Hashbased signatures Hashandsign without collisionresistance Andreas Hlsing 22
Hash-based signatures & Hash-and-sign without collision-resistance Andreas Hülsing 22. 12. 2016
![Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood](http://slidetodoc.com/presentation_image_h2/69ac7151e137cb350db6d56411991ac3/image-2.jpg)
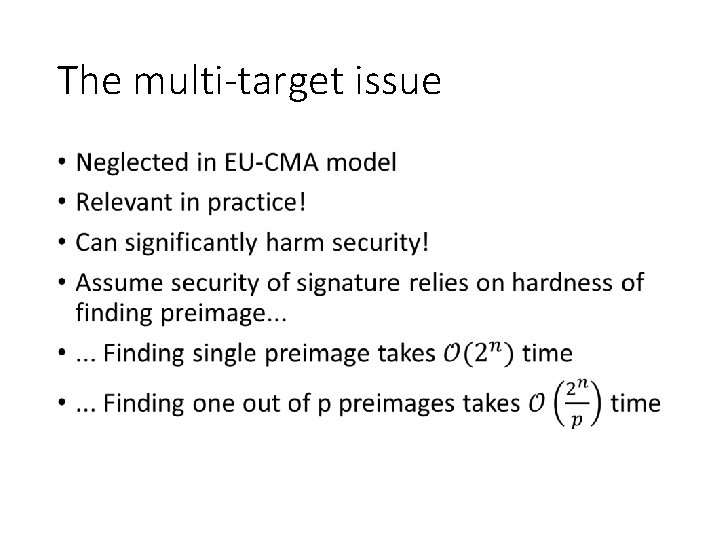
Hash-based Signature Schemes [Mer 89] Post quantum Only secure hash function Security well understood Fast 12 -6 -2021 PAGE 2
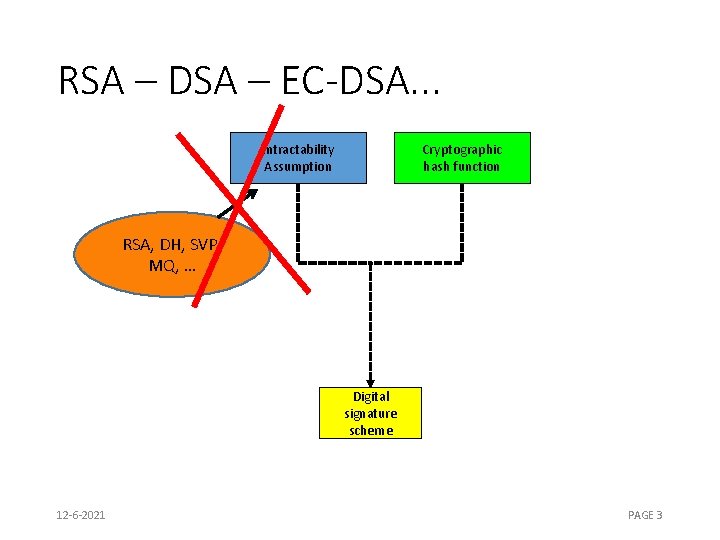
RSA – DSA – EC-DSA. . . Intractability Assumption Cryptographic hash function RSA, DH, SVP, MQ, … Digital signature scheme 12 -6 -2021 PAGE 3
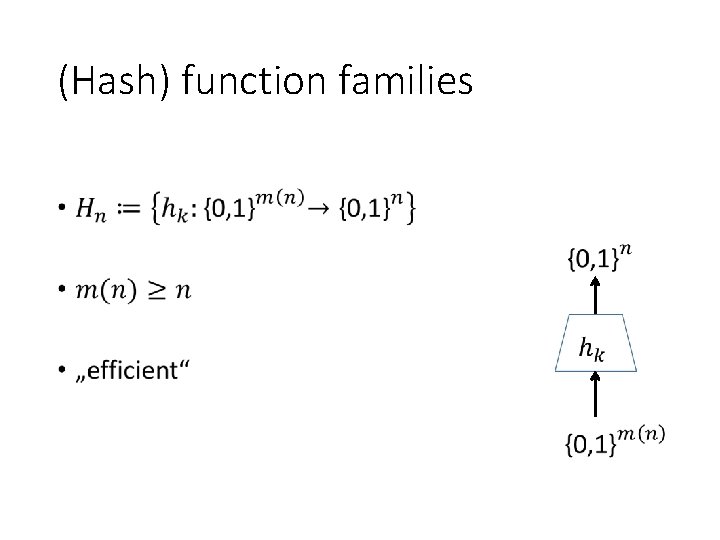
(Hash) function families •
One-wayness •
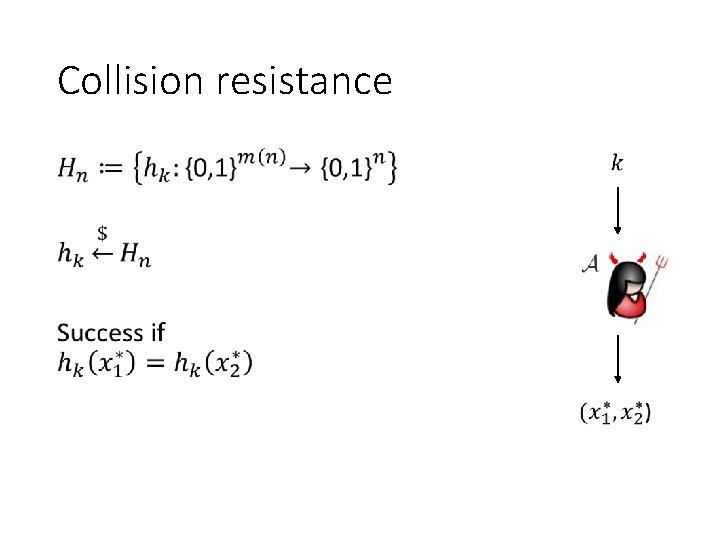
Collision resistance
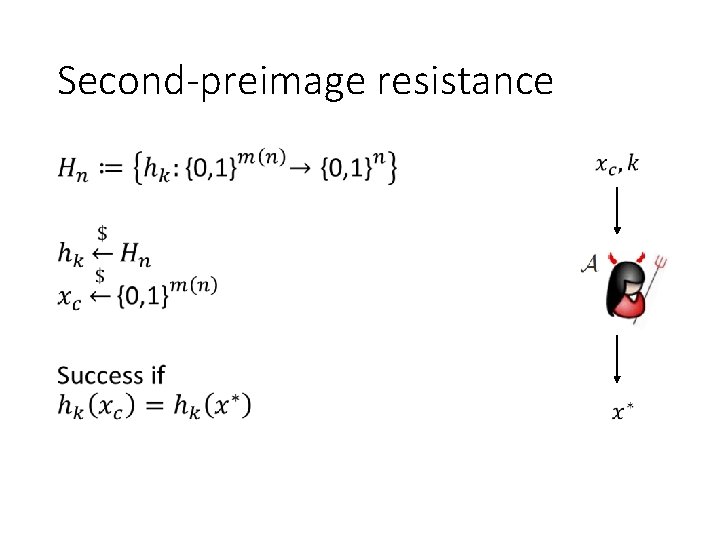
Second-preimage resistance •
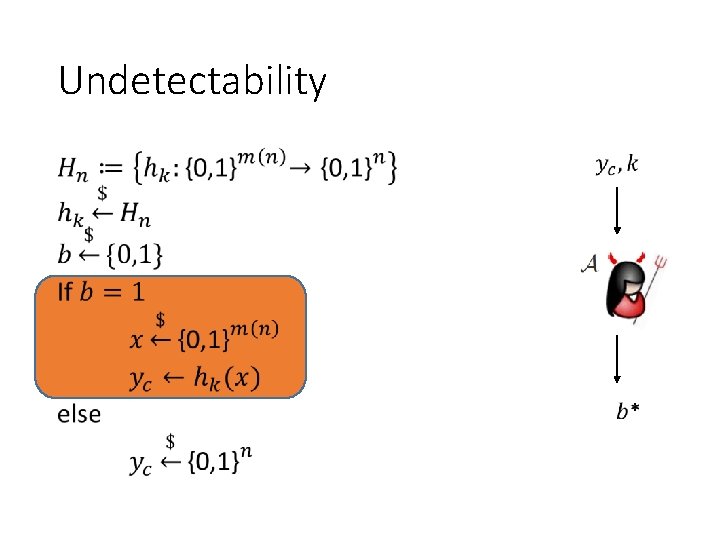
Undetectability •
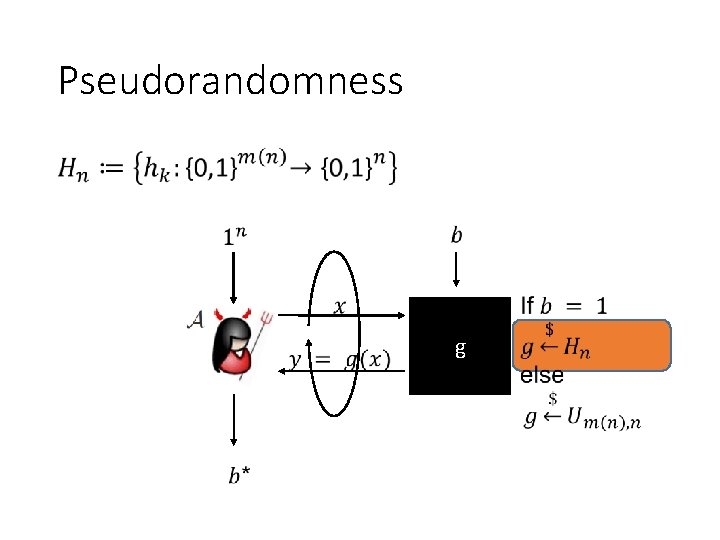
Pseudorandomness • g
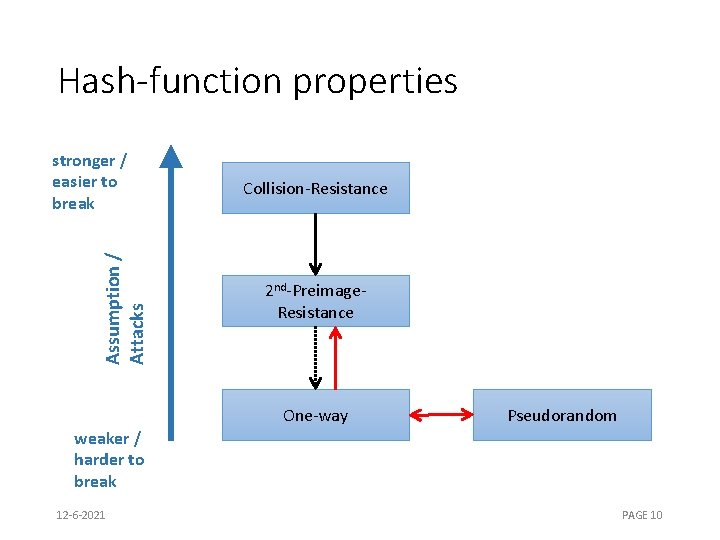
Hash-function properties Assumption / Attacks stronger / easier to break Collision-Resistance 2 nd-Preimage. Resistance One-way Pseudorandom weaker / harder to break 12 -6 -2021 PAGE 10
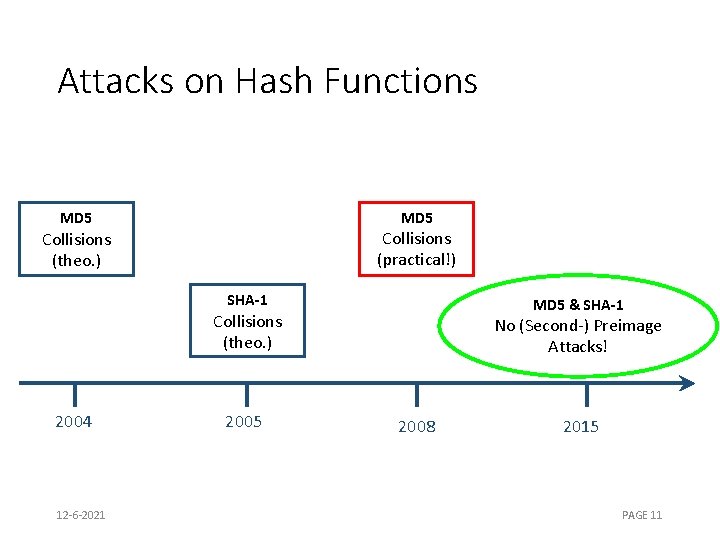
Attacks on Hash Functions MD 5 Collisions (practical!) Collisions (theo. ) SHA-1 MD 5 & SHA-1 Collisions (theo. ) 2004 12 -6 -2021 2005 No (Second-) Preimage Attacks! 2008 2015 PAGE 11
