Fuzzing Brute Force Vulnerability Discovery Michael Sutton Director

Fuzzing Brute Force Vulnerability Discovery Michael Sutton Director, i. Defense Labs msutton@idefense. com Contains Veri. Sign Confidential and Proprietary Information
Agenda + Background ▪ What is fuzzing and who should do it? + Phases ▪ What are the various stages when fuzzing a target? + Fuzzer classes ▪ What can be fuzzed? + Automation ▪ Making theoretical practical + Tools/Demos ▪ ▪ ▪ File. Fuzz Web. Fuzz COMRaider + Advanced topics + The future or fuzzing 2 Contains Veri. Sign Confidential and Proprietary Information
Vulnerability Discovery Methodologies – White Box + “Also known as glass box, structural, clear box and open box testing. A software testing technique whereby explicit knowledge of the internal workings of the item being tested are used to select the test data. ” ▪ Webopedia + Source code review ▪ Static analysis ▪ Pros – Coverage ▪ Cons – Dependencies – Are we testing reality? • Compiler issues • Implementation scenarios 3 Contains Veri. Sign Confidential and Proprietary Information
Vulnerability Discovery Methodologies – Black Box + “Also known as functional testing. A software testing technique whereby the internal workings of the item being tested are not known by the tester. ” ▪ Webopedia + Reverse engineering ▪ ▪ ▪ Static analysis Pros – Complex vulnerabilities uncovered Cons – Time consuming – Deep knowledge required + Fuzzing ▪ ▪ ▪ Dynamic analysis Pros – Relatively simple – Realistic Cons – Coverage – Complex vulnerabilities missed 4 Contains Veri. Sign Confidential and Proprietary Information
What is Fuzzing? + “Fuzz testing or fuzzing is a software testing technique. The basic idea is to attach the inputs of a program to a source of random data ("fuzz"). If the program fails (for example, by crashing, or by failing built-in code assertions), then there are defects to correct. The great advantage of fuzz testing is that the test design is extremely simple, and free of preconceptions about system behavior. ” ▪ Wikipedia + “Unexpected input causes unexpected results. ” ▪ 5 Michael Sutton Contains Veri. Sign Confidential and Proprietary Information
