ecs 236 Winter 2006 Intrusion Detection 2 Vulnerability
ecs 236 Winter 2006: Intrusion Detection #2: Vulnerability Analysis Dr. S. Felix Wu Computer Science Department University of California, Davis http: //www. cs. ucdavis. edu/~wu/ sfelixwu@gmail. com 01/04/2006 ecs 236 winter 2006 1
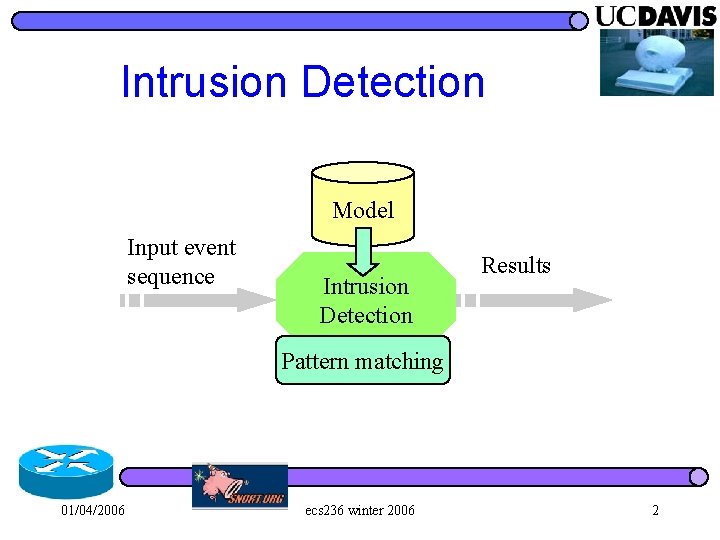
Intrusion Detection Model Input event sequence Intrusion Detection Results Pattern matching 01/04/2006 ecs 236 winter 2006 2
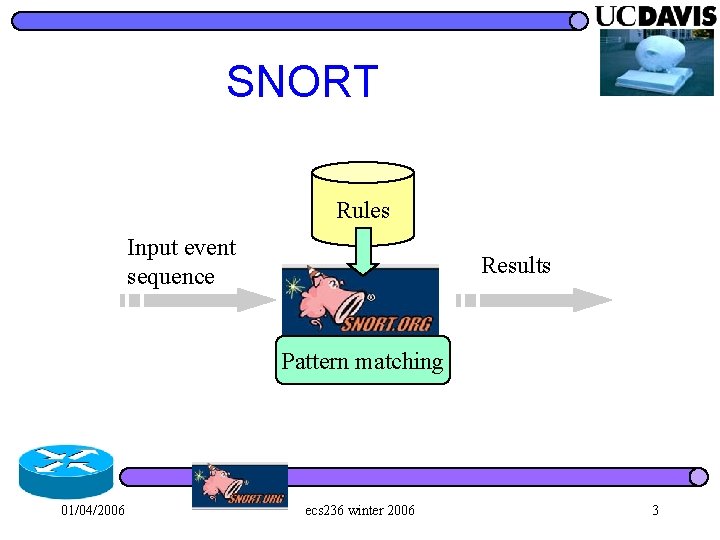
SNORT Rules Input event sequence Results Pattern matching 01/04/2006 ecs 236 winter 2006 3
WORM l Since November 2 nd of 1988… – Robert T. Morris, Code Red, Nimda, Slammer, Blaster, and many others… l inject infect spread 01/04/2006 ecs 236 winter 2006 4
WORM l Since November 2 nd of 1988… – Robert T. Morris, Code Red, Nimda, Slammer, Blaster, and many others… l inject infect spread l WORM is causing Internet-wide instability. 01/04/2006 ecs 236 winter 2006 5
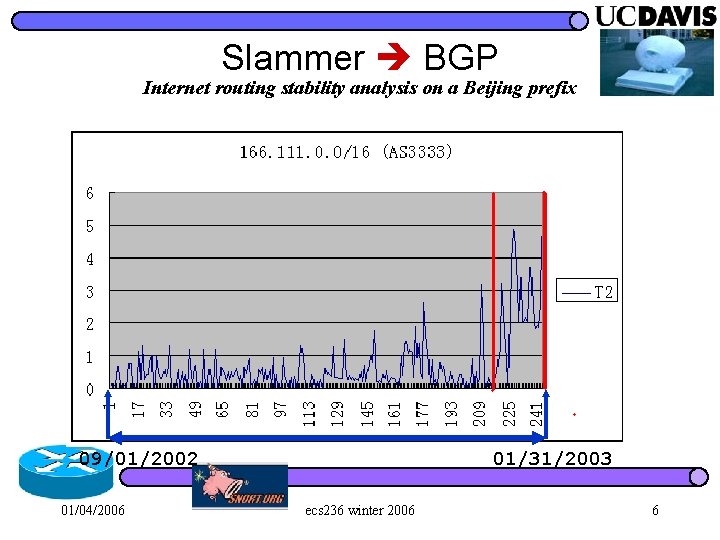
Slammer BGP Internet routing stability analysis on a Beijing prefix 09/01/2002 01/04/2006 01/31/2003 ecs 236 winter 2006 6
Network meets Software An interesting interaction among the Internet, the software on the hosts, and the worms themselves. l The “short-term” Reality: l – Estimated 40~50% of Internet hosts are still vulnerable to Code. Red. 01/04/2006 ecs 236 winter 2006 7
WORM l Since November 2 nd of 1988… – Robert T. Morris, Code Red, Nimda, Slammer, Blaster, and many others… inject infect spread l WORM is causing Internet-wide instability. l WORM is a critical first step for the attacker to quickly build the large-scale attacking infrastructure. l 01/04/2006 ecs 236 winter 2006 8
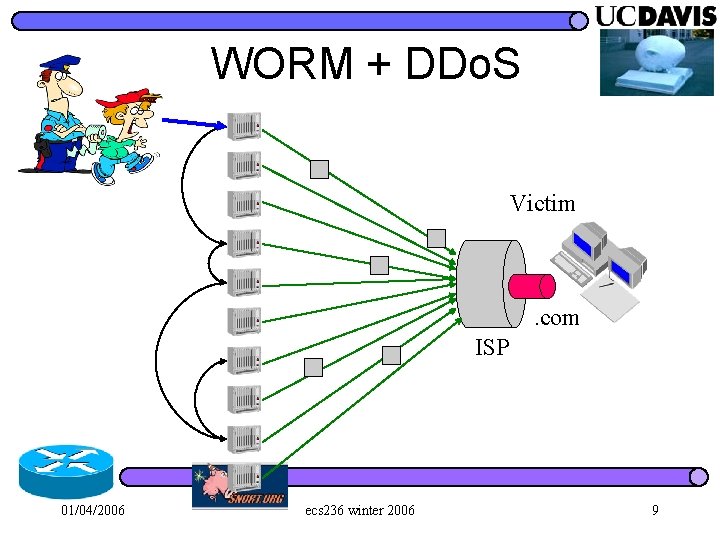
WORM + DDo. S Victim . com ISP 01/04/2006 ecs 236 winter 2006 9
They are getting better… l The rapid evolution of the “attacker’s community” 01/04/2006 ecs 236 winter 2006 10
They are getting better… l The rapid evolution of the “attacker’s community” l And, many thanks to our rapid growing software industry in the past “N” years as well… 01/04/2006 ecs 236 winter 2006 11
Software Vulnerability l Software vulnerabilities are weaknesses, being introduced during the “software engineering” process, that can potentially be exploited by attackers. – OS kernels, device drivers, applications… l There are other types of vulnerabilities in our software systems that can be exploited. 01/04/2006 ecs 236 winter 2006 12
Software Vulnerability l Difficulties in security management – we don’t know how attackers are going to attack us, – And, we don’t know which vulnerabilities can/will be exploited, either. 01/04/2006 ecs 236 winter 2006 13
Software Vulnerability Focus on Software Vulnerabilities l Two approaches l – better software engineering – better vulnerabilities understanding 01/04/2006 ecs 236 winter 2006 14
Software Vulnerability Focus on Software Vulnerabilities l Two approaches l – better software engineering – better vulnerabilities understanding Practically, around the Internet, we currently have and will still have a large number of legacy software systems around for “quite a while. ” 01/04/2006 ecs 236 winter 2006 15
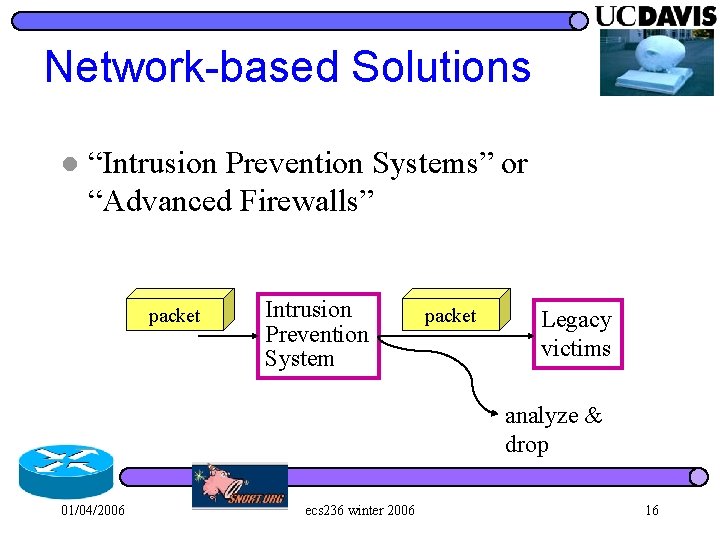
Network-based Solutions l “Intrusion Prevention Systems” or “Advanced Firewalls” packet Intrusion Prevention System packet Legacy victims analyze & drop 01/04/2006 ecs 236 winter 2006 16
