ROCA Vulnerable RSA generation in cryptographic smartcards Workshop
ROCA: Vulnerable RSA generation in cryptographic smartcards Workshop on Attacks in Cryptography, Santa Barbara, 18. 8. 2018 Petr Švenda svenda@fi. muni. cz @rngsec Centre for Research on Cryptography and Security, Masaryk University Joint work with: Matúš Nemec, Marek Sýs, Dušan Klinec, Peter Sekan, Rudolf Kvašnovský, David Formánek, David Komárek and Vashek Matyáš https: //crocs. fi. muni. cz @CRo. CS_MUNI
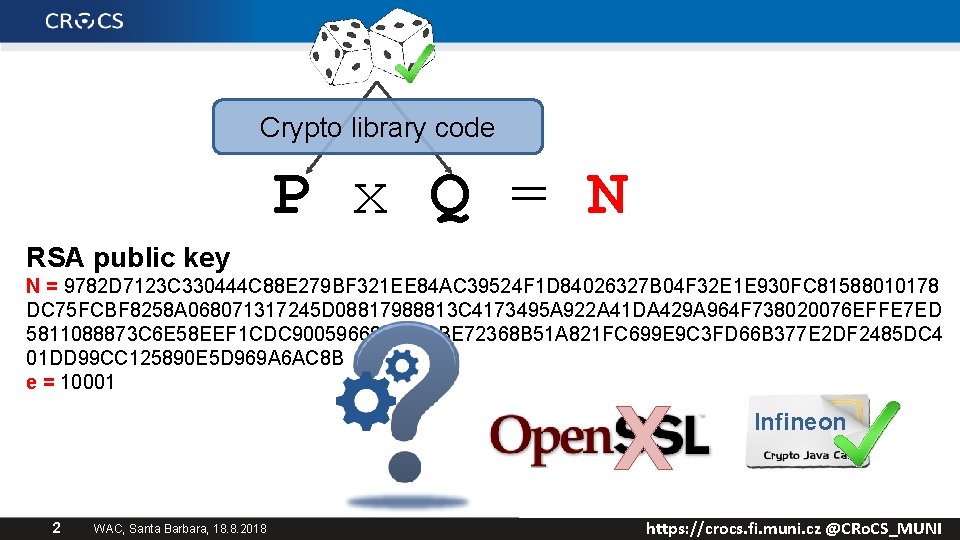
Crypto library code P x Q = N RSA public key N = 9782 D 7123 C 330444 C 88 E 279 BF 321 EE 84 AC 39524 F 1 D 84026327 B 04 F 32 E 1 E 930 FC 81588010178 DC 75 FCBF 8258 A 068071317245 D 08817988813 C 4173495 A 922 A 41 DA 429 A 964 F 738020076 EFFE 7 ED 5811088873 C 6 E 58 EEF 1 CDC 900596681 F 490 BE 72368 B 51 A 821 FC 699 E 9 C 3 FD 66 B 377 E 2 DF 2485 DC 4 01 DD 99 CC 125890 E 5 D 969 A 6 AC 8 B e = 10001 X 2 WAC, Santa Barbara, 18. 8. 2018 Infineon https: //crocs. fi. muni. cz @CRo. CS_MUNI
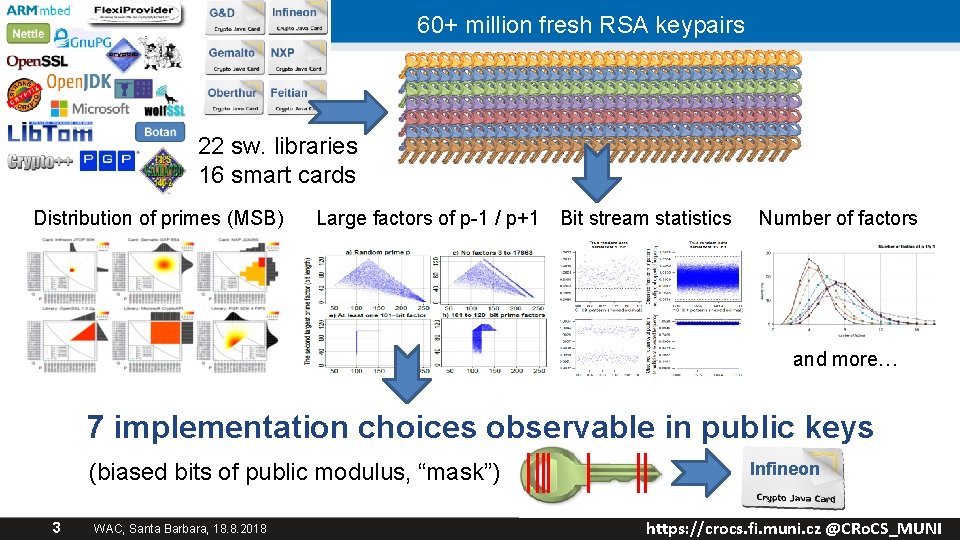
60+ million fresh RSA keypairs 22 sw. libraries 16 smart cards Distribution of primes (MSB) Large factors of p-1 / p+1 Bit stream statistics Number of factors and more… 7 implementation choices observable in public keys (biased bits of public modulus, “mask”) 3 WAC, Santa Barbara, 18. 8. 2018 Infineon https: //crocs. fi. muni. cz @CRo. CS_MUNI
