Hashbased Signatures Andreas Hlsing PostQuantum Signatures Lattice MQ
Hash-based Signatures Andreas Hülsing
Post-Quantum Signatures Lattice, MQ, Coding Signature and/or key sizes Runtimes Secure parameters 5 -9 -2021 PAGE 2
![Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-3.jpg)
Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Fast 5 -9 -2021 PAGE 3
RSA – DSA – EC-DSA. . . Intractability Assumption Cryptographic hash function RSA, DH, SVP, MQ, … Digital signature scheme 5 -9 -2021 PAGE 4
Hash function families
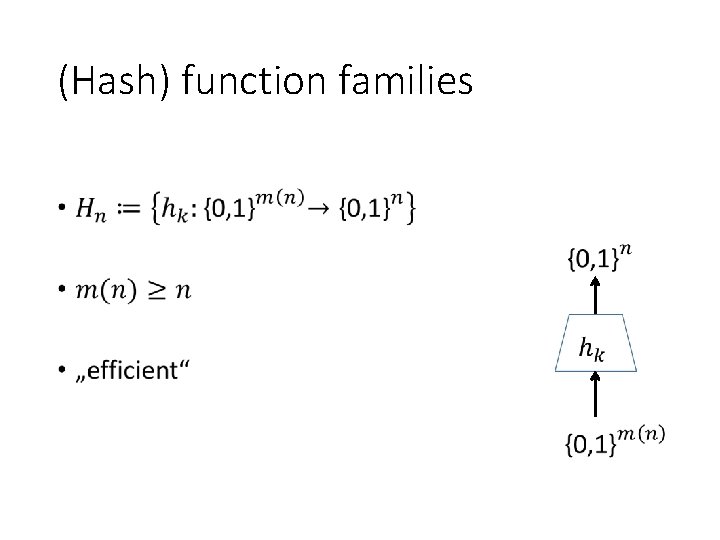
(Hash) function families •
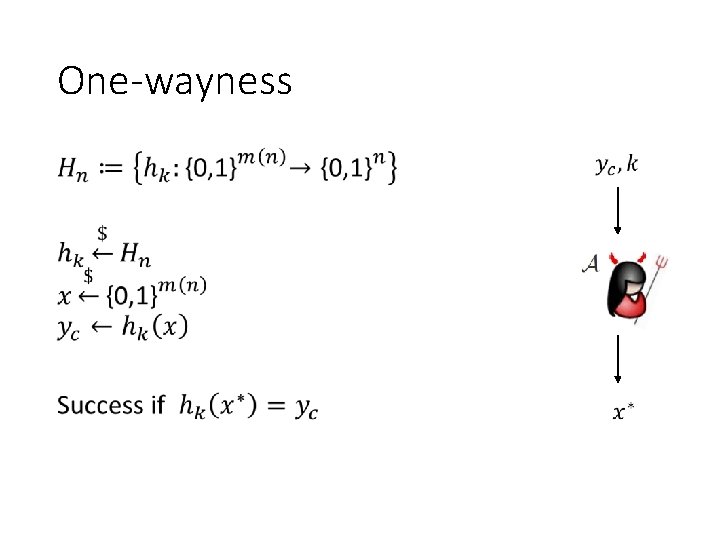
One-wayness •
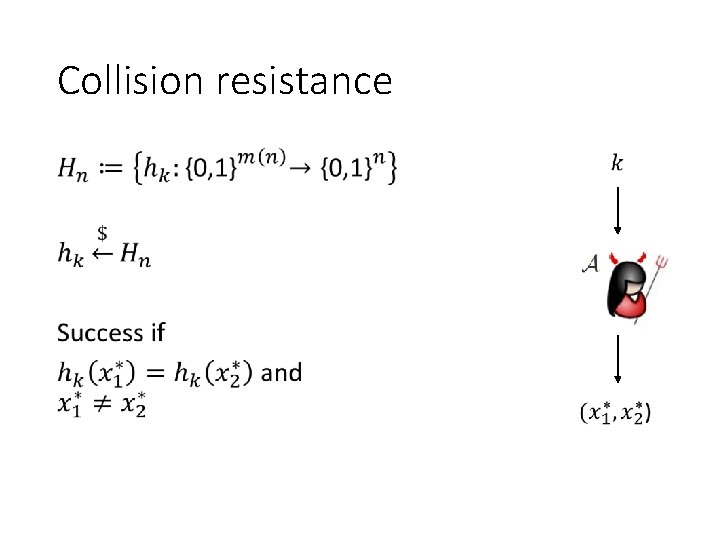
Collision resistance
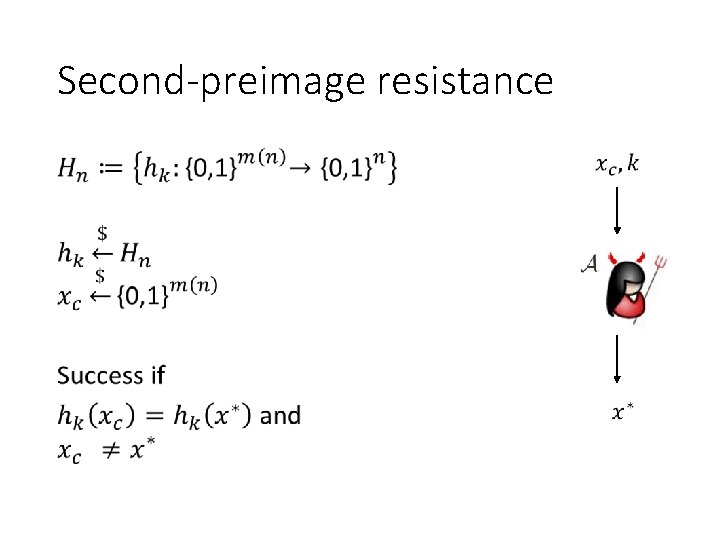
Second-preimage resistance •
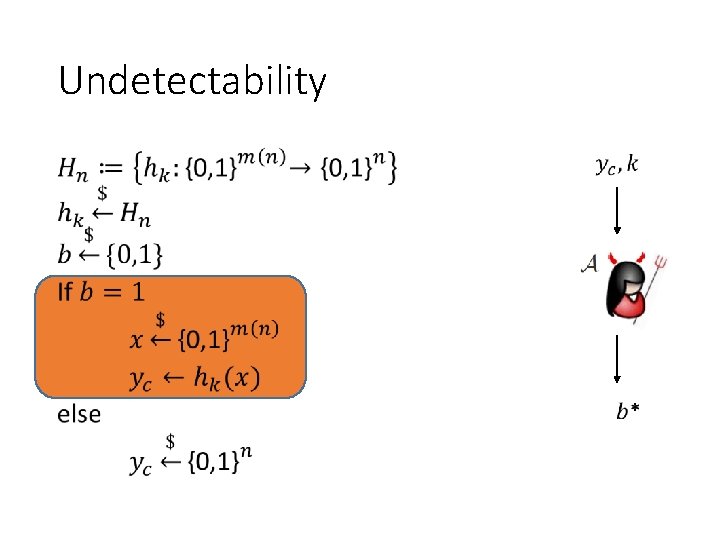
Undetectability •
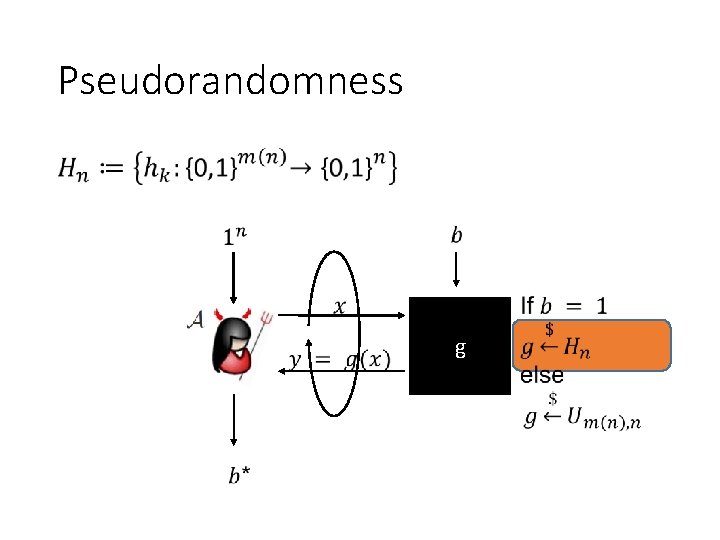
Pseudorandomness • g
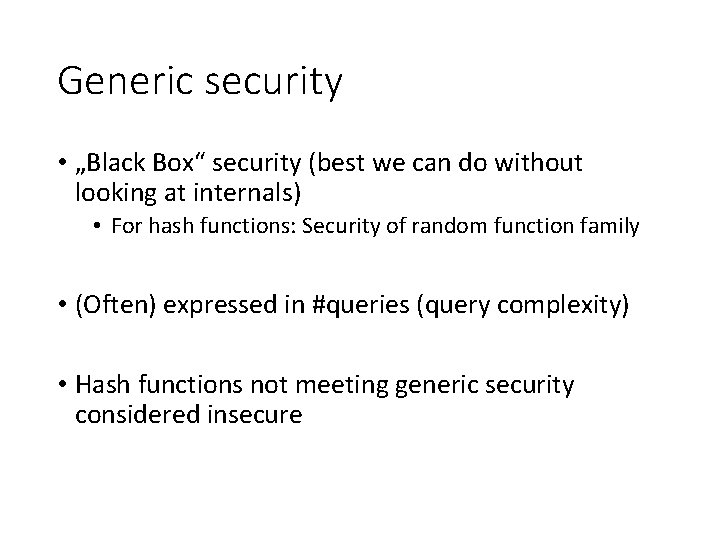
Generic security • „Black Box“ security (best we can do without looking at internals) • For hash functions: Security of random function family • (Often) expressed in #queries (query complexity) • Hash functions not meeting generic security considered insecure
