PairingBased Noninteractive Proofs Jens Groth University College London
Pairing-Based Non-interactive Proofs Jens Groth University College London Joint work with Rafail Ostrovsky and Amit Sahai Thanks also to Brent Waters
Motivation Why does Bob want to know my password, No! bank statement, etc. ? Did Alice honestly follow Show me all the protocol? Alice Bob your inputs!
History • Goldwasser, Micali and Rackoff introduced interactive zero-knowledge proofs in 1985 • First the paper was rejected a couple of times • . . . then they won the Gödel award for it
Interactive proof Statement Prover OK, statement is true Verifier
Statements • • Mathematical theorem: 2+2=4 Identification: I am me! Verification: I followed the protocol Anything: X belongs to NP-language L
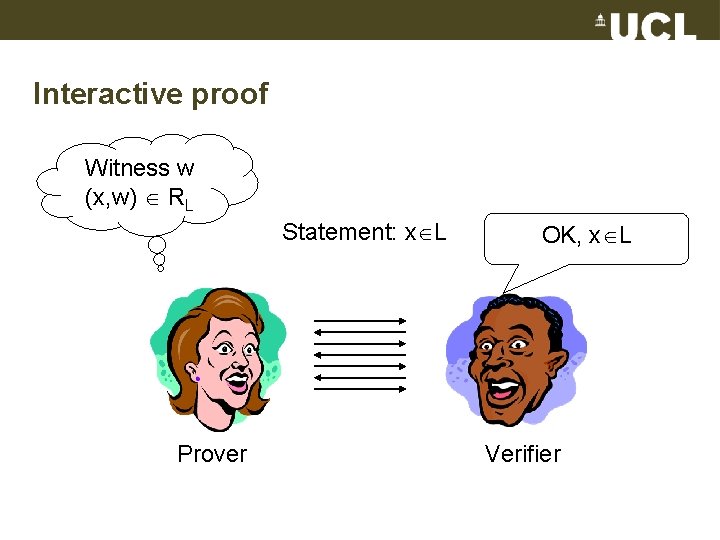
Interactive proof Witness w (x, w) RL Statement: x L Prover OK, x L Verifier
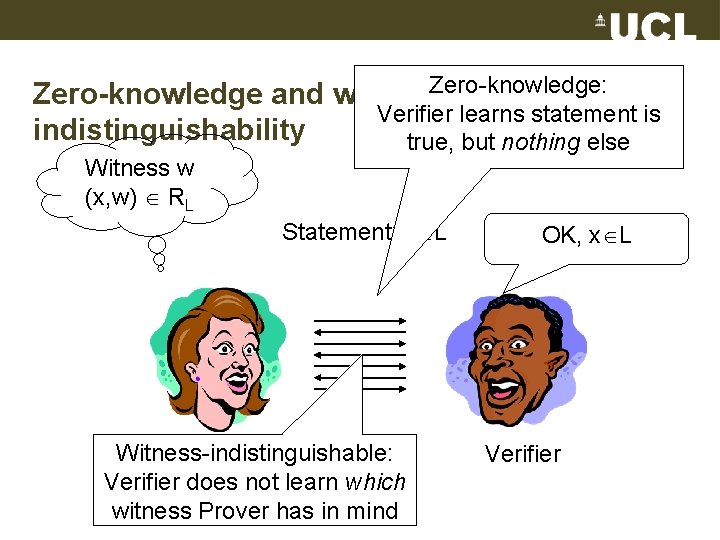
Zero-knowledge and witness. Zero-knowledge: Verifier learns statement is indistinguishability true, but nothing else Witness w (x, w) RL Statement: x L Witness-indistinguishable: Prover Verifier does not learn which witness Prover has in mind OK, x L Verifier
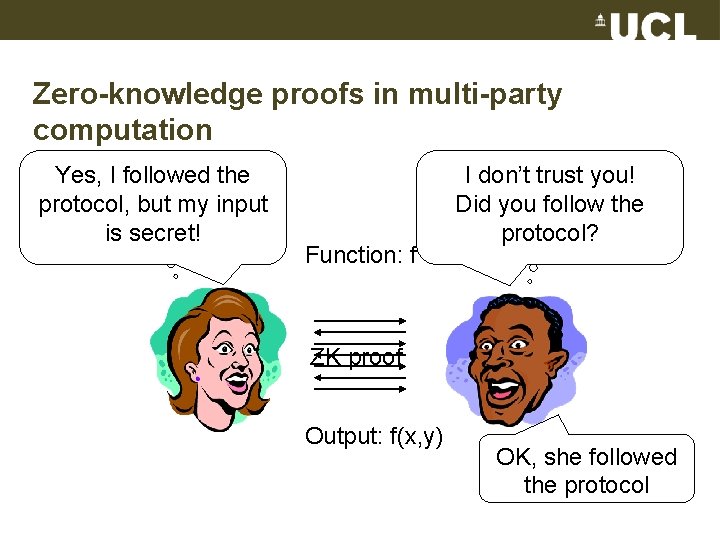
Zero-knowledge proofs in multi-party computation Yes, I followed the Input: protocol, butxmy input is secret! Function: f I don’t trust you! Input: y the Did you follow protocol? ZK proof Output: f(x, y) OK, she followed the protocol
History • Goldwasser, Micali and Rackoff introduced interactive zero-knowledge proofs in 1985 • Many actions are non-interactive – Signature – Encryption –. . .
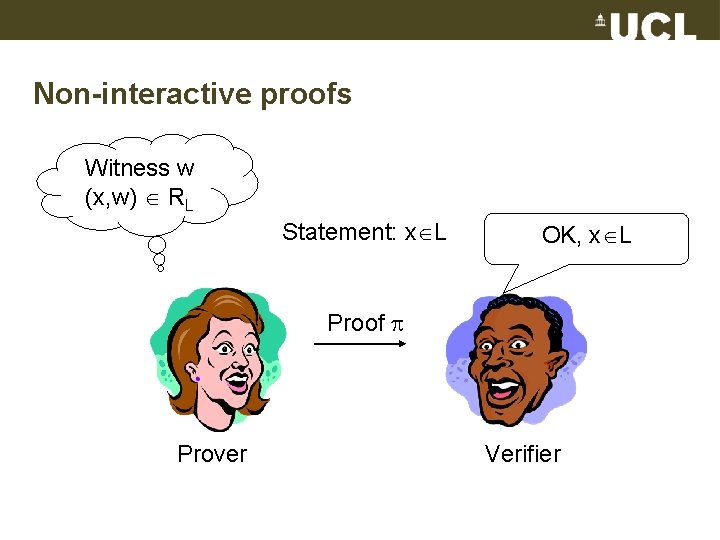
Non-interactive proofs Witness w (x, w) RL Statement: x L OK, x L Proof Prover Verifier
Non-interactive zero-knowledge (NIZK) proofs • Completeness – Can prove a true statement • Soundness – Cannot prove false statement • Zero-knowledge – Proof reveals nothing (except truth of statement)
NIZK proofs only for trivial languages (BPP) Sketch of proof: Decision algorithm for x in L: • Learn nothing from proof = can simulate proof • If x L: ZK and complete so verifier algorithm accepts • If x L: Sound so verifier algorithm rejects
History • Goldwasser, Micali and Rackoff introduced interactive zero-knowledge proofs in 1985 • Many actions are non-interactive – Signature – Encryption –. . . • Blum, Feldman and Micali introduced noninteractive zero-knowledge proofs in the common reference string model in 1986
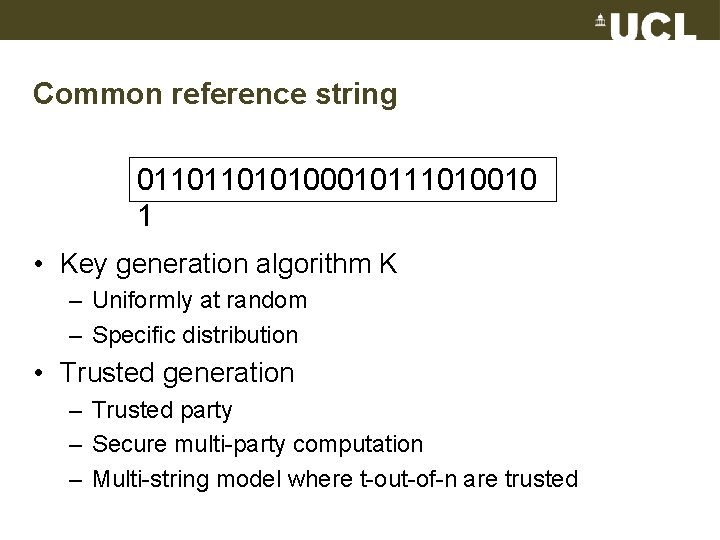
Common reference string 011011010100010111010010 1 • Key generation algorithm K – Uniformly at random – Specific distribution • Trusted generation – Trusted party – Secure multi-party computation – Multi-string model where t-out-of-n are trusted
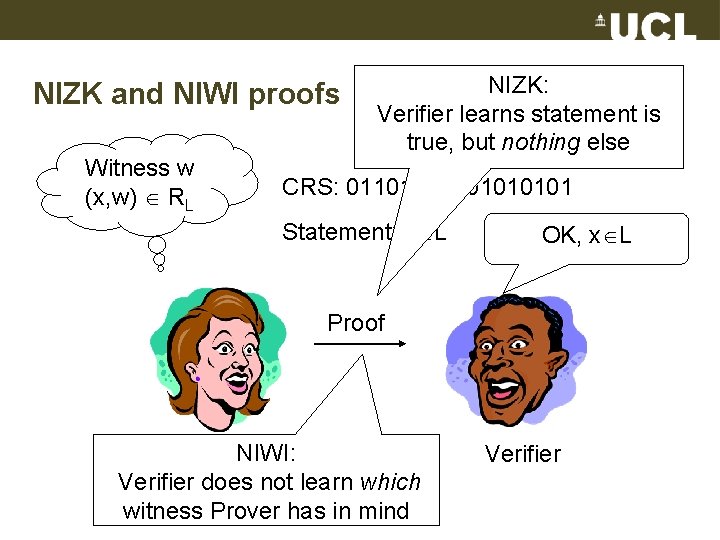
NIZK and NIWI proofs Witness w (x, w) RL NIZK: Verifier learns statement is true, but nothing else CRS: 01101010101 Statement: x L OK, x L Proof Prover. NIWI: Verifier does not learn which witness Prover has in mind Verifier
Defining NIZK proofs • NP language L: x L if is witness w so (x, w) RL • NIZK proof consists of three probabilistic polynomial time algorithms (K, P, V) • K(1 k): Generates common reference string σ • P(σ, x, w): Generates a proof • V(σ, x, ): Verifies the proof (outputs 1 or 0)
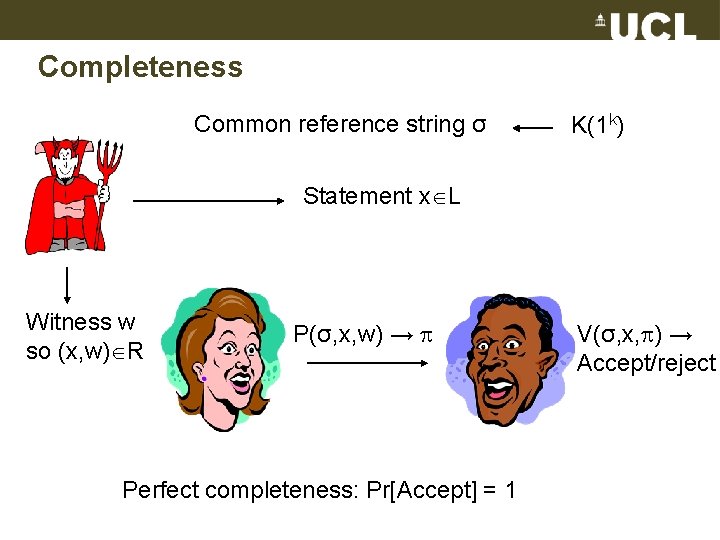
Completeness Common reference string σ K(1 k) Statement x L Witness w so (x, w) R P(σ, x, w) → Perfect completeness: Pr[Accept] = 1 V(σ, x, ) → Accept/reject
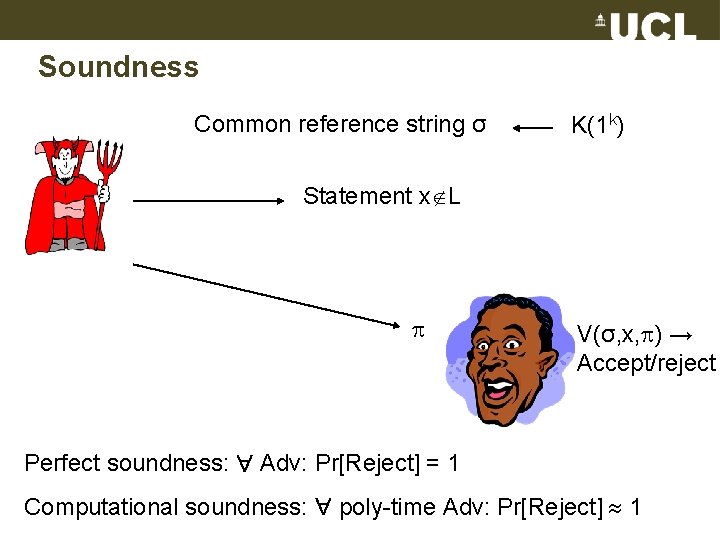
Soundness Common reference string σ K(1 k) Statement x L V(σ, x, ) → Accept/reject Perfect soundness: Adv: Pr[Reject] = 1 Computational soundness: poly-time Adv: Pr[Reject] 1
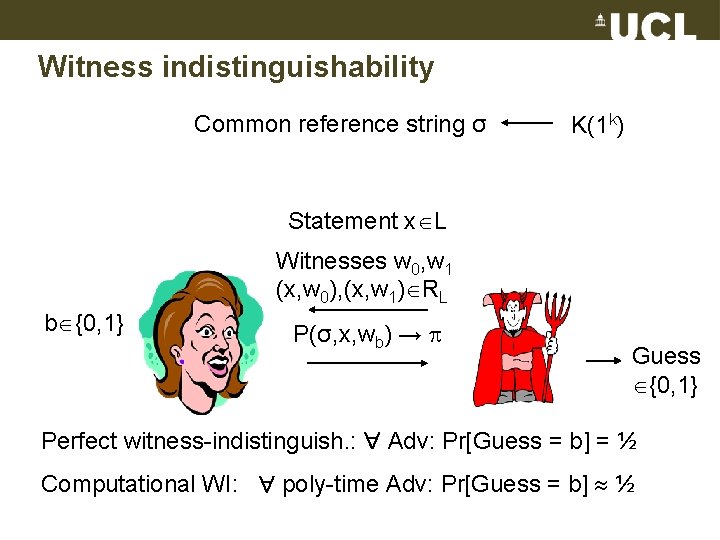
Witness indistinguishability Common reference string σ K(1 k) Statement x L Witnesses w 0, w 1 (x, w 0), (x, w 1) RL b {0, 1} P(σ, x, wb) → Guess {0, 1} Perfect witness-indistinguish. : Adv: Pr[Guess = b] = ½ Computational WI: poly-time Adv: Pr[Guess = b] ½
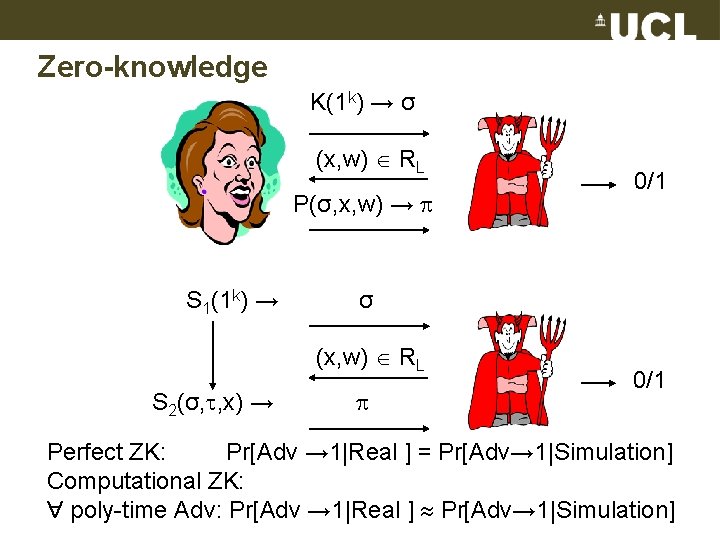
Zero-knowledge K(1 k) → σ (x, w) RL P(σ, x, w) → S 1(1 k) → σ (x, w) RL S 2(σ, , x) → 0/1 Perfect ZK: Pr[Adv → 1|Real ] = Pr[Adv→ 1|Simulation] Computational ZK: poly-time Adv: Pr[Adv → 1|Real ] Pr[Adv→ 1|Simulation]
Trade-off • Perfect soundness and perfect zero-knowledge only possible for trivial languages – Sketch of proof: • Perfect ZK implies real common reference string and simulated common reference string has same probability distribution • To decide whether x in L simulate common reference string, simulate proof, run verifier on simulated proof • If x L: By perfect ZK and completeness verifier accepts • If x L: By perfect soundness verifier rejects • Choice: – Perfect soundness and computational zero-knowledge – Computational soundness and perfect zero-knowledge
The world in 2005 • Much research in NIZK proofs – – – Blum-Feldman-Micali 88 Damgård 92 Feige-Lapidot-Shamir 99 Kilian-Petrank 98 De Santis-Di Crescenzo-Persiano 02 • Inefficient • Alternatives – Fiat-Shamir heuristic transforms interactive zero-knowledge proof into non-interactive scheme, however, there are examples of insecure Fiat-Shamir transformation – Designated verifier proofs such as Damgård, Fazio, Nicolosi 05, however, the verification is not public
Applications • • Public-key encryption Mix-nets for anonymous broadcast Internet voting Group signatures Ring signatures Identification Verifying outsourced computation. . .
