Electronics and Telecommunications Research Institute ETRI Center by

Electronics and Telecommunications Research Institute (ETRI), Center by for National information security Supported Institute of technologies (CIST), Information and Communications KDDI R&D Laboratories Technology (NICT), Kyushu University, and Institute of Systems & Information Technologies/ KYUSHU (ISIT) collaborate 12/6/2020 1
CIST/ETRI/ISIT/KDDI/Kyushu Univ. /NICT Joint Research Workshop on Ubiquitous Network Security 2005 Nov. 16 -17, 2005 at Tokyo, Japan 12/6/2020 2

CIST/ETRI/ISIT/KDDI/Kyushu Univ. /NICT Joint Research Workshop on Ubiquitous Network Security 2005 Introduction of Institute of Systems & Information Technologies/ KYUSHU (ISIT) Speaker: Yoshifumi Ueshige (ISIT 2 nd Laboratory) 12/6/2020 3
About ISIT l Establishment: Dec. 1995 – This year is 10 years anniversary! – We hold Ceremony on 10 th birthday of ISIT on 18 Nov. l Purpose: to be a hub of Research institutions for IT l Fund: 300 million YEN – including 250 million YEN from FUKUOKA CITY l Staffs: 40 (including assistant staffs) l Activities: – – – 12/6/2020 R&D(Technology Transfer/Use of Advances in Research Exchange meetings Consulting Information gathering and offering Development of human resources 4
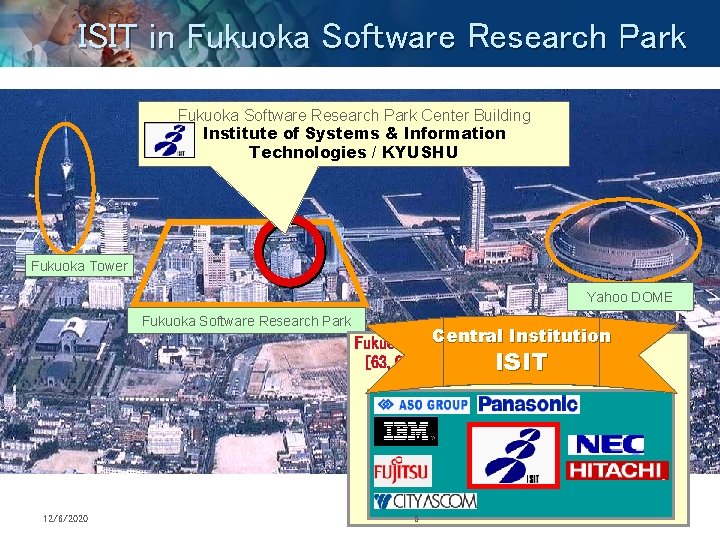
ISIT in Fukuoka Software Research Park Center Building Institute of Systems & Information Technologies / KYUSHU Fukuoka Tower Yahoo DOME Fukuoka Software Research Park 12/6/2020 Central Institution Fukuoka Software Research Park Area 2 [63, 000 m ] ISIT 5
