TEMA Intrusion Detection EBITEMA TEMA Intrusion Detection Temaline

TEMA Intrusion Detection EBI-TEMA
TEMA Intrusion Detection Temaline Intrusion Detection Module EBI-TEMA
TEMA Intrusion Detection Temaline Intrusion Detection Module The Module is an option integrated into the Temaline Interface subsystem. It is used for the configuration, via the Temaline Interface's displays (EBI), of ID (Intrusion Detection) Tema. Servers, which are used for the management of the intrusion detection peripheral devices, i. e. detectors, actuators, and all man-machine interface's peripheral devices. The option is enabled through the Tema License, not through the EBI License. EBI-TEMA
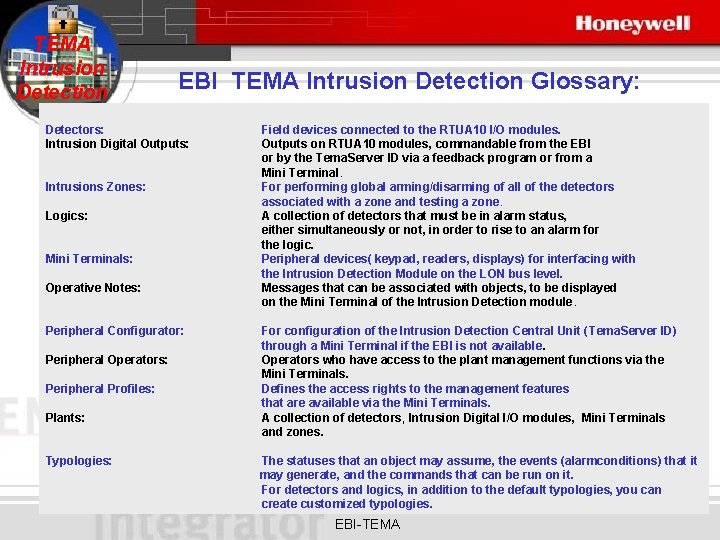
TEMA Intrusion Detection EBI TEMA Intrusion Detection Glossary: Detectors: Intrusion Digital Outputs: Intrusions Zones: Logics: Mini Terminals: Operative Notes: Peripheral Configurator: Peripheral Operators: Peripheral Profiles: Plants: Typologies: Field devices connected to the RTUA 10 I/O modules. Outputs on RTUA 10 modules, commandable from the EBI or by the Tema. Server ID via a feedback program or from a Mini Terminal. For performing global arming/disarming of all of the detectors associated with a zone and testing a zone. A collection of detectors that must be in alarm status, either simultaneously or not, in order to rise to an alarm for the logic. Peripheral devices( keypad, readers, displays) for interfacing with the Intrusion Detection Module on the LON bus level. Messages that can be associated with objects, to be displayed on the Mini Terminal of the Intrusion Detection module. For configuration of the Intrusion Detection Central Unit (Tema. Server ID) through a Mini Terminal if the EBI is not available. Operators who have access to the plant management functions via the Mini Terminals. Defines the access rights to the management features that are available via the Mini Terminals. A collection of detectors, Intrusion Digital I/O modules, Mini Terminals and zones. The statuses that an object may assume, the events (alarmconditions) that it may generate, and the commands that can be run on it. For detectors and logics, in addition to the default typologies, you can create customized typologies. EBI-TEMA
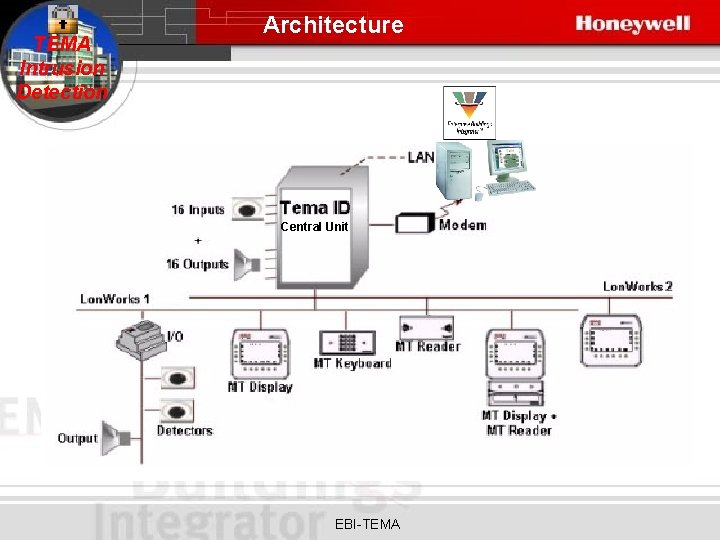
TEMA Intrusion Detection Architecture Central Unit EBI-TEMA
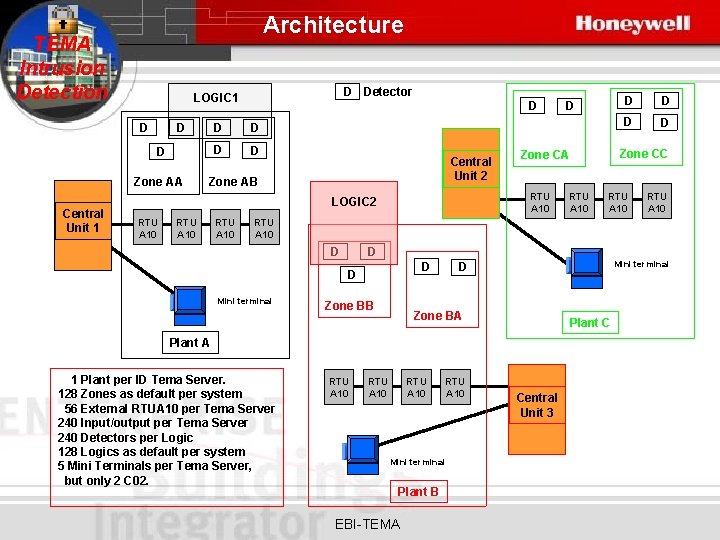
Architecture TEMA Intrusion Detection D D D Zone AA Central Unit 1 D Detector LOGIC 1 D D D Central Unit 2 Zone AB RTU A 10 D D Zone CC Zone CA RTU A 10 LOGIC 2 D RTU A 10 D D Mini terminal Zone BB Mini terminal D Zone BA Plant C Plant A 1 Plant per ID Tema Server. 128 Zones as default per system 56 External RTUA 10 per Tema Server 240 Input/output per Tema Server 240 Detectors per Logic 128 Logics as default per system 5 Mini Terminals per Tema Server, but only 2 C 02. RTU A 10 Mini terminal Plant B EBI-TEMA Central Unit 3

TEMA Intrusion Detection Hardware EBI-TEMA
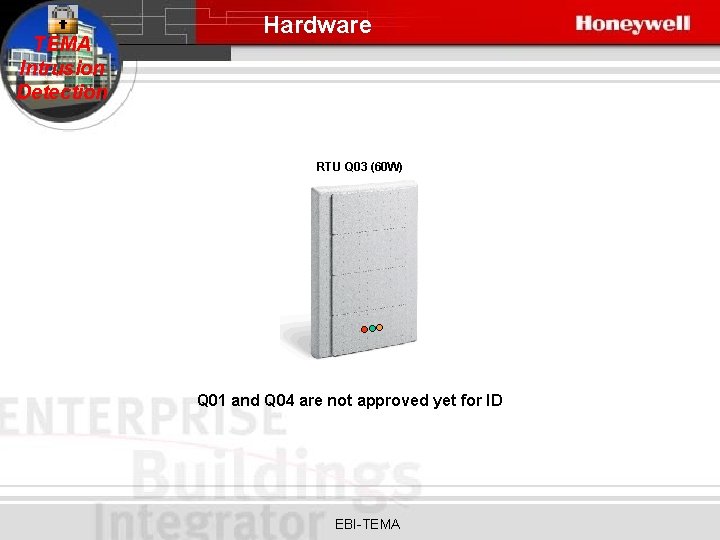
TEMA Intrusion Detection Hardware RTU Q 03 (60 W) Q 01 and Q 04 are not approved yet for ID EBI-TEMA
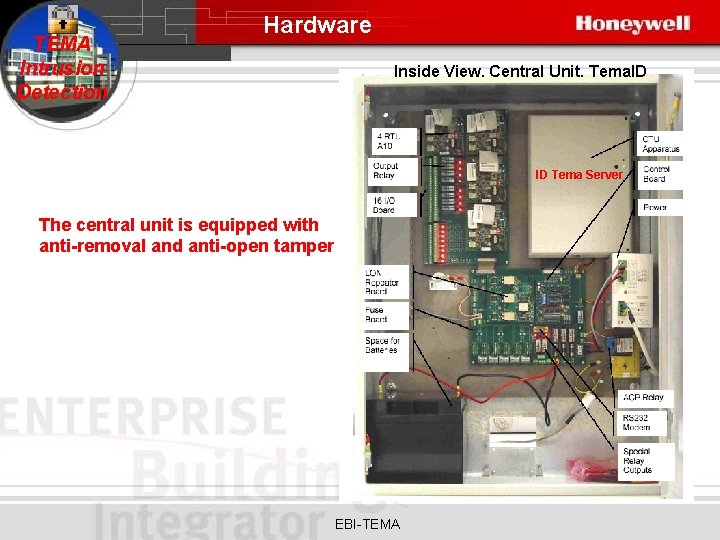
TEMA Intrusion Detection Hardware Inside View. Central Unit. Tema. ID ID Tema Server The central unit is equipped with anti-removal and anti-open tamper EBI-TEMA
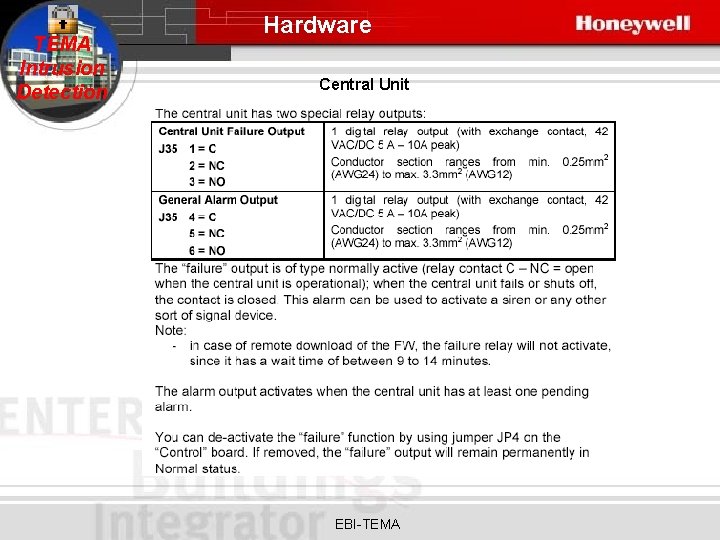
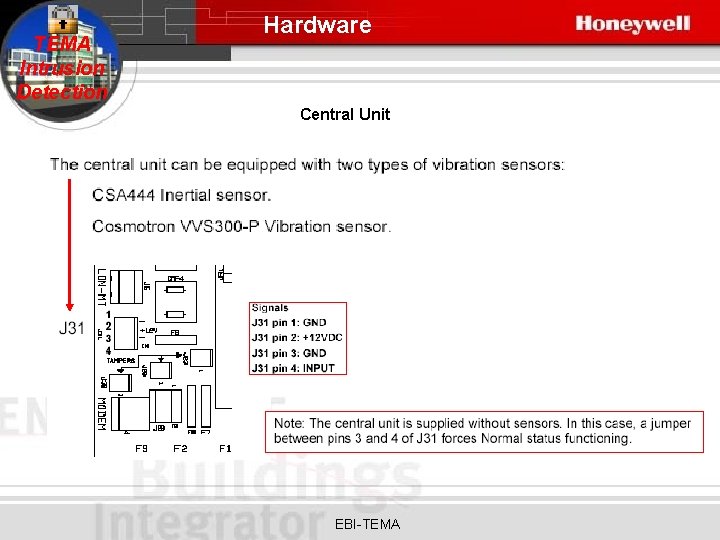
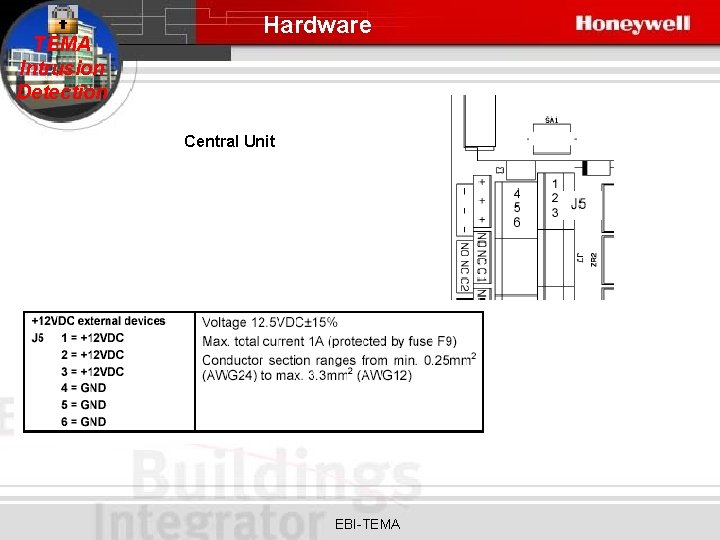
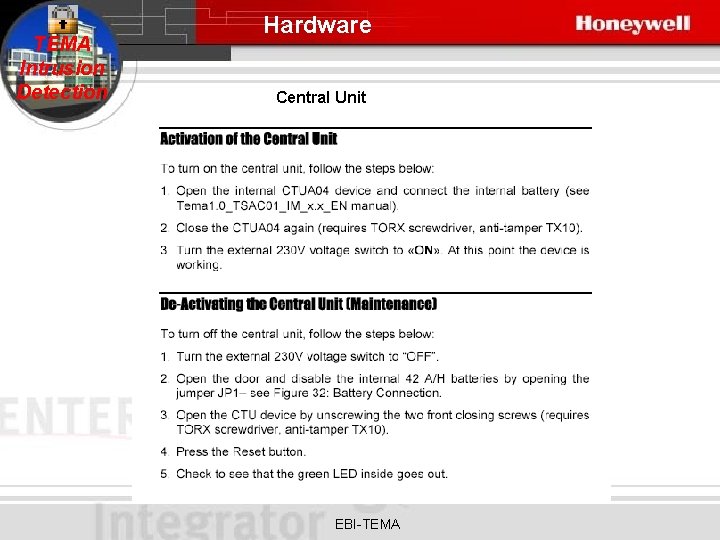
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
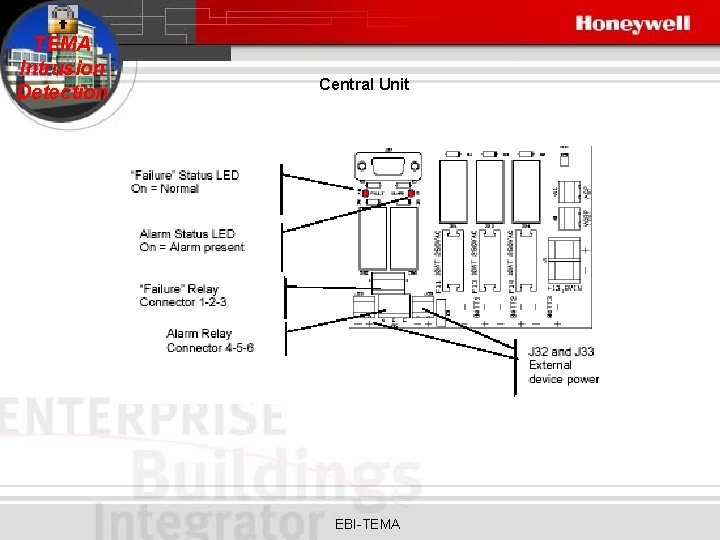
TEMA Intrusion Detection Central Unit EBI-TEMA
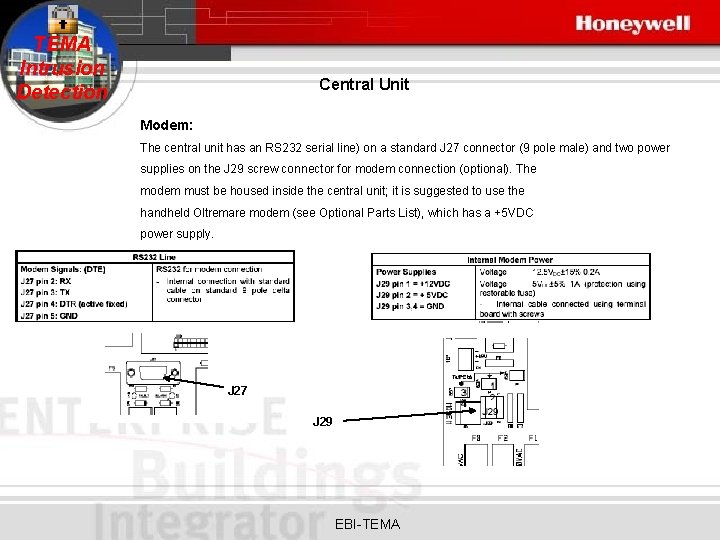
TEMA Intrusion Detection Central Unit Modem: The central unit has an RS 232 serial line) on a standard J 27 connector (9 pole male) and two power supplies on the J 29 screw connector for modem connection (optional). The modem must be housed inside the central unit; it is suggested to use the handheld Oltremare modem (see Optional Parts List), which has a +5 VDC power supply. J 27 J 29 EBI-TEMA