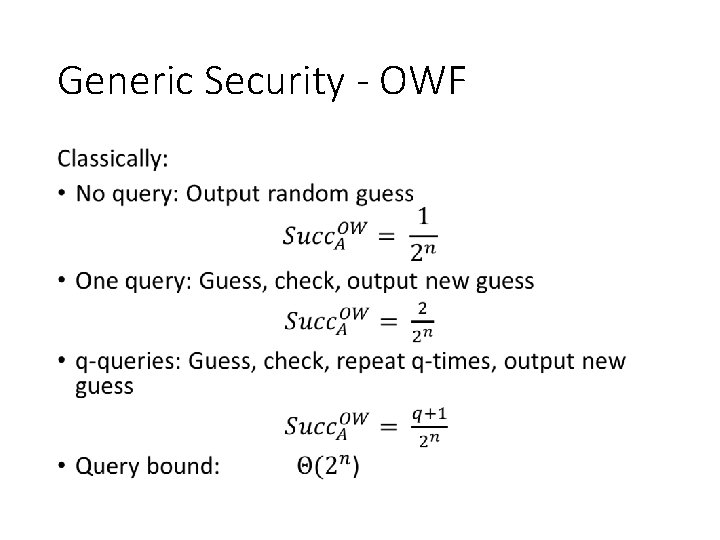
Generic Security - OWF •
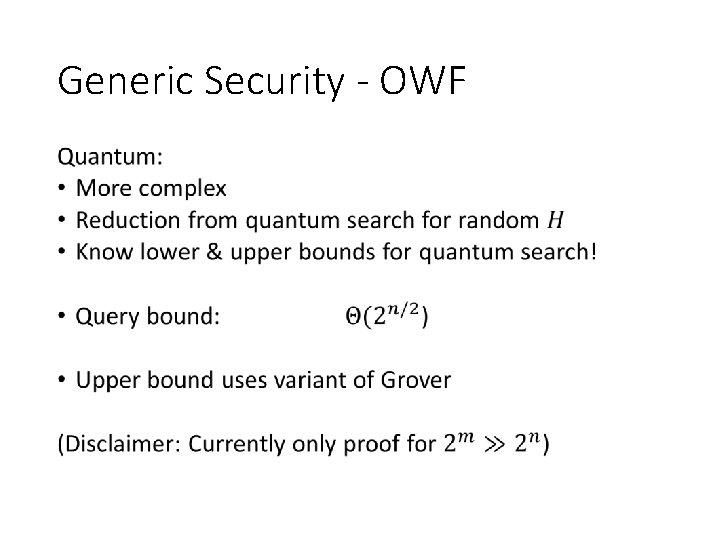
Generic Security - OWF •
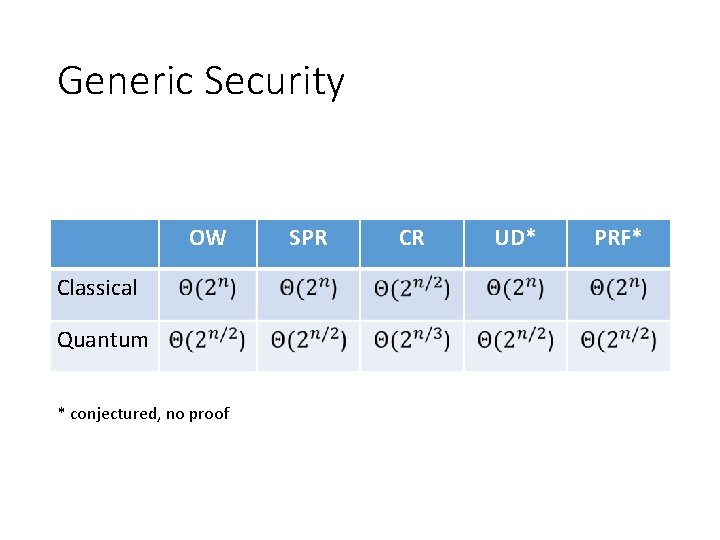
Generic Security OW Classical Quantum * conjectured, no proof SPR CR UD* PRF*
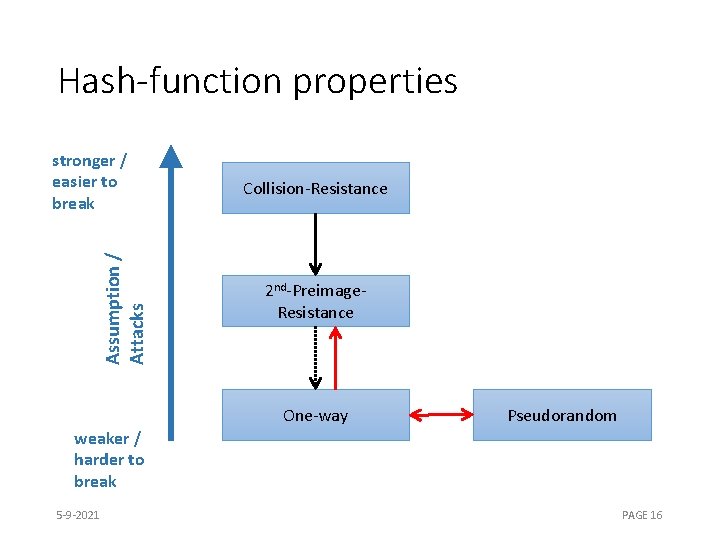
Hash-function properties Assumption / Attacks stronger / easier to break Collision-Resistance 2 nd-Preimage. Resistance One-way Pseudorandom weaker / harder to break 5 -9 -2021 PAGE 16
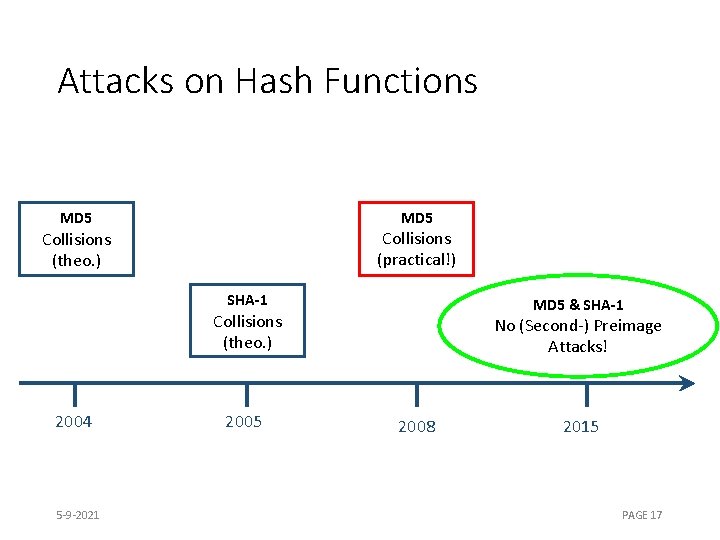
Attacks on Hash Functions MD 5 Collisions (practical!) Collisions (theo. ) SHA-1 MD 5 & SHA-1 Collisions (theo. ) 2004 5 -9 -2021 2005 No (Second-) Preimage Attacks! 2008 2015 PAGE 17
Basic Construction 5 -9 -2021 PAGE 18
![Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-19.jpg)
Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK sk 1, 0 sk 1, 1 H PK Sig 5 -9 -2021 skm, 0 H pk 1, 0 b 1 = n bit * H H pk 1, 1 Mux sk 1, b 1 skm, 1 H H pkm, 0 b 2 Mux bm pkm, 1 Mux skm, bm PAGE 19
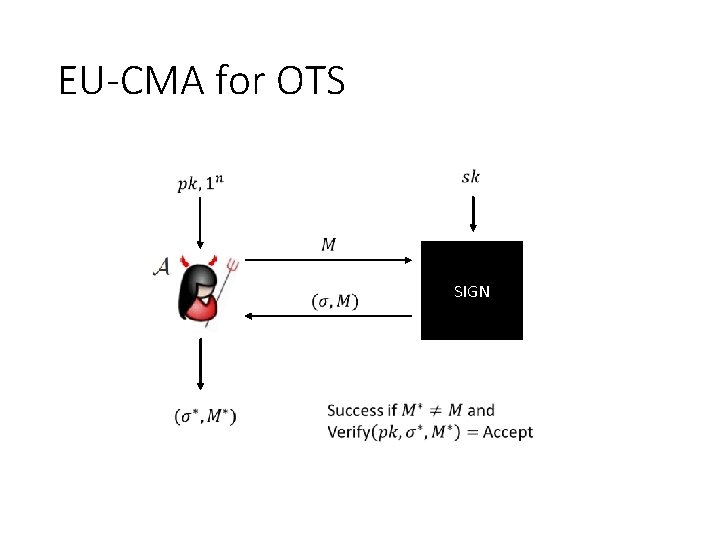
EU-CMA for OTS SIGN
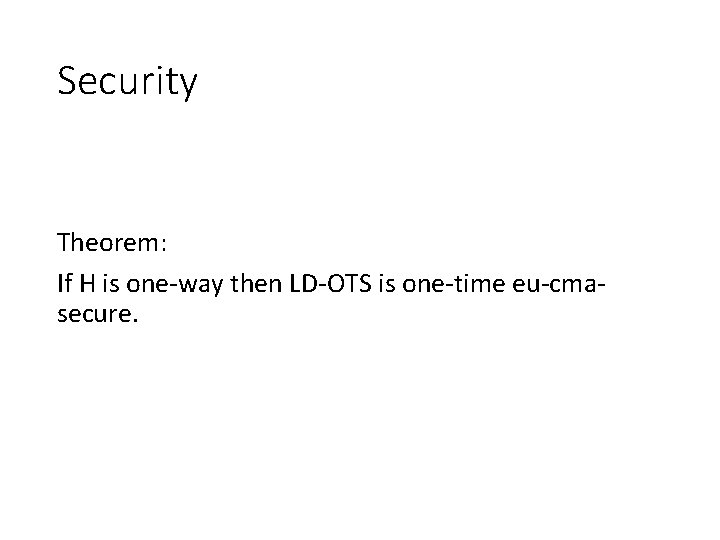
Security Theorem: If H is one-way then LD-OTS is one-time eu-cmasecure.
