Cryptography in Subgroups of Zn Jens Groth UCLA
Cryptography in * Subgroups of Zn Jens Groth UCLA
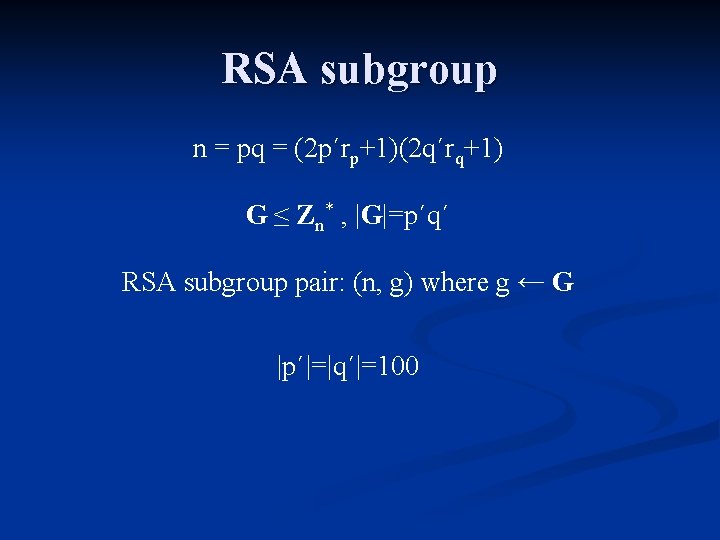
RSA subgroup n = pq = (2 p´rp+1)(2 q´rq+1) G ≤ Zn* , |G|=p´q´ RSA subgroup pair: (n, g) where g ← G |p´|=|q´|=100
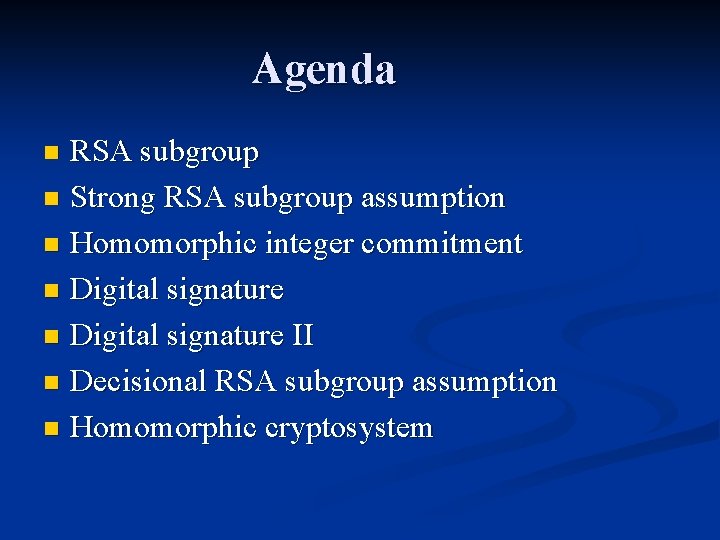
Agenda RSA subgroup n Strong RSA subgroup assumption n Homomorphic integer commitment n Digital signature II n Decisional RSA subgroup assumption n Homomorphic cryptosystem n
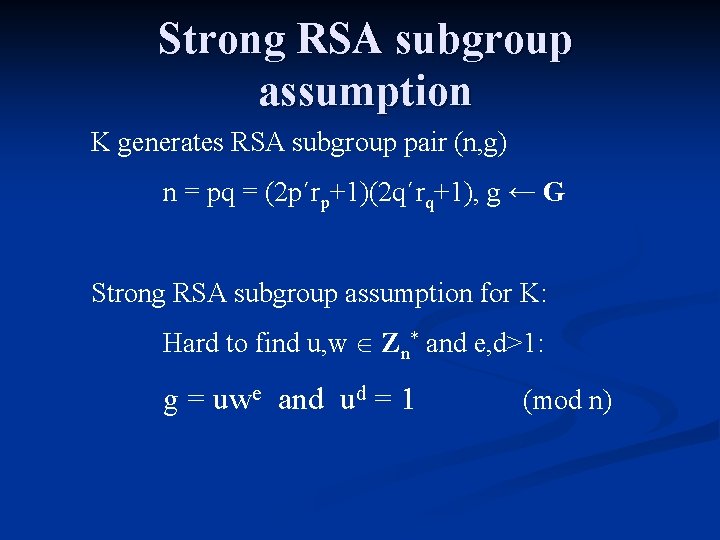
Strong RSA subgroup assumption K generates RSA subgroup pair (n, g) n = pq = (2 p´rp+1)(2 q´rq+1), g ← G Strong RSA subgroup assumption for K: Hard to find u, w Zn* and e, d>1: g = uwe and ud = 1 (mod n)
