ecs 236 Winter 2007 Intrusion Detection 2 Explanationbased
ecs 236 Winter 2007: Intrusion Detection #2: Explanation-based Anomaly Detection Dr. S. Felix Wu Computer Science Department University of California, Davis http: //www. cs. ucdavis. edu/~wu/ sfelixwu@gmail. com 01/04/2007 ecs 236 winter 2007 1
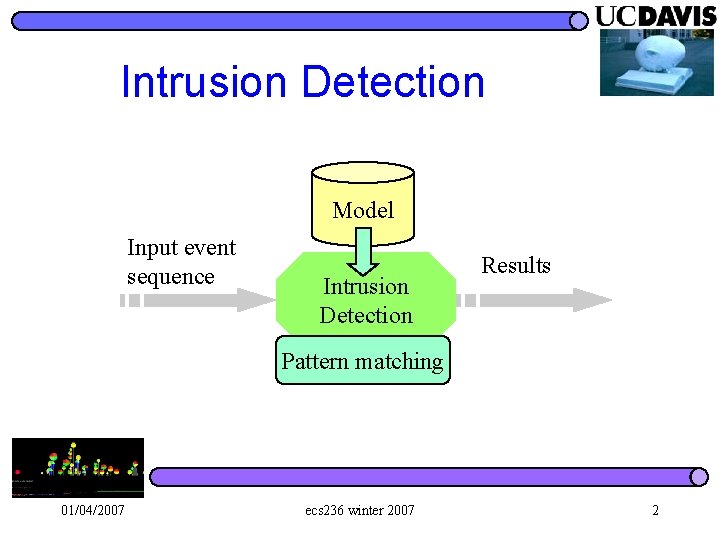
Intrusion Detection Model Input event sequence Intrusion Detection Results Pattern matching 01/04/2007 ecs 236 winter 2007 2
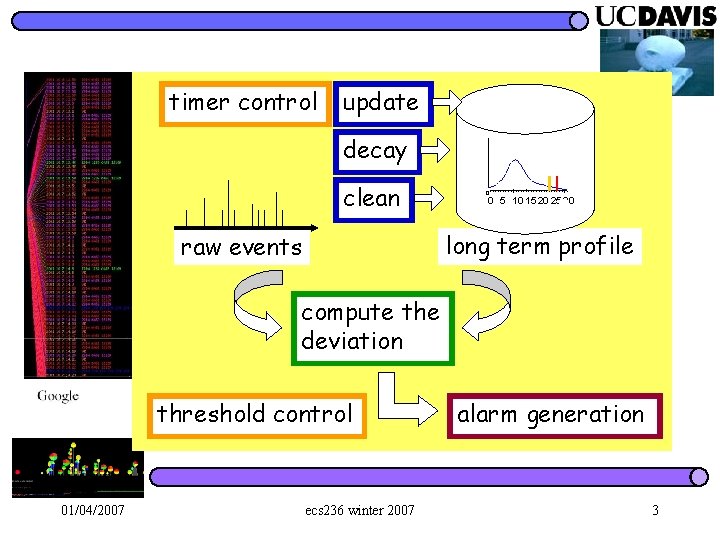
timer control update decay clean 0 0 5 10 15 20 25 30 long term profile raw events compute the deviation threshold control 01/04/2007 ecs 236 winter 2007 alarm generation 3
What is an anomaly? 01/04/2007 ecs 236 winter 2007 4
What is an anomaly? l The observation of a target system is inconsistent, somewhat, with the expected conceptual model of the same system 01/04/2007 ecs 236 winter 2007 5
What is an anomaly? l The observation of a target system is inconsistent, somewhat, with the expected conceptual model of the same system l And, this conceptual model can be ANYTHING. – Statistical, logical, or something else 01/04/2007 ecs 236 winter 2007 6
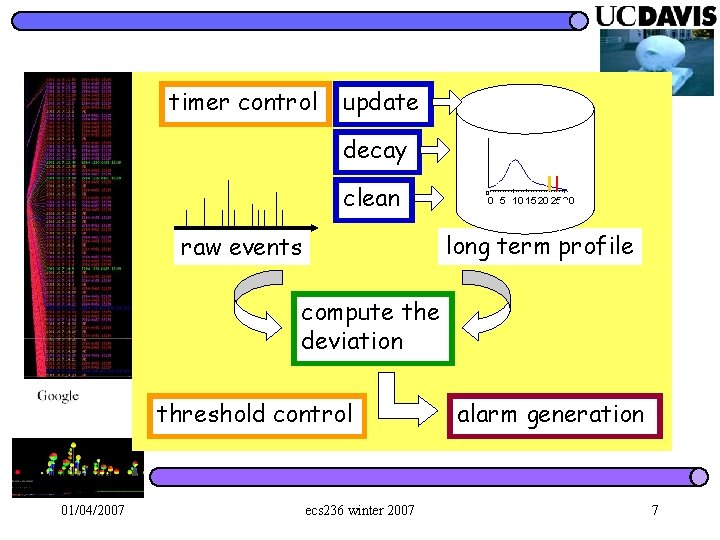
timer control update decay clean 0 0 5 10 15 20 25 30 long term profile raw events compute the deviation threshold control 01/04/2007 ecs 236 winter 2007 alarm generation 7
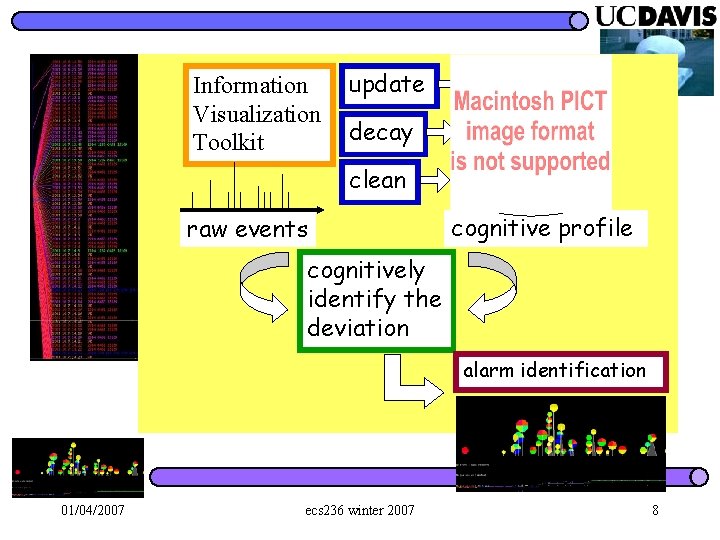
Information Visualization Toolkit update decay clean raw events cognitive profile cognitively identify the deviation alarm identification 01/04/2007 ecs 236 winter 2007 8
Challenge of AND We know that the detected anomalies can be either true-positive or false-positive. l We try all our best to resolve the puzzle by examining all information available to us. l But, the “ground truth” of these anomalies is very hard to obtain l – even with human intelligence – Practically this might or might not be OK… 01/04/2007 ecs 236 winter 2007 9
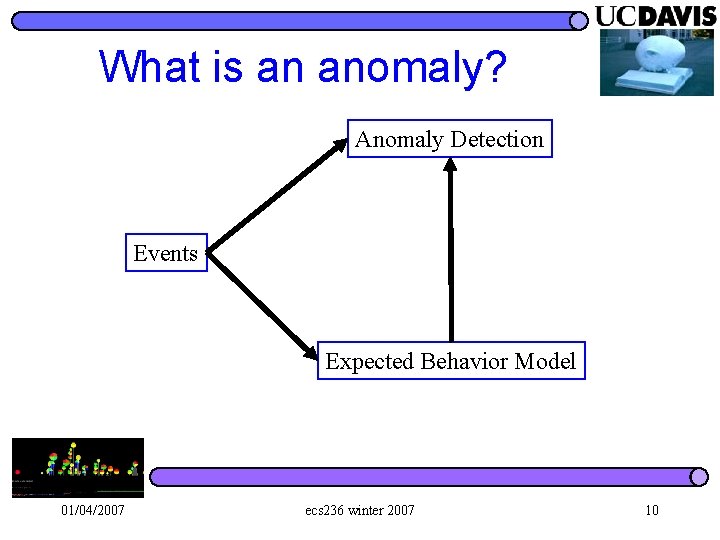
What is an anomaly? Anomaly Detection Events Expected Behavior Model 01/04/2007 ecs 236 winter 2007 10