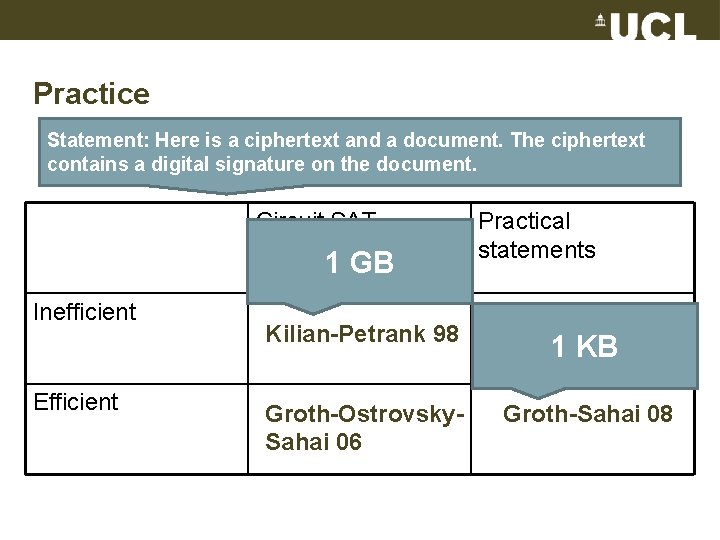
Practice Statement: Here is a ciphertext and a document. The ciphertext contains a digital signature on the document. Circuit SAT 1 GB Inefficient Efficient Practical statements Kilian-Petrank 98 Groth 06 1 KB Groth-Ostrovsky. Sahai 06 Groth-Sahai 08
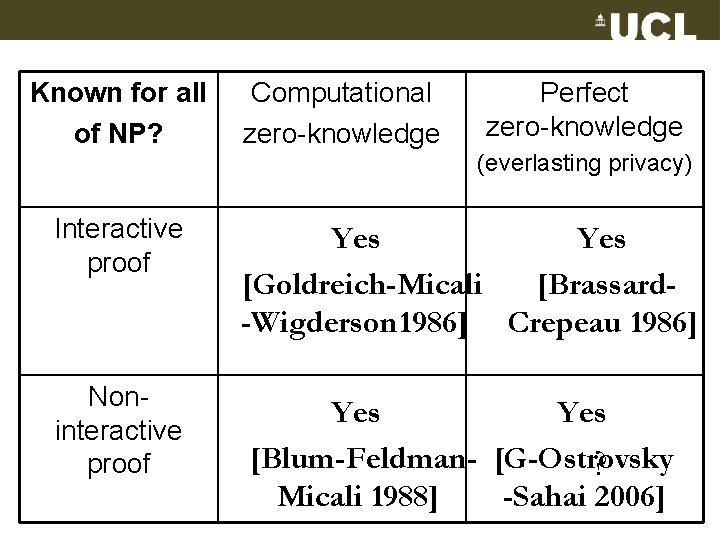
Known for all of NP? Computational zero-knowledge Perfect zero-knowledge (everlasting privacy) Interactive proof Yes [Goldreich-Micali [Brassard-Wigderson 1986] Crepeau 1986] Noninteractive proof Yes [Blum-Feldman- [G-Ostrovsky ? Micali 1988] -Sahai 2006]
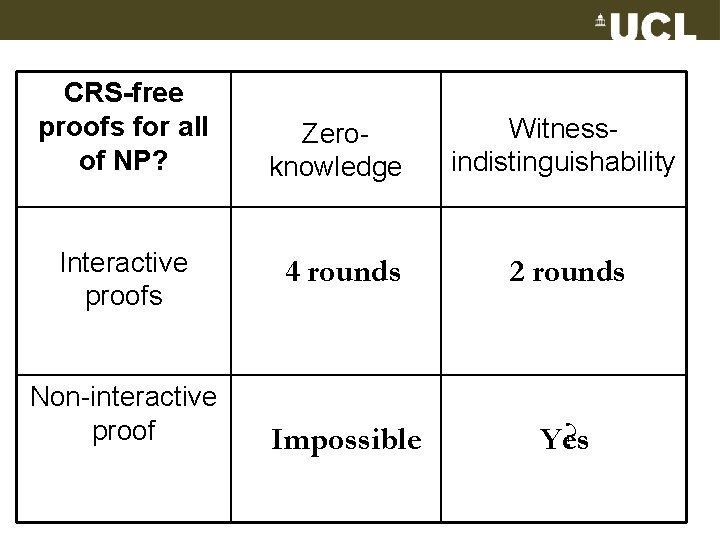
CRS-free proofs for all of NP? Interactive proofs Non-interactive proof Zeroknowledge Witnessindistinguishability 4 rounds 2 rounds Impossible ? Yes
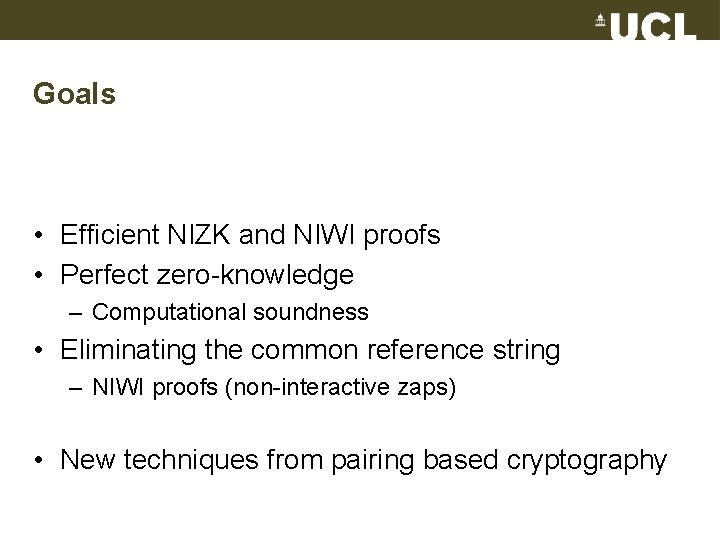
Goals • Efficient NIZK and NIWI proofs • Perfect zero-knowledge – Computational soundness • Eliminating the common reference string – NIWI proofs (non-interactive zaps) • New techniques from pairing based cryptography
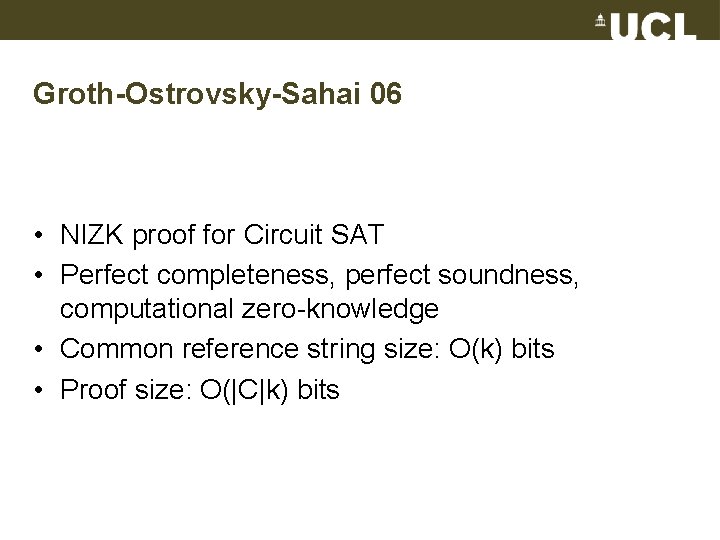
Groth-Ostrovsky-Sahai 06 • NIZK proof for Circuit SAT • Perfect completeness, perfect soundness, computational zero-knowledge • Common reference string size: O(k) bits • Proof size: O(|C|k) bits
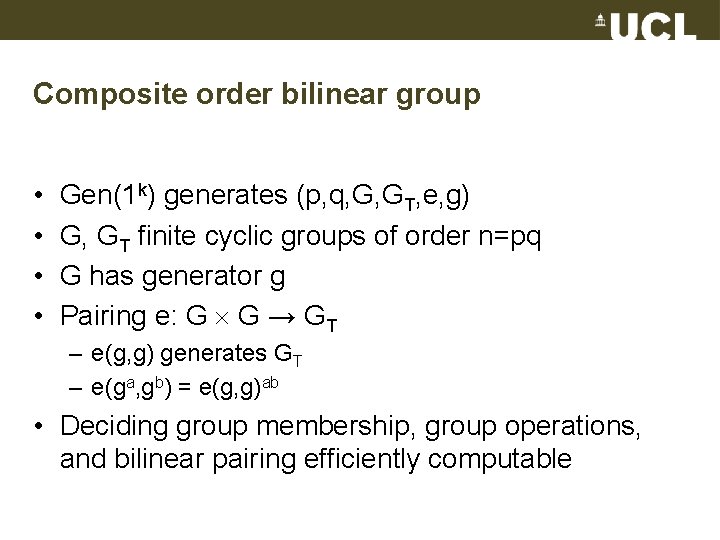
Composite order bilinear group • • Gen(1 k) generates (p, q, G, GT, e, g) G, GT finite cyclic groups of order n=pq G has generator g Pairing e: G G → GT – e(g, g) generates GT – e(ga, gb) = e(g, g)ab • Deciding group membership, group operations, and bilinear pairing efficiently computable
Elliptic curves
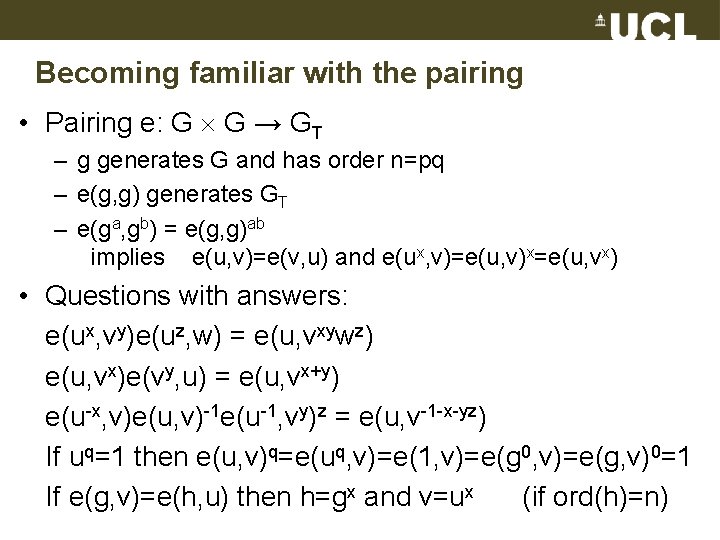
Becoming familiar with the pairing • Pairing e: G G → GT – g generates G and has order n=pq – e(g, g) generates GT – e(ga, gb) = e(g, g)ab implies e(u, v)=e(v, u) and e(ux, v)=e(u, v)x=e(u, vx) • Questions with answers: e(ux, vy)e(uz, w) = e(u, vxywz) e(u, vx)e(vy, u) = e(u, vx+y) e(u-x, v)e(u, v)-1 e(u-1, vy)z = e(u, v-1 -x-yz) If uq=1 then e(u, v)q=e(uq, v)=e(1, v)=e(g 0, v)=e(g, v)0=1 If e(g, v)=e(h, u) then h=gx and v=ux (if ord(h)=n)
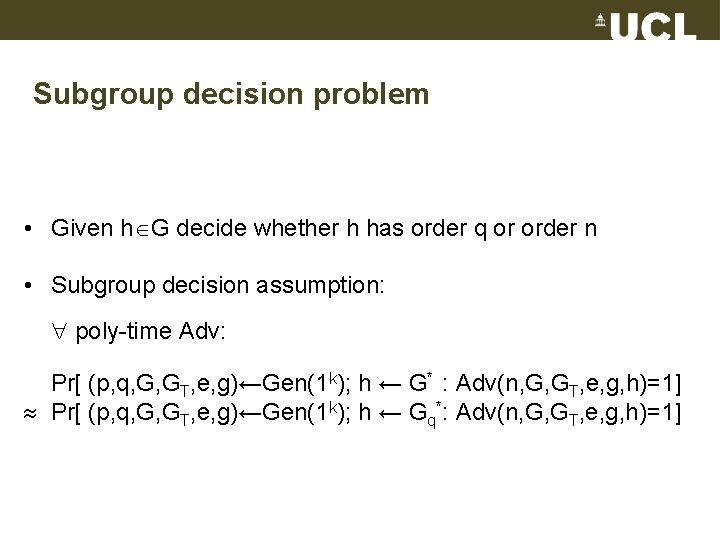
Subgroup decision problem • Given h G decide whether h has order q or order n • Subgroup decision assumption: poly-time Adv: Pr[ (p, q, G, GT, e, g)←Gen(1 k); h ← G* : Adv(n, G, GT, e, g, h)=1] Pr[ (p, q, G, GT, e, g)←Gen(1 k); h ← Gq*: Adv(n, G, GT, e, g, h)=1]
![BGN encryption [Boneh-Goh-Nissim 05] Public key: g, h G h order q Secret key: BGN encryption [Boneh-Goh-Nissim 05] Public key: g, h G h order q Secret key:](http://slidetodoc.com/presentation_image/50a3c28ecc66c8a875050858b319d98e/image-33.jpg)
BGN encryption [Boneh-Goh-Nissim 05] Public key: g, h G h order q Secret key: p, q n=pq Encryption: c = g ah r r ← Zn Decryption: cq = (gahr)q = gqahqr = (gq)a IND-CPA secure: Without secret key, ciphertext does not reveal poly-time computable information about plaintext. Sketch of proof: By subgroup decision assumption public key looks the same as if h had order n. But if h had order n, ciphertext would have no information about the plaintext a.
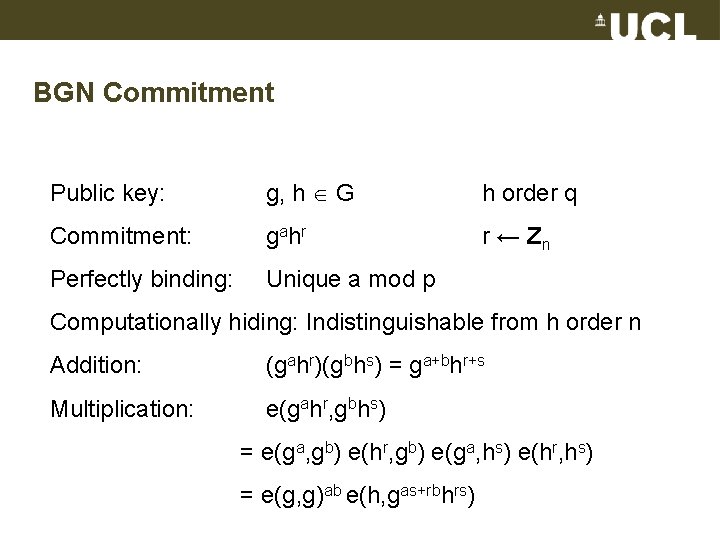
BGN Commitment Public key: g, h G h order q Commitment: g ah r r ← Zn Perfectly binding: Unique a mod p Computationally hiding: Indistinguishable from h order n Addition: (gahr)(gbhs) = ga+bhr+s Multiplication: e(gahr, gbhs) = e(ga, gb) e(hr, gb) e(ga, hs) e(hr, hs) = e(g, g)ab e(h, gas+rbhrs)
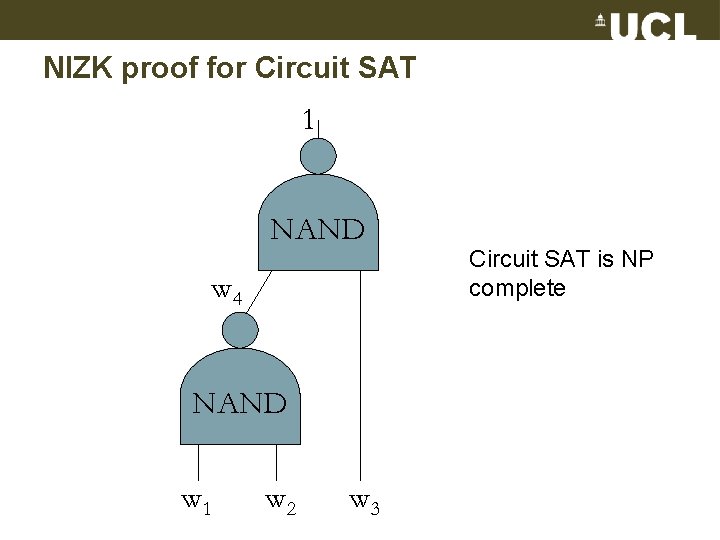
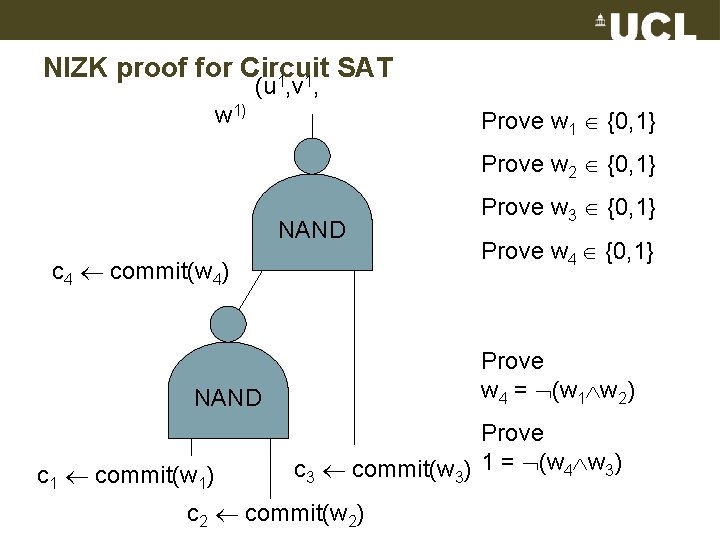
NIZK proof for Circuit SAT 1 NAND w 4 NAND w 1 w 2 w 3 Circuit SAT is NP complete
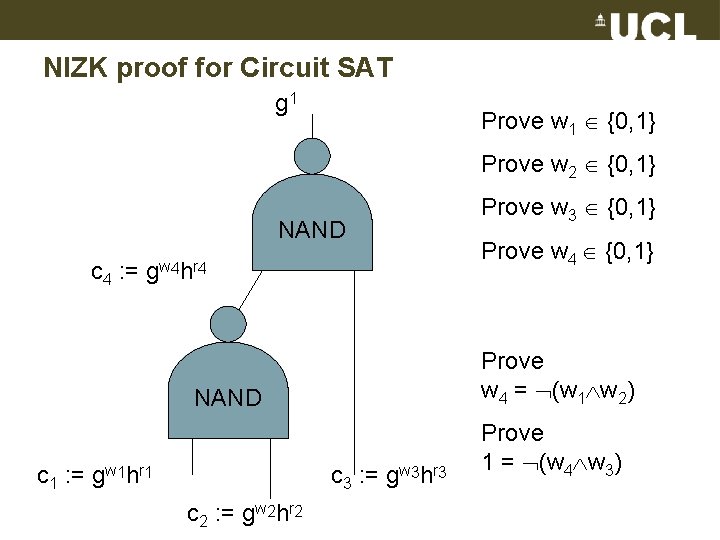
NIZK proof for Circuit SAT g 1 Prove w 1 {0, 1} Prove w 2 {0, 1} NAND c 4 : = g w 4 h r 4 c 3 : = gw 3 hr 3 c 2 : = gw 2 hr 2 Prove w 4 {0, 1} Prove w 4 = (w 1 w 2) NAND c 1 : = gw 1 hr 1 Prove w 3 {0, 1} Prove 1 = (w 4 w 3)
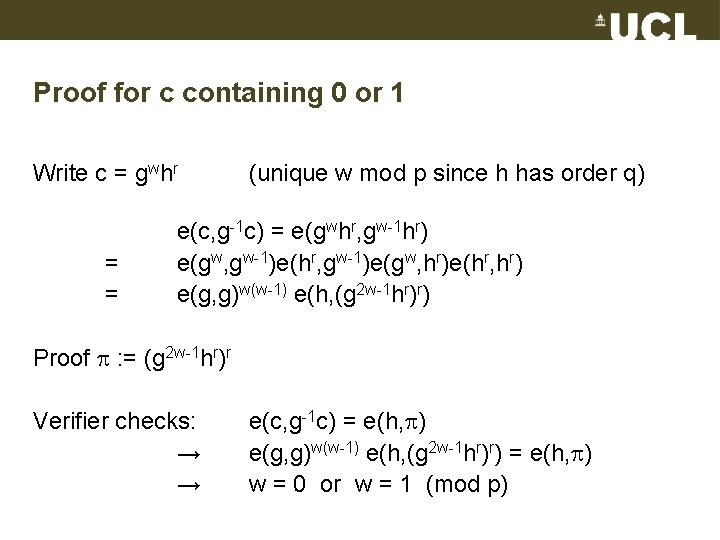
Proof for c containing 0 or 1 Write c = gwhr = = (unique w mod p since h has order q) e(c, g-1 c) = e(gwhr, gw-1 hr) e(gw, gw-1)e(hr, gw-1)e(gw, hr)e(hr, hr) e(g, g)w(w-1) e(h, (g 2 w-1 hr)r) Proof : = (g 2 w-1 hr)r Verifier checks: → → e(c, g-1 c) = e(h, ) e(g, g)w(w-1) e(h, (g 2 w-1 hr)r) = e(h, ) w = 0 or w = 1 (mod p)
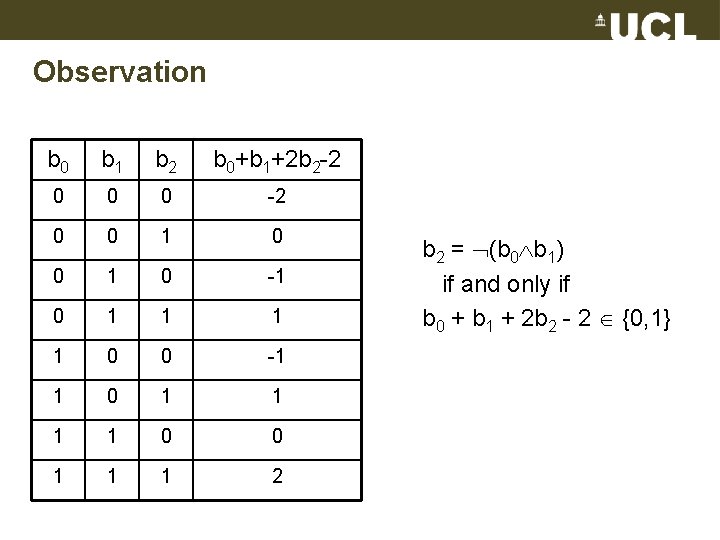
