PostQuantum Cryptography Privacy Andreas Hlsing Privacy Too abstract
Post-Quantum Cryptography & Privacy Andreas Hülsing
Privacy?

Too abstract?
How to achieve privacy?
Under the hood. . . Public-key crypto • ECC • RSA • DSA Secret-key crypto • AES • SHA 2 • SHA 1 • . . . Combination of both needed!
Secret-key cryptography
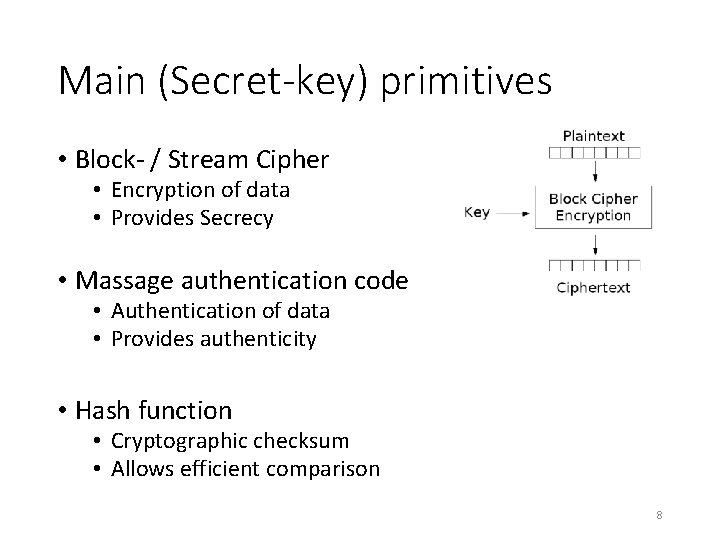
Main (Secret-key) primitives • Block- / Stream Cipher • Encryption of data • Provides Secrecy • Massage authentication code • Authentication of data • Provides authenticity • Hash function • Cryptographic checksum • Allows efficient comparison 8
Public-key cryptography
Main (public-key) primitives • Digital signature • Proof of authorship • Provides: • Authentication • Non-repudiation • Public-key encryption / key exchange • Establishment of commonly known secret key • Provides secrecy 10
Applications • Code signing (Signatures) • Software updates • Software distribution • Mobile code • Communication security (Signatures, PKE / KEX) • TLS, SSH, IPSec, . . . • e. Commerce, online banking, e. Government, . . . • Private online communication 11
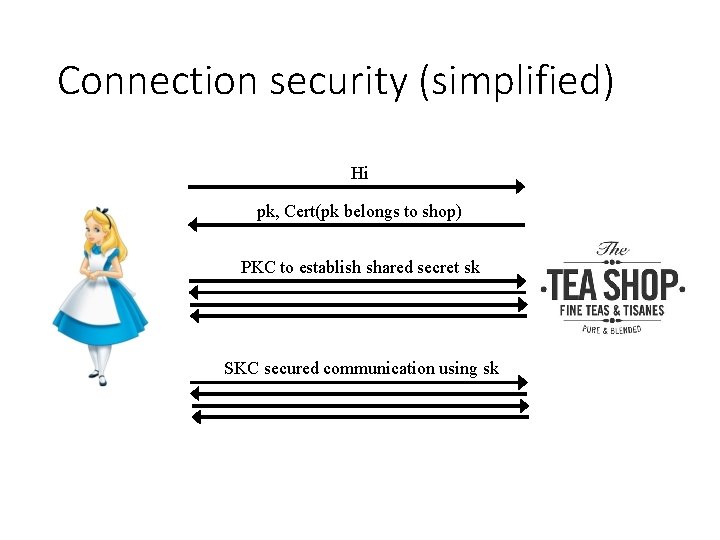
Connection security (simplified) Hi pk, Cert(pk belongs to shop) PKC to establish shared secret sk SKC secured communication using sk
We need secret- and public-key crypto to achieve privacy!