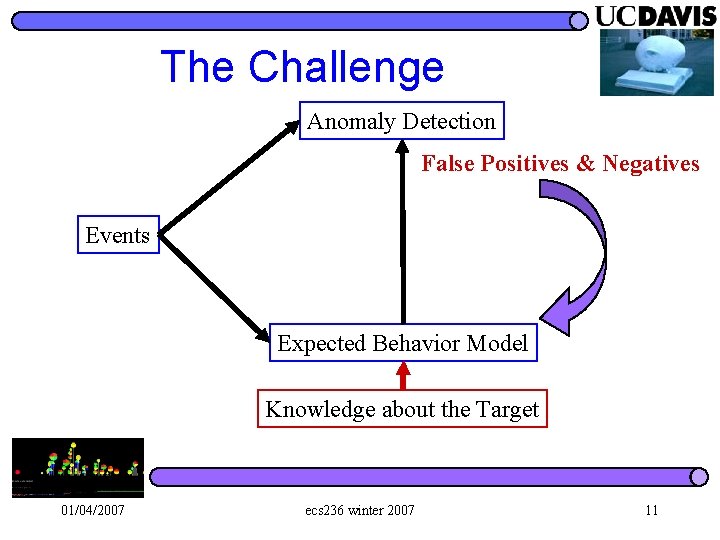
The Challenge Anomaly Detection False Positives & Negatives Events Expected Behavior Model Knowledge about the Target 01/04/2007 ecs 236 winter 2007 11
Problems with AND We are not sure about whatever we want to detect… l We are not sure either when something is caught… l We are still in the dark… at least in many cases… l 01/04/2007 ecs 236 winter 2007 12
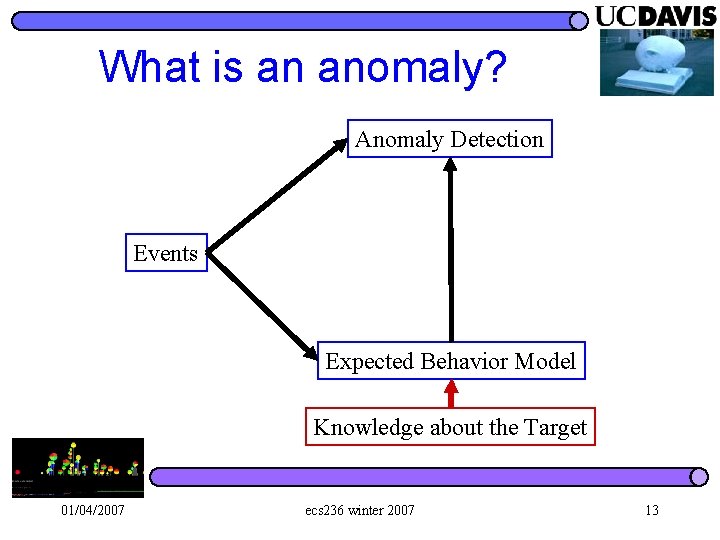
What is an anomaly? Anomaly Detection Events Expected Behavior Model Knowledge about the Target 01/04/2007 ecs 236 winter 2007 13
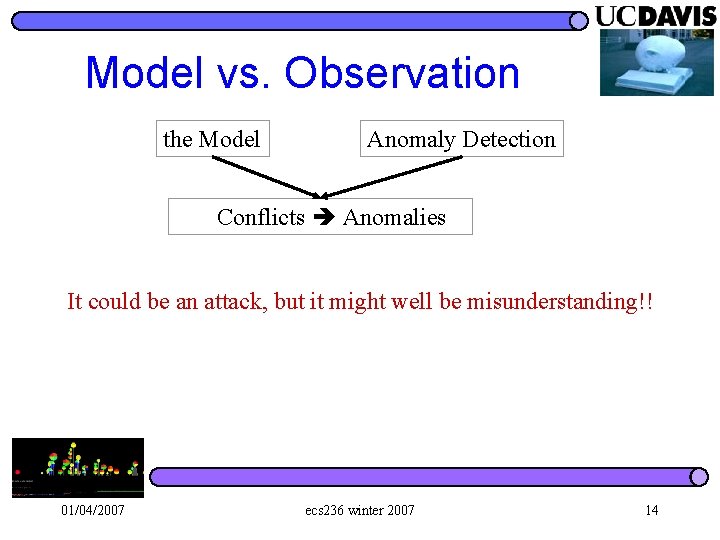
Model vs. Observation the Model Anomaly Detection Conflicts Anomalies It could be an attack, but it might well be misunderstanding!! 01/04/2007 ecs 236 winter 2007 14
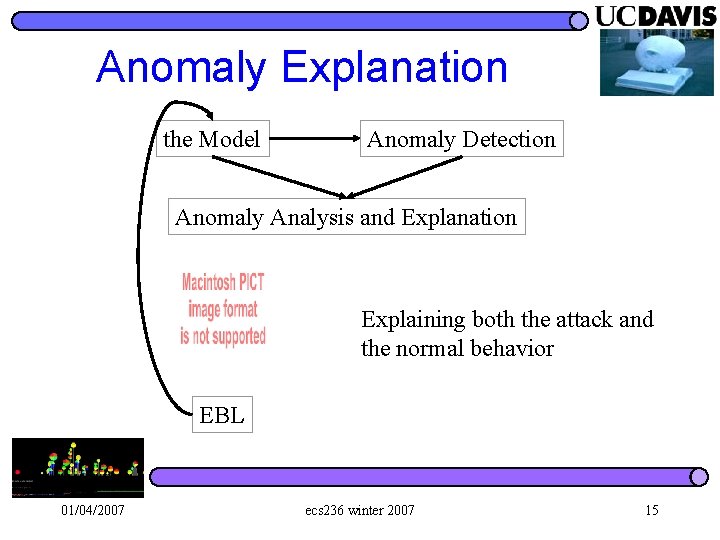
Anomaly Explanation the Model Anomaly Detection Anomaly Analysis and Explanation Explaining both the attack and the normal behavior EBL 01/04/2007 ecs 236 winter 2007 15
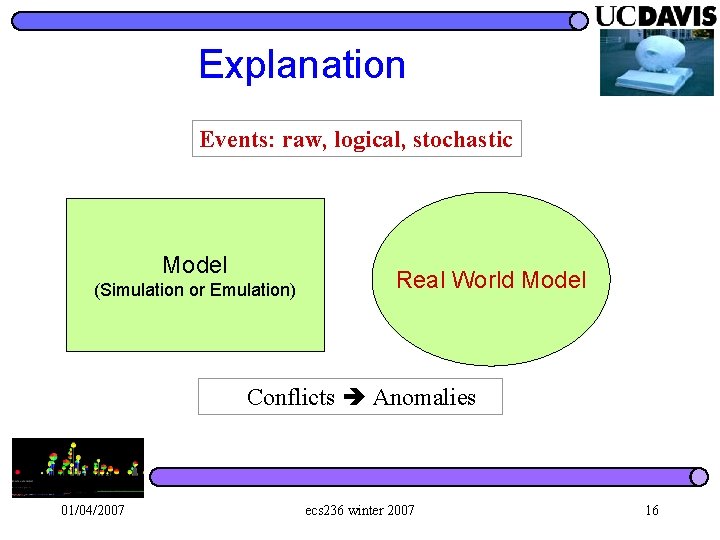
Explanation Events: raw, logical, stochastic Model (Simulation or Emulation) Real World Model Conflicts Anomalies 01/04/2007 ecs 236 winter 2007 16
EXPAND l Good events go into the Model 01/04/2007 ecs 236 winter 2007 17
EXPAND Good events go into the Model l Malicious events also go into the Model as signatures (but with an analysis process) l l We want to put as much as ground truth into our model! – And, that means discovering their relationship as well. 01/04/2007 ecs 236 winter 2007 18
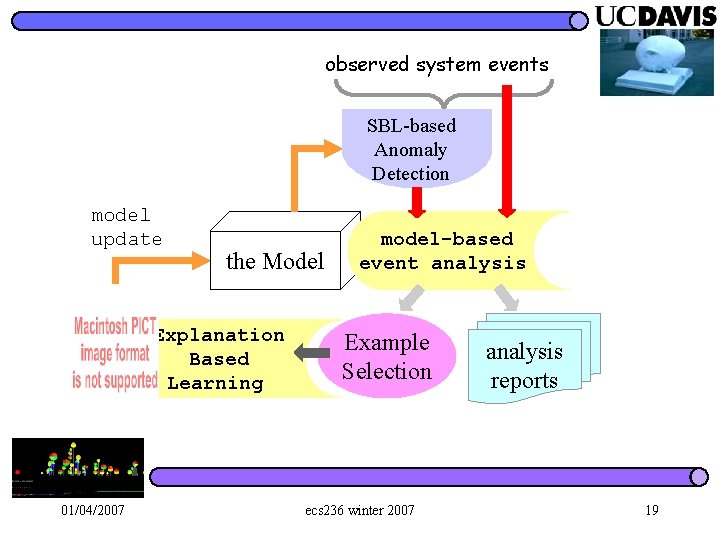
observed system events SBL-based Anomaly Detection model update the Model Explanation Based Learning 01/04/2007 model-based event analysis Example Selection ecs 236 winter 2007 analysis reports 19
AND EXPAND l Anomaly Detection – Detect – Analysis and Explanation – Application 01/04/2007 ecs 236 winter 2007 20
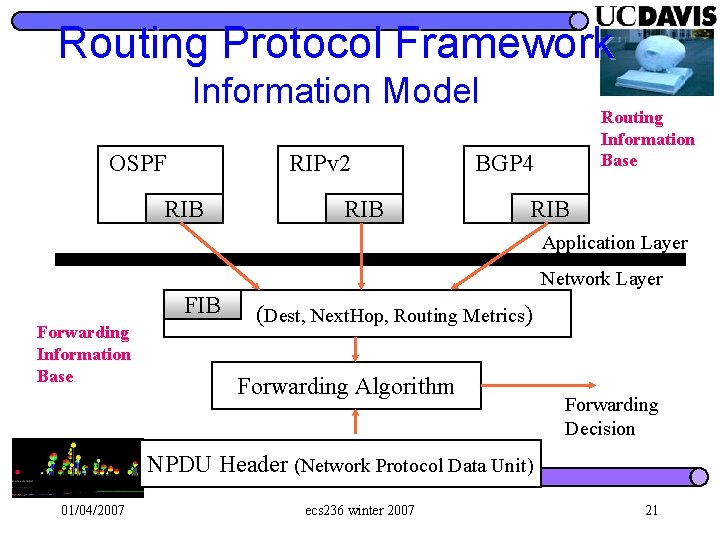
