TRNG I HC BCH KHOA H NI VIN
TRƯỜNG ĐẠI HỌC BÁCH KHOA HÀ NỘI VIỆN ĐIỆN TỬ VIỄN THÔNG PH N TÍCH THIẾT KẾ HƯỚNG ĐỐI TƯỢNG CHƯƠNG 4 Thiết kế (tiếp theo và hết) Bộ môn Điện tử Kỹ thuật máy tính
Chương 4. Thiết kế o o o 4. 1. Chuẩn bị thiết kế 4. 2. Thiết kế lớp và phương thức 4. 3. Thiết kế lớp quản lý dữ liệu 4. 4. Thiết kế giao diện giao tiếp người-máy 4. 5. Thiết kế kiến trúc vật lý January 22 OOD - DEI. FET. HUT 2
Key Definitions o Physical Architecture Layer Design n The plan for the o Hardware o Software o Communications infrastructure o Security o Global support January 22 OOD - DEI. FET. HUT 3
Key Definitions o Must decide on the architecture n Server-based o Processing built in to the server n Client-based o Processing done on client PCs n Client-server based o Processing shared between client and server January 22 OOD - DEI. FET. HUT 4
Key Definitions o Network model n Shows major components of the system n Where they are located n How they will be interconnected o Hardware and software specification n Give details of NW model components n Guides purchase and acquisition January 22 OOD - DEI. FET. HUT 5
Key Definitions o Global support and security plan n Address global issues of the app. o Standards, support, culture, etc. n Addresses security o Disruption, data corruption, disaster recovery, unauthorized access, etc. January 22 OOD - DEI. FET. HUT 6

ARCHITECTURAL COMPONENTS