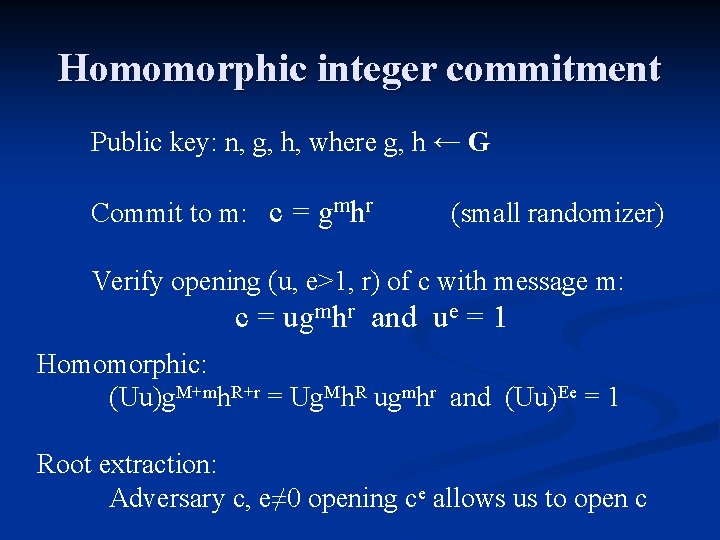
Homomorphic integer commitment Public key: n, g, h, where g, h ← G Commit to m: c = gmhr (small randomizer) Verify opening (u, e>1, r) of c with message m: c = ugmhr and ue = 1 Homomorphic: (Uu)g. M+mh. R+r = Ug. Mh. R ugmhr and (Uu)Ee = 1 Root extraction: Adversary c, e≠ 0 opening ce allows us to open c
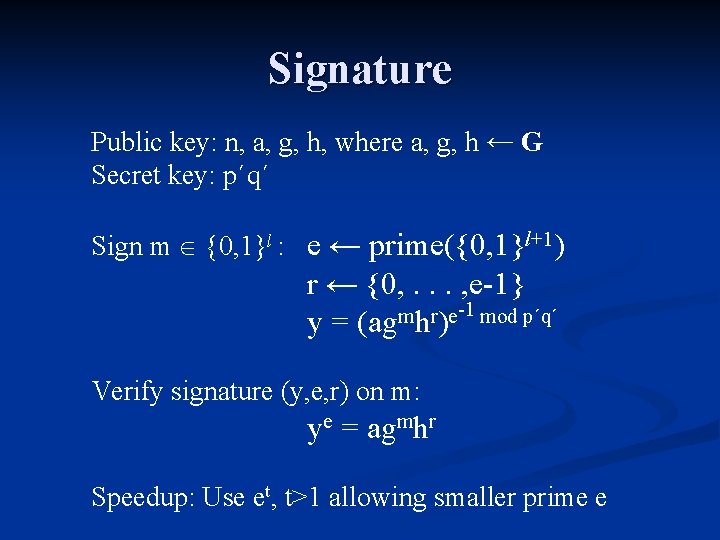
Signature Public key: n, a, g, h, where a, g, h ← G Secret key: p´q´ Sign m {0, 1}l : e ← prime({0, 1}l+1) r ← {0, . . . , e-1} -1 mod p´q´ m r e y = (ag h ) Verify signature (y, e, r) on m: ye = agmhr Speedup: Use et, t>1 allowing smaller prime e
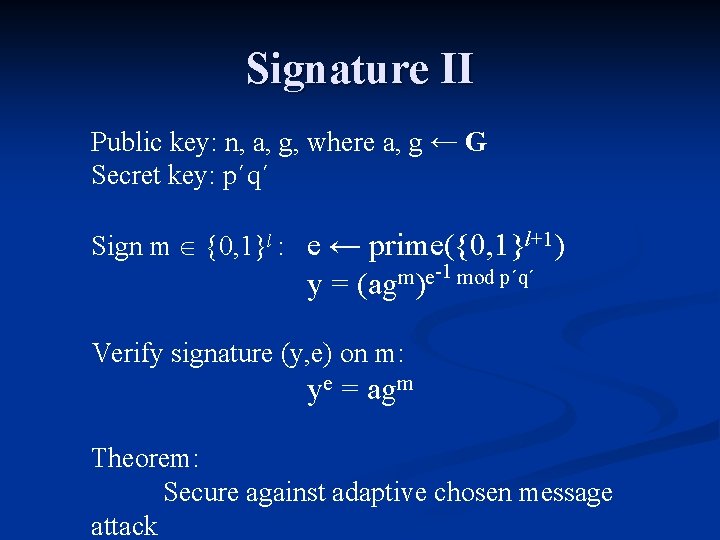
