Telecommunications and Network Security CISSP Guide to Security
- Slides: 119
Telecommunications and Network Security CISSP Guide to Security Essentials Chapter 10
Objectives • Wireline and wireless telecommunication technologies • Wired and wireless network technologies • Network topologies and cabling • The OSI and TCP/IP network models CISSP Guide to Security Essentials 2
Objectives (cont. ) • TCP/IP networks, protocols, addressing, devices, routing, authentication, access control, tunneling, and services • Network based threats, attacks, vulnerabilities, and countermeasures CISSP Guide to Security Essentials 3
Wired Telecom Technologies • DS-1, aka T-1 – 24 voice or data channels, each 1. 544 Mbit/sec • Other T-carrier protocols – DS-3 (673 voice channels, 45 m. Bit/s) – DS-4 (4, 032 channels, 274 m. Bit/s) – DS-5 (5, 760 channels, 400 m. Bit/s) CISSP Guide to Security Essentials 4
Wired Telecom Technologies (cont. ) • E-1 – Euro version – 32 channels instead of 24, otherwise similar • SONET (Synchronous Optical NETwork) – High speed, fiber optic, encapsulates T-protocols, ATM, TCP/IP – OC-1 - 48. 960 Mbit/sec CISSP Guide to Security Essentials 5
Wired Telecom Technologies (cont. ) • SONET (cont. ) – OC-3 - 150. 336 Mbit/sec – OC-12 - 601. 344 Mbit/sec – OC-24 - 1, 202. 688 Mbit/sec CISSP Guide to Security Essentials 6
Wired Telecom Technologies (cont. ) • SONET (cont. ) – OC-48 - 2, 405. 376 Mbit/sec – OC-96 - 4, 810. 752 Mbit/sec – OC-192 - 9, 621. 504 Mbit/sec CISSP Guide to Security Essentials 7
Wired Telecom Technologies (cont. ) • Frame Relay – Link layer protocol * – Early packet-switched technology that used to transmit data between locations at a lower cost than dedicated DS-1 circuits – Switched Virtual Circuits (SVCs) and Permanent Virtual Circuits (PVCs) emulate dedicated T-1 * - discussed later in this chapter CISSP Guide to Security Essentials 8
Wired Telecom Technologies (cont. ) • ATM (Asynchronous Transfer Mode) – Synchronous, connection-oriented packet protocol – Packets called cells, are fixed length (5 byte header, 48 byte payload) CISSP Guide to Security Essentials 9
Wired Telecom Technologies (cont. ) • ATM (cont. ) – Intended to replace 10 m. B Ethernet, but it didn’t really catch on. 100 m. B and 1000 m. B Ethernet was favored instead, also giving way to MPLS. CISSP Guide to Security Essentials 10
Wired Telecom Technologies (cont. ) • DSL (Digital Subscriber Line) – Digital packet over copper voice circuits at higher clock rate, coexists with low frequency voice CISSP Guide to Security Essentials 11
Wired Telecom Technologies (cont. ) • DSL (cont. ) – Modem used on subscriber side to convert DSL signals to Ethernet (and sometimes Wi-Fi) – DSLAM (Digital Subscriber Line Access Multiplexer) on telco end aggregates signals CISSP Guide to Security Essentials 12
Wired Telecom Technologies (cont. ) • MPLS (Multiprotocol Label Switching) – Packet switched technology, encapsulates TCP/IP, ATM, SONET, Ethernet frames) – Carries voice + data, has Qo. S (quality of service) capabilities to guarantee jitter-free voice and other media such as video – Replacing Frame Relay and ATM CISSP Guide to Security Essentials 13
Wired Telecom Technologies (cont. ) • Other wired telecom technologies – Data Over Cable Service Interface Specification (DOCSIS) – PSTN (Public Switched Telephone Network) – ISDN (Integrated Services Digital Network) – SDH (Synchronous Digital Hierarchy) – X. 25 CISSP Guide to Security Essentials 14
