1 Layer 2 Switching Switching breaks up large
1
Layer 2 Switching Ø Switching breaks up large collision domains into smaller ones Ø Collision domain is a network segment with two or more devices sharing the same bandwidth. Ø A hub network is a typical example of this type of technology Ø Each port on a switch is actually its own collision domain, you can make a much better Ethernet LAN network just by replacing your hubs with switches 2
Switching Services Ø Unlike bridges that use software to create and manage a filter table, switches use Application Specific Integrated Circuits (ASICs) Ø Layer 2 switches and bridges are faster than routers because they don’t take up time looking at the Network layer header information. Ø They look at the frame’s hardware addresses before deciding to either forward the frame or drop it. Ø layer 2 switching so efficient is that no modification to the data packet takes place 3
How Switches and Bridges Learn Addresses Bridges and switches learn in the following ways: • Reading the source MAC address of each frame or datagram • received Recording the port on which the MAC address was received. In this way, the bridge or switch learns which addresses belong to the devices connected to each port. 4
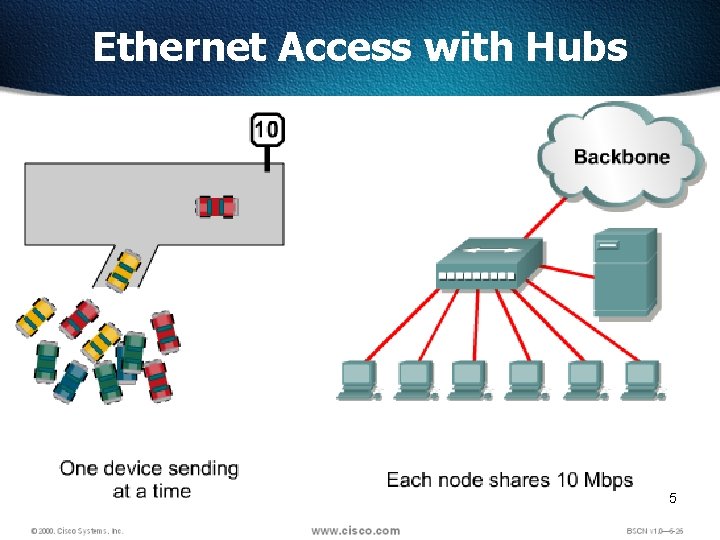
Ethernet Access with Hubs 5
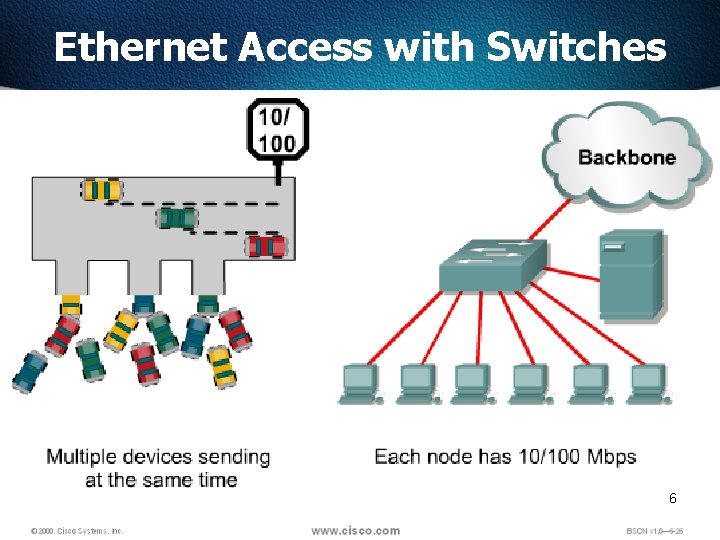
Ethernet Access with Switches 6
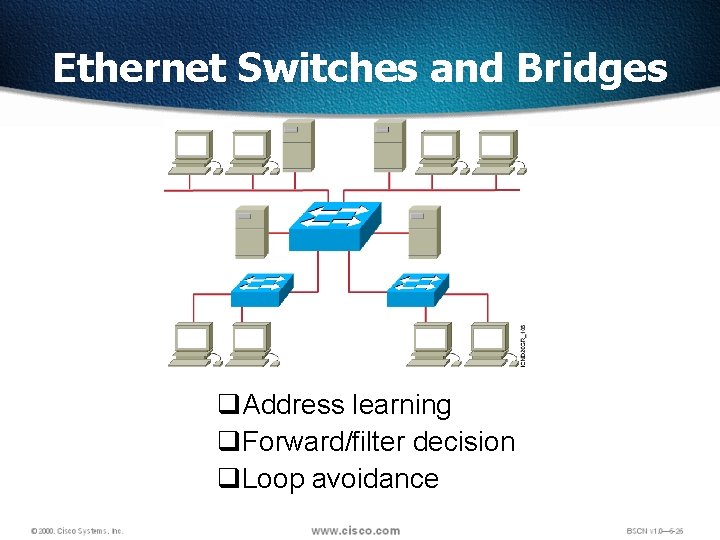
Ethernet Switches and Bridges q. Address learning q. Forward/filter decision q. Loop avoidance
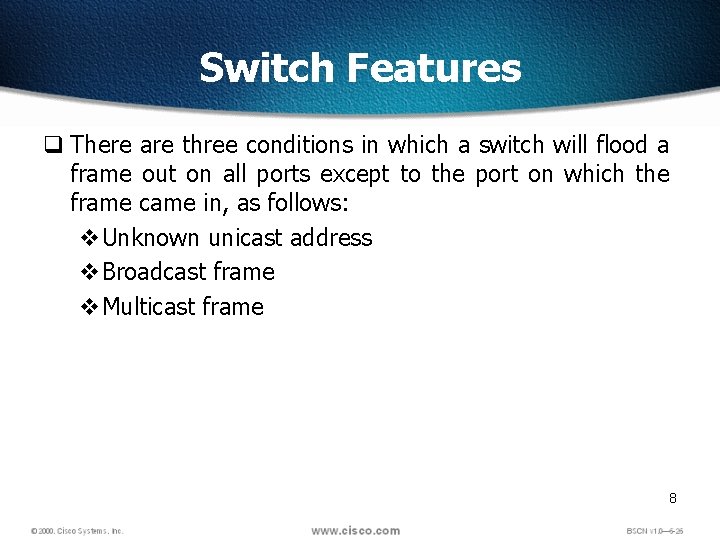
Switch Features q There are three conditions in which a switch will flood a frame out on all ports except to the port on which the frame came in, as follows: v. Unknown unicast address v. Broadcast frame v. Multicast frame 8
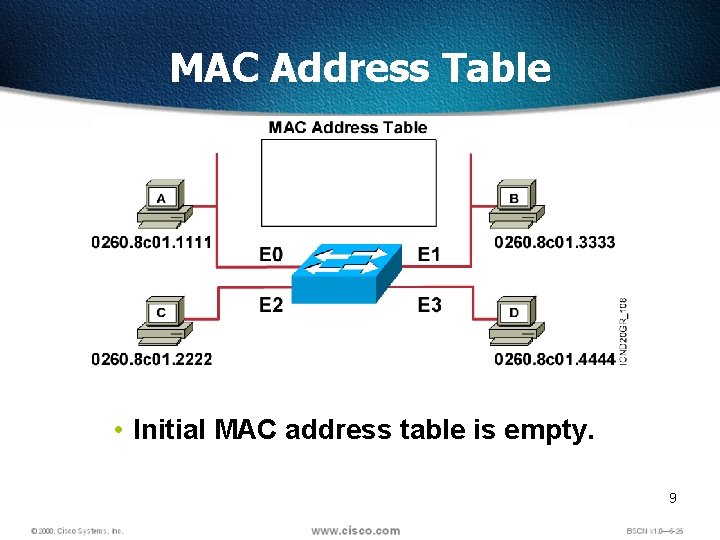
MAC Address Table • Initial MAC address table is empty. 9
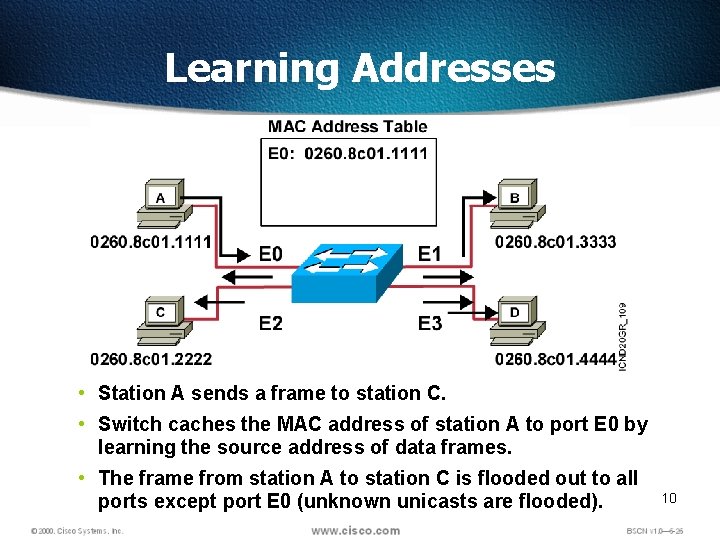
Learning Addresses • Station A sends a frame to station C. • Switch caches the MAC address of station A to port E 0 by learning the source address of data frames. • The frame from station A to station C is flooded out to all ports except port E 0 (unknown unicasts are flooded). 10
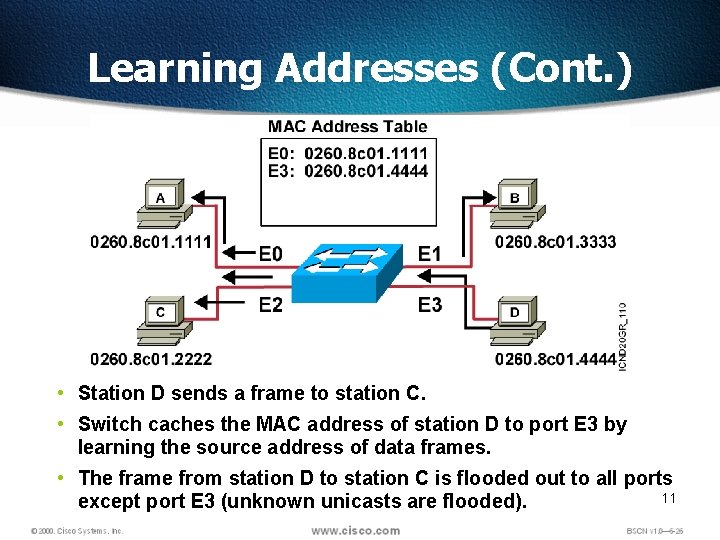
Learning Addresses (Cont. ) • Station D sends a frame to station C. • Switch caches the MAC address of station D to port E 3 by learning the source address of data frames. • The frame from station D to station C is flooded out to all ports 11 except port E 3 (unknown unicasts are flooded).
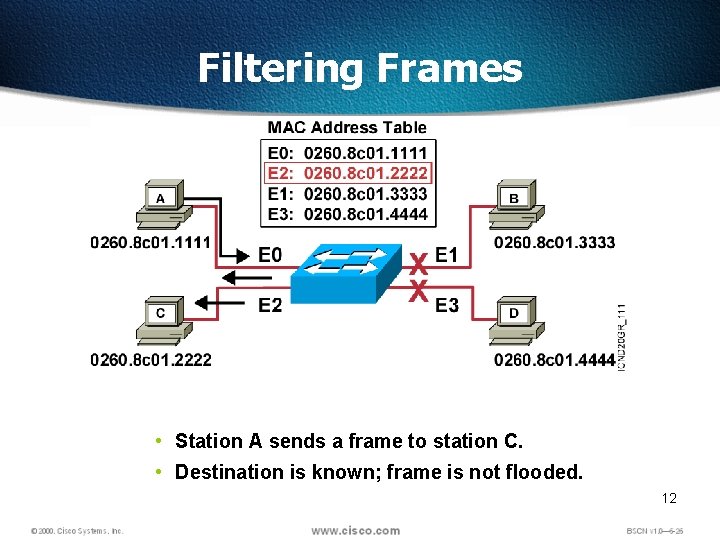
Filtering Frames • Station A sends a frame to station C. • Destination is known; frame is not flooded. 12
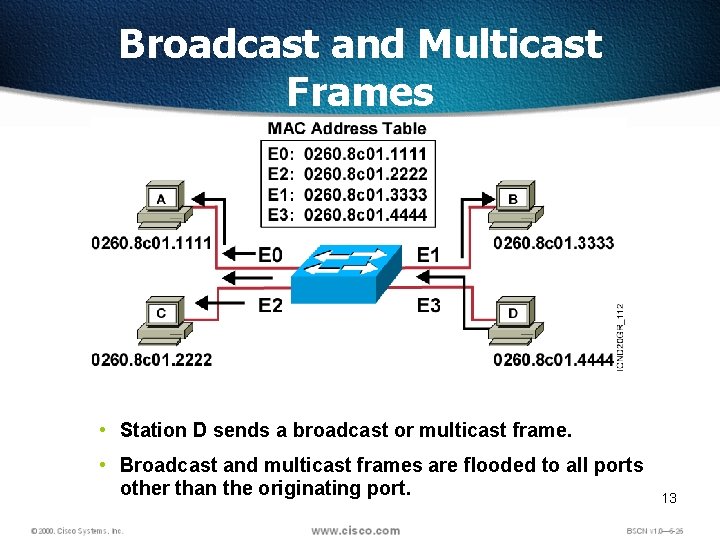
Broadcast and Multicast Frames • Station D sends a broadcast or multicast frame. • Broadcast and multicast frames are flooded to all ports other than the originating port. 13
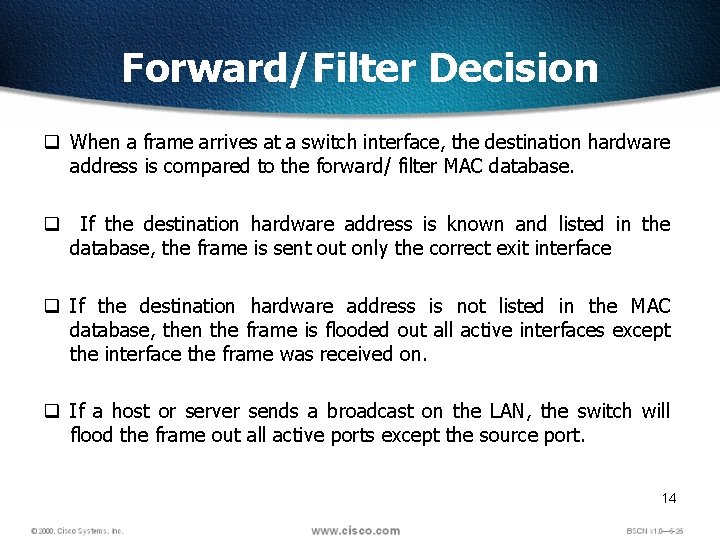
Forward/Filter Decision q When a frame arrives at a switch interface, the destination hardware address is compared to the forward/ filter MAC database. q If the destination hardware address is known and listed in the database, the frame is sent out only the correct exit interface q If the destination hardware address is not listed in the MAC database, then the frame is flooded out all active interfaces except the interface the frame was received on. q If a host or server sends a broadcast on the LAN, the switch will flood the frame out all active ports except the source port. 14
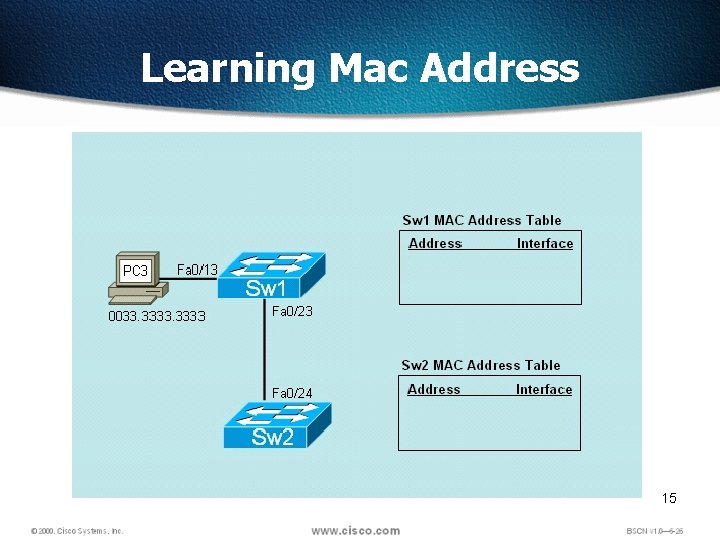
Learning Mac Address 15
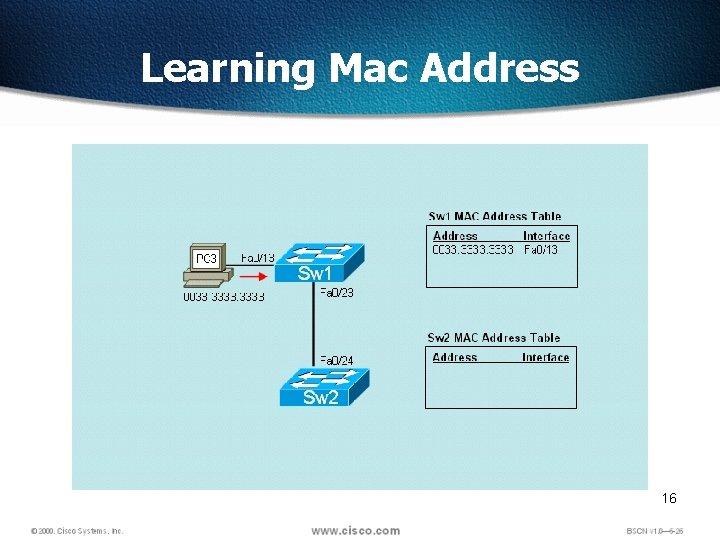
Learning Mac Address 16
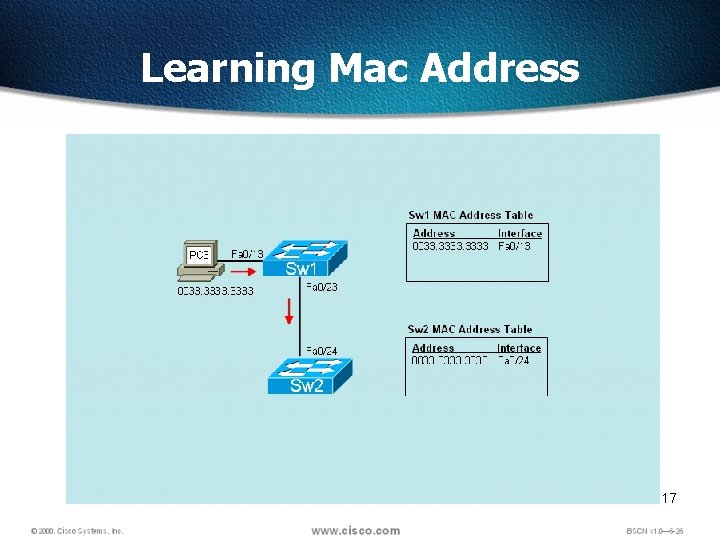
Learning Mac Address 17
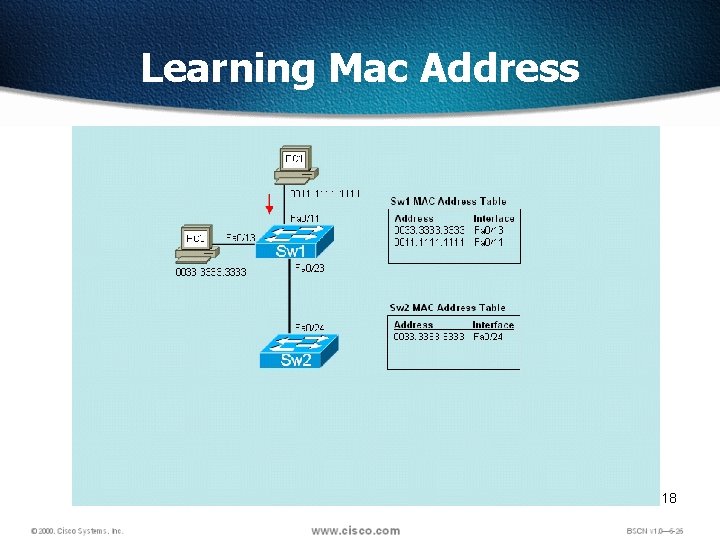
Learning Mac Address 18
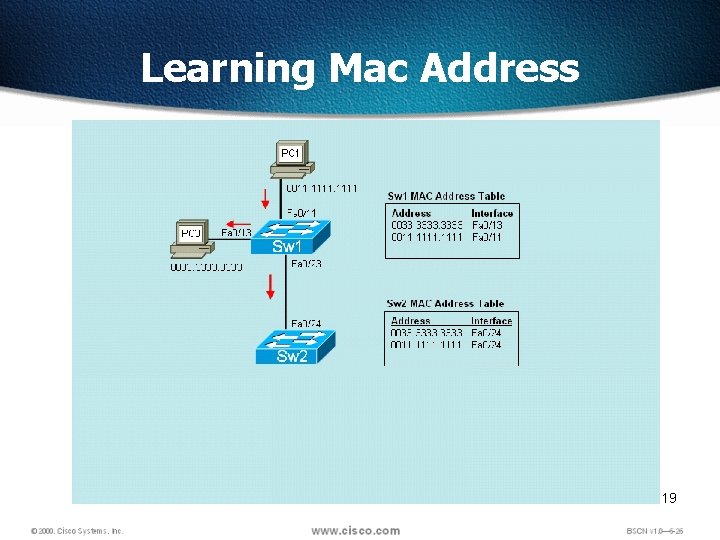
Learning Mac Address 19
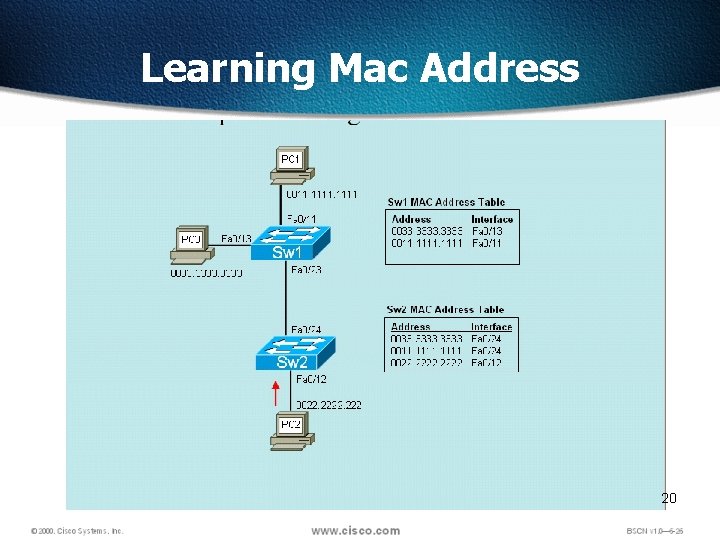
Learning Mac Address 20
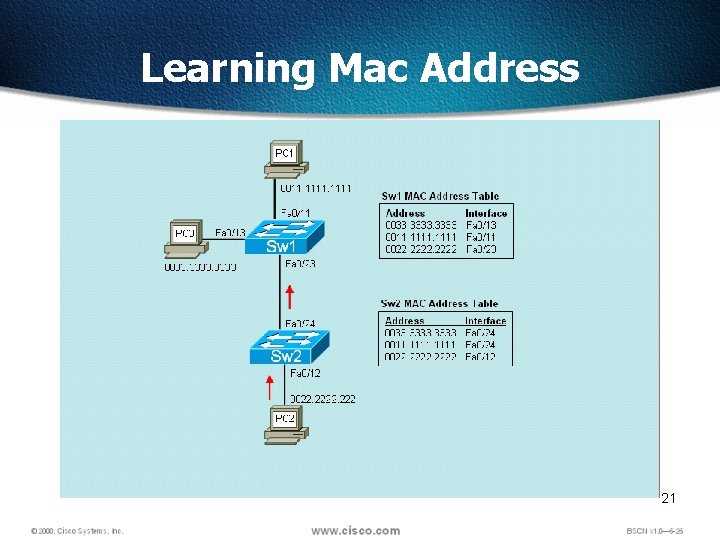
Learning Mac Address 21
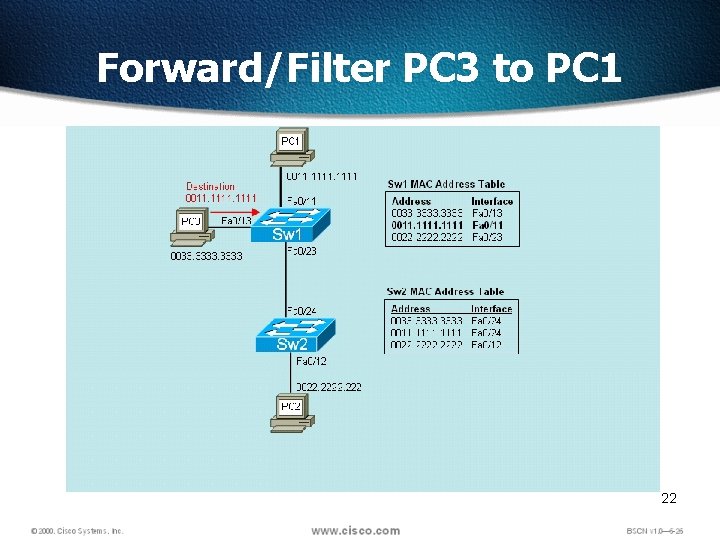
Forward/Filter PC 3 to PC 1 22
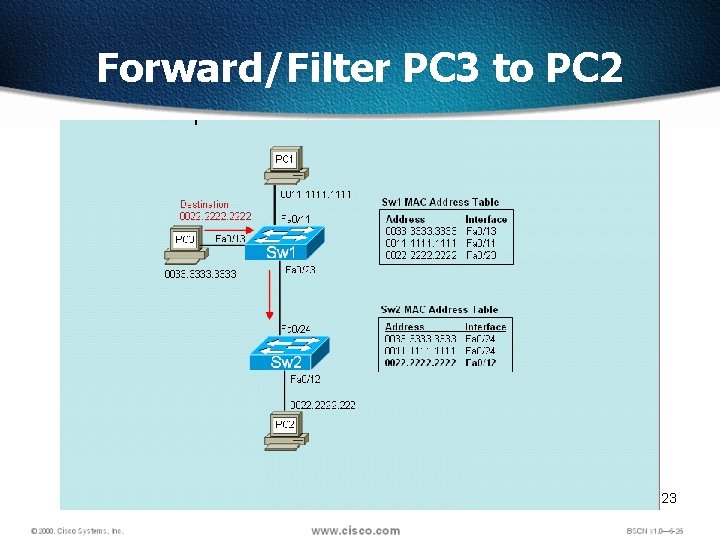
Forward/Filter PC 3 to PC 2 23
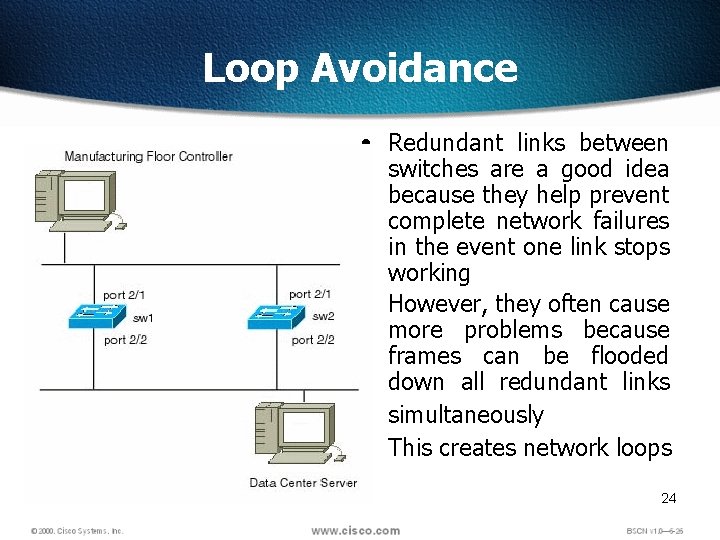
