DIRECT ACCESS DOS AND DONTS KIERAN JACOBSEN HP
DIRECT ACCESS, DO’S AND DON’TS KIERAN JACOBSEN HP ENTERPRISE SERVICES
PLAN FOR THE NIGHT • Pre-deployment design considerations • Deploying your first server • Diagnosing Issues
WINDOWS 7 OR 8/8. 1 Windows 7: • Requires certificate based computer authentication • Doesn’t support the use of NULL ciphers when IPHTTPS is used • Will require connectivity assistant to be installed • Has limited support for multi site deployments
HIGH AVAILABILITY OPTIONS • Load Balancing • NLB • External Load Balancer • Multi Site • Clients can select entry points automatically or can specify them manually • Global load balanced IP support • Limited Windows 7 support • Cannot deploy Direct. Access load balancing or multi-site on 2012 R 2 when Web Proxy Server installed
3 RD PARTLY LOAD BALANCERS • F 5 & Riverbed support various different deployment types • Ensure you enable NULL SSL Ciphers • Can provide SSL offload support (if supporting Windows 7)
DIRECTACCESS AND PKI • CRL and Strong CRL validation • IPSEC will fail to establish a connection if using certificate based computer authentication with computer certificates that use SHA 512 hashing algorithm
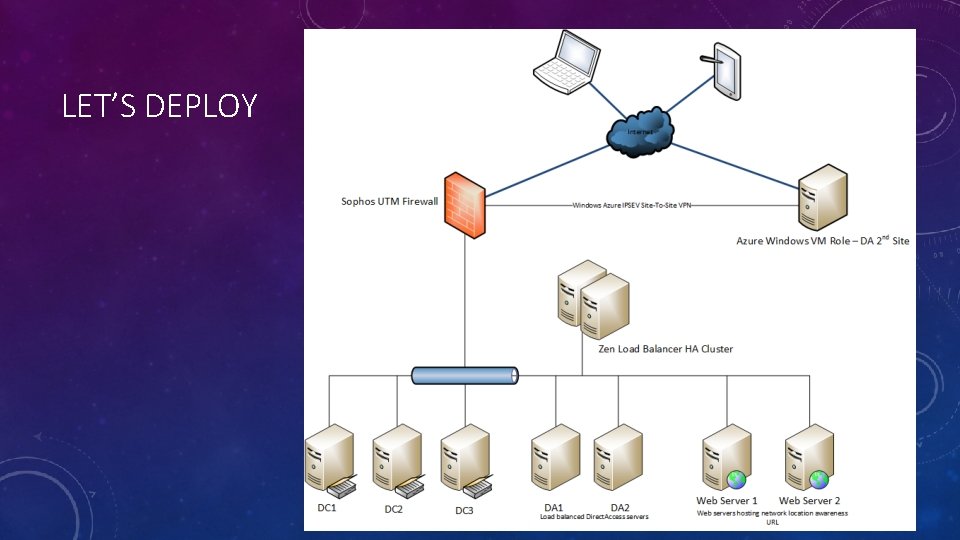
LET’S DEPLOY
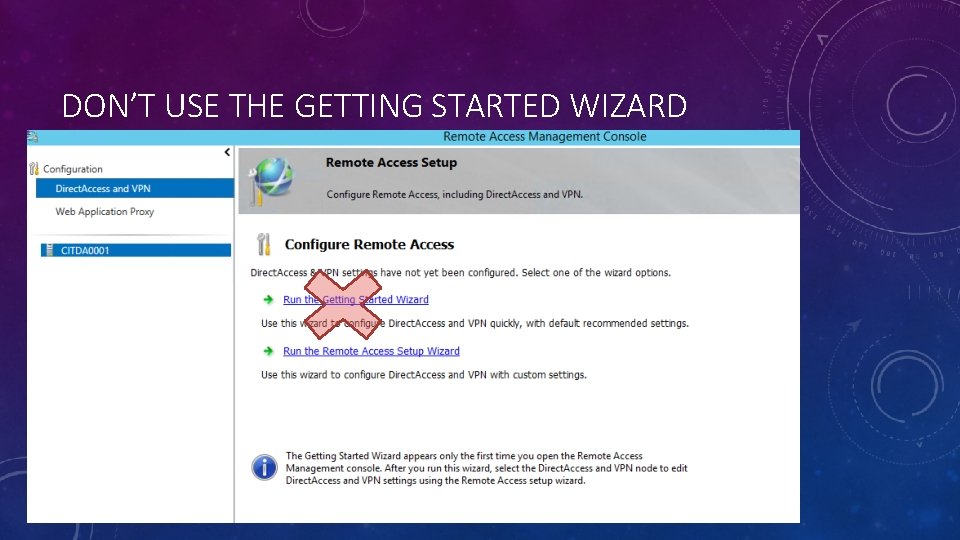
DON’T USE THE GETTING STARTED WIZARD
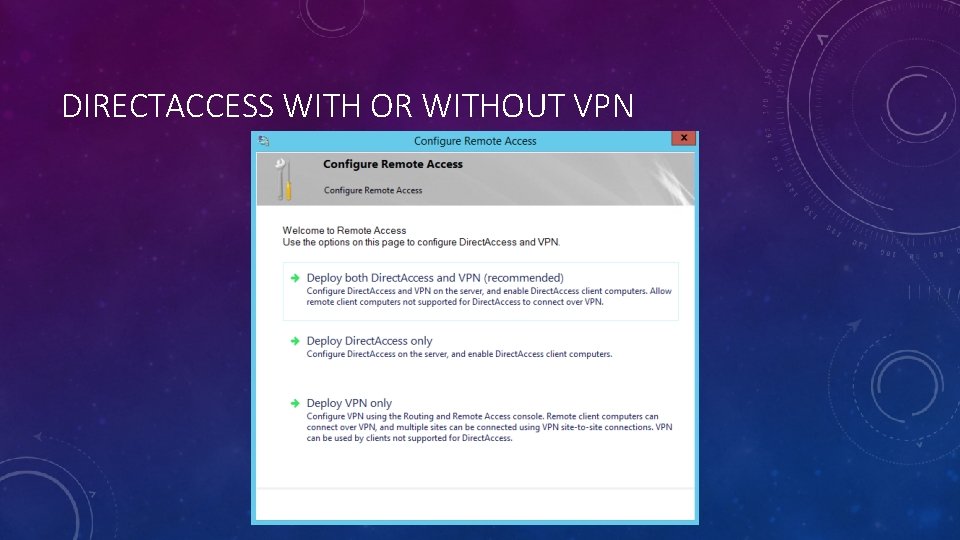
DIRECTACCESS WITH OR WITHOUT VPN
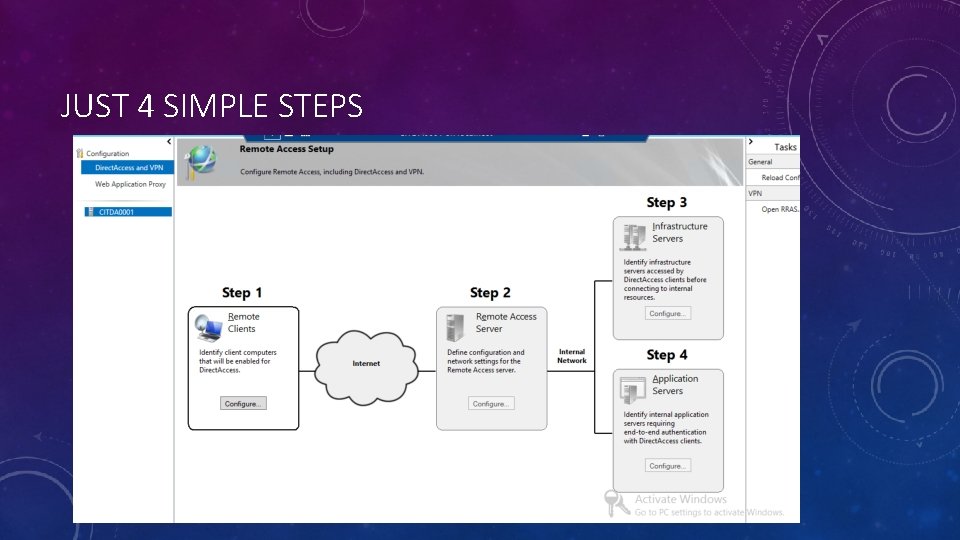
JUST 4 SIMPLE STEPS
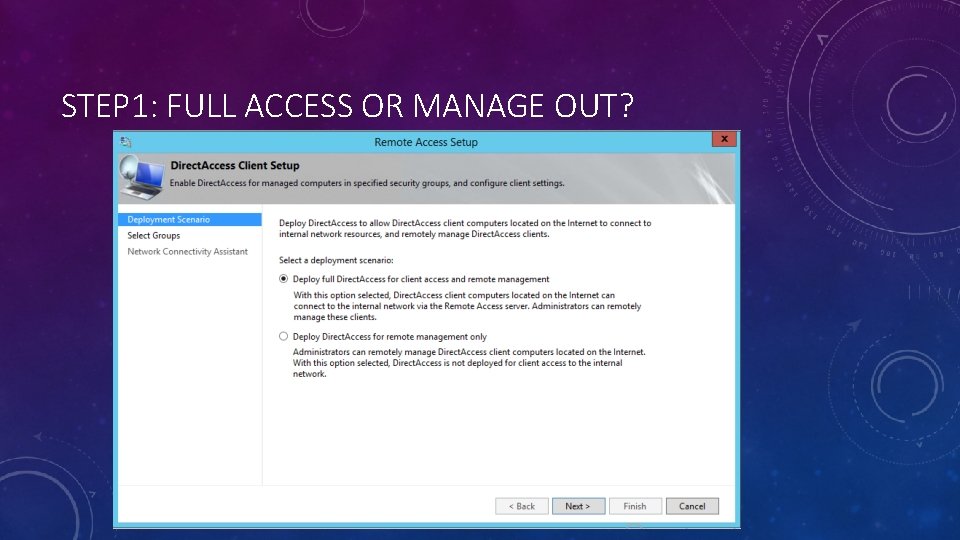
STEP 1: FULL ACCESS OR MANAGE OUT?