Wireless Telecom Technologies • CDMA 2000 (code division multiple access) – Data transport: 1 XRTT (153 kbit/s), EVDO (2. 4 Mbit/s), EVDV (3. 1 Mbit/s) • GPRS (General Packet Radio Service) – Encapsulated in GSM (Global System for Mobile communications) protocol (114 kbit/s) CISSP Guide to Security Essentials 15
Wireless Telecom Technologies (cont. ) • EDGE (Enhanced Data rates for GSM Evolution) – Up to 1 Mbit/s • UMTS (Universal Mobile Telecommunications System) – Transported over WCDMA, up to 14 Mbit/s) CISSP Guide to Security Essentials 16
Wireless Telecom Technologies (cont. ) • Wi. MAX (Worldwide Interoperability for Microwave Access) – Based on IEEE 802. 16, Wi. MAX is a wireless competitor to DSL and cable modems, also competes with CDMA, GPRS, EDGE, UMTS CISSP Guide to Security Essentials 17
Wireless Telecom Technologies (cont. ) • Wi. MAX (cont. ) – Rates range from 2 to 12 Mbit/s, theoretically as high as 70 Mbit/s • CDPD (Cellular Digital Packet Data) – first data over cellular, used AMPS analog carrier, up to 19. 2 kbit/s CISSP Guide to Security Essentials 18
Wired Network Technologies • Ethernet – Frame-based protocol • • 14 byte header Payload (46 -1500 bytes) Checksum Inter-frame gap CISSP Guide to Security Essentials 19
Wired Network Technologies (cont. ) • Ethernet (cont. ) – Error detection: Carrier Sense Multiple Access with Collision Detection (CSMA/CD) – MAC address: 6 bytes. Format xx. xx. yy. yy. • xx. xx assigned to manufacturer CISSP Guide to Security Essentials 20
Wired Network Technologies (cont. ) • Ethernet devices – Hub – connects local stations together; broadcast – Repeater – extend signal over distances – Switch – like a hub but does not broadcast CISSP Guide to Security Essentials 21
Wired Network Technologies (cont. ) • Ethernet devices (cont. ) – Router – connect networks to each other – Gateway – translates various types of communications CISSP Guide to Security Essentials 22
Wired Network Technologies (cont. ) • Token ring – Logical ring – Speed: 4 Mbit/s and 16 Mbit/s – Mostly replaced by Ethernet CISSP Guide to Security Essentials 23
Wired Network Technologies (cont. ) • Universal Serial Bus (USB) – Successor to RS-232 serial – Speeds • USB 1. 0/1. 1 – 1. 5 Mbits/s and 12 Mbits/s • USB 2. 0 – 480 Mbits/s • USB 3. 0 – 4. 8 Gbits/s CISSP Guide to Security Essentials 24
Wired Network Technologies (cont. ) • Universal Serial Bus (cont. ) – Hot pluggable – Used to connect peripheral and human interface devices CISSP Guide to Security Essentials 25
Wired Network Technologies (cont. ) • RS-232 – Serial communications, speeds 110 bit/s – 57. 7 kbit/s – Used to connect communications devices such as modems, and human interface devices such as mice – Largely replaced by USB CISSP Guide to Security Essentials 26
Wired Network Technologies (cont. ) • HSSI (High Speed Serial Interface) – 52 Mbits/s, cable length 50’, used to connect WAN devices • Fibre Channel – Gigabit protocol used in SANs (Storage Area Networks) CISSP Guide to Security Essentials 27
Wired Network Technologies (cont. ) • FDDI (Fiber Distributed Data Interface) – Token technology over fiber that has been replaced by gigabit Ethernet and SONET CISSP Guide to Security Essentials 28
Wired Network Technologies (cont. ) • Network cabling – Ethernet • 10 BASE-T – this is the commonly twisted-pair network cable that supports the Category 3, 5, or 6 ANSI standard. This cable… CISSP Guide to Security Essentials 29
