost all network roll-outs. • OS vendors learning from past mistakes (? ) and coming out with patches rapidly. • Increased maturity in coding practices.
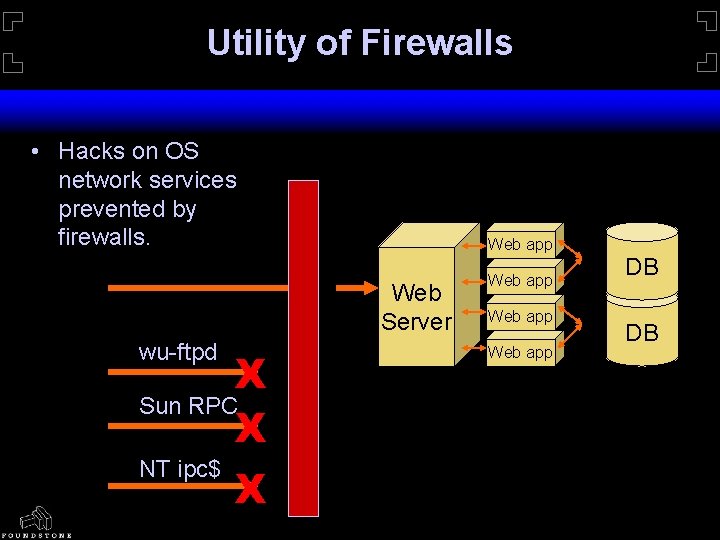
Utility of Firewalls • Hacks on OS network services prevented by firewalls. Web app Web Server wu-ftpd X Sun RPC X NT ipc$ X Web app DB DB
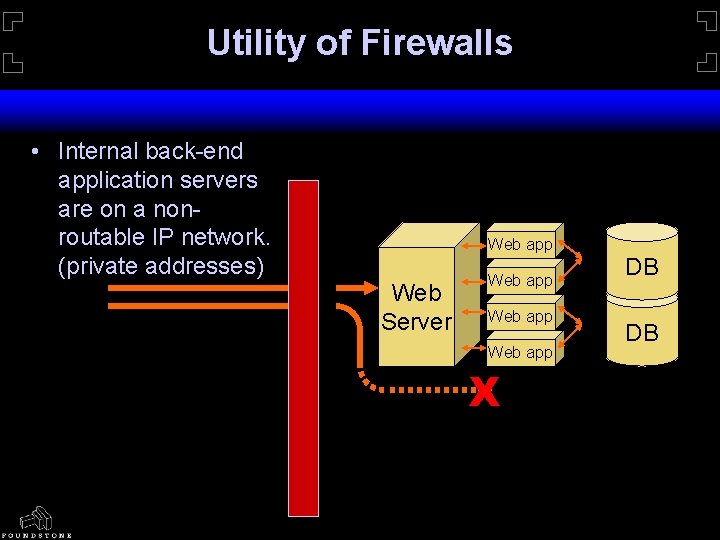
Utility of Firewalls • Internal back-end application servers are on a nonroutable IP network. (private addresses) Web app Web Server Web app X DB DB
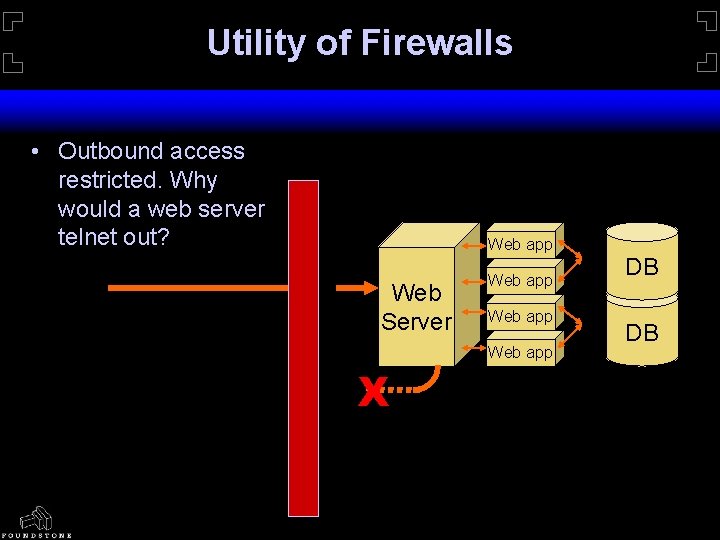
Utility of Firewalls • Outbound access restricted. Why would a web server telnet out? Web app Web Server X Web app DB DB
Futility of Firewalls • E-commerce / Web hacking is unfettered. • Web traffic is the most commonly allowed of protocols through Internet firewalls. • Why fight the wall when you’ve got an open door? • HTTP is perceived as “friendly” traffic. • Content/Application based attacks are still perceived as rare.
