MAC Layer Survey 1 The Medium Access Sublayer
MAC Layer Survey 1
The Medium Access Sublayer q q q MAC: Medium Access Control – As opposed to “high access control” or “low access control”? – NO! – It means: controlling access to the medium. – provides arbitration mechanism for shared medium What are arbitration mechanisms in this classroom? – Raising your hand – Verbal cues, e. g. “go ahead, Fred”. – Eye contact Background: review of: – Broadcast vs. Point-to-Point media – Topologies: Bus, Ring Then: Static vs. Dynamic channel allocation Finally: ALOHA, and CSMA/CD (Ethernet) 2
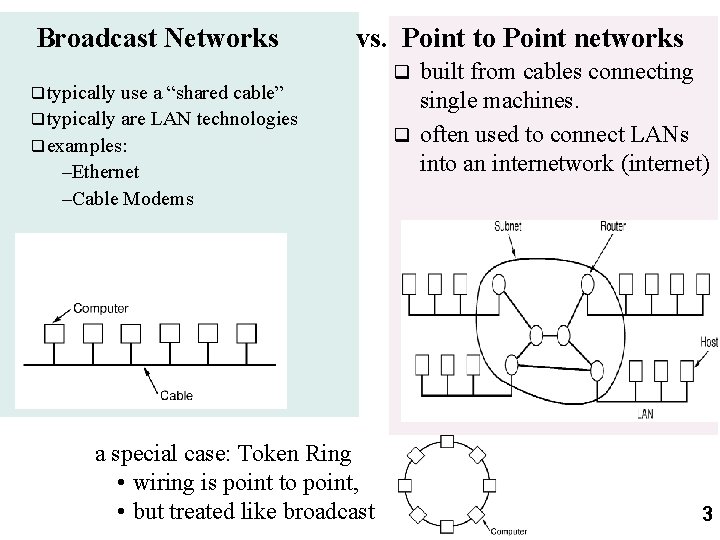
Broadcast Networks vs. Point to Point networks q typically use a “shared cable” q typically are LAN technologies q examples: –Ethernet –Cable Modems a special case: Token Ring • wiring is point to point, • but treated like broadcast built from cables connecting single machines. q often used to connect LANs into an internetwork (internet) q 3
The Channel Allocation Problem (continued) q Statistical multiplexing is preferred to FDM and TDM. – Arrange all the packets in a giant central queue, and share the bandwidth on a first come first served basis. – Don’t pre-allocate bandwidth for users that may just waste it. – For details, need to review some basic queuing theory, and know what an exponential and poisson distribution are. 4
Dynamic channel allocation Five characteristics of channel allocation models: 1) Station model: stations independent 2) Single channel assumption 3) Collisions 4) Continuous (free-for-all, pure Aloha) vs Discrete Time (time is slotted) 5) Carrier sense (polite, listen first) vs. no Carrier Sense (just blurt out) 5
Aloha Norman Abramson et. al, University of Hawaii q Send packets on shared channel; if collisions occur, wait random amount of time, and try again. q Original purpose: – host to terminal communication (very bursty) – ground-based radio channel; want to share it. q However, basic ideas have application to any environment where there is a shared medium, and uncoordinated users – a bus-topology LAN – the up-link part of a Satellite channel q 1970 s 6
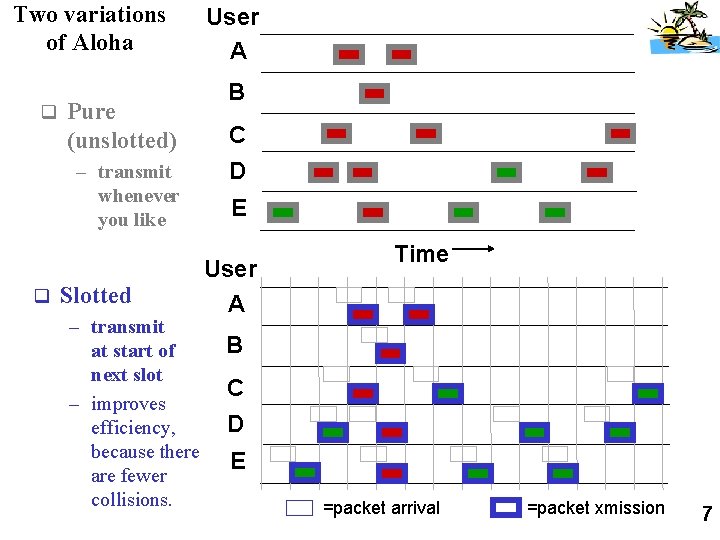
Two variations of Aloha q Pure (unslotted) – transmit whenever you like q Slotted – transmit at start of next slot – improves efficiency, because there are fewer collisions. User A B C D E User A Time B C D E =packet arrival =packet xmission 7
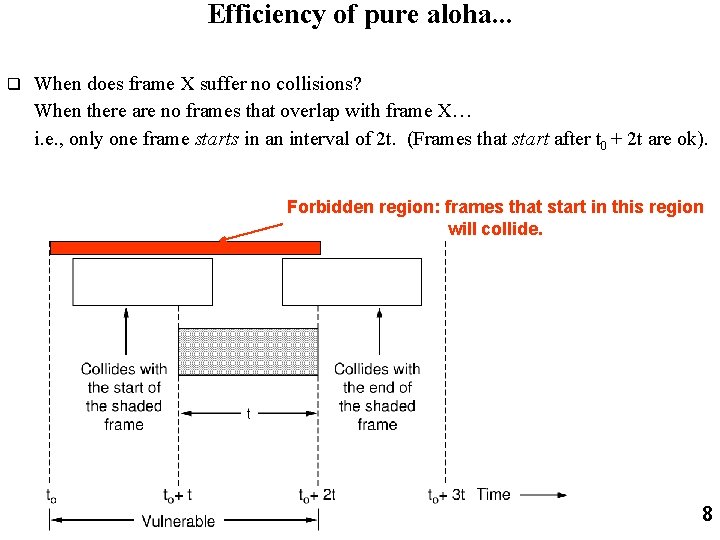
Efficiency of pure aloha. . . q When does frame X suffer no collisions? When there are no frames that overlap with frame X… i. e. , only one frame starts in an interval of 2 t. (Frames that start after t 0 + 2 t are ok). Forbidden region: frames that start in this region will collide. 8