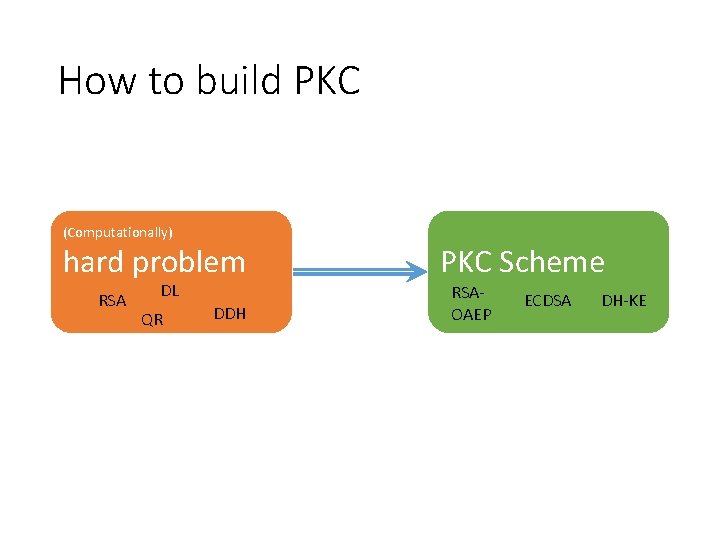
How to build PKC (Computationally) hard problem RSA DL QR DDH PKC Scheme RSAOAEP ECDSA DH-KE
Quantum Computing
Quantum Computing “Quantum computing studies theoretical computation systems (quantum computers) that make direct use of quantum-mechanical phenomena, such as superposition and entanglement, to perform operations on data. ” -- Wikipedia
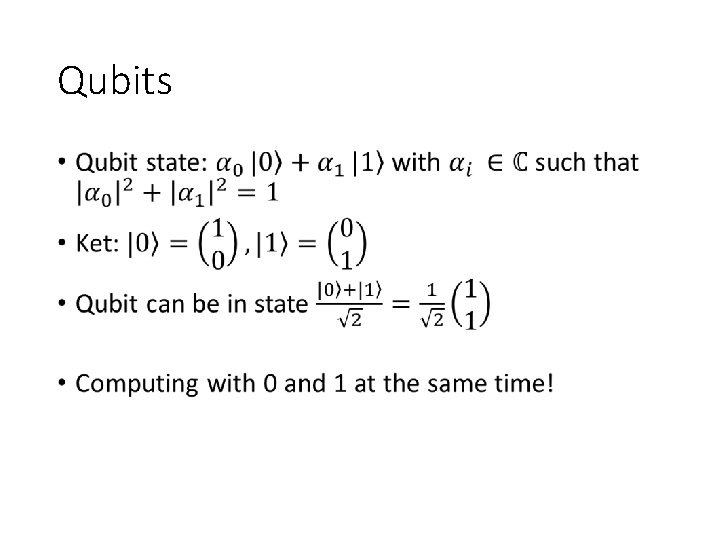
Qubits •
Quantum computers are not almighty • To learn outcome one has to measure. • Collapses state • 1 qubit leads 1 classical bit of information • Randomized process • Only invertible computation. • Impossible to clone (copy) quantum state.
The Quantum Threat
Shor‘s algorithm (1994) • Quantum computers can do FFT very efficiently • Can be used to find period of a function • This can be exploited to factor efficiently (RSA) • Shor also shows how to solve discrete log efficiently (DSA, DH, ECDSA, ECDH)
Grover‘s algorithm (1996) •
To sum up • All asymmetric crypto is broken by QC • No more digital signatures • No more public key encryption • No more key exchange • No secure shopping for tea. . .
Quantum Cryptography
Why not beat ‘em with their own weapons? • QKD: Quantum Key distribution. • Based on some nice quantum properties: entanglement & collapsing measurments • Information theoretic security (at least in theory) -> Great! • For sale today! • So why don‘t we use this? • Only short distance, point-to-point connections! • Internet? No way! • Longer distances require „trusted-repeaters“ • We all know where this leads. . .