The Web Hacker’s Toolbox Essentially, all a web hacker needs is … • a web browser, • an Internet connection, • … and a clear mind.
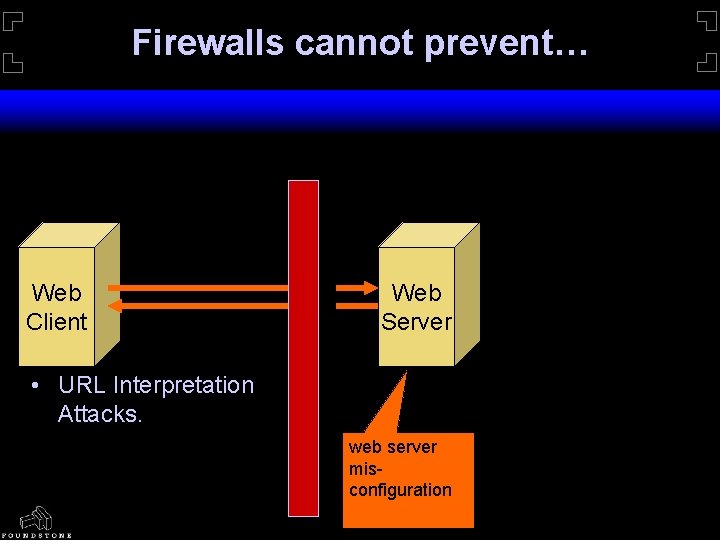
Firewalls cannot prevent… Web Client Web Server • URL Interpretation Attacks. web server misconfiguration
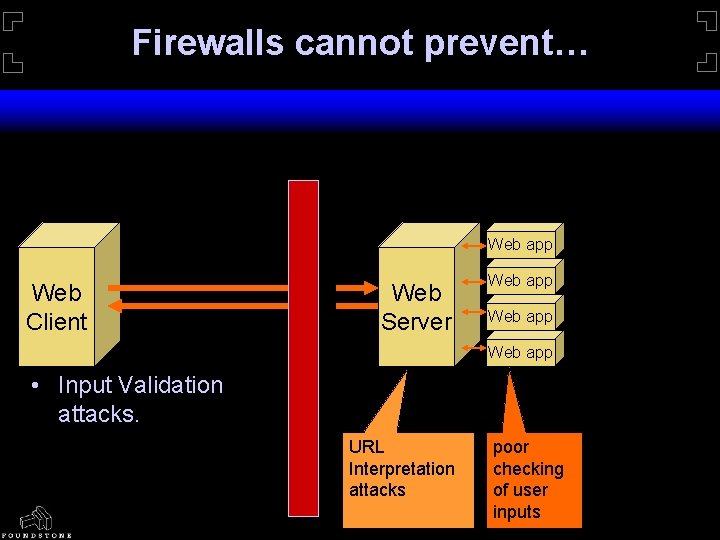
Firewalls cannot prevent… Web app Web Client Web Server Web app • Input Validation attacks. URL Interpretation attacks poor checking of user inputs
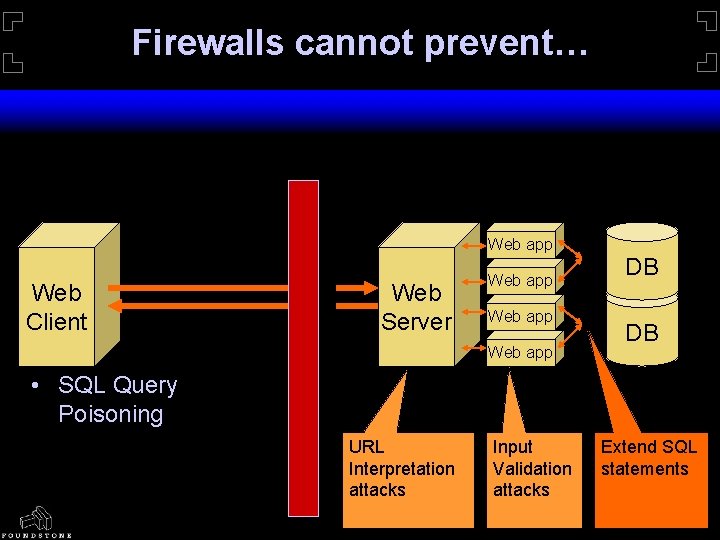
Firewalls cannot prevent… Web app Web Client Web Server Web app DB DB • SQL Query Poisoning URL Interpretation attacks Input Validation attacks Extend SQL statements
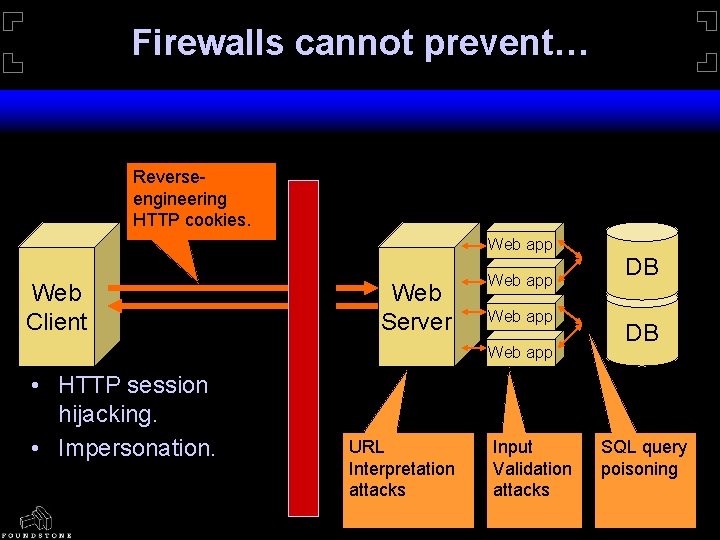