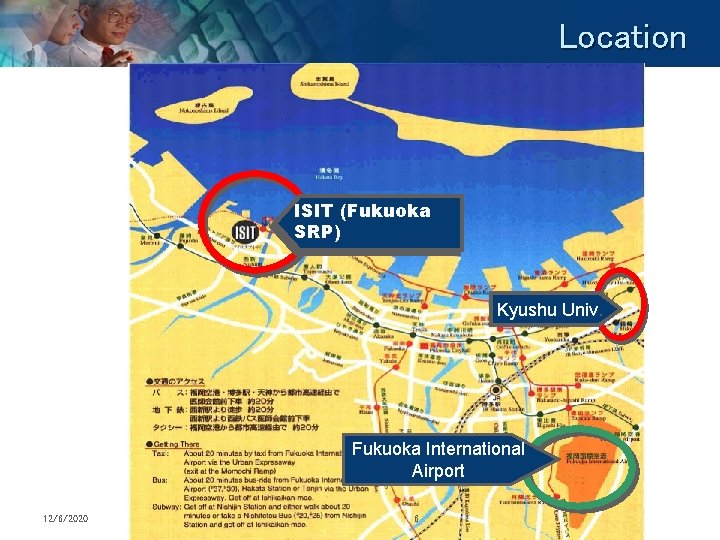
Location ISIT (Fukuoka SRP) Kyushu Univ. Fukuoka International Airport 12/6/2020 6
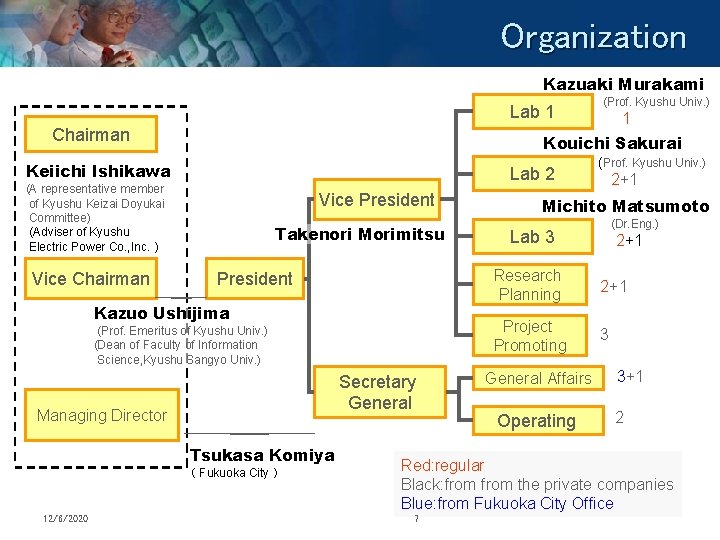
Organization Kazuaki Murakami (Prof. Kyushu Univ. ) Lab 1 Chairman Kouichi Sakurai Keiichi Ishikawa Lab 2 (A representative member of Kyushu Keizai Doyukai Committee) (Adviser of Kyushu Electric Power Co. , Inc.) Vice Chairman Vice President Takenori Morimitsu President Kazuo Ushijima (Prof. Emeritus of Kyushu Univ. ) (Dean of Faculty of Information Science, Kyushu Sangyo Univ. ) Secretary General Managing Director Tsukasa Komiya ( Fukuoka City ) 12/6/2020 1 (Prof. Kyushu Univ. ) 2+1 4 Michito Matsumoto Lab 3 3 (Dr. Eng. ) 2+1 Research Planning 2+1 Project Promoting 3 General Affairs Operating 3+1 2 Red: regular Black: from the private companies Blue: from Fukuoka City Office 7
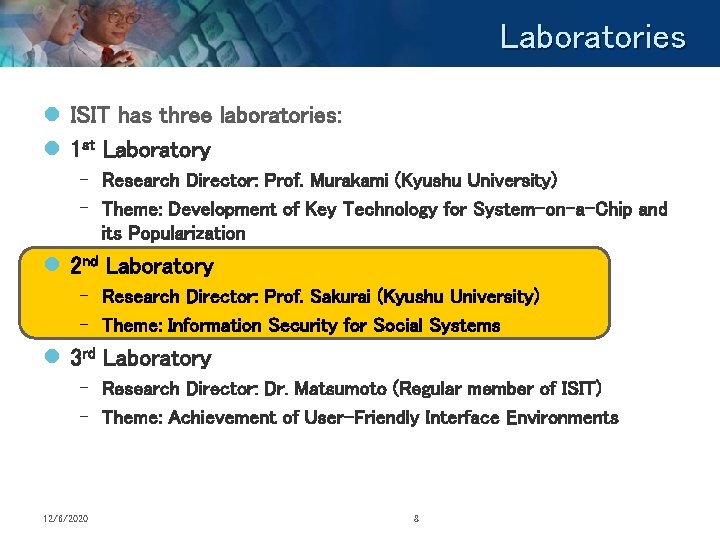
Laboratories l ISIT has three laboratories: l 1 st Laboratory – Research Director: Prof. Murakami (Kyushu University) – Theme: Development of Key Technology for System-on-a-Chip and its Popularization l 2 nd Laboratory – Research Director: Prof. Sakurai (Kyushu University) – Theme: Information Security for Social Systems l 3 rd Laboratory – Research Director: Dr. Matsumoto (Regular member of ISIT) – Theme: Achievement of User-Friendly Interface Environments 12/6/2020 8
CIST/ETRI/ISIT/KDDI/Kyushu Univ. /NICT Joint Research Workshop on Ubiquitous Network Security 2005 Introduction of 2 nd Laboratory 12/6/2020 9
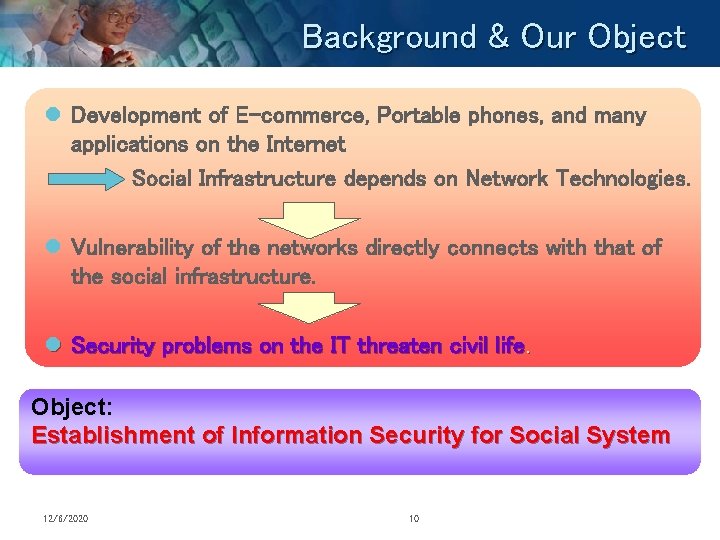