Routing Protocol Framework Information Model OSPF RIPv 2 RIB Routing Information Base BGP 4 RIB Application Layer Network Layer Forwarding Information Base FIB (Dest, Next. Hop, Routing Metrics) Forwarding Algorithm Forwarding Decision NPDU Header (Network Protocol Data Unit) 01/04/2007 ecs 236 winter 2007 21
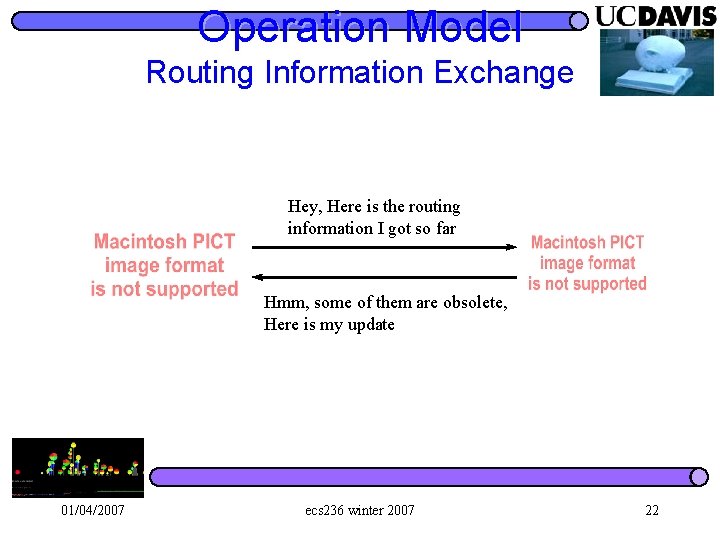
Operation Model Routing Information Exchange Hey, Here is the routing information I got so far Hmm, some of them are obsolete, Here is my update 01/04/2007 ecs 236 winter 2007 22
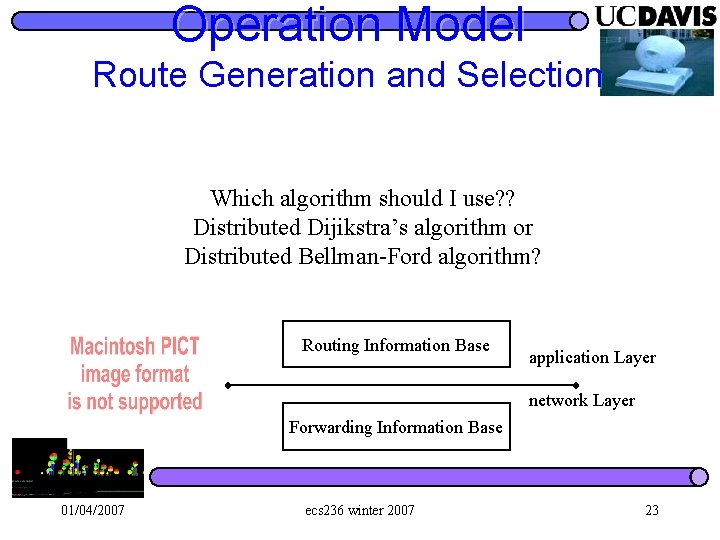
Operation Model Route Generation and Selection Which algorithm should I use? ? Distributed Dijikstra’s algorithm or Distributed Bellman-Ford algorithm? Routing Information Base application Layer network Layer Forwarding Information Base 01/04/2007 ecs 236 winter 2007 23
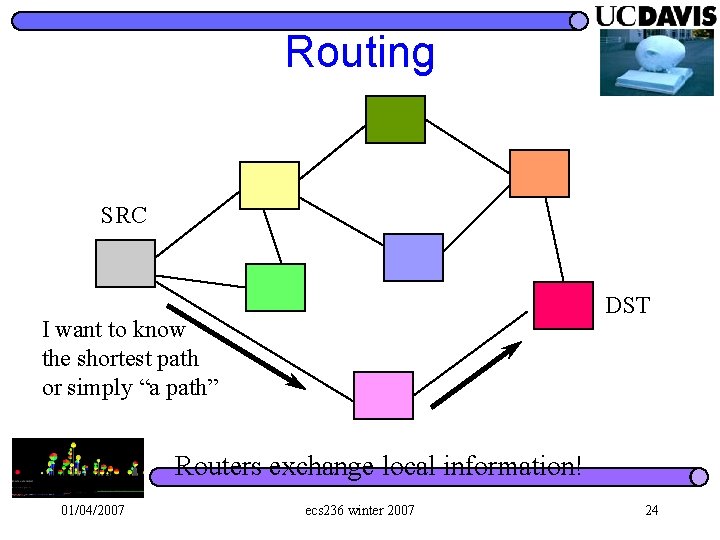
Routing SRC DST I want to know the shortest path or simply “a path” Routers exchange local information! 01/04/2007 ecs 236 winter 2007 24
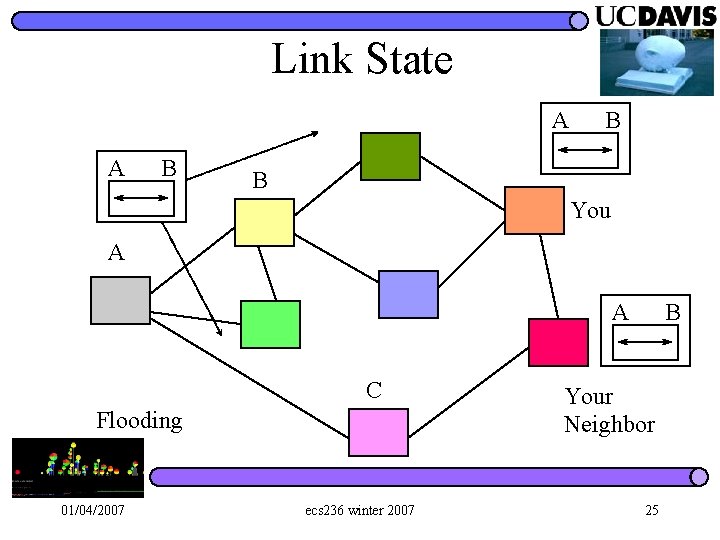
Link State A A B B B You A A C Flooding 01/04/2007 ecs 236 winter 2007 B Your Neighbor 25
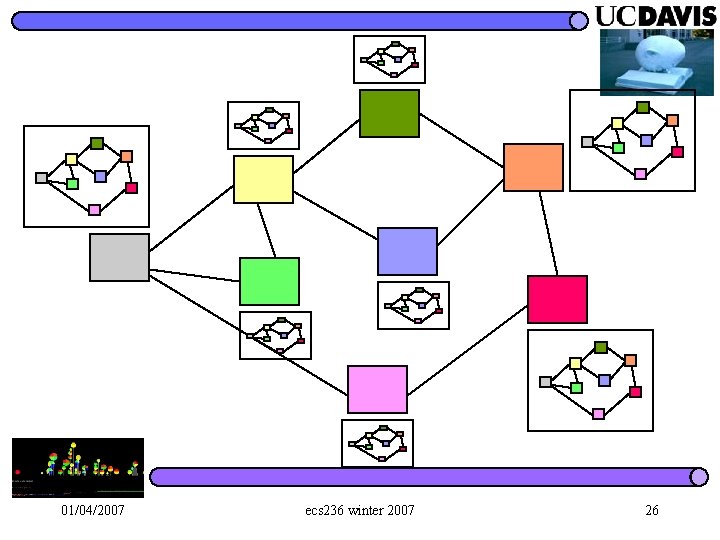
01/04/2007 ecs 236 winter 2007 26
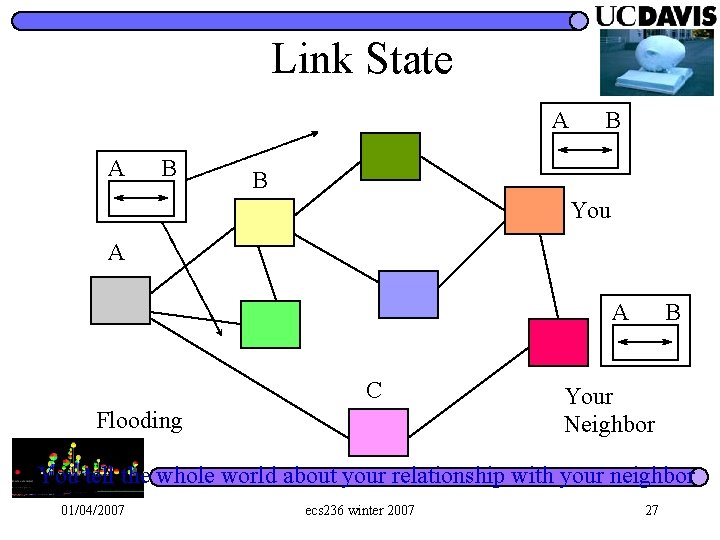
Link State A A B B B You A A C Flooding B Your Neighbor You tell the whole world about your relationship with your neighbor 01/04/2007 ecs 236 winter 2007 27
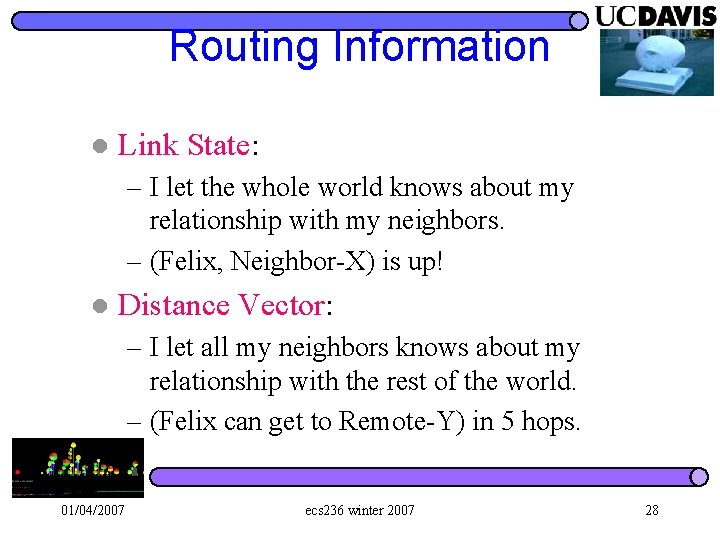
Routing Information l Link State: – I let the whole world knows about my relationship with my neighbors. – (Felix, Neighbor-X) is up! l Distance Vector: – I let all my neighbors knows about my relationship with the rest of the world. – (Felix can get to Remote-Y) in 5 hops. 01/04/2007 ecs 236 winter 2007 28
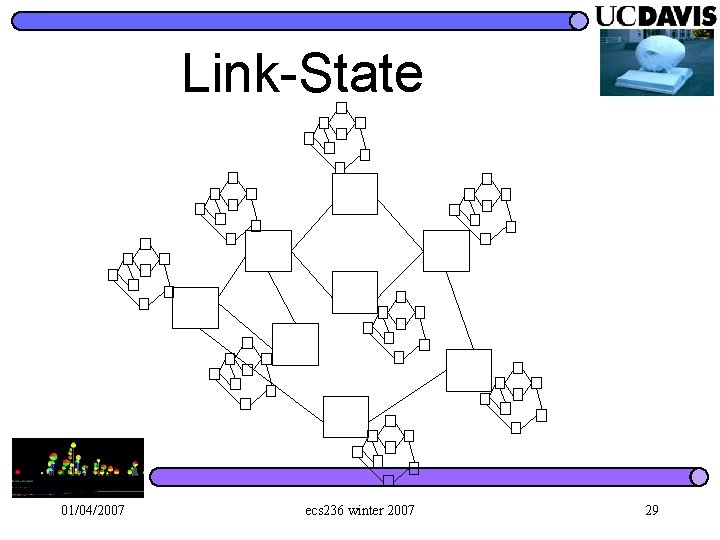
Link-State 01/04/2007 ecs 236 winter 2007 29
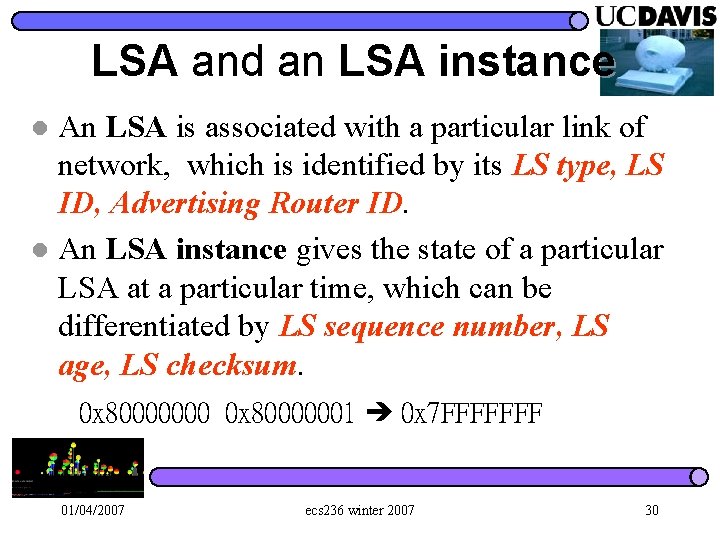
LSA and an LSA instance An LSA is associated with a particular link of network, which is identified by its LS type, LS ID, Advertising Router ID. l An LSA instance gives the state of a particular LSA at a particular time, which can be differentiated by LS sequence number, LS age, LS checksum. l 0 x 80000000 0 x 80000001 0 x 7 FFFFFFF 01/04/2007 ecs 236 winter 2007 30