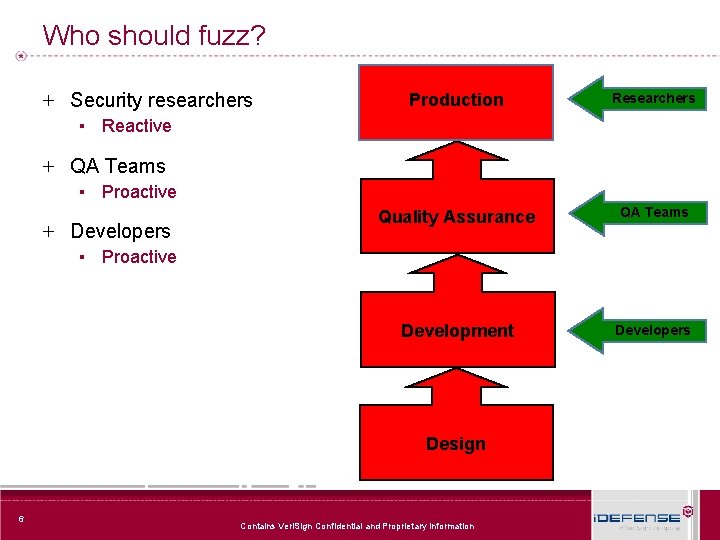
Who should fuzz? + Security researchers Production Researchers Quality Assurance QA Teams Development Developers ▪ Reactive + QA Teams ▪ Proactive + Developers ▪ Proactive Design 6 Contains Veri. Sign Confidential and Proprietary Information
What can fuzzing do for you? + MS 06 -01 - Graphics Rendering Engine Vulnerability ▪ ▪ ▪ aka “Windows WMF Vulnerability” Appears to have been discovered through fuzzing Evidence – Google search on strings in initial exploit identified probable source file • JNK = c, Jun N, terminal, kitase • kitase kinase – At the time, Google didn’t recognize WMF file types and therefore treated them as text allowing a search for strings within the binary – Diffing original file and exploit revealed evidence that fuzzing was used to discover the vulnerability 7 Contains Veri. Sign Confidential and Proprietary Information
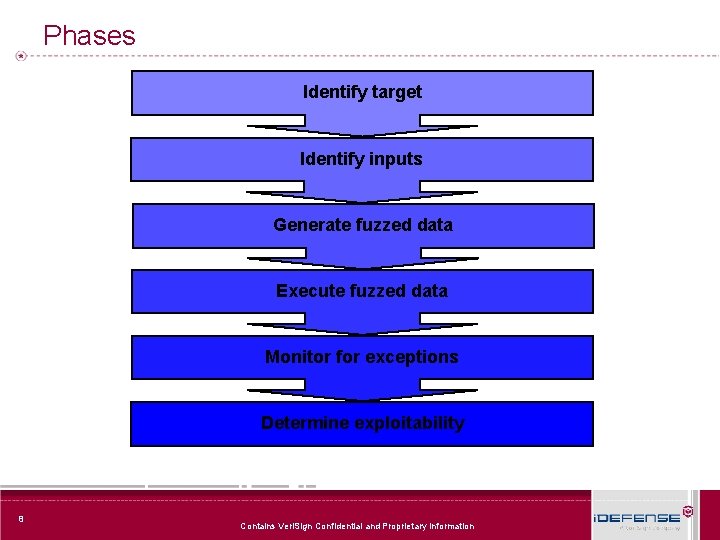
Phases Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability 8 Contains Veri. Sign Confidential and Proprietary Information
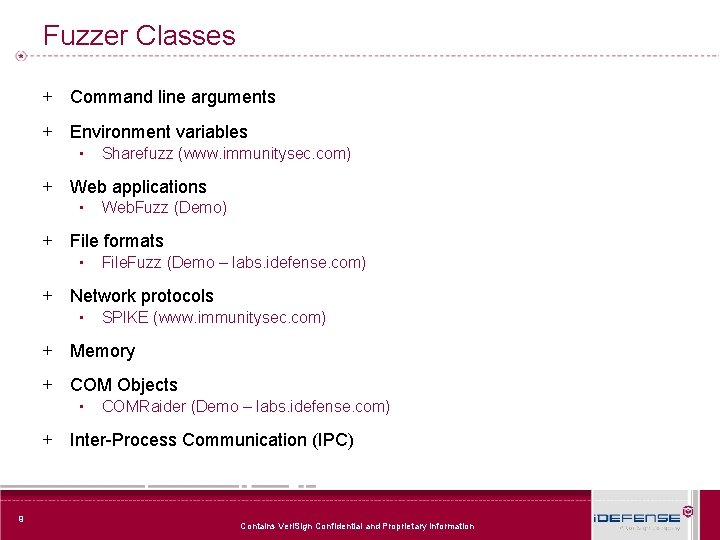
Fuzzer Classes + Command line arguments + Environment variables ▪ Sharefuzz (www. immunitysec. com) + Web applications ▪ Web. Fuzz (Demo) + File formats ▪ File. Fuzz (Demo – labs. idefense. com) + Network protocols ▪ SPIKE (www. immunitysec. com) + Memory + COM Objects ▪ COMRaider (Demo – labs. idefense. com) + Inter-Process Communication (IPC) 9 Contains Veri. Sign Confidential and Proprietary Information
Automation + Test cases ▪ Approach – Pre-generated test cases ▪ Tools – PROTOS Test Suites ▪ Pro – Consistency ▪ Con – Static – Time consuming 10 Contains Veri. Sign Confidential and Proprietary Information