Components of the Architectures o Servers n Mainframes, Minis, Micros, Cloud’s VMs o Clients n Input/Output HW used by users n Terminals, PCs, Mobiles, special purpose HW o Network n HW and SW to connect clients to servers January 22 OOD - DEI. FET. HUT 8
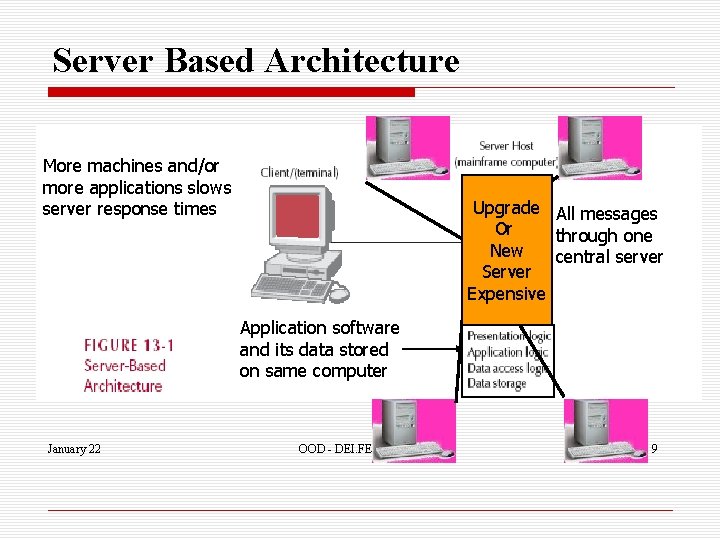
Server Based Architecture More machines and/or more applications slows server response times Upgrade Server All messages Must Or through one Process New central server Server All Expensive Messages Application software and its data stored on same computer 9 January 22 OOD - DEI. FET. HUT 9
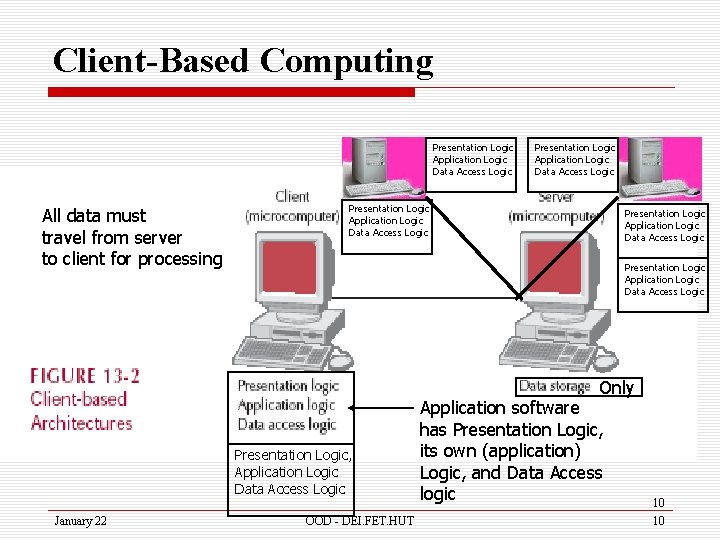
Client-Based Computing Presentation Logic Application Logic Data Access Logic All data must travel from server to client for processing Presentation Logic Application Logic Data Access Logic Only Presentation Logic, Application Logic Data Access Logic January 22 OOD - DEI. FET. HUT Application software has Presentation Logic, its own (application) Logic, and Data Access logic 10 10
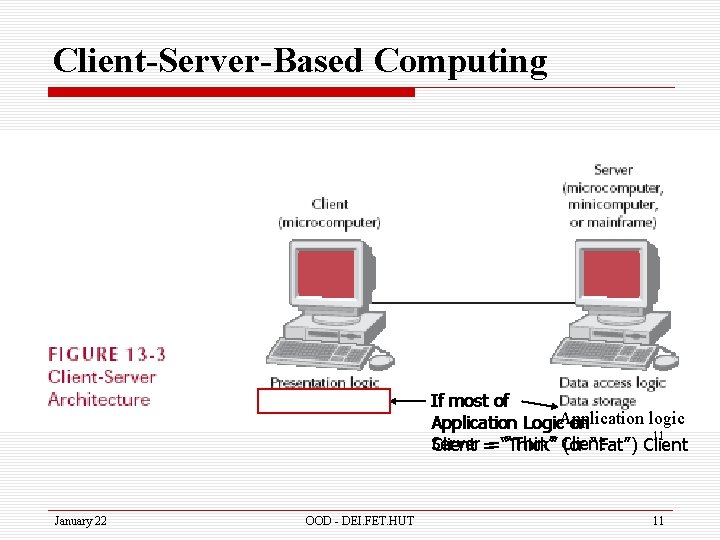
Client-Server-Based Computing If most of logic Application Logic. Application on 11 Server “Thin” Client ==“Thick” (or “Fat”) Client January 22 OOD - DEI. FET. HUT 11
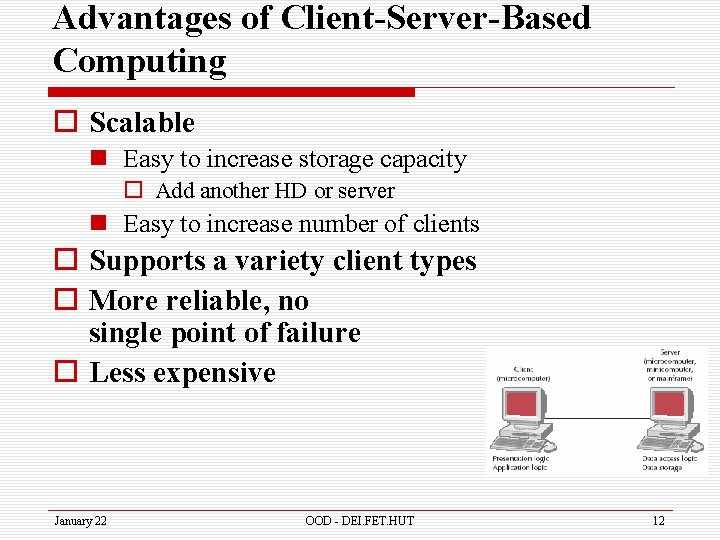
Advantages of Client-Server-Based Computing o Scalable n Easy to increase storage capacity o Add another HD or server n Easy to increase number of clients o Supports a variety client types o More reliable, no single point of failure o Less expensive January 22 OOD - DEI. FET. HUT 12