Signature II Public key: n, a, g, where a, g ← G Secret key: p´q´ Sign m {0, 1}l : e ← prime({0, 1}l+1) y= -1 mod p´q´ m e (ag ) Verify signature (y, e) on m: ye = agm Theorem: Secure against adaptive chosen message attack
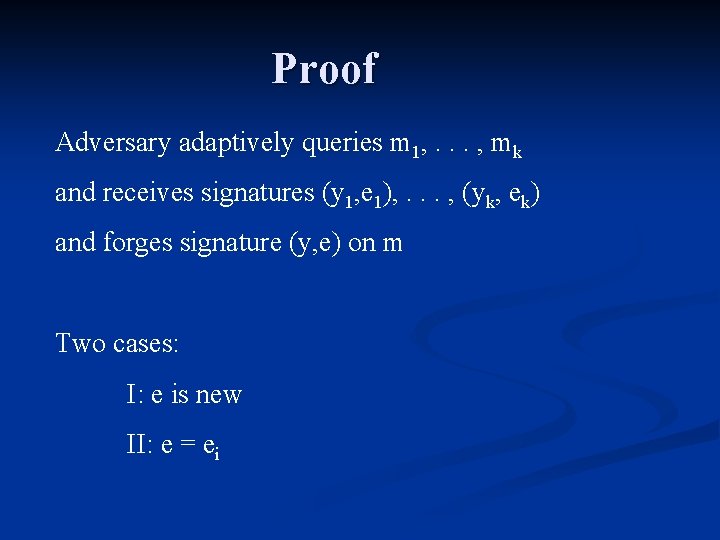
Proof Adversary adaptively queries m 1, . . . , mk and receives signatures (y 1, e 1), . . . , (yk, ek) and forges signature (y, e) on m Two cases: I: e is new II: e = ei
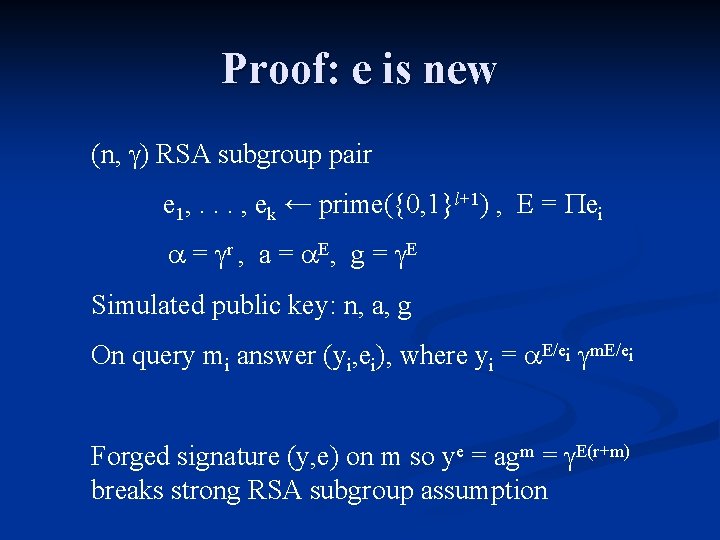
Proof: e is new (n, ) RSA subgroup pair e 1, . . . , ek ← prime({0, 1}l+1) , E = ei = r , a = E , g = E Simulated public key: n, a, g On query mi answer (yi, ei), where yi = E/ei m. E/ei Forged signature (y, e) on m so ye = agm = E(r+m) breaks strong RSA subgroup assumption
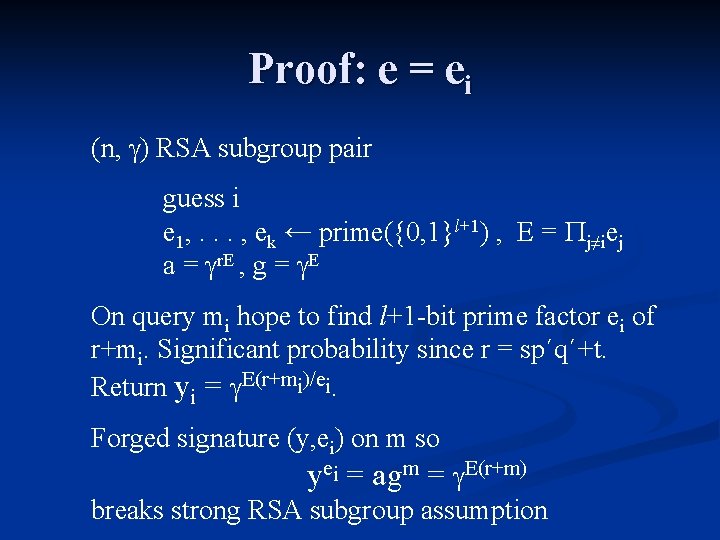