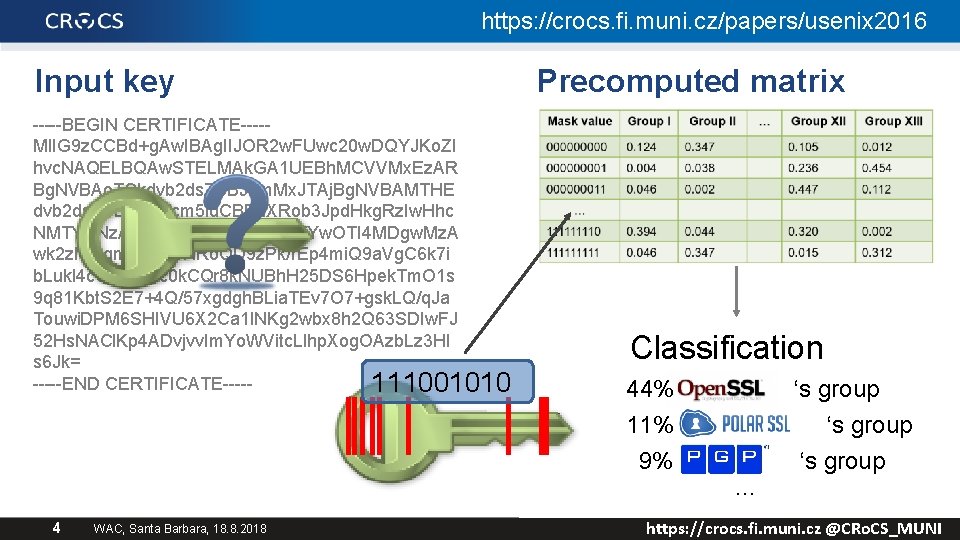
https: //crocs. fi. muni. cz/papers/usenix 2016 Input key -----BEGIN CERTIFICATE----MIIG 9 z. CCBd+g. Aw. IBAg. IIJOR 2 w. FUwc 20 w. DQYJKo. ZI hvc. NAQELBQAw. STELMAk. GA 1 UEBh. MCVVMx. Ez. AR Bg. NVBAo. TCkdvb 2 ds. ZSBJbm. Mx. JTAj. Bg. NVBAMTHE dvb 2 ds. ZSBJbn. Rlcm 5 ld. CBBd. XRob 3 Jpd. Hkg. Rz. Iw. Hhc NMTYw. Nz. A 2 MDgx. Nz. Qz. Whc. NMTYw. OTI 4 MDgw. Mz. A wk 2 zl. QSqmq. HS 14 NRo. QD 9 z. Pk/r. Ep 4 mi. Q 9 a. Vg. C 6 k 7 i b. Lukl 4 c. Gi 5 my. Pc 0 k. CQr 8 k. NUBh. H 25 DS 6 Hpek. Tm. O 1 s 9 q 81 Kbt. S 2 E 7+4 Q/57 xgdgh. BLia. TEv 7 O 7+gsk. LQ/q. Ja Touwi. DPM 6 SHIVU 6 X 2 Ca 1 l. NKg 2 wbx 8 h 2 Q 63 SDIw. FJ 52 Hs. NACl. Kp 4 ADvjvv. Im. Yo. WVitc. Llhp. Xog. OAzb. Lz 3 HI s 6 Jk= -----END CERTIFICATE----111001010 4 WAC, Santa Barbara, 18. 8. 2018 Precomputed matrix Classification 44% ‘s group 11% ‘s group 9% ‘s group … https: //crocs. fi. muni. cz @CRo. CS_MUNI
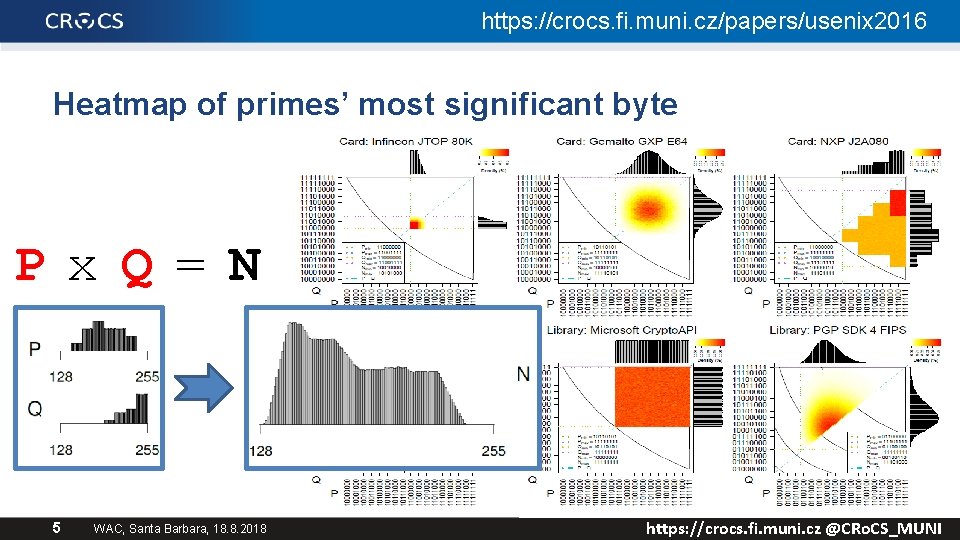
https: //crocs. fi. muni. cz/papers/usenix 2016 Heatmap of primes’ most significant byte P x Q = N 5 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