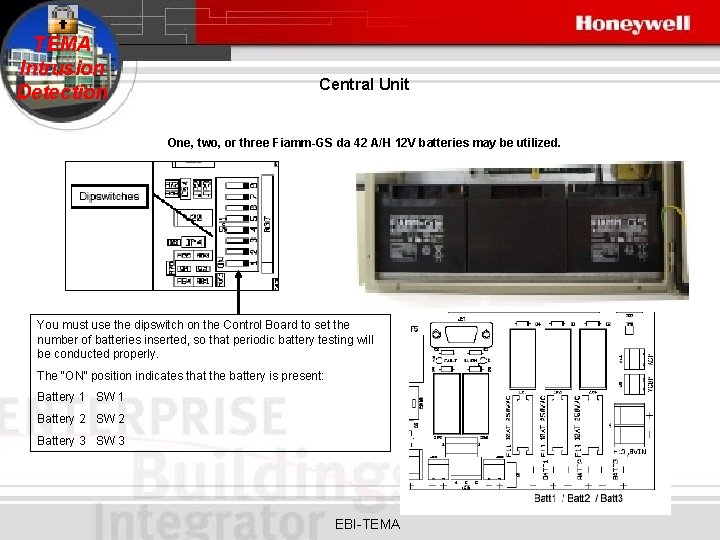
TEMA Intrusion Detection Central Unit One, two, or three Fiamm-GS da 42 A/H 12 V batteries may be utilized. You must use the dipswitch on the Control Board to set the number of batteries inserted, so that periodic battery testing will be conducted properly. The “ON” position indicates that the battery is present: Battery 1 SW 1 Battery 2 SW 2 Battery 3 SW 3 EBI-TEMA
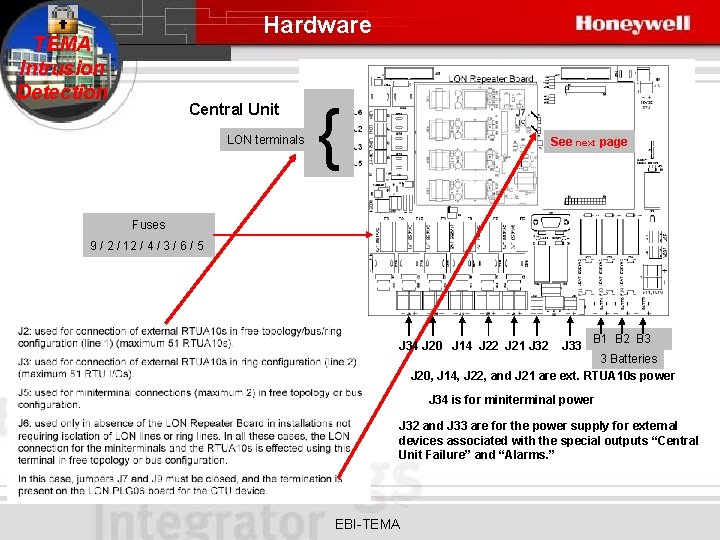
Hardware TEMA Intrusion Detection Central Unit LON terminals { See next page Fuses 9 / 2 / 12 / 4 / 3 / 6 / 5 J 34 J 20 J 14 J 22 J 21 J 32 J 33 B 1 B 2 B 3 3 Batteries J 20, J 14, J 22, and J 21 are ext. RTUA 10 s power J 34 is for miniterminal power J 32 and J 33 are for the power supply for external devices associated with the special outputs “Central Unit Failure” and “Alarms. ” EBI-TEMA
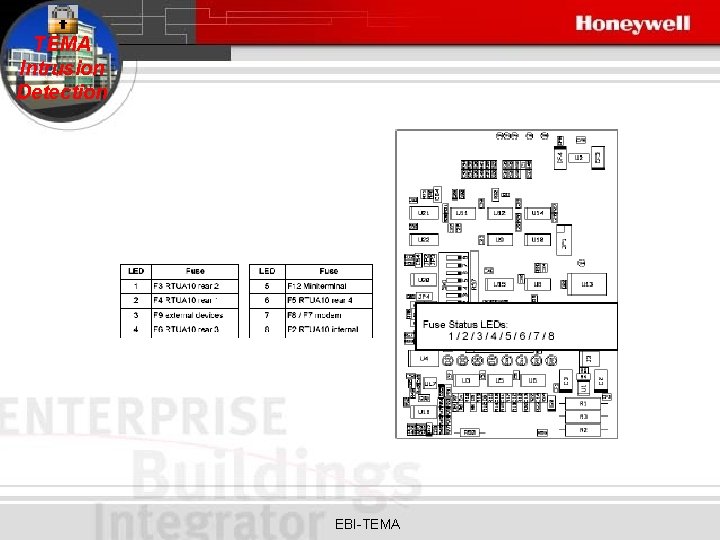
TEMA Intrusion Detection EBI-TEMA

Hardware TEMA Intrusion Detection Lon Daisy Chain Configuration Central Unit Note: JP 3 closed on LON Repeater Board JP 4 open on LON Repeater Board EBI-TEMA
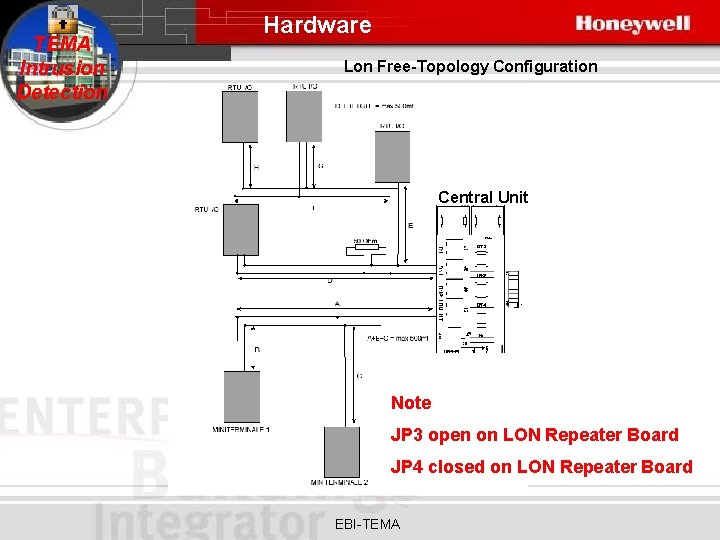
TEMA Intrusion Detection Hardware Lon Free-Topology Configuration Central Unit Note JP 3 open on LON Repeater Board JP 4 closed on LON Repeater Board EBI-TEMA
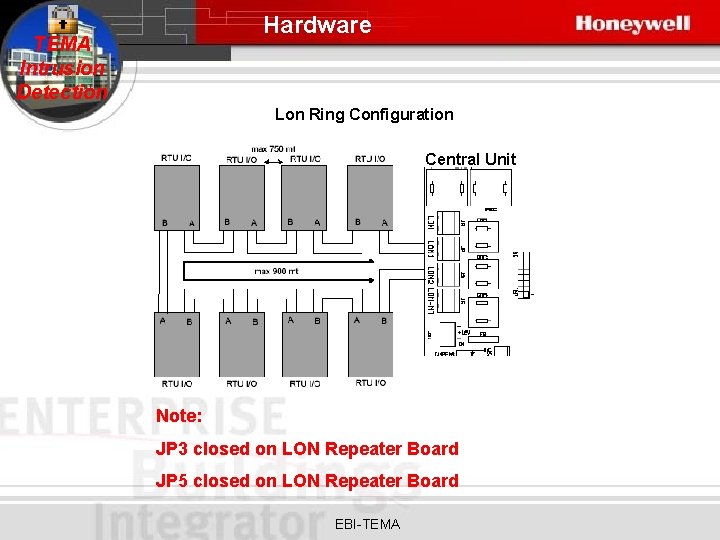
Hardware TEMA Intrusion Detection Lon Ring Configuration Central Unit Note: JP 3 closed on LON Repeater Board JP 5 closed on LON Repeater Board EBI-TEMA
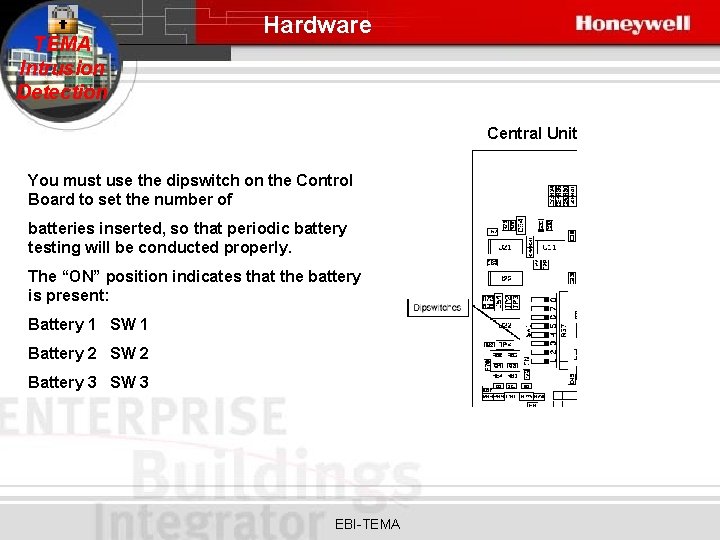
TEMA Intrusion Detection Hardware Central Unit You must use the dipswitch on the Control Board to set the number of batteries inserted, so that periodic battery testing will be conducted properly. The “ON” position indicates that the battery is present: Battery 1 SW 1 Battery 2 SW 2 Battery 3 SW 3 EBI-TEMA
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
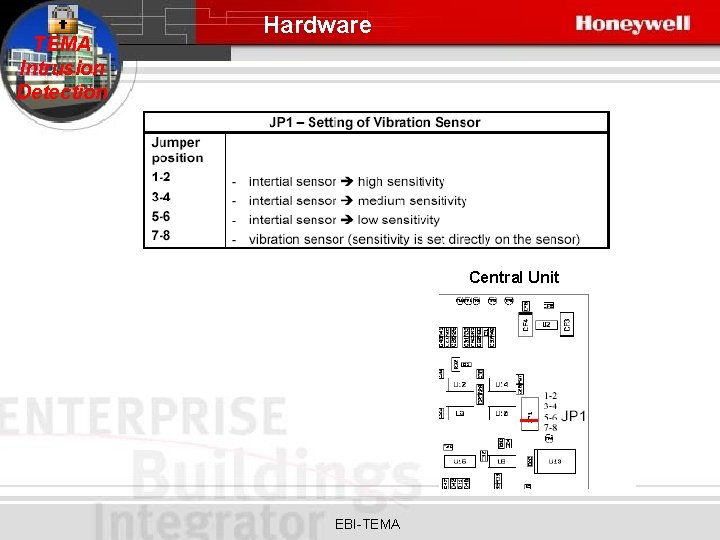
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
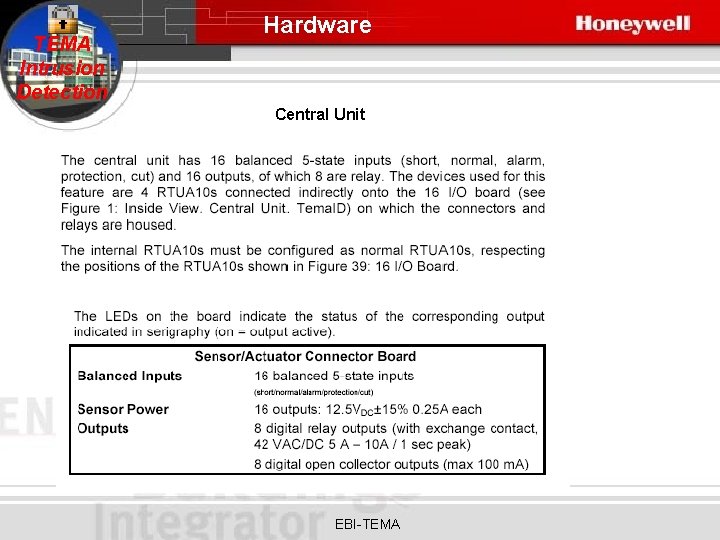
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
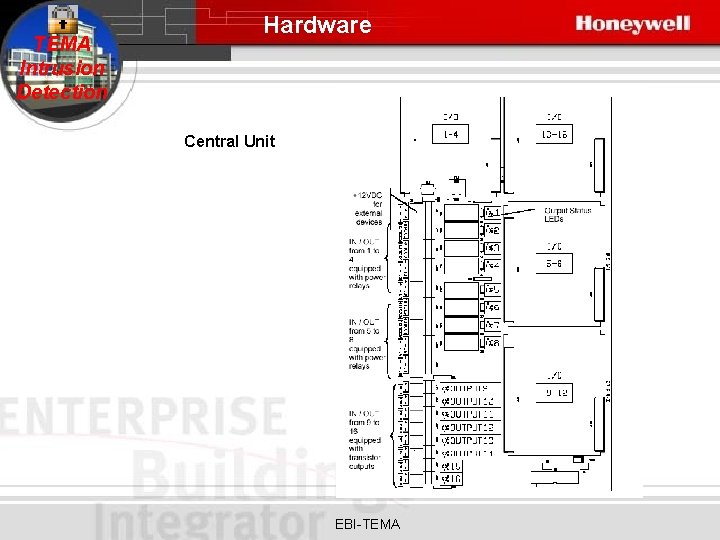
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
TEMA Intrusion Detection Hardware Central Unit EBI-TEMA
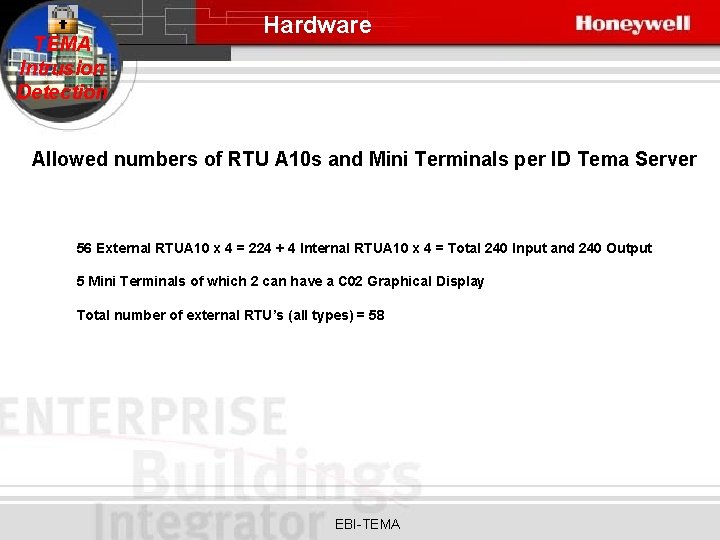
TEMA Intrusion Detection Hardware Allowed numbers of RTU A 10 s and Mini Terminals per ID Tema Server 56 External RTUA 10 x 4 = 224 + 4 Internal RTUA 10 x 4 = Total 240 Input and 240 Output 5 Mini Terminals of which 2 can have a C 02 Graphical Display Total number of external RTU’s (all types) = 58 EBI-TEMA
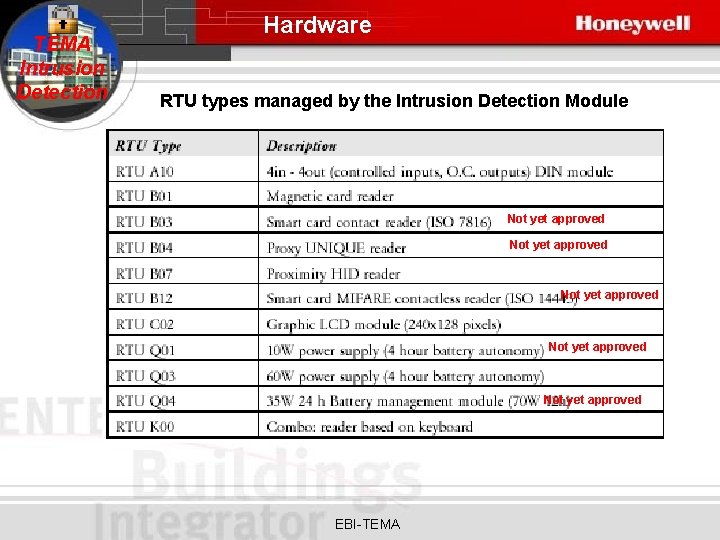
TEMA Intrusion Detection Hardware RTU types managed by the Intrusion Detection Module Not yet approved Not yet approved EBI-TEMA
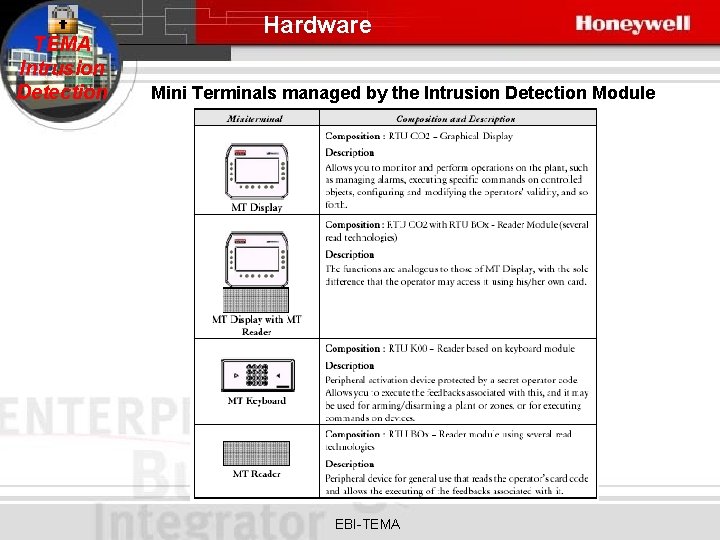
TEMA Intrusion Detection Hardware Mini Terminals managed by the Intrusion Detection Module EBI-TEMA
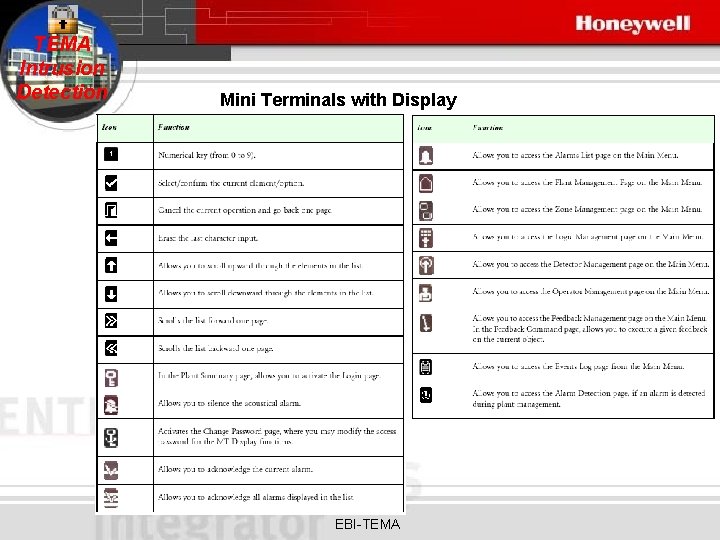
TEMA Intrusion Detection Mini Terminals with Display EBI-TEMA
TEMA Intrusion Detection RTUA 10 connections EBI-TEMA
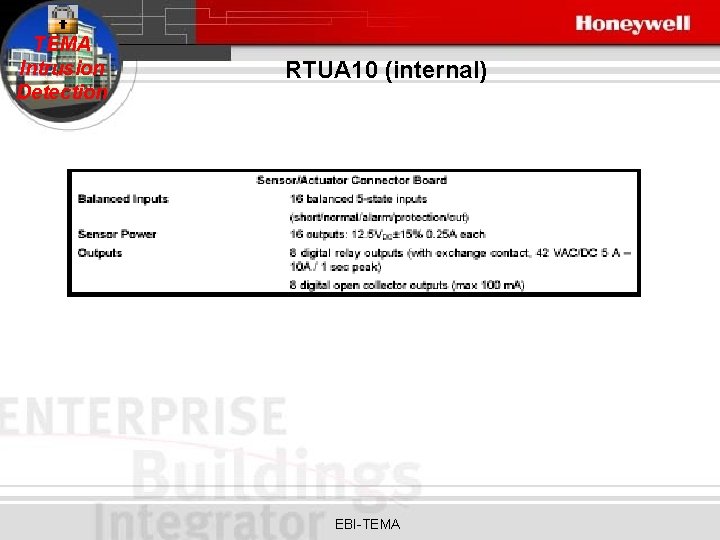
TEMA Intrusion Detection RTUA 10 (internal) EBI-TEMA
TEMA Intrusion Detection The internal RTUA 10 s must be configured as normal RTUA 10 s. RTUs have three leds as below: - Red Led = status for +12 V out sensors • ON = +12 V present (internal fuse working) • OFF = +12 V not present (internal fuse not working) - Green Led = Communication status between RTUA 10 and CTU: • ON = Communication OK • Blinking = Communication not present • OFF = Fail status - Yellow LED: [Lon. Works Service LED] • Off: normal status • Steady On: Neuron Chip without application and not configured • Blinking 0. 5 Hz: Neuron Chip in application status present, but not configured. Note: the LED also goes on as an indication of activation of the service PIN via internal button or via EBI “WINK” command EBI-TEMA