Vulnerability vs. Exploit l Vulnerability – the “weak” points in the software – applications or even the kernel itself – “control flow hijack” based on buffer overflow. l Exploit – the attack code utilizing one or more vulnerabilities 01/04/2006 ecs 236 winter 2006 17
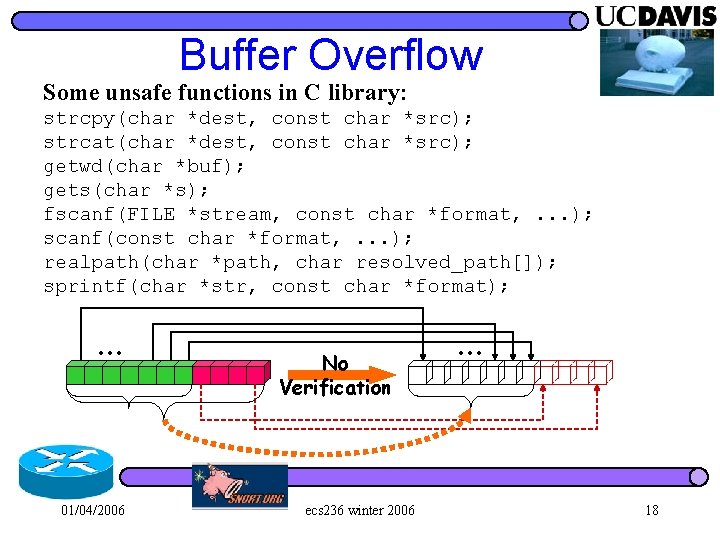
Buffer Overflow Some unsafe functions in C library: strcpy(char *dest, const char *src); strcat(char *dest, const char *src); getwd(char *buf); gets(char *s); fscanf(FILE *stream, const char *format, . . . ); scanf(const char *format, . . . ); realpath(char *path, char resolved_path[]); sprintf(char *str, const char *format); … 01/04/2006 No Verification ecs 236 winter 2006 … 18
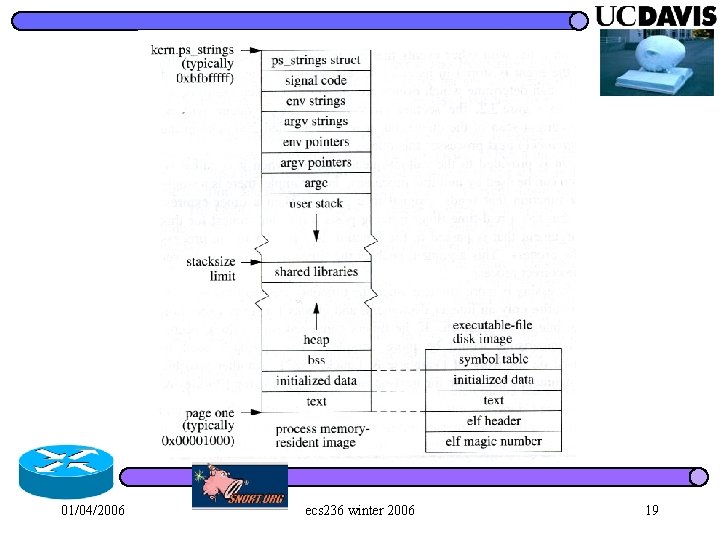
01/04/2006 ecs 236 winter 2006 19
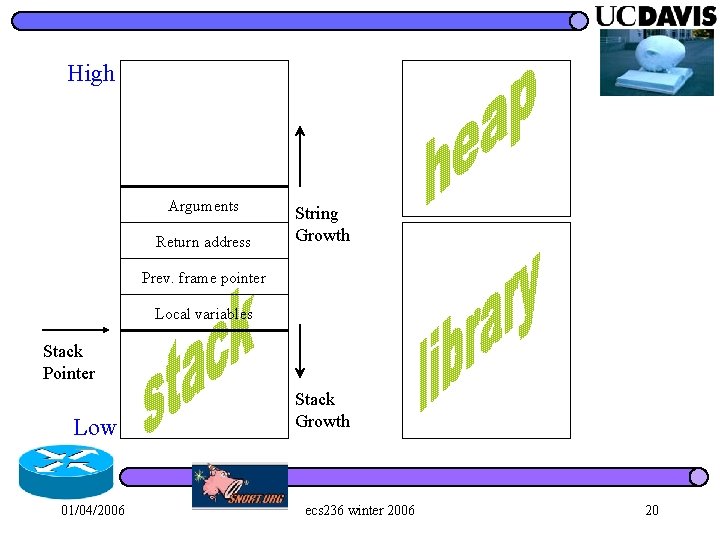
High Arguments Return address String Growth Prev. frame pointer Local variables Stack Pointer Low 01/04/2006 Stack Growth ecs 236 winter 2006 20
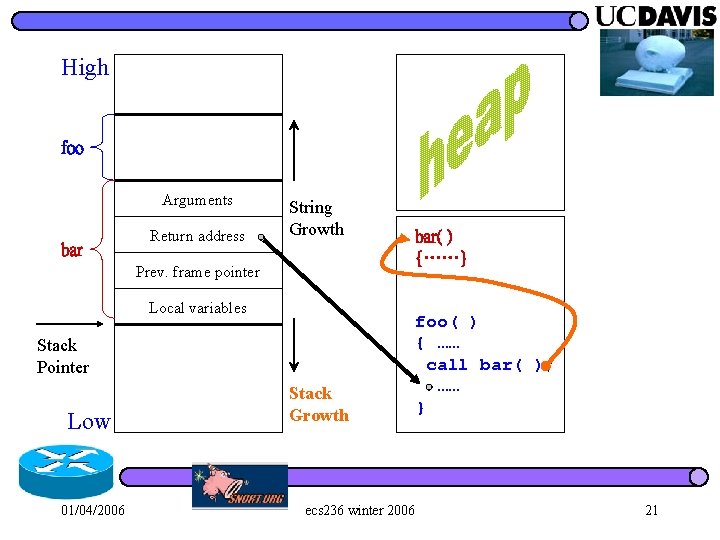
High foo Arguments bar Return address String Growth Prev. frame pointer Local variables Stack Pointer Low 01/04/2006 Stack Growth ecs 236 winter 2006 bar( ) {……} foo( ) { …… call bar( ); …… } 21
![b int bar(int a, int b) { int i, j; char buf[9]; } a b int bar(int a, int b) { int i, j; char buf[9]; } a](http://slidetodoc.com/presentation_image/62218348616c52174d612deeb7554496/image-22.jpg)
b int bar(int a, int b) { int i, j; char buf[9]; } a ret address SFP i = 5; j = 123; strcpy(buf, “securephdbcde”); Buffer Overflow 01/04/2006 high ecs 236 winter 2006 05 00 00 e 00 00 00 65 d 62 b 63 c 64 d 64 r 65 e 70 p 68 h 72 s 65 e 63 c 75 u 73 low 22
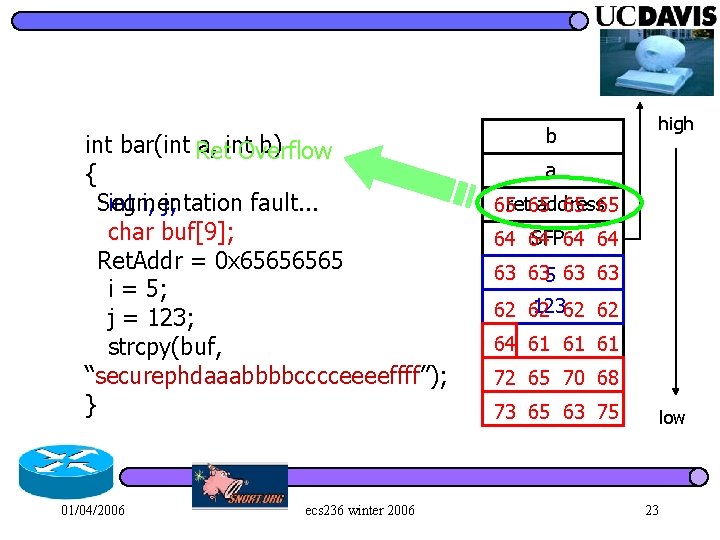
int bar(int Ret a, int b) Overflow { int i, j; Segmentation fault. . . char buf[9]; Ret. Addr = 0 x 6565 i = 5; j = 123; strcpy(buf, “securephdaaabbbbcccceeeeffff”); } 01/04/2006 ecs 236 winter 2006 high b a address 65 ret 65 65 65 SFP 64 64 63 635 63 63 12362 62 64 61 61 61 72 65 70 68 73 65 63 75 low 23
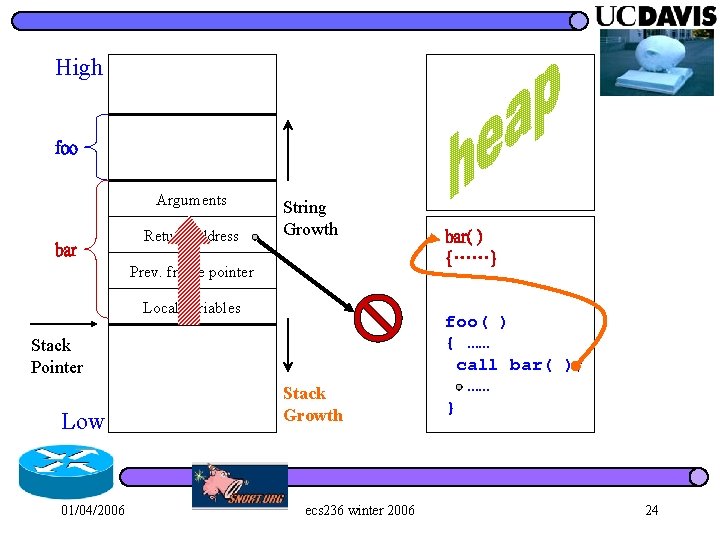
High foo Arguments bar Return address String Growth Prev. frame pointer Local variables Stack Pointer Low 01/04/2006 Stack Growth ecs 236 winter 2006 bar( ) {……} foo( ) { …… call bar( ); …… } 24
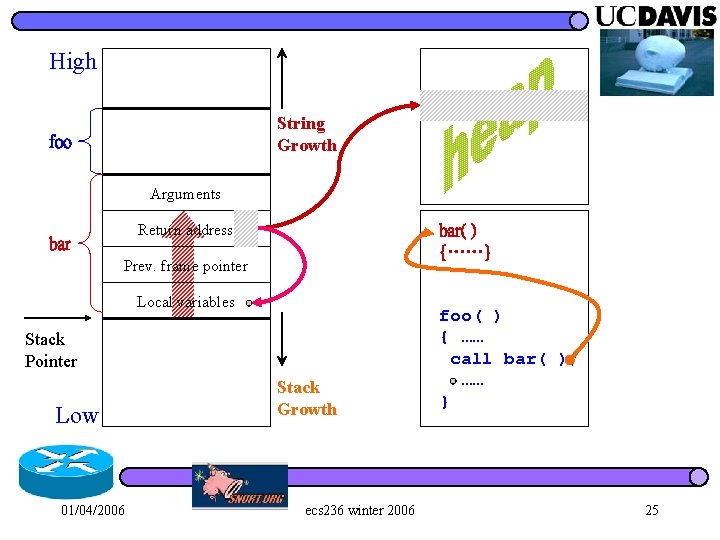
High String Growth foo Arguments Return address bar( ) {……} Prev. frame pointer Local variables Stack Pointer Low 01/04/2006 Stack Growth ecs 236 winter 2006 foo( ) { …… call bar( ); …… } 25
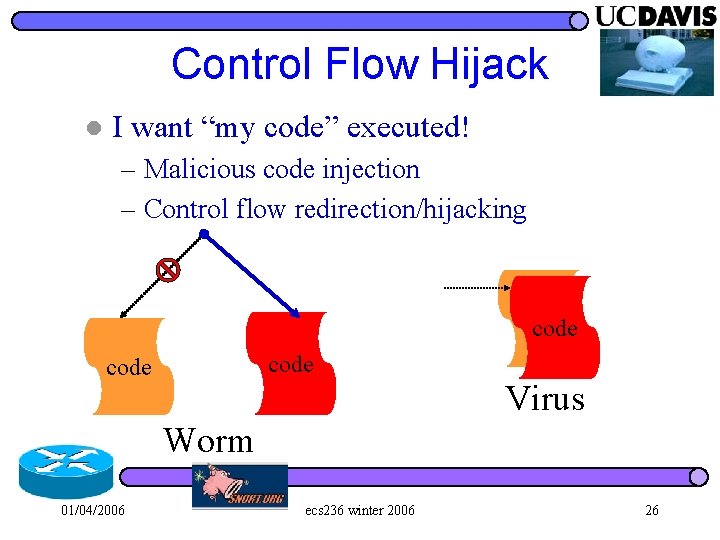
Control Flow Hijack l I want “my code” executed! – Malicious code injection – Control flow redirection/hijacking code Virus Worm 01/04/2006 ecs 236 winter 2006 26
What is a “vulnerability”? l ? ? ? 01/04/2006 ecs 236 winter 2006 27
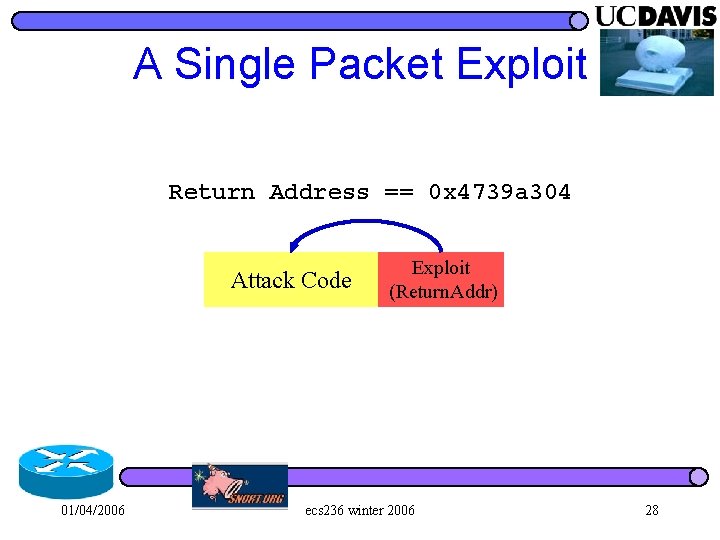
A Single Packet Exploit Return Address == 0 x 4739 a 304 Attack Code 01/04/2006 Exploit (Return. Addr) ecs 236 winter 2006 28
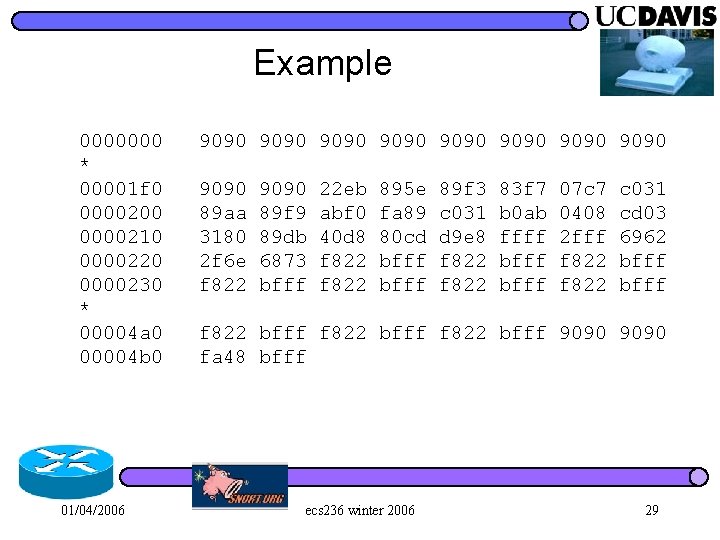
Example 0000000 9090 9090 * 00001 f 0 9090 22 eb 895 e 89 f 3 83 f 7 07 c 7 c 031 0000200 89 aa 89 f 9 abf 0 fa 89 c 031 b 0 ab 0408 cd 03 0000210 3180 89 db 40 d 8 80 cd d 9 e 8 ffff 2 fff 6962 0000220 2 f 6 e 6873 f 822 bfff 0000230 f 822 bfff * 00004 a 0 f 822 bfff 9090 00004 b 0 fa 48 bfff 01/04/2006 ecs 236 winter 2006 29
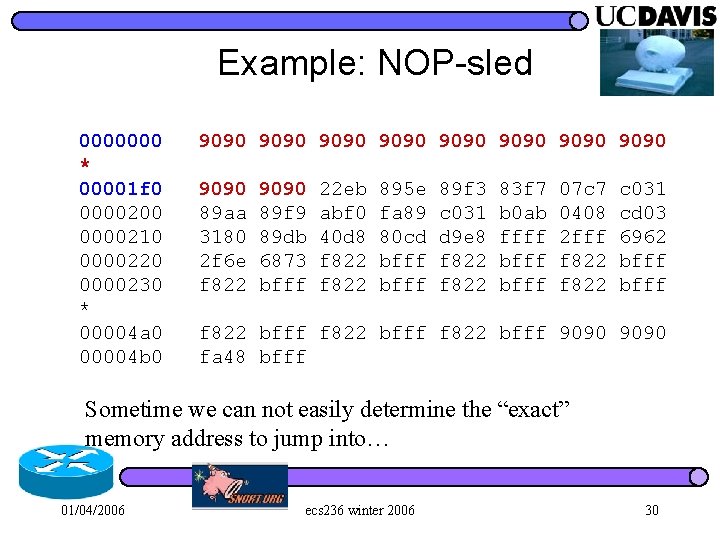