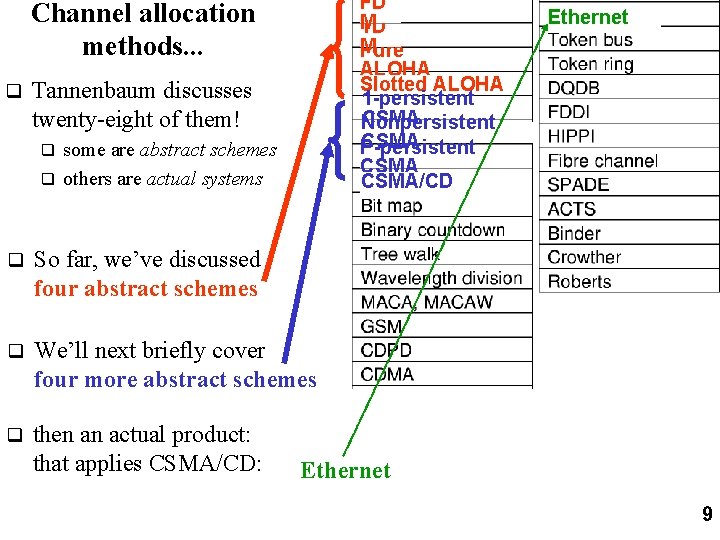
FD M TD M Pure ALOHA Slotted ALOHA 1 -persistent CSMA Nonpersistent CSMA P-persistent CSMA/CD Channel allocation methods. . . q Tannenbaum discusses twenty-eight of them! some are abstract schemes q others are actual systems q q So far, we’ve discussed four abstract schemes q We’ll next briefly cover four more abstract schemes q then an actual product: that applies CSMA/CD: Ethernet 9
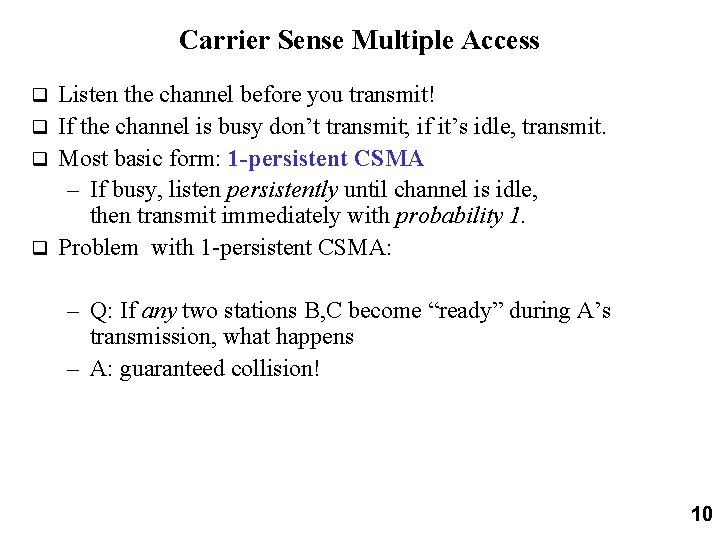
Carrier Sense Multiple Access Listen the channel before you transmit! q If the channel is busy don’t transmit; if it’s idle, transmit. q Most basic form: 1 -persistent CSMA – If busy, listen persistently until channel is idle, then transmit immediately with probability 1. q Problem with 1 -persistent CSMA: q – Q: If any two stations B, C become “ready” during A’s transmission, what happens – A: guaranteed collision! 10
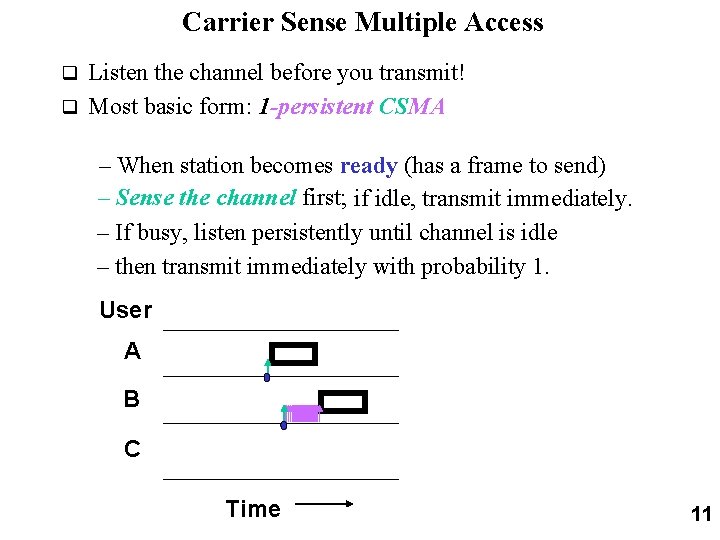
Carrier Sense Multiple Access Listen the channel before you transmit! q Most basic form: 1 -persistent CSMA q – When station becomes ready (has a frame to send) – Sense the channel first; if idle, transmit immediately. – If busy, listen persistently until channel is idle – then transmit immediately with probability 1. User A B C Time 11
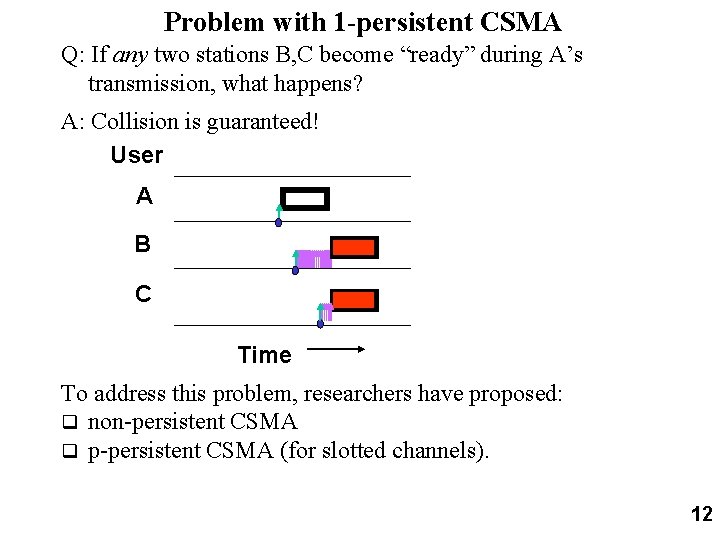
Problem with 1 -persistent CSMA Q: If any two stations B, C become “ready” during A’s transmission, what happens? A: Collision is guaranteed! User A B C Time To address this problem, researchers have proposed: q non-persistent CSMA q p-persistent CSMA (for slotted channels). 12
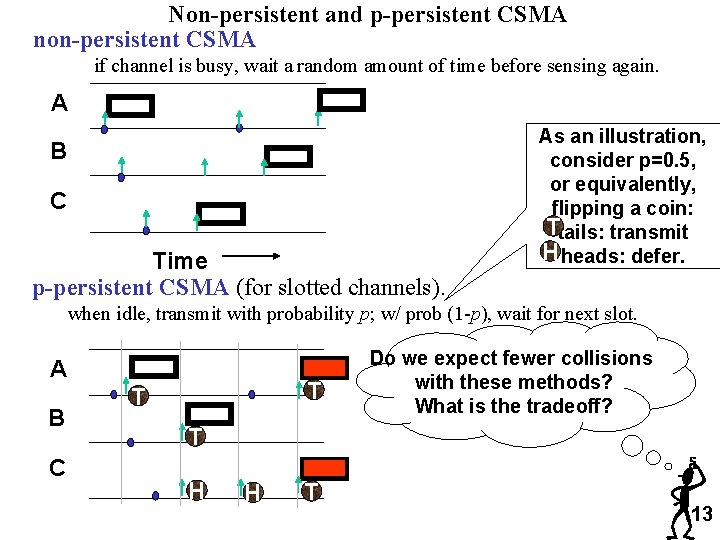
Non-persistent and p-persistent CSMA non-persistent CSMA if channel is busy, wait a random amount of time before sensing again. A B C Time p-persistent CSMA (for slotted channels). As an illustration, consider p=0. 5, or equivalently, flipping a coin: Ttails: transmit H heads: defer. when idle, transmit with probability p; w/ prob (1 -p), wait for next slot. A B C T T Do we expect fewer collisions with these methods? What is the tradeoff? T H H T 13
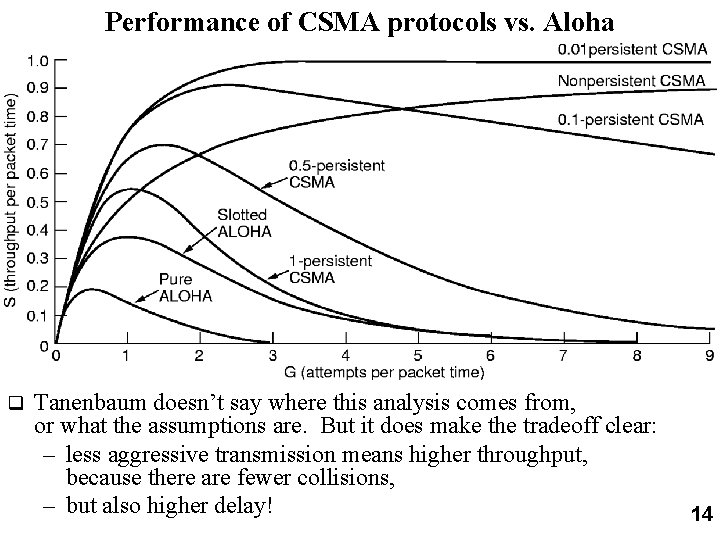
Performance of CSMA protocols vs. Aloha q Tanenbaum doesn’t say where this analysis comes from, or what the assumptions are. But it does make the tradeoff clear: – less aggressive transmission means higher throughput, because there are fewer collisions, – but also higher delay! 14
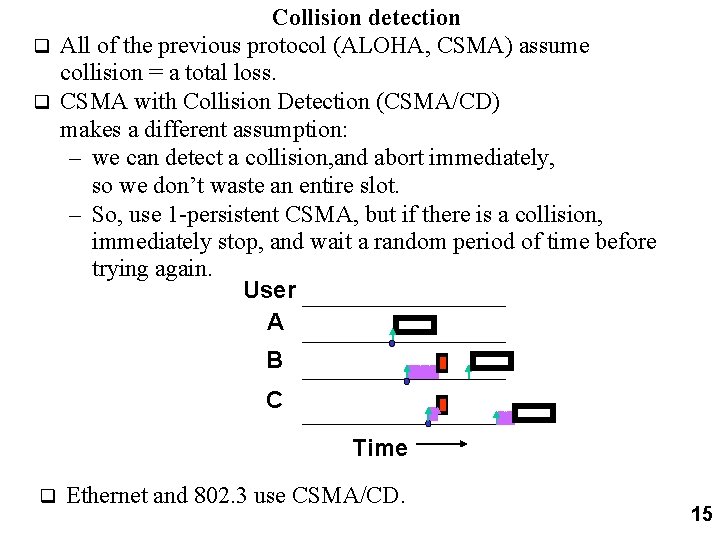
