NSXv 6 4 Logical Load Balancer LB Configuration
NSX-v 6. 4 Logical Load Balancer LB Configuration Examples + Log format + API examples + Troubleshooting Dimitri Desmidt – TPM ddesmidt@vmware. com © 2017 VMware Inc. All rights reserved
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 2
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 3
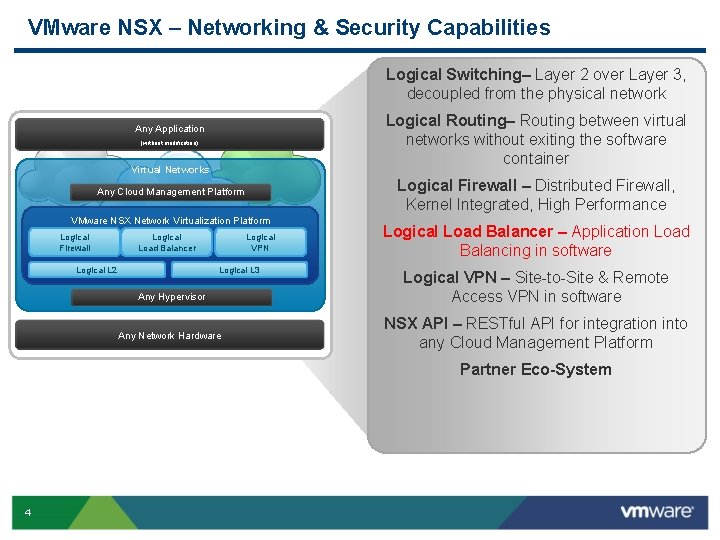
VMware NSX – Networking & Security Capabilities Logical Switching– Layer 2 over Layer 3, decoupled from the physical network Logical Routing– Routing between virtual networks without exiting the software container Any Application (without modification) Virtual Networks Logical Firewall – Distributed Firewall, Kernel Integrated, High Performance Any Cloud Management Platform VMware NSX Network Virtualization Platform Logical Firewall Logical Load Balancer Logical VPN Logical L 3 Logical L 2 Any Hypervisor Any Network Hardware Logical Load Balancer – Application Load Balancing in software Logical VPN – Site-to-Site & Remote Access VPN in software NSX API – RESTful API for integration into any Cloud Management Platform Partner Eco-System 4
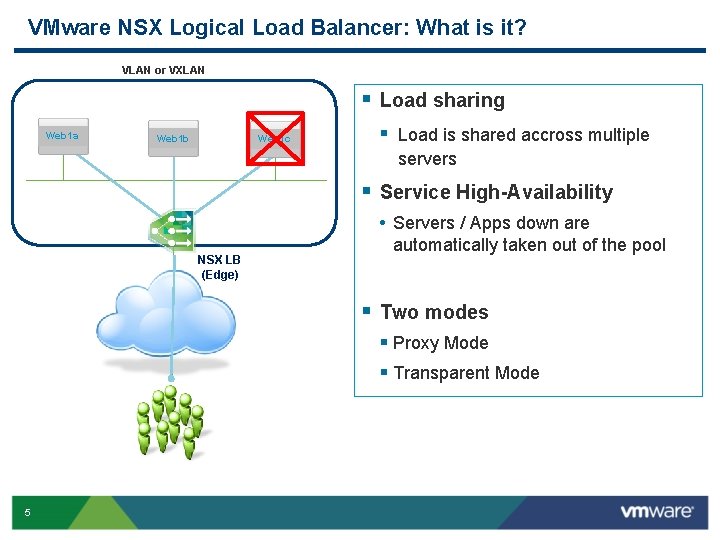
VMware NSX Logical Load Balancer: What is it? VLAN or VXLAN § Load sharing Web 1 a Web 1 b Web 1 c § Load is shared accross multiple servers § Service High-Availability • Servers / Apps down are NSX LB (Edge) automatically taken out of the pool § Two modes § Proxy Mode § Transparent Mode 5
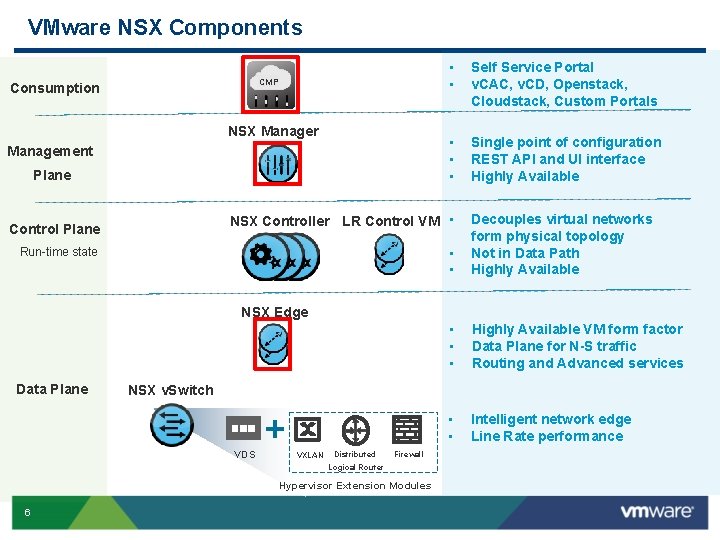
VMware NSX Components CMP Consumption NSX Manager Management Plane • • Self Service Portal v. CAC, v. CD, Openstack, Cloudstack, Custom Portals • • • Single point of configuration REST API and UI interface Highly Available NSX Controller LR Control VM • Control Plane Run-time state • • Decouples virtual networks form physical topology Not in Data Path Highly Available • • • Highly Available VM form factor Data Plane for N-S traffic Routing and Advanced services • • Intelligent network edge Line Rate performance NSX Edge Data Plane NSX v. Switch VDS VXLAN Distributed Firewall Logical Router Hypervisor Extension Modules 6
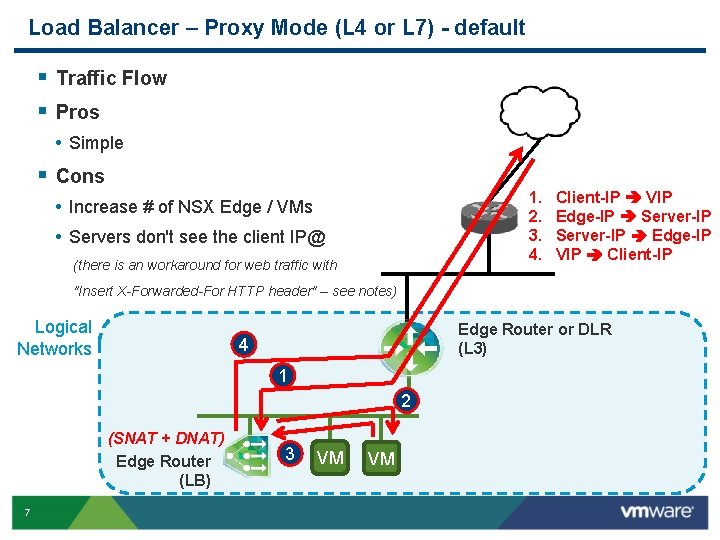
Load Balancer – Proxy Mode (L 4 or L 7) - default § Traffic Flow § Pros • Simple § Cons 1. 2. 3. 4. • Increase # of NSX Edge / VMs • Servers don't see the client IP@ (there is an workaround for web traffic with Client-IP VIP Edge-IP Server-IP Edge-IP VIP Client-IP "Insert X-Forwarded-For HTTP header" – see notes) Logical Networks Edge Router or DLR (L 3) 4 1 2 (SNAT + DNAT) Edge Router (LB) 7 3 VM VM
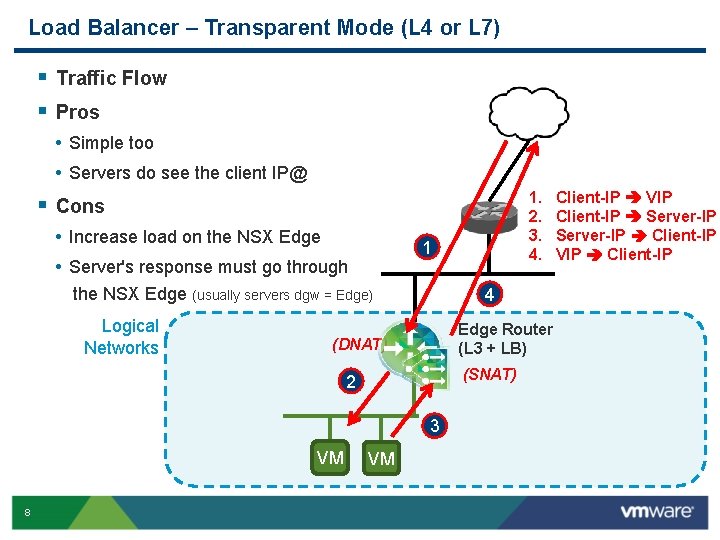
Load Balancer – Transparent Mode (L 4 or L 7) § Traffic Flow § Pros • Simple too • Servers do see the client IP@ 1. 2. 3. 4. § Cons • Increase load on the NSX Edge • Server's response must go through 1 the NSX Edge (usually servers dgw = Edge) Logical Networks 4 Edge Router (L 3 + LB) (DNAT) (SNAT) 2 3 VM 8 VM Client-IP VIP Client-IP Server-IP Client-IP VIP Client-IP
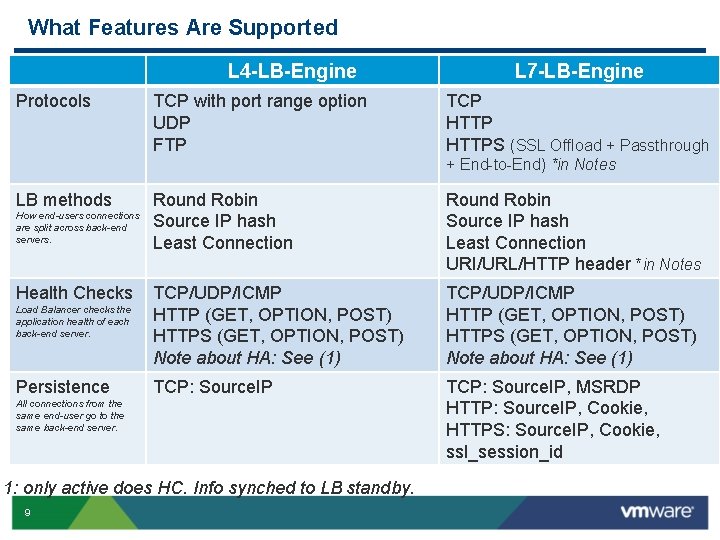
What Features Are Supported L 4 -LB-Engine Protocols TCP with port range option UDP FTP L 7 -LB-Engine TCP HTTPS (SSL Offload + Passthrough + End-to-End) *in Notes LB methods Round Robin Source IP hash Least Connection URI/URL/HTTP header *in Notes Load Balancer checks the application health of each back-end server. TCP/UDP/ICMP HTTP (GET, OPTION, POST) HTTPS (GET, OPTION, POST) Note about HA: See (1) Persistence TCP: Source. IP, MSRDP HTTP: Source. IP, Cookie, HTTPS: Source. IP, Cookie, ssl_session_id How end-users connections are split across back-end servers. Health Checks All connections from the same end-user go to the same back-end server. 1: only active does HC. Info synched to LB standby. 9
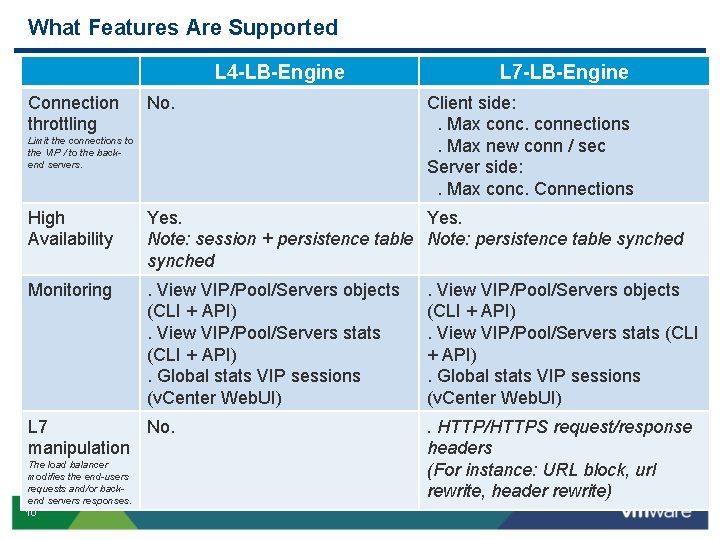
What Features Are Supported L 4 -LB-Engine Connection throttling No. Limit the connections to the VIP / to the backend servers. L 7 -LB-Engine Client side: . Max conc. connections. Max new conn / sec Server side: . Max conc. Connections High Availability Yes. Note: session + persistence table Note: persistence table synched Monitoring . View VIP/Pool/Servers objects (CLI + API). View VIP/Pool/Servers stats (CLI + API). Global stats VIP sessions (v. Center Web. UI) L 7 No. manipulation The load balancer modifies the end-users requests and/or backend servers responses. 10 . View VIP/Pool/Servers objects (CLI + API). View VIP/Pool/Servers stats (CLI + API). Global stats VIP sessions (v. Center Web. UI). HTTP/HTTPS request/response headers (For instance: URL block, url rewrite, header rewrite)
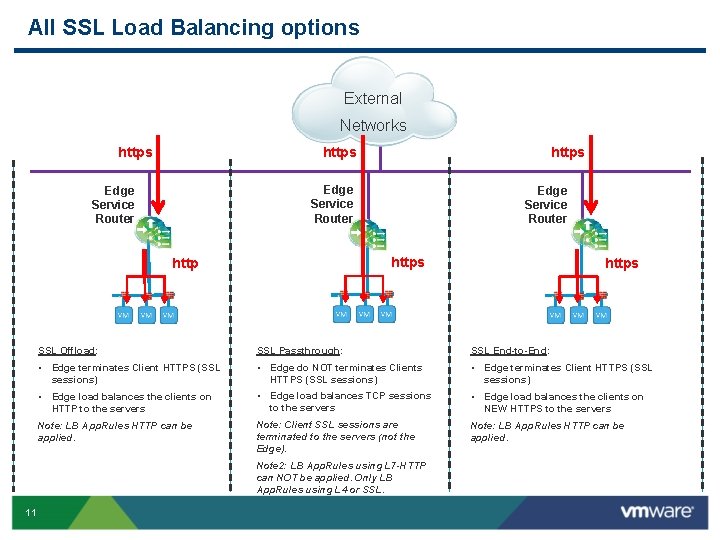
All SSL Load Balancing options External Networks https Edge Service Router https http SSL Offload: SSL Passthrough: SSL End-to-End: • Edge terminates Client HTTPS (SSL sessions) • Edge do NOT terminates Clients HTTPS (SSL sessions) • Edge terminates Client HTTPS (SSL sessions) • Edge load balances the clients on HTTP to the servers • Edge load balances TCP sessions to the servers • Edge load balances the clients on NEW HTTPS to the servers Note: LB App. Rules HTTP can be applied. Note: Client SSL sessions are terminated to the servers (not the Edge). Note: LB App. Rules HTTP can be applied. Note 2: LB App. Rules using L 7 -HTTP can NOT be applied. Only LB App. Rules using L 4 or SSL. 11 https
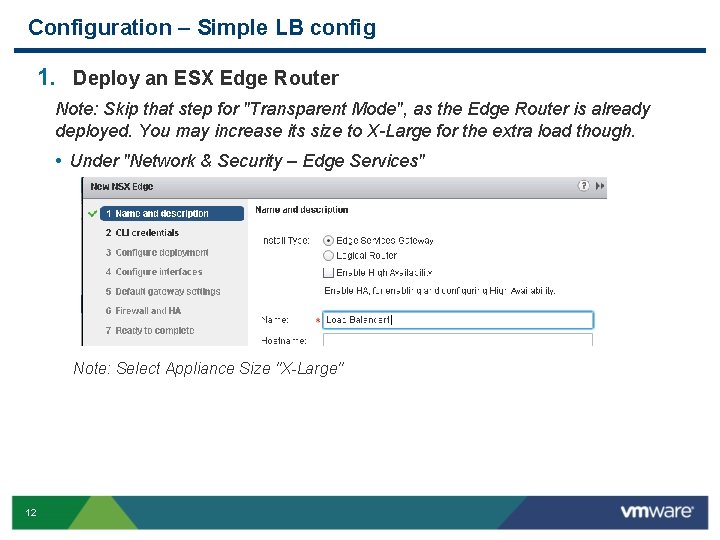
Configuration – Simple LB config 1. Deploy an ESX Edge Router Note: Skip that step for "Transparent Mode", as the Edge Router is already deployed. You may increase its size to X-Large for the extra load though. • Under "Network & Security – Edge Services" Note: Select Appliance Size "X-Large" 12
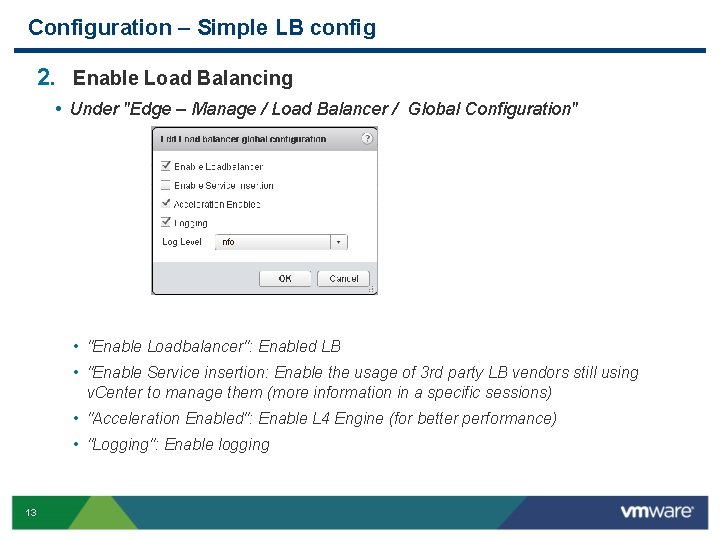
Configuration – Simple LB config 2. Enable Load Balancing • Under "Edge – Manage / Load Balancer / Global Configuration" • "Enable Loadbalancer": Enabled LB • "Enable Service insertion: Enable the usage of 3 rd party LB vendors still using v. Center to manage them (more information in a specific sessions) • "Acceleration Enabled": Enable L 4 Engine (for better performance) • "Logging": Enable logging 13
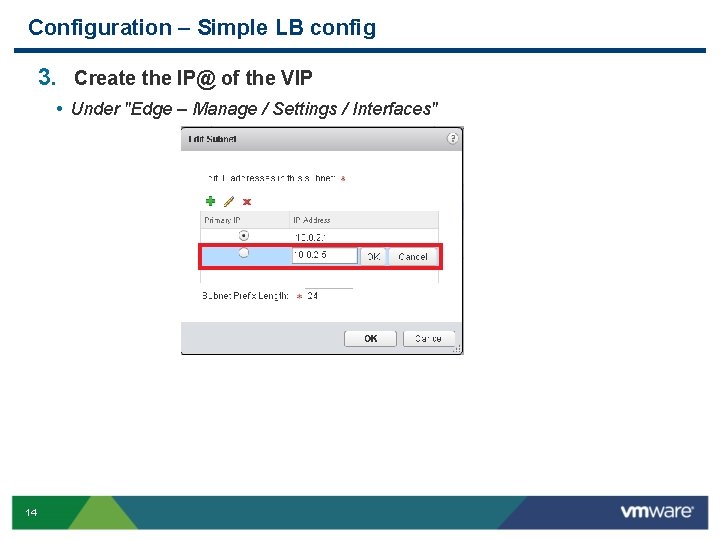
Configuration – Simple LB config 3. Create the IP@ of the VIP • Under "Edge – Manage / Settings / Interfaces" 14
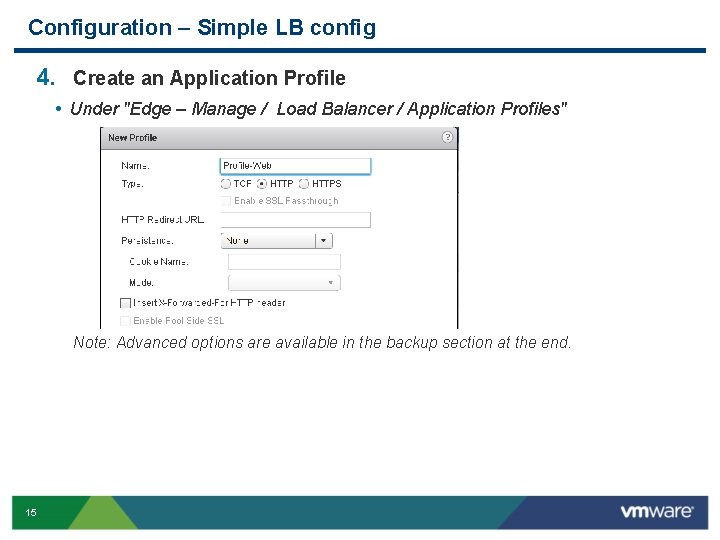
Configuration – Simple LB config 4. Create an Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" Note: Advanced options are available in the backup section at the end. 15
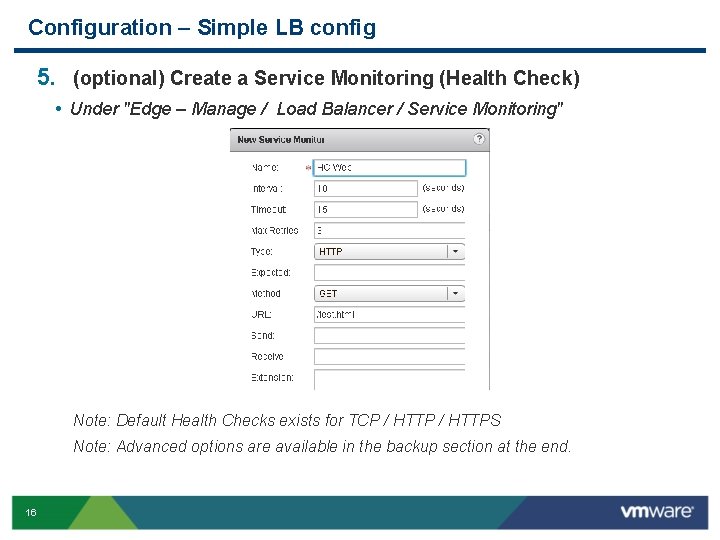
Configuration – Simple LB config 5. (optional) Create a Service Monitoring (Health Check) • Under "Edge – Manage / Load Balancer / Service Monitoring" Note: Default Health Checks exists for TCP / HTTPS Note: Advanced options are available in the backup section at the end. 16
