Cryptographic Tools cryptographic capabilities ability to conceal the
Cryptographic Tools • cryptographic capabilities – ability to conceal the message, verify the contents, id of sender etc • Cryptographic tools - bring the functions of cryptography to the world of information systems. • • • Public key infrastructure Digital Signatures Digital Certificates Hybrid cryptography systems Steganography
Public key Infrastructure (PKI) • based on public-key cryptosystems and include digital certificates and certificate authorities (CAs). • digital certificates (allow the PKI components and their users ) - to validate keys and identify key owners. • protection of information assets by making verifiable digital certificates • allows the applications to implement several key characteristics of information security and integrate these characteristics
PKI • Characteristics- for business process • Authentication: Individuals, organizations, and Web servers validate the identity of each party in an Internet transaction. • Integrity: Content signed by the certificate – not altered while in transit from host to host or server to client. • Privacy: Information protected from interception. • Authorization: The validated identity of users and programs enable authorization rules of a transaction - reduces overhead and allows for more control of access privileges for specific transactions. • Nonrepudiation: Customers or partners - accountable for transactions, such as online purchases, which they cannot later dispute.
PKI • PKI solution protects - transmission and reception of secure information • A certificate authority (CA), - issues, manages, authenticates, signs, and revokes users’ digital certificates. -certificates contain - user name, public key, and other identifying information. • A registration authority (RA) - handles certification functions – verifying registration information, generating end-user keys, revoking certificates, and validating user certificates, in collaboration with the CA. • Certificate directories - central locations for certificate storage , provide a single access point for administration and distribution.
PKI • Management protocols - organize and manage communications among CAs, RAs, and end users • Management protocols - includes the functions and procedures for setting up new users, issuing keys, recovering keys, updating keys, revoking keys, and enabling the transfer of certificates and status information among the parties involved in the PKI’s area of authority. • Policies and procedures - assist an organization in the application and management of certificates, in the formalization of legal liabilities and limitations, and in actual business use.

PKI • implementations of PKI include systems that issue digital certificates to users and servers, directory enrolment, key issuing systems, tools for managing key issue, verification and return of certificates. • CA performs many housekeeping activities regarding the use of keys and certificates that are issued and used in its zone of authority • CA can issue new or replacement keys, track issued keys, provide a directory of public-key values for all known users, and perform other management activities. • When a private key is compromised or the user loses the privilege of using keys in the area of authority, CA can revoke the user’s keys. • CA periodically distributes a certificate revocation list (CRL) to all users. • specific applications can make a real-time request to the CA to verify any user against the current CRL.

PKI • A central system - operated by a CA or RA - generate cryptographically strong keys and provide services for users such as private-key backup, key recovery, and key revocation • strength of a cryptosystem relies on - raw strength of its key’s complexity and the overall quality of its key management security. • PKI solutions - limiting access and possible exposure of the private keys. • mechanisms include password protection, smart cards, hardware tokens, and other hardware-based key storage devices that are memory-capable, like flash memory or PC memory cards
DIGITAL SIGNATURES • encrypted messages that can be mathematically proven as authentic. • Asymmetric encryption creates DS • sender’s private key – encryption, sender’s public key – decryption, successful decryption – verification for message sent by sender, no refute – nonrepudiation • Principle of cryptography - authentication mechanism collectively - DS

Digital Signature • Management of DS –Web browser • Created by DSS(Digital Signature Standard) • For encryption and non repudiation -DSS algorithms in conjunction with the sender’s public and private keys, the receiver’s public key, and the Secure Hash Standard • message digest using hash algorithm, input into the digital signature algorithm along with a random number to generate the digital signature. • digital signature function – depends on the sender’s private key and other information provided by the CA.
Digital Certificates • an electronic document or container file - a key value and information about the entity controlling the key. • issued and certified by a third party – CA • digital signature attached to the certificate - certifies the file’s origin and integrity. • verification process – during download or update software via the Internet. • authenticate the cryptographic key that is embedded in the certificate. • enable diligent users to verify the authenticity of any organization’s certificates.
Digital Certificates • Different client-server applications - different types of digital certificates to accomplish their assigned functions, as follows: • The CA application suite issues and uses certificates (keys) that identify and establish a trust relationship with a CA to determine what additional certificates can be authenticated. • Secure/Multipurpose Internet Mail Extension (S/MIME) certificates for signing and encrypting e-mail applications and forms. • object-signing certificates to identify signers of object oriented code and scripts for development applications • Secure Sockets Layer (SSL) certificates to authenticate servers via the SSL protocol in order to establish an encrypted SSL session - Web servers and Web application servers. • client SSL certificates to authenticate users, sign forms, and participate in single sign-on solutions via SSL for Web clients.
Digital certificates • 2 popular certificate types – PGP and X. 509 v 3 • ITU-T recommendation- x. 509 v 3 • directory service - database of information (repository) about a group of users holding X. 509 v 3 certificates. • Certificates bind a distinguished name (DN)identifies a certificate entity, to a user’s public key. • Signed certificate - placed in the directory by the CA for retrieval and verification by the user’s associated public key. • does not specify an encryption algorithm (RSA, with its hashed digital signature)

