MAC Layer Security 1 Outline MAC Basics MAC
MAC Layer Security 1
Outline § MAC Basics § MAC Layer Security in Wired Networks § MAC Layer Security in Wireless Networks 2
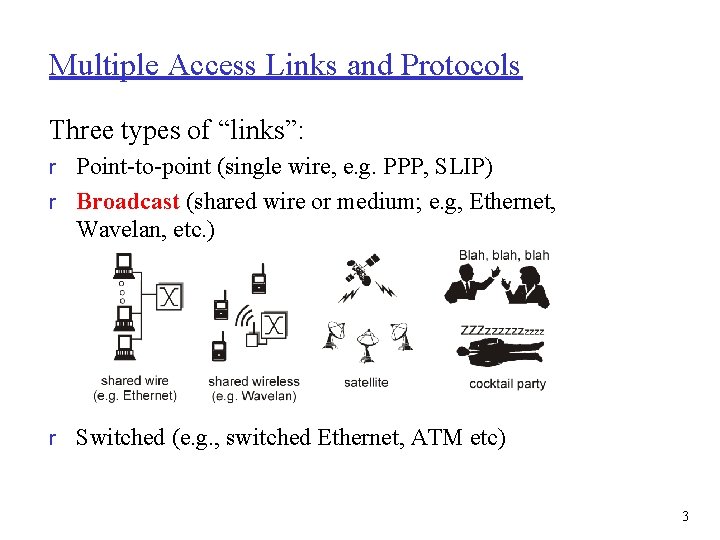
Multiple Access Links and Protocols Three types of “links”: r Point-to-point (single wire, e. g. PPP, SLIP) r Broadcast (shared wire or medium; e. g, Ethernet, Wavelan, etc. ) r Switched (e. g. , switched Ethernet, ATM etc) 3
Multiple Access protocols r Single shared communication channel r Two or more simultaneous transmissions by nodes: interference m Only one node can send successfully at a time r Multiple access protocol: m Distributed algorithm that determines how stations share channel, i. e. , determine when station can transmit m Communication about channel sharing must use channel itself! m What to look for in multiple access protocols: • Synchronous or asynchronous • Information needed about other stations • Robustness (e. g. , to channel errors) • Performance 4
MAC Protocols: a taxonomy Three broad classes: r Channel Partitioning m TDMA: time division multiple access FDMA: frequency division multiple access m CDMA (Code Division Multiple Access) Read! m r Random Access Allow collisions m “Recover” from collisions r “Taking turns” m m Tightly coordinate shared access to avoid collisions Goal: efficient, fair, simple, decentralized 5
Random Access protocols r When node has packet to send m Transmit at full channel data rate R. m No a priori coordination among nodes r Two or more transmitting nodes -> “collision”, r Random access MAC protocol specifies: m How to detect collisions m How to recover from collisions (e. g. , via delayed retransmissions) r Examples of random access MAC protocols: m Slotted ALOHA and ALOHA m CSMA and CSMA/CD 6
CSMA: Carrier Sense Multiple Access) CSMA: listen before transmit: r If channel sensed idle: transmit entire pkt r If channel sensed busy, defer transmission m Persistent CSMA: retry immediately with probability p when channel becomes idle (may cause instability) m Non-persistent CSMA: retry after random interval r Human analogy: don’t interrupt others! 7
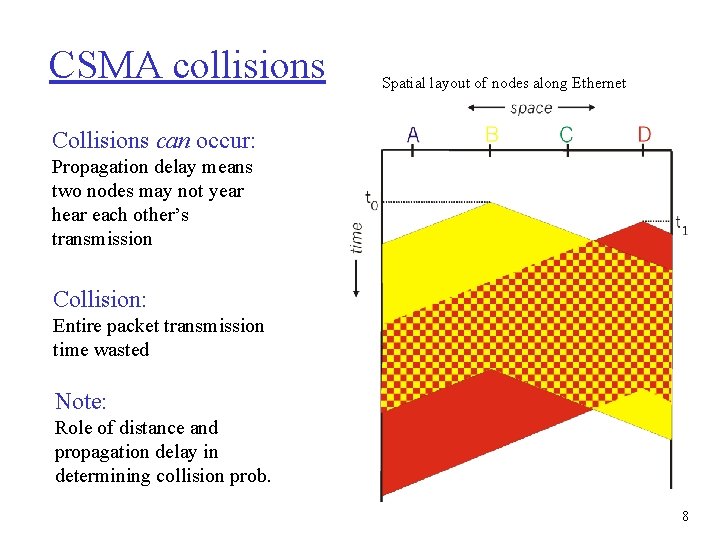
CSMA collisions Spatial layout of nodes along Ethernet Collisions can occur: Propagation delay means two nodes may not year hear each other’s transmission Collision: Entire packet transmission time wasted Note: Role of distance and propagation delay in determining collision prob. 8
