LanguageBased Protection in the Jkernel David Walker COS
Language-Based Protection in the J-kernel David Walker COS 598 E: Foundations of Language-Based Security Princeton University (slides from Chris Hawblitzel, Dartmouth)
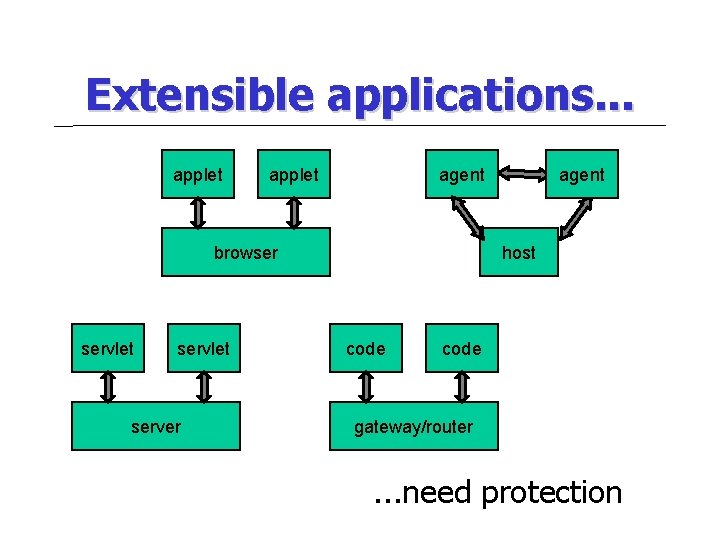
Extensible applications. . . applet agent browser servlet server agent host code gateway/router . . . need protection
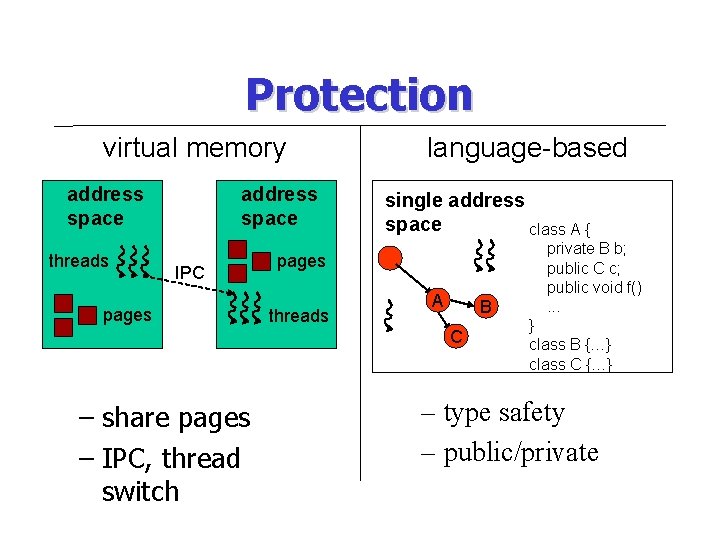
Protection virtual memory address space threads address space IPC pages language-based single address space class A { pages threads A B C – share pages – IPC, thread switch private B b; public C c; public void f(). . . } class B {…} class C {…} – type safety – public/private
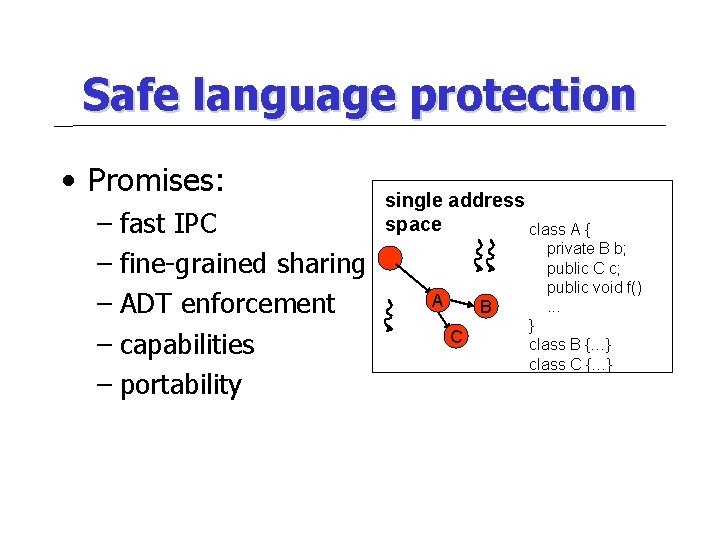
Safe language protection • Promises: – fast IPC – fine-grained sharing – ADT enforcement – capabilities – portability single address space class A { A B C private B b; public C c; public void f(). . . } class B {…} class C {…}
Talk outline • Extensible applications, protection • Language-based protection – current state – problems • The J-Kernel • Luna

Java thread groups • Thread groups applet 1 applet 2 thread group – Terminate group of threads browser thread group
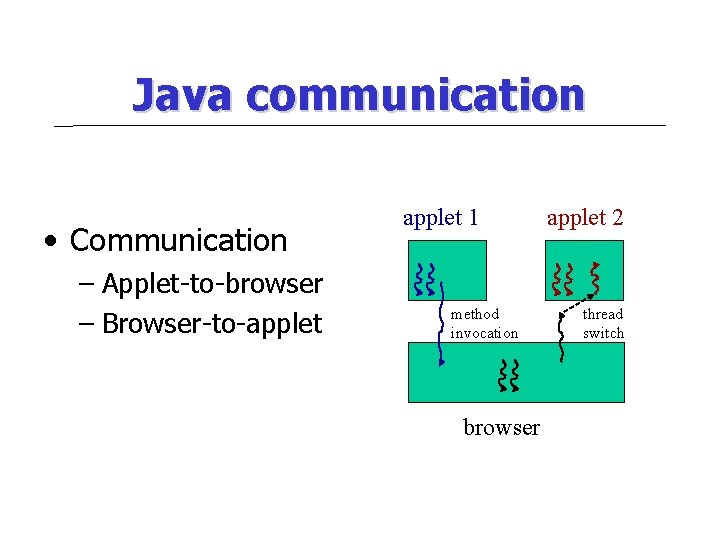
Java communication • Communication – Applet-to-browser – Browser-to-applet 1 method invocation browser applet 2 thread switch
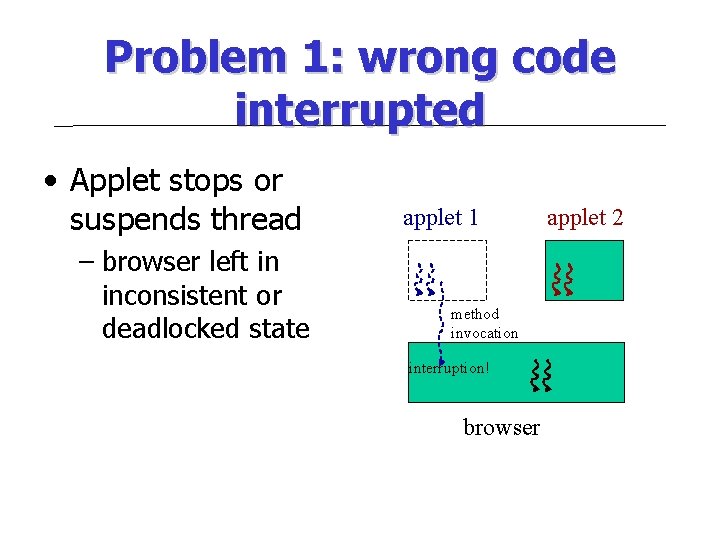
Problem 1: wrong code interrupted • Applet stops or suspends thread – browser left in inconsistent or deadlocked state applet 1 method invocation interruption! browser applet 2