Observation b 0 b 1 b 2 b 0+b 1+2 b 2 -2 0 0 0 -2 0 0 1 0 -1 0 1 1 0 0 -1 1 0 0 1 1 1 2 b 2 = (b 0 b 1) if and only if b 0 + b 1 + 2 b 2 - 2 {0, 1}
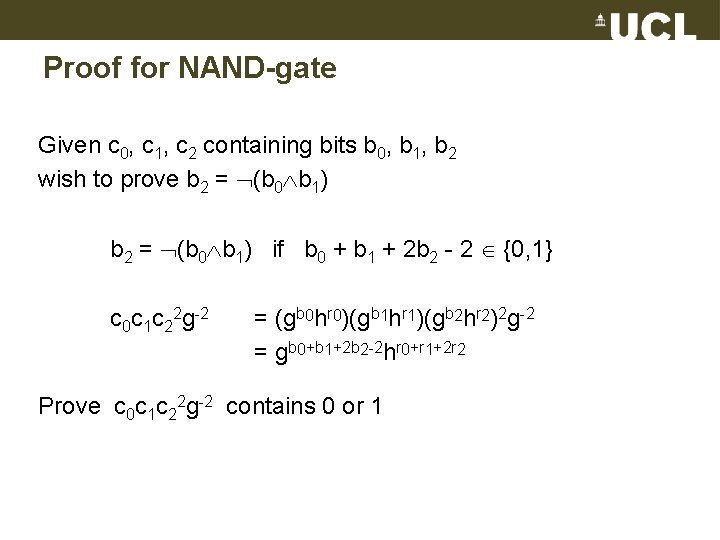
Proof for NAND-gate Given c 0, c 1, c 2 containing bits b 0, b 1, b 2 wish to prove b 2 = (b 0 b 1) if b 0 + b 1 + 2 b 2 - 2 {0, 1} c 0 c 1 c 22 g-2 = (gb 0 hr 0)(gb 1 hr 1)(gb 2 hr 2)2 g-2 = gb 0+b 1+2 b 2 -2 hr 0+r 1+2 r 2 Prove c 0 c 1 c 22 g-2 contains 0 or 1
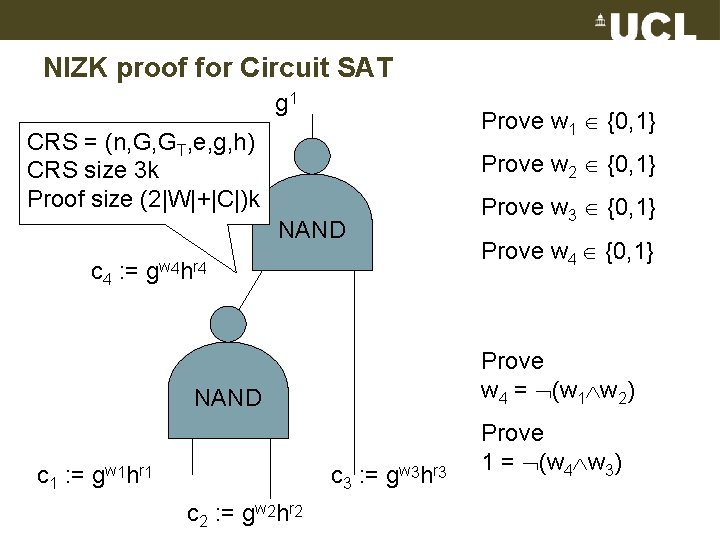
NIZK proof for Circuit SAT g 1 Prove w 1 {0, 1} CRS = (n, G, GT, e, g, h) CRS size 3 k Proof size (2|W|+|C|)k Prove w 2 {0, 1} NAND c 4 : = g w 4 h r 4 c 3 : = gw 3 hr 3 c 2 : = gw 2 hr 2 Prove w 4 {0, 1} Prove w 4 = (w 1 w 2) NAND c 1 : = gw 1 hr 1 Prove w 3 {0, 1} Prove 1 = (w 4 w 3)
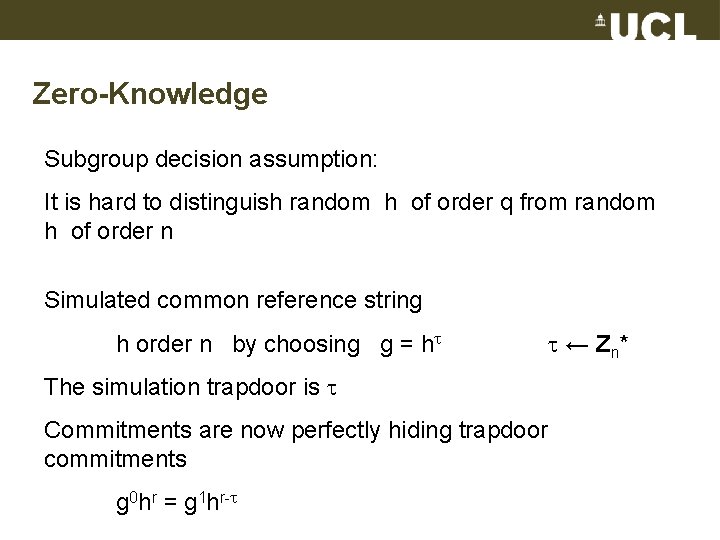
Zero-Knowledge Subgroup decision assumption: It is hard to distinguish random h of order q from random h of order n Simulated common reference string h order n by choosing g = h The simulation trapdoor is Commitments are now perfectly hiding trapdoor commitments g 0 hr = g 1 hr- ← Z n*
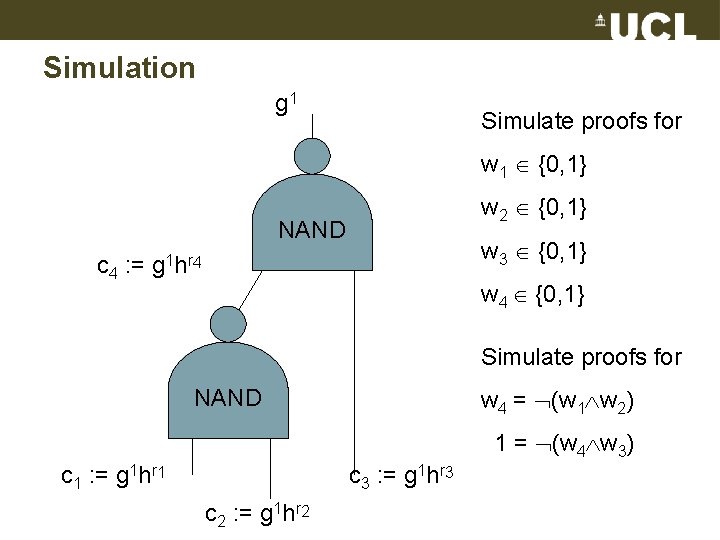
Simulation g 1 Simulate proofs for w 1 {0, 1} w 2 {0, 1} NAND c 4 : = w 3 {0, 1} g 1 h r 4 w 4 {0, 1} Simulate proofs for w 4 = (w 1 w 2) NAND 1 = (w 4 w 3) c 1 : = g 1 hr 1 c 3 : = g 1 hr 3 c 2 : = g 1 hr 2
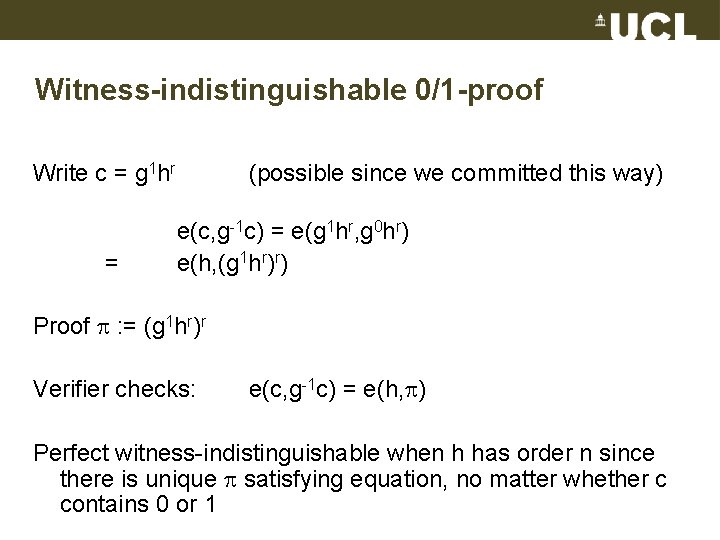
Witness-indistinguishable 0/1 -proof Write c = g 1 hr = (possible since we committed this way) e(c, g-1 c) = e(g 1 hr, g 0 hr) e(h, (g 1 hr)r) Proof : = (g 1 hr)r Verifier checks: e(c, g-1 c) = e(h, ) Perfect witness-indistinguishable when h has order n since there is unique satisfying equation, no matter whether c contains 0 or 1
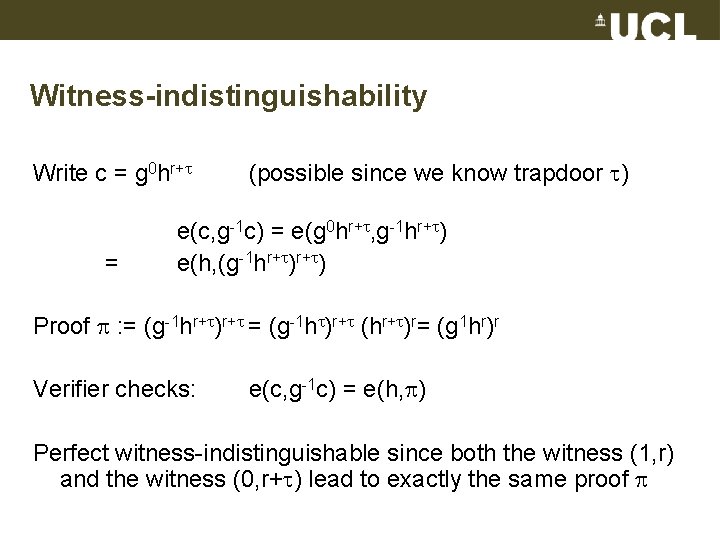
Witness-indistinguishability Write c = g 0 hr+ = (possible since we know trapdoor ) e(c, g-1 c) = e(g 0 hr+ , g-1 hr+ ) e(h, (g-1 hr+ ) Proof : = (g-1 hr+ )r+ = (g-1 h )r+ (hr+ )r= (g 1 hr)r Verifier checks: e(c, g-1 c) = e(h, ) Perfect witness-indistinguishable since both the witness (1, r) and the witness (0, r+ ) lead to exactly the same proof
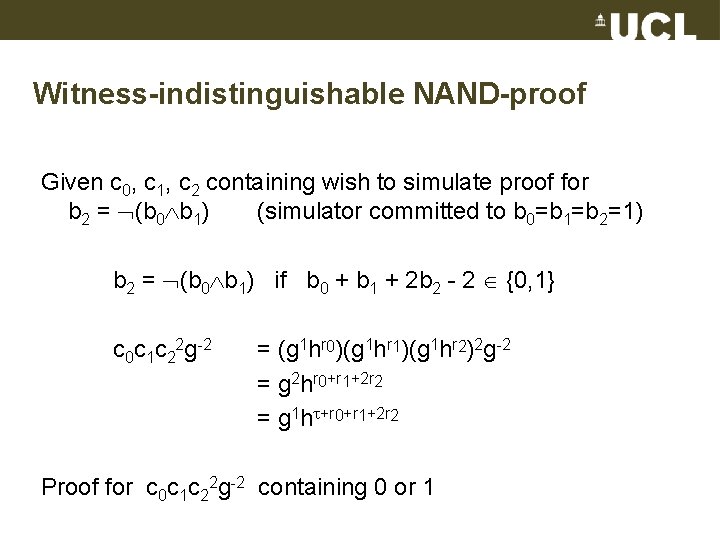
Witness-indistinguishable NAND-proof Given c 0, c 1, c 2 containing wish to simulate proof for b 2 = (b 0 b 1) (simulator committed to b 0=b 1=b 2=1) b 2 = (b 0 b 1) if b 0 + b 1 + 2 b 2 - 2 {0, 1} c 0 c 1 c 22 g-2 = (g 1 hr 0)(g 1 hr 1)(g 1 hr 2)2 g-2 = g 2 hr 0+r 1+2 r 2 = g 1 h +r 0+r 1+2 r 2 Proof for c 0 c 1 c 22 g-2 containing 0 or 1
![Zero-knowledge Sketch of proof: Pr[Adv→ 1|Real proof] Pr[Adv→ 1|Real proof on h with order Zero-knowledge Sketch of proof: Pr[Adv→ 1|Real proof] Pr[Adv→ 1|Real proof on h with order](http://slidetodoc.com/presentation_image/50a3c28ecc66c8a875050858b319d98e/image-46.jpg)
Zero-knowledge Sketch of proof: Pr[Adv→ 1|Real proof] Pr[Adv→ 1|Real proof on h with order n] = Pr[Adv→ 1|Hybrid proof where h has order n and commitments to 1 trapdoor opened to witness and then real proofs] = Pr[Adv→ 1|Hybrid proof where h has order n and commitments to 1 and trapdoor opening when making 0/1 -proofs] = Pr[Adv→ 1|Simulated proof]
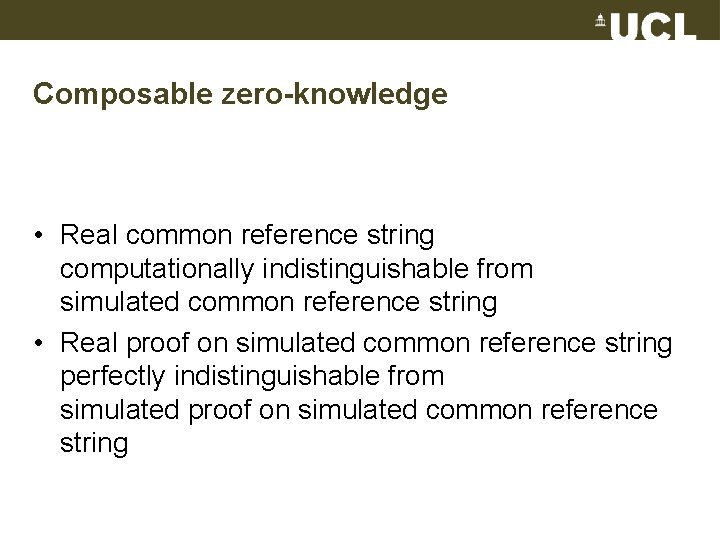
Composable zero-knowledge • Real common reference string computationally indistinguishable from simulated common reference string • Real proof on simulated common reference string perfectly indistinguishable from simulated proof on simulated common reference string
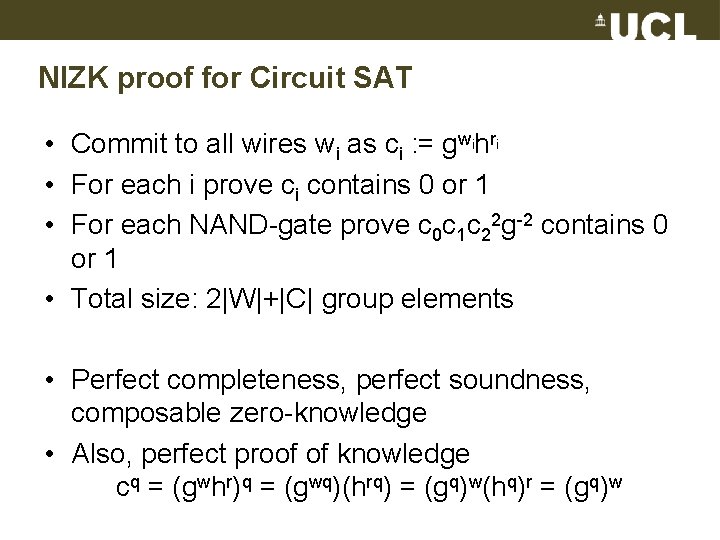
NIZK proof for Circuit SAT • Commit to all wires wi as ci : = gwihri • For each i prove ci contains 0 or 1 • For each NAND-gate prove c 0 c 1 c 22 g-2 contains 0 or 1 • Total size: 2|W|+|C| group elements • Perfect completeness, perfect soundness, composable zero-knowledge • Also, perfect proof of knowledge cq = (gwhr)q = (gwq)(hrq) = (gq)w(hq)r = (gq)w
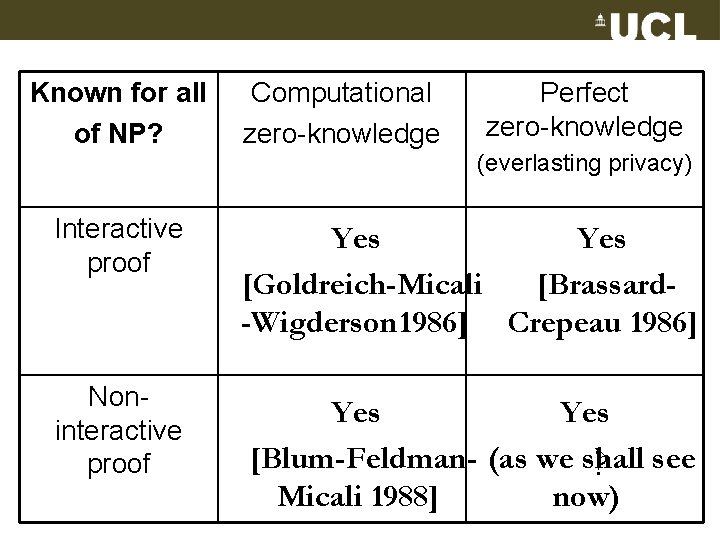
Known for all of NP? Computational zero-knowledge Perfect zero-knowledge (everlasting privacy) Interactive proof Yes [Goldreich-Micali [Brassard-Wigderson 1986] Crepeau 1986] Noninteractive proof Yes [Blum-Feldman- (as we shall ? see Micali 1988] now)
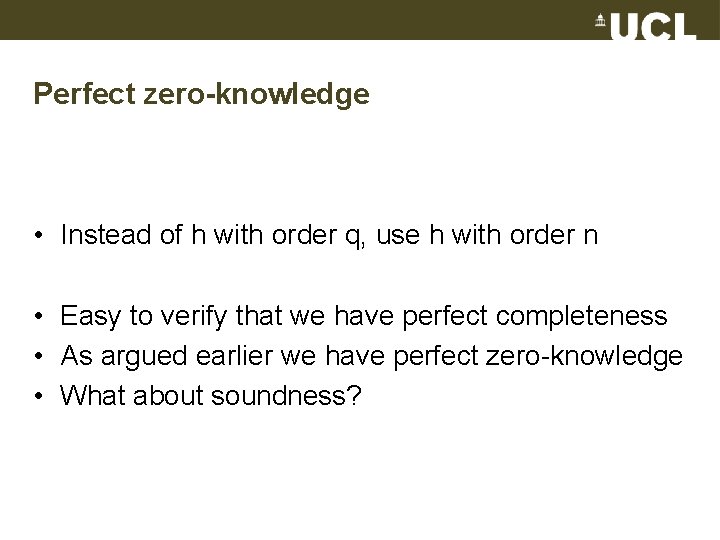
Perfect zero-knowledge • Instead of h with order q, use h with order n • Easy to verify that we have perfect completeness • As argued earlier we have perfect zero-knowledge • What about soundness?