Hybrid Cryptography Systems Symmetric and asymmetric encryption most common hybrid system - Diffie-Hellman key exchange uses asymmetric encryption to exchange session keys. limited-use symmetric keys that allow two entities to conduct quick, efficient, secure communications based on symmetric encryption • More efficient than asymmetric encryption for sending messages. • •
Diffie-Hellman Key Exchange • Secure key exchange between two users • Depends on the effectiveness on the difficulty of computing discrete logarithms • Developed by Whitfield Diffie and Martin Hellman in 1976

Key exchange between Alice & Bob • Agree on 2 numbers, prime number q and an integer α that is the primitive root of q • Alice chooses a large random number XA<q, and Calculates YA = αXA mod q • Sends YA, α and q to Bob. • Bob chooses a large random number XB<q, and Calculates YB = αXB mod q • Sends YB to Alice.
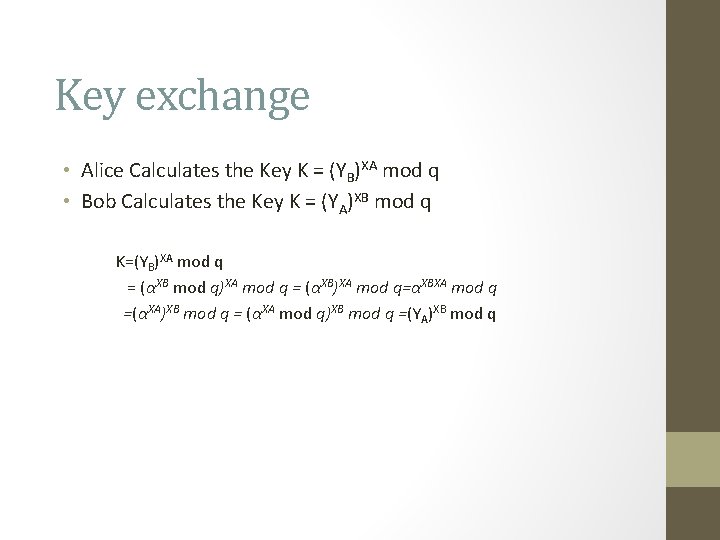
Key exchange • Alice Calculates the Key K = (YB)XA mod q • Bob Calculates the Key K = (YA)XB mod q K=(YB)XA mod q = (αXB mod q)XA mod q = (αXB)XA mod q=αXBXA mod q =(αXA)XB mod q = (αXA mod q)XB mod q =(YA)XB mod q

Example • • • Prime number q=97, primitive root α=5 A and B select XA =36 and XB =58 respectively. Public key YA = 536 =50 mod 97 Public key YB = 558=44 mod 97 Common Secret key § K = (YB)XA mod 97=4436 =75 mod 97 § K = (YA)XB mod 97=5058 =75 mod 97 • From {50, 44}, an attacker cannot easily compute 75.
The Key • • Only Alice and Bob know k Good for only one session Used if there is a need for symmetric key No authentication
Steganography • the art of secret writing—derived from the Greek words steganos, meaning “covered, ” and graphein, meaning “to write. ” • The Greek historian Herodotus whose fellow greek- one of the first steganographers -writing a message on the wood beneath a wax writing tablet • technically not a form of cryptography • another way of protecting the confidentiality of information in transit. • modern version of steganography – hiding information within files that contain digital pictures or other images.
Steganography • an alternative to encryption • hides existence of message • • • subset of letters/words in a longer message Invisible ink Character marking Pin punctures Typewriter correction ribbon hiding in LSB in graphic image or sound file • has drawbacks • high overhead to hide relatively few info bits

Steganography Example • • • Image storage – RGB- each colour- 8 bit value One bit change – not visible to normal eye, Each color image – 3 colors x 8 bits=24 bits picture from a digital camera or a computer program - the number of horizontal and vertical pixels captured and recorded - the image’s resolution. for example, if 1024 horizontal pixels and 768 vertical pixels are captured, the image has 1024 768 resolution and has 786, 432 pixels, or three-quarters of a megapixel. Image=1024 x 768 pixels contains 786, 432 groups of 24 bits to represent the red, green, and blue data. The raw image size can be calculated as 1024 768 24, or 5. 66 megabytes. T There are plenty of bits in this picture data file in which to hide a secret message. one bit of payload per colour (or three bits per pixel for all 786, 432 pixels, able to store 236 kilobytes of hidden data within the uncompressed image.