Basic Construction 12 -6 -2021 PAGE 12
![Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK](http://slidetodoc.com/presentation_image_h2/69ac7151e137cb350db6d56411991ac3/image-13.jpg)
Lamport-Diffie OTS [Lam 79] Message M = b 1, …, bm, OWF H SK sk 1, 0 sk 1, 1 H PK Sig 12 -6 -2021 skm, 0 H pk 1, 0 b 1 = n bit * H H pk 1, 1 Mux sk 1, b 1 skm, 1 H H pkm, 0 b 2 Mux bm pkm, 1 Mux skm, bm PAGE 13
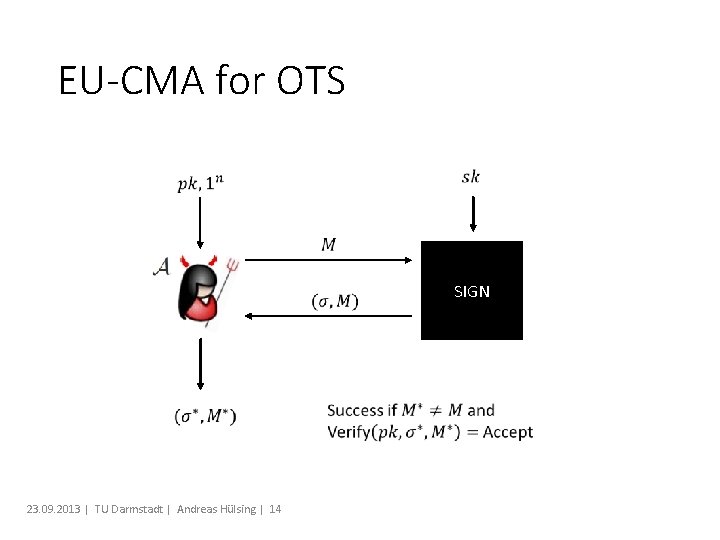
EU-CMA for OTS SIGN 23. 09. 2013 | TU Darmstadt | Andreas Hülsing | 14
Security Theorem: If H is one-way then LD-OTS is one-time eu-cmasecure.
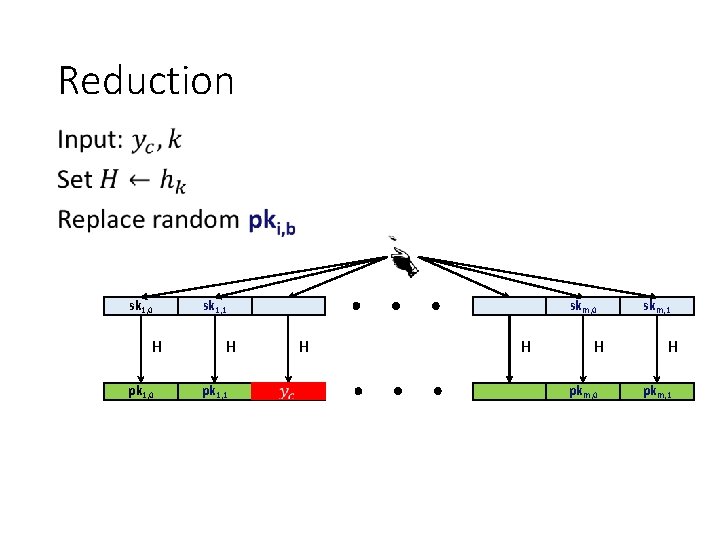
Reduction • sk 1, 0 H pk 1, 0 sk 1, 1 H pk 1, 1 skm, 0 H H H pkm, 0 skm, 1 H pkm, 1
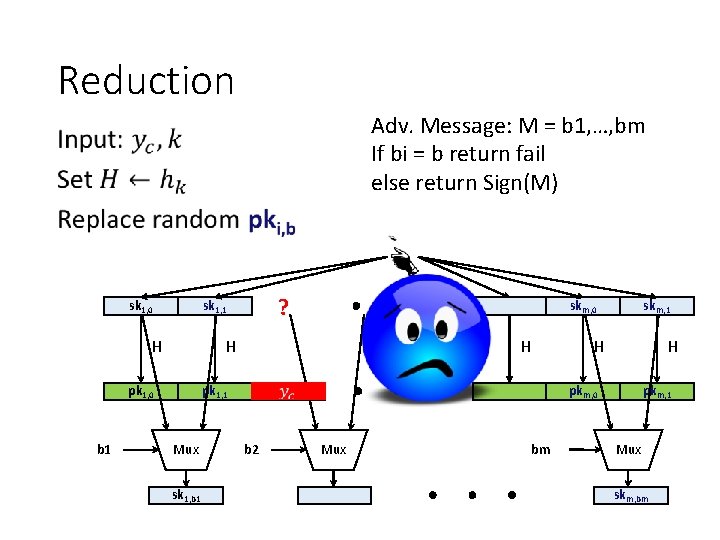
Reduction Adv. Message: M = b 1, …, bm If bi = b return fail else return Sign(M) • sk 1, 0 H skm, 0 H pk 1, 0 b 1 ? sk 1, 1 H H pk 1, 1 Mux sk 1, b 1 skm, 1 H pkm, 0 b 2 Mux bm pkm, 1 Mux skm, bm
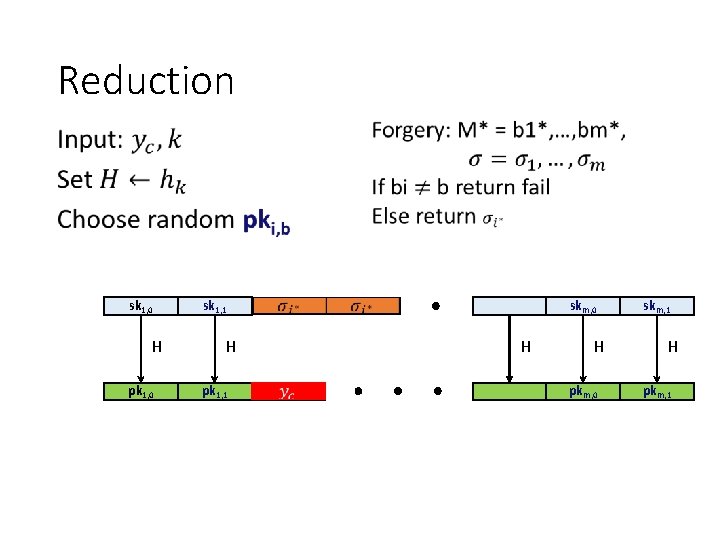
Reduction • sk 1, 0 H pk 1, 0 sk 1, 1 H pk 1, 1 ? skm, 0 H H pkm, 0 skm, 1 H pkm, 1
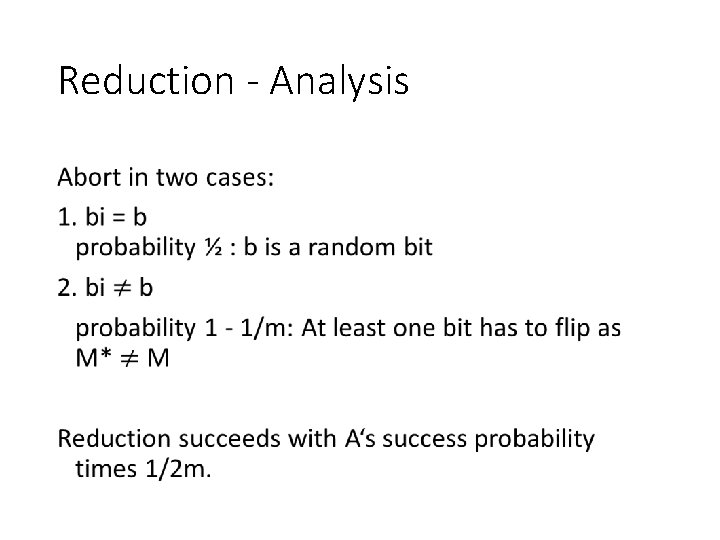
Reduction - Analysis •
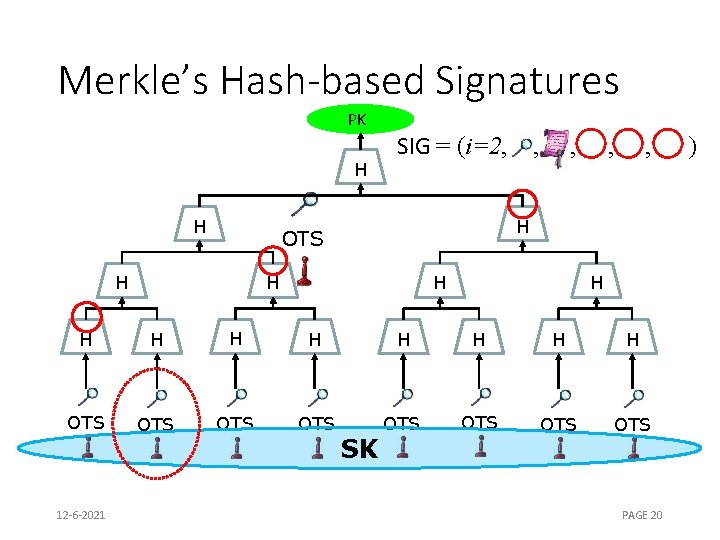
Merkle’s Hash-based Signatures PK H H SIG = (i=2, , H OTS H , H H H OTS OTS 12 -6 -2021 SK PAGE 20 )
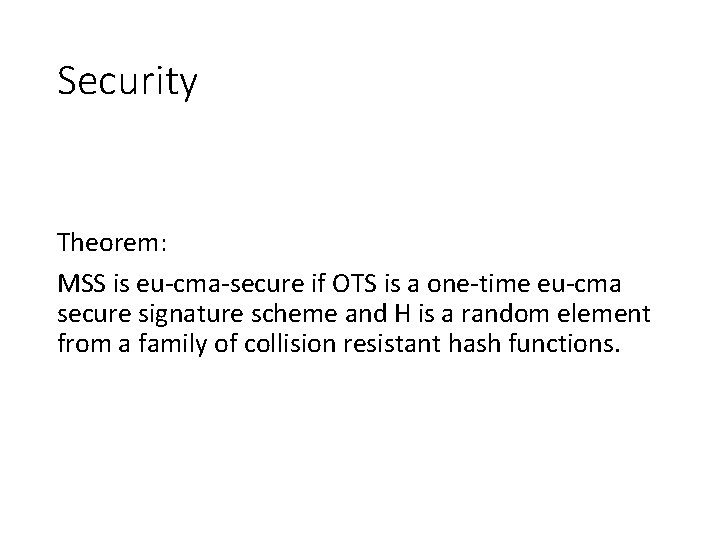
Security Theorem: MSS is eu-cma-secure if OTS is a one-time eu-cma secure signature scheme and H is a random element from a family of collision resistant hash functions.