CSMA/CD (Collision Detection) CSMA/CD: Carrier sensing, deferral as in CSMA Collisions detected within short time m Colliding transmissions aborted, reducing channel wastage m Persistent or non-persistent retransmission m r Collision detection: m Easy in wired LANs: measure signal strengths, compare transmitted, received signals m Difficult in wireless LANs: receiver shut off while transmitting r Human analogy: Polite conversationalist 9
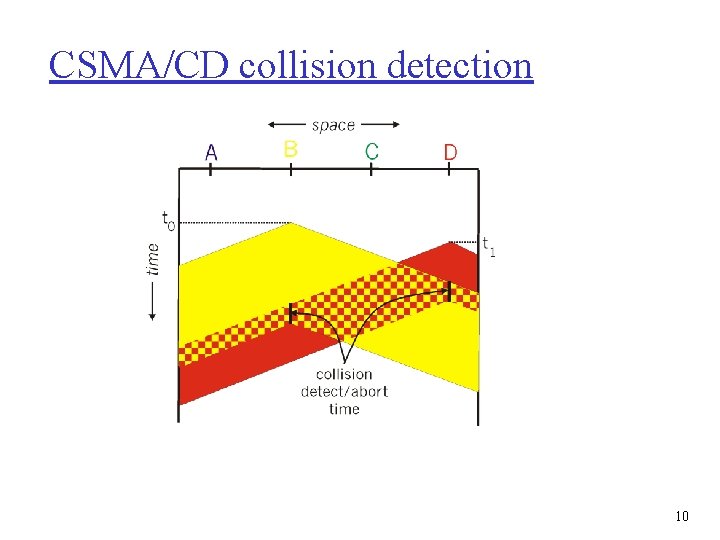
CSMA/CD collision detection 10
“Taking Turns” MAC protocols Channel partitioning MAC protocols: m Share channel efficiently at high load m Inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols m Efficient at low load: single node can fully utilize channel m High load: collision overhead “Taking turns” protocols Look for best of both worlds! 11
“Taking Turns” MAC protocols Polling: r Master node “invites” slave nodes to transmit in turn r Request to Send, Clear to Send msgs r Concerns: m m m Polling overhead Latency Single point of failure (master) Token passing: r Control token passed from one node to next sequentially. r Token message r Toncerns: m m m token overhead latency single point of failure (token) 12
Summary of MAC protocols r What do you do with a shared media? m Channel Partitioning, by time, frequency or code • Time Division, Code Division, Frequency Division m Random partitioning (dynamic), • ALOHA, S-ALOHA, CSMA/CD • Carrier sensing: easy in some technologies (wire), hard in others (wireless) • CSMA/CD used in Ethernet m Taking Turns • Polling from a central cite, token passing 13
LAN Addresses and ARP 32 -bit IP address: r Network-layer address r Used to get datagram to destination network (recall IP network definition) LAN (or MAC or physical) address: r Used to get datagram from one interface to another physically-connected interface (same network) r 48 bit MAC address (for most LANs) burned in the adapter ROM 14
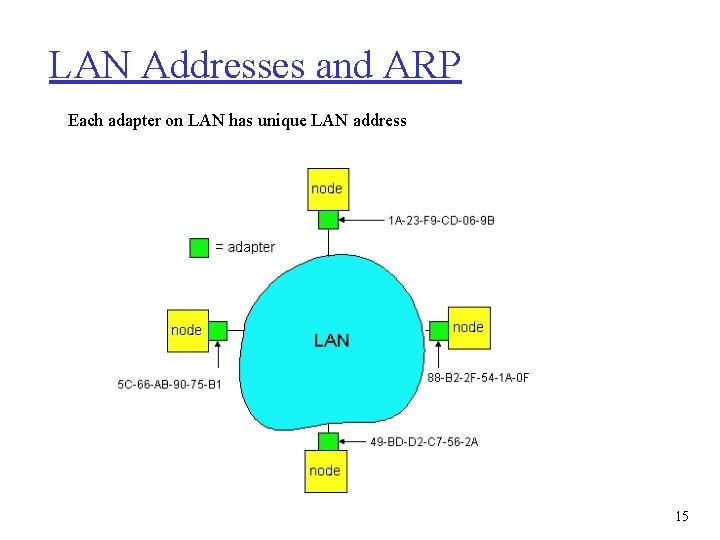
LAN Addresses and ARP Each adapter on LAN has unique LAN address 15
LAN Address (more) r MAC address allocation administered by IEEE r Manufacturer buys portion of MAC address space (to assure uniqueness) r Analogy: (a) MAC address: like Social Security Number (b) IP address: like postal address r MAC flat address � portability m Can move LAN card from one LAN to another r IP hierarchical address NOT portable m Depends on network to which one attaches 16