Automation + Brute force fuzzing ▪ Approach – Raw byte manipulation ▪ Tool(s) – File. Fuzz ▪ Pro – Simple ▪ Con – Inefficient – Fails to account for dependent values (e. g. checksums) 11 Contains Veri. Sign Confidential and Proprietary Information
Automation + ‘Intelligent’ fuzzing ▪ Approach – Templates developed based on protocol definitions ▪ Tools – SPIKEfile ▪ Pro – Efficient ▪ Con – Time consuming 12 Contains Veri. Sign Confidential and Proprietary Information
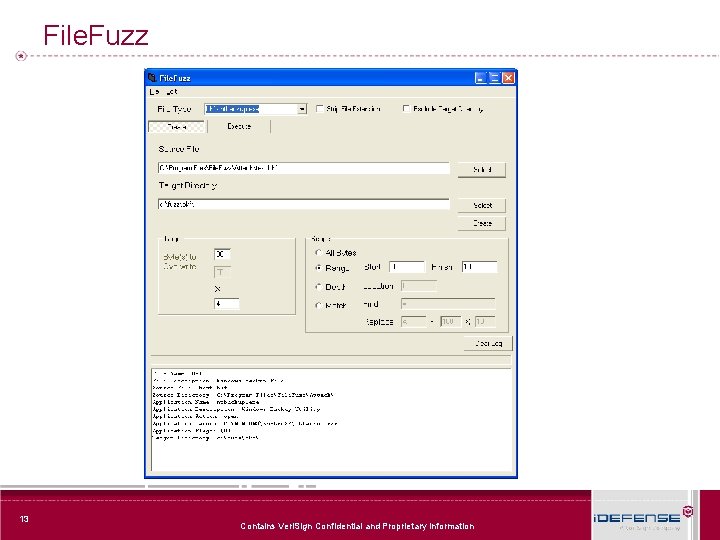
File. Fuzz 13 Contains Veri. Sign Confidential and Proprietary Information
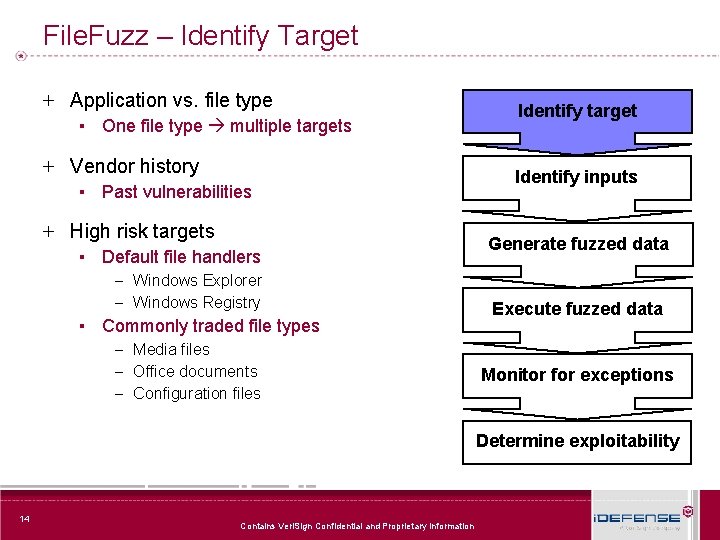
File. Fuzz – Identify Target + Application vs. file type ▪ One file type multiple targets + Vendor history ▪ Past vulnerabilities + High risk targets ▪ Default file handlers – Windows Explorer – Windows Registry ▪ Commonly traded file types – Media files – Office documents – Configuration files Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability 14 Contains Veri. Sign Confidential and Proprietary Information
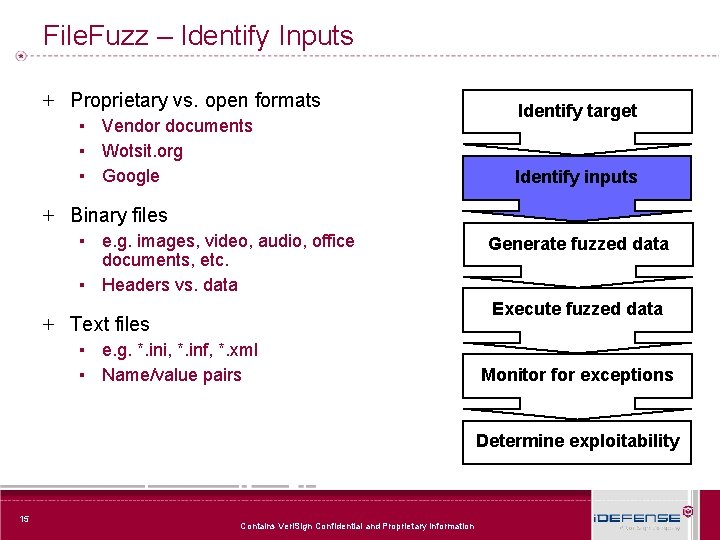
File. Fuzz – Identify Inputs + Proprietary vs. open formats ▪ Vendor documents ▪ Wotsit. org ▪ Google Identify target Identify inputs + Binary files ▪ e. g. images, video, audio, office documents, etc. ▪ Headers vs. data Generate fuzzed data Execute fuzzed data + Text files ▪ e. g. *. ini, *. inf, *. xml ▪ Name/value pairs Monitor for exceptions Determine exploitability 15 Contains Veri. Sign Confidential and Proprietary Information
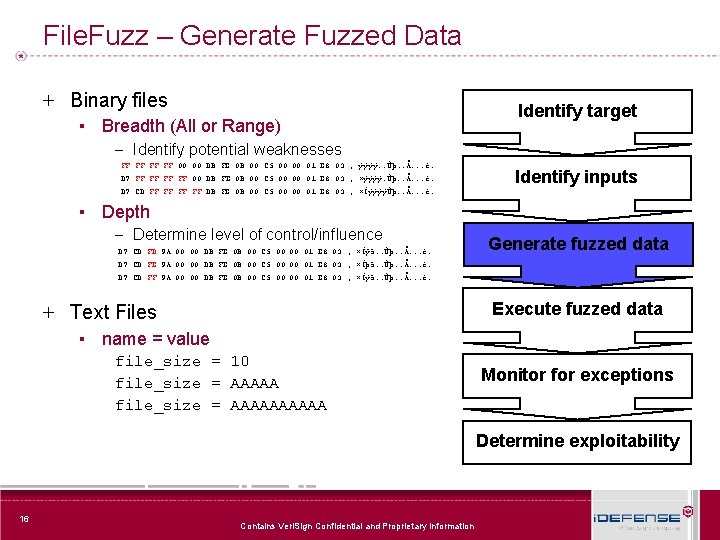
File. Fuzz – Generate Fuzzed Data + Binary files ▪ Breadth (All or Range) – Identify potential weaknesses FF FF 00 00 DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ÿÿÿÿ. . Ûþ. . Å. . . è. D 7 FF FF 00 DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ×ÿÿÿÿ. Ûþ. . Å. . . è. Identify target Identify inputs D 7 CD FF FF DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ×ÍÿÿÿÿÛþ. . Å. . . è. ▪ Depth – Determine level of control/influence D 7 CD FD 9 A 00 00 DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ×Íýš. . Ûþ. . Å. . . è. Generate fuzzed data D 7 CD FE 9 A 00 00 DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ×Íþš. . Ûþ. . Å. . . è. D 7 CD FF 9 A 00 00 DB FE 0 B 00 C 5 00 00 01 E 8 03 ; ×Íÿš. . Ûþ. . Å. . . è. Execute fuzzed data + Text Files ▪ name = value file_size = 10 file_size = AAAAAAAAAA Monitor for exceptions Determine exploitability 16 Contains Veri. Sign Confidential and Proprietary Information
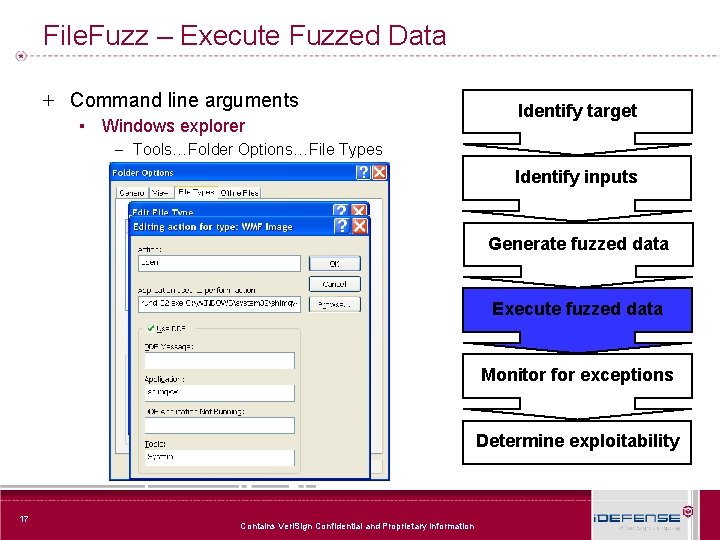
File. Fuzz – Execute Fuzzed Data + Command line arguments ▪ Windows explorer – Tools…Folder Options…File Types Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability 17 Contains Veri. Sign Confidential and Proprietary Information
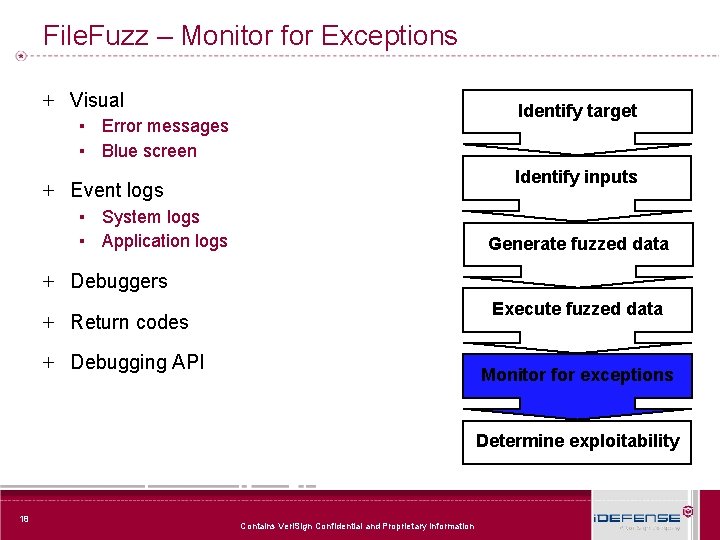
File. Fuzz – Monitor for Exceptions + Visual Identify target ▪ Error messages ▪ Blue screen Identify inputs + Event logs ▪ System logs ▪ Application logs Generate fuzzed data + Debuggers Execute fuzzed data + Return codes + Debugging API Monitor for exceptions Determine exploitability 18 Contains Veri. Sign Confidential and Proprietary Information
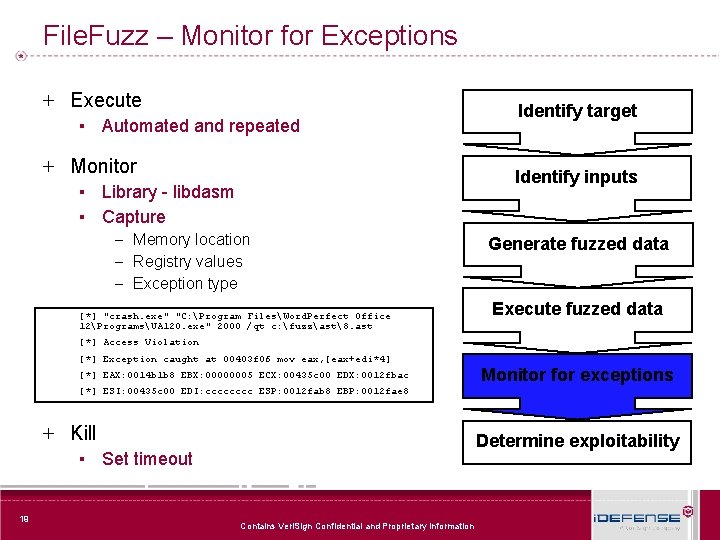
File. Fuzz – Monitor for Exceptions + Execute ▪ Automated and repeated + Monitor ▪ Library - libdasm ▪ Capture – Memory location – Registry values – Exception type [*] "crash. exe" "C: Program FilesWord. Perfect Office 12ProgramsUA 120. exe" 2000 /qt c: fuzzast8. ast Identify target Identify inputs Generate fuzzed data Execute fuzzed data [*] Access Violation [*] Exception caught at 00403 f 06 mov eax, [eax+edi*4] [*] EAX: 0014 b 1 b 8 EBX: 00000005 ECX: 00435 c 00 EDX: 0012 fbac Monitor for exceptions [*] ESI: 00435 c 00 EDI: cccc ESP: 0012 fab 8 EBP: 0012 fae 8 + Kill Determine exploitability ▪ Set timeout 19 Contains Veri. Sign Confidential and Proprietary Information