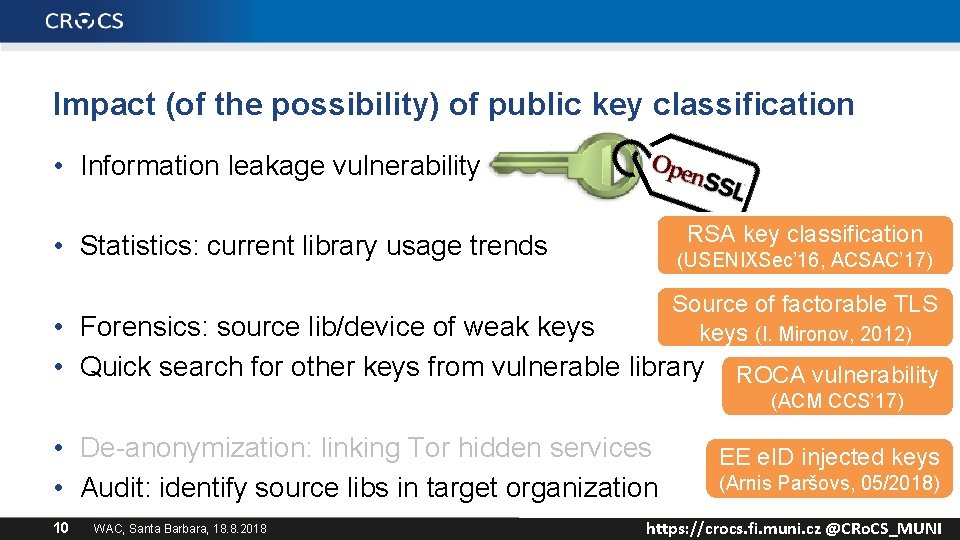
Impact (of the possibility) of public key classification • Information leakage vulnerability RSA key classification • Statistics: current library usage trends (USENIXSec’ 16, ACSAC’ 17) Source of factorable TLS keys (I. Mironov, 2012) • Forensics: source lib/device of weak keys • Quick search for other keys from vulnerable library ROCA vulnerability (ACM CCS’ 17) • De-anonymization: linking Tor hidden services • Audit: identify source libs in target organization 10 WAC, Santa Barbara, 18. 8. 2018 EE e. ID injected keys (Arnis Paršovs, 05/2018) https: //crocs. fi. muni. cz @CRo. CS_MUNI
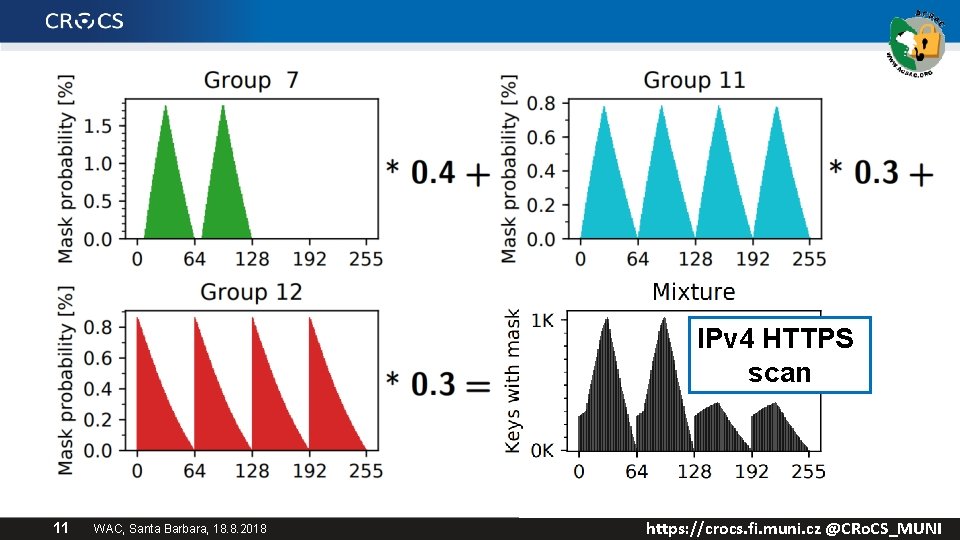
IPv 4 HTTPS scan 11 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
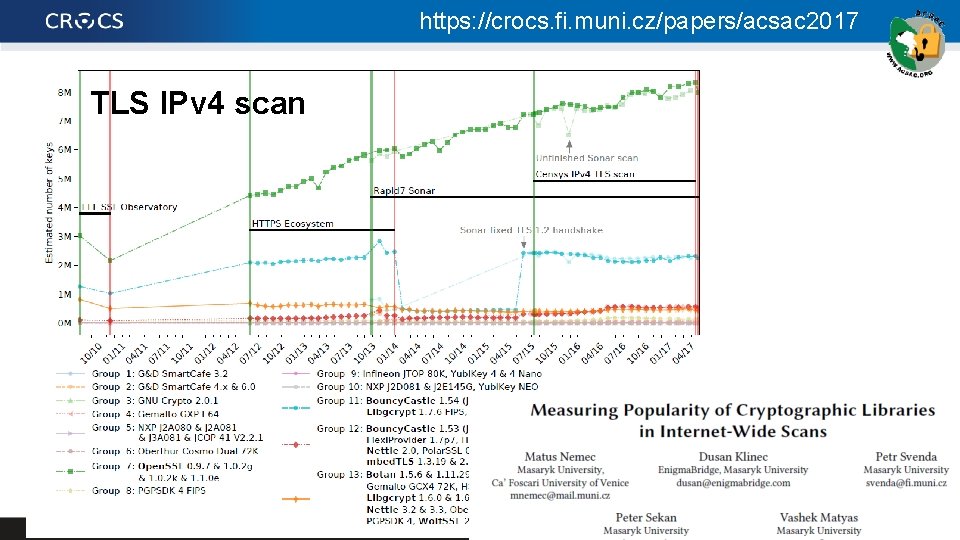
https: //crocs. fi. muni. cz/papers/acsac 2017 TLS IPv 4 scan 12 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
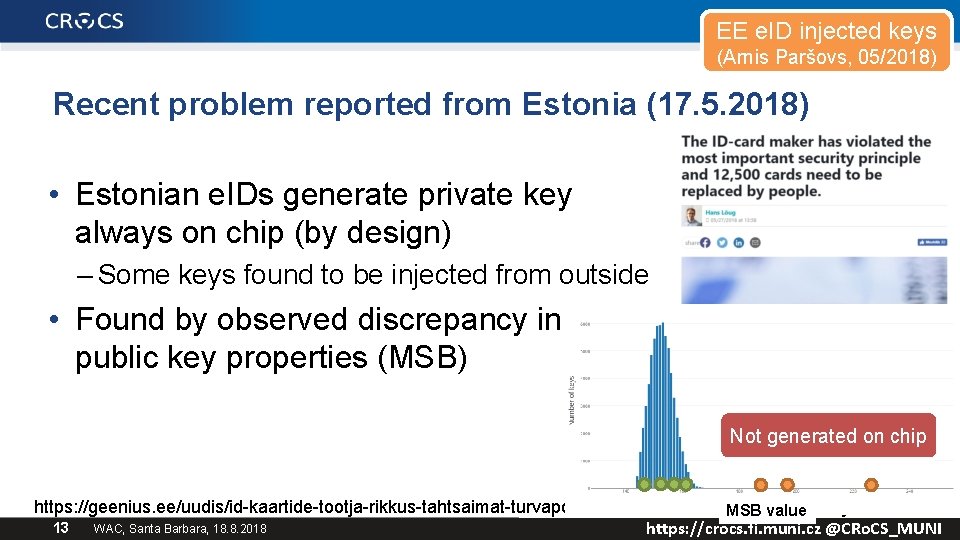
EE e. ID injected keys (Arnis Paršovs, 05/2018) Recent problem reported from Estonia (17. 5. 2018) • Estonian e. IDs generate private key always on chip (by design) – Some keys found to be injected from outside • Found by observed discrepancy in RSA public key properties (MSB) Not generated on chip https: //geenius. ee/uudis/id-kaartide-tootja-rikkus-tahtsaimat-turvapohimotet-12 -500 -tuleb-inimestel-valja-vahetada/ MSB value 13 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
