Cyber Security Incident Response Playbooks Version v 1
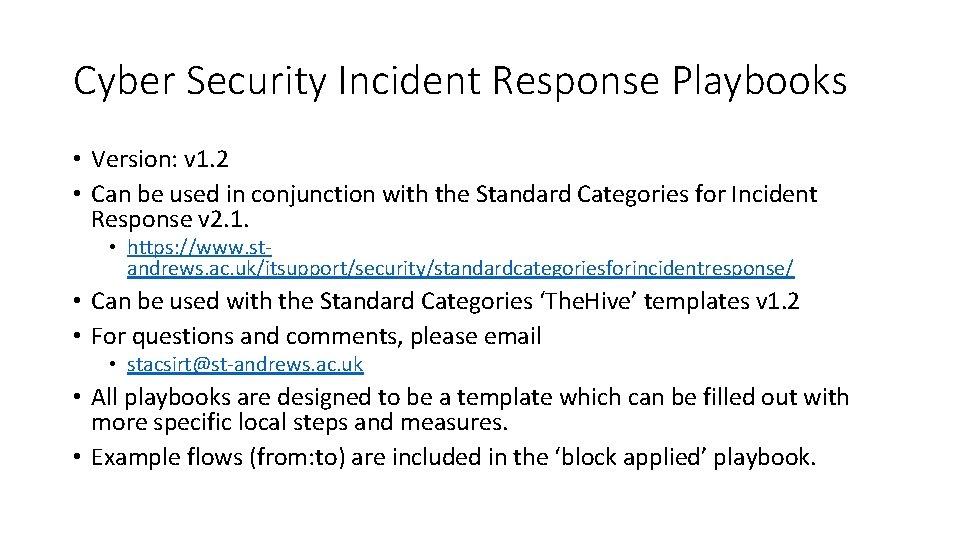
Cyber Security Incident Response Playbooks • Version: v 1. 2 • Can be used in conjunction with the Standard Categories for Incident Response v 2. 1. • https: //www. standrews. ac. uk/itsupport/security/standardcategoriesforincidentresponse/ • Can be used with the Standard Categories ‘The. Hive’ templates v 1. 2 • For questions and comments, please email • stacsirt@st-andrews. ac. uk • All playbooks are designed to be a template which can