Steganography Example
Steganography Example
Steganography • Messages can also be hidden in computer files that do not hold images • data can be placed where software ignores it and people almost never look. • Some applications can hide messages in. bmp, . wav, . mp 3, and. au files, in otherwise unused storage space on CDs and DVDs. • Another approach - to hide a message in a text or document file and store the payload in what appears to be unused whitespace.
Protocols for Secure Communications Securing Internet Communication with S-HTTP and SSL • Secure Hypertext Transfer Protocol and Secure Socket Layer • SSL - Heartbleed bug - buffer overread error - allow an attacker to bypass some of the controls that protect sensitive information- encryption keys, passwords, or account numbers. • Open. SSL tool - to implement Secure Sockets Layer/Transport Layer Security (SSL/TLS) • Open. SSL tool is widely used for Internet sites around the world.
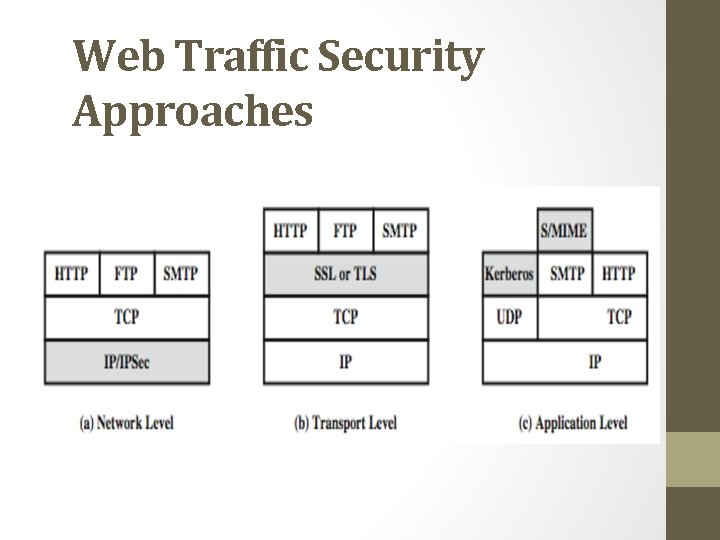
Web Traffic Security Approaches

SSL (Secure Socket Layer) transport layer security service originally developed by Netscape version 3 designed with public input subsequently became Internet standard known as TLS (Transport Layer Security) • uses TCP to provide a reliable end-to-end service • SSL has two layers of protocols • •
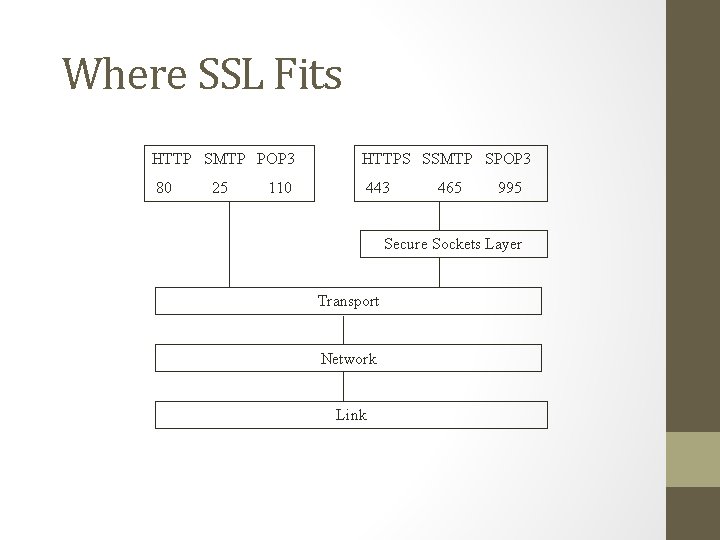
Where SSL Fits HTTP SMTP POP 3 HTTPS SSMTP SPOP 3 80 443 25 110 465 995 Secure Sockets Layer Transport Network Link
Uses Public Key Scheme • Each client-server pair uses • 2 public keys • one for client (browser) • created when browser is installed on client machine • one for server (http server) • created when server is installed on server hardware • 2 private keys • one for client browser • one for server (http server)