Example: NOP-sled 0000000 9090 9090 * 00001 f 0 9090 22 eb 895 e 89 f 3 83 f 7 07 c 7 c 031 0000200 89 aa 89 f 9 abf 0 fa 89 c 031 b 0 ab 0408 cd 03 0000210 3180 89 db 40 d 8 80 cd d 9 e 8 ffff 2 fff 6962 0000220 2 f 6 e 6873 f 822 bfff 0000230 f 822 bfff * 00004 a 0 f 822 bfff 9090 00004 b 0 fa 48 bfff Sometime we can not easily determine the “exact” memory address to jump into… 01/04/2006 ecs 236 winter 2006 30
![“NOP Sled” Engineering Attack Code Exploit (Return. Addr) code[] = “xebx 2 ax 5 “NOP Sled” Engineering Attack Code Exploit (Return. Addr) code[] = “xebx 2 ax 5](http://slidetodoc.com/presentation_image/62218348616c52174d612deeb7554496/image-31.jpg)
“NOP Sled” Engineering Attack Code Exploit (Return. Addr) code[] = “xebx 2 ax 5 fxc 6x 47x 00x 89x 7 fx 08xc 7x 47”; strcpy(buf, code); buf = “xebx 2 ax 5 fxc 6x 47x 07” NOP NOP Attack Code Exploit (Return. Addr) And, sometimes, we simply want to find a way to avoid “x 00”. 01/04/2006 ecs 236 winter 2006 31
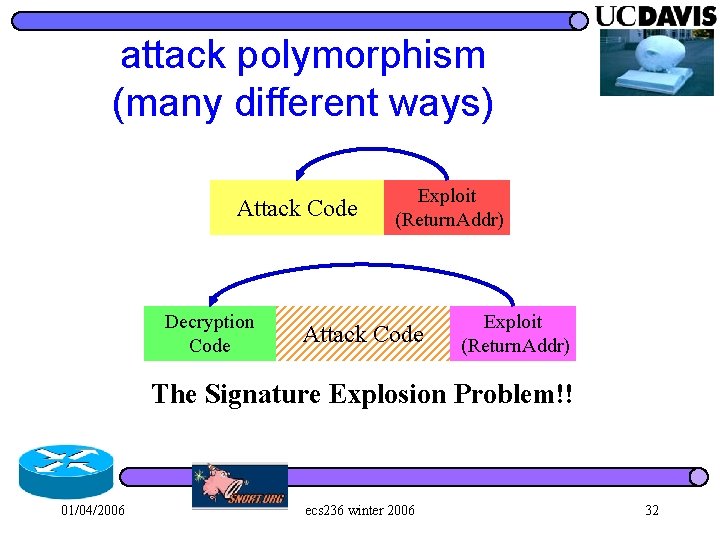
attack polymorphism (many different ways) Attack Code Decryption Code Exploit (Return. Addr) Attack Code Exploit (Return. Addr) The Signature Explosion Problem!! 01/04/2006 ecs 236 winter 2006 32
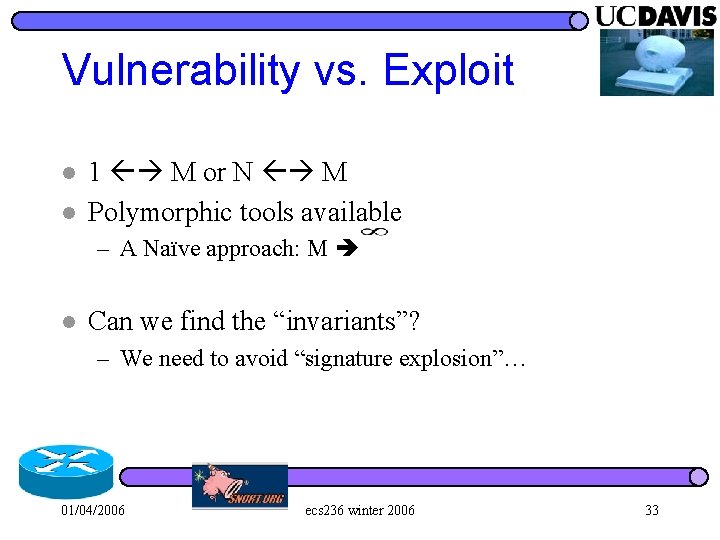
Vulnerability vs. Exploit l l 1 M or N M Polymorphic tools available – A Naïve approach: M l Can we find the “invariants”? – We need to avoid “signature explosion”… 01/04/2006 ecs 236 winter 2006 33
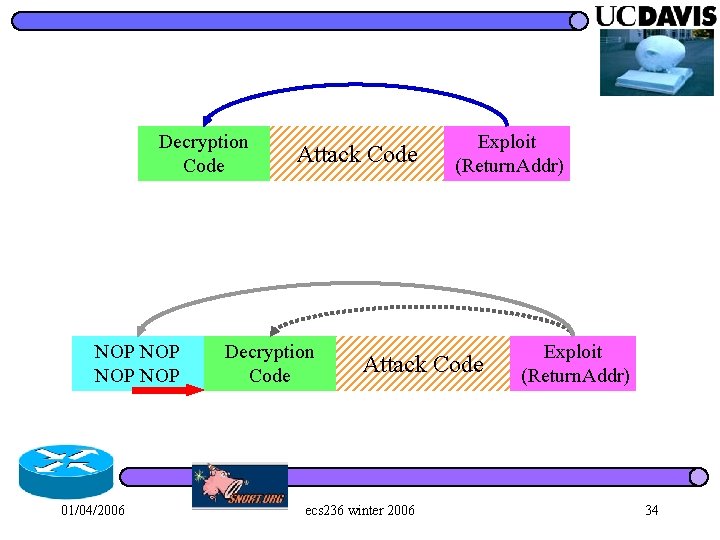
Decryption Code NOP NOP 01/04/2006 Attack Code Decryption Code Exploit (Return. Addr) Attack Code ecs 236 winter 2006 Exploit (Return. Addr) 34
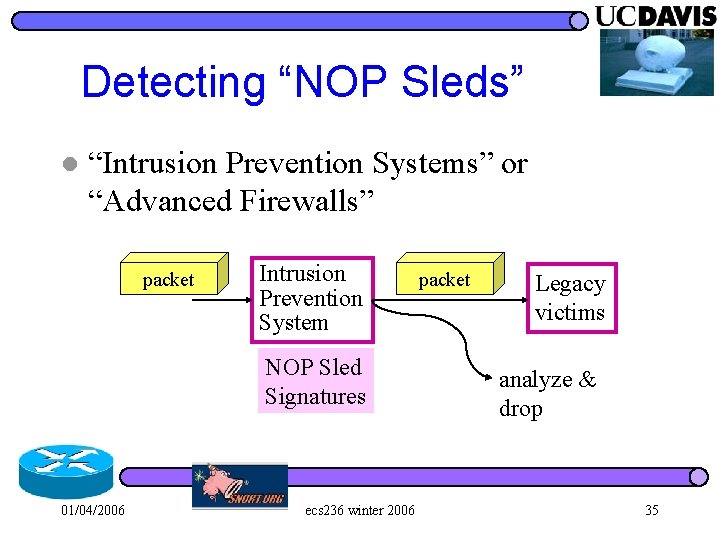
Detecting “NOP Sleds” l “Intrusion Prevention Systems” or “Advanced Firewalls” packet Intrusion Prevention System NOP Sled Signatures 01/04/2006 ecs 236 winter 2006 packet Legacy victims analyze & drop 35
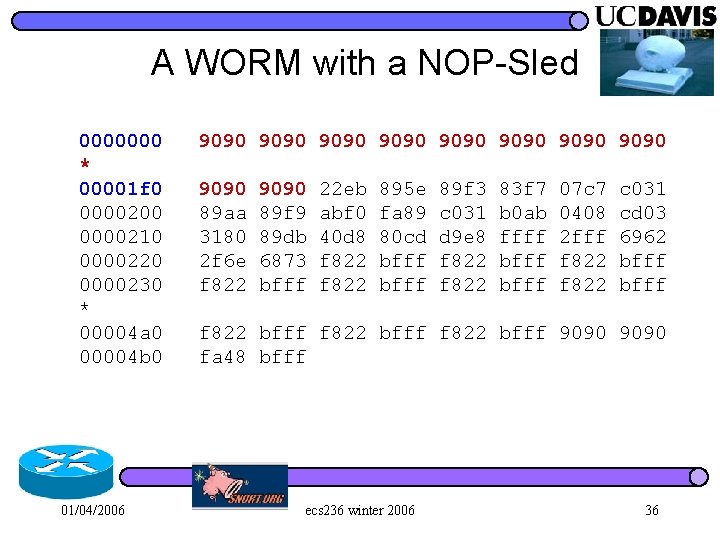
A WORM with a NOP-Sled 0000000 9090 9090 * 00001 f 0 9090 22 eb 895 e 89 f 3 83 f 7 07 c 7 c 031 0000200 89 aa 89 f 9 abf 0 fa 89 c 031 b 0 ab 0408 cd 03 0000210 3180 89 db 40 d 8 80 cd d 9 e 8 ffff 2 fff 6962 0000220 2 f 6 e 6873 f 822 bfff 0000230 f 822 bfff * 00004 a 0 f 822 bfff 9090 00004 b 0 fa 48 bfff 01/04/2006 ecs 236 winter 2006 36
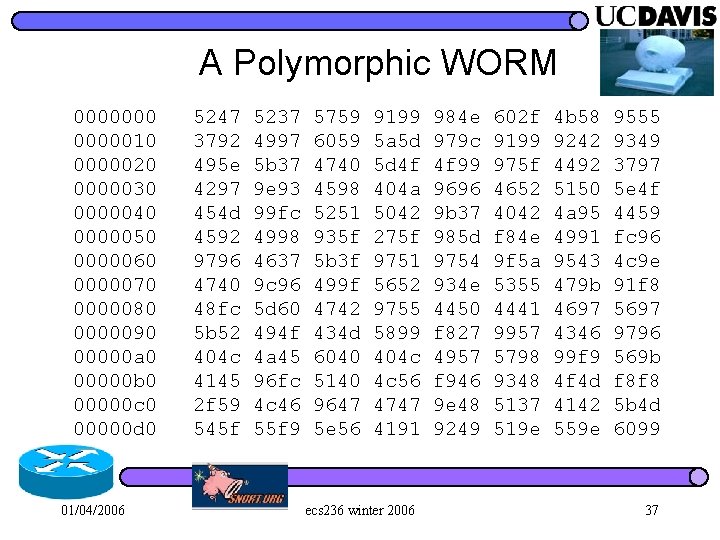
A Polymorphic WORM 0000000 5247 5237 5759 9199 984 e 602 f 4 b 58 9555 0000010 3792 4997 6059 5 a 5 d 979 c 9199 9242 9349 0000020 495 e 5 b 37 4740 5 d 4 f 4 f 99 975 f 4492 3797 0000030 4297 9 e 93 4598 404 a 9696 4652 5150 5 e 4 f 0000040 454 d 99 fc 5251 5042 9 b 37 4042 4 a 95 4459 0000050 4592 4998 935 f 275 f 985 d f 84 e 4991 fc 96 0000060 9796 4637 5 b 3 f 9751 9754 9 f 5 a 9543 4 c 9 e 0000070 4740 9 c 96 499 f 5652 934 e 5355 479 b 91 f 8 0000080 48 fc 5 d 60 4742 9755 4450 4441 4697 5697 0000090 5 b 52 494 f 434 d 5899 f 827 9957 4346 9796 00000 a 0 404 c 4 a 45 6040 404 c 4957 5798 99 f 9 569 b 00000 b 0 4145 96 fc 5140 4 c 56 f 946 9348 4 f 4 d f 8 f 8 00000 c 0 2 f 59 4 c 46 9647 4747 9 e 48 5137 4142 5 b 4 d 00000 d 0 545 f 55 f 9 5 e 56 4191 9249 519 e 559 e 6099 01/04/2006 ecs 236 winter 2006 37
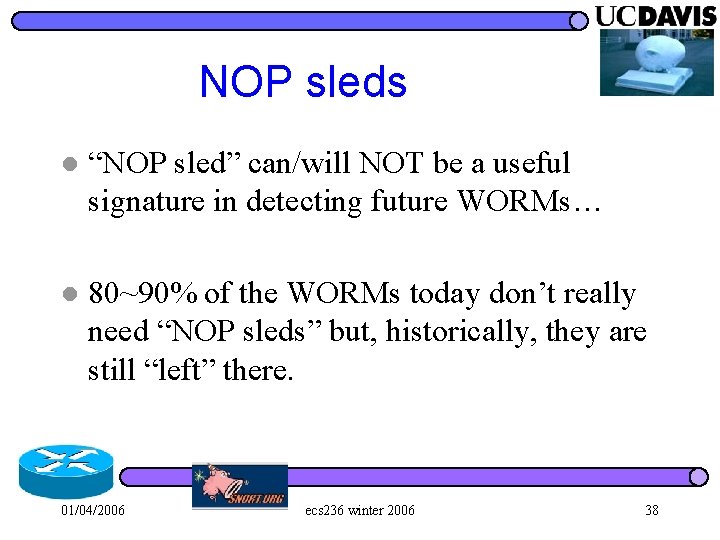
NOP sleds l “NOP sled” can/will NOT be a useful signature in detecting future WORMs… l 80~90% of the WORMs today don’t really need “NOP sleds” but, historically, they are still “left” there. 01/04/2006 ecs 236 winter 2006 38