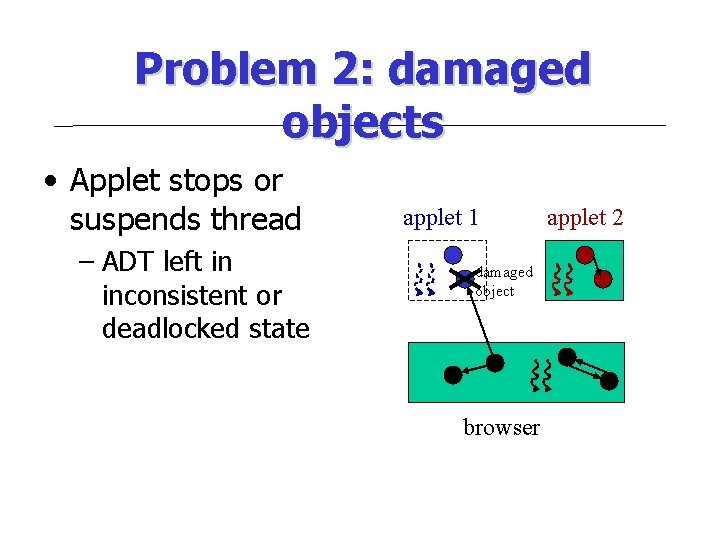
Problem 2: damaged objects • Applet stops or suspends thread – ADT left in inconsistent or deadlocked state applet 1 damaged object browser applet 2
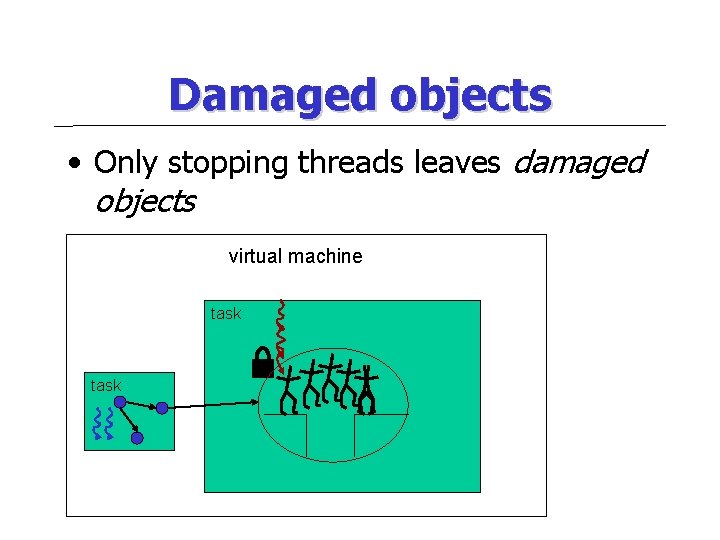
Damaged objects • Only stopping threads leaves damaged objects virtual machine task
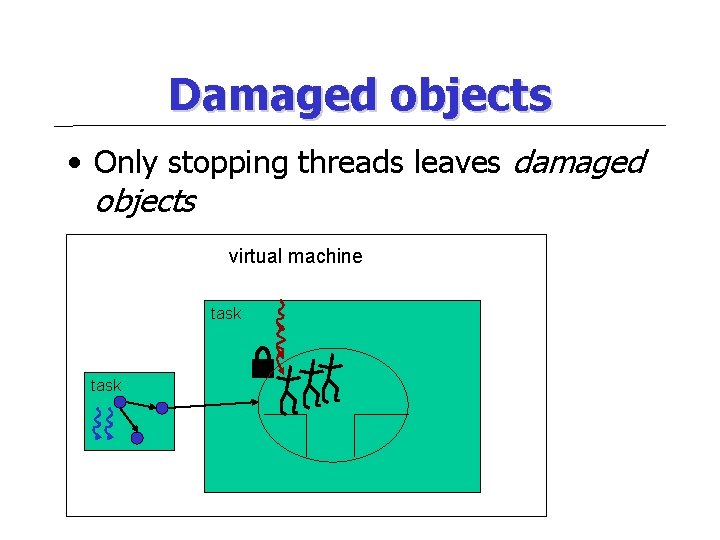
Damaged objects • Only stopping threads leaves damaged objects virtual machine task
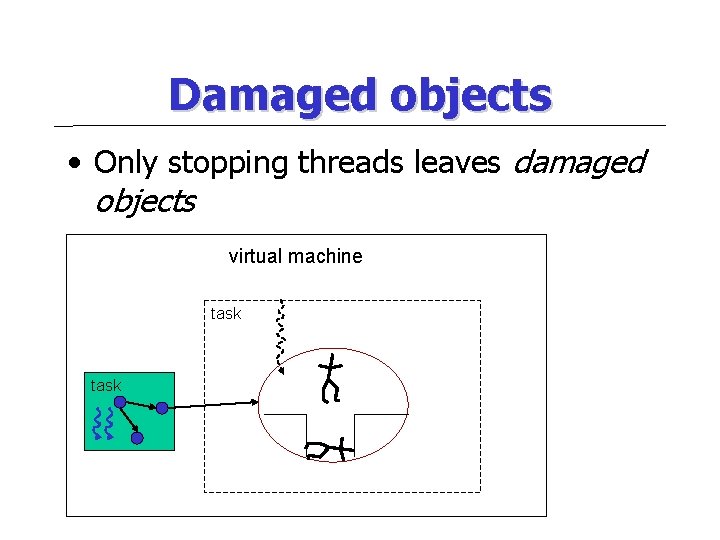
Damaged objects • Only stopping threads leaves damaged objects virtual machine task
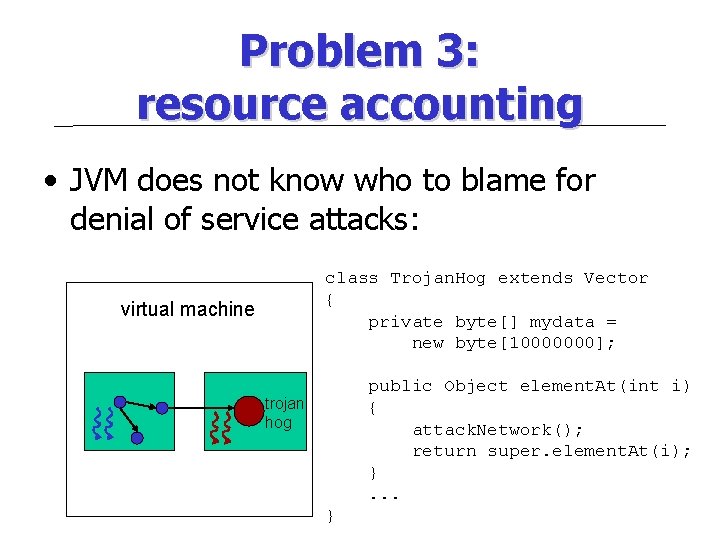
Problem 3: resource accounting • JVM does not know who to blame for denial of service attacks: class Trojan. Hog extends Vector { private byte[] mydata = new byte[10000000]; virtual machine public Object element. At(int i) { attack. Network(); return super. element. At(i); }. . . trojan hog }
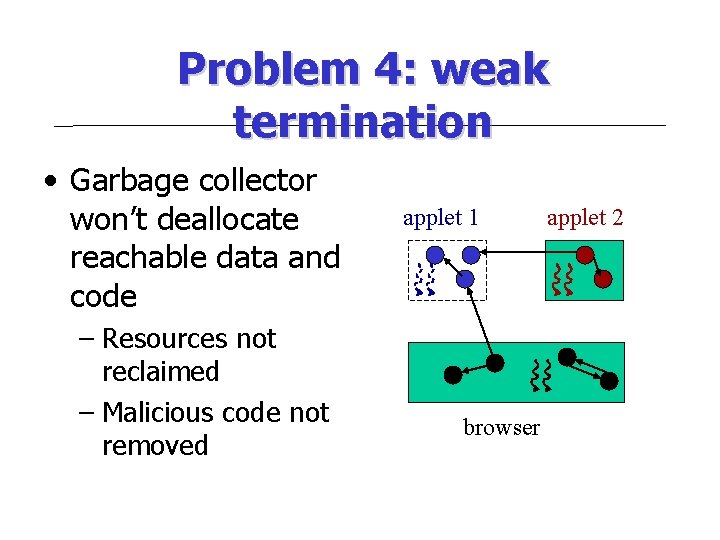
Problem 4: weak termination • Garbage collector won’t deallocate reachable data and code – Resources not reclaimed – Malicious code not removed applet 1 browser applet 2
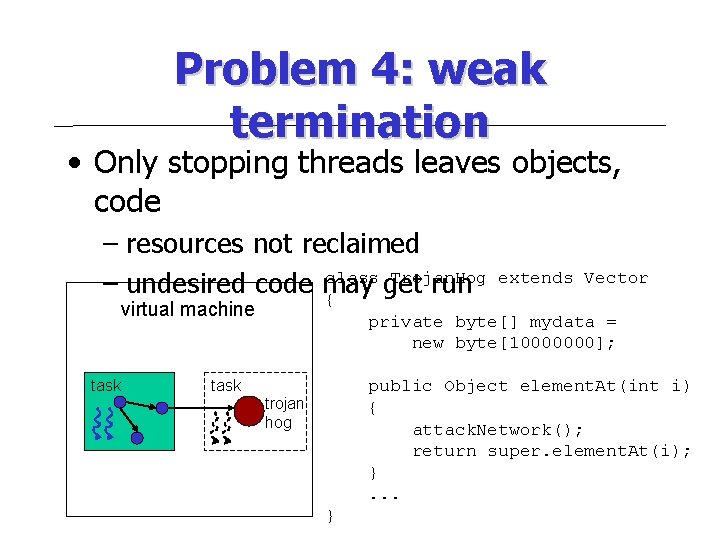
Problem 4: weak termination • Only stopping threads leaves objects, code – resources not reclaimed class Trojan. Hog – undesired code may get run { virtual machine task extends Vector private byte[] mydata = new byte[10000000]; public Object element. At(int i) { attack. Network(); return super. element. At(i); }. . . task trojan hog }
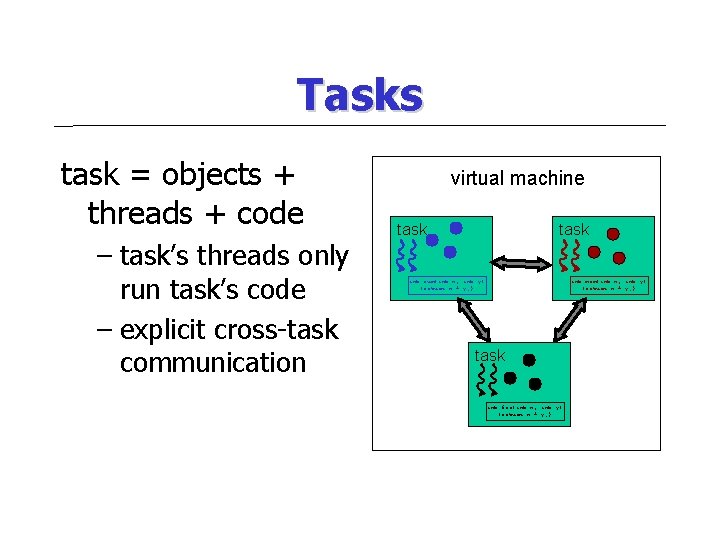