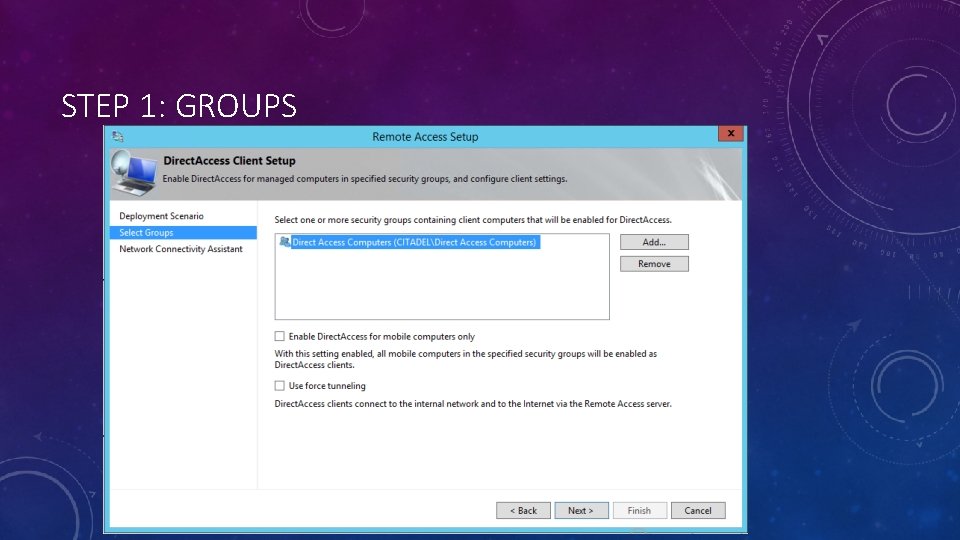
STEP 1: GROUPS
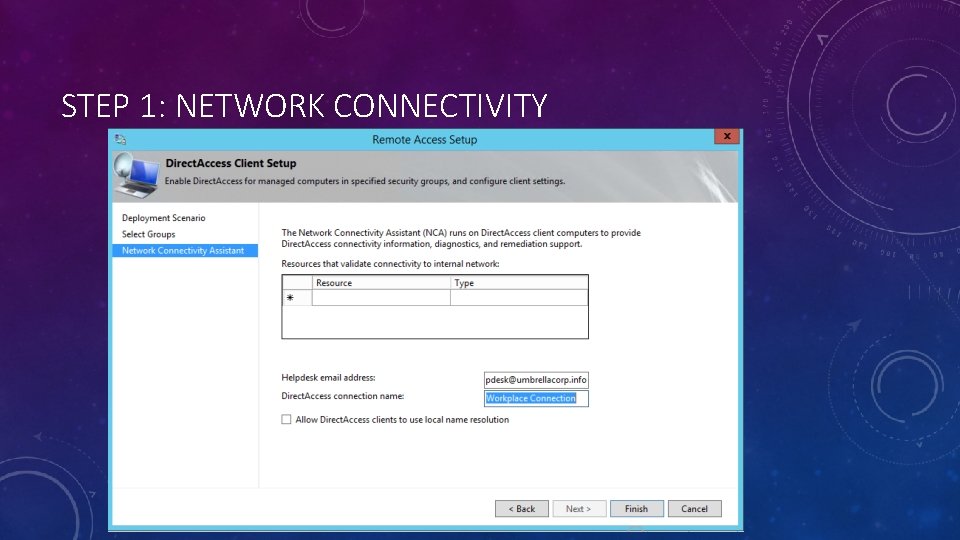
STEP 1: NETWORK CONNECTIVITY
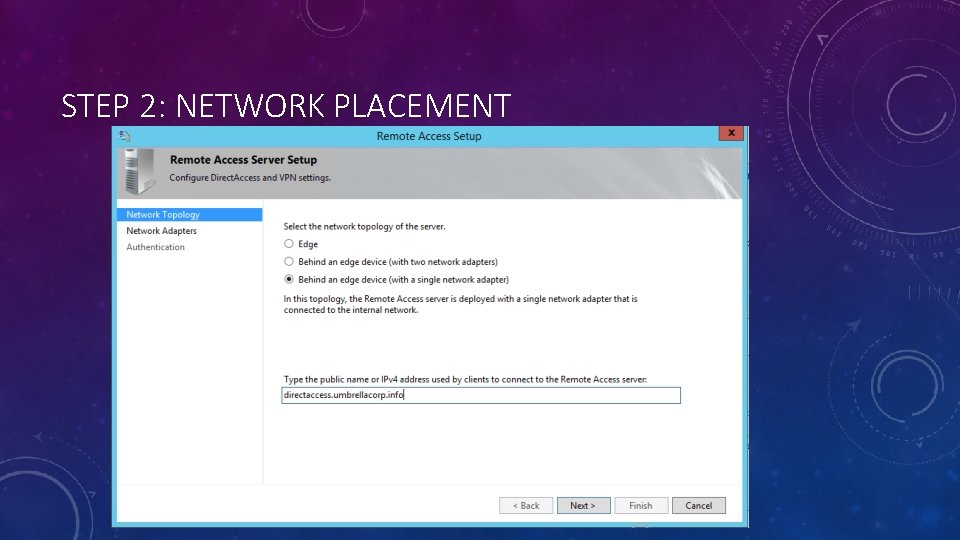
STEP 2: NETWORK PLACEMENT
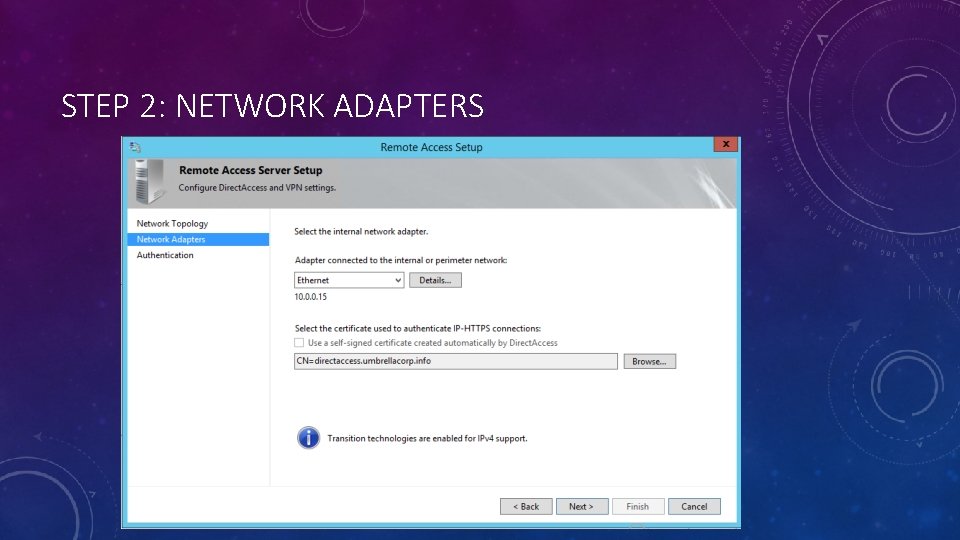
STEP 2: NETWORK ADAPTERS
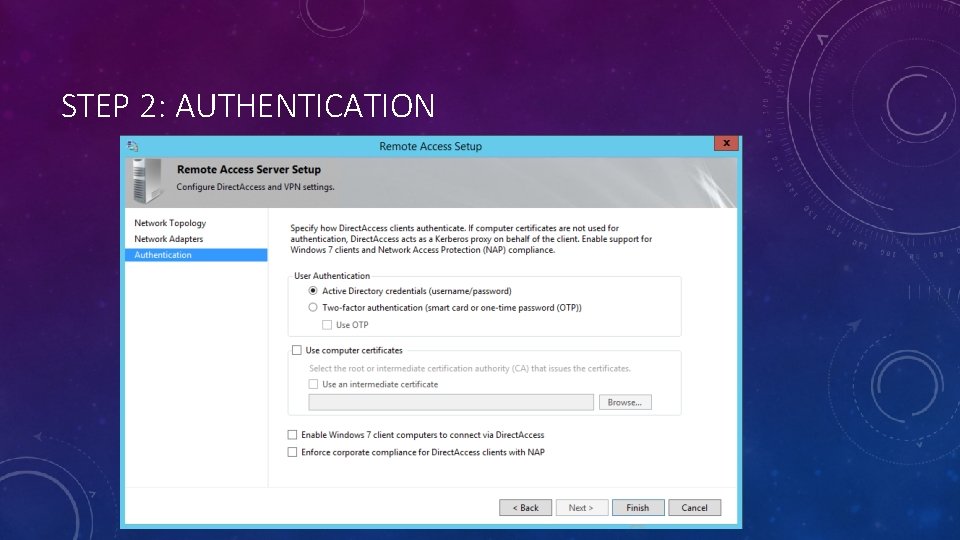
STEP 2: AUTHENTICATION
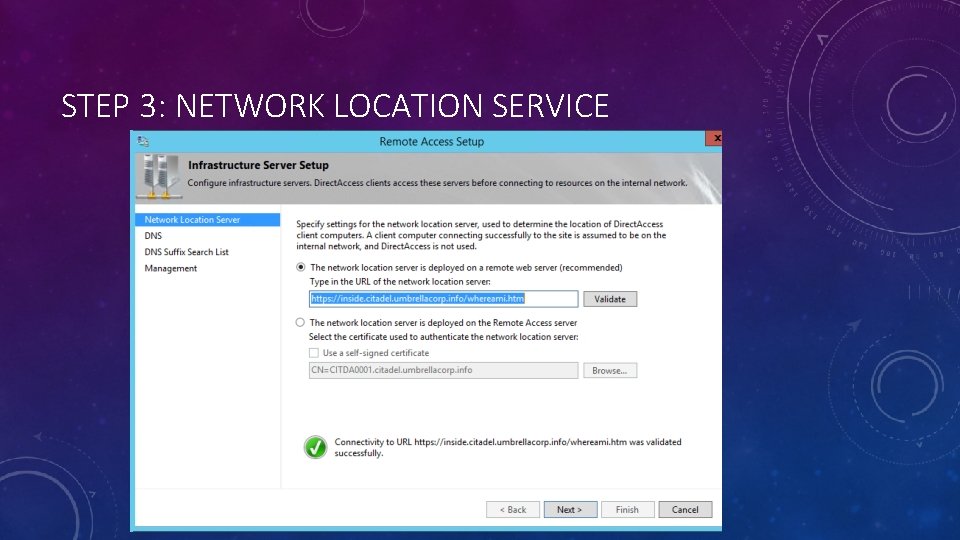
STEP 3: NETWORK LOCATION SERVICE
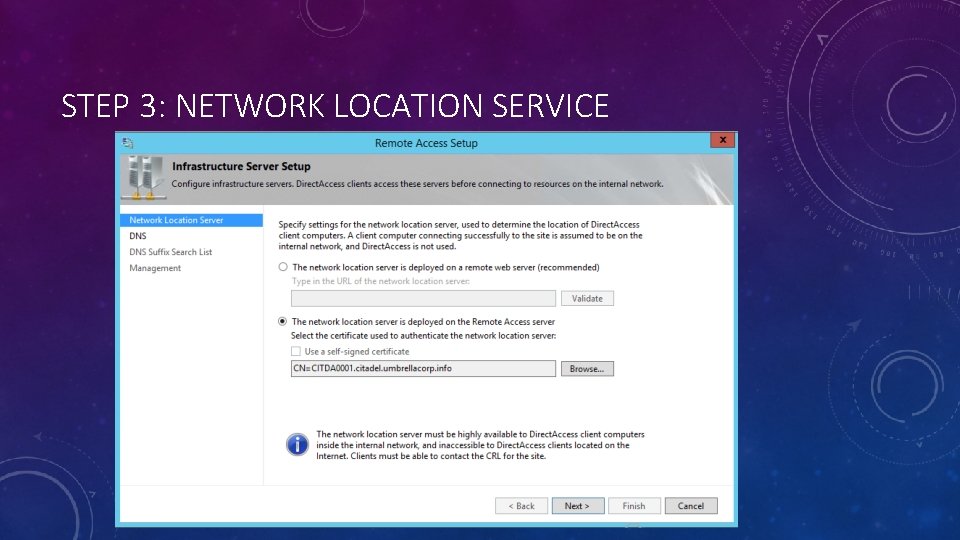
STEP 3: NETWORK LOCATION SERVICE
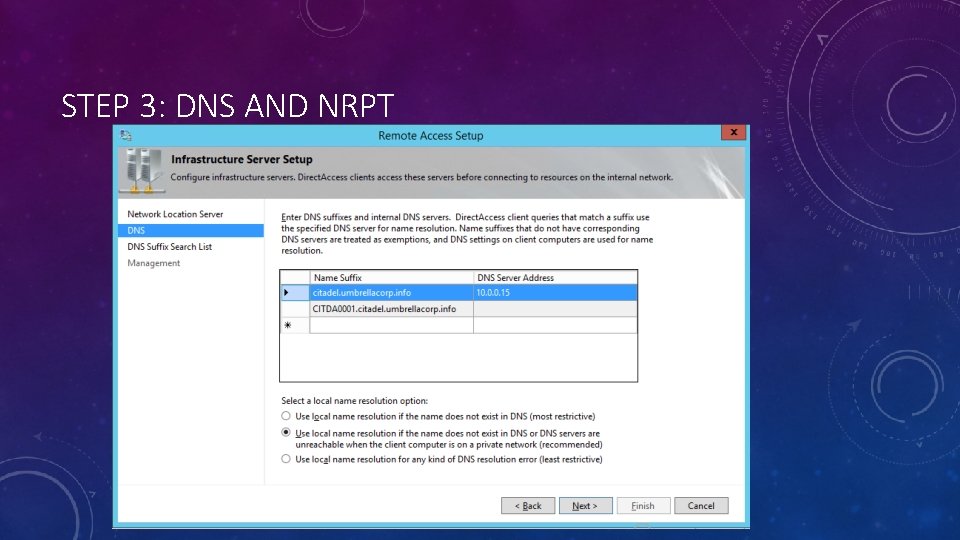
STEP 3: DNS AND NRPT
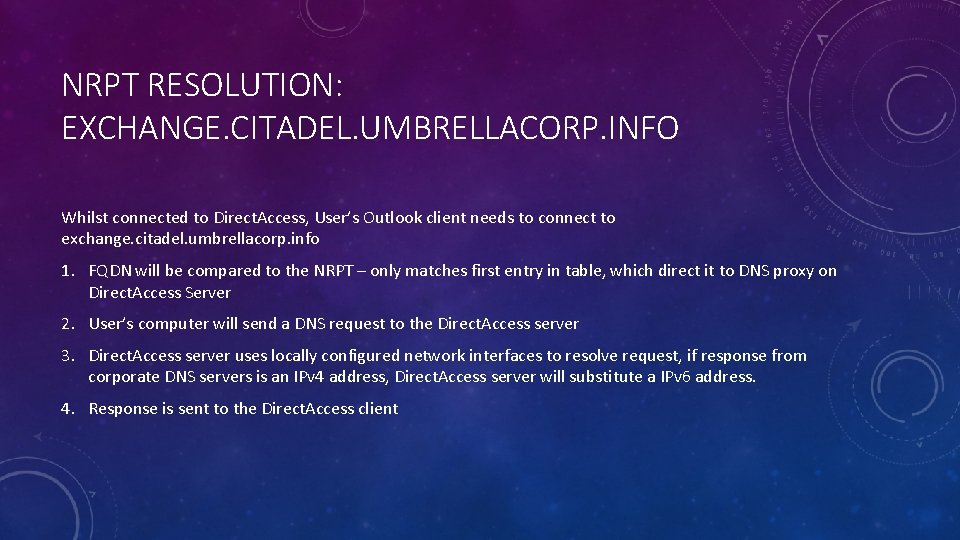
NRPT RESOLUTION: EXCHANGE. CITADEL. UMBRELLACORP. INFO Whilst connected to Direct. Access, User’s Outlook client needs to connect to exchange. citadel. umbrellacorp. info 1. FQDN will be compared to the NRPT – only matches first entry in