SSL Architecture
SSL Architecture • SSL session • • an association between client & server created by the Handshake Protocol define a set of cryptographic parameters may be shared by multiple SSL connections • SSL connection • a transient, peer-to-peer, communications link • associated with 1 SSL session
SSL Protocols • SSL Record Protocol and Standard HTTP. • SSL Record Protocol - responsible for the fragmentation, compression, encryption, and attachment of an SSL header to the plaintext prior to transmission. • Received encrypted messages are decrypted and reassembled for presentation to the higher levels of the protocol - provides basic security and communication services to the top levels of the SSL protocol stack. • Standard HTTP provides the Internet communication services between client and host without consideration for encryption of the data that is transmitted between client and server.
SSL Record Protocol • confidentiality • using symmetric encryption with a shared secret key defined by Handshake Protocol • IDEA, RC 2 -40, DES, 3 DES, Fortezza, RC 4 -40, RC 4 -128 • message is compressed before encryption • message integrity • using a MAC (Message Authentication Code) created using a shared secret key and a short message
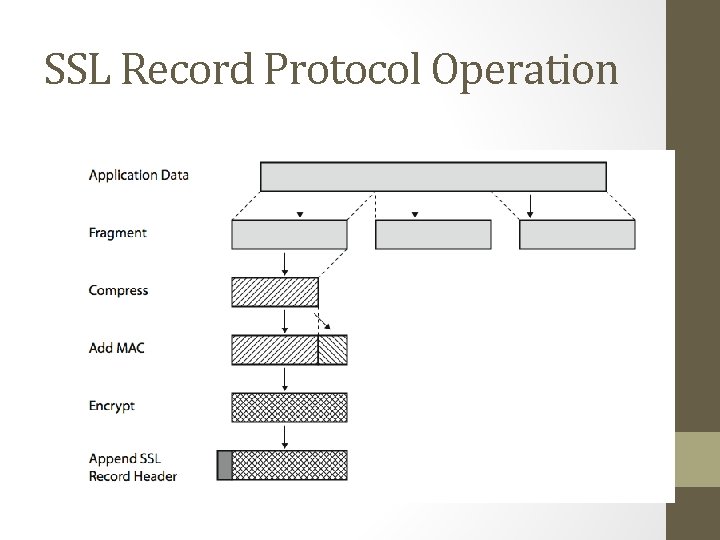
SSL Record Protocol Operation
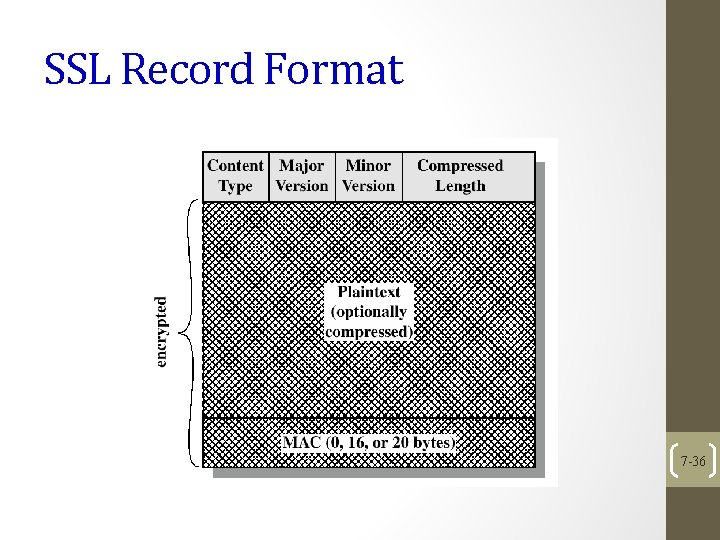
SSL Record Format 7 -36
Working of SSL Protocol • Normal client/server HTTP session • Client requests access to a portion of the Web site • Server sends a message to the client indicating that a secure connection must be established. • Client sends its public key and security parameters. • Handshaking phase is complete • Server finds a public key match and sends a digital certificate to the client to authenticate itself. • Client verifies that the certificate is valid and trustworthy, the SSL session is established. • Until the client or the server terminates the session, any amount of data can be transmitted securely.
Secure HTTP (S-HTTP) • extended version of Hypertext Transfer Protocol • Provides encryption of individual messages transmitted via the Internet between a client and server. • application of SSL over HTTP - encryption of all information protected and secure virtual connection. • No secure channel is established for the duration of a session (as in SSL) - designed for sending individual messages over the Internet – session for each individual exchange of data. • provide confidentiality, authentication, and data integrity through a variety of trust models and cryptographic algorithms. • Easy integration with existing HTTP applications and for implementation in conjunction with HTTP.
S-HTTP • To establish a session, the client and server - must have compatible cryptosystems and agree on the configuration. • The S-HTTP client then must send the server its public key so that the server can generate a session key. • The session key from the server is then encrypted with the client’s public key and returned to the client. • After the client decrypts the key using its private key, the client and server possess identical session keys, which they can use to encrypt the messages sent between them.

Securing E-mail with S/MIME, PEM, and PGP • Secure Multipurpose Internet Mail Extensions (S/MIME) encoding format of MIME protocol and uses digital signatures based on public-key cryptosystems • IETF - Privacy-Enhanced Mail (PEM) standard - use 3 DES symmetric key encryption and RSA for key exchanges and digital signatures • Pretty Good Privacy (PGP) - developed by Phil Zimmermann, uses the IDEA cipher for message encoding, also uses RSA for symmetric key exchange and digital signatures
Securing E-Mail • Common Internet e-mail standard – SMTP – limitations - an inability to transmit executable files or binary objects and an inability to handle character sets other than 7 -bit ASCII • to address the problems associated with SMTP - MIME.
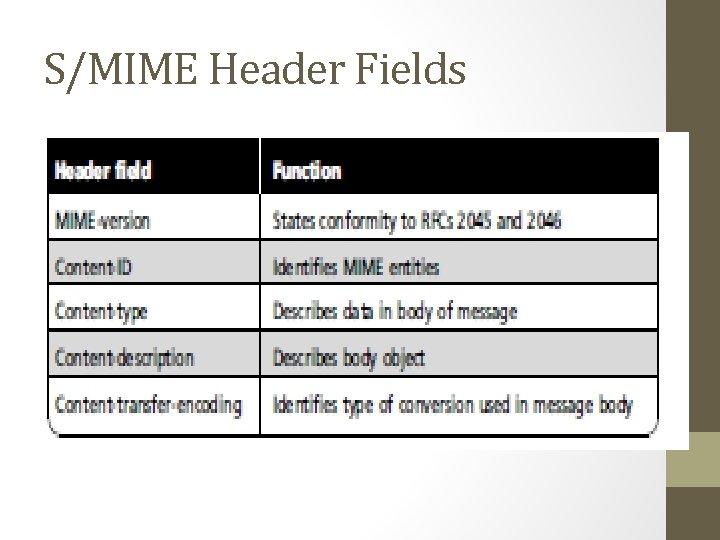
S/MIME Header Fields

