PairingBased Cryptography Dan Boneh Stanford University Tutorial FOCS
![Pairing-Based Cryptography Dan Boneh Stanford University [Tutorial: FOCS 2007] Pairing-Based Cryptography Dan Boneh Stanford University [Tutorial: FOCS 2007]](https://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-1.jpg)
Pairing-Based Cryptography Dan Boneh Stanford University [Tutorial: FOCS 2007]
A new tool: • pairings (>1200 papers) Encryption schemes with new properties: Identity-based, Broadcast, Forward secure, Homomorphic, Searchable, Proxiable, CCA, … • Signature systems with new properties: Short, Aggregate, Append-only, VRF, Short group sigs, e-cash, … • Efficient non-interactive zero-knowledge (NIZK)
Conferences: Pi. C 2005
Conferences: Pairings 2007
Commercial Interest
Gemalto (formerly Gemplus)
Part 1: What is a pairing?
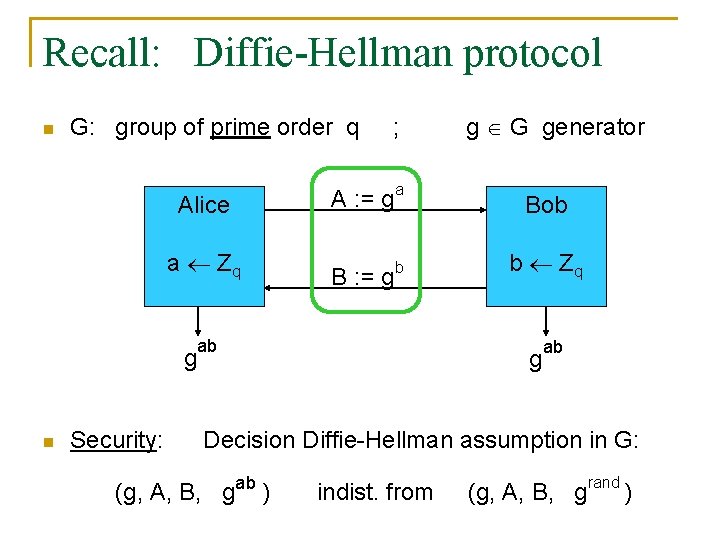
Recall: Diffie-Hellman protocol n G: group of prime order q Alice a Zq g n Security: ; A : = g a B : = g b ab g G generator Bob b Zq g ab Decision Diffie-Hellman assumption in G: (g, A, B, gab ) indist. from (g, A, B, grand )
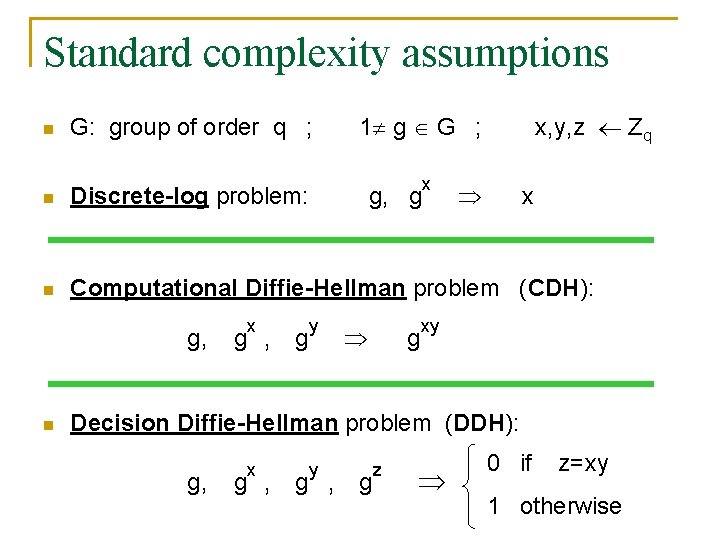
Standard complexity assumptions n G: group of order q ; 1 g G ; n Discrete-log problem: n Computational Diffie-Hellman problem (CDH): g, n x g , g y g, g x x, y, z Zq g x xy Decision Diffie-Hellman problem (DDH): g, x y g , g z 0 if z=xy 1 otherwise
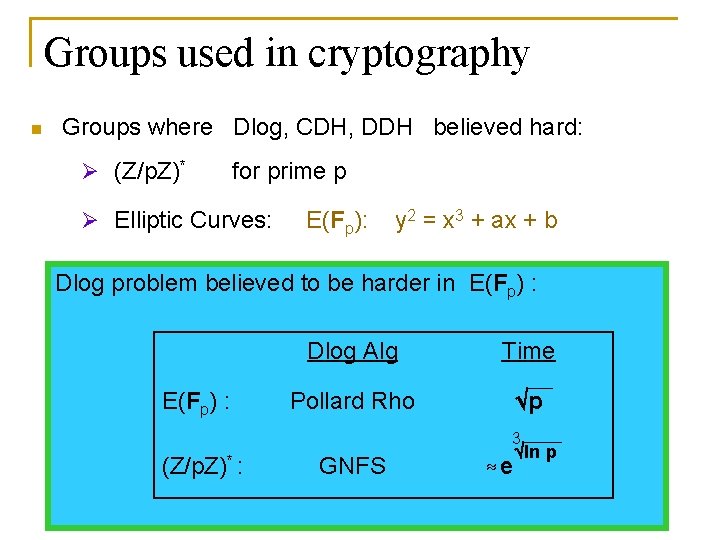
Groups used in cryptography n Groups where Dlog, CDH, DDH believed hard: Ø (Z/p. Z)* for prime p Ø Elliptic Curves: E(Fp): y 2 = x 3 + ax + b Dlog problem believed to be harder in E(Fp) : Dlog Alg Time Pollard Rho p 3 (Z/p. Z)* : GNFS e ln p
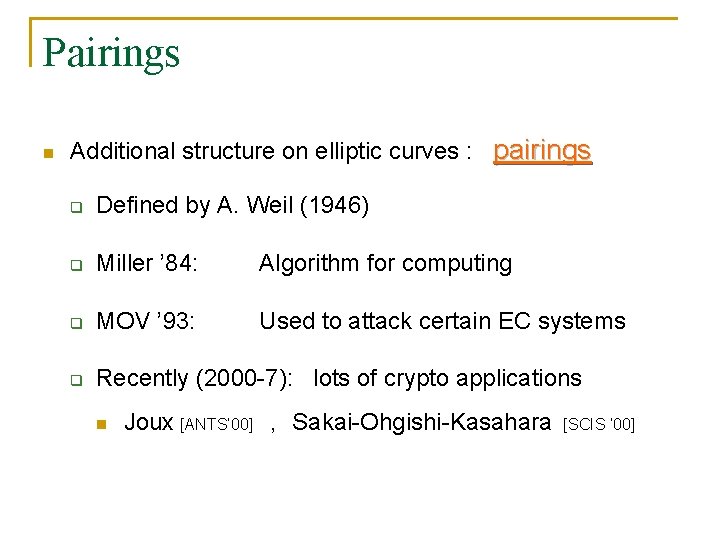
Pairings n Additional structure on elliptic curves : pairings q Defined by A. Weil (1946) q Miller ’ 84: Algorithm for computing q MOV ’ 93: Used to attack certain EC systems q Recently (2000 -7): lots of crypto applications n Joux [ANTS’ 00] , Sakai-Ohgishi-Kasahara [SCIS ’ 00]
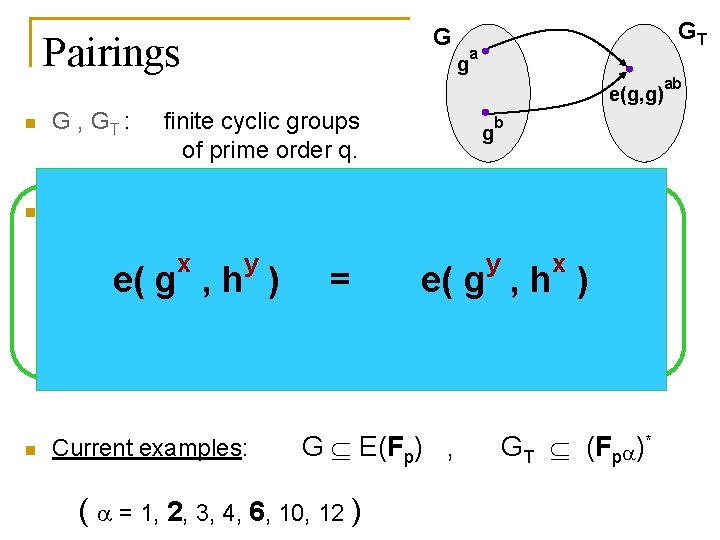