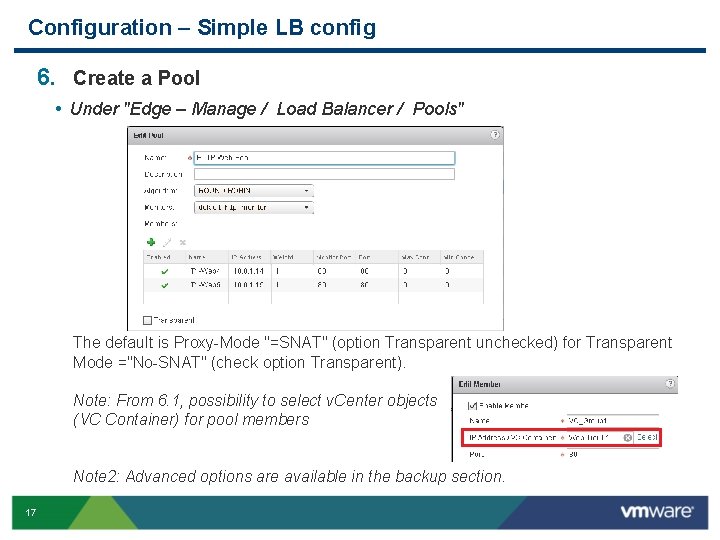
Configuration – Simple LB config 6. Create a Pool • Under "Edge – Manage / Load Balancer / Pools" The default is Proxy-Mode "=SNAT" (option Transparent unchecked) for Transparent Mode ="No-SNAT" (check option Transparent). Note: From 6. 1, possibility to select v. Center objects (VC Container) for pool members Note 2: Advanced options are available in the backup section. 17
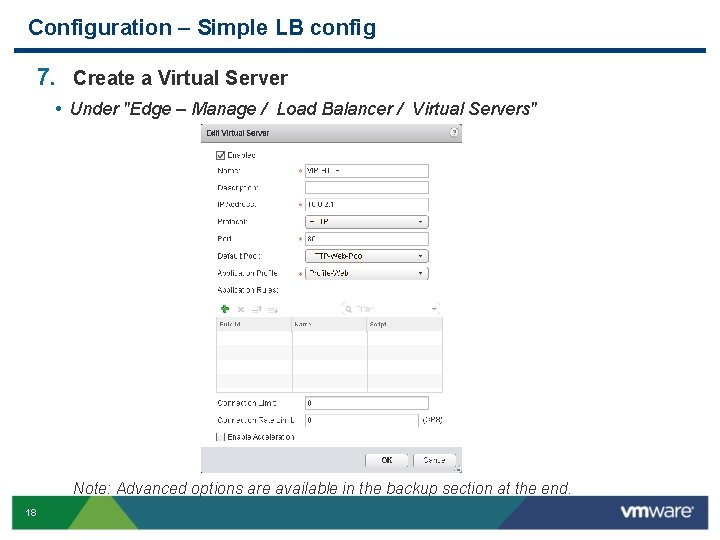
Configuration – Simple LB config 7. Create a Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Note: Advanced options are available in the backup section at the end. 18
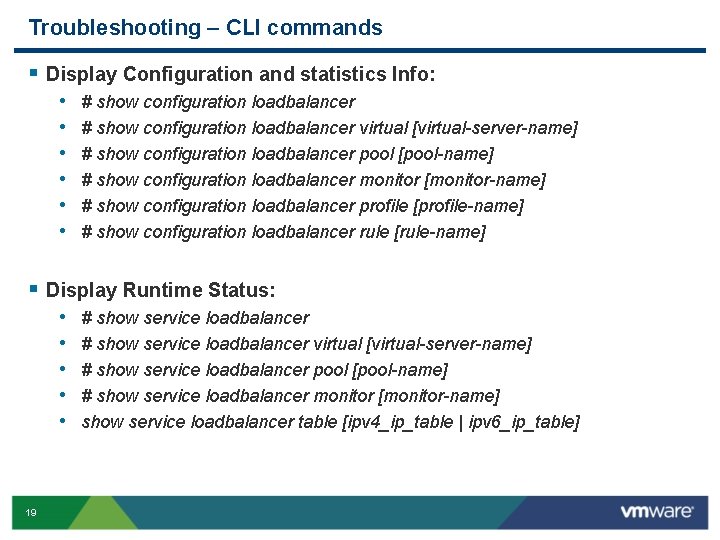
Troubleshooting – CLI commands § Display Configuration and statistics Info: • • • # show configuration loadbalancer virtual [virtual-server-name] # show configuration loadbalancer pool [pool-name] # show configuration loadbalancer monitor [monitor-name] # show configuration loadbalancer profile [profile-name] # show configuration loadbalancer rule [rule-name] § Display Runtime Status: • • • 19 # show service loadbalancer virtual [virtual-server-name] # show service loadbalancer pool [pool-name] # show service loadbalancer monitor [monitor-name] show service loadbalancer table [ipv 4_ip_table | ipv 6_ip_table]
Key Takeaways § NSX | v. Sphere Load Balancing is about • A Cloud Ready solution with LB Services • REST APIs • Easy to manage • Integrated into v. Center • Single point of management • Offering built-in LB services for most common applications § NSX | v. Sphere Load Balancing is NOT about • # of features However we have already a rich feature set that already replies to 80+% needs • Very high-end scale However our scale are very decent and reply to most customers needs 20
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 21
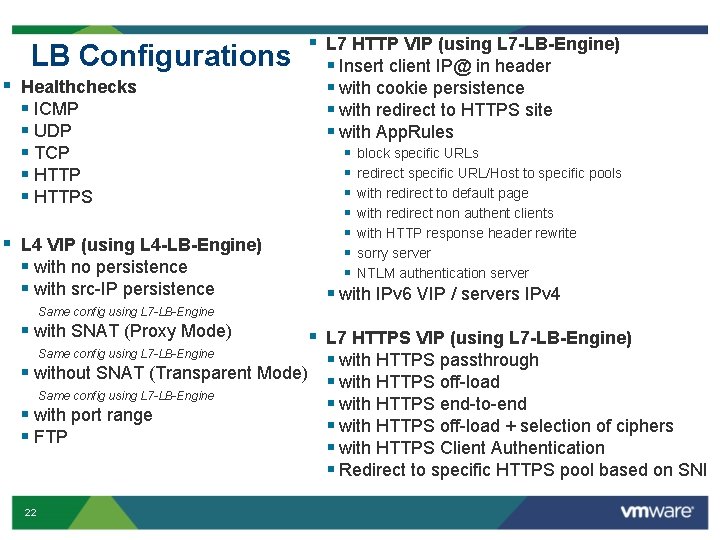
LB Configurations § Healthchecks § ICMP § UDP § TCP § HTTPS § L 4 VIP (using L 4 -LB-Engine) § with no persistence § with src-IP persistence § L 7 HTTP VIP (using L 7 -LB-Engine) § Insert client IP@ in header § with cookie persistence § with redirect to HTTPS site § with App. Rules § § § § block specific URLs redirect specific URL/Host to specific pools with redirect to default page with redirect non authent clients with HTTP response header rewrite sorry server NTLM authentication server § with IPv 6 VIP / servers IPv 4 Same config using L 7 -LB-Engine § with SNAT (Proxy Mode) § L 7 HTTPS VIP (using L 7 -LB-Engine) Same config using L 7 -LB-Engine § with HTTPS passthrough § without SNAT (Transparent Mode) § with HTTPS off-load Same config using L 7 -LB-Engine § with HTTPS end-to-end § with port range § with HTTPS off-load + selection of ciphers § FTP § with HTTPS Client Authentication § Redirect to specific HTTPS pool based on SNI 22
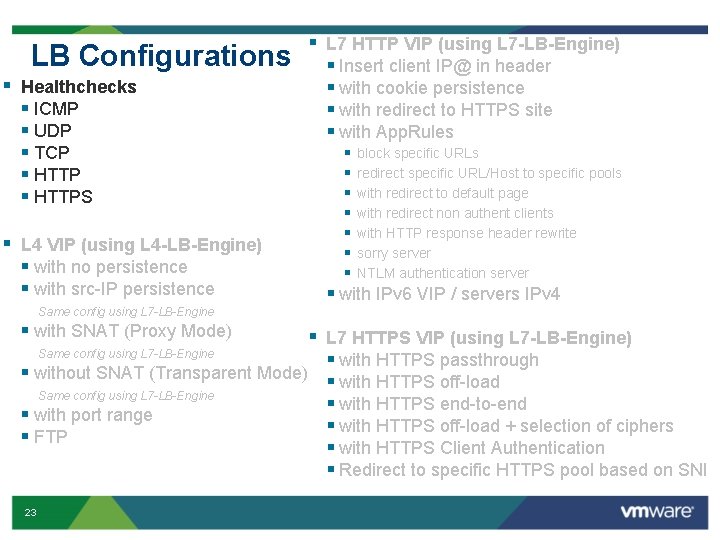
LB Configurations § Healthchecks § ICMP § UDP § TCP § HTTPS § L 4 VIP (using L 4 -LB-Engine) § with no persistence § with src-IP persistence § L 7 HTTP VIP (using L 7 -LB-Engine) § Insert client IP@ in header § with cookie persistence § with redirect to HTTPS site § with App. Rules § § § § block specific URLs redirect specific URL/Host to specific pools with redirect to default page with redirect non authent clients with HTTP response header rewrite sorry server NTLM authentication server § with IPv 6 VIP / servers IPv 4 Same config using L 7 -LB-Engine § with SNAT (Proxy Mode) § L 7 HTTPS VIP (using L 7 -LB-Engine) Same config using L 7 -LB-Engine § with HTTPS passthrough § without SNAT (Transparent Mode) § with HTTPS off-load Same config using L 7 -LB-Engine § with HTTPS end-to-end § with port range § with HTTPS off-load + selection of ciphers § FTP § with HTTPS Client Authentication § Redirect to specific HTTPS pool based on SNI 23
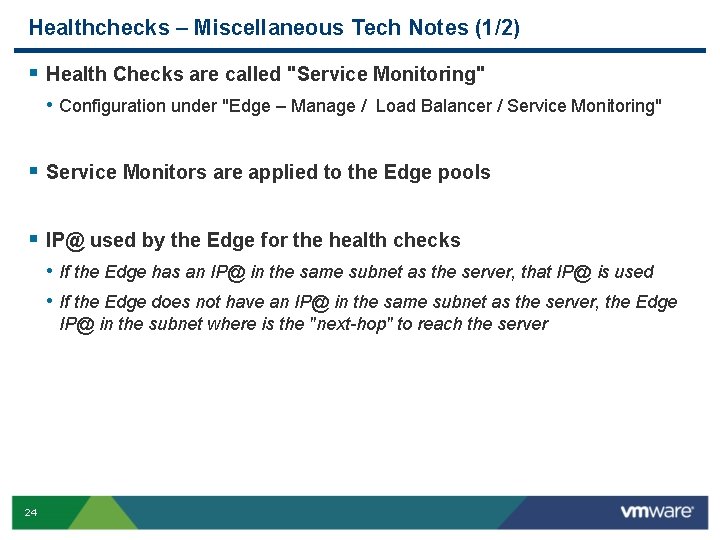
Healthchecks – Miscellaneous Tech Notes (1/2) § Health Checks are called "Service Monitoring" • Configuration under "Edge – Manage / Load Balancer / Service Monitoring" § Service Monitors are applied to the Edge pools § IP@ used by the Edge for the health checks • If the Edge has an IP@ in the same subnet as the server, that IP@ is used • If the Edge does not have an IP@ in the same subnet as the server, the Edge IP@ in the subnet where is the "next-hop" to reach the server 24
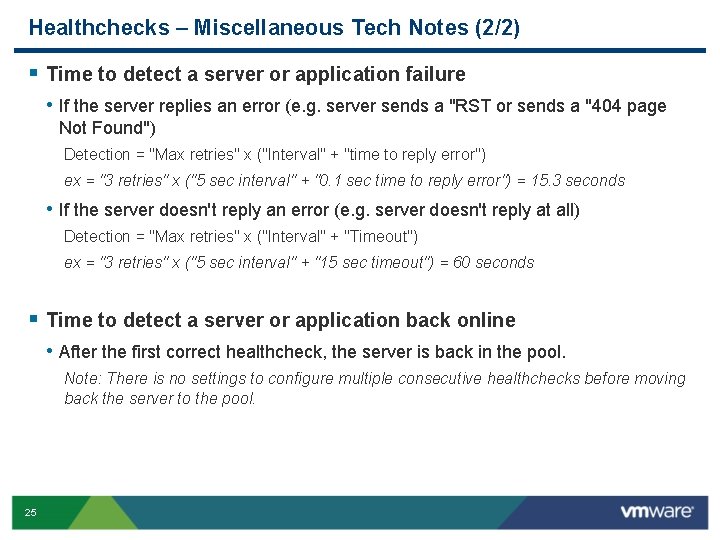
Healthchecks – Miscellaneous Tech Notes (2/2) § Time to detect a server or application failure • If the server replies an error (e. g. server sends a "RST or sends a "404 page Not Found") Detection = "Max retries" x ("Interval" + "time to reply error") ex = "3 retries" x ("5 sec interval" + "0. 1 sec time to reply error") = 15. 3 seconds • If the server doesn't reply an error (e. g. server doesn't reply at all) Detection = "Max retries" x ("Interval" + "Timeout") ex = "3 retries" x ("5 sec interval" + "15 sec timeout") = 60 seconds § Time to detect a server or application back online • After the first correct healthcheck, the server is back in the pool. Note: There is no settings to configure multiple consecutive healthchecks before moving back the server to the pool. 25
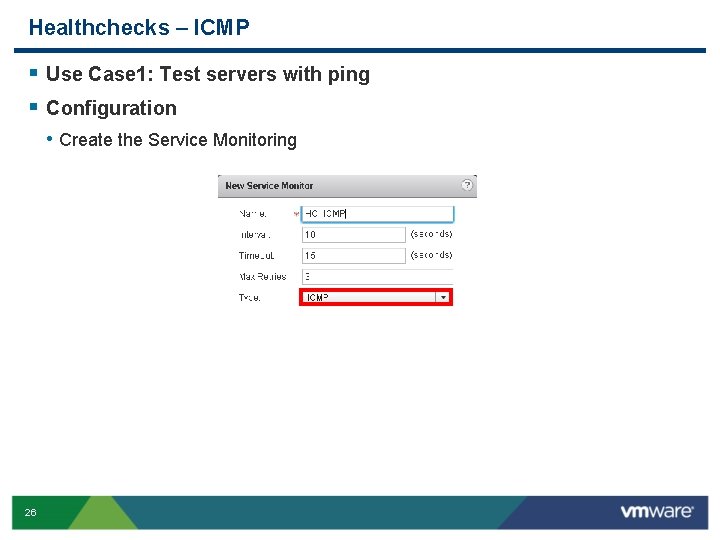
Healthchecks – ICMP § Use Case 1: Test servers with ping § Configuration • Create the Service Monitoring 26
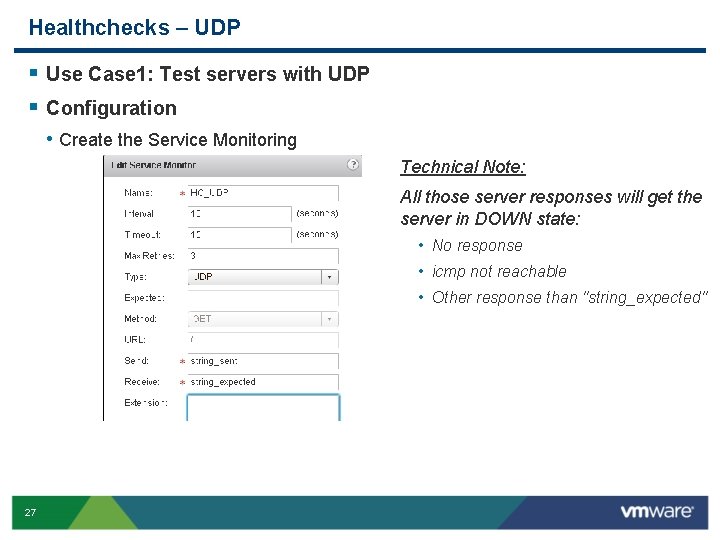
Healthchecks – UDP § Use Case 1: Test servers with UDP § Configuration • Create the Service Monitoring Technical Note: All those server responses will get the server in DOWN state: • No response • icmp not reachable • Other response than "string_expected" 27
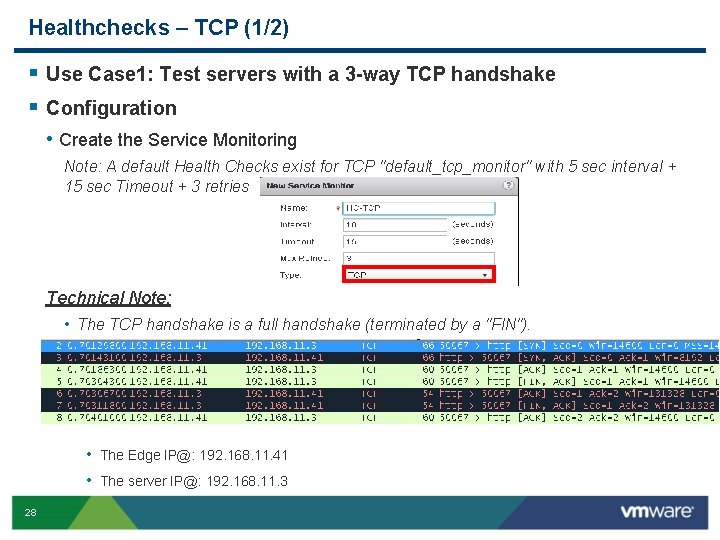
Healthchecks – TCP (1/2) § Use Case 1: Test servers with a 3 -way TCP handshake § Configuration • Create the Service Monitoring Note: A default Health Checks exist for TCP "default_tcp_monitor" with 5 sec interval + 15 sec Timeout + 3 retries Technical Note: • The TCP handshake is a full handshake (terminated by a "FIN"). • The Edge IP@: 192. 168. 11. 41 • The server IP@: 192. 168. 11. 3 28
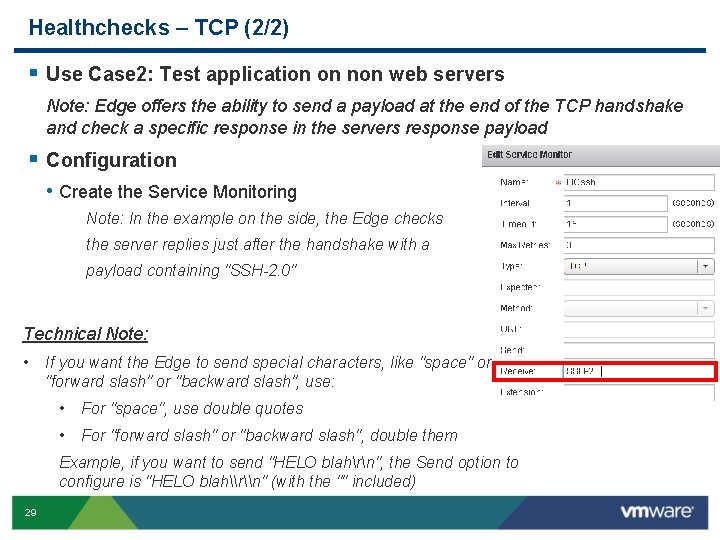
Healthchecks – TCP (2/2) § Use Case 2: Test application on non web servers Note: Edge offers the ability to send a payload at the end of the TCP handshake and check a specific response in the servers response payload § Configuration • Create the Service Monitoring Note: In the example on the side, the Edge checks the server replies just after the handshake with a payload containing "SSH-2. 0" Technical Note: • If you want the Edge to send special characters, like "space" or "forward slash" or "backward slash", use: • For "space", use double quotes • For "forward slash" or "backward slash", double them Example, if you want to send "HELO blahrn", the Send option to configure is "HELO blah\r\n" (with the "" included) 29