PQCRYPTO to the rescue
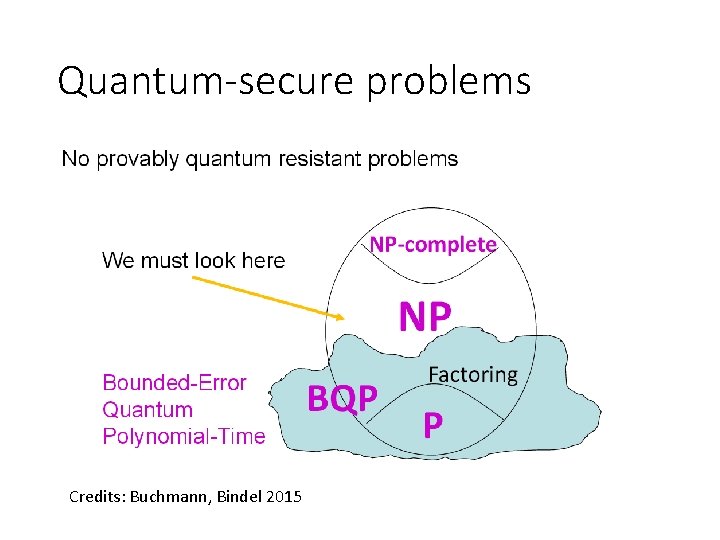
Quantum-secure problems Credits: Buchmann, Bindel 2015
Conjectured quantum-secure problems • Solving multivariate quadratic equations (MQproblem) -> Multivariate Crypto • Bounded-distance decoding (BDD) -> Code-based crypto • Short(est) and close(st) vector problem (SVP, CVP) -> Lattice-based crypto • Breaking security of symmetric primitives (SHAx-, AES-, Keccak-, . . . problem) -> Hash-based signatures / symmetric crypto