G Pairings g GT a e(g, g) n G , GT : n Def: A pairing q q n finite cyclic groups of prime order q. e: G G GT Bilinear: xe(ga, ygb) = e(g, g)ab e( g , h ) = g b is a map: a, b Z, y g G x e( g , h ) Poly-time computable and non-degenerate: g generates G e(g, g) generates GT Current examples: G E(Fp) , ( = 1, 2, 3, 4, 6, 10, 12 ) GT (Fp )* ab
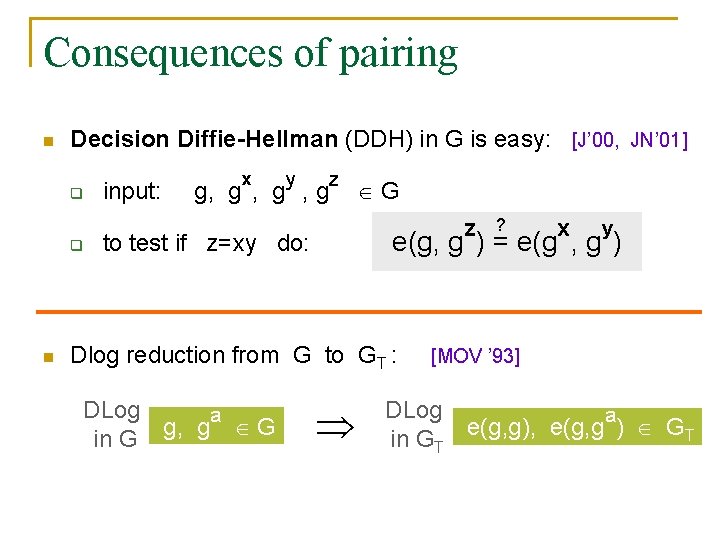
Consequences of pairing n Decision Diffie-Hellman (DDH) in G is easy: [J’ 00, JN’ 01] q q n input: x y g, g , g z G z x y e(g, g ) = e(g , g ) to test if z=xy do: Dlog reduction from G to GT : DLog a g, g G in G ? [MOV ’ 93] DLog a e(g, g), e(g, g ) GT in GT
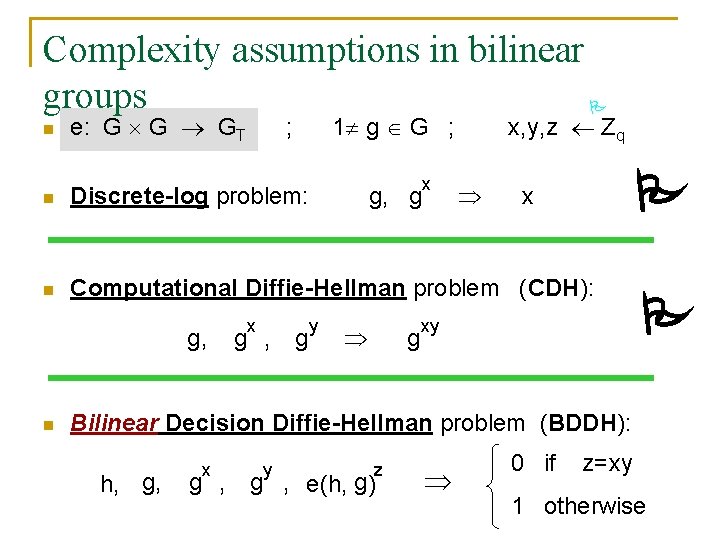
Complexity assumptions in bilinear groups n e: G G GT 1 g G ; ; n Discrete-log problem: n Computational Diffie-Hellman problem (CDH): g, n x g , g y g, g x x, y, z Zq g x xy Bilinear Decision Diffie-Hellman problem (BDDH): h, g, x y z g , e(h, g) 0 if z=xy 1 otherwise
![Where pairings come from … P Q E(Fp )[q] q E(Fp) = G q Where pairings come from … P Q E(Fp )[q] q E(Fp) = G q](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-15.jpg)
Where pairings come from … P Q E(Fp )[q] q E(Fp) = G q Tate pairing: V. Miller (84): … but: e(P, Q) : = f. P(Q) f. P (p -1)/q , (f. P) = q (P) - q (O) has a short straight line program P, Q E(Fp) : e(P, Q) = 1
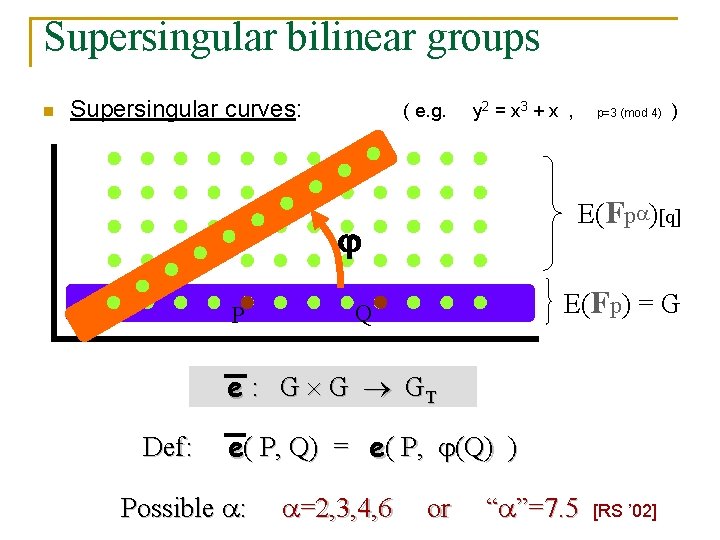
Supersingular bilinear groups n Supersingular curves: ( e. g. y 2 = x 3 + x , E(Fp) = G Q e : G G GT Def: e( P, Q) = e( P, (Q) ) Possible : =2, 3, 4, 6 ) E(Fp )[q] P p=3 (mod 4) or “ ”=7. 5 [RS ’ 02]
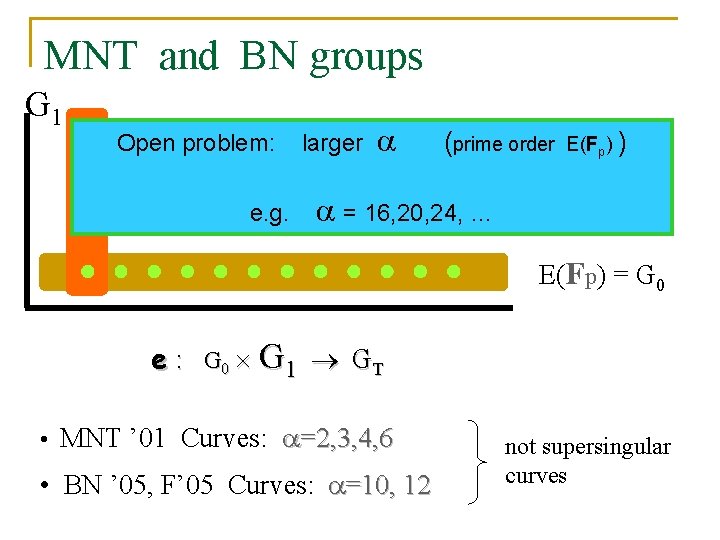
MNT and BN groups G 1 Open problem: e. g. larger (prime order = 16, 20, 24, … E(Fp) ) E(Fp )[q] E(Fp) = G 0 e : G 0 G 1 GT • MNT ’ 01 Curves: =2, 3, 4, 6 • BN ’ 05, F’ 05 Curves: =10, 12 not supersingular curves
Part 2: Crypto Applications
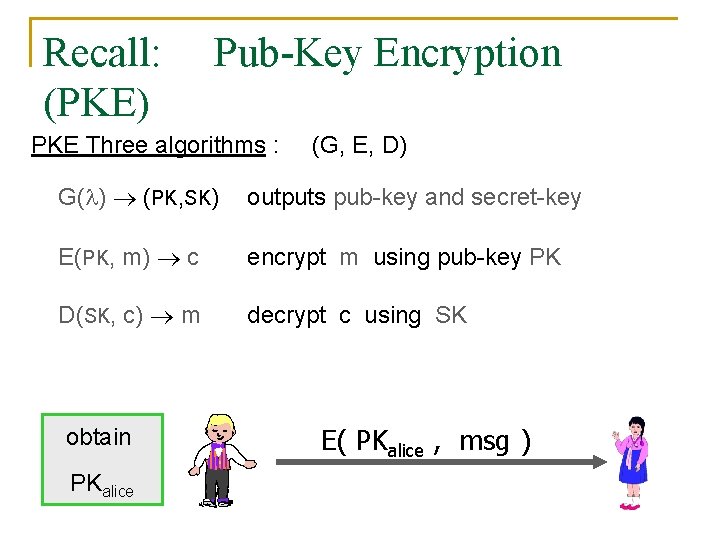
Recall: (PKE) Pub-Key Encryption PKE Three algorithms : (G, E, D) G( ) (PK, SK) outputs pub-key and secret-key E(PK, m) c encrypt m using pub-key PK D(SK, c) m decrypt c using SK obtain PKalice E( PKalice , msg )
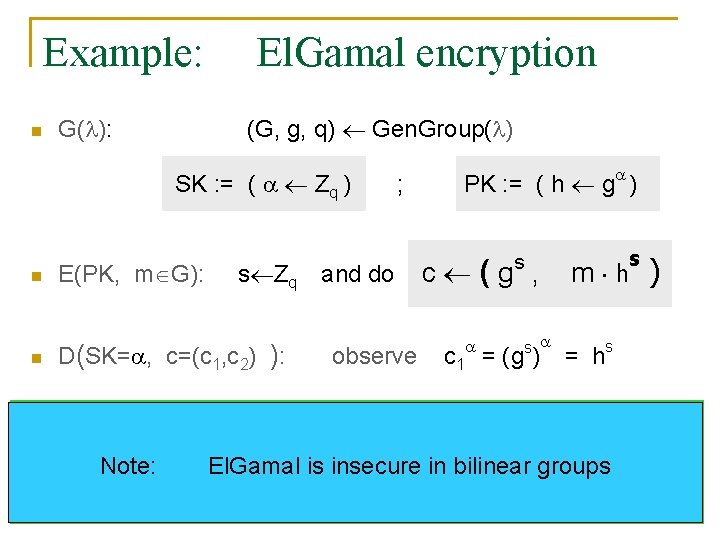