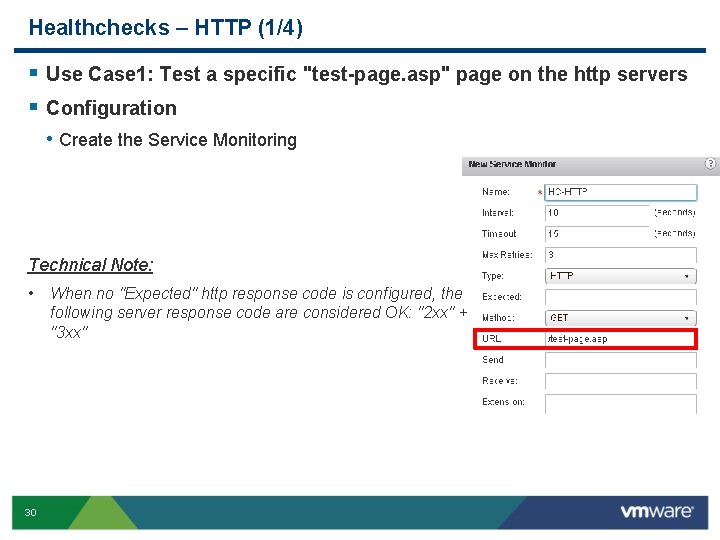
Healthchecks – HTTP (1/4) § Use Case 1: Test a specific "test-page. asp" page on the http servers § Configuration • Create the Service Monitoring Technical Note: • 30 When no "Expected" http response code is configured, the following server response code are considered OK: "2 xx" + "3 xx"
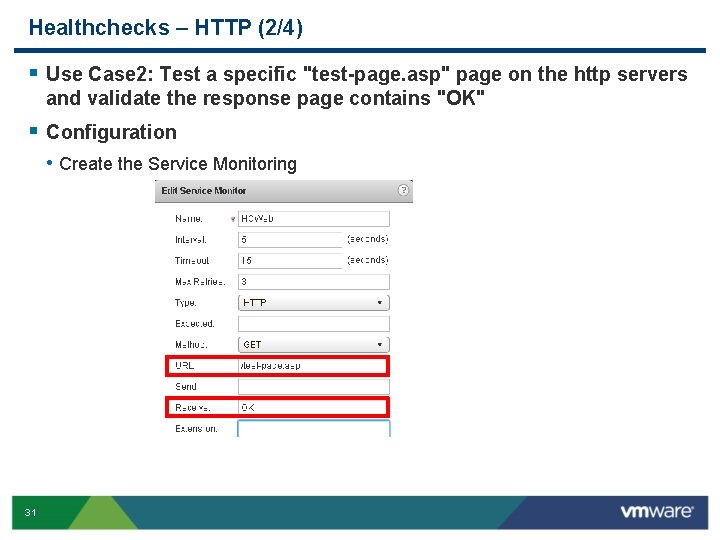
Healthchecks – HTTP (2/4) § Use Case 2: Test a specific "test-page. asp" page on the http servers and validate the response page contains "OK" § Configuration • Create the Service Monitoring 31
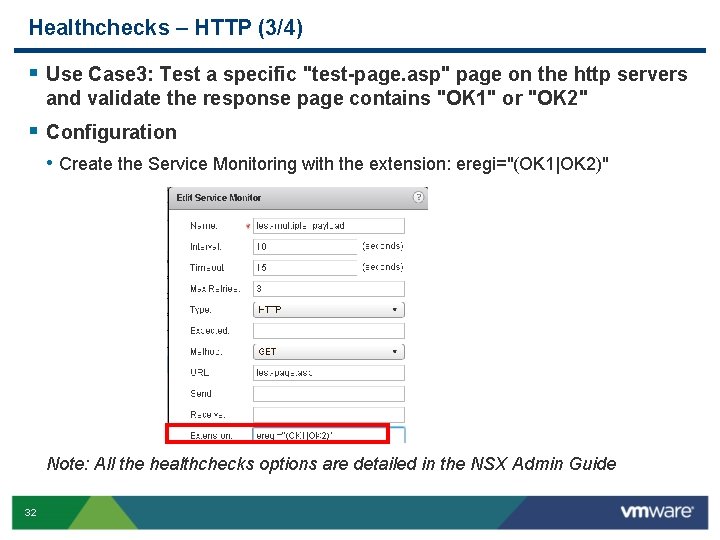
Healthchecks – HTTP (3/4) § Use Case 3: Test a specific "test-page. asp" page on the http servers and validate the response page contains "OK 1" or "OK 2" § Configuration • Create the Service Monitoring with the extension: eregi="(OK 1|OK 2)" Note: All the healthchecks options are detailed in the NSX Admin Guide 32
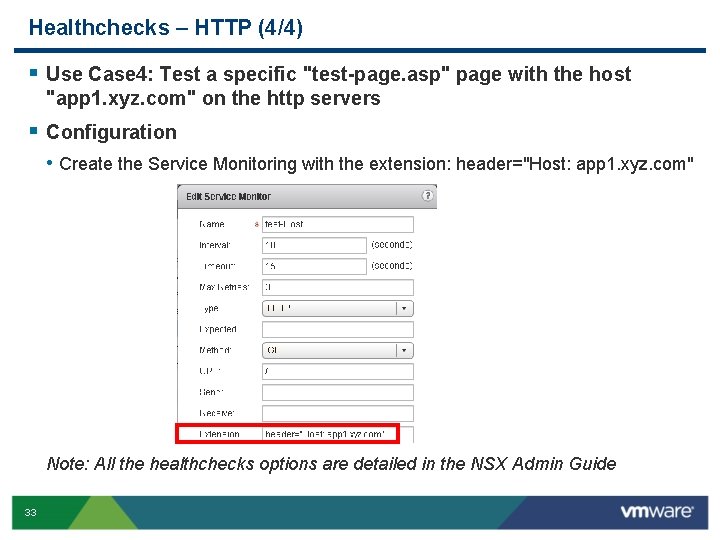
Healthchecks – HTTP (4/4) § Use Case 4: Test a specific "test-page. asp" page with the host "app 1. xyz. com" on the http servers § Configuration • Create the Service Monitoring with the extension: header="Host: app 1. xyz. com" Note: All the healthchecks options are detailed in the NSX Admin Guide 33
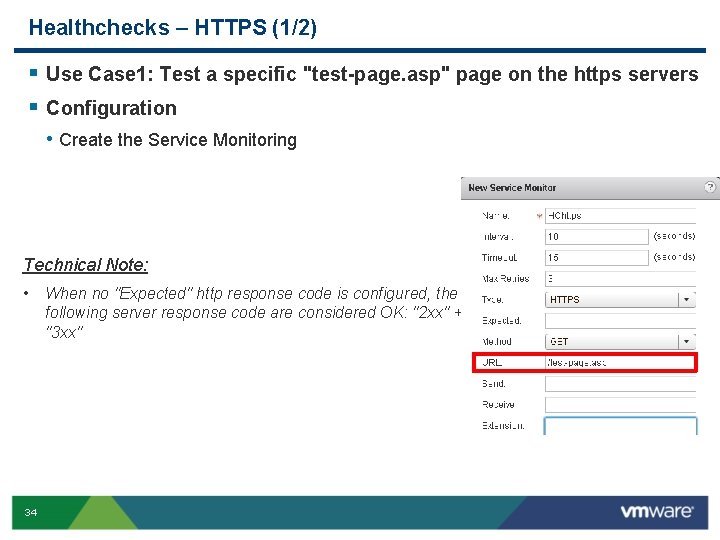
Healthchecks – HTTPS (1/2) § Use Case 1: Test a specific "test-page. asp" page on the https servers § Configuration • Create the Service Monitoring Technical Note: • 34 When no "Expected" http response code is configured, the following server response code are considered OK: "2 xx" + "3 xx"
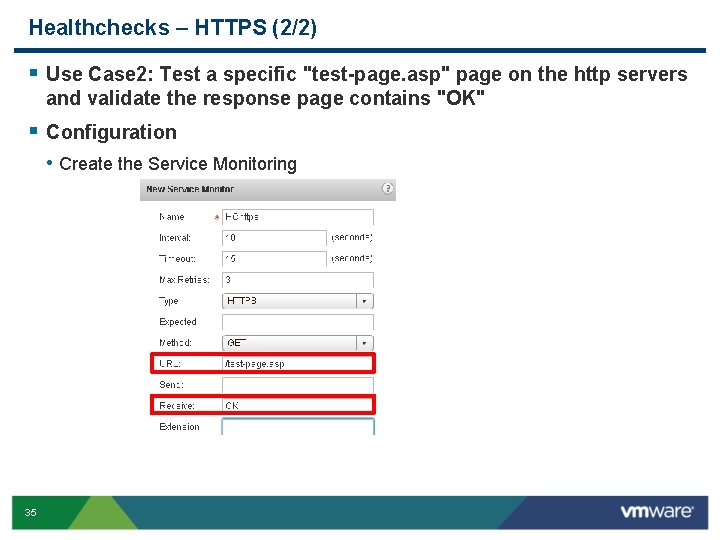
Healthchecks – HTTPS (2/2) § Use Case 2: Test a specific "test-page. asp" page on the http servers and validate the response page contains "OK" § Configuration • Create the Service Monitoring 35
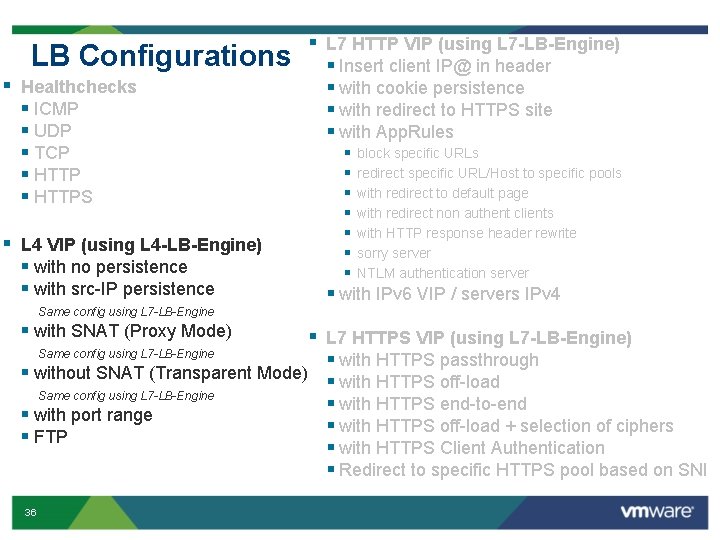
LB Configurations § Healthchecks § ICMP § UDP § TCP § HTTPS § L 4 VIP (using L 4 -LB-Engine) § with no persistence § with src-IP persistence § L 7 HTTP VIP (using L 7 -LB-Engine) § Insert client IP@ in header § with cookie persistence § with redirect to HTTPS site § with App. Rules § § § § block specific URLs redirect specific URL/Host to specific pools with redirect to default page with redirect non authent clients with HTTP response header rewrite sorry server NTLM authentication server § with IPv 6 VIP / servers IPv 4 Same config using L 7 -LB-Engine § with SNAT (Proxy Mode) § L 7 HTTPS VIP (using L 7 -LB-Engine) Same config using L 7 -LB-Engine § with HTTPS passthrough § without SNAT (Transparent Mode) § with HTTPS off-load Same config using L 7 -LB-Engine § with HTTPS end-to-end § with port range § with HTTPS off-load + selection of ciphers § FTP § with HTTPS Client Authentication § Redirect to specific HTTPS pool based on SNI 36
L 4 VIP – Miscellaneous Tech Notes § The Edge offers 2 load balancer engines: • L 4 -Eng • L 7 -Eng § The L 4 -Eng can be used to load balance any UDP/TCP application such as DNS, LDAP, IMAP, FTP, or even HTTP/HTTPS § L 4 VIP is processed before the Edge Firewall • Edge Firewall (under "Edge – Manage / Firewall") can not block access to L 4 VIP • However Firewall must be enabled in case of L 4 with SNAT (non transparent mode) 37
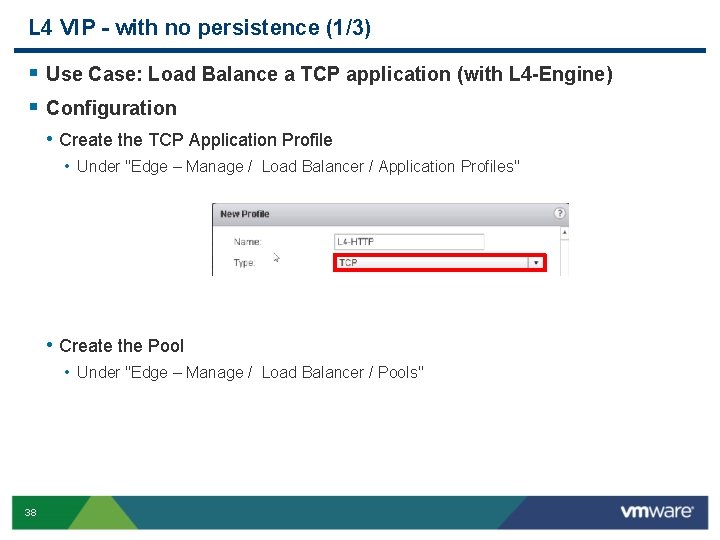
L 4 VIP - with no persistence (1/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) § Configuration • Create the TCP Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" • Create the Pool • Under "Edge – Manage / Load Balancer / Pools" 38
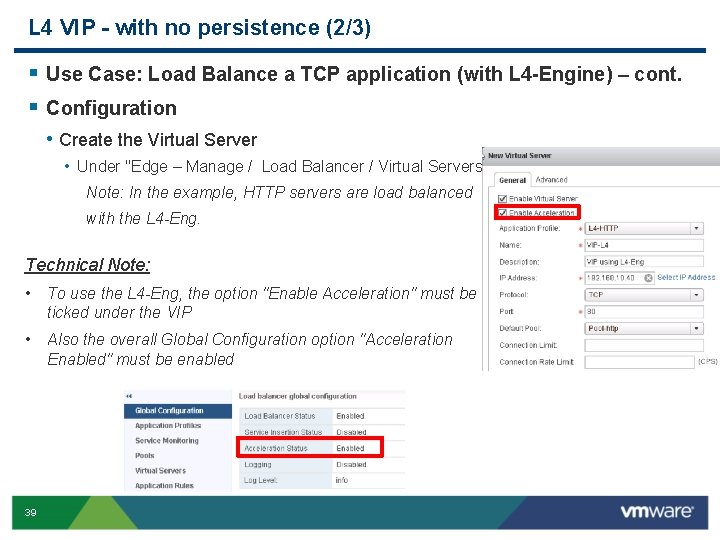
L 4 VIP - with no persistence (2/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) – cont. § Configuration • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Note: In the example, HTTP servers are load balanced with the L 4 -Eng. Technical Note: • To use the L 4 -Eng, the option "Enable Acceleration" must be ticked under the VIP • Also the overall Global Configuration option "Acceleration Enabled" must be enabled 39
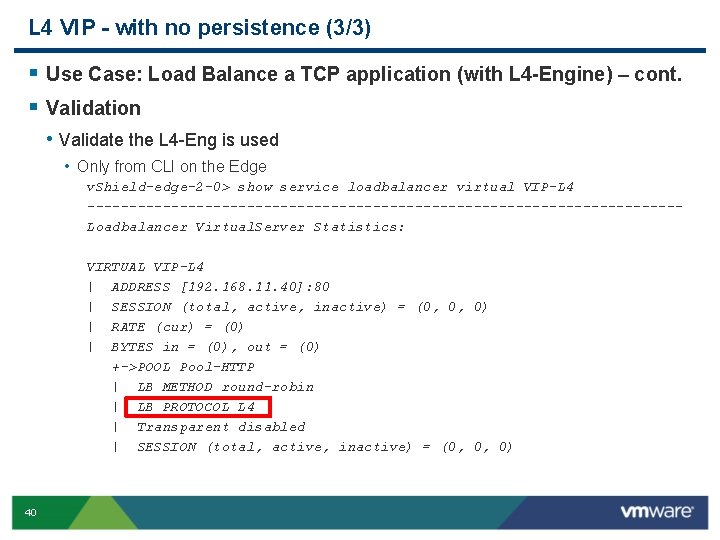
L 4 VIP - with no persistence (3/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) – cont. § Validation • Validate the L 4 -Eng is used • Only from CLI on the Edge v. Shield-edge-2 -0> show service loadbalancer virtual VIP-L 4 -----------------------------------Loadbalancer Virtual. Server Statistics: VIRTUAL VIP-L 4 | ADDRESS [192. 168. 11. 40]: 80 | SESSION (total, active, inactive) = (0, 0, 0) | RATE (cur) = (0) | BYTES in = (0), out = (0) +->POOL Pool-HTTP | LB METHOD round-robin | LB PROTOCOL L 4 | Transparent disabled | SESSION (total, active, inactive) = (0, 0, 0) 40
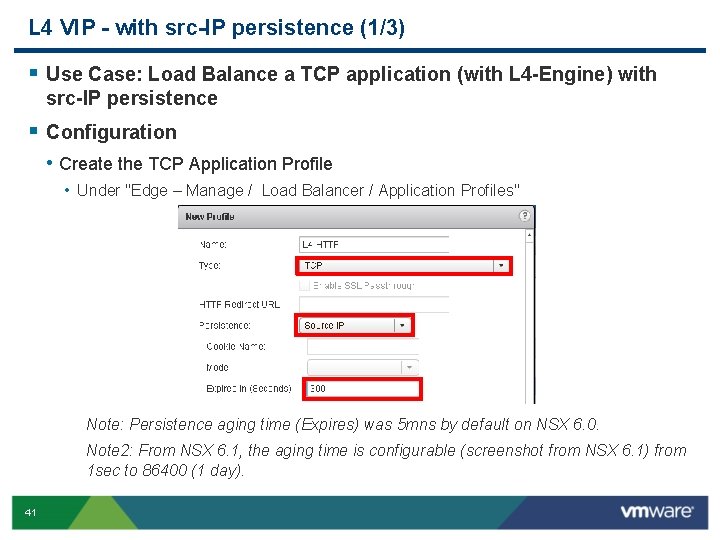
L 4 VIP - with src-IP persistence (1/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) with src-IP persistence § Configuration • Create the TCP Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" Note: Persistence aging time (Expires) was 5 mns by default on NSX 6. 0. Note 2: From NSX 6. 1, the aging time is configurable (screenshot from NSX 6. 1) from 1 sec to 86400 (1 day). 41
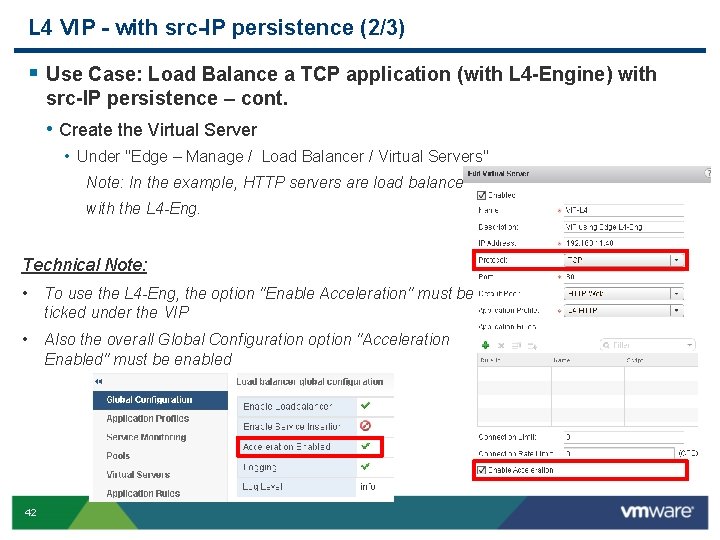
L 4 VIP - with src-IP persistence (2/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) with src-IP persistence – cont. • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Note: In the example, HTTP servers are load balanced with the L 4 -Eng. Technical Note: • To use the L 4 -Eng, the option "Enable Acceleration" must be ticked under the VIP • Also the overall Global Configuration option "Acceleration Enabled" must be enabled 42
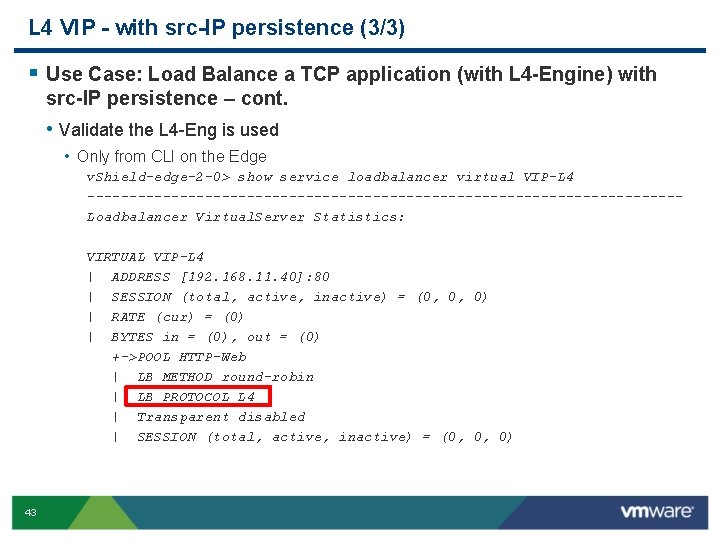
L 4 VIP - with src-IP persistence (3/3) § Use Case: Load Balance a TCP application (with L 4 -Engine) with src-IP persistence – cont. • Validate the L 4 -Eng is used • Only from CLI on the Edge v. Shield-edge-2 -0> show service loadbalancer virtual VIP-L 4 -----------------------------------Loadbalancer Virtual. Server Statistics: VIRTUAL VIP-L 4 | ADDRESS [192. 168. 11. 40]: 80 | SESSION (total, active, inactive) = (0, 0, 0) | RATE (cur) = (0) | BYTES in = (0), out = (0) +->POOL HTTP-Web | LB METHOD round-robin | LB PROTOCOL L 4 | Transparent disabled | SESSION (total, active, inactive) = (0, 0, 0) 43
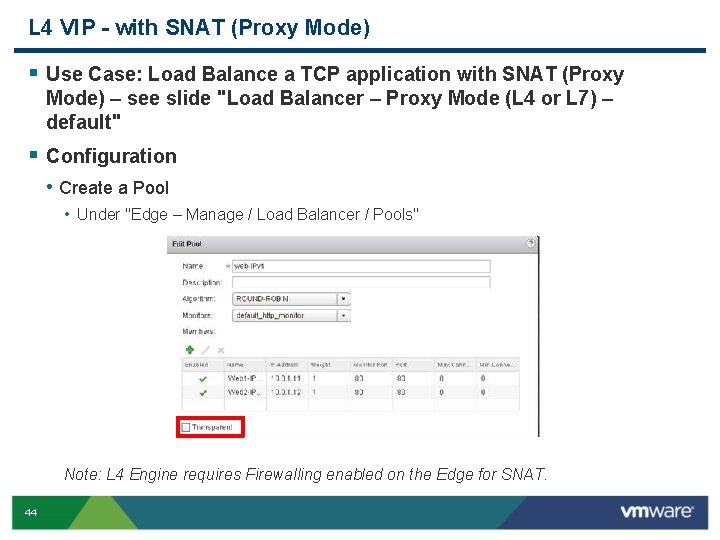
L 4 VIP - with SNAT (Proxy Mode) § Use Case: Load Balance a TCP application with SNAT (Proxy Mode) – see slide "Load Balancer – Proxy Mode (L 4 or L 7) – default" § Configuration • Create a Pool • Under "Edge – Manage / Load Balancer / Pools" Note: L 4 Engine requires Firewalling enabled on the Edge for SNAT. 44
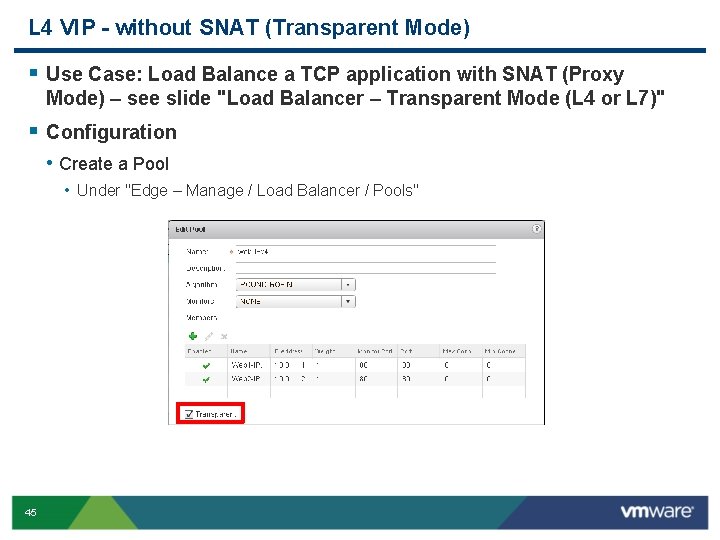