Tasks task = objects + threads + code – task’s threads only run task’s code – explicit cross-task communication virtual machine task int sum(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; } task int foo(int x, int y) {return x + y; }
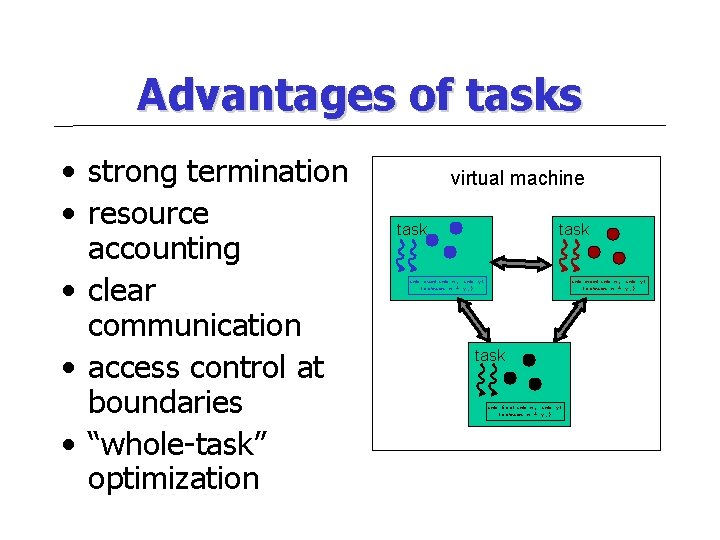
Advantages of tasks • strong termination • resource accounting • clear communication • access control at boundaries • “whole-task” optimization virtual machine task int sum(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; } task int foo(int x, int y) {return x + y; }
Talk outline • Extensible applications, protection • Language-based protection • The J-Kernel – Prototype implementation of the task model • written in Java • no changes to VM, language • Luna
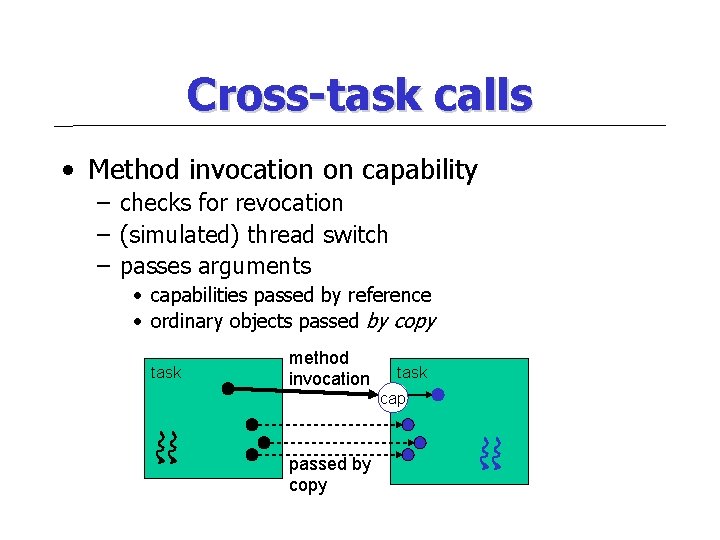
Cross-task calls • Method invocation on capability – checks for revocation – (simulated) thread switch – passes arguments • capabilities passed by reference • ordinary objects passed by copy task method invocation task cap passed by copy
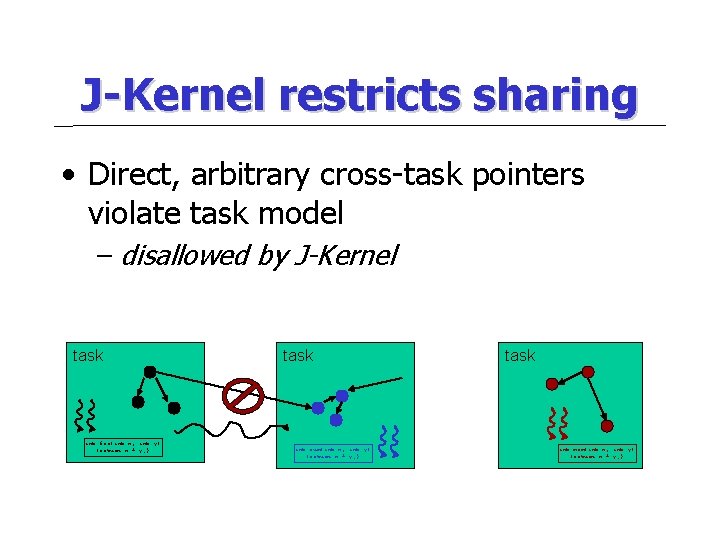
J-Kernel restricts sharing • Direct, arbitrary cross-task pointers violate task model – disallowed by J-Kernel task int foo(int x, int y) {return x + y; } task int sum(int x, int y) {return x + y; } task int mom(int x, int y) {return x + y; }
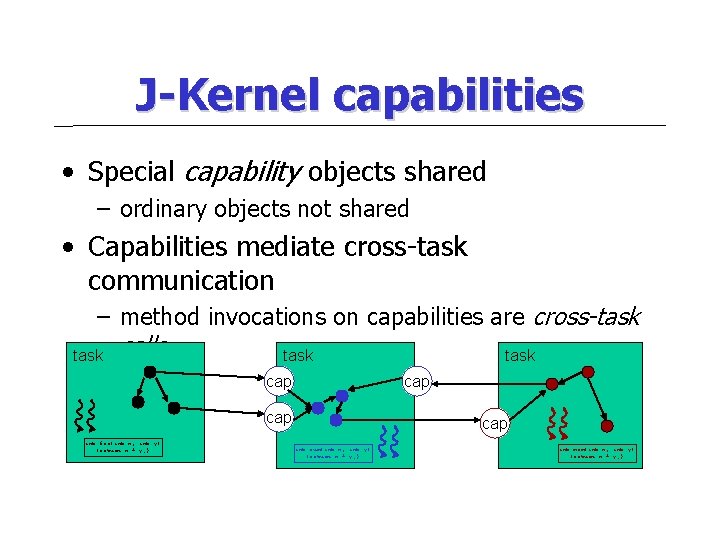
J-Kernel capabilities • Special capability objects shared – ordinary objects not shared • Capabilities mediate cross-task communication – method invocations on capabilities are cross-task calls task cap cap int foo(int x, int y) {return x + y; } cap int sum(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; }
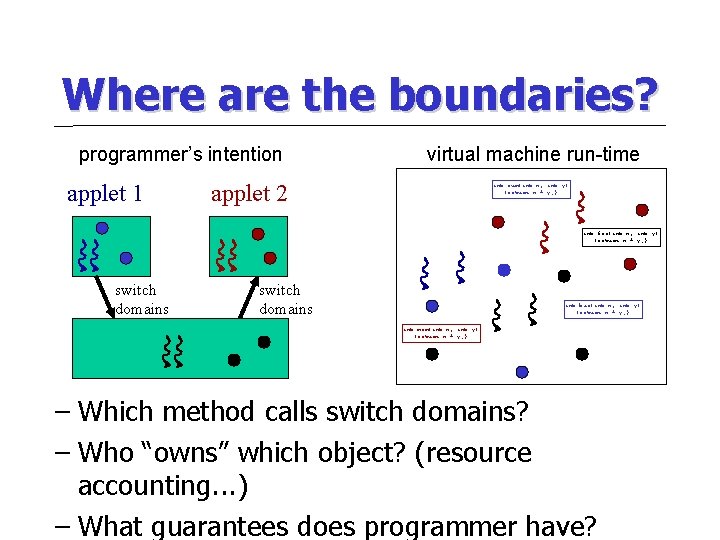