Example: n El. Gamal encryption (G, g, q) Gen. Group( ) G( ): SK : = ( Zq ) n n n E(PK, m G): s Zq D(SK= , c=(c 1, c 2) ): ; and do observe PK : = ( h g ) s c (g , s c 1 = (g ) s m h ) = hs Security (IND-CPA) based on the DDH assumption: Note: El. Gamal is insecure in bilinear groups (g, h, gs , hs ) indist. from (g, h, gs , grand )
![Identity Based Encryption n IBE: • [Sha ’ 84] PKE system where PK is Identity Based Encryption n IBE: • [Sha ’ 84] PKE system where PK is](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-21.jpg)
Identity Based Encryption n IBE: • [Sha ’ 84] PKE system where PK is an arbitrary string e. g. e-mail address, phone number, IP addr… email encrypted using public key: “ali I ce@ am gm ail. c o “alice@gmail. com” Pr iv at e ke y m” CA/PKG master-key
![Identity Based Encryption Four algorithms : S( ) (PP, MK) [Sha ’ 84] (S, Identity Based Encryption Four algorithms : S( ) (PP, MK) [Sha ’ 84] (S,](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-22.jpg)
Identity Based Encryption Four algorithms : S( ) (PP, MK) [Sha ’ 84] (S, K, E, D) output params, PP, and master-key, MK K(MK, ID) d. ID outputs private key, d. ID , for ID E(PP, ID, m) c encrypt m using pub-key ID (and PP) D(d. ID, c) m decrypt c using d. ID IBE “compresses” exponentially many PKs into a short PP
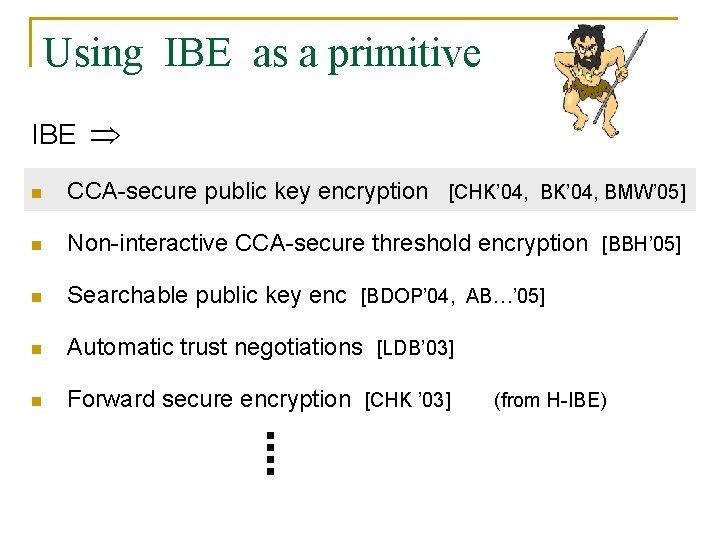
Using IBE as a primitive IBE n CCA-secure public key encryption [CHK’ 04, BMW’ 05] n Non-interactive CCA-secure threshold encryption [BBH’ 05] n Searchable public key enc [BDOP’ 04, AB…’ 05] n Automatic trust negotiations [LDB’ 03] n Forward secure encryption [CHK ’ 03] (from H-IBE)
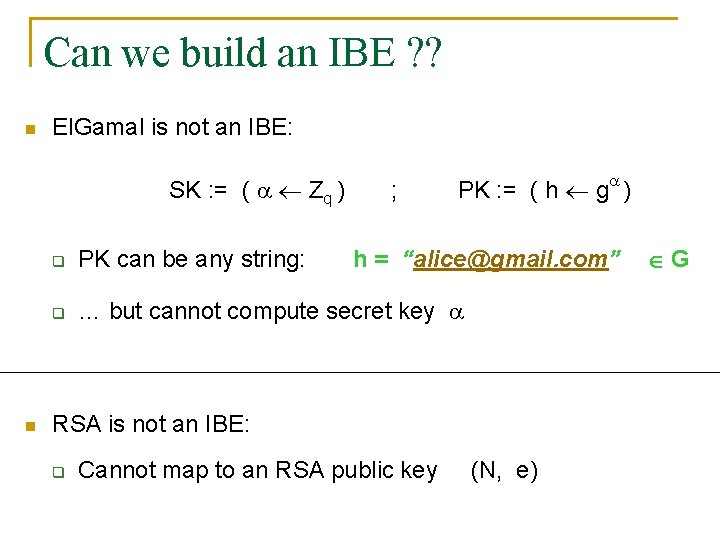
Can we build an IBE ? ? n El. Gamal is not an IBE: SK : = ( Zq ) n ; PK : = ( h g ) q PK can be any string: h = “alice@gmail. com” q … but cannot compute secret key RSA is not an IBE: q Cannot map to an RSA public key (N, e) G

Pairings to the rescue: n S( ): BF-IBE (G, GT, g, q) Gen. Bil. Group( ) , PP : = [g, y g ] G d H(ID) n K(MK, ID): n E(PP, ID, m): C (g , MK : = ; H: m e(y, H(ID)) ID G s ) s = e(g , H(ID) ) D( d, (c 1, c 2) ): observe: Zq s Zq and do s n [BF’ 01] s e( c 1 , d ) = e( g , H(ID) )