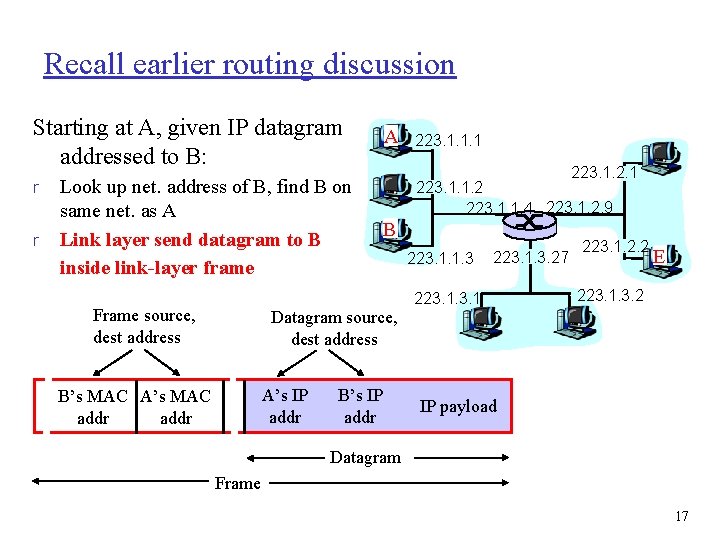
Recall earlier routing discussion Starting at A, given IP datagram addressed to B: r r Look up net. address of B, find B on same net. as A Link layer send datagram to B inside link-layer frame Frame source, dest address A 223. 1. 2. 1 223. 1. 1. 2 223. 1. 1. 4 223. 1. 2. 9 B Datagram source, dest address A’s IP addr B’s MAC A’s MAC addr 223. 1. 1. 1 B’s IP addr 223. 1. 1. 3 223. 1. 3. 27 223. 1. 2. 2 E 223. 1. 3. 2 IP payload Datagram Frame 17
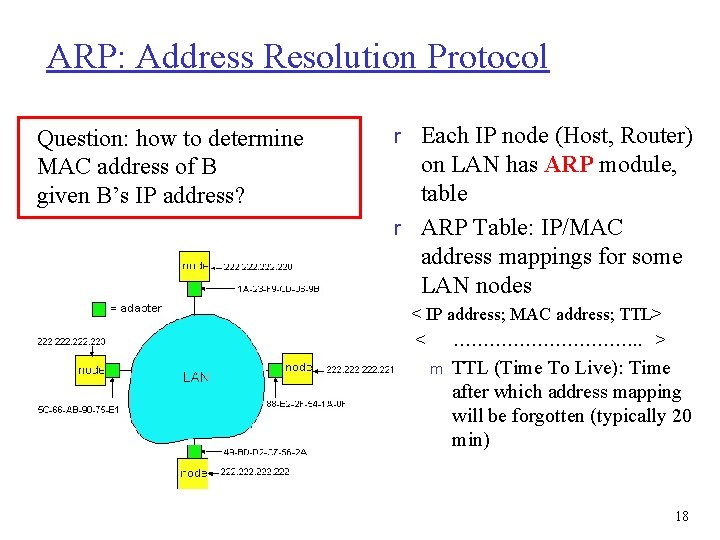
ARP: Address Resolution Protocol Question: how to determine MAC address of B given B’s IP address? r Each IP node (Host, Router) on LAN has ARP module, table r ARP Table: IP/MAC address mappings for some LAN nodes < IP address; MAC address; TTL> < ……………. . > m TTL (Time To Live): Time after which address mapping will be forgotten (typically 20 min) 18
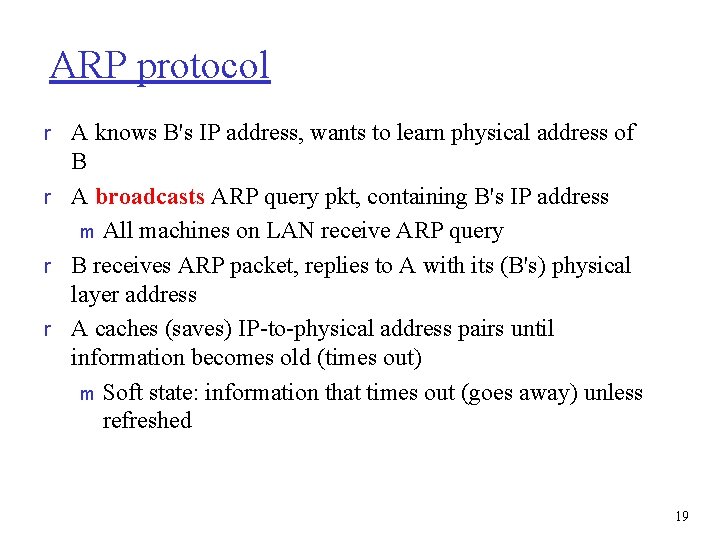
ARP protocol r A knows B's IP address, wants to learn physical address of B r A broadcasts ARP query pkt, containing B's IP address m All machines on LAN receive ARP query r B receives ARP packet, replies to A with its (B's) physical layer address r A caches (saves) IP-to-physical address pairs until information becomes old (times out) m Soft state: information that times out (goes away) unless refreshed 19
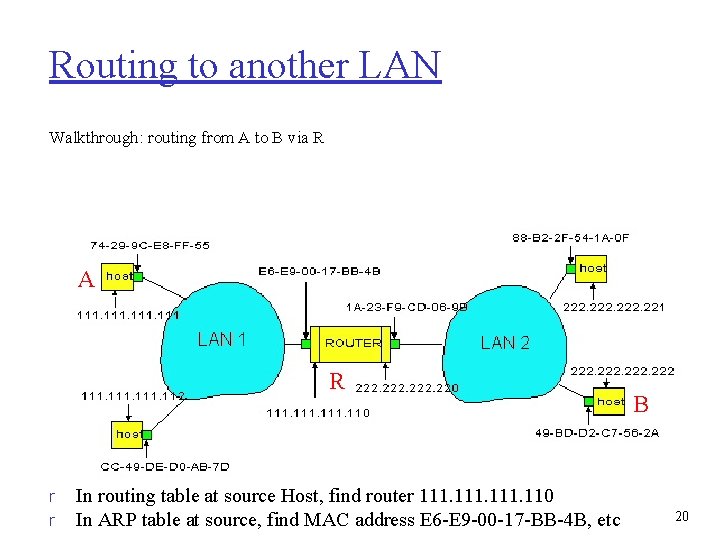
Routing to another LAN Walkthrough: routing from A to B via R A R r r In routing table at source Host, find router 111. 110 In ARP table at source, find MAC address E 6 -E 9 -00 -17 -BB-4 B, etc B 20
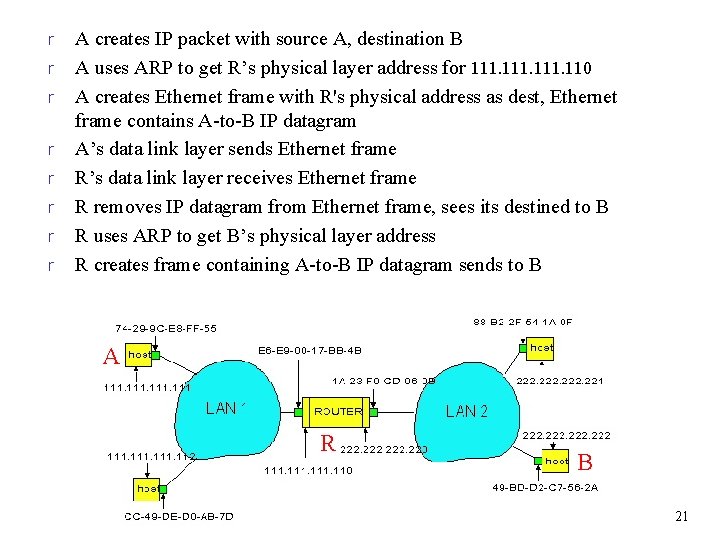
r r r r A creates IP packet with source A, destination B A uses ARP to get R’s physical layer address for 111. 110 A creates Ethernet frame with R's physical address as dest, Ethernet frame contains A-to-B IP datagram A’s data link layer sends Ethernet frame R’s data link layer receives Ethernet frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s physical layer address R creates frame containing A-to-B IP datagram sends to B A R B 21
Ethernet “Dominant” LAN technology: r Cheap: $20 for 100 Mbps! r First widely used LAN technology r Simpler, cheaper than token LANs and ATM r Kept up with speed race: 10, 1000 Mbps Metcalfe’s Ethernet sketch 22