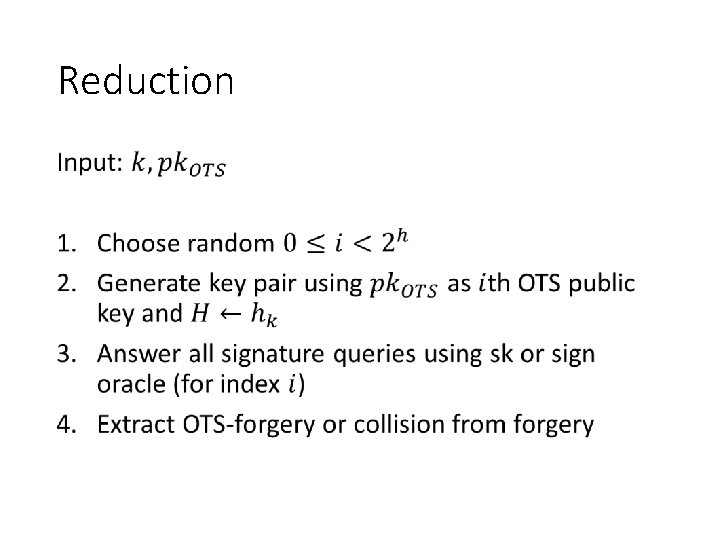
Reduction •
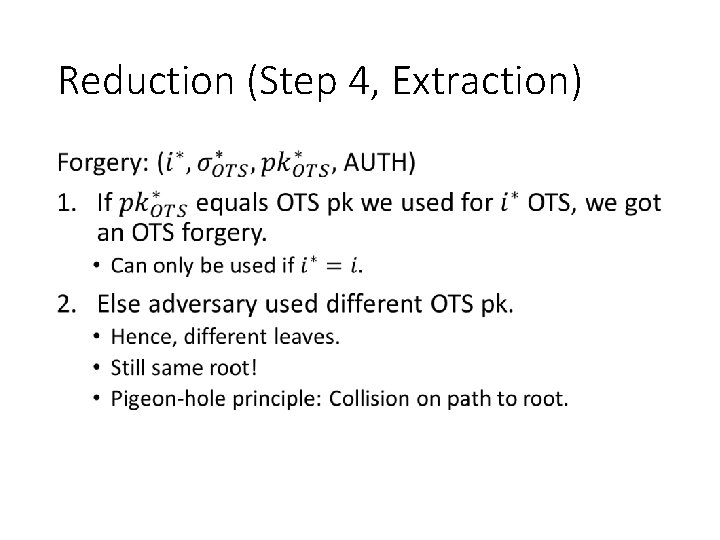
Reduction (Step 4, Extraction) •

Winternitz-OTS
![Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK](http://slidetodoc.com/presentation_image_h2/69ac7151e137cb350db6d56411991ac3/image-25.jpg)
Recap LD-OTS [Lam 79] Message M = b 1, …, bm, OWF H SK sk 1, 0 Sig skm, 0 H pk 1, 0 b 1 = n bit sk 1, 1 H PK * H H H pk 1, 1 Mux sk 1, b 1 skm, 1 H pkm, 0 b 2 Mux bn pkm, 1 Mux skm, bm
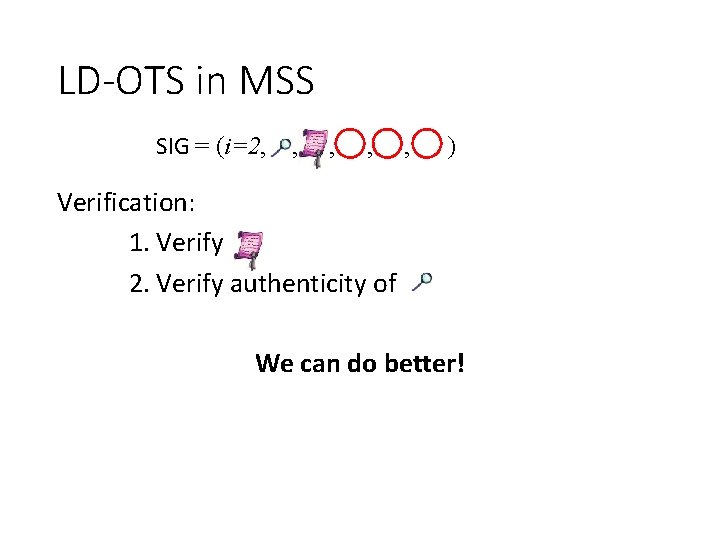
LD-OTS in MSS SIG = (i=2, , , ) Verification: 1. Verify 2. Verify authenticity of We can do better!
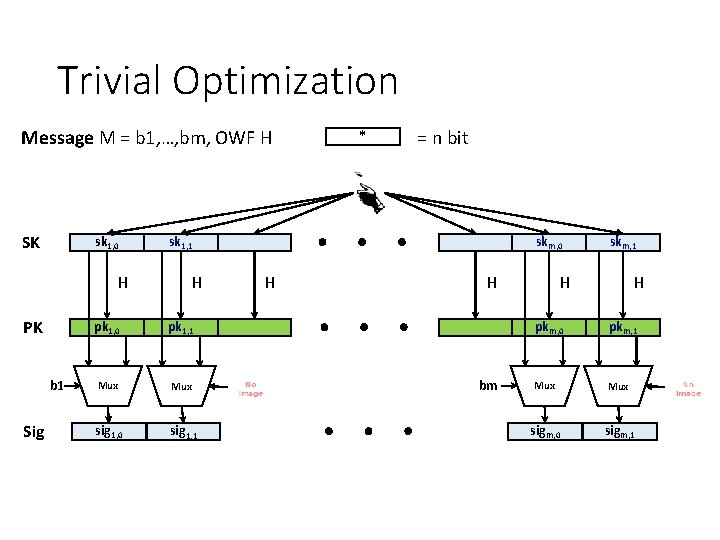
Trivial Optimization Message M = b 1, …, bm, OWF H SK sk 1, 0 H PK b 1 Sig * = n bit sk 1, 1 H pk 1, 0 pk 1, 1 Mux sig 1, 0 sig 1, 1 skm, 0 H H bm skm, 1 H H pkm, 0 pkm, 1 Mux sigm, 0 sigm, 1
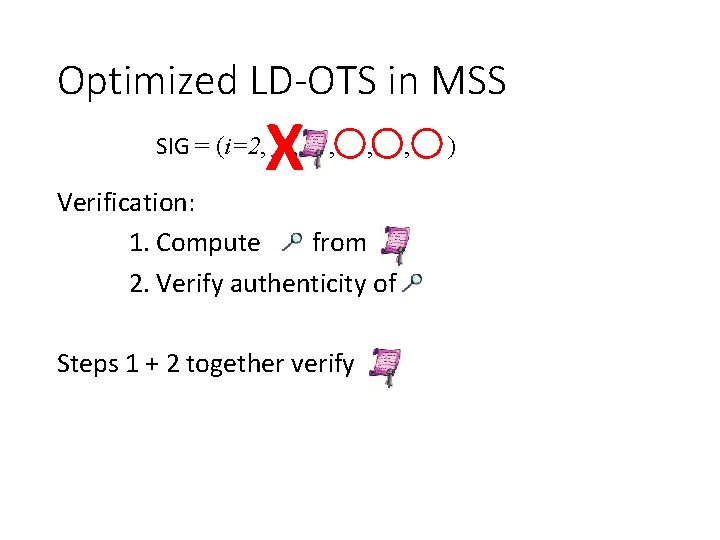
Optimized LD-OTS in MSS X SIG = (i=2, , , , Verification: 1. Compute from 2. Verify authenticity of Steps 1 + 2 together verify , )
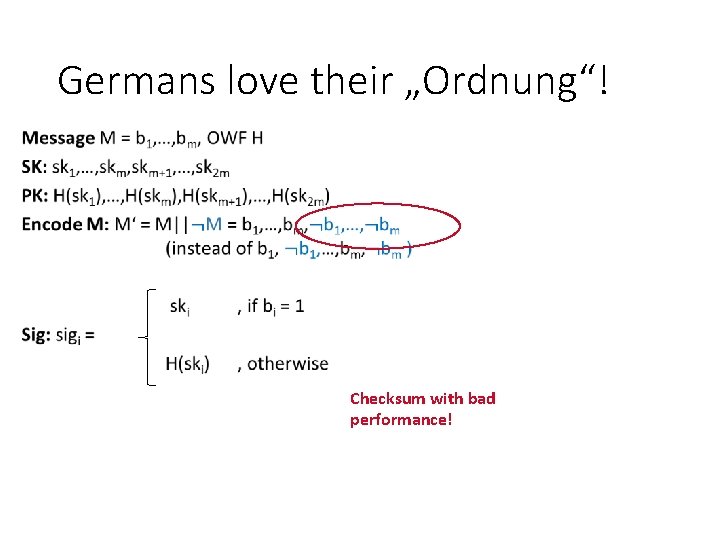
Germans love their „Ordnung“! Checksum with bad performance!