Wired Network Technologies (cont. ) • 10 BASE-T (cont. ) …has 8 conductors, of which 4 are used. An 8 -pin RJ 45 connector is used to connect a cable to a device. CISSP Guide to Security Essentials 30
Wired Network Technologies (cont. ) – Ethernet (cont. ) • 100 BASE-TX – the same twisted-pair network cable (Category 5 and 6) and connectors as 10 BASE-T, and also uses just 4 of the 8 conductors CISSP Guide to Security Essentials 31
Wired Network Technologies (cont. ) – Ethernet (cont. ) • 1000 BASE-T – the same twisted-pair network cable and connectors as 100 BASE-TX, except that all 8 conductors are used. CISSP Guide to Security Essentials 32
Wired Network Technologies (cont. ) – Ethernet (cont. ) • 10 BASE 2 – the old “thinnet” coaxial cabling with twist-lock BNC connectors – rarely used. • 10 BASE 5 – the old “thicknet” coaxial cabling that is rarely used. CISSP Guide to Security Essentials 33
Wired Network Technologies (cont. ) • Twisted pair cabling – Category 3 – consists of four twisted pairs in a single jacket. Suitable only for 10 Mbit/s Ethernet. Superseded by Category 5 and 5 e. CISSP Guide to Security Essentials 34
Wired Network Technologies (cont. ) • Twisted pair cabling (cont. ) – Category 5 – consists of four twisted pairs in a single jacket. Maximum length is 100 m. Suitable for 100 Mbit/s and can be used for Gigabit Ethernet. CISSP Guide to Security Essentials 35
Wired Network Technologies (cont. ) • Twisted pair cabling (cont. ) – Category 5 e – supersedes Category 5 and includes specifications for far end crosstalk. – Category 6 – backward compatible with Category 5 and 5 e, but higher specifications for noise and crosstalk, making it more suitable for Gigabit Ethernet. CISSP Guide to Security Essentials 36
Wired Network Technologies (cont. ) • Twisted pair cabling (cont. ) – Category 7 – even more stringent than Category 6 cabling, Cat-7 is suitable for 10 Gbit/s networks. CISSP Guide to Security Essentials 37
Wired Network Technologies (cont. ) • Cabling – Optical • Carries signal in the form of light instead of electricity • Greater speeds and distances possible • More expensive CISSP Guide to Security Essentials 38
Network Topologies • Bus. All of the nodes in the network are connected to a single conductor. A break in the network conductor will cause some or the entire network to stop functioning. Early Ethernet networks consisting of thinnet coaxial cabling were bus networks. CISSP Guide to Security Essentials 39
Network Topologies (cont. ) • Ring. All of the nodes are connected to exactly two other nodes, forming a circular loop. Breaking any conductor will cause the network to stop functioning. • Star. All nodes are connected to a central device. A break in a conductor… CISSP Guide to Security Essentials 40
Network Topologies (cont. ) • Star. (cont. ) …will disconnect only one node, and the remaining nodes will continue functioning. Ethernet networks are physical stars, with computers connected to central hubs or switches. Token ring networks, while logically as a ring, are physically wired as a star. CISSP Guide to Security Essentials 41
Wireless Network Technologies • Wi-Fi, also known as WLAN, Wireless LAN – Wireless data link layer network protocol – Bandwidth up to 54 Mbit/s, distances to 100 m CISSP Guide to Security Essentials 42
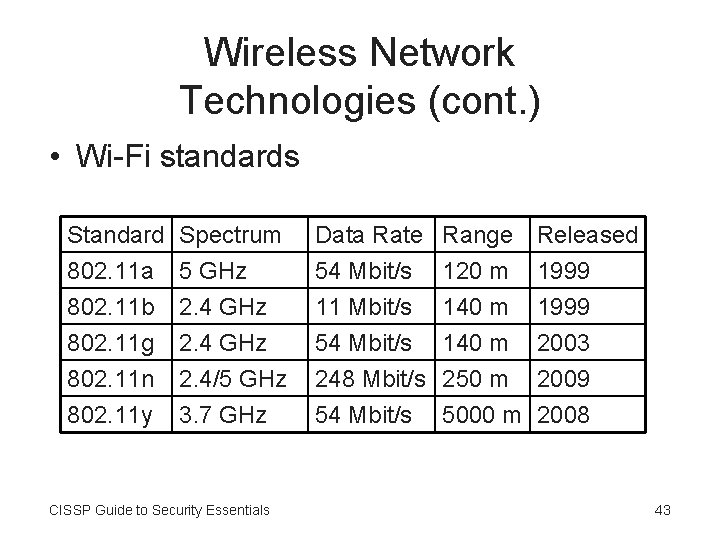