Firewalls cannot prevent… Reverseengineering HTTP cookies. Web app Web Client Web Server Web app • HTTP session hijacking. • Impersonation. URL Interpretation attacks Input Validation attacks DB DB SQL query poisoning
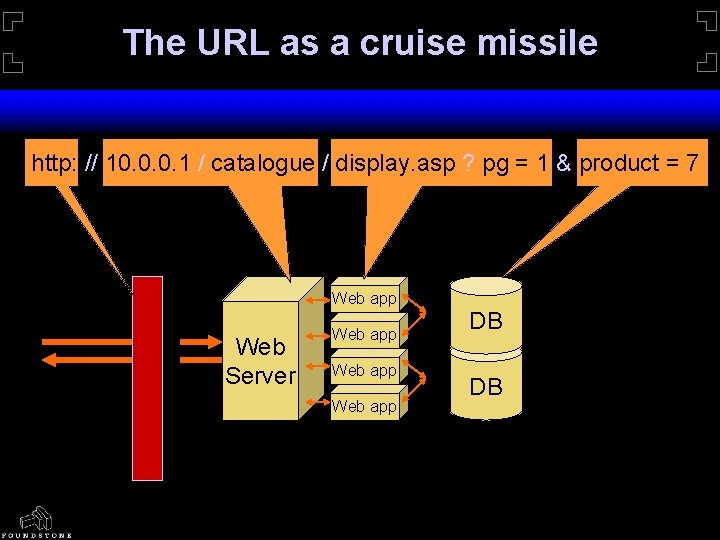
The URL as a cruise missile http: // 10. 0. 0. 1 / catalogue / display. asp ? pg = 1 & product = 7 Web app Web Server Web app DB DB
Web Hacks - net effects Web Hacks cause three types of effects: • Extra information disclosure. (paths, etc. ) • Source code and arbitrary file content disclosure. • Extra data disclosure (e. g. return all rows) • Arbitrary command execution.
The Web Hacker’s Toolbox Some desired accessories would be … • • a port scanner, netcat, vulnerability checker (e. g. whisker), Open. SSL, … etc.