Where are the boundaries? programmer’s intention applet 1 virtual machine run-time applet 2 int sum(int x, int y) {return x + y; } int foo(int x, int y) {return x + y; } switch domains int bar(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; } – Which method calls switch domains? – Who “owns” which object? (resource accounting. . . ) – What guarantees does programmer have?
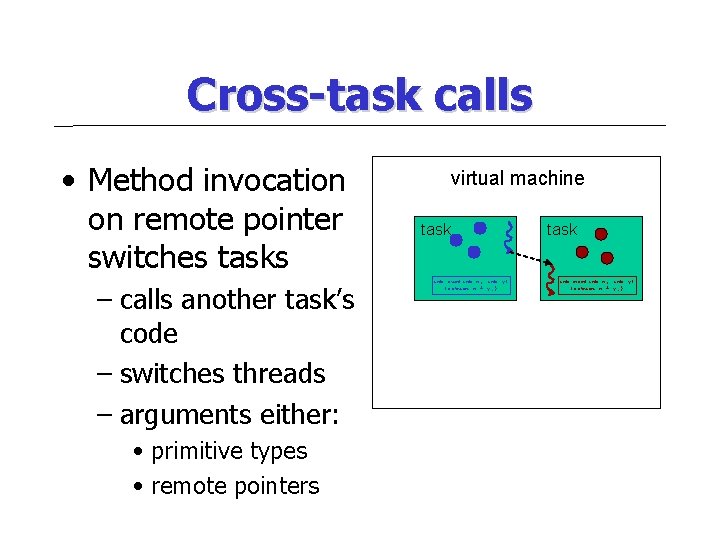
Cross-task calls • Method invocation on remote pointer switches tasks – calls another task’s code – switches threads – arguments either: • primitive types • remote pointers virtual machine task int sum(int x, int y) {return x + y; } task int mom(int x, int y) {return x + y; }
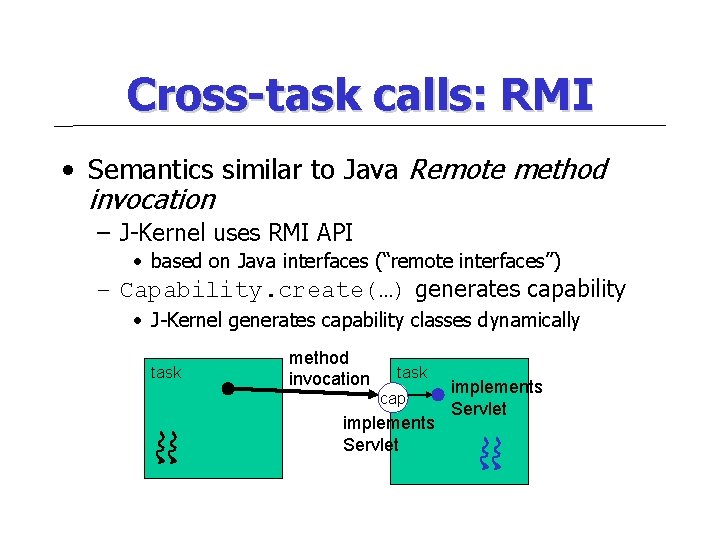
Cross-task calls: RMI • Semantics similar to Java Remote method invocation – J-Kernel uses RMI API • based on Java interfaces (“remote interfaces”) – Capability. create(…) generates capability • J-Kernel generates capability classes dynamically task method invocation task cap implements Servlet
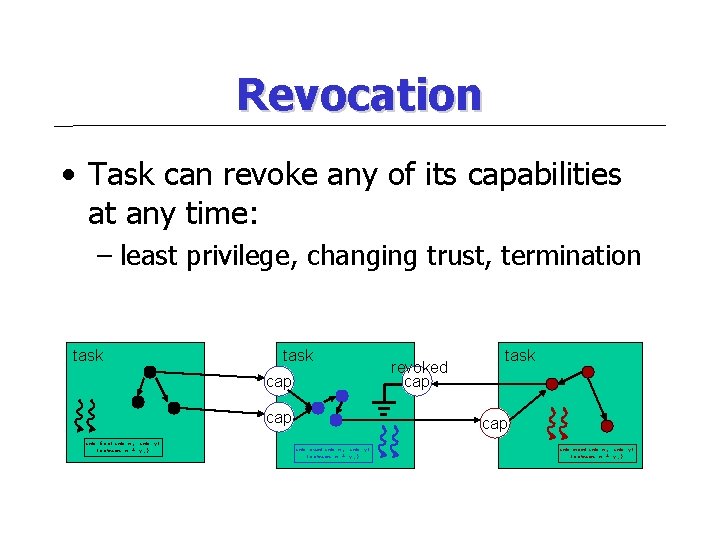
Revocation • Task can revoke any of its capabilities at any time: – least privilege, changing trust, termination task cap int foo(int x, int y) {return x + y; } revoked cap task cap int sum(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; }
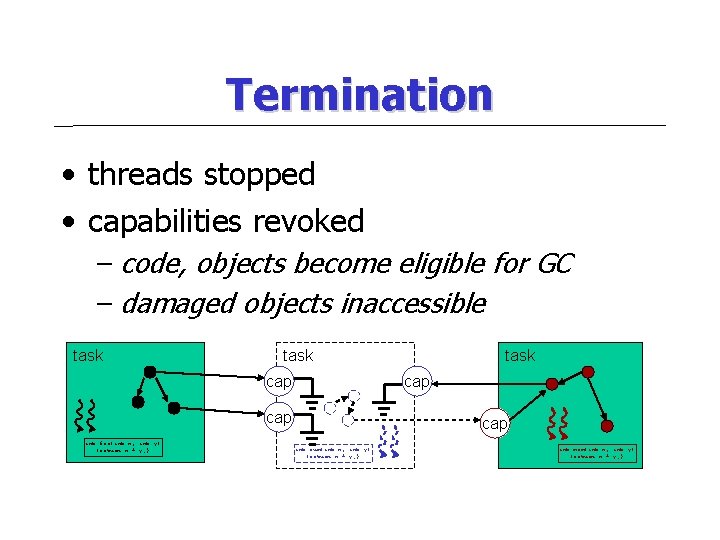
Termination • threads stopped • capabilities revoked – code, objects become eligible for GC – damaged objects inaccessible task cap cap int foo(int x, int y) {return x + y; } task cap int sum(int x, int y) {return x + y; } int mom(int x, int y) {return x + y; }