Loop Avoidance • Redundant links between switches are a good idea because they help prevent complete network failures in the event one link stops working • However, they often cause more problems because frames can be flooded down all redundant links simultaneously • This creates network loops 24
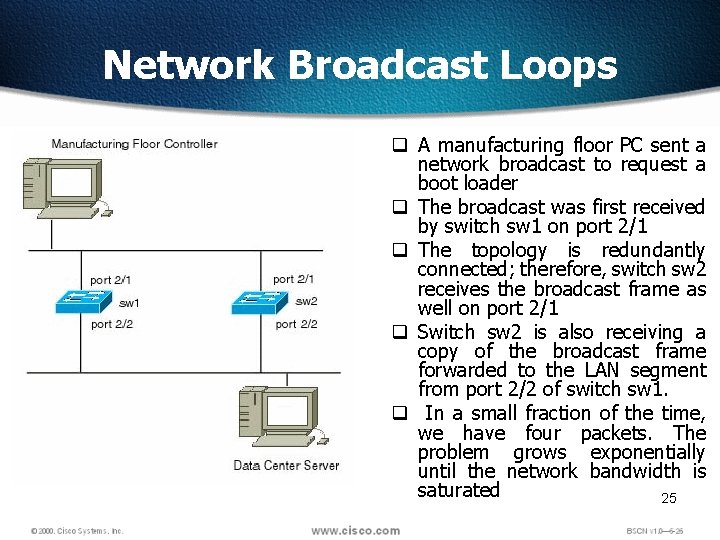
Network Broadcast Loops q A manufacturing floor PC sent a network broadcast to request a boot loader q The broadcast was first received by switch sw 1 on port 2/1 q The topology is redundantly connected; therefore, switch sw 2 receives the broadcast frame as well on port 2/1 q Switch sw 2 is also receiving a copy of the broadcast frame forwarded to the LAN segment from port 2/2 of switch sw 1. q In a small fraction of the time, we have four packets. The problem grows exponentially until the network bandwidth is saturated 25
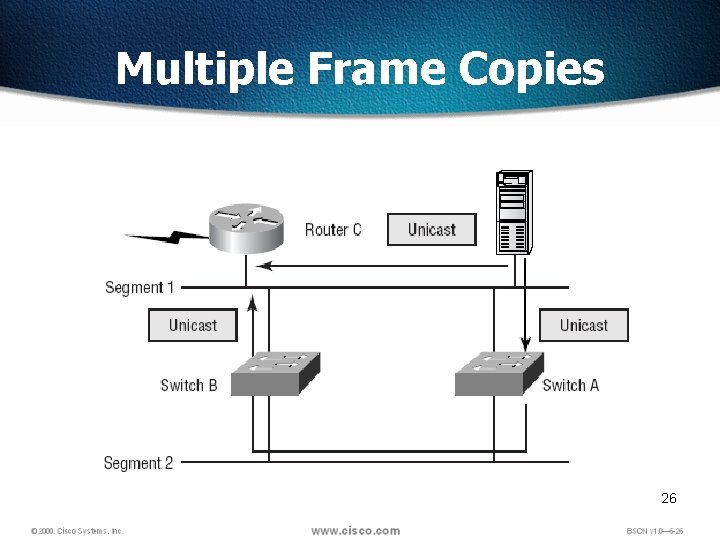
Multiple Frame Copies 26
27
Overview q. Redundancy in a network is extremely important because redundancy allows networks to be fault tolerant. q. Redundant topologies based on switches and bridges are subject to broadcast storms, multiple frame transmissions, and MAC address database instability. q. Therefore network redundancy requires careful planning and monitoring to function properly. q. The Spanning-Tree Protocol is used in switched networks to create a loop free network 28
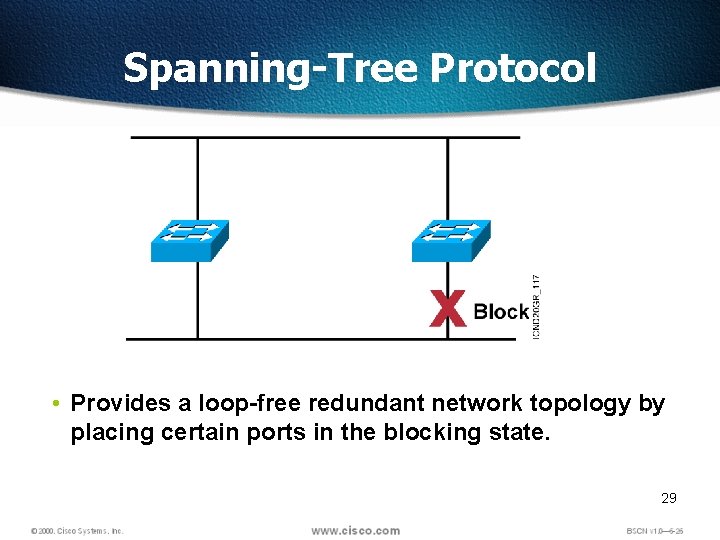
Spanning-Tree Protocol • Provides a loop-free redundant network topology by placing certain ports in the blocking state. 29
Spanning Tree Protocol q. Spanning Tree Protocol resides in Data link Layer q. Ethernet bridges and switches can implement the IEEE 802. 1 D Spanning-Tree Protocol and use the spanning-tree algorithm to construct a loop free network. 30
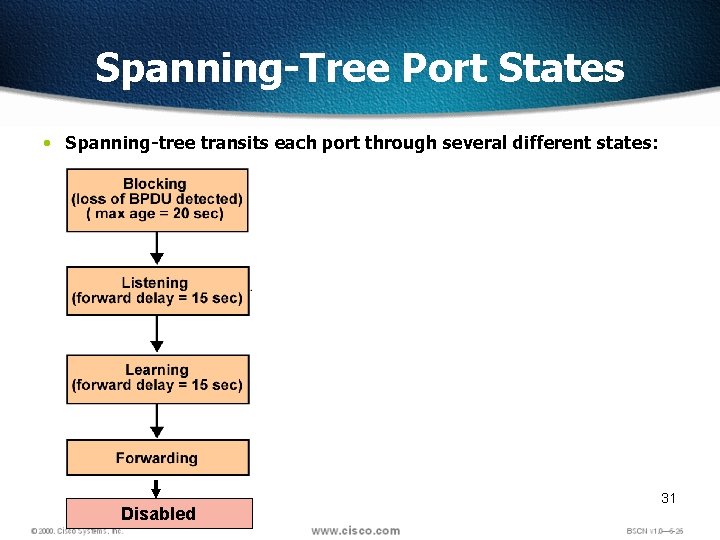
Spanning-Tree Port States • Spanning-tree transits each port through several different states: Disabled 31
Selecting the Root Bridge q. The first decision that all switches in the network make, is to identify the root bridge. q. When a switch is turned on, the spanning-tree algorithm is used to identify the root bridge. BPDUs are sent out with the Bridge ID (BID). q. The BID consists of a bridge priority that defaults to 32768 and the switch base MAC address. q. When a switch first starts up, it assumes it is the root switch and sends BPDUs. These BPDUs contain BID. q. All bridges see these and decide that the bridge with the smallest BID value will be the root bridge. q. A network administrator may want to influence the decision by setting the switch priority to a smaller value than the default. 32
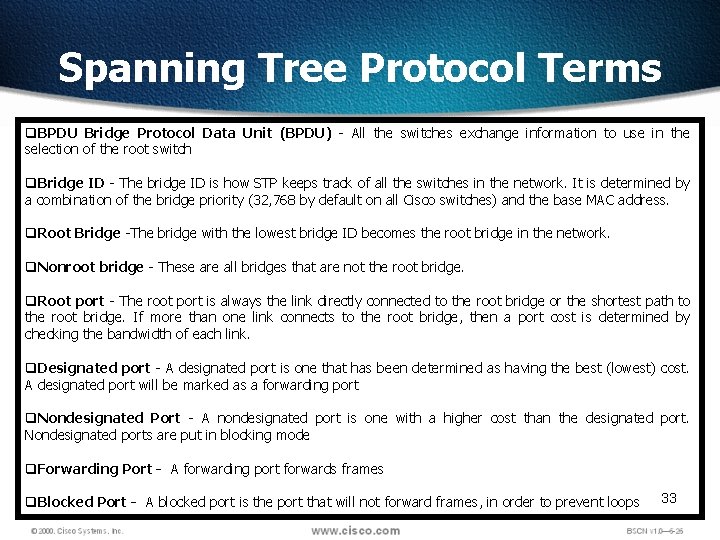
Spanning Tree Protocol Terms q. BPDU Bridge Protocol Data Unit (BPDU) - All the switches exchange information to use in the selection of the root switch q. Bridge ID - The bridge ID is how STP keeps track of all the switches in the network. It is determined by a combination of the bridge priority (32, 768 by default on all Cisco switches) and the base MAC address. q. Root Bridge -The bridge with the lowest bridge ID becomes the root bridge in the network. q. Nonroot bridge - These are all bridges that are not the root bridge. q. Root port - The root port is always the link directly connected to the root bridge or the shortest path to the root bridge. If more than one link connects to the root bridge, then a port cost is determined by checking the bandwidth of each link. q. Designated port - A designated port is one that has been determined as having the best (lowest) cost. A designated port will be marked as a forwarding port q. Nondesignated Port - A nondesignated port is one with a higher cost than the designated port. Nondesignated ports are put in blocking mode q. Forwarding Port - A forwarding port forwards frames q. Blocked Port - A blocked port is the port that will not forward frames, in order to prevent loops 33
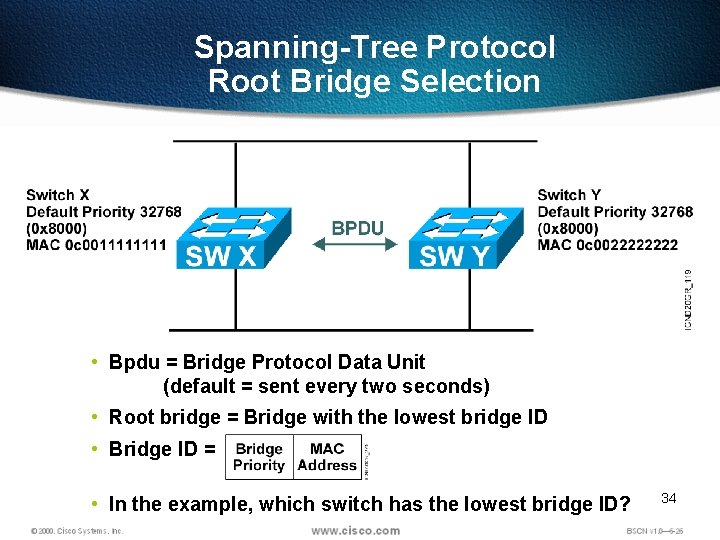
Spanning-Tree Protocol Root Bridge Selection • Bpdu = Bridge Protocol Data Unit (default = sent every two seconds) • Root bridge = Bridge with the lowest bridge ID • Bridge ID = • In the example, which switch has the lowest bridge ID? 34
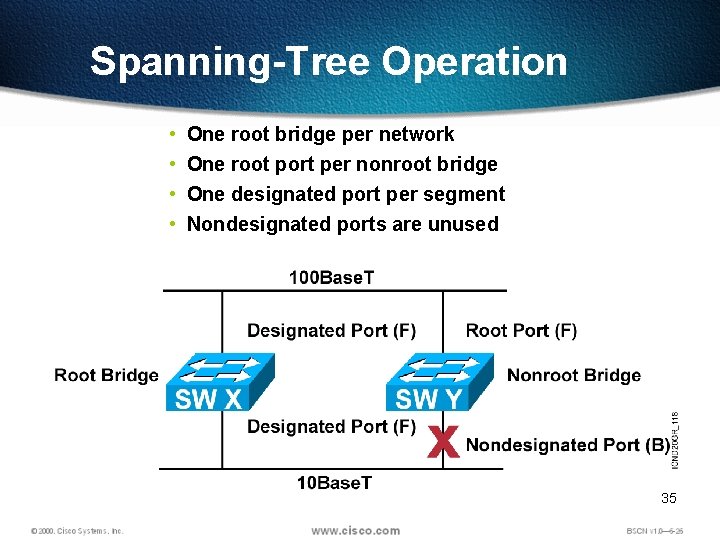
Spanning-Tree Operation • • One root bridge per network One root port per nonroot bridge One designated port per segment Nondesignated ports are unused 35