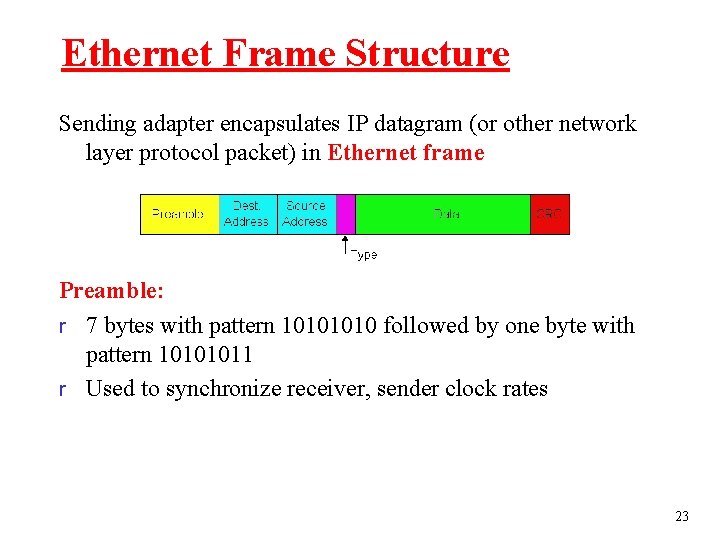
Ethernet Frame Structure Sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame Preamble: r 7 bytes with pattern 1010 followed by one byte with pattern 10101011 r Used to synchronize receiver, sender clock rates 23
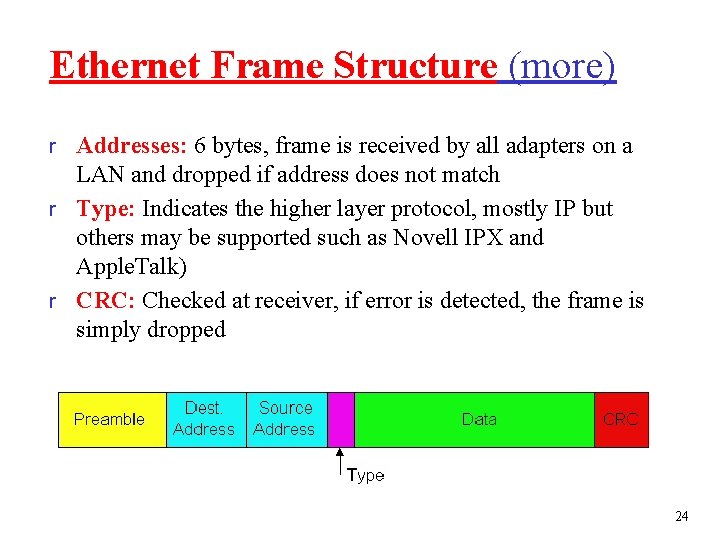
Ethernet Frame Structure (more) r Addresses: 6 bytes, frame is received by all adapters on a LAN and dropped if address does not match r Type: Indicates the higher layer protocol, mostly IP but others may be supported such as Novell IPX and Apple. Talk) r CRC: Checked at receiver, if error is detected, the frame is simply dropped 24
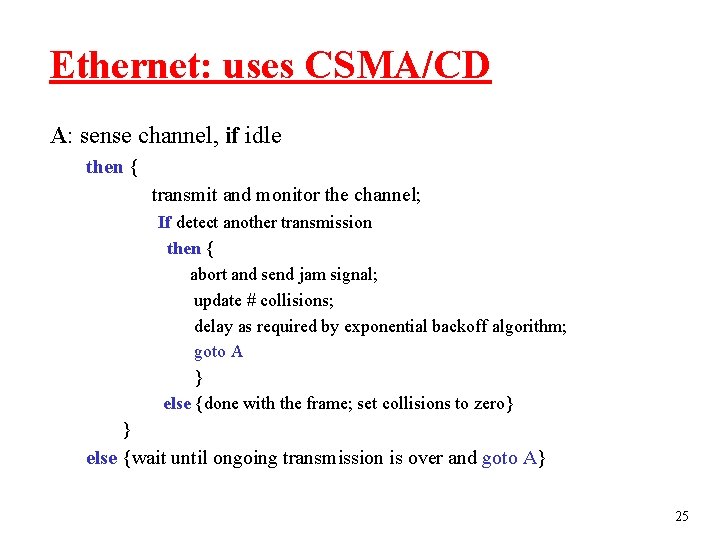
Ethernet: uses CSMA/CD A: sense channel, if idle then { transmit and monitor the channel; If detect another transmission then { abort and send jam signal; update # collisions; delay as required by exponential backoff algorithm; goto A } else {done with the frame; set collisions to zero} } else {wait until ongoing transmission is over and goto A} 25
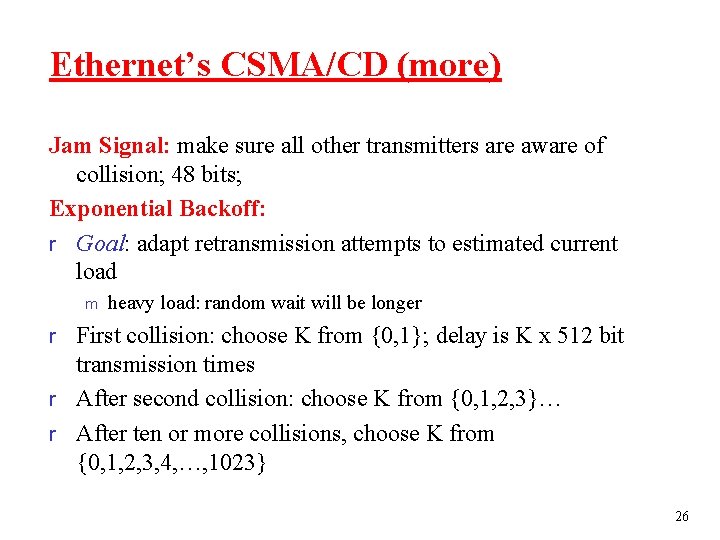
Ethernet’s CSMA/CD (more) Jam Signal: make sure all other transmitters are aware of collision; 48 bits; Exponential Backoff: r Goal: adapt retransmission attempts to estimated current load m heavy load: random wait will be longer r First collision: choose K from {0, 1}; delay is K x 512 bit transmission times r After second collision: choose K from {0, 1, 2, 3}… r After ten or more collisions, choose K from {0, 1, 2, 3, 4, …, 1023} 26
Outline § MAC Basics § MAC Layer Security in Wired Networks § MAC Layer Security in Wireless Networks 27
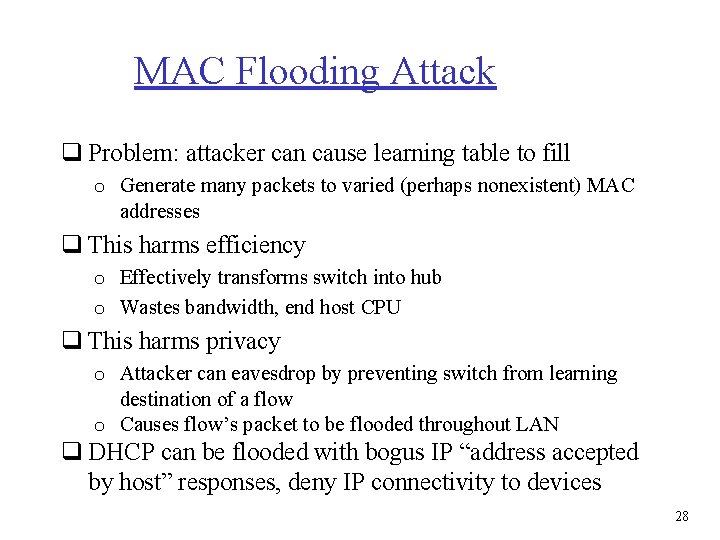
MAC Flooding Attack q Problem: attacker can cause learning table to fill o Generate many packets to varied (perhaps nonexistent) MAC addresses q This harms efficiency o Effectively transforms switch into hub o Wastes bandwidth, end host CPU q This harms privacy o Attacker can eavesdrop by preventing switch from learning destination of a flow o Causes flow’s packet to be flooded throughout LAN q DHCP can be flooded with bogus IP “address accepted by host” responses, deny IP connectivity to devices 28