”Natural” computational soundness fails • Natural way to prove soundness fails • Start with h of order n and Adv that produces false statement and valid proof • Switch to h of order q, which Adv cannot distinguish from order n. Here Adv cannot produce false statement and valid proof • Problem: Consider the statement ”h has order q”
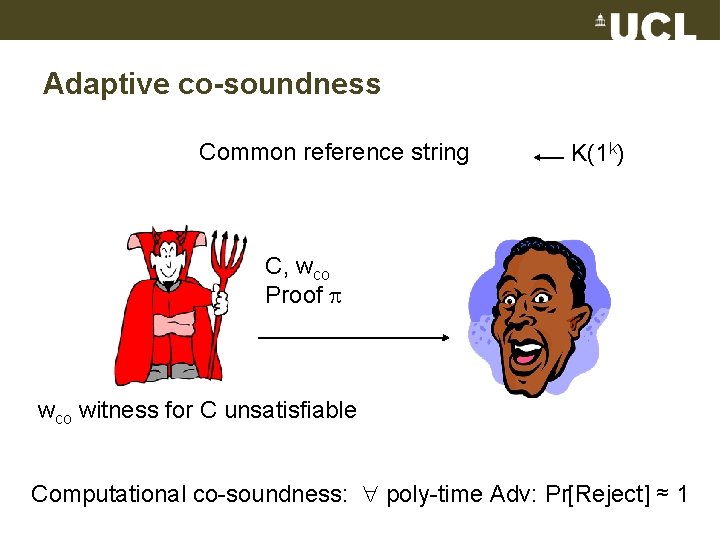
Adaptive co-soundness Common reference string K(1 k) C, wco Proof wco witness for C unsatisfiable Computational co-soundness: poly-time Adv: Pr[Reject] ≈ 1
Computational co-soundness Sketch of proof: • Imagine poly-time Adv could break co-soundness. I. e. , after seeing CRS = (n, G, GT, e, g, h) where h has order n, Adv produces valid (C, wco, ). • By subgroup decision assumption approximately same success probability for Adv producing valid (C, wco, ) when h has order q. • But wco guarantees C is unsatisfiable and when h has order q the perfect soundness guarantees C is satisfiable.
Co-soundness the ”right” definition • Abe-Fehr 07 show that impossible to achieve ”natural” soundness definition with standard direct black-box methods • In many scenarios a co-witness exists. – Consider for instance verifiable encryption, where the secret key can be a co-NP witness for false statement • Computational co-soundness sufficient for constructing universally composable NIZK proofs
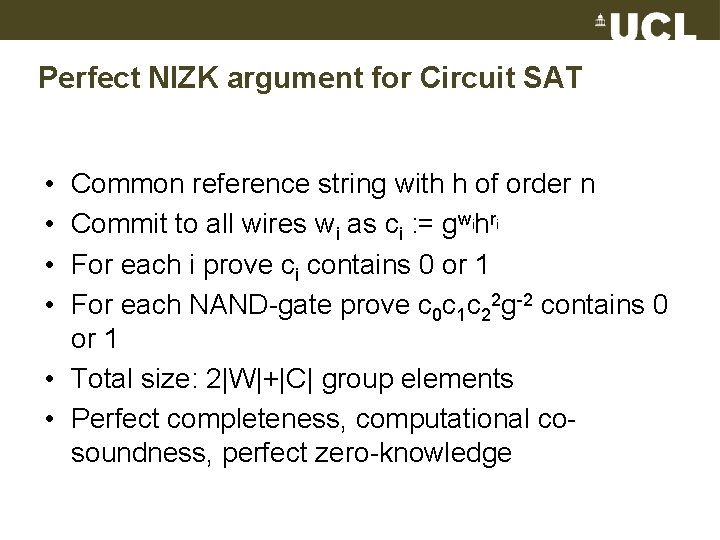
Perfect NIZK argument for Circuit SAT • • Common reference string with h of order n Commit to all wires wi as ci : = gwihri For each i prove ci contains 0 or 1 For each NAND-gate prove c 0 c 1 c 22 g-2 contains 0 or 1 • Total size: 2|W|+|C| group elements • Perfect completeness, computational cosoundness, perfect zero-knowledge
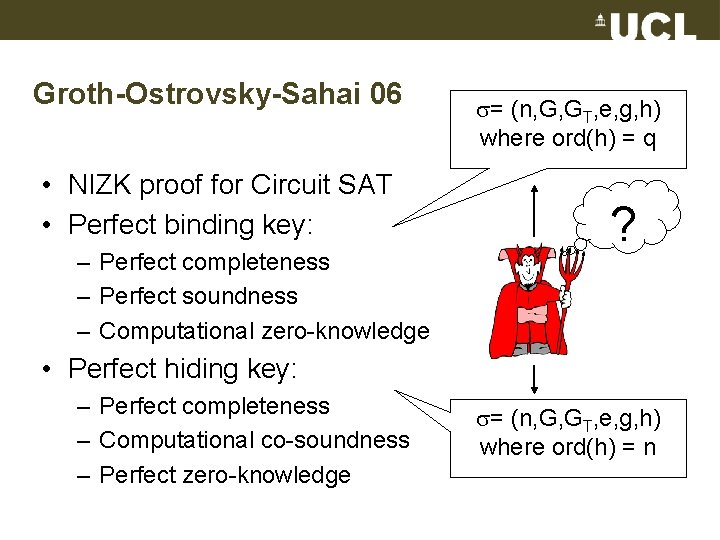
Groth-Ostrovsky-Sahai 06 • NIZK proof for Circuit SAT • Perfect binding key: – Perfect completeness – Perfect soundness – Computational zero-knowledge = (n, G, GT, e, g, h) where ord(h) = q ? • Perfect hiding key: – Perfect completeness – Computational co-soundness – Perfect zero-knowledge = (n, G, GT, e, g, h) where ord(h) = n
Non-interactive proofs in the plain model • NIZK proofs rely on trusted setup of common reference string. • What if no such setup exists? • Well, NIZK proofs do not exist in the plain model. • OK, how much privacy can we get in plain model? • NIWI proofs do exist in the plain model!
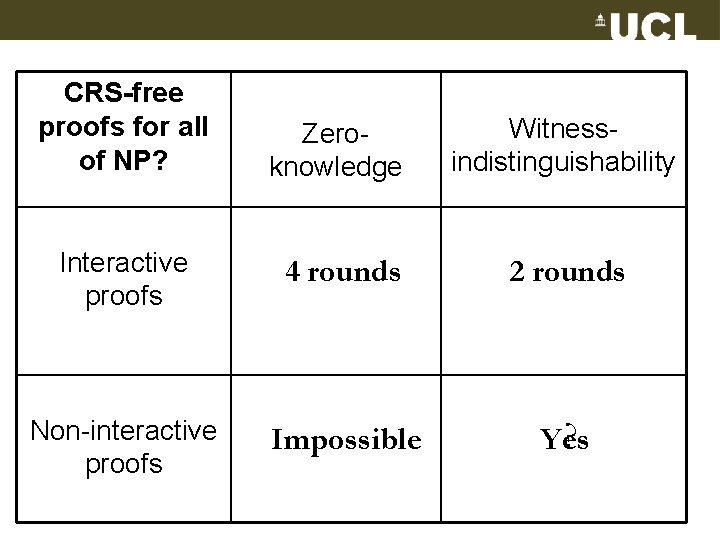
CRS-free proofs for all of NP? Zeroknowledge Witnessindistinguishability Interactive proofs 4 rounds 2 rounds Non-interactive proofs Impossible ? Yes
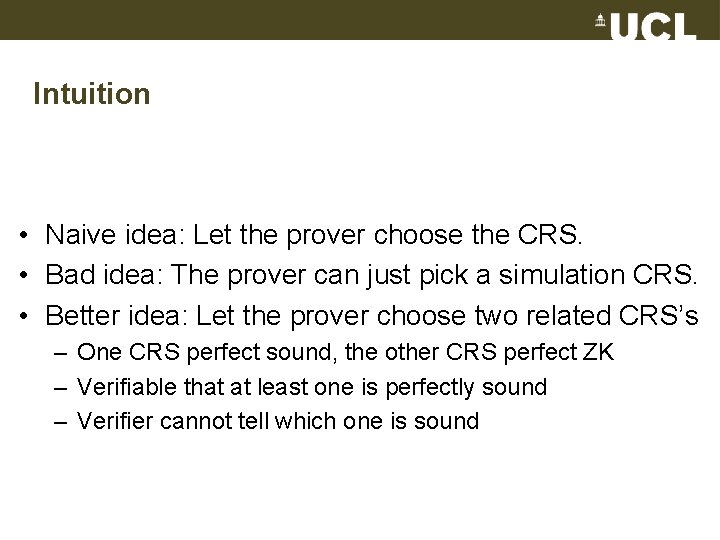
Intuition • Naive idea: Let the prover choose the CRS. • Bad idea: The prover can just pick a simulation CRS. • Better idea: Let the prover choose two related CRS’s – One CRS perfect sound, the other CRS perfect ZK – Verifiable that at least one is perfectly sound – Verifier cannot tell which one is sound
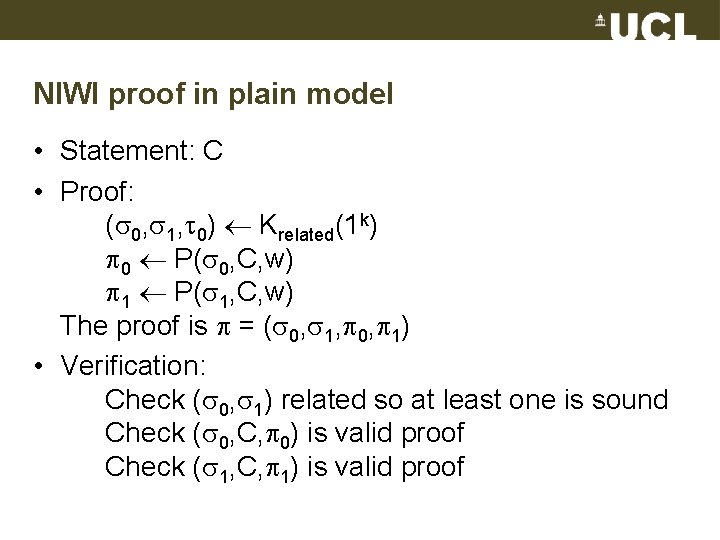
NIWI proof in plain model • Statement: C • Proof: ( 0, 1, 0) Krelated(1 k) 0 P( 0, C, w) 1 P( 1, C, w) The proof is = ( 0, 1, 0, 1) • Verification: Check ( 0, 1) related so at least one is sound Check ( 0, C, 0) is valid proof Check ( 1, C, 1) is valid proof
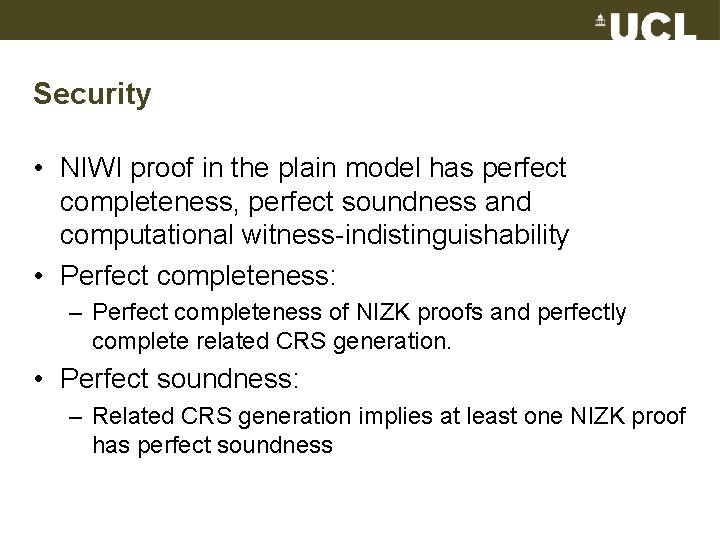
Security • NIWI proof in the plain model has perfect completeness, perfect soundness and computational witness-indistinguishability • Perfect completeness: – Perfect completeness of NIZK proofs and perfectly complete related CRS generation. • Perfect soundness: – Related CRS generation implies at least one NIZK proof has perfect soundness
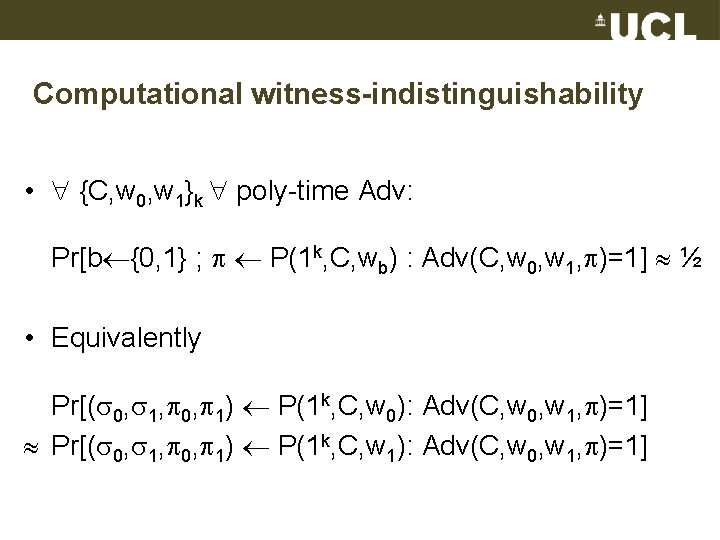
Computational witness-indistinguishability • {C, w 0, w 1}k poly-time Adv: Pr[b {0, 1} ; P(1 k, C, wb) : Adv(C, w 0, w 1, )=1] ½ • Equivalently Pr[( 0, 1, 0, 1) P(1 k, C, w 0): Adv(C, w 0, w 1, )=1] Pr[( 0, 1, 0, 1) P(1 k, C, w 1): Adv(C, w 0, w 1, )=1]
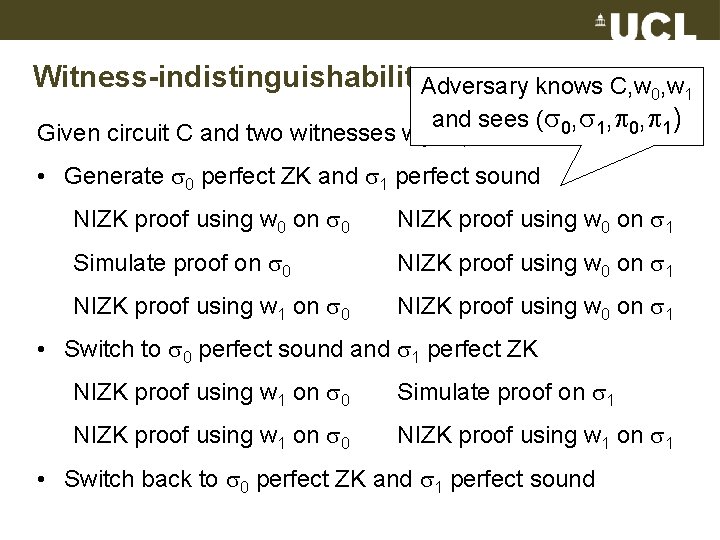
Witness-indistinguishability. Adversary knows C, w 0, w 1 and sees ( 0, 1, 0, 1) Given circuit C and two witnesses w 0, w 1 • Generate 0 perfect ZK and 1 perfect sound NIZK proof using w 0 on 0 NIZK proof using w 0 on 1 Simulate proof on 0 NIZK proof using w 0 on 1 NIZK proof using w 1 on 0 NIZK proof using w 0 on 1 • Switch to 0 perfect sound and 1 perfect ZK NIZK proof using w 1 on 0 Simulate proof on 1 NIZK proof using w 1 on 0 NIZK proof using w 1 on 1 • Switch back to 0 perfect ZK and 1 perfect sound
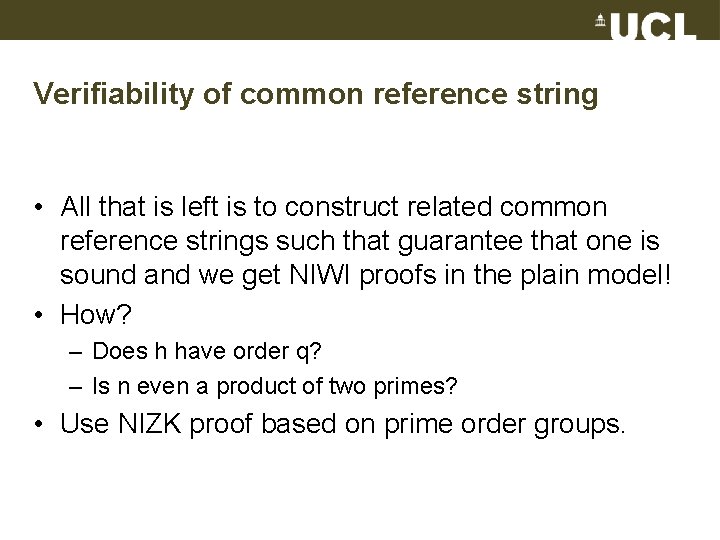
Verifiability of common reference string • All that is left is to construct related common reference strings such that guarantee that one is sound and we get NIWI proofs in the plain model! • How? – Does h have order q? – Is n even a product of two primes? • Use NIZK proof based on prime order groups.
