Intrusion Detection Systems Network Intrusion Detection System NIDS
- Slides: 14
Intrusion Detection Systems ● Network Intrusion Detection System – NIDS ● Host-based Intrusion Detection System – HIDS ● Intrusion Prevention/Protection System – IPS ● IDS Service Centers ● System Logs
Network Intrusion Detection ● ● Open Source NIDS – Snort - www. snort. org – Bro - www. icir. org/vern/bro. html Commercial NIDS – ISS Real. Secure Network Sensor - www. iss. net – Intrusion Inc. Secure. Net Sensorwww. intrusion. com – Still. Secure Border Guard - www. stillsecure. com
Host Intrusion Detection ● ● Open Source HIDS – Samhain – la-samhna. de/samhain – LIDS - www. lids. org – AIDE - www. cs. tut. fi/~rammer/aide. html Commercial HIDS – Tripwire - www. tripwire. com – e. Eye Blink - www. eeye. com – Symantec Host IDS - www. symantec. com
Intrusion Prevention/Protection ● Open Source IPS – ● Lak-IPS - lak-ips. sourceforge. net Commercial IPS – ISS Preventia - www. iss. net – Fore. Scout Active Scout - www. forescout. com – Netscreen IDP - www. netscreen. com – Mc. Afee Intru. Shield www. networkassociates. com
IDS Service Centers ● Mynetwatchman - www. mynetwatchman. com ● DShield - www. dshield. org ● Internet Storm Center - isc. sans. org
System Logs ● Firewall logs ● Audit logs ● System logs ● TCP wrappers logs ● Web server logs ● SMTP server logs ● FTP server logs
Snort NIDS ● Open Source ● Home page - www. snort. org ● Supports UNIX and Windows ● Requires packet capturing library libpcap. ● Signature based ● Has many frontends and plugins
Building Snort ● Build libpcap if require. ● Obtain source code from www. snort. org. ● Unpack source tar ball. ● $. /configure ● $ make install ● Binary installs in /usr/loca/bin/snort.
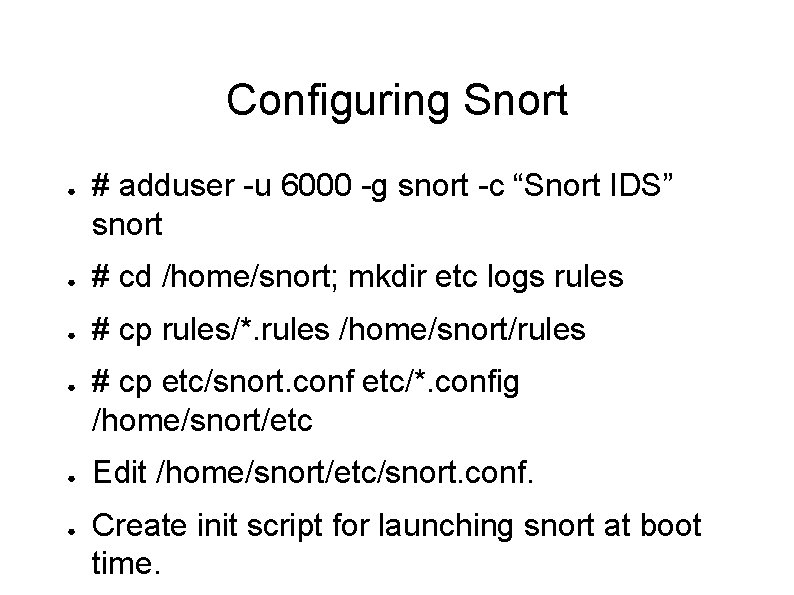
Configuring Snort ● # adduser -u 6000 -g snort -c “Snort IDS” snort ● # cd /home/snort; mkdir etc logs rules ● # cp rules/*. rules /home/snort/rules ● ● ● # cp etc/snort. conf etc/*. config /home/snort/etc Edit /home/snort/etc/snort. conf. Create init script for launching snort at boot time.
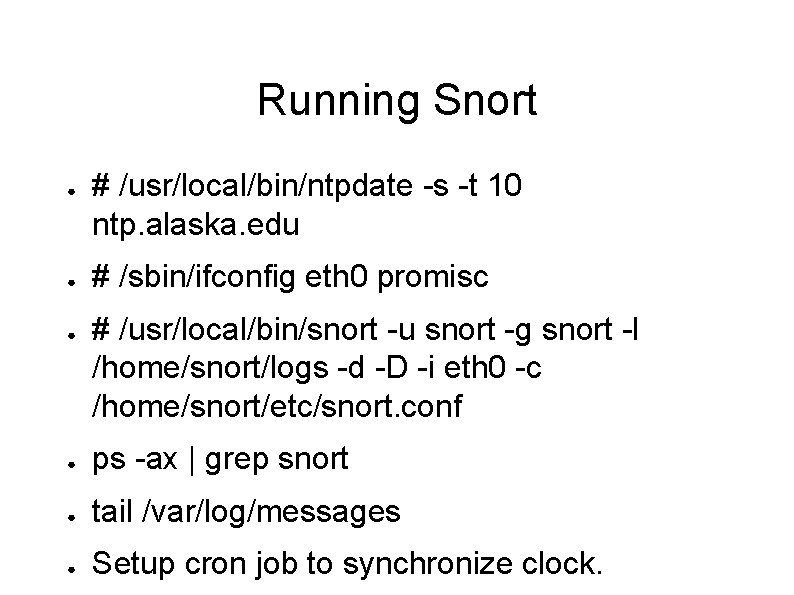
Running Snort ● ● ● # /usr/local/bin/ntpdate -s -t 10 ntp. alaska. edu # /sbin/ifconfig eth 0 promisc # /usr/local/bin/snort -u snort -g snort -l /home/snort/logs -d -D -i eth 0 -c /home/snort/etc/snort. conf ● ps -ax | grep snort ● tail /var/log/messages ● Setup cron job to synchronize clock.
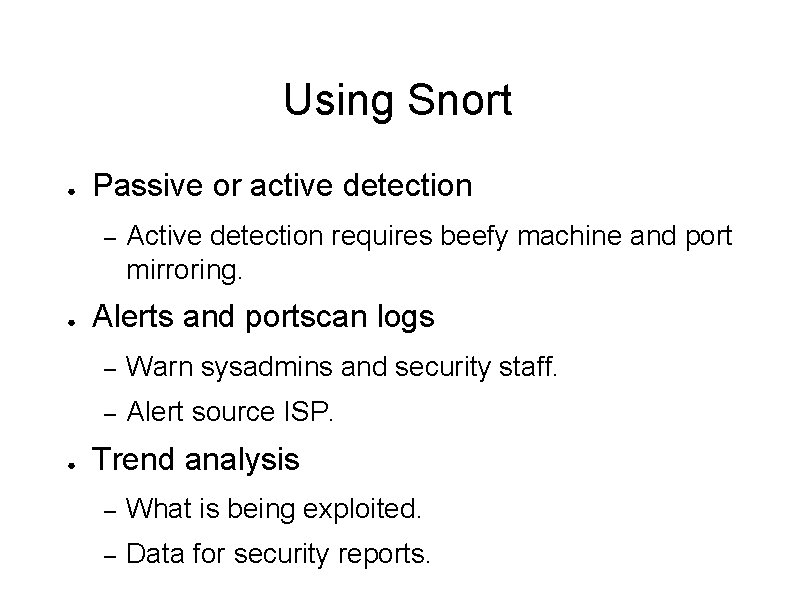
Using Snort ● Passive or active detection – ● ● Active detection requires beefy machine and port mirroring. Alerts and portscan logs – Warn sysadmins and security staff. – Alert source ISP. Trend analysis – What is being exploited. – Data for security reports.
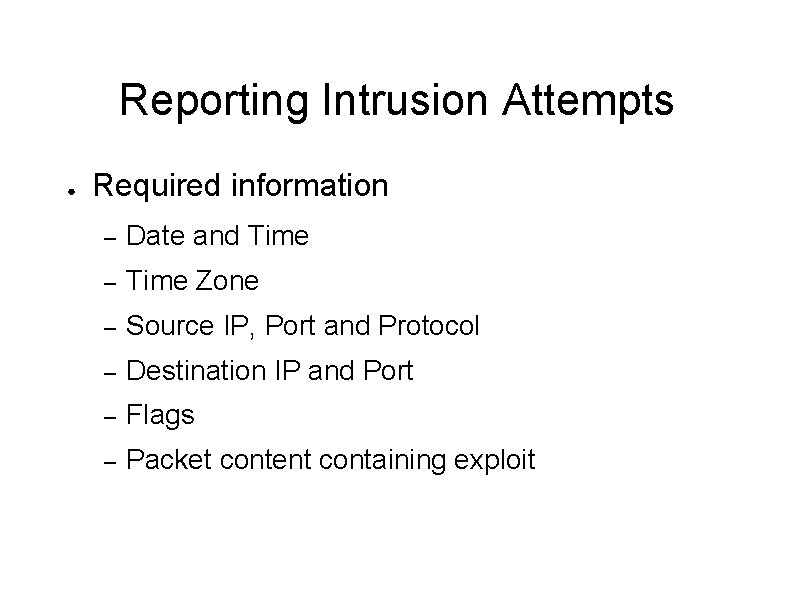
Reporting Intrusion Attempts ● Required information – Date and Time – Time Zone – Source IP, Port and Protocol – Destination IP and Port – Flags – Packet content containing exploit
Whom to Report ● Search whois database – whois. arin. net (North America & Academia) – whois. ripe. net (Europe, Middle East & Africa) – whois. apnic. net (Asia Pacific) – ● whois. krnic. net (South Korea) ● whois. nic. ad. jp (Japan) ● whois. twnic. net (Taiwan) whois. lacnic. net (Latin America) ● whois. nic. br (Brazil)
Questions and Comments ● Questions and comments about IDS/IPS ● Questions and comments about Snort.