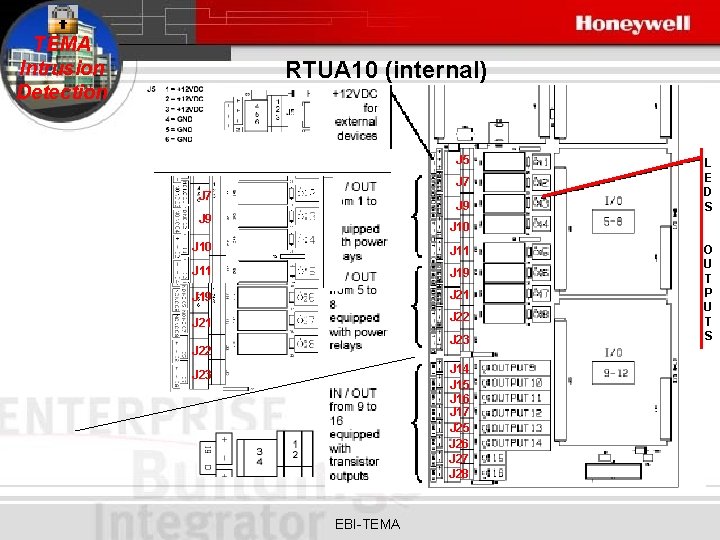
TEMA Intrusion Detection RTUA 10 (internal) J 5 J 7 J 9 L E D S J 10 J 11 J 19 J 21 J 22 J 23 J 22 J 14 J 15 J 16 J 17 J 25 J 26 J 27 J 28 J 23 EBI-TEMA O U T P U T S
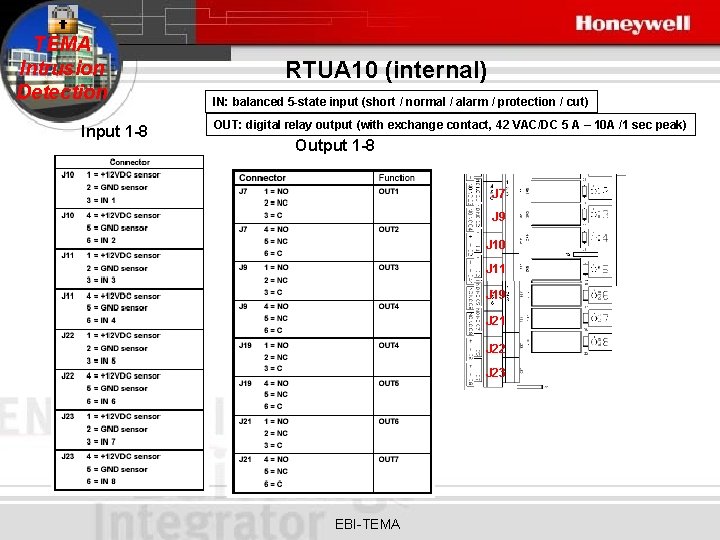
TEMA Intrusion Detection Input 1 -8 RTUA 10 (internal) IN: balanced 5 -state input (short / normal / alarm / protection / cut) OUT: digital relay output (with exchange contact, 42 VAC/DC 5 A – 10 A /1 sec peak) Output 1 -8 J 7 J 9 J 10 J 11 J 19 J 21 J 22 J 23 EBI-TEMA
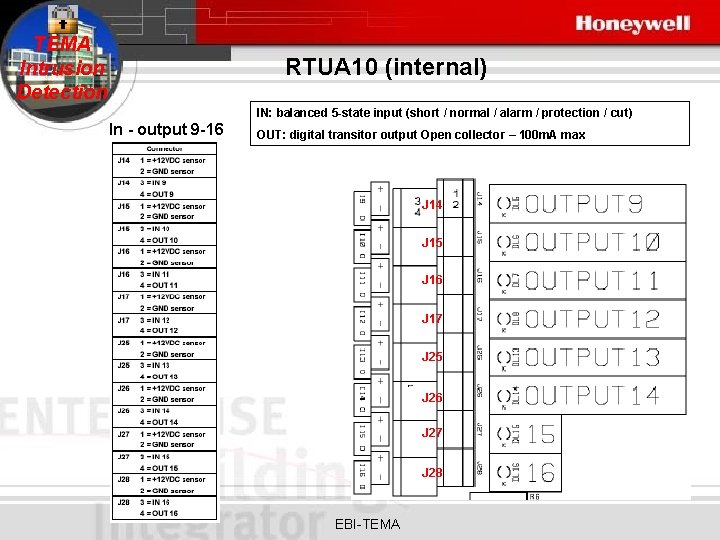
TEMA Intrusion Detection RTUA 10 (internal) IN: balanced 5 -state input (short / normal / alarm / protection / cut) In - output 9 -16 OUT: digital transitor output Open collector – 100 m. A max J 14 J 15 J 16 J 17 J 25 J 26 J 27 J 28 EBI-TEMA
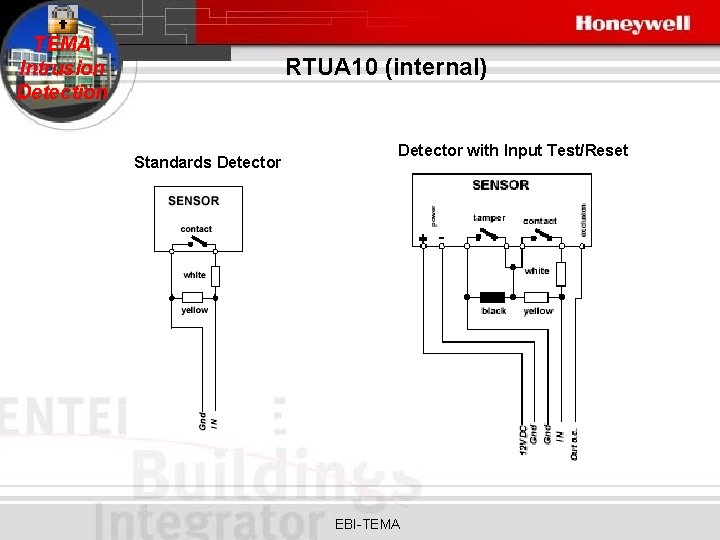
TEMA Intrusion Detection RTUA 10 (internal) Standards Detector with Input Test/Reset EBI-TEMA
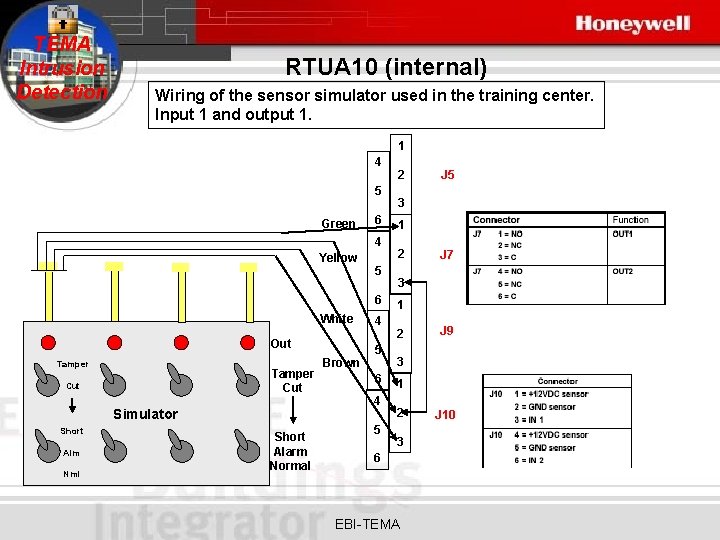
TEMA Intrusion Detection RTUA 10 (internal) Wiring of the sensor simulator used in the training center. Input 1 and output 1. 1 4 5 Green 6 4 Yellow 5 6 White Out Tamper Cut Simulator Short Alm Nml Short Alarm Normal Brown 4 5 6 4 5 2 J 5 3 1 2 J 7 3 1 2 J 9 3 1 2 3 6 EBI-TEMA J 10
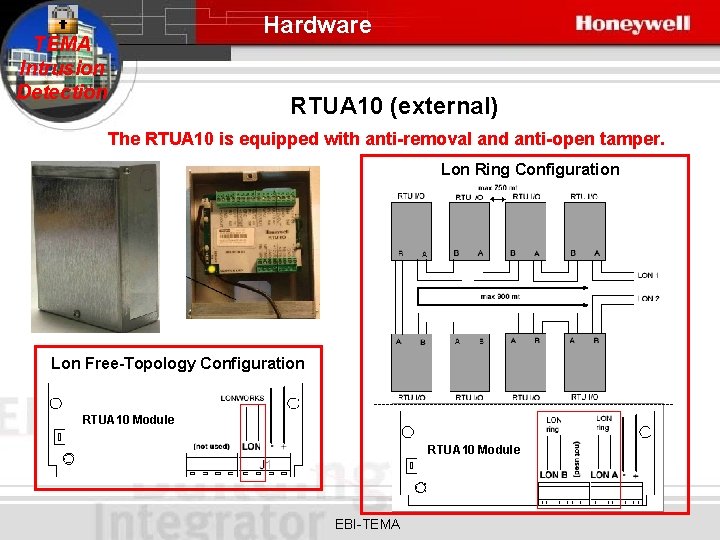
Hardware TEMA Intrusion Detection RTUA 10 (external) The RTUA 10 is equipped with anti-removal and anti-open tamper. Lon Ring Configuration Lon Free-Topology Configuration -------------------------------------RTUA 10 Module EBI-TEMA
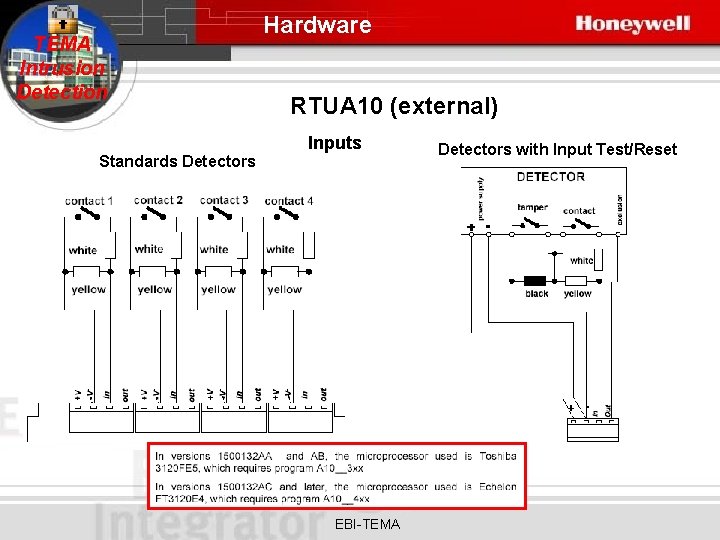
TEMA Intrusion Detection Standards Detectors Hardware RTUA 10 (external) Inputs EBI-TEMA Detectors with Input Test/Reset
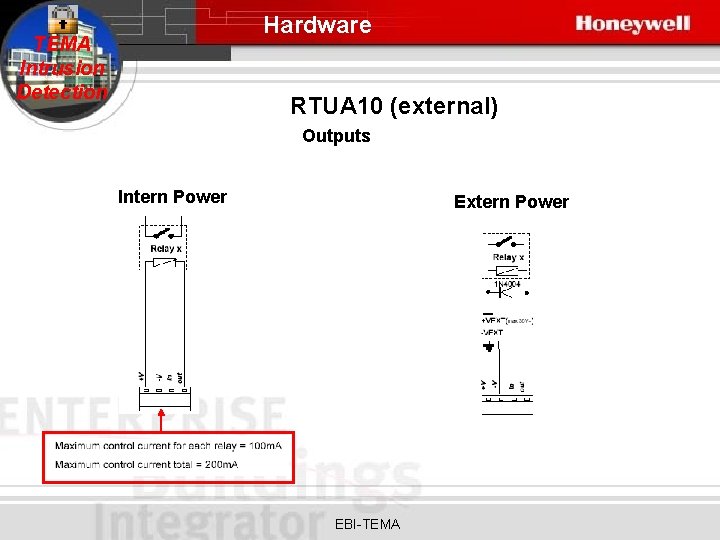
Hardware TEMA Intrusion Detection RTUA 10 (external) Outputs Intern Power Extern Power EBI-TEMA
TEMA Intrusion Detection Software components and Installation EBI-TEMA

TEMA Intrusion Detection Software and Installation Software components and Installation Windows 2000 Server or Windows 2000 Professionel Microsoft. NET Framework 1. 1 with SP 1(for the Temaline subsystem WEB modules) EBI 300. 1 with SP 1 EBI/TEMA 4. 5. 4. Server. Client. EBIR 300_1_Tema. Gen. Update_ver 4 (from the EBI homepage) ctu 45407. ID firmware for the Intrusion Detection Tema servers A EBI license without Access control, but with TEMA Interface. A Tema license with Intrusion detection enabled. RTFM EBI-TEMA
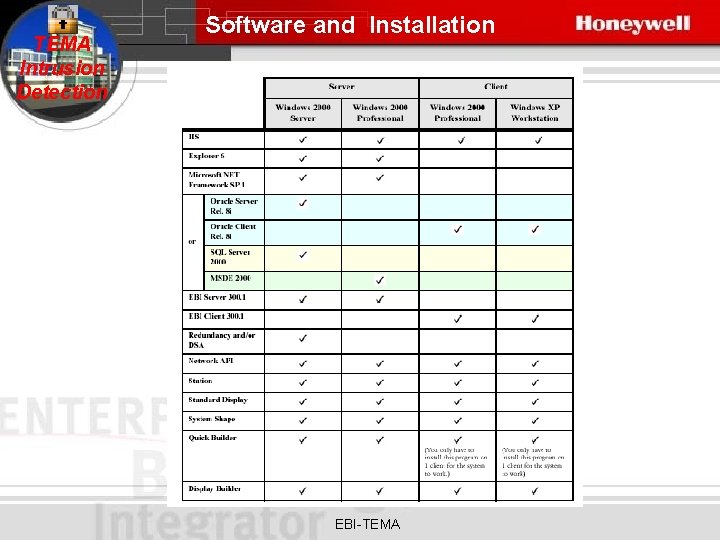
TEMA Intrusion Detection Software and Installation EBI-TEMA
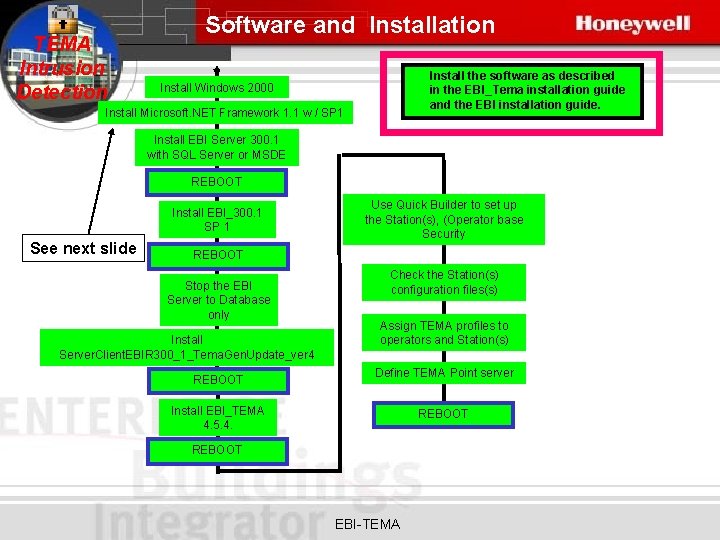
TEMA Intrusion Detection Software and Installation Install the software as described in the EBI_Tema installation guide and the EBI installation guide. Install Windows 2000 Install Microsoft. NET Framework 1. 1 w / SP 1 Install EBI Server 300. 1 with SQL Server or MSDE REBOOT Install EBI_300. 1 SP 1 See next slide Use Quick Builder to set up the Station(s), (Operator base Security REBOOT Stop the EBI Server to Database only Install Server. Client. EBIR 300_1_Tema. Gen. Update_ver 4 REBOOT Check the Station(s) configuration files(s) Assign TEMA profiles to operators and Station(s) Define TEMA Point server Install EBI_TEMA 4. 5. 4. REBOOT EBI-TEMA
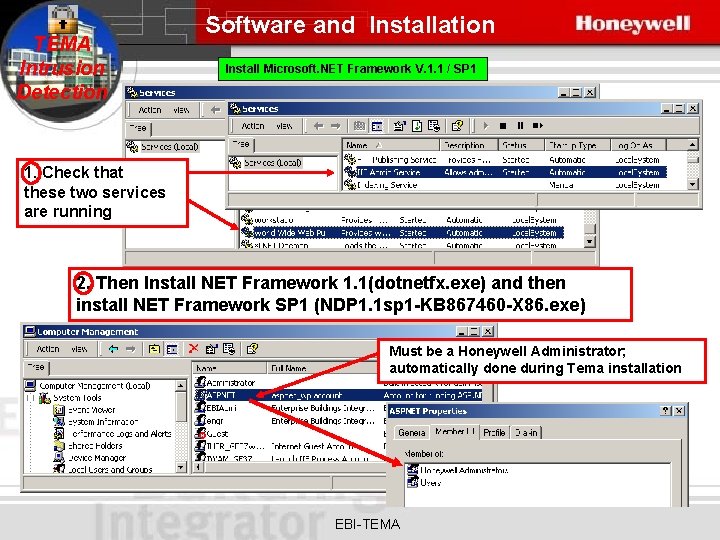
TEMA Intrusion Detection Software and Installation Install Microsoft. NET Framework V. 1. 1 / SP 1 1. Check that these two services are running 2. Then Install NET Framework 1. 1(dotnetfx. exe) and then install NET Framework SP 1 (NDP 1. 1 sp 1 -KB 867460 -X 86. exe) Must be a Honeywell Administrator; automatically done during Tema installation EBI-TEMA
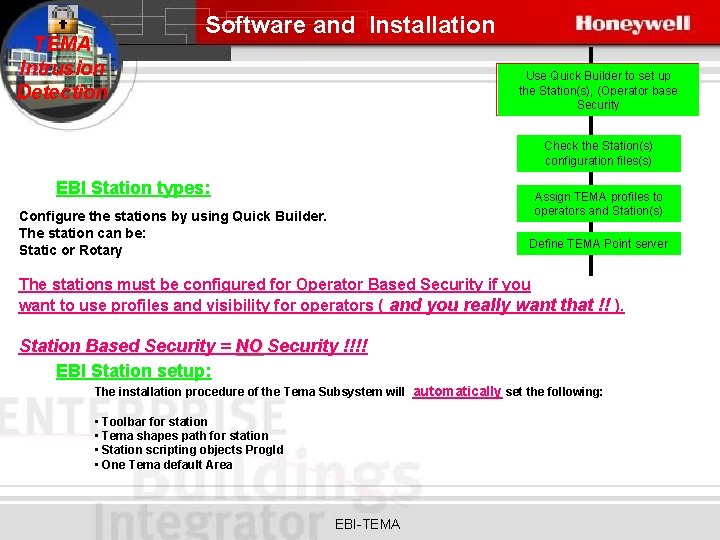