be filled out with more specific local steps and measures. • Example flows (from: to) are included in the ‘block applied’ playbook.
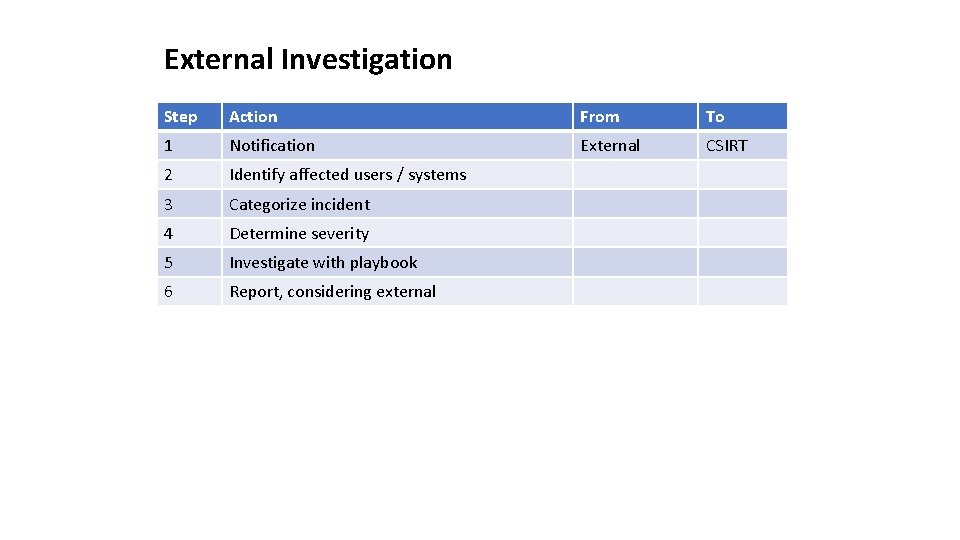
External Investigation Step Action From To 1 Notification External CSIRT 2 Identify affected users / systems 3 Categorize incident 4 Determine severity 5 Investigate with playbook 6 Report, considering external
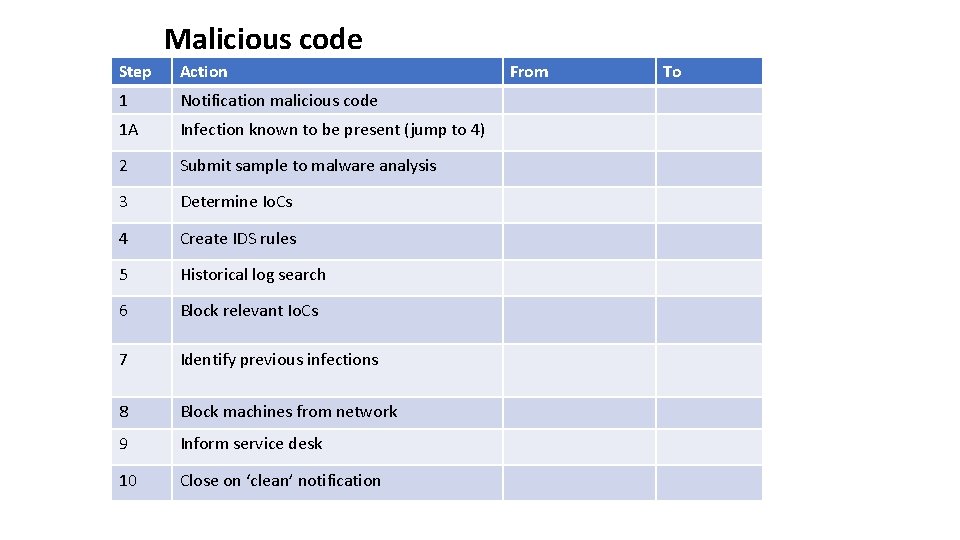
Malicious code Step Action 1 Notification malicious code 1 A Infection known to be present (jump to 4) 2 Submit