Collision detection q All of the previous protocol (ALOHA, CSMA) assume collision = a total loss. q CSMA with Collision Detection (CSMA/CD) makes a different assumption: – we can detect a collision, and abort immediately, so we don’t waste an entire slot. – So, use 1 -persistent CSMA, but if there is a collision, immediately stop, and wait a random period of time before trying again. User A B C Time q Ethernet and 802. 3 use CSMA/CD. 15
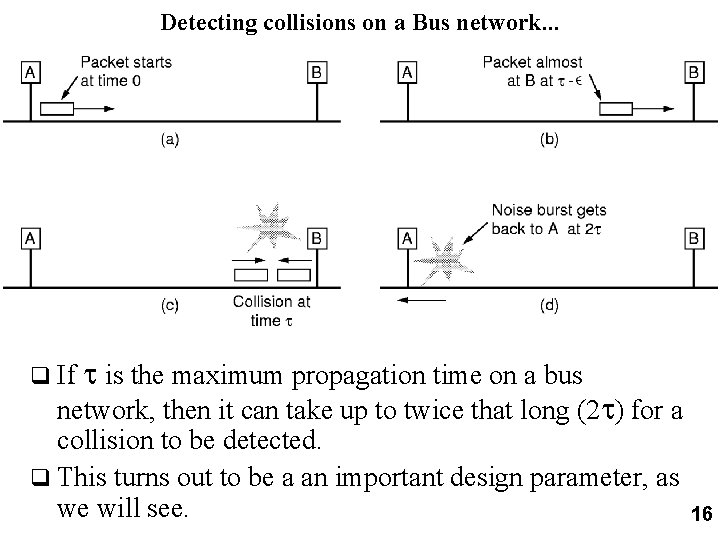
Detecting collisions on a Bus network. . . q If is the maximum propagation time on a bus network, then it can take up to twice that long (2 ) for a collision to be detected. q This turns out to be a an important design parameter, as we will see. 16
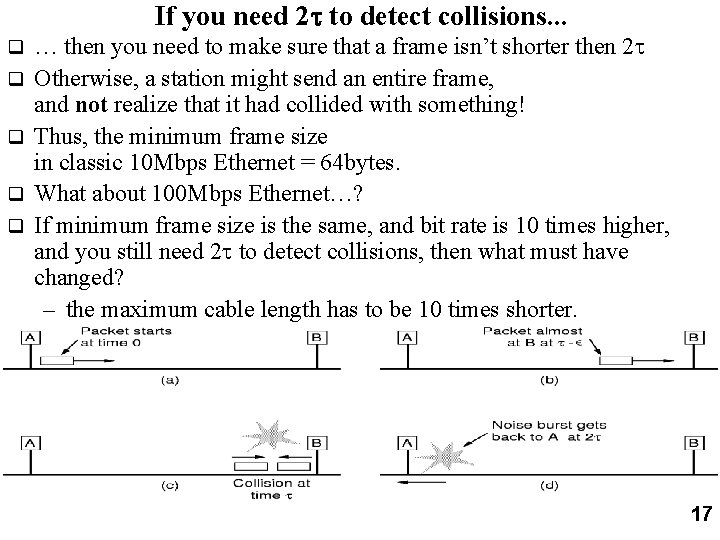
If you need 2 to detect collisions. . . q q q … then you need to make sure that a frame isn’t shorter then 2 Otherwise, a station might send an entire frame, and not realize that it had collided with something! Thus, the minimum frame size in classic 10 Mbps Ethernet = 64 bytes. What about 100 Mbps Ethernet…? If minimum frame size is the same, and bit rate is 10 times higher, and you still need 2 to detect collisions, then what must have changed? – the maximum cable length has to be 10 times shorter. 17
Ethernet and 802. 3 q Ethernet came first, invented at Xerox PARC (Palo Alto Research Center). (Bob Metcalfe was key figure; later went on to be a founder of 3 COM. ) Xerox, Digital, and Intel were the “partners” in original commercial Ethernet spec. q Later, IEEE make 802. 3 a standard – lots of variations at various bit rates using various media, – changed packet type field to a length field. (packet type values are all illegal lengths, so its easy to distinguish) q For most purposes of our discussion, we’ll consider them one and the same, although purists would insist that they are different standards. q 18
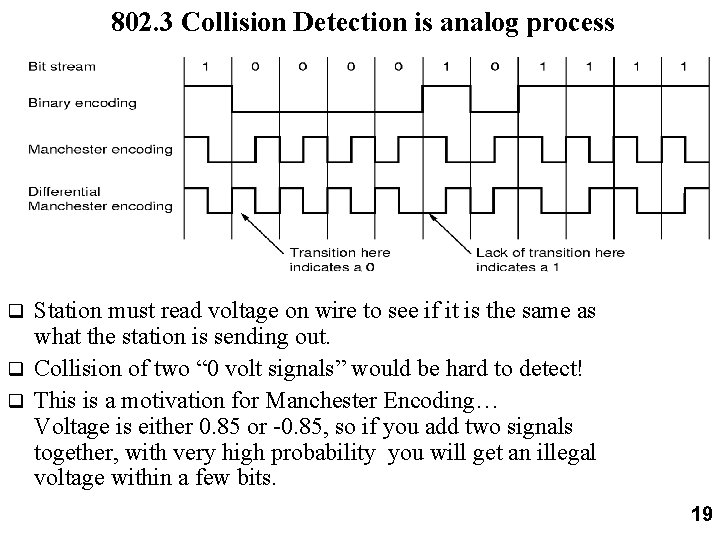
802. 3 Collision Detection is analog process Station must read voltage on wire to see if it is the same as what the station is sending out. q Collision of two “ 0 volt signals” would be hard to detect! q This is a motivation for Manchester Encoding… Voltage is either 0. 85 or -0. 85, so if you add two signals together, with very high probability you will get an illegal voltage within a few bits. q 19
Ethernet “dominant” LAN technology: q cheap $20 for 100 Mbs! q first widely used LAN technology q Simpler, cheaper than token LANs and ATM q Kept up with speed race: 10, 1000 Mbps Metcalfe’s Ethernet sketch 20
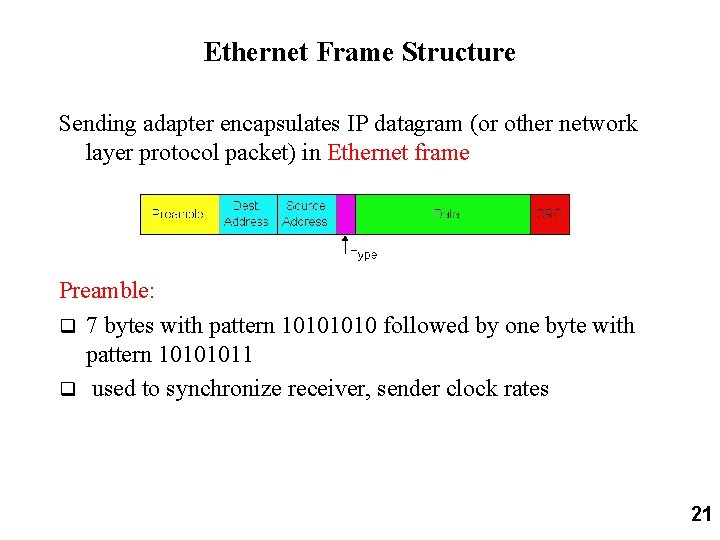
Ethernet Frame Structure Sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame Preamble: q 7 bytes with pattern 1010 followed by one byte with pattern 10101011 q used to synchronize receiver, sender clock rates 21