S/MIME functions and algorithms
Securing Web Transactions with SET, SSL, and S-HTTP • to secure Web browsers, especially at e-commerce sites. • Protocols are SET, SSL, S-HTTP, Secure Shell (SSH-2), and IP Security (IPSec)
Secure Electronic Transactions (SET) • developed by Master. Card and Visa in 1997 to protect against electronic payment fraud. • uses DES to encrypt credit card information transfers, RSA for key exchange. • provides security both for Internet-based credit card transactions and credit card swipe systems in retail stores. • SSL provides secure online e-commerce transactions. • SSL relies on RSA for key transfer and uses IDEA, DES, or 3 DES for encrypted symmetric key-based data transfer.
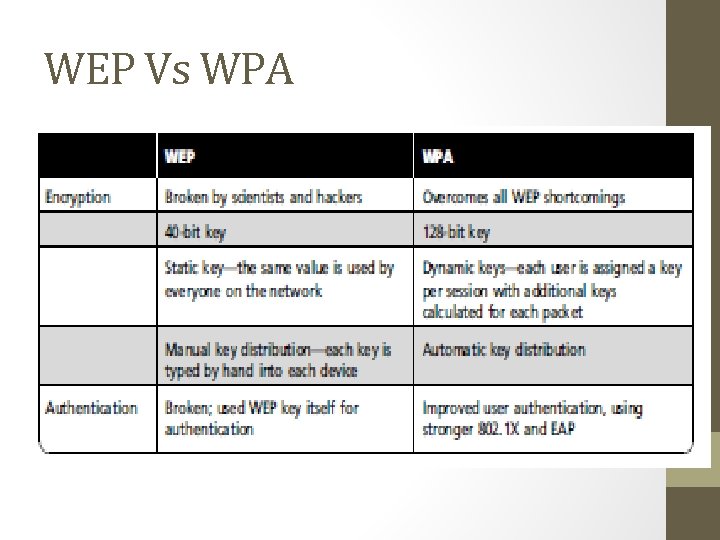
Securing Wireless Networks with WEP and WPA • Wireless local area networks (also known by the brand name Wi-Fi, or wireless fidelity networks) - inherently insecure. • Communication channel between the wireless network - uses radio transmissions - intercepted by anyone with a wireless packet sniffer. • Two sets of protocols - secure wireless transmissions • Wired Equivalent Privacy and Wi-Fi Protected Access designed for use with the IEEE 802. 11 wireless networks.

Wired Equivalent Privacy (WEP) • security for low-sensitivity networks. • uses the RC 4 cipher stream to encrypt each packet using a 64 bit key. • key is created using a 24 -bit initialization vector and a 40 -bit key value. • The packets are formed with an XOR function to use the RC 4 key value stream to encrypt the data packet. • A 4 -byte integrity check value (ICV) is calculated for each packet and then appended.
WEP • WEP is too weak because • Key management is not effective - single shared secret key value for each node. (Synchronizing key changes is a tedious process, no defined key management, seldom change of keys) • Too small initialization vector (IV) - results in the recycling of IVs. • (In 2007, a brute force decryption was accomplished in less than one minute)
Wi-Fi Protected Access (WPA and WPA 2) • to resolve the issues with WEP. • key size of 128 bits • uses dynamic keys created and shared by an authentication server. • through the use of the Temporal Key Integrity Protocol (TKIP). • TKIP - suite of algorithms - deliver the best security possible given the constraints of the wireless network.
WPA • TKIP adds four new algorithms (in addition to those that were used in WEP) • ● A cryptographic message integrity code, or MIC, called Michael - to defeat forgeries • ● A new IV sequencing discipline - to remove replay attacks • ● A per-packet key mixing function - to de correlate the public IVs from weak keys • ● A rekeying mechanism - to provide fresh encryption and integrity keys - undo threat of attacks from key reuse
WEP Vs WPA

WPA 2 • a replacement for WPA. • WPA 2 provided many of the elements missing from WPA - AES -based encryption. • 2006, WPA 2 became mandatory for all new Wi-Fi devices. • backward-compatible with WPA

Next Generation Wireless Protocols • Robust Secure Networks (RSN) - a protocol for replacement for TKIP in WPA • extends AES with the Counter Mode CBC MAC Protocol (CCMP) • Transitional Security Network (TSN) – co existence of RSN and WEP in same WLAN

RSN protocol • 1. Probe request from wireless network interface card (NIC) • 2. Probe Response (with RSN Information Exchange (IE) frame) from wireless access point • 3. Authentication request from wireless NIC • 4. Authentication from wireless access point. • 5. Association request (with an RSN IE frame) from wireless NIC. • 6. Association response from wireless access point