sample to malware analysis 3 Determine Io. Cs 4 Create IDS rules 5 Historical log search 6 Block relevant Io. Cs 7 Identify previous infections 8 Block machines from network 9 Inform service desk 10 Close on ‘clean’ notification From To
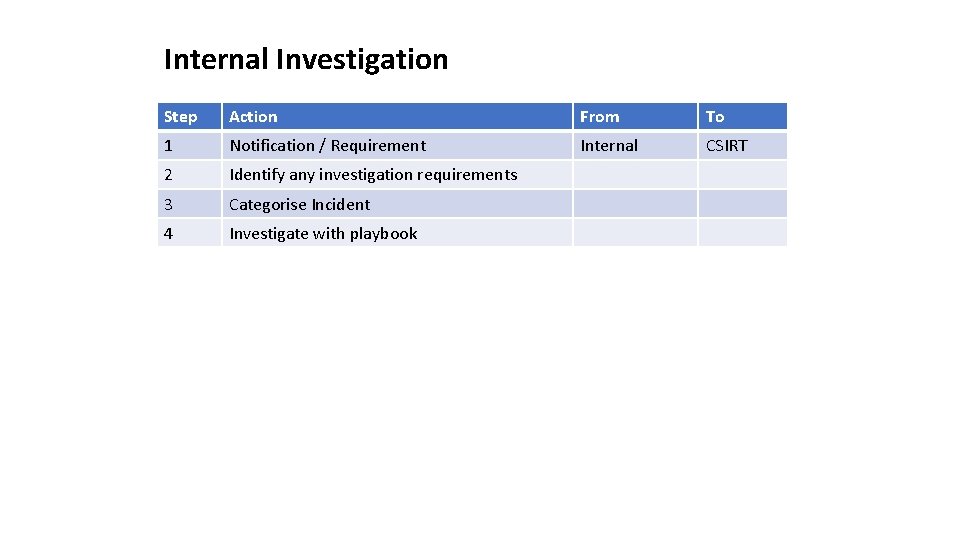
Internal Investigation Step Action From To 1 Notification / Requirement Internal CSIRT 2 Identify any investigation requirements 3 Categorise Incident 4 Investigate with playbook
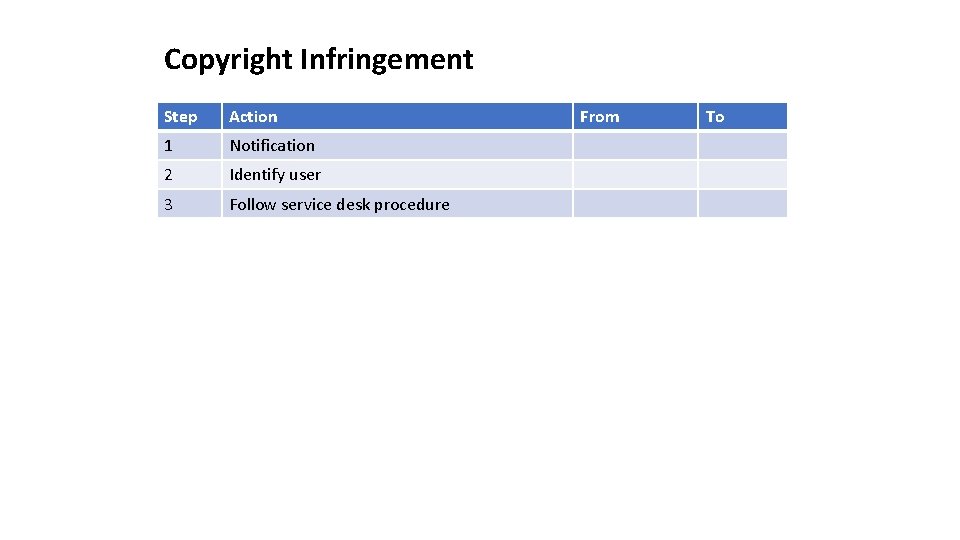