Reduction • sk 1, 0 H pk 1, 0 sk 1, 1 H pk 1, 1 skm, 0 H H H pkm, 0 skm, 1 H pkm, 1
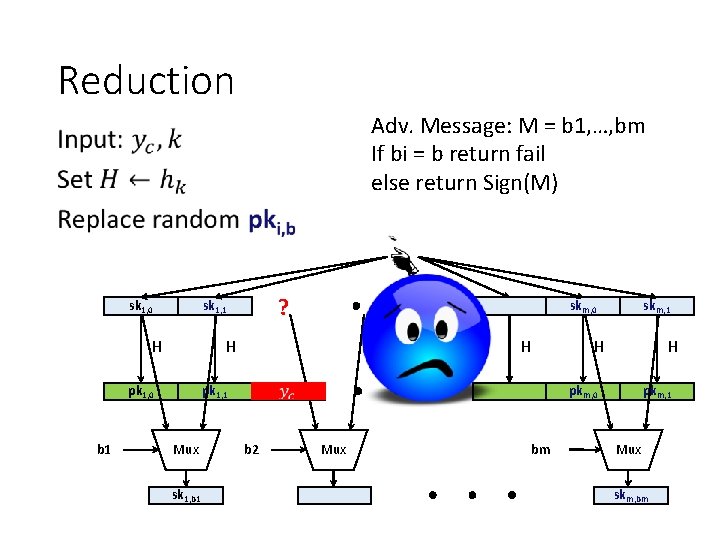
Reduction Adv. Message: M = b 1, …, bm If bi = b return fail else return Sign(M) • sk 1, 0 H skm, 0 H pk 1, 0 b 1 ? sk 1, 1 H H pk 1, 1 Mux sk 1, b 1 skm, 1 H pkm, 0 b 2 Mux bm pkm, 1 Mux skm, bm
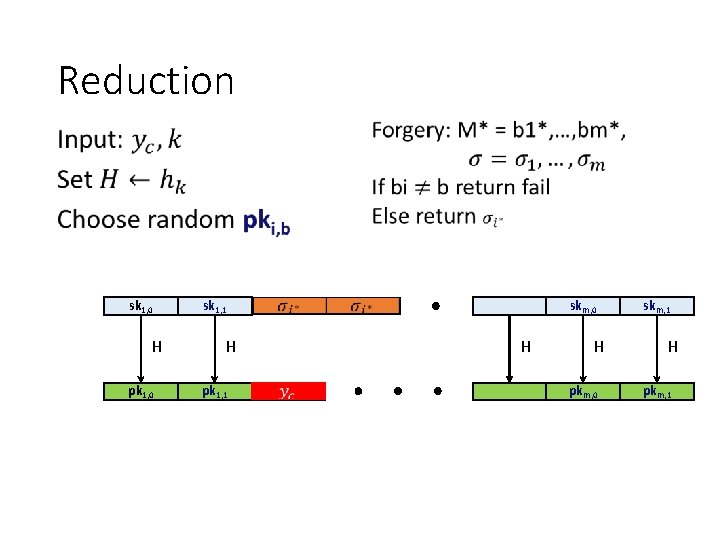
Reduction • sk 1, 0 H pk 1, 0 sk 1, 1 H pk 1, 1 ? skm, 0 H H pkm, 0 skm, 1 H pkm, 1
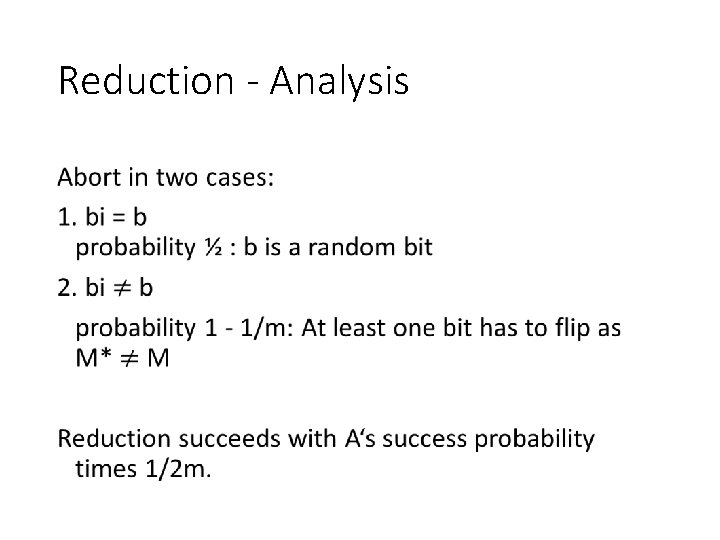
Reduction - Analysis •
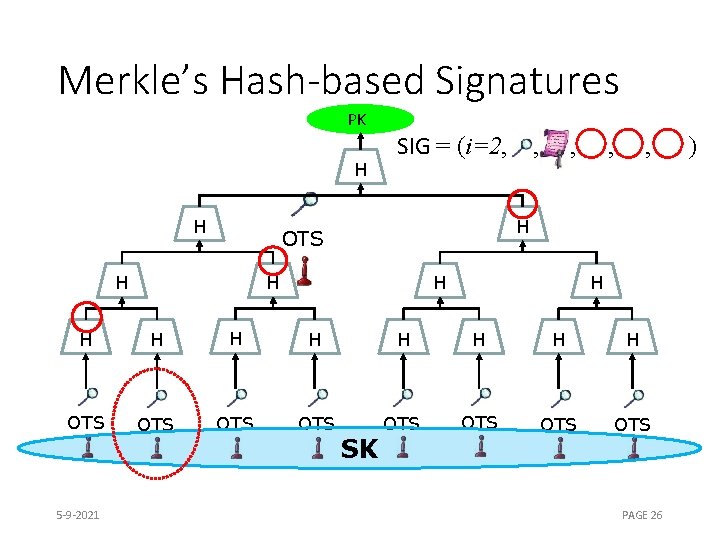
Merkle’s Hash-based Signatures PK H H SIG = (i=2, , H OTS H , H H H OTS OTS 5 -9 -2021 SK PAGE 26 )
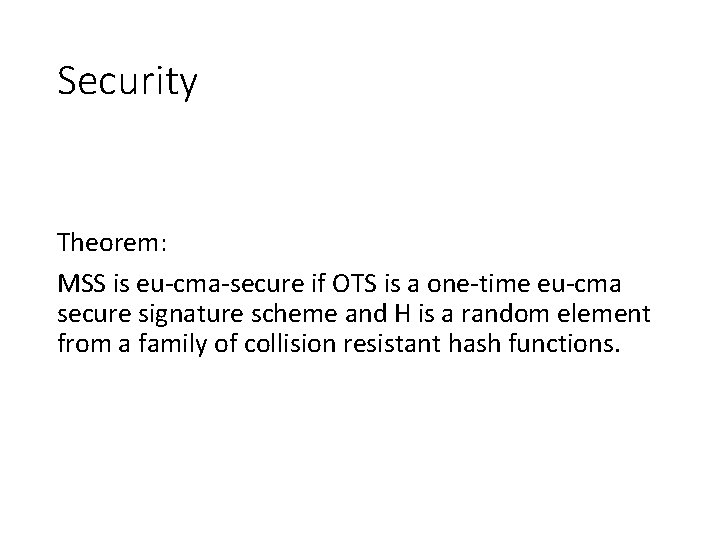
Security Theorem: MSS is eu-cma-secure if OTS is a one-time eu-cma secure signature scheme and H is a random element from a family of collision resistant hash functions.