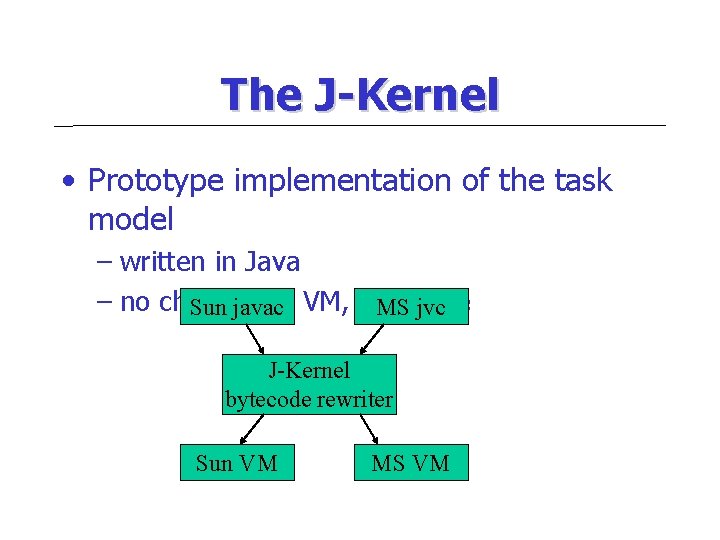
The J-Kernel • Prototype implementation of the task model – written in Java – no changes to VM, language Sun javac MS jvc J-Kernel bytecode rewriter Sun VM MS VM
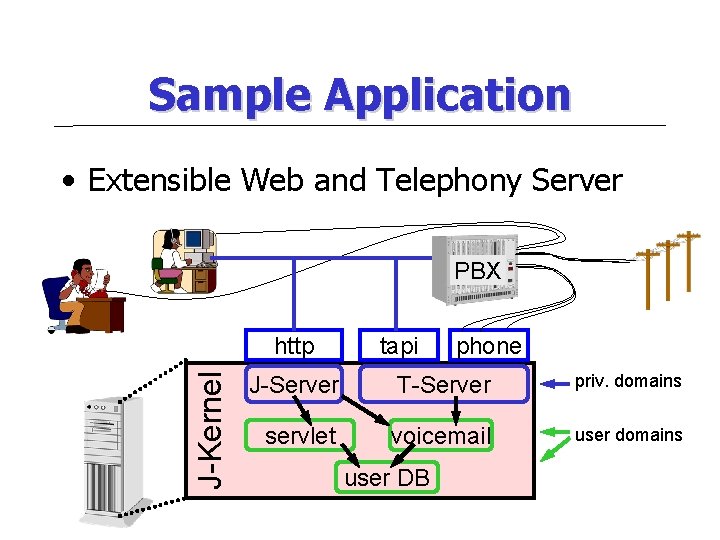
Sample Application • Extensible Web and Telephony Server PBX J-Kernel http tapi phone J-Server T-Server priv. domains servlet voicemail user domains user DB
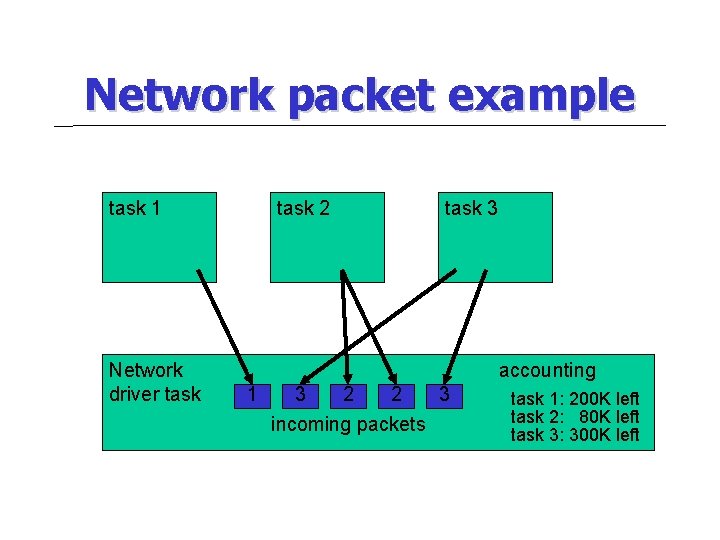
Network packet example task 1 Network driver task 2 task 3 accounting 1 3 2 2 3 incoming packets task 1: 200 K left task 2: 80 K left task 3: 300 K left
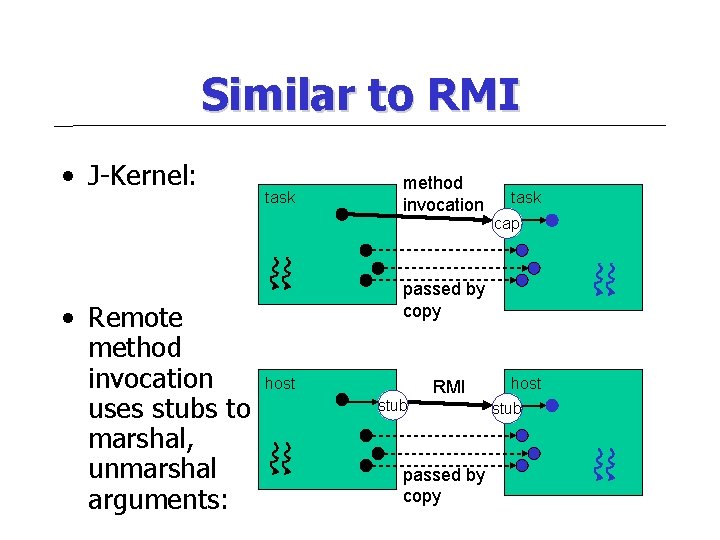
Similar to RMI • J-Kernel: task method invocation task cap • Remote method invocation uses stubs to marshal, unmarshal arguments: passed by copy host stub RMI passed by copy host stub
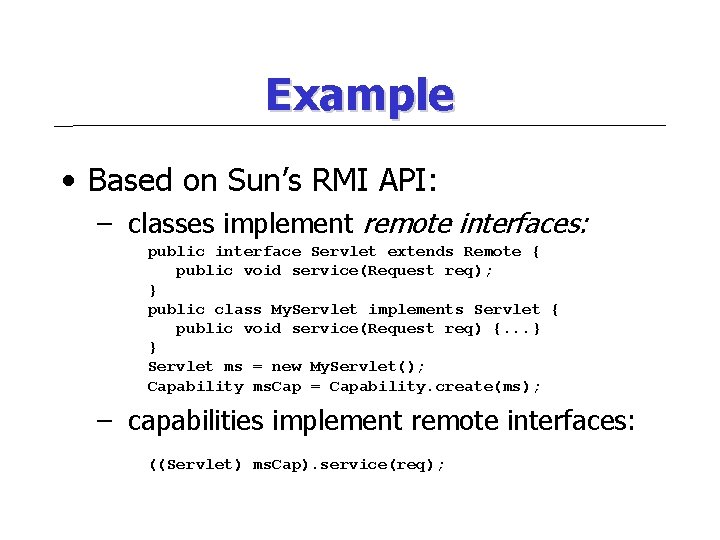
Example • Based on Sun’s RMI API: – classes implement remote interfaces: public interface Servlet extends Remote { public void service(Request req); } public class My. Servlet implements Servlet { public void service(Request req) {. . . } } Servlet ms = new My. Servlet(); Capability ms. Cap = Capability. create(ms); – capabilities implement remote interfaces: ((Servlet) ms. Cap). service(req);
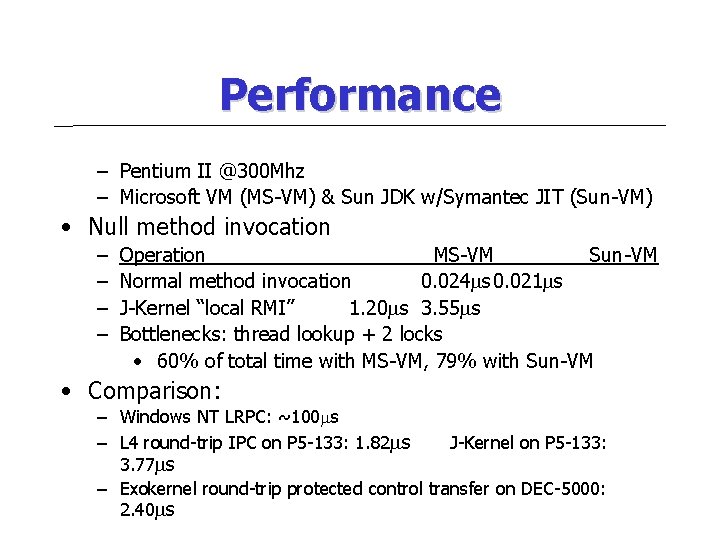
Performance – Pentium II @300 Mhz – Microsoft VM (MS-VM) & Sun JDK w/Symantec JIT (Sun-VM) • Null method invocation – – Operation MS-VM Sun-VM Normal method invocation 0. 024 s 0. 021 s J-Kernel “local RMI” 1. 20 s 3. 55 s Bottlenecks: thread lookup + 2 locks • 60% of total time with MS-VM, 79% with Sun-VM • Comparison: – Windows NT LRPC: ~100 s – L 4 round-trip IPC on P 5 -133: 1. 82 s J-Kernel on P 5 -133: 3. 77 s – Exokernel round-trip protected control transfer on DEC-5000: 2. 40 s
