Computer Security Incident Handling Guide Chapters 4 5
- Slides: 28
Computer Security Incident Handling Guide (Chapters 4, 5, 6 and 8) NIST 800 -61 Presented by: Emily Ecoff April 22, 2008
Denial of Service Incidents A denial of service (Do. S) is an action that prevents or impairs the authorized use of networks, systems, or applications by exhausting resources such as central processing units, memory, bandwidth, or disk space. � Examples: � › Using all available network bandwidth by generating unusually large volumes of traffic › Sending malformed TCP/IP packets to a server so that its operating system will crash › Sending illegal requests to an application to crash it › Making many processor-intensive requests so that the server’s processing resources are full › Consuming all available disk space by creating many large files
Distributed Denial of Service Attacks Network bandwidth is so large for most organizations that a single attacking machine cannot cause a network Do. S. � DDo. S attacks coordinate an attack among many computers � Lack of availability of computing and network services causes significant disruption an major financial lost � Two types of components: � › Agents: which run on compromised hosts and perform the actual attacks (bots) › Handler: which is a program that controls the agents, telling them when, what, and how to attack.
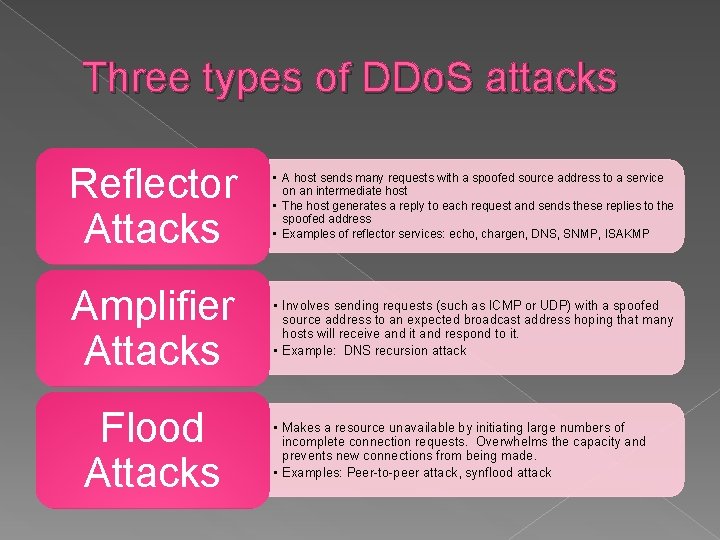
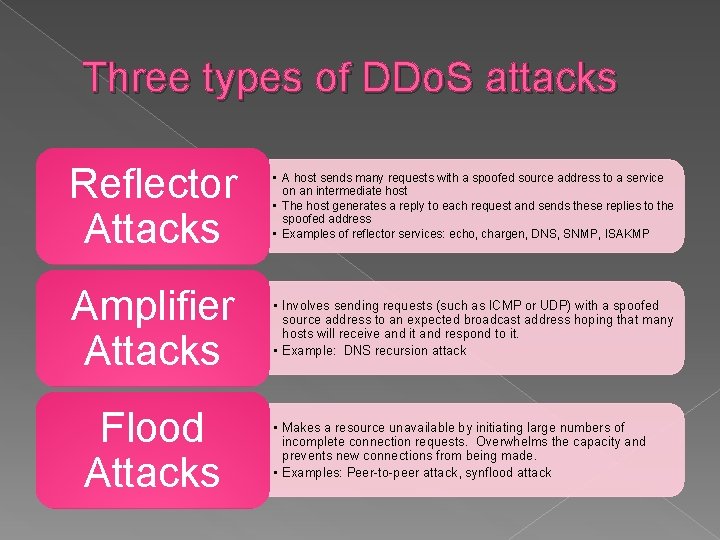
Three types of DDo. S attacks Reflector Attacks • A host sends many requests with a spoofed source address to a service on an intermediate host • The host generates a reply to each request and sends these replies to the spoofed address • Examples of reflector services: echo, chargen, DNS, SNMP, ISAKMP Amplifier Attacks • Involves sending requests (such as ICMP or UDP) with a spoofed source address to an expected broadcast address hoping that many hosts will receive and it and respond to it. • Example: DNS recursion attack Flood Attacks • Makes a resource unavailable by initiating large numbers of incomplete connection requests. Overwhelms the capacity and prevents new connections from being made. • Examples: Peer-to-peer attack, synflood attack