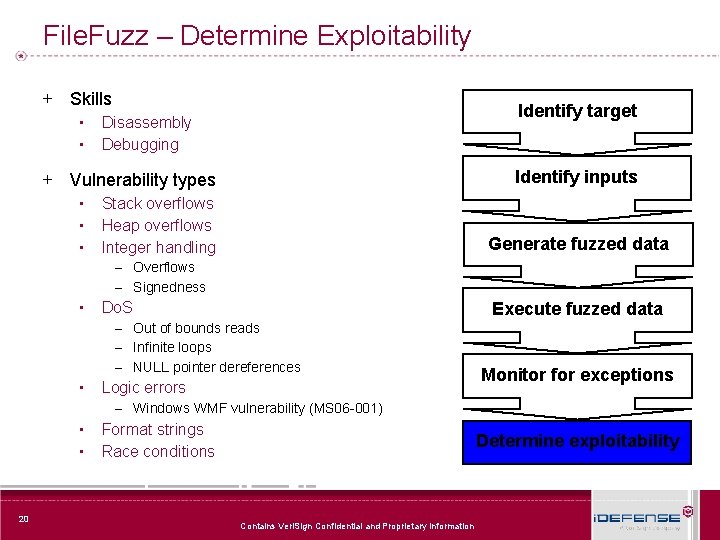
File. Fuzz – Determine Exploitability + Skills ▪ ▪ Identify target Disassembly Debugging Identify inputs + Vulnerability types ▪ ▪ ▪ Stack overflows Heap overflows Integer handling Generate fuzzed data – Overflows – Signedness ▪ Execute fuzzed data Do. S – Out of bounds reads – Infinite loops – NULL pointer dereferences ▪ Logic errors Monitor for exceptions – Windows WMF vulnerability (MS 06 -001) ▪ ▪ 20 Format strings Race conditions Determine exploitability Contains Veri. Sign Confidential and Proprietary Information
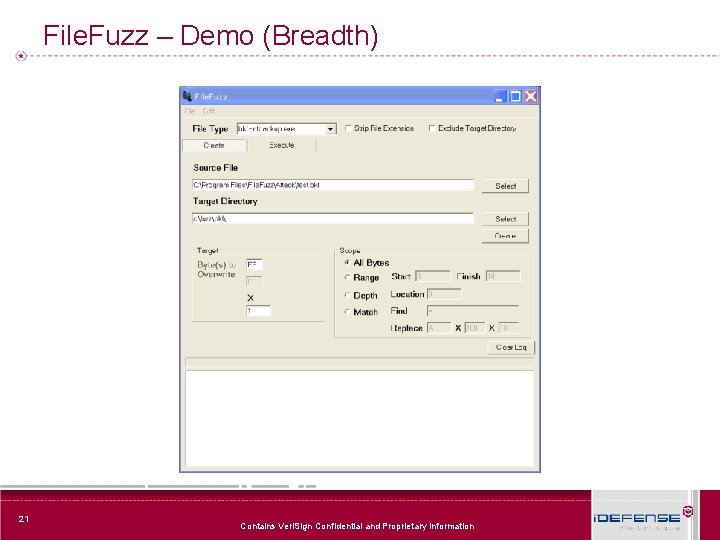
File. Fuzz – Demo (Breadth) 21 Contains Veri. Sign Confidential and Proprietary Information
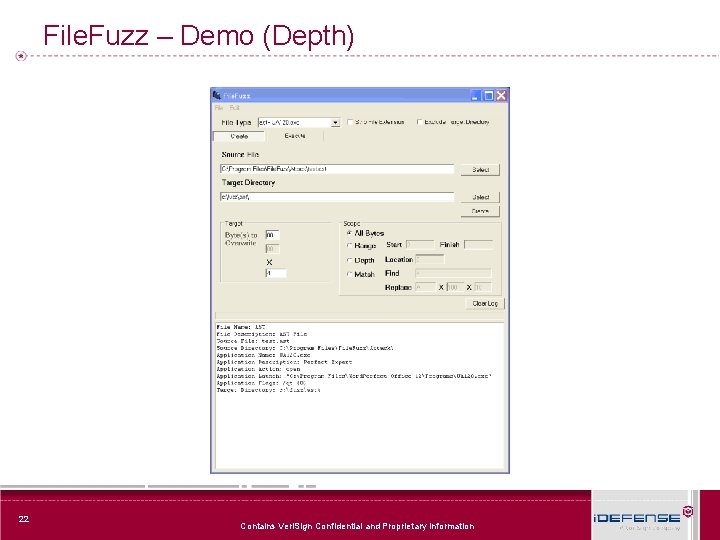
File. Fuzz – Demo (Depth) 22 Contains Veri. Sign Confidential and Proprietary Information
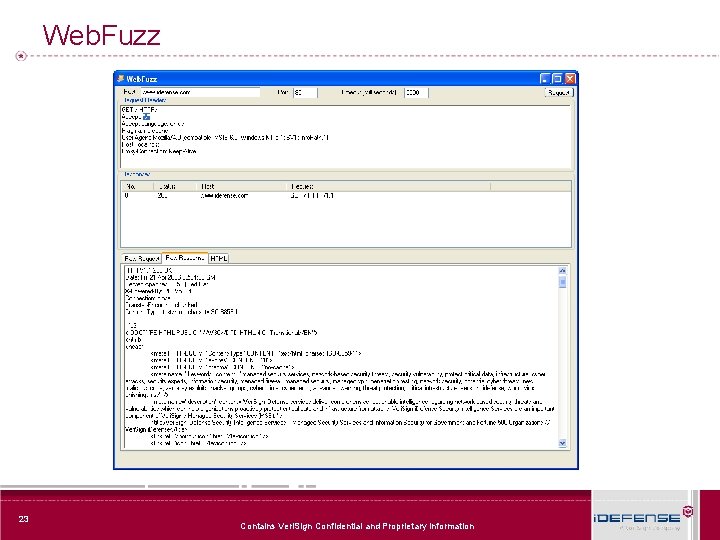
Web. Fuzz 23 Contains Veri. Sign Confidential and Proprietary Information
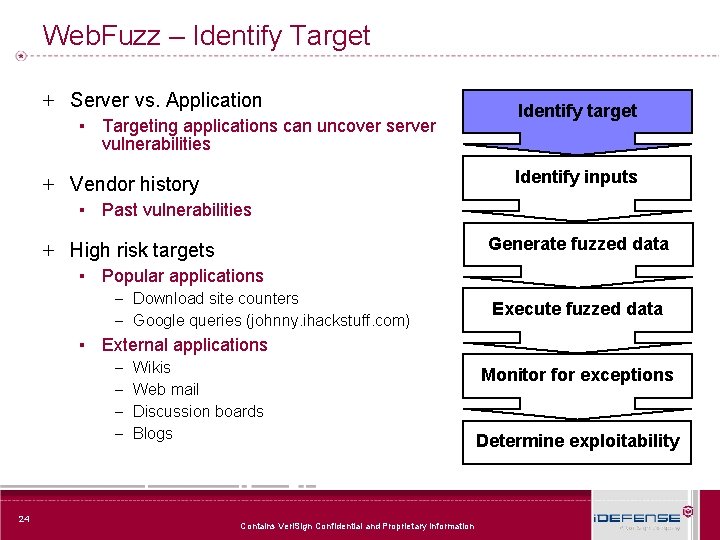
Web. Fuzz – Identify Target + Server vs. Application ▪ Targeting applications can uncover server Identify target vulnerabilities Identify inputs + Vendor history ▪ Past vulnerabilities Generate fuzzed data + High risk targets ▪ Popular applications – Download site counters – Google queries (johnny. ihackstuff. com) ▪ External applications – Wikis – Web mail – Discussion boards – Blogs 24 Contains Veri. Sign Confidential and Proprietary Information Execute fuzzed data Monitor for exceptions Determine exploitability
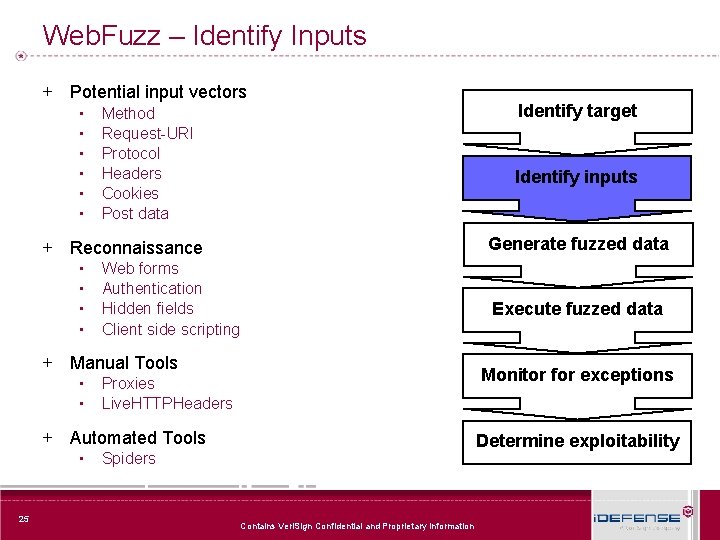
Web. Fuzz – Identify Inputs + Potential input vectors ▪ ▪ ▪ Method Request-URI Protocol Headers Cookies Post data Identify inputs Generate fuzzed data + Reconnaissance ▪ ▪ Web forms Authentication Hidden fields Client side scripting + Manual Tools ▪ ▪ 25 Execute fuzzed data Monitor for exceptions Proxies Live. HTTPHeaders + Automated Tools ▪ Identify target Determine exploitability Spiders Contains Veri. Sign Confidential and Proprietary Information