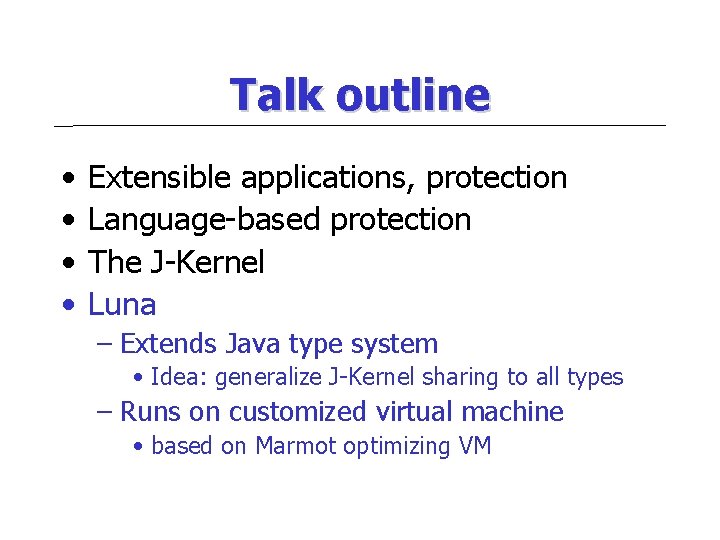
Talk outline • • Extensible applications, protection Language-based protection The J-Kernel Luna – Extends Java type system • Idea: generalize J-Kernel sharing to all types – Runs on customized virtual machine • based on Marmot optimizing VM
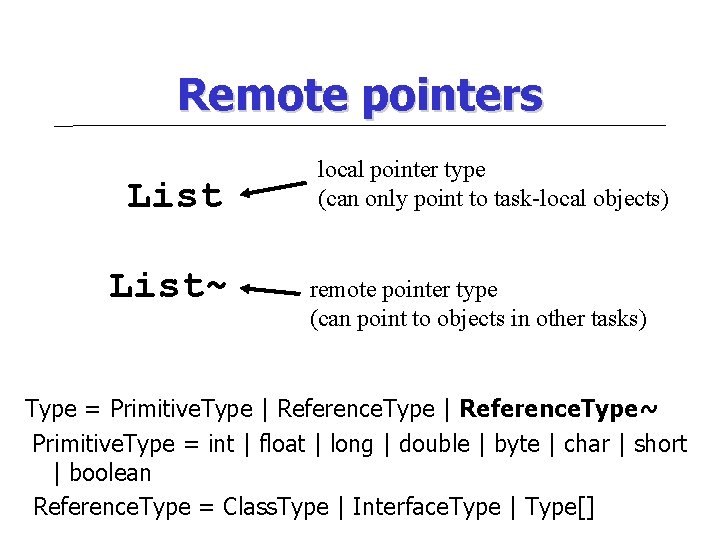
Remote pointers List~ local pointer type (can only point to task-local objects) remote pointer type (can point to objects in other tasks) Type = Primitive. Type | Reference. Type~ Primitive. Type = int | float | long | double | byte | char | short | boolean Reference. Type = Class. Type | Interface. Type | Type[]
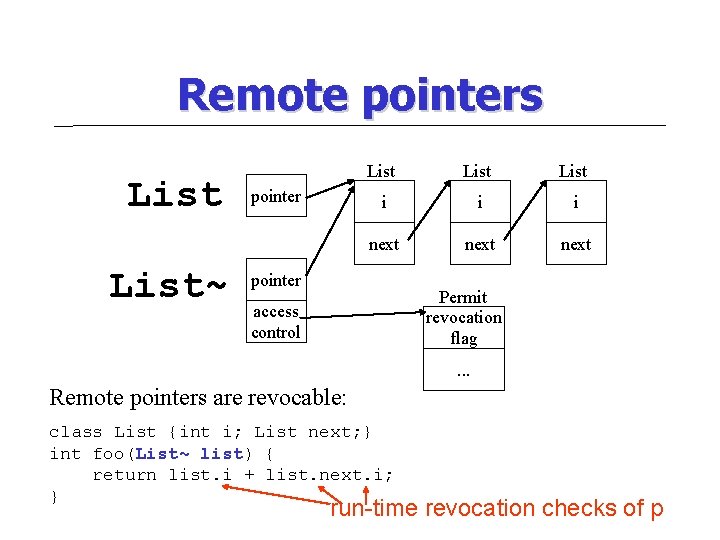
Remote pointers List~ pointer List i i i next pointer Permit revocation flag access control . . . Remote pointers are revocable: class List {int i; List next; } int foo(List~ list) { return list. i + list. next. i; } run-time revocation checks of p
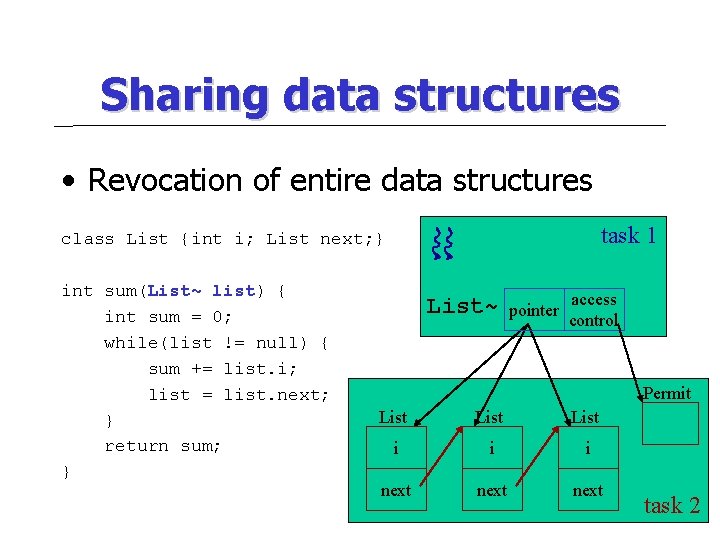
Sharing data structures • Revocation of entire data structures task 1 class List {int i; List next; } int sum(List~ list) { int sum = 0; while(list != null) { sum += list. i; list = list. next; } return sum; } List~ pointer access control Permit List i i i next task 2
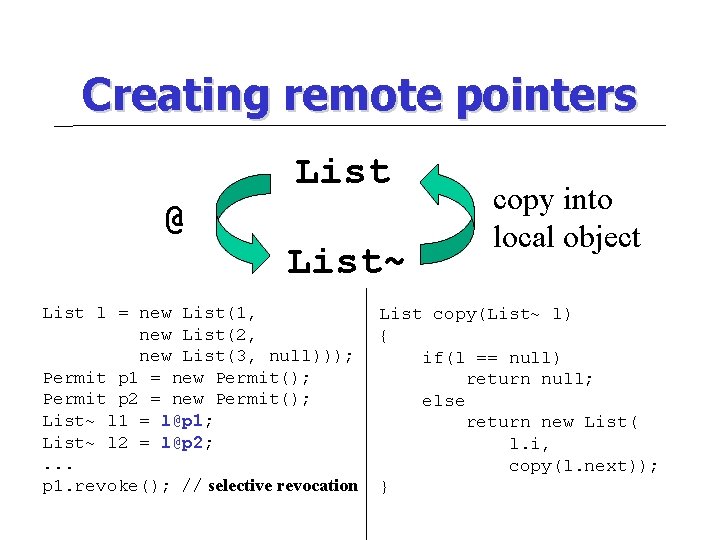