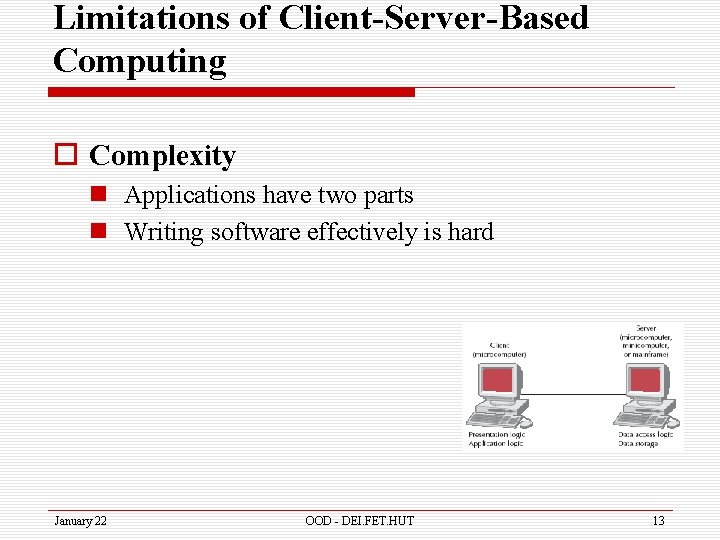
Limitations of Client-Server-Based Computing o Complexity n Applications have two parts n Writing software effectively is hard January 22 OOD - DEI. FET. HUT 13
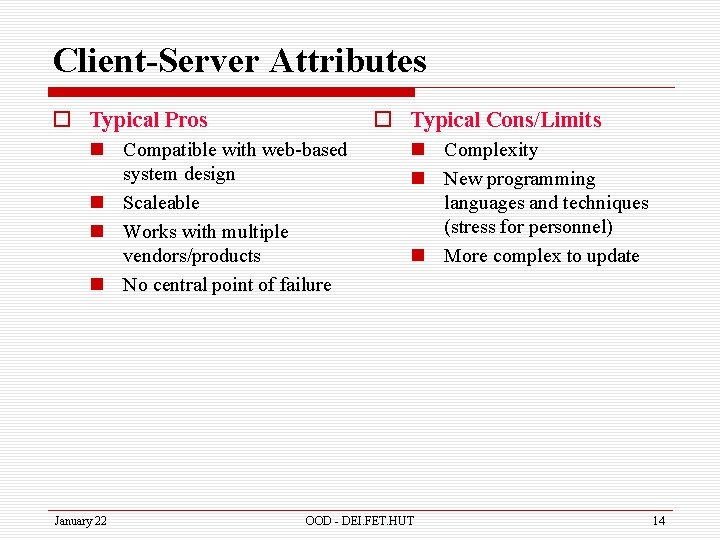
Client-Server Attributes o Typical Pros o Typical Cons/Limits n Compatible with web-based system design n Scaleable n Works with multiple vendors/products n No central point of failure January 22 n Complexity n New programming languages and techniques (stress for personnel) n More complex to update OOD - DEI. FET. HUT 14
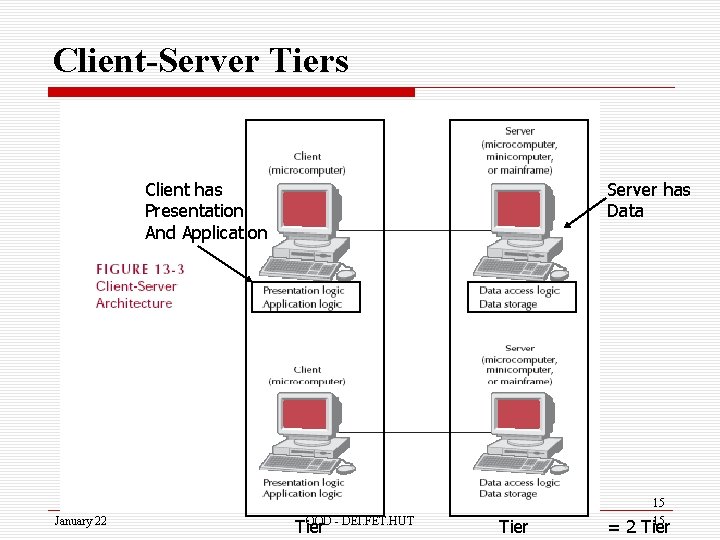
Client-Server Tiers Client has Presentation And Application Server has Data 15 January 22 OOD - DEI. FET. HUT Tier 15 = 2 Tier
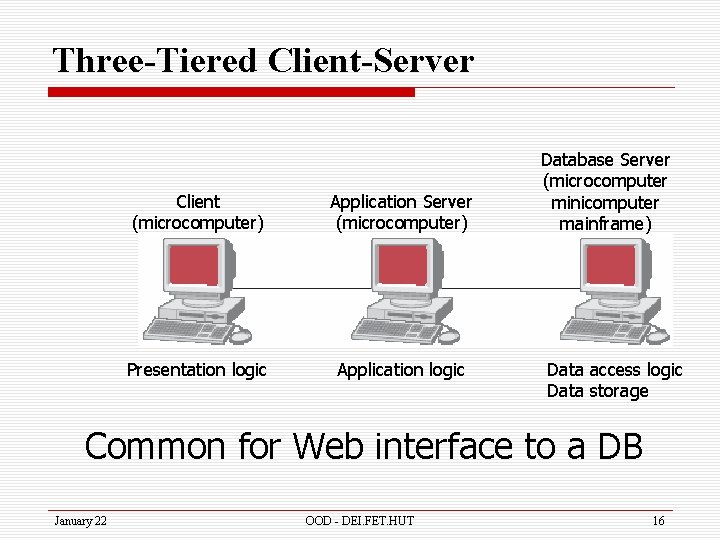
Three-Tiered Client-Server Client (microcomputer) Application Server (microcomputer) Presentation logic Application logic Database Server (microcomputer minicomputer mainframe) Data access logic Data storage Common for Web interface to a DB January 22 OOD - DEI. FET. HUT 16
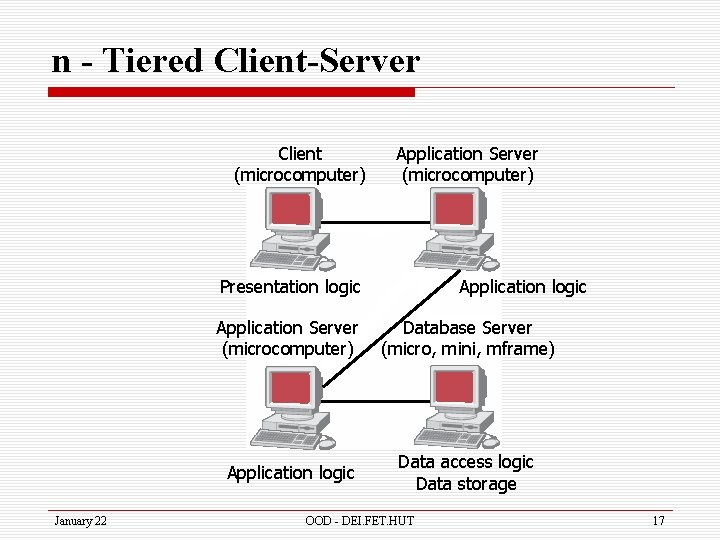
n - Tiered Client-Server Client (microcomputer) Application Server (microcomputer) Presentation logic January 22 Application logic Application Server (microcomputer) Database Server (micro, mini, mframe) Application logic Data access logic Data storage OOD - DEI. FET. HUT 17