Hacking over SSL • • Some SSL Myths: “We are secure because we use SSL!” “Strong 128 bit crypto being used” “We use Digital Certificates signed by Veri. Sign”
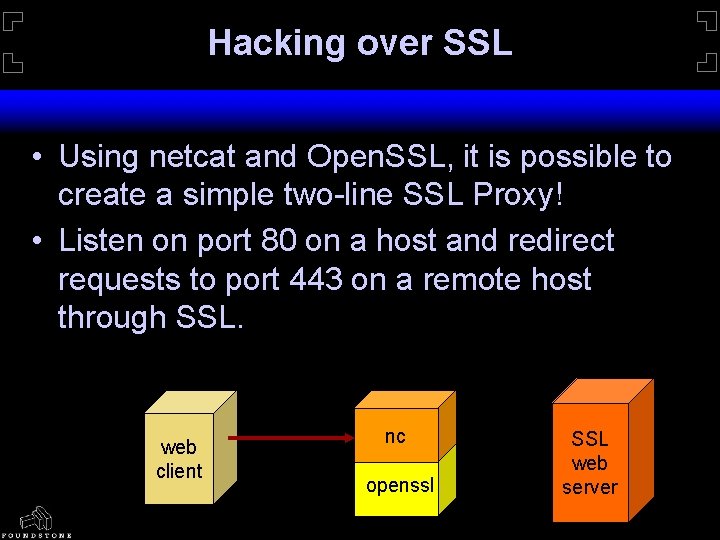
Hacking over SSL • Using netcat and Open. SSL, it is possible to create a simple two-line SSL Proxy! • Listen on port 80 on a host and redirect requests to port 443 on a remote host through SSL. web client nc openssl SSL web server
Use the Source, Luke • Source code disclosure may reveal any flaws in the application design. • Can be used to retrieve application configuraiton files. • e. g. global. asa, etc.
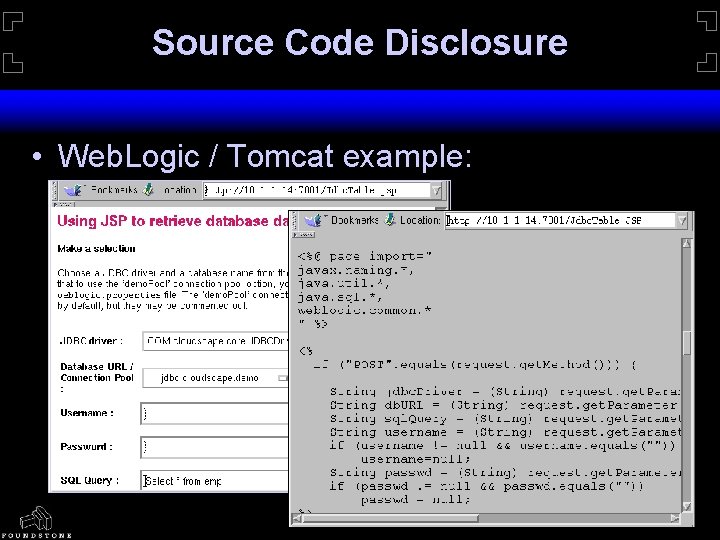
Source Code Disclosure • Web. Logic / Tomcat example:
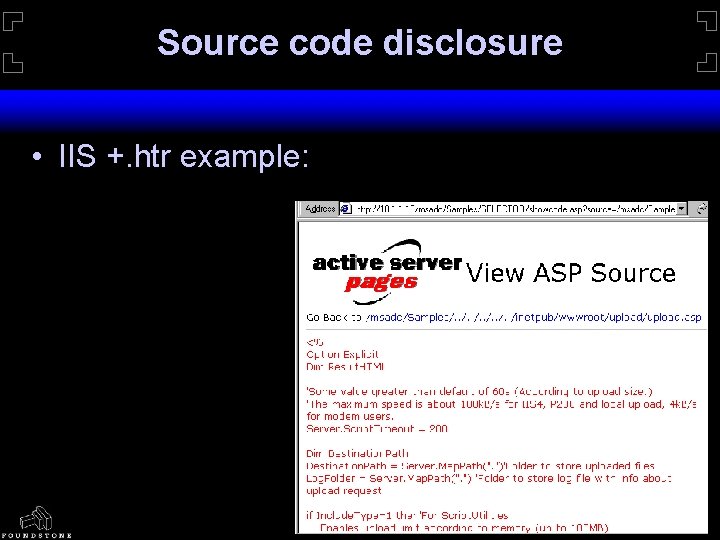
Source code disclosure • IIS +. htr example:
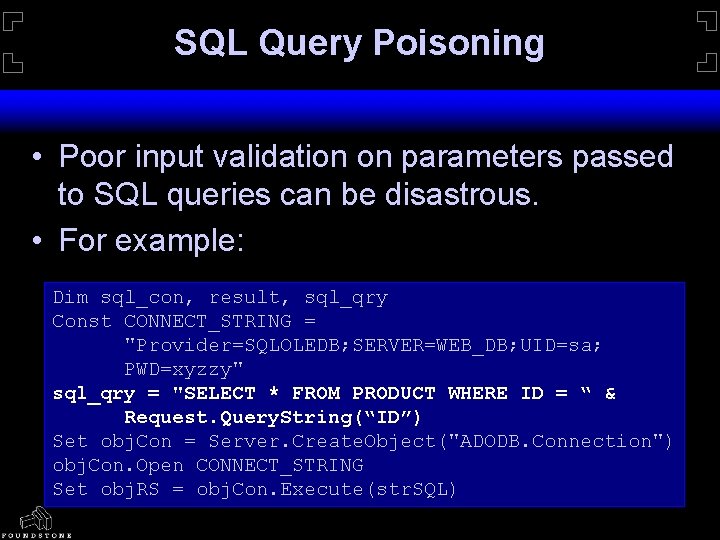
SQL Query Poisoning • Poor input validation on parameters passed to SQL queries can be disastrous. • For example: Dim sql_con, result, sql_qry Const CONNECT_STRING = "Provider=SQLOLEDB; SERVER=WEB_DB; UID=sa; PWD=xyzzy" sql_qry = "SELECT * FROM PRODUCT WHERE ID = “ & Request. Query. String(“ID”) Set obj. Con = Server. Create. Object("ADODB. Connection") obj. Con. Open CONNECT_STRING Set obj. RS = obj. Con. Execute(str. SQL)
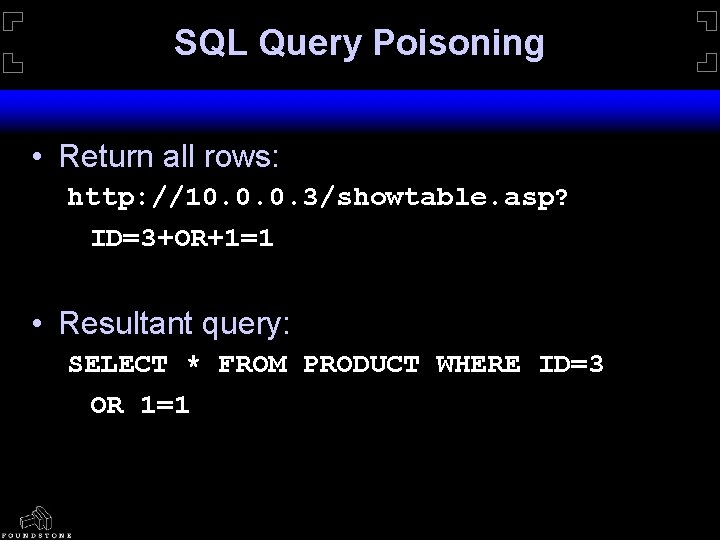
SQL Query Poisoning • Return all rows: http: //10. 0. 0. 3/showtable. asp? ID=3+OR+1=1 • Resultant query: SELECT * FROM PRODUCT WHERE ID=3 OR 1=1
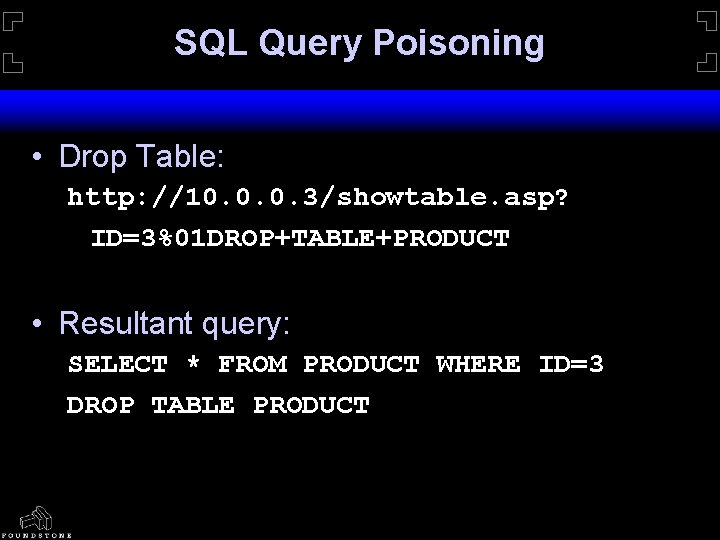