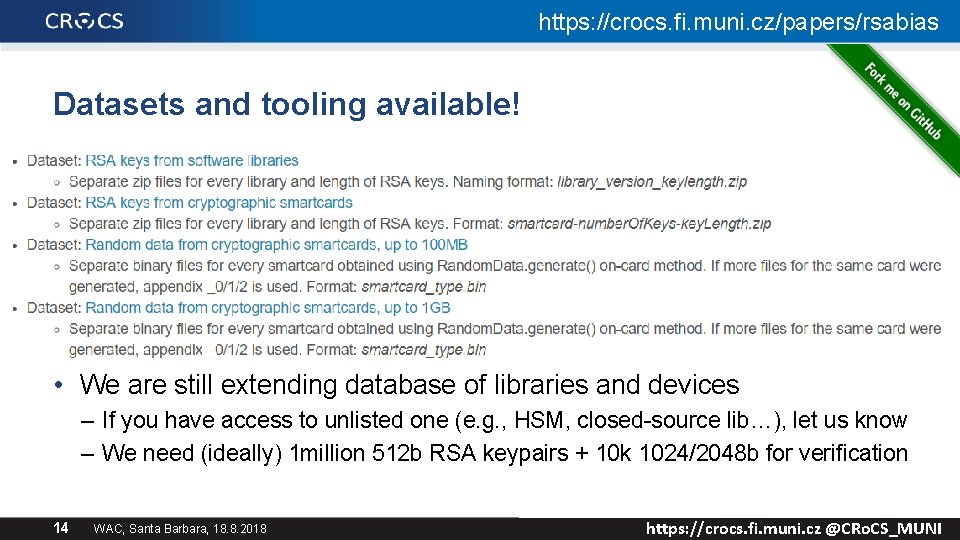
https: //crocs. fi. muni. cz/papers/rsabias Datasets and tooling available! • We are still extending database of libraries and devices – If you have access to unlisted one (e. g. , HSM, closed-source lib…), let us know – We need (ideally) 1 million 512 b RSA keypairs + 10 k 1024/2048 b for verification 14 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
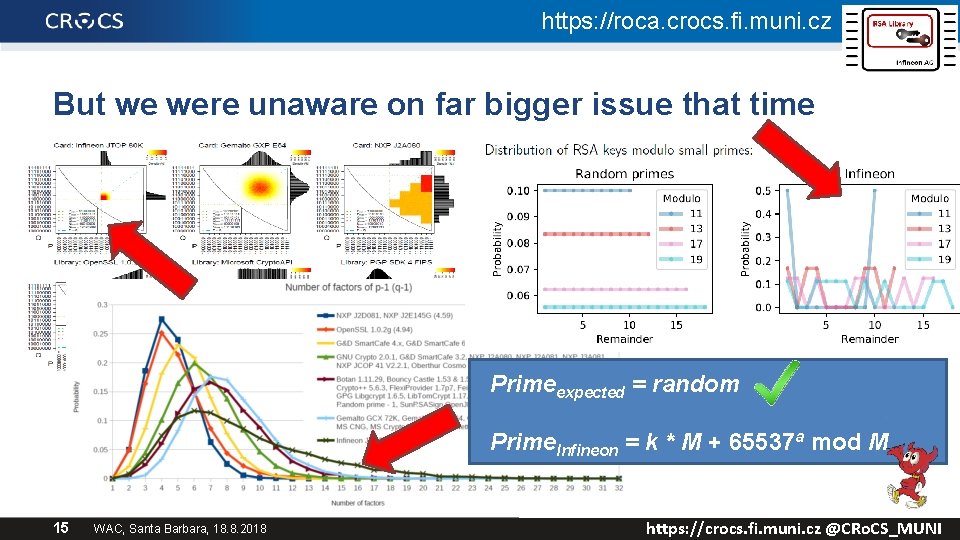
https: //roca. crocs. fi. muni. cz But we were unaware on far bigger issue that time Primeexpected = random Prime. Infineon = k * M + 65537 a mod M 15 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
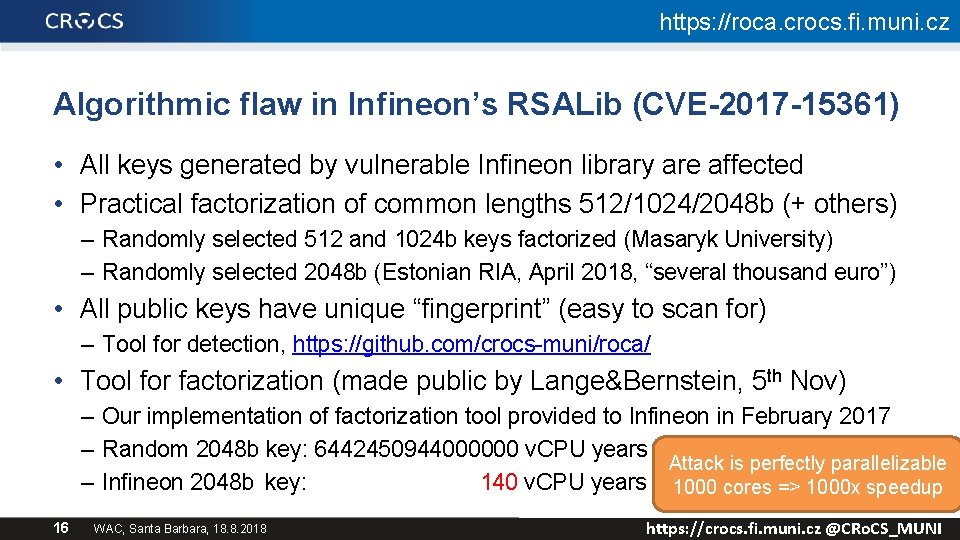
https: //roca. crocs. fi. muni. cz Algorithmic flaw in Infineon’s RSALib (CVE-2017 -15361) • All keys generated by vulnerable Infineon library are affected • Practical factorization of common lengths 512/1024/2048 b (+ others) – Randomly selected 512 and 1024 b keys factorized (Masaryk University) – Randomly selected 2048 b (Estonian RIA, April 2018, “several thousand euro”) • All public keys have unique “fingerprint” (easy to