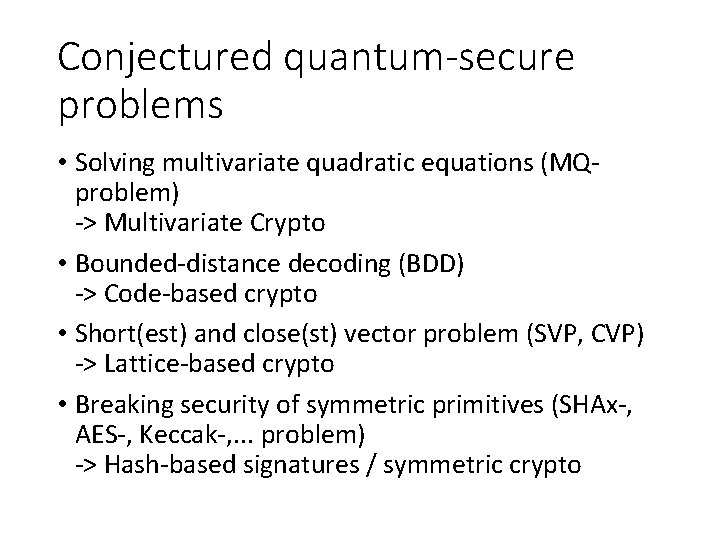
MQ-Problem
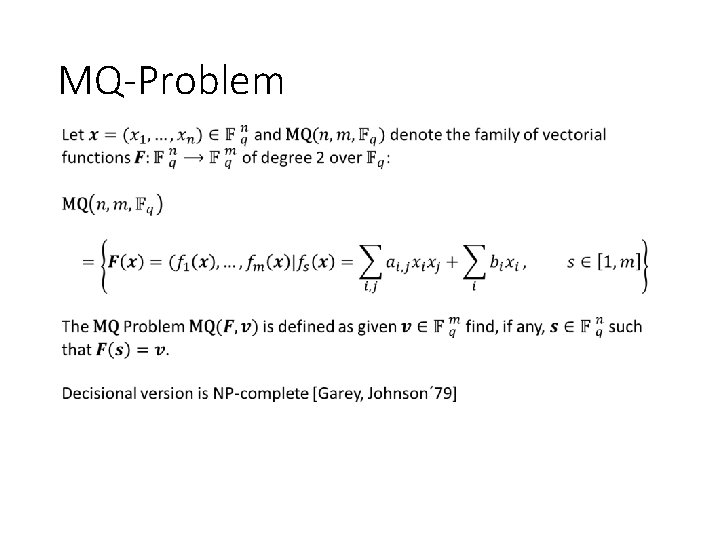
Multivariate Signatures (trad. approach) Credits: Buchmann, Bindel 2015
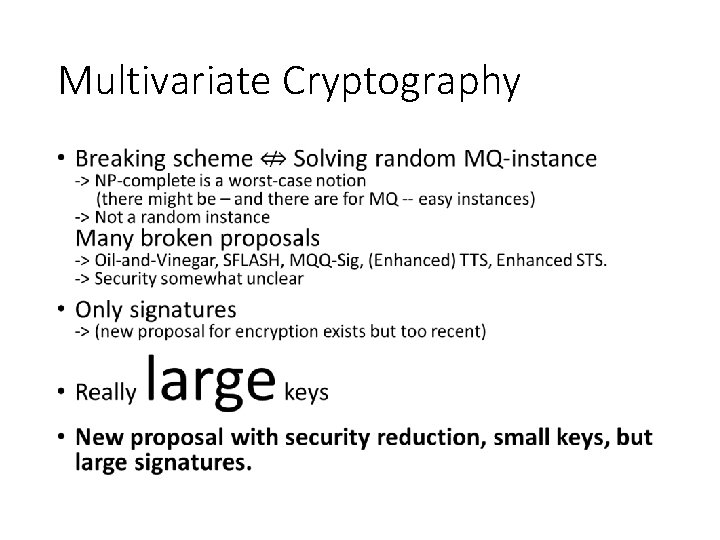
Multivariate Cryptography •
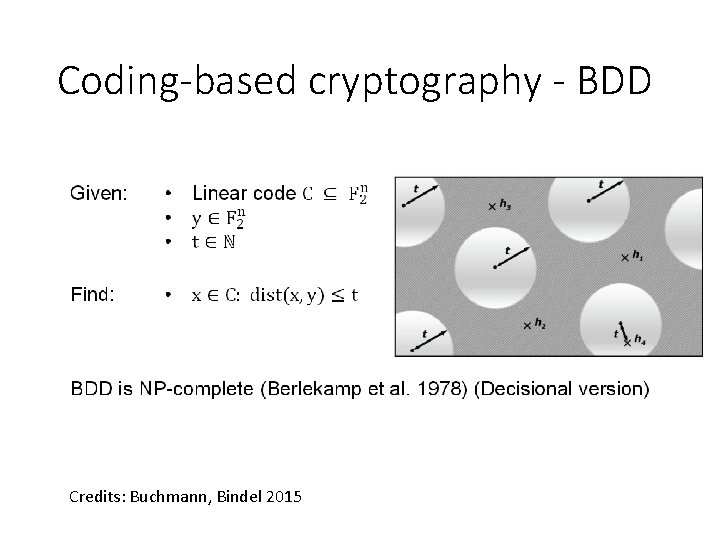
Coding-based cryptography - BDD Credits: Buchmann, Bindel 2015
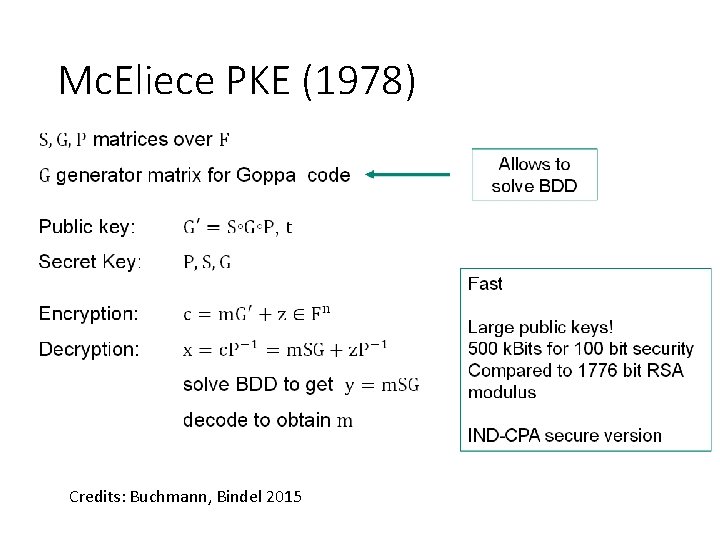
Mc. Eliece PKE (1978) Credits: Buchmann, Bindel 2015