n - Tiered Client-Server Attributes o Typical Pros o Typical Cons/Limits n Separates processing to better balance load n More scaleable January 22 n Greater load on the network n More difficult to program and test OOD - DEI. FET. HUT 18
Distributed Objects Computing (DOC) o Middleware n n Between clients and servers Support objects in distributed computing Makes physical network transparent Allows developer to focus on the application, rather than which server has which objects n Can ignore physical location of server objects January 22 OOD - DEI. FET. HUT 19
Distributed Objects Computing (DOC) o So servers can be added / removed without updating client code n Only the middleware needs to be changed o The price? n May reduce efficiency of the application January 22 OOD - DEI. FET. HUT 20
Competing Approaches o Object Management Group n Common Object Request Broker Architecture (CORBA) o Sun n Enterprise Java. Beans (EJB) n Java 2 Enterprise Edition (J 2 EE) o Microsoft n Distributed Component Object Model (DCOM) n. net framework January 22 OOD - DEI. FET. HUT 21
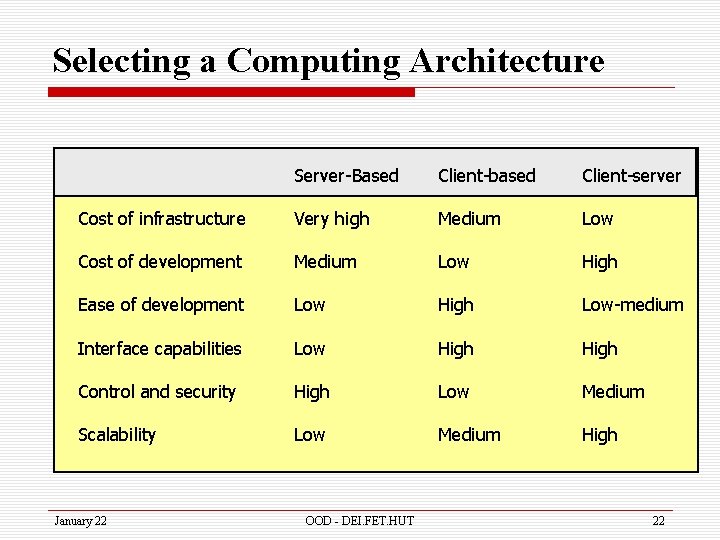
Selecting a Computing Architecture Server-Based Client-based Client-server Cost of infrastructure Very high Medium Low Cost of development Medium Low High Ease of development Low High Low-medium Interface capabilities Low High Control and security High Low Medium Scalability Low Medium High January 22 OOD - DEI. FET. HUT 22

INFRASTUCTURE DESIGN
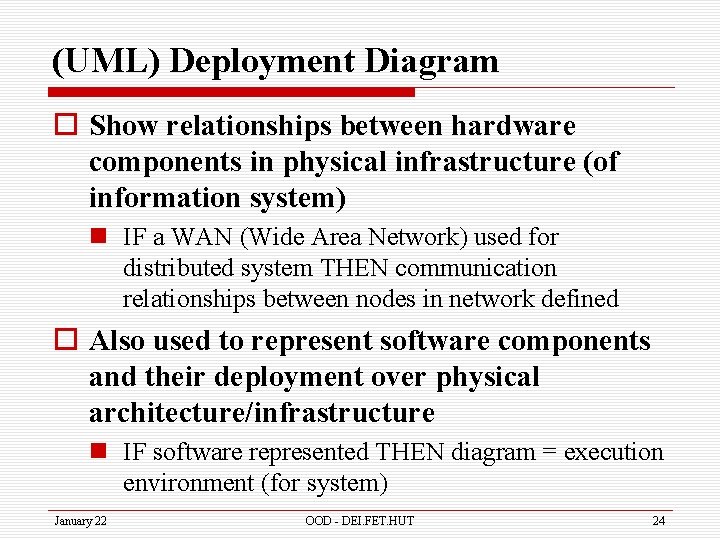