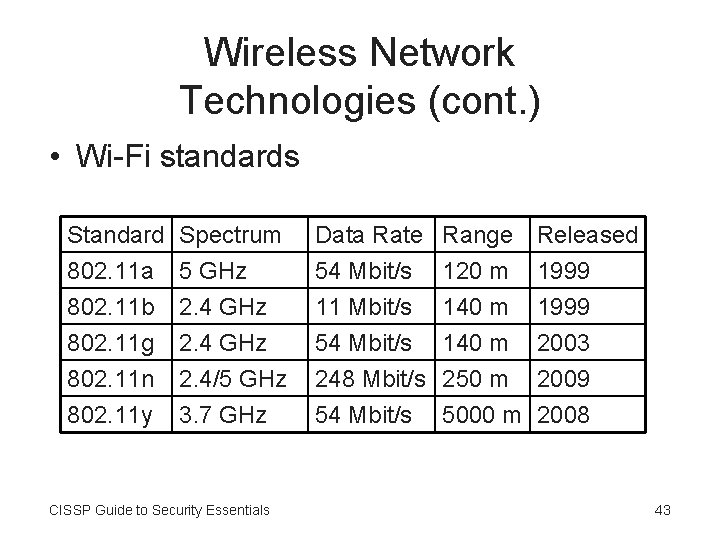
Wireless Network Technologies (cont. ) • Wi-Fi standards Standard 802. 11 a 802. 11 b 802. 11 g Spectrum 5 GHz 2. 4 GHz Data Rate 54 Mbit/s 11 Mbit/s 54 Mbit/s 802. 11 n 802. 11 y 2. 4/5 GHz 3. 7 GHz 248 Mbit/s 250 m 2009 54 Mbit/s 5000 m 2008 CISSP Guide to Security Essentials Range 120 m 140 m Released 1999 2003 43
Wireless Network Technologies (cont. ) • Wi-Fi security – SSID should be a non-default value – SSID broadcast should be disabled – MAC access control CISSP Guide to Security Essentials 44
Wireless Network Technologies (cont. ) • Wi-Fi security (cont. ) – Authentication – Encryption • WEP (Wired Equivalent Privacy) • WPA (Wireless Protected Access) • WPA 2 (superset of WPA, full standard) CISSP Guide to Security Essentials 45
Wireless Network Technologies (cont. ) • Bluetooth – Personal Area Network (PAN) technology – Data rate: 1 Mbit/s – 3 Mbit/s – Distance: up to 10 m CISSP Guide to Security Essentials 46
Wireless Network Technologies (cont. ) • Bluetooth (cont. ) – Devices can authenticate through a process called “pairing”, during which two devices can exchange a cryptographic secret key that the two devices can later use CISSP Guide to Security Essentials 47
Wireless Network Technologies (cont. ) • Bluetooth (cont. ) – Communications between paired devices can also be encrypted CISSP Guide to Security Essentials 48
Wireless Network Technologies (cont. ) • Ir. DA – Infrared Data Association standard – Infrared light spectrum from 2. 4 kbit/s to 16 Mbit/s • Requires line-of-sight – Once popular, now being replaced with Bluetooth CISSP Guide to Security Essentials 49
Wireless Network Technologies (cont. ) • Wireless USB (WUSB) – Wireless protocol designed for wireless connectivity of various computer peripherals • Printers, digital cameras, hard disks, and other high-throughput devices. CISSP Guide to Security Essentials 50
Wireless Network Technologies (cont. ) • Wireless USB (cont. ) – Bandwidth ranges from 110 Mbit/s at 10 meters to 480 Mbit/s at 3 meters – 3. 1 to 10. 6 GHz frequency range CISSP Guide to Security Essentials 51
Wireless Network Technologies (cont. ) • Near Field Communication (NFC) – Ultra-short distance (up to 10 cm or 4”) – Rates: 106 kbit/s, 212 kbit/s, or 424 kbit/s – Active or passive mode • Passive mode ideal for key card access control CISSP Guide to Security Essentials 52
OSI Protocol Model • • Physical Data link Network Transport Session Presentation Application CISSP Guide to Security Essentials 53
OSI Protocol Model: Physical • Concerned with a network’s physical media – Electrical – Optical – Radio frequency CISSP Guide to Security Essentials 54
OSI Protocol Model: Physical (cont. ) • Example standards – RS-232, RS-422, T 1, E 1, 10 Base-T, SONET, DSL, 802. 11 a (physical), Twinax CISSP Guide to Security Essentials 55
OSI Protocol Model: Data Link • Concerned with the transfer of data between nodes • Manages error correction for any errors that take place at the physical layer CISSP Guide to Security Essentials 56
OSI Protocol Model: Data Link (cont. ) • Example standards – 802. 3 (Ethernet), 802. 11 a MAC, GPRS, Apple. Talk, ATM, FDDI, Fibre Channel, Frame Relay, PPP, SLIP, Token Ring, Wi-MAX CISSP Guide to Security Essentials 57
OSI Protocol Model: Network • Used to transport variable-length data sequences between nodes • Manages fragmentation and reassembly • Communications are point-to-point CISSP Guide to Security Essentials 58