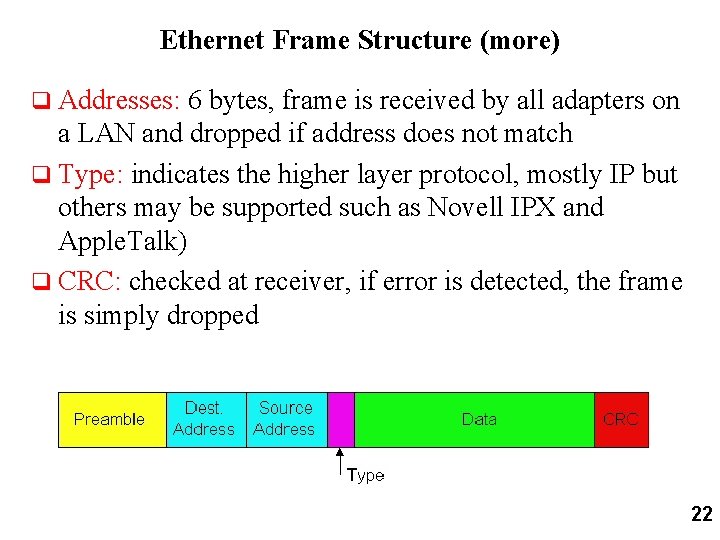
Ethernet Frame Structure (more) q Addresses: 6 bytes, frame is received by all adapters on a LAN and dropped if address does not match q Type: indicates the higher layer protocol, mostly IP but others may be supported such as Novell IPX and Apple. Talk) q CRC: checked at receiver, if error is detected, the frame is simply dropped 22
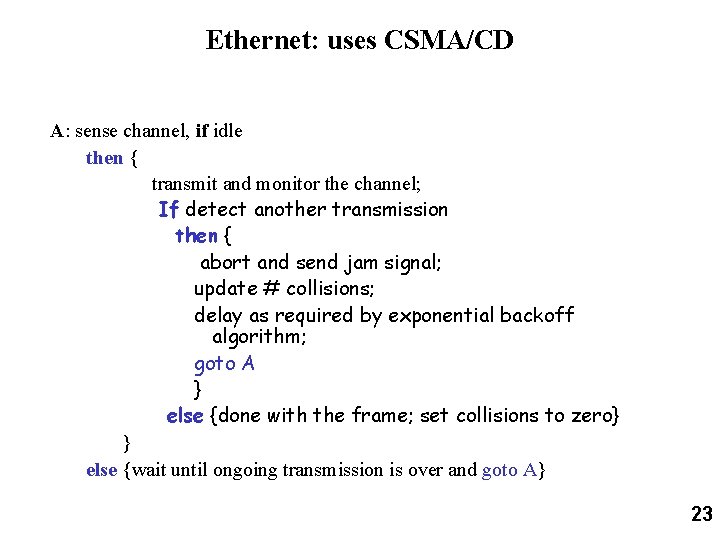
Ethernet: uses CSMA/CD A: sense channel, if idle then { transmit and monitor the channel; If detect another transmission then { abort and send jam signal; update # collisions; delay as required by exponential backoff algorithm; goto A } else {done with the frame; set collisions to zero} } else {wait until ongoing transmission is over and goto A} 23
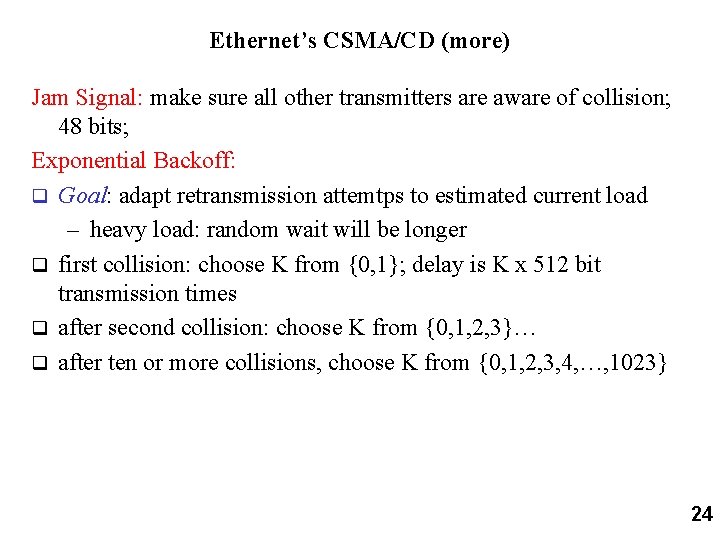
Ethernet’s CSMA/CD (more) Jam Signal: make sure all other transmitters are aware of collision; 48 bits; Exponential Backoff: q Goal: adapt retransmission attemtps to estimated current load – heavy load: random wait will be longer q first collision: choose K from {0, 1}; delay is K x 512 bit transmission times q after second collision: choose K from {0, 1, 2, 3}… q after ten or more collisions, choose K from {0, 1, 2, 3, 4, …, 1023} 24
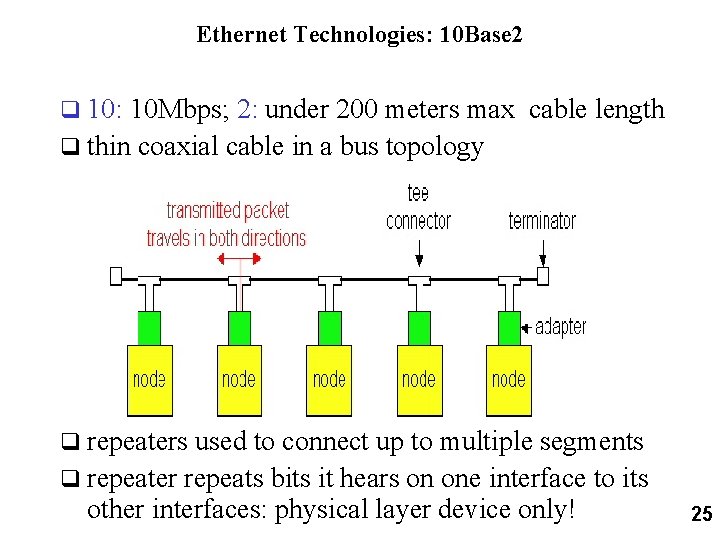
Ethernet Technologies: 10 Base 2 q 10: 10 Mbps; 2: under 200 meters max cable length q thin coaxial cable in a bus topology q repeaters used to connect up to multiple segments q repeater repeats bits it hears on one interface to its other interfaces: physical layer device only! 25
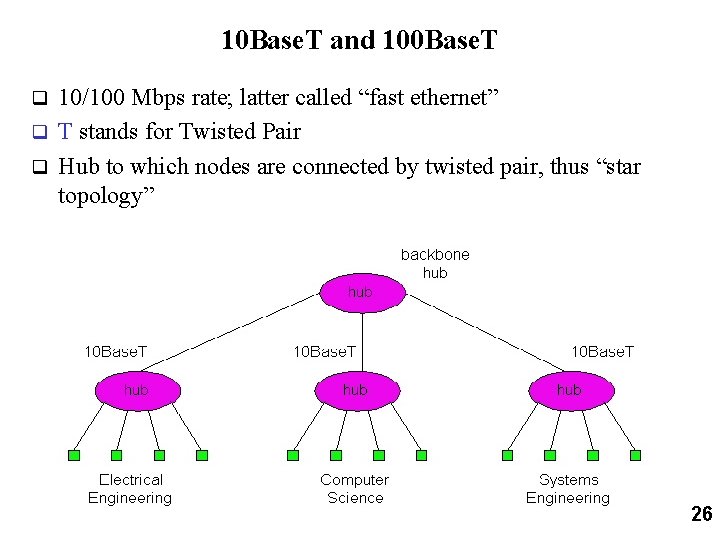
10 Base. T and 100 Base. T 10/100 Mbps rate; latter called “fast ethernet” q T stands for Twisted Pair q Hub to which nodes are connected by twisted pair, thus “star topology” q 26
LAN Addresses and ARP 32 -bit IP address: q network-layer address q used to get datagram to destination network (recall IP network definition) LAN (or MAC or physical) address: q used to get datagram from one interface to another physically-connected interface (same network) q 48 bit MAC address (for most LANs) burned in the adapter ROM 27
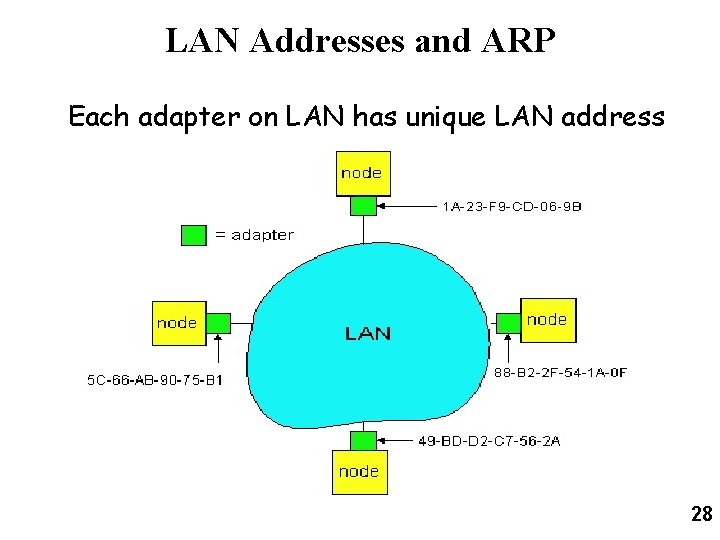
LAN Addresses and ARP Each adapter on LAN has unique LAN address 28
LAN Address (more) q MAC address allocation administered by IEEE q manufacturer buys portion of MAC address space (to assure uniqueness) q Analogy: (a) MAC address: like Social Security Number (b) IP address: like postal address q MAC flat address => portability – can move LAN card from one LAN to another q IP hierarchical address NOT portable – depends on network to which one attaches 29