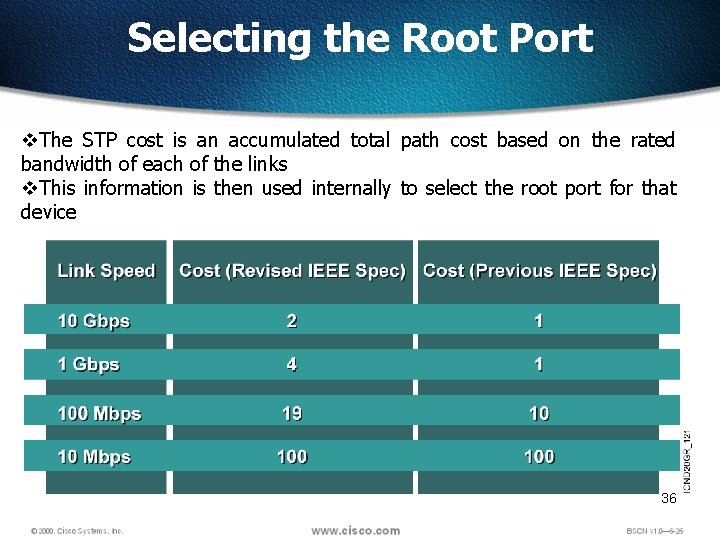
Selecting the Root Port v. The STP cost is an accumulated total path cost based on the rated bandwidth of each of the links v. This information is then used internally to select the root port for that device 36
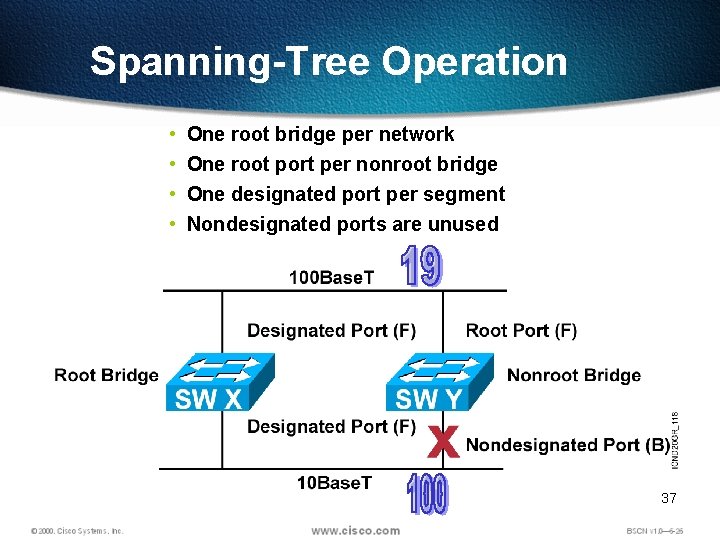
Spanning-Tree Operation • • One root bridge per network One root port per nonroot bridge One designated port per segment Nondesignated ports are unused 37
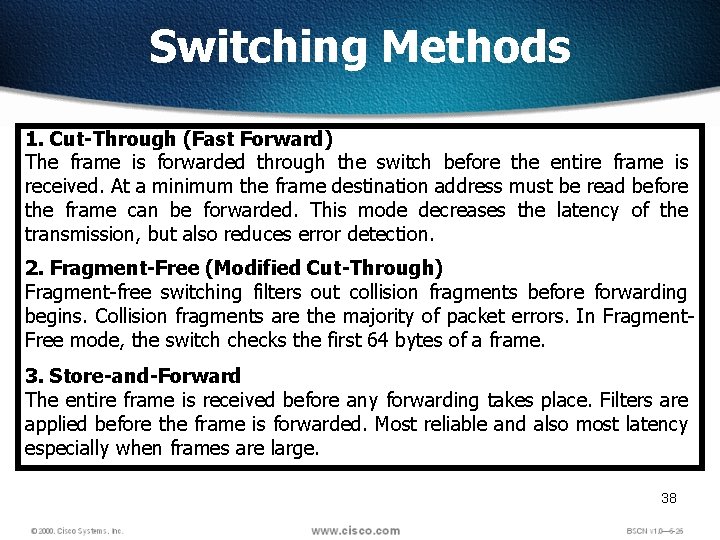
Switching Methods 1. Cut-Through (Fast Forward) The frame is forwarded through the switch before the entire frame is received. At a minimum the frame destination address must be read before the frame can be forwarded. This mode decreases the latency of the transmission, but also reduces error detection. 2. Fragment-Free (Modified Cut-Through) Fragment-free switching filters out collision fragments before forwarding begins. Collision fragments are the majority of packet errors. In Fragment. Free mode, the switch checks the first 64 bytes of a frame. 3. Store-and-Forward The entire frame is received before any forwarding takes place. Filters are applied before the frame is forwarded. Most reliable and also most latency especially when frames are large. 38
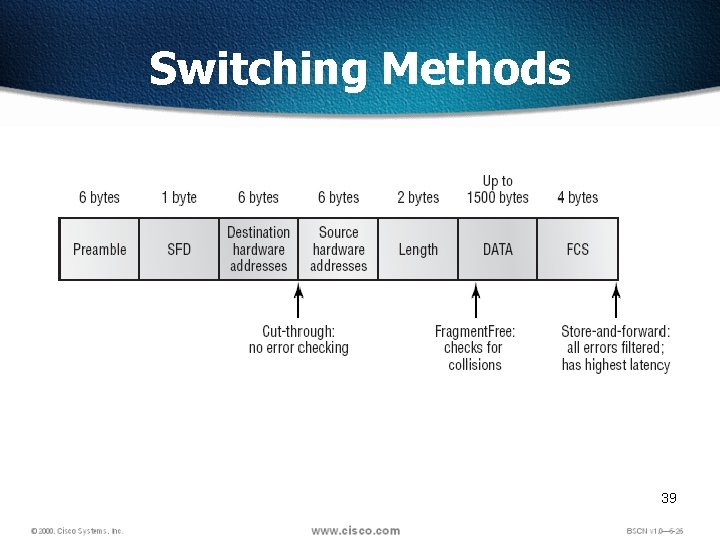
Switching Methods 39

40
Physical Startup of the Catalyst Switch q. Switches are dedicated, specialized computers, which contain a CPU, RAM, and an operating system. q. Switches usually have several ports for the purpose of connecting hosts, as well as specialized ports for the purpose of management. q. A switch can be managed by connecting to the console port to view and make changes to the configuration. q. Switches typically have no power switch to turn them on and off. They simply connect or disconnect from a power source. 41
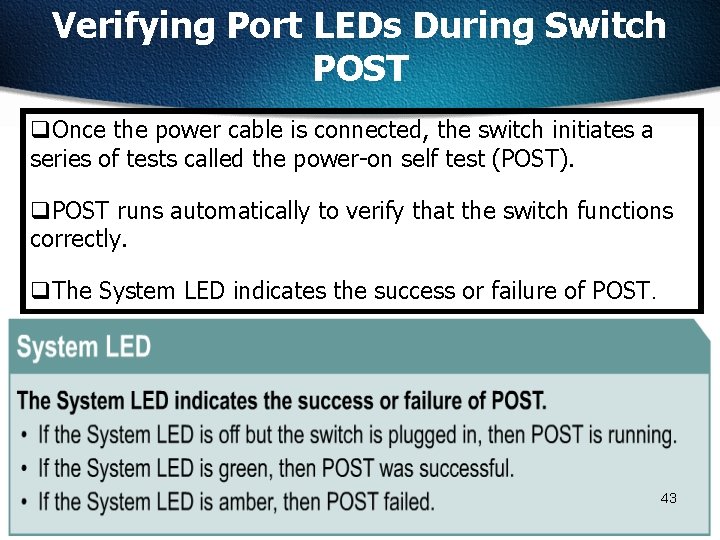
Verifying Port LEDs During Switch POST q. Once the power cable is connected, the switch initiates a series of tests called the power-on self test (POST). q. POST runs automatically to verify that the switch functions correctly. q. The System LED indicates the success or failure of POST. 43
Switch Command Modes q. Switches have several command modes. q. The default mode is User EXEC mode, which ends in a greaterthan character (>). q. The commands available in User EXEC mode are limited to those that change terminal settings, perform basic tests, and display system information. q. The enable command is used to change from User EXEC mode to Privileged EXEC mode, which ends in a pound-sign character (#). q. The configure command allows other command modes to be accessed. 44
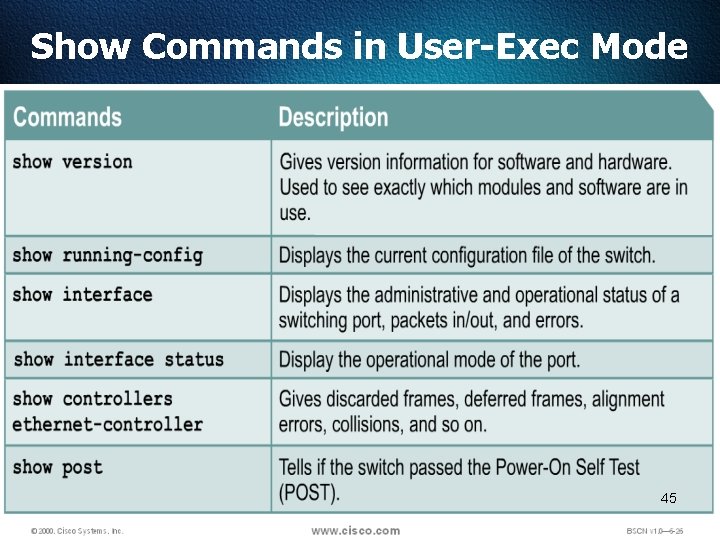
Show Commands in User-Exec Mode 45
Tasks Ø Setting the passwords (Password must be between 4 and 8 characters) Ø Setting the hostname Ø Configuring the IP address and subnet mask Ø Erasing the switch configurations 46
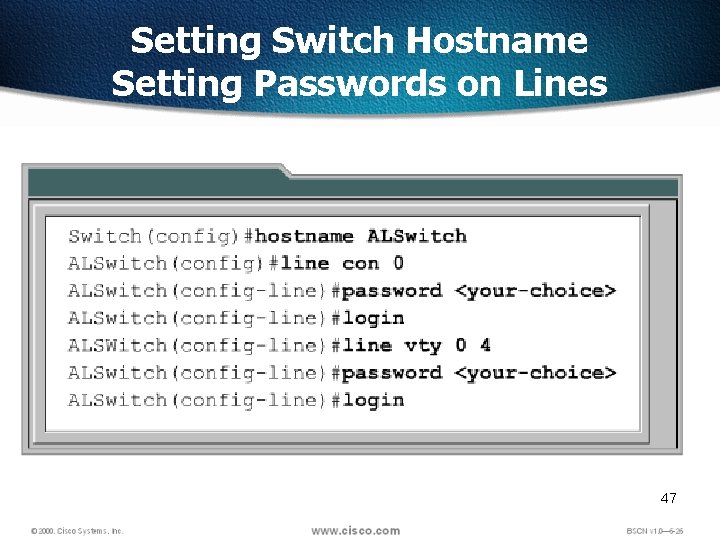
Setting Switch Hostname Setting Passwords on Lines 47
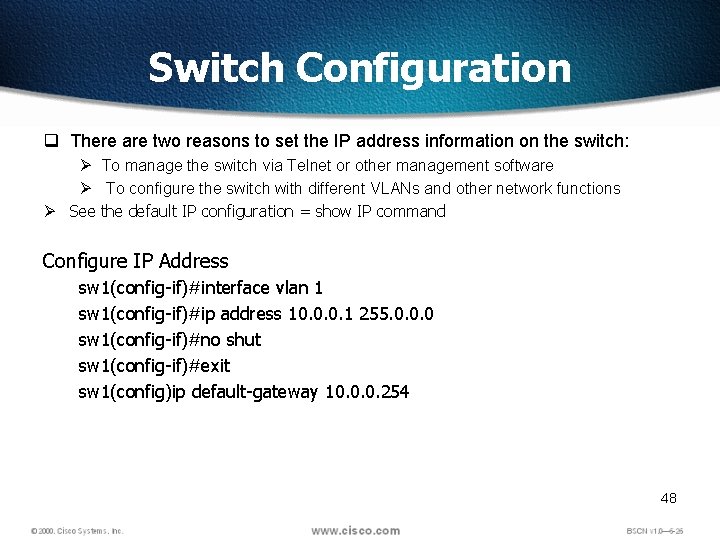
Switch Configuration q There are two reasons to set the IP address information on the switch: Ø To manage the switch via Telnet or other management software Ø To configure the switch with different VLANs and other network functions Ø See the default IP configuration = show IP command Configure IP Address sw 1(config-if)#interface vlan 1 sw 1(config-if)#ip address 10. 0. 0. 1 255. 0. 0. 0 sw 1(config-if)#no shut sw 1(config-if)#exit sw 1(config)ip default-gateway 10. 0. 0. 254 48
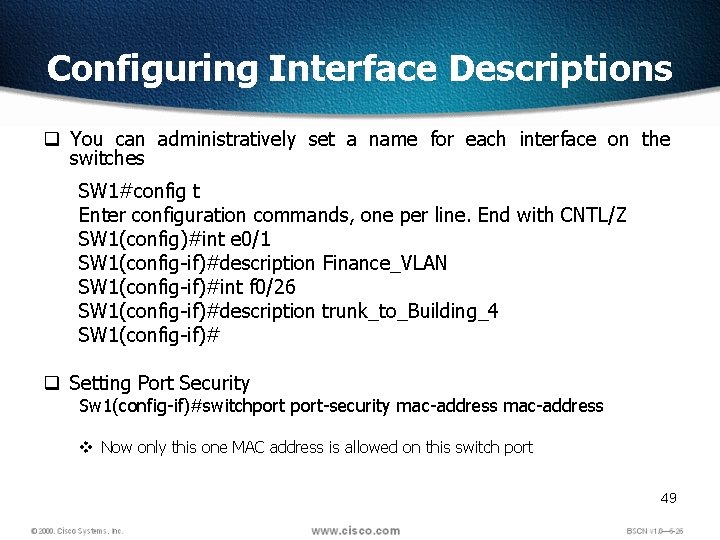
Configuring Interface Descriptions q You can administratively set a name for each interface on the switches SW 1#config t Enter configuration commands, one per line. End with CNTL/Z SW 1(config)#int e 0/1 SW 1(config-if)#description Finance_VLAN SW 1(config-if)#int f 0/26 SW 1(config-if)#description trunk_to_Building_4 SW 1(config-if)# q Setting Port Security Sw 1(config-if)#switchport-security mac-address v Now only this one MAC address is allowed on this switch port 49
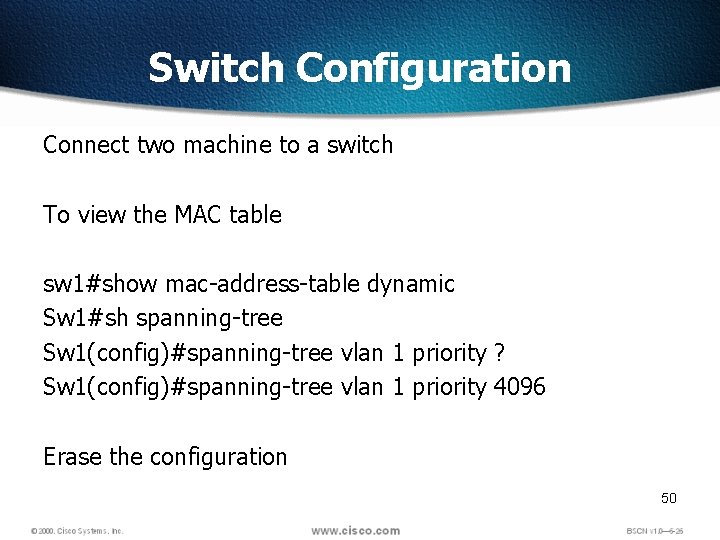