OSI Protocol Model: Network (cont. ) • No notion of a “connection” • Delivery of data not done here • Example standards – IP, ICMP, ARP, IPX CISSP Guide to Security Essentials 59
OSI Protocol Model: Transport • Manages the delivery of data from node to node on a network – Even when there are intermediate devices such as routers and a variety of physical media between the nodes CISSP Guide to Security Essentials 60
OSI Protocol Model: Transport (cont. ) • Manages the delivery of data from node to node on a network (cont. ) – Manages “connections” • Guarantee the order of delivery of data packets, packet reassembly, error recovery – Examples: UDP, TCP, IPsec, PPTP, L 2 TP, SPX CISSP Guide to Security Essentials 61
OSI Protocol Model: Session • Manages connections between nodes, including session establishment, communication, and teardown • Example standards – Net. BIOS, TCP, SIP CISSP Guide to Security Essentials 62
OSI Protocol Model: Presentation • Deals with the presentation or representation of data in a communications session – Character set translation – Compression – Encryption CISSP Guide to Security Essentials 63
OSI Protocol Model: Presentation (cont. ) • Examples of presentation - layer standards include SSL, TLS, MIME, and MPEG CISSP Guide to Security Essentials 64
OSI Protocol Model: Application • Top-most layer in the OSI network model • Concerned with the delivery of data to and from applications • Examples standards – DNS, NFS, NTP, DHCP, SMTP, HTTP, SNMP, SSH, Telnet, WHOIS CISSP Guide to Security Essentials 65
TCP/IP Protocol Model • • • Physical Data link Network / internet Transport Application CISSP Guide to Security Essentials 66
TCP/IP Protocol Model: Physical • Physical medium used to carry traffic – – Twisted pair cable Coaxial cable Optical fiber SONET CISSP Guide to Security Essentials 67
TCP/IP Protocol Model: Physical (cont. ) • Physical medium (cont. ) – – T-1 and E-1 telecommunications links DSL ISDN Wi-Fi CISSP Guide to Security Essentials 68
TCP/IP Protocol Model: Physical (cont. ) • Physical medium (cont. ) – – Bluetooth USB GPRS CDMA CISSP Guide to Security Essentials 69
TCP/IP Protocol Model: Data Link • Concerned with node to node delivery • Example standards – Wi-Fi – Ethernet – Token Ring CISSP Guide to Security Essentials 70
TCP/IP Protocol Model: Data Link (cont. ) • Example standards (cont. ) – ATM – Frame Relay – PPP CISSP Guide to Security Essentials 71
TCP/IP Protocol Model: Network • Also known as the Internet layer • Concerned with end-to-end packet delivery, even through intermediate devices such as switches and routers CISSP Guide to Security Essentials 72
TCP/IP Protocol Model: Network (cont. ) • Protocols – – IPv 4 IPv 6 ARP RARP CISSP Guide to Security Essentials 73
TCP/IP Protocol Model: Network (cont. ) • Protocols (cont. ) – ICMP – IGMP – IPsec CISSP Guide to Security Essentials 74
TCP/IP Protocol Model: Network (cont. ) • Network layer routing protocols – – RIP OSPF IS-IS BGP CISSP Guide to Security Essentials 75
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing – Network addresses in IPv 4 are 32 bits in length • Expressed as a dot-decimal notation, xx. xx. xx, where the range of each ‘xx’ is 0 -255 decimal. • Typical network address is 141. 204. 13. 200 CISSP Guide to Security Essentials 76