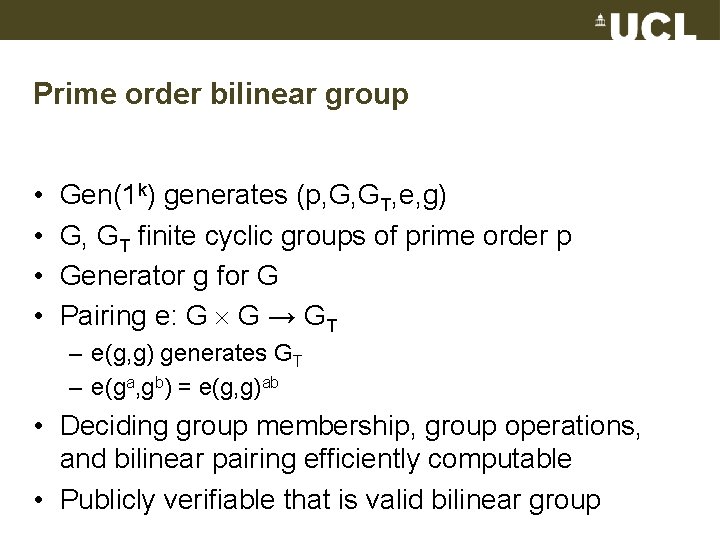
Prime order bilinear group • • Gen(1 k) generates (p, G, GT, e, g) G, GT finite cyclic groups of prime order p Generator g for G Pairing e: G G → GT – e(g, g) generates GT – e(ga, gb) = e(g, g)ab • Deciding group membership, group operations, and bilinear pairing efficiently computable • Publicly verifiable that is valid bilinear group
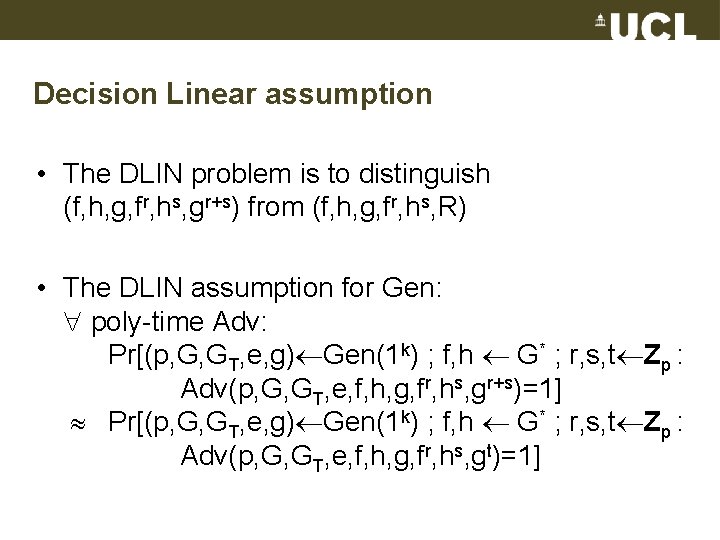
Decision Linear assumption • The DLIN problem is to distinguish (f, h, g, fr, hs, gr+s) from (f, h, g, fr, hs, R) • The DLIN assumption for Gen: poly-time Adv: Pr[(p, G, GT, e, g) Gen(1 k) ; f, h G* ; r, s, t Zp : Adv(p, G, GT, e, f, h, g, fr, hs, gr+s)=1] Pr[(p, G, GT, e, g) Gen(1 k) ; f, h G* ; r, s, t Zp : Adv(p, G, GT, e, f, h, g, fr, hs, gt)=1]
![Linear encryption [Boneh-Boyen-Shacham 04] • • Public key: Secret key: Encryption: Decryption: f, h, Linear encryption [Boneh-Boyen-Shacham 04] • • Public key: Secret key: Encryption: Decryption: f, h,](http://slidetodoc.com/presentation_image/50a3c28ecc66c8a875050858b319d98e/image-67.jpg)
Linear encryption [Boneh-Boyen-Shacham 04] • • Public key: Secret key: Encryption: Decryption: f, h, g x, y (u, v, w) = (fr, hs, gr+sm) m = wu-1/xv-1/y f, h, g G* f=gx, h=gy r, s Zp • IND-CPA security: The ciphertext contains no poly -time computable information about plaintext • Sketch of proof: Look at public key and ciphertext (f, h, g, fr, hs, gr+sm) (f, h, g, fr, hs, gtm) = (f, h, g, fr, hs, R)
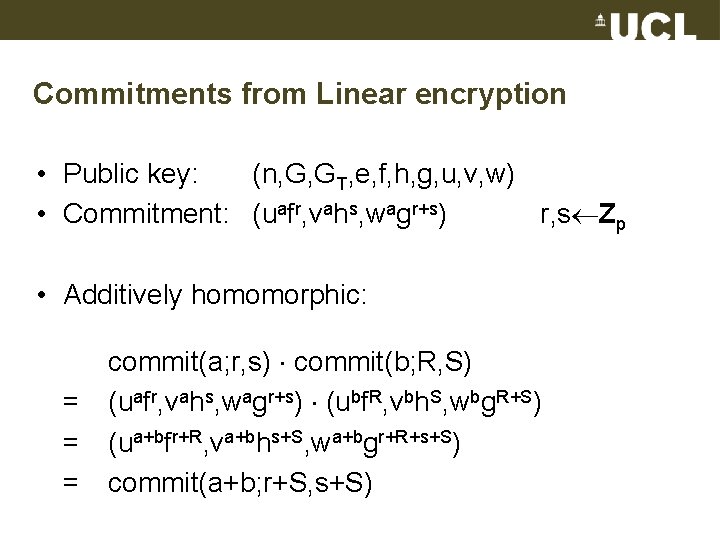
Commitments from Linear encryption • Public key: (n, G, GT, e, f, h, g, u, v, w) • Commitment: (uafr, vahs, wagr+s) r, s Zp • Additively homomorphic: = = = commit(a; r, s) commit(b; R, S) (uafr, vahs, wagr+s) (ubf. R, vbh. S, wbg. R+S) (ua+bfr+R, va+bhs+S, wa+bgr+R+s+S) commit(a+b; r+S, s+S)
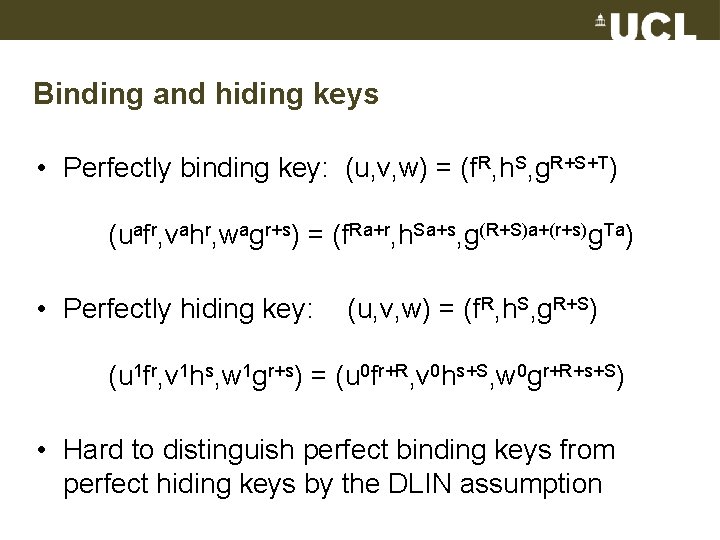
Binding and hiding keys • Perfectly binding key: (u, v, w) = (f. R, h. S, g. R+S+T) (uafr, vahr, wagr+s) = (f. Ra+r, h. Sa+s, g(R+S)a+(r+s)g. Ta) • Perfectly hiding key: (u, v, w) = (f. R, h. S, g. R+S) (u 1 fr, v 1 hs, w 1 gr+s) = (u 0 fr+R, v 0 hs+S, w 0 gr+R+s+S) • Hard to distinguish perfect binding keys from perfect hiding keys by the DLIN assumption
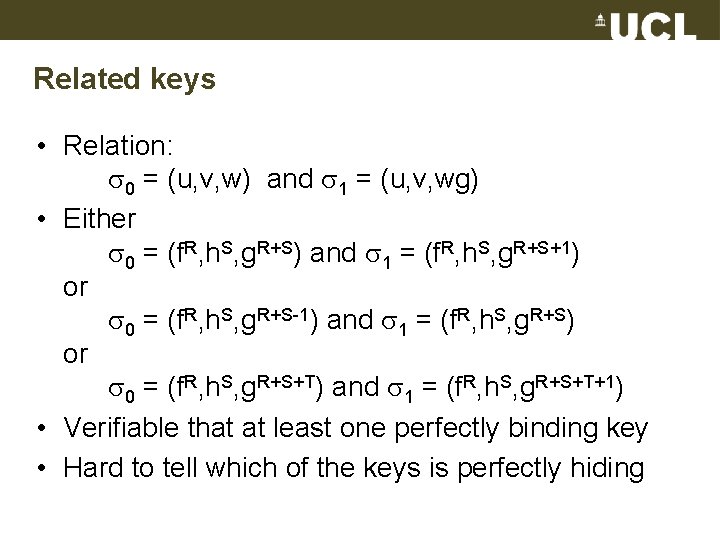
Related keys • Relation: 0 = (u, v, w) and 1 = (u, v, wg) • Either 0 = (f. R, h. S, g. R+S) and 1 = (f. R, h. S, g. R+S+1) or 0 = (f. R, h. S, g. R+S-1) and 1 = (f. R, h. S, g. R+S) or 0 = (f. R, h. S, g. R+S+T) and 1 = (f. R, h. S, g. R+S+T+1) • Verifiable that at least one perfectly binding key • Hard to tell which of the keys is perfectly hiding
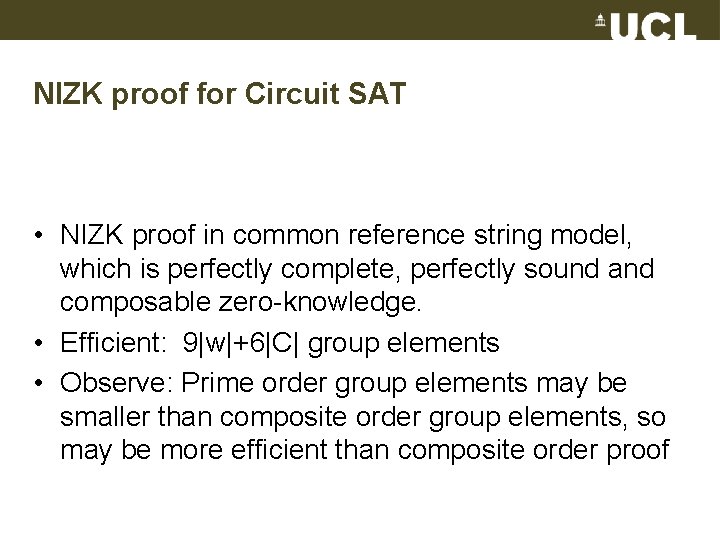
NIZK proof for Circuit SAT • NIZK proof in common reference string model, which is perfectly complete, perfectly sound and composable zero-knowledge. • Efficient: 9|w|+6|C| group elements • Observe: Prime order group elements may be smaller than composite order group elements, so may be more efficient than composite order proof
NIZK proof for Circuit SAT 1 1 (u , v , w 1) Prove w 1 {0, 1} Prove w 2 {0, 1} NAND c 4 commit(w 4) Prove w 4 {0, 1} Prove w 4 = (w 1 w 2) NAND c 1 commit(w 1) Prove w 3 {0, 1} Prove c 3 commit(w 3) 1 = (w 4 w 3) c 2 commit(w 2)
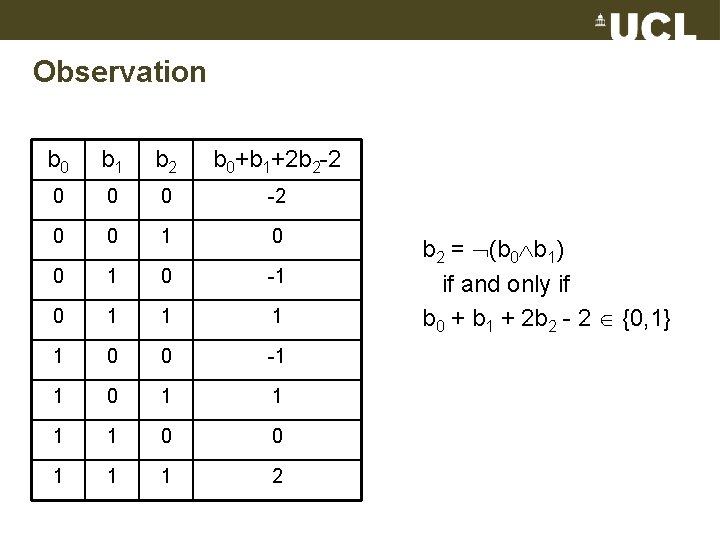
Observation b 0 b 1 b 2 b 0+b 1+2 b 2 -2 0 0 0 -2 0 0 1 0 -1 0 1 1 0 0 -1 1 0 0 1 1 1 2 b 2 = (b 0 b 1) if and only if b 0 + b 1 + 2 b 2 - 2 {0, 1}
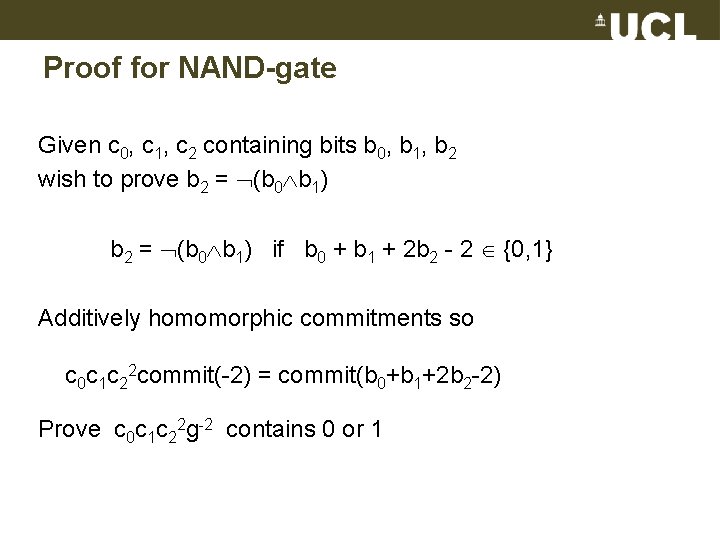
Proof for NAND-gate Given c 0, c 1, c 2 containing bits b 0, b 1, b 2 wish to prove b 2 = (b 0 b 1) if b 0 + b 1 + 2 b 2 - 2 {0, 1} Additively homomorphic commitments so c 0 c 1 c 22 commit(-2) = commit(b 0+b 1+2 b 2 -2) Prove c 0 c 1 c 22 g-2 contains 0 or 1
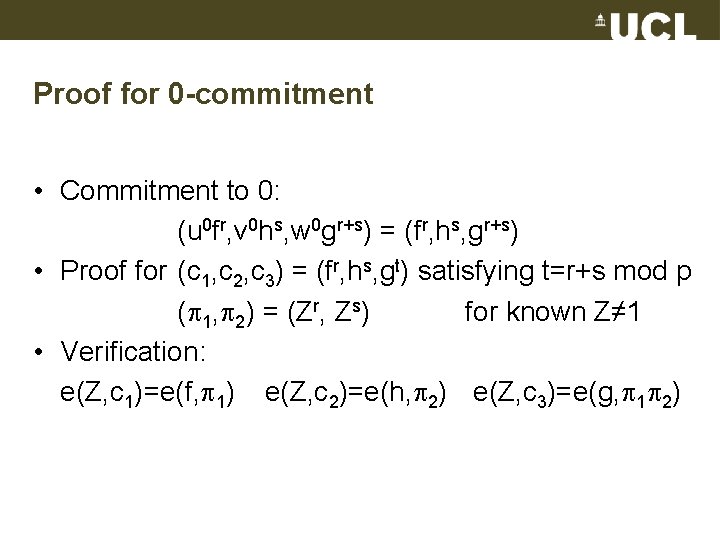
Proof for 0 -commitment • Commitment to 0: (u 0 fr, v 0 hs, w 0 gr+s) = (fr, hs, gr+s) • Proof for (c 1, c 2, c 3) = (fr, hs, gt) satisfying t=r+s mod p ( 1, 2) = (Zr, Zs) for known Z≠ 1 • Verification: e(Z, c 1)=e(f, 1) e(Z, c 2)=e(h, 2) e(Z, c 3)=e(g, 1 2)
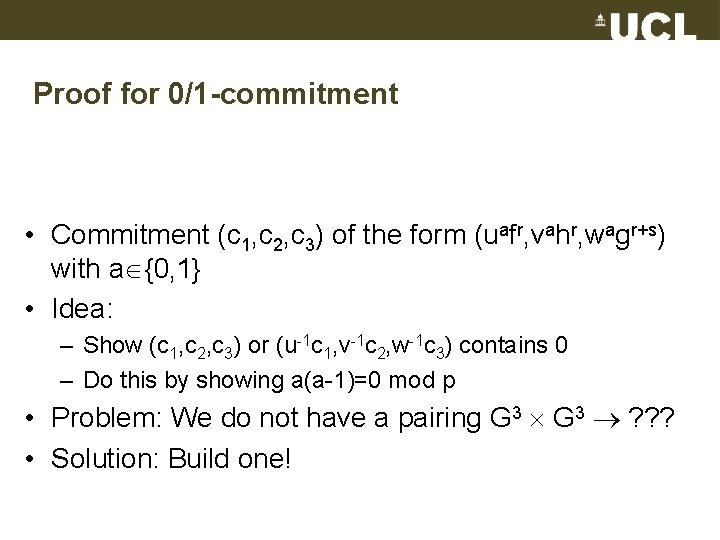
Proof for 0/1 -commitment • Commitment (c 1, c 2, c 3) of the form (uafr, vahr, wagr+s) with a {0, 1} • Idea: – Show (c 1, c 2, c 3) or (u-1 c 1, v-1 c 2, w-1 c 3) contains 0 – Do this by showing a(a-1)=0 mod p • Problem: We do not have a pairing G 3 ? ? ? • Solution: Build one!