Switch Configuration Connect two machine to a switch To view the MAC table sw 1#show mac-address-table dynamic Sw 1#sh spanning-tree Sw 1(config)#spanning-tree vlan 1 priority ? Sw 1(config)#spanning-tree vlan 1 priority 4096 Erase the configuration 50
51
VLAN’s q A VLAN is a logical grouping of network users and resources connected to administratively defined ports on a switch. q Ability to create smaller broadcast domains within a layer 2 switched internetwork by assigning different ports on the switch to different subnetworks. q Frames broadcast onto the network are only switched between the ports logically grouped within the same VLAN q By default, no hosts in a specific VLAN can communicate with any other hosts that are members of another VLAN, q For Inter VLAN communication you need routers 52
VLANs q. VLAN implementation combines Layer 2 switching and Layer 3 routing technologies to limit both collision domains and broadcast domains. q. VLANs can also be used to provide security by creating the VLAN groups according to function and by using routers to communicate between VLANs. q. A physical port association is used to implement VLAN assignment. q. Communication between VLANs can occur only through the router. q. This limits the size of the broadcast domains and uses the router to determine whether one VLAN can talk to another VLAN. q. NOTE: This is the only way a switch can break up a broadcast domain! 53
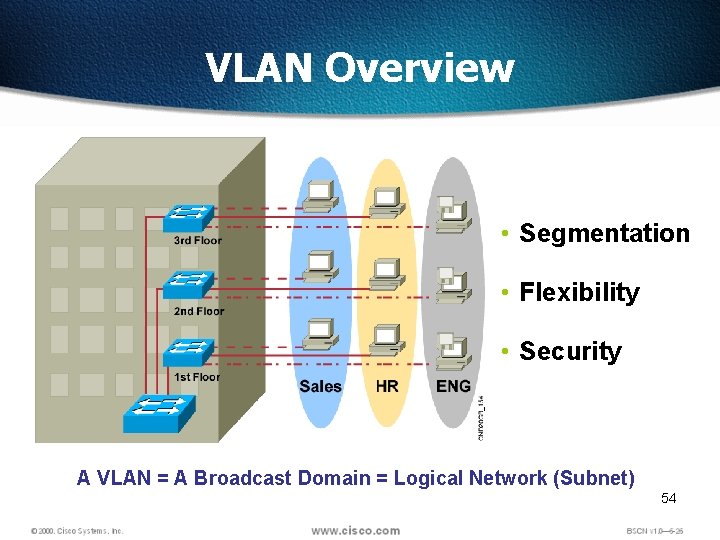
VLAN Overview • Segmentation • Flexibility • Security A VLAN = A Broadcast Domain = Logical Network (Subnet) 54
History q 11 Hosts are connected to the switch q. All From same Broadcast domain q. Need to divide them in separate logical segment q. High broadcast traffic reasons q. ARP q. DHCP q. SAP q. XWindows q. Net. BIOS 55
Definition q Logically Defined community of interest that limits a Broadcast domain q LAN are created on the software of Switch q All devices in a VLAN are members of the same broadcast domain and receive all broadcasts q The broadcasts, by default, are filtered from all ports on a switch that are not members of the same VLAN. 56
Security q A Flat internetwork’s security used to be tackled by connecting hubs and switches together with routers q This arrangement is ineffective because q Anyone connecting physical network could access network resources located on that physical LAN q Can observe the network traffic by plugging network analyzer into the HUB q Users could join a workgroup by just plugging their workstations into the existing hub q By creating VLAN’s administrators have control over each port and user 57
How VLANs Simplify Network Management q If we need to break the broadcast domain we need to connect a router q By using VLAN’s we can divide Broadcast domain at Layer-2 q A group of users needing high security can be put into a VLAN so that no users outside of the VLAN can communicate with them. q As a logical grouping of users by function, VLANs can be considered independent from their physical locations. 58
VLAN Memberships q VLAN created based on port is known as Static VLAN. q VLAN assigned based on hardware addresses into a database, is called a dynamic VLAN 59
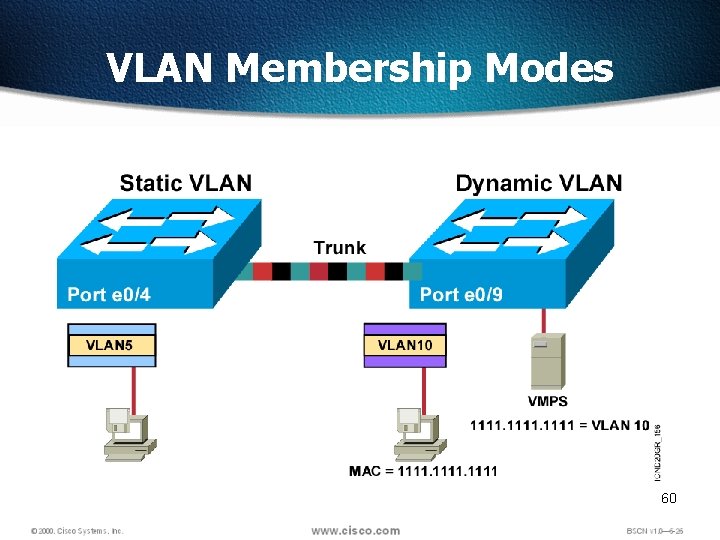
VLAN Membership Modes 60
Static VLANs q Most secure q Easy to set up and monitor q Works well in a network where the movement of users within the network is controlled 61
Dynamic VLANs q A dynamic VLAN determines a node’s VLAN assignment automatically q Using intelligent management software, you can base VLAN assignments on hardware (MAC) addresses. q Dynamic VLAN need VLAN Management Policy Server (VMPS) server 62
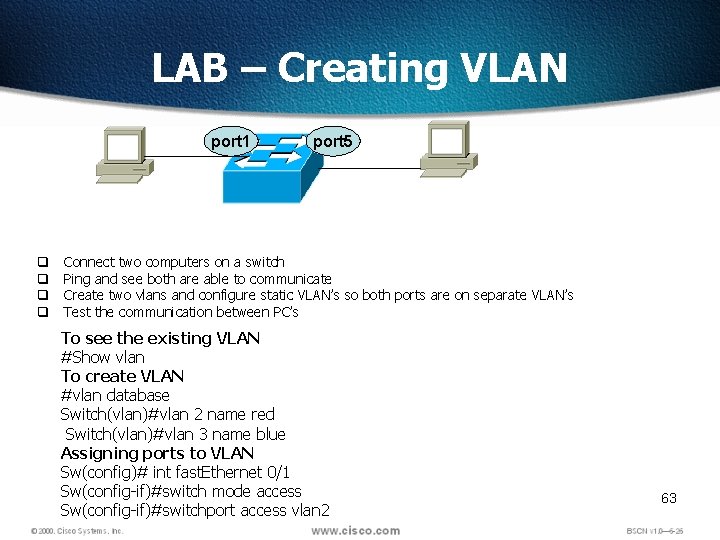
LAB – Creating VLAN port 1 q q port 5 Connect two computers on a switch Ping and see both are able to communicate Create two vlans and configure static VLAN’s so both ports are on separate VLAN’s Test the communication between PC’s To see the existing VLAN #Show vlan To create VLAN #vlan database Switch(vlan)#vlan 2 name red Switch(vlan)#vlan 3 name blue Assigning ports to VLAN Sw(config)# int fast. Ethernet 0/1 Sw(config-if)#switch mode access Sw(config-if)#switchport access vlan 2 63
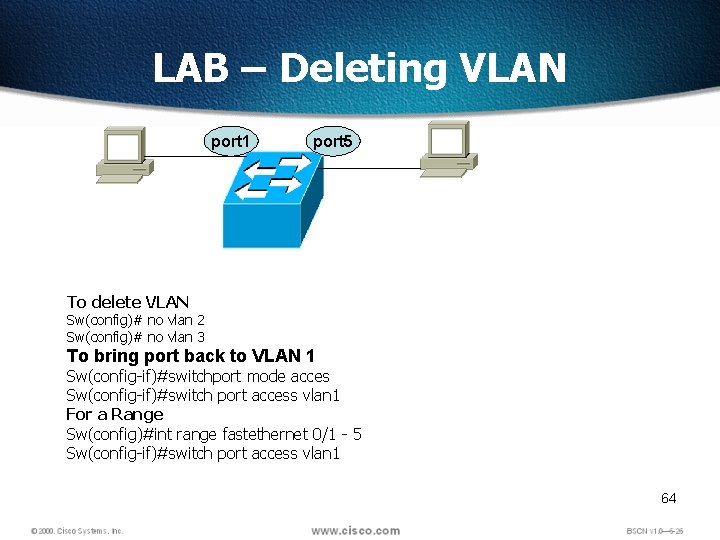