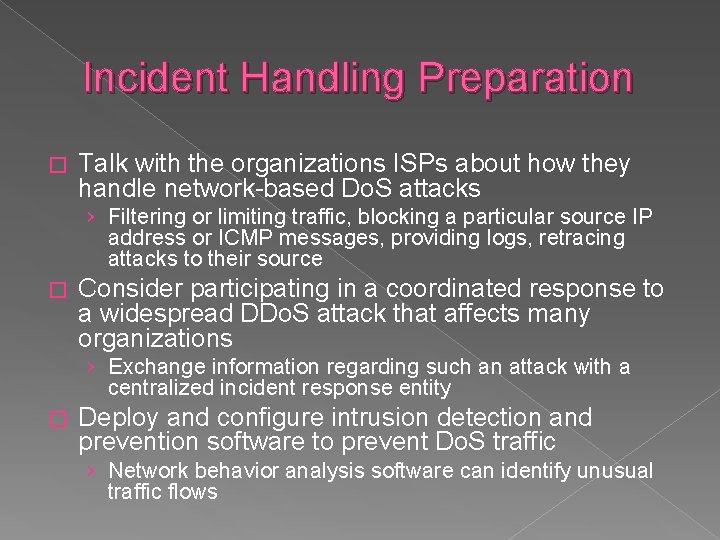
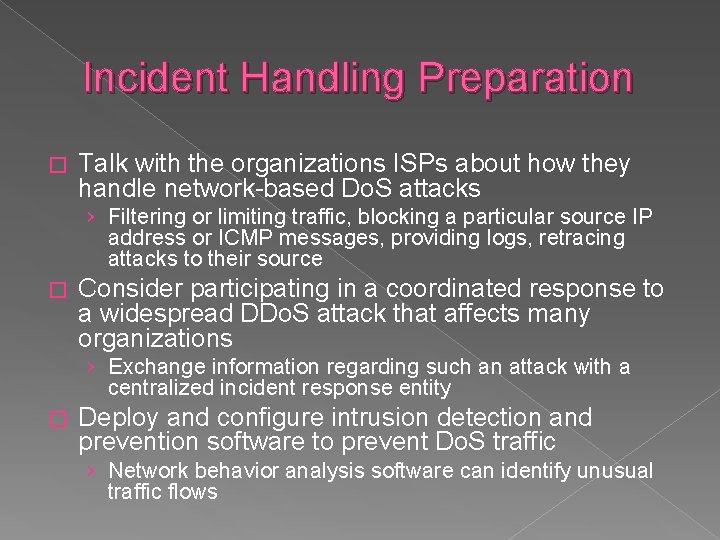
Incident Handling Preparation � Talk with the organizations ISPs about how they handle network-based Do. S attacks › Filtering or limiting traffic, blocking a particular source IP address or ICMP messages, providing logs, retracing attacks to their source � Consider participating in a coordinated response to a widespread DDo. S attack that affects many organizations › Exchange information regarding such an attack with a centralized incident response entity � Deploy and configure intrusion detection and prevention software to prevent Do. S traffic › Network behavior analysis software can identify unusual traffic flows
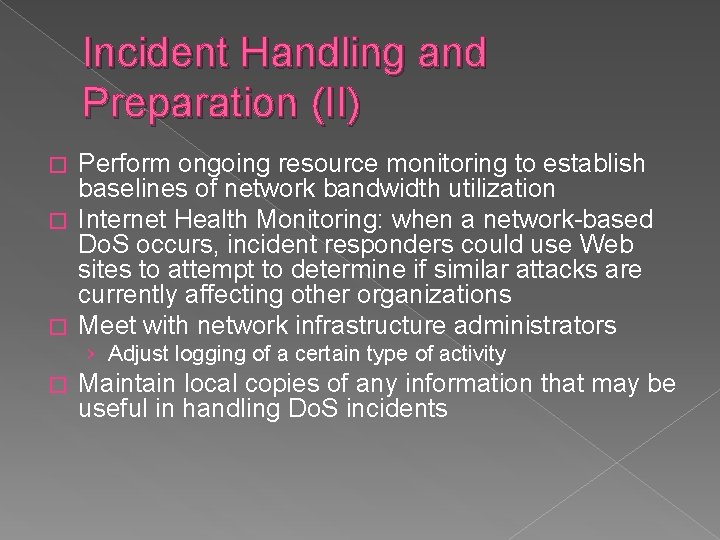
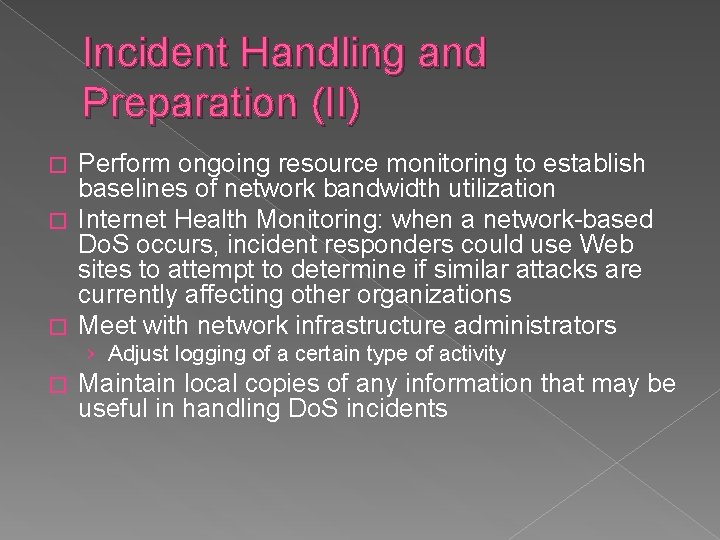
Incident Handling and Preparation (II) Perform ongoing resource monitoring to establish baselines of network bandwidth utilization � Internet Health Monitoring: when a network-based Do. S occurs, incident responders could use Web sites to attempt to determine if similar attacks are currently affecting other organizations � Meet with network infrastructure administrators � › Adjust logging of a certain type of activity � Maintain local copies of any information that may be useful in handling Do. S incidents
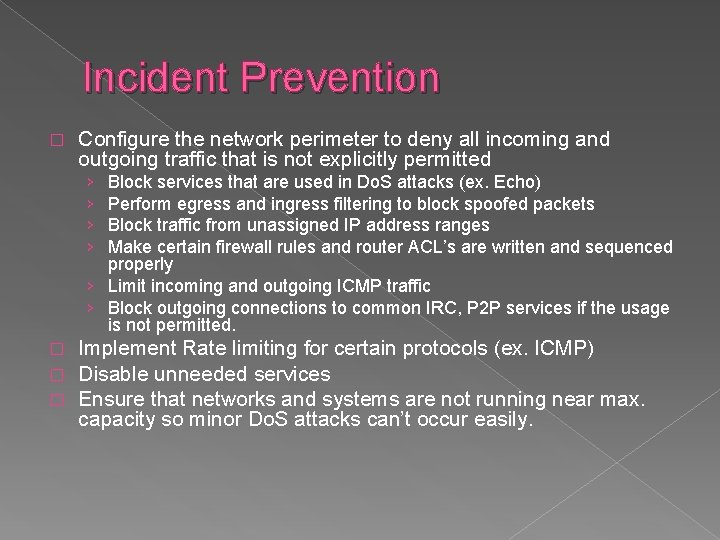
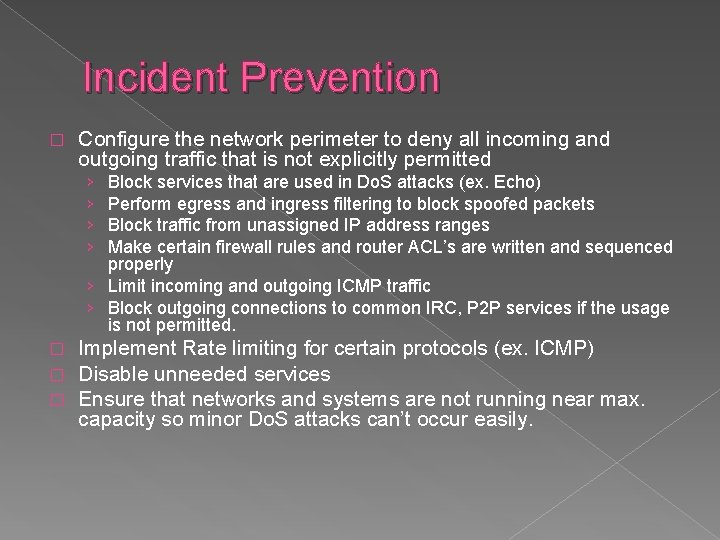
Incident Prevention � Configure the network perimeter to deny all incoming and outgoing traffic that is not explicitly permitted › › Block services that are used in Do. S attacks (ex. Echo) Perform egress and ingress filtering to block spoofed packets Block traffic from unassigned IP address ranges Make certain firewall rules and router ACL’s are written and sequenced properly › Limit incoming and outgoing ICMP traffic › Block outgoing connections to common IRC, P 2 P services if the usage is not permitted. � � � Implement Rate limiting for certain protocols (ex. ICMP) Disable unneeded services Ensure that networks and systems are not running near max. capacity so minor Do. S attacks can’t occur easily.