Copyright Infringement Step Action 1 Notification 2 Identify user 3 Follow service desk procedure From To
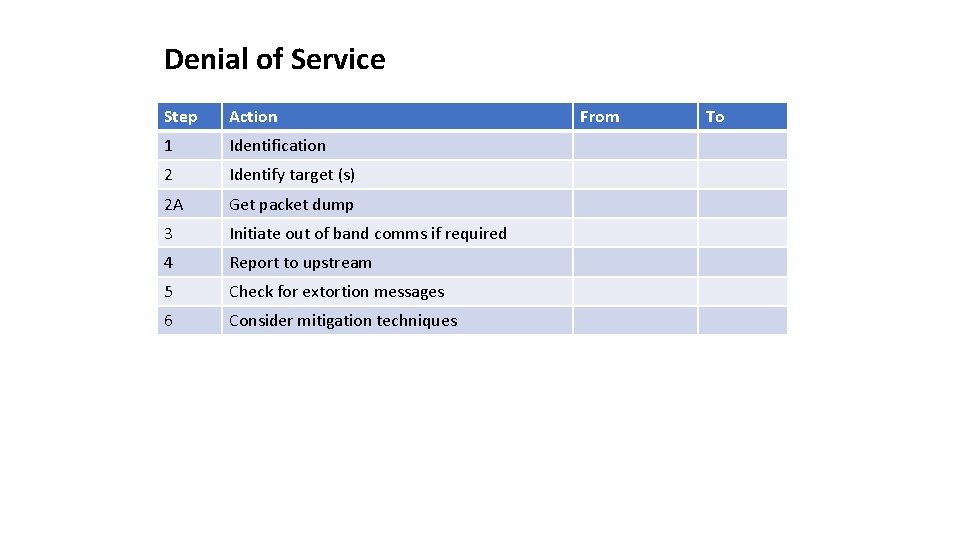
Denial of Service Step Action 1 Identification 2 Identify target (s) 2 A Get packet dump 3 Initiate out of band comms if required 4 Report to upstream 5 Check for extortion messages 6 Consider mitigation techniques From To
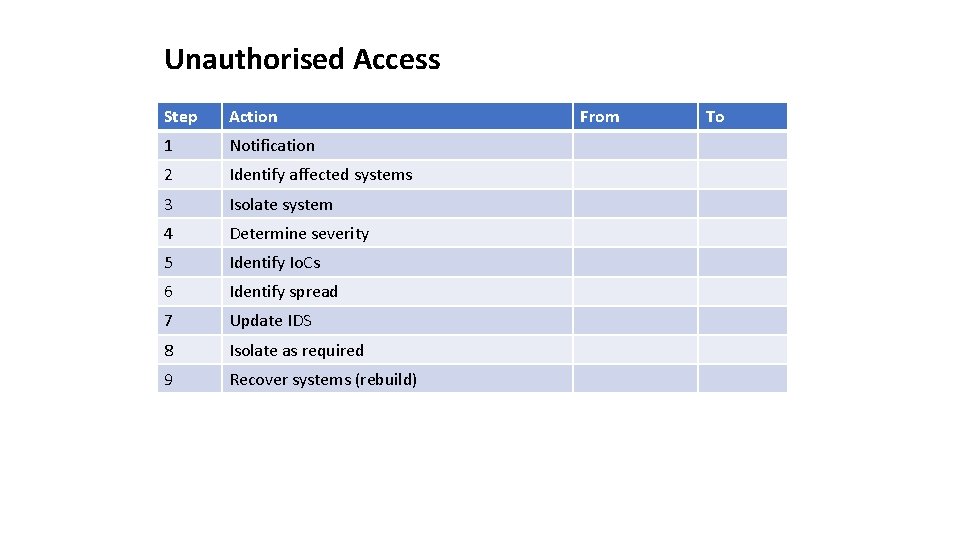
Unauthorised Access Step Action 1 Notification 2 Identify affected systems 3 Isolate system 4 Determine severity 5 Identify Io. Cs 6 Identify spread 7 Update IDS 8 Isolate as required 9 Recover systems (rebuild) From To