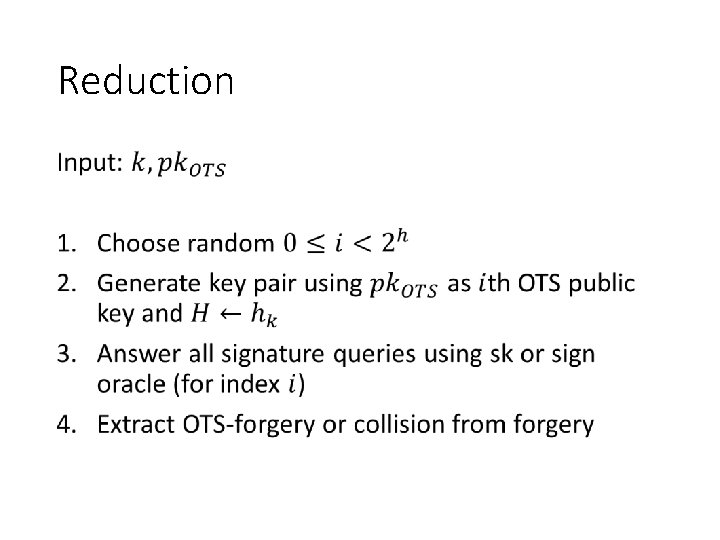
Reduction •
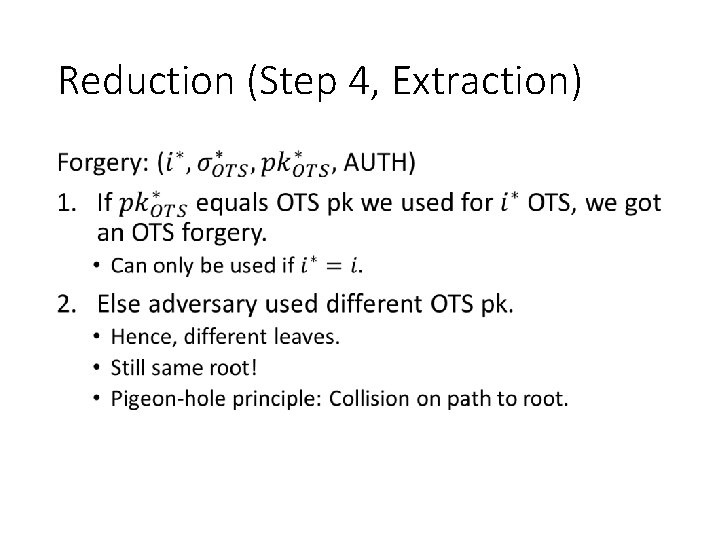
Reduction (Step 4, Extraction) •

Winternitz-OTS
![Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-31.jpg)
Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK sk 1, 0 Sig skm, 0 H pk 1, 0 b 1 = n bit sk 1, 1 H PK * H H H pk 1, 1 Mux sk 1, b 1 skm, 1 H pkm, 0 b 2 Mux bn pkm, 1 Mux skm, bm
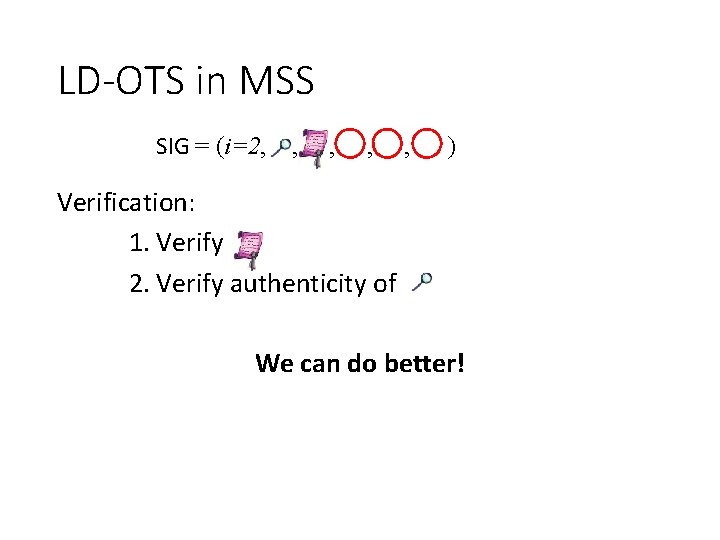
LD-OTS in MSS SIG = (i=2, , , ) Verification: 1. Verify 2. Verify authenticity of We can do better!
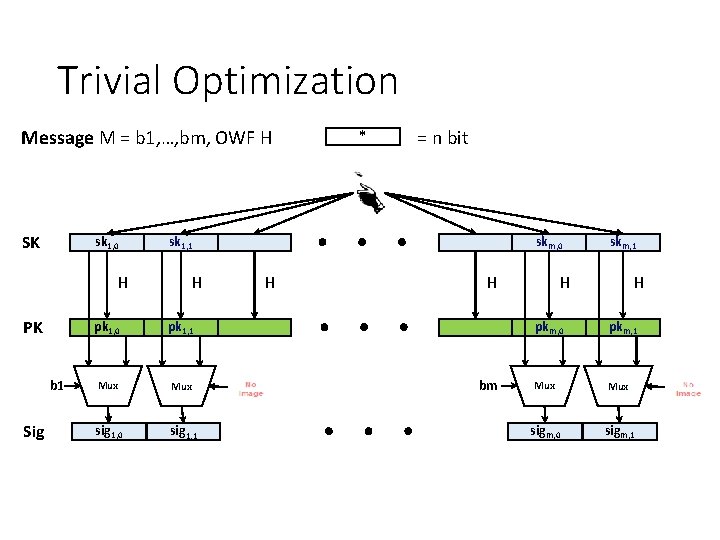
Trivial Optimization Message M = b 1, …, bm, OWF H SK sk 1, 0 H PK b 1 Sig * = n bit sk 1, 1 H pk 1, 0 pk 1, 1 Mux sig 1, 0 sig 1, 1 skm, 0 H H bm skm, 1 H H pkm, 0 pkm, 1 Mux sigm, 0 sigm, 1
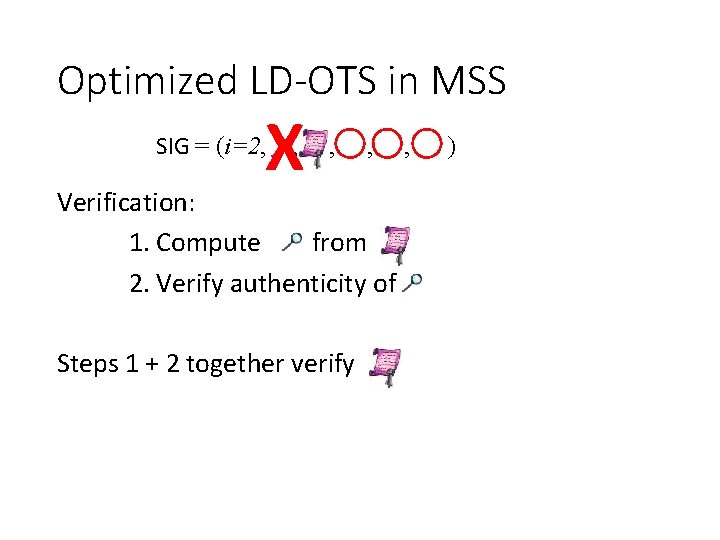
Optimized LD-OTS in MSS X SIG = (i=2, , , , Verification: 1. Compute from 2. Verify authenticity of Steps 1 + 2 together verify , )
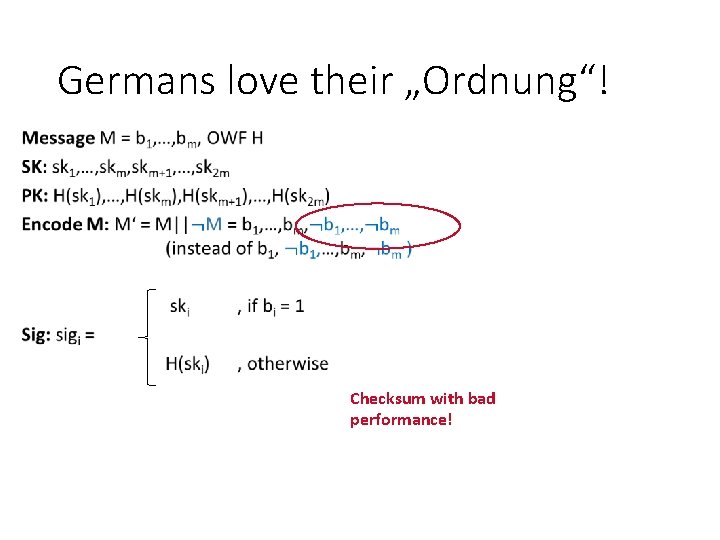
Germans love their „Ordnung“! Checksum with bad performance!