(UML) Deployment Diagram o Show relationships between hardware components in physical infrastructure (of information system) n IF a WAN (Wide Area Network) used for distributed system THEN communication relationships between nodes in network defined o Also used to represent software components and their deployment over physical architecture/infrastructure n IF software represented THEN diagram = execution environment (for system) January 22 OOD - DEI. FET. HUT 24
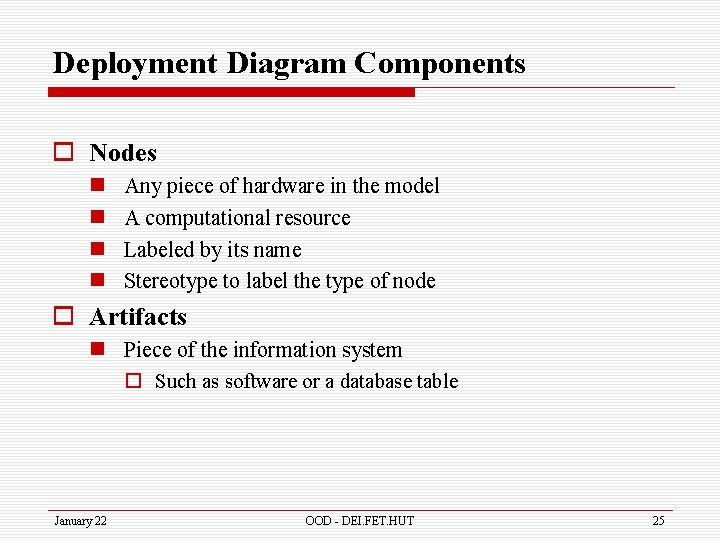
Deployment Diagram Components o Nodes n n Any piece of hardware in the model A computational resource Labeled by its name Stereotype to label the type of node o Artifacts n Piece of the information system o Such as software or a database table January 22 OOD - DEI. FET. HUT 25
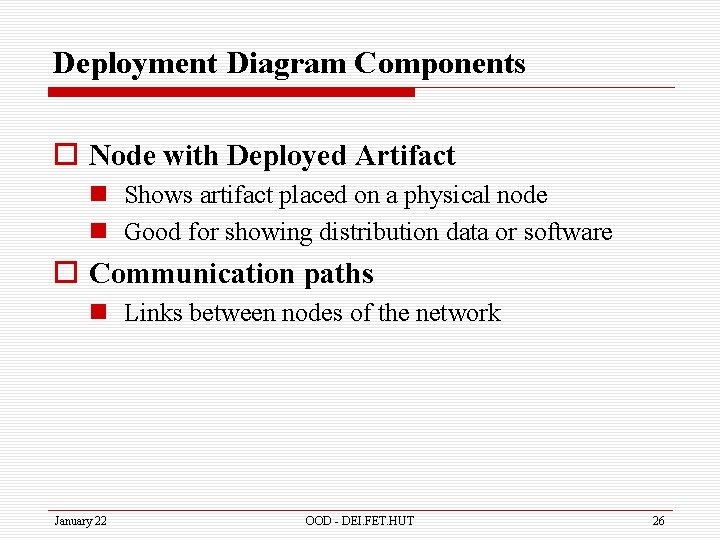
Deployment Diagram Components o Node with Deployed Artifact n Shows artifact placed on a physical node n Good for showing distribution data or software o Communication paths n Links between nodes of the network January 22 OOD - DEI. FET. HUT 26
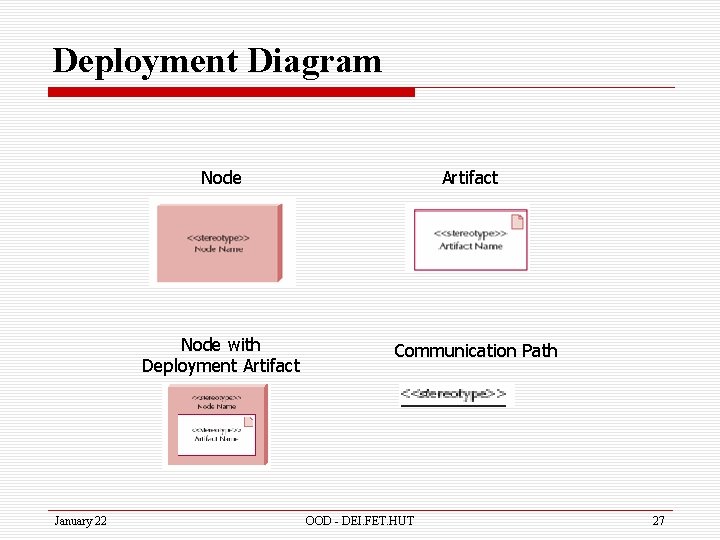
Deployment Diagram Node with Deployment Artifact January 22 Artifact Communication Path OOD - DEI. FET. HUT 27
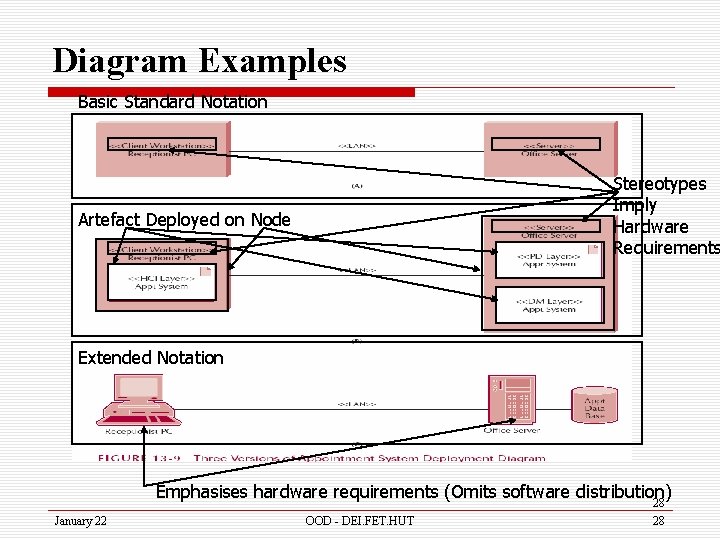
Diagram Examples Basic Standard Notation Stereotypes Imply Hardware Requirements Artefact Deployed on Node Extended Notation Emphasises hardware requirements (Omits software distribution) 28 January 22 OOD - DEI. FET. HUT 28