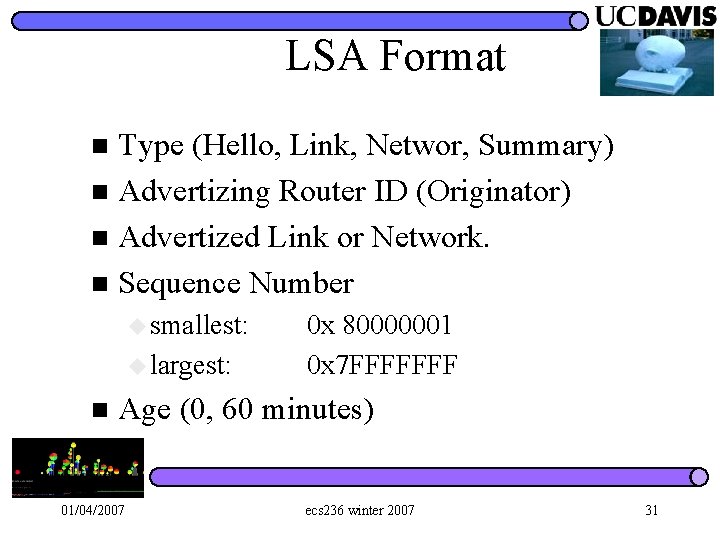
LSA Format Type (Hello, Link, Networ, Summary) n Advertizing Router ID (Originator) n Advertized Link or Network. n Sequence Number n u smallest: u largest: n 0 x 80000001 0 x 7 FFFFFFF Age (0, 60 minutes) 01/04/2007 ecs 236 winter 2007 31
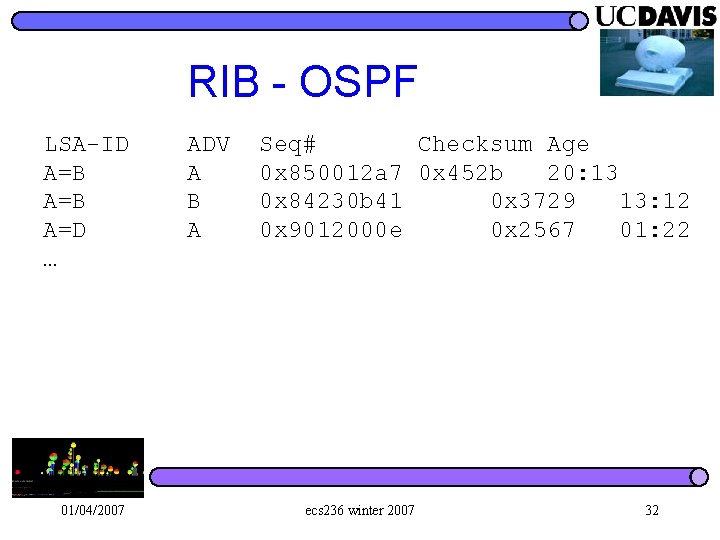
RIB - OSPF LSA-ID A=B A=D … 01/04/2007 ADV A B A Seq# Checksum Age 0 x 850012 a 7 0 x 452 b 20: 13 0 x 84230 b 41 0 x 3729 13: 12 0 x 9012000 e 0 x 2567 01: 22 ecs 236 winter 2007 32
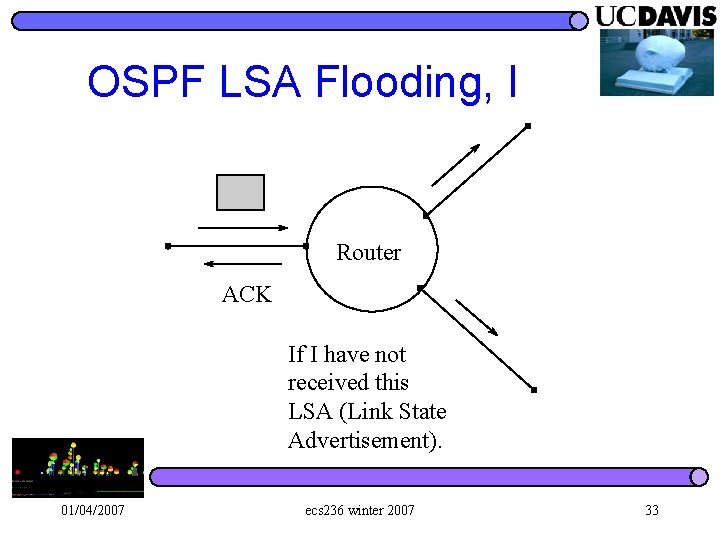
OSPF LSA Flooding, I Router ACK If I have not received this LSA (Link State Advertisement). 01/04/2007 ecs 236 winter 2007 33
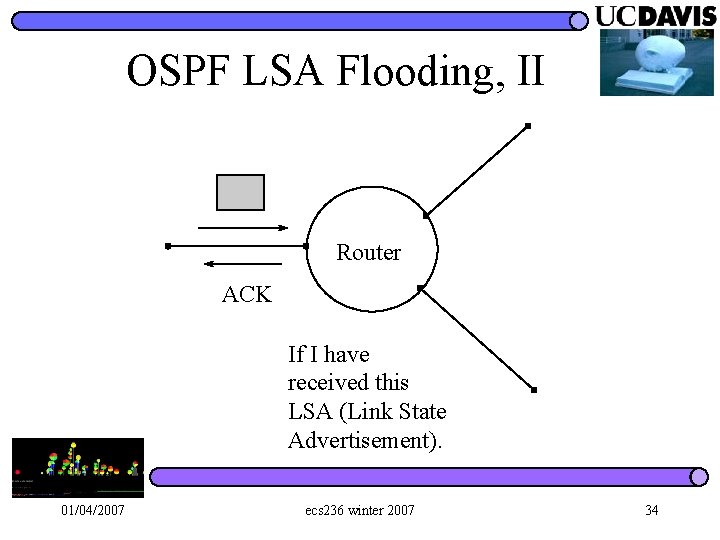
OSPF LSA Flooding, II Router ACK If I have received this LSA (Link State Advertisement). 01/04/2007 ecs 236 winter 2007 34
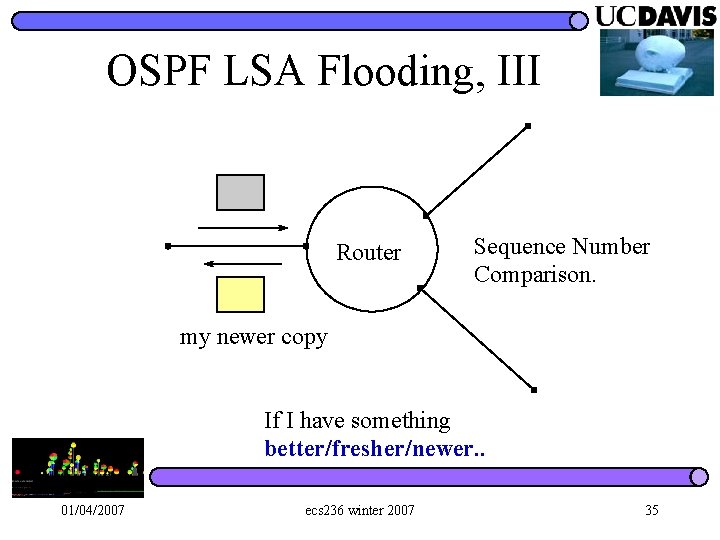
OSPF LSA Flooding, III Router Sequence Number Comparison. my newer copy If I have something better/fresher/newer. . 01/04/2007 ecs 236 winter 2007 35
How to decide “freshness”? ? 01/04/2007 ecs 236 winter 2007 36
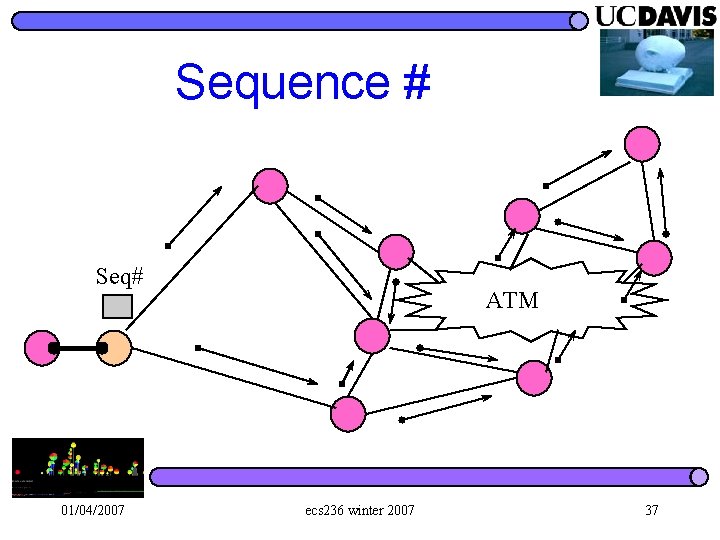
Sequence # Seq# 01/04/2007 ATM ecs 236 winter 2007 37
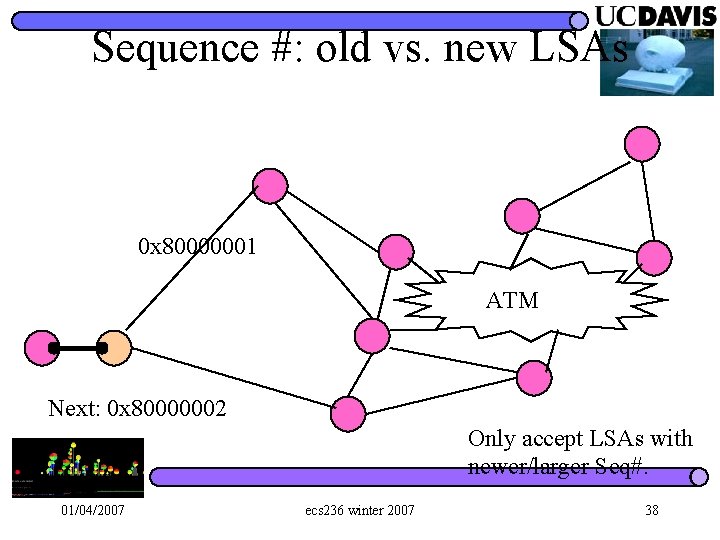
Sequence #: old vs. new LSAs 0 x 80000001 ATM Next: 0 x 80000002 Only accept LSAs with newer/larger Seq#. 01/04/2007 ecs 236 winter 2007 38
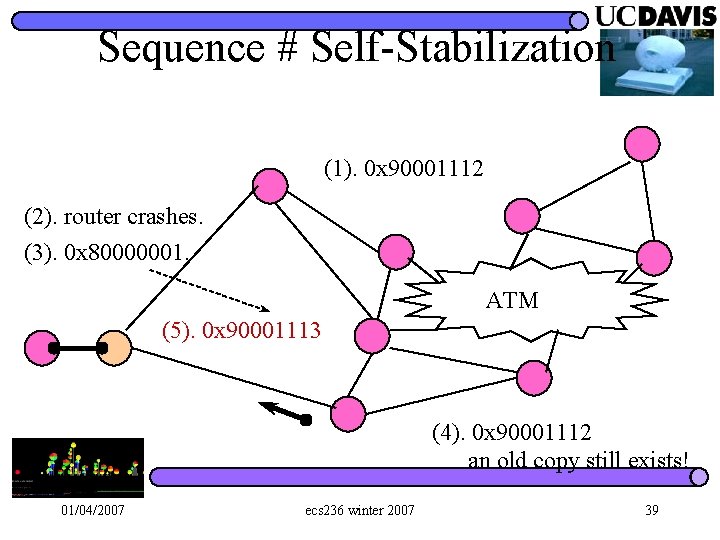
Sequence # Self-Stabilization (1). 0 x 90001112 (2). router crashes. (3). 0 x 80000001. ATM (5). 0 x 90001113 (4). 0 x 90001112 an old copy still exists! 01/04/2007 ecs 236 winter 2007 39
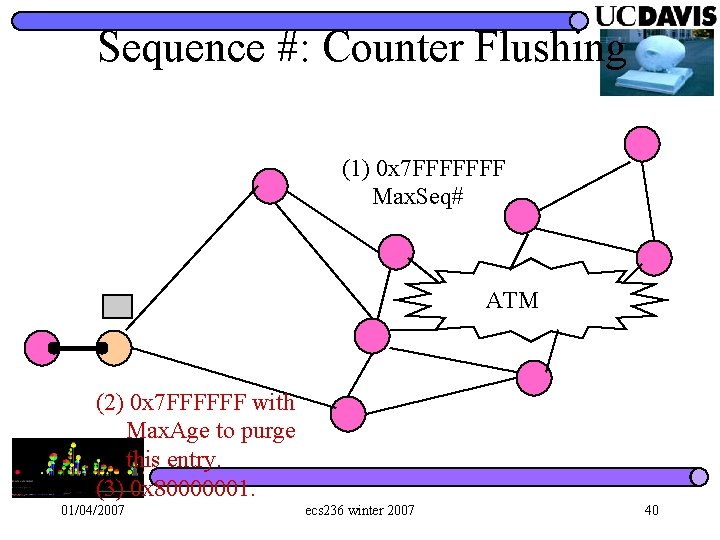
Sequence #: Counter Flushing (1) 0 x 7 FFFFFFF Max. Seq# ATM (2) 0 x 7 FFFFFF with Max. Age to purge this entry. (3) 0 x 80000001. 01/04/2007 ecs 236 winter 2007 40
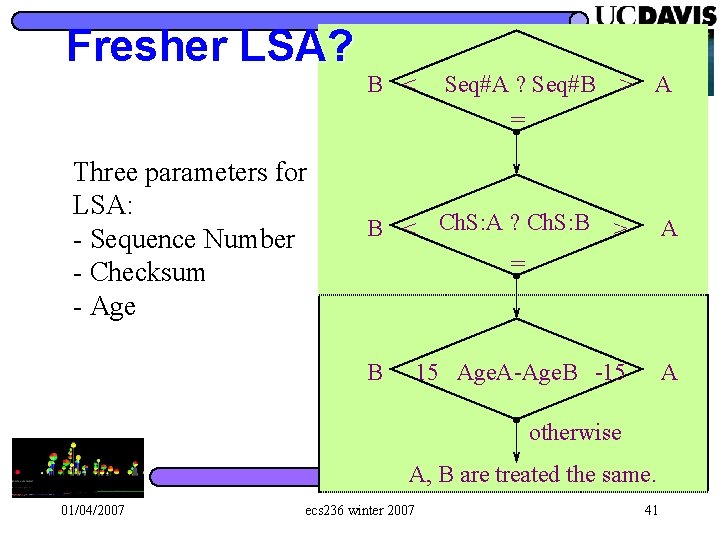
Fresher LSA? Three parameters for LSA: - Sequence Number - Checksum - Age B < Seq#A ? Seq#B > A = B < Ch. S: A ? Ch. S: B > A = B 15 Age. A-Age. B -15 A otherwise A, B are treated the same. 01/04/2007 ecs 236 winter 2007 41