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Subnets and subnet masking • IP address divided into two parts: network and node • Subnet mask used to distinguish network and node portions; e. g. 255. 0 CISSP Guide to Security Essentials 77
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Default gateway – node that connects to other networks – Address allocation by Regional Internet Registry (RIR), ISPs CISSP Guide to Security Essentials 78
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Reserved address blocks • Private networks – 10. 0 – 10. 255 – 172. 16. 0. 0 - 172. 31. 255 – 192. 168. 0. 0 - 192. 168. 255 CISSP Guide to Security Essentials 79
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Reserved address blocks (cont. ) • Loopback: 127. 0. 0. 1 - 127. 0. 0. 255 (127. 0. 0. 1 = “me”) • Multicast: 224. 0. 0. 0 -239. 255 CISSP Guide to Security Essentials 80
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Network address translation (NAT) • Internal private addresses are translated into public routable addresses at the network boundary CISSP Guide to Security Essentials 81
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Classful networks • Class A • Class B • Class C CISSP Guide to Security Essentials 82
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Classless networks (Classless Internet Domain Routing (CIDR) • Variable length subnet masks, not limited to just Class A, B, C CISSP Guide to Security Essentials 83
TCP/IP Protocol Model: Network (cont. ) • Network layer addressing (cont. ) – Types of addressing • Unicast (regular node addresses) • Broadcast (send to all nodes on a subnet) CISSP Guide to Security Essentials 84
TCP/IP Protocol Model: Network (cont. ) – Types of addressing (cont. ) • Multicast (send to a group of notes on different networks) • Anycast (send to only one of a group of nodes) CISSP Guide to Security Essentials 85
TCP/IP Protocol Model: Transport • TCP Protocol – Connection oriented, persistent connections, dedicated and ephemeral ports, sequencing, guaranteed delivery – Examples: FTP, HTTP, Telnet CISSP Guide to Security Essentials 86
TCP/IP Protocol Model: Transport (cont. ) • UDP Protocol – Connectionless, dedicated port numbers only, no sequencing, no guarantee of delivery – Examples: DNS, TFTP, Vo. IP CISSP Guide to Security Essentials 87
TCP/IP Protocol Model: Application • Topmost layer in the TCP/IP protocol stack • Protocols: DHCP, DNS, Finger, FTP, HTTP, LDAP, NFS, NIS, NTP, Rlogin, RPC, Rsh, SIP, SMTP, SNMP, Telnet, TFTP, Vo. IP, Whois CISSP Guide to Security Essentials 88
TCP/IP Routing Protocols • Router-to-router communication protocol used by routers to help determine the most efficient network routes between two nodes on a network • Helps routers make good routing decisions (making the right choice about which way to forward packets) CISSP Guide to Security Essentials 89
TCP/IP Routing Protocols (cont. ) • RIP (Routing Information Protocol) – one of the early routing protocols – Hop count the primary metric, maximum = 15 • IGRP (Interior Gateway Routing Protocol) – Cisco proprietary – Multiple metrics: hop count (max 255), bandwidth, delay, load, MTU, and reliability CISSP Guide to Security Essentials 90
TCP/IP Routing Protocols (cont. ) • EIGRP (Enhanced Interior Gateway Routing Protocol) – Cisco proprietary – Advances over IGRP including VLSM • OSPF (Open Shortest Path First) – Open standard for enterprise networks – Metric is “path cost” (primarily hops and speed) – Uses authentication to prevent route spoofing CISSP Guide to Security Essentials 91