Background & Our Object l Development of E-commerce, Portable phones, and many applications on the Internet Social Infrastructure depends on Network Technologies. l Vulnerability of the networks directly connects with that of the social infrastructure. l Security problems on the IT threaten civil life. Object: Establishment of Information Security for Social System 12/6/2020 10

Research Policy l Information Security is achieved from efforts towards – Developing Technologies, – Managing and maintaining Systems, – Establishing Regulation and Laws. Technologies Secure Society Management 12/6/2020 11 Rules
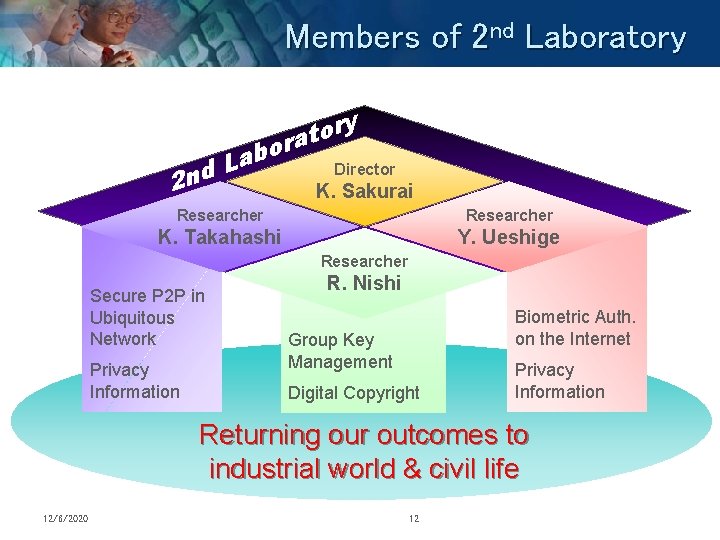
Members of 2 nd Laboratory 2 nd o b a L ry o t ra Director K. Sakurai Researcher K. Takahashi Y. Ueshige Researcher Secure P 2 P in Ubiquitous Network Privacy Information R. Nishi Biometric Auth. on the Internet Group Key Management Digital Copyright Privacy Information Returning our outcomes to industrial world & civil life 12/6/2020 12
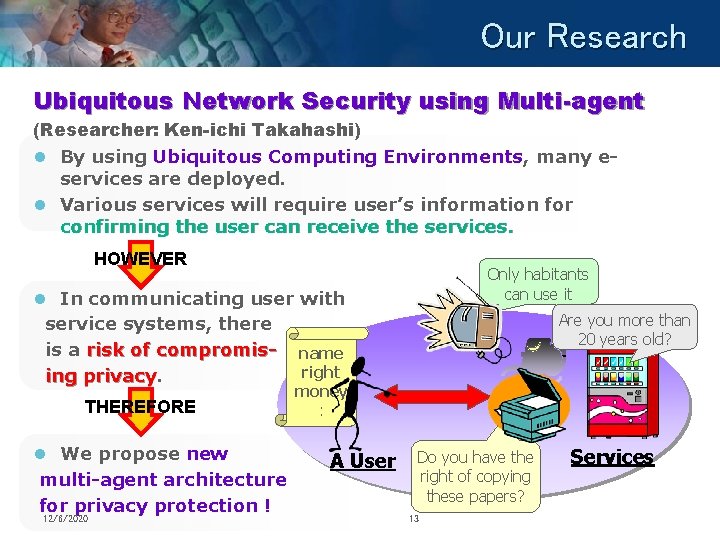
Our Research Ubiquitous Network Security using Multi-agent (Researcher: Ken-ichi Takahashi) l By using Ubiquitous Computing Environments, many eservices are deployed. l Various services will require user’s information for confirming the user can receive the services. HOWEVER Only habitants can use it l In communicating user with service systems, there is a risk of compromis- name right ing privacy THEREFORE l We propose new multi-agent architecture for privacy protection ! 12/6/2020 Are you more than 20 years old? money : A User Do you have the right of copying these papers? 13 Services