LAB – Deleting VLAN port 1 port 5 To delete VLAN Sw(config)# no vlan 2 Sw(config)# no vlan 3 To bring port back to VLAN 1 Sw(config-if)#switchport mode acces Sw(config-if)#switch port access vlan 1 For a Range Sw(config)#int range fastethernet 0/1 - 5 Sw(config-if)#switch port access vlan 1 64
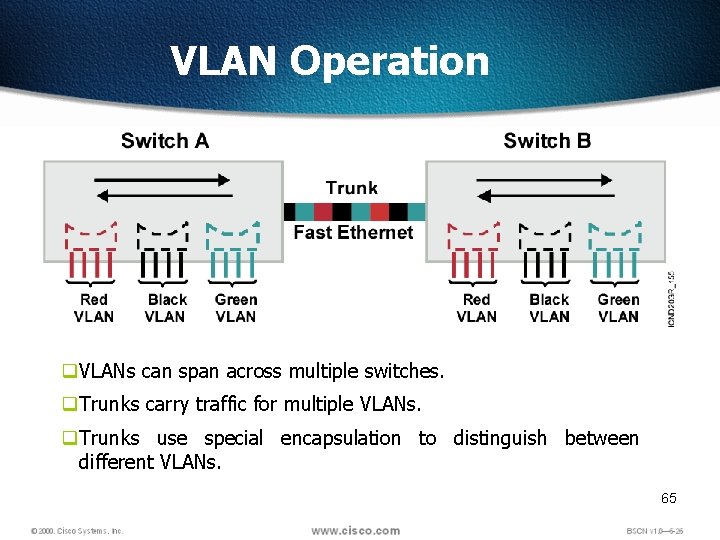
VLAN Operation q. VLANs can span across multiple switches. q. Trunks carry traffic for multiple VLANs. q. Trunks use special encapsulation to distinguish between different VLANs. 65
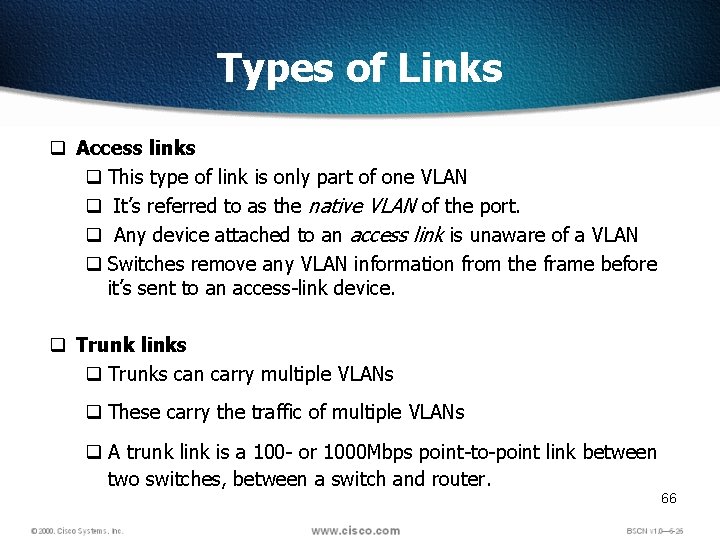
Types of Links q Access links q This type of link is only part of one VLAN q It’s referred to as the native VLAN of the port. q Any device attached to an access link is unaware of a VLAN q Switches remove any VLAN information from the frame before it’s sent to an access-link device. q Trunk links q Trunks can carry multiple VLANs q These carry the traffic of multiple VLANs q A trunk link is a 100 - or 1000 Mbps point-to-point link between two switches, between a switch and router. 66
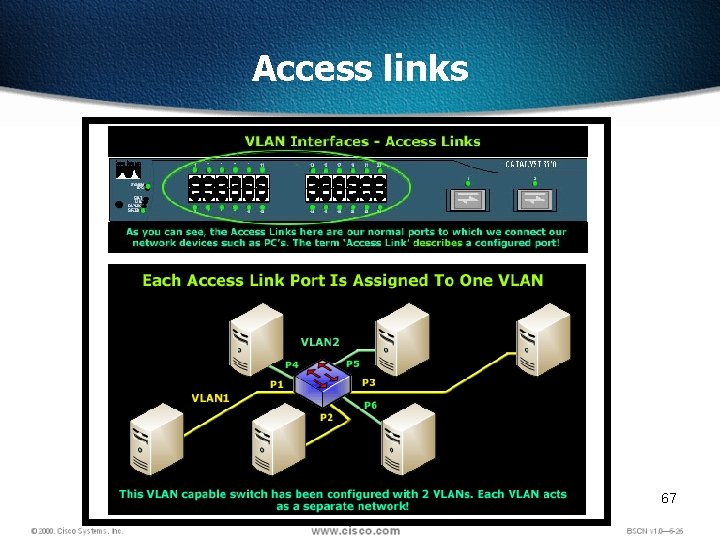
Access links 67
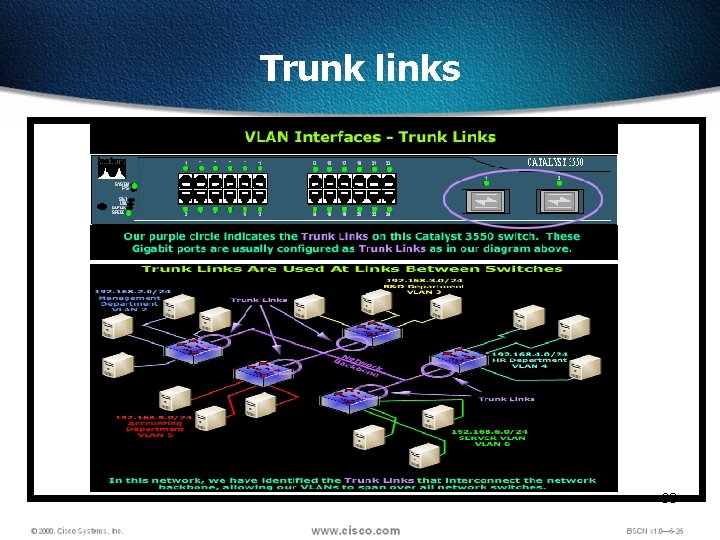
Trunk links 68
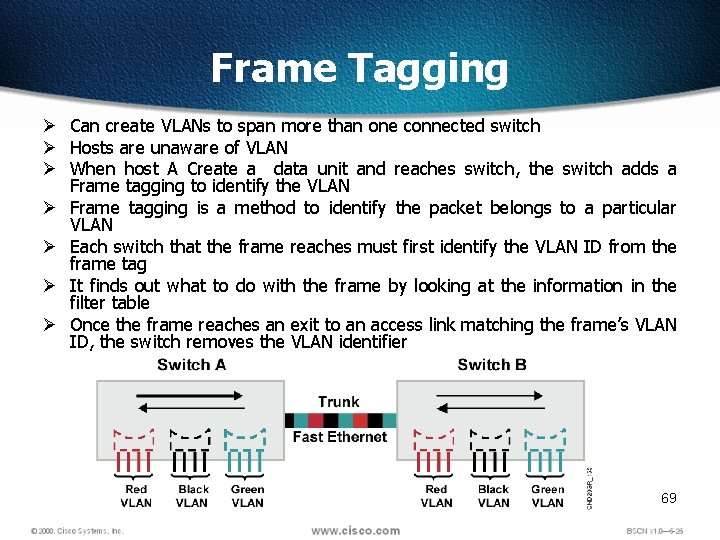
Frame Tagging Ø Can create VLANs to span more than one connected switch Ø Hosts are unaware of VLAN Ø When host A Create a data unit and reaches switch, the switch adds a Frame tagging to identify the VLAN Ø Frame tagging is a method to identify the packet belongs to a particular VLAN Ø Each switch that the frame reaches must first identify the VLAN ID from the frame tag Ø It finds out what to do with the frame by looking at the information in the filter table Ø Once the frame reaches an exit to an access link matching the frame’s VLAN ID, the switch removes the VLAN identifier 69
Frame Tagging Methods q There are two frame tagging methods Ø Inter-Switch Link (ISL) Ø IEEE 802. 1 Q q Inter-Switch Link (ISL) Ø proprietary to Cisco switches Ø used for Fast Ethernet and Gigabit Ethernet links only q IEEE 802. 1 Q Ø Created by the IEEE as a standard method of frame tagging Ø it actually inserts a field into the frame to identify the VLAN Ø If you’re trunking between a Cisco switched link and a different brand of switch, you have to use 802. 1 Q for the trunk to work. 70
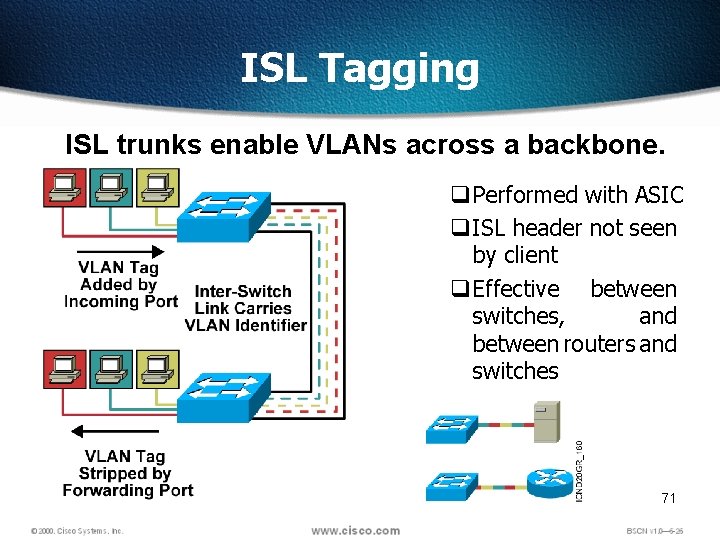
ISL Tagging ISL trunks enable VLANs across a backbone. q Performed with ASIC q ISL header not seen by client q Effective between switches, and between routers and switches 71
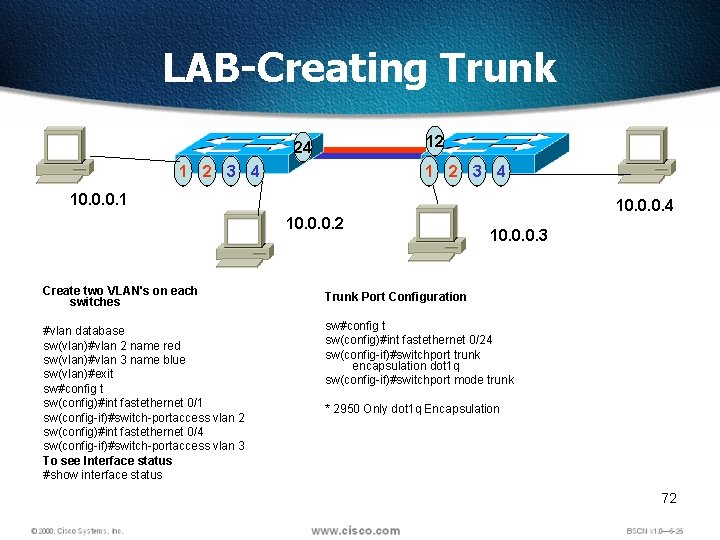
LAB-Creating Trunk 12 24 1 2 3 4 10. 0. 0. 1 10. 0. 0. 4 10. 0. 0. 2 10. 0. 0. 3 Create two VLAN's on each switches Trunk Port Configuration #vlan database sw(vlan)#vlan 2 name red sw(vlan)#vlan 3 name blue sw(vlan)#exit sw#config t sw(config)#int fastethernet 0/1 sw(config-if)#switch-portaccess vlan 2 sw(config)#int fastethernet 0/4 sw(config-if)#switch-portaccess vlan 3 To see Interface status #show interface status sw#config t sw(config)#int fastethernet 0/24 sw(config-if)#switchport trunk encapsulation dot 1 q sw(config-if)#switchport mode trunk * 2950 Only dot 1 q Encapsulation 72
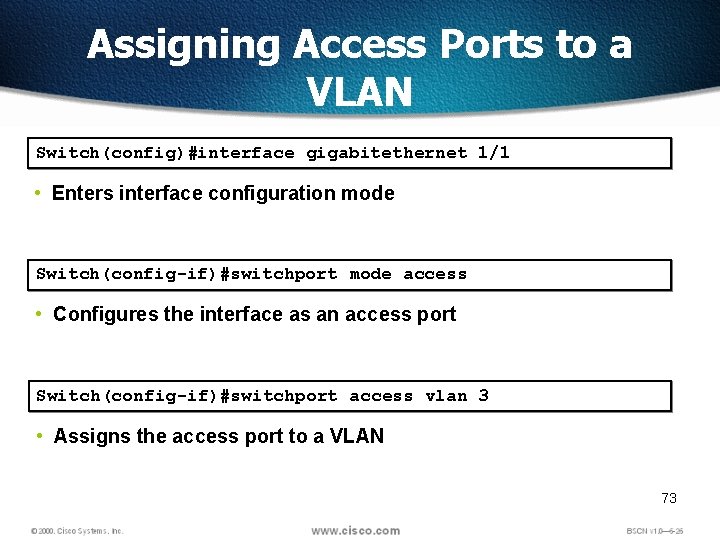
Assigning Access Ports to a VLAN Switch(config)#interface gigabitethernet 1/1 • Enters interface configuration mode Switch(config-if)#switchport mode access • Configures the interface as an access port Switch(config-if)#switchport access vlan 3 • Assigns the access port to a VLAN 73
![Verifying the VLAN Configuration Switch#show vlan [id | name] [vlan_num | vlan_name] VLAN Name Verifying the VLAN Configuration Switch#show vlan [id | name] [vlan_num | vlan_name] VLAN Name](http://slidetodoc.com/presentation_image/5496646cfb48c46c22efef8e1b9095cc/image-73.jpg)
Verifying the VLAN Configuration Switch#show vlan [id | name] [vlan_num | vlan_name] VLAN Name Status Ports --------------------1 default active Fa 0/1, Fa 0/2, Fa 0/5, Fa 0/7 Fa 0/8, Fa 0/9, Fa 0/11, Fa 0/12 Gi 0/1, Gi 0/2 2 VLAN 0002 active 51 VLAN 0051 active 52 VLAN 0052 active … VLAN ---1 2 51 52 … Type ----enet SAID -----100001 100002 100051 100052 MTU ----1500 Parent ------ Ring. No ------ Bridge. No ---- Stp ---- Brdg. Mode ---- Trans 1 -----1002 0 0 0 Trans 2 -----1003 0 0 0 Remote SPAN VLANs ---------------------------------------74 Primary Secondary Type Ports -----------------------------
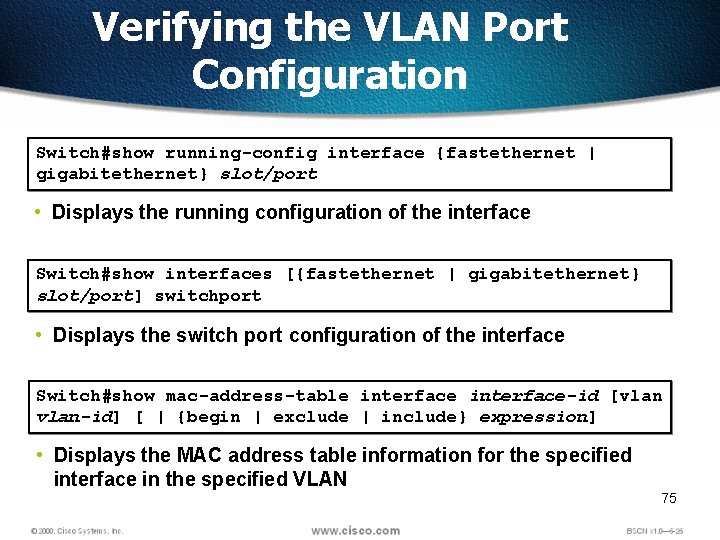