Optimized LD-OTS
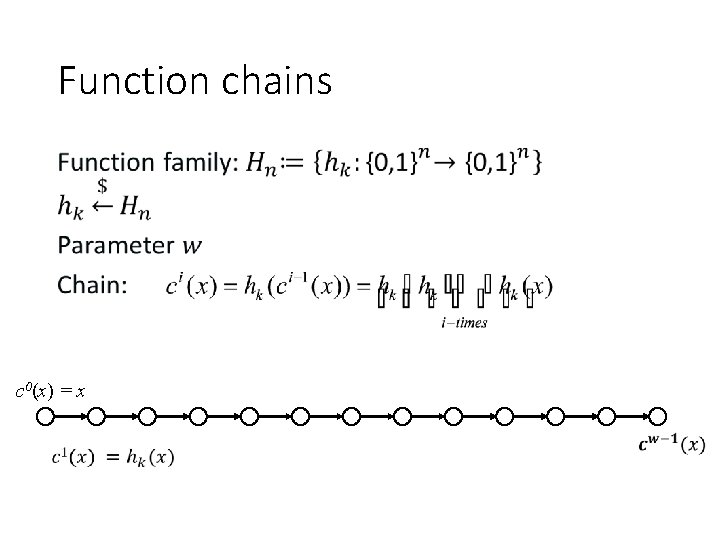
Function chains • c 0(x) = x
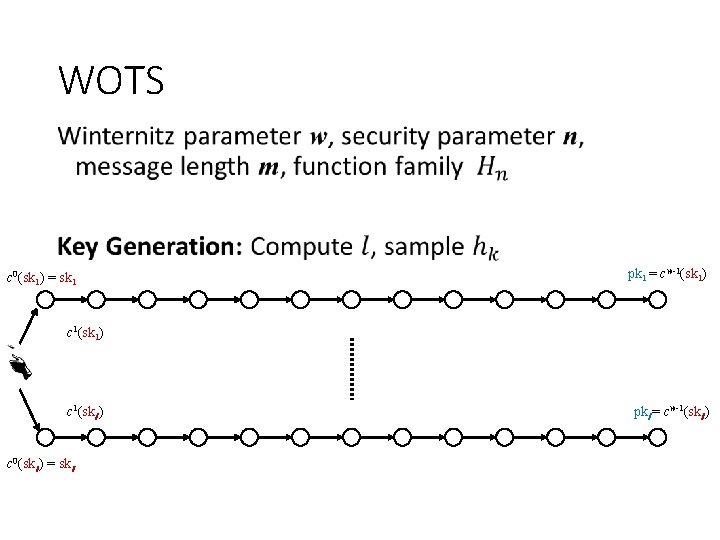
WOTS • c 0(sk 1) = sk 1 pk 1 = cw-1(sk 1) c 1(skl ) c 0(skl ) = skl pkl = cw-1(skl )
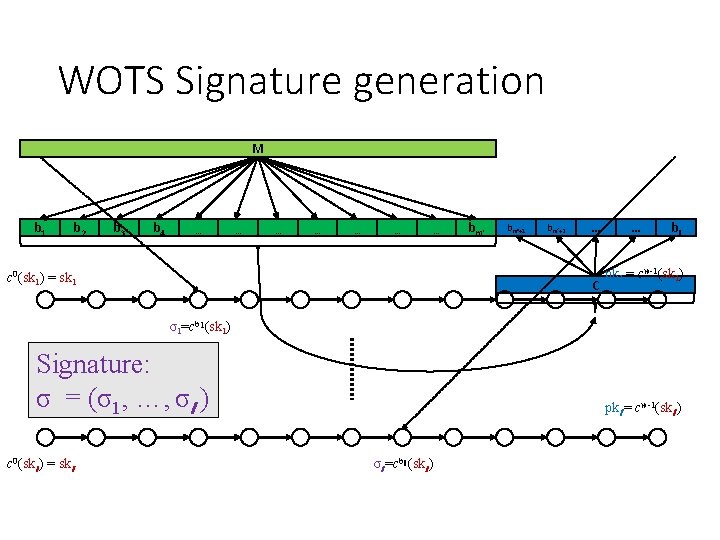
WOTS Signature generation M b 1 b 2 b 3 b 4 … … … … c 0(sk 1) = sk 1 bm‘+1 bm‘+2 … C … bl pk 1 = cw-1(sk 1) σ1=cb 1(sk 1) Signature: σ = (σ1, …, σl ) c 0(skl ) = skl pkl = cw-1(skl ) σl =cbl (skl )
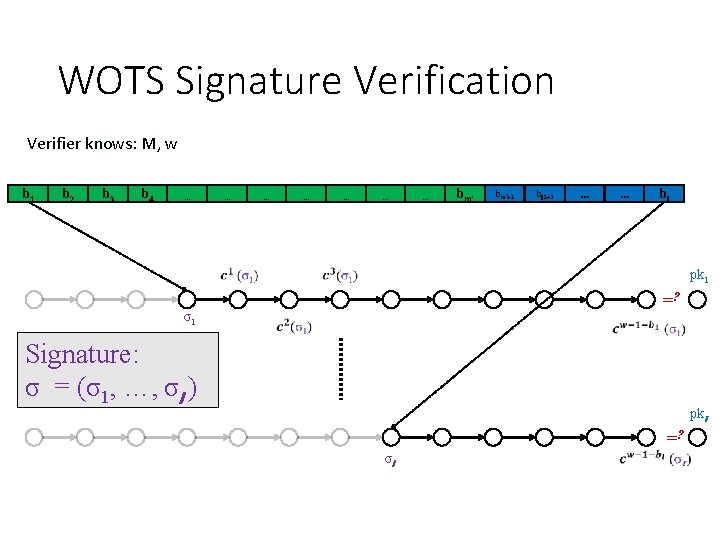
WOTS Signature Verification Verifier knows: M, w b 1 b 2 b 3 b 4 … … … … bm‘+1 bl 1+2 … … bl pk 1 =? σ1 Signature: σ = (σ1, …, σl ) pkl =? σl
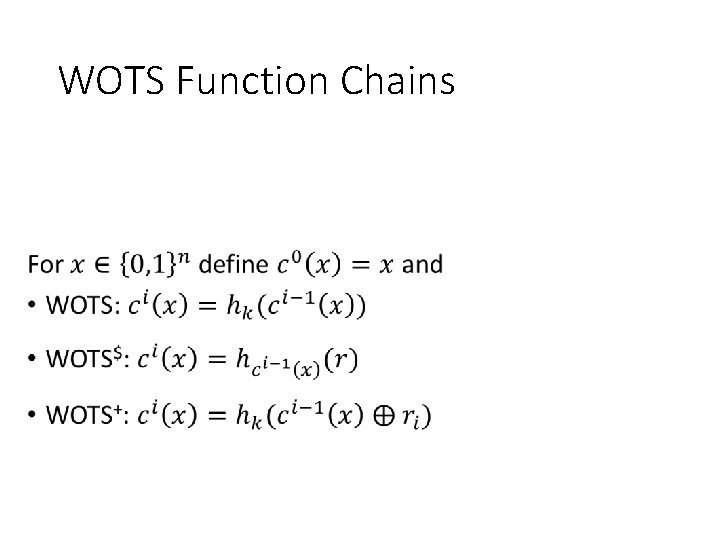
WOTS Function Chains •
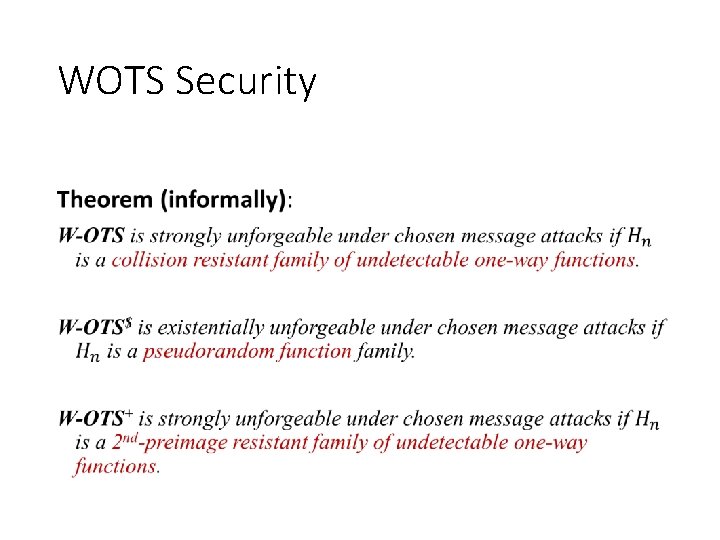
WOTS Security •

XMSS
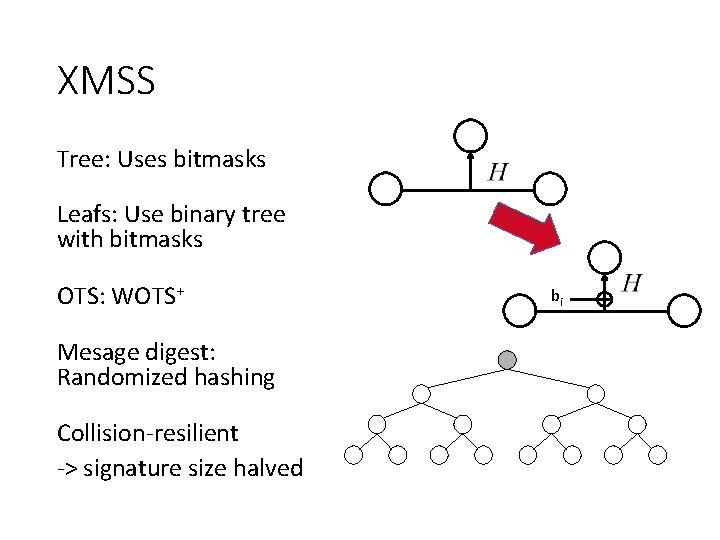
XMSS Tree: Uses bitmasks Leafs: Use binary tree with bitmasks OTS: WOTS+ Mesage digest: Randomized hashing Collision-resilient -> signature size halved bi
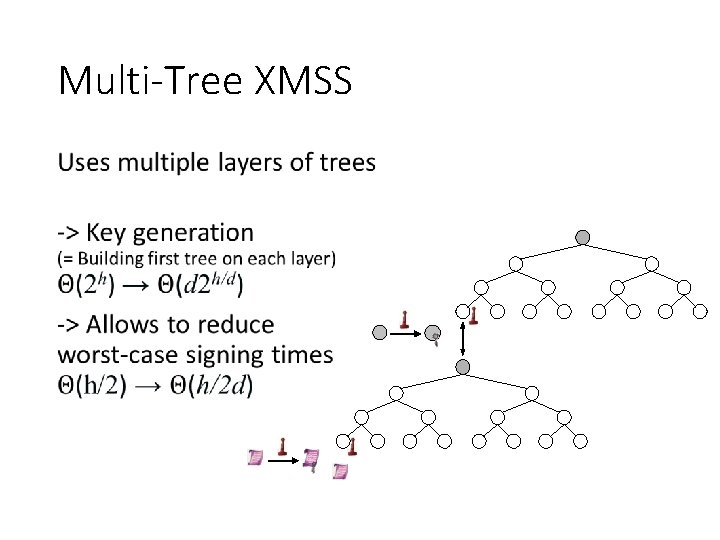
Multi-Tree XMSS •

How to Eliminate the State

Protest? PAGE 42 12 -6 -2021

Few-Time Signature Schemes 12 -6 -2021 PAGE 43
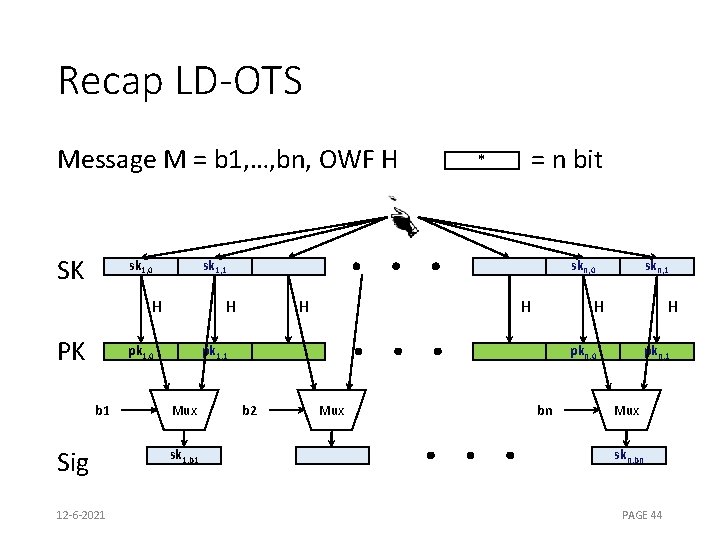
Recap LD-OTS Message M = b 1, …, bn, OWF H SK sk 1, 0 sk 1, 1 H PK Sig 12 -6 -2021 skn, 0 H pk 1, 0 b 1 = n bit * H H H pk 1, 1 Mux sk 1, b 1 skn, 1 H pkn, 0 b 2 Mux bn pkn, 1 Mux skn, bn PAGE 44
![HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters](http://slidetodoc.com/presentation_image_h2/69ac7151e137cb350db6d56411991ac3/image-44.jpg)
HORS [RR 02] * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) SK sk 1 sk 2 H PK 12 -6 -2021 pk 1 skt-1 H pk 1 H H skt H pkt-1 H pkt PAGE 45
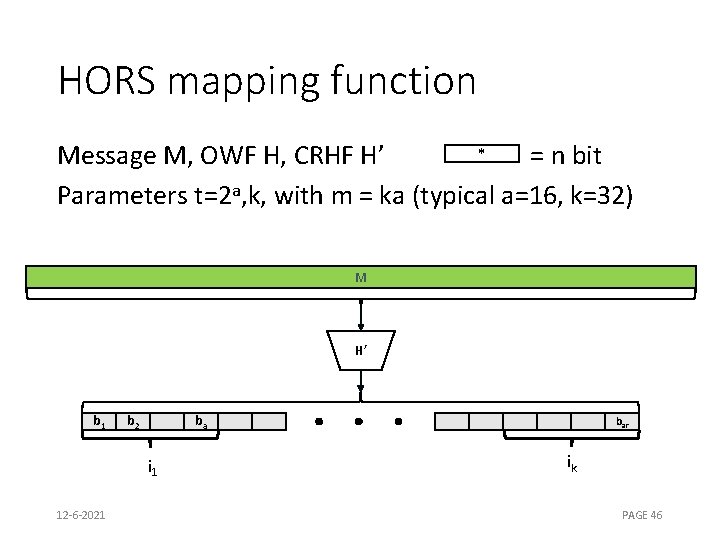
HORS mapping function * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) M H’ b 1 b 2 ba i 1 12 -6 -2021 bar ik PAGE 46