table, which direct it to DNS proxy on Direct. Access Server 2. User’s computer will send a DNS request to the Direct. Access server 3. Direct. Access server uses locally configured network interfaces to resolve request, if response from corporate DNS servers is an IPv 4 address, Direct. Access server will substitute a IPv 6 address. 4. Response is sent to the Direct. Access client
NRPT RESOLUTION: INSIDE. CITADEL. UMBRELLACORP. INFO (NLS ADDRESS) Whilst connected to Direct. Access, Direct. Access performs a connectivity test to see if it is connected to the corporate network 1. FQDN will be compared to the NRPT – matches second entry in table, which is the NRPT exemption. 2. User’s computer will send a DNS request directly to the DNS server configured on the client’s NIC 3. Public DNS unable to resolve the address, Direct. Access determines it is still externally connected.
NRPT RESOLUTION: MICROSOFT. COM Whilst connected to Direct. Access, User opens Internet Explorer and attempts to open up the Microsoft web page 1. FQDN will be compared to the NRPT – no matching entries are found 2. If Split Tunnelling (Default) : User’s computer will send a DNS request directly to the DNS server configured on the client’s NIC, Public DNS will then resolve the address and respond to the client. OR If Force Tunnelling: User’s computer will send DNS request to Direct. Access server, and the Direct. Access server will use locally configured network interfaces to resolve request, if response from corporate DNS servers is an IPv 4 address, Direct. Access server will substitute a IPv 6 address. The address is then sent to the client.