Optimized LD-OTS
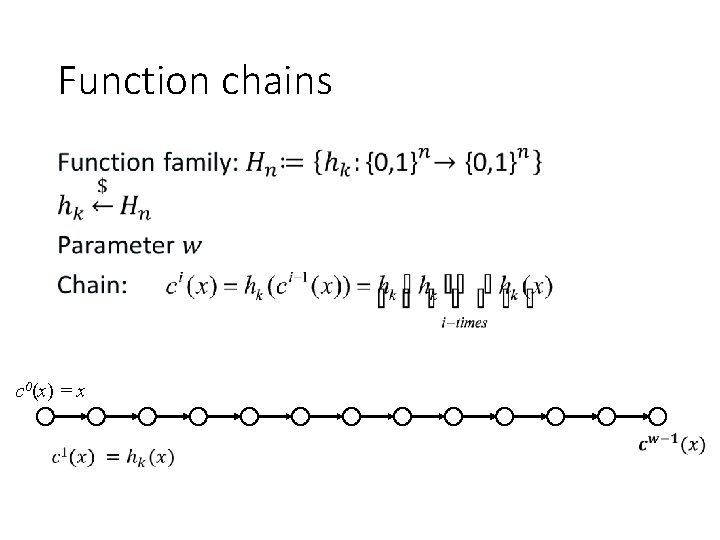
Function chains • c 0(x) = x
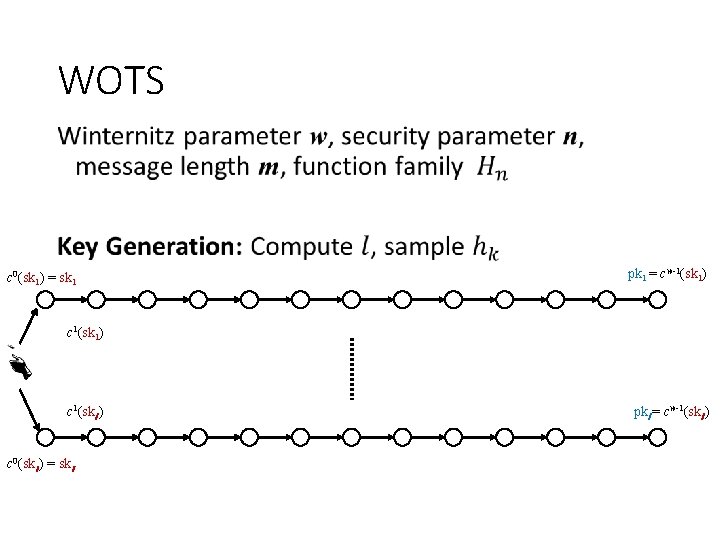
WOTS • c 0(sk 1) = sk 1 pk 1 = cw-1(sk 1) c 1(skl ) c 0(skl ) = skl pkl = cw-1(skl )
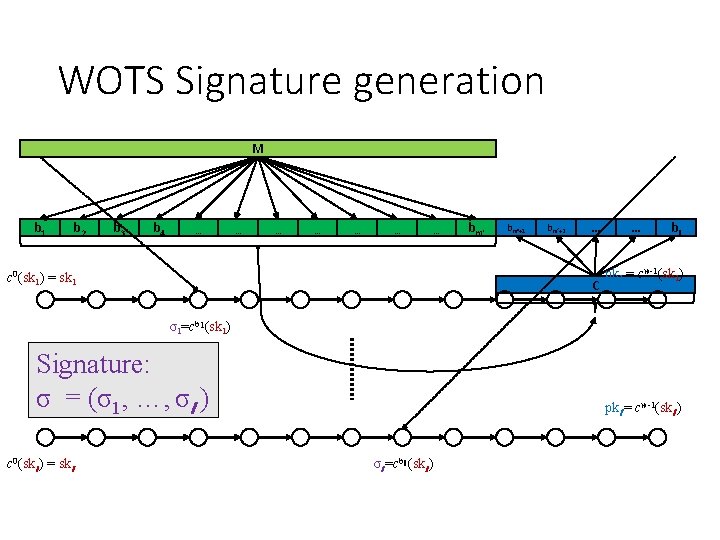
WOTS Signature generation M b 1 b 2 b 3 b 4 … … … … c 0(sk 1) = sk 1 bm‘+1 bm‘+2 … C … bl pk 1 = cw-1(sk 1) σ1=cb 1(sk 1) Signature: σ = (σ1, …, σl ) c 0(skl ) = skl pkl = cw-1(skl ) σl =cbl (skl )
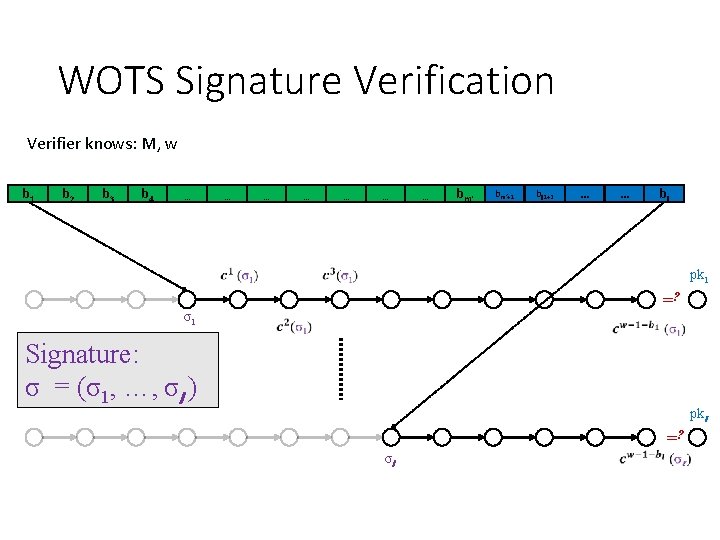
WOTS Signature Verification Verifier knows: M, w b 1 b 2 b 3 b 4 … … … … bm‘+1 bl 1+2 … … bl pk 1 =? σ1 Signature: σ = (σ1, …, σl ) pkl =? σl
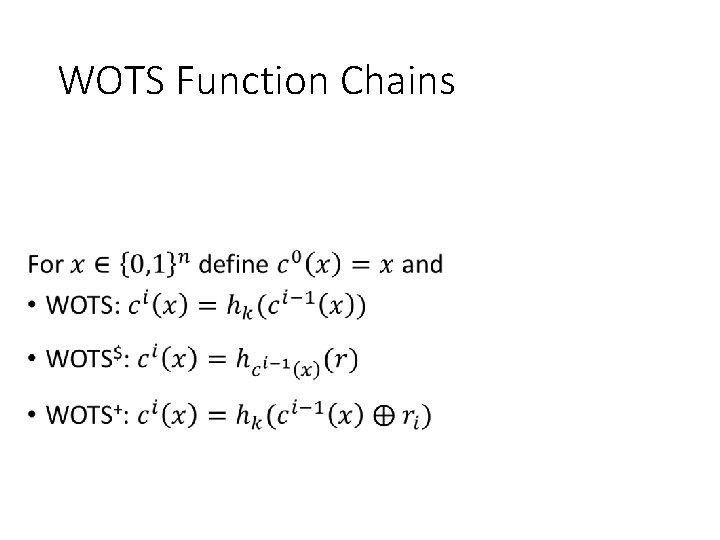
WOTS Function Chains •
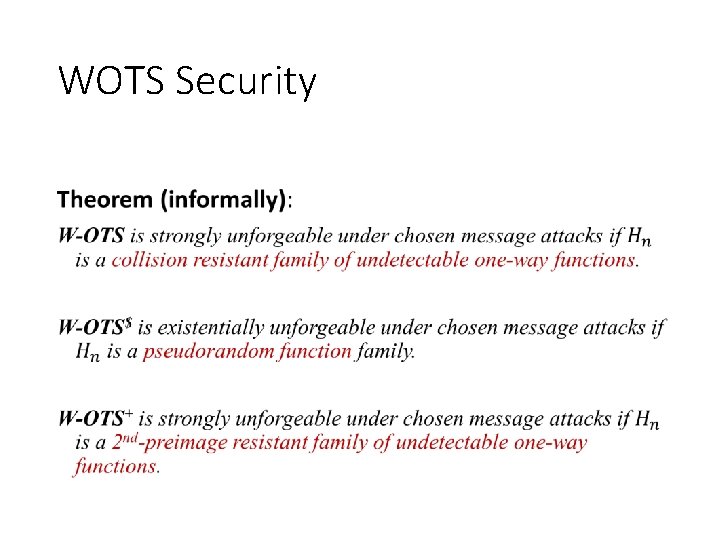
WOTS Security •

XMSS
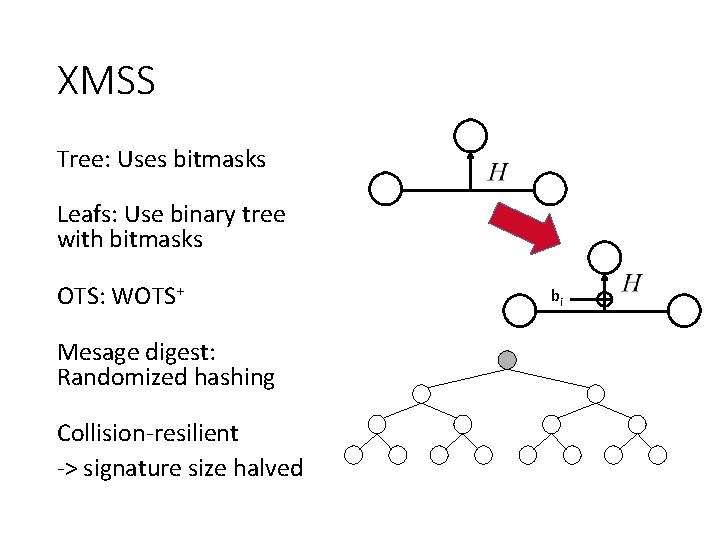
XMSS Tree: Uses bitmasks Leafs: Use binary tree with bitmasks OTS: WOTS+ Mesage digest: Randomized hashing Collision-resilient -> signature size halved bi
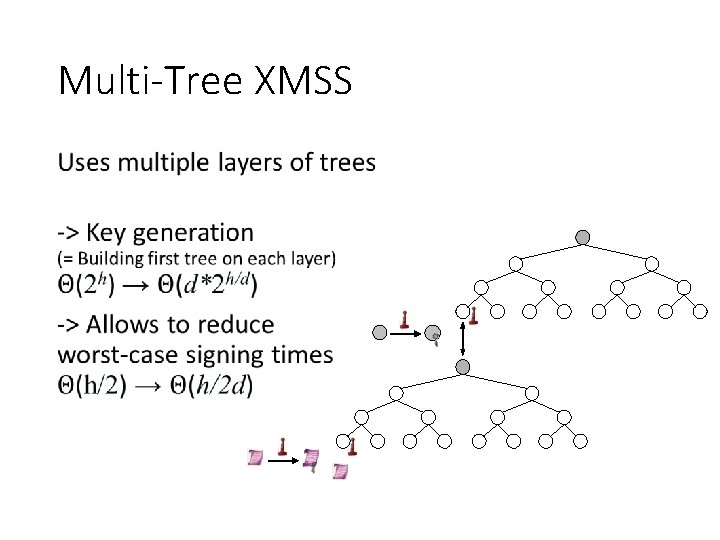
Multi-Tree XMSS •
Authentication path computation
Tree. Hash (Mer 89)
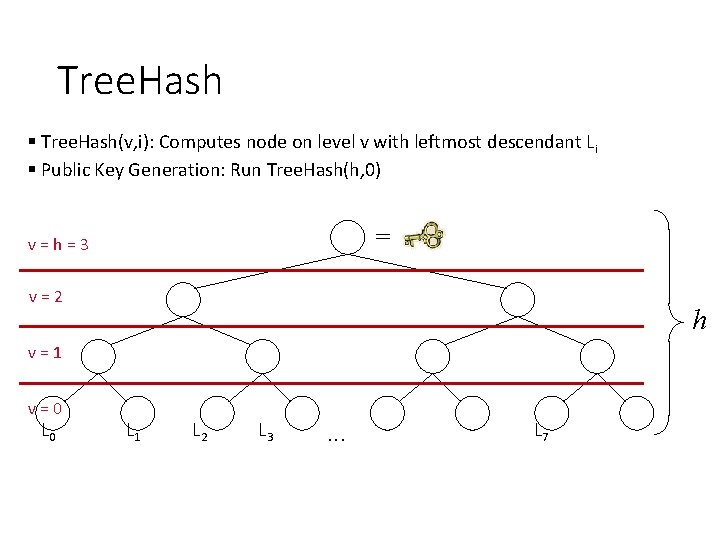
Tree. Hash § Tree. Hash(v, i): Computes node on level v with leftmost descendant Li § Public Key Generation: Run Tree. Hash(h, 0) = v=h=3 v=2 h v=1 v=0 L 1 L 2 L 3 . . . L 7
Tree. Hash(v, i) 1: Init Stack, N 1, N 2 2: For j = i to i+2 v-1 do 3: N 1 = Leaf. Calc(j) 4: While N 1. level() == Stack. top(). level() do 5: N 2 = Stack. pop() 6: N 1 = Compute. Parent( N 2, N 1 ) 7: Stack. push(N 1) 8: Return Stack. pop()
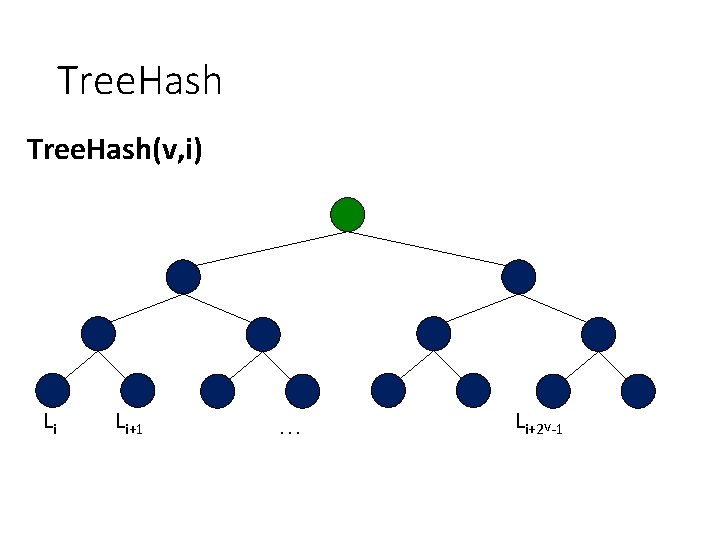
Tree. Hash(v, i) Li Li+1 . . . Li+2 v-1
Efficiency? Key generation: Every node has to be computed once. cost = 2 h leaves + 2 h-1 nodes => optimal Signature: One node on each level 0 <= v < h. cost 2 h-1 leaves + 2 h-1 -h nodes. Many nodes are computed many times! (e. g. those on level v=h-1 are computed 2 h-1 times) -> Not optimal if state allowed