TEMA Intrusion Detection Software and Installation Use Quick Builder to set up the Station(s), (Operator base Security Check the Station(s) configuration files(s) EBI Station types: Assign TEMA profiles to operators and Station(s) Configure the stations by using Quick Builder. The station can be: Static or Rotary Define TEMA Point server The stations must be configured for Operator Based Security if you want to use profiles and visibility for operators ( and you really want that !! ). Station Based Security = NO Security !!!! EBI Station setup: The installation procedure of the Tema Subsystem will automatically set the following: • Toolbar for station • Tema shapes path for station • Station scripting objects Prog. Id • One Tema default Area EBI-TEMA
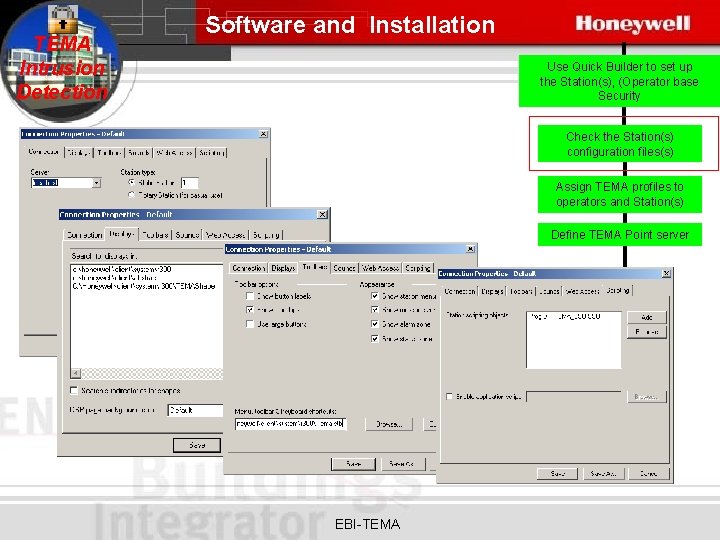
TEMA Intrusion Detection Software and Installation Use Quick Builder to set up the Station(s), (Operator base Security Check the Station(s) configuration files(s) Assign TEMA profiles to operators and Station(s) Define TEMA Point server EBI-TEMA
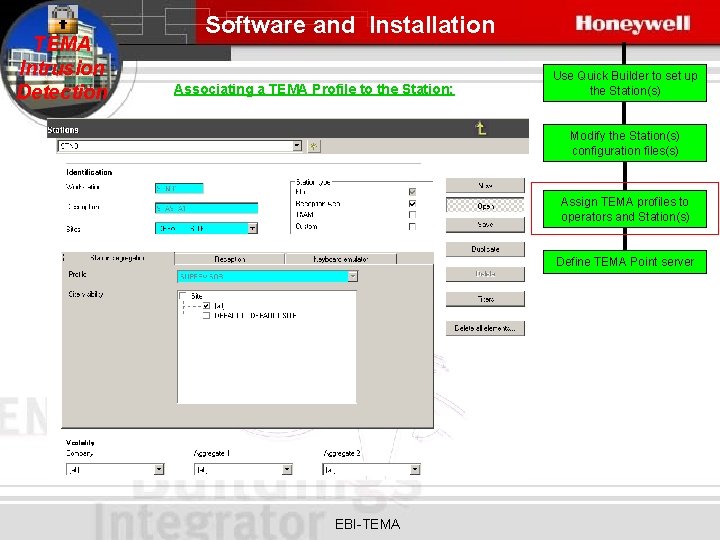
TEMA Intrusion Detection Software and Installation Associating a TEMA Profile to the Station: Use Quick Builder to set up the Station(s) Modify the Station(s) configuration files(s) Assign TEMA profiles to operators and Station(s) Define TEMA Point server EBI-TEMA
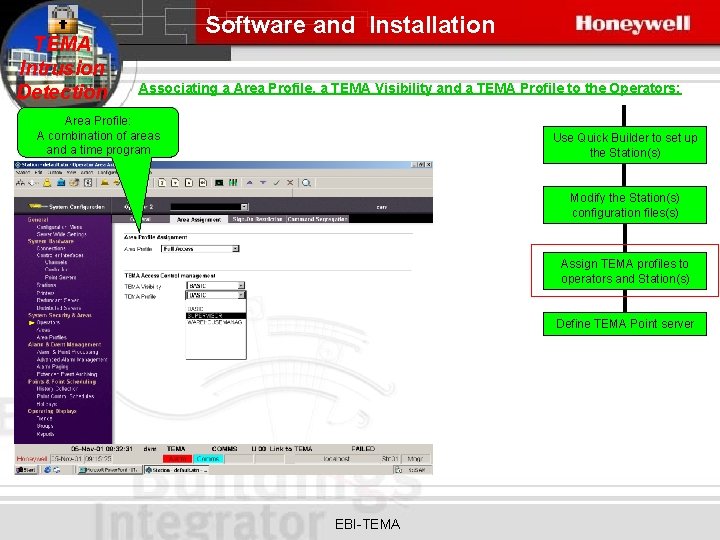
TEMA Intrusion Detection Software and Installation Associating a Area Profile, a TEMA Visibility and a TEMA Profile to the Operators: Area Profile: A combination of areas and a time program Use Quick Builder to set up the Station(s) Modify the Station(s) configuration files(s) Assign TEMA profiles to operators and Station(s) Define TEMA Point server EBI-TEMA
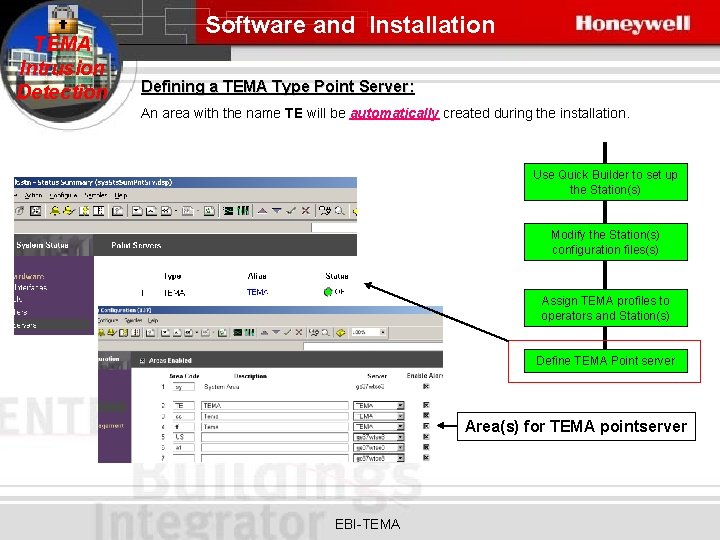
TEMA Intrusion Detection Software and Installation Defining a TEMA Type Point Server: An area with the name TE will be automatically created during the installation. Use Quick Builder to set up the Station(s) Modify the Station(s) configuration files(s) Assign TEMA profiles to operators and Station(s) Define TEMA Point server Area(s) for TEMA pointserver EBI-TEMA
TEMA Intrusion Detection Configuration of Tema Intrusion Detection EBI-TEMA
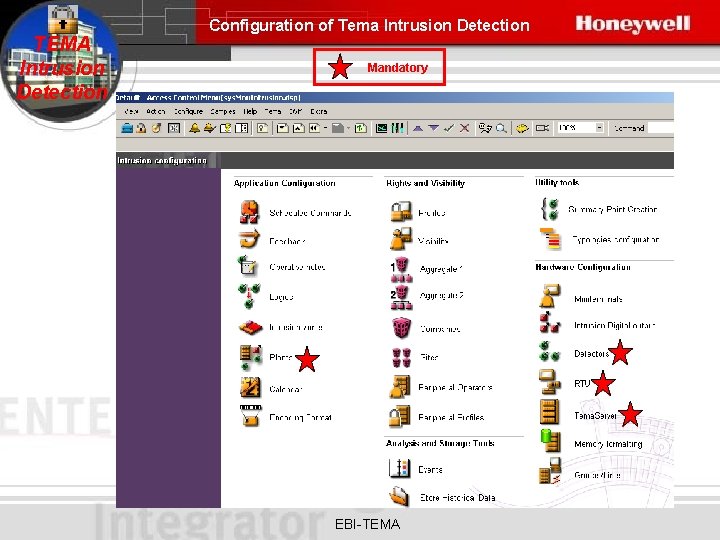
TEMA Intrusion Detection Configuration of Tema Intrusion Detection Mandatory EBI-TEMA
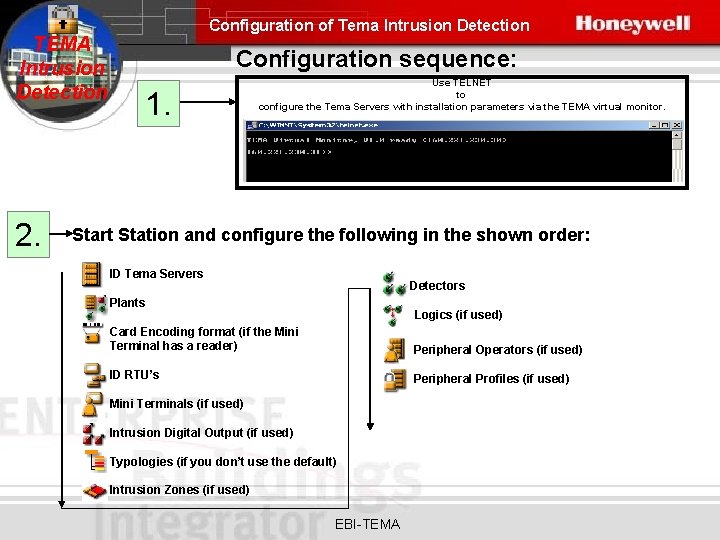
TEMA Intrusion Detection 2. Configuration of Tema Intrusion Detection Configuration sequence: 1. Use TELNET to configure the Tema Servers with installation parameters via the TEMA virtual monitor. Start Station and configure the following in the shown order: ID Tema Servers Detectors Plants Logics (if used) Card Encoding format (if the Mini Terminal has a reader) Peripheral Operators (if used) ID RTU’s Peripheral Profiles (if used) Mini Terminals (if used) Intrusion Digital Output (if used) Typologies (if you don’t use the default) Intrusion Zones (if used) EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration In order to be able to use the Temaline Interface Intrusion Detection Module, you must first configure one or more ID type (Intrusion Detection) Tema Server(s), which will then manage the Intrusion Detection system. EBI-TEMA
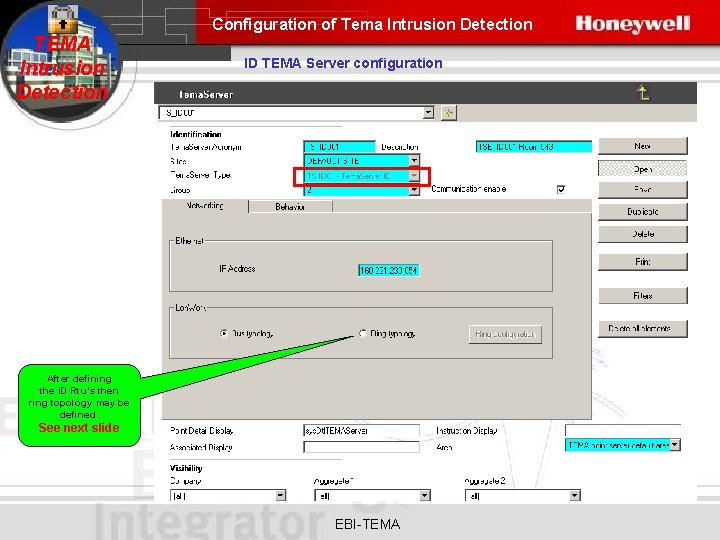
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration After defining the ID Rtu’s then ring topology may be defined. See next slide EBI-TEMA
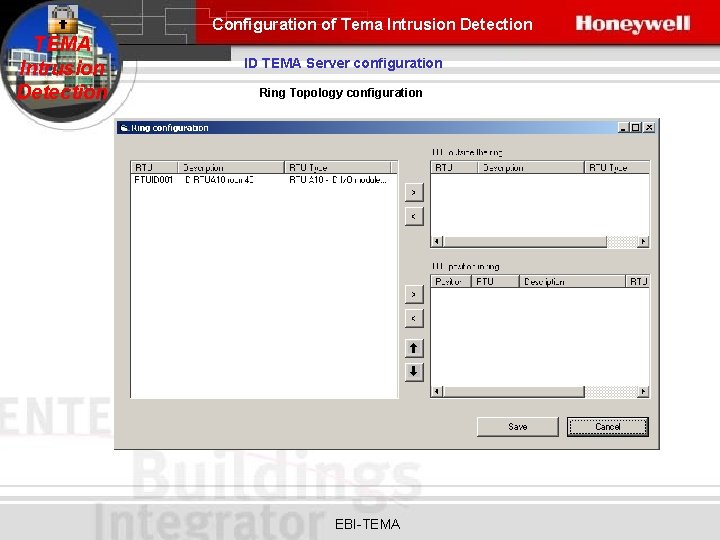
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration Ring Topology configuration EBI-TEMA
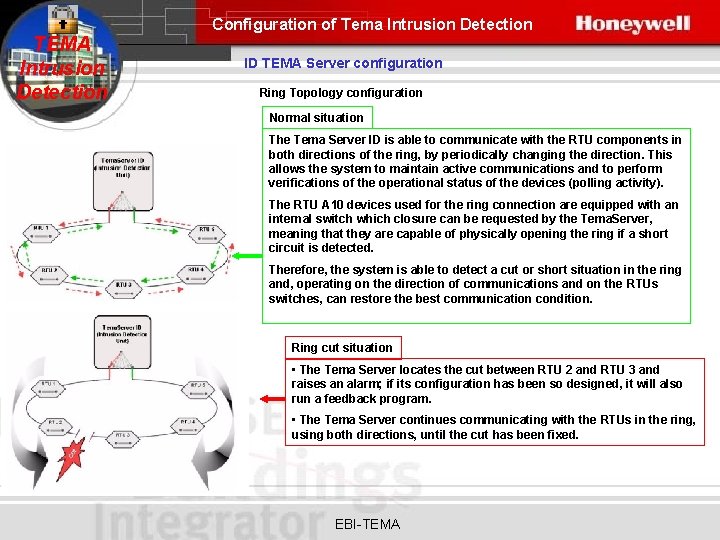