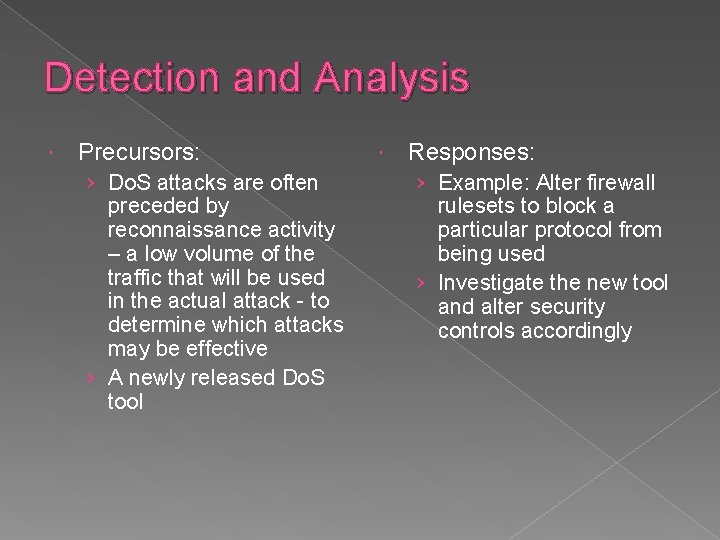
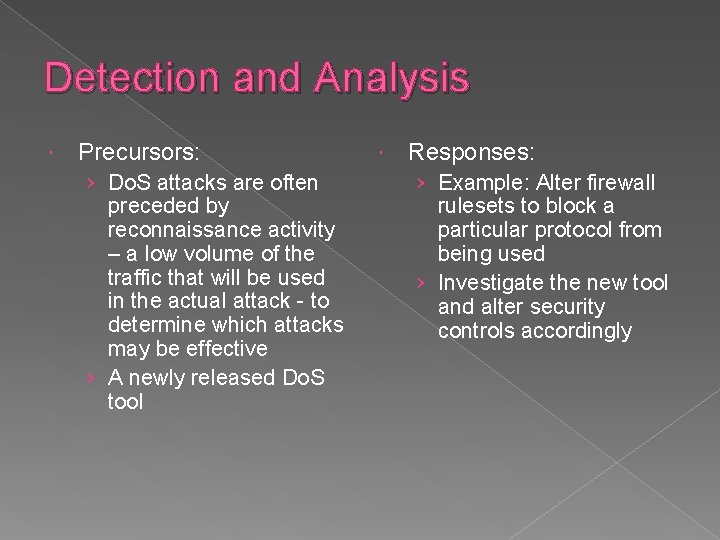
Detection and Analysis Precursors: › Do. S attacks are often preceded by reconnaissance activity – a low volume of the traffic that will be used in the actual attack - to determine which attacks may be effective › A newly released Do. S tool Responses: › Example: Alter firewall rulesets to block a particular protocol from being used › Investigate the new tool and alter security controls accordingly
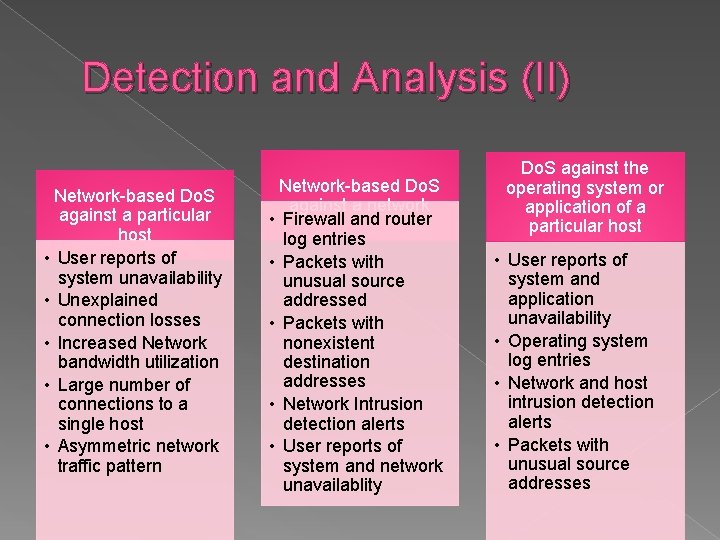
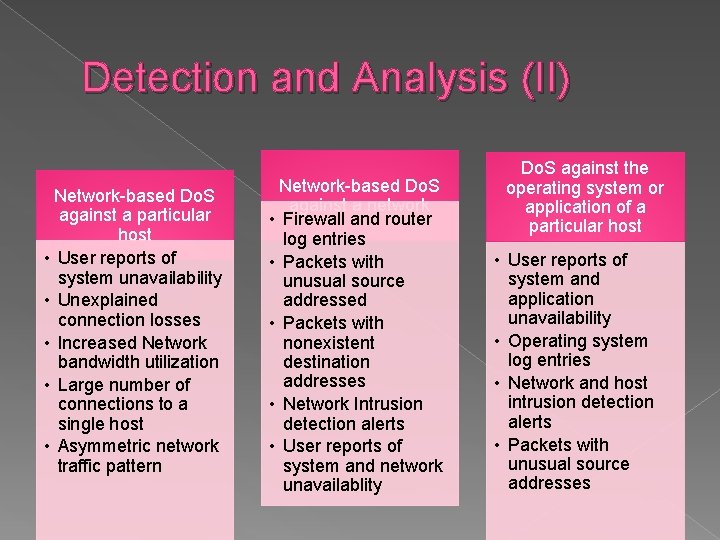
Detection and Analysis (II) Network-based Do. S against a particular host • User reports of system unavailability • Unexplained connection losses • Increased Network bandwidth utilization • Large number of connections to a single host • Asymmetric network traffic pattern Network-based Do. S against a network • Firewall and router log entries • Packets with unusual source addressed • Packets with nonexistent destination addresses • Network Intrusion detection alerts • User reports of system and network unavailablity Do. S against the operating system or application of a particular host • User reports of system and application unavailability • Operating system log entries • Network and host intrusion detection alerts • Packets with unusual source addresses
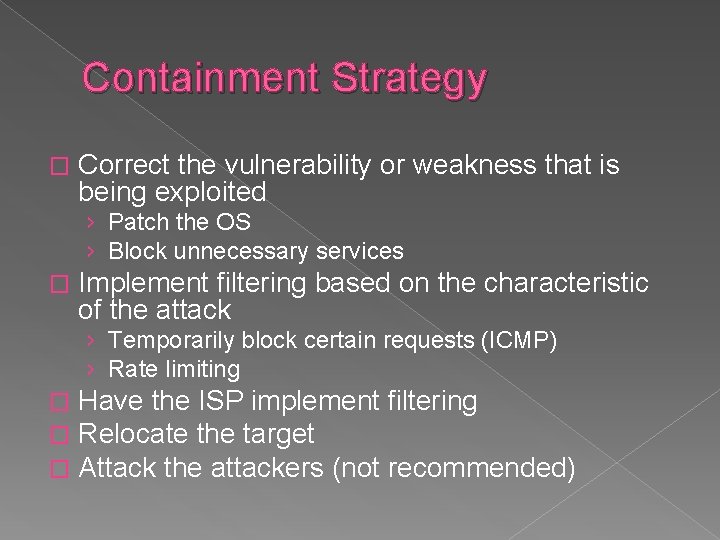
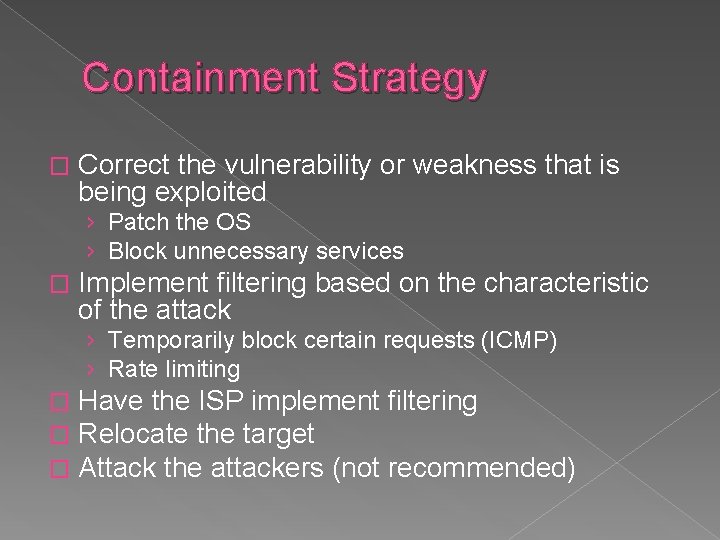
Containment Strategy � Correct the vulnerability or weakness that is being exploited › Patch the OS › Block unnecessary services � Implement filtering based on the characteristic of the attack › Temporarily block certain requests (ICMP) › Rate limiting � � � Have the ISP implement filtering Relocate the target Attack the attackers (not recommended)