![The BDS Algorithm [BDS 08] The BDS Algorithm [BDS 08]](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-52.jpg)
The BDS Algorithm [BDS 08]
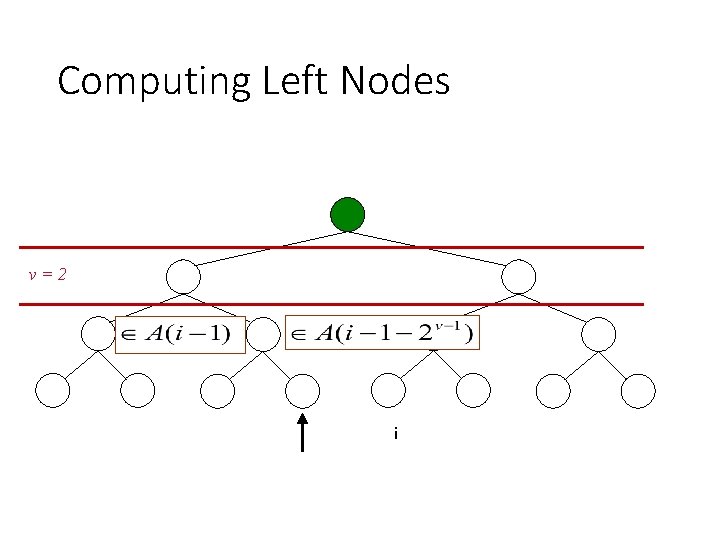
Motivation (for all Tree Traversal Algorithms) No Storage: Signature: Compute one node on each level 0 <= v < h. Costs: 2 h-1 leaf + 2 h-1 -h node computations. Example: XMSS with SHA 2 -256 and h = 20 -> approx. 15 min Store whole tree: 2 hn bits. Example: h=20, n=256; storage: 228 bits = 32 MB Idea: Look for time-memory trade-off!
Use a State
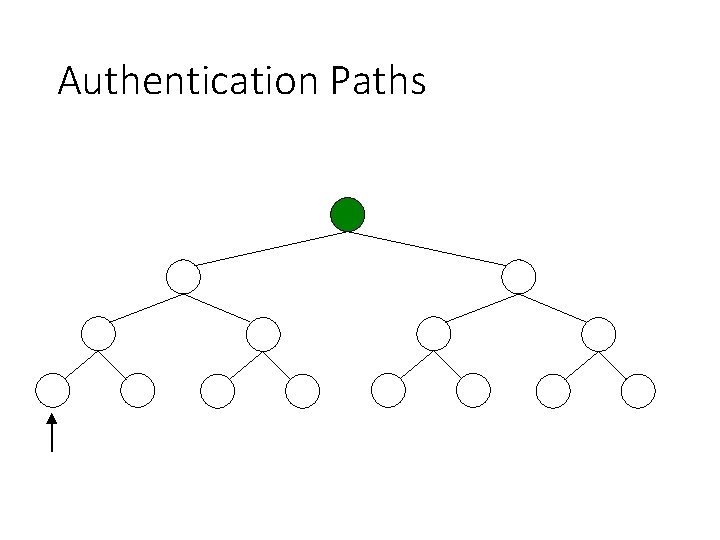
Authentication Paths
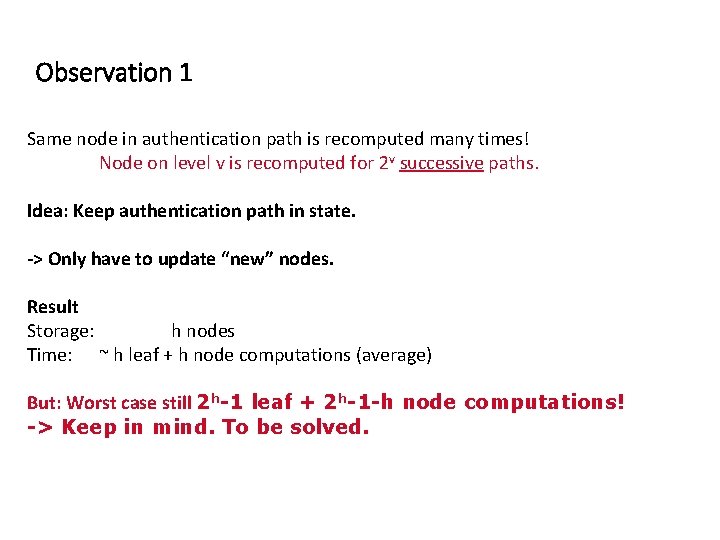
Observation 1 Same node in authentication path is recomputed many times! Node on level v is recomputed for 2 v successive paths. Idea: Keep authentication path in state. -> Only have to update “new” nodes. Result Storage: h nodes Time: ~ h leaf + h node computations (average) But: Worst case still 2 h-1 leaf + 2 h-1 -h node computations! -> Keep in mind. To be solved.
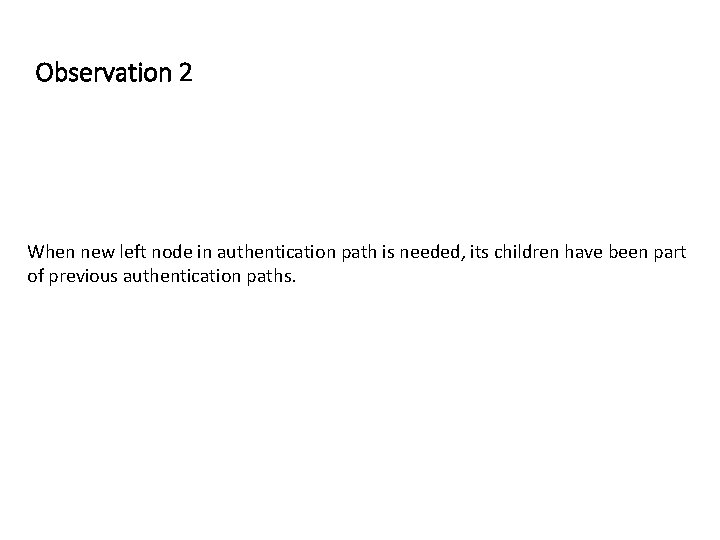
Observation 2 When new left node in authentication path is needed, its children have been part of previous authentication paths.
Computing Left Nodes v=2 i
Result Storing nodes all left nodes can be computed with one node computation / node
Observation 3 Right child nodes on high levels are most costly. Computing node on level v requires 2 v leaf and 2 v-1 node computations. Idea: Store right nodes on top k levels during key generation. Result Storage: 2 k-2 n bit nodes Time: ~ h-k leaf + h-k node computations (average) Still: Worst case 2 h-k-1 leaf + 2 h-k-1 -(h-k) node computations!