L 4 VIP - without SNAT (Transparent Mode) § Use Case: Load Balance a TCP application with SNAT (Proxy Mode) – see slide "Load Balancer – Transparent Mode (L 4 or L 7)" § Configuration • Create a Pool • Under "Edge – Manage / Load Balancer / Pools" 45
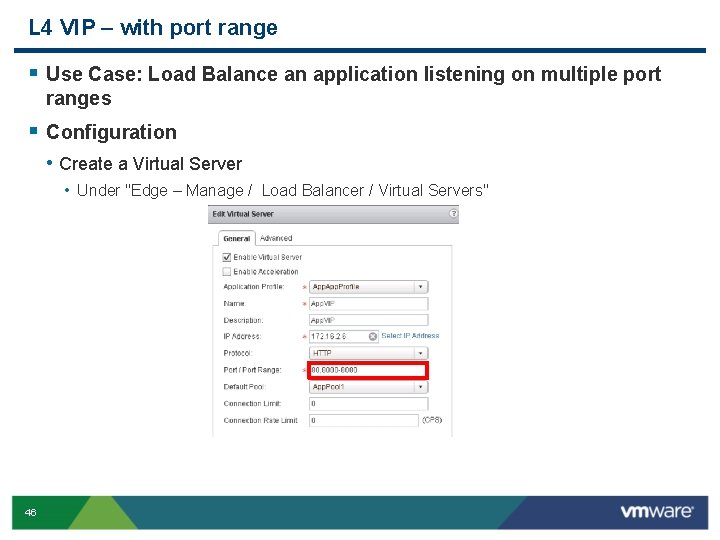
L 4 VIP – with port range § Use Case: Load Balance an application listening on multiple port ranges § Configuration • Create a Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 46
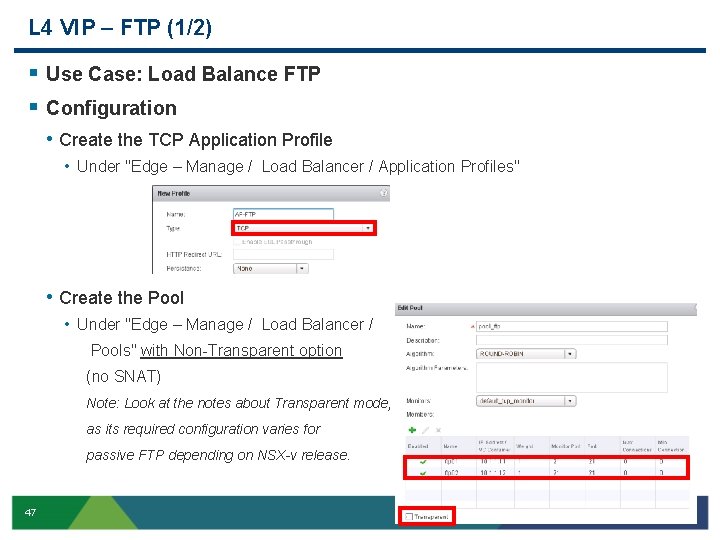
L 4 VIP – FTP (1/2) § Use Case: Load Balance FTP § Configuration • Create the TCP Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" • Create the Pool • Under "Edge – Manage / Load Balancer / Pools" with Non-Transparent option (no SNAT) Note: Look at the notes about Transparent mode, as its required configuration varies for passive FTP depending on NSX-v release. 47
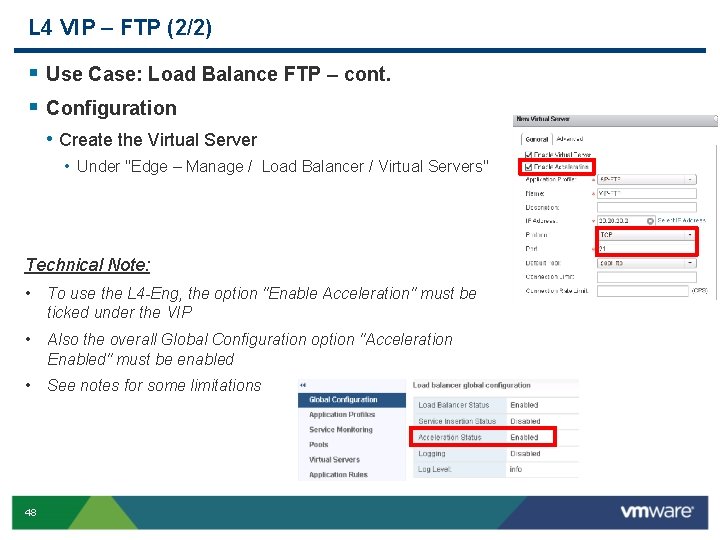
L 4 VIP – FTP (2/2) § Use Case: Load Balance FTP – cont. § Configuration • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: • To use the L 4 -Eng, the option "Enable Acceleration" must be ticked under the VIP • Also the overall Global Configuration option "Acceleration Enabled" must be enabled • See notes for some limitations 48
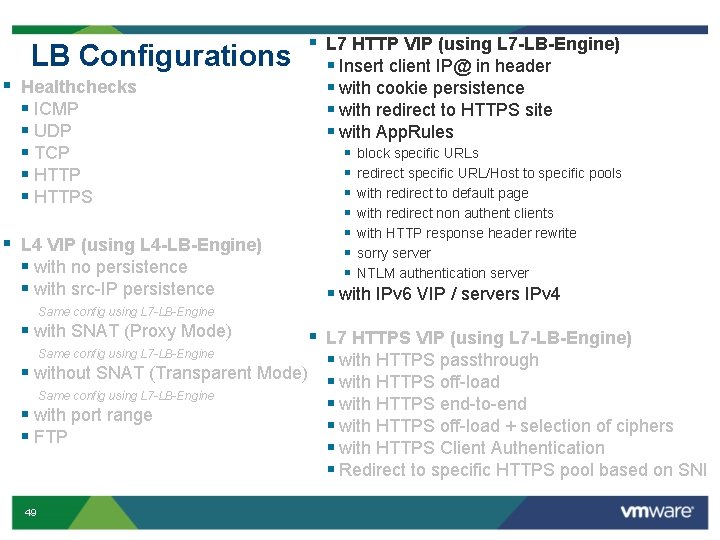
LB Configurations § Healthchecks § ICMP § UDP § TCP § HTTPS § L 4 VIP (using L 4 -LB-Engine) § with no persistence § with src-IP persistence § L 7 HTTP VIP (using L 7 -LB-Engine) § Insert client IP@ in header § with cookie persistence § with redirect to HTTPS site § with App. Rules § § § § block specific URLs redirect specific URL/Host to specific pools with redirect to default page with redirect non authent clients with HTTP response header rewrite sorry server NTLM authentication server § with IPv 6 VIP / servers IPv 4 Same config using L 7 -LB-Engine § with SNAT (Proxy Mode) § L 7 HTTPS VIP (using L 7 -LB-Engine) Same config using L 7 -LB-Engine § with HTTPS passthrough § without SNAT (Transparent Mode) § with HTTPS off-load Same config using L 7 -LB-Engine § with HTTPS end-to-end § with port range § with HTTPS off-load + selection of ciphers § FTP § with HTTPS Client Authentication § Redirect to specific HTTPS pool based on SNI 49
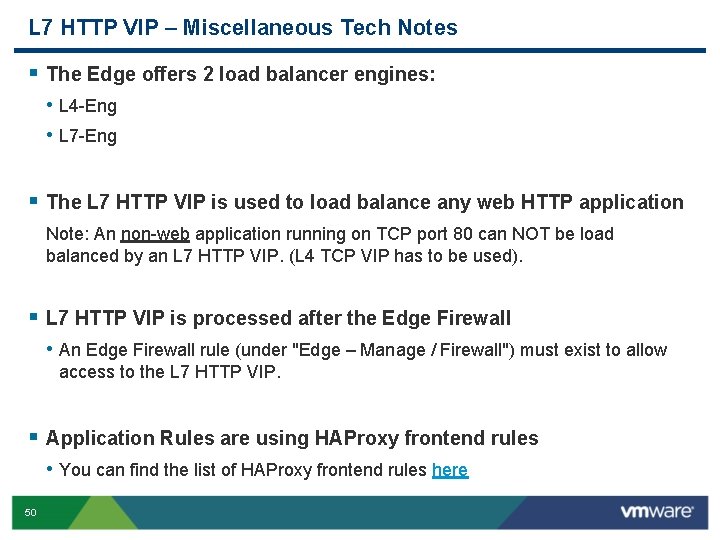
L 7 HTTP VIP – Miscellaneous Tech Notes § The Edge offers 2 load balancer engines: • L 4 -Eng • L 7 -Eng § The L 7 HTTP VIP is used to load balance any web HTTP application Note: An non-web application running on TCP port 80 can NOT be load balanced by an L 7 HTTP VIP. (L 4 TCP VIP has to be used). § L 7 HTTP VIP is processed after the Edge Firewall • An Edge Firewall rule (under "Edge – Manage / Firewall") must exist to allow access to the L 7 HTTP VIP. § Application Rules are using HAProxy frontend rules • You can find the list of HAProxy frontend rules here 50
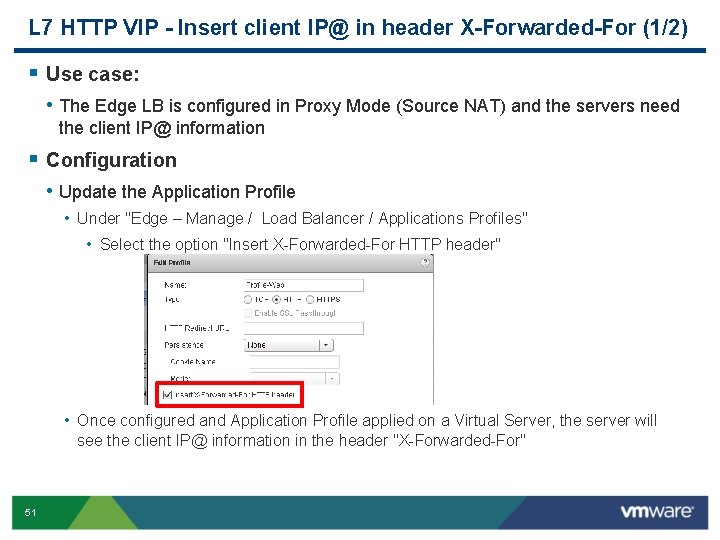
L 7 HTTP VIP - Insert client IP@ in header X-Forwarded-For (1/2) § Use case: • The Edge LB is configured in Proxy Mode (Source NAT) and the servers need the client IP@ information § Configuration • Update the Application Profile • Under "Edge – Manage / Load Balancer / Applications Profiles" • Select the option "Insert X-Forwarded-For HTTP header" • Once configured and Application Profile applied on a Virtual Server, the server will see the client IP@ information in the header "X-Forwarded-For" 51
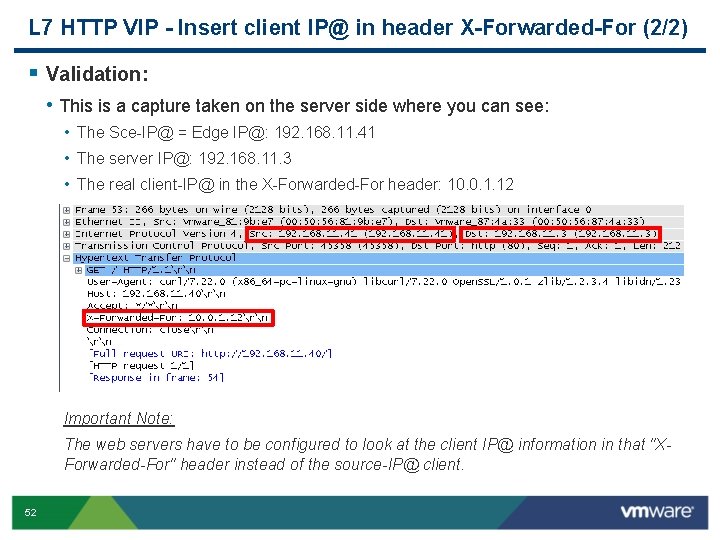
L 7 HTTP VIP - Insert client IP@ in header X-Forwarded-For (2/2) § Validation: • This is a capture taken on the server side where you can see: • The Sce-IP@ = Edge IP@: 192. 168. 11. 41 • The server IP@: 192. 168. 11. 3 • The real client-IP@ in the X-Forwarded-For header: 10. 0. 1. 12 Important Note: The web servers have to be configured to look at the client IP@ information in that "XForwarded-For" header instead of the source-IP@ client. 52
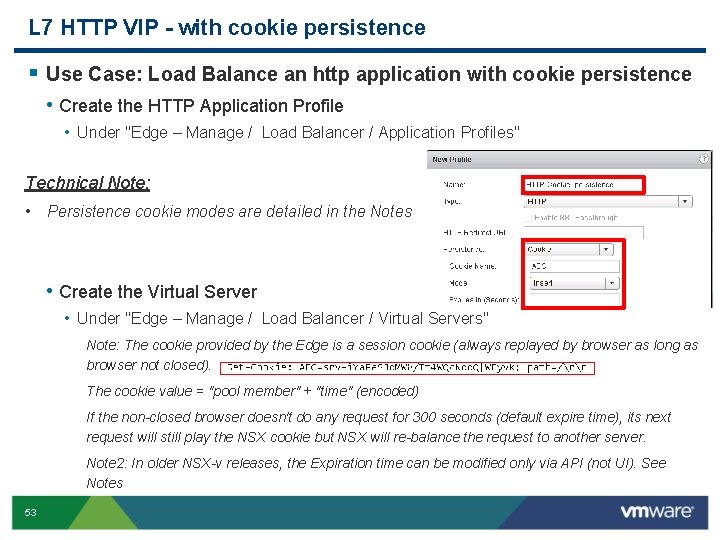
L 7 HTTP VIP - with cookie persistence § Use Case: Load Balance an http application with cookie persistence • Create the HTTP Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" Technical Note: • Persistence cookie modes are detailed in the Notes • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Note: The cookie provided by the Edge is a session cookie (always replayed by browser as long as browser not closed). The cookie value = "pool member" + "time" (encoded) If the non-closed browser doesn't do any request for 300 seconds (default expire time), its next request will still play the NSX cookie but NSX will re-balance the request to another server. Note 2: In older NSX-v releases, the Expiration time can be modified only via API (not UI). See Notes 53
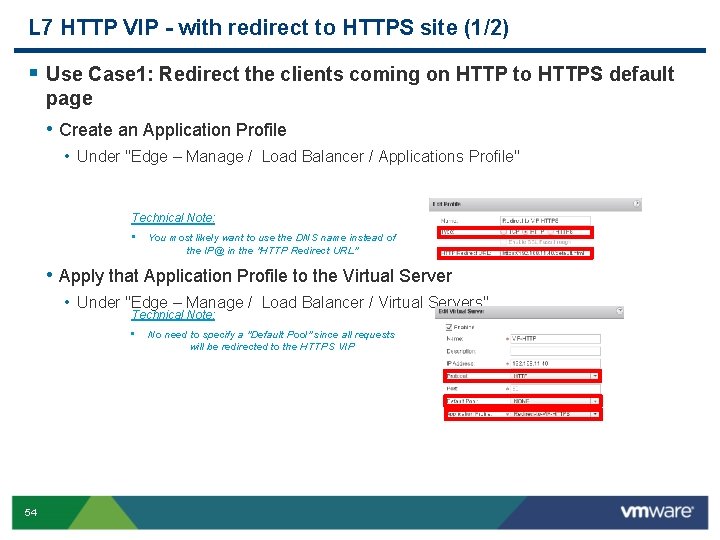
L 7 HTTP VIP - with redirect to HTTPS site (1/2) § Use Case 1: Redirect the clients coming on HTTP to HTTPS default page • Create an Application Profile • Under "Edge – Manage / Load Balancer / Applications Profile" Technical Note: • You most likely want to use the DNS name instead of the IP@ in the "HTTP Redirect URL" • Apply that Application Profile to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: • 54 No need to specify a "Default Pool" since all requests will be redirected to the HTTPS VIP
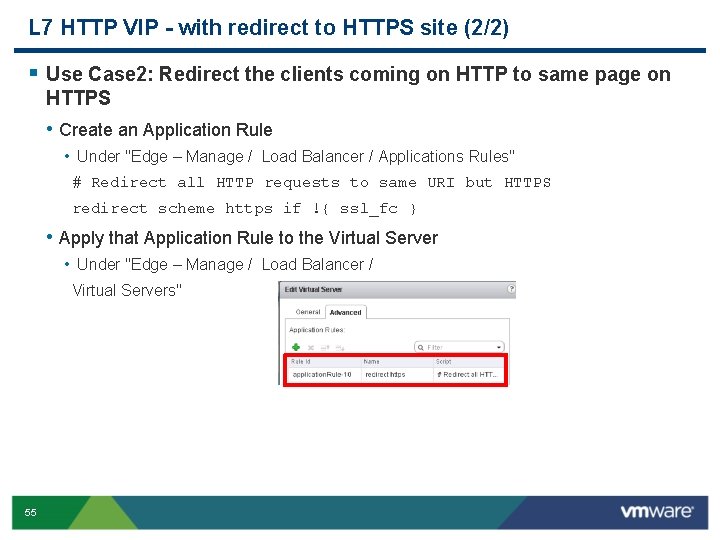
L 7 HTTP VIP - with redirect to HTTPS site (2/2) § Use Case 2: Redirect the clients coming on HTTP to same page on HTTPS • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Redirect all HTTP requests to same URI but HTTPS redirect scheme https if !{ ssl_fc } • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 55
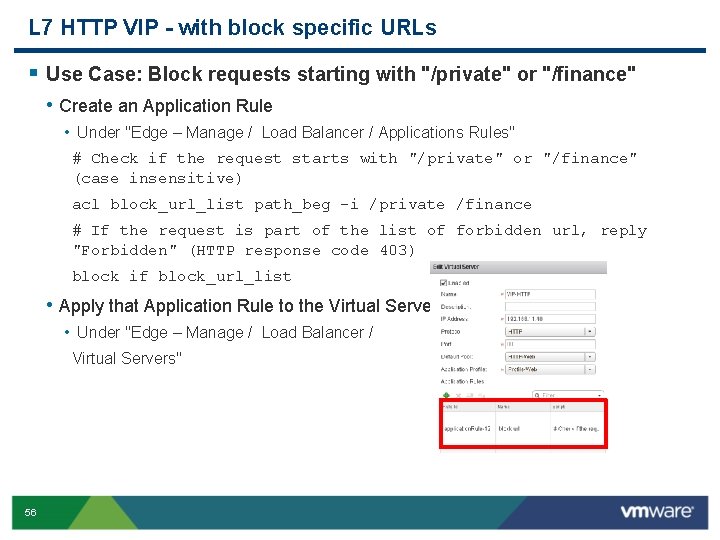
L 7 HTTP VIP - with block specific URLs § Use Case: Block requests starting with "/private" or "/finance" • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check if the request starts with "/private" or "/finance" (case insensitive) acl block_url_list path_beg -i /private /finance # If the request is part of the list of forbidden url, reply "Forbidden" (HTTP response code 403) block if block_url_list • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 56
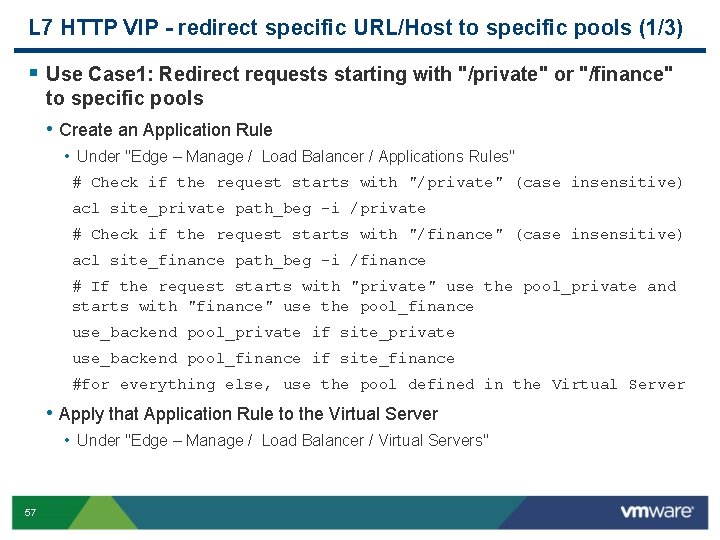
L 7 HTTP VIP - redirect specific URL/Host to specific pools (1/3) § Use Case 1: Redirect requests starting with "/private" or "/finance" to specific pools • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check if the request starts with "/private" (case insensitive) acl site_private path_beg -i /private # Check if the request starts with "/finance" (case insensitive) acl site_finance path_beg -i /finance # If the request starts with "private" use the pool_private and starts with "finance" use the pool_finance use_backend pool_private if site_private use_backend pool_finance if site_finance #for everything else, use the pool defined in the Virtual Server • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 57