Evidence Gathering and Handling � Identify the source of the attack from observed traffic (very difficult) � Trace attacks back through ISPs (easier if attack is ongoing) � Review Log Entries (Some may be overwritten depending on logging practices)
Recommendations � Configure firewall rulesets to prevent reflector attacks › Reject suspicious combinations of source and destination ports � Configure border routers to prevent amplifier attacks › Do not forward directed broadcasts Determine how ISP can assist Configure security software Perimeter security – deny all incoming and outgoing traffic not expressly permitted � Create a containment strategy that includes several solutions in sequence � � �
Malicious Code � Viruses – designed to self-replicated › Compiled viruses: executed by the operating system �File Infector viruses: Attach themselves to an executable program �Boot Sector viruses: Infects the master boot record of a hard drive or removable media › Interpreted viruses: executed by an application (most common) �Macro viruses: Attach themselves to application documents �Script viruses: Similar to a macro but written in a language understood by the OS
Malicious Code � Worms – self-replicating programs that are completely self-contained. › Network Service Worms: spread by exploiting a vulnerability in a network service associated with an OS or an application › Mass Mailing Worms: Similar to email-borne viruses but are self-contained instead of infecting an existing file. Trojan Horses – non-replicating programs that appear to be benign but actually have a hidden malicious purpose � Others: � › › Malicious Mobile Code Blended Attack (Ex: Nimda worm) Tracking Cookies Attacker Tools: � Backdoors � Keystroke Loggers � Rootkits � Web browser plug-ins › Non-Malware Threats: � Social Engineering � Phishing � Virus Hoaxes