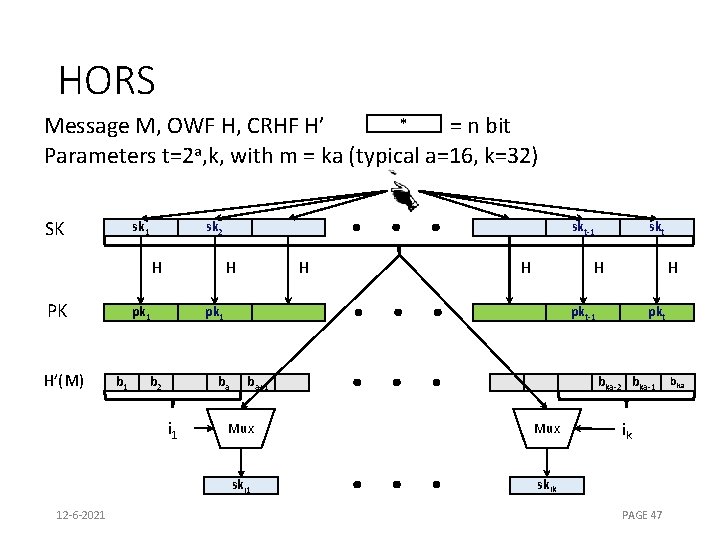
HORS * Message M, OWF H, CRHF H’ = n bit Parameters t=2 a, k, with m = ka (typical a=16, k=32) SK sk 1 sk 2 H PK H’(M) H pk 1 b 1 H H b 2 skt H pk 1 H pkt-1 ba i 1 12 -6 -2021 skt-1 ba+1 pkt bka-2 bka-1 Mux ski 1 skik ik PAGE 47 bka
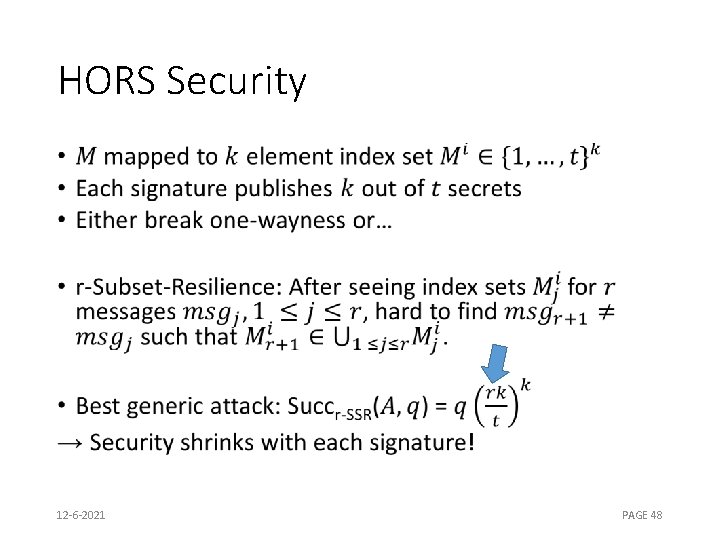
HORS Security • 12 -6 -2021 PAGE 48
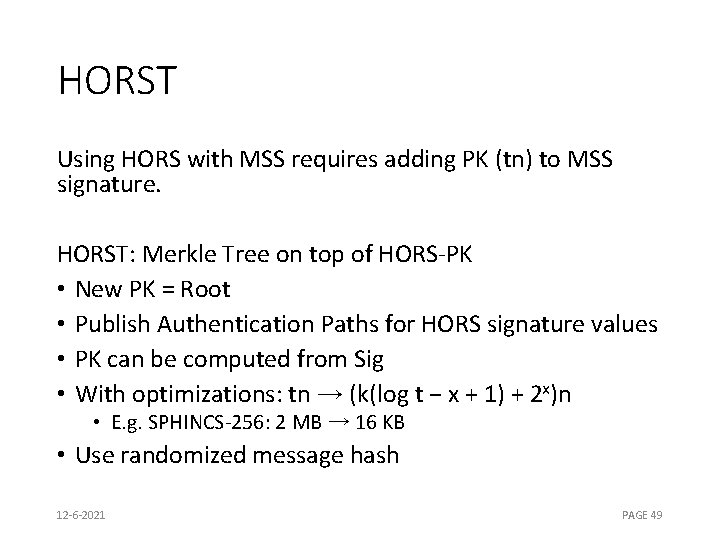
HORST Using HORS with MSS requires adding PK (tn) to MSS signature. HORST: Merkle Tree on top of HORS-PK • New PK = Root • Publish Authentication Paths for HORS signature values • PK can be computed from Sig • With optimizations: tn → (k(log t − x + 1) + 2 x)n • E. g. SPHINCS-256: 2 MB → 16 KB • Use randomized message hash 12 -6 -2021 PAGE 49
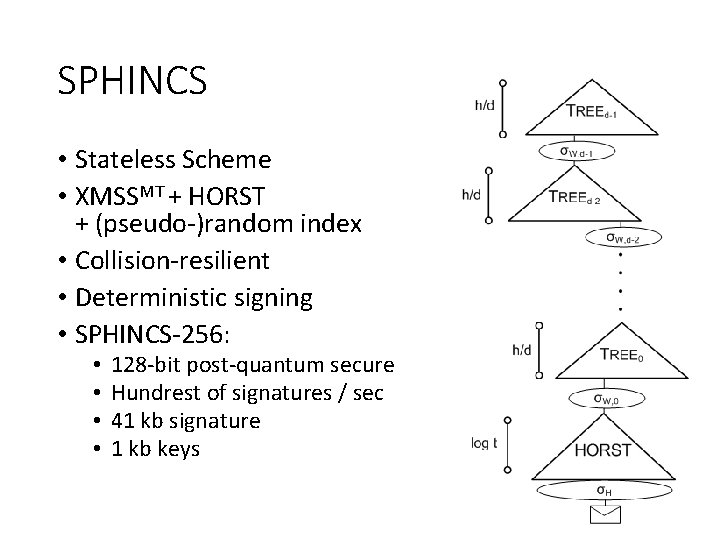
SPHINCS • Stateless Scheme • XMSSMT + HORST + (pseudo-)random index • Collision-resilient • Deterministic signing • SPHINCS-256: • • 128 -bit post-quantum secure Hundrest of signatures / sec 41 kb signature 1 kb keys
Hash & sign without collision resistance
PKC with variable-length inputs • Hard to build variable input length constructions (Schoolbook RSA) • Direct constructions are inefficient (See the hash-based constructions for long messages) • Full adversarial control over input can harm security (Schoolbook RSA) • For encryption: Use hybrid encryption -> PKE only encrypts “short” symmetric key. • For signatures: Hash-and-sign -> SIG only signs “short” message digest
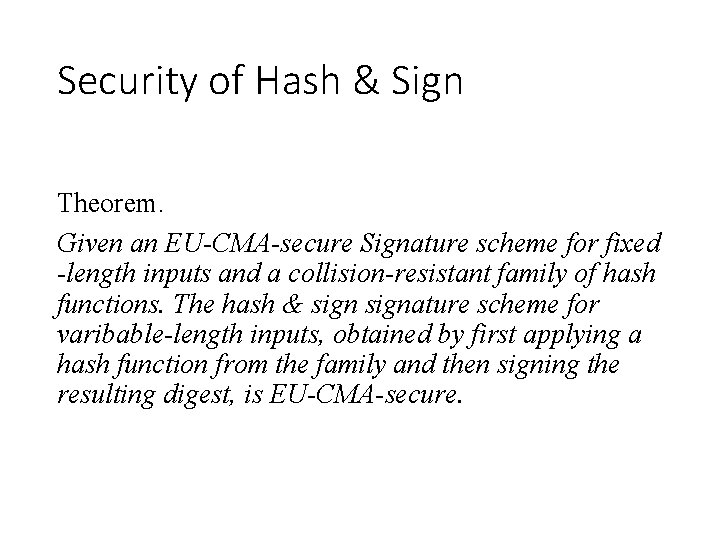
Security of Hash & Sign Theorem. Given an EU-CMA-secure Signature scheme for fixed -length inputs and a collision-resistant family of hash functions. The hash & signature scheme for varibable-length inputs, obtained by first applying a hash function from the family and then signing the resulting digest, is EU-CMA-secure.