SQL Query Poisoning • Drop Table: http: //10. 0. 0. 3/showtable. asp? ID=3%01 DROP+TABLE+PRODUCT • Resultant query: SELECT * FROM PRODUCT WHERE ID=3 DROP TABLE PRODUCT
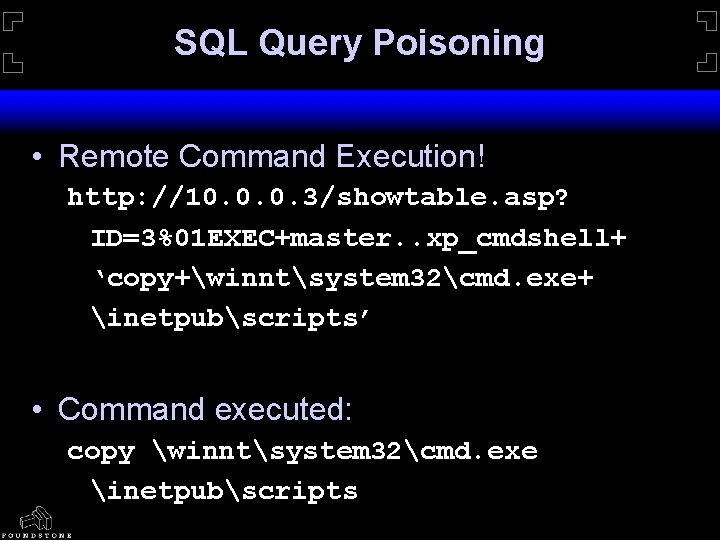
SQL Query Poisoning • Remote Command Execution! http: //10. 0. 0. 3/showtable. asp? ID=3%01 EXEC+master. . xp_cmdshell+ ‘copy+winntsystem 32cmd. exe+ inetpubscripts’ • Command executed: copy winntsystem 32cmd. exe inetpubscripts
One-way attacks • • • Assume the tightest firewall configuration. All legal HTTP requests. No outbound traffic from internal network. …yet, total control. Illustrates how the smallest of openings can be big enough to drive a truck through it!
One-way attacks … entry point • One entry point required. • Arbitrary command execution. • Can be achieved in many ways: • Known vulnerability (e. g. IIS Unicode / ddecode) • Buffer overflow (sometimes kills server!) • Fooling the application itself! (metacharacters, SQL query poisoning)
One-way attacks … uploader • Create an HTTP multipart-MIME upload mechanism. • The same process as sending attachments over web-based mail (yahoo, hotmail). • Uploader allows the attacker to plant and execute tools on the server. • The hole widens.
One-way attacks … remote prompt • Install a remote web-based command prompt. • HTML form, passes inputs to the commandshell on the server. • Semi-interactive.
One-way attacks … SQL prompts! • A step further, install a SQL query prompt page! • Allows attackers to arbitrarily pick and attack back-end SQL servers. • Web programming languages such as ASP, PHP allow back-end database interfaces. • Pilfering of database credentials from source code disclosure attacks would be useful!