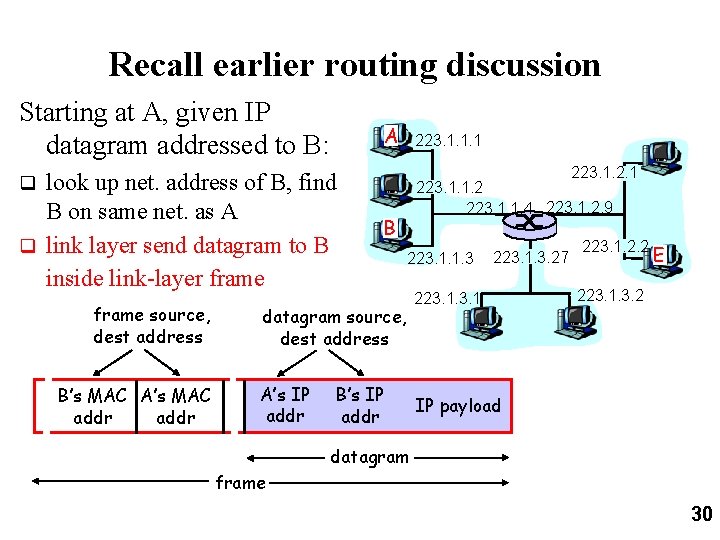
Recall earlier routing discussion Starting at A, given IP datagram addressed to B: A look up net. address of B, find B on same net. as A q link layer send datagram to B inside link-layer frame 223. 1. 1. 1 223. 1. 2. 1 q frame source, dest address B’s MAC A’s MAC addr 223. 1. 1. 2 223. 1. 1. 4 223. 1. 2. 9 B 223. 1. 1. 3 datagram source, dest address A’s IP addr B’s IP addr 223. 1. 3. 27 223. 1. 2. 2 E 223. 1. 3. 2 IP payload datagram frame 30
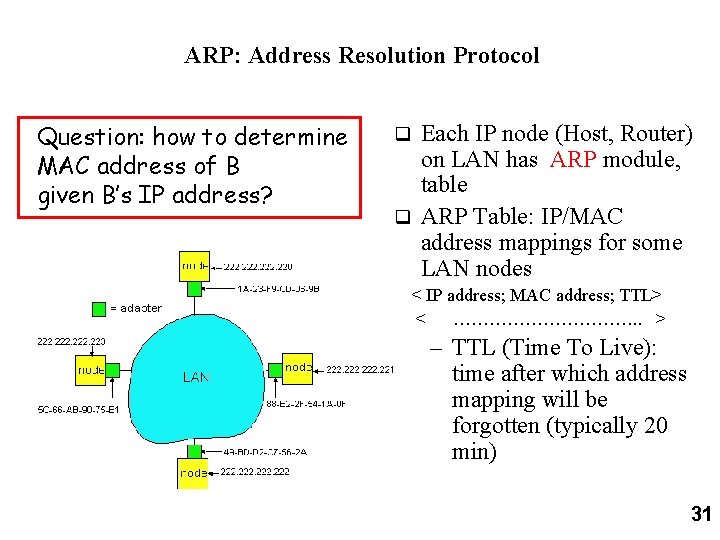
ARP: Address Resolution Protocol Question: how to determine MAC address of B given B’s IP address? Each IP node (Host, Router) on LAN has ARP module, table q ARP Table: IP/MAC address mappings for some LAN nodes q < IP address; MAC address; TTL> < ……………. . > – TTL (Time To Live): time after which address mapping will be forgotten (typically 20 min) 31
ARP protocol A knows B's IP address, wants to learn physical address of B q A broadcasts ARP query pkt, containing B's IP address q – all machines on LAN receive ARP query B receives ARP packet, replies to A with its (B's) physical layer address q A caches (saves) IP-to-physical address pairs until information becomes old (times out) q – soft state: information that times out (goes away) unless refreshed 32
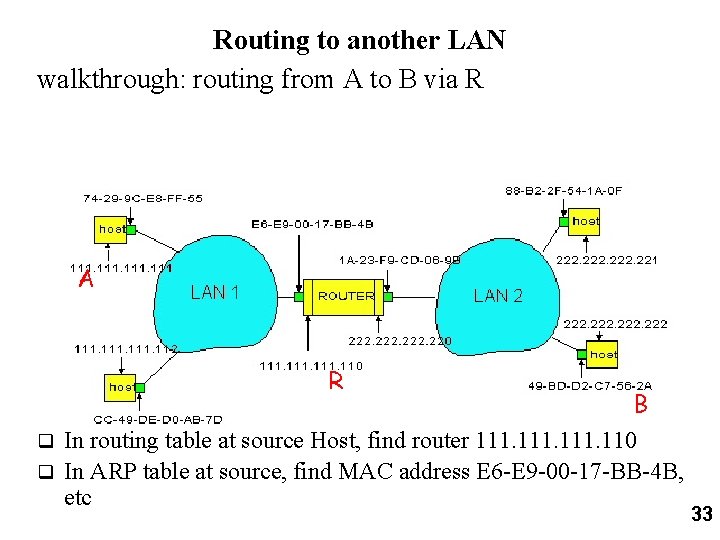
Routing to another LAN walkthrough: routing from A to B via R A R B In routing table at source Host, find router 111. 110 q In ARP table at source, find MAC address E 6 -E 9 -00 -17 -BB-4 B, etc q 33
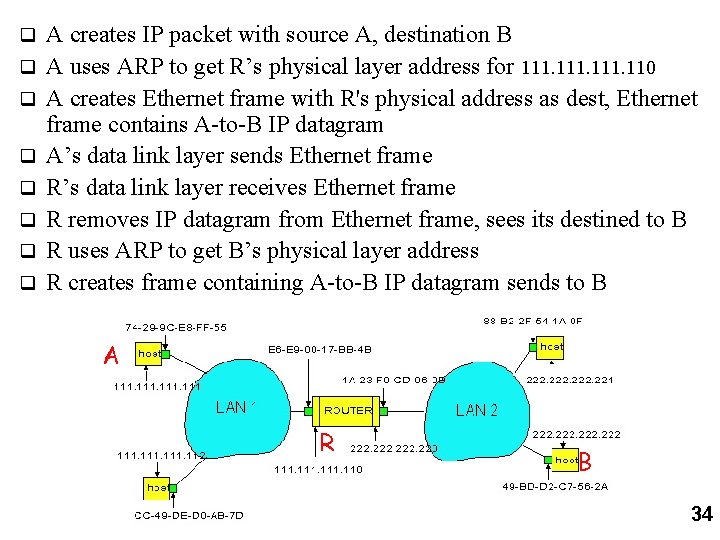
q q q q A creates IP packet with source A, destination B A uses ARP to get R’s physical layer address for 111. 110 A creates Ethernet frame with R's physical address as dest, Ethernet frame contains A-to-B IP datagram A’s data link layer sends Ethernet frame R’s data link layer receives Ethernet frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s physical layer address R creates frame containing A-to-B IP datagram sends to B A R B 34
Bridges, Internetworking q Before talking about bridges in the context of the MAC sub-layer, lets briefly skip ahead, and cover the differences among: gateways routers bridges repeaters 35
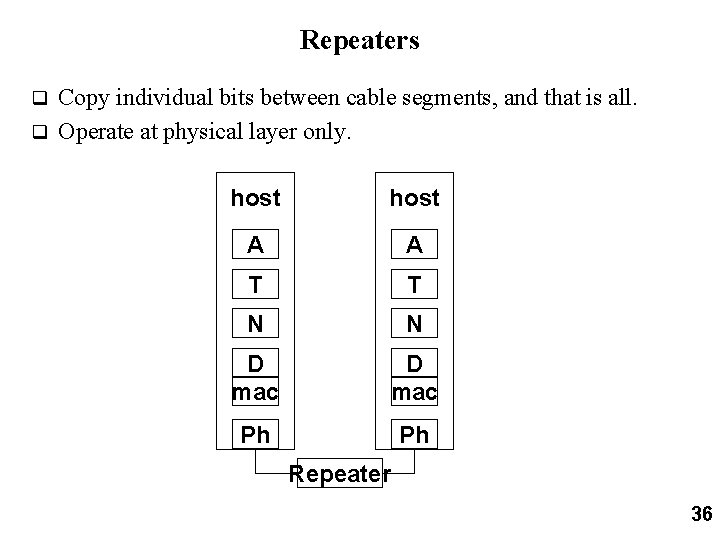
Repeaters Copy individual bits between cable segments, and that is all. q Operate at physical layer only. q host A A T T N N D mac Ph Ph Repeater 36
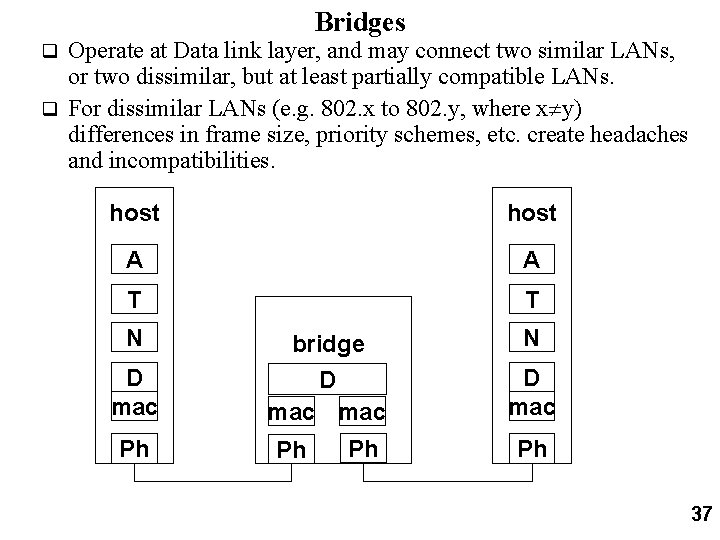