Bluetooth • de facto industry standard for short-range wireless communications between devices. • used to establish communications links between wireless telephones and headsets, between PDAs and desktop computers, and between laptops. • established by Ericsson scientists, soon involved Intel, Nokia, IBM, and Toshiba. • Microsoft, Lucent Technologies and 3 Com joined shortly
Bluetooth • a range of approximately 30 feet • Discoverable mode—other Bluetooth systems to detect and connect —easy access of devices like a shared folder on a networked computer • Non discoverable mode - susceptible to access by other devices connected it in the past • No authentication of connections • some degree of security for dial-up accounts and local-area file transfers. • Paired devices—usually a computer or a phone and a peripheral same passkey (to generate a session key for all future communications) to be entered on both devices
Bluetooth Security • Attack – to get the passkey • Simulate blue tooth access point - capture and store all communications • a virus called Cabir infected dozens of phones - drained the phones’ batteries • to secure Bluetooth-enabled devices - Turn off Bluetooth when not used and do not accept pairing request unless you know the identity of the requestor
Securing TCP/IP with IPSec and PGP • Internet Protocol Security (IPSec) - an open-source protocol framework (TCP/IP family of protocol standards) • secure communications across IP-based networks such as LANs, WANs, and the Internet. • designed to protect data integrity, user confidentiality, and authenticity at the IP packet level. • security system from IP version 6, the future version of the TCP/IP protocol - retrofitted for use with IP version 4 • IPSec - defined in Request for Comments (RFC) 1825, 1826, and 1827 • used to create virtual private networks (VPNs)
IPSec • specifies the information to be added to an IP packet how to encrypt packet data, Internet Key Exchange, (uses an asymmetric-based key exchange) • uses several different cryptosystems: • ● Diffie-Hellman key exchange for deriving key material between peers on a public network • ● Public-key cryptography for signing the Diffie. Hellman exchanges to guarantee the identity of the two parties • ● Bulk encryption algorithms, such as DES, for encrypting the data • ● Digital certificates signed by a certificate authority to act as digital ID cards

Transport and Tunnel Mode • transport mode is used to encrypt & optionally authenticate IP data • data protected (encrypted) but header left in clear • Intermediate nodes read source and destination address • can do traffic analysis but is efficient • good for ESP host to host traffic • tunnel mode encrypts entire IP packet • add new header for next hop • Intermediate systems act as proxies • good for VPNs, gateway to gateway security
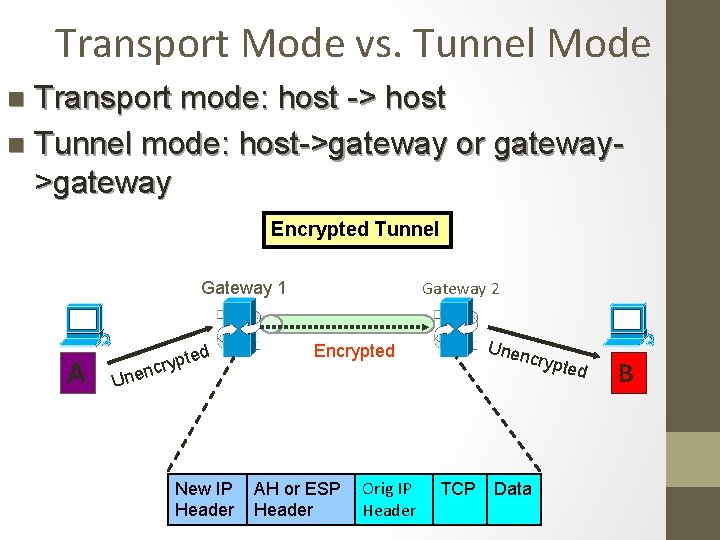
Transport Mode vs. Tunnel Mode Transport mode: host -> host n Tunnel mode: host->gateway or gateway>gateway n Encrypted Tunnel Gateway 2 Gateway 1 A ted p y r c Unen Encrypted n Une New IP Header AH or ESP Header Orig IP Header TCP crypt Data ed B
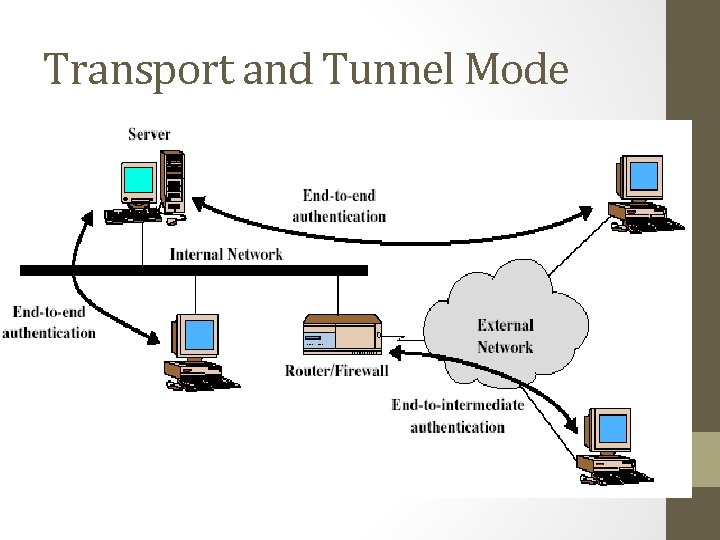
Transport and Tunnel Mode
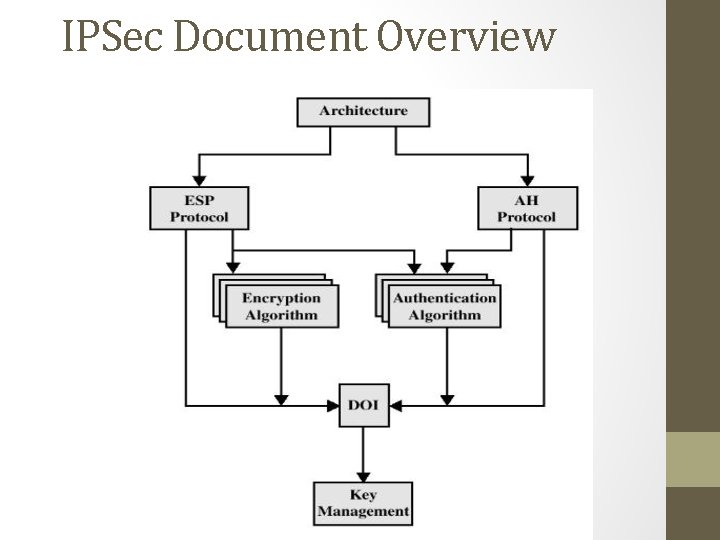
IPSec Document Overview