Verifying the VLAN Port Configuration Switch#show running-config interface {fastethernet | gigabitethernet} slot/port • Displays the running configuration of the interface Switch#show interfaces [{fastethernet | gigabitethernet} slot/port] switchport • Displays the switch port configuration of the interface Switch#show mac-address-table interface-id [vlan-id] [ | {begin | exclude | include} expression] • Displays the MAC address table information for the specified interface in the specified VLAN 75
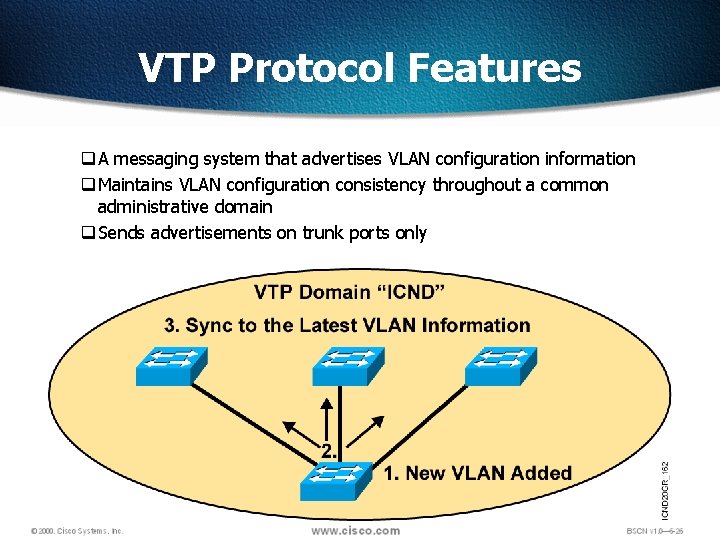
VTP Protocol Features q A messaging system that advertises VLAN configuration information q Maintains VLAN configuration consistency throughout a common administrative domain q Sends advertisements on trunk ports only
VLAN Trunking Protocol (VTP) q. Benefits of VTP q. Consistent VLAN configuration across all switches in the network q. Accurate tracking and monitoring of VLANs q. Dynamic reporting of added VLANs to all switches in the VTP domain 77
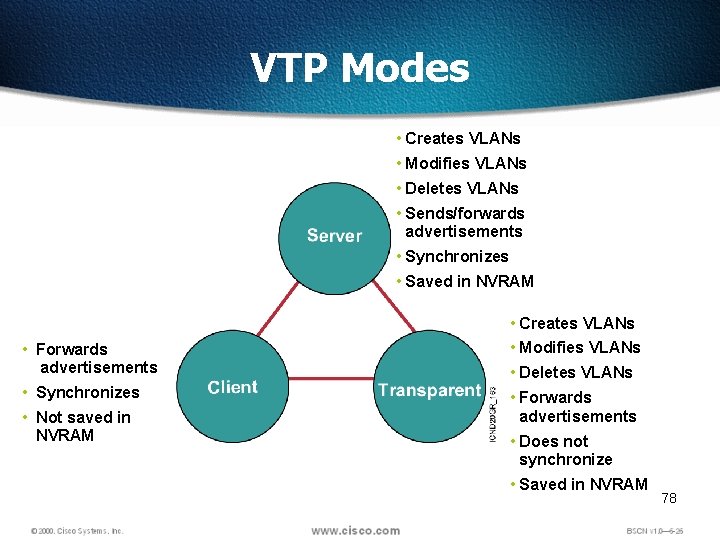
VTP Modes • Creates VLANs • Modifies VLANs • Deletes VLANs • Sends/forwards advertisements • Synchronizes • Saved in NVRAM • Creates VLANs • Forwards advertisements • Modifies VLANs • Synchronizes • Forwards advertisements • Not saved in NVRAM • Deletes VLANs • Does not synchronize • Saved in NVRAM 78
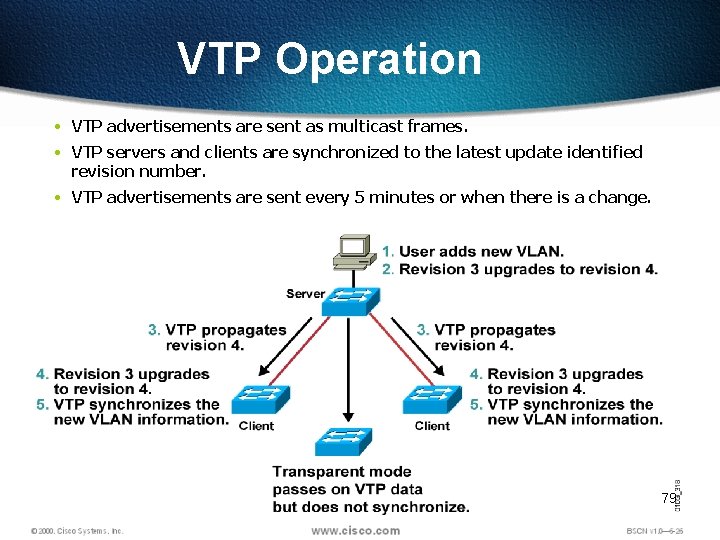
VTP Operation • VTP advertisements are sent as multicast frames. • VTP servers and clients are synchronized to the latest update identified revision number. • VTP advertisements are sent every 5 minutes or when there is a change. 79
VTP Pruning • VTP pruning provides a way for you to preserve bandwidth by configuring it to reduce the amount of broadcasts, multicasts, and unicast packets. • If Switch A doesn’t have any ports configured for VLAN 5, and a broadcast is sent throughout VLAN 5, that broadcast would not traverse the trunk link to Switch A. • By default, VTP pruning is disabled on all switches. • Pruning is enabled for the entire domain 80
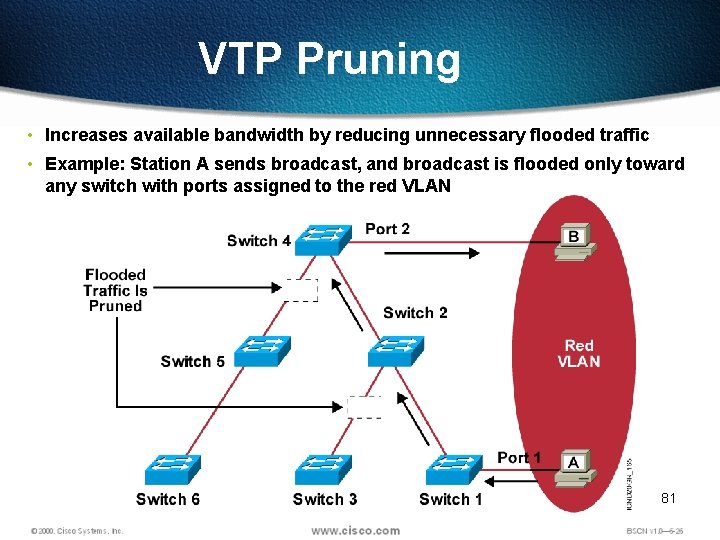
VTP Pruning • Increases available bandwidth by reducing unnecessary flooded traffic • Example: Station A sends broadcast, and broadcast is flooded only toward any switch with ports assigned to the red VLAN 81
VTP Configuration Guidelines – Configure the following: • VTP domain name • VTP mode (server mode is the default) • VTP pruning • VTP password Switch(config)#vtp mode server Switch(config)#vtp domain gates Switch. A#sh vtp status 82
![Creating a VTP Domain Catalyst 1900 wg_sw_1900(config)#vtp [server | transparent | client] [domain-name] [trap Creating a VTP Domain Catalyst 1900 wg_sw_1900(config)#vtp [server | transparent | client] [domain-name] [trap](http://slidetodoc.com/presentation_image/5496646cfb48c46c22efef8e1b9095cc/image-82.jpg)
Creating a VTP Domain Catalyst 1900 wg_sw_1900(config)#vtp [server | transparent | client] [domain-name] [trap {enable | disable}] [password] [pruning {enable | disable}] wg_sw_1900#configure terminal Enter configuration commands, one per line. wg_sw_1900(config)#vtp transparent wg_sw_1900(config)#vtp domain switchlab End with CNTL/Z Catalyst 2950 wg_sw_2950#vlan database wg_sw_2950(vlan)#vtp [ server | client | transparent ] wg_sw_2950(vlan)#vtp domain-name wg_sw_2950(vlan)#vtp password wg_sw_2950(vlan)#vtp pruning 83
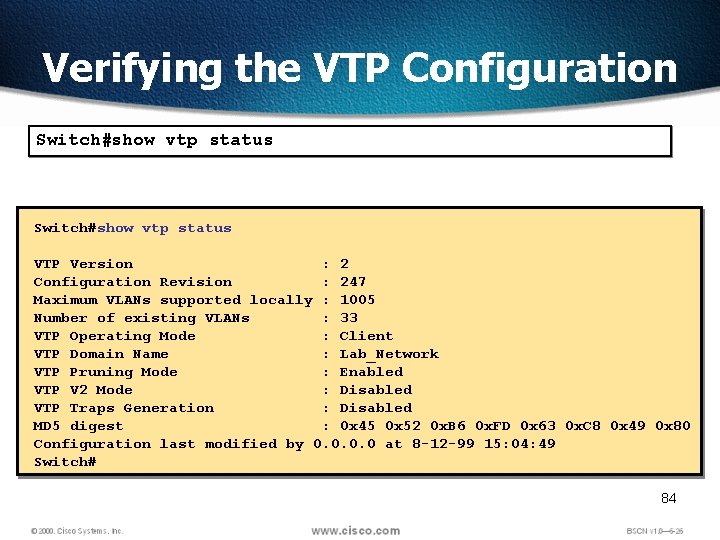
Verifying the VTP Configuration Switch#show vtp status VTP Version : 2 Configuration Revision : 247 Maximum VLANs supported locally : 1005 Number of existing VLANs : 33 VTP Operating Mode : Client VTP Domain Name : Lab_Network VTP Pruning Mode : Enabled VTP V 2 Mode : Disabled VTP Traps Generation : Disabled MD 5 digest : 0 x 45 0 x 52 0 x. B 6 0 x. FD 0 x 63 0 x. C 8 0 x 49 0 x 80 Configuration last modified by 0. 0 at 8 -12 -99 15: 04: 49 Switch# 84
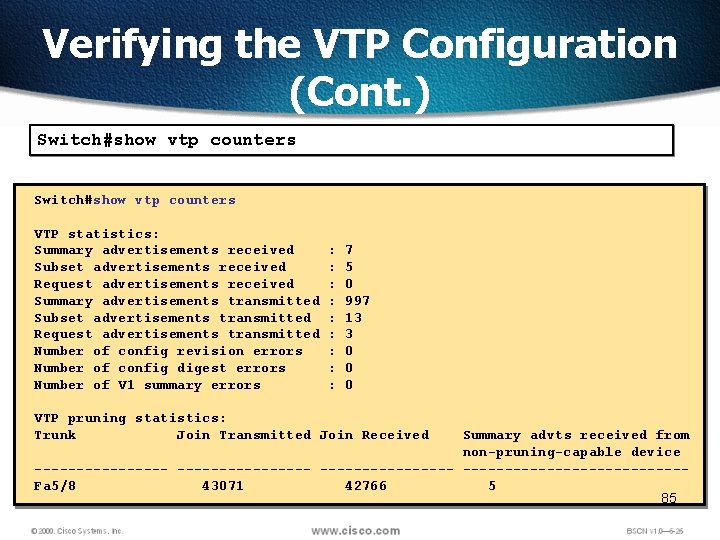
Verifying the VTP Configuration (Cont. ) Switch#show vtp counters VTP statistics: Summary advertisements received Subset advertisements received Request advertisements received Summary advertisements transmitted Subset advertisements transmitted Request advertisements transmitted Number of config revision errors Number of config digest errors Number of V 1 summary errors : : : : : 7 5 0 997 13 3 0 0 0 VTP pruning statistics: Trunk Join Transmitted Join Received Summary advts received from non-pruning-capable device ---------------------Fa 5/8 43071 42766 5 85