Bridges Operate at Data link layer, and may connect two similar LANs, or two dissimilar, but at least partially compatible LANs. q For dissimilar LANs (e. g. 802. x to 802. y, where x y) differences in frame size, priority schemes, etc. create headaches and incompatibilities. q host A A T T N D mac Ph bridge D mac Ph Ph N D mac Ph 37
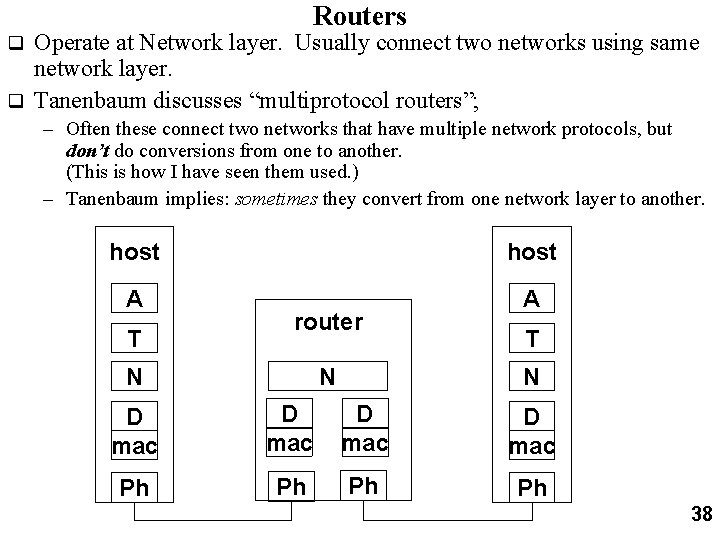
Routers Operate at Network layer. Usually connect two networks using same network layer. q Tanenbaum discusses “multiprotocol routers”; q – Often these connect two networks that have multiple network protocols, but don’t do conversions from one to another. (This is how I have seen them used. ) – Tanenbaum implies: sometimes they convert from one network layer to another. host A A T router N N T N D mac Ph Ph 38
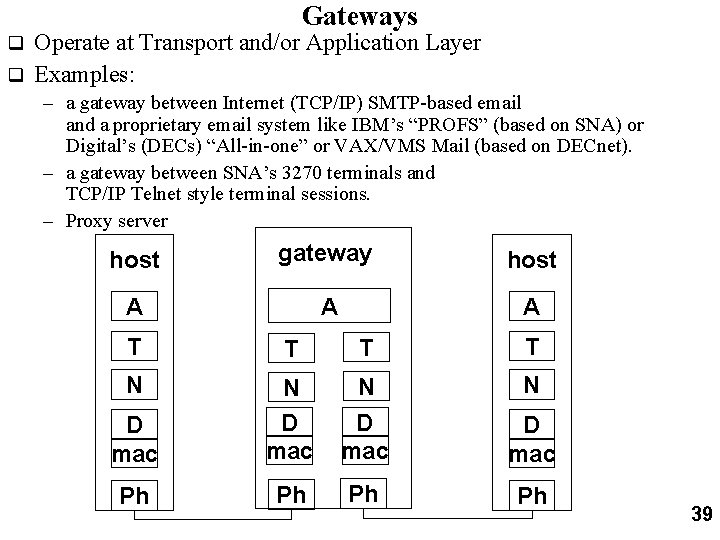
Gateways Operate at Transport and/or Application Layer q Examples: q – a gateway between Internet (TCP/IP) SMTP-based email and a proprietary email system like IBM’s “PROFS” (based on SNA) or Digital’s (DECs) “All-in-one” or VAX/VMS Mail (based on DECnet). – a gateway between SNA’s 3270 terminals and TCP/IP Telnet style terminal sessions. – Proxy server host gateway host A A A T T N N D mac Ph Ph 39
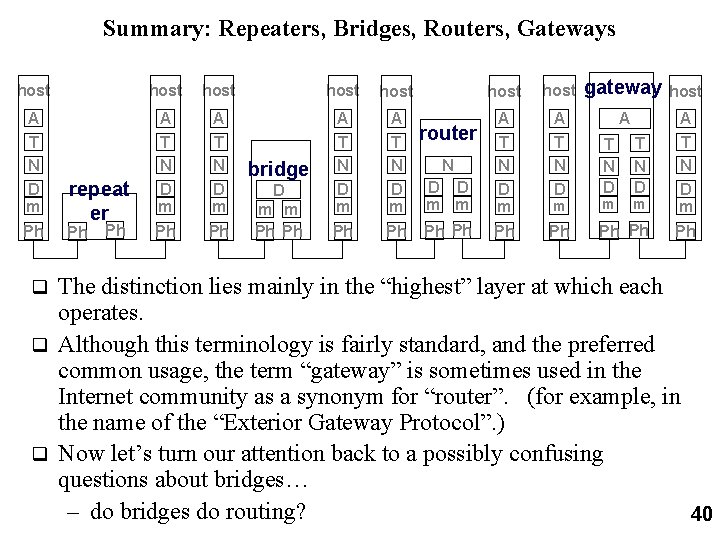
Summary: Repeaters, Bridges, Routers, Gateways host host gateway host A T N D m A T N D m A T N D A D D m m A T N D m Ph Ph repeat er Ph Ph bridge D m m Ph Ph router N T N D m m m A T N D m Ph Ph The distinction lies mainly in the “highest” layer at which each operates. q Although this terminology is fairly standard, and the preferred common usage, the term “gateway” is sometimes used in the Internet community as a synonym for “router”. (for example, in the name of the “Exterior Gateway Protocol”. ) q Now let’s turn our attention back to a possibly confusing questions about bridges… – do bridges do routing? 40 q
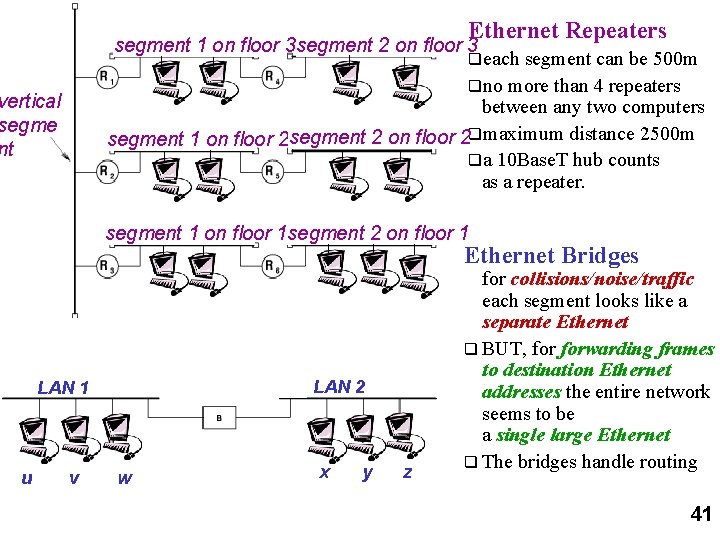
Ethernet Repeaters segment 1 on floor 3 segment 2 on floor 3 qeach segment can be 500 m qno more than 4 repeaters between any two computers segment 1 on floor 2 segment 2 on floor 2 qmaximum distance 2500 m qa 10 Base. T hub counts as a repeater. vertical segme nt segment 1 on floor 1 segment 2 on floor 1 Ethernet Bridges LAN 2 LAN 1 u v w x y z for collisions/noise/traffic each segment looks like a separate Ethernet q BUT, forwarding frames to destination Ethernet addresses the entire network seems to be a single large Ethernet q The bridges handle routing 41
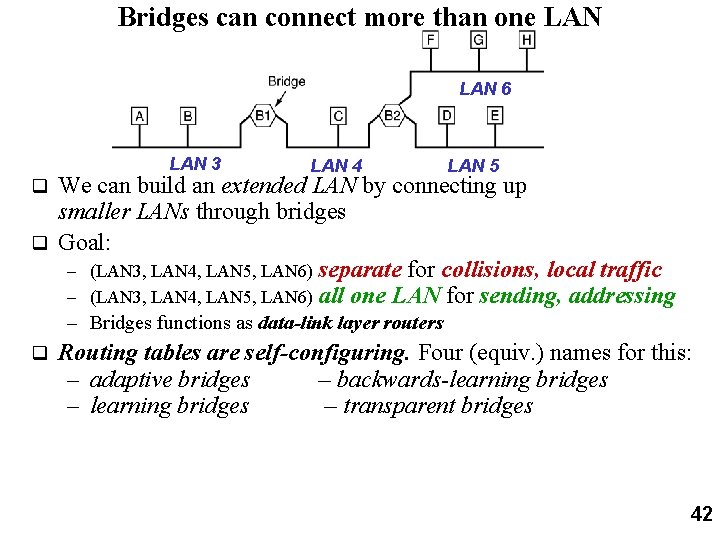
Bridges can connect more than one LAN 6 LAN 3 LAN 4 LAN 5 We can build an extended LAN by connecting up smaller LANs through bridges q Goal: – (LAN 3, LAN 4, LAN 5, LAN 6) separate for collisions, local traffic – (LAN 3, LAN 4, LAN 5, LAN 6) all one LAN for sending, addressing q – Bridges functions as data-link layer routers q Routing tables are self-configuring. Four (equiv. ) names for this: – adaptive bridges – backwards-learning bridges – transparent bridges 42