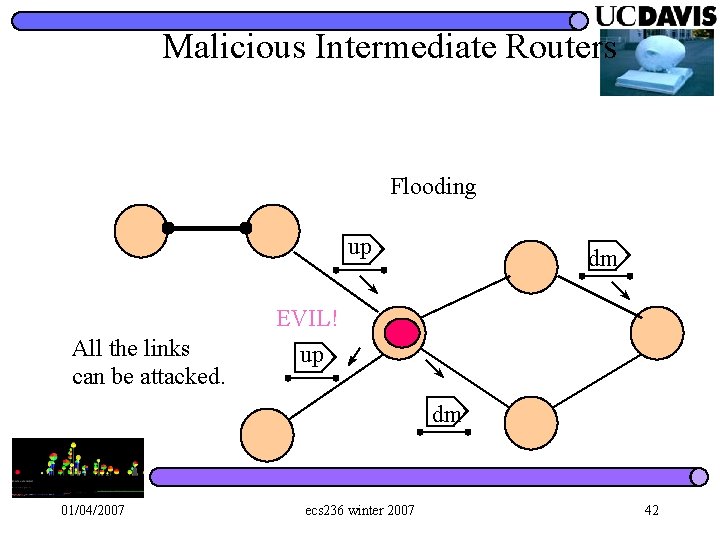
Malicious Intermediate Routers Flooding up All the links can be attacked. dm EVIL! up dm 01/04/2007 ecs 236 winter 2007 42
How to Attack OSPF? Think… l Try it!! l – What is the objective? – How to accomplish your goal? 01/04/2007 ecs 236 winter 2007 43
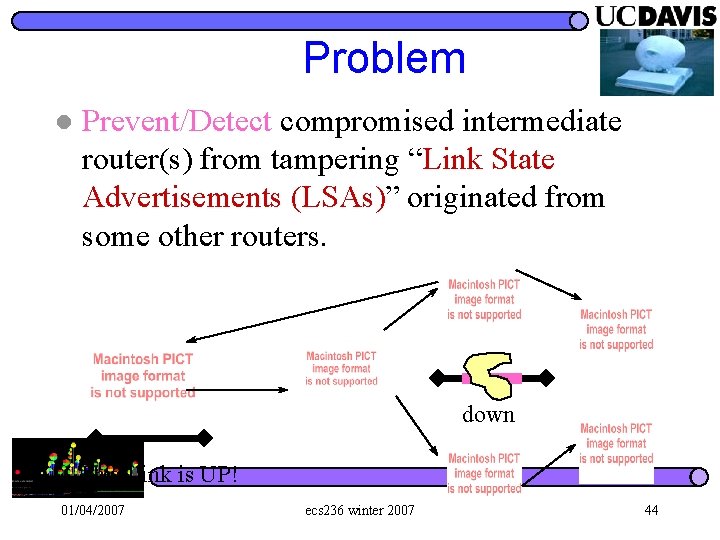
Problem l Prevent/Detect compromised intermediate router(s) from tampering “Link State Advertisements (LSAs)” originated from some other routers. down This Link is UP! 01/04/2007 ecs 236 winter 2007 44
Defense? ? Crypto-based l Non-crypto-based l 01/04/2007 ecs 236 winter 2007 45
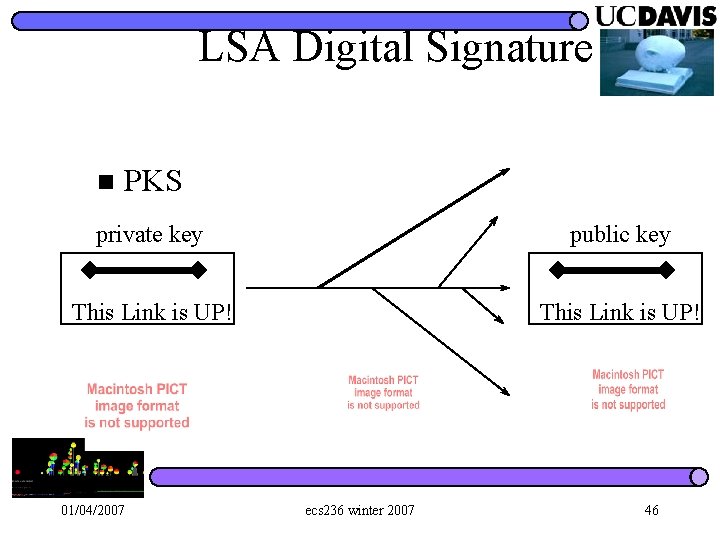
LSA Digital Signature n PKS private key public key This Link is UP! 01/04/2007 ecs 236 winter 2007 46
Advantages for PKS One compromised router will not be able to affect others about other links. n With only key-MD 5, one compromised router can disable all the crypto. n 01/04/2007 ecs 236 winter 2007 47
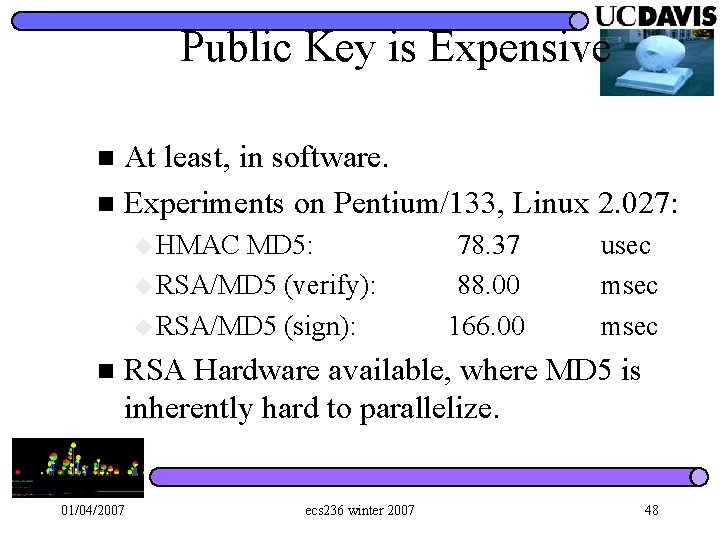
Public Key is Expensive At least, in software. n Experiments on Pentium/133, Linux 2. 027: n u HMAC MD 5: u RSA/MD 5 (verify): u RSA/MD 5 (sign): n 78. 37 88. 00 166. 00 usec msec RSA Hardware available, where MD 5 is inherently hard to parallelize. 01/04/2007 ecs 236 winter 2007 48
Prevention LSA Originator Digital Signature (Perlman, Murphy/Badger, Smith/JJ) n Debatable Concerns: (OSPF wk-group) n u RSA is too expensive (about 1, 000 times worse in signature verification with 512 bit keys) u PKI Certificate is expensive. u There are other routing infrastructure attacks that can not be prevented by LSA Digital Signatures. (Cost/Market concern) u Political and Technical. 01/04/2007 ecs 236 winter 2007 49
Can we do it without PKI? l Preventing compromised intermediate routers? ? ? 01/04/2007 ecs 236 winter 2007 50
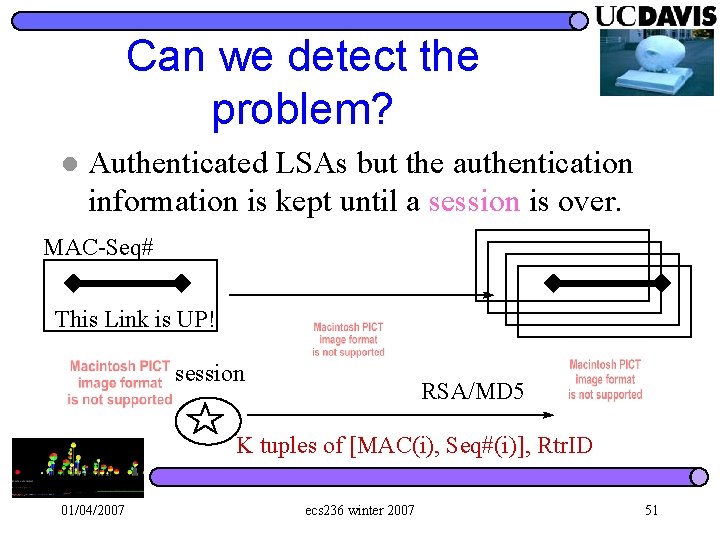
Can we detect the problem? l Authenticated LSAs but the authentication information is kept until a session is over. MAC-Seq# This Link is UP! session RSA/MD 5 K tuples of [MAC(i), Seq#(i)], Rtr. ID 01/04/2007 ecs 236 winter 2007 51