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration Ring Topology configuration Normal situation The Tema Server ID is able to communicate with the RTU components in both directions of the ring, by periodically changing the direction. This allows the system to maintain active communications and to perform verifications of the operational status of the devices (polling activity). The RTU A 10 devices used for the ring connection are equipped with an internal switch which closure can be requested by the Tema. Server, meaning that they are capable of physically opening the ring if a short circuit is detected. Therefore, the system is able to detect a cut or short situation in the ring and, operating on the direction of communications and on the RTUs switches, can restore the best communication condition. Ring cut situation • The Tema Server locates the cut between RTU 2 and RTU 3 and raises an alarm; if its configuration has been so designed, it will also run a feedback program. • The Tema Server continues communicating with the RTUs in the ring, using both directions, until the cut has been fixed. EBI-TEMA
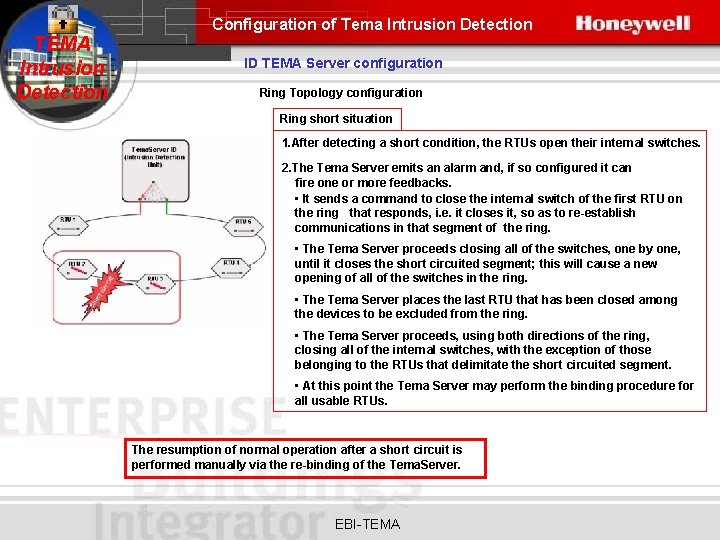
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration Ring Topology configuration Ring short situation 1. After detecting a short condition, the RTUs open their internal switches. 2. The Tema Server emits an alarm and, if so configured it can fire one or more feedbacks. • It sends a command to close the internal switch of the first RTU on the ring that responds, i. e. it closes it, so as to re-establish communications in that segment of the ring. • The Tema Server proceeds closing all of the switches, one by one, until it closes the short circuited segment; this will cause a new opening of all of the switches in the ring. • The Tema Server places the last RTU that has been closed among the devices to be excluded from the ring. • The Tema Server proceeds, using both directions of the ring, closing all of the internal switches, with the exception of those belonging to the RTUs that delimitate the short circuited segment. • At this point the Tema Server may perform the binding procedure for all usable RTUs. The resumption of normal operation after a short circuit is performed manually via the re-binding of the Tema. Server. EBI-TEMA
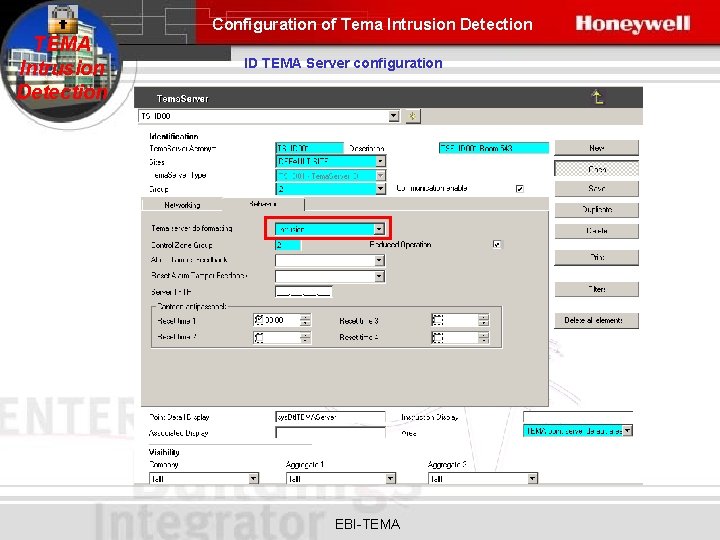
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server configuration EBI-TEMA
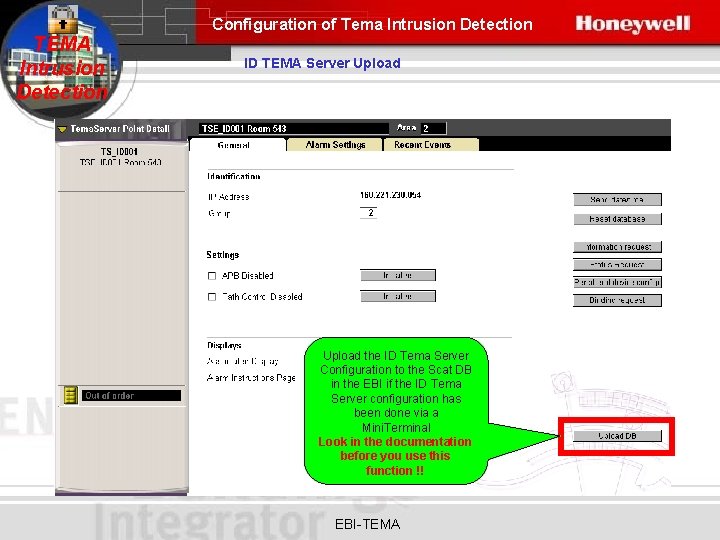
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID TEMA Server Upload the ID Tema Server Configuration to the Scat DB in the EBI if the ID Tema Server configuration has been done via a Mini. Terminal Look in the documentation before you use this function !! EBI-TEMA
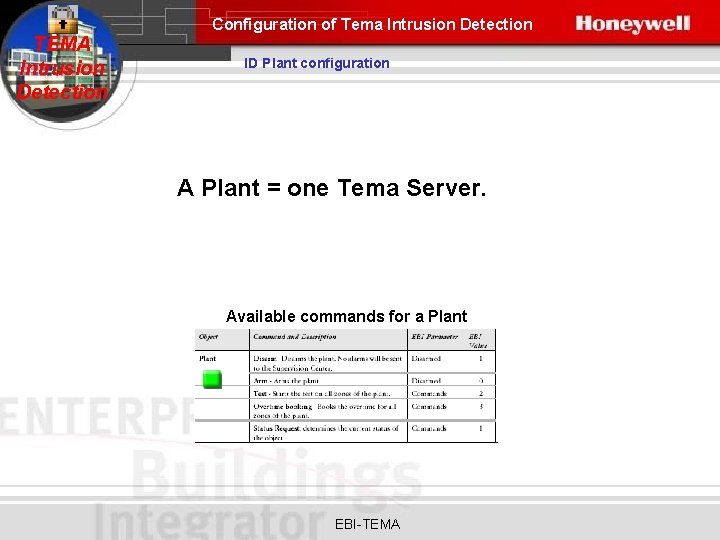
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Plant configuration A Plant = one Tema Server. Available commands for a Plant EBI-TEMA
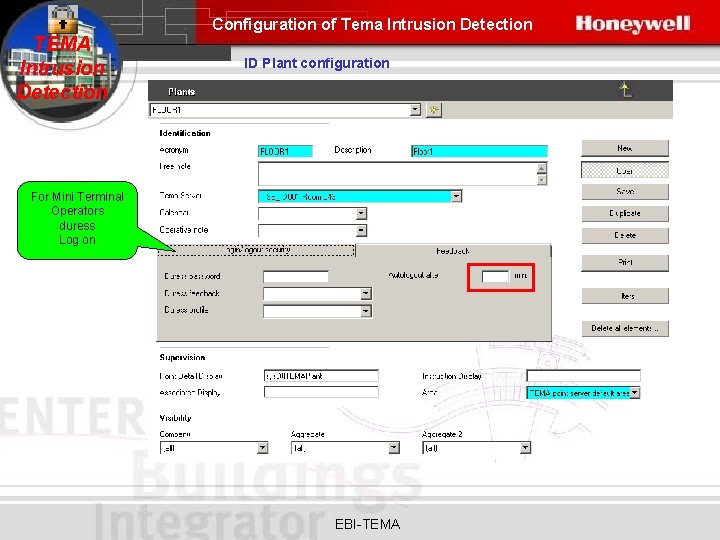
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Plant configuration For Mini Terminal Operators duress Log on EBI-TEMA
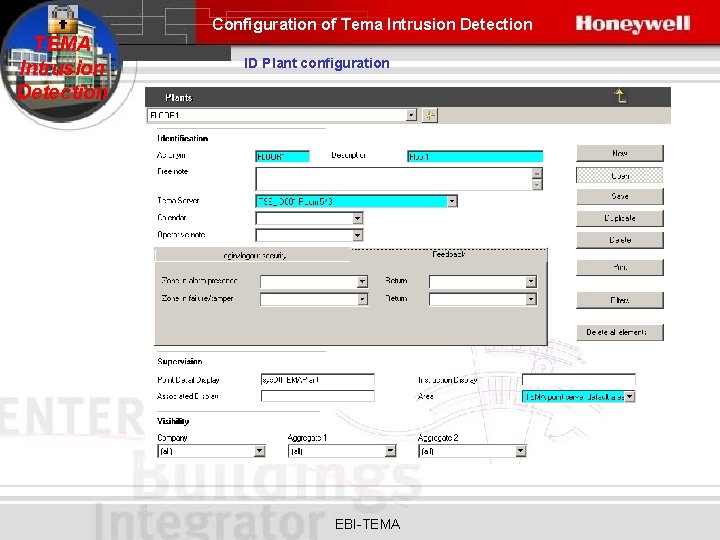
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Plant configuration EBI-TEMA
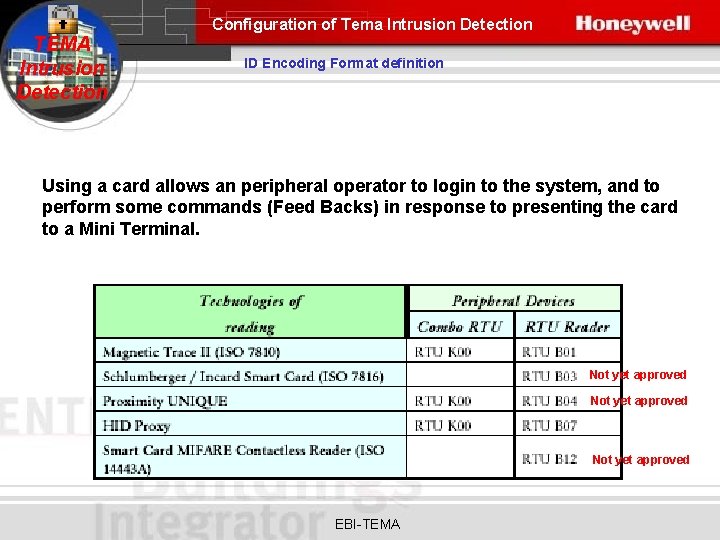
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Encoding Format definition Using a card allows an peripheral operator to login to the system, and to perform some commands (Feed Backs) in response to presenting the card to a Mini Terminal. Not yet approved EBI-TEMA
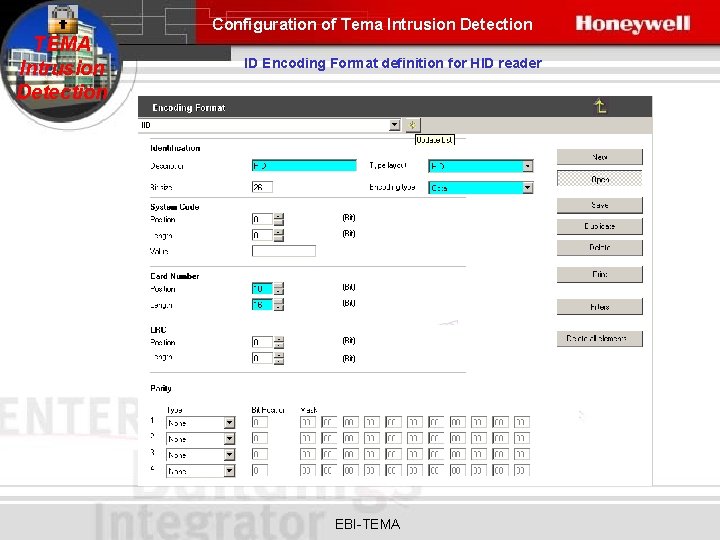
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Encoding Format definition for HID reader EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID RTU Configuration The RTU components are the base modules -readers, displays, keyboardsthat make up the Mini Terminals, and the RTUA 10 I/O module as interface for the intrusion detection Detectors. EBI-TEMA
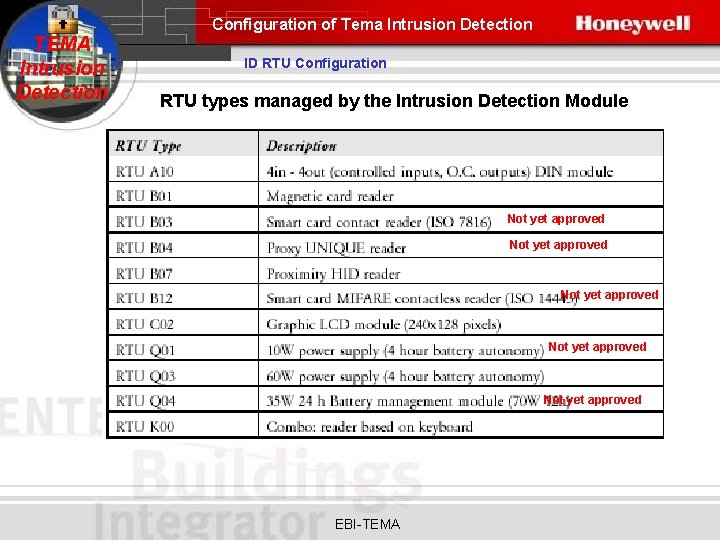
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID RTU Configuration RTU types managed by the Intrusion Detection Module Not yet approved Not yet approved EBI-TEMA