Distribute Computation
Intuition Observation: § For every second signature only one leaf computation § Average runtime: ~ h-k leaf + h-k node computations Idea: Distribute computation to achieve average runtime in worst case. Focus on distributing computation of leaves
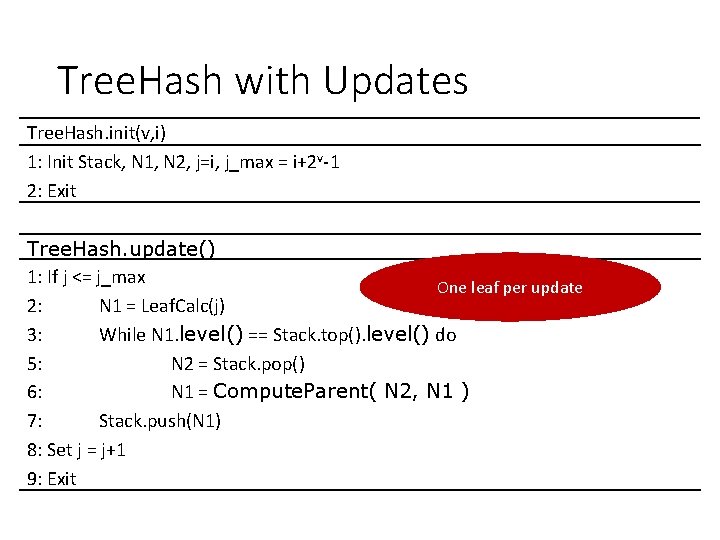
Tree. Hash with Updates Tree. Hash. init(v, i) 1: Init Stack, N 1, N 2, j=i, j_max = i+2 v-1 2: Exit Tree. Hash. update() 1: If j <= j_max One leaf per update 2: N 1 = Leaf. Calc(j) 3: While N 1. level() == Stack. top(). level() do 5: N 2 = Stack. pop() 6: N 1 = Compute. Parent( N 2, N 1 ) 7: Stack. push(N 1) 8: Set j = j+1 9: Exit
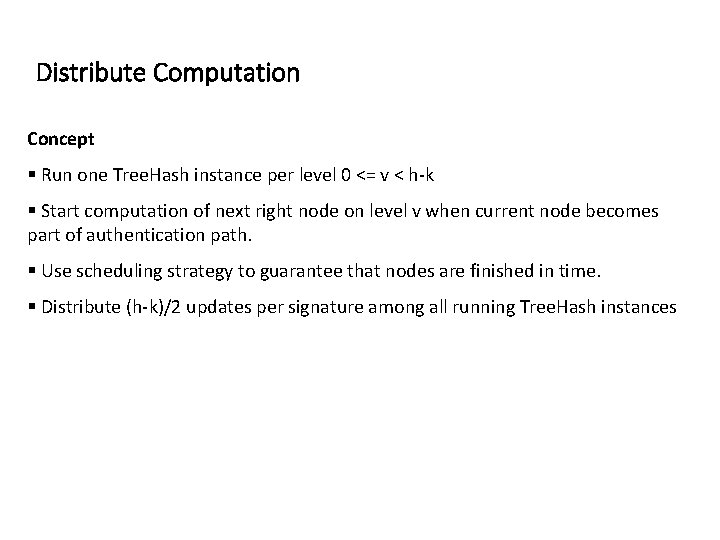
Distribute Computation Concept § Run one Tree. Hash instance per level 0 <= v < h-k § Start computation of next right node on level v when current node becomes part of authentication path. § Use scheduling strategy to guarantee that nodes are finished in time. § Distribute (h-k)/2 updates per signature among all running Tree. Hash instances
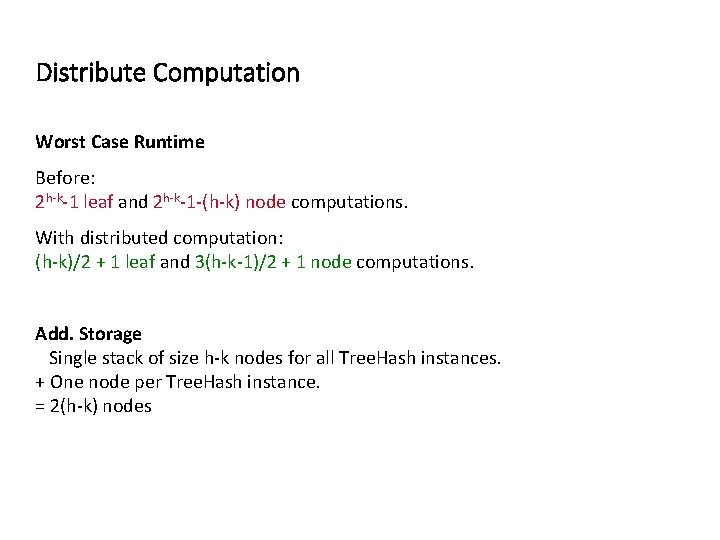
Distribute Computation Worst Case Runtime Before: 2 h-k-1 leaf and 2 h-k-1 -(h-k) node computations. With distributed computation: (h-k)/2 + 1 leaf and 3(h-k-1)/2 + 1 node computations. Add. Storage Single stack of size h-k nodes for all Tree. Hash instances. + One node per Tree. Hash instance. = 2(h-k) nodes
BDS Performance Storage: n bit nodes Runtime: (h−k)/2+1 leaf and 3(h−k− 1)/2+1 node computations.
XMSS in practice
XMSS Internet-Draft (draft-irtf-cfrg-xmss-hash-based-signatures) • Protecting against multi-target attacks / tight security • n-bit hash => n bit security • Small public key (2 n bit) • At the cost of ROM for proving PK compression secure • Function families based on SHA 2 • Equal to XMSS-T [HRS 16] up-to message digest
![XMSS / XMSS-T Implementation C Implementation, using Open. SSL [HRS 16] Sign (ms) Signature XMSS / XMSS-T Implementation C Implementation, using Open. SSL [HRS 16] Sign (ms) Signature](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-69.jpg)
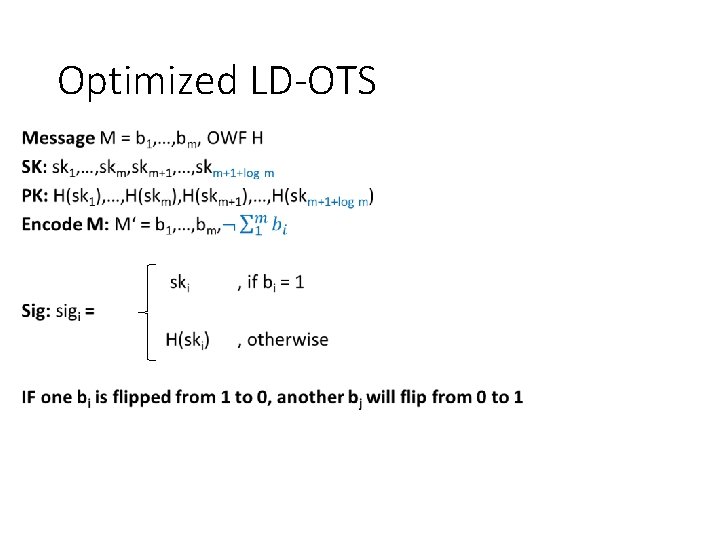
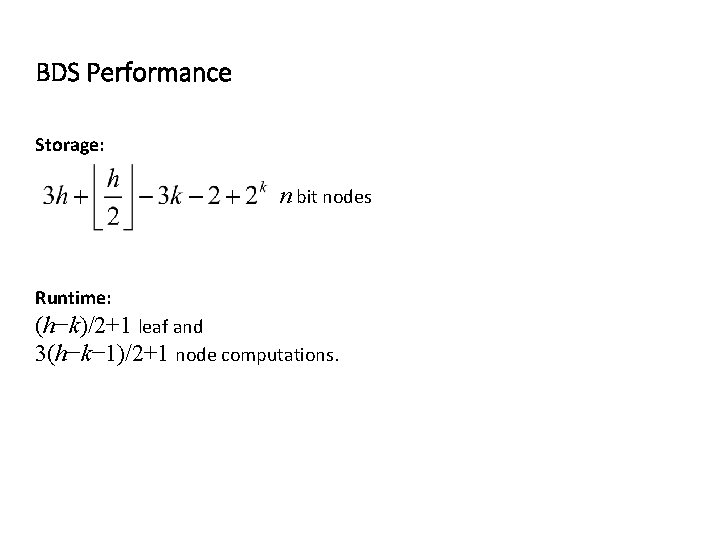
XMSS / XMSS-T Implementation C Implementation, using Open. SSL [HRS 16] Sign (ms) Signature (k. B) Public Key (k. B) Secret Key (k. B) Bit Security classical/ quantum Comment XMSS 3. 24 2. 8 1. 3 2. 2 236 / 118 h = 20, d = 1, XMSS-T 9. 48 2. 8 0. 064 2. 2 256 / 128 h = 20, d=1 XMSS 3. 59 8. 3 14. 6 196 / 98 h = 60, d=3 XMSS-T 10. 54 8. 3 0. 064 14. 6 256 / 128 h = 60, d=3 Intel(R) Core(TM) i 7 CPU @ 3. 50 GHz XMSS-T uses message digest from Internet-Draft All using SHA 2 -256, w = 16 and k = 2