IPSec Document Overview • Architecture: covers general concepts, security requirements, definitions, mechanisms. • ESP: covers issues related to packet format, packet encryption and optionally authentication • AH: covers issues related to packet format and authentication • Encryption & Authentication algorithms, key management schemes. • Domain of Interpretation DOI: values of documents to relate to each other- id for algorithms and parameters such as key life time.
IPSec Services • Two protocols are used to provide security: • Authentication Header Protocol (AH) • Encapsulation Security Payload (ESP) • Services provided are: • • Access control Connectionless integrity Data origin authentication Rejection of replayed packets • a form of partial sequence integrity • Confidentiality (encryption) • Limited traffic flow confidentiality
IP Layer Security • system-to-system authentication and data integrity verification – AH • secrecy for the contents of network communications, system to- system authentication , data integrity verification - ESP • two networked systems form an association - uses encryption and authentication keys, algorithms, and key lifetimes -either the AH or the ESP protocol, but not both. • For both protocols - multiple security associations bundled to provide correct sequence through which the IP traffic must be processed to deliver the desired security features.

Authentication Header • Data integrity • Entire packet has not been tampered with • Authentication • Can “trust” IP address source • Use MAC to authenticate • Symmetric encryption, e. g, DES • One-way hash functions, e. g, HMAC-MD 5 -96 or HMAC-SHA-1 -96 • Anti-replay feature • Integrity check value
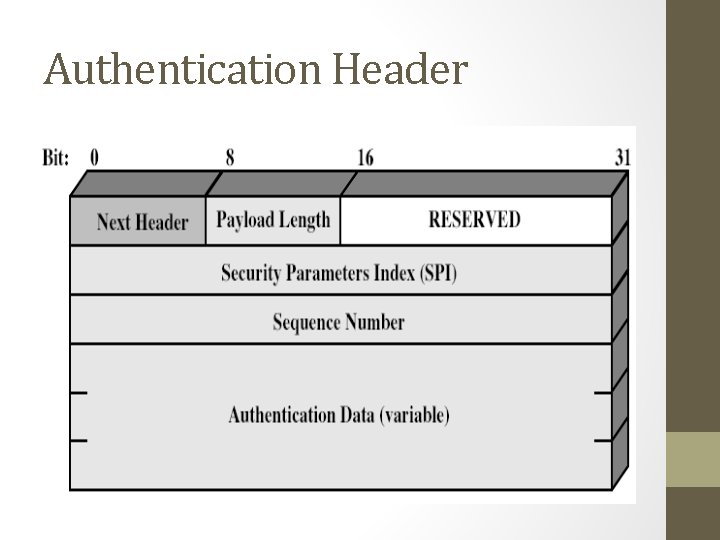
Authentication Header

AH • Next header: Identifies the next higher level protocol, such as TCP or ESP. • Payload length: Specifies the AH content’s length. • Reserved: For future use. • Security parameters index: Identifies the security association for this IP packet. • Sequence number: Provides a monotonically increasing counter number for each packet sent. Allows the recipient to order the packet and provides protection against replay attacks. • Authentication data: Variable-length data (multiple of 32 bits) containing the ICV (integrity check value) for this packet.

AH • provide data integrity and IP packet authentication. No confidentiality protection • IP packets - protected from replay attacks and address spoofing , other types of cyber attacks against open networks • security parameters index (SPI) - references the session key and algorithm used to protect the data being transported. • Sequence numbers allow packets reassembly. • The integrity check value (ICV) - checksum to verify that the packet itself is unaltered. • IPv 4 or IPv 6 - authentication secures the entire packet • tunnel mode - entire inner IP packet is secured
Encapsulating Security Payload (ESP) • RFC 2406 • provides message content confidentiality & limited traffic flow confidentiality • can optionally provide the same authentication services as AH • supports range of ciphers, modes, padding • incl. DES, Triple-DES, RC 5, IDEA, CAST etc • CBC most common • pad to meet blocksize, for traffic flow
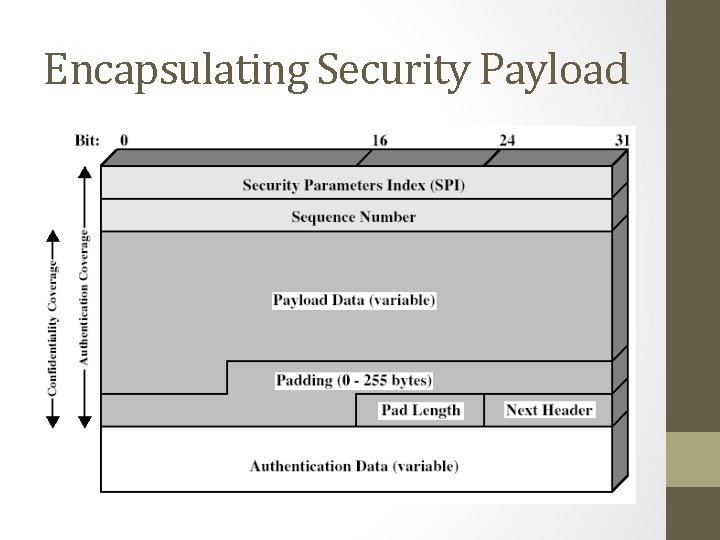
Encapsulating Security Payload