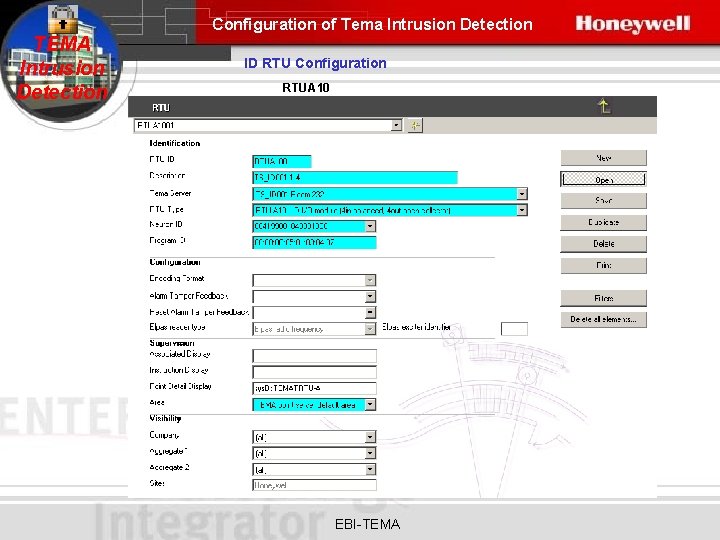
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID RTU Configuration RTUA 10 EBI-TEMA
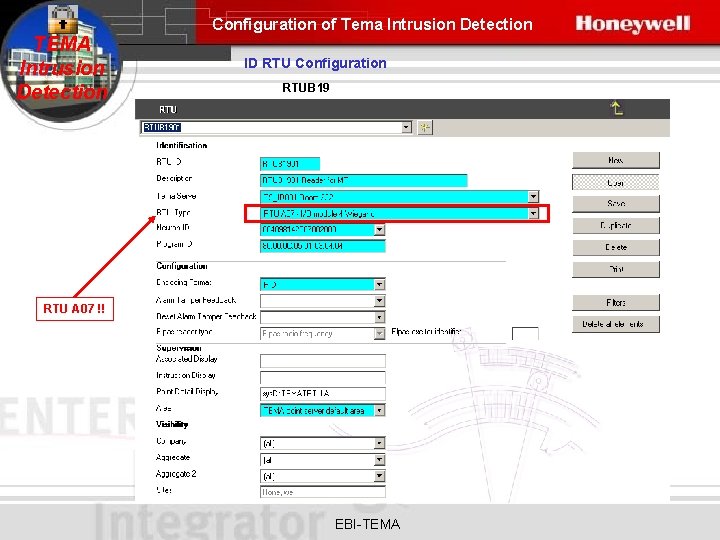
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID RTU Configuration RTUB 19 RTU A 07 !! EBI-TEMA
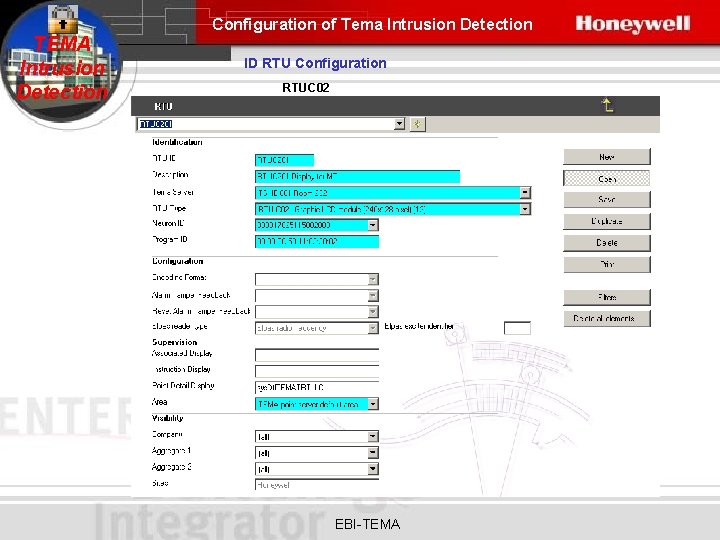
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID RTU Configuration RTUC 02 EBI-TEMA
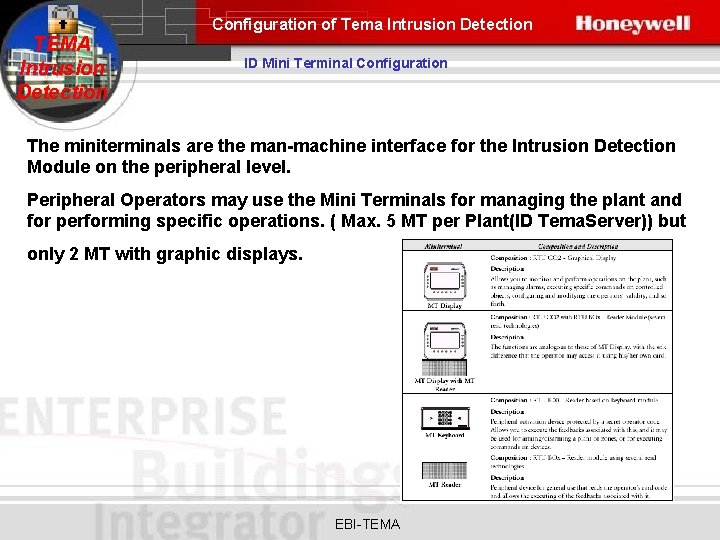
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Mini Terminal Configuration The miniterminals are the man-machine interface for the Intrusion Detection Module on the peripheral level. Peripheral Operators may use the Mini Terminals for managing the plant and for performing specific operations. ( Max. 5 MT per Plant(ID Tema. Server)) but only 2 MT with graphic displays. EBI-TEMA
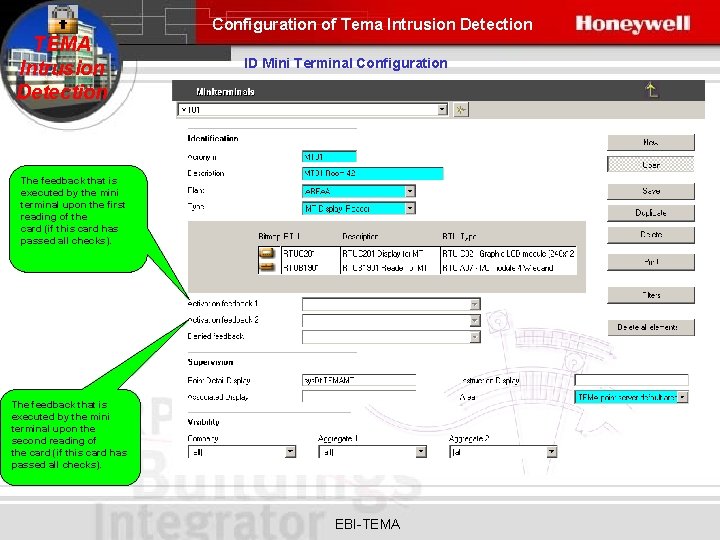
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Mini Terminal Configuration The feedback that is executed by the mini terminal upon the first reading of the card (if this card has passed all checks). The feedback that is executed by the mini terminal upon the second reading of the card (if this card has passed all checks). EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Digital Output Configuration Intrusion digital outputs allow you to execute commands from the EBI or by the Tema. Server ID via a feedback program. They are digital output on the RTU A 10 (I/O type RTU). The outputs may be associated to a zone, and in such a case, they will inherit the zone status (armed/disarmed). Specifically, the outputs in the Temaline Interface Intrusion Detection Module are used to manage the testing and reset of detectors, in addition to normal control, such as sirens, lights ect. EBI-TEMA
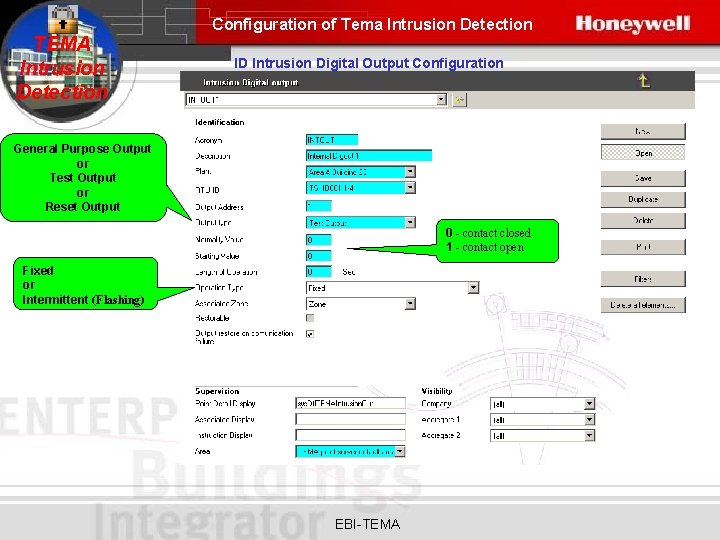
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Digital Output Configuration General Purpose Output or Test Output or Reset Output 0 - contact closed 1 - contact open Fixed or Intermittent (Flashing) EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Typologies Configuration The statuses that an object may assume, the events that it may generate, and the commands that can be run on it are called Typologies. For detectors and logics, in addition to the default typologies, you can create customized typologies. EBI-TEMA
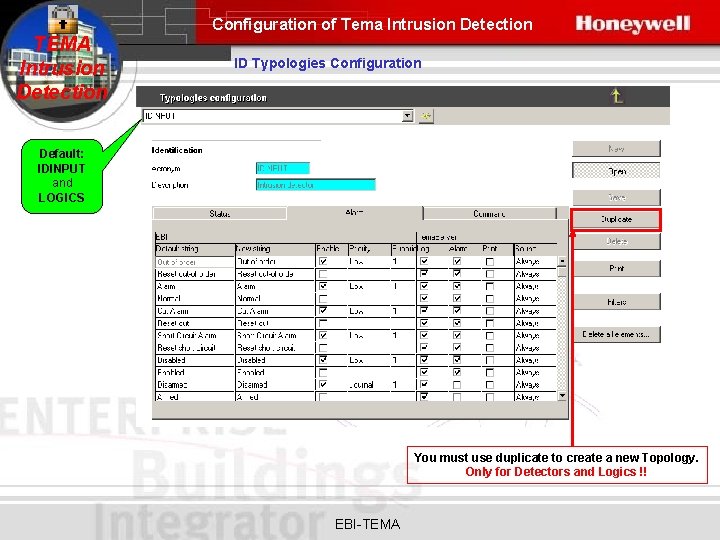
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Typologies Configuration Default: IDINPUT and LOGICS You must use duplicate to create a new Topology. Only for Detectors and Logics !! EBI-TEMA
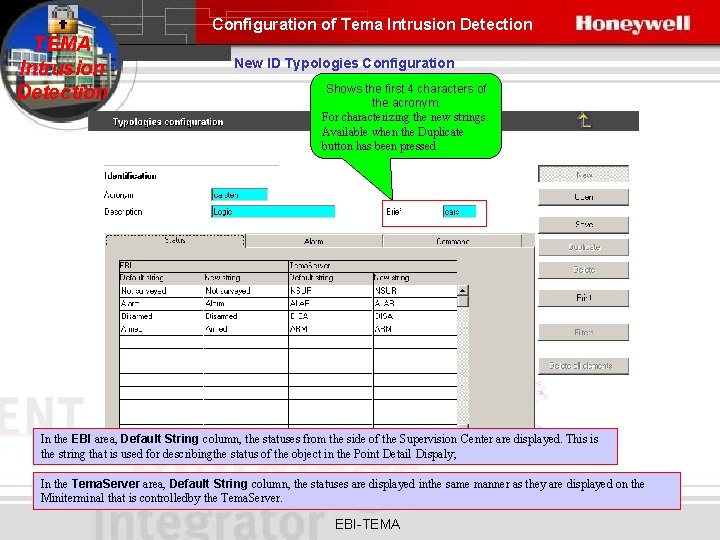
Configuration of Tema Intrusion Detection TEMA Intrusion Detection New ID Typologies Configuration Shows the first 4 characters of the acronym. For characterizing the new strings. Available when the Duplicate button has been pressed In the EBI area, Default String column, the statuses from the side of the Supervision Center are displayed. This is the string that is used for describingthe status of the object in the Point Detail Dispaly; In the Tema. Server area, Default String column, the statuses are displayed inthe same manner as they are displayed on the Miniterminal that is controlledby the Tema. Server. EBI-TEMA
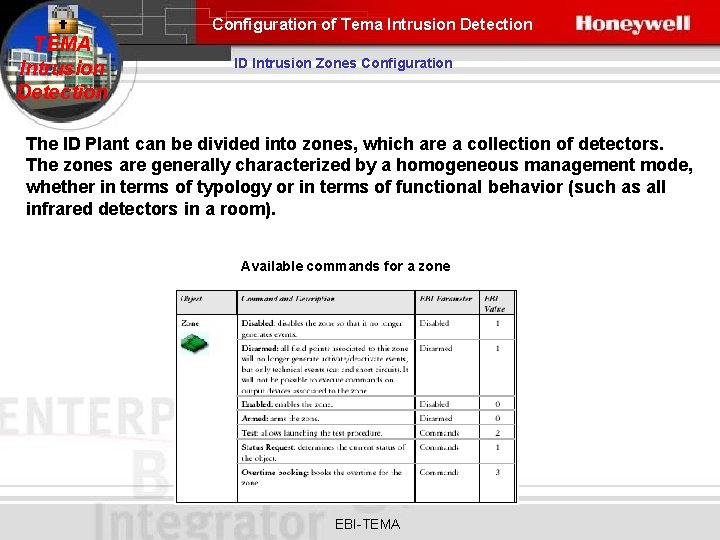
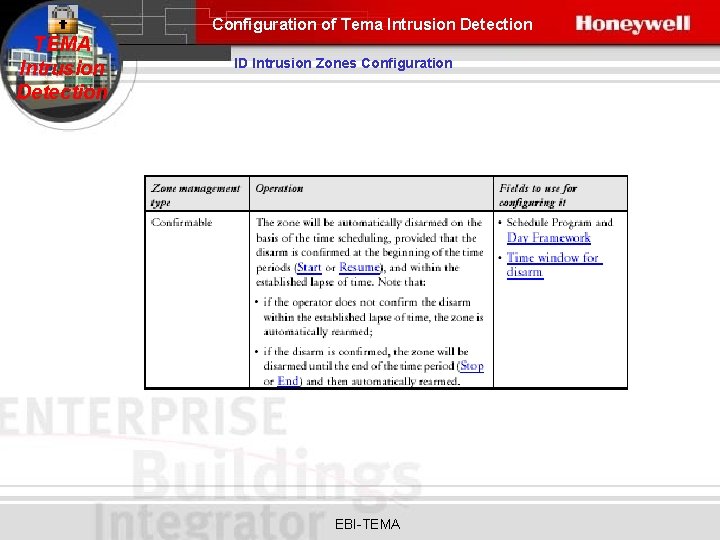
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Zones Configuration The ID Plant can be divided into zones, which are a collection of detectors. The zones are generally characterized by a homogeneous management mode, whether in terms of typology or in terms of functional behavior (such as all infrared detectors in a room). Available commands for a zone EBI-TEMA
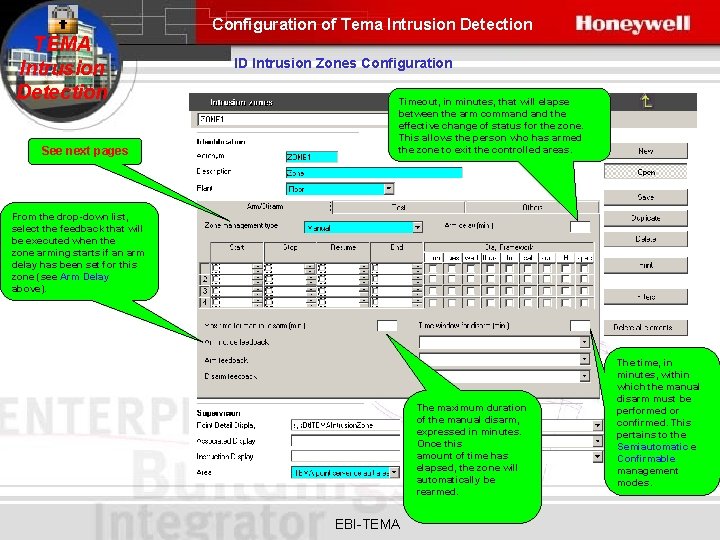