scan for) – Tool for detection, https: //github. com/crocs-muni/roca/ • Tool for factorization (made public by Lange&Bernstein, 5 th Nov) – Our implementation of factorization tool provided to Infineon in February 2017 – Random 2048 b key: 6442450944000000 v. CPU years Attack is perfectly parallelizable – Infineon 2048 b key: 140 v. CPU years 1000 cores => 1000 x speedup 16 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
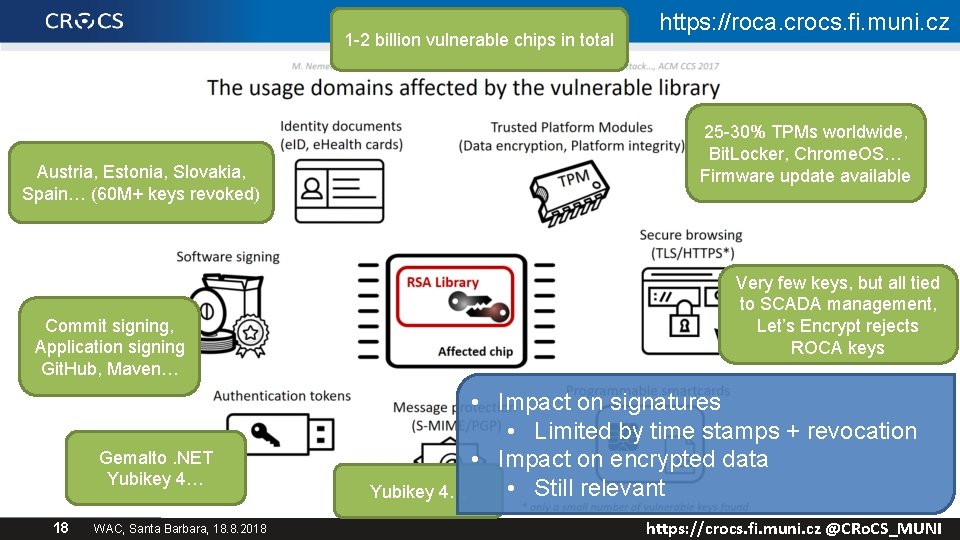
1 -2 billion vulnerable chips in total Austria, Estonia, Slovakia, Spain… (60 M+ keys revoked) Commit signing, Application signing Git. Hub, Maven… Gemalto. NET Yubikey 4… 18 WAC, Santa Barbara, 18. 8. 2018 https: //roca. crocs. fi. muni. cz 25 -30% TPMs worldwide, Bit. Locker, Chrome. OS… Firmware update available Very few keys, but all tied to SCADA management, Let’s Encrypt rejects ROCA keys • Impact on signatures • Limited by time stamps + revocation • Impact on encrypted data • Still relevant Yubikey 4… https: //crocs. fi. muni. cz @CRo. CS_MUNI
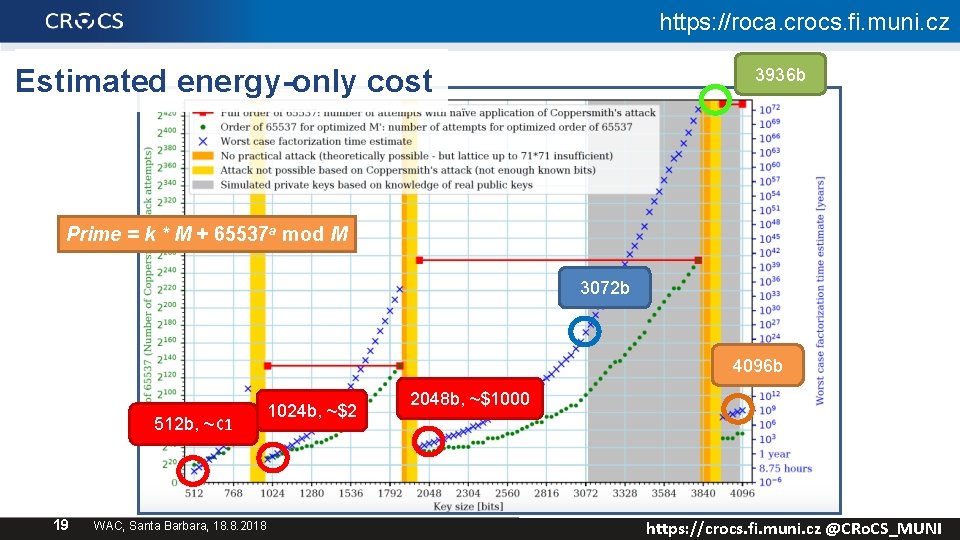
https: //roca. crocs. fi. muni. cz Estimated energy-only cost 3936 b Prime = k * M + 65537 a mod M 3072 b 4096 b 512 b, ~¢ 1 19 WAC, Santa Barbara, 18. 8. 2018 1024 b, ~$2 2048 b, ~$1000 https: //crocs. fi. muni. cz @CRo. CS_MUNI