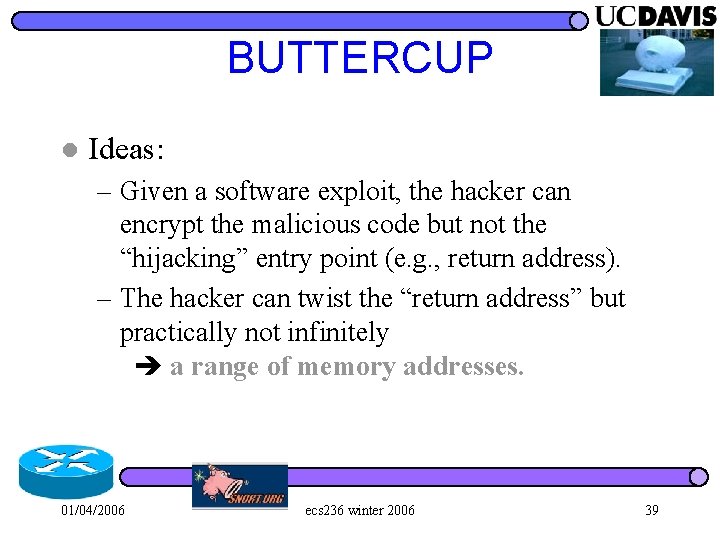
BUTTERCUP l Ideas: – Given a software exploit, the hacker can encrypt the malicious code but not the “hijacking” entry point (e. g. , return address). – The hacker can twist the “return address” but practically not infinitely a range of memory addresses. 01/04/2006 ecs 236 winter 2006 39
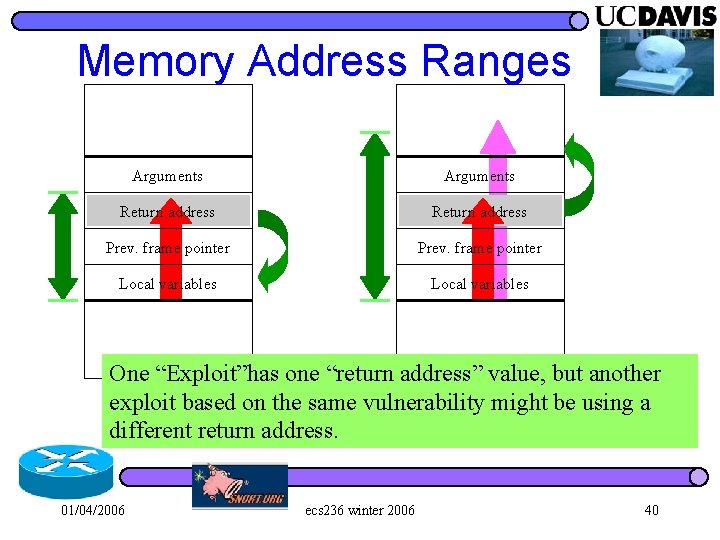
Memory Address Ranges Arguments Return address Prev. frame pointer Local variables One “Exploit”has one “return address” value, but another exploit based on the same vulnerability might be using a different return address. 01/04/2006 ecs 236 winter 2006 40
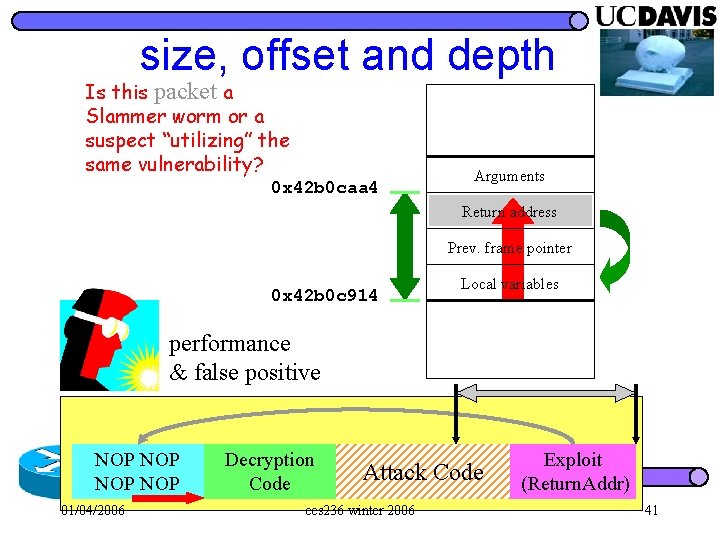
size, offset and depth Is this packet a Slammer worm or a suspect “utilizing” the same vulnerability? 0 x 42 b 0 caa 4 Arguments Return address Prev. frame pointer 0 x 42 b 0 c 914 Local variables performance & false positive NOP NOP 01/04/2006 Decryption Code Attack Code ecs 236 winter 2006 Exploit (Return. Addr) 41
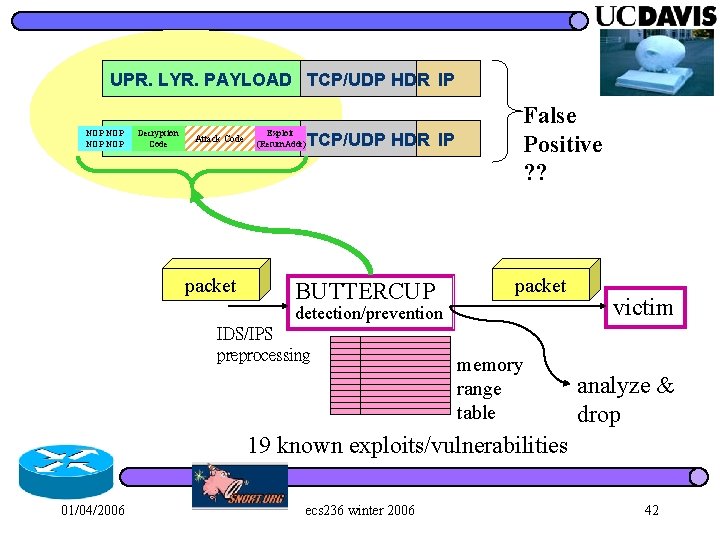
UPR. LYR. PAYLOAD TCP/UDP HDR IP NOP NOP Decryption Code Exploit (Return. Addr) Code UPR. LYR. Attack PAYLOAD TCP/UDP HDR IP packet BUTTERCUP False Positive ? ? packet detection/prevention IDS/IPS preprocessing memory range table victim analyze & drop 19 known exploits/vulnerabilities 01/04/2006 ecs 236 winter 2006 42
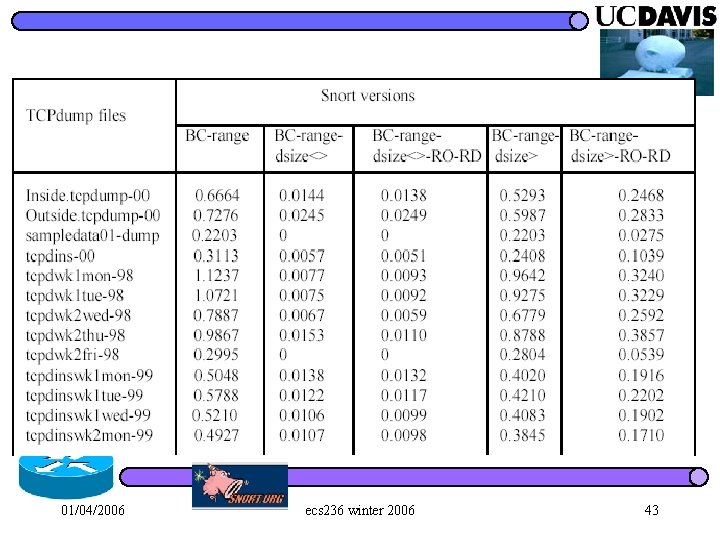
01/04/2006 ecs 236 winter 2006 43
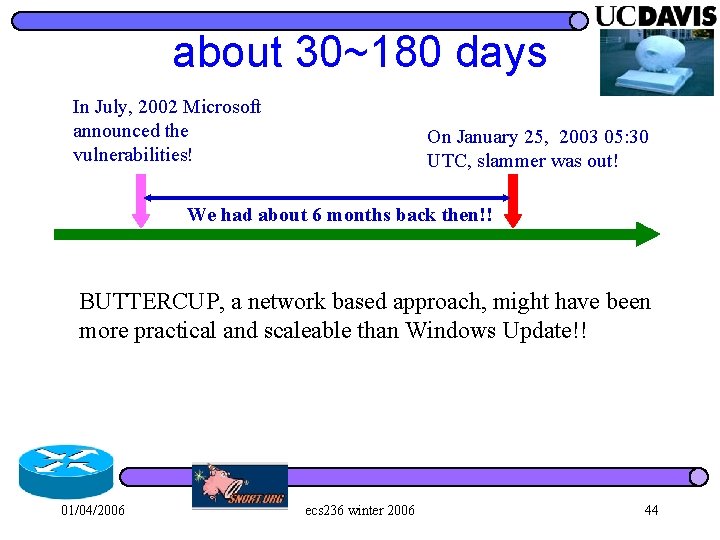
about 30~180 days In July, 2002 Microsoft announced the vulnerabilities! On January 25, 2003 05: 30 UTC, slammer was out! We had about 6 months back then!! BUTTERCUP, a network based approach, might have been more practical and scaleable than Windows Update!! 01/04/2006 ecs 236 winter 2006 44
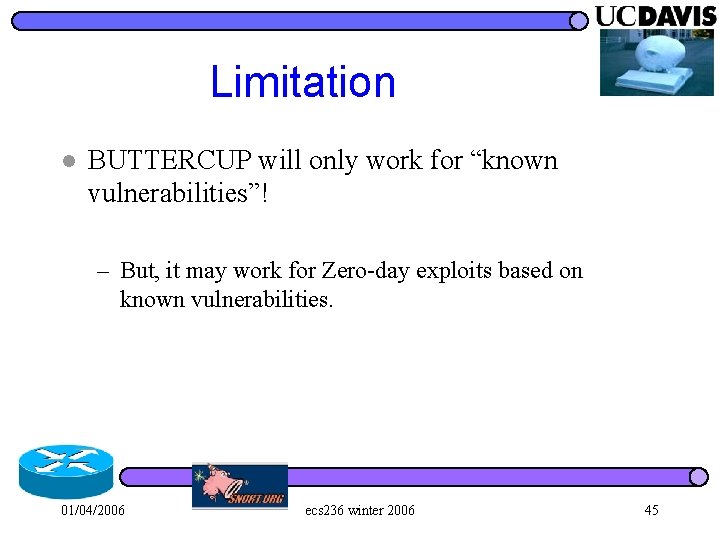
Limitation l BUTTERCUP will only work for “known vulnerabilities”! – But, it may work for Zero-day exploits based on known vulnerabilities. 01/04/2006 ecs 236 winter 2006 45
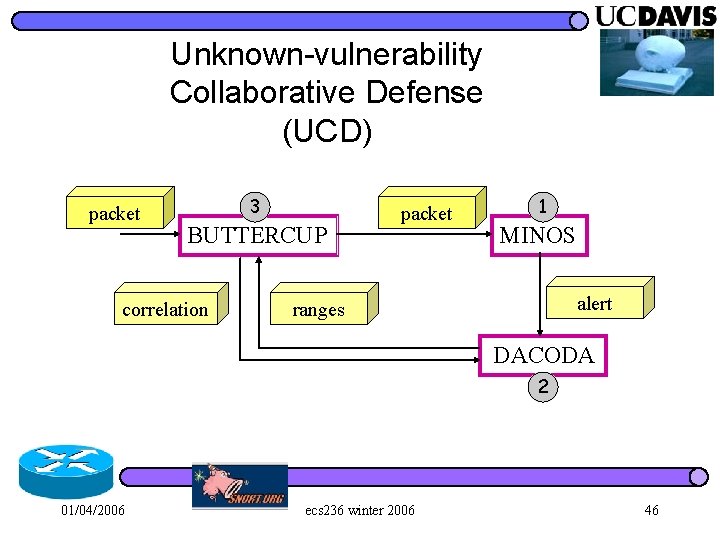
Unknown-vulnerability Collaborative Defense (UCD) packet 3 BUTTERCUP correlation packet 1 MINOS alert ranges DACODA 2 01/04/2006 ecs 236 winter 2006 46
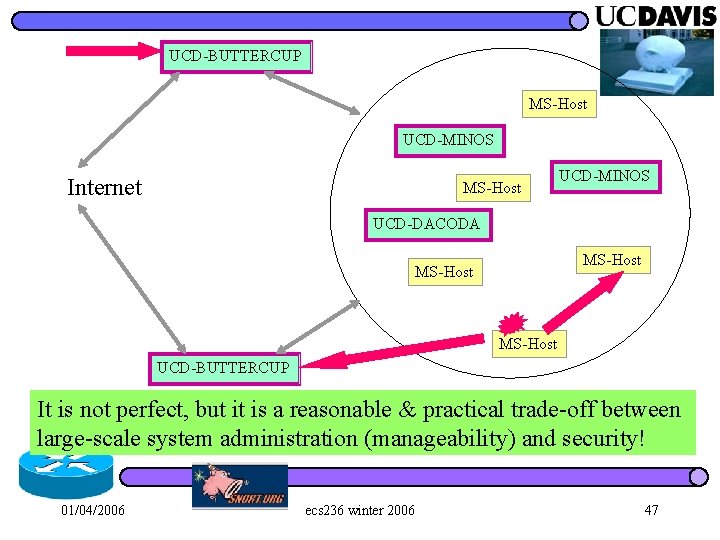
UCD-BUTTERCUP MS-Host UCD-MINOS Internet MS-Host UCD-MINOS UCD-DACODA MS-Host UCD-BUTTERCUP It is not perfect, but it is a reasonable & practical trade-off between large-scale system administration (manageability) and security! 01/04/2006 ecs 236 winter 2006 47
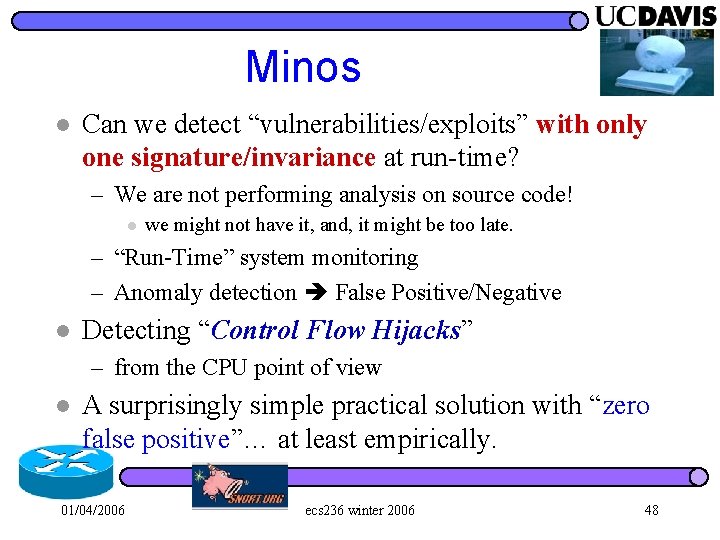
Minos l Can we detect “vulnerabilities/exploits” with only one signature/invariance at run-time? – We are not performing analysis on source code! l we might not have it, and, it might be too late. – “Run-Time” system monitoring – Anomaly detection False Positive/Negative l Detecting “Control Flow Hijacks” – from the CPU point of view l A surprisingly simple practical solution with “zero false positive”… at least empirically. 01/04/2006 ecs 236 winter 2006 48
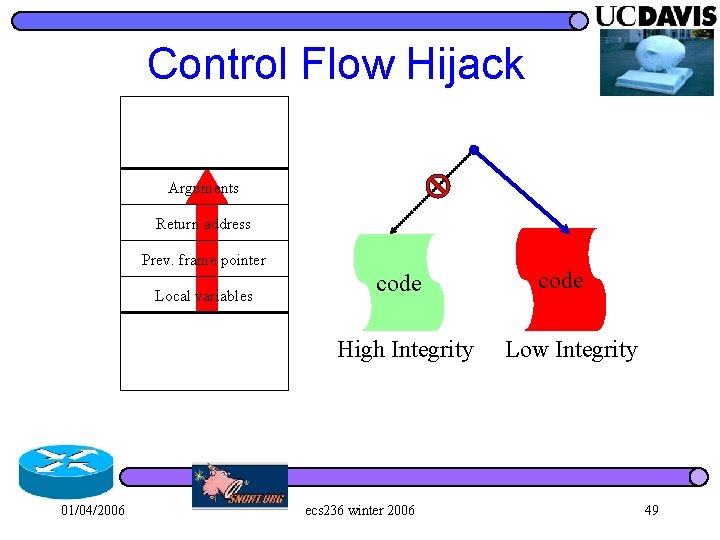
Control Flow Hijack Arguments Return address Prev. frame pointer Local variables code High Integrity 01/04/2006 ecs 236 winter 2006 code Low Integrity 49
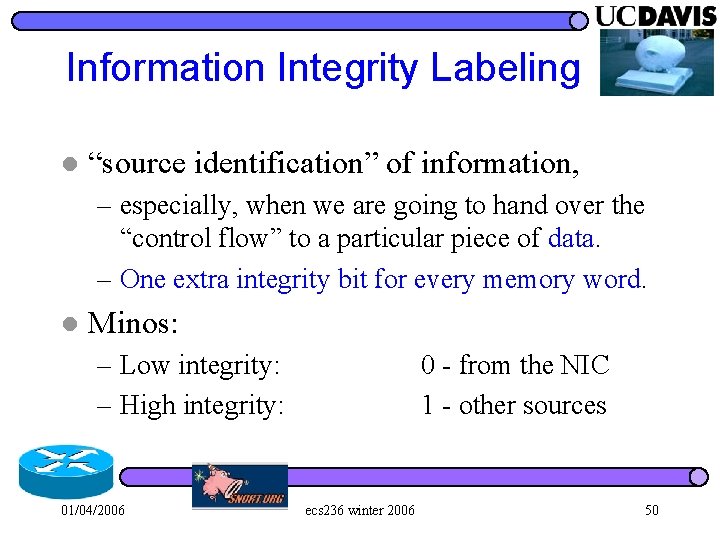
Information Integrity Labeling l “source identification” of information, – especially, when we are going to hand over the “control flow” to a particular piece of data. – One extra integrity bit for every memory word. l Minos: – Low integrity: – High integrity: 01/04/2006 0 - from the NIC 1 - other sources ecs 236 winter 2006 50