Creating remote pointers List @ List~ List l = new List(1, new List(2, new List(3, null))); Permit p 1 = new Permit(); Permit p 2 = new Permit(); List~ l 1 = l@p 1; List~ l 2 = l@p 2; . . . p 1. revoke(); // selective revocation copy into local object List copy(List~ l) { if(l == null) return null; else return new List( l. i, copy(l. next)); }
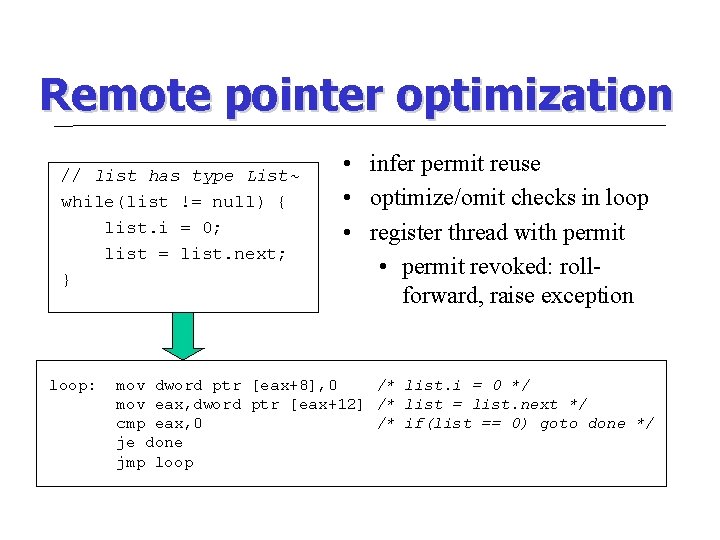
Remote pointer optimization // list has type List~ while(list != null) { list. i = 0; list = list. next; } loop: • infer permit reuse • optimize/omit checks in loop • register thread with permit • permit revoked: rollforward, raise exception mov dword ptr [eax+8], 0 /* list. i = 0 */ mov eax, dword ptr [eax+12] /* list = list. next */ cmp eax, 0 /* if(list == 0) goto done */ je done jmp loop
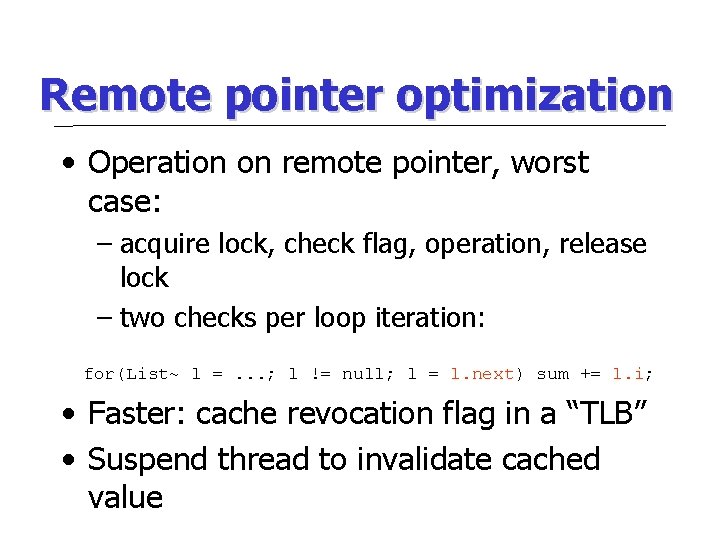
Remote pointer optimization • Operation on remote pointer, worst case: – acquire lock, check flag, operation, release lock – two checks per loop iteration: for(List~ l =. . . ; l != null; l = l. next) sum += l. i; • Faster: cache revocation flag in a “TLB” • Suspend thread to invalidate cached value
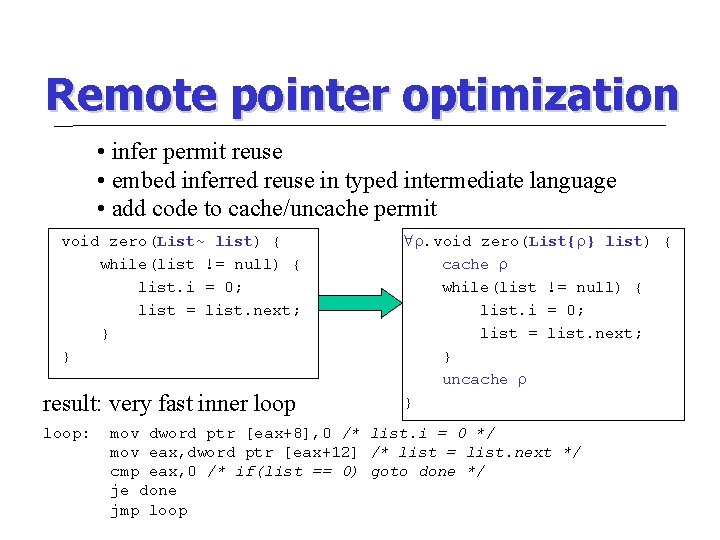
Remote pointer optimization • infer permit reuse • embed inferred reuse in typed intermediate language • add code to cache/uncache permit void zero(List~ list) { while(list != null) { list. i = 0; list = list. next; } } result: very fast inner loop: . void zero(List{ } list) { cache while(list != null) { list. i = 0; list = list. next; } uncache } mov dword ptr [eax+8], 0 /* list. i = 0 */ mov eax, dword ptr [eax+12] /* list = list. next */ cmp eax, 0 /* if(list == 0) goto done */ je done jmp loop
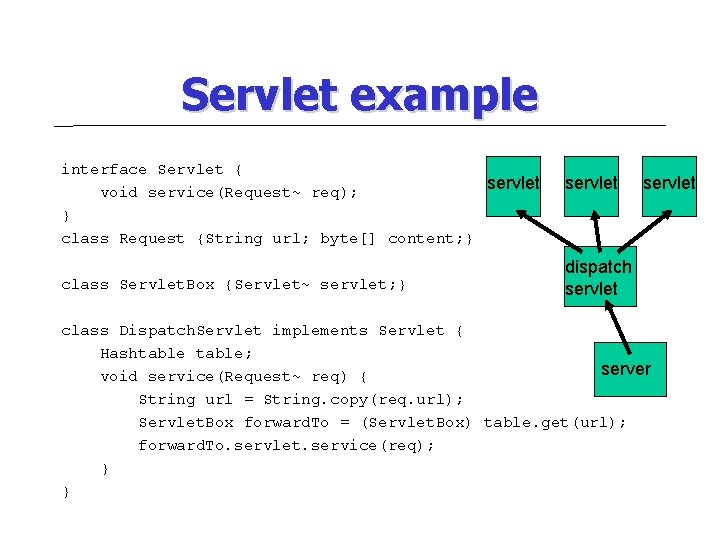