TCP/IP Routing Protocols (cont. ) • BGP (Border Gateway Protocol) – the dominant Internet routing algorithm • IS-IS (Intermediate system to intermediate system) – used primarily by large ISP networks CISSP Guide to Security Essentials 92
Remote Access / Tunneling Protocols • Tunneling: encapsulating packets of one protocol within another – can include encryption – Reasons: protection of encapsulated protocol; hide details of intermediary network, authentication of traffic CISSP Guide to Security Essentials 93
Remote Access / Tunneling Protocols (cont. ) • Tunneling: (cont. ) – Protocols • VPN – generic term for tunneled (and usually encrypted) network connection from a public network to a private network CISSP Guide to Security Essentials 94
Remote Access / Tunneling Protocols (cont. ) – Protocols (cont. ) • • SSL / TLS SSH IPsec Others: L 2 TP, PPTP, SLIP CISSP Guide to Security Essentials 95
Authentication Protocols • RADIUS (Remote Authentication Dial In User Service) – Over-the-wire protocol from client to AAA (authentication, authorization, accounting) server • Diameter – more advanced RADIUS replacement CISSP Guide to Security Essentials 96
Authentication Protocols (cont. ) • TACACS (Terminal Access Controller Access. Control System) – authenticates user to a network. – Between access point or gateway and an AAA server • 802. 1 X – port level access control. System authenticates before user. CISSP Guide to Security Essentials 97
Authentication Protocols (cont. ) • CHAP (Challenge-Handshake Authentication Protocol) – Between client system and gateway • PPP uses CHAP CISSP Guide to Security Essentials 98
Authentication Protocols (cont. ) • EAP (Extensible Authentication Protocol) – Authentication Framework – used to authenticate users in wired and wireless networks. Used by WPA and WPA 2 wireless network standards. CISSP Guide to Security Essentials 99
Authentication Protocols (cont. ) • PEAP (Protected Extensible Authentication Protocol) – used in wireless networks to authenticate users – PEAP uses an SSL/TLS tunnel to encrypt authentication information • PAP (Password Authentication Protocol) – unsecure because protocol is unencrypted CISSP Guide to Security Essentials 100
Network Threats • The expressed potential for the occurrence of a harmful event such as an attack – Do. S / DDo. S – designed to flood or cause malfunction – Teardrop - attacker sends mangled packet fragments with overlapping and oversized payloads to a target system CISSP Guide to Security Essentials 101
Network Threats (cont. ) • Threats (cont. ) – Sequence number – guesses upcoming sequence numbers as a method for disrupting communications – Smurf - large number of forged ICMP echo requests. The packets are sent to a target network’s broadcast address, which causes all systems on the network to respond CISSP Guide to Security Essentials 102
Network Threats (cont. ) • Threats (cont. ) – Ping of Death – ICMP echo request, 64 k length – SYN flood – large volume of TCP SYN packets, consumes resources on target system – Worm – automated, self-replicating program CISSP Guide to Security Essentials 103
Network Threats (cont. ) • Threats (cont. ) – Spam – unsolicited commercial e-mail (UCE): fraud, malware, marketing – Phishing – emails luring users to fraudulent sites – Pharming – attack on DNS that redirects access to legitimate sites to imposter sites CISSP Guide to Security Essentials 104