One-way attacks … getting root! • Upload your favourite privilege escalation $pl 01 t! • Run it through the web-based command prompt. • Get admin/root privileges!
One-way attacks … going further • • • Drive through the back-end network. Portscanning Service enumeration Network packet sniffing Recovering passwords / credentials … it’s all open now!
Win. Dump • Loads dynamically – don’t have to reboot box. • Works great with MDAC, Unicode, etc… • Sniff internal networks after attack. • Grep for user/pass – Pipe output. • Send results back through nc. • Send results back through firewall as an HTML page – ultra cool because it bypasses firewall
Root Causes of Web Hacks • Complex web architectures may cause oversight in web server configuration. • URL Parsing. • File Canonicalization. • Combination of underlying operating system and web server may leave holes.
Root Causes of Web Hacks • Untested code used in web applications, to save time. • Level of security consciousness low in web application developers. • Security vs. convenience. • Security vs. time-to-market. • Zero knowledge administration breeds zero knowledge administrators.
Web Security Measures • Heighten security awareness amongst administrators, developers and most important - TOP MANAGEMENT! • Firewalls and SSL do not solve all security problems. • Keep abreast of latest vendor advisories and patches. • Monitor security mailing lists such as Bug. Traq. : -/
Thank You! jd. glaser@foundstone. com saumil. shah@foundstone. com
- Slides: 36