![Another IBE: n S( ): BB-IBE [BB’ 04] (G, GT, g, q) Gen. Bil. Another IBE: n S( ): BB-IBE [BB’ 04] (G, GT, g, q) Gen. Bil.](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-26.jpg)
Another IBE: n S( ): BB-IBE [BB’ 04] (G, GT, g, q) Gen. Bil. Group( ) , PP : = [g, y g , g 1 , h] G n ID d. ID ( MK (y h) K(MK, ID): r Zq ; , MK : = g 1 r g ) r Zq n E(PP, ID, m): s Zq and do s C (g , n ID s (y h) , m e(y, g 1) s ) D( (d 1, d 2), (c 1, c 2, c 3) ): observe: e(c 1, d 1) / e(c 2, d 2) = e(y, g 1) s
![IBE Security n (IND-IDCPA) [BF’ 01] Security when attacker can request several private keys IBE Security n (IND-IDCPA) [BF’ 01] Security when attacker can request several private keys](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-27.jpg)
IBE Security n (IND-IDCPA) [BF’ 01] Security when attacker can request several private keys Challenger d. ID ID K(MK, ID) Attacker A PP PP, MK S( ) * (ID, m 0, m 1) b {0, 1} C* E( PP, ID* , mb) b’ {0, 1} (S, K, E, D) is IND-IDCPA secure if PPT A: |Pr[b=b’] – ½| < neg( )
![IBE Security n (IND-s. IDCPA) [CHK’ 04] Security when attacker can request several private IBE Security n (IND-s. IDCPA) [CHK’ 04] Security when attacker can request several private](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-28.jpg)
IBE Security n (IND-s. IDCPA) [CHK’ 04] Security when attacker can request several private keys ID* Challenger d. ID ID K(MK, ID) Attacker A PP PP, MK S( ) ( ID* m 0, m 1) b {0, 1} C* E( PP, ID* , mb) b’ {0, 1} (S, K, E, D) is IND-s. IDCPA secure if PPT A: |Pr[b=b’] – ½| < neg( )
![IBE Security n BB-IBE security theorem: BDDH n Waters-IBE: [W’ 05] BDDH n BB-IBE IBE Security n BB-IBE security theorem: BDDH n Waters-IBE: [W’ 05] BDDH n BB-IBE](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-29.jpg)
IBE Security n BB-IBE security theorem: BDDH n Waters-IBE: [W’ 05] BDDH n BB-IBE is IND-s. IDCPA secure generalizes BB-IBE Gentry-IBE: [G’ 06] q-BDHE [BB’ 04] Waters-IBE is IND-IDCPA secure short PP Gentry-IBE is IND-IDCPA secure
New Signature Systems CDH short and efficient sigs (!!)