MAC Spoofing Attack q Host pretends to own the MAC address of another host o Easy to do: most Ethernet adapters allow their address to be modified o Powerful: can immediately cause complete Do. S to spoofed host – All learning table entries switch to point to the attacker – All traffic redirected to attacker – Can enable attacker to evade ACLs set based on MAC information 29
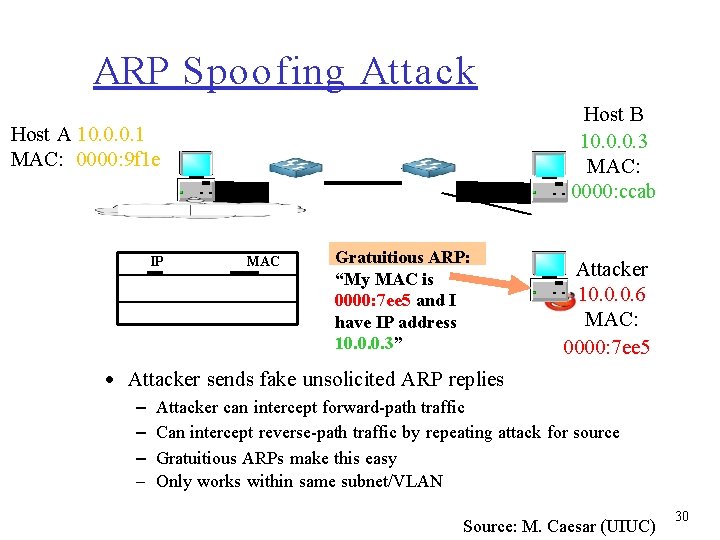
ARP Spoofing Attack Host B 10. 0. 0. 3 MAC: 0000: ccab Host A 10. 0. 0. 1 MAC: 0000: 9 f 1 e IP 10. 0. 0. 3 MAC 0000: 7 ee 5 Gratuitious ARP: “My MAC is 0000: 7 ee 5 and I have IP address 10. 0. 0. 3” Attacker 10. 0. 0. 6 MAC: 0000: 7 ee 5 • Attacker sends fake unsolicited ARP replies – – Attacker can intercept forward-path traffic Can intercept reverse-path traffic by repeating attack for source Gratuitious ARPs make this easy Only works within same subnet/VLAN Source: M. Caesar (UIUC) 30
Counte rme asure s to ARP Spoofing q Ignore Gratuitious ARP o Problems: gratuitious ARP is useful, doesn’t completely solve the problem q Dynamic ARP Inspection (DAI) o Switches record <IP, MAC> mappings learned from DHCP messages, drop all mismatching ARP replies q Intrusion detection systems (IDS) o Monitor all <IP, MAC> mappings, signal alarms q Can also partition Ethernet networks into “virtual” LANs that are disjoint from each other Source: M. Caesar (UIUC) 31
Outline § MAC Basics § MAC Layer Security in Wired Networks § MAC Layer Security in Wireless Networks 32
WEP Design Goals r Symmetric key crypto m Confidentiality m End host authorization m Data integrity r Self-synchronizing: each packet separately encrypted m Given encrypted packet and key, can decrypt; can continue to decrypt packets when preceding packet was lost (unlike Cipher Block Chaining (CBC) in block ciphers) r Efficient m Implementable in hardware or software 33
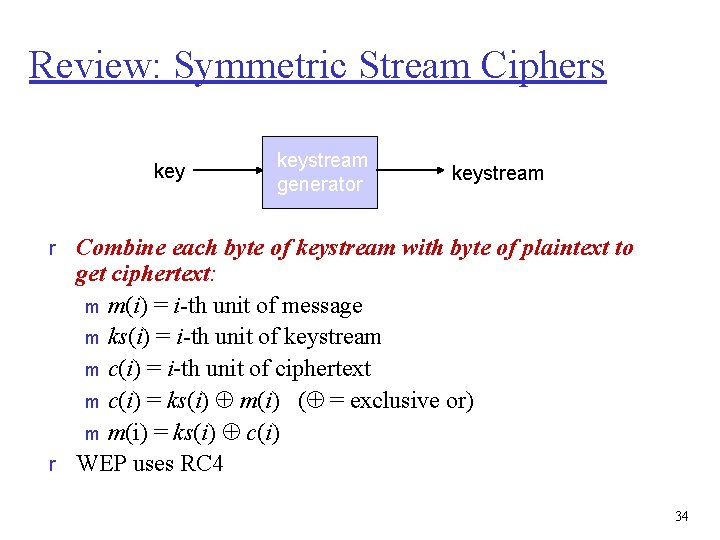
Review: Symmetric Stream Ciphers keystream generator keystream r Combine each byte of keystream with byte of plaintext to get ciphertext: m m(i) = i-th unit of message m ks(i) = i-th unit of keystream m c(i) = i-th unit of ciphertext m c(i) = ks(i) m(i) ( = exclusive or) m m(i) = ks(i) c(i) r WEP uses RC 4 34
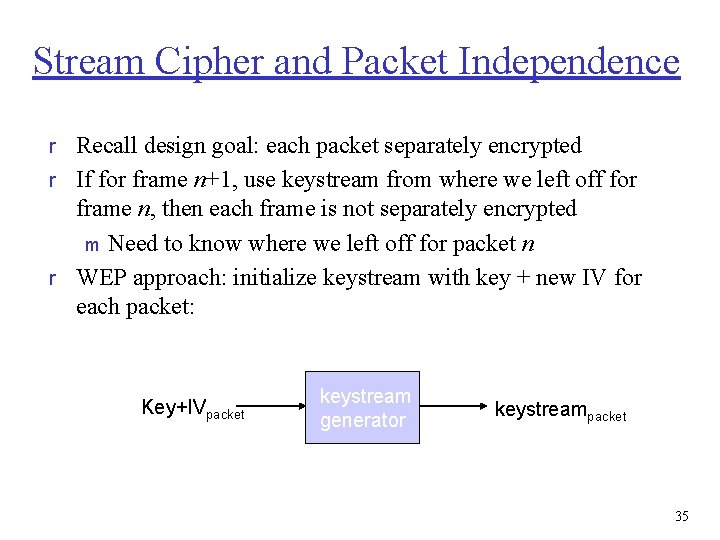
Stream Cipher and Packet Independence r Recall design goal: each packet separately encrypted r If for frame n+1, use keystream from where we left off for frame n, then each frame is not separately encrypted m Need to know where we left off for packet n r WEP approach: initialize keystream with key + new IV for each packet: Key+IVpacket keystream generator keystreampacket 35