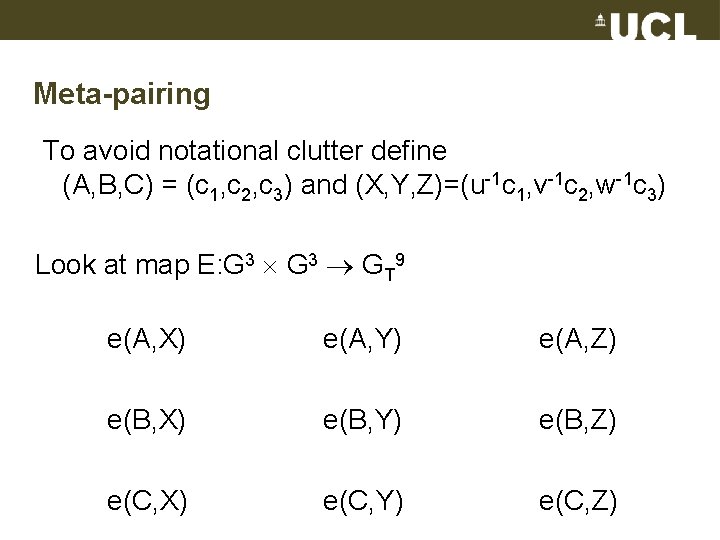
Meta-pairing To avoid notational clutter define (A, B, C) = (c 1, c 2, c 3) and (X, Y, Z)=(u-1 c 1, v-1 c 2, w-1 c 3) Look at map E: G 3 GT 9 e(A, X) e(A, Y) e(A, Z) e(B, X) e(B, Y) e(B, Z) e(C, X) e(C, Y) e(C, Z)
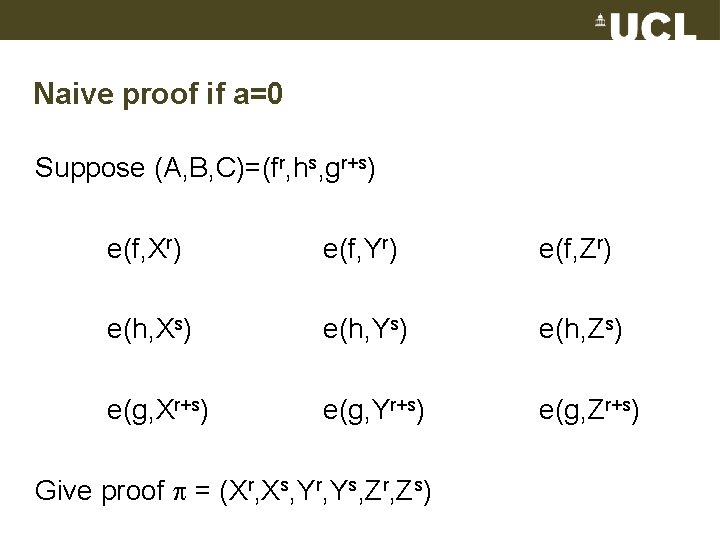
Naive proof if a=0 Suppose (A, B, C)=(fr, hs, gr+s) e(f, Xr) e(f, Yr) e(f, Zr) e(h, Xs) e(h, Ys) e(h, Zs) e(g, Xr+s) e(g, Yr+s) e(g, Zr+s) Give proof = (Xr, Xs, Yr, Ys, Zr, Zs)
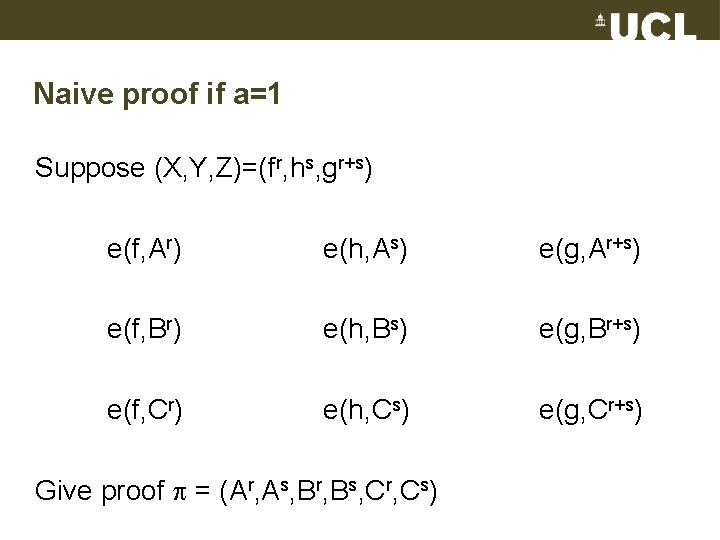
Naive proof if a=1 Suppose (X, Y, Z)=(fr, hs, gr+s) e(f, Ar) e(h, As) e(g, Ar+s) e(f, Br) e(h, Bs) e(g, Br+s) e(f, Cr) e(h, Cs) e(g, Cr+s) Give proof = (Ar, As, Br, Bs, Cr, Cs)
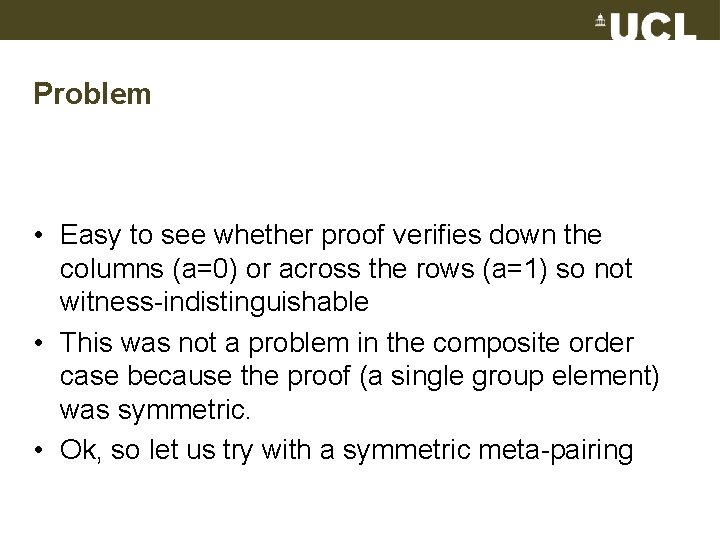
Problem • Easy to see whether proof verifies down the columns (a=0) or across the rows (a=1) so not witness-indistinguishable • This was not a problem in the composite order case because the proof (a single group element) was symmetric. • Ok, so let us try with a symmetric meta-pairing
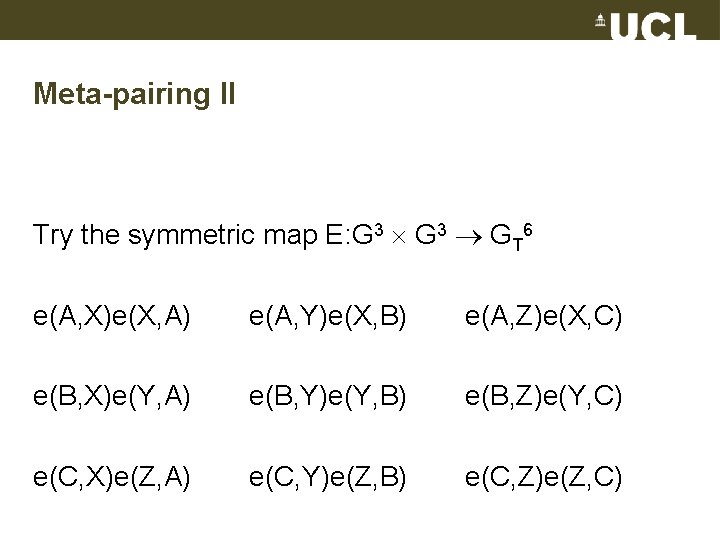
Meta-pairing II Try the symmetric map E: G 3 GT 6 e(A, X)e(X, A) e(A, Y)e(X, B) e(A, Z)e(X, C) e(B, X)e(Y, A) e(B, Y)e(Y, B) e(B, Z)e(Y, C) e(C, X)e(Z, A) e(C, Y)e(Z, B) e(C, Z)e(Z, C)
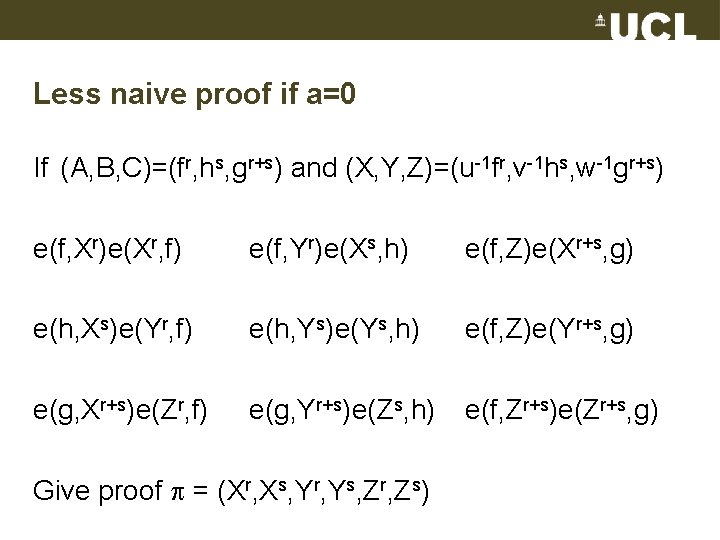
Less naive proof if a=0 If (A, B, C)=(fr, hs, gr+s) and (X, Y, Z)=(u-1 fr, v-1 hs, w-1 gr+s) e(f, Xr)e(Xr, f) e(f, Yr)e(Xs, h) e(f, Z)e(Xr+s, g) e(h, Xs)e(Yr, f) e(h, Ys)e(Ys, h) e(f, Z)e(Yr+s, g) e(g, Xr+s)e(Zr, f) e(g, Yr+s)e(Zs, h) e(f, Zr+s)e(Zr+s, g) Give proof = (Xr, Xs, Yr, Ys, Zr, Zs)
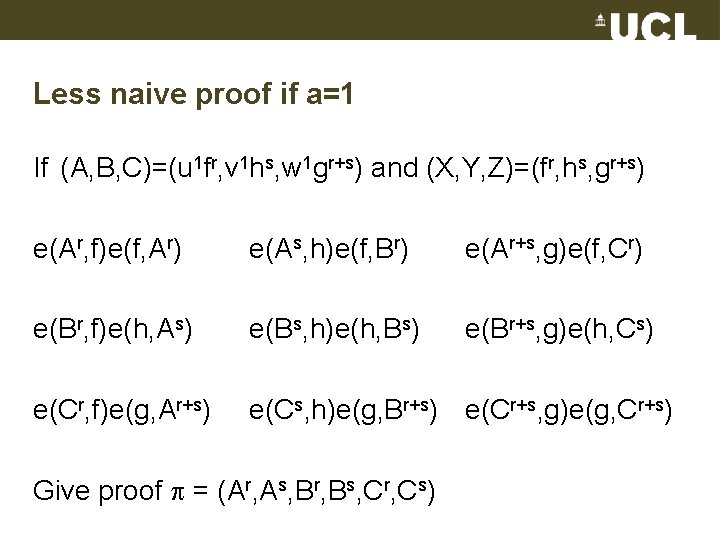
Less naive proof if a=1 If (A, B, C)=(u 1 fr, v 1 hs, w 1 gr+s) and (X, Y, Z)=(fr, hs, gr+s) e(Ar, f)e(f, Ar) e(As, h)e(f, Br) e(Ar+s, g)e(f, Cr) e(Br, f)e(h, As) e(Bs, h)e(h, Bs) e(Br+s, g)e(h, Cs) e(Cr, f)e(g, Ar+s) e(Cs, h)e(g, Br+s) e(Cr+s, g)e(g, Cr+s) Give proof = (Ar, As, Br, Bs, Cr, Cs)
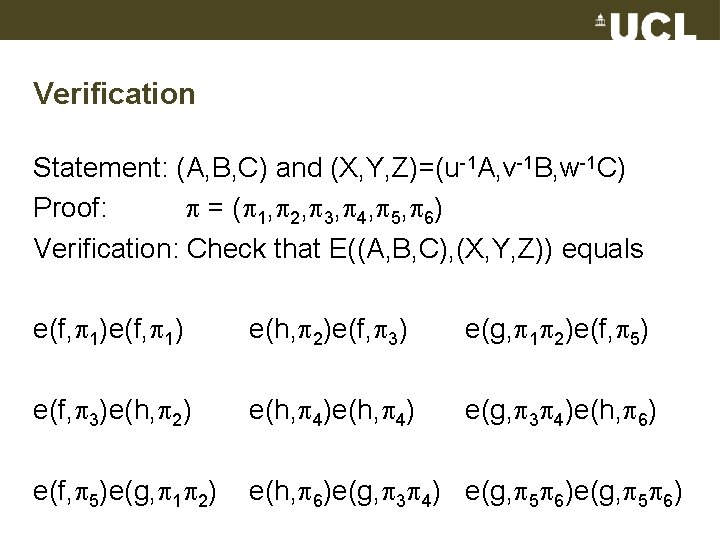
Verification Statement: (A, B, C) and (X, Y, Z)=(u-1 A, v-1 B, w-1 C) Proof: = ( 1, 2, 3, 4, 5, 6) Verification: Check that E((A, B, C), (X, Y, Z)) equals e(f, 1) e(h, 2)e(f, 3) e(g, 1 2)e(f, 5) e(f, 3)e(h, 2) e(h, 4) e(g, 3 4)e(h, 6) e(f, 5)e(g, 1 2) e(h, 6)e(g, 3 4) e(g, 5 6)
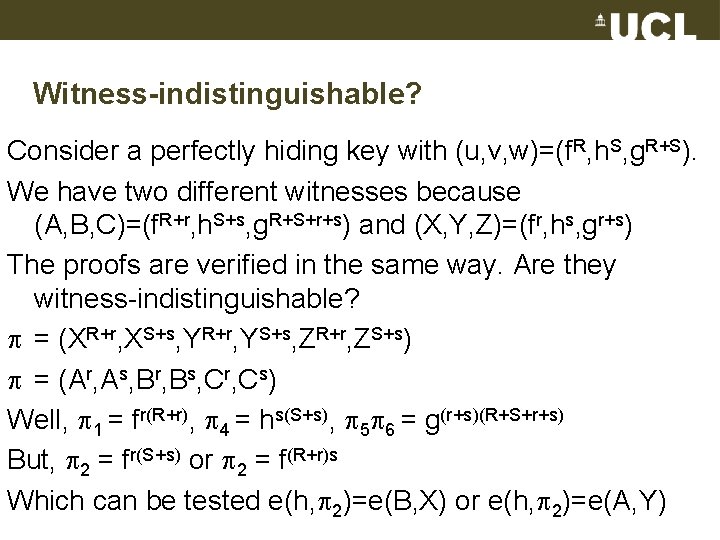
Witness-indistinguishable? Consider a perfectly hiding key with (u, v, w)=(f. R, h. S, g. R+S). We have two different witnesses because (A, B, C)=(f. R+r, h. S+s, g. R+S+r+s) and (X, Y, Z)=(fr, hs, gr+s) The proofs are verified in the same way. Are they witness-indistinguishable? = (XR+r, XS+s, YR+r, YS+s, ZR+r, ZS+s) = (Ar, As, Br, Bs, Cr, Cs) Well, 1 = fr(R+r), 4 = hs(S+s), 5 6 = g(r+s)(R+S+r+s) But, 2 = fr(S+s) or 2 = f(R+r)s Which can be tested e(h, 2)=e(B, X) or e(h, 2)=e(A, Y)
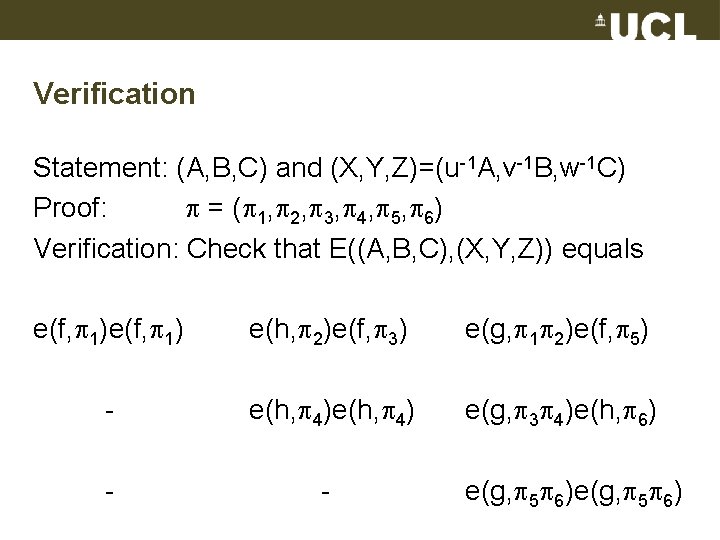
Verification Statement: (A, B, C) and (X, Y, Z)=(u-1 A, v-1 B, w-1 C) Proof: = ( 1, 2, 3, 4, 5, 6) Verification: Check that E((A, B, C), (X, Y, Z)) equals e(f, 1) e(h, 2)e(f, 3) e(g, 1 2)e(f, 5) - e(h, 4) e(g, 3 4)e(h, 6) - - e(g, 5 6)
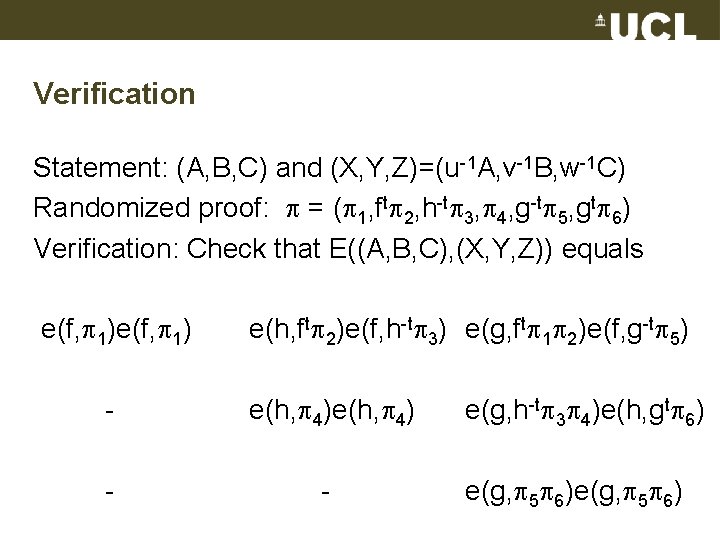
Verification Statement: (A, B, C) and (X, Y, Z)=(u-1 A, v-1 B, w-1 C) Randomized proof: = ( 1, ft 2, h-t 3, 4, g-t 5, gt 6) Verification: Check that E((A, B, C), (X, Y, Z)) equals e(f, 1) e(h, ft 2)e(f, h-t 3) e(g, ft 1 2)e(f, g-t 5) - e(h, 4) - - e(g, h-t 3 4)e(h, gt 6) e(g, 5 6)
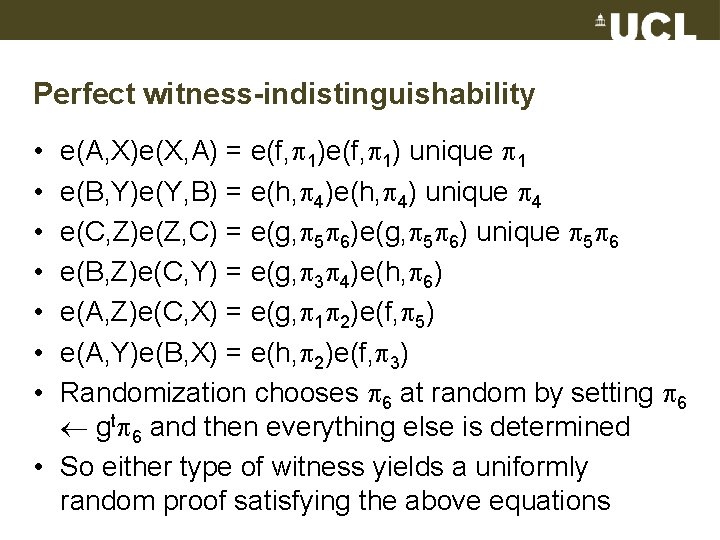
Perfect witness-indistinguishability e(A, X)e(X, A) = e(f, 1) unique 1 e(B, Y)e(Y, B) = e(h, 4) unique 4 e(C, Z)e(Z, C) = e(g, 5 6) unique 5 6 e(B, Z)e(C, Y) = e(g, 3 4)e(h, 6) e(A, Z)e(C, X) = e(g, 1 2)e(f, 5) e(A, Y)e(B, X) = e(h, 2)e(f, 3) Randomization chooses 6 at random by setting 6 gt 6 and then everything else is determined • So either type of witness yields a uniformly random proof satisfying the above equations • •
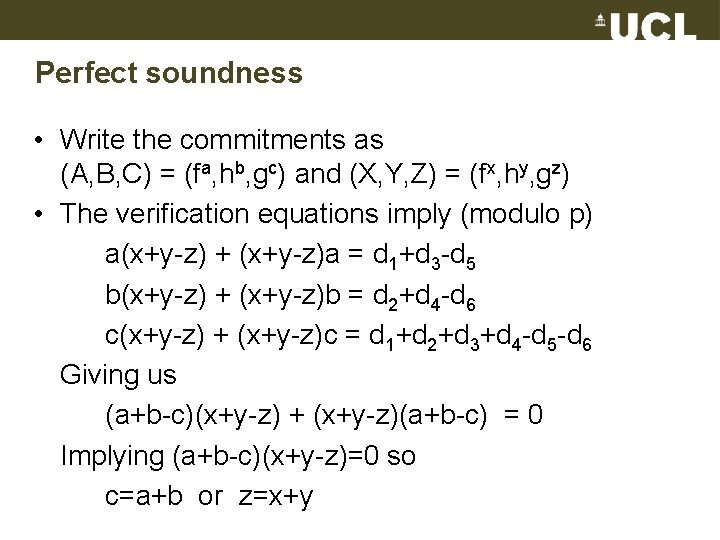
Perfect soundness • Write the commitments as (A, B, C) = (fa, hb, gc) and (X, Y, Z) = (fx, hy, gz) • The verification equations imply (modulo p) a(x+y-z) + (x+y-z)a = d 1+d 3 -d 5 b(x+y-z) + (x+y-z)b = d 2+d 4 -d 6 c(x+y-z) + (x+y-z)c = d 1+d 2+d 3+d 4 -d 5 -d 6 Giving us (a+b-c)(x+y-z) + (x+y-z)(a+b-c) = 0 Implying (a+b-c)(x+y-z)=0 so c=a+b or z=x+y
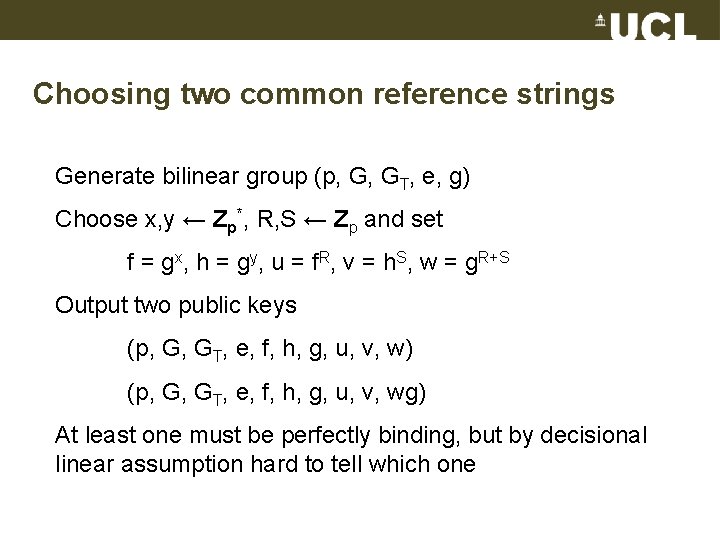
Choosing two common reference strings Generate bilinear group (p, G, GT, e, g) Choose x, y ← Zp*, R, S ← Zp and set f = gx, h = gy, u = f. R, v = h. S, w = g. R+S Output two public keys (p, G, GT, e, f, h, g, u, v, w) (p, G, GT, e, f, h, g, u, v, wg) At least one must be perfectly binding, but by decisional linear assumption hard to tell which one
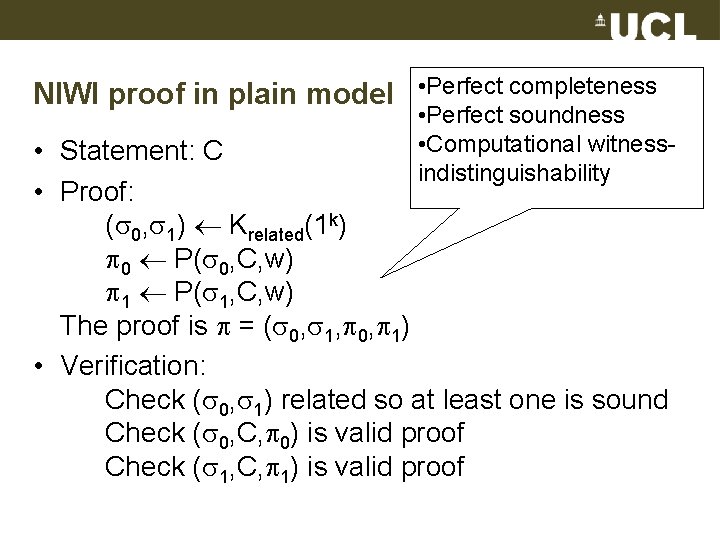
NIWI proof in plain model • Perfect completeness • Perfect soundness • Computational witnessindistinguishability • Statement: C • Proof: ( 0, 1) Krelated(1 k) 0 P( 0, C, w) 1 P( 1, C, w) The proof is = ( 0, 1, 0, 1) • Verification: Check ( 0, 1) related so at least one is sound Check ( 0, C, 0) is valid proof Check ( 1, C, 1) is valid proof
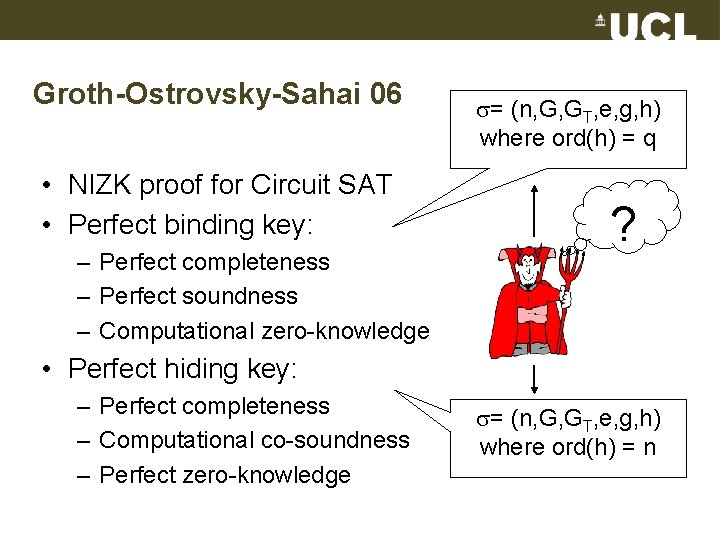
Groth-Ostrovsky-Sahai 06 • NIZK proof for Circuit SAT • Perfect binding key: – Perfect completeness – Perfect soundness – Computational zero-knowledge = (n, G, GT, e, g, h) where ord(h) = q ? • Perfect hiding key: – Perfect completeness – Computational co-soundness – Perfect zero-knowledge = (n, G, GT, e, g, h) where ord(h) = n
Efficiency problems with non-interactive zero -knowledge proofs • Non-interactive proofs for general NP-complete language such as Circuit SAT. Any practical statement such as ”the ciphertext c contains a signature on this message m” must go through a size-increasing NP-reduction.