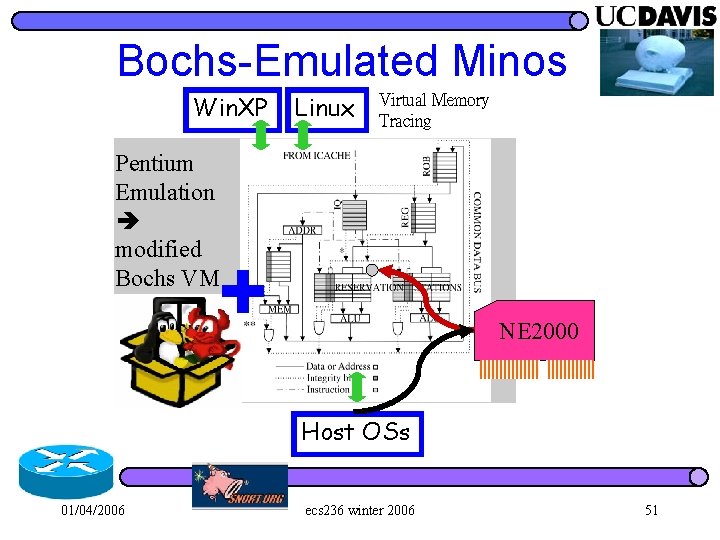
Bochs-Emulated Minos Win. XP Linux Virtual Memory Tracing Pentium Emulation modified Bochs VM NE 2000 Host OSs 01/04/2006 ecs 236 winter 2006 51
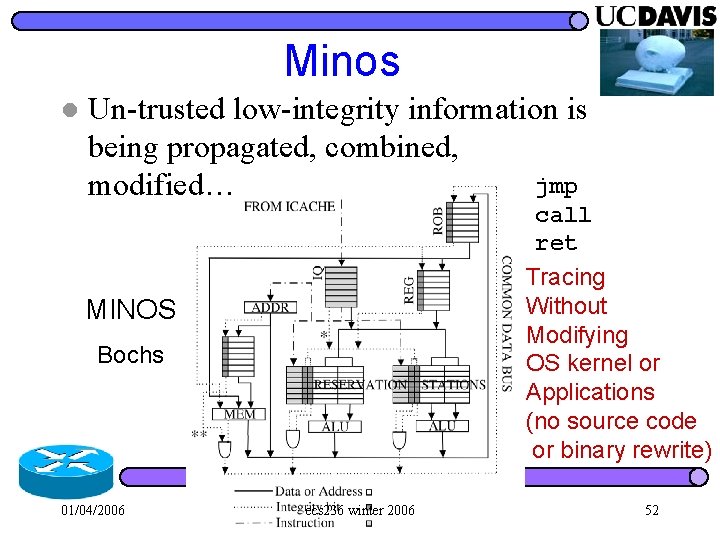
Minos l Un-trusted low-integrity information is being propagated, combined, jmp modified… call ret Tracing Without Modifying OS kernel or Applications (no source code or binary rewrite) MINOS Bochs 01/04/2006 ecs 236 winter 2006 52
Biba’s Low-water-mark Integrity Policy Tracks the “taintedness” of data l Access controls are based on accesses a subject has made in the past l 01/04/2006 ecs 236 winter 2006 53
When an attack is caught… l Control-flow related instructions low integrity data – Examples: call, jmp, ret 01/04/2006 ecs 236 winter 2006 54
FP & FN l Against real attacks (30~50 per months) under 4 static IP addresses – We have changed/reconfigured to try different software patches and versions. – Many high-frequency attacks were patched. l Control Flow Hijack – Zero false positive (a proof? ) l How about False Negative? – Information flow, and virtual memory 01/04/2006 ecs 236 winter 2006 55
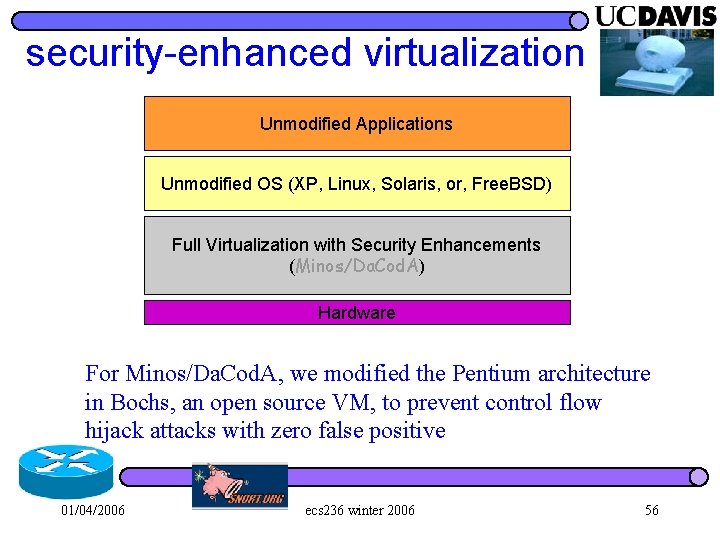
security-enhanced virtualization Unmodified Applications Unmodified OS (XP, Linux, Solaris, or, Free. BSD) Full Virtualization with Security Enhancements (Minos/Da. Cod. A) Hardware For Minos/Da. Cod. A, we modified the Pentium architecture in Bochs, an open source VM, to prevent control flow hijack attacks with zero false positive 01/04/2006 ecs 236 winter 2006 56
MINOS DACODA exploit vulnerability invariant signature 01/04/2006 ecs 236 winter 2006 57
MINOS DACODA Buttercup: NOMS’ 2004 l Minos: Micro’ 2004 l Minos Honeypot: DIMVA’ 2005 l 01/04/2006 ecs 236 winter 2006 58
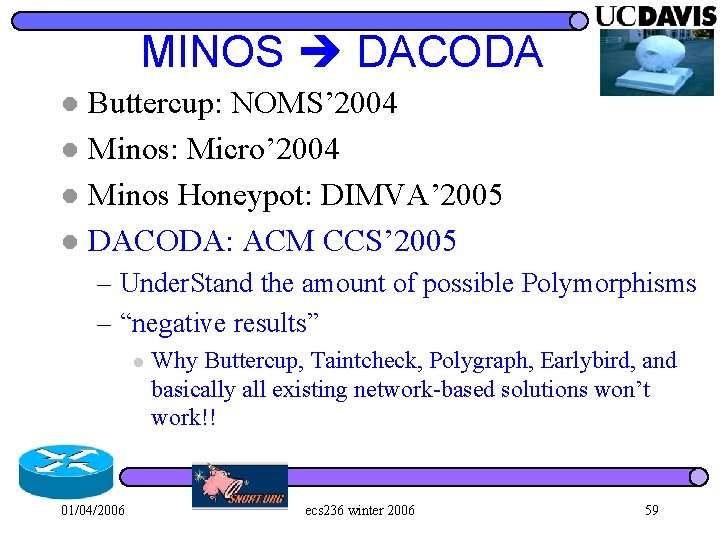
MINOS DACODA Buttercup: NOMS’ 2004 l Minos: Micro’ 2004 l Minos Honeypot: DIMVA’ 2005 l DACODA: ACM CCS’ 2005 l – Under. Stand the amount of possible Polymorphisms – “negative results” l 01/04/2006 Why Buttercup, Taintcheck, Polygraph, Earlybird, and basically all existing network-based solutions won’t work!! ecs 236 winter 2006 59
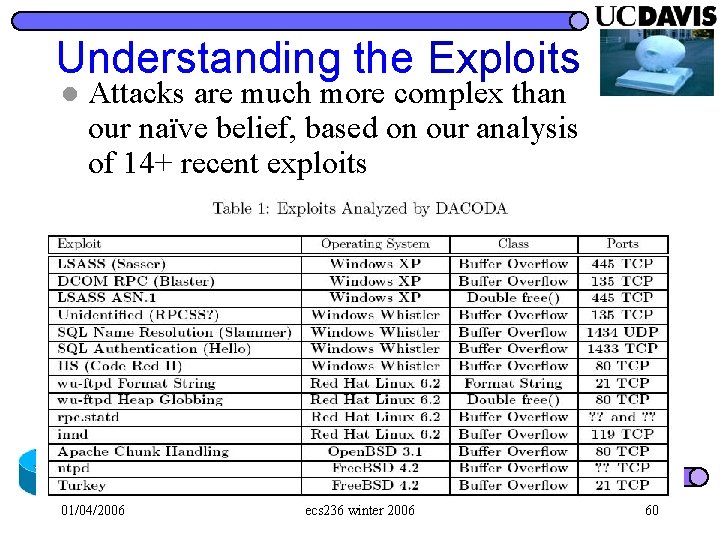
Understanding the Exploits l Attacks are much more complex than our naïve belief, based on our analysis of 14+ recent exploits 01/04/2006 ecs 236 winter 2006 60
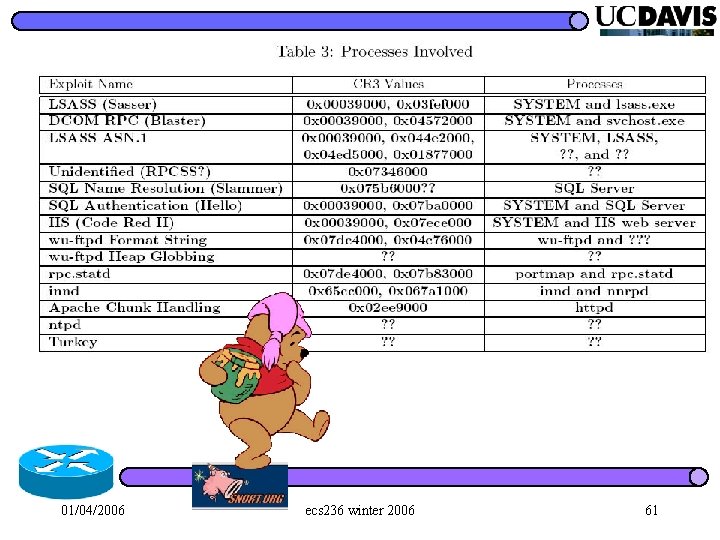
01/04/2006 ecs 236 winter 2006 61
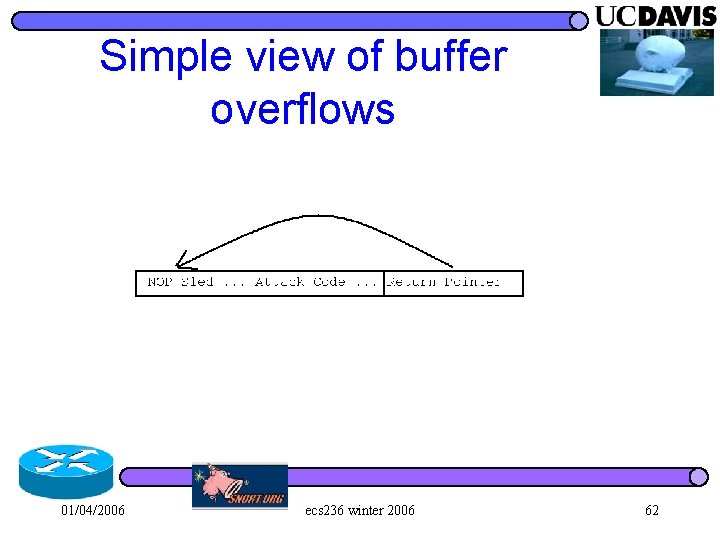
Simple view of buffer overflows 01/04/2006 ecs 236 winter 2006 62
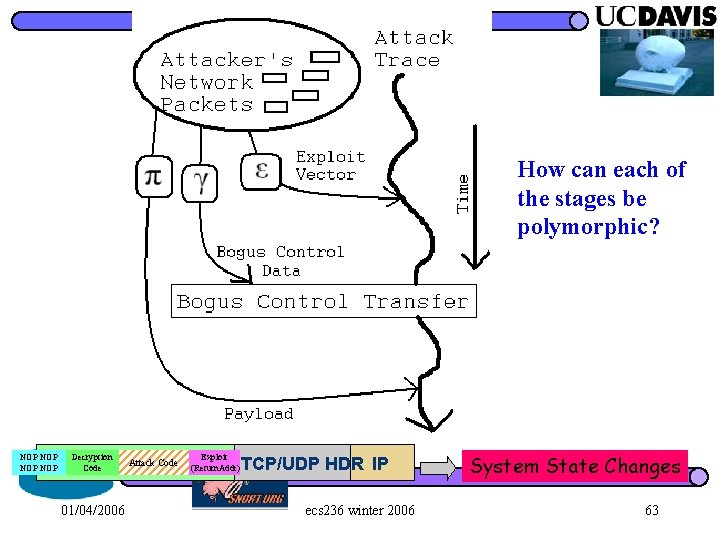
How can each of the stages be polymorphic? NOP NOP Decryption Exploit Code UPR. Code LYR. Attack PAYLOAD (Return. Addr) TCP/UDP HDR IP 01/04/2006 ecs 236 winter 2006 System State Changes 63
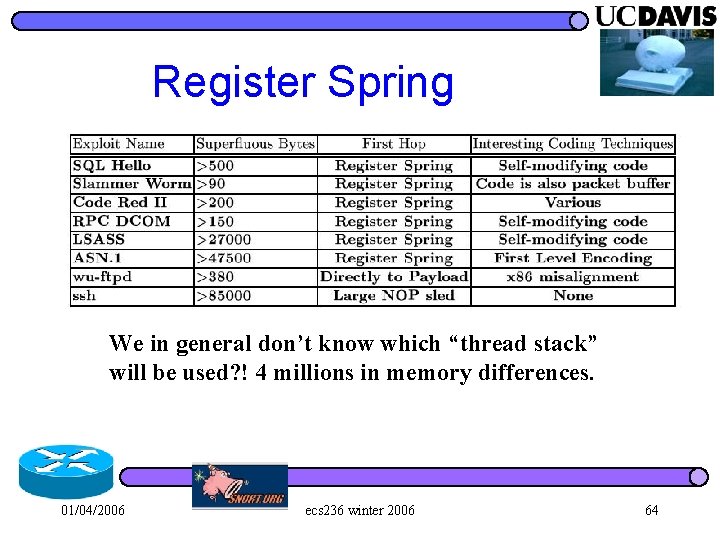
Register Spring We in general don’t know which “thread stack” will be used? ! 4 millions in memory differences. 01/04/2006 ecs 236 winter 2006 64
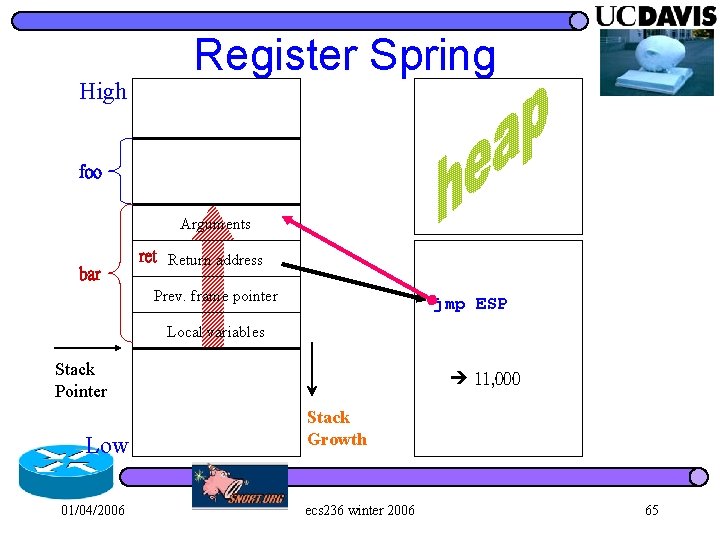
High Register Spring foo Arguments bar ret Return address Prev. frame pointer jmp ESP Local variables Stack Pointer Low 01/04/2006 11, 000 Stack Growth ecs 236 winter 2006 65
Slammer 01/04/2006 ecs 236 winter 2006 66