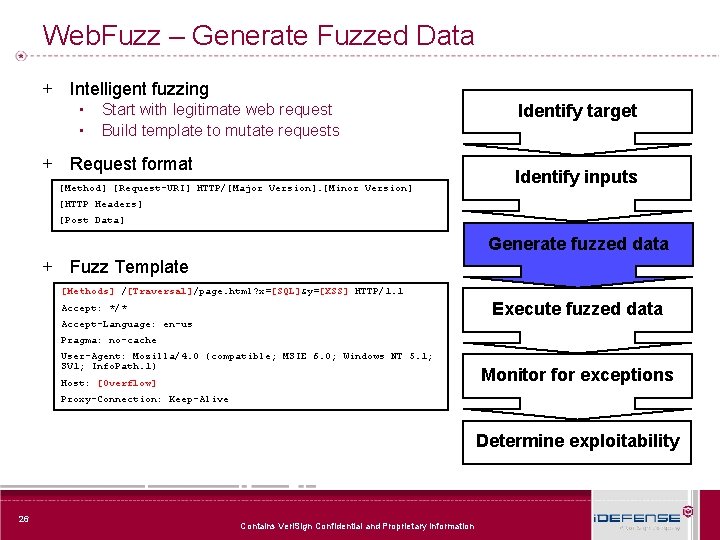
Web. Fuzz – Generate Fuzzed Data + Intelligent fuzzing ▪ ▪ Start with legitimate web request Build template to mutate requests + Request format [Method] [Request-URI] HTTP/[Major Version]. [Minor Version] Identify target Identify inputs [HTTP Headers] [Post Data] Generate fuzzed data + Fuzz Template [Methods] /[Traversal]/page. html? x=[SQL]&y=[XSS] HTTP/1. 1 Execute fuzzed data Accept: */* Accept-Language: en-us Pragma: no-cache User-Agent: Mozilla/4. 0 (compatible; MSIE 6. 0; Windows NT 5. 1; SV 1; Info. Path. 1) Host: [Overflow] Monitor for exceptions Proxy-Connection: Keep-Alive Determine exploitability 26 Contains Veri. Sign Confidential and Proprietary Information
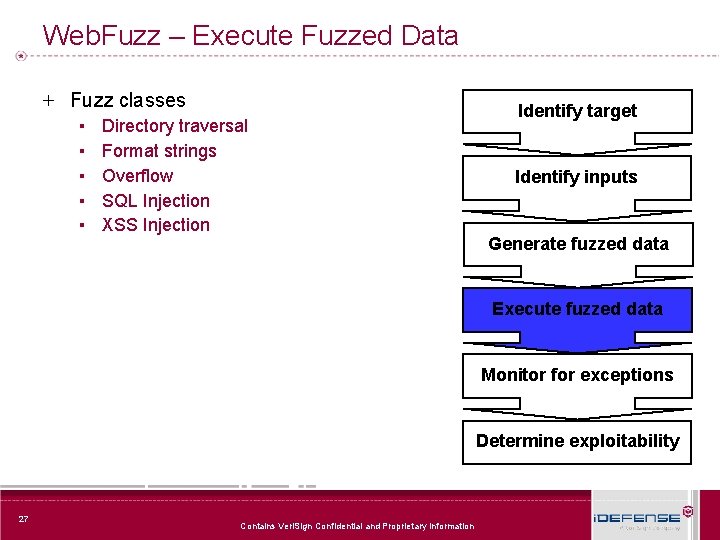
Web. Fuzz – Execute Fuzzed Data + Fuzz classes ▪ ▪ ▪ Directory traversal Format strings Overflow SQL Injection XSS Injection Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability 27 Contains Veri. Sign Confidential and Proprietary Information
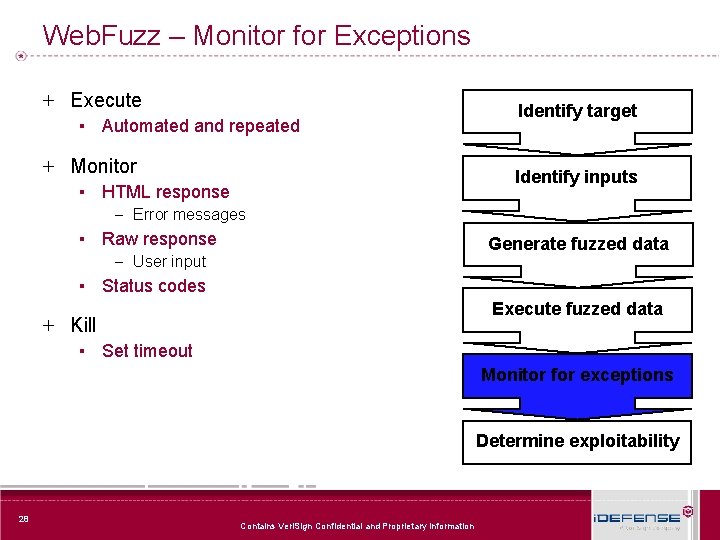
Web. Fuzz – Monitor for Exceptions + Execute ▪ Automated and repeated + Monitor ▪ HTML response – Error messages ▪ Raw response – User input ▪ Status codes Identify target Identify inputs Generate fuzzed data Execute fuzzed data + Kill ▪ Set timeout Monitor for exceptions Determine exploitability 28 Contains Veri. Sign Confidential and Proprietary Information
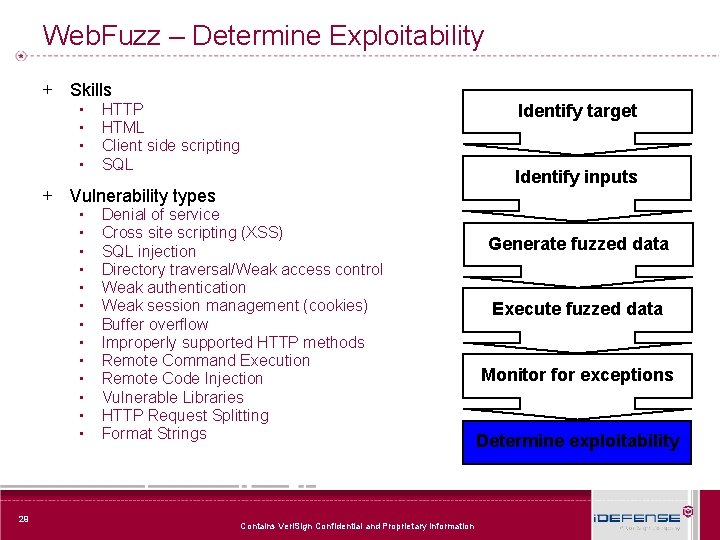
Web. Fuzz – Determine Exploitability + Skills ▪ ▪ HTTP HTML Client side scripting SQL + Vulnerability types ▪ ▪ ▪ ▪ 29 Denial of service Cross site scripting (XSS) SQL injection Directory traversal/Weak access control Weak authentication Weak session management (cookies) Buffer overflow Improperly supported HTTP methods Remote Command Execution Remote Code Injection Vulnerable Libraries HTTP Request Splitting Format Strings Contains Veri. Sign Confidential and Proprietary Information Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability
Web. Fuzz - Demo 30 Contains Veri. Sign Confidential and Proprietary Information
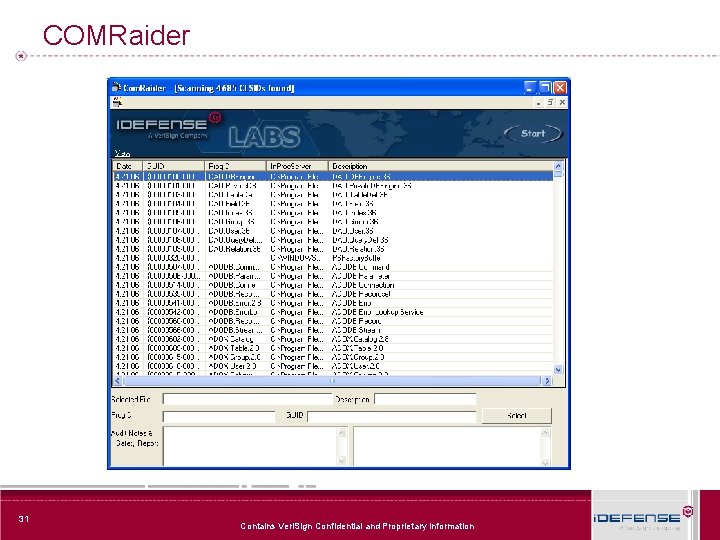
COMRaider 31 Contains Veri. Sign Confidential and Proprietary Information
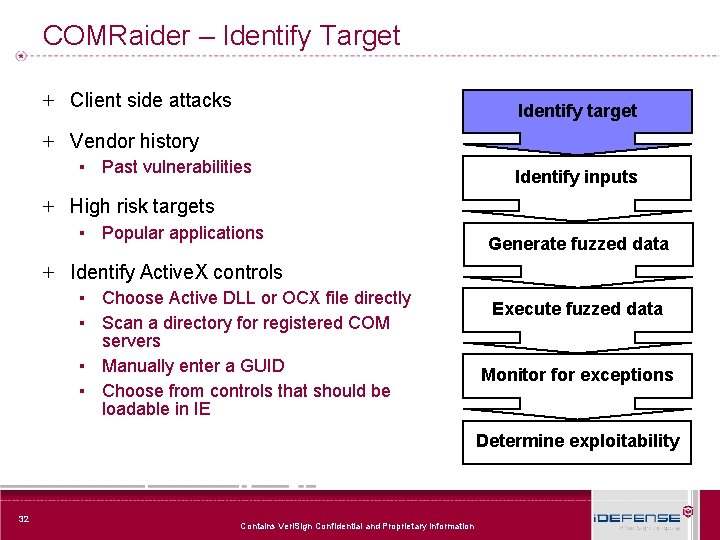
COMRaider – Identify Target + Client side attacks Identify target + Vendor history ▪ Past vulnerabilities Identify inputs + High risk targets ▪ Popular applications Generate fuzzed data + Identify Active. X controls ▪ Choose Active DLL or OCX file directly ▪ Scan a directory for registered COM servers ▪ Manually enter a GUID ▪ Choose from controls that should be loadable in IE Execute fuzzed data Monitor for exceptions Determine exploitability 32 Contains Veri. Sign Confidential and Proprietary Information
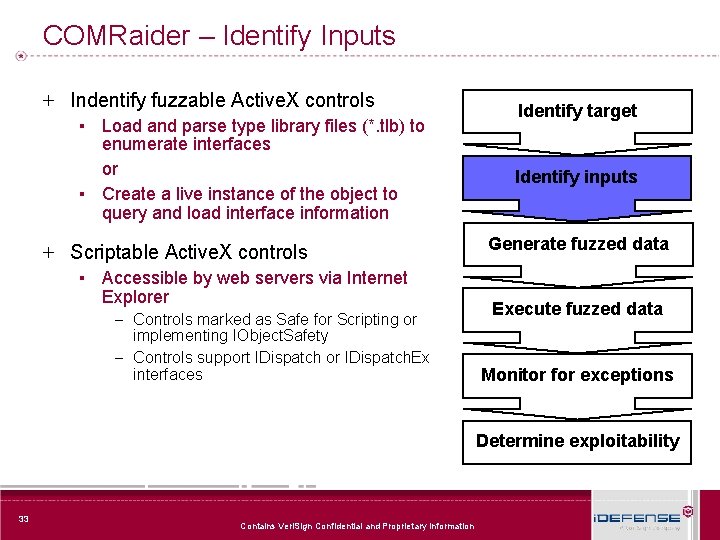
COMRaider – Identify Inputs + Indentify fuzzable Active. X controls ▪ Load and parse type library files (*. tlb) to enumerate interfaces or ▪ Create a live instance of the object to query and load interface information + Scriptable Active. X controls Identify target Identify inputs Generate fuzzed data ▪ Accessible by web servers via Internet Explorer – Controls marked as Safe for Scripting or implementing IObject. Safety – Controls support IDispatch or IDispatch. Ex interfaces Execute fuzzed data Monitor for exceptions Determine exploitability 33 Contains Veri. Sign Confidential and Proprietary Information
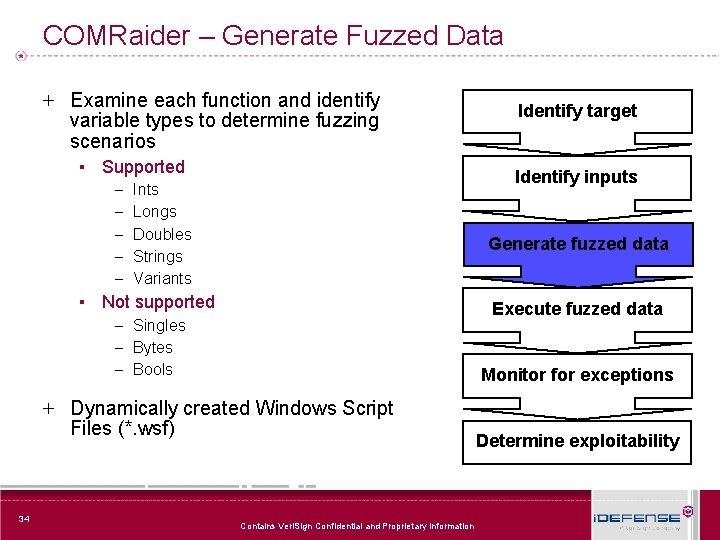
COMRaider – Generate Fuzzed Data + Examine each function and identify variable types to determine fuzzing scenarios ▪ Supported – Ints – Longs – Doubles – Strings – Variants ▪ Not supported – Singles – Bytes – Bools Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions + Dynamically created Windows Script Files (*. wsf) 34 Identify target Contains Veri. Sign Confidential and Proprietary Information Determine exploitability