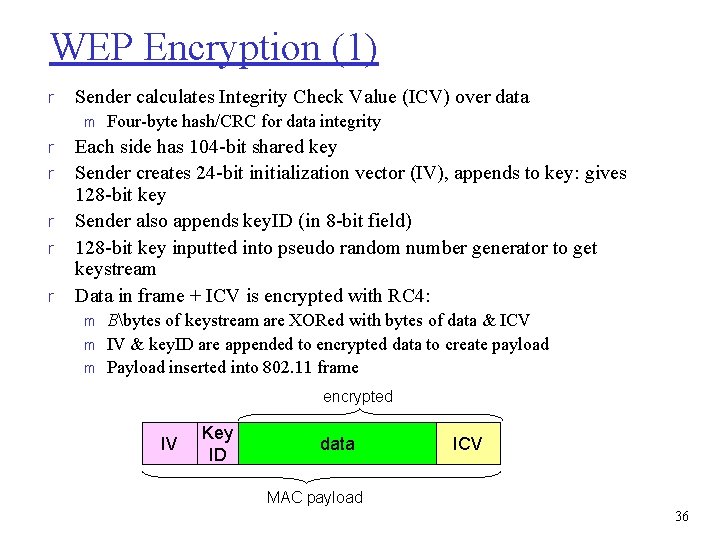
WEP Encryption (1) r Sender calculates Integrity Check Value (ICV) over data m r r r Four-byte hash/CRC for data integrity Each side has 104 -bit shared key Sender creates 24 -bit initialization vector (IV), appends to key: gives 128 -bit key Sender also appends key. ID (in 8 -bit field) 128 -bit key inputted into pseudo random number generator to get keystream Data in frame + ICV is encrypted with RC 4: m m m Bbytes of keystream are XORed with bytes of data & ICV IV & key. ID are appended to encrypted data to create payload Payload inserted into 802. 11 frame encrypted IV Key ID data ICV MAC payload 36
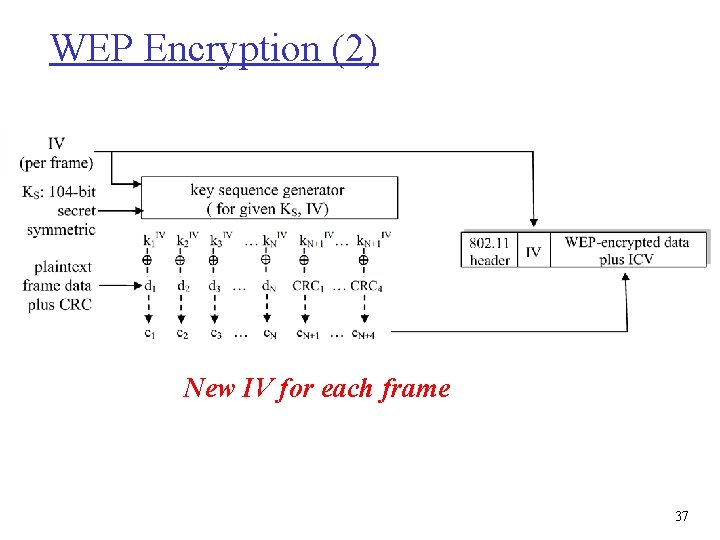
WEP Encryption (2) New IV for each frame 37
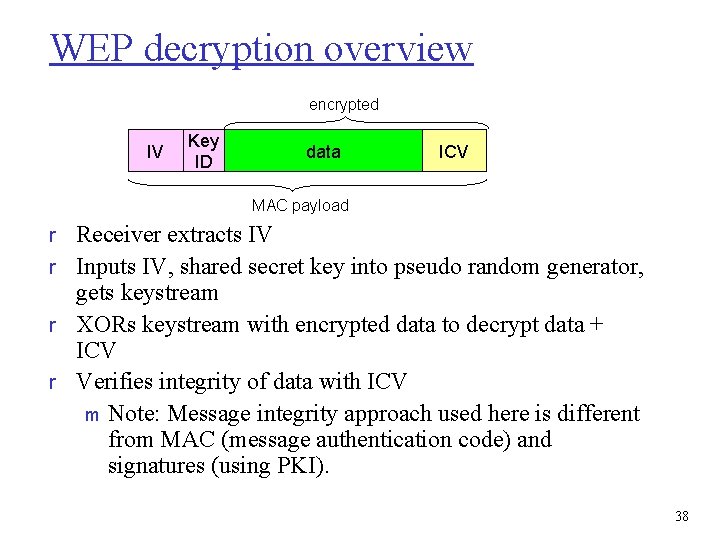
WEP decryption overview encrypted IV Key ID data ICV MAC payload r Receiver extracts IV r Inputs IV, shared secret key into pseudo random generator, gets keystream r XORs keystream with encrypted data to decrypt data + ICV r Verifies integrity of data with ICV m Note: Message integrity approach used here is different from MAC (message authentication code) and signatures (using PKI). 38
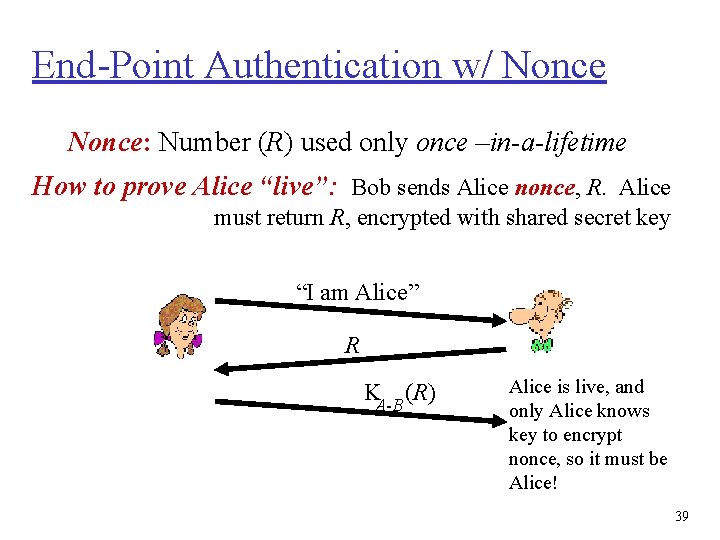
End-Point Authentication w/ Nonce: Number (R) used only once –in-a-lifetime How to prove Alice “live”: Bob sends Alice nonce, R. Alice must return R, encrypted with shared secret key “I am Alice” R KA-B (R) Alice is live, and only Alice knows key to encrypt nonce, so it must be Alice! 39
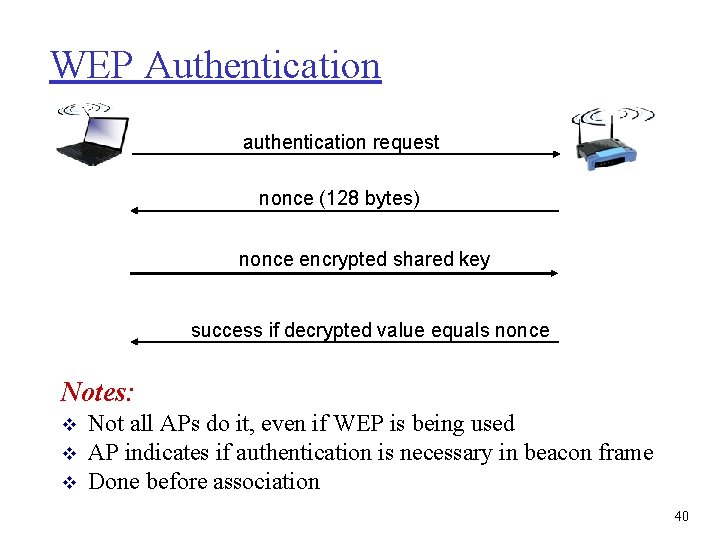
WEP Authentication authentication request nonce (128 bytes) nonce encrypted shared key success if decrypted value equals nonce Notes: v v v Not all APs do it, even if WEP is being used AP indicates if authentication is necessary in beacon frame Done before association 40
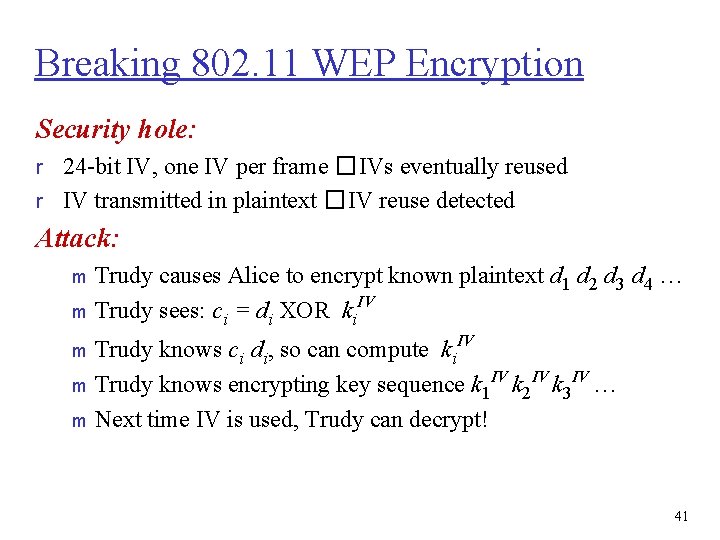
Breaking 802. 11 WEP Encryption Security hole: r 24 -bit IV, one IV per frame � IVs eventually reused r IV transmitted in plaintext � IV reuse detected Attack: Trudy causes Alice to encrypt known plaintext d 1 d 2 d 3 d 4 … IV m Trudy sees: ci = di XOR ki m Trudy knows ci di, so can compute ki. IV IV m Trudy knows encrypting key sequence k 1 k 2 k 3 … m Next time IV is used, Trudy can decrypt! m 41