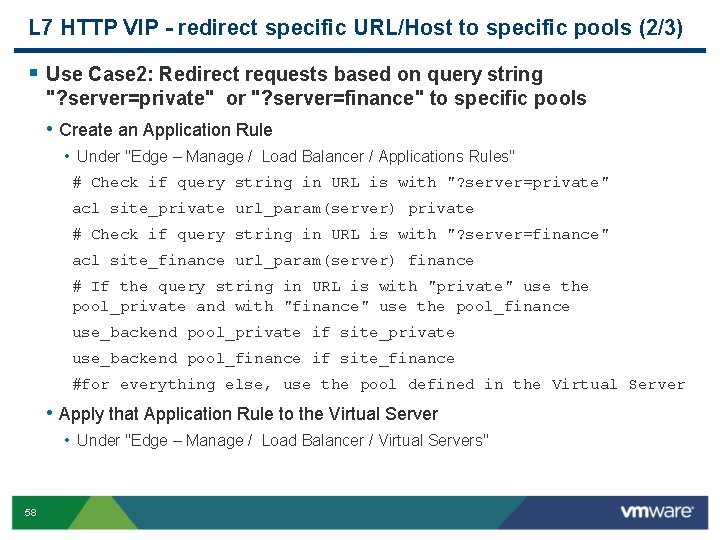
L 7 HTTP VIP - redirect specific URL/Host to specific pools (2/3) § Use Case 2: Redirect requests based on query string "? server=private" or "? server=finance" to specific pools • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check if query string in URL is with "? server=private" acl site_private url_param(server) private # Check if query string in URL is with "? server=finance" acl site_finance url_param(server) finance # If the query string in URL is with "private" use the pool_private and with "finance" use the pool_finance use_backend pool_private if site_private use_backend pool_finance if site_finance #for everything else, use the pool defined in the Virtual Server • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 58
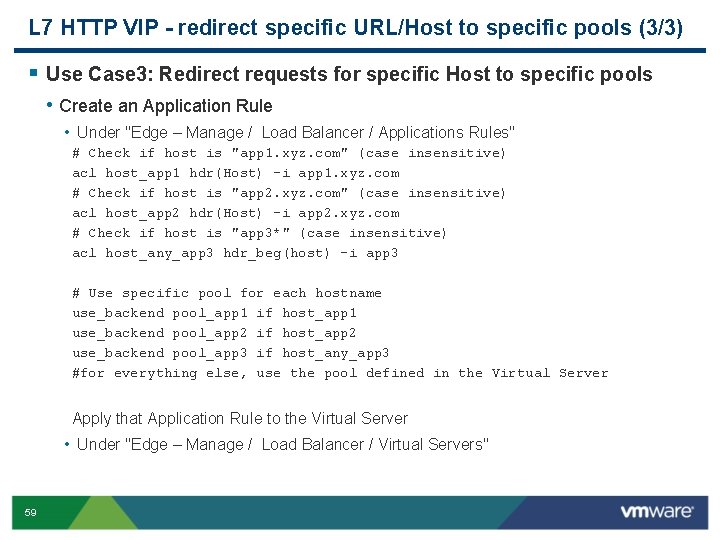
L 7 HTTP VIP - redirect specific URL/Host to specific pools (3/3) § Use Case 3: Redirect requests for specific Host to specific pools • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check if host is "app 1. xyz. com" (case insensitive) acl host_app 1 hdr(Host) -i app 1. xyz. com # Check if host is "app 2. xyz. com" (case insensitive) acl host_app 2 hdr(Host) -i app 2. xyz. com # Check if host is "app 3*" (case insensitive) acl host_any_app 3 hdr_beg(host) -i app 3 # Use specific pool for each hostname use_backend pool_app 1 if host_app 1 use_backend pool_app 2 if host_app 2 use_backend pool_app 3 if host_any_app 3 #for everything else, use the pool defined in the Virtual Server Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 59
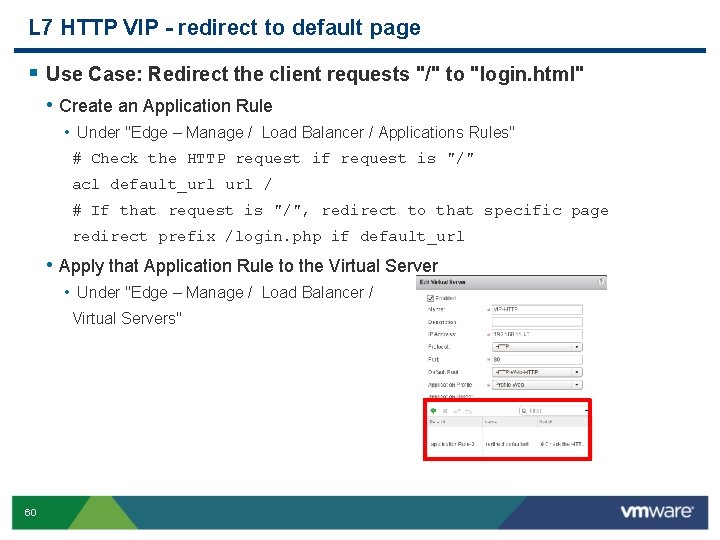
L 7 HTTP VIP - redirect to default page § Use Case: Redirect the client requests "/" to "login. html" • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check the HTTP request if request is "/" acl default_url / # If that request is "/", redirect to that specific page redirect prefix /login. php if default_url • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 60
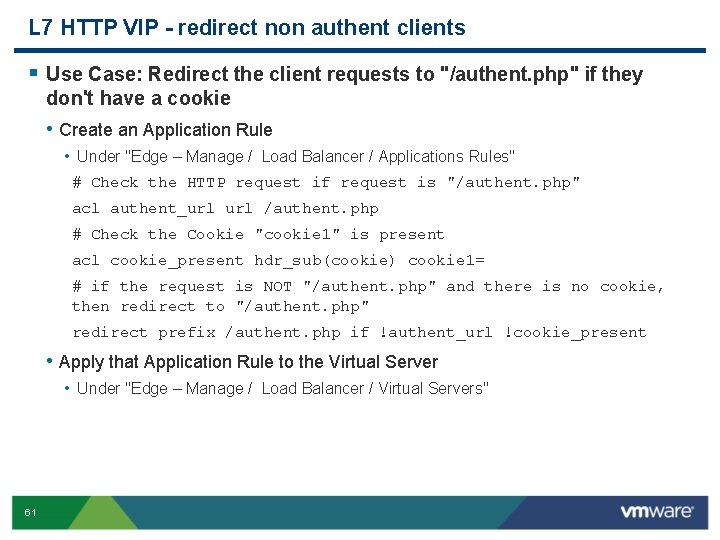
L 7 HTTP VIP - redirect non authent clients § Use Case: Redirect the client requests to "/authent. php" if they don't have a cookie • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Check the HTTP request if request is "/authent. php" acl authent_url /authent. php # Check the Cookie "cookie 1" is present acl cookie_present hdr_sub(cookie) cookie 1= # if the request is NOT "/authent. php" and there is no cookie, then redirect to "/authent. php" redirect prefix /authent. php if !authent_url !cookie_present • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 61
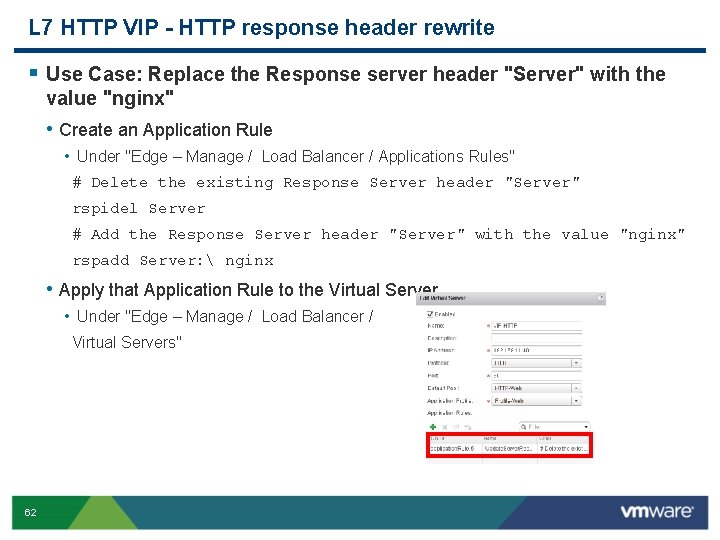
L 7 HTTP VIP - HTTP response header rewrite § Use Case: Replace the Response server header "Server" with the value "nginx" • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # Delete the existing Response Server header "Server" rspidel Server # Add the Response Server header "Server" with the value "nginx" rspadd Server: nginx • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 62
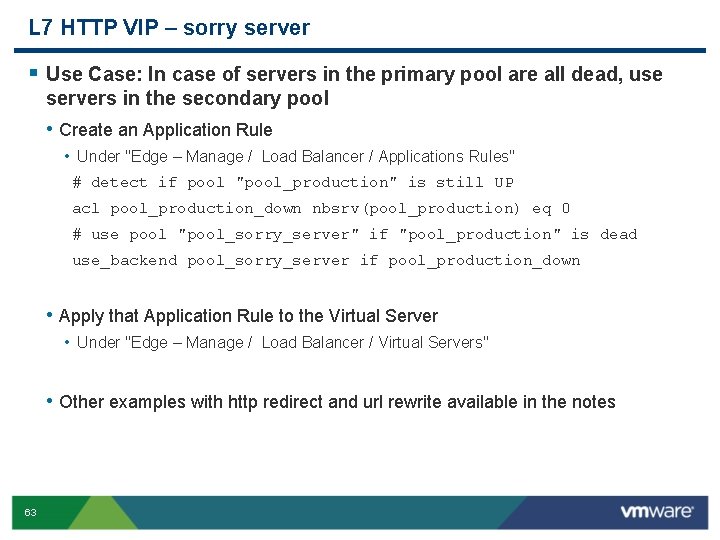
L 7 HTTP VIP – sorry server § Use Case: In case of servers in the primary pool are all dead, use servers in the secondary pool • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # detect if pool "pool_production" is still UP acl pool_production_down nbsrv(pool_production) eq 0 # use pool "pool_sorry_server" if "pool_production" is dead use_backend pool_sorry_server if pool_production_down • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" • Other examples with http redirect and url rewrite available in the notes 63
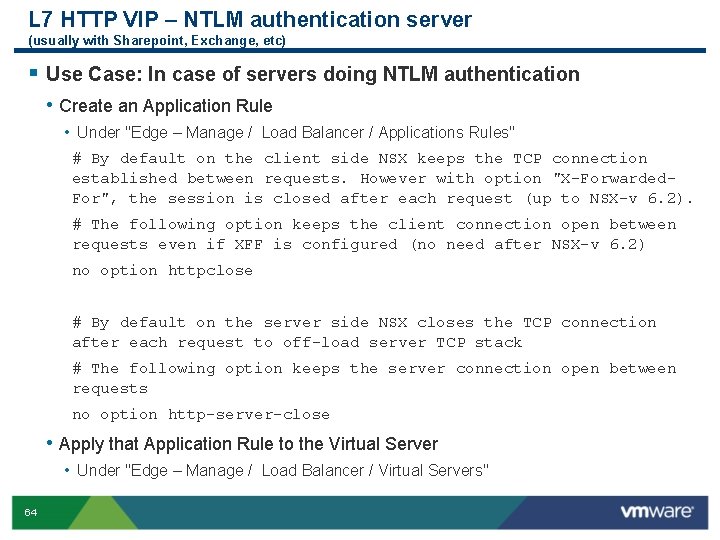
L 7 HTTP VIP – NTLM authentication server (usually with Sharepoint, Exchange, etc) § Use Case: In case of servers doing NTLM authentication • Create an Application Rule • Under "Edge – Manage / Load Balancer / Applications Rules" # By default on the client side NSX keeps the TCP connection established between requests. However with option "X-Forwarded. For", the session is closed after each request (up to NSX-v 6. 2). # The following option keeps the client connection open between requests even if XFF is configured (no need after NSX-v 6. 2) no option httpclose # By default on the server side NSX closes the TCP connection after each request to off-load server TCP stack # The following option keeps the server connection open between requests no option http-server-close • Apply that Application Rule to the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" 64
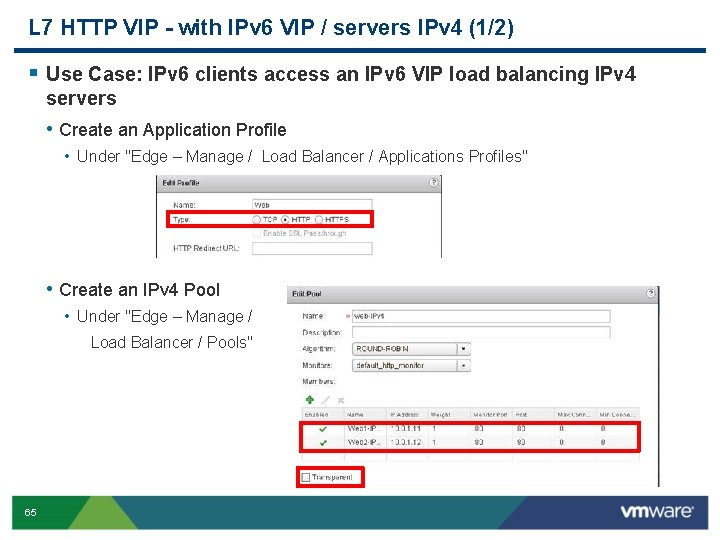
L 7 HTTP VIP - with IPv 6 VIP / servers IPv 4 (1/2) § Use Case: IPv 6 clients access an IPv 6 VIP load balancing IPv 4 servers • Create an Application Profile • Under "Edge – Manage / Load Balancer / Applications Profiles" • Create an IPv 4 Pool • Under "Edge – Manage / Load Balancer / Pools" 65
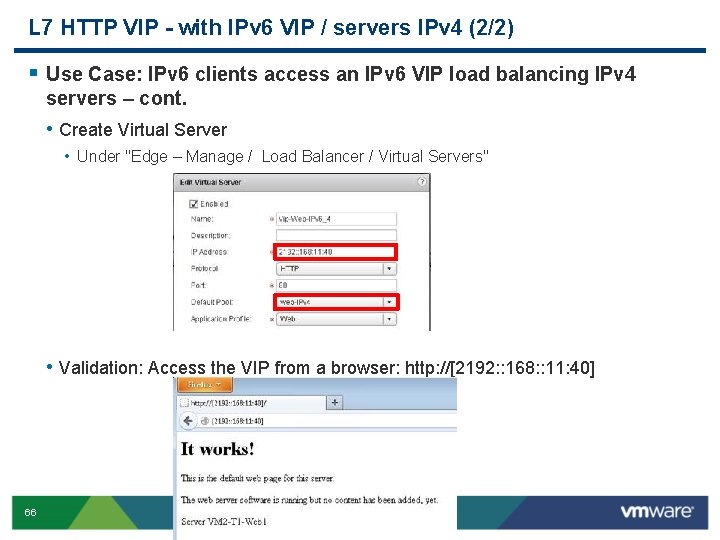
L 7 HTTP VIP - with IPv 6 VIP / servers IPv 4 (2/2) § Use Case: IPv 6 clients access an IPv 6 VIP load balancing IPv 4 servers – cont. • Create Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" • Validation: Access the VIP from a browser: http: //[2192: : 168: : 11: 40] 66
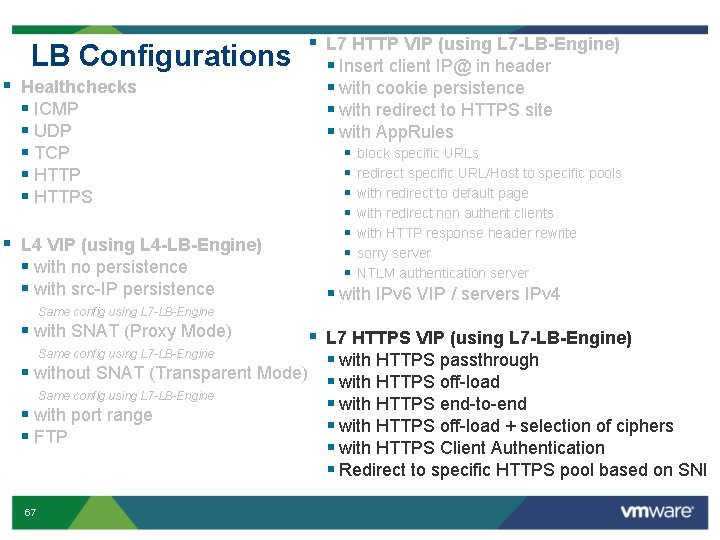
LB Configurations § Healthchecks § ICMP § UDP § TCP § HTTPS § L 4 VIP (using L 4 -LB-Engine) § with no persistence § with src-IP persistence § L 7 HTTP VIP (using L 7 -LB-Engine) § Insert client IP@ in header § with cookie persistence § with redirect to HTTPS site § with App. Rules § § § § block specific URLs redirect specific URL/Host to specific pools with redirect to default page with redirect non authent clients with HTTP response header rewrite sorry server NTLM authentication server § with IPv 6 VIP / servers IPv 4 Same config using L 7 -LB-Engine § with SNAT (Proxy Mode) § L 7 HTTPS VIP (using L 7 -LB-Engine) Same config using L 7 -LB-Engine § with HTTPS passthrough § without SNAT (Transparent Mode) § with HTTPS off-load Same config using L 7 -LB-Engine § with HTTPS end-to-end § with port range § with HTTPS off-load + selection of ciphers § FTP § with HTTPS Client Authentication § Redirect to specific HTTPS pool based on SNI 67
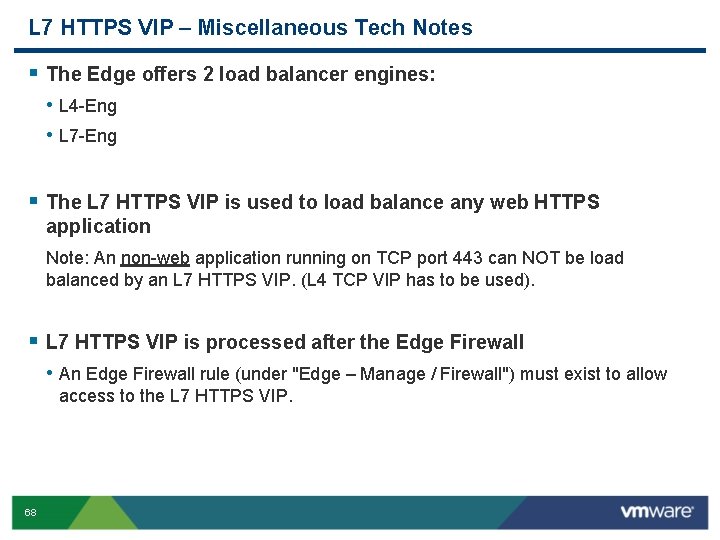
L 7 HTTPS VIP – Miscellaneous Tech Notes § The Edge offers 2 load balancer engines: • L 4 -Eng • L 7 -Eng § The L 7 HTTPS VIP is used to load balance any web HTTPS application Note: An non-web application running on TCP port 443 can NOT be load balanced by an L 7 HTTPS VIP. (L 4 TCP VIP has to be used). § L 7 HTTPS VIP is processed after the Edge Firewall • An Edge Firewall rule (under "Edge – Manage / Firewall") must exist to allow access to the L 7 HTTPS VIP. 68