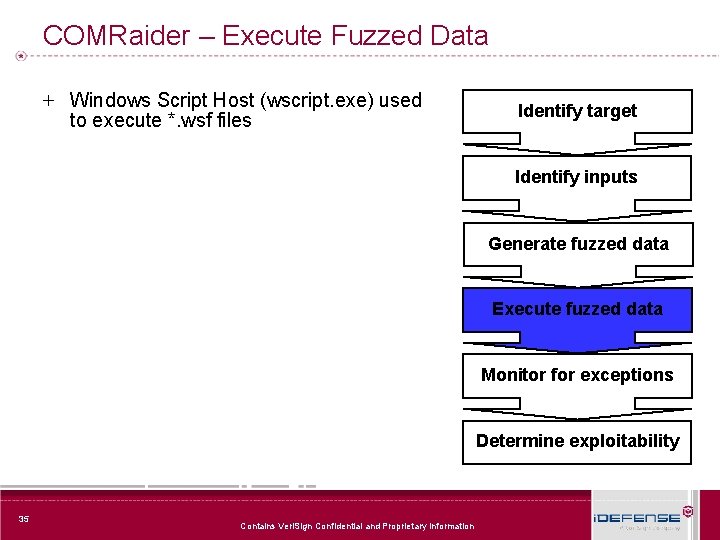
COMRaider – Execute Fuzzed Data + Windows Script Host (wscript. exe) used to execute *. wsf files Identify target Identify inputs Generate fuzzed data Execute fuzzed data Monitor for exceptions Determine exploitability 35 Contains Veri. Sign Confidential and Proprietary Information
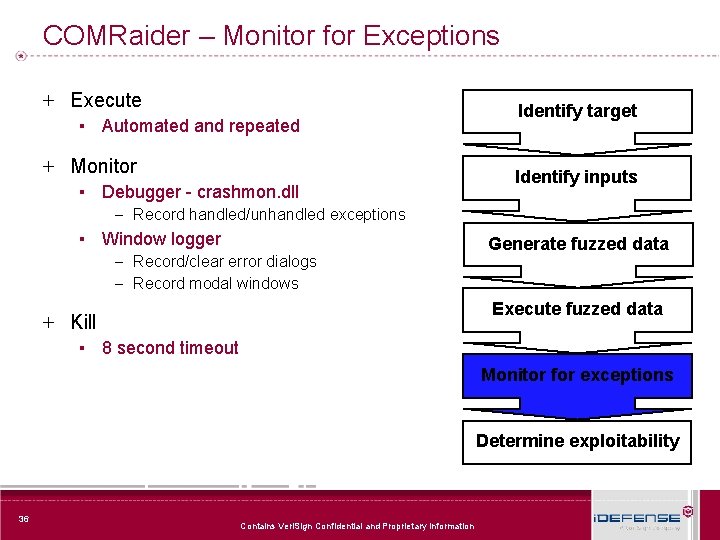
COMRaider – Monitor for Exceptions + Execute ▪ Automated and repeated + Monitor ▪ Debugger - crashmon. dll – Record handled/unhandled exceptions ▪ Window logger – Record/clear error dialogs – Record modal windows Identify target Identify inputs Generate fuzzed data Execute fuzzed data + Kill ▪ 8 second timeout Monitor for exceptions Determine exploitability 36 Contains Veri. Sign Confidential and Proprietary Information
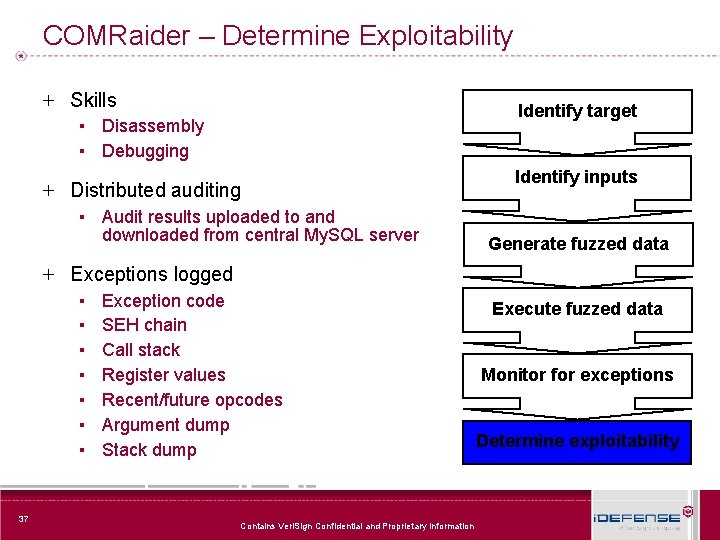
COMRaider – Determine Exploitability + Skills Identify target ▪ Disassembly ▪ Debugging + Distributed auditing Identify inputs ▪ Audit results uploaded to and downloaded from central My. SQL server Generate fuzzed data + Exceptions logged ▪ ▪ ▪ ▪ 37 Exception code SEH chain Call stack Register values Recent/future opcodes Argument dump Stack dump Contains Veri. Sign Confidential and Proprietary Information Execute fuzzed data Monitor for exceptions Determine exploitability
COMRaider - Demo 38 Contains Veri. Sign Confidential and Proprietary Information
Advanced Topics + Fuzzing Frameworks + Automated structure identification + Fuzzer tracking (code coverage) + Intelligent exception detection and processing 39 Contains Veri. Sign Confidential and Proprietary Information
The Future of Fuzzing + Tools ▪ Frameworks ▪ Integrated test environments ▪ Commercial tools + People ▪ Wider audience ▪ Proactive fuzzing – the shift from offense to defense 40 Contains Veri. Sign Confidential and Proprietary Information
Questions 41 Contains Veri. Sign Confidential and Proprietary Information
- Slides: 41