802. 11 i: Improved Security r Numerous (stronger) forms of encryption possible r Provides key distribution r Uses authentication server separate from access point 42
WPA: Wi. Fi Protected Access r “Snapshot of 802. 11 i” developed Oct. 2002 to fix WEP flaws r Short-term solution: patch WEP using same hardware Temporal Key Integrity Protocol (TKIP) generates perpacket keys m Keys have short lifetime; continuously “refreshed” m TKIP includes Message Authentication Code for data integrity m 43
WPA 2: A Long-Term Solution r WPA 2 provides confidentiality, data integrity, protection against replay attacks Uses AES in counter mode with cipher block chaining (CBC) and message authentication code (MAC) with a different key m This is the Counter mode/CBC-MAC Protocol (CCMP) m r Both WPA and WPA 2 use 802. 11 i authentication mechanisms, described next 44
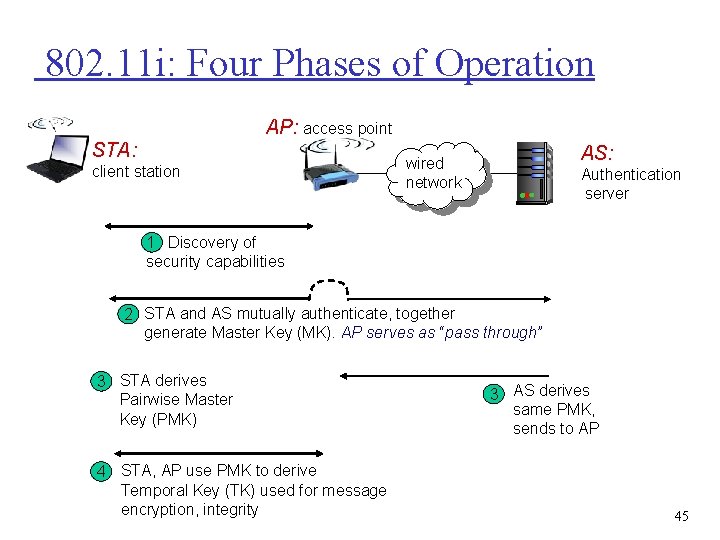
802. 11 i: Four Phases of Operation AP: access point STA: client station AS: wired network Authentication server 1 Discovery of security capabilities 2 STA and AS mutually authenticate, together generate Master Key (MK). AP serves as “pass through” 3 STA derives Pairwise Master Key (PMK) 4 STA, AP use PMK to derive Temporal Key (TK) used for message encryption, integrity 3 AS derives same PMK, sends to AP 45
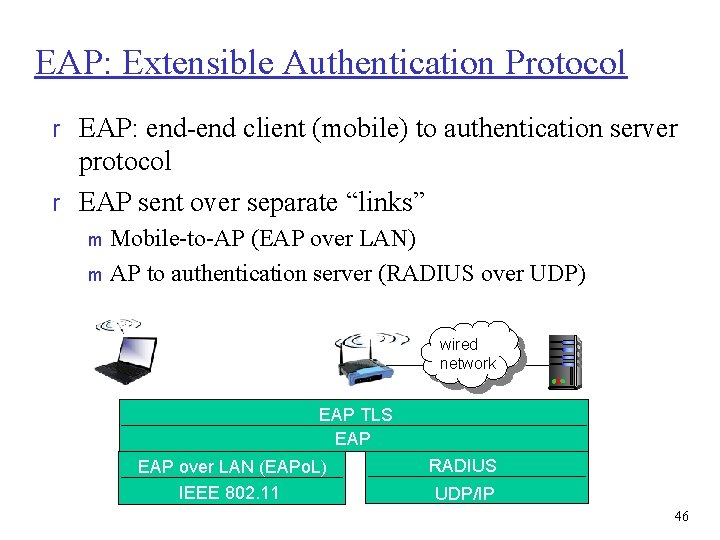
EAP: Extensible Authentication Protocol r EAP: end-end client (mobile) to authentication server protocol r EAP sent over separate “links” Mobile-to-AP (EAP over LAN) m AP to authentication server (RADIUS over UDP) m wired network EAP TLS EAP over LAN (EAPo. L) IEEE 802. 11 RADIUS UDP/IP 46
Simple Messages in Networking Systems r The messages that are short, unencrypted and used for controlling r Examples SYN message in TCP m Keep alive message in BGP m RTS/CTS/null data frames in 802. 11 WLANs m 47
Null Data Frames in 802. 11 WLANs r A special type of data frame that contains no data m Widely used for power management, channel scanning and association keeping alive r Security vulnerabilities of null data frames in 802. 11 WLANs Functionality based Denial-of-Service attack m Implementation based fingerprinting attack m 48
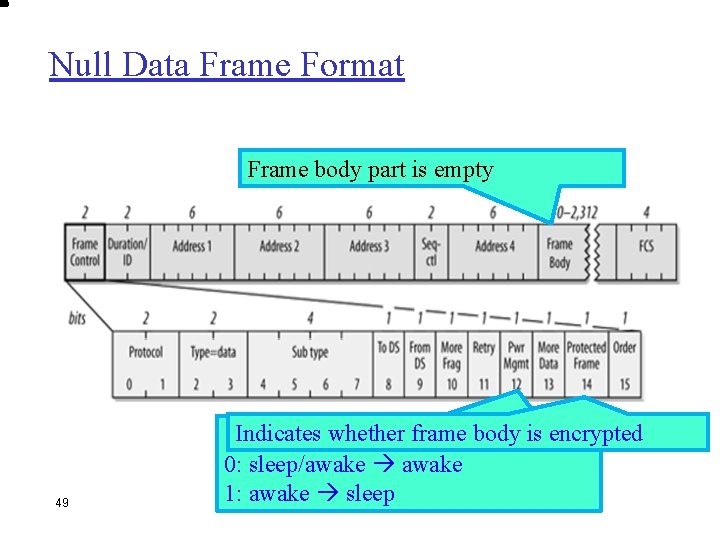
Null Data Frame Format Frame body part is empty 49 Indicates whether frame body is encrypted 0: sleep/awake 1: awake sleep