Prevention versus Detection Prevention: pay a fixed price anyway, even no bad guy exists. l Detection/Isolation: “hopefully” pay less when no bad guy exists. pay more when trying to isolate the bad guys. l Self-Stabilization Time: l – (Detection + Isolation) 01/04/2007 ecs 236 winter 2007 52
Let’s look at the attack again!! l Why do we need to ADD something to handle OSPF attacks? 01/04/2007 ecs 236 winter 2007 53
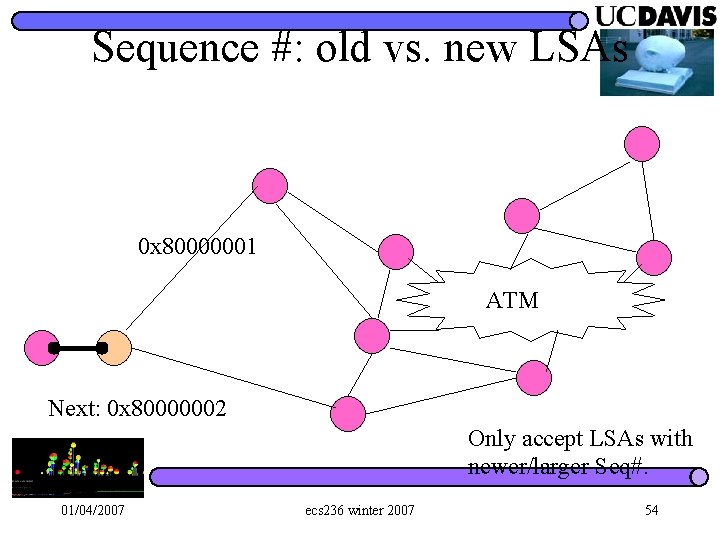
Sequence #: old vs. new LSAs 0 x 80000001 ATM Next: 0 x 80000002 Only accept LSAs with newer/larger Seq#. 01/04/2007 ecs 236 winter 2007 54
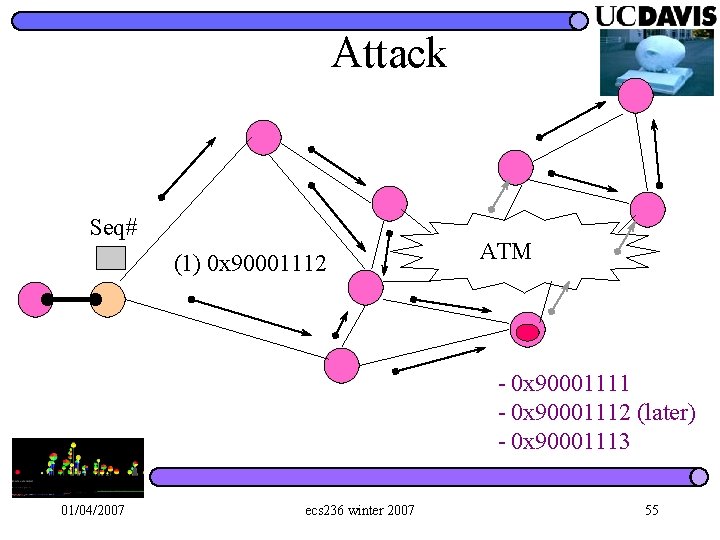
Attack Seq# (1) 0 x 90001112 ATM - 0 x 90001111 - 0 x 90001112 (later) - 0 x 90001113 01/04/2007 ecs 236 winter 2007 55
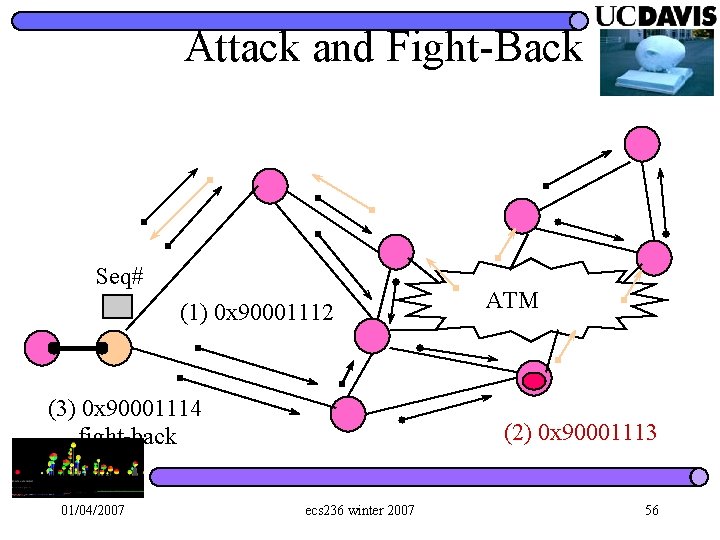
Attack and Fight-Back Seq# (1) 0 x 90001112 (3) 0 x 90001114 fight-back 01/04/2007 ATM (2) 0 x 90001113 ecs 236 winter 2007 56
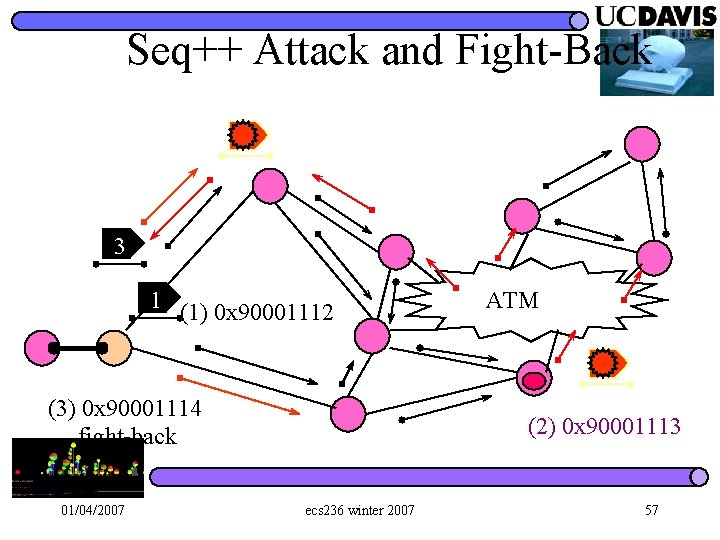
Seq++ Attack and Fight-Back 3 1 (1) 0 x 90001112 (3) 0 x 90001114 fight-back 01/04/2007 ATM (2) 0 x 90001113 ecs 236 winter 2007 57
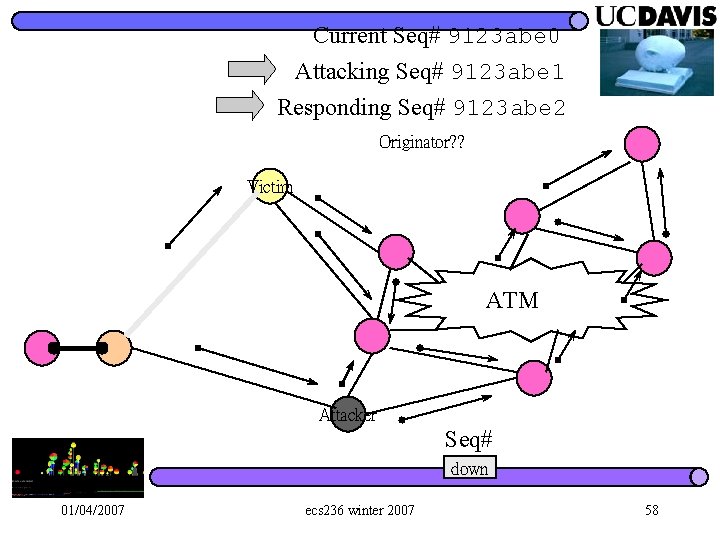
Current Seq# 9123 abe 0 Attacking Seq# 9123 abe 1 Responding Seq# 9123 abe 2 Originator? ? Victim ATM Attacker Seq# down 01/04/2007 ecs 236 winter 2007 58
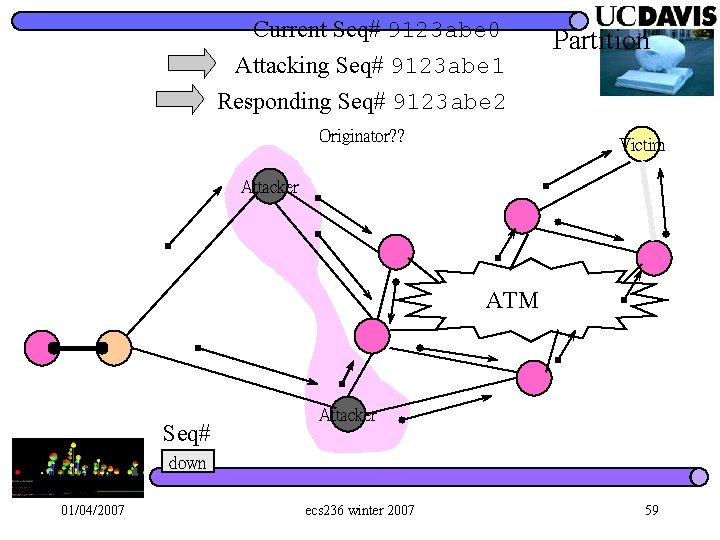
Current Seq# 9123 abe 0 Attacking Seq# 9123 abe 1 Responding Seq# 9123 abe 2 Originator? ? Partition Victim Attacker ATM Seq# Attacker down 01/04/2007 ecs 236 winter 2007 59
OSPF Security Strength In most cases, if something goes wrong, the advertizing router will detect it and try to correct it. l The bad guy has to persistently inject bad LSAs. l Self-Stabilization Protocols: can not handle continuous faults but force the attacker to perform only persistent attacks. l 01/04/2007 ecs 236 winter 2007 60