Servlet example interface Servlet { servlet void service(Request~ req); } class Request {String url; byte[] content; } class Servlet. Box {Servlet~ servlet; } servlet dispatch servlet class Dispatch. Servlet implements Servlet { Hashtable; server void service(Request~ req) { String url = String. copy(req. url); Servlet. Box forward. To = (Servlet. Box) table. get(url); forward. To. servlet. service(req); } }
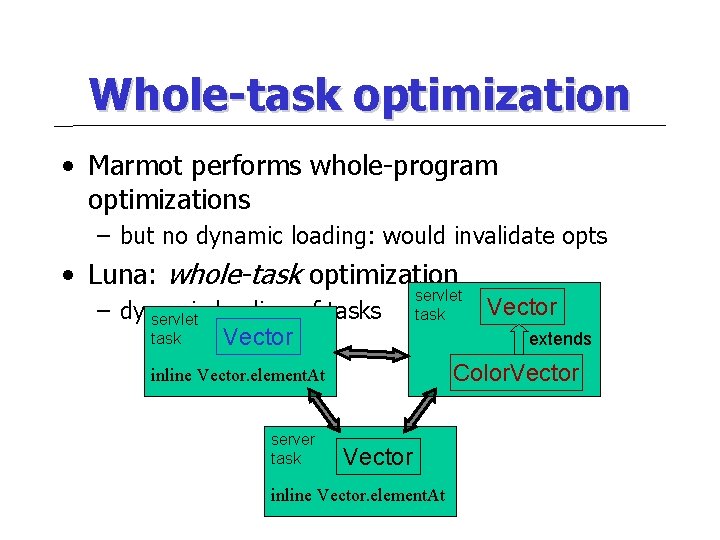
Whole-task optimization • Marmot performs whole-program optimizations – but no dynamic loading: would invalidate opts • Luna: whole-task optimization – dynamic servlet loading of tasks task Vector servlet task extends Color. Vector inline Vector. element. At server task Vector inline Vector. element. At
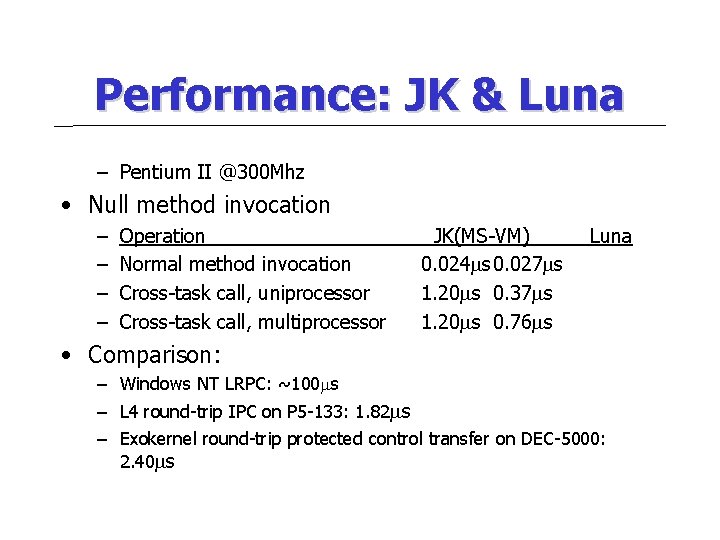
Performance: JK & Luna – Pentium II @300 Mhz • Null method invocation – – Operation Normal method invocation Cross-task call, uniprocessor Cross-task call, multiprocessor JK(MS-VM) 0. 024 s 0. 027 s 1. 20 s 0. 37 s 1. 20 s 0. 76 s Luna • Comparison: – Windows NT LRPC: ~100 s – L 4 round-trip IPC on P 5 -133: 1. 82 s – Exokernel round-trip protected control transfer on DEC-5000: 2. 40 s
Related work • Dr. Scheme – no peer-to-peer communication – task model not guaranteed • Alta – shared data – tradeoff between flexibility, resource tracking • Kaffe. OS – shared data buffers
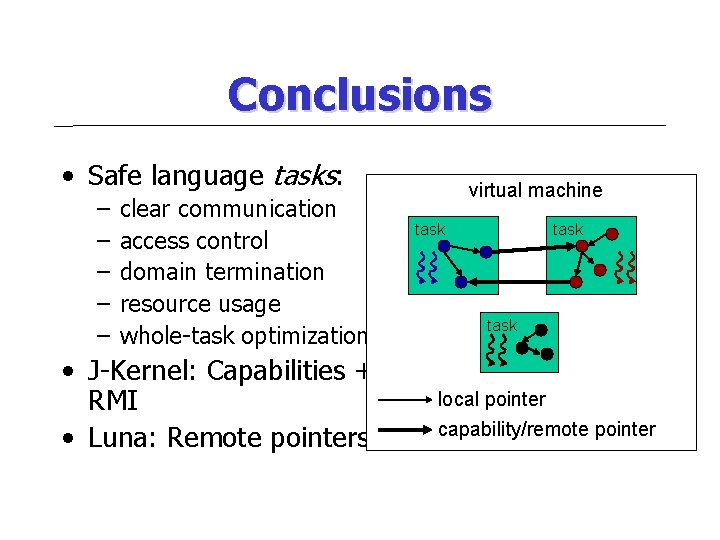
Conclusions • Safe language tasks: – – – clear communication access control domain termination resource usage whole-task optimization • J-Kernel: Capabilities + RMI • Luna: Remote pointers virtual machine task local pointer capability/remote pointer

- Slides: 46