NRPT RESOLUTION: INTRANET (SINGLE LABEL) Whilst connected to Direct. Access, User opens Internet Explorer, types intranet in the box, hits enter: 1. Single-label is in use, append DNS suffix to request to form an FQDN 2. FQDN will be compared to the NRPT – only matches first entry in table, which direct it to DNS proxy on Direct. Access Server 3. User’s computer will send a DNS request to the Direct. Access server 4. Direct. Access server uses locally configured network interfaces to resolve request, if response from corporate DNS servers is an IPv 4 address, Direct. Access server will substitute a IPv 6 address. 5. Response is sent to the Direct. Access client – Either 1) resolved address or 2) Name not found 6. If name has been resolved, process completed all is done, if name not found, return to step 2 and try the next entry in the DNS suffix search order. If all suffix search entries have been exhausted, continue to 7. 7. Attempt to use LLMNR, Net. BIOS or WINS * Special Warning *
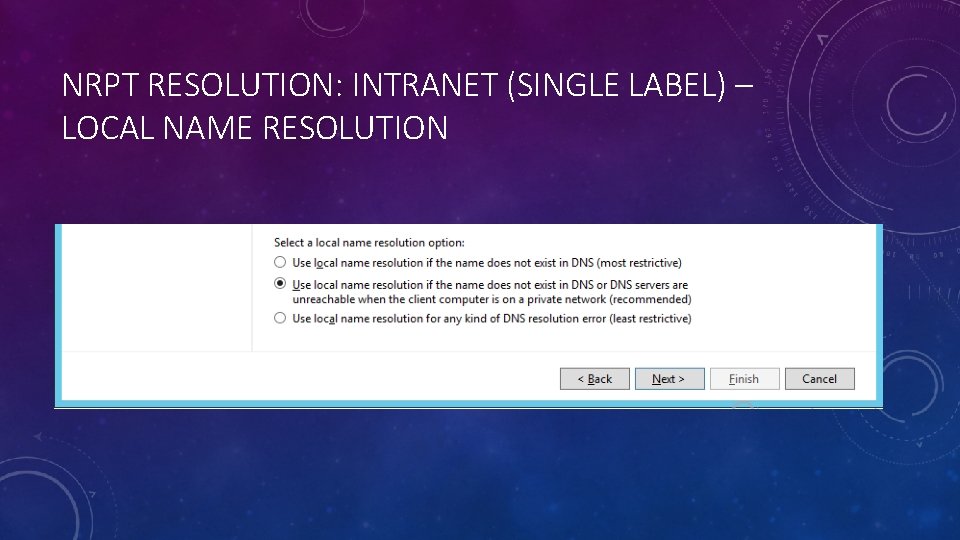
NRPT RESOLUTION: INTRANET (SINGLE LABEL) – LOCAL NAME RESOLUTION