ESP l Register springs off of ESP utilize the compiler conventions for managing stack frames 01/04/2006 ecs 236 winter 2006 67
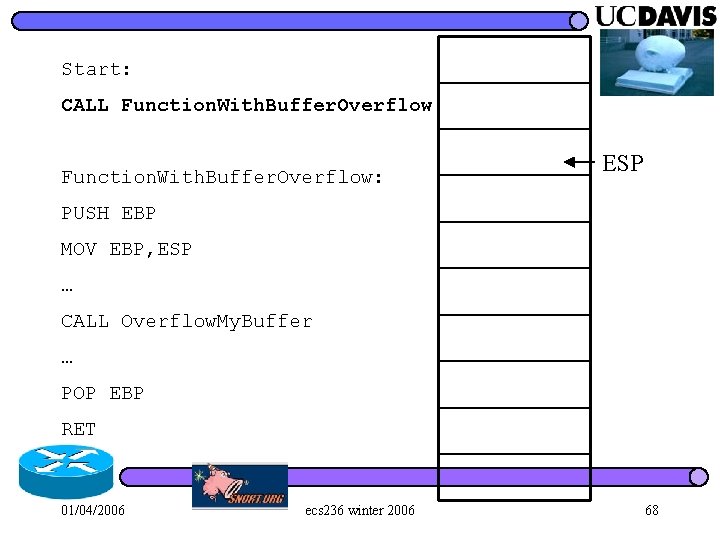
Start: CALL Function. With. Buffer. Overflow: ESP PUSH EBP MOV EBP, ESP … CALL Overflow. My. Buffer … POP EBP RET 01/04/2006 ecs 236 winter 2006 68
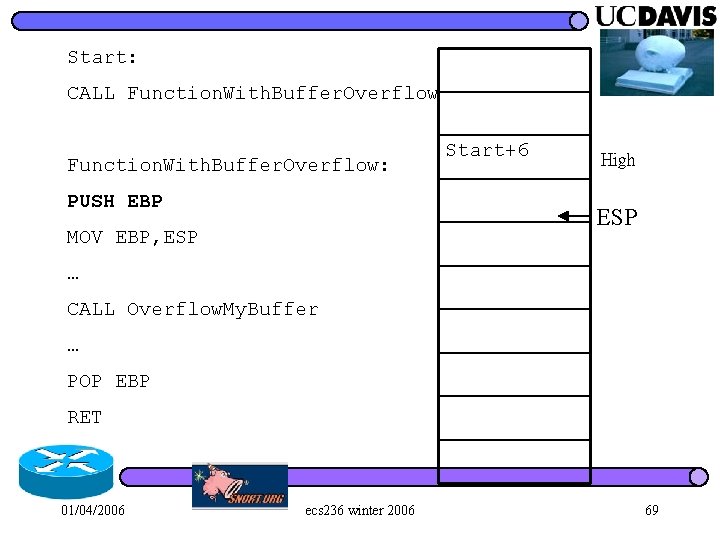
Start: CALL Function. With. Buffer. Overflow: PUSH EBP Start+6 High ESP MOV EBP, ESP … CALL Overflow. My. Buffer … POP EBP RET 01/04/2006 ecs 236 winter 2006 69
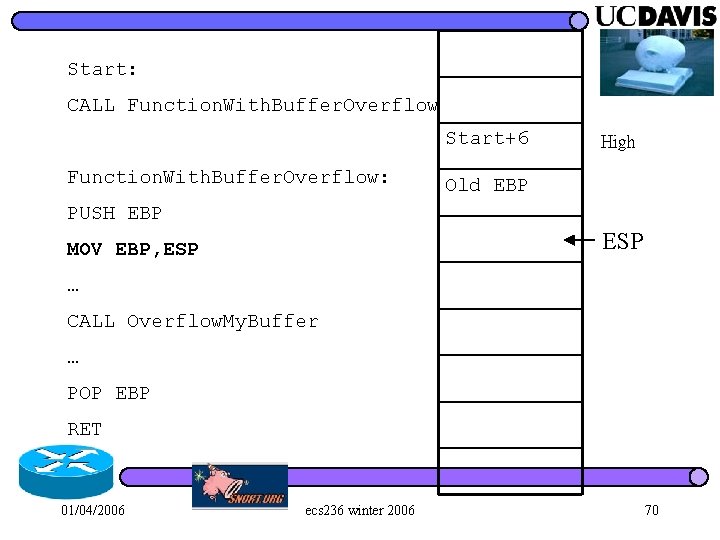
Start: CALL Function. With. Buffer. Overflow Start+6 Function. With. Buffer. Overflow: High Old EBP PUSH EBP ESP MOV EBP, ESP … CALL Overflow. My. Buffer … POP EBP RET 01/04/2006 ecs 236 winter 2006 70
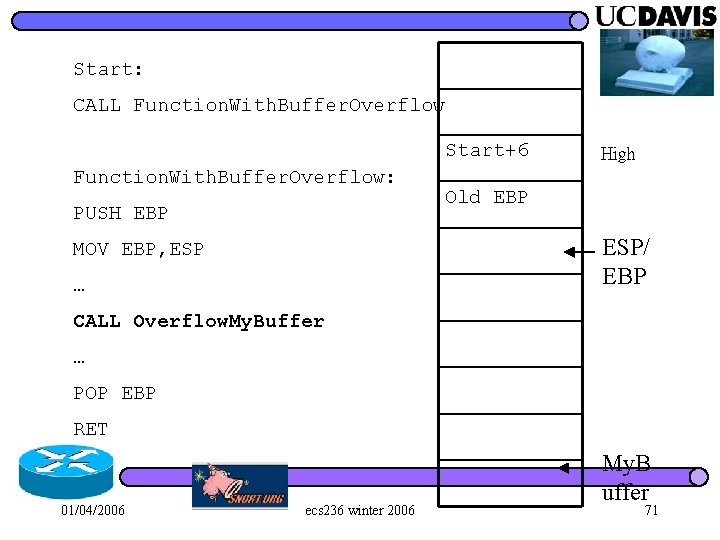
Start: CALL Function. With. Buffer. Overflow Start+6 Function. With. Buffer. Overflow: PUSH EBP High Old EBP ESP/ EBP MOV EBP, ESP … CALL Overflow. My. Buffer … POP EBP RET 01/04/2006 ecs 236 winter 2006 My. B uffer 71
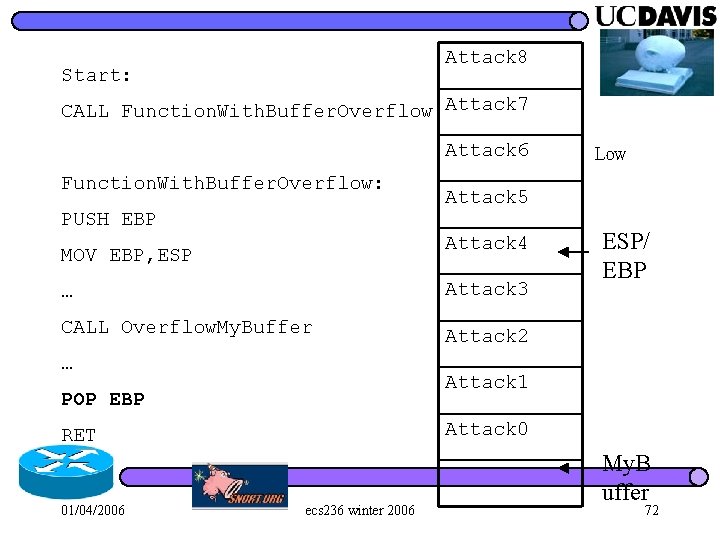
Attack 8 Start: CALL Function. With. Buffer. Overflow Attack 7 Attack 6 Function. With. Buffer. Overflow: PUSH EBP Attack 5 Attack 4 MOV EBP, ESP … Attack 3 CALL Overflow. My. Buffer Attack 2 … ESP/ EBP Attack 1 POP EBP Attack 0 RET 01/04/2006 Low ecs 236 winter 2006 My. B uffer 72
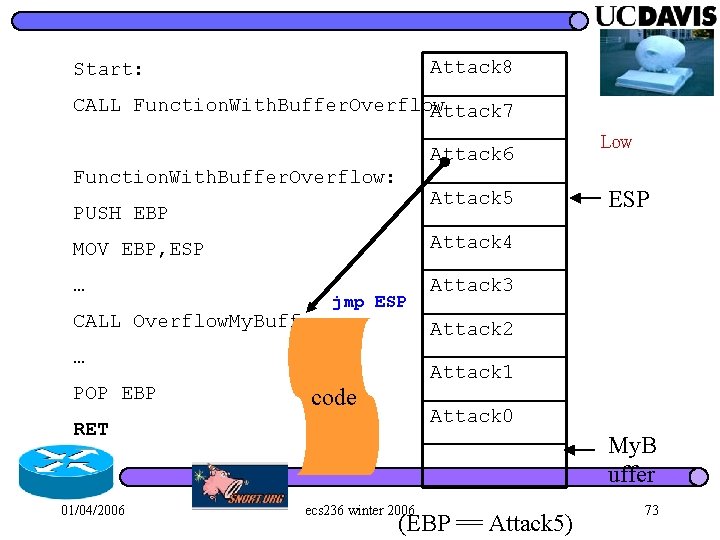
Attack 8 Start: CALL Function. With. Buffer. Overflow Attack 7 Attack 6 Function. With. Buffer. Overflow: Attack 5 PUSH EBP MOV EBP, ESP Attack 4 … Attack 3 CALL Overflow. My. Buffer jmp ESP Attack 1 code Attack 0 RET 01/04/2006 ESP Attack 2 … POP EBP Low My. B uffer ecs 236 winter 2006 (EBP == Attack 5) 73
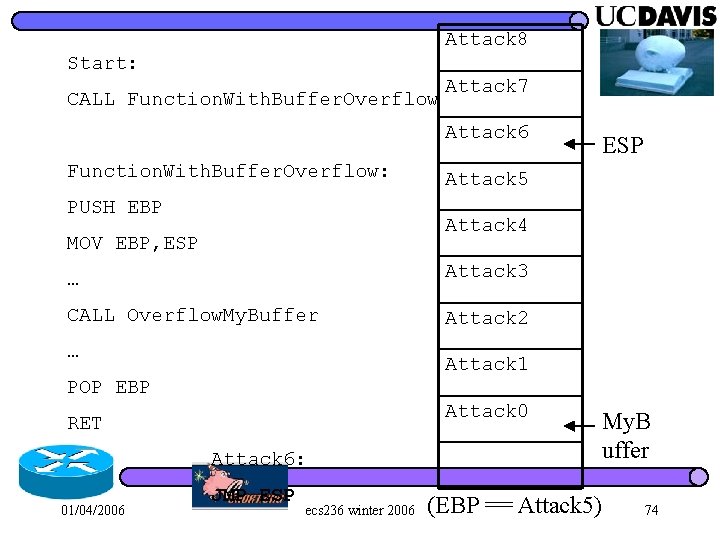
Attack 8 Start: CALL Function. With. Buffer. Overflow Attack 7 Attack 6 Function. With. Buffer. Overflow: PUSH EBP ESP Attack 5 Attack 4 MOV EBP, ESP … Attack 3 CALL Overflow. My. Buffer Attack 2 … Attack 1 POP EBP Attack 0 RET Attack 6: 01/04/2006 JMP ESP ecs 236 winter 2006 My. B uffer (EBP == Attack 5) 74
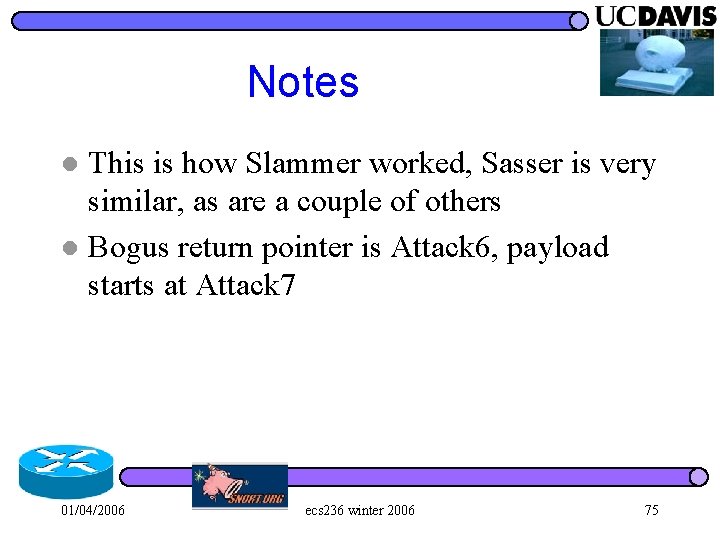
Notes This is how Slammer worked, Sasser is very similar, as are a couple of others l Bogus return pointer is Attack 6, payload starts at Attack 7 l 01/04/2006 ecs 236 winter 2006 75
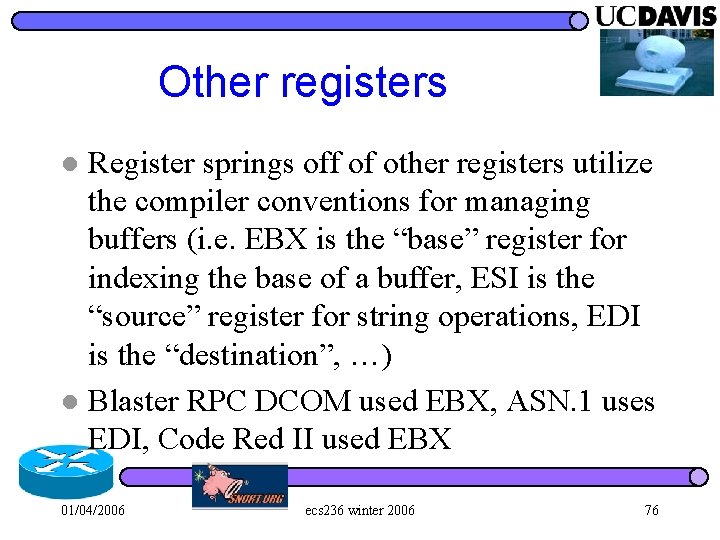
Other registers Register springs off of other registers utilize the compiler conventions for managing buffers (i. e. EBX is the “base” register for indexing the base of a buffer, ESI is the “source” register for string operations, EDI is the “destination”, …) l Blaster RPC DCOM used EBX, ASN. 1 uses EDI, Code Red II used EBX l 01/04/2006 ecs 236 winter 2006 76
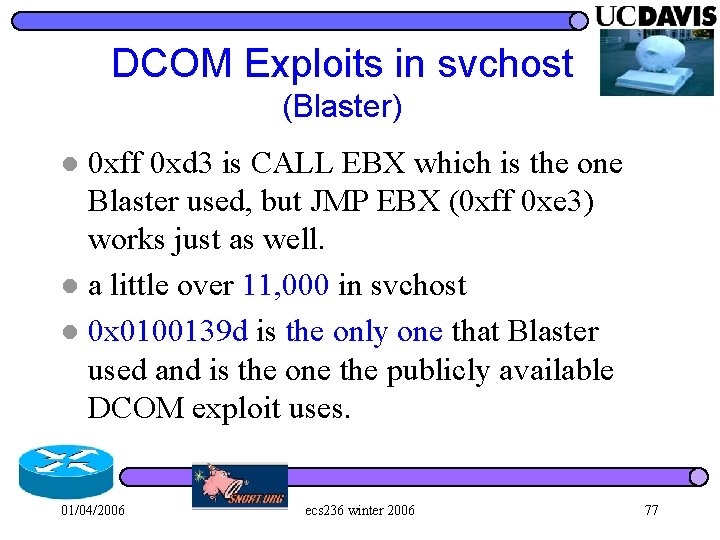
DCOM Exploits in svchost (Blaster) 0 xff 0 xd 3 is CALL EBX which is the one Blaster used, but JMP EBX (0 xff 0 xe 3) works just as well. l a little over 11, 000 in svchost l 0 x 0100139 d is the only one that Blaster used and is the one the publicly available DCOM exploit uses. l 01/04/2006 ecs 236 winter 2006 77
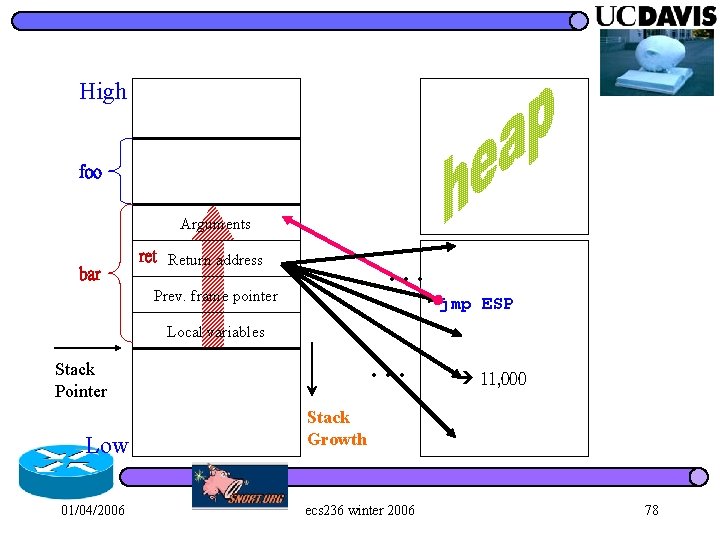
High foo Arguments bar … ret Return address Prev. frame pointer jmp ESP Local variables … Stack Pointer Low 01/04/2006 11, 000 Stack Growth ecs 236 winter 2006 78
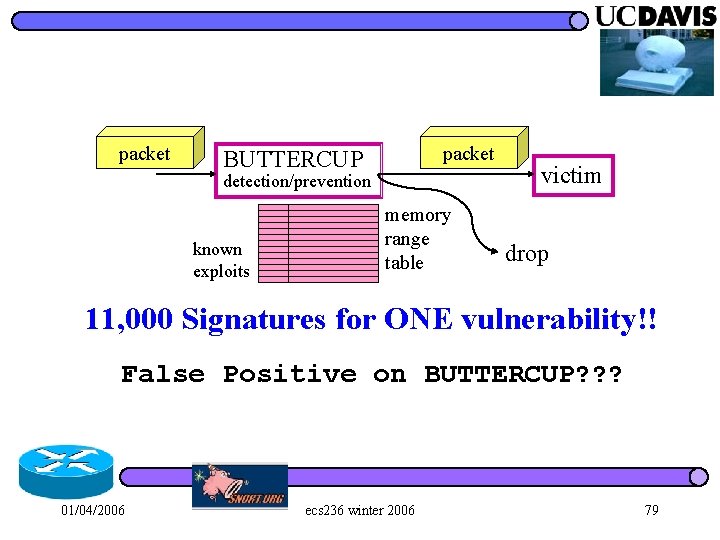
packet BUTTERCUP detection/prevention known exploits memory range table victim drop 11, 000 Signatures for ONE vulnerability!! False Positive on BUTTERCUP? ? ? 01/04/2006 ecs 236 winter 2006 79