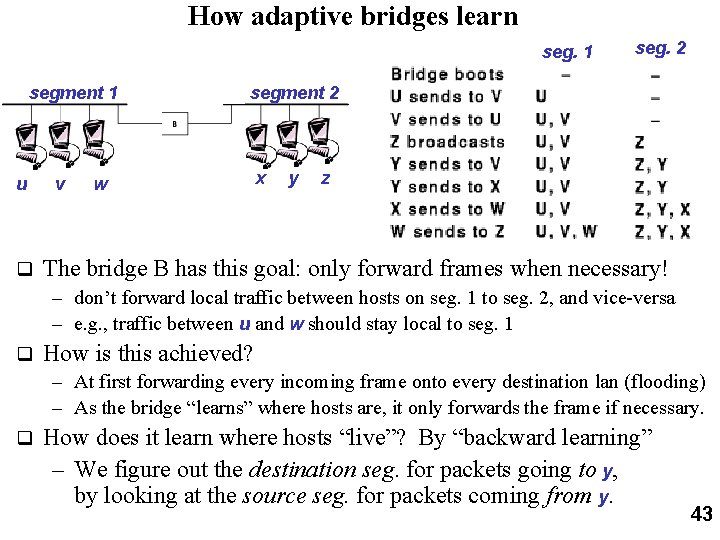
How adaptive bridges learn seg. 1 segment 1 u q v seg. 2 segment 2 w x y z The bridge B has this goal: only forward frames when necessary! – don’t forward local traffic between hosts on seg. 1 to seg. 2, and vice-versa – e. g. , traffic between u and w should stay local to seg. 1 q How is this achieved? – At first forwarding every incoming frame onto every destination lan (flooding) – As the bridge “learns” where hosts are, it only forwards the frame if necessary. q How does it learn where hosts “live”? By “backward learning” – We figure out the destination seg. for packets going to y, by looking at the source seg. for packets coming from y. 43
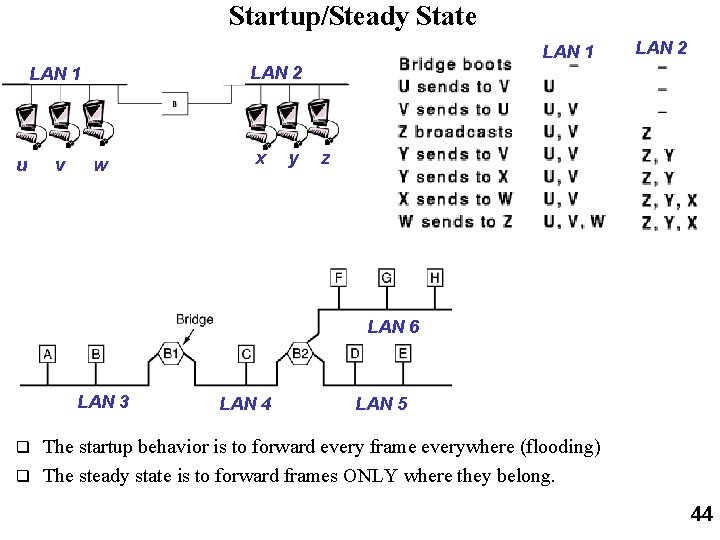
Startup/Steady State LAN 1 LAN 2 LAN 1 u v LAN 2 w x y z LAN 6 LAN 3 LAN 4 LAN 5 The startup behavior is to forward every frame everywhere (flooding) q The steady state is to forward frames ONLY where they belong. q 44
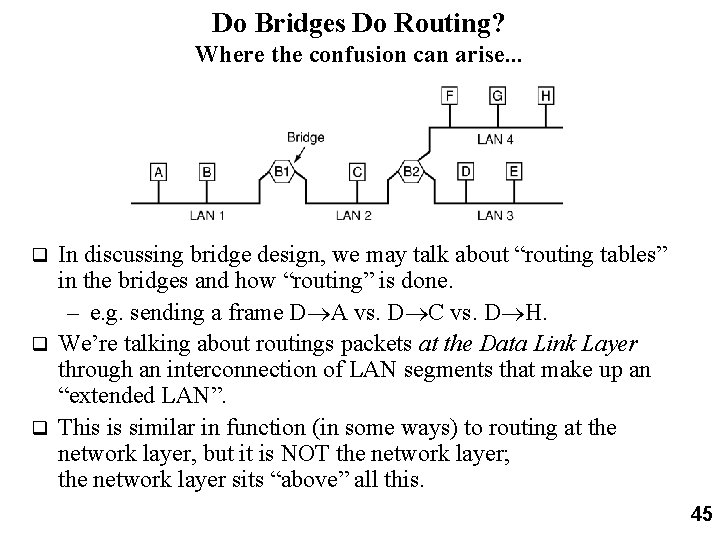
Do Bridges Do Routing? Where the confusion can arise. . . In discussing bridge design, we may talk about “routing tables” in the bridges and how “routing” is done. – e. g. sending a frame D A vs. D C vs. D H. q We’re talking about routings packets at the Data Link Layer through an interconnection of LAN segments that make up an “extended LAN”. q This is similar in function (in some ways) to routing at the network layer, but it is NOT the network layer; the network layer sits “above” all this. q 45
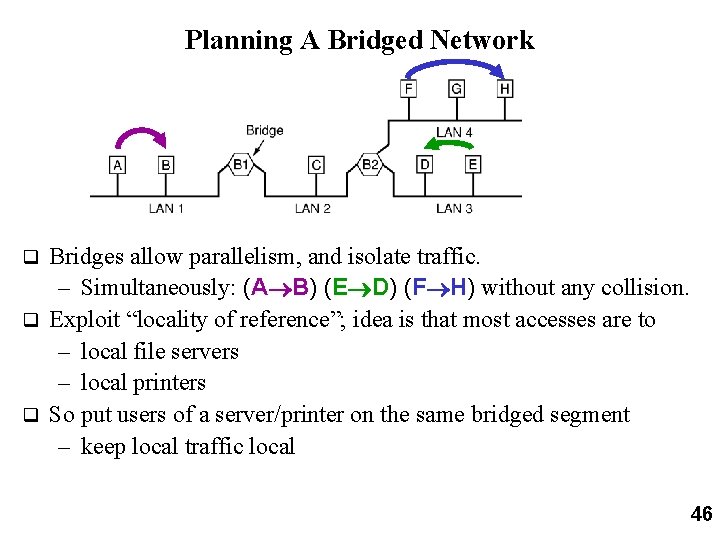
Planning A Bridged Network Bridges allow parallelism, and isolate traffic. – Simultaneously: (A B) (E D) (F H) without any collision. q Exploit “locality of reference”; idea is that most accesses are to – local file servers – local printers q So put users of a server/printer on the same bridged segment – keep local traffic local q 46
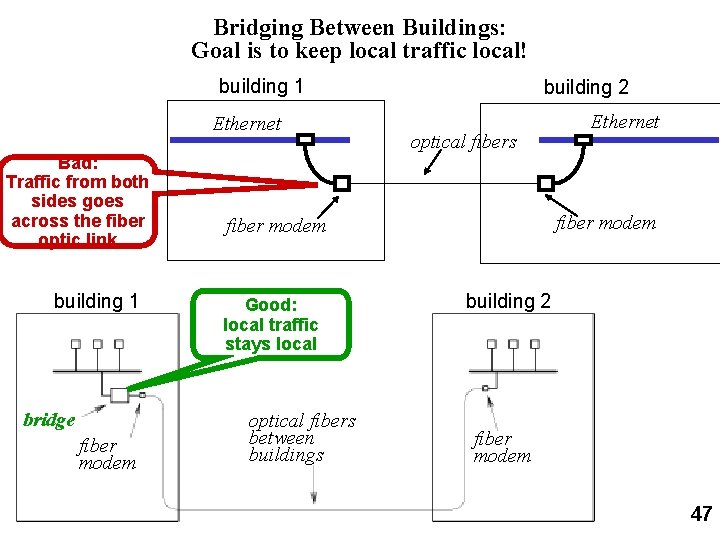
Bridging Between Buildings: Goal is to keep local traffic local! building 1 Ethernet Bad: Traffic from both sides goes across the fiber optic link building 1 bridge fiber modem building 2 optical fibers fiber modem Good: local traffic stays local optical fibers between buildings Ethernet building 2 fiber modem 47
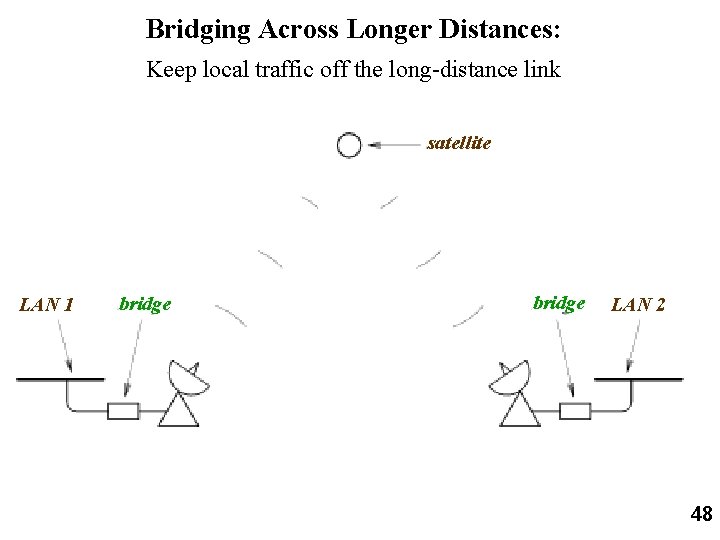
Bridging Across Longer Distances: Keep local traffic off the long-distance link satellite LAN 1 bridge LAN 2 48
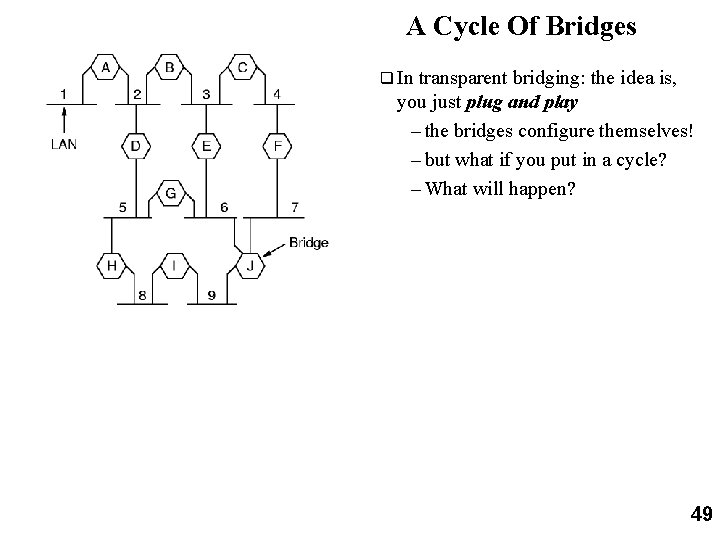