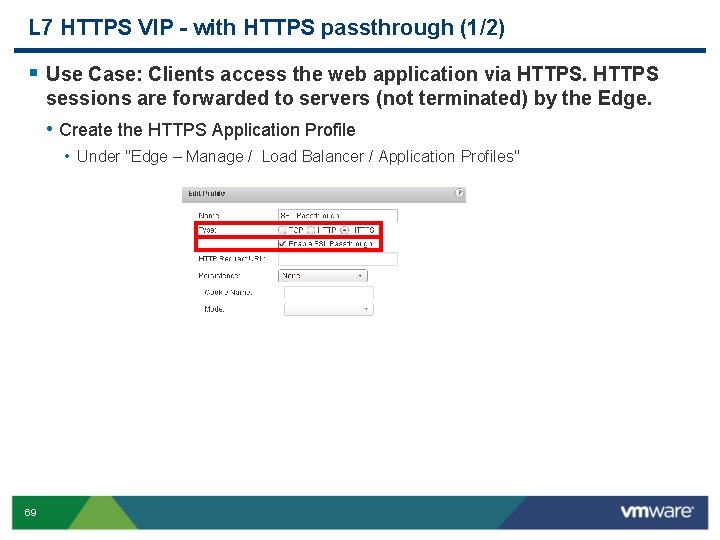
L 7 HTTPS VIP - with HTTPS passthrough (1/2) § Use Case: Clients access the web application via HTTPS sessions are forwarded to servers (not terminated) by the Edge. • Create the HTTPS Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" 69
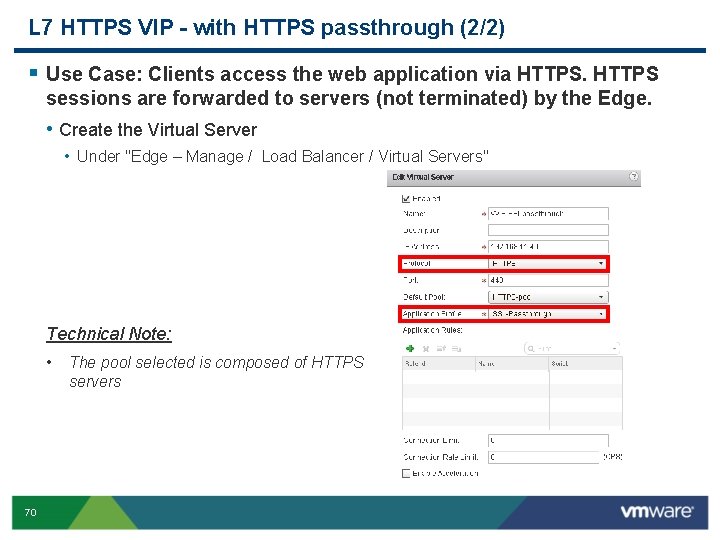
L 7 HTTPS VIP - with HTTPS passthrough (2/2) § Use Case: Clients access the web application via HTTPS sessions are forwarded to servers (not terminated) by the Edge. • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: • 70 The pool selected is composed of HTTPS servers
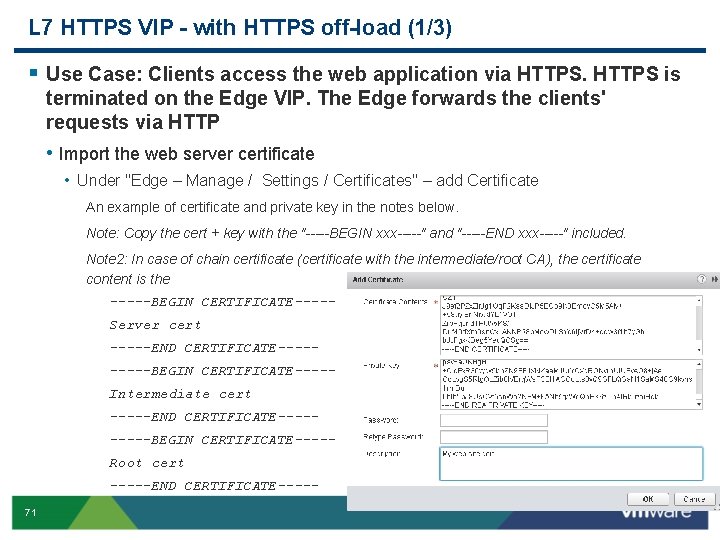
L 7 HTTPS VIP - with HTTPS off-load (1/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge forwards the clients' requests via HTTP • Import the web server certificate • Under "Edge – Manage / Settings / Certificates" – add Certificate An example of certificate and private key in the notes below. Note: Copy the cert + key with the "-----BEGIN xxx-----" and "-----END xxx-----" included. Note 2: In case of chain certificate (certificate with the intermediate/root CA), the certificate content is the -----BEGIN CERTIFICATE----Server cert -----END CERTIFICATE-----BEGIN CERTIFICATE----Intermediate cert -----END CERTIFICATE-----BEGIN CERTIFICATE----Root cert -----END CERTIFICATE----71
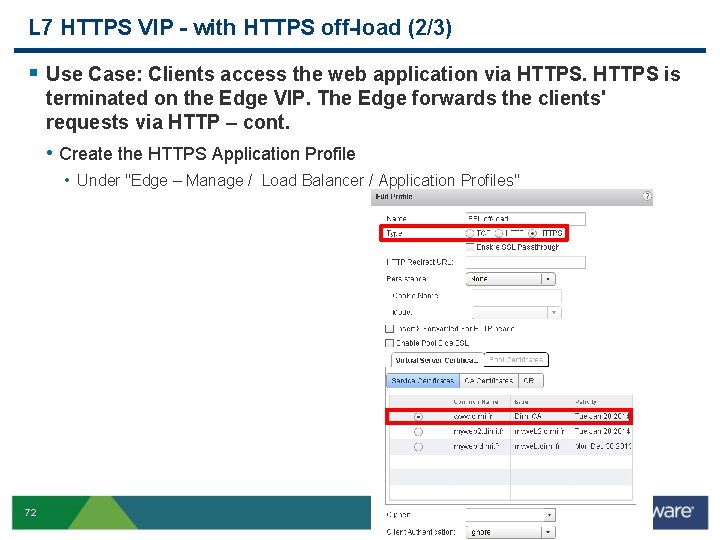
L 7 HTTPS VIP - with HTTPS off-load (2/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge forwards the clients' requests via HTTP – cont. • Create the HTTPS Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" 72
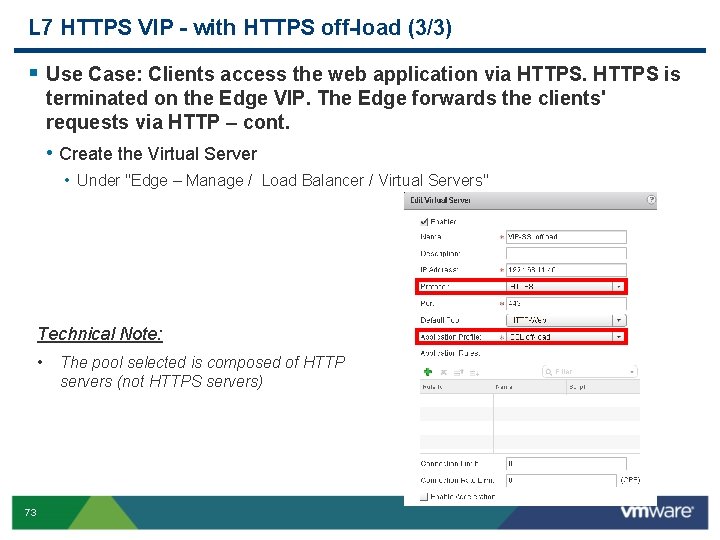
L 7 HTTPS VIP - with HTTPS off-load (3/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge forwards the clients' requests via HTTP – cont. • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: • 73 The pool selected is composed of HTTP servers (not HTTPS servers)
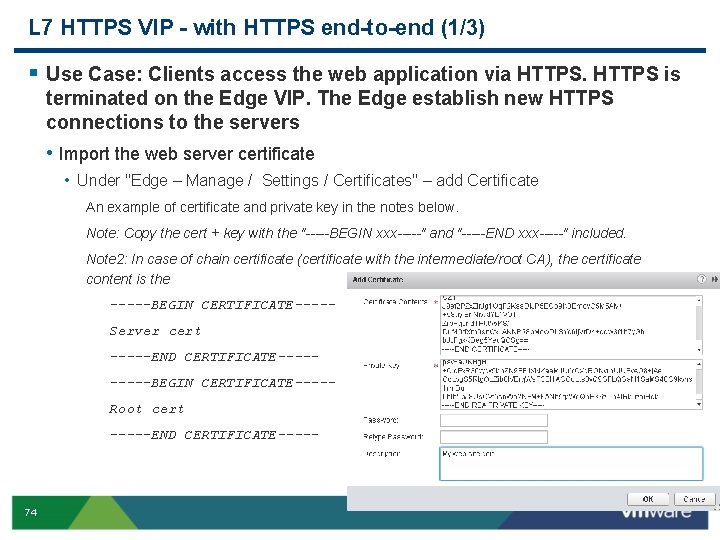
L 7 HTTPS VIP - with HTTPS end-to-end (1/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge establish new HTTPS connections to the servers • Import the web server certificate • Under "Edge – Manage / Settings / Certificates" – add Certificate An example of certificate and private key in the notes below. Note: Copy the cert + key with the "-----BEGIN xxx-----" and "-----END xxx-----" included. Note 2: In case of chain certificate (certificate with the intermediate/root CA), the certificate content is the -----BEGIN CERTIFICATE----Server cert -----END CERTIFICATE-----BEGIN CERTIFICATE----Root cert -----END CERTIFICATE----- 74
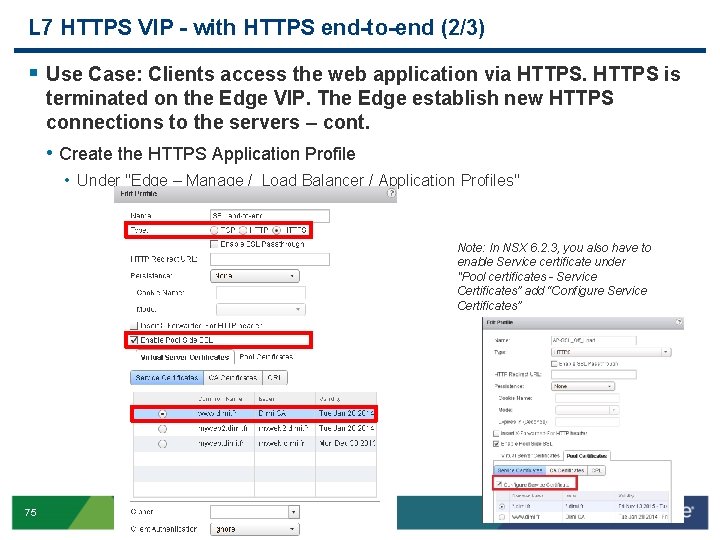
L 7 HTTPS VIP - with HTTPS end-to-end (2/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge establish new HTTPS connections to the servers – cont. • Create the HTTPS Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" Note: In NSX 6. 2. 3, you also have to enable Service certificate under "Pool certificates - Service Certificates” add “Configure Service Certificates” 75
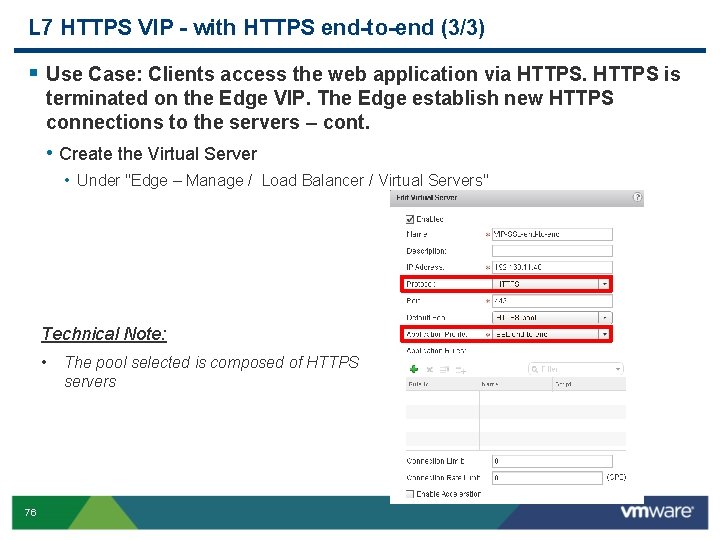
L 7 HTTPS VIP - with HTTPS end-to-end (3/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge establish new HTTPS connections to the servers – cont. • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: • 76 The pool selected is composed of HTTPS servers
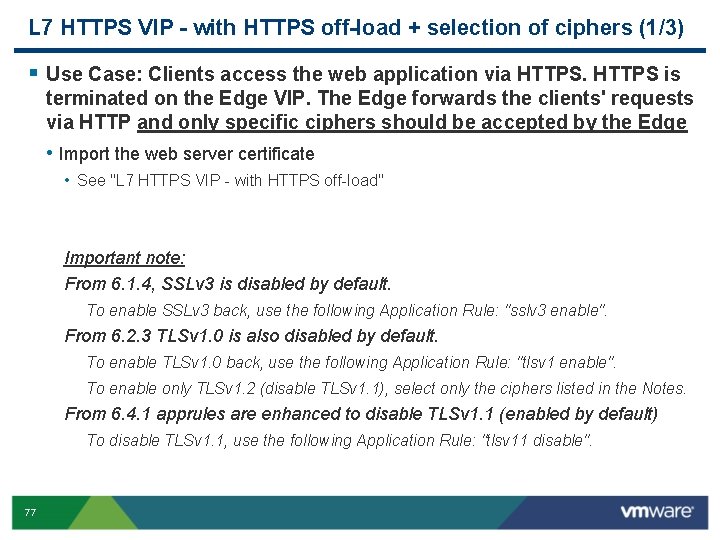
L 7 HTTPS VIP - with HTTPS off-load + selection of ciphers (1/3) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP. The Edge forwards the clients' requests via HTTP and only specific ciphers should be accepted by the Edge • Import the web server certificate • See "L 7 HTTPS VIP - with HTTPS off-load" Important note: From 6. 1. 4, SSLv 3 is disabled by default. To enable SSLv 3 back, use the following Application Rule: "sslv 3 enable". From 6. 2. 3 TLSv 1. 0 is also disabled by default. To enable TLSv 1. 0 back, use the following Application Rule: "tlsv 1 enable". To enable only TLSv 1. 2 (disable TLSv 1. 1), select only the ciphers listed in the Notes. From 6. 4. 1 apprules are enhanced to disable TLSv 1. 1 (enabled by default) To disable TLSv 1. 1, use the following Application Rule: "tlsv 11 disable". 77
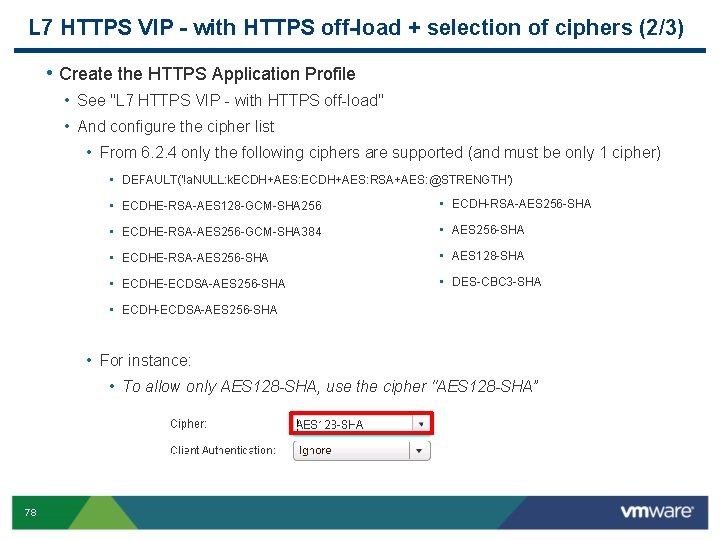
L 7 HTTPS VIP - with HTTPS off-load + selection of ciphers (2/3) • Create the HTTPS Application Profile • See "L 7 HTTPS VIP - with HTTPS off-load" • And configure the cipher list • From 6. 2. 4 only the following ciphers are supported (and must be only 1 cipher) • DEFAULT('!a. NULL: k. ECDH+AES: RSA+AES: @STRENGTH') • ECDHE-RSA-AES 128 -GCM-SHA 256 • ECDH-RSA-AES 256 -SHA • ECDHE-RSA-AES 256 -GCM-SHA 384 • AES 256 -SHA • ECDHE-RSA-AES 256 -SHA • AES 128 -SHA • ECDHE-ECDSA-AES 256 -SHA • DES-CBC 3 -SHA • ECDH-ECDSA-AES 256 -SHA • For instance: • To allow only AES 128 -SHA, use the cipher "AES 128 -SHA” 78
L 7 HTTPS VIP - with HTTPS off-load + selection of ciphers (3/3) • Create the Virtual Server • See "L 7 HTTPS VIP - with HTTPS off-load" 79
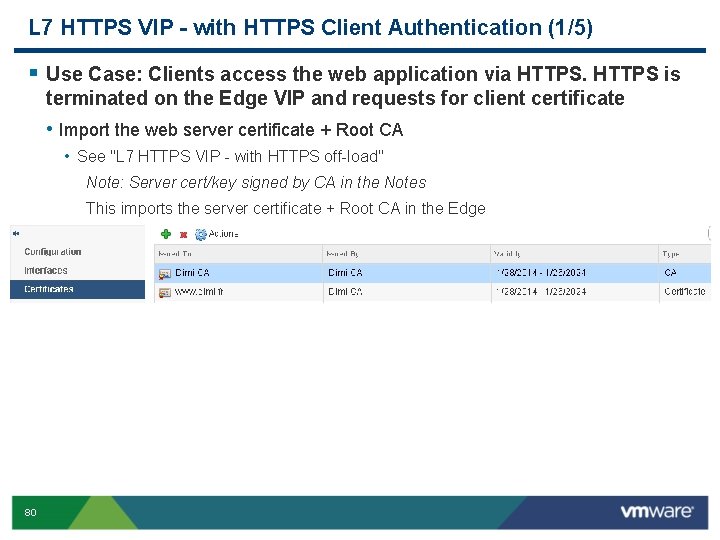
L 7 HTTPS VIP - with HTTPS Client Authentication (1/5) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP and requests for client certificate • Import the web server certificate + Root CA • See "L 7 HTTPS VIP - with HTTPS off-load" Note: Server cert/key signed by CA in the Notes This imports the server certificate + Root CA in the Edge 80
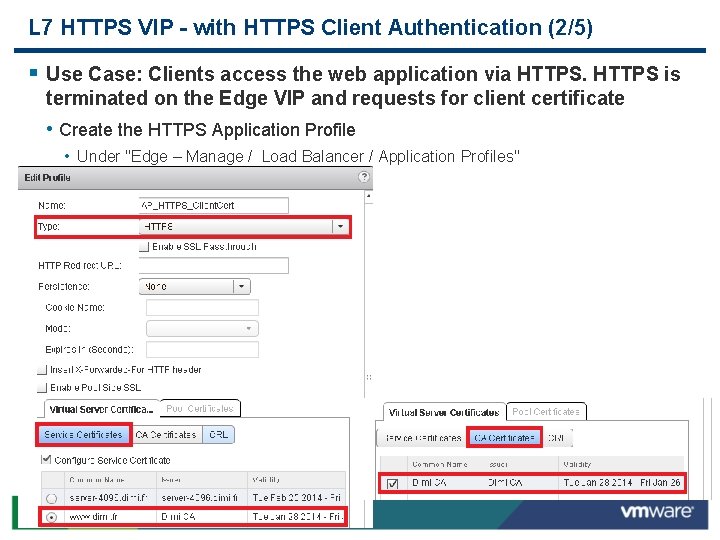
L 7 HTTPS VIP - with HTTPS Client Authentication (2/5) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP and requests for client certificate • Create the HTTPS Application Profile • Under "Edge – Manage / Load Balancer / Application Profiles" 81
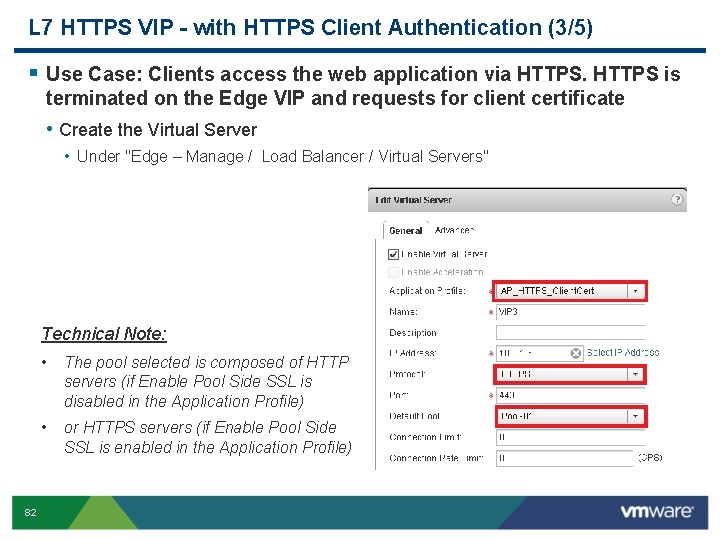
L 7 HTTPS VIP - with HTTPS Client Authentication (3/5) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP and requests for client certificate • Create the Virtual Server • Under "Edge – Manage / Load Balancer / Virtual Servers" Technical Note: 82 • The pool selected is composed of HTTP servers (if Enable Pool Side SSL is disabled in the Application Profile) • or HTTPS servers (if Enable Pool Side SSL is enabled in the Application Profile)
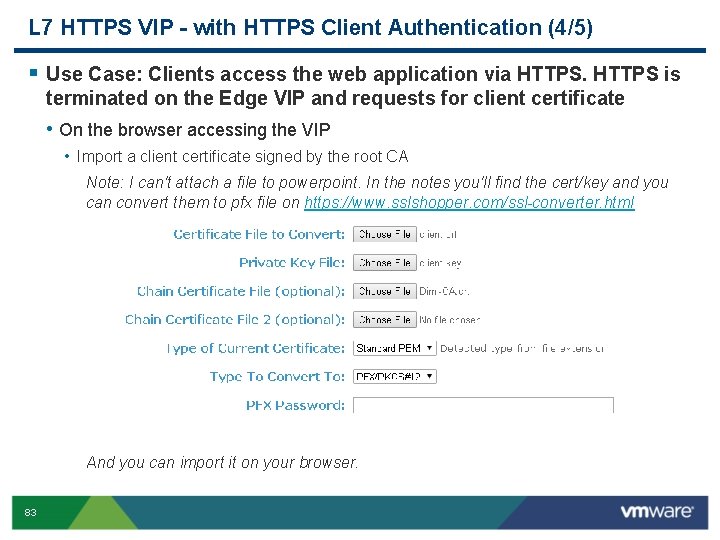
L 7 HTTPS VIP - with HTTPS Client Authentication (4/5) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP and requests for client certificate • On the browser accessing the VIP • Import a client certificate signed by the root CA Note: I can't attach a file to powerpoint. In the notes you'll find the cert/key and you can convert them to pfx file on https: //www. sslshopper. com/ssl-converter. html And you can import it on your browser. 83
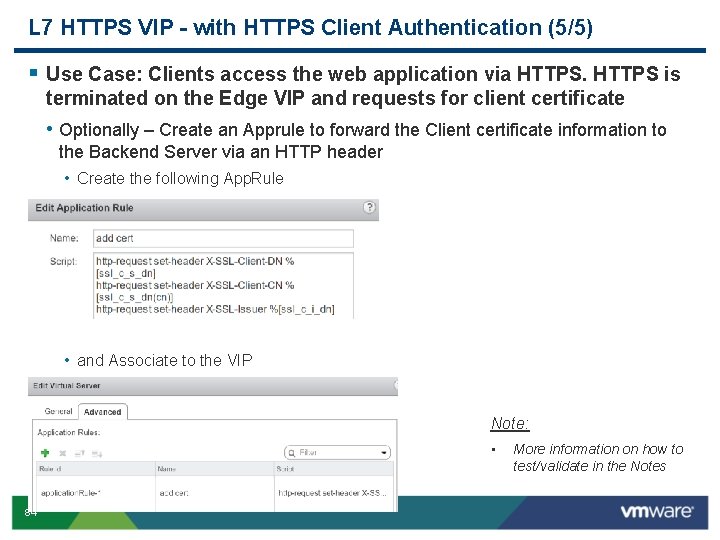
