Do Strong Web Passwords Accomplish Anything Florencio Herley
Do Strong Web Passwords Accomplish Anything? Florencio, Herley and Coskun Presented by: Ryan Lehan November 19, 2008 CSC 682
Outline n Introduction n Duh!, but rather be safe than sorry. Strong Passwords n Attack Scenarios n Why Use Strong Passwords? n Strength of User ID-Password Combination n Strength alone is not enough n Conclusion n
Introduction n Authentication Traditionally Depends Upon n Something you have n n Something you are n n Fingerprint, voice Something you know n n Badge Password Authentication Most Used Method n Something you know n User ID (Account) in conjunction with a password
Introduction (continued) n User IDs n Creation n Created for you (network administrator) n Created by you n Could be public knowledge n Person who created the account for you n Email address (jdoe@yahoo. com) n Part of standardization process (first initial + last name)
Introduction (continued) n Passwords Should not be public knowledge n To prevent “Credential Theft”, advised to: n n Create Strong Passwords n Change Password Frequently n Never Write Password Down
Introduction (continued) n Threats to a user’s credentials n n n Phishing Key Logging Brute Force n n Bulk Guessing n n Attack on a known User ID Attack on all accounts Special Knowledge or Access n n n Shoulder Surfing Knowledgeable Information about the user Access to Password Manager n List, application, database
Strong Passwords n Not based upon personal information that can be guessed n n Not based upon a word found in the dictionary n n n Subject to dictionary attacks Should have a minimum length Should contain the following n n n Names, dates, etc. Combination of upper and lower casing Special characters and numbers Problems n n Hard to remember More likely to be written down
Attack Scenarios n What Strong Passwords will not prevent n n Phishing Key Logging Special Knowledge or Access Why? n n User supplied information Overt Method n n Phishing, Password List/Manager Covert Method n Key Logging
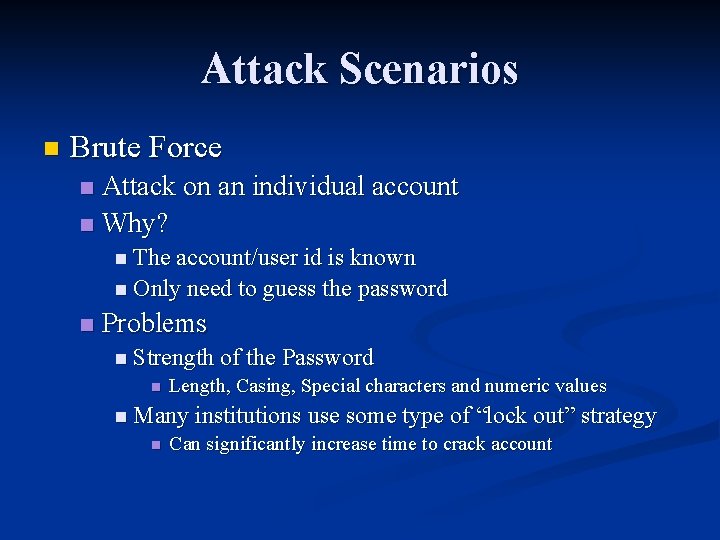
Attack Scenarios n Brute Force Attack on an individual account n Why? n n The account/user id is known n Only need to guess the password n Problems n Strength of the Password n Length, Casing, Special characters and numeric values n Many institutions use some type of “lock out” strategy n Can significantly increase time to crack account
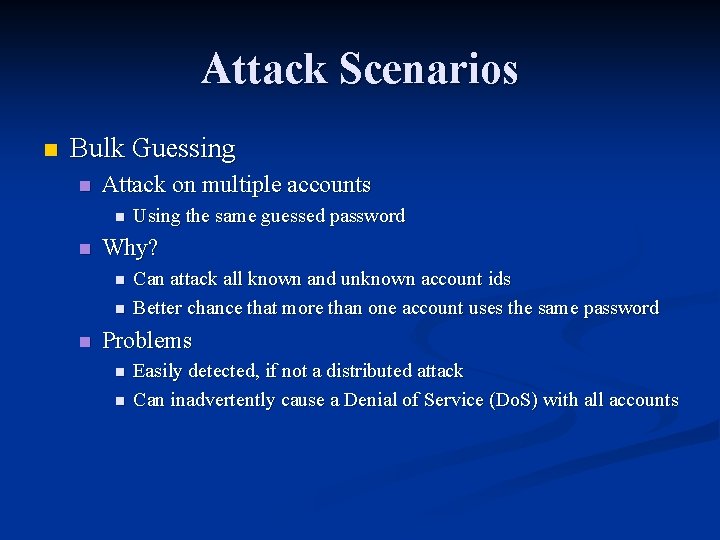
Attack Scenarios n Bulk Guessing n Attack on multiple accounts n n Why? n n n Using the same guessed password Can attack all known and unknown account ids Better chance that more than one account uses the same password Problems n n Easily detected, if not a distributed attack Can inadvertently cause a Denial of Service (Do. S) with all accounts
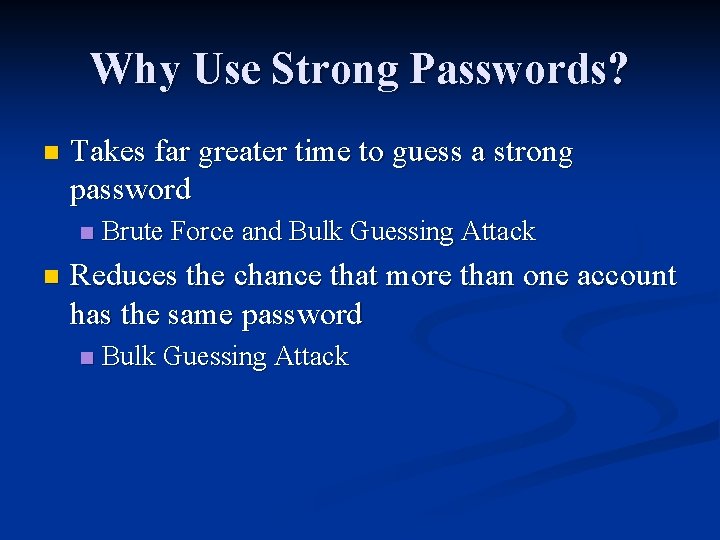
Why Use Strong Passwords? n Takes far greater time to guess a strong password n n Brute Force and Bulk Guessing Attack Reduces the chance that more than one account has the same password n Bulk Guessing Attack
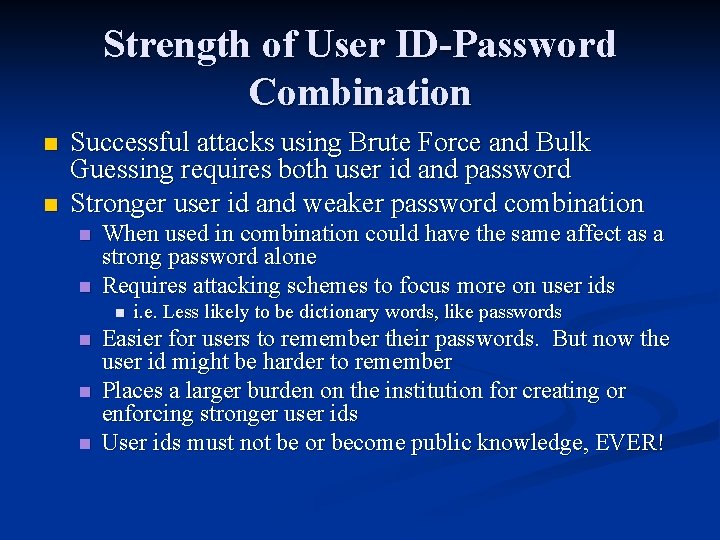
Strength of User ID-Password Combination n n Successful attacks using Brute Force and Bulk Guessing requires both user id and password Stronger user id and weaker password combination n n When used in combination could have the same affect as a strong password alone Requires attacking schemes to focus more on user ids n n i. e. Less likely to be dictionary words, like passwords Easier for users to remember their passwords. But now the user id might be harder to remember Places a larger burden on the institution for creating or enforcing stronger user ids User ids must not be or become public knowledge, EVER!
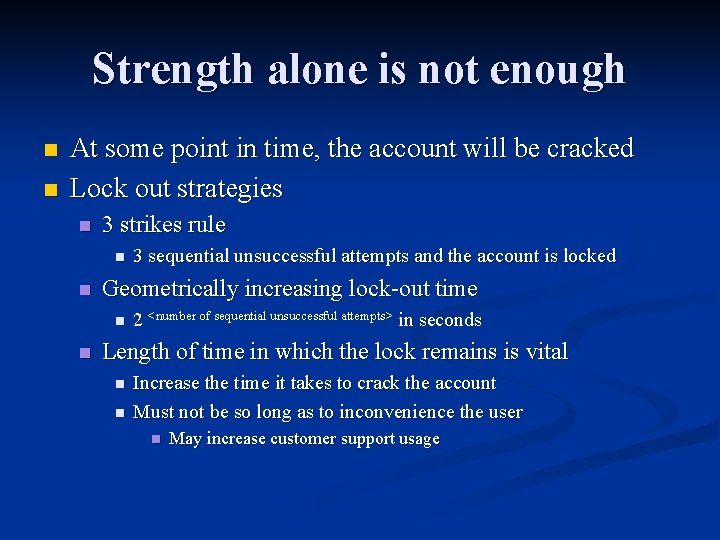
Strength alone is not enough n n At some point in time, the account will be cracked Lock out strategies n 3 strikes rule n n Geometrically increasing lock-out time n n 3 sequential unsuccessful attempts and the account is locked 2 <number of sequential unsuccessful attempts> in seconds Length of time in which the lock remains is vital n n Increase the time it takes to crack the account Must not be so long as to inconvenience the user n May increase customer support usage
Conclusions Makes attacking more difficult n User id or the process of user id creation is more likely to be public knowledge than your password n Most effective when some type of lock out strategy is being used n Not just for web, but for everything where a password is used n
- Slides: 14