A Cycle Of Bridges q In transparent bridging: the idea is, you just plug and play – the bridges configure themselves! – but what if you put in a cycle? – What will happen? 49
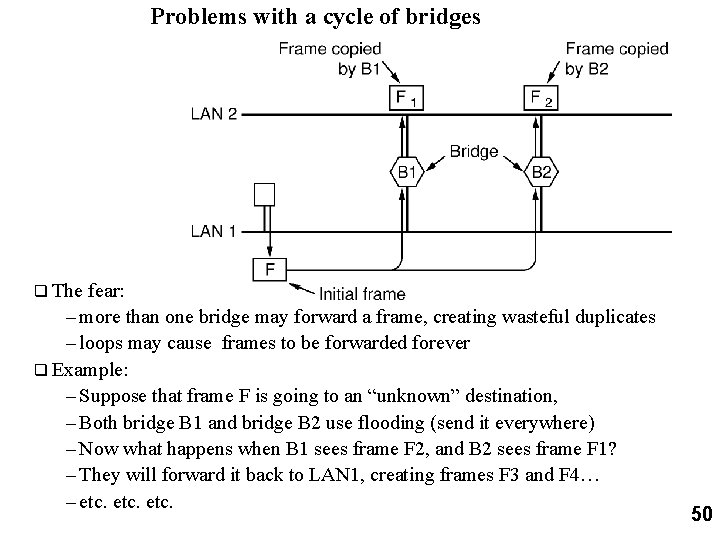
Problems with a cycle of bridges q The fear: – more than one bridge may forward a frame, creating wasteful duplicates – loops may cause frames to be forwarded forever q Example: – Suppose that frame F is going to an “unknown” destination, – Both bridge B 1 and bridge B 2 use flooding (send it everywhere) – Now what happens when B 1 sees frame F 2, and B 2 sees frame F 1? – They will forward it back to LAN 1, creating frames F 3 and F 4… – etc. 50
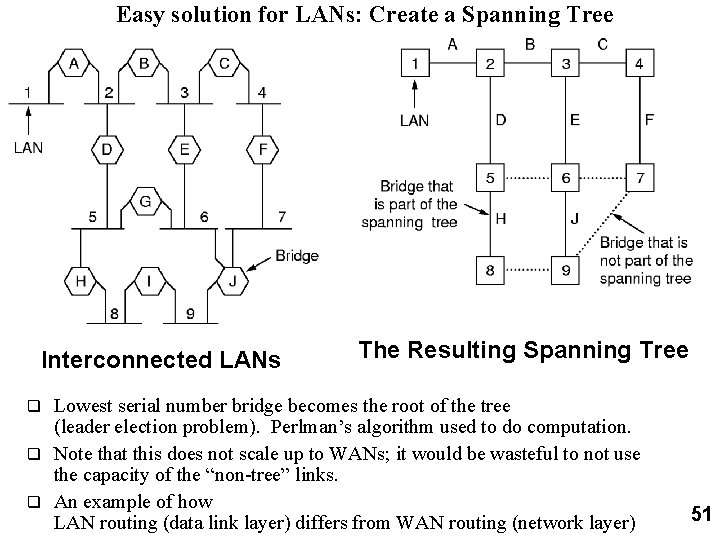
Easy solution for LANs: Create a Spanning Tree Interconnected LANs The Resulting Spanning Tree Lowest serial number bridge becomes the root of the tree (leader election problem). Perlman’s algorithm used to do computation. q Note that this does not scale up to WANs; it would be wasteful to not use the capacity of the “non-tree” links. q An example of how LAN routing (data link layer) differs from WAN routing (network layer) q 51
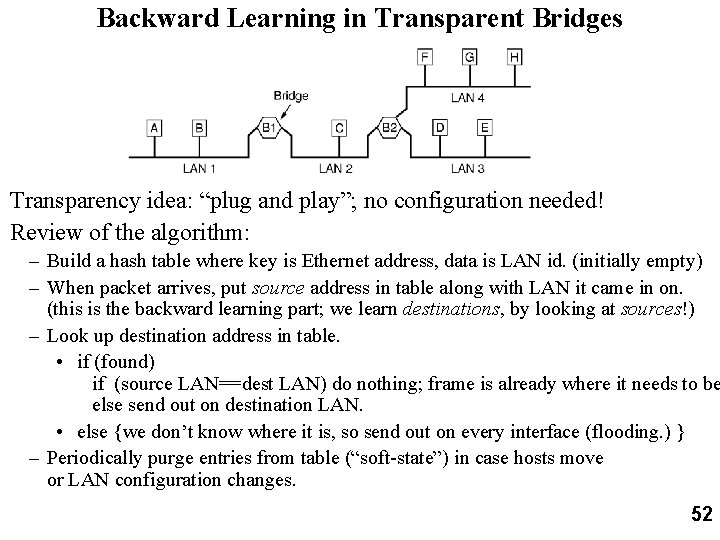
Backward Learning in Transparent Bridges Transparency idea: “plug and play”; no configuration needed! Review of the algorithm: – Build a hash table where key is Ethernet address, data is LAN id. (initially empty) – When packet arrives, put source address in table along with LAN it came in on. (this is the backward learning part; we learn destinations, by looking at sources!) – Look up destination address in table. • if (found) if (source LAN==dest LAN) do nothing; frame is already where it needs to be else send out on destination LAN. • else {we don’t know where it is, so send out on every interface (flooding. ) } – Periodically purge entries from table (“soft-state”) in case hosts move or LAN configuration changes. 52
Source Routing Bridges (used in IBM Token Ring, 802. 5) Source chooses the route the host. q Route chosen by using “discovery packets” – broadcast packet from x saying “what is route to y”? – bridges record route taken; use info to get reply back to x. – x receives a reply for every possible route to y, and picks the best one. q Advantage: can use the bandwidth more effectively. Transparent bridges only use the spanning tree. q Disadvantages: – Not transparent. (not “plug and play”). Administrator must configure bridge addresses to be unique among all bridges attached to a particular LAN – Frame explosion problem; # discovery frames can grow exponentially. (only linear growth with flooding in spanning tree bridges. ) q 53
- Slides: 53