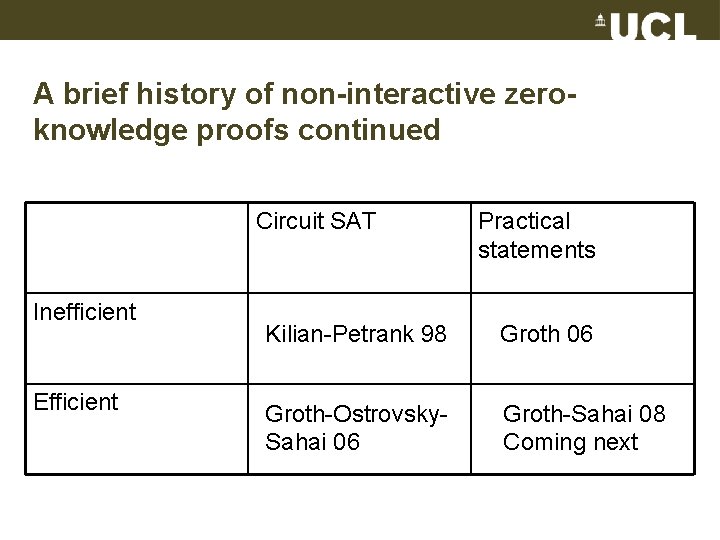
A brief history of non-interactive zeroknowledge proofs continued Circuit SAT Inefficient Efficient Practical statements Kilian-Petrank 98 Groth 06 Groth-Ostrovsky. Sahai 06 Groth-Sahai 08 Coming next
Our goal • We want high efficiency. Practical non-interactive proofs! • We want non-interactive proofs for statements arising in practice such as ”the ciphertext c contains a signature on m”. No NP-reduction!
Constructions in bilinear groups a, c G , b, d Zn t = b+yd (mod n) t. G = xyayct t. T = e(t. G, ct. Gb)
Non-interactive cryptographic proofs for correctness of constructions Yes, here is a proof. Are the constructions correct? I do not know your secret x, y. t = b+yd (mod n) t. G = xyayct t. T = e(t. G, ct. Gb) Proof
Cryptographic constructions • Constructions can be built from – public exponents and public group elements – secret exponents and secret group elements • Using any of the bilinear group operations – – Addition and multiplication of exponents Multiplication of elements in G Bilinear map e Multiplication in GT • Our goal: Non-interactive cryptographic proofs for correctness of a set of bilinear group constructions (soundness holds for the order p subgroups of G and Zn)
Examples of statements we can prove • Here is a ciphertext c and a signature s. They have been constructed such that s is a signature on the secret plaintext. • Here are three commitments A, B and C to secret exponents a, b and c. They have been constructed such that c=ab mod p.
Applications of efficient NIWI and NIZK proofs • Constant size group signatures Boyen-Waters 07 (independently of our work) Groth 07 • Sub-linear size ring signatures Chandran-Groth-Sahai 07 • Non-interactive NIZK proof for correctness of shuffle Groth-Lu 07 • Non-interactive anonymous credentials Belienky-Chase-Kohlweiss-Lysyanskaya 08 • …
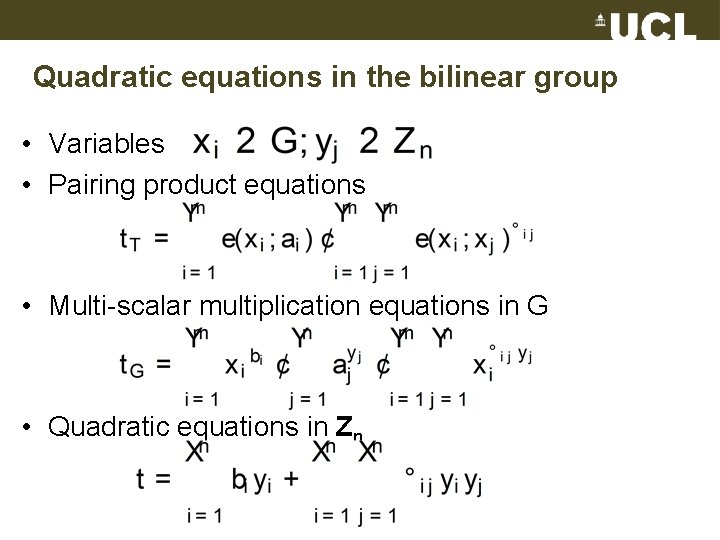
Quadratic equations in the bilinear group • Variables • Pairing product equations • Multi-scalar multiplication equations in G • Quadratic equations in Zn
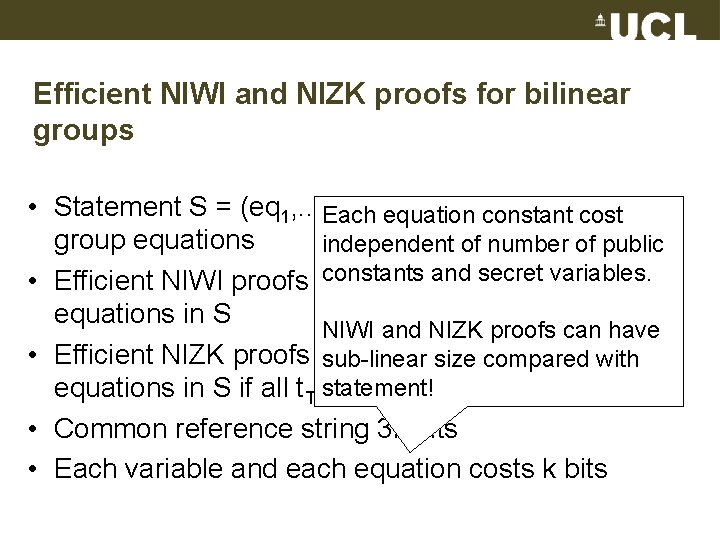
Efficient NIWI and NIZK proofs for bilinear groups • Statement S = (eq 1, . . . , eq quadratic bilinear N)equation Each constant cost group equations independent of number of public constants and secret variables. • Efficient NIWI proofs for satisfiability of all equations in S NIWI and NIZK proofs can have • Efficient NIZK proofs for satisfiability of all with sub-linear size compared statement! equations in S if all t. T=1 • Common reference string 3 k bits • Each variable and each equation costs k bits
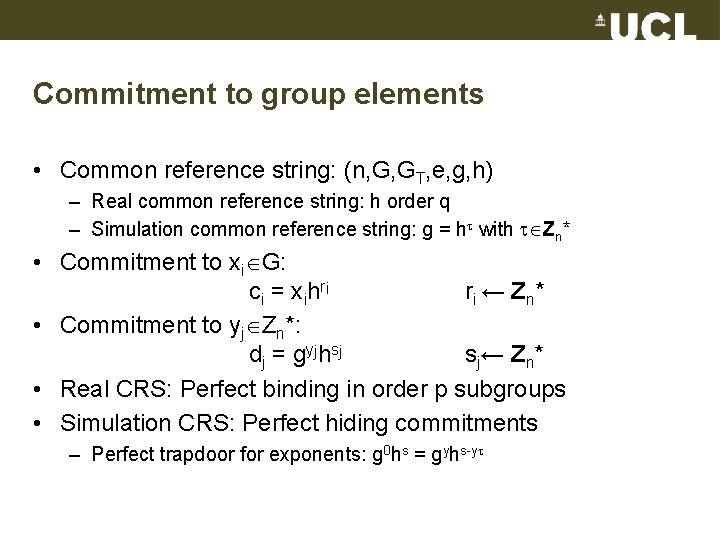
Commitment to group elements • Common reference string: (n, G, GT, e, g, h) – Real common reference string: h order q – Simulation common reference string: g = h with Zn* • Commitment to xi G: ci = xihri ri ← Z n * • Commitment to yj Zn*: d j = g yj h sj sj← Zn* • Real CRS: Perfect binding in order p subgroups • Simulation CRS: Perfect hiding commitments – Perfect trapdoor for exponents: g 0 hs = gyhs-y
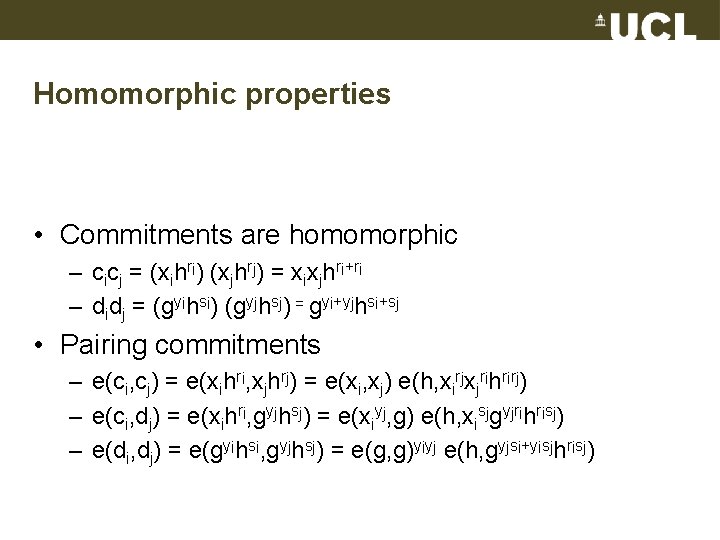
Homomorphic properties • Commitments are homomorphic – cicj = (xihri) (xjhrj) = xixjhri+ri – didj = (gyihsi) (gyjhsj) = gyi+yjhsi+sj • Pairing commitments – e(ci, cj) = e(xihri, xjhrj) = e(xi, xj) e(h, xirjxjrihrirj) – e(ci, dj) = e(xihri, gyjhsj) = e(xiyj, g) e(h, xisjgyjrihrisj) – e(di, dj) = e(gyihsi, gyjhsj) = e(g, g)yiyj e(h, gyjsi+yisjhrisj)
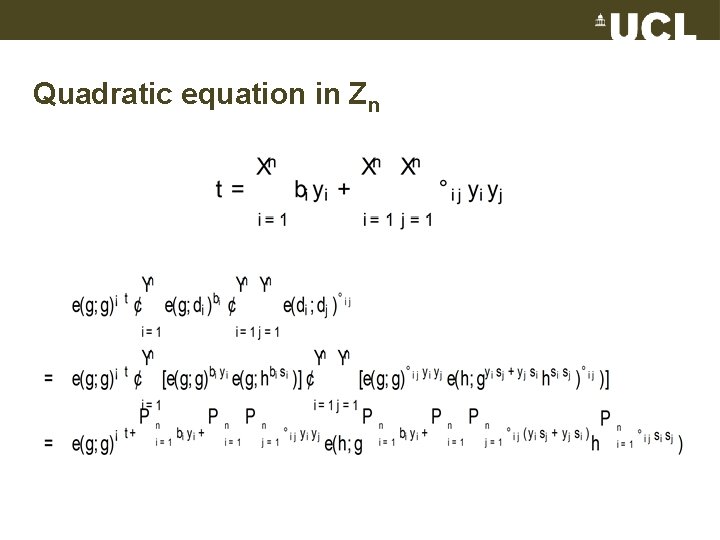
Quadratic equation in Zn
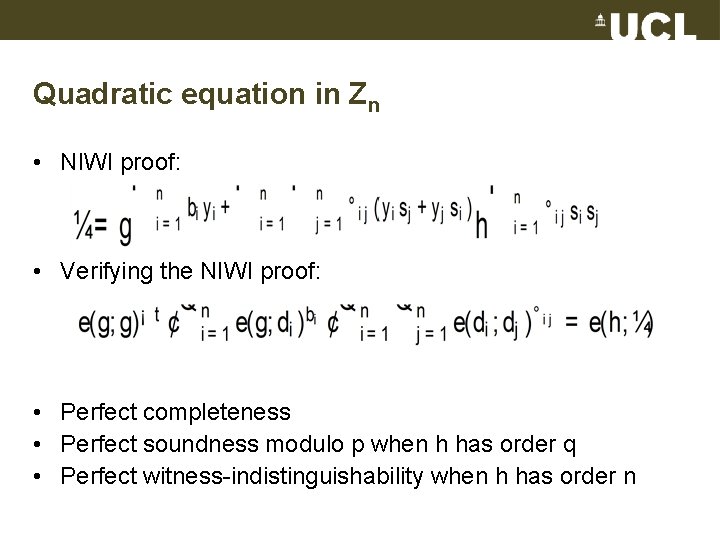
Quadratic equation in Zn • NIWI proof: • Verifying the NIWI proof: • Perfect completeness • Perfect soundness modulo p when h has order q • Perfect witness-indistinguishability when h has order n
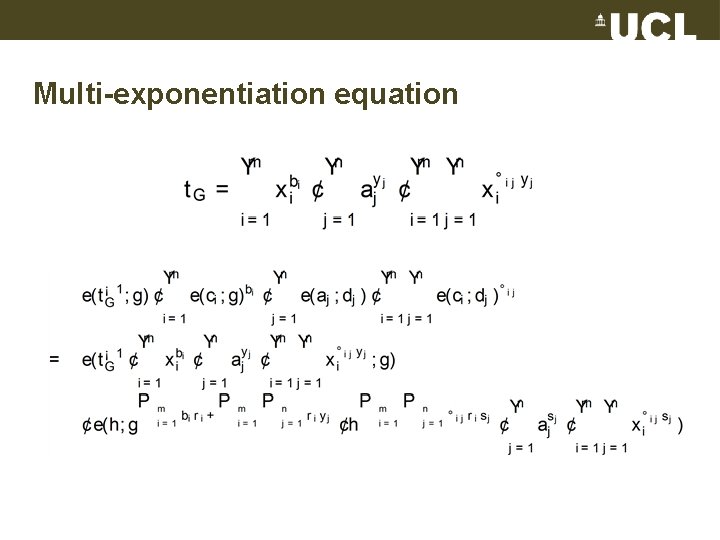
Multi-exponentiation equation
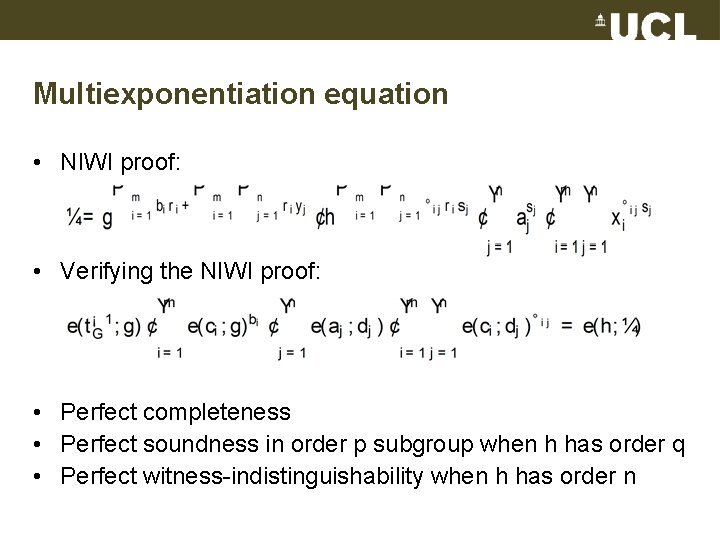
Multiexponentiation equation • NIWI proof: • Verifying the NIWI proof: • Perfect completeness • Perfect soundness in order p subgroup when h has order q • Perfect witness-indistinguishability when h has order n
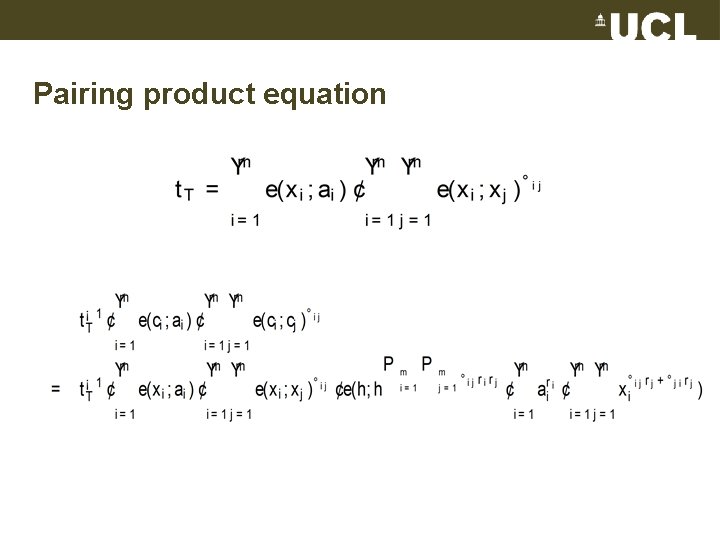
Pairing product equation
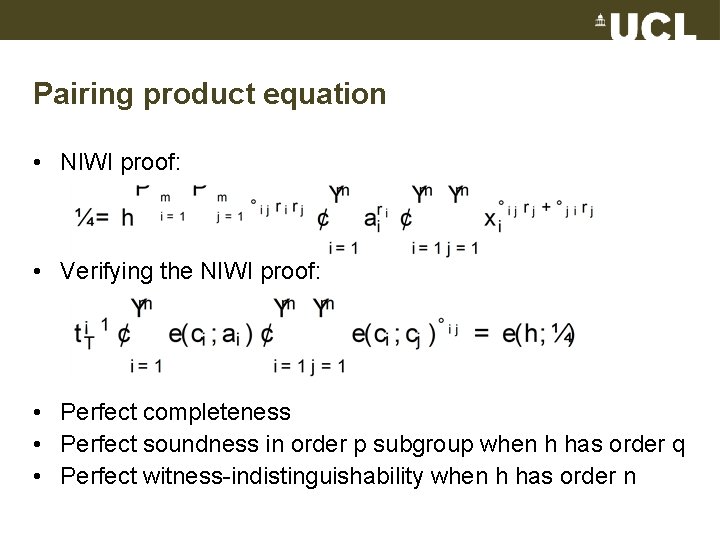
Pairing product equation • NIWI proof: • Verifying the NIWI proof: • Perfect completeness • Perfect soundness in order p subgroup when h has order q • Perfect witness-indistinguishability when h has order n
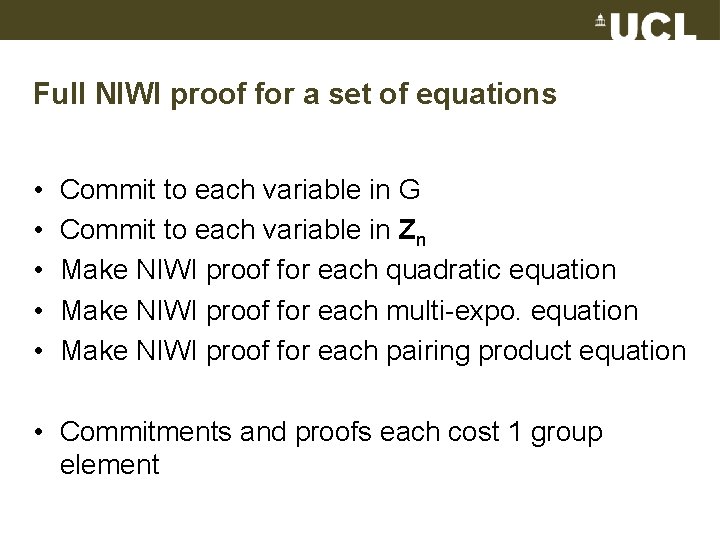
Full NIWI proof for a set of equations • • • Commit to each variable in G Commit to each variable in Zn Make NIWI proof for each quadratic equation Make NIWI proof for each multi-expo. equation Make NIWI proof for each pairing product equation • Commitments and proofs each cost 1 group element
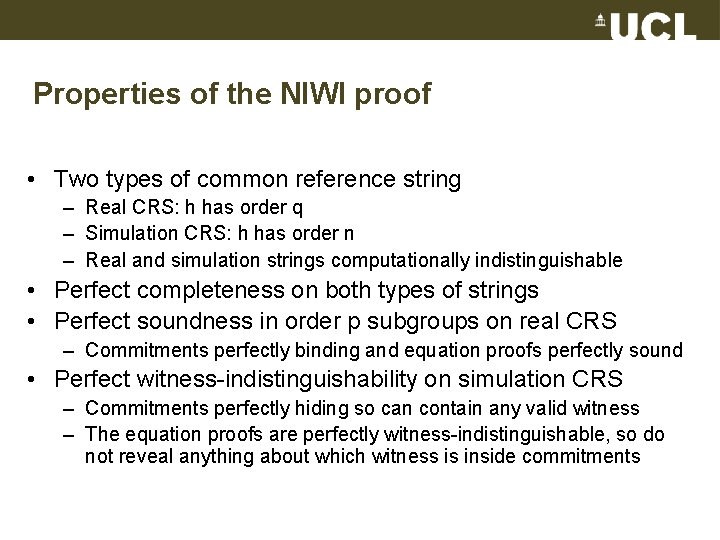
Properties of the NIWI proof • Two types of common reference string – Real CRS: h has order q – Simulation CRS: h has order n – Real and simulation strings computationally indistinguishable • Perfect completeness on both types of strings • Perfect soundness in order p subgroups on real CRS – Commitments perfectly binding and equation proofs perfectly sound • Perfect witness-indistinguishability on simulation CRS – Commitments perfectly hiding so can contain any valid witness – The equation proofs are perfectly witness-indistinguishable, so do not reveal anything about which witness is inside commitments