Proof: e = ei (n, ) RSA subgroup pair guess i e 1, . . . , ek ← prime({0, 1}l+1) , E = j≠iej a = r. E , g = E On query mi hope to find l+1 -bit prime factor ei of r+mi. Significant probability since r = sp´q´+t. Return yi = E(r+mi)/ei. Forged signature (y, ei) on m so yei = agm = E(r+m) breaks strong RSA subgroup assumption
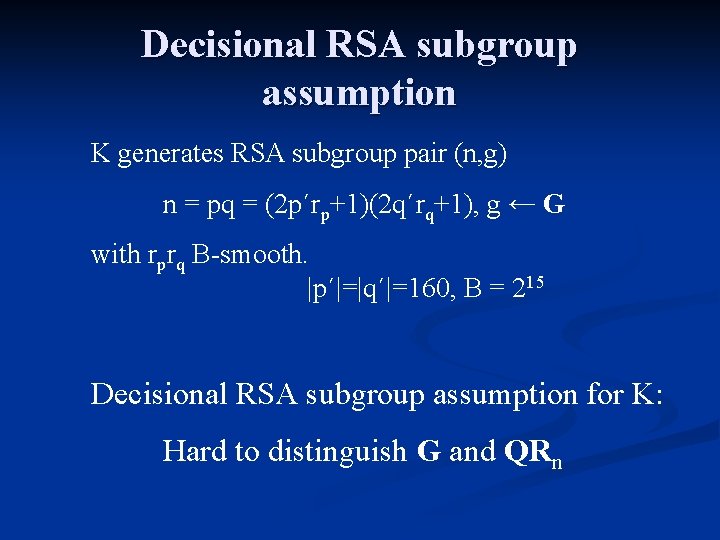
Decisional RSA subgroup assumption K generates RSA subgroup pair (n, g) n = pq = (2 p´rp+1)(2 q´rq+1), g ← G with rprq B-smooth. |p´|=|q´|=160, B = 215 Decisional RSA subgroup assumption for K: Hard to distinguish G and QRn
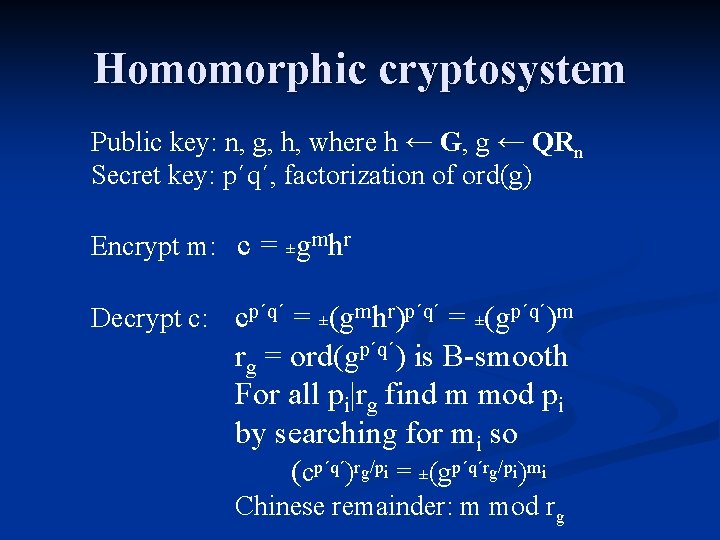
Homomorphic cryptosystem Public key: n, g, h, where h ← G, g ← QRn Secret key: p´q´, factorization of ord(g) Encrypt m: c = ±gmhr Decrypt c: cp´q´ = ±(gmhr)p´q´ = ±(gp´q´)m rg = ord(gp´q´) is B-smooth For all pi|rg find m mod pi by searching for mi so (cp´q´)rg/pi = ±(gp´q´rg/pi)mi Chinese remainder: m mod rg
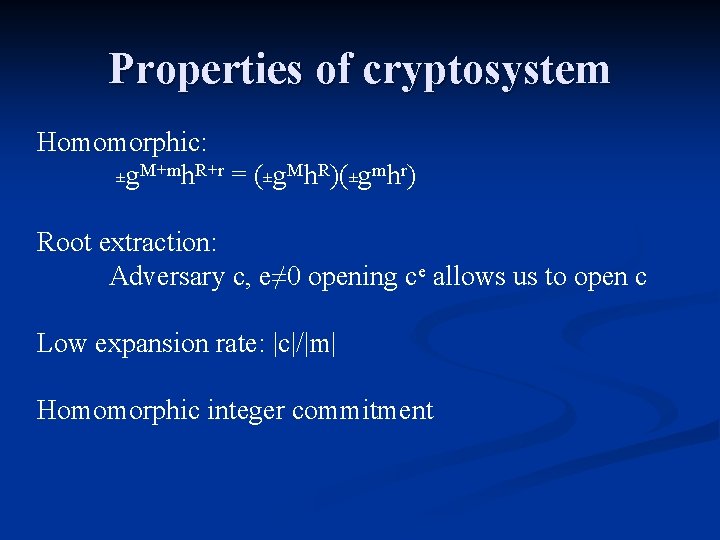
Properties of cryptosystem Homomorphic: ±g. M+mh. R+r = (±g. Mh. R)(±gmhr) Root extraction: Adversary c, e≠ 0 opening ce allows us to open c Low expansion rate: |c|/|m| Homomorphic integer commitment
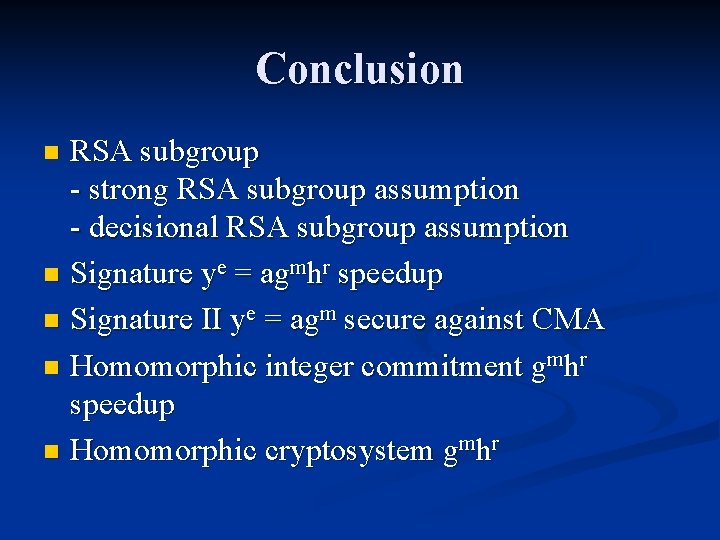
Conclusion RSA subgroup - strong RSA subgroup assumption - decisional RSA subgroup assumption n Signature ye = agmhr speedup n Signature II ye = agm secure against CMA n Homomorphic integer commitment gmhr speedup n Homomorphic cryptosystem gmhr n
- Slides: 14