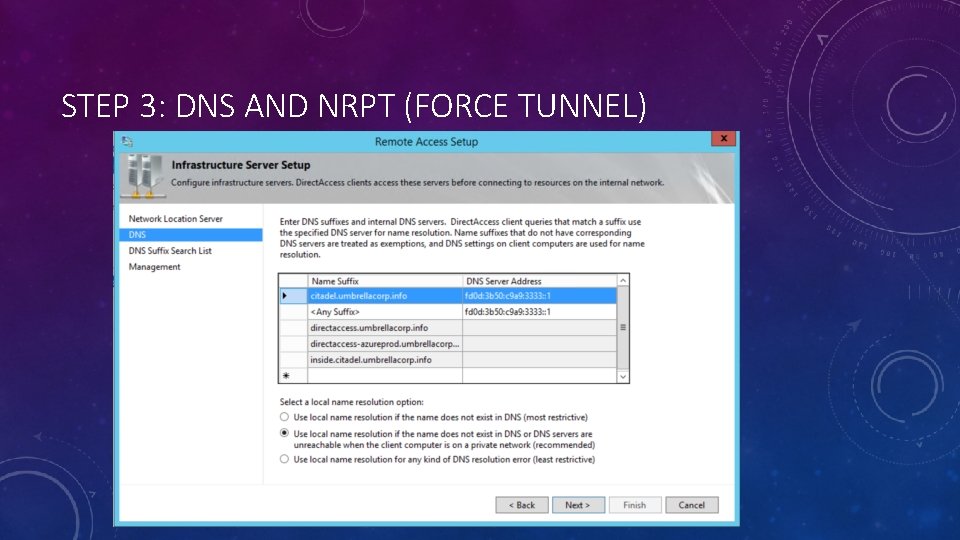
STEP 3: DNS AND NRPT (FORCE TUNNEL)
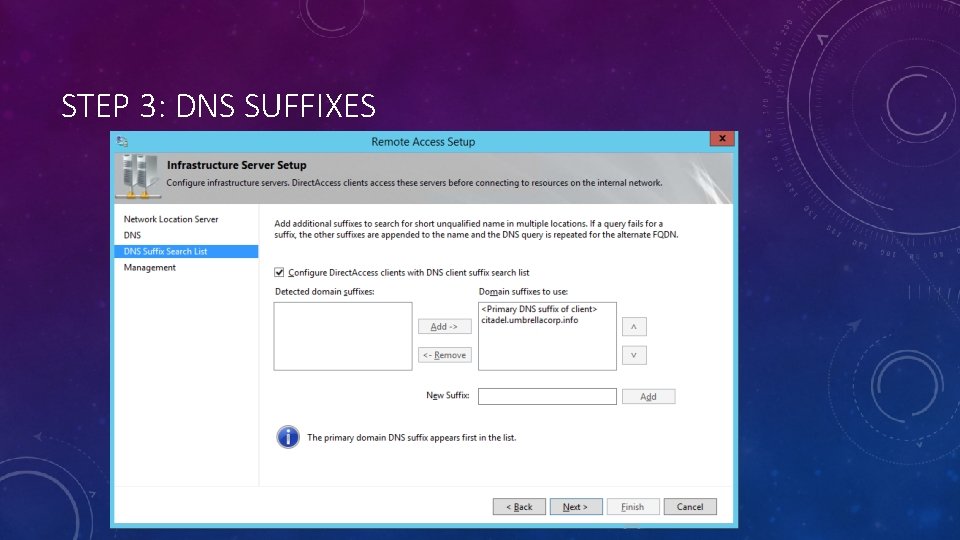
STEP 3: DNS SUFFIXES
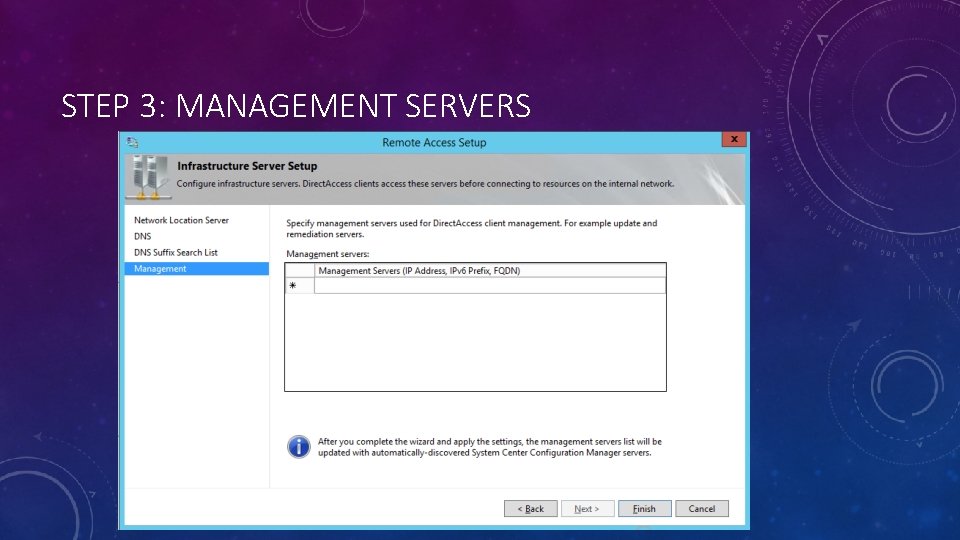
STEP 3: MANAGEMENT SERVERS
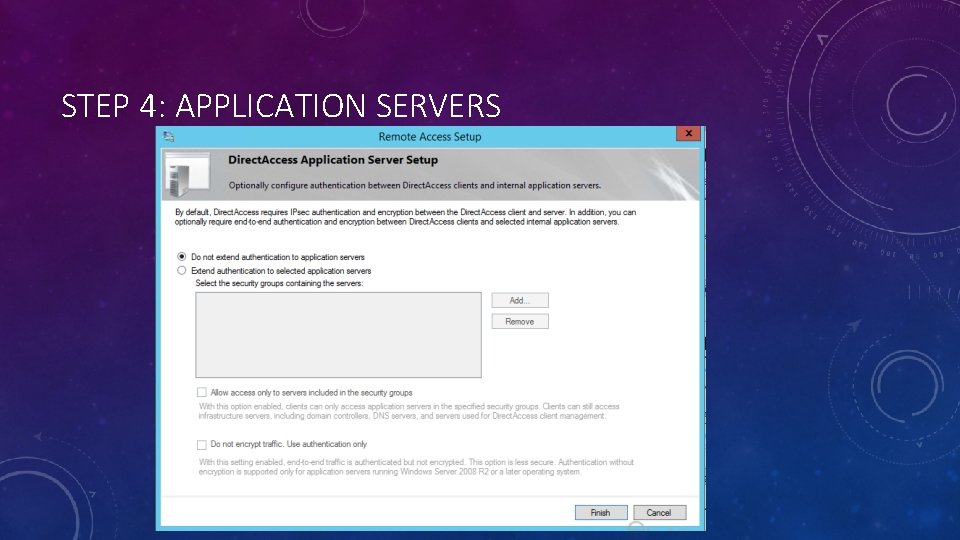
STEP 4: APPLICATION SERVERS
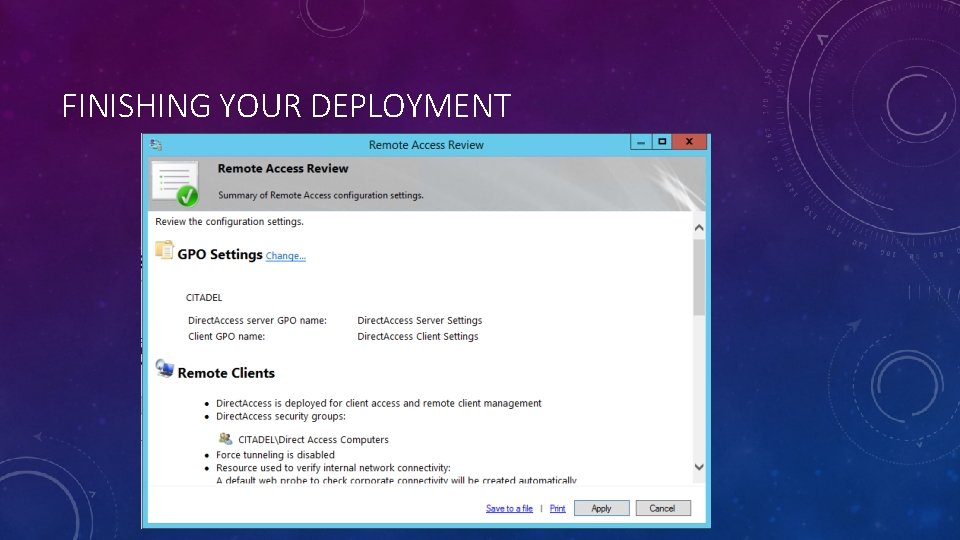
FINISHING YOUR DEPLOYMENT
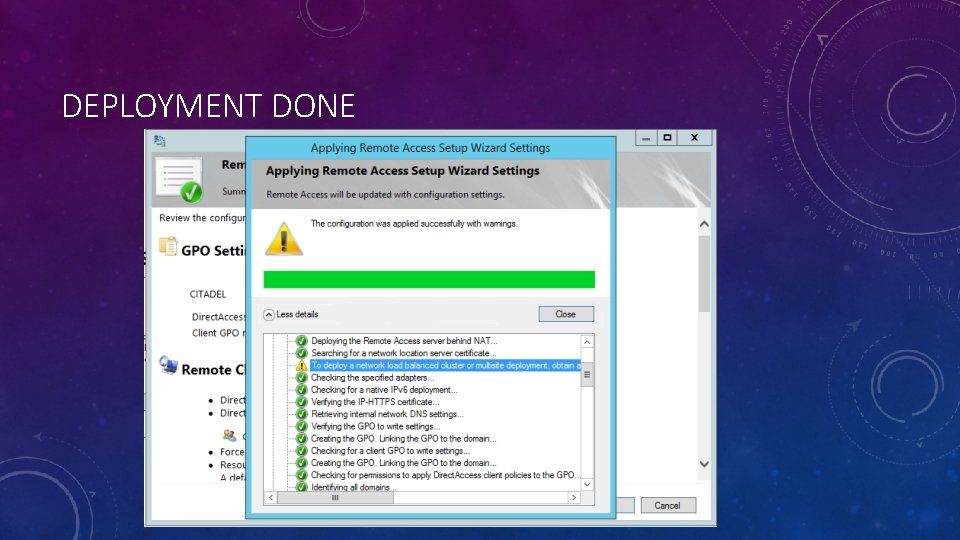
DEPLOYMENT DONE
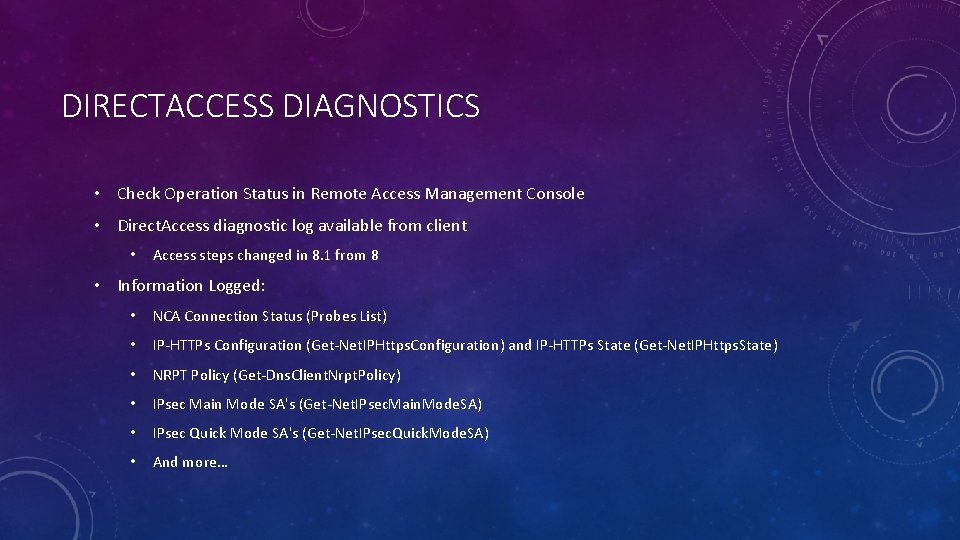
DIRECTACCESS DIAGNOSTICS • Check Operation Status in Remote Access Management Console • Direct. Access diagnostic log available from client • Access steps changed in 8. 1 from 8 • Information Logged: • NCA Connection Status (Probes List) • IP-HTTPs Configuration (Get-Net. IPHttps. Configuration) and IP-HTTPs State (Get-Net. IPHttps. State) • NRPT Policy (Get-Dns. Client. Nrpt. Policy) • IPsec Main Mode SA's (Get-Net. IPsec. Main. Mode. SA) • IPsec Quick Mode SA's (Get-Net. IPsec. Quick. Mode. SA) • And more…
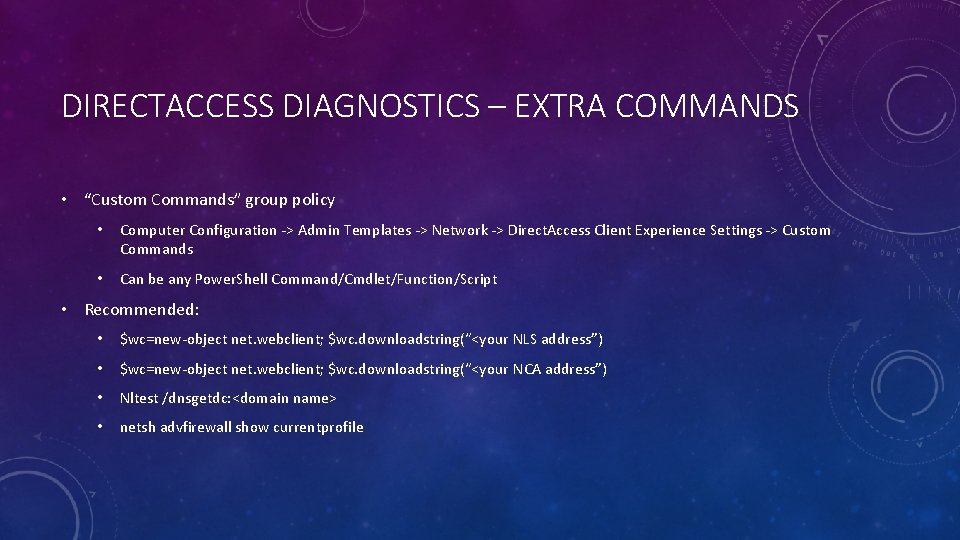
DIRECTACCESS DIAGNOSTICS – EXTRA COMMANDS • “Custom Commands” group policy • Computer Configuration -> Admin Templates -> Network -> Direct. Access Client Experience Settings -> Custom Commands • Can be any Power. Shell Command/Cmdlet/Function/Script • Recommended: • $wc=new-object net. webclient; $wc. downloadstring(“<your NLS address”) • $wc=new-object net. webclient; $wc. downloadstring(“<your NCA address”) • Nltest /dnsgetdc: <domain name> • netsh advfirewall show currentprofile
DIRECTACCESS AND GROUP POLICY • Server and workstation configured using group policy • Created by management console • Server policy filtered by server AD account • Client policy filtered by specified groups in step 1 wizard • Multi site creates server policies for each site • Policies created at root of domain
ANTIVIRUS AND SECURITY SOFTWARE • Direct. Access requires Windows Firewall IPSEC components • Be careful of web filtering functions • Ensure network IPS/IDS exclusions are correct
QUESTIONS AND LINKS • My Blog: http: //aperturescience. su • My Twitter: @kjacobsen • Richard Hicks’ Blog: http: //directaccess. richardhicks. com/ • Tom Schinder’s Blog: http: //blogs. technet. com/b/tomshinder
- Slides: 35