![IBE Simple digital Signatures [N’ 01] q q n Sign(MK, m): sig K(MK, m) IBE Simple digital Signatures [N’ 01] q q n Sign(MK, m): sig K(MK, m)](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-31.jpg)
IBE Simple digital Signatures [N’ 01] q q n Sign(MK, m): sig K(MK, m) Verify(PP, m, sig): Test that sig decrypts messages encrypted using m Conversely: which sig systems give an IBE? q Rabin signatures: q Open problem: q Blackbox Impossibility: IBE from trapdoor perms [Cocks’ 01, BGH’ 07] IBE from GMR, GHR, CS, … [BPRVW’ 07]
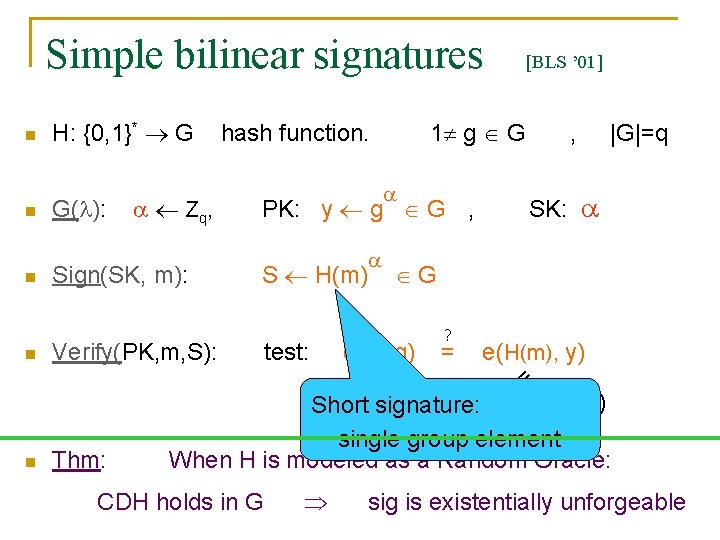
Simple bilinear signatures n n G( ): Z q, Sign(SK, m): 1 g G hash function. S H(m) Verify(PK, m, S): test: n Thm: , |G|=q SK: PK: y g G , G e(S, g) = n H: {0, 1}* G ? = e(H(m), y) = n [BLS ’ 01] e(H(m) , g) = e(H(m), g ) Short signature: single group element When H is modeled as a Random Oracle: CDH holds in G sig is existentially unforgeable
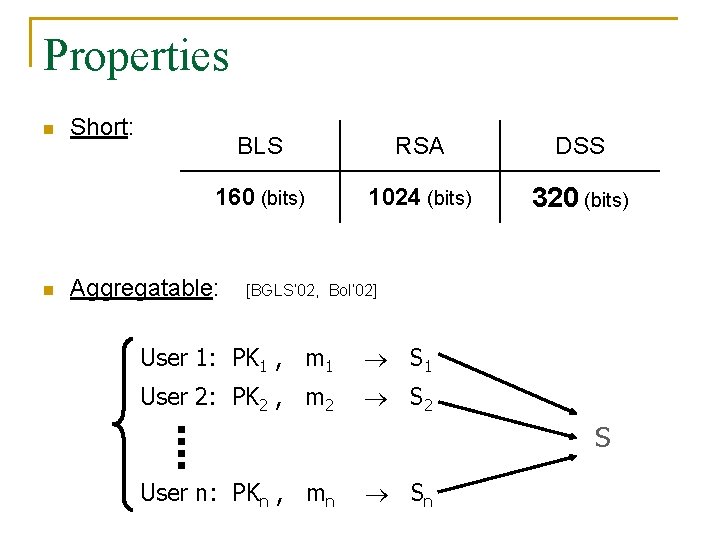
Properties n n Short: BLS RSA DSS 160 (bits) 1024 (bits) 320 (bits) Aggregatable: [BGLS’ 02, Bol’ 02] User 1: PK 1 , m 1 S 1 User 2: PK 2 , m 2 S 2 S User n: PKn , mn Sn
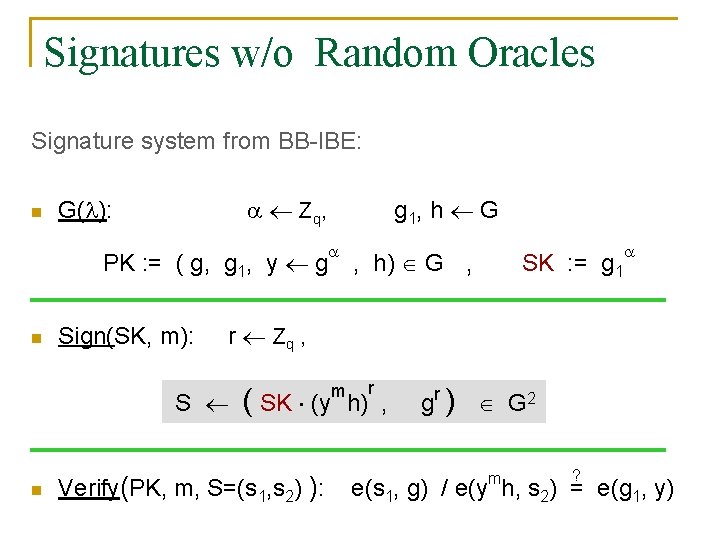
Signatures w/o Random Oracles Signature system from BB-IBE: n Z q, G( ): PK : = ( g, g 1, y g n Sign(SK, m): , h) G , SK : = g 1 r Zq , S n g 1, h G ( SK (y Verify(PK, m, S=(s 1, s 2) ): m r h) , gr ) G 2 ? e(s 1, g) / e(ymh, s 2) = e(g 1, y)
![Selectively unforgeable sigs [GMR’ 88] m* : msg to attack (PK, SK) K( ) Selectively unforgeable sigs [GMR’ 88] m* : msg to attack (PK, SK) K( )](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-35.jpg)
Selectively unforgeable sigs [GMR’ 88] m* : msg to attack (PK, SK) K( ) m m* S Sign(SK, m) S* Attacker Challenger PK G Sig is selectively unforgrable if PPT A: Pr[Verify(PK, m*, S*) = “yes”] < neg( )
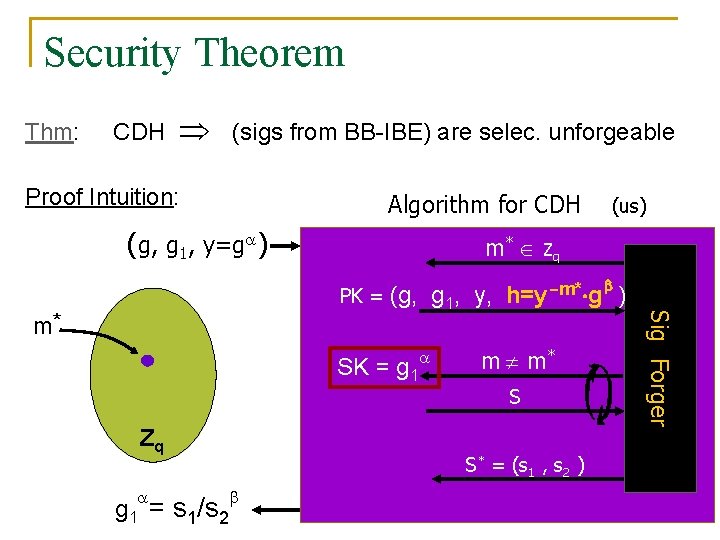