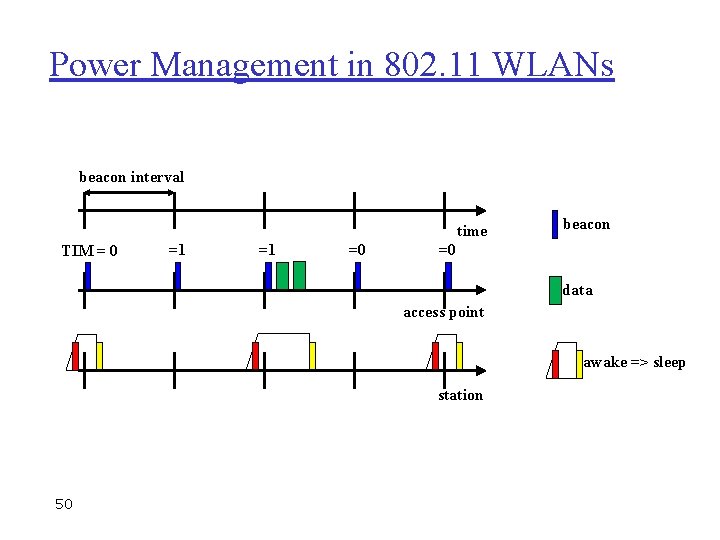
Power Management in 802. 11 WLANs beacon interval time TIM = 0 =1 =1 =0 beacon =0 data access point awake => sleep station 50
Security Vulnerability r The attacker can spoof the identity of a sleeping station, and steal its buffered data frames r Null data frame is short m Allows efficient fake frame generation r Null data frame is unencrypted m Allows fake frame generation 51
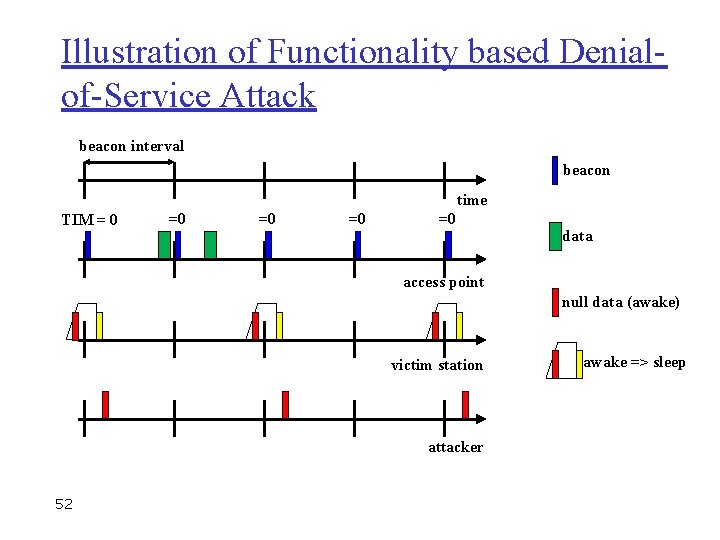
Illustration of Functionality based Denialof-Service Attack beacon interval beacon time TIM = 0 =0 =0 data access point null data (awake) victim station attacker 52 awake => sleep
Salient Features of the Attack r Easy to implement m Short frame without encryption r Hard to detect in real time m MAC address and sequence number are changeable r Little communication overhead m Not require frame flooding 53
802. 11 WLAN Issues (1) r No protection in open-access WLANs r Consequences: m Passive eavesdropping m Traffic analysis m Message injection m Masquerading m Malicious AP m Session hijacking m Man-in-the-middle m Denial-of-service m Etc. 54
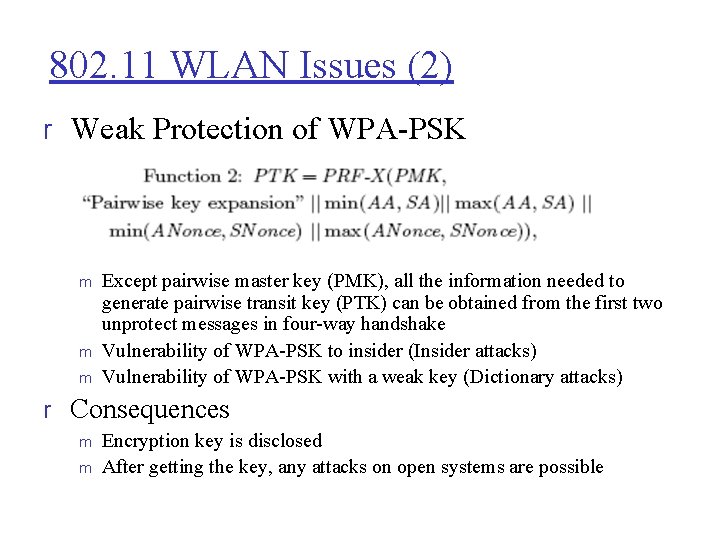
802. 11 WLAN Issues (2) r Weak Protection of WPA-PSK m m m Except pairwise master key (PMK), all the information needed to generate pairwise transit key (PTK) can be obtained from the first two unprotect messages in four-way handshake Vulnerability of WPA-PSK to insider (Insider attacks) Vulnerability of WPA-PSK with a weak key (Dictionary attacks) r Consequences m m Encryption key is disclosed After getting the key, any attacks on open systems are possible
Null Data Frame Authentication r Basic Idea m Encryption of link layer frames needs an encryption key m How to set up this key? r Replace “open system authentication” (OSA ) algorithm with “dummy authentication keyestablishment” algorithm to set up a session key r Why is the algorithm called dummy authentication? m m It occupies the position of an authentication algorithm in 802. 11 medium access control protocols It does not perform real authentication. It only sets up a cryptographic key
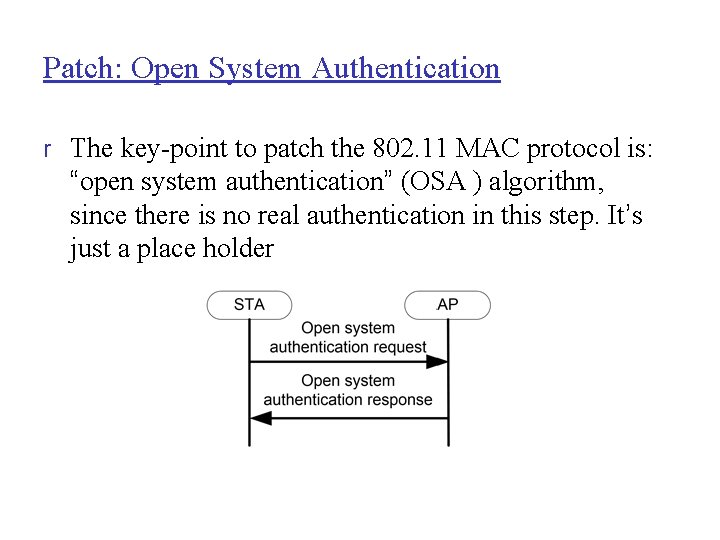
Patch: Open System Authentication r The key-point to patch the 802. 11 MAC protocol is: “open system authentication” (OSA ) algorithm, since there is no real authentication in this step. It’s just a place holder