Configuration of Tema Intrusion Detection TEMA Intrusion Detection See next pages ID Intrusion Zones Configuration Timeout, in minutes, that will elapse between the arm command the effective change of status for the zone. This allows the person who has armed the zone to exit the controlled areas. From the drop-down list, select the feedback that will be executed when the zone arming starts if an arm delay has been set for this zone (see Arm Delay above). The maximum duration of the manual disarm, expressed in minutes. Once this amount of time has elapsed, the zone will automatically be rearmed. EBI-TEMA The time, in minutes, within which the manual disarm must be performed or confirmed. This pertains to the Semiautomatic e Confirmable management modes.
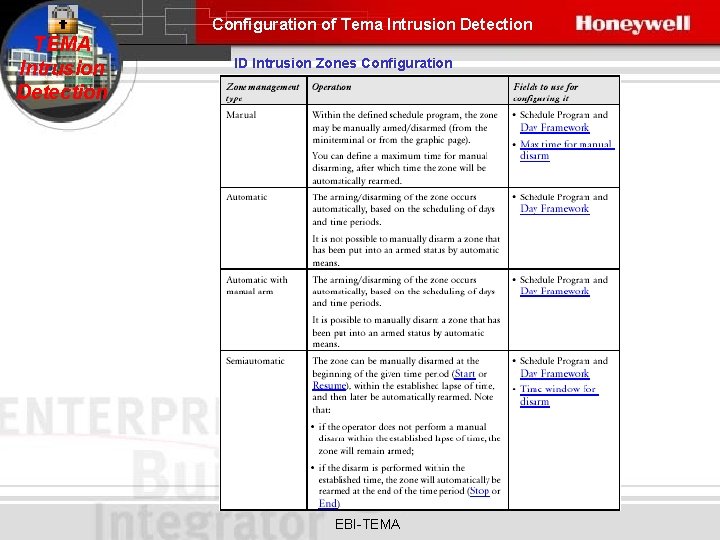
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Zones Configuration EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Zones Configuration EBI-TEMA
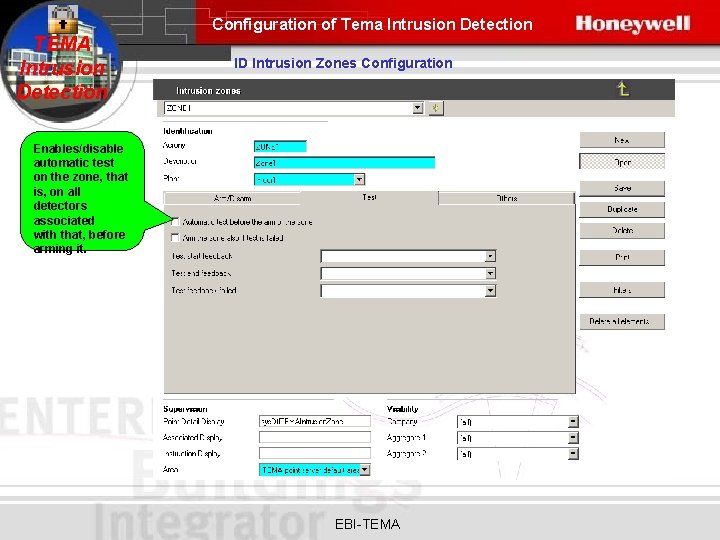
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Zones Configuration Enables/disable automatic test on the zone, that is, on all detectors associated with that, before arming it. EBI-TEMA
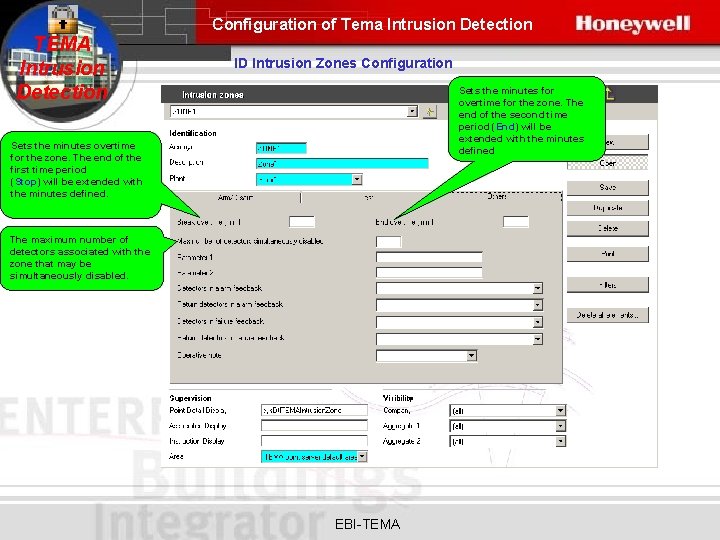
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Intrusion Zones Configuration Sets the minutes for overtime for the zone. The end of the second time period (End) will be extended with the minutes defined Sets the minutes overtime for the zone. The end of the first time period (Stop) will be extended with the minutes defined. The maximum number of detectors associated with the zone that may be simultaneously disabled. EBI-TEMA
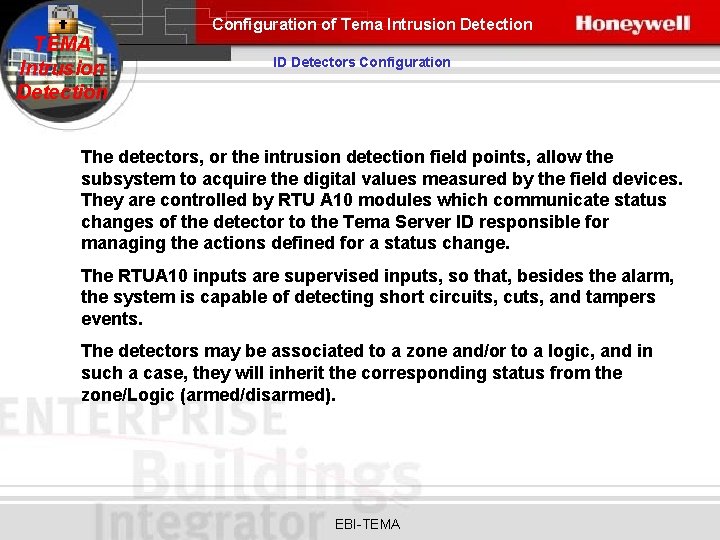
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration The detectors, or the intrusion detection field points, allow the subsystem to acquire the digital values measured by the field devices. They are controlled by RTU A 10 modules which communicate status changes of the detector to the Tema Server ID responsible for managing the actions defined for a status change. The RTUA 10 inputs are supervised inputs, so that, besides the alarm, the system is capable of detecting short circuits, cuts, and tampers events. The detectors may be associated to a zone and/or to a logic, and in such a case, they will inherit the corresponding status from the zone/Logic (armed/disarmed). EBI-TEMA
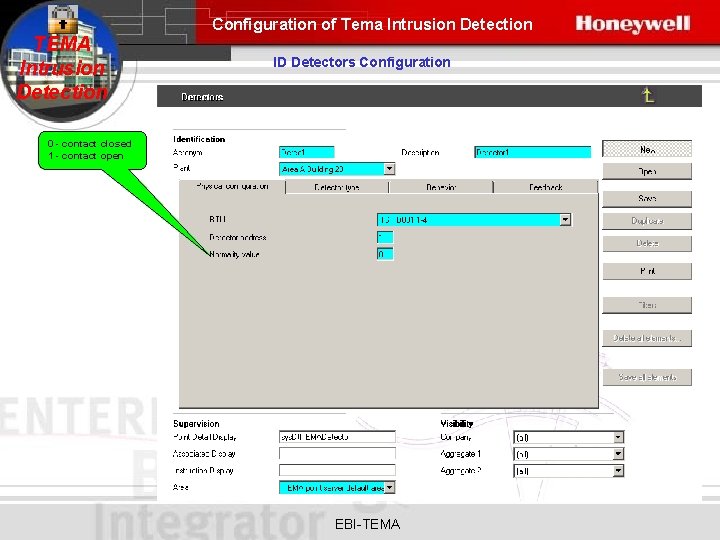
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration 0 - contact closed 1 - contact open EBI-TEMA
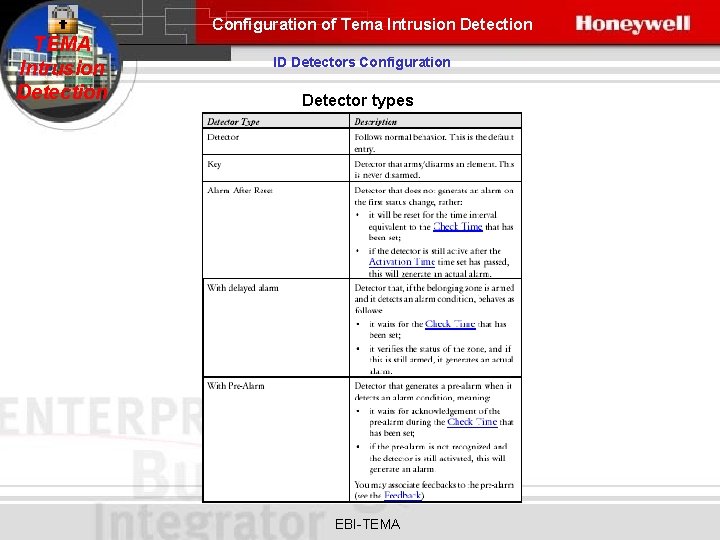
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration Detector types EBI-TEMA
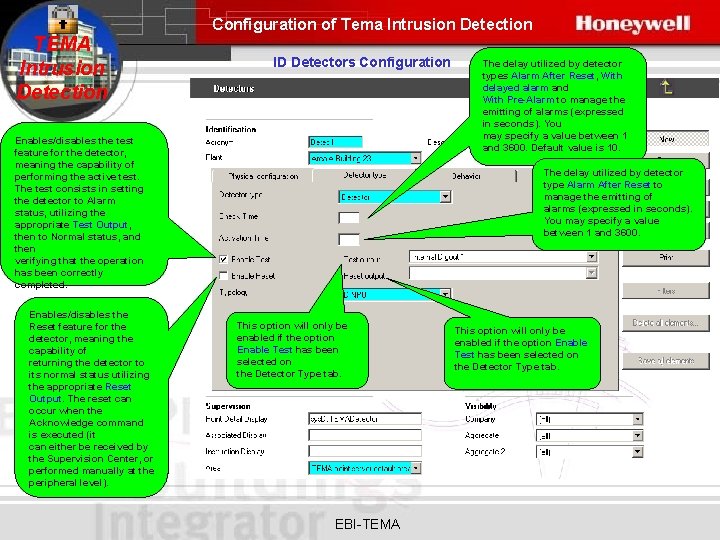
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration Enables/disables the test feature for the detector, meaning the capability of performing the active test. The test consists in setting the detector to Alarm status, utilizing the appropriate Test Output, then to Normal status, and then verifying that the operation has been correctly completed. Enables/disables the Reset feature for the detector, meaning the capability of returning the detector to its normal status utilizing the appropriate Reset Output. The reset can occur when the Acknowledge command is executed (it can either be received by the Supervision Center, or performed manually at the peripheral level). The delay utilized by detector types Alarm After Reset, With delayed alarm and With Pre-Alarm to manage the emitting of alarms (expressed in seconds). You may specify a value between 1 and 3600. Default value is 10. The delay utilized by detector type Alarm After Reset to manage the emitting of alarms (expressed in seconds). You may specify a value between 1 and 3600. This option will only be enabled if the option Enable Test has been selected on the Detector Type tab. EBI-TEMA This option will only be enabled if the option Enable Test has been selected on the Detector Type tab.