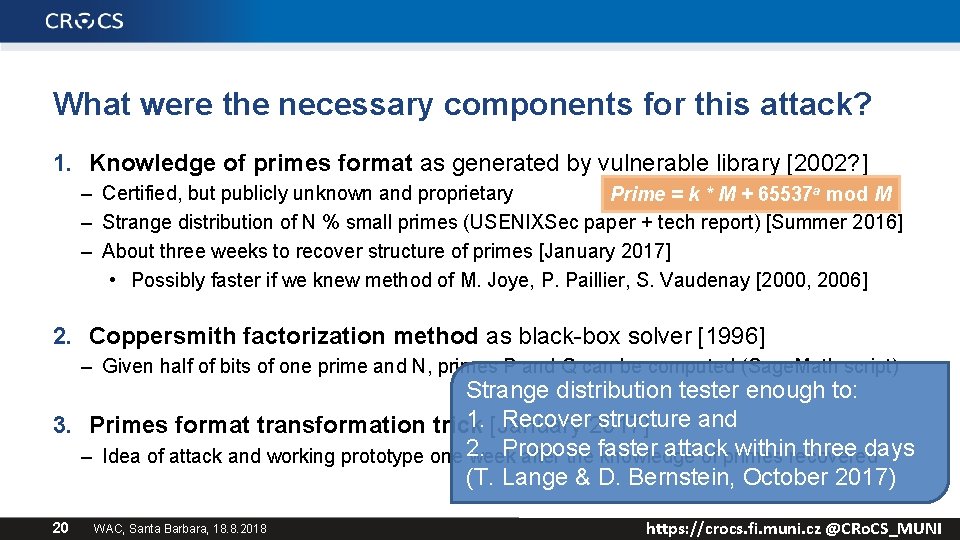
What were the necessary components for this attack? 1. Knowledge of primes format as generated by vulnerable library [2002? ] – Certified, but publicly unknown and proprietary Prime = k * M + 65537 a mod M – Strange distribution of N % small primes (USENIXSec paper + tech report) [Summer 2016] – About three weeks to recover structure of primes [January 2017] • Possibly faster if we knew method of M. Joye, P. Paillier, S. Vaudenay [2000, 2006] 2. Coppersmith factorization method as black-box solver [1996] – Given half of bits of one prime and N, primes P and Q can be computed (Sage. Math script) Strange distribution tester enough to: 1. [January 2017] Recover structure and 3. Primes format transformation trick 2. Propose faster attack within three days – Idea of attack and working prototype one week after the knowledge of primes recovered (T. Lange & D. Bernstein, October 2017) 20 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI

21 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
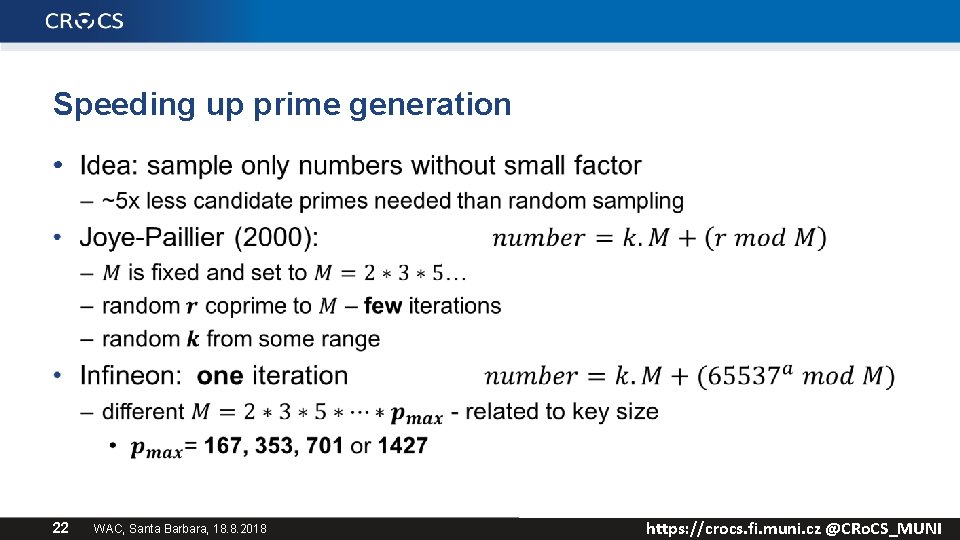
Speeding up prime generation • 22 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
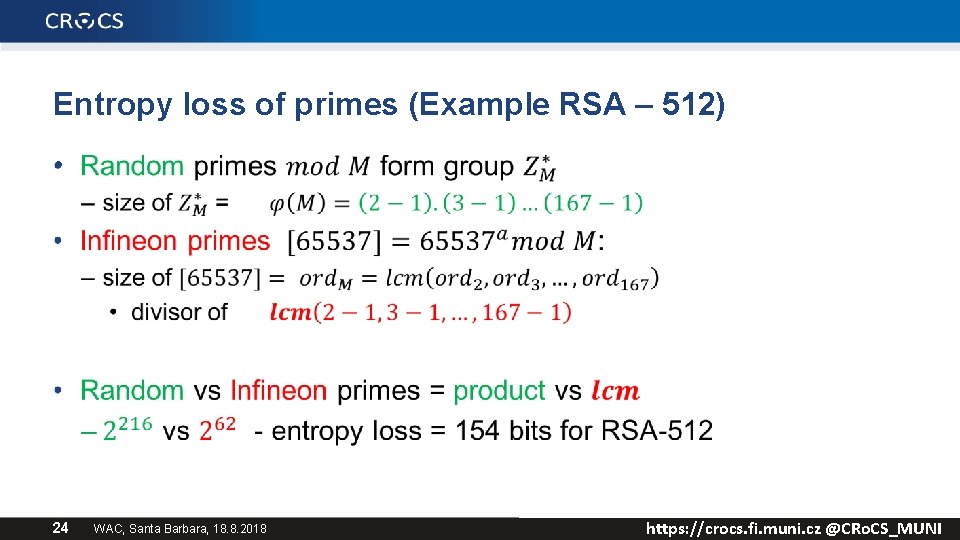