Incident Prevention � � � � � Use Antivirus Software Prevent the installation of Spyware Block suspicious files Filtering Spam Limit the use of nonessential programs with file transfer capabilities (IM, P 2 P, etc. ) Educate users about email attachments Eliminate Open Window Shares Use Web Browser Security to Limit Mobile Code Prevent open relaying of email Configure email clients to act more securely
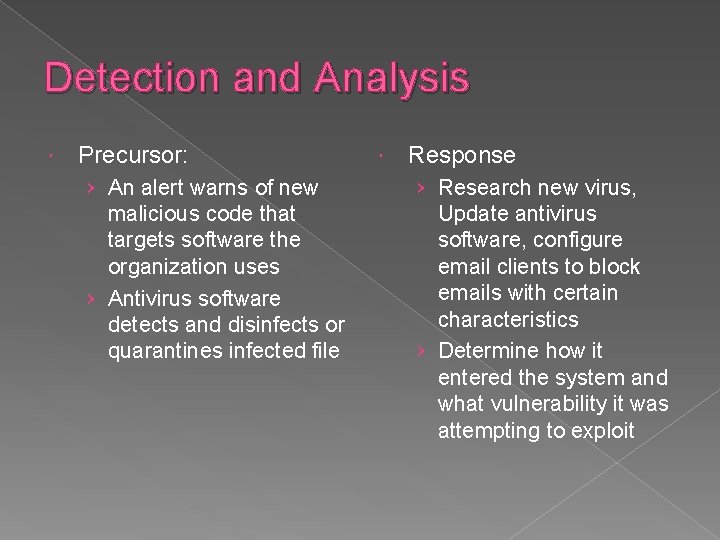
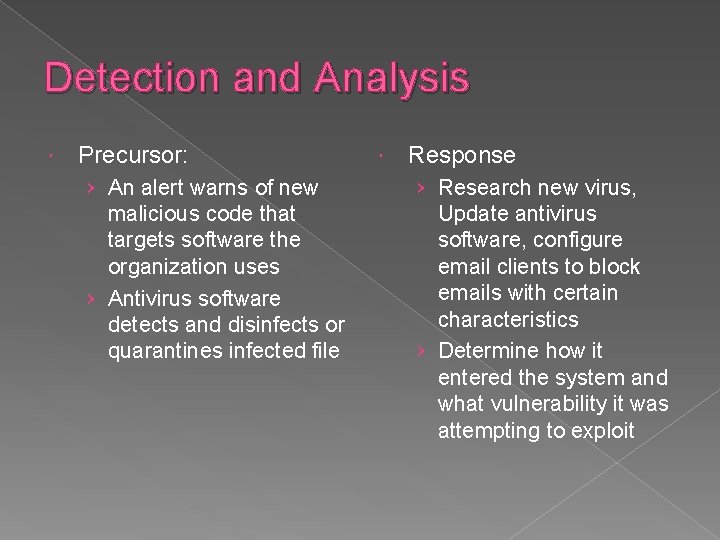
Detection and Analysis Precursor: › An alert warns of new malicious code that targets software the organization uses › Antivirus software detects and disinfects or quarantines infected file Response › Research new virus, Update antivirus software, configure email clients to block emails with certain characteristics › Determine how it entered the system and what vulnerability it was attempting to exploit
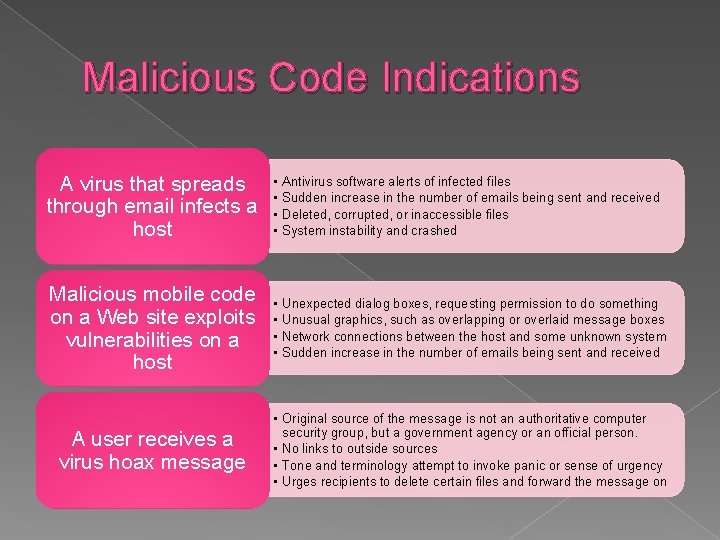
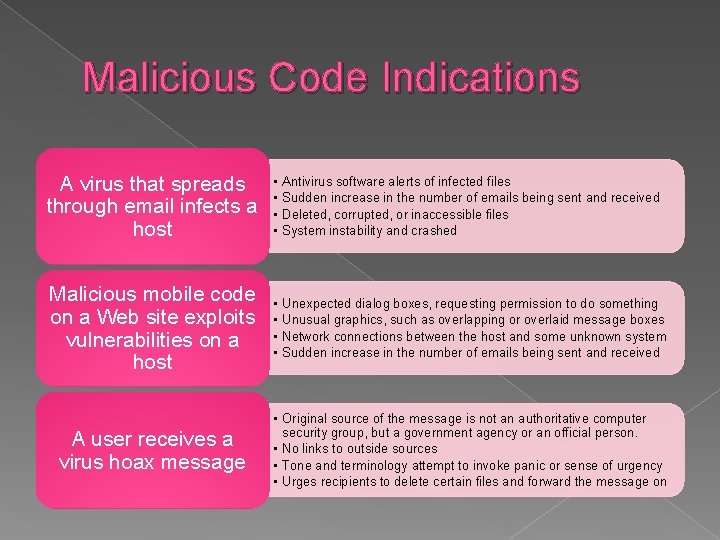
Malicious Code Indications A virus that spreads through email infects a host • • Antivirus software alerts of infected files Sudden increase in the number of emails being sent and received Deleted, corrupted, or inaccessible files System instability and crashed Malicious mobile code on a Web site exploits vulnerabilities on a host • • Unexpected dialog boxes, requesting permission to do something Unusual graphics, such as overlapping or overlaid message boxes Network connections between the host and some unknown system Sudden increase in the number of emails being sent and received