A Principle/Heuristic Rule of Intrusion Detection l Hit-and-Run Attacks: Hard to Detect/Isolate – Inject one (or very few) bad packet causing permanent or long term damage. l Persistent Attacks: – The bad guy has to continuously inject attack packets. 01/04/2007 ecs 236 winter 2007 61
Network Protocol/System Design If we can force the attackers to only launch “persistent attacks, ” we have a better chance to detect and isolate the attack sources. l OSPF Flooding, for example, does a fairly good job. (still need some formal/theoretical research work here…) l 01/04/2007 ecs 236 winter 2007 62
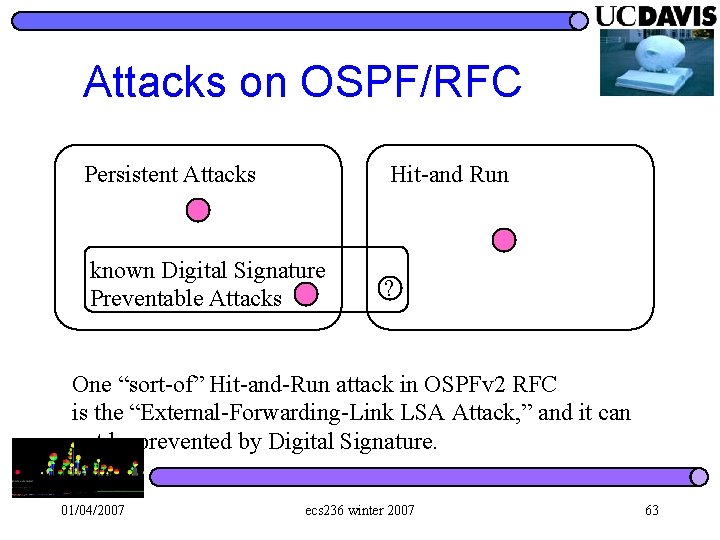
Attacks on OSPF/RFC Persistent Attacks Hit-and Run known Digital Signature Preventable Attacks ? One “sort-of” Hit-and-Run attack in OSPFv 2 RFC is the “External-Forwarding-Link LSA Attack, ” and it can not be prevented by Digital Signature. 01/04/2007 ecs 236 winter 2007 63
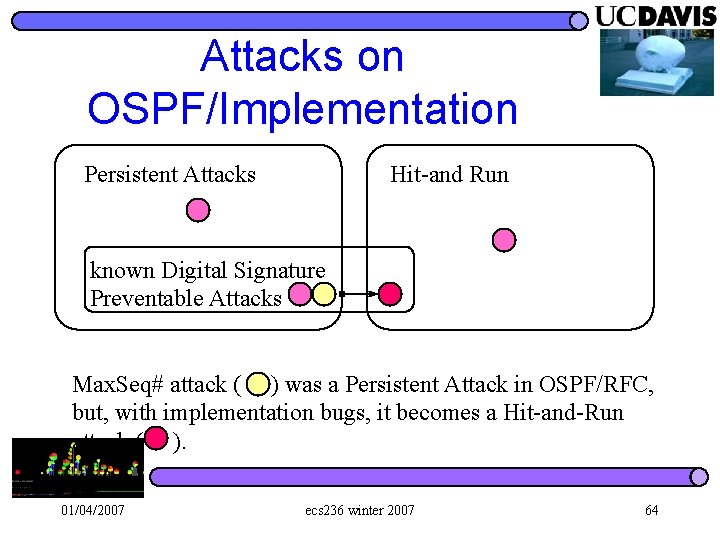
Attacks on OSPF/Implementation Persistent Attacks Hit-and Run known Digital Signature Preventable Attacks Max. Seq# attack ( ) was a Persistent Attack in OSPF/RFC, but, with implementation bugs, it becomes a Hit-and-Run attack ( ). 01/04/2007 ecs 236 winter 2007 64
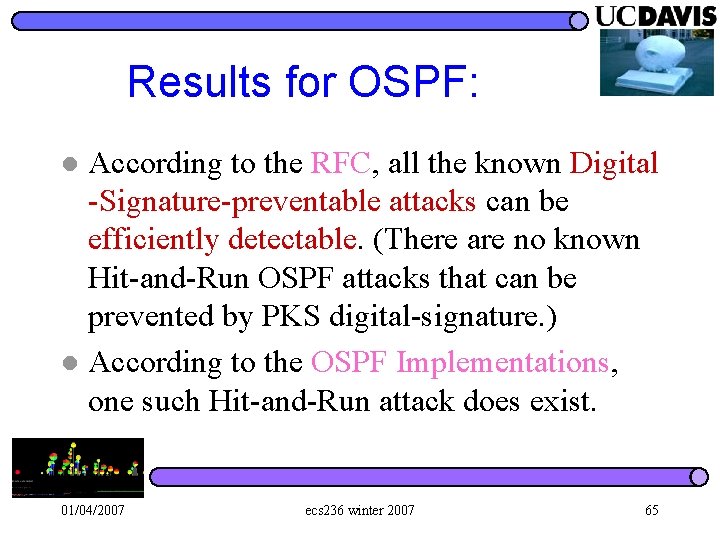
Results for OSPF: According to the RFC, all the known Digital -Signature-preventable attacks can be efficiently detectable. (There are no known Hit-and-Run OSPF attacks that can be prevented by PKS digital-signature. ) l According to the OSPF Implementations, one such Hit-and-Run attack does exist. l 01/04/2007 ecs 236 winter 2007 65
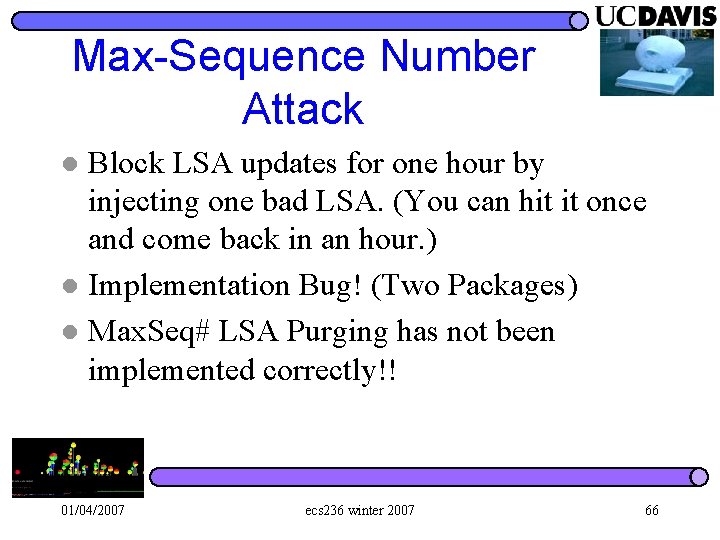
Max-Sequence Number Attack Block LSA updates for one hour by injecting one bad LSA. (You can hit it once and come back in an hour. ) l Implementation Bug! (Two Packages) l Max. Seq# LSA Purging has not been implemented correctly!! l 01/04/2007 ecs 236 winter 2007 66
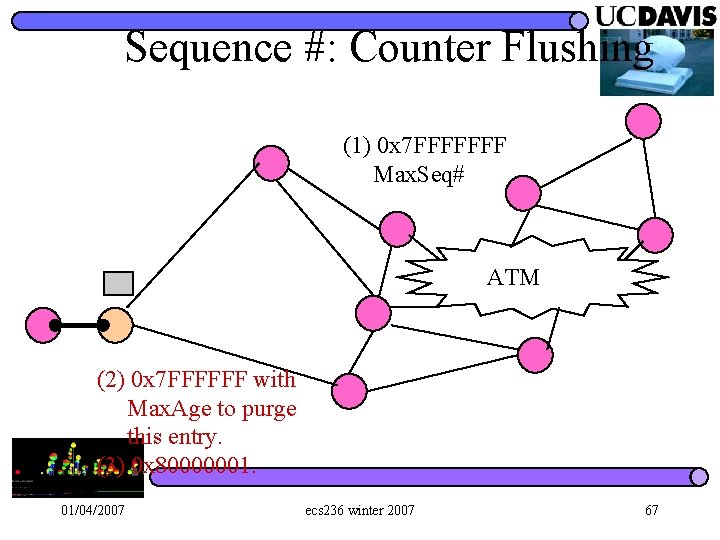
Sequence #: Counter Flushing (1) 0 x 7 FFFFFFF Max. Seq# ATM (2) 0 x 7 FFFFFF with Max. Age to purge this entry. (3) 0 x 80000001. 01/04/2007 ecs 236 winter 2007 67
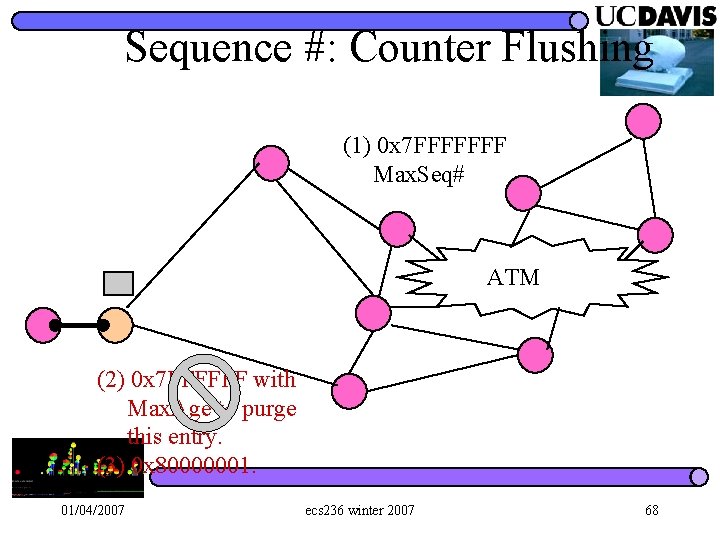