Open research topics 1. Message compression which • • is collision-resilient, provdies tight provable security, especially resists multi-target attacks (=> no e. TCR) => Has applications outside hash-based crypto! 2. Quantum query complexity for further properties • E. g. PRF, UD, a. Sec, . . . 3. Quantum security of existing hash function constructions. • E. g. can classical attacks be improved (e. g. differential cryptanalysis)
SPHINCS
About the statefulness • Works great for some settings • However. . . . back-up. . . multi-threading. . . load-balancing

How to Eliminate the State

Few-Time Signature Schemes 5 -9 -2021 PAGE 77
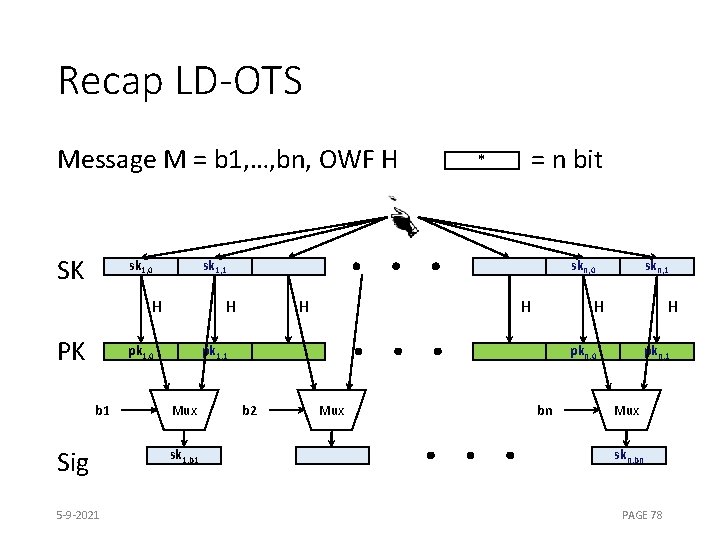
Recap LD-OTS Message M = b 1, …, bn, OWF H SK sk 1, 0 sk 1, 1 H PK Sig 5 -9 -2021 skn, 0 H pk 1, 0 b 1 = n bit * H H H pk 1, 1 Mux sk 1, b 1 skn, 1 H pkn, 0 b 2 Mux bn pkn, 1 Mux skn, bn PAGE 78
![HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters](http://slidetodoc.com/presentation_image_h2/8961d8b45dfcda9c8c0cb7ce8416cb8c/image-76.jpg)
HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) SK sk 1 sk 2 H PK 5 -9 -2021 pk 1 skt-1 H pk 1 H H skt H pkt-1 H pkt PAGE 79
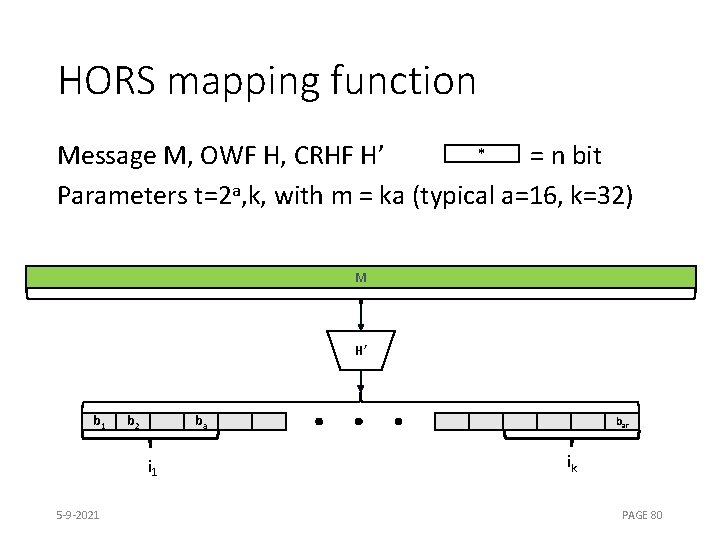
HORS mapping function * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) M H’ b 1 b 2 ba i 1 5 -9 -2021 bar ik PAGE 80
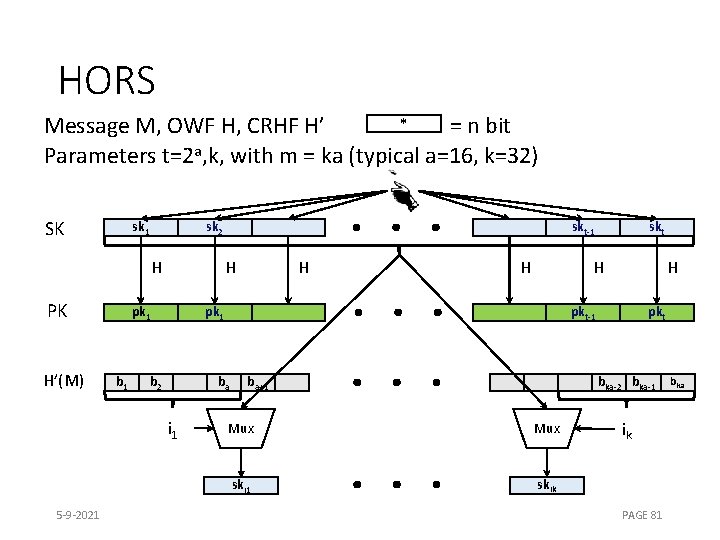
HORS * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) SK sk 1 sk 2 H PK H’(M) H pk 1 b 1 H H b 2 skt H pk 1 H pkt-1 ba i 1 5 -9 -2021 skt-1 ba+1 pkt bka-2 bka-1 Mux ski 1 skik ik PAGE 81 bka
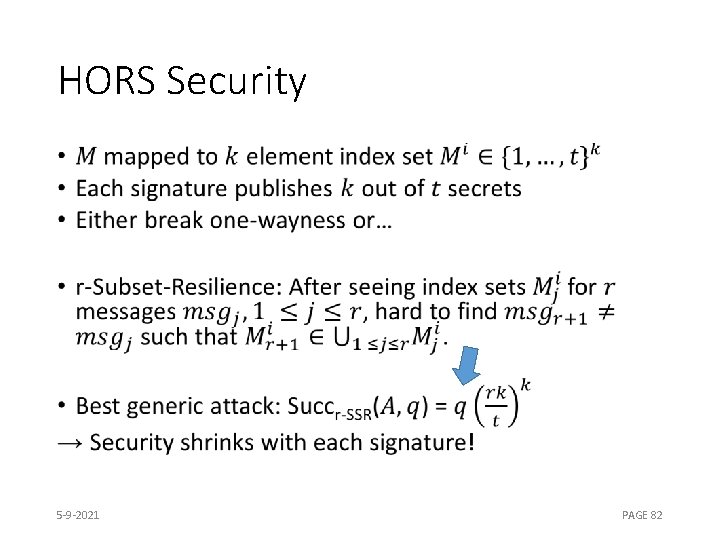
HORS Security • 5 -9 -2021 PAGE 82
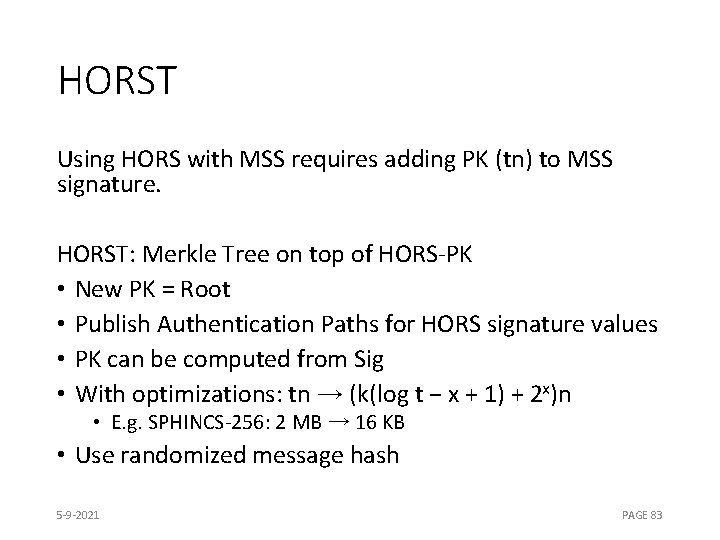
HORST Using HORS with MSS requires adding PK (tn) to MSS signature. HORST: Merkle Tree on top of HORS-PK • New PK = Root • Publish Authentication Paths for HORS signature values • PK can be computed from Sig • With optimizations: tn → (k(log t − x + 1) + 2 x)n • E. g. SPHINCS-256: 2 MB → 16 KB • Use randomized message hash 5 -9 -2021 PAGE 83
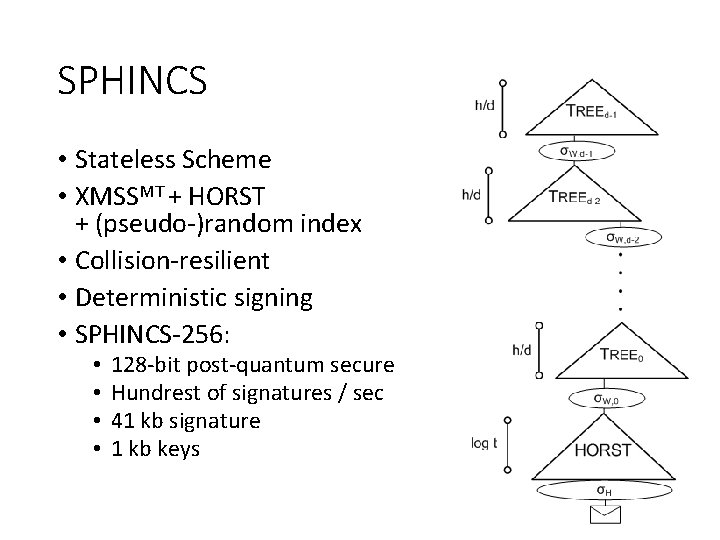
SPHINCS • Stateless Scheme • XMSSMT + HORST + (pseudo-)random index • Collision-resilient • Deterministic signing • SPHINCS-256: • • 128 -bit post-quantum secure Hundrest of signatures / sec 41 kb signature 1 kb keys
Open research topics II • More efficient few-time signatures • Different constructions? • . . . ?
Thank you! Questions? For references & further literature see https: //huelsing. wordpress. com/hash-based-signature-schemes/literature/ 5 -9 -2021 PAGE 86
- Slides: 83