VLAN to VLAN q. If you want to connect between two VLANs you need a layer 3 device 86
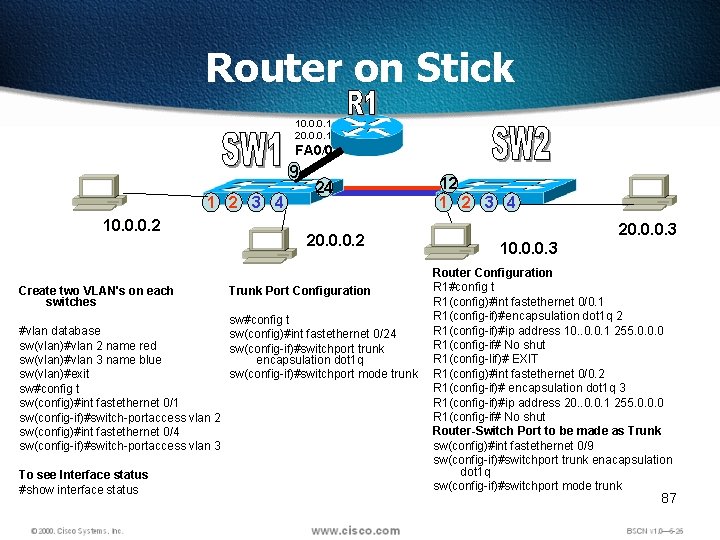
Router on Stick 10. 0. 0. 1 20. 0. 0. 1 FA 0/0 9 1 2 3 4 10. 0. 0. 2 Create two VLAN's on each switches 24 20. 0. 0. 2 Trunk Port Configuration sw#config t #vlan database sw(config)#int fastethernet 0/24 sw(vlan)#vlan 2 name red sw(config-if)#switchport trunk sw(vlan)#vlan 3 name blue encapsulation dot 1 q sw(vlan)#exit sw(config-if)#switchport mode trunk sw#config t sw(config)#int fastethernet 0/1 sw(config-if)#switch-portaccess vlan 2 sw(config)#int fastethernet 0/4 sw(config-if)#switch-portaccess vlan 3 To see Interface status #show interface status 12 1 2 3 4 20. 0. 0. 3 10. 0. 0. 3 Router Configuration R 1#config t R 1(config)#int fastethernet 0/0. 1 R 1(config-if)#encapsulation dot 1 q 2 R 1(config-if)#ip address 10. . 0. 0. 1 255. 0. 0. 0 R 1(config-if# No shut R 1(config-Iif)# EXIT R 1(config)#int fastethernet 0/0. 2 R 1(config-if)# encapsulation dot 1 q 3 R 1(config-if)#ip address 20. . 0. 0. 1 255. 0. 0. 0 R 1(config-if# No shut Router-Switch Port to be made as Trunk sw(config)#int fastethernet 0/9 sw(config-if)#switchport trunk enacapsulation dot 1 q sw(config-if)#switchport mode trunk 87
88 Fig. 3 NAT (TI 1332 EU 02 TI_0003 New Address Concepts, 7)
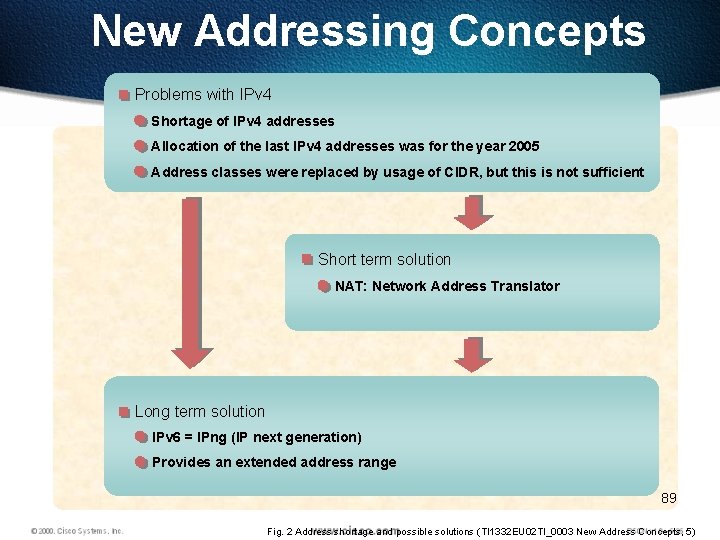
New Addressing Concepts Problems with IPv 4 Shortage of IPv 4 addresses Allocation of the last IPv 4 addresses was for the year 2005 Address classes were replaced by usage of CIDR, but this is not sufficient Short term solution NAT: Network Address Translator Long term solution IPv 6 = IPng (IP next generation) Provides an extended address range 89 Fig. 2 Address shortage and possible solutions (TI 1332 EU 02 TI_0003 New Address Concepts, 5)
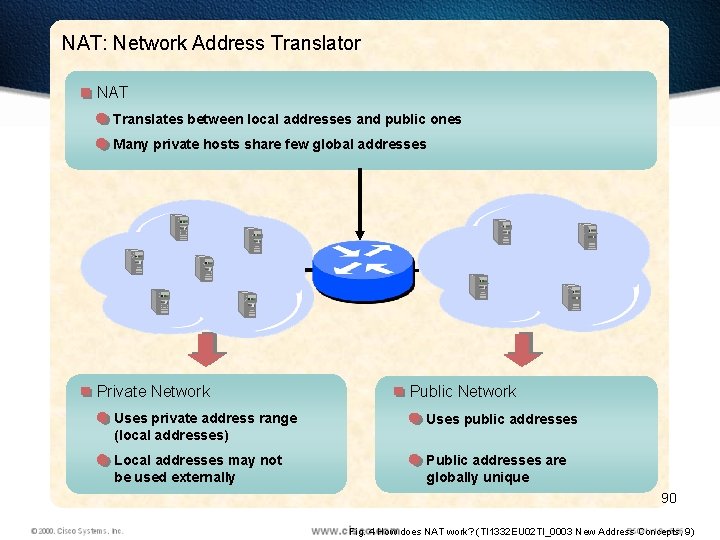
NAT: Network Address Translator NAT Translates between local addresses and public ones Many private hosts share few global addresses Private Network Public Network Uses private address range (local addresses) Uses public addresses Local addresses may not be used externally Public addresses are globally unique 90 Fig. 4 How does NAT work? (TI 1332 EU 02 TI_0003 New Address Concepts, 9)
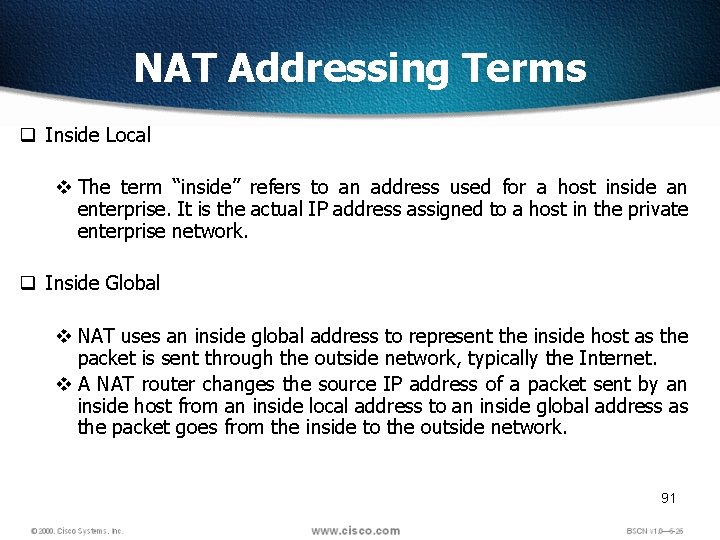
NAT Addressing Terms q Inside Local v The term “inside” refers to an address used for a host inside an enterprise. It is the actual IP address assigned to a host in the private enterprise network. q Inside Global v NAT uses an inside global address to represent the inside host as the packet is sent through the outside network, typically the Internet. v A NAT router changes the source IP address of a packet sent by an inside host from an inside local address to an inside global address as the packet goes from the inside to the outside network. 91
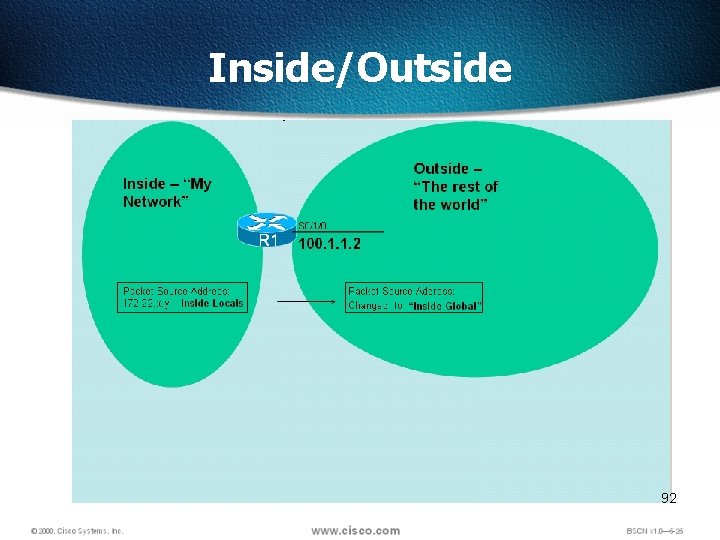
Inside/Outside 92
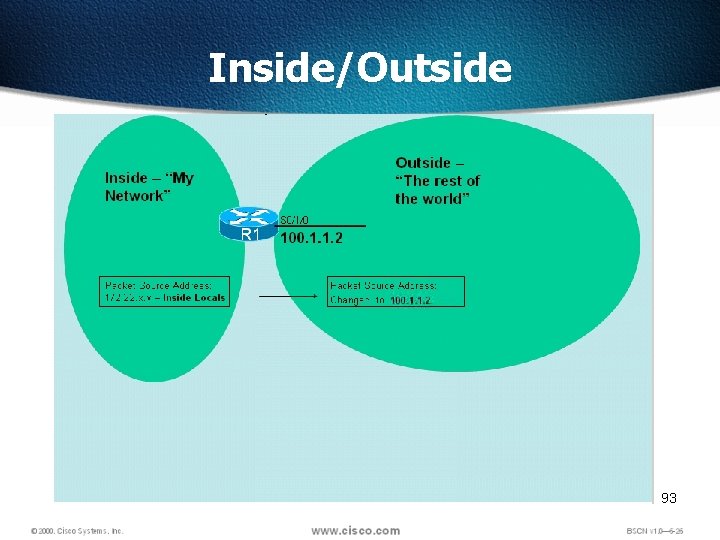
Inside/Outside 93
NAT Addressing Terms q Outside Global v The term “outside” refers to an address used for a host outside an enterprise, the Internet. v An outside global is the actual IP address assigned to a host that resides in the outside network, typically the Internet. q Outside Local v NAT uses an outside local address to represent the outside host as the packet is sent through the private network. v This address is outside private, outside host with a private address 94
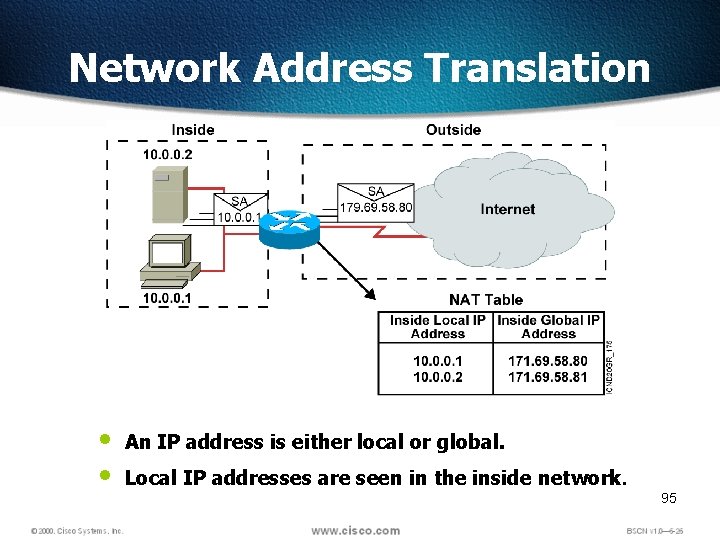
Network Address Translation • • An IP address is either local or global. Local IP addresses are seen in the inside network. 95
Types Of NAT q. There are different types of NAT that can be used, which are v. Static NAT v. Dynamic NAT v. Overloading NAT with PAT (NAPT) 96
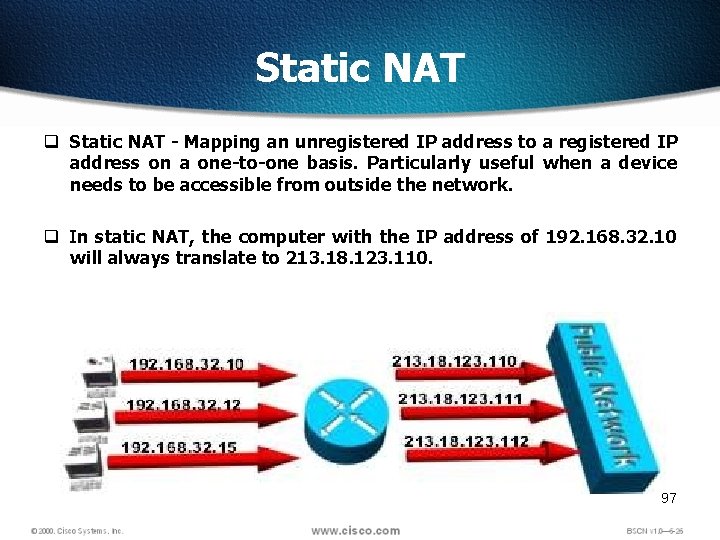
Static NAT q Static NAT - Mapping an unregistered IP address to a registered IP address on a one-to-one basis. Particularly useful when a device needs to be accessible from outside the network. q In static NAT, the computer with the IP address of 192. 168. 32. 10 will always translate to 213. 18. 123. 110. 97