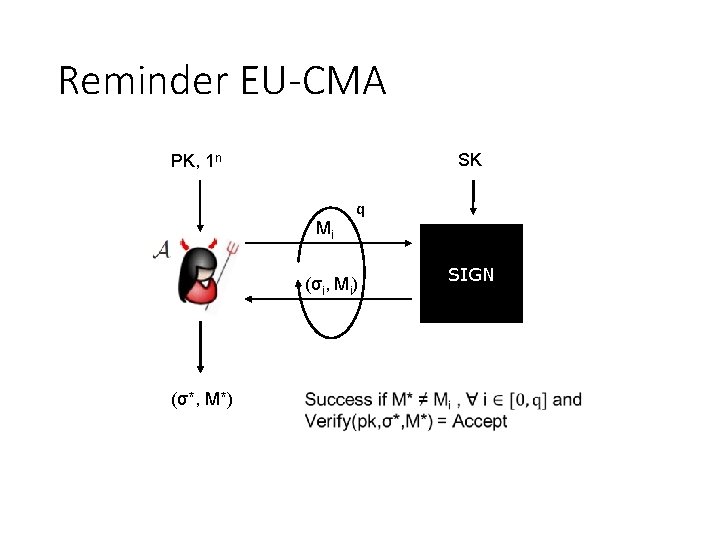
Reminder EU-CMA SK PK, 1 n Mi q (σi, Mi) (σ*, M*) SIGN
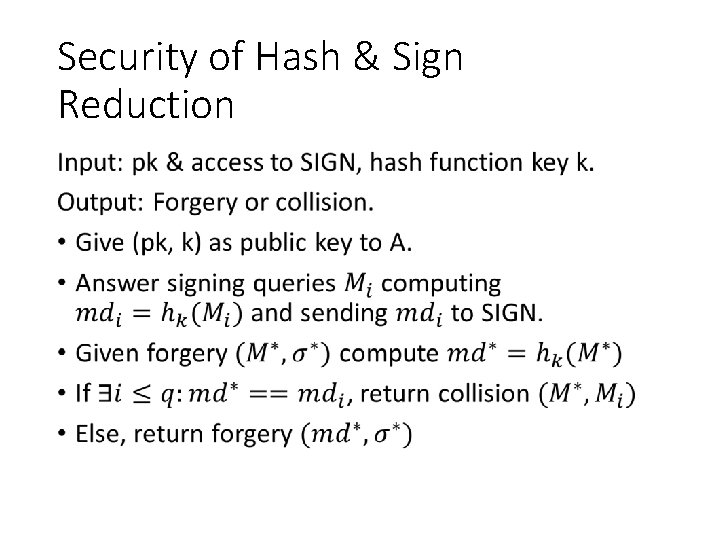
Security of Hash & Sign Reduction •

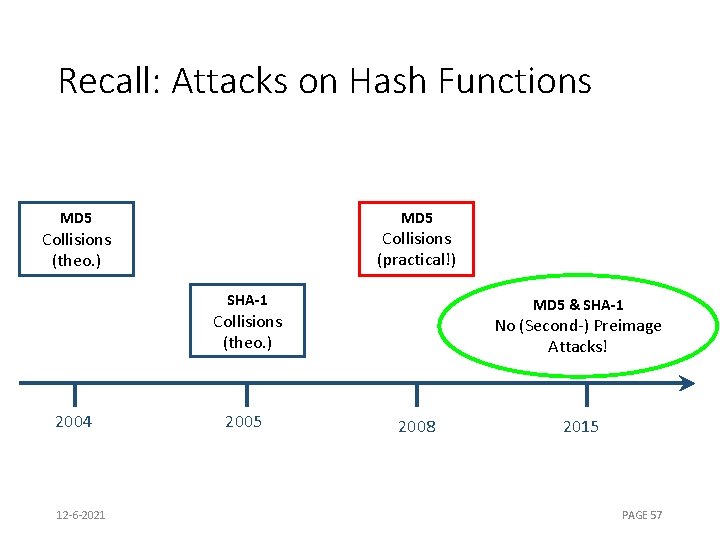
Recall: Attacks on Hash Functions MD 5 Collisions (practical!) Collisions (theo. ) SHA-1 MD 5 & SHA-1 Collisions (theo. ) 2004 12 -6 -2021 2005 No (Second-) Preimage Attacks! 2008 2015 PAGE 57
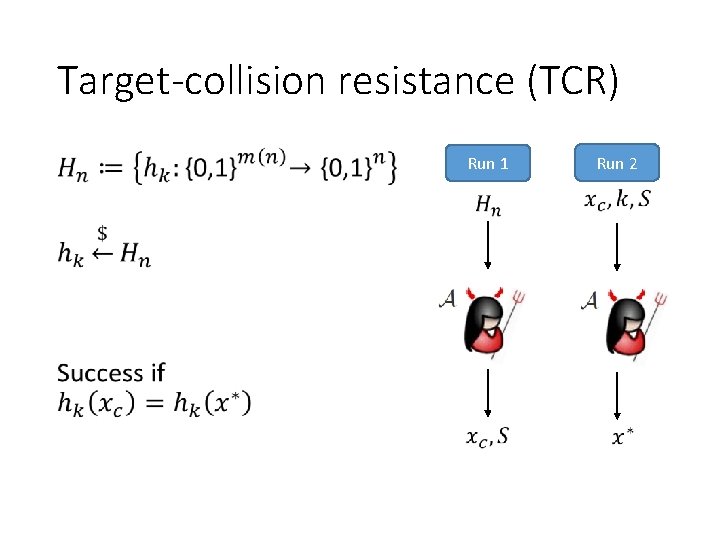
Target-collision resistance (TCR) • Run 1 Run 2
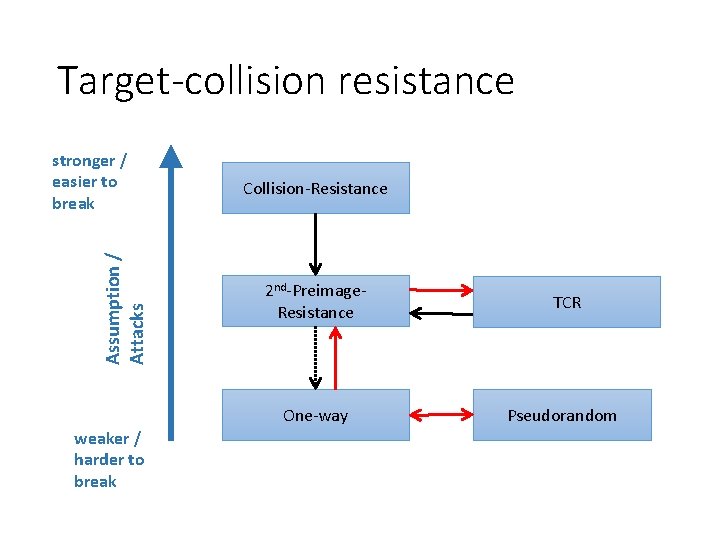
Target-collision resistance Assumption / Attacks stronger / easier to break weaker / harder to break Collision-Resistance 2 nd-Preimage. Resistance TCR One-way Pseudorandom
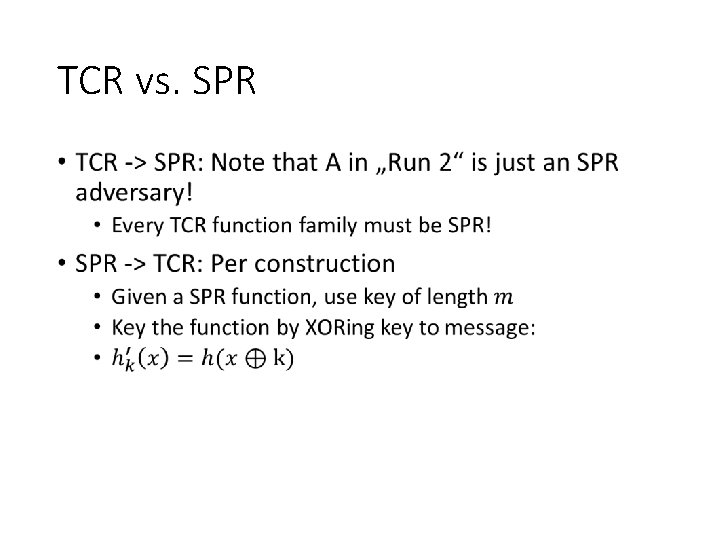
TCR vs. SPR •