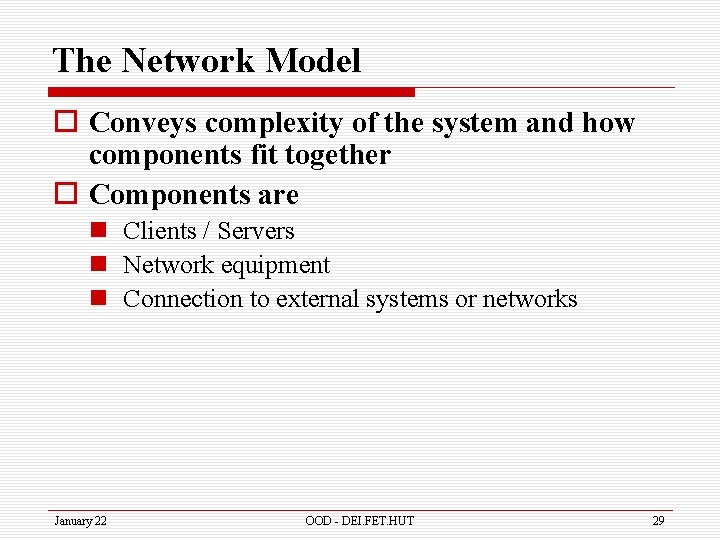
The Network Model o Conveys complexity of the system and how components fit together o Components are n Clients / Servers n Network equipment n Connection to external systems or networks January 22 OOD - DEI. FET. HUT 29
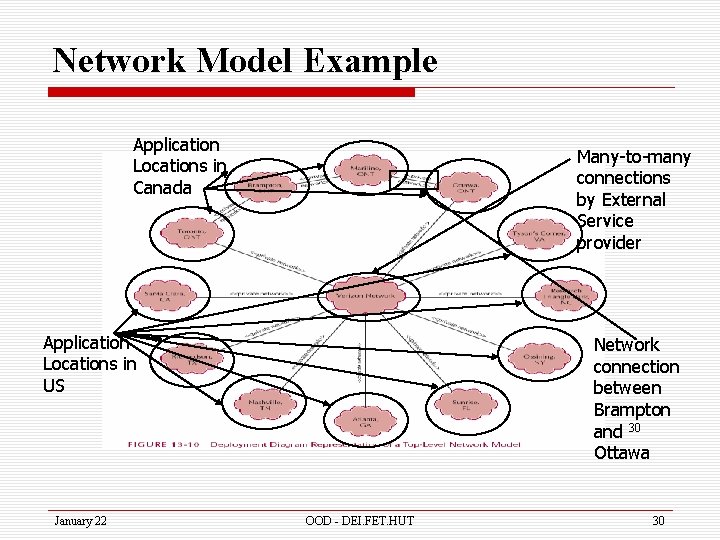
Network Model Example Application Locations in Canada Many-to-many connections by External Service provider Application Locations in US January 22 Network connection between Brampton and 30 Ottawa OOD - DEI. FET. HUT 30
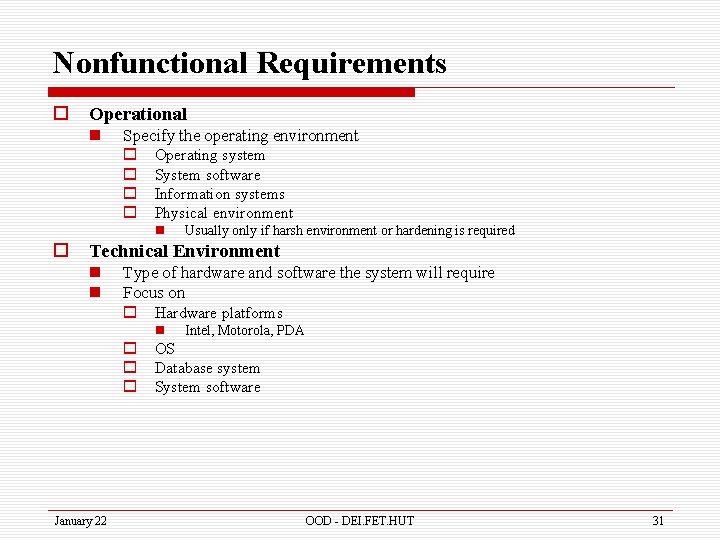
Nonfunctional Requirements o Operational n Specify the operating environment o Operating system o System software o Information systems o Physical environment n o Usually only if harsh environment or hardening is required Technical Environment n n Type of hardware and software the system will require Focus on o Hardware platforms n Intel, Motorola, PDA o OS o Database system o System software January 22 OOD - DEI. FET. HUT 31
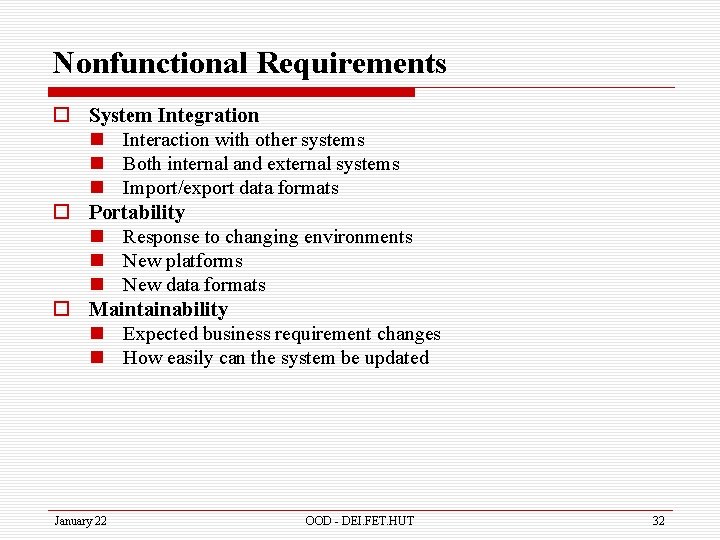
Nonfunctional Requirements o System Integration n Interaction with other systems n Both internal and external systems n Import/export data formats o Portability n Response to changing environments n New platforms n New data formats o Maintainability n Expected business requirement changes n How easily can the system be updated January 22 OOD - DEI. FET. HUT 32