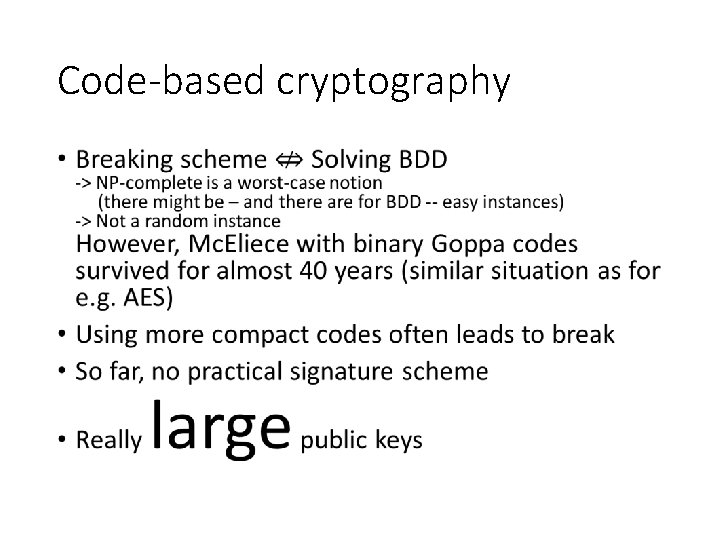
Code-based cryptography •
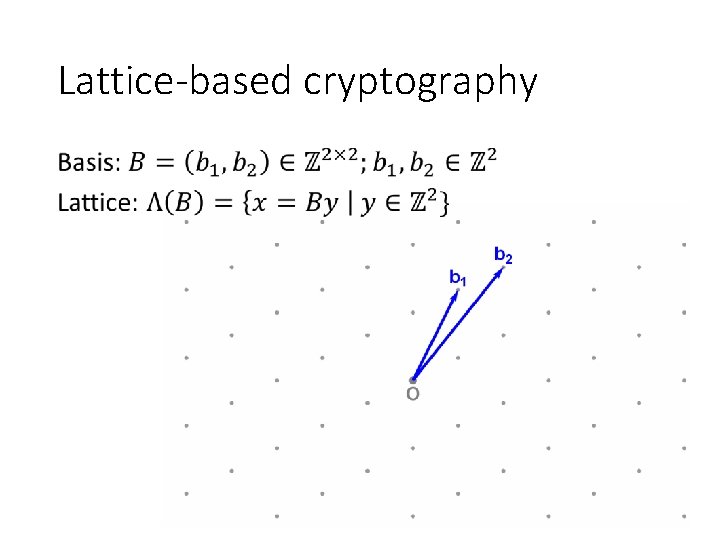
Lattice-based cryptography •
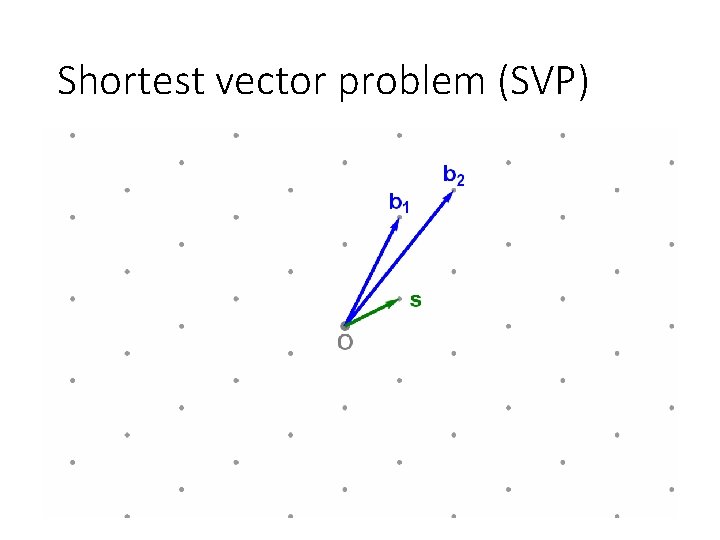
Shortest vector problem (SVP)
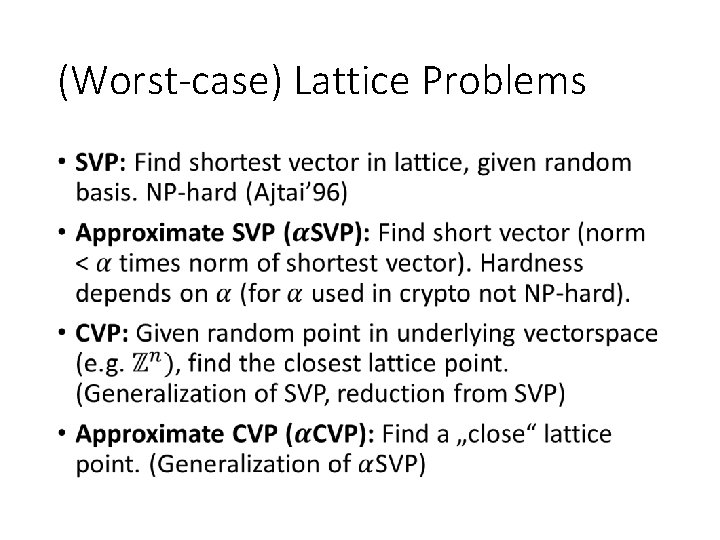
(Worst-case) Lattice Problems •
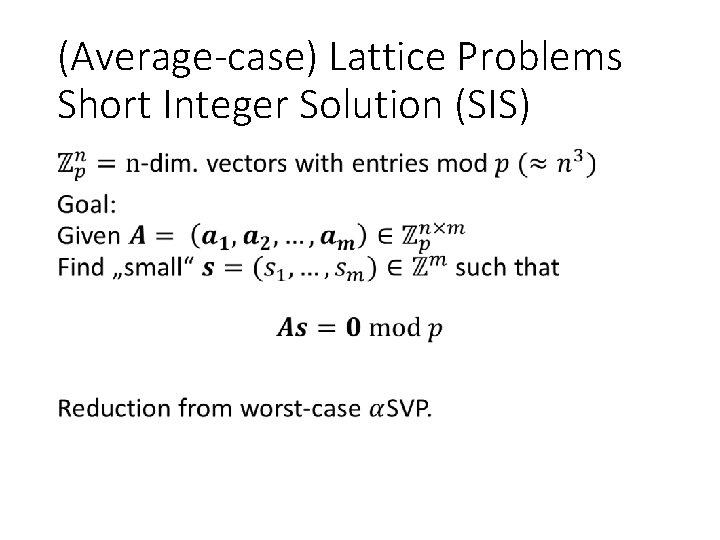
(Average-case) Lattice Problems Short Integer Solution (SIS) •
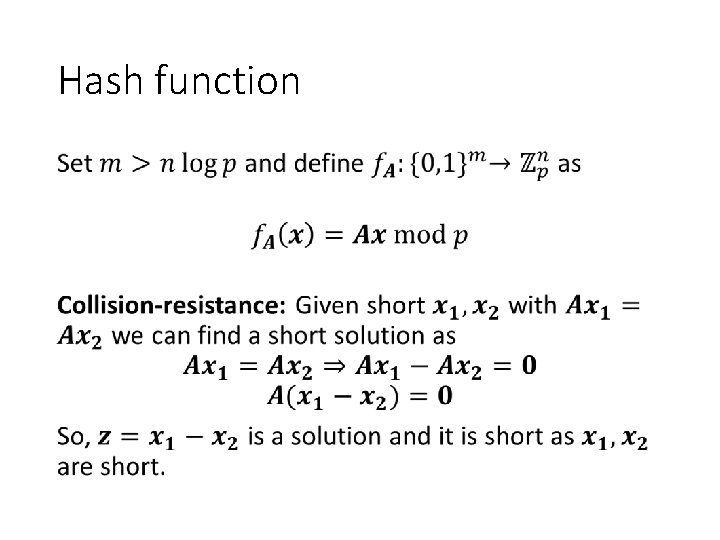
Hash function •
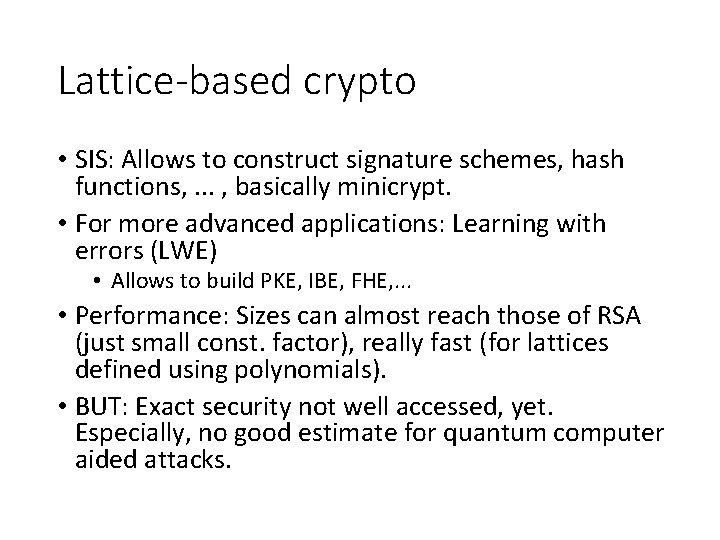
Lattice-based crypto • SIS: Allows to construct signature schemes, hash functions, . . . , basically minicrypt. • For more advanced applications: Learning with errors (LWE) • Allows to build PKE, IBE, FHE, . . . • Performance: Sizes can almost reach those of RSA (just small const. factor), really fast (for lattices defined using polynomials). • BUT: Exact security not well accessed, yet. Especially, no good estimate for quantum computer aided attacks.
![Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood](http://slidetodoc.com/presentation_image_h2/deeff6d6170e697c7c37545cb9125e6b/image-40.jpg)
Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Fast 22 -10 -2021 PAGE 51
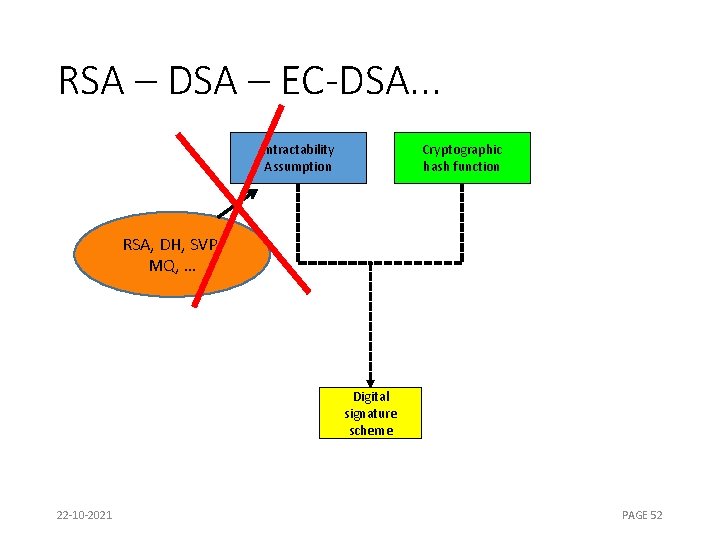
RSA – DSA – EC-DSA. . . Intractability Assumption Cryptographic hash function RSA, DH, SVP, MQ, … Digital signature scheme 22 -10 -2021 PAGE 52
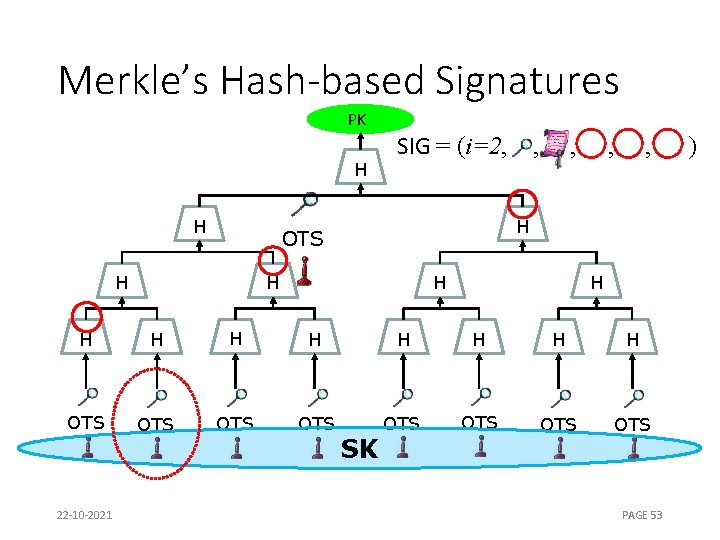
Merkle’s Hash-based Signatures PK H H SIG = (i=2, , H OTS H , H H H OTS OTS 22 -10 -2021 SK PAGE 53 )
Hash-based signatures • Only signatures • Minimal security assumptions • Well understood • Fast & compact (2 k. B, few ms), but stateful, or • Stateless, bigger and slower (41 k. B, several ms). • Two Internet drafts (drafts for RFCs), one in „RFC Editor queue“
NIST Competition 10/22/2021 Andreas Hülsing https: //huelsing. net 55
Resources • PQ Summer School: https: //2017. pqcrypto. org/school/index. html • NIST PQC Standardization Project: https: //csrc. nist. gov/Projects/Post-Quantum. Cryptography • Master Math (Selected Areas in Cryptology): https: //elo. mastermath. nl/
Thank you! Questions? 22 -10 -2021 PAGE 57
- Slides: 46