NIZK proofs • Is our NIWI proof zero-knowledge? • Problem: The simulator may not know a witness • Answer: If all pairing product equations have t. T=1, then the proof is perfect zero-knowledge on a simulation CRS where h has order n
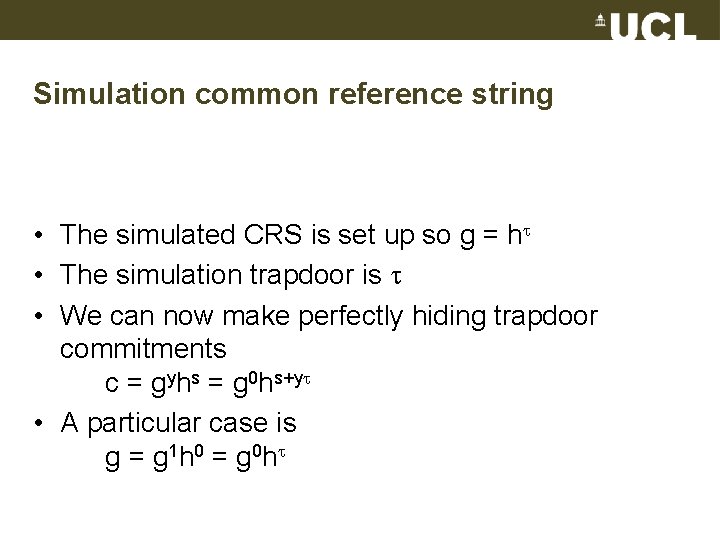
Simulation common reference string • The simulated CRS is set up so g = h • The simulation trapdoor is • We can now make perfectly hiding trapdoor commitments c = gyhs = g 0 hs+y • A particular case is g = g 1 h 0 = g 0 h
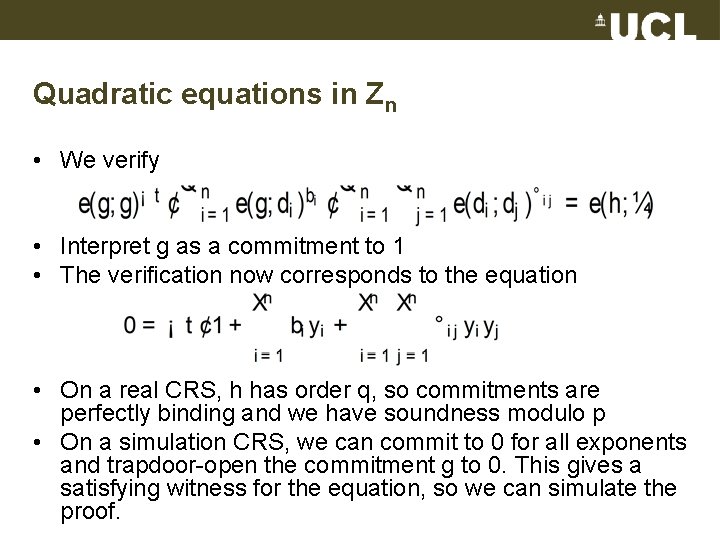
Quadratic equations in Zn • We verify • Interpret g as a commitment to 1 • The verification now corresponds to the equation • On a real CRS, h has order q, so commitments are perfectly binding and we have soundness modulo p • On a simulation CRS, we can commit to 0 for all exponents and trapdoor-open the commitment g to 0. This gives a satisfying witness for the equation, so we can simulate the proof.
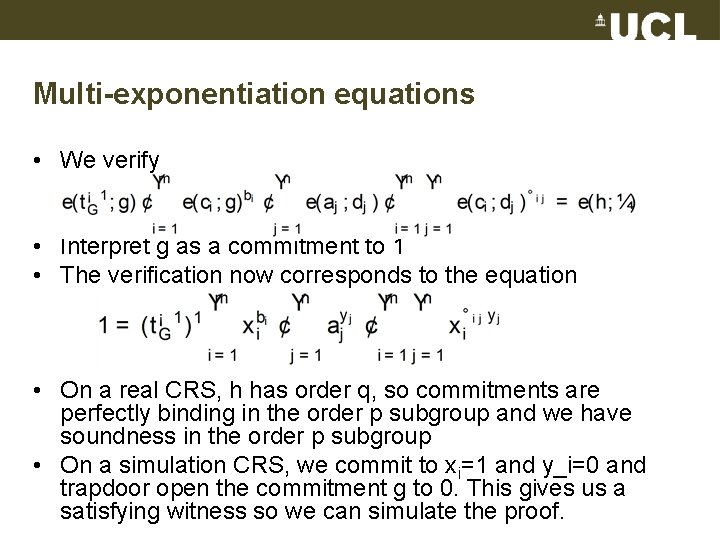
Multi-exponentiation equations • We verify • Interpret g as a commitment to 1 • The verification now corresponds to the equation • On a real CRS, h has order q, so commitments are perfectly binding in the order p subgroup and we have soundness in the order p subgroup • On a simulation CRS, we commit to xi=1 and y_i=0 and trapdoor open the commitment g to 0. This gives us a satisfying witness so we can simulate the proof.
Pairing product equations • We restrict to pairing product equations with t. T=1 • This means (x 1=1, . . . , xm=1) is a satisfying witness
Perfect zero-knowledge • For all three types of equations, we use witness xi=1 and yj=0, so the three types of simulation fit together • The perfect witness-indistinguishability of the NIWI proof implies perfect zero-knowledge; the real witness cannot be distinguished from the witness we get when trapdoor opening g to 0
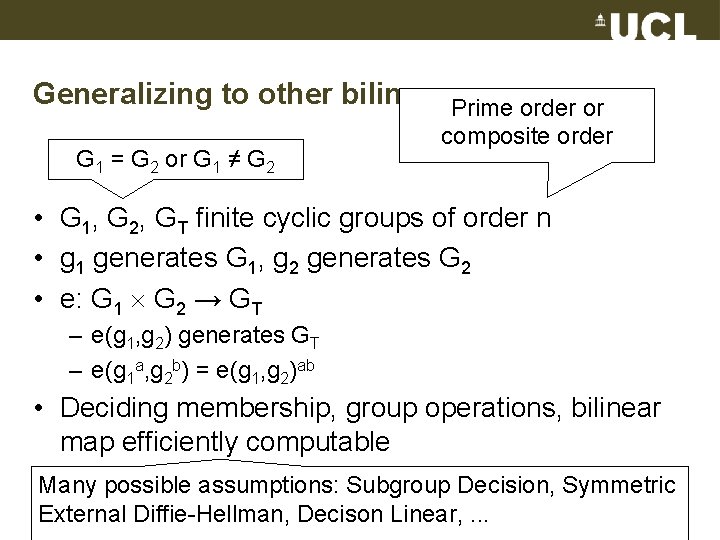
Generalizing to other bilinear Prime groups order or G 1 = G 2 or G 1 ≠ G 2 composite order • G 1, G 2, GT finite cyclic groups of order n • g 1 generates G 1, g 2 generates G 2 • e: G 1 G 2 → GT – e(g 1, g 2) generates GT – e(g 1 a, g 2 b) = e(g 1, g 2)ab • Deciding membership, group operations, bilinear map efficiently computable Many possible assumptions: Subgroup Decision, Symmetric External Diffie-Hellman, Decison Linear, . . .
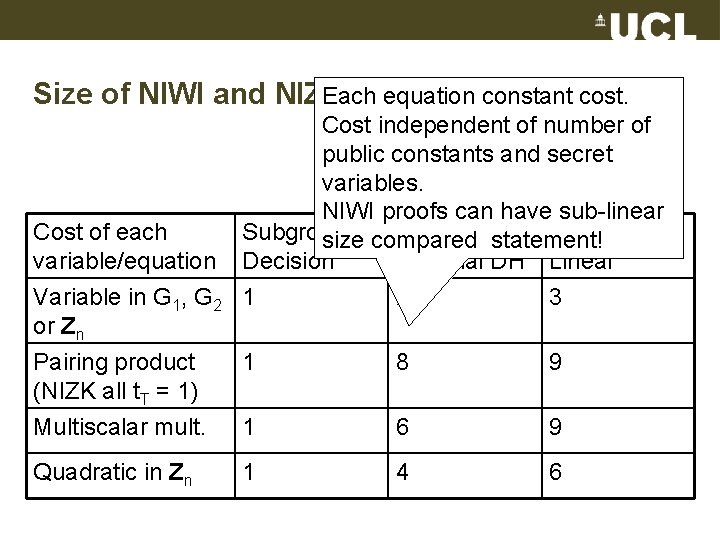
Each equation constant cost. Size of NIWI and NIZK proofs Cost of each variable/equation Variable in G 1, G 2 or Zn Cost independent of number of public constants and secret variables. NIWI proofs can have sub-linear Subgroup Symmetric Decision size compared statement! Decision External DH Linear 1 2 3 Pairing product (NIZK all t. T = 1) Multiscalar mult. 1 8 9 1 6 9 Quadratic in Zn 1 4 6
Bilinear groups as bilinear modules • View bilinear groups as special cases of modules with a bilinear map • Commutative ring R • R-modules A 1, A 2, AT • Bilinear map f: A 1 A 2 → AT • Map to another set of R-modules B 1, B 2, BT • Bilinear map F: B 1 B 2 → BT
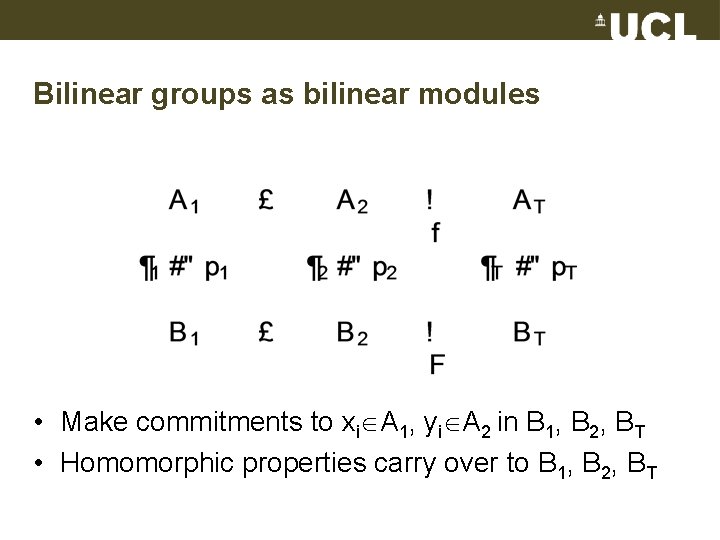
Bilinear groups as bilinear modules • Make commitments to xi A 1, yi A 2 in B 1, B 2, BT • Homomorphic properties carry over to B 1, B 2, BT
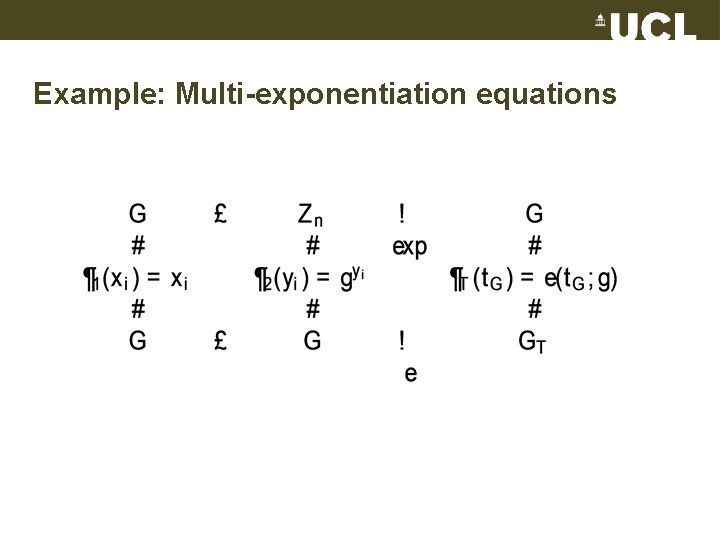
Example: Multi-exponentiation equations
Generality continued • All four types of bilinear group equations can be seen as example of quadratic equations over modules with bilinear map • The assumptions Subgroup Decision, Symmetric External Diffie-Hellman, Decision Linear, etc. , can be interpreted as assumptions in modules with bilinear map as well
Summary • Practical: – Efficient NIWI and NIZK proofs for practical statements arising in pairing-based cryptography • Theoretical: – Perfect zero-knowledge – Witness-indistinguishability in the plain model • Upcoming: – Quasi-linear size NIZK proofs without pairings – NIZK arguments with smaller size than circuit
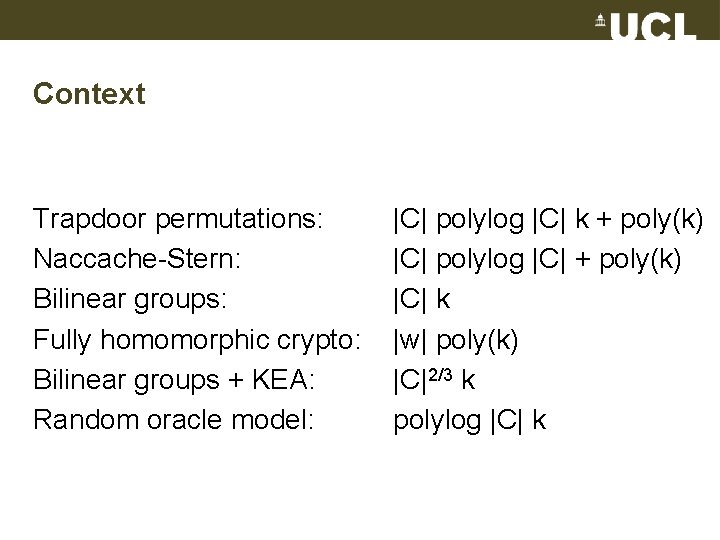
Context Trapdoor permutations: Naccache-Stern: Bilinear groups: Fully homomorphic crypto: Bilinear groups + KEA: Random oracle model: |C| polylog |C| k + poly(k) |C| polylog |C| + poly(k) |C| k |w| poly(k) |C|2/3 k polylog |C| k
Open problems • • • Even more efficient NIZK proofs Efficient post-quantum NIZK proofs from one-way functions Non-interactive witness-hiding proofs in plain model Construct cryptographically useful modules with bilinear map that are not based on bilinear groups • Continuous NIZK arguments
References • Chapman et al. : Life of Brian. BBC 1979. • Groth, Sahai: Efficient Non-interactive Proofs for Bilinear Groups. EUROCRYPT 2008. • Groth, Sahai, Ostrovsky: New Techniques for Noninteractive Zero-Knowledge. EWSCS 2010. • Lipmaa: Collected works. Springer 1998 • Rhinehart: The Dice Man. Harper. Collins 1971. • Tolkien: Lord of the Rings. Allen and Unwin 1954 -1955. • Zhang: Fuzzy Private Matching and Privacy Preserving Information Retrieval. UCL MSc thesis 2008.
Thanks ? Any (more) questions?
- Slides: 129