Sequence #: Counter Flushing (1) 0 x 7 FFFFFFF Max. Seq# ATM (2) 0 x 7 FFFFFF with Max. Age to purge this entry. (3) 0 x 80000001. 01/04/2007 ecs 236 winter 2007 68
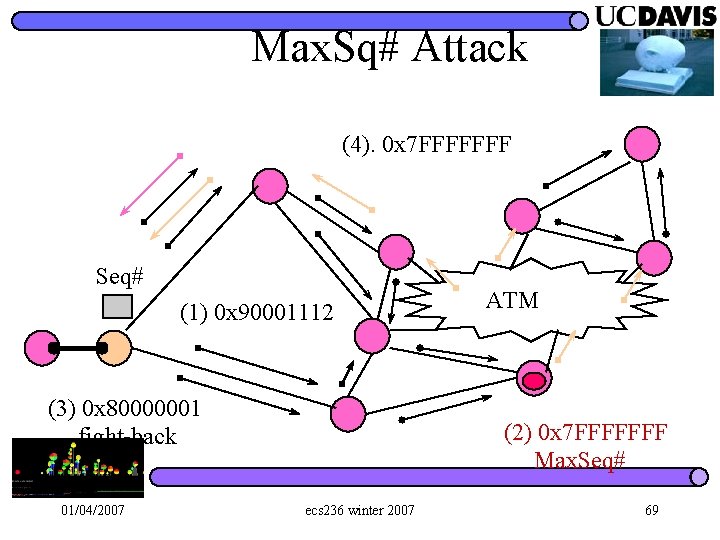
Max. Sq# Attack (4). 0 x 7 FFFFFFF Seq# (1) 0 x 90001112 (3) 0 x 80000001 fight-back 01/04/2007 ATM (2) 0 x 7 FFFFFFF Max. Seq# ecs 236 winter 2007 69
Properties of Max. Seq# Attacks l l Hit-and-Run for an Hour. The bad guy can “control” the topology database for an hour. The Victim continuously argues with its (very likely, honest) neighbors about which LSA is fresher. (0 x 7 FFFFFFF versus 0 x 80000001). To eliminate the problem before one hour, “All” routers must be shut down “simultaneously. ” Or, have an active process to pump the purging packets into the network. 01/04/2007 ecs 236 winter 2007 70
Max-Sequence Number Attack l l Block LSA updates for one hour by injecting one bad LSA. (You can hit it once and come back in an hour. ) Implementation Bug! (Two independently developed OSPF packages. ) Max. Seq# LSA Purging has not been implemented correctly!! Announced in May, 1997. 01/04/2007 ecs 236 winter 2007 71
Detection Isolation Detection l Understand l Isolation l 01/04/2007 ecs 236 winter 2007 72
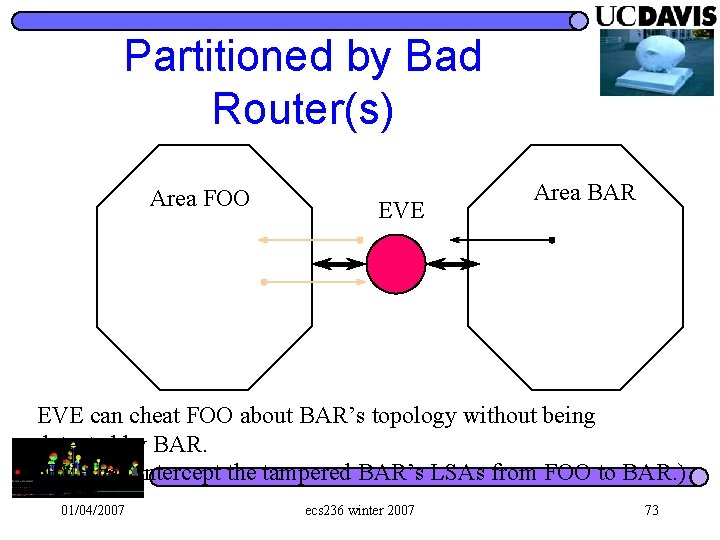
Partitioned by Bad Router(s) Area FOO EVE Area BAR EVE can cheat FOO about BAR’s topology without being detected by BAR. (EVE can intercept the tampered BAR’s LSAs from FOO to BAR. ) 01/04/2007 ecs 236 winter 2007 73
But…. Any packets from FOO to BAR will pass EVE anyway. (I. e. , EVE already has the access to all the packet streams between FOO and BAR. ) l It is not necessary for EVE to attack the routing information exchange protocols. l 01/04/2007 ecs 236 winter 2007 74
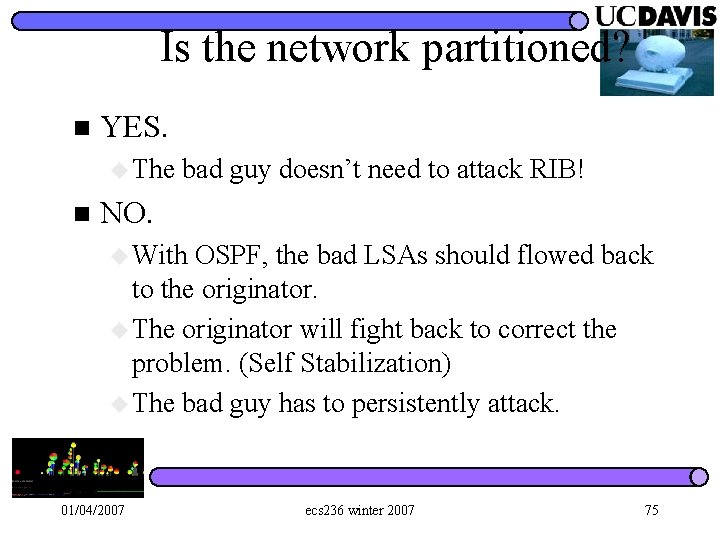
Is the network partitioned? n YES. u The bad guy doesn’t need to attack RIB! n NO. u With OSPF, the bad LSAs should flowed back to the originator. u The originator will fight back to correct the problem. (Self Stabilization) u The bad guy has to persistently attack. 01/04/2007 ecs 236 winter 2007 75
- Slides: 75