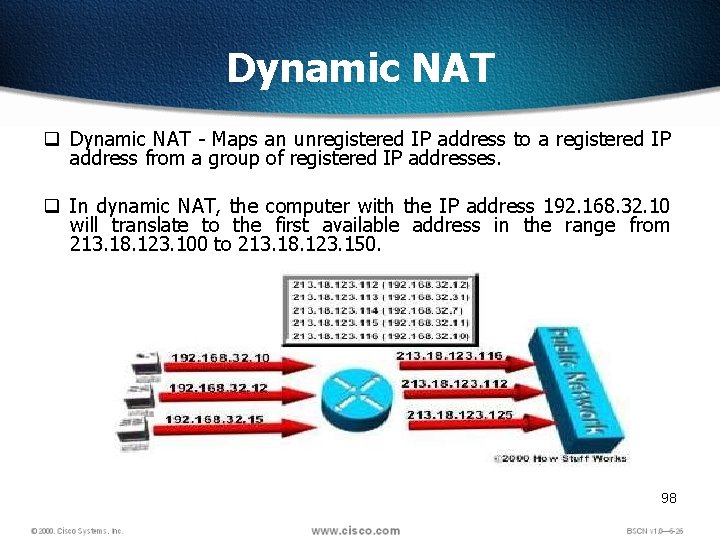
Dynamic NAT q Dynamic NAT - Maps an unregistered IP address to a registered IP address from a group of registered IP addresses. q In dynamic NAT, the computer with the IP address 192. 168. 32. 10 will translate to the first available address in the range from 213. 18. 123. 100 to 213. 18. 123. 150. 98
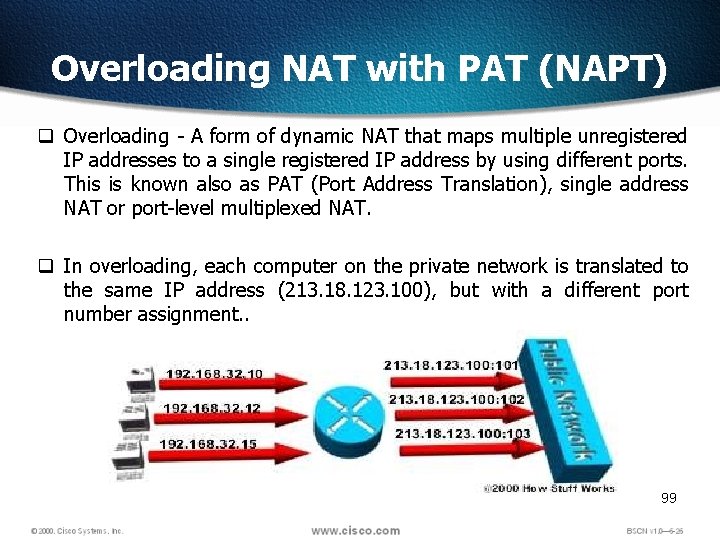
Overloading NAT with PAT (NAPT) q Overloading - A form of dynamic NAT that maps multiple unregistered IP addresses to a single registered IP address by using different ports. This is known also as PAT (Port Address Translation), single address NAT or port-level multiplexed NAT. q In overloading, each computer on the private network is translated to the same IP address (213. 18. 123. 100), but with a different port number assignment. . 99
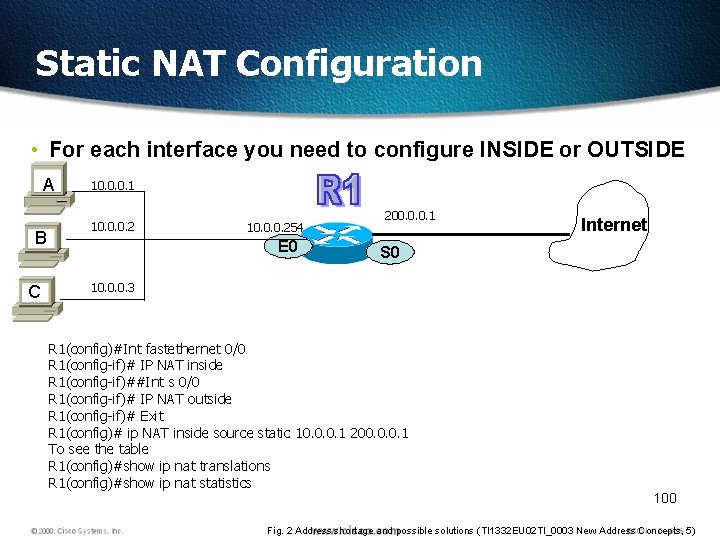
Static NAT Configuration • For each interface you need to configure INSIDE or OUTSIDE A B C 10. 0. 0. 1 10. 0. 0. 254 E 0 200. 0. 0. 1 Internet S 0 10. 0. 0. 3 R 1(config)#Int fastethernet 0/0 R 1(config-if)# IP NAT inside R 1(config-if)##Int s 0/0 R 1(config-if)# IP NAT outside R 1(config-if)# Exit R 1(config)# ip NAT inside source static 10. 0. 0. 1 200. 0. 0. 1 To see the table R 1(config)#show ip nat translations R 1(config)#show ip nat statistics 100 Fig. 2 Address shortage and possible solutions (TI 1332 EU 02 TI_0003 New Address Concepts, 5)
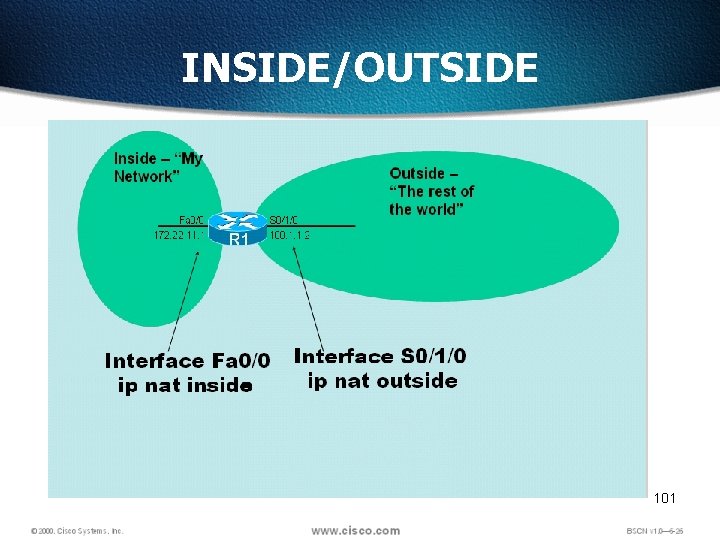
INSIDE/OUTSIDE 101
Dynamic NAT q Dynamic NAT sets up a pool of possible inside global addresses and defines criteria for the set of inside local IP addresses whose traffic should be translated with NAT. q The dynamic entry in the NAT table stays in there as long as traffic flows occasionally. q If a new packet arrives, and it needs a NAT entry, but all the pooled IP addresses are in use, the router simply discards the packet. 102 Fig. 2 Address shortage and possible solutions (TI 1332 EU 02 TI_0003 New Address Concepts, 5)
Dynamic NAT q Instead of creating static IP, create a pool of IP Address, Specify a range q Create an access list and permit hosts q Link Access list to the Pool 103 Fig. 2 Address shortage and possible solutions (TI 1332 EU 02 TI_0003 New Address Concepts, 5)
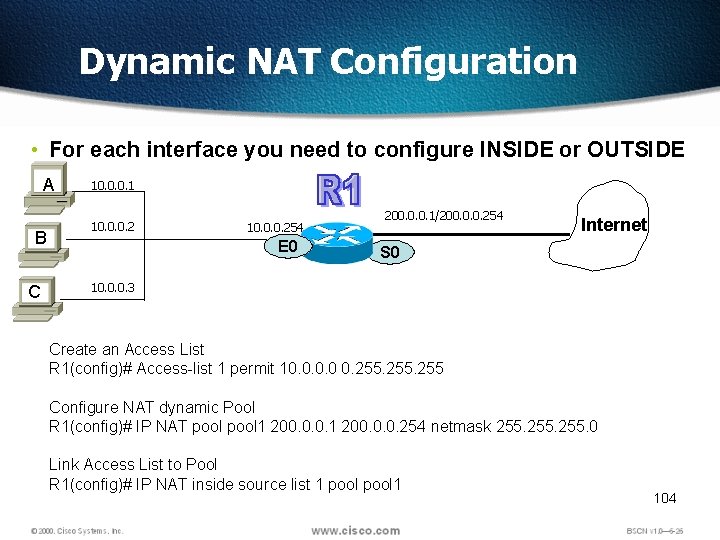
Dynamic NAT Configuration • For each interface you need to configure INSIDE or OUTSIDE A B C 10. 0. 0. 1 10. 0. 0. 254 E 0 200. 0. 0. 1/200. 0. 0. 254 Internet S 0 10. 0. 0. 3 Create an Access List R 1(config)# Access-list 1 permit 10. 0 0. 255 Configure NAT dynamic Pool R 1(config)# IP NAT pool 1 200. 0. 0. 254 netmask 255. 0 Link Access List to Pool R 1(config)# IP NAT inside source list 1 pool 1 104
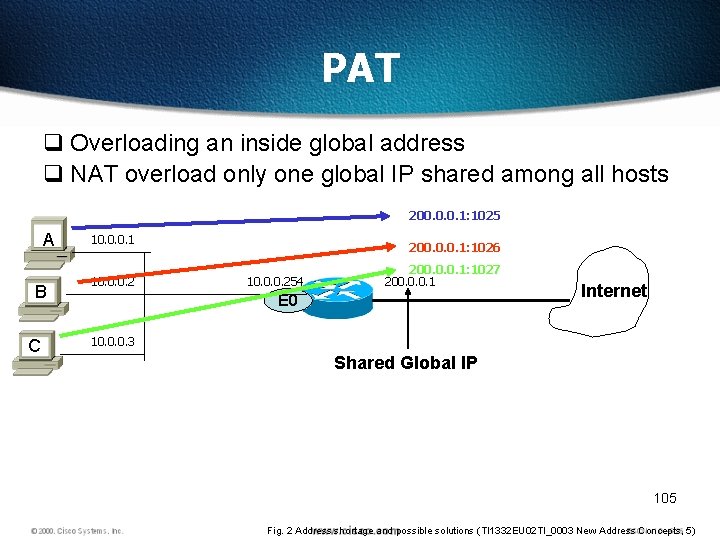
PAT q Overloading an inside global address q NAT overload only one global IP shared among all hosts 200. 0. 0. 1: 1025 A B C 10. 0. 0. 1 10. 0. 0. 2 200. 0. 0. 1: 1026 10. 0. 0. 254 200. 0. 0. 1: 1027 200. 0. 0. 1 E 0 Internet 10. 0. 0. 3 Shared Global IP 105 Fig. 2 Address shortage and possible solutions (TI 1332 EU 02 TI_0003 New Address Concepts, 5)
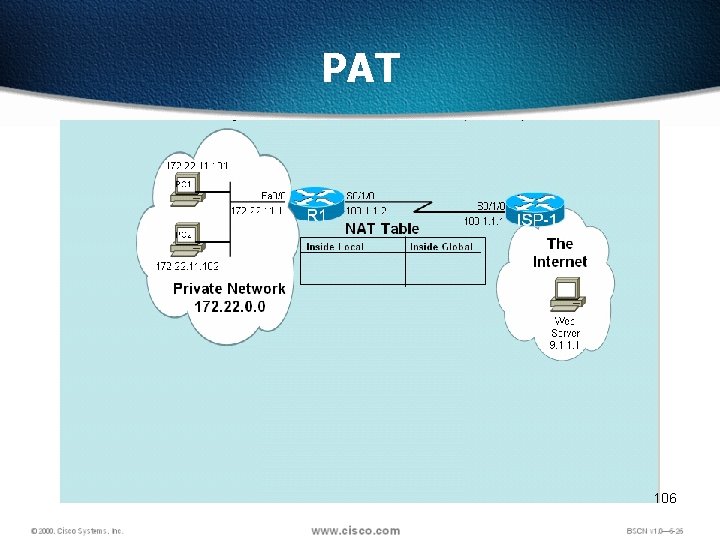
PAT 106
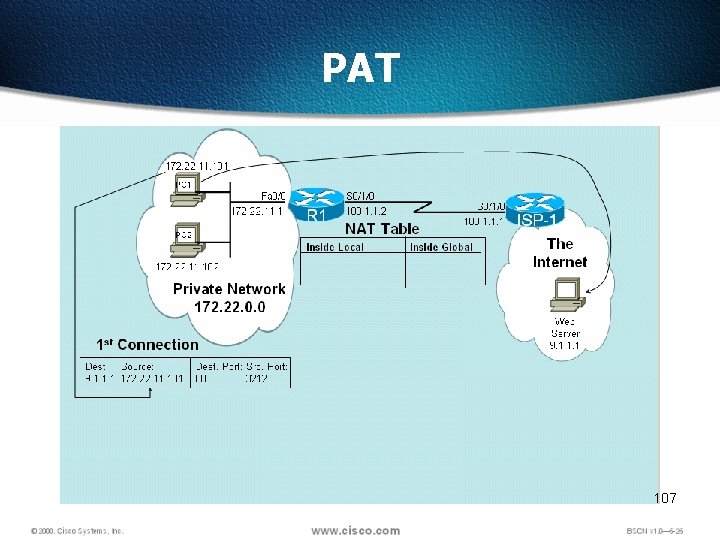
PAT 107
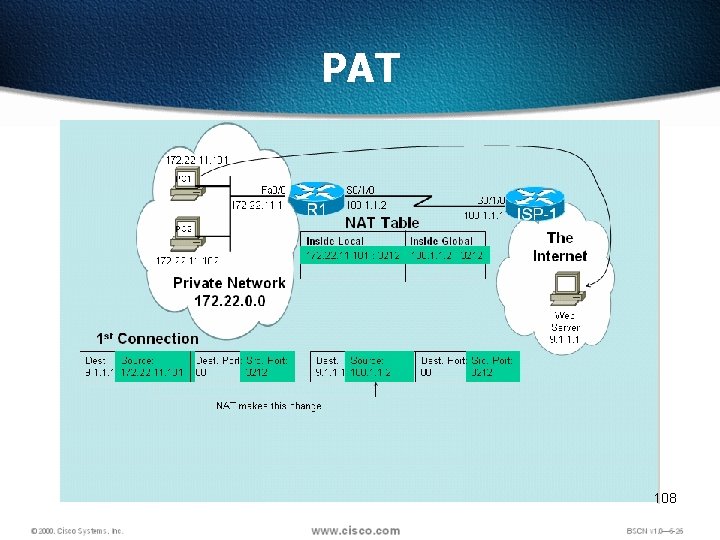
PAT 108
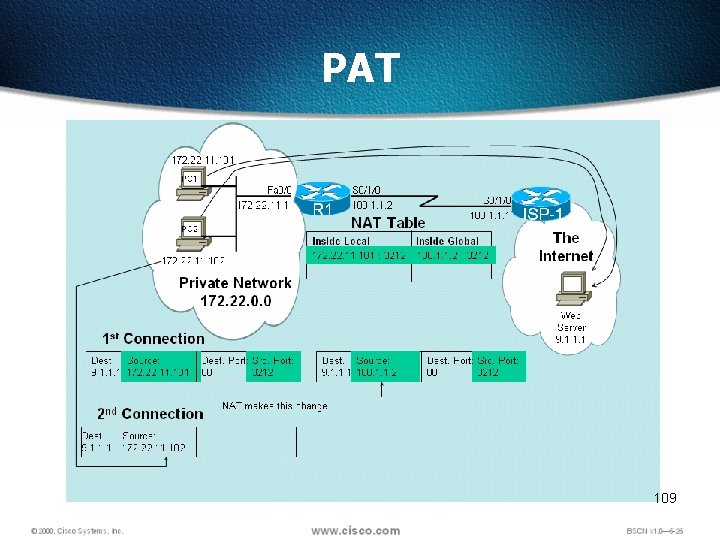
PAT 109
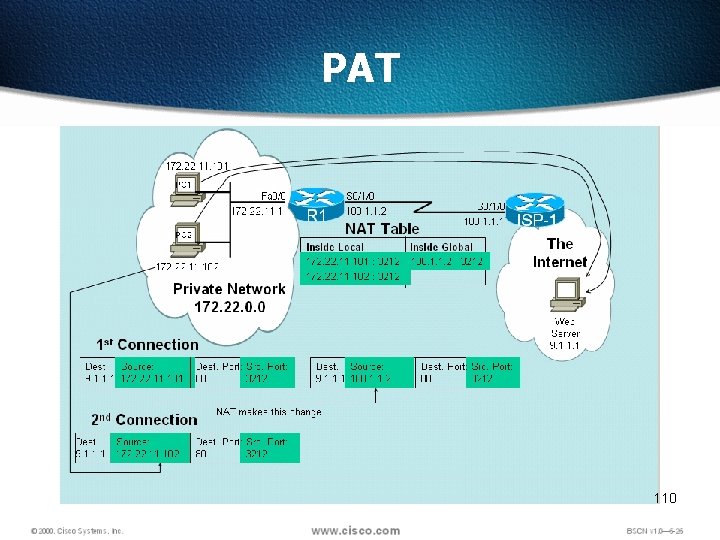
PAT 110
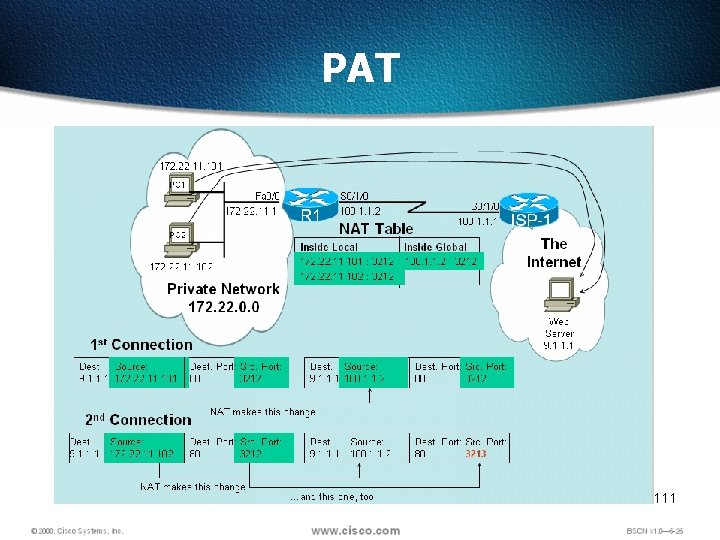
PAT 111
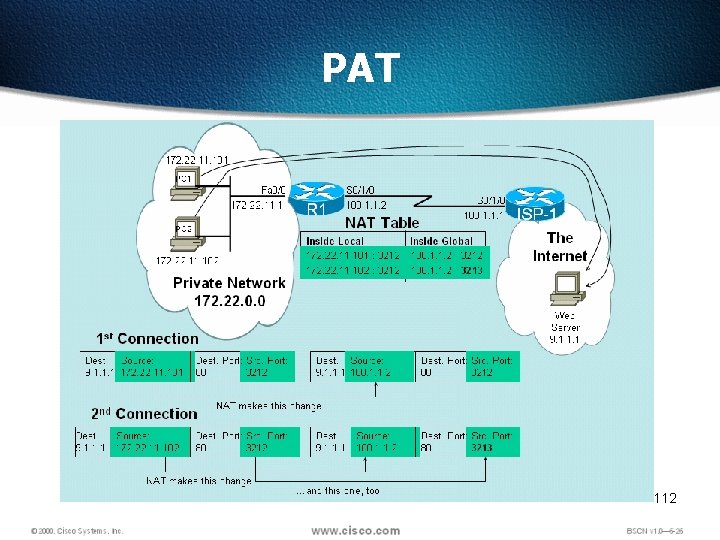
PAT 112
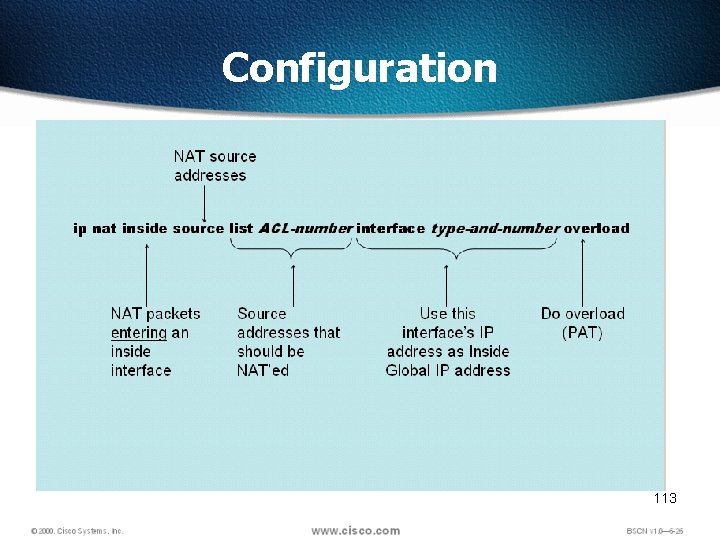
Configuration 113
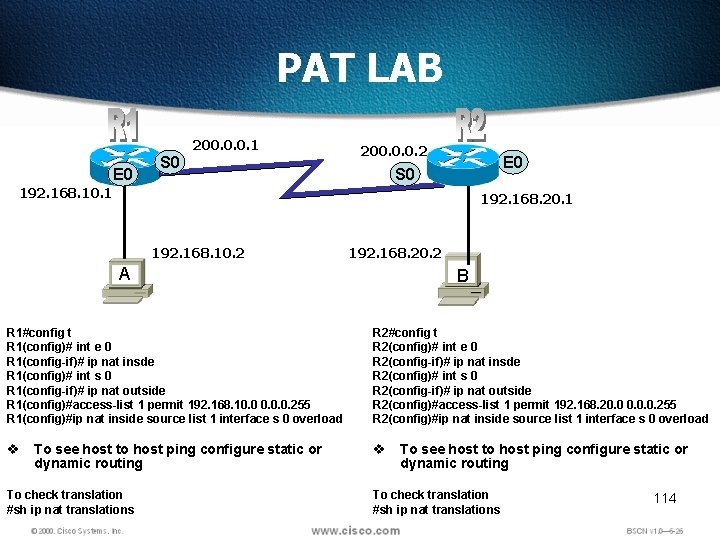
PAT LAB 200. 0. 0. 1 E 0 S 0 200. 0. 0. 2 E 0 S 0 192. 168. 10. 1 192. 168. 20. 1 192. 168. 10. 2 A 192. 168. 20. 2 B R 1#config t R 1(config)# int e 0 R 1(config-if)# ip nat insde R 1(config)# int s 0 R 1(config-if)# ip nat outside R 1(config)#access-list 1 permit 192. 168. 10. 0. 0. 255 R 1(config)#ip nat inside source list 1 interface s 0 overload R 2#config t R 2(config)# int e 0 R 2(config-if)# ip nat insde R 2(config)# int s 0 R 2(config-if)# ip nat outside R 2(config)#access-list 1 permit 192. 168. 20. 0. 0. 255 R 2(config)#ip nat inside source list 1 interface s 0 overload v To see host to host ping configure static or dynamic routing To check translation #sh ip nat translations 114
- Slides: 113