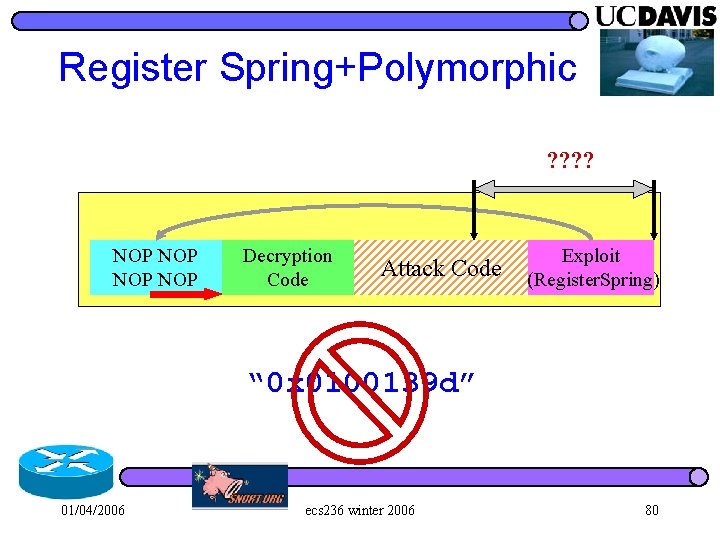
Register Spring+Polymorphic ? ? NOP NOP Decryption Code Attack Code Exploit (Register. Spring) “ 0 x 0100139 d” 01/04/2006 ecs 236 winter 2006 80
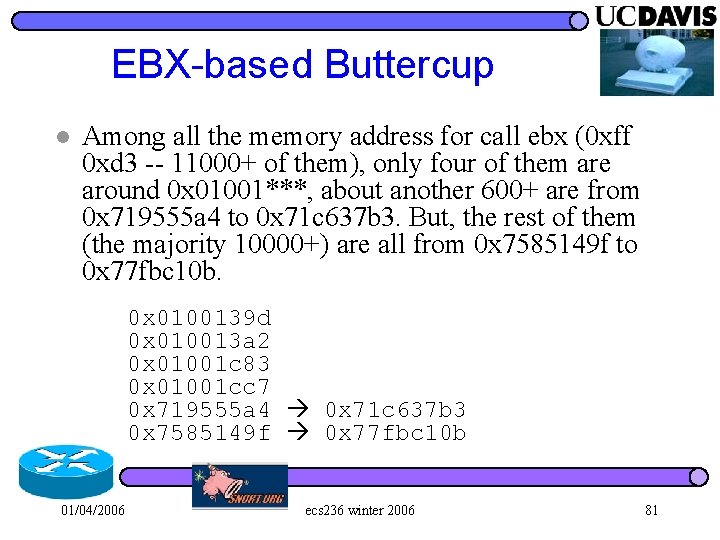
EBX-based Buttercup l Among all the memory address for call ebx (0 xff 0 xd 3 -- 11000+ of them), only four of them are around 0 x 01001***, about another 600+ are from 0 x 719555 a 4 to 0 x 71 c 637 b 3. But, the rest of them (the majority 10000+) are all from 0 x 7585149 f to 0 x 77 fbc 10 b. 0 x 0100139 d 0 x 010013 a 2 0 x 01001 c 83 0 x 01001 cc 7 0 x 719555 a 4 0 x 71 c 637 b 3 0 x 7585149 f 0 x 77 fbc 10 b 01/04/2006 ecs 236 winter 2006 81
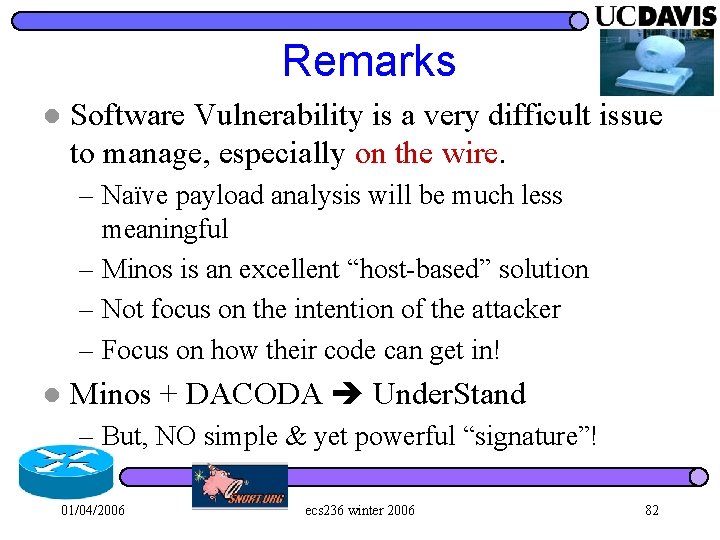
Remarks l Software Vulnerability is a very difficult issue to manage, especially on the wire. – Naïve payload analysis will be much less meaningful – Minos is an excellent “host-based” solution – Not focus on the intention of the attacker – Focus on how their code can get in! l Minos + DACODA Under. Stand – But, NO simple & yet powerful “signature”! 01/04/2006 ecs 236 winter 2006 82
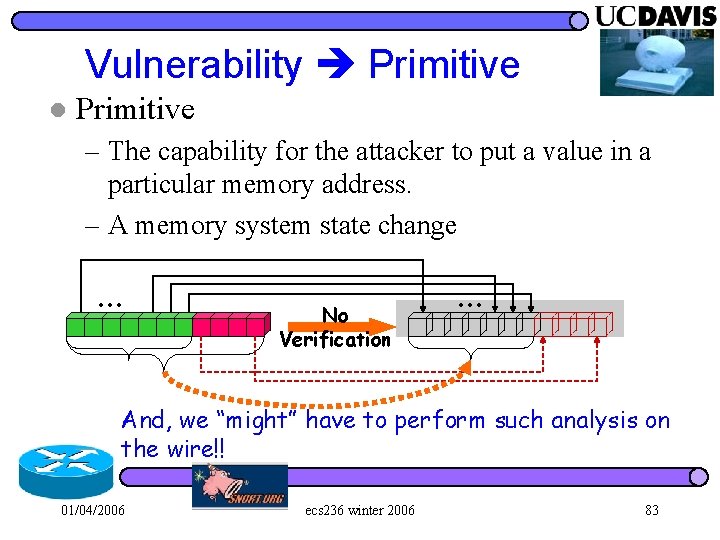
Vulnerability Primitive l Primitive – The capability for the attacker to put a value in a particular memory address. – A memory system state change … No Verification … And, we “might” have to perform such analysis on the wire!! 01/04/2006 ecs 236 winter 2006 83
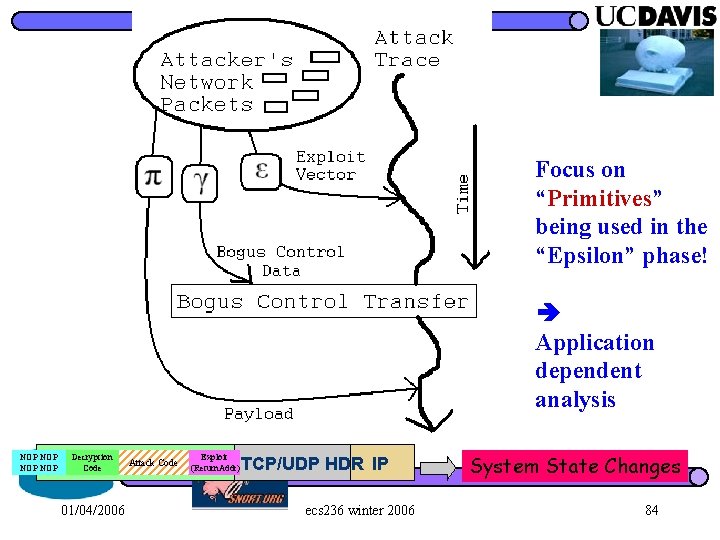
Focus on “Primitives” being used in the “Epsilon” phase! Application dependent analysis NOP NOP Decryption Exploit Code UPR. Code LYR. Attack PAYLOAD (Return. Addr) TCP/UDP HDR IP 01/04/2006 ecs 236 winter 2006 System State Changes 84
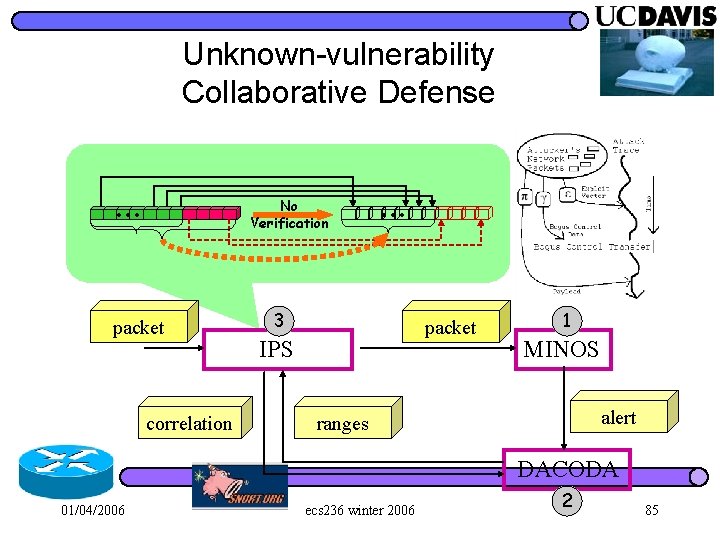
Unknown-vulnerability Collaborative Defense … No Verification packet correlation … 3 packet IPS 1 MINOS alert ranges DACODA 01/04/2006 ecs 236 winter 2006 2 85
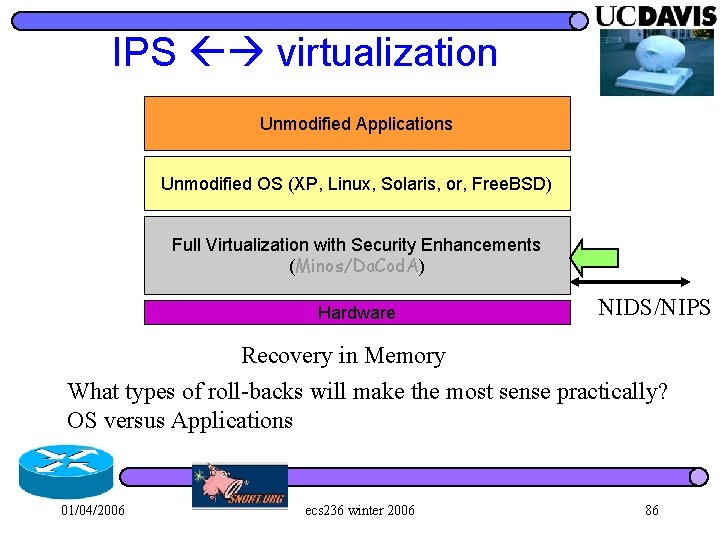
IPS virtualization Unmodified Applications Unmodified OS (XP, Linux, Solaris, or, Free. BSD) Full Virtualization with Security Enhancements (Minos/Da. Cod. A) Hardware NIDS/NIPS Recovery in Memory What types of roll-backs will make the most sense practically? OS versus Applications 01/04/2006 ecs 236 winter 2006 86
Recovery l VM level: Files – Virtual Hard Disk l File Recovery – OS kernel – #1: what will be the challenges in doing it in the VM level? – #2: how exactly to recover the most from an attack? 01/04/2006 ecs 236 winter 2006 87
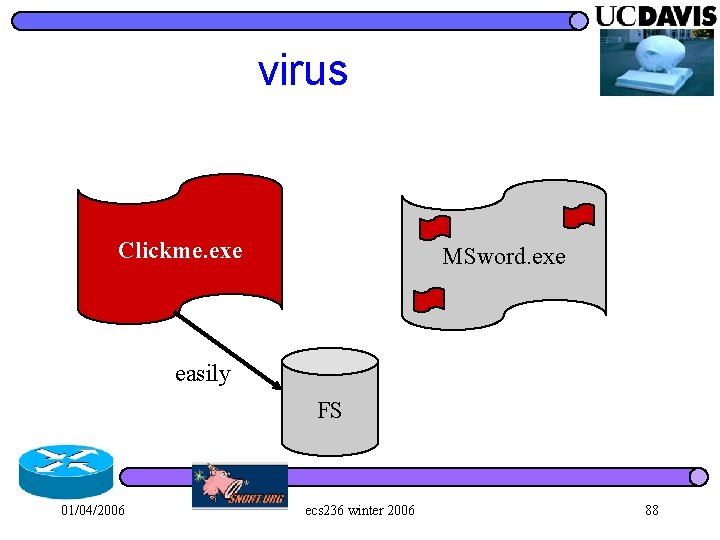
virus Clickme. exe MSword. exe easily FS 01/04/2006 ecs 236 winter 2006 88
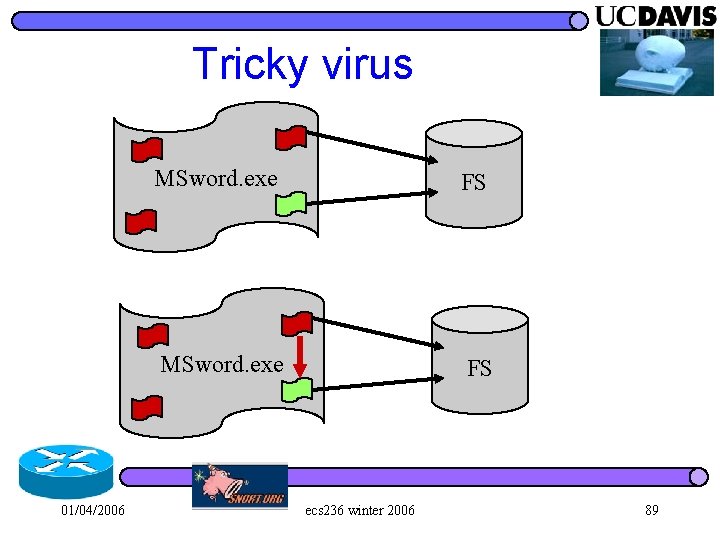
Tricky virus 01/04/2006 MSword. exe FS ecs 236 winter 2006 89
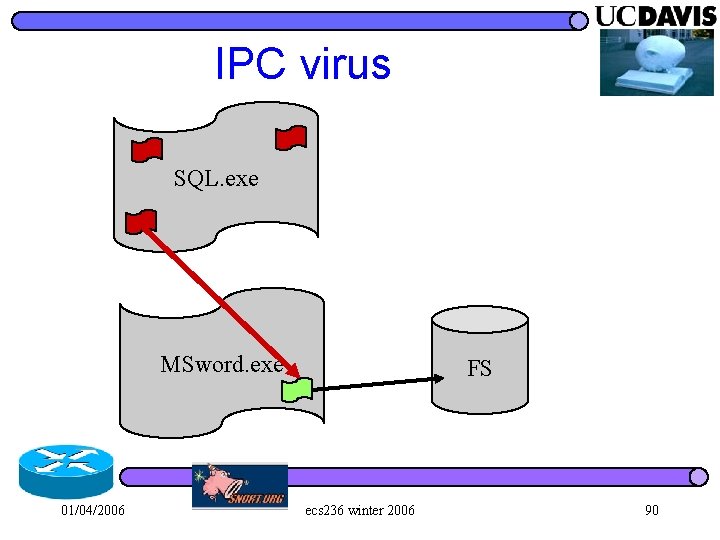
IPC virus SQL. exe MSword. exe 01/04/2006 FS ecs 236 winter 2006 90
Simple Solutions l I just remove the “bad effects” of the virus “pessimistically”. – I assume that, eventually, you know that this executable is a virus. – In the IPC case, if I know the relationship between the virus and the MSword, then I can also kill the MSword – contaminated applications. l Simple solutions similar/existing solutions… – niche doing it at the VM level. – Even impossible for OS. 01/04/2006 ecs 236 winter 2006 91