Network Vulnerabilities • • Unnecessary open ports Unpatched systems Poor and outdated configurations Exposed cabling CISSP Guide to Security Essentials 105
Network Countermeasures • Access control lists • Firewalls • Intrusion Detection System (IDS) – Network based (NIDS) – Host based (HIDS) CISSP Guide to Security Essentials 106
Network Countermeasures (cont. ) • Intrusion Prevention System (IPS) – Network and host based • Protection of network cabling • Anti-virus software • Private addressing (10. *. *. *, etc. ) CISSP Guide to Security Essentials 107
Network Countermeasures (cont. ) • • Close unnecessary ports and services Security patches Unified Threat Management (UTM) Gateways – filtering intermediaries CISSP Guide to Security Essentials 108
Summary • Wired telecom technologies include DS-1 (T-1), SONET, Frame Relay, ATM, DSL, and MPLS • Wireless telecom technologies include CDMA 2000 (which includes 1 x. RTT and EVDO), GPRS, EDGE, UMTS, and Wi. MAX CISSP Guide to Security Essentials 109
Summary (cont. ) • Wired network technologies include Ethernet, ATM, Token Ring, USB, RS-232 • Wireless network technologies include Wi -Fi and Ir. DA CISSP Guide to Security Essentials 110
Summary (cont. ) • Ethernet is a frame technology that uses an 8 -octet address • The three network topologies are bus, ring, and star CISSP Guide to Security Essentials 111
Summary (cont. ) • Wi-Fi wireless networks can be secured by turning off SSID broadcast, using a non-default SSID, utilizing WPA or WPA 2 encryption, using user based authentication, and MAC based access control CISSP Guide to Security Essentials 112
Summary (cont. ) • The seven layers of OSI are: physical, data link, network, transport, session, presentation, and application • The five-layer of TCP/IP are: physical, data link, network / internet, transport, and application CISSP Guide to Security Essentials 113
Summary (cont. ) • Common tunneling (encapsulation) protocols are SSL, SSH, IPsec, L 2 TP, PPTP, and PPP • Common authentication protocols are RADIUS, Diameter, CHAP, EAP, and PEAP. TACACS and PAP are no longer widely used. CISSP Guide to Security Essentials 114
Summary (cont. ) • TCP/IP data link layer protocols are Ethernet, Token Ring, ATM, Frame Relay, and PPP • TCP/IP network layer protocols are IPv 4, IPv 6, ARP, RARP, ICMP, IGMP, and IPsec CISSP Guide to Security Essentials 115
Summary (cont. ) • TCP/IP transport layer protocols are TCP and UDP • TCP/IP application layer protocols are DHCP, DNS, FTP, HTTP, LDAP, NTP, RPC, SIP, SMTP, SNMP, TELNET, TFTP, and Vo. IP CISSP Guide to Security Essentials 116
Summary (cont. ) • Common network based attacks are Denial of Service (Do. S), Distributed Denial of Service (DDo. S), Teardrop, Sequence number, Smurf, Ping of Death, SYN flood, worms, spam, and phishing. CISSP Guide to Security Essentials 117
Summary (cont. ) • Common network based vulnerabilities are unneeded open ports, unpatched systems and devices, and misconfigured systems and devices. • Effective countermeasures are access control lists (ACLs), firewalls, intrusion… CISSP Guide to Security Essentials 118
Summary (cont. ) • …detection systems, intrusion prevention systems, private addressing, closing unnecessary ports and services, installing security patches, and using gateways. UTM devices that perform many defensive functions are gaining use. CISSP Guide to Security Essentials 119