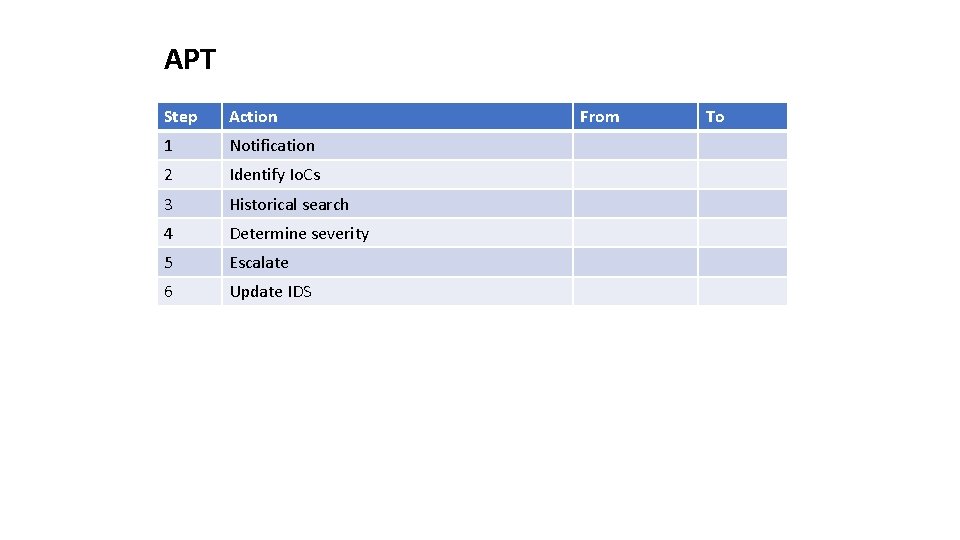
APT Step Action 1 Notification 2 Identify Io. Cs 3 Historical search 4 Determine severity 5 Escalate 6 Update IDS From To
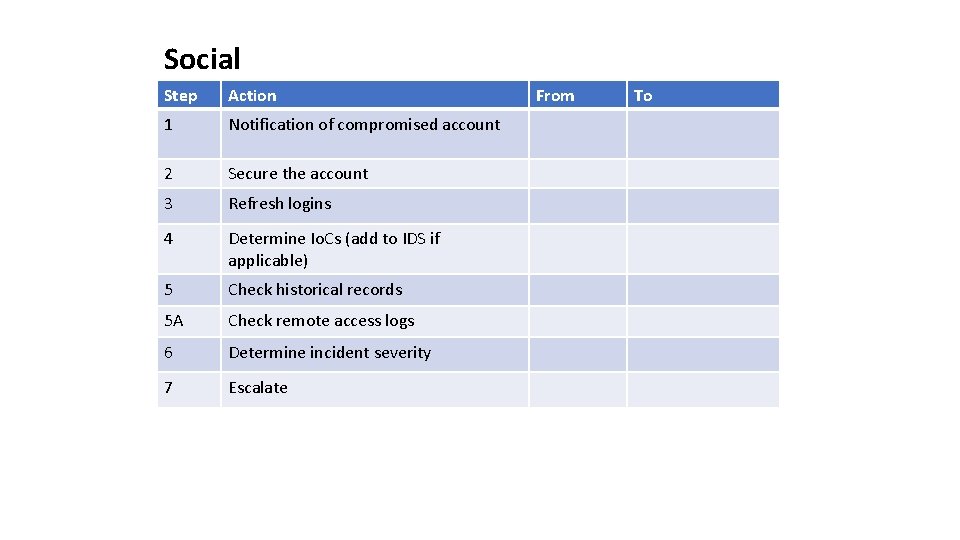
Social Step Action 1 Notification of compromised account 2 Secure the account 3 Refresh logins 4 Determine Io. Cs (add to IDS if applicable) 5 Check historical records 5 A Check remote access logs 6 Determine incident severity 7 Escalate From To
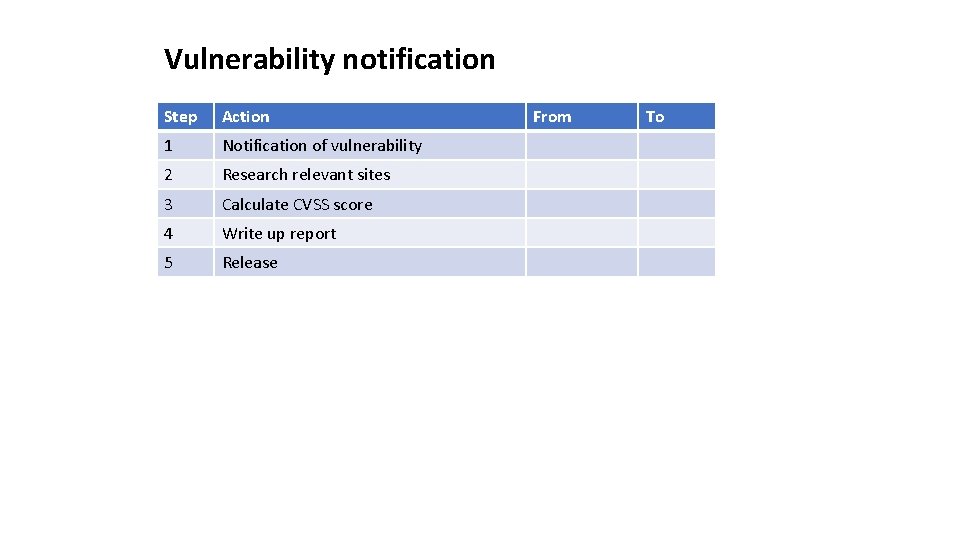