L 7 HTTPS VIP - with HTTPS Client Authentication (5/5) § Use Case: Clients access the web application via HTTPS is terminated on the Edge VIP and requests for client certificate • Optionally – Create an Apprule to forward the Client certificate information to the Backend Server via an HTTP header • Create the following App. Rule • and Associate to the VIP Note: • 84 More information on how to test/validate in the Notes
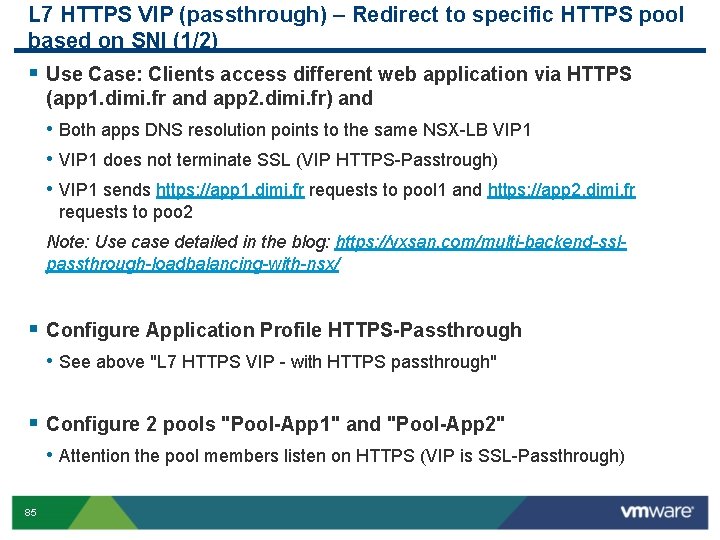
L 7 HTTPS VIP (passthrough) – Redirect to specific HTTPS pool based on SNI (1/2) § Use Case: Clients access different web application via HTTPS (app 1. dimi. fr and app 2. dimi. fr) and • Both apps DNS resolution points to the same NSX-LB VIP 1 • VIP 1 does not terminate SSL (VIP HTTPS-Passtrough) • VIP 1 sends https: //app 1. dimi. fr requests to pool 1 and https: //app 2. dimi. fr requests to poo 2 Note: Use case detailed in the blog: https: //vxsan. com/multi-backend-sslpassthrough-loadbalancing-with-nsx/ § Configure Application Profile HTTPS-Passthrough • See above "L 7 HTTPS VIP - with HTTPS passthrough" § Configure 2 pools "Pool-App 1" and "Pool-App 2" • Attention the pool members listen on HTTPS (VIP is SSL-Passthrough) 85
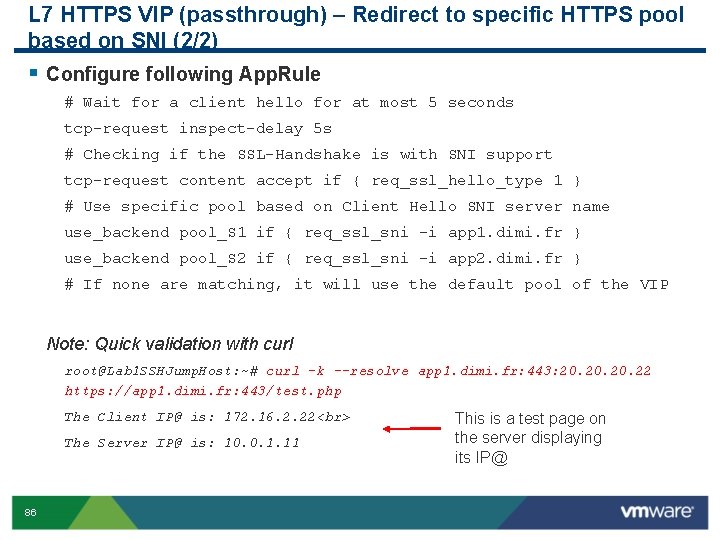
L 7 HTTPS VIP (passthrough) – Redirect to specific HTTPS pool based on SNI (2/2) § Configure following App. Rule # Wait for a client hello for at most 5 seconds tcp-request inspect-delay 5 s # Checking if the SSL-Handshake is with SNI support tcp-request content accept if { req_ssl_hello_type 1 } # Use specific pool based on Client Hello SNI server name use_backend pool_S 1 if { req_ssl_sni -i app 1. dimi. fr } use_backend pool_S 2 if { req_ssl_sni -i app 2. dimi. fr } # If none are matching, it will use the default pool of the VIP Note: Quick validation with curl root@Lab 1 SSHJump. Host: ~# curl -k --resolve app 1. dimi. fr: 443: 20. 20. 22 https: //app 1. dimi. fr: 443/test. php The Client IP@ is: 172. 16. 2. 22 The Server IP@ is: 10. 0. 1. 11 86 This is a test page on the server displaying its IP@
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 87
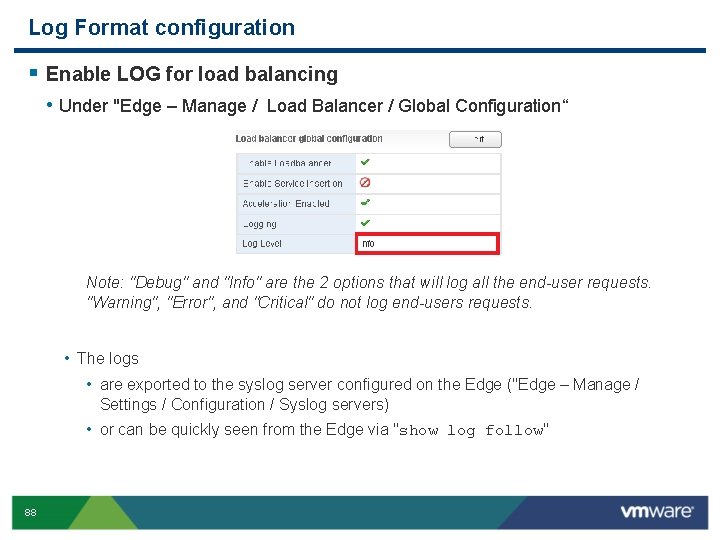
Log Format configuration § Enable LOG for load balancing • Under "Edge – Manage / Load Balancer / Global Configuration“ Note: "Debug" and "Info" are the 2 options that will log all the end-user requests. "Warning", "Error", and "Critical" do not log end-users requests. • The logs • are exported to the syslog server configured on the Edge ("Edge – Manage / Settings / Configuration / Syslog servers) • or can be quickly seen from the Edge via "show log follow" 88
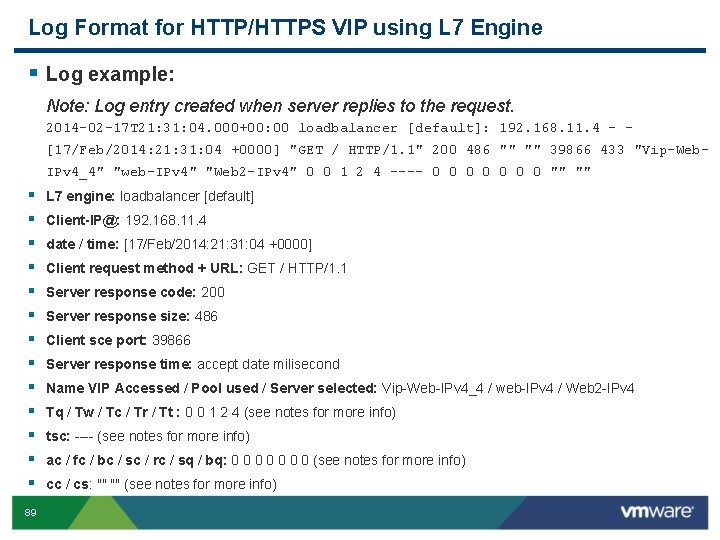
Log Format for HTTP/HTTPS VIP using L 7 Engine § Log example: Note: Log entry created when server replies to the request. 2014 -02 -17 T 21: 31: 04. 000+00: 00 loadbalancer [default]: 192. 168. 11. 4 - [17/Feb/2014: 21: 31: 04 +0000] "GET / HTTP/1. 1" 200 486 "" "" 39866 433 "Vip-Web. IPv 4_4" "web-IPv 4" "Web 2 -IPv 4" 0 0 1 2 4 ---- 0 0 0 0 "" "" § § § § 89 L 7 engine: loadbalancer [default] Client-IP@: 192. 168. 11. 4 date / time: [17/Feb/2014: 21: 31: 04 +0000] Client request method + URL: GET / HTTP/1. 1 Server response code: 200 Server response size: 486 Client sce port: 39866 Server response time: accept date milisecond Name VIP Accessed / Pool used / Server selected: Vip-Web-IPv 4_4 / web-IPv 4 / Web 2 -IPv 4 Tq / Tw / Tc / Tr / Tt : 0 0 1 2 4 (see notes for more info) tsc: ---- (see notes for more info) ac / fc / bc / sc / rc / sq / bq: 0 0 0 0 (see notes for more info) cc / cs: "" "" (see notes for more info)
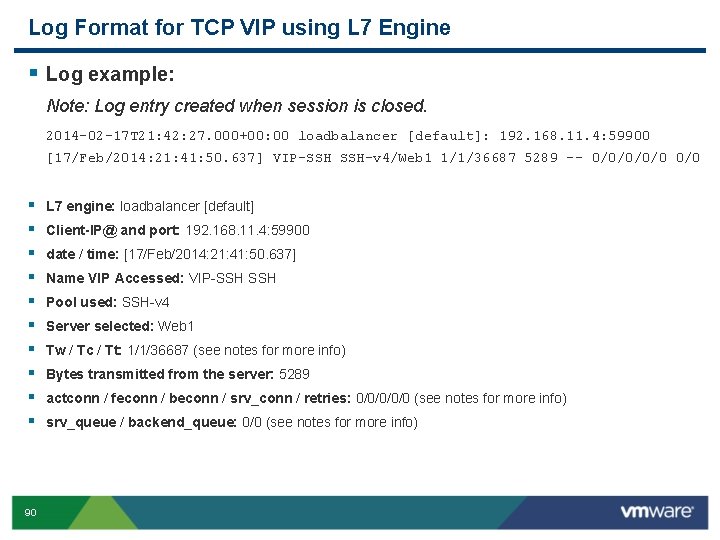
Log Format for TCP VIP using L 7 Engine § Log example: Note: Log entry created when session is closed. 2014 -02 -17 T 21: 42: 27. 000+00: 00 loadbalancer [default]: 192. 168. 11. 4: 59900 [17/Feb/2014: 21: 41: 50. 637] VIP-SSH SSH-v 4/Web 1 1/1/36687 5289 -- 0/0/0 0/0 § § § § § 90 L 7 engine: loadbalancer [default] Client-IP@ and port: 192. 168. 11. 4: 59900 date / time: [17/Feb/2014: 21: 41: 50. 637] Name VIP Accessed: VIP-SSH Pool used: SSH-v 4 Server selected: Web 1 Tw / Tc / Tt: 1/1/36687 (see notes for more info) Bytes transmitted from the server: 5289 actconn / feconn / beconn / srv_conn / retries: 0/0/0 (see notes for more info) srv_queue / backend_queue: 0/0 (see notes for more info)
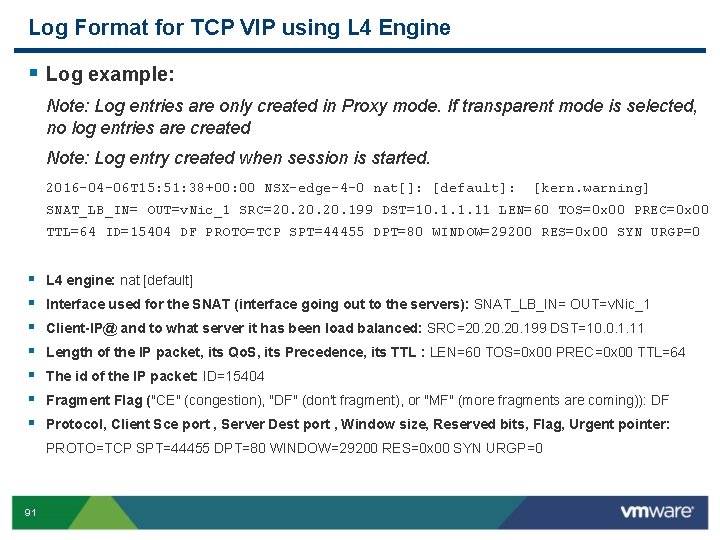
Log Format for TCP VIP using L 4 Engine § Log example: Note: Log entries are only created in Proxy mode. If transparent mode is selected, no log entries are created Note: Log entry created when session is started. 2016 -04 -06 T 15: 51: 38+00: 00 NSX-edge-4 -0 nat[]: [default]: [kern. warning] SNAT_LB_IN= OUT=v. Nic_1 SRC=20. 20. 199 DST=10. 1. 1. 11 LEN=60 TOS=0 x 00 PREC=0 x 00 TTL=64 ID=15404 DF PROTO=TCP SPT=44455 DPT=80 WINDOW=29200 RES=0 x 00 SYN URGP=0 § § § § L 4 engine: nat [default] Interface used for the SNAT (interface going out to the servers): SNAT_LB_IN= OUT=v. Nic_1 Client-IP@ and to what server it has been load balanced: SRC=20. 20. 199 DST=10. 0. 1. 11 Length of the IP packet, its Qo. S, its Precedence, its TTL : LEN=60 TOS=0 x 00 PREC=0 x 00 TTL=64 The id of the IP packet: ID=15404 Fragment Flag ("CE" (congestion), "DF" (don't fragment), or "MF" (more fragments are coming)): DF Protocol, Client Sce port , Server Dest port , Window size, Reserved bits, Flag, Urgent pointer: PROTO=TCP SPT=44455 DPT=80 WINDOW=29200 RES=0 x 00 SYN URGP=0 91
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 92
API examples § Create a LB pool § Update a LB pool § Add new member § Disable a member § More on VMware Google Drive here Note: requires a Google Drive VMware account. 93
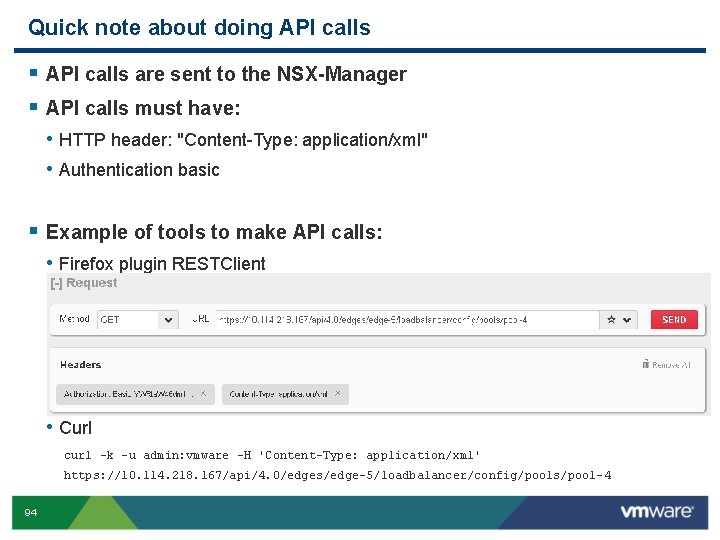
Quick note about doing API calls § API calls are sent to the NSX-Manager § API calls must have: • HTTP header: "Content-Type: application/xml" • Authentication basic § Example of tools to make API calls: • Firefox plugin RESTClient • Curl curl -k -u admin: vmware -H 'Content-Type: application/xml' https: //10. 114. 218. 167/api/4. 0/edges/edge-5/loadbalancer/config/pools/pool-4 94
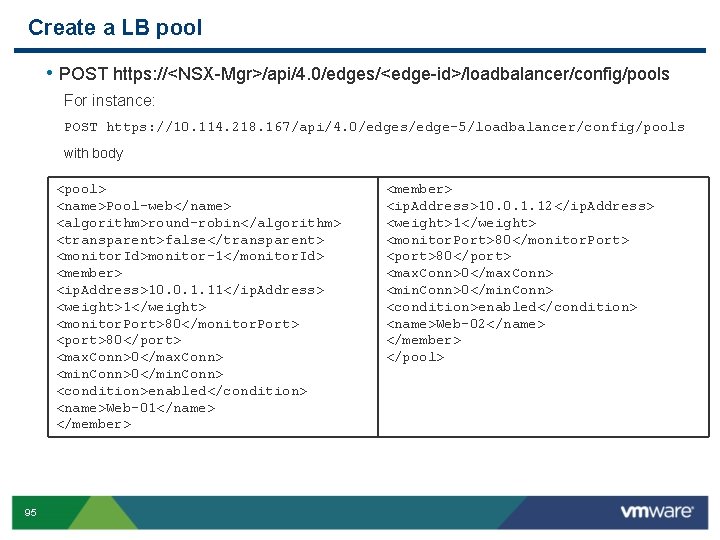
Create a LB pool • POST https: //<NSX-Mgr>/api/4. 0/edges/<edge-id>/loadbalancer/config/pools For instance: POST https: //10. 114. 218. 167/api/4. 0/edges/edge-5/loadbalancer/config/pools with body <pool> <name>Pool-web</name> <algorithm>round-robin</algorithm> <transparent>false</transparent> <monitor. Id>monitor-1</monitor. Id> <member> <ip. Address>10. 0. 1. 11</ip. Address> <weight>1</weight> <monitor. Port>80</monitor. Port> <port>80</port> <max. Conn>0</max. Conn> <min. Conn>0</min. Conn> <condition>enabled</condition> <name>Web-01</name> </member> 95 <member> <ip. Address>10. 0. 1. 12</ip. Address> <weight>1</weight> <monitor. Port>80</monitor. Port> <port>80</port> <max. Conn>0</max. Conn> <min. Conn>0</min. Conn> <condition>enabled</condition> <name>Web-02</name> </member> </pool>