ESP • Security parameters index: Identifies the security association for this IP packet. • Sequence number: Provides a monotonically increasing counter number for each packet sent. Allows the recipient to order the packets and provides protection against replay attacks. • Payload data: Contains the encrypted data of the IP packet. • Padding: Space for adding bytes if required by encryption algorithm; also helps conceal the actual payload size. • Pad length: Specifies how much of the payload is padding. • Next header: Identifies the next higher level protocol, such as TCP. • Authentication data: Variable-length data (multiple of 32 bits) containing the ICV (integrity check value) for this packet.

ESP • provides confidentiality services for IP packets across insecure networks. • provide the authentication services of AH. • in tunnel mode - to establish a virtual private network, (encryption and authentication ) - entire IP packet encrypted with the attached ESP header - new IP header is attached to the encrypted payload – provides the required routing information.
ESP • ESP header in IP packet - prior to the TCP header, an ESP trailer - after the IPv 4 packet. • for authentication - append ESP authentication data field after the ESP trailer • complete transport segment with ESP trailer - encrypted. • IPv 6 transmission - ESP header - after the hop-by-hop and routing headers - Encryption under IPv 6 - transport segment and ESP trailer. • Authentication in both IPv 4 and IPv 6 - ciphertext data plus the ESP header. • IPSec ESP-compliant systems - support the implementation of the DES algorithm using the. CBC (cipher block chaining) mode (Triple DES, IDEA, RC 5, CAST, and Blowfish)

AH: Tunnel and Transport Mode • Original • Transport Mode • Cover most of the original packet • Tunnel Mode • Cover entire original packet
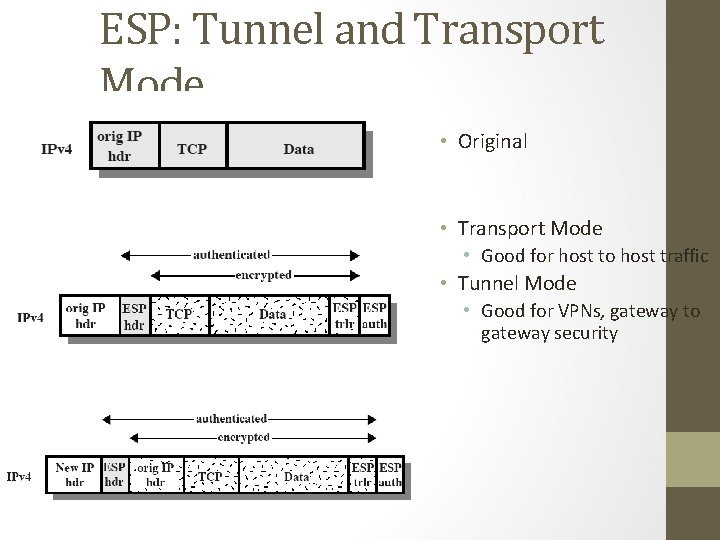
ESP: Tunnel and Transport Mode • Original • Transport Mode • Good for host to host traffic • Tunnel Mode • Good for VPNs, gateway to gateway security

PGP-Pretty Good Privacy • hybrid cryptosystem • open-source de facto standard for encryption and authentication of e-mail and file storage applications. • PGP Functions
PGP Services • • • Authentication by digital signatures Message encryption Compression E-mail compatibility Segmentation Key management.
PGP – Public Key Encryption • Secure Hash Algorithm 1 (SHA-1) - 160 -bit hash code • Hash code encryption - DSS or RSA - appended to the original message. • Decryption - sender’s public key to recover the hash code. • Same encryption algorithm - new hash code by recipient • If identical hash codes – authentic message and sender

PGP – Conventional Encryption • to protect entire contents of the message from unauthorized view. • standard algorithms - 3 DES, IDEA, or CAST - 128 -bit session key. • RSA -session key encryption by recipient’s public key and appended to the message. • Recipient’s private key with RSA - decrypt and recover the session key. • recovered session key – to decrypt the message. • Authentication and message encryption - digital signature of the message with a private key, encrypting the message with a unique session key, and then encrypting the session key with the intended recipient’s public key.
PGP – File Management • freeware ZIP algorithm to compress the message after digital signing before encryption • saves space and generates a more secure encrypted document • Radix-64 process - encodes non textual data and encrypted data transfer using e-mail systems by maintaining the required 8 -bit blocks of ASCII text • format maps three octets of binary data into four ASCII characters and appends a cyclic redundancy check (CRC) to detect transmission errors.
PGP – File Management • Automatic segmentation to manageable stream size, performed after all other encryption and conversion functions, reassembling at recipient end prior to decompression and decryption. • no rigid structure for public-key management, assigns a levelof trust, degree of trust in any specific key. • If the trust of a given credential is broken, (key is compromised) the owner issues a digitally signed key revocation certificate - updates the credential trust bytes when the credential is next verified.
- Slides: 83