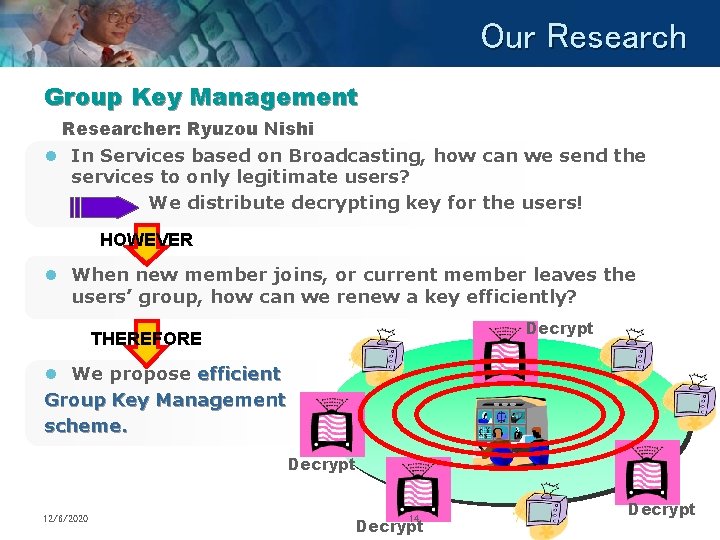
Our Research Group Key Management Researcher: Ryuzou Nishi l In Services based on Broadcasting, how can we send the services to only legitimate users? We distribute decrypting key for the users! HOWEVER l When new member joins, or current member leaves the users’ group, how can we renew a key efficiently? Decrypt THEREFORE l We propose efficient Group Key Management scheme. Decrypt 12/6/2020 14 Decrypt
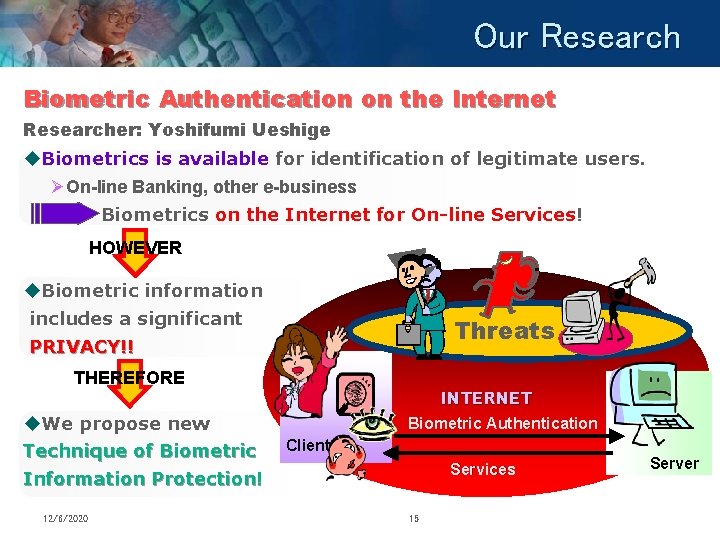
Our Research Biometric Authentication on the Internet Researcher: Yoshifumi Ueshige u. Biometrics is available for identification of legitimate users. ØOn-line Banking, other e-business Biometrics on the Internet for On-line Services! HOWEVER u. Biometric information includes a significant PRIVACY!! Threats THEREFORE u. We propose new Technique of Biometric Information Protection! 12/6/2020 INTERNET Biometric Authentication Client Services 15 Server
Towards Collaborations l We interact with other institutes and universities. – Electronics and Telecommunications Research Institute (ETRI), Korea : We exchange MOU. – Center of Information Security Technology (CIST), Korea University, Korea – Kyushu University, Japan – Institute for Infocomm. Research (I 2 R), Singapore – Institute of Information Security, Japan – Etc. 12/6/2020 16

CIST/ETRI/ISIT/KDDI/Kyushu Univ. /NICT Joint Research Workshop on Ubiquitous Network Security 2005 Thank you for your attention. Institute of Systems & Information Technologies/ KYUSHU 12/6/2020 17
- Slides: 17