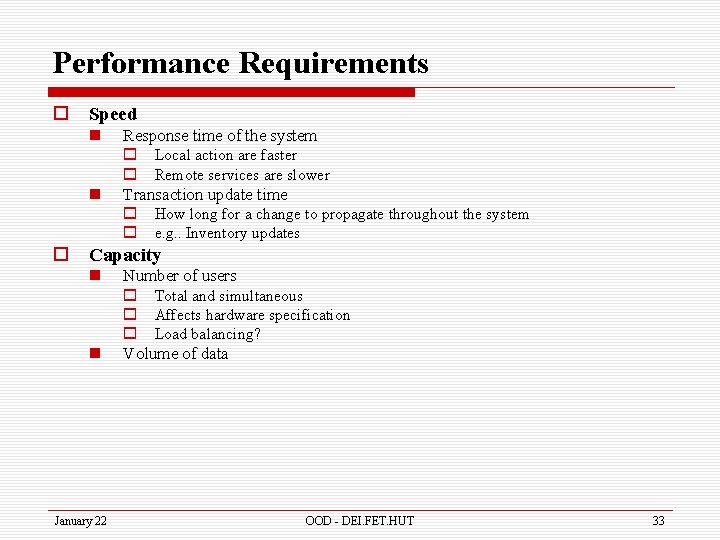
Performance Requirements o Speed n n o Response time of the system o Local action are faster o Remote services are slower Transaction update time o How long for a change to propagate throughout the system o e. g. . Inventory updates Capacity n n January 22 Number of users o Total and simultaneous o Affects hardware specification o Load balancing? Volume of data OOD - DEI. FET. HUT 33
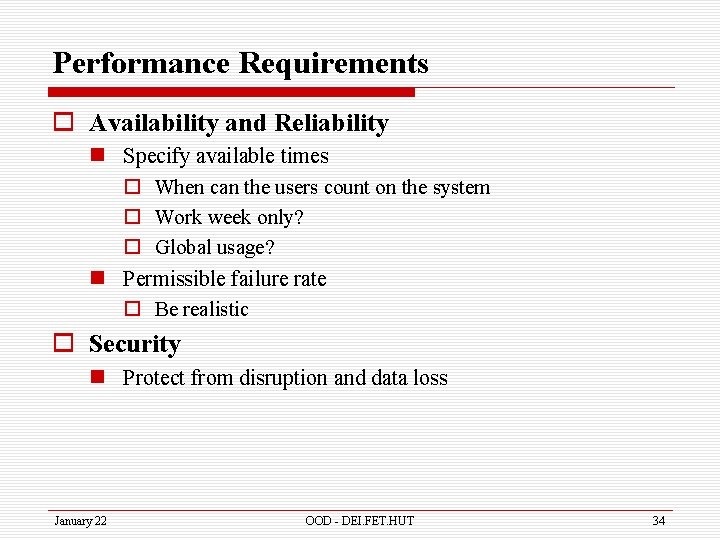
Performance Requirements o Availability and Reliability n Specify available times o When can the users count on the system o Work week only? o Global usage? n Permissible failure rate o Be realistic o Security n Protect from disruption and data loss January 22 OOD - DEI. FET. HUT 34

SECURITY
Identifying Threats to the System o Threat n Any potential adverse occurrence that can harm the application or its data o Threats come from n Internal sources n External sources January 22 OOD - DEI. FET. HUT 36
Identifying Threats to the System o Two categories of threats n Disruptions, destruction and disaster o Disruption – can't use app for awhile o Destruction – corrupt files, crash HD o Disaster – natural or man-made n Unauthorized access o Internal and external January 22 OOD - DEI. FET. HUT 37
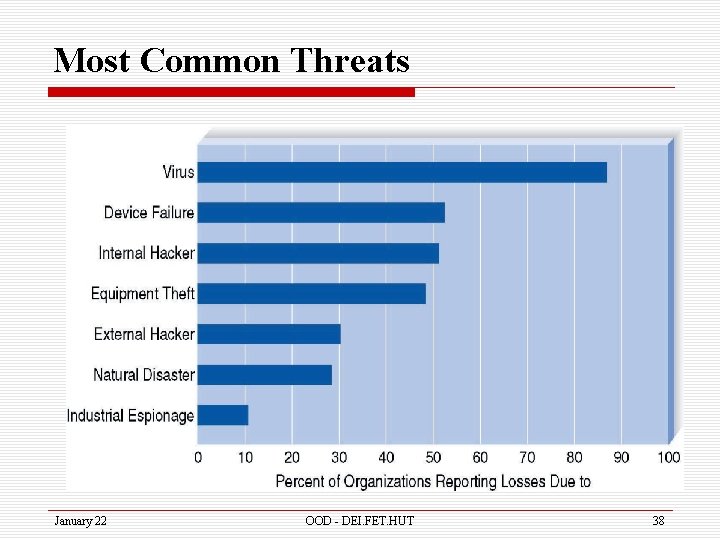
Most Common Threats January 22 OOD - DEI. FET. HUT 38