A user receives a virus hoax message • Original source of the message is not an authoritative computer security group, but a government agency or an official person. • No links to outside sources • Tone and terminology attempt to invoke panic or sense of urgency • Urges recipients to delete certain files and forward the message on
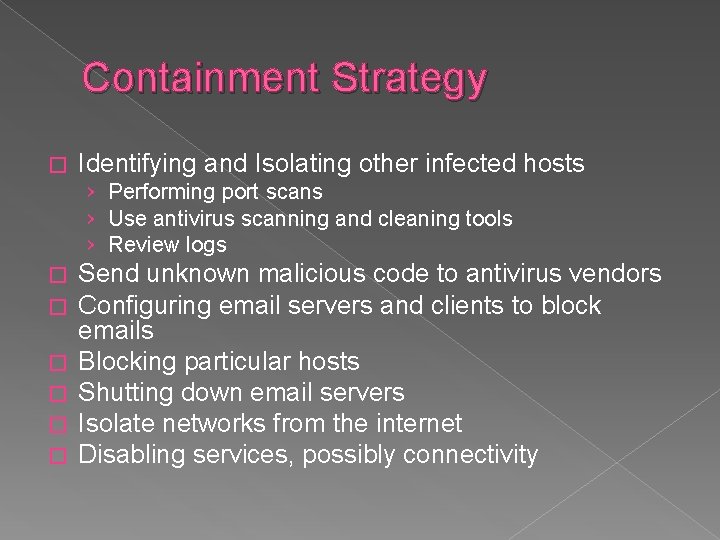
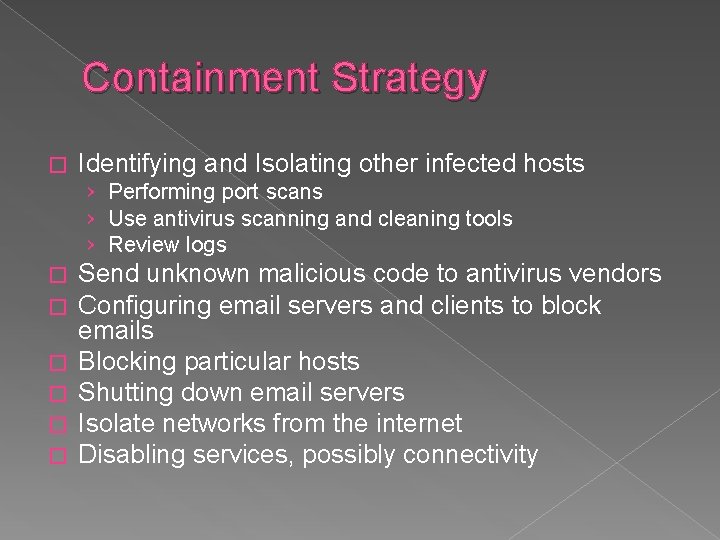
Containment Strategy � Identifying and Isolating other infected hosts › Performing port scans › Use antivirus scanning and cleaning tools › Review logs � � � Send unknown malicious code to antivirus vendors Configuring email servers and clients to block emails Blocking particular hosts Shutting down email servers Isolate networks from the internet Disabling services, possibly connectivity
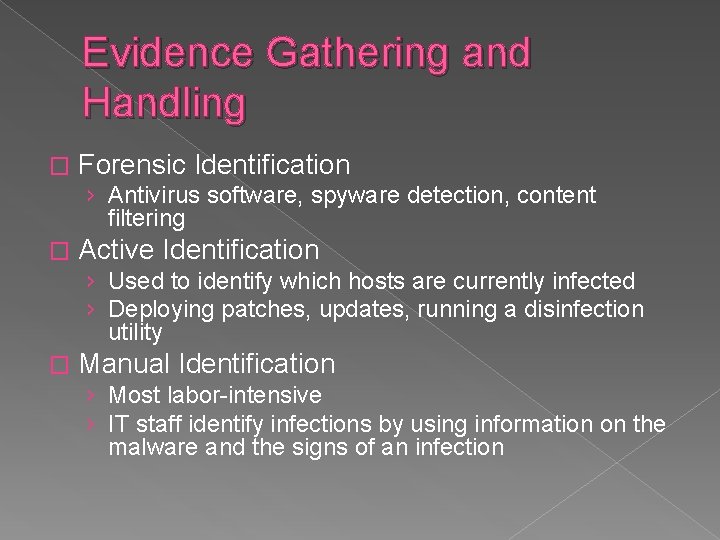
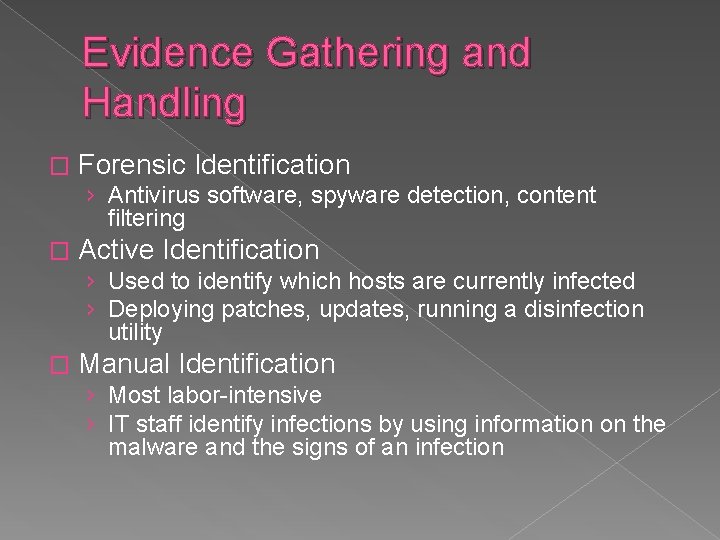
Evidence Gathering and Handling � Forensic Identification › Antivirus software, spyware detection, content filtering � Active Identification › Used to identify which hosts are currently infected › Deploying patches, updates, running a disinfection utility � Manual Identification › Most labor-intensive › IT staff identify infections by using information on the malware and the signs of an infection
Recommendations Make users aware of malicious code issues – Education!! � Read antivirus bulletins � Use antivirus software and update regularly � Configure software to block suspicious files � Eliminate open window shares � Contain malicious code incidents as fast as possible � Deploy host-based intrusion detection and prevention systems �
Handling Unauthorized Access Incidents An unauthorized access incident occurs when a person gains access to resources that the person was not intended to have. It is typically gained through the exploitation of operating system or application vulnerabilities, the acquisition of usernames and passwords, or social engineering. � Examples: � › Guessing or cracking passwords › Viewing or copying sensitive data › Running a packet sniffer on a workstation to capture usernames and passwords › Using an unattended, logged-in workstation without permission
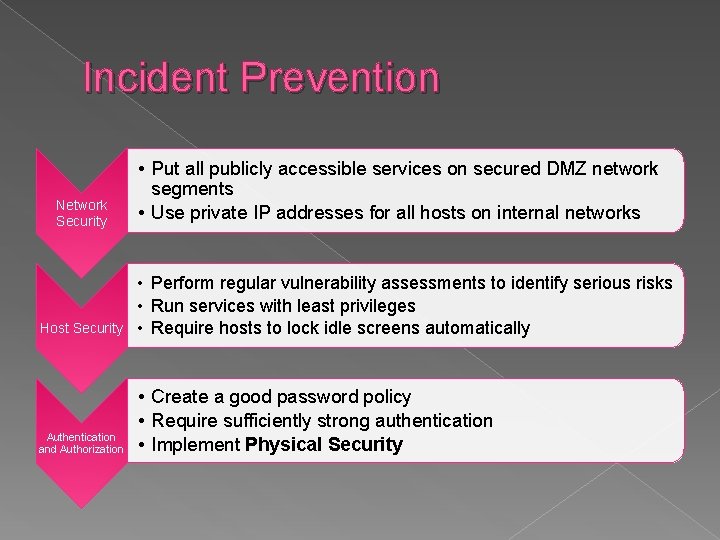
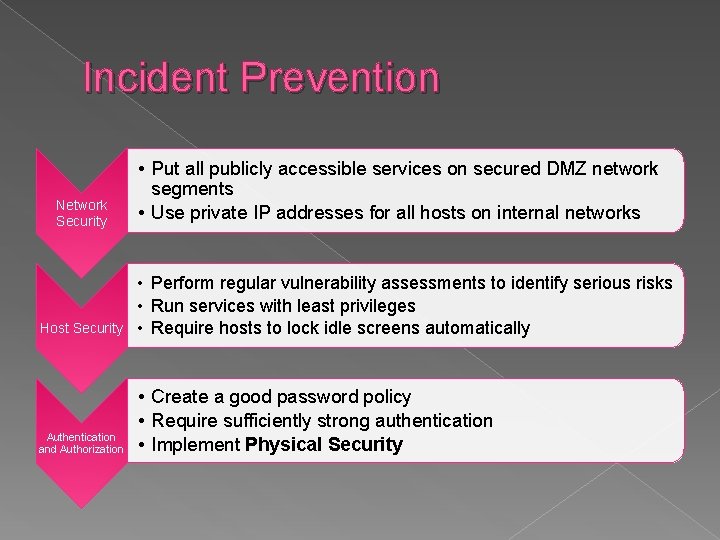
Incident Prevention Network Security • Put all publicly accessible services on secured DMZ network segments • Use private IP addresses for all hosts on internal networks Host Security • Perform regular vulnerability assessments to identify serious risks • Run services with least privileges • Require hosts to lock idle screens automatically Authentication and Authorization • Create a good password policy • Require sufficiently strong authentication • Implement Physical Security
Detection and Analysis � Precursors: › Users report possible social engineering attacks �Response: Give advice to all users on how to handle social engineering attempts › A person or system may observe a failed physical access attempt �Response: Detain the person. Strengthen physical and computer security controls if necessary
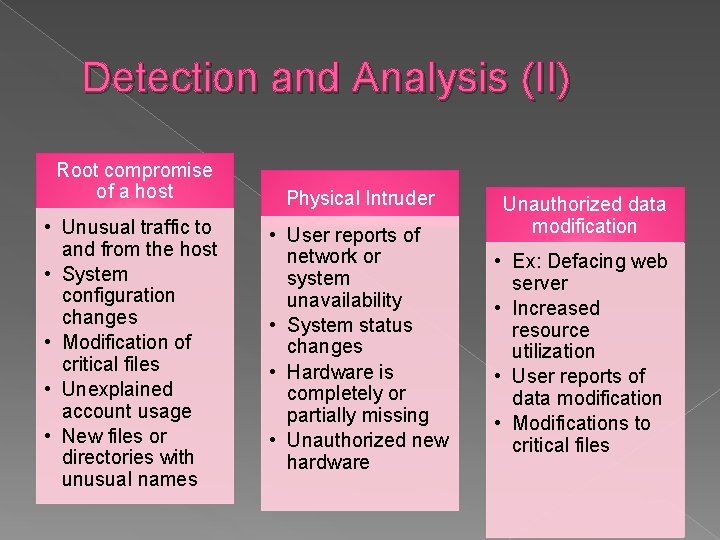
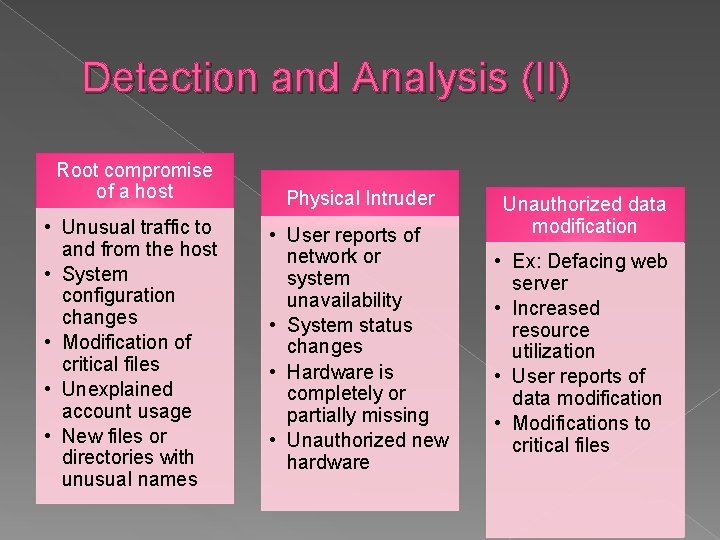
Detection and Analysis (II) Root compromise of a host • Unusual traffic to and from the host • System configuration changes • Modification of critical files • Unexplained account usage • New files or directories with unusual names Physical Intruder • User reports of network or system unavailability • System status changes • Hardware is completely or partially missing • Unauthorized new hardware Unauthorized data modification • Ex: Defacing web server • Increased resource utilization • User reports of data modification • Modifications to critical files
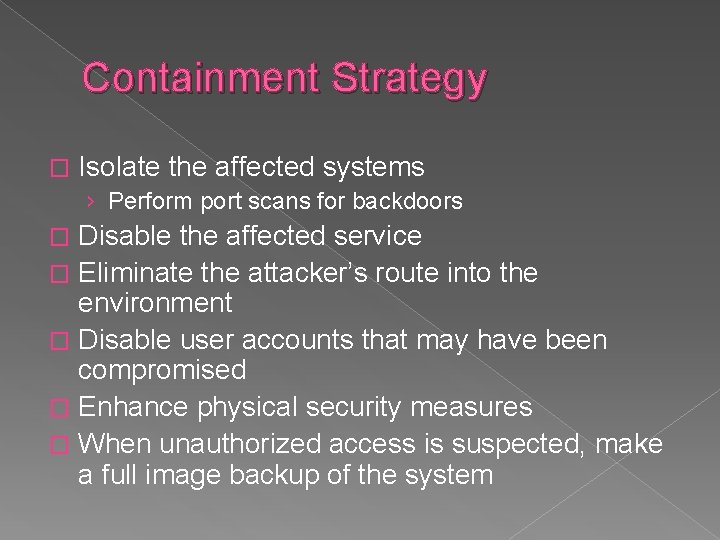
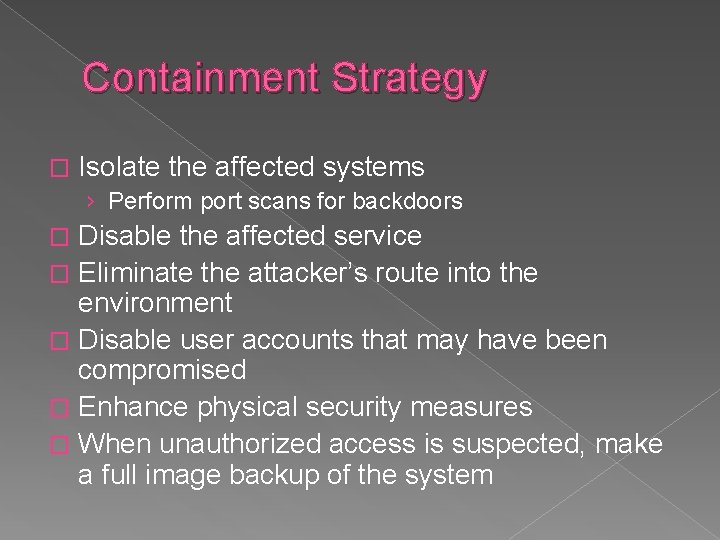
Containment Strategy � Isolate the affected systems › Perform port scans for backdoors Disable the affected service � Eliminate the attacker’s route into the environment � Disable user accounts that may have been compromised � Enhance physical security measures � When unauthorized access is suspected, make a full image backup of the system �
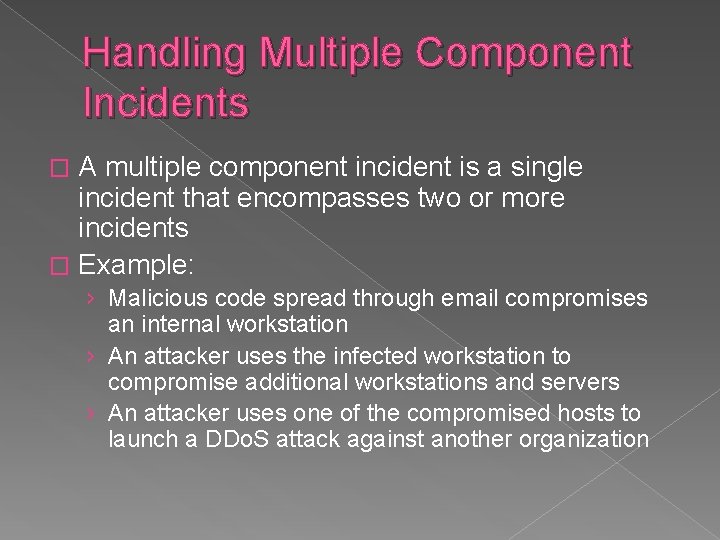
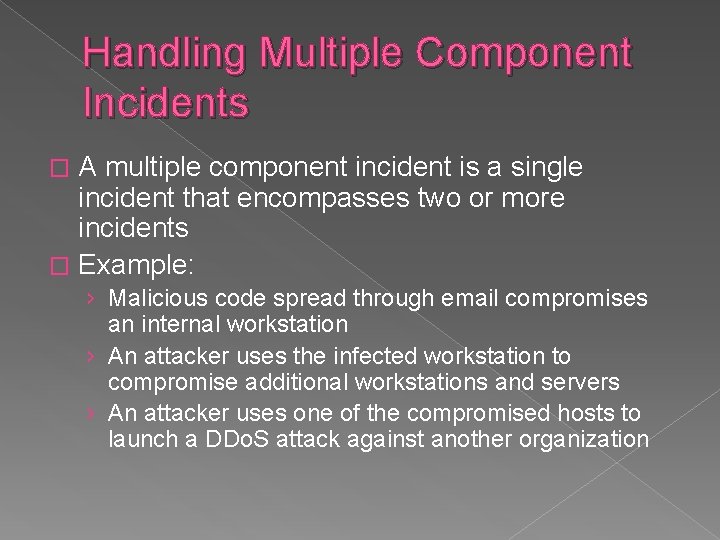
Handling Multiple Component Incidents A multiple component incident is a single incident that encompasses two or more incidents � Example: � › Malicious code spread through email compromises an internal workstation › An attacker uses the infected workstation to compromise additional workstations and servers › An attacker uses one of the compromised hosts to launch a DDo. S attack against another organization
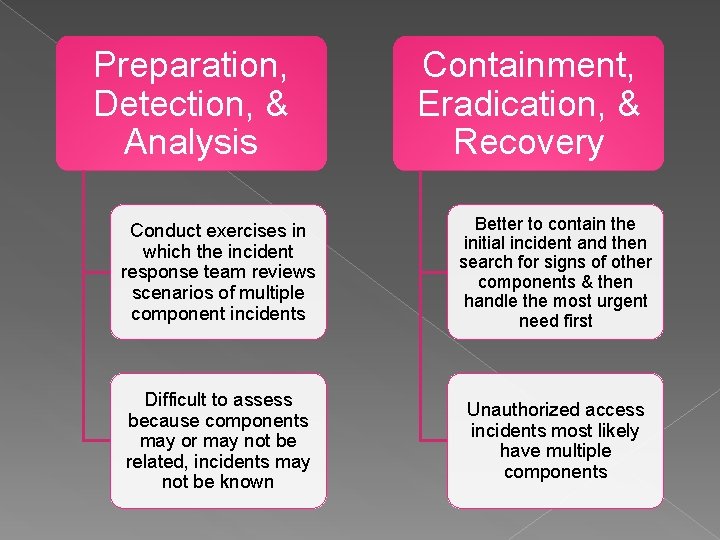
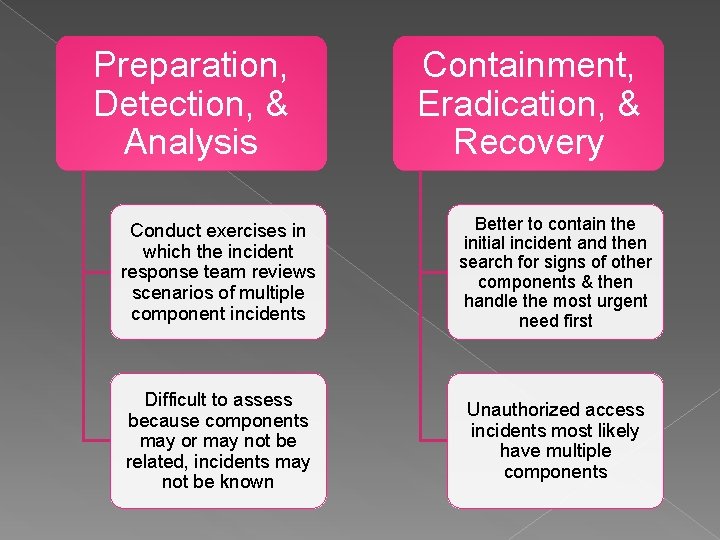
Preparation, Detection, & Analysis Containment, Eradication, & Recovery Conduct exercises in which the incident response team reviews scenarios of multiple component incidents Better to contain the initial incident and then search for signs of other components & then handle the most urgent need first Difficult to assess because components may or may not be related, incidents may not be known Unauthorized access incidents most likely have multiple components