Security Theorem Thm: CDH (sigs from BB-IBE) are selec. unforgeable Proof Intuition: Algorithm for CDH (g, g 1, y=g ) m* PK = (g, g 1, y, h=y-m* g ) SK = g 1 Zq g 1 = s 1/s 2 Zq m m* S S* = (s 1 , s 2 ) Sig Forger m* (us)
![Waters Sigs: existentially unforgeable [Wat ’ 05] n G( ): Zq , g 1, Waters Sigs: existentially unforgeable [Wat ’ 05] n G( ): Zq , g 1,](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-37.jpg)
Waters Sigs: existentially unforgeable [Wat ’ 05] n G( ): Zq , g 1, h, y 1, …, yn G SK: g 1 PK: (g, g 1, y g , h, y 1 , …, yn) G , n Sign(SK, M): S ( n r Zq , M=m 1 m 2 … mn {0, 1}n m M SK ( y 1 1 y… hyn mn r h ) , g r ) G 2 Verify(PK, M, S=(s 1, s 2) ): e(s 1 , g) / e(y 1 m 1 … yn mn h, s 2 ) = e(g 1, y)
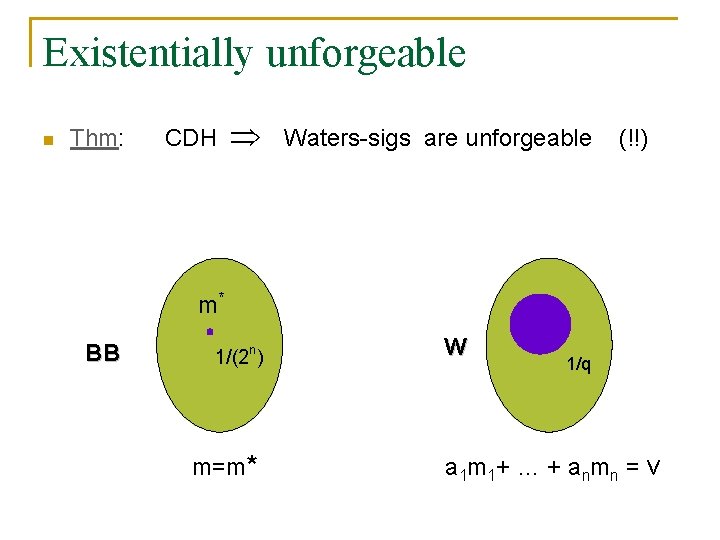
Existentially unforgeable n Thm: CDH Waters-sigs are unforgeable (!!) m* BB 1/(2 n) m=m* W 1/q a 1 m 1 + … + a n mn = v
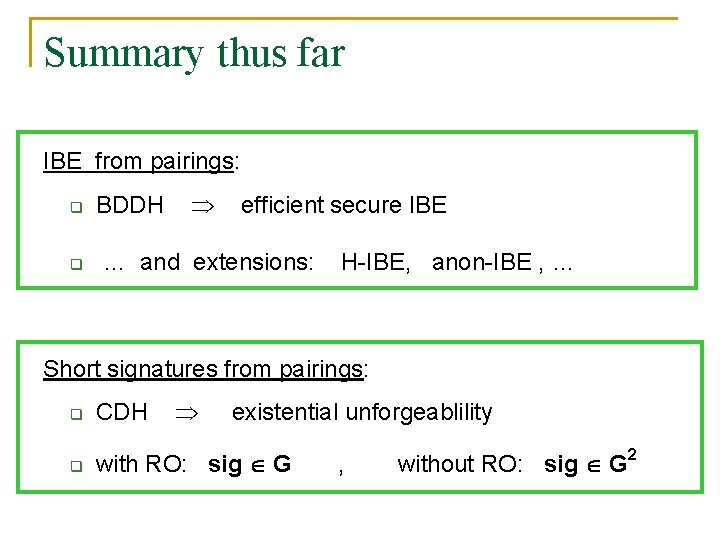
Summary thus far IBE from pairings: q q BDDH efficient secure IBE … and extensions: H-IBE, anon-IBE , … Short signatures from pairings: q CDH existential unforgeablility q with RO: sig G , without RO: sig G 2
Part 3: Computing on Ciphertexts
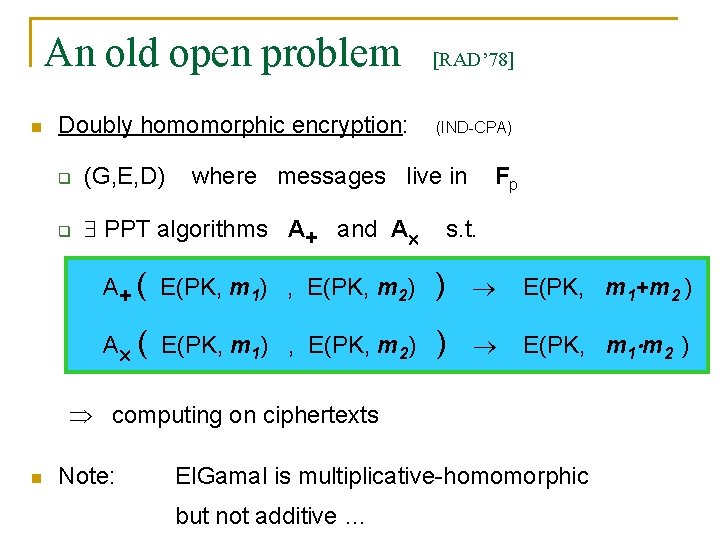
An old open problem n Doubly homomorphic encryption: q (G, E, D) q PPT algorithms A+ and A [RAD’ 78] (IND-CPA) where messages live in Fp s. t. A+ ( E(PK, m 1) , E(PK, m 2) ) E(PK, m 1+m 2 ) A ( E(PK, m 1) , E(PK, m 2) ) E(PK, m 1 m 2 ) computing on ciphertexts n Note: El. Gamal is multiplicative-homomorphic but not additive …
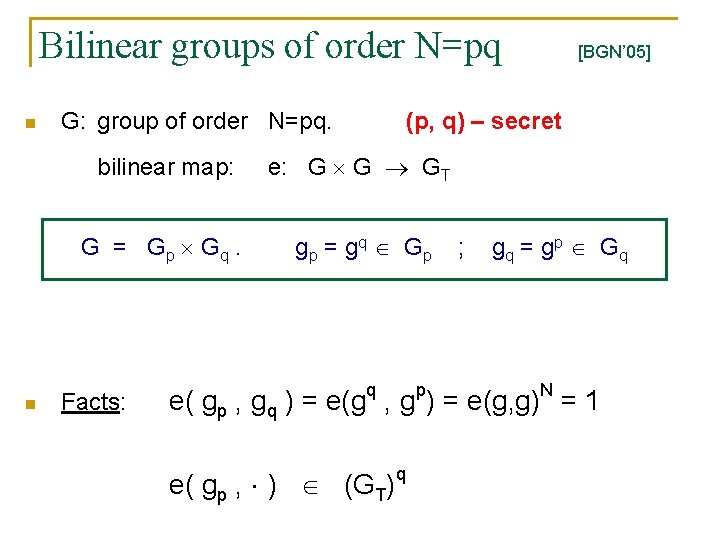
Bilinear groups of order N=pq n n G: group of order N=pq. (p, q) – secret bilinear map: e: G G GT G = Gp Gq. gp = gq G p Facts: [BGN’ 05] ; gq = gp G q e( gp , gq ) = e(gq , gp) = e(g, g)N = 1 e( gp , ) (GT) q
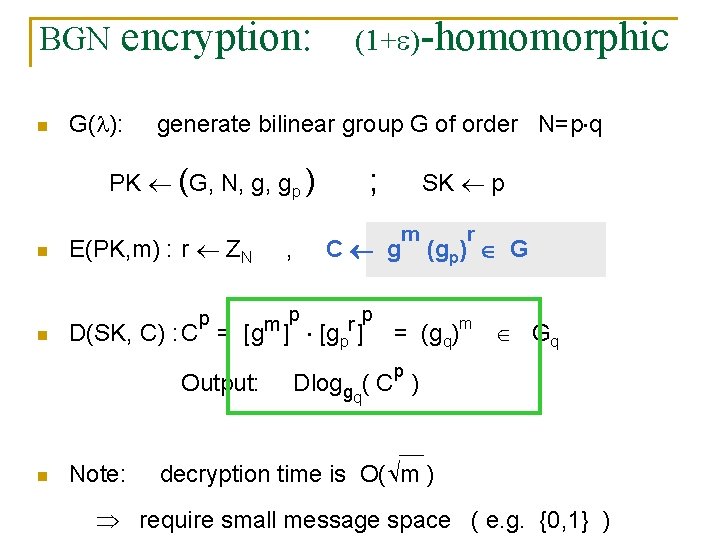
BGN n encryption: G( ): (1+ )-homomorphic generate bilinear group G of order N=p q PK (G, N, g, gp ) ; SK p r n E(PK, m) : r ZN n p p m r D(SK, C) : C = [g ] [gp ] = (gq)m (gp) G p Output: n , C g m Note: Gq p Dloggq( C ) decryption time is O( m ) require small message space ( e. g. {0, 1} )