Hao Chen’s idea Why VM? VM can not be touched. l Implement “special things” in the OS kernel, but your VM will protect such that your “special things” can not be modified. l 01/04/2006 ecs 236 winter 2006 92
Well… (Felix) l l I don’t want to modify OS! I want to research on the limitations of what I can do or I cannot do in the VM layer. – Whether it makes sense to “understand” or “interpret” the semantic meaning of OS and applications? – Obviously, we don’t want to interpret everything in VM we want to have an abstraction sufficient to do whatever we want to do. 01/04/2006 ecs 236 winter 2006 93
For academic research. . I am not going to solve ALL the virus or worm-types of problems. l But, maybe it is good to focus on ONE particular type of virus on a particular application… l – E. g. , php related virus on w 32 and IIS+. 01/04/2006 ecs 236 winter 2006 94
PHP Viruses PHP/Caracula, 2001 l PHP/Feast, polymorphic virus l We should do a little bit google on PHPrelated viruses just to see whether it is a good target to start: l – Whether this is a challenging/hot area – Whethere are many instances that we can test http: //securityresponse. symantec. com/avcenter/venc/data/php. fe 01/04/2006 ecs 236 winter 2006 95
Links http: //www. openantivirus. org/projects. php 01/04/2006 ecs 236 winter 2006 96
Sober Virus http: //securityresponse. symantec. com/avcenter/venc/data/w 32. sober@mm. 01/04/2006 ecs 236 winter 2006 97
FS versus Memory l Minos memory, execution state – Control flow hijack l Virtual HD File recovery, transaction 01/04/2006 ecs 236 winter 2006 98
The Optimistic Approach PE assuming this is bad so I remove it. l OP assuming it is good but I will verify later. . l l Optimistic Recovery – Some works being done 10 years on OR. 01/04/2006 ecs 236 winter 2006 99
Cache Buffer versus DD l If we only look at VHDisk, we will miss the actions against the buffer cache… 01/04/2006 ecs 236 winter 2006 100
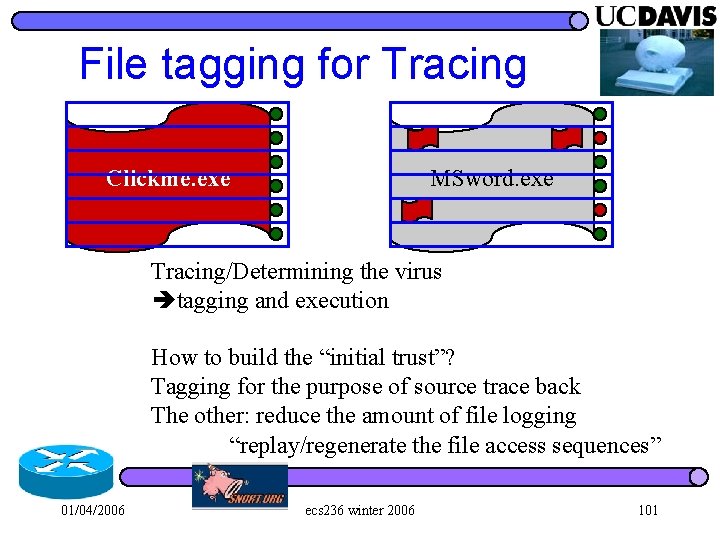
File tagging for Tracing Clickme. exe MSword. exe Tracing/Determining the virus tagging and execution How to build the “initial trust”? Tagging for the purpose of source trace back The other: reduce the amount of file logging “replay/regenerate the file access sequences” 01/04/2006 ecs 236 winter 2006 101
Purposes l Recovery – Virtual HD VM level l Tracing – I am not completely sure about the goals… l Identification – Exciting? ? 01/04/2006 ecs 236 winter 2006 102
Anti. Virus does two things l Signature and pattern matching – Clam. AV has 100 K+ signatures. l Virtual execution and interpretation – Some viruses won’t reveal their evilness unless you decompress/interpret some parts of that. 01/04/2006 ecs 236 winter 2006 103
Two definitions of Virus l A virus is a program that is able to infect other programs by modifying them to include a possibly evolved copy of itself. – Fred Cohen l A computer virus is a program that recursively and explicitly copies a possibly evolved version of itself. – Peter Szor 01/04/2006 ecs 236 winter 2006 104
In real applications… l I suspect… for some features MSword. exe 01/04/2006 ecs 236 winter 2006 105
CEF & MSIL l CEF (Common Executable File) – CEF might be the right way to do Virus… l MSIL (Microsoft Intermediate Language) 01/04/2006 ecs 236 winter 2006 106
Minos Recovery Minos on detecting a problem will stop the process. l Minos recovers to a “most recent” “safe state” and continuous to run. l 01/04/2006 ecs 236 winter 2006 107
- Slides: 107