Intrusion Tolerance The Killer App for BFT Alysson
Intrusion Tolerance: The Killer App for BFT (? ) Alysson Bessani, Miguel Correia, Paulo Sousa, Nuno Ferreira Neves, Paulo Veríssimo Universidade de Lisboa, Faculdade de Ciências Workshop on Theory and Practice of BFT 3 W'09 1
The Promise of BFT • From the abstract of Castro & Liskov OSDI’ 99 paper: “We believe that Byzantine fault-tolerant algorithms will be increasingly important in the future because malicious attacks and software errors are increasingly common and can cause faulty nodes to exhibit arbitrary behavior. ” BFT 3 W'09 2
The Promise of BFT Our claim: • BFT can be used to tolerate certain accidental value faults But there are simpler techniques to do that • The real appeal of the technique is to tolerate attacks, intrusions and bugs BFT → Intrusion Tolerance BFT 3 W'09 3
Intrusion Tolerance • Coined by Joni Fraga and David Powell “A Fault- and Intrusion-Tolerant File System”, IFIP SEC, 1985 • An intrusion-tolerant system can maintain its security properties (confidentiality, integrity and availability) despite some of its components being compromised. • Appeal: since it’s impossible to prove that a system has no vulnerabilities, it is more safe to assume that intrusions can happen. BFT 3 W'09 4
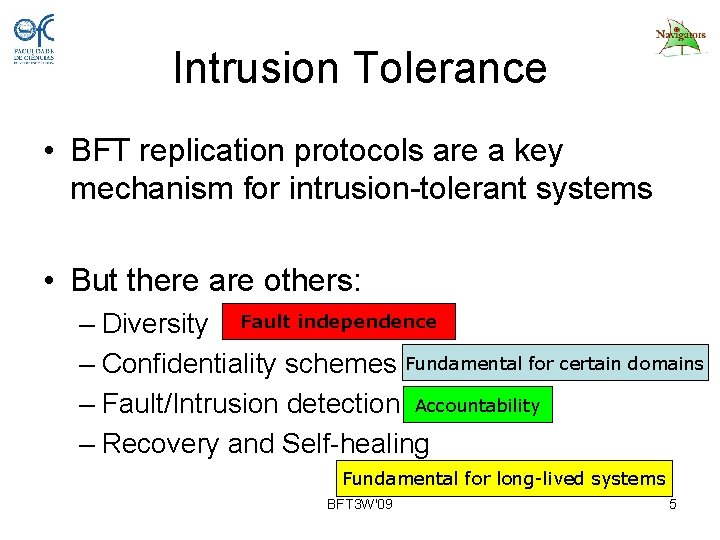
Intrusion Tolerance • BFT replication protocols are a key mechanism for intrusion-tolerant systems • But there are others: – Diversity Fault independence – Confidentiality schemes Fundamental for certain domains – Fault/Intrusion detection Accountability – Recovery and Self-healing Fundamental for long-lived systems BFT 3 W'09 5
Intrusion Tolerance • The resulting system is very COMPLEX! • There comes the In. Tol dilemma: – Complex systems tend to have more vulnerabilities and be more prone to configuration errors – So, an intrusion-tolerant system build to be more secure, tend to be less secure… BFT 3 W'09 6
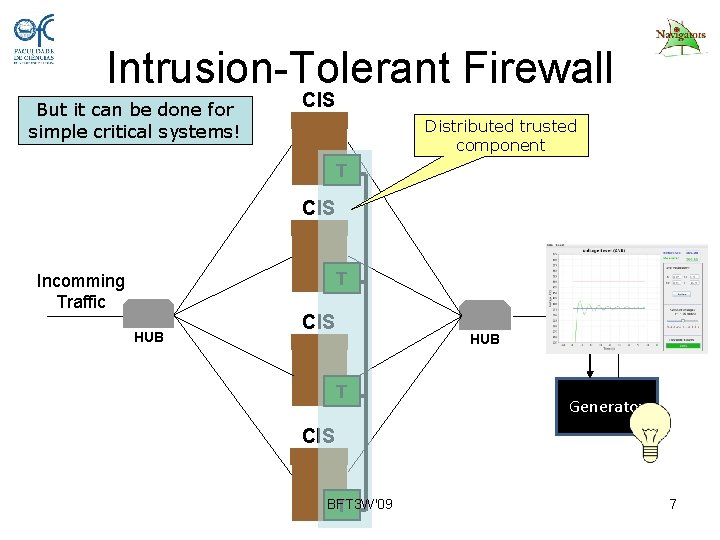
Intrusion-Tolerant Firewall But it can be done for simple critical systems! CIS Distributed trusted component T CIS T Incomming Traffic HUB CIS x = d. P(V, f)/dt Controller HUB T Generator CIS BFT 3 W'09 T 7
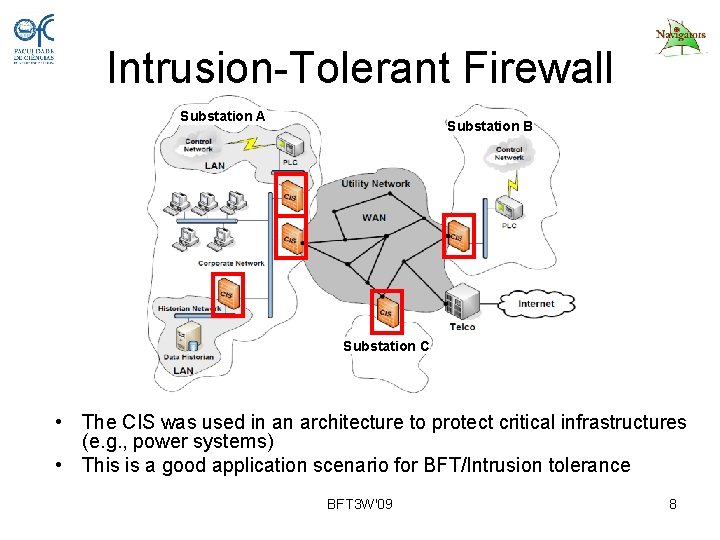
Intrusion-Tolerant Firewall Substation A Substation B Substation C • The CIS was used in an architecture to protect critical infrastructures (e. g. , power systems) • This is a good application scenario for BFT/Intrusion tolerance BFT 3 W'09 8
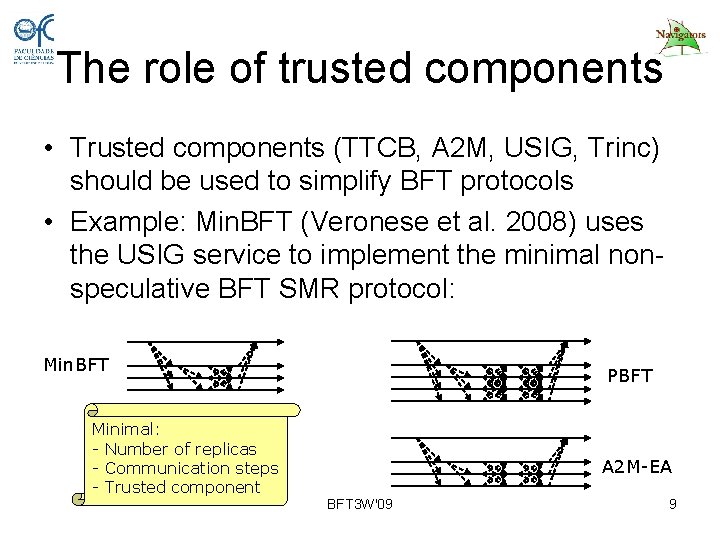
The role of trusted components • Trusted components (TTCB, A 2 M, USIG, Trinc) should be used to simplify BFT protocols • Example: Min. BFT (Veronese et al. 2008) uses the USIG service to implement the minimal nonspeculative BFT SMR protocol: Min. BFT Minimal: - Number of replicas - Communication steps - Trusted component PBFT A 2 M-EA BFT 3 W'09 9
Concerns for BFT/IT Adoption • BFT Usefulness • BFT Implementations • BFT Abstractions BFT 3 W'09 10
BFT Added Value • The key challenge: “How to show that an intrusion tolerant service is more secure than a non-intrusion-tolerant counterpart? ” • The equivalent question: “How to measure the security of a system? ” BFT 3 W'09 11
BFT Systems • We need at least one stable and robust BFT replication lib! • JBP (Java Byzantine Paxos) – Under development since 2007 for use on the replication layer of Dep. Space – Peak throughput competitive to PBFT (~22 Kop/s*) – Key concerns on the current version: • Modularity is a top priority: scalable communication, total order multicast, Byzantine paxos consensus and checkpoint • Avoid optimizations that bring complexity (e. g. , authenticators, agreement over message hashes) BFT 3 W'09 12
BFT Abstractions BFT ≠ BFT State Machine Replication BFT 3 W'09 13
BFT Abstractions • SMR has its limitations: – CFT systems are usually based on primarybackup – Most modern services do not employ consensus protocol on their critical path • What options? – High-level abstractions – Low-level abstractions BFT 3 W'09 14
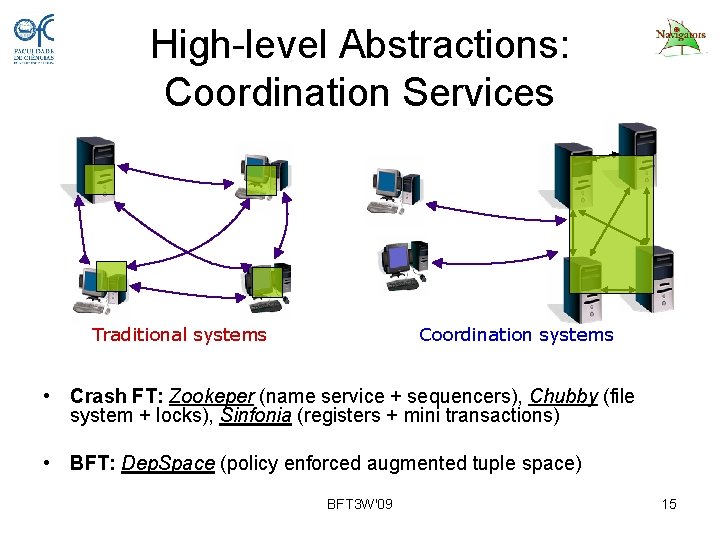
High-level Abstractions: Coordination Services Traditional systems Coordination systems • Crash FT: Zookeper (name service + sequencers), Chubby (file system + locks), Sinfonia (registers + mini transactions) • BFT: Dep. Space (policy enforced augmented tuple space) BFT 3 W'09 15
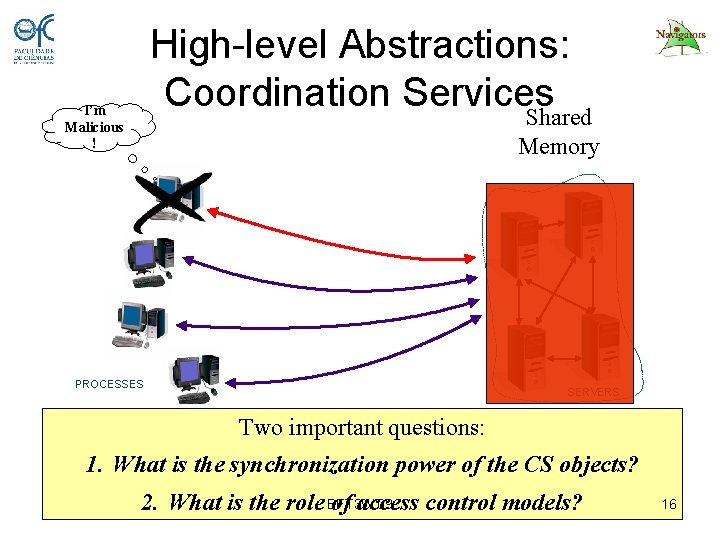
High-level Abstractions: Coordination Services Shared I’m Malicious ! Memory PROCESSES SERVERS Two important questions: 1. What is the synchronization power of the CS objects? 2. What is the role BFT 3 W'09 of access control models? 16
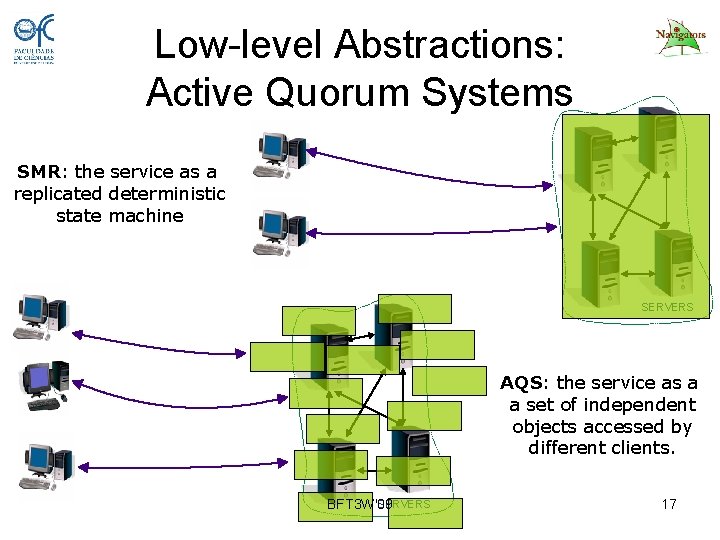
Low-level Abstractions: Active Quorum Systems SMR: the service as a replicated deterministic state machine SERVERS AQS: the service as a a set of independent objects accessed by different clients. SERVERS BFT 3 W'09 17
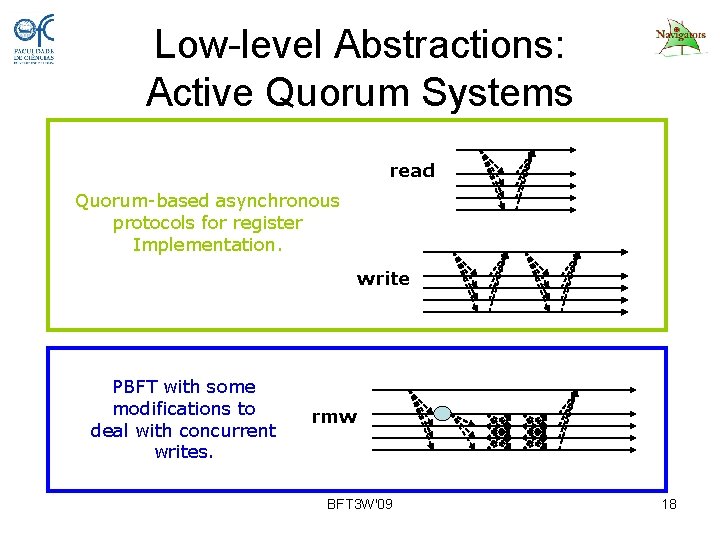
Low-level Abstractions: Active Quorum Systems read Quorum-based asynchronous protocols for register Implementation. write PBFT with some modifications to deal with concurrent writes. rmw BFT 3 W'09 18
Low-level Abstractions: Active Quorum Systems • Is it useful? Some services: – LDAP: • Main AQS Object: LDAP Entry • Only Entry creation and removal require rmw – Smart block storage: • Main AQS Object: Data Block • Uses rmw to modify single bytes of large blocks – Tuple Space: • Main AQS Object: Tuple • Only tuple removal uses rmw BFT 3 W'09 19
Summary • The promise of BFT: tolerate intrusions – Can be done for simple services – Require other mechanisms • Concerns to be addressed: – How to show the improved security of BFT/intrusion tolerant systems? – Build a stable and robust BFT library – BFT is not SMR: • Coordination Services • Active Quorum Systems BFT 3 W'09 20
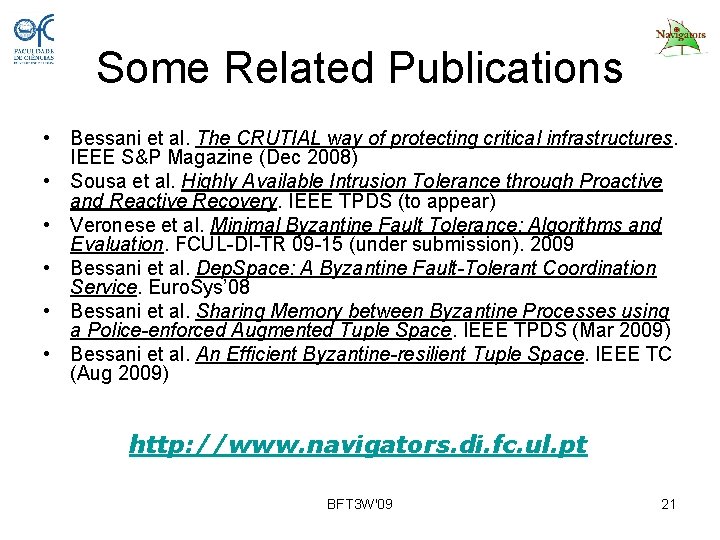
Some Related Publications • Bessani et al. The CRUTIAL way of protecting critical infrastructures. IEEE S&P Magazine (Dec 2008) • Sousa et al. Highly Available Intrusion Tolerance through Proactive and Reactive Recovery. IEEE TPDS (to appear) • Veronese et al. Minimal Byzantine Fault Tolerance: Algorithms and Evaluation. FCUL-DI-TR 09 -15 (under submission). 2009 • Bessani et al. Dep. Space: A Byzantine Fault-Tolerant Coordination Service. Euro. Sys’ 08 • Bessani et al. Sharing Memory between Byzantine Processes using a Police-enforced Augmented Tuple Space. IEEE TPDS (Mar 2009) • Bessani et al. An Efficient Byzantine-resilient Tuple Space. IEEE TC (Aug 2009) http: //www. navigators. di. fc. ul. pt BFT 3 W'09 21
- Slides: 21