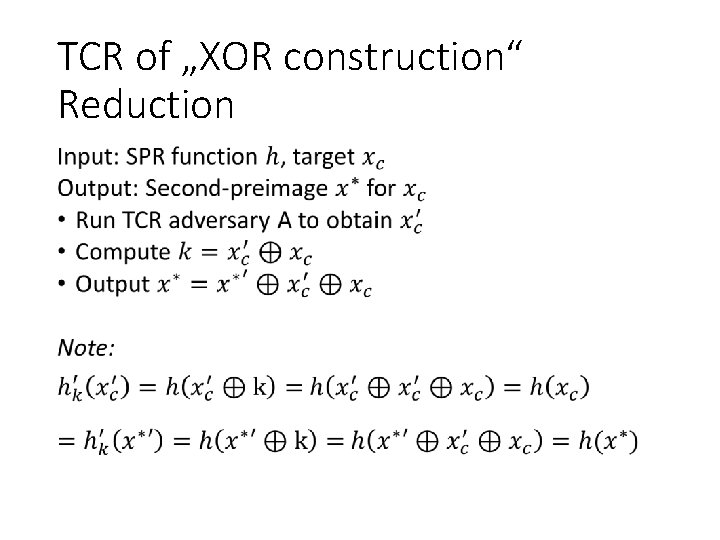
TCR of „XOR construction“ Reduction •
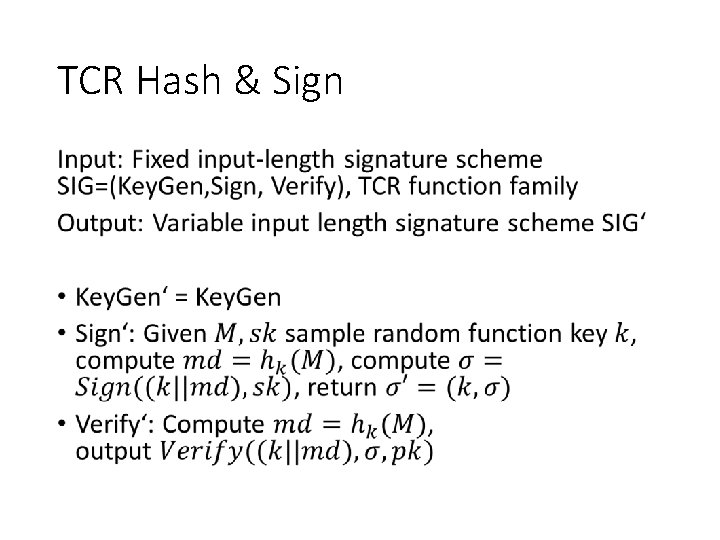
TCR Hash & Sign •
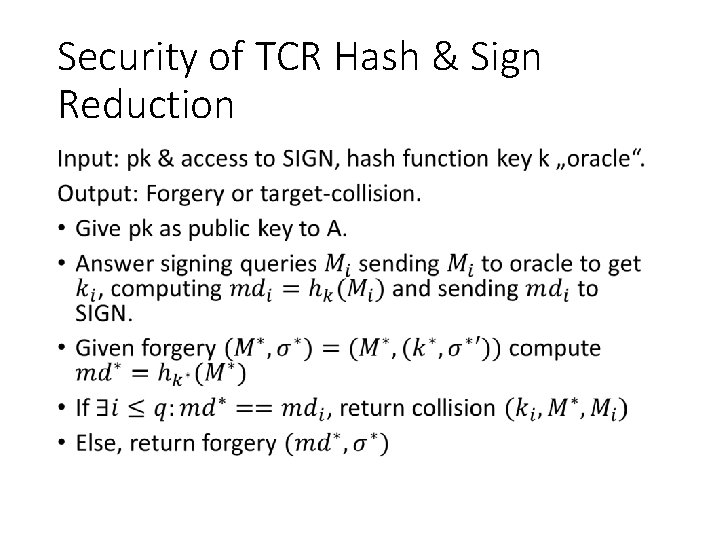
Security of TCR Hash & Sign Reduction •
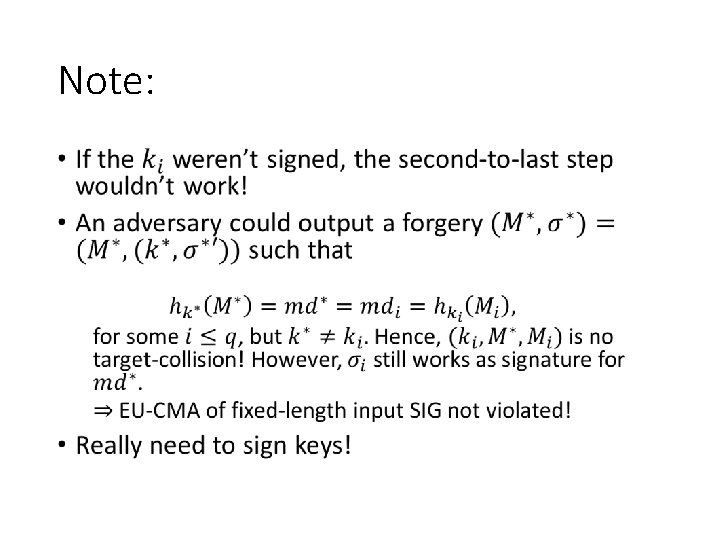
Note: •
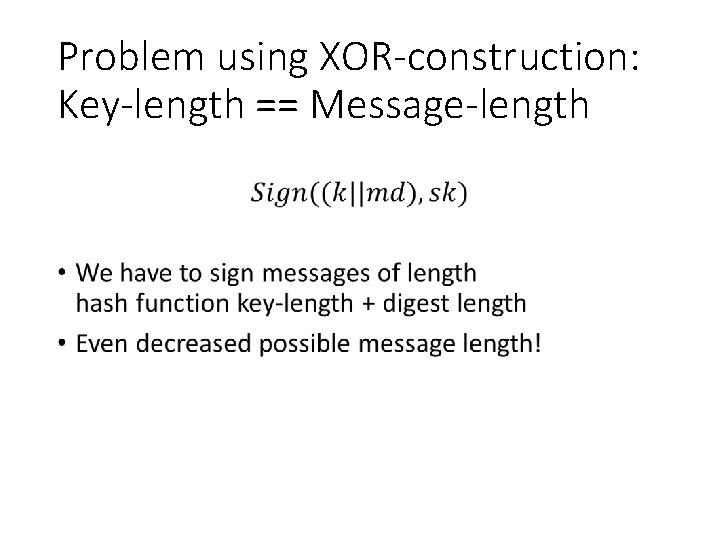
Problem using XOR-construction: Key-length == Message-length •
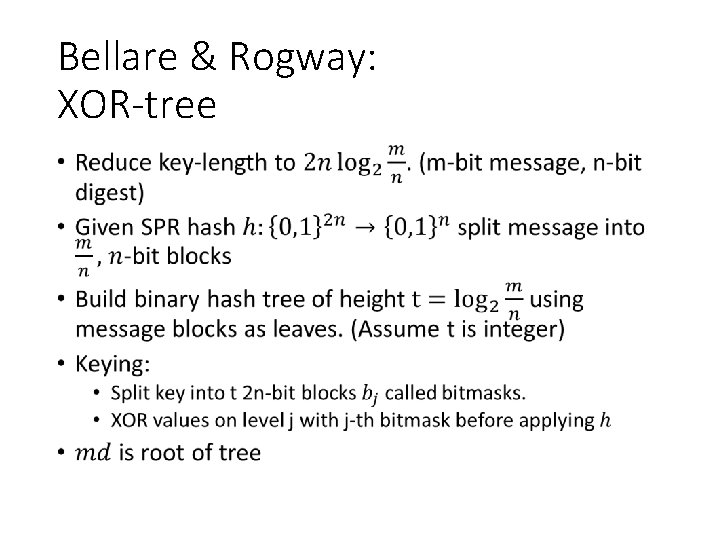
Bellare & Rogway: XOR-tree •

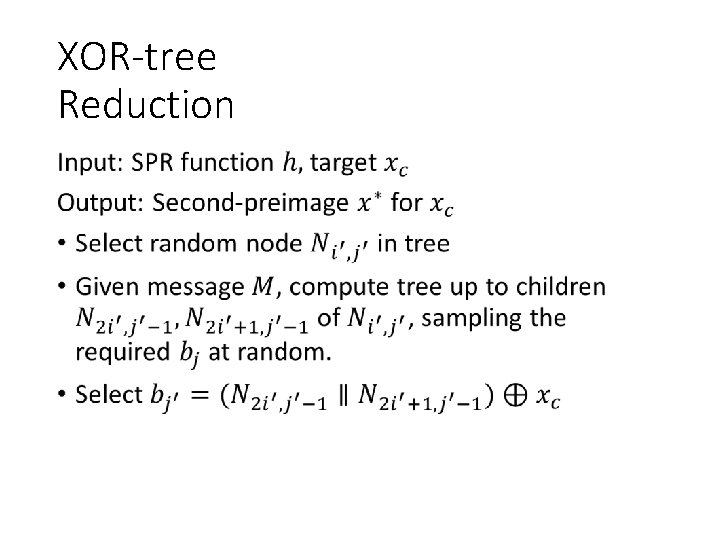
XOR-tree Reduction •

XOR-tree Reduction, cont‘d •
XOR-tree Reduction, cont‘d •
XOR-tree •

Approach 1: ROM • An RO, keyed by prefixing with key, is a TCR hash function. • No way to get TCR from Merkle-Damgard construction without (implicitly) assuming collision resistance.