Vulnerability notification Step Action 1 Notification of vulnerability 2 Research relevant sites 3 Calculate CVSS score 4 Write up report 5 Release From To
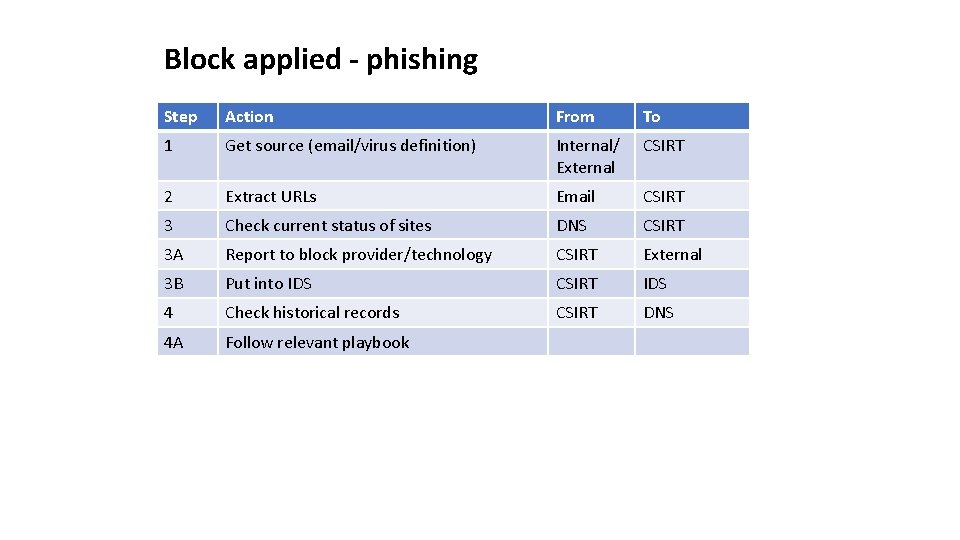
Block applied - phishing Step Action From To 1 Get source (email/virus definition) Internal/ External CSIRT 2 Extract URLs Email CSIRT 3 Check current status of sites DNS CSIRT 3 A Report to block provider/technology CSIRT External 3 B Put into IDS CSIRT IDS 4 Check historical records CSIRT DNS 4 A Follow relevant playbook