Entropy loss of primes (Example RSA – 512) • 24 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
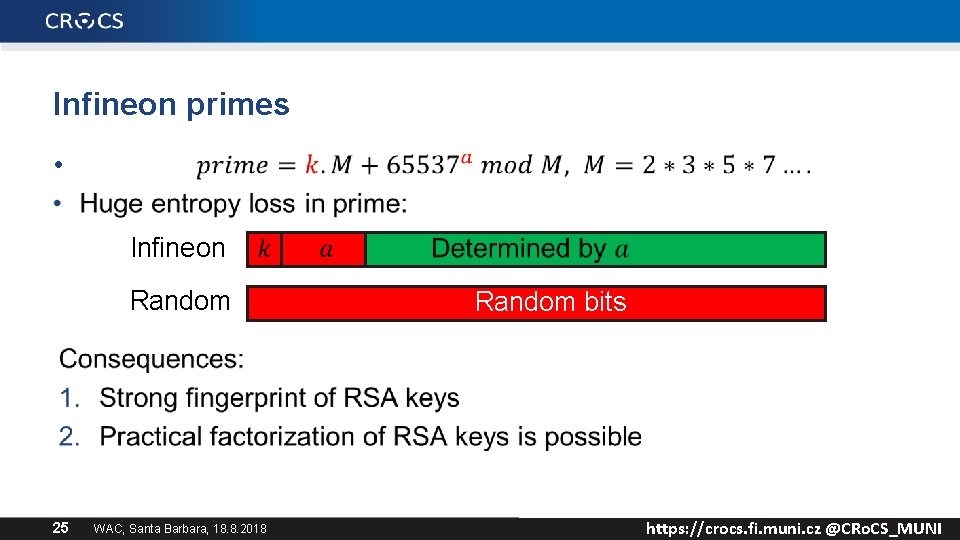
Infineon primes • Infineon Random 25 WAC, Santa Barbara, 18. 8. 2018 Random bits https: //crocs. fi. muni. cz @CRo. CS_MUNI
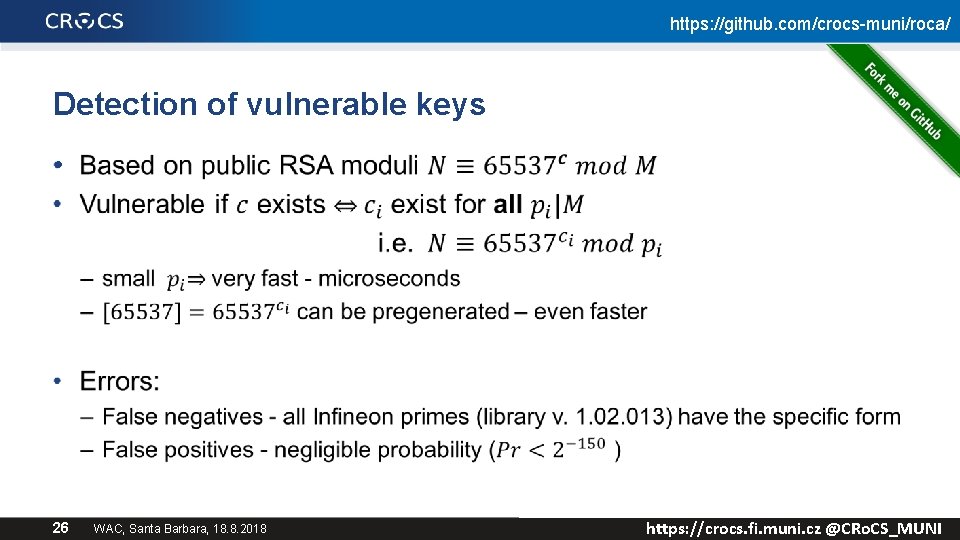
https: //github. com/crocs-muni/roca/ Detection of vulnerable keys • 26 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
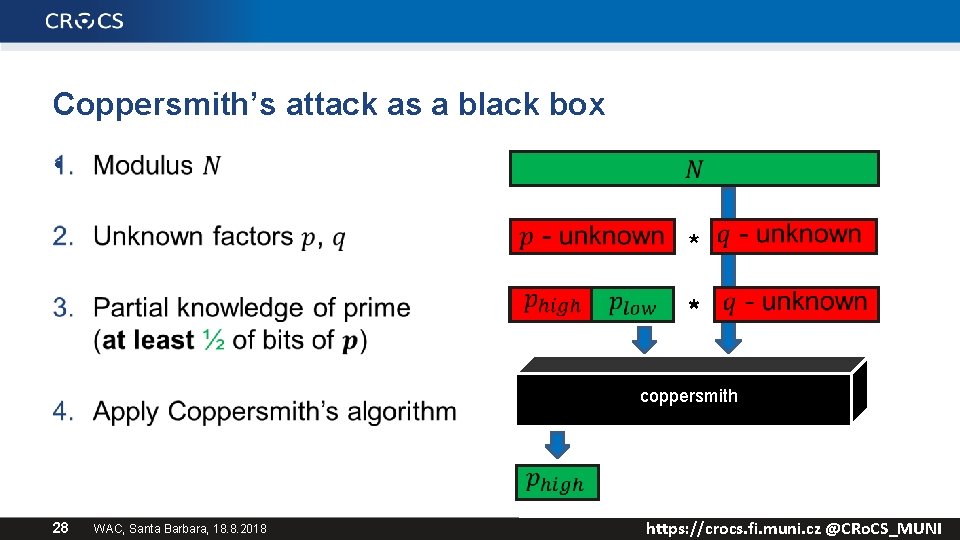
Coppersmith’s attack as a black box • * * coppersmith 28 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
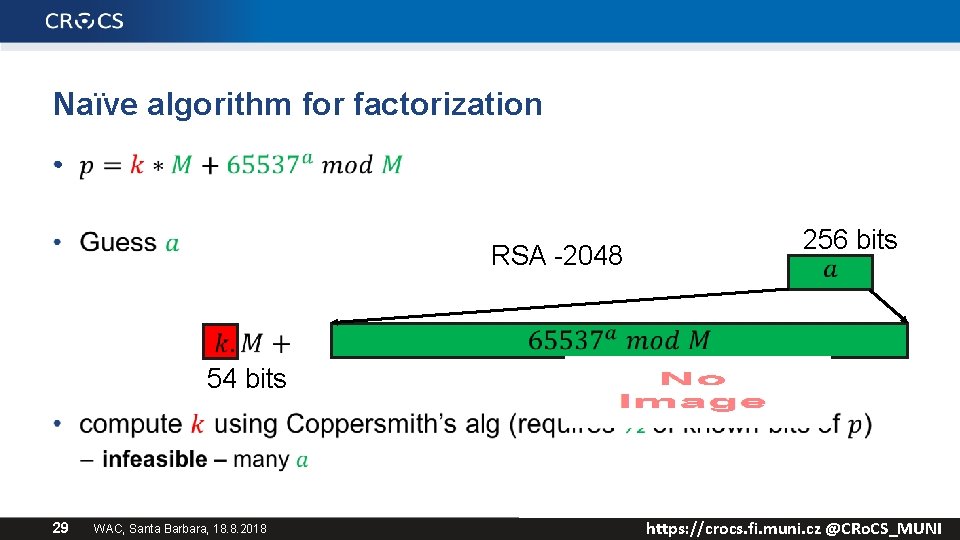
Naïve algorithm for factorization • RSA -2048 54 bits 29 WAC, Santa Barbara, 18. 8. 2018 256 bits https: //crocs. fi. muni. cz @CRo. CS_MUNI
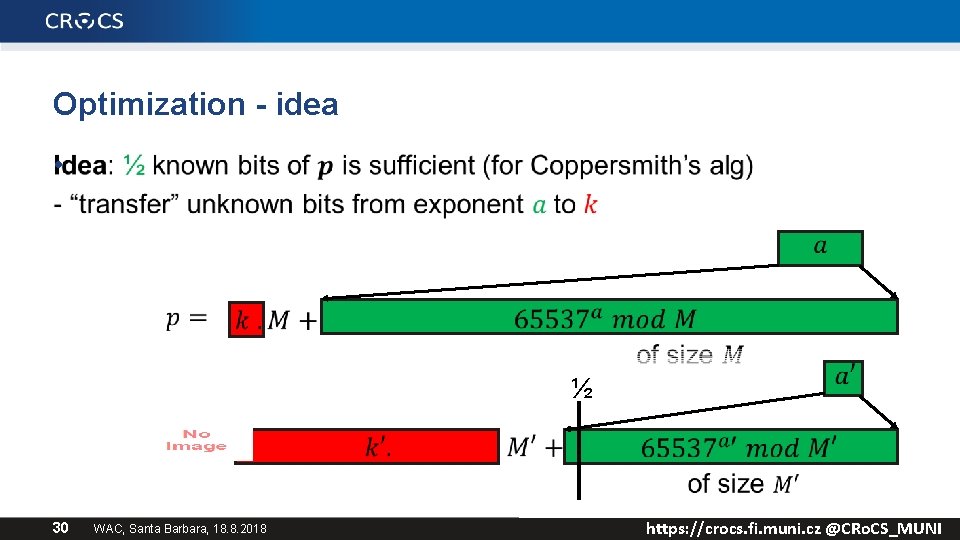
Optimization - idea • ½ 30 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
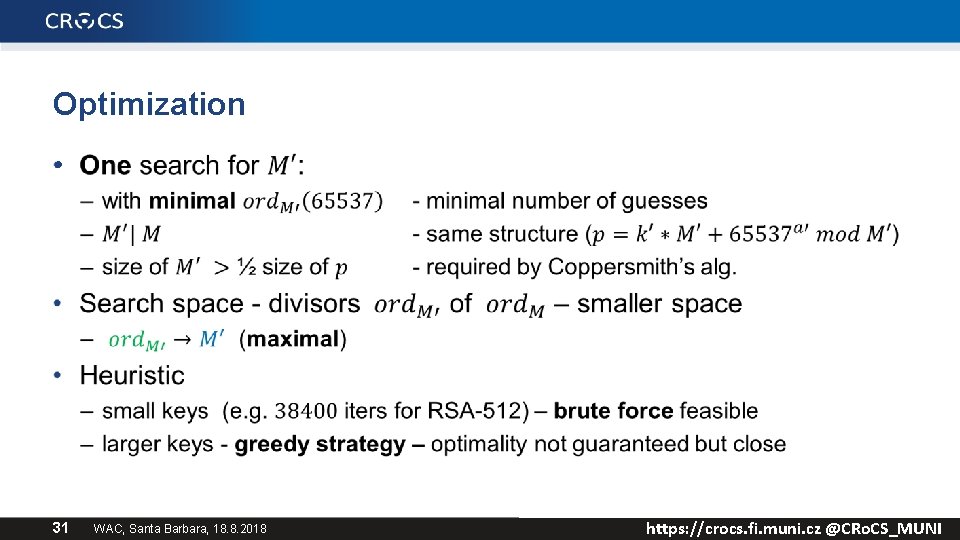
Optimization • 31 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
ROOM FOR IMPROVEMENTS 32 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
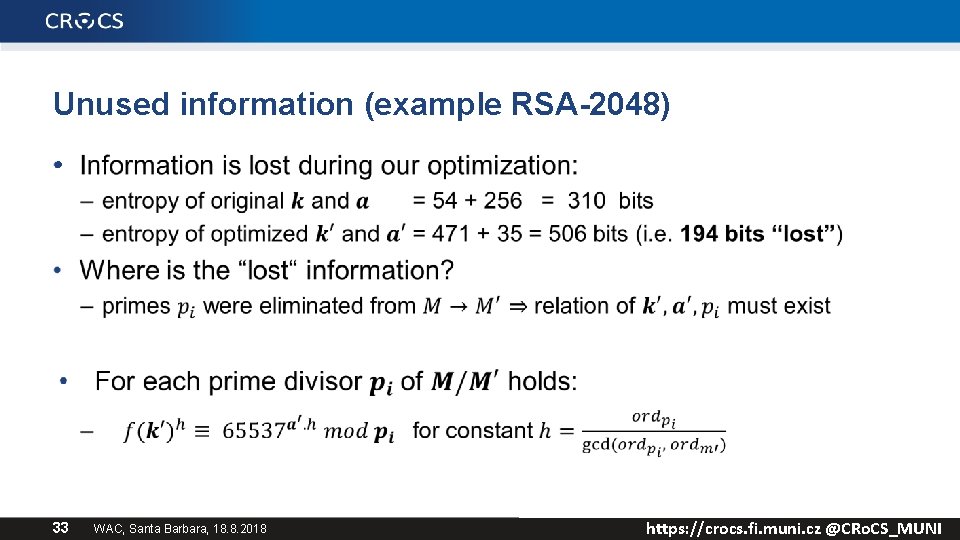
Unused information (example RSA-2048) • 33 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
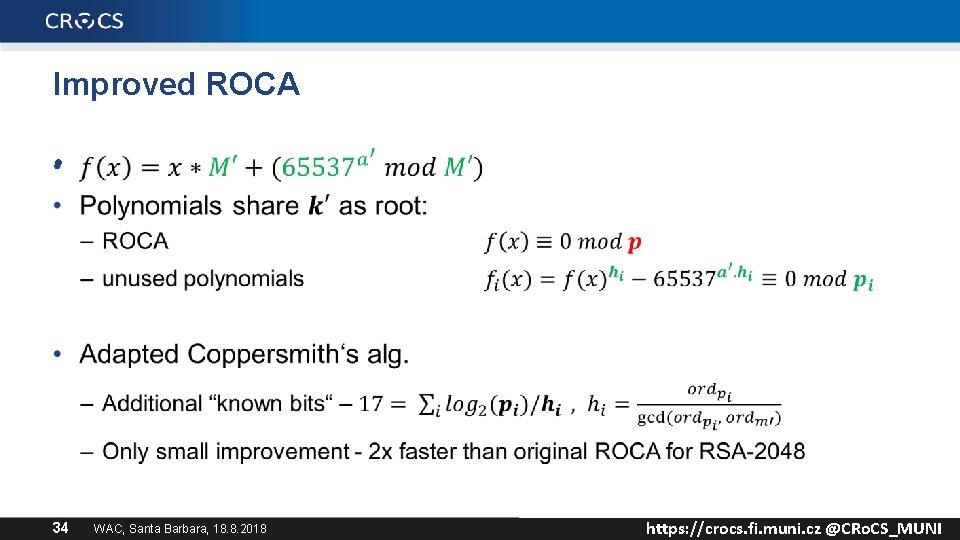
Improved ROCA • 34 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
https: //roca. crocs. fi. muni. cz Take-homes and conclusions • Even small bias hints about potential weakness • RSA public keys can be attributed to origin library (prime selection algorithm) – Datasets and tools available, systematic database build • Don’t trust black-box designs and implementations (ROCA) – Secret design => delayed discovery of flaws => increased impacts – More transparency required also for the critical hardware • Possible improvements of the attack? 35 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
Links • Our paper: The Return of Coppersmith's Attack: Practical Factorization of Widely Used RSA Moduli https: //dl. acm. org/citation. cfm? id=3133969 • Our page with some info and detection tool: https: //crocs. fi. muni. cz/papers/rsa_ccs 17 • Joye, Pailier: Fast Generation of Prime Numbers on Portable Devices https: //link. springer. com/chapter/10. 1007/11894063_13 • Svenda et. al: The Million-Key Question—Investigating the Origins of RSA Public Keys https: //www. usenix. org/node/197198 – Technical report https: //crocs. fi. muni. cz/papers/usenixsec 16 Questions 36 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
37 WAC, Santa Barbara, 18. 8. 2018 https: //crocs. fi. muni. cz @CRo. CS_MUNI
- Slides: 30