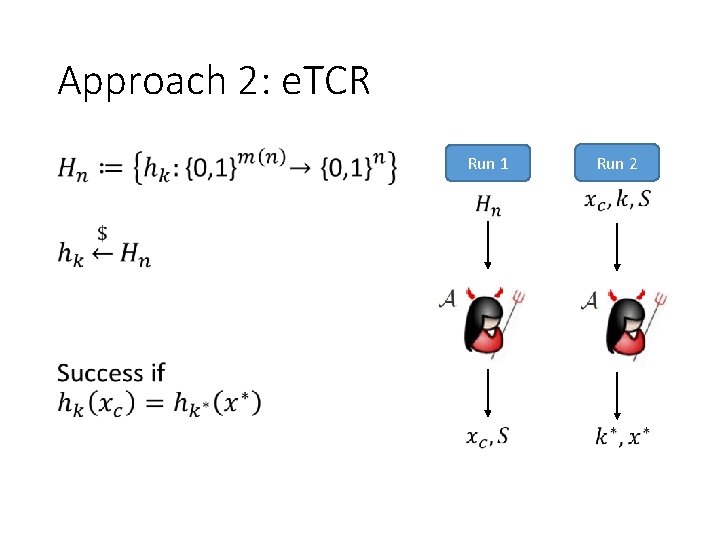
Approach 2: e. TCR Run 1 Run 2
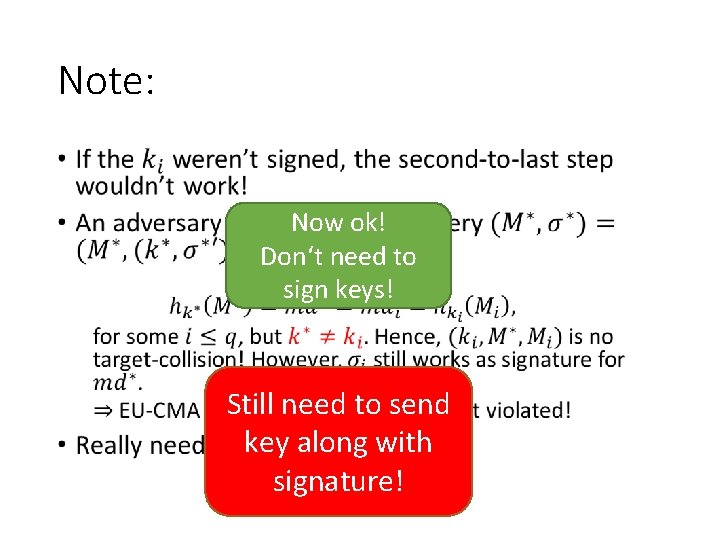
Note: • Now ok! Don‘t need to sign keys! Still need to send key along with signature!
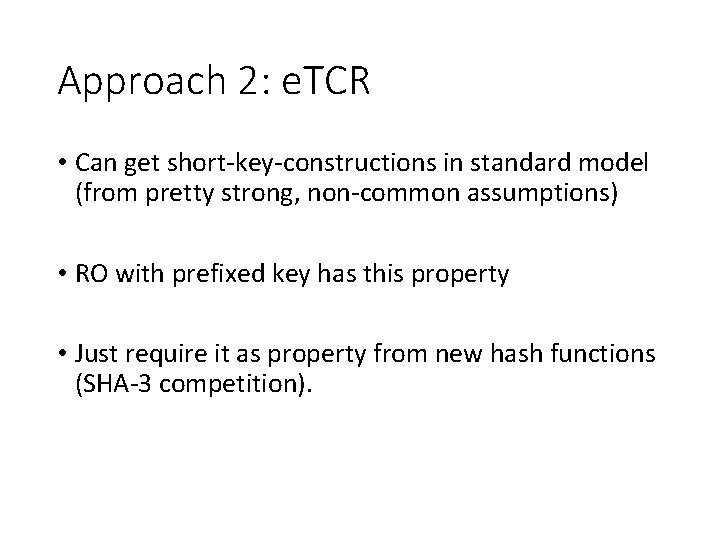
Approach 2: e. TCR • Can get short-key-constructions in standard model (from pretty strong, non-common assumptions) • RO with prefixed key has this property • Just require it as property from new hash functions (SHA-3 competition).
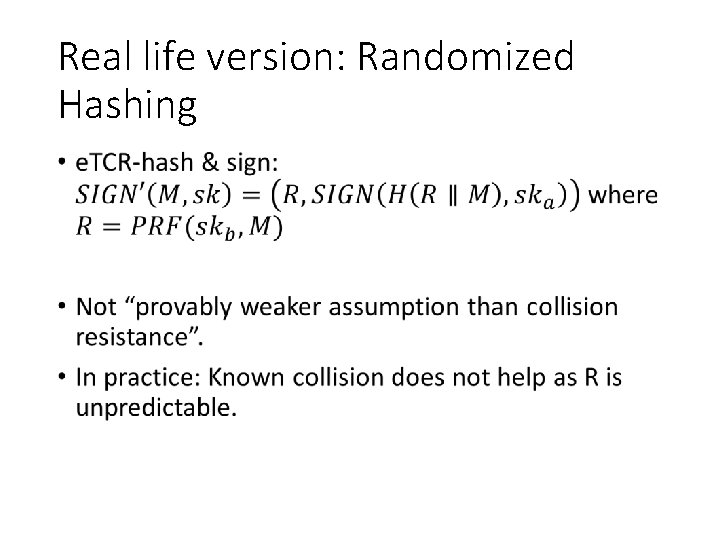
Real life version: Randomized Hashing •
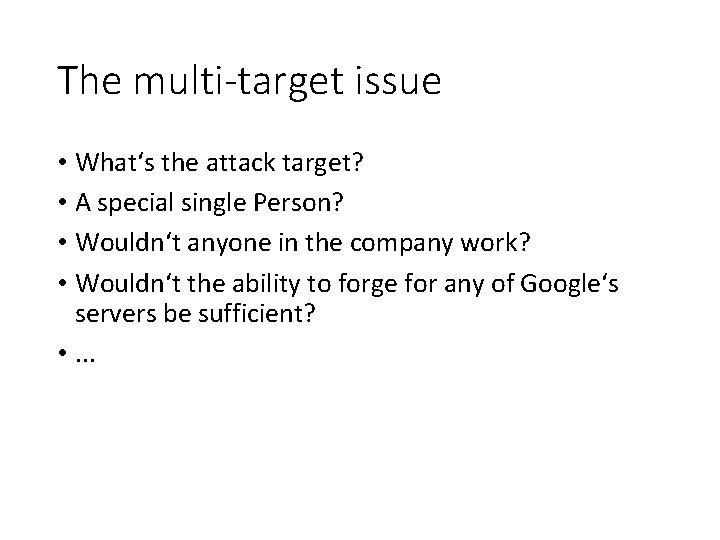
The multi-target issue • What‘s the attack target? • A special single Person? • Wouldn‘t anyone in the company work? • Wouldn‘t the ability to forge for any of Google‘s servers be sufficient? • . . .

The multi-target issue •
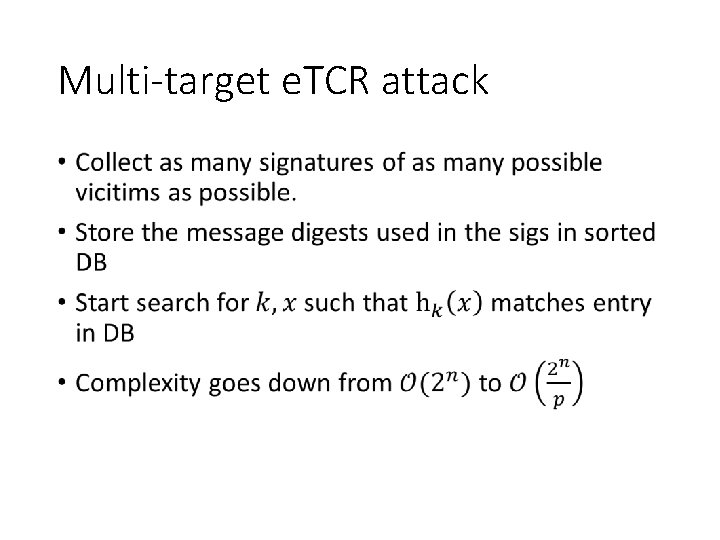
Multi-target e. TCR attack •
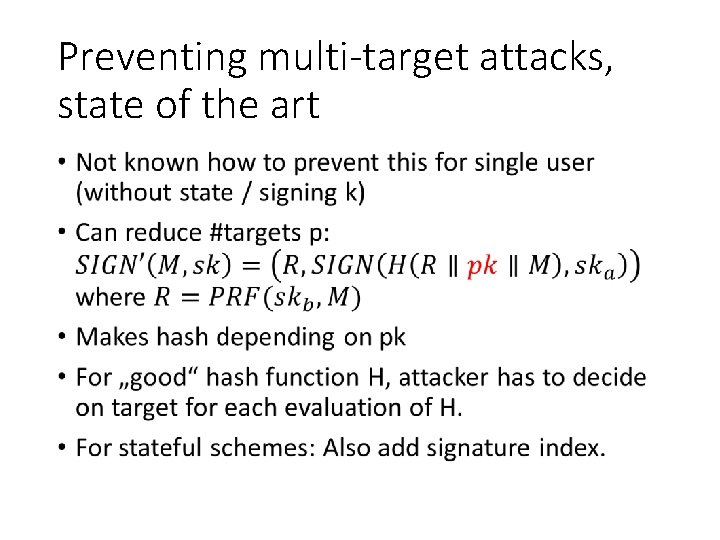
Preventing multi-target attacks, state of the art •
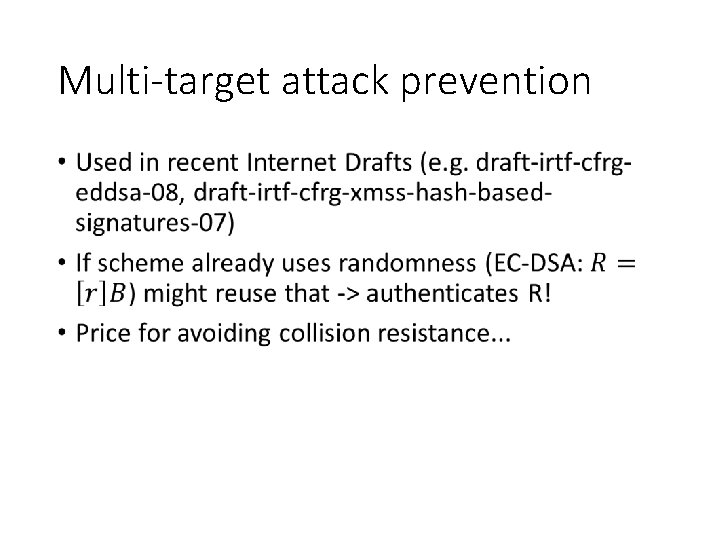
Multi-target attack prevention •
Thank you! Questions? For references & further literature see https: //huelsing. wordpress. com/hash-based-signature-schemes/literature/ 12 -6 -2021 PAGE 84
- Slides: 83