Homomorphic Properties n C 1 gm 1 (gp)r 1 q q n C 2 gm 2 (gp)r 2 G Additive hom: E(m 1+m 2) = C 1 C 2 (gp)s ^ One mult hom: E(m 1 m 2) = e(C 1, C 2) e(gp, gp)s More generally: For any n , ^ E(m 1), …, E(mn) E(F(m 1, …, mn)) F ZN[X 1, …, Xn] of total degree 2 Example: dot product on encrypted vectors [AW’ 07]
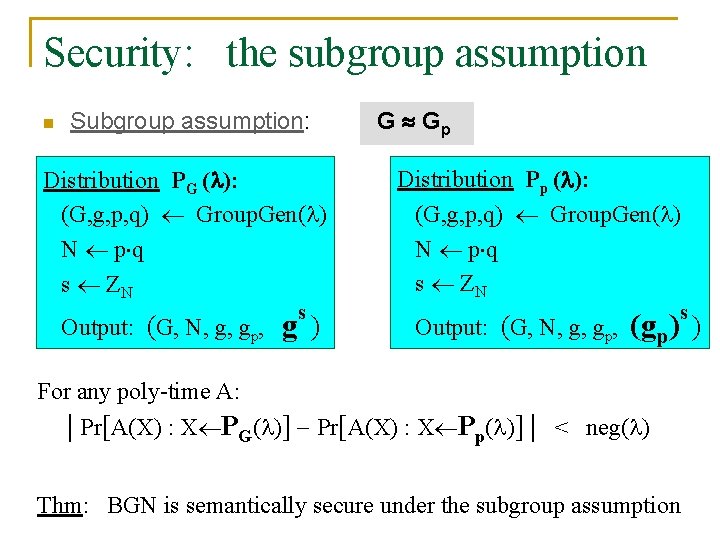
Security: the subgroup assumption n Subgroup assumption: Distribution PG ( ): (G, g, p, q) Group. Gen( ) N p q s ZN Output: (G, N, g, gp, s g) G Gp Distribution Pp ( ): (G, g, p, q) Group. Gen( ) N p q s ZN Output: (G, N, g, gp, s (gp) ) For any poly-time A: | Pr[A(X) : X PG( )] Pr[A(X) : X Pp( )] | < neg( ) Thm: BGN is semantically secure under the subgroup assumption
![Non-Interactive Zero Knowledge [GOS’ 06] NIZK proof size: O(|# gates| ) CRS size: O( Non-Interactive Zero Knowledge [GOS’ 06] NIZK proof size: O(|# gates| ) CRS size: O(](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-46.jpg)
Non-Interactive Zero Knowledge [GOS’ 06] NIZK proof size: O(|# gates| ) CRS size: O( )
![Goal: NIZK for circuit SAT [BFM’ 88] z AND OR boolean circuit NOT OR Goal: NIZK for circuit SAT [BFM’ 88] z AND OR boolean circuit NOT OR](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-47.jpg)
Goal: NIZK for circuit SAT [BFM’ 88] z AND OR boolean circuit NOT OR NOT AND b 1 b 2 b 3 b 4 b 5 b 6 b 7 b 8 {0, 1} Goal: prover wants to convince verifier that circuit is satisfiable in zero knowledge and without interaction
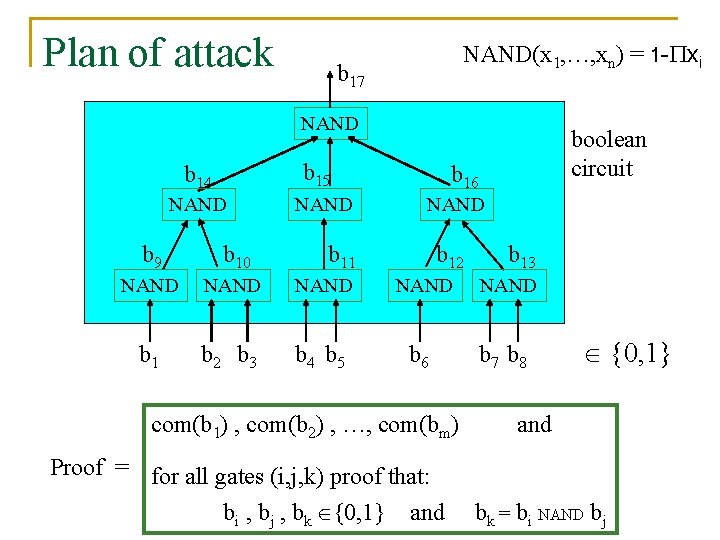
Plan of attack NAND(x 1, …, xn) = 1 - xi b 17 NAND b 15 b 14 NAND boolean circuit b 16 NAND b 9 b 10 b 11 b 12 NAND NAND b 1 b 2 b 3 b 4 b 5 b 6 b 7 b 8 com(b 1) , com(b 2) , …, com(bm) Proof = for all gates (i, j, k) proof that: bi , bj , bk {0, 1} and b 13 {0, 1} and bk = bi NAND bj
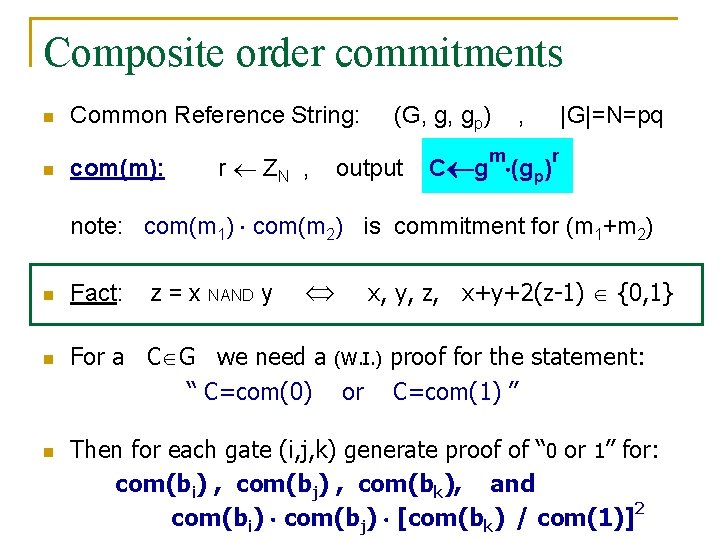