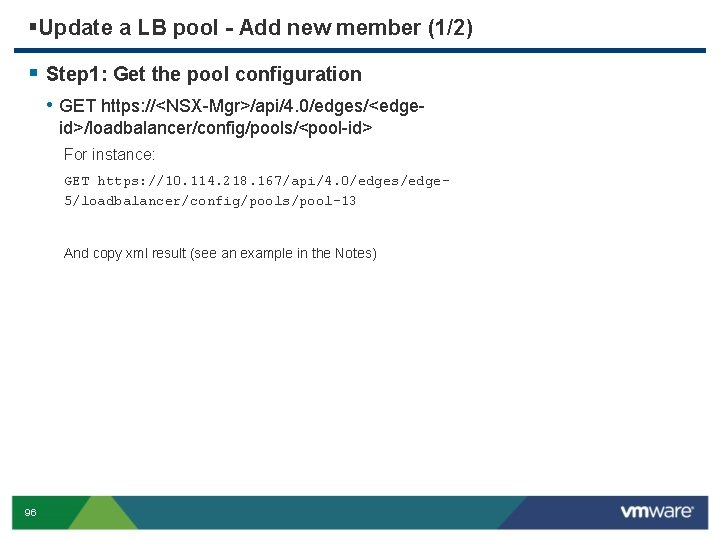
§Update a LB pool - Add new member (1/2) § Step 1: Get the pool configuration • GET https: //<NSX-Mgr>/api/4. 0/edges/<edgeid>/loadbalancer/config/pools/<pool-id> For instance: GET https: //10. 114. 218. 167/api/4. 0/edges/edge 5/loadbalancer/config/pools/pool-13 And copy xml result (see an example in the Notes) 96
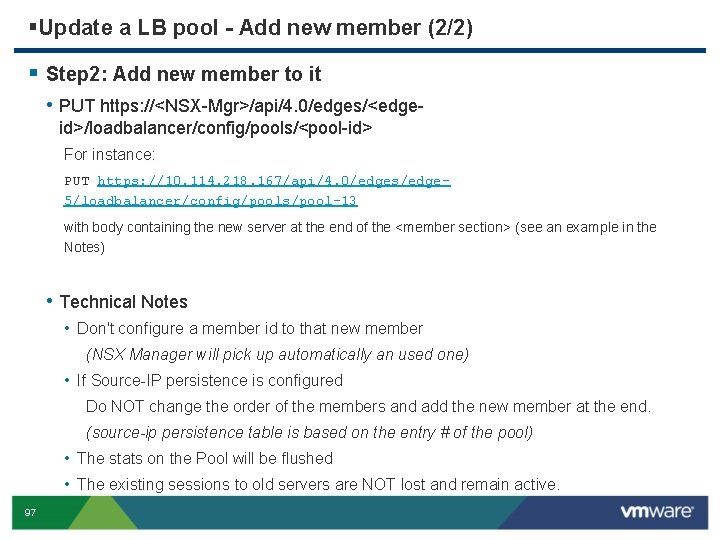
§Update a LB pool - Add new member (2/2) § Step 2: Add new member to it • PUT https: //<NSX-Mgr>/api/4. 0/edges/<edgeid>/loadbalancer/config/pools/<pool-id> For instance: PUT https: //10. 114. 218. 167/api/4. 0/edges/edge 5/loadbalancer/config/pools/pool-13 with body containing the new server at the end of the <member section> (see an example in the Notes) • Technical Notes • Don't configure a member id to that new member (NSX Manager will pick up automatically an used one) • If Source-IP persistence is configured Do NOT change the order of the members and add the new member at the end. (source-ip persistence table is based on the entry # of the pool) • The stats on the Pool will be flushed • The existing sessions to old servers are NOT lost and remain active. 97
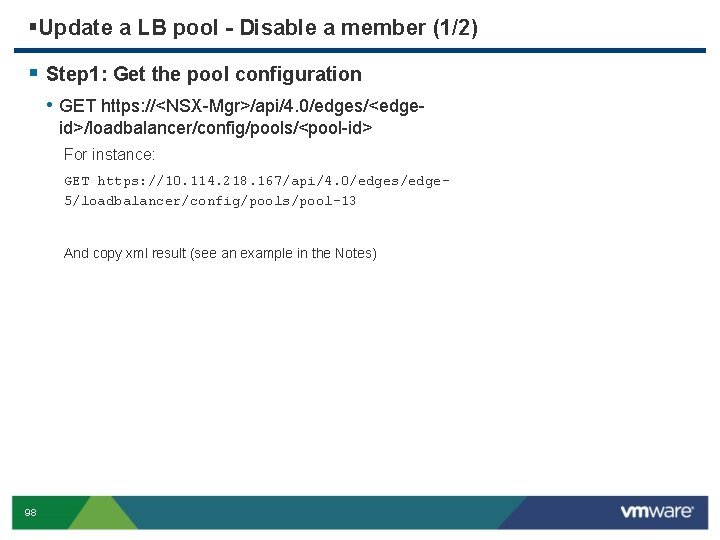
§Update a LB pool - Disable a member (1/2) § Step 1: Get the pool configuration • GET https: //<NSX-Mgr>/api/4. 0/edges/<edgeid>/loadbalancer/config/pools/<pool-id> For instance: GET https: //10. 114. 218. 167/api/4. 0/edges/edge 5/loadbalancer/config/pools/pool-13 And copy xml result (see an example in the Notes) 98
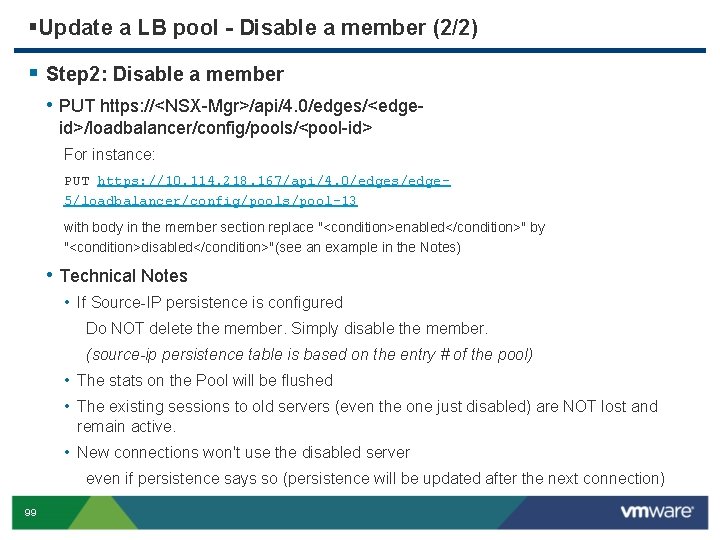
§Update a LB pool - Disable a member (2/2) § Step 2: Disable a member • PUT https: //<NSX-Mgr>/api/4. 0/edges/<edgeid>/loadbalancer/config/pools/<pool-id> For instance: PUT https: //10. 114. 218. 167/api/4. 0/edges/edge 5/loadbalancer/config/pools/pool-13 with body in the member section replace "<condition>enabled</condition>" by "<condition>disabled</condition>"(see an example in the Notes) • Technical Notes • If Source-IP persistence is configured Do NOT delete the member. Simply disable the member. (source-ip persistence table is based on the entry # of the pool) • The stats on the Pool will be flushed • The existing sessions to old servers (even the one just disabled) are NOT lost and remain active. • New connections won't use the disabled server even if persistence says so (persistence will be updated after the next connection) 99
Agenda Overview LB Configuration examples Log format API calls examples Deep Troubleshooting 100
Check Configuration § REST API (xml format) § URL : /api/4. 0/edges/{edge. Id}/loadbalancer/config § CLI (json format) • • • # show configuration loadbalancer virtual [virtual-server-name] # show configuration loadbalancer pool [pool-name] # show configuration loadbalancer monitor [monitor-name] # show configuration loadbalancer profile [profile-name] # show configuration loadbalancer rule [rule-name] § LB configuration in Tech Support Logs (haproxy config file) • Search for “haproxy. conf” 101
Check Runtime (Connectivity) § Check 2 sides connectivity. • Client to LB • LB to backend server • CLI • • #ping xxx #show arp #dnslookup xxx #traceroute xxx § Check flow table in CLI/Techsupport Log • # show flowtable § Check firewall • CLI: # show firewall • Allow virtual server service. • Don’t disable firewall when you are using load balancer L 4 non-transparent mode 102
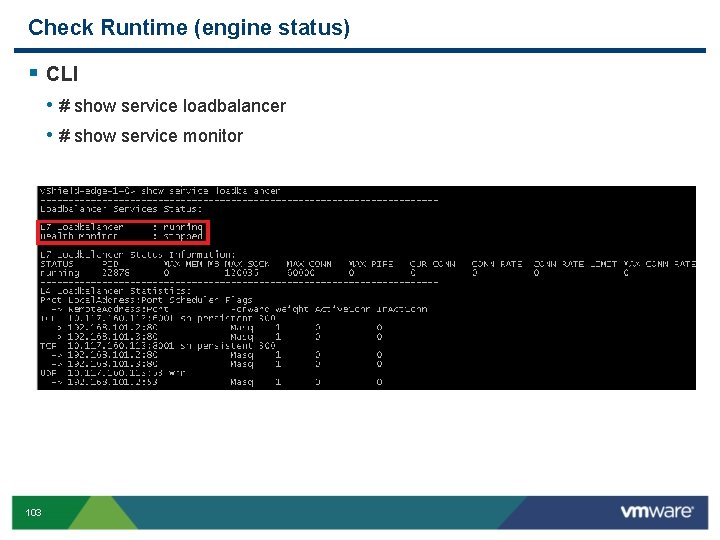
Check Runtime (engine status) § CLI • # show service loadbalancer • # show service monitor 103
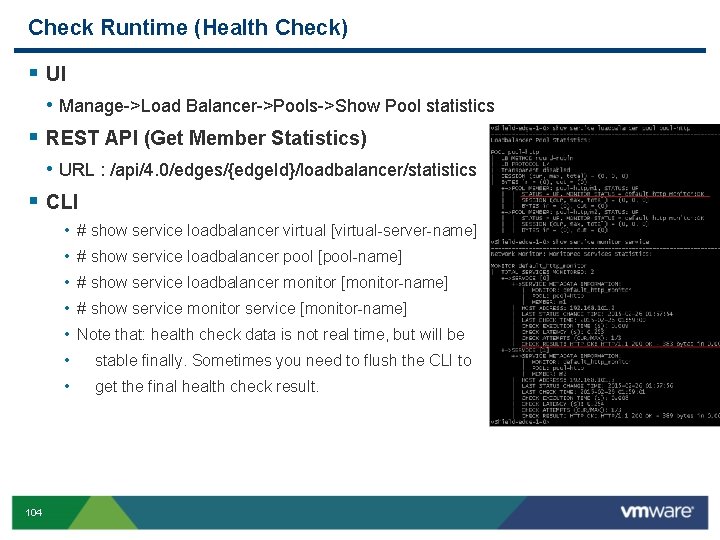
Check Runtime (Health Check) § UI • Manage->Load Balancer->Pools->Show Pool statistics § REST API (Get Member Statistics) • URL : /api/4. 0/edges/{edge. Id}/loadbalancer/statistics § CLI • • 104 # show service loadbalancer virtual [virtual-server-name] # show service loadbalancer pool [pool-name] # show service loadbalancer monitor [monitor-name] # show service monitor service [monitor-name] Note that: health check data is not real time, but will be stable finally. Sometimes you need to flush the CLI to get the final health check result.
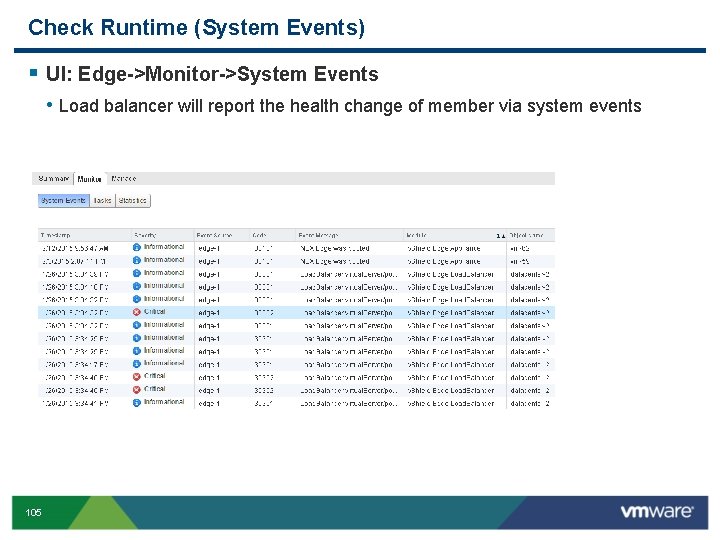
Check Runtime (System Events) § UI: Edge->Monitor->System Events • Load balancer will report the health change of member via system events 105
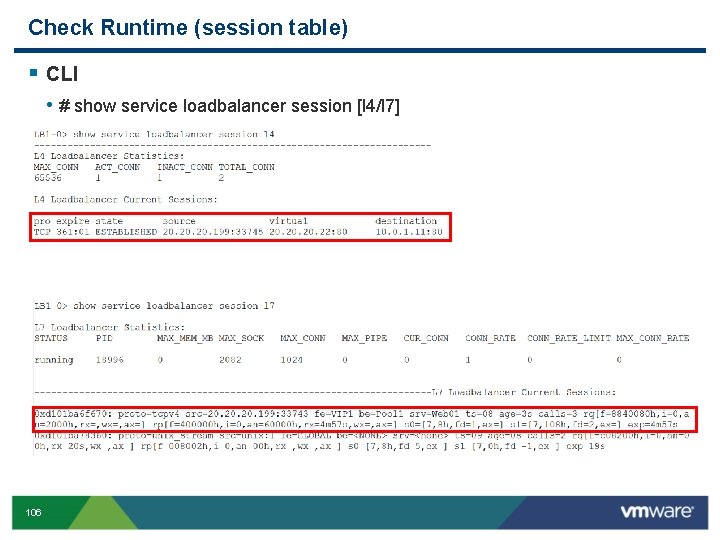
Check Runtime (session table) § CLI • # show service loadbalancer session [l 4/l 7] 106
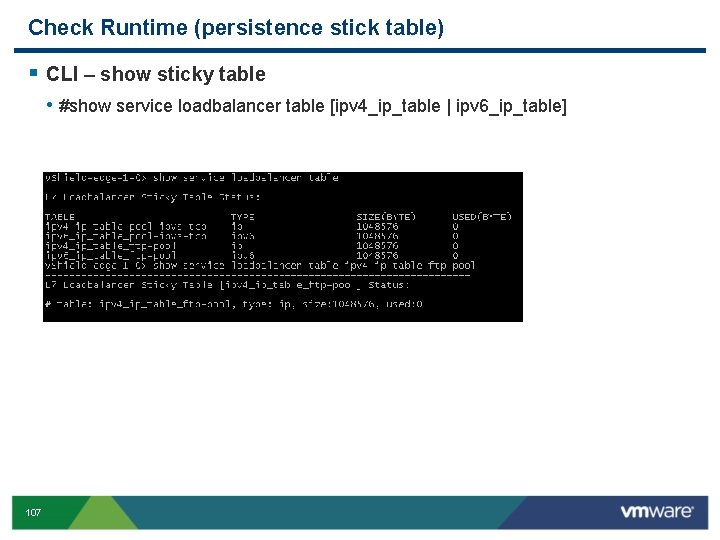
Check Runtime (persistence stick table) § CLI – show sticky table • #show service loadbalancer table [ipv 4_ip_table | ipv 6_ip_table] 107
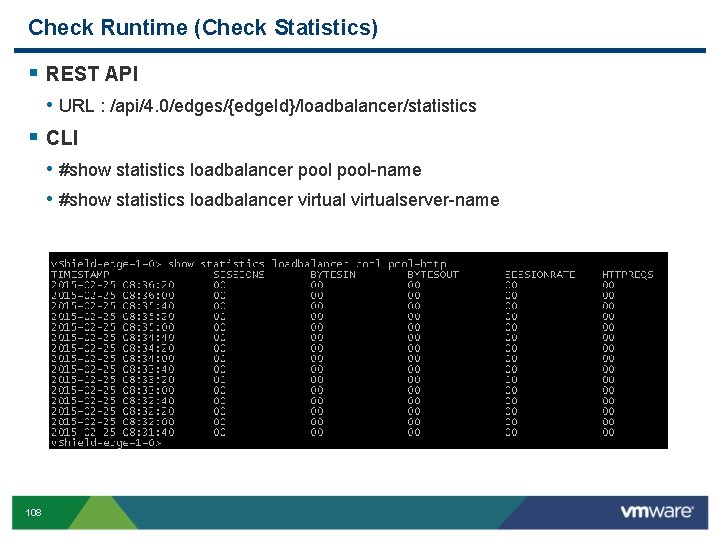
Check Runtime (Check Statistics) § REST API • URL : /api/4. 0/edges/{edge. Id}/loadbalancer/statistics § CLI • #show statistics loadbalancer pool-name • #show statistics loadbalancer virtualserver-name 108
Check Runtime (Log) Log Format configuration § Enable LOG for load balancing • Under "Edge – Manage / Load Balancer / Global Configuration“ • Note: "Debug" and "Info" are the 2 options that will log all the end-user requests. "Warning", "Error", and "Critical" do not log end-users requests. • The logs • are exported to the syslog server configured on the Edge ("Edge – Manage / Settings / Configuration / Syslog servers) • or can be quickly seen from the Edge via "show log follow" 109
Check Runtime (Packet Capture) § Sometimes you need to capture the packets to detect LB abnormal failure. It is suggested to capture packets from 2 directions. • Capture the packets from client. • Capture the packets sent to backend server. § CLI • #debug packet capture interface-name [filter using _ for space] • #debug packet display interface-name [filter using _ for space] • For instance: • Capture on v. NIC_0 debug packet display interface v. Nic_0 • Capture on all interfaces debug packet display interface any • Capture on v. Nic_0 with a filter debug packet display interface v. Nic_0 host_192. 168. 11. 3_and_host_192. 168. 11. 41 • #debug show files • #debug copy scp user@url: path file-name/all 110
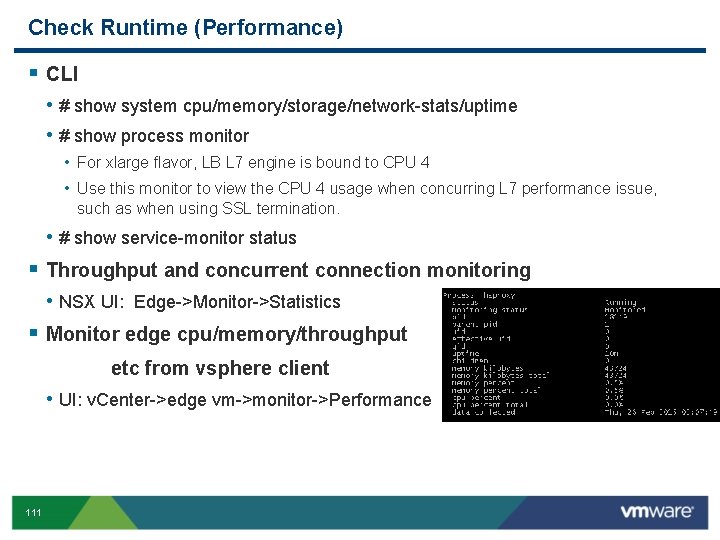
Check Runtime (Performance) § CLI • # show system cpu/memory/storage/network-stats/uptime • # show process monitor • For xlarge flavor, LB L 7 engine is bound to CPU 4 • Use this monitor to view the CPU 4 usage when concurring L 7 performance issue, such as when using SSL termination. • # show service-monitor status § Throughput and concurrent connection monitoring • NSX UI: Edge->Monitor->Statistics § Monitor edge cpu/memory/throughput etc from vsphere client • UI: v. Center->edge vm->monitor->Performance 111
- Slides: 111