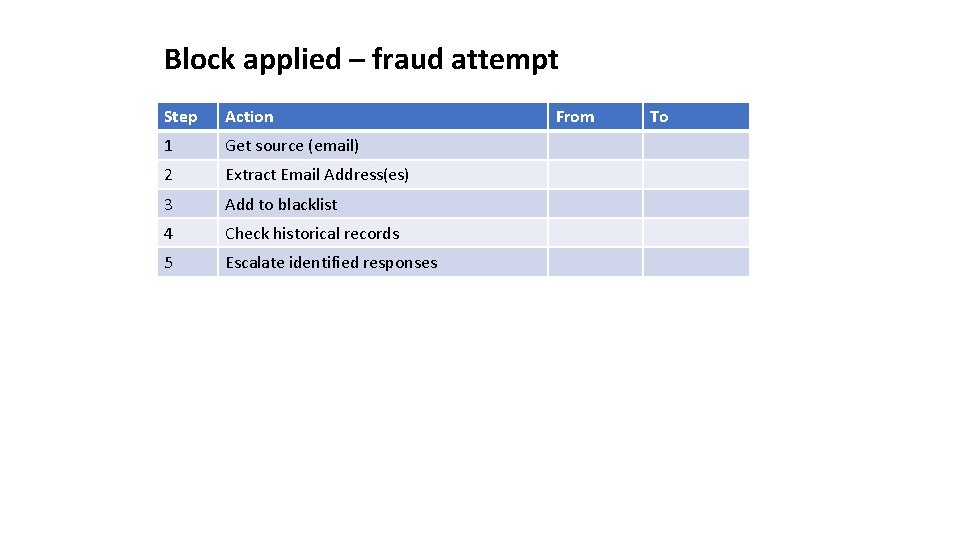
Block applied – fraud attempt Step Action 1 Get source (email) 2 Extract Email Address(es) 3 Add to blacklist 4 Check historical records 5 Escalate identified responses From To
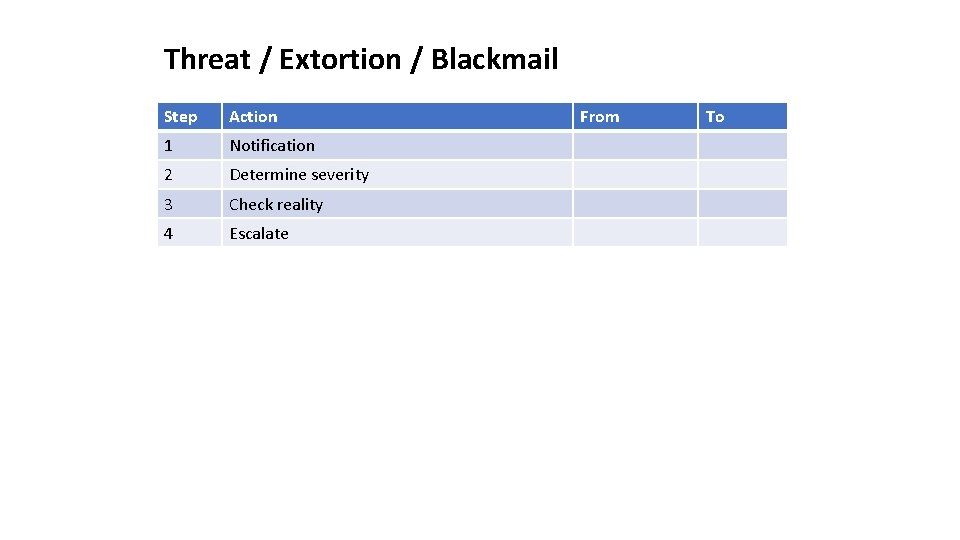
Threat / Extortion / Blackmail Step Action 1 Notification 2 Determine severity 3 Check reality 4 Escalate From To
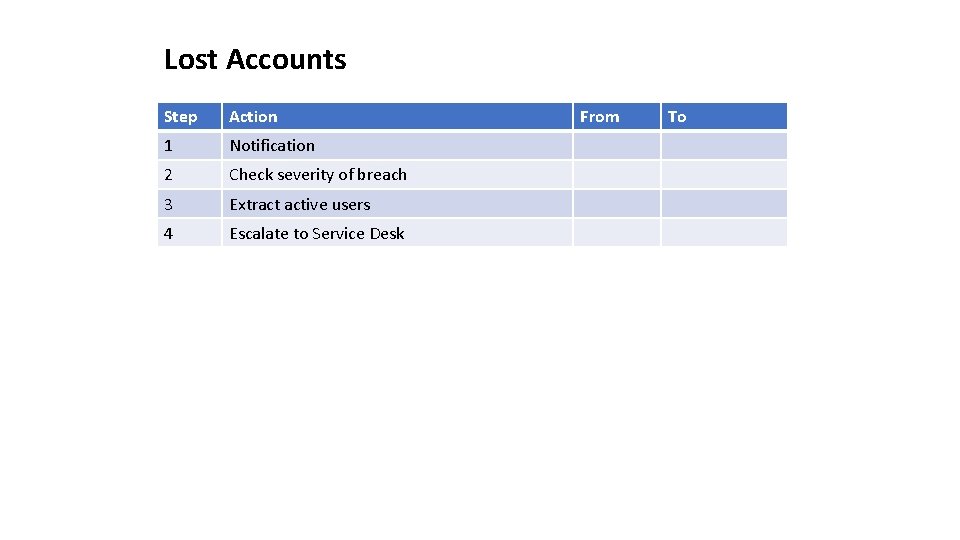
Lost Accounts Step Action 1 Notification 2 Check severity of breach 3 Extract active users 4 Escalate to Service Desk From To
- Slides: 14