Composite order commitments n n Common Reference String: com(m): r ZN , (G, g, gp) output m , C g (gp) |G|=N=pq r note: com(m 1) com(m 2) is commitment for (m 1+m 2) n n n Fact: z = x NAND y x, y, z, x+y+2(z-1) {0, 1} For a C G we need a (W. I. ) proof for the statement: “ C=com(0) or C=com(1) ” Then for each gate (i, j, k) generate proof of “ 0 or 1” for: com(bi) , com(bj) , com(bk), and com(bi) com(bj) [com(bk) / com(1)]2
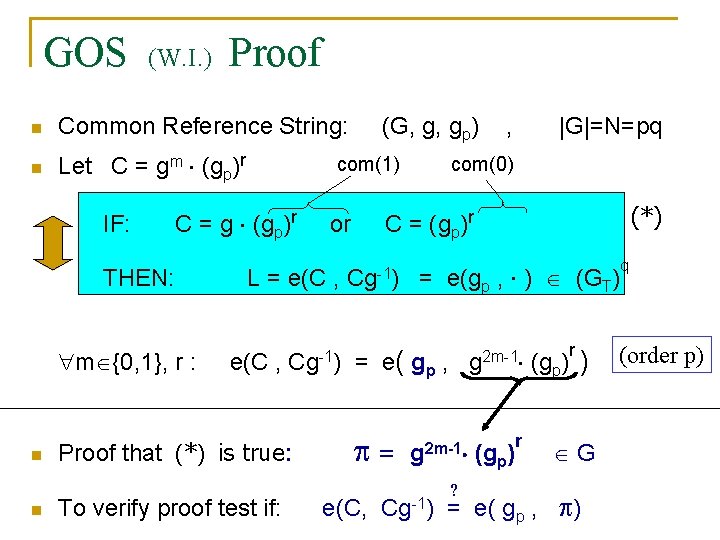
GOS (W. I. ) Proof n Common Reference String: n Let C = gm (gp)r IF: m {0, 1}, r : n n com(1) C = g (gp)r THEN: (G, g, gp) e(C , Cg-1) Proof that (*) is true: To verify proof test if: |G|=N=pq com(0) (*) C = (gp)r or L = e(C , , Cg-1) = e(gp , ) (GT) = e ( gp , = e(C, g 2 m-1 Cg-1) ? (gp) r r (gp) ) G = e( gp , ) q (order p)
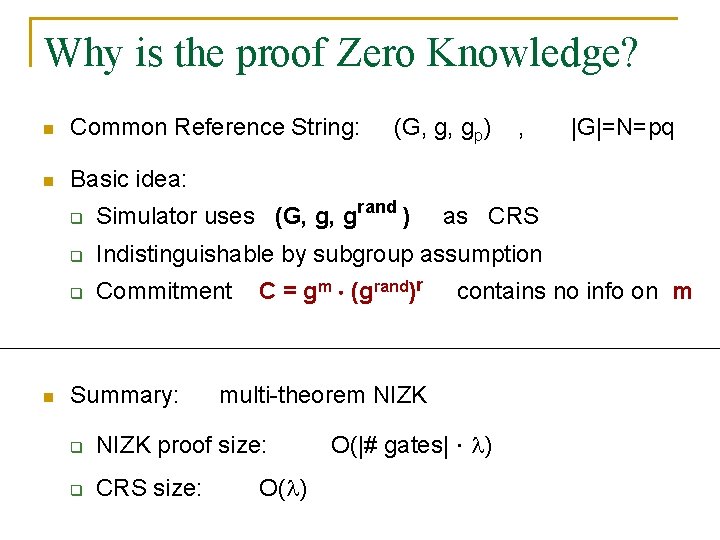
Why is the proof Zero Knowledge? n Common Reference String: n Basic idea: n (G, g, gp) , q Simulator uses (G, g, grand ) q Indistinguishable by subgroup assumption q Commitment Summary: C = gm (grand)r as CRS contains no info on m multi-theorem NIZK q NIZK proof size: q CRS size: O( ) |G|=N=pq O(|# gates| )
Part 4: open problems
Open problems n n-linear maps? n q e: G GT q Motivation: n where Dlog in G is intractable Homomorphic encryption, broadcast enc, … [BS’ 02]
![2. Verifiable Random Functions [MRV’ 99] n n Verifiable Random Function (VRF): q Setup( 2. Verifiable Random Functions [MRV’ 99] n n Verifiable Random Function (VRF): q Setup(](http://slidetodoc.com/presentation_image_h/bd111ca7c06e952efd97af6a3c9ead07/image-54.jpg)
2. Verifiable Random Functions [MRV’ 99] n n Verifiable Random Function (VRF): q Setup( ): (PK, SK) and proof q PRF F(SK, x): q verify(PK, x, y, ): yes/no y Pairing-based constructions: PK=(g, g ) , [L’ 02, DY 05] SK= F( , x) = e(g, g) 1/( +x) ; = g 1/( +x) but, security reduction takes exponential time in |x| n Question: “simple” construction with poly-time reduction
THE END Pairings: A powerful tool for building cryptosystems
- Slides: 55