Assessing the Risk of Each Threat o After the threats are identified n List threats across top of page n List components down side o In order of importance n List controls in the cells created o Control – Something that stops or mitigates the consequences of the threat January 22 OOD - DEI. FET. HUT 39
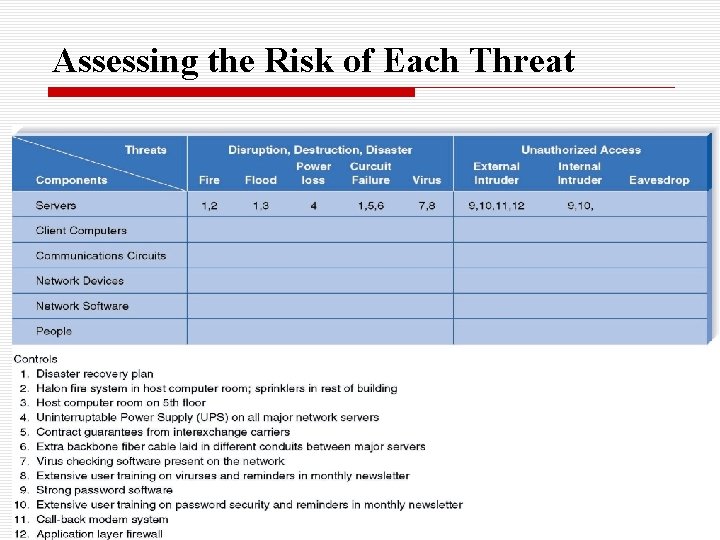
Assessing the Risk of Each Threat January 22 OOD - DEI. FET. HUT 40
Creating Controls o Controls for disruption, destruction and disaster n redundancy o Fault tolerant o Auto transfer n disaster recovery plans n Virus protection January 22 OOD - DEI. FET. HUT 41
Creating Controls o Controls for unauthorized access n n n January 22 Security policy and training Screen users Use authentication and encryption Firewalls Physical security OOD - DEI. FET. HUT 42
Additional Controls Include o A security policy o Passwords and encryption o Firewalls January 22 OOD - DEI. FET. HUT 43

Cultural and Political Requirements
Multilingual Requirements o Need good translations n KFC example o Concurrent multilingual systems n Handle language on the fly o Discrete multilingual systems n Separate parts written for each language January 22 OOD - DEI. FET. HUT 45
Customization o Who has control of the application? o Can each region make changes to the system o Can they allow subsidiaries to make changes? January 22 OOD - DEI. FET. HUT 46
Unstated Norms o Make assumptions explicit o Some examples: n n January 22 Date format Numeric format Name order 24/7 support OOD - DEI. FET. HUT 47
- Slides: 47