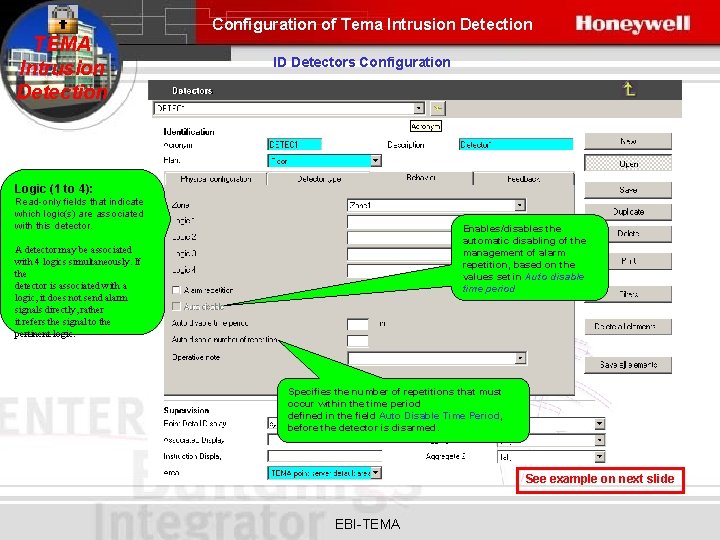
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration Logic (1 to 4): Read-only fields that indicate which logic(s) are associated with this detector. Enables/disables the automatic disabling of the management of alarm repetition, based on the values set in Auto disable time period A detector may be associated with 4 logics simultaneously. If the detector is associated with a logic, it does not send alarm signals directly, rather it refers the signal to the pertinent logic. Specifies the number of repetitions that must occur within the time period defined in the field Auto Disable Time Period, before the detector is disarmed. See example on next slide EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration The Auto disabled can only be selected if Alarm repetition has been checked !! – The Auto disable is selected. – The Auto Disable Time Period is set to 2. – The Auto Disable Number of Repetitions is set to 5. Result: – If the detector goes into alarm 5 or more times within a period of 2 minutes, the detector will be disarmed. The detector then must be re-armed using a manual command (via the Mini Terminal or the EBI). EBI-TEMA
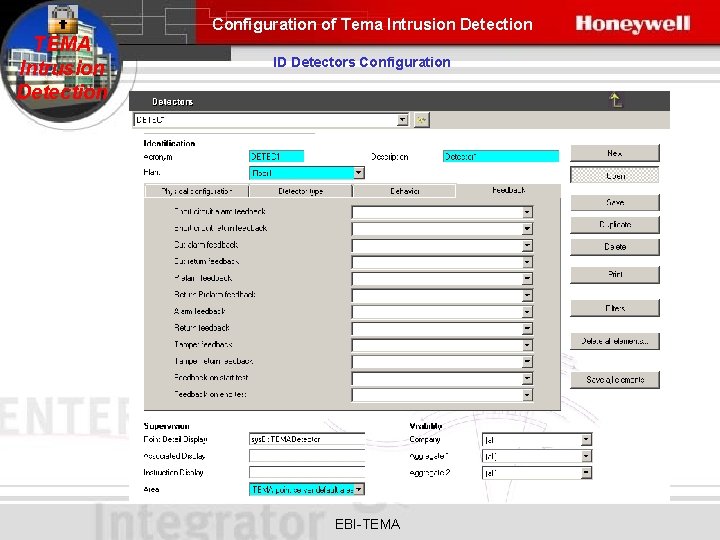
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Detectors Configuration EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Logics Configuration A collection of detectors that must be in alarm status, either simultaneously or not, in order to rise to an alarm for the logic. EBI-TEMA
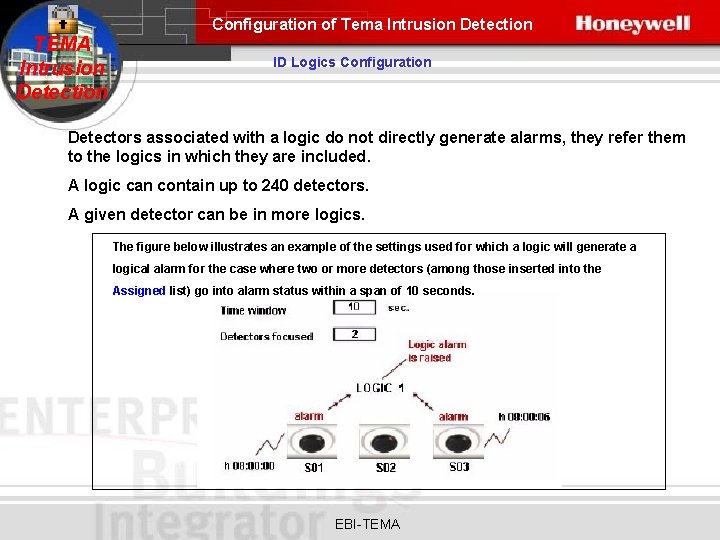
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Logics Configuration Detectors associated with a logic do not directly generate alarms, they refer them to the logics in which they are included. A logic can contain up to 240 detectors. A given detector can be in more logics. The figure below illustrates an example of the settings used for which a logic will generate a logical alarm for the case where two or more detectors (among those inserted into the Assigned list) go into alarm status within a span of 10 seconds. EBI-TEMA
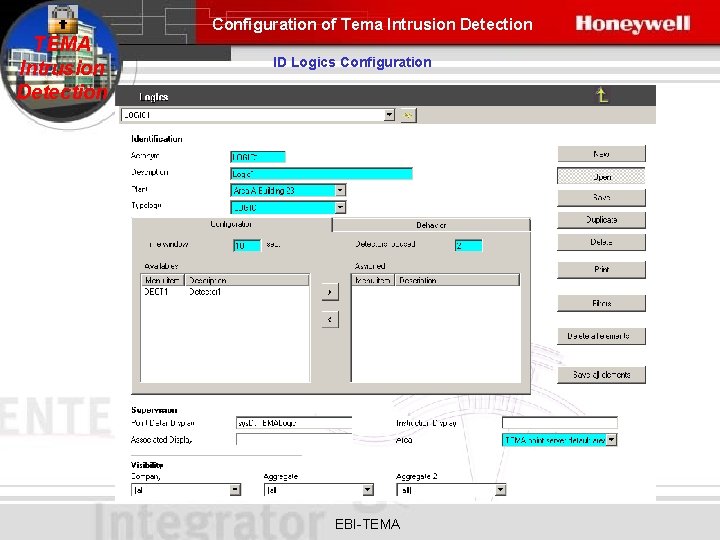
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Logics Configuration EBI-TEMA
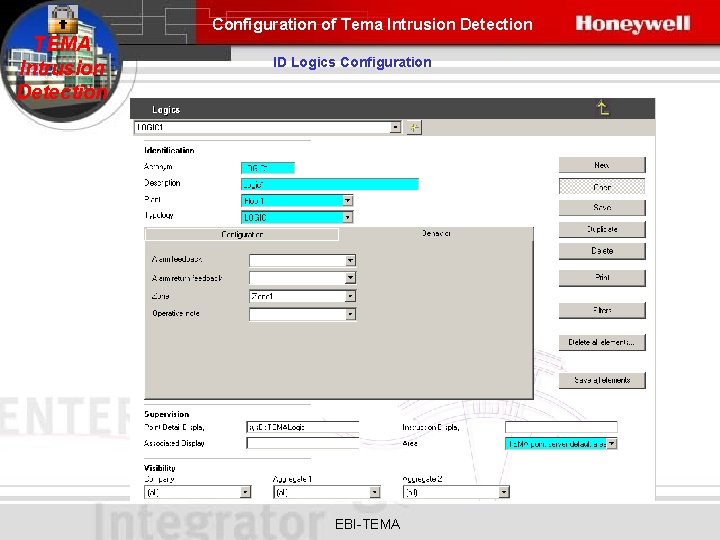
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Logics Configuration EBI-TEMA
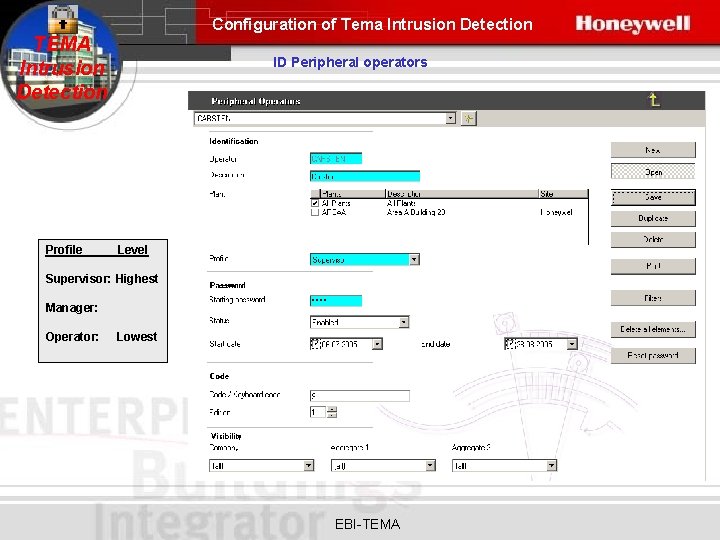
Configuration of Tema Intrusion Detection TEMA Intrusion Detection Profile ID Peripheral operators Level Supervisor: Highest Manager: Operator: Lowest EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Peripheral Configurator The Tema ID Peripheral Configurator allows you to configure an Intrusion Detection Central Unit (Tema. Server ID) at the peripheral level, i. e. a Central Unit that is not connected with the EBI-TEMA
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Peripheral Configurator After having installed the peripheral hardware, this application will allow you to automate the configuration procedures of the Intrusion Detection Central Unit, and, in particular: • identify the MT Display (RTU C 02 - Graphical Display) Mini Terminals to beutilized as operational interfaces for the configuration and diagnostics of the Central Unit; • identify all the peripheral devices that make up the Central Unit; • perform diagnostics (tests) on the devices and generate related messages; • create a final report with configuration data for the central unit, in terms of devices detected and test results. EBI-TEMA
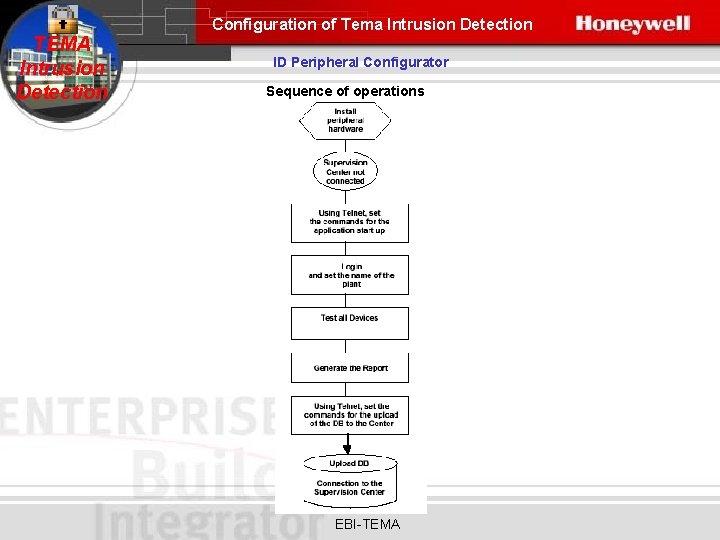
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Peripheral Configurator Sequence of operations EBI-TEMA
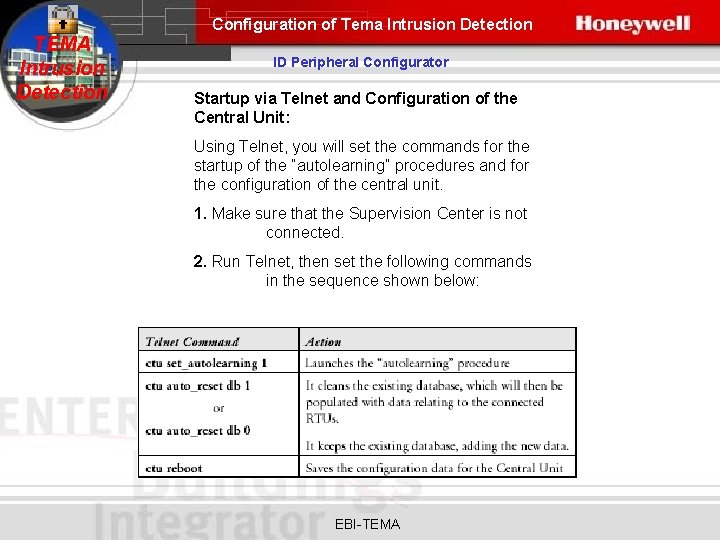
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Peripheral Configurator Startup via Telnet and Configuration of the Central Unit: Using Telnet, you will set the commands for the startup of the “autolearning” procedures and for the configuration of the central unit. 1. Make sure that the Supervision Center is not connected. 2. Run Telnet, then set the following commands in the sequence shown below: EBI-TEMA
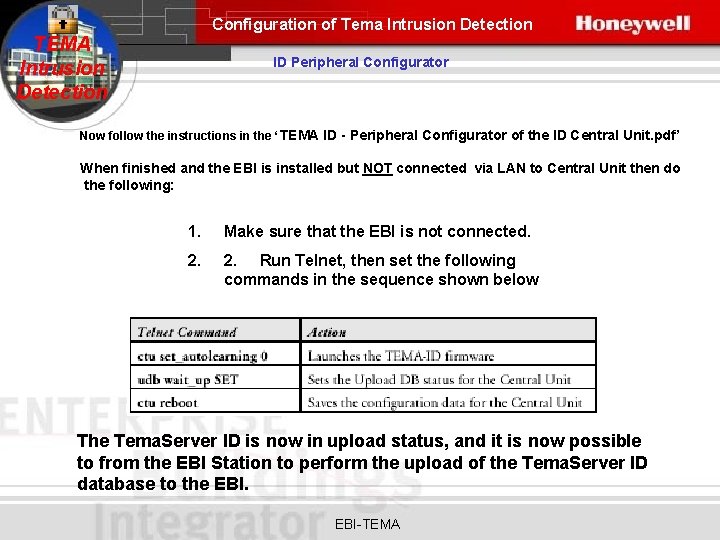
Configuration of Tema Intrusion Detection TEMA Intrusion Detection ID Peripheral Configurator Now follow the instructions in the ‘ TEMA ID - Peripheral Configurator of the ID Central Unit. pdf’ When finished and the EBI is installed but NOT connected via LAN to Central Unit then do the following: 1. Make sure that the EBI is not connected. 2. Run Telnet, then set the following commands in the sequence shown below The Tema. Server ID is now in upload status, and it is now possible to from the EBI Station to perform the upload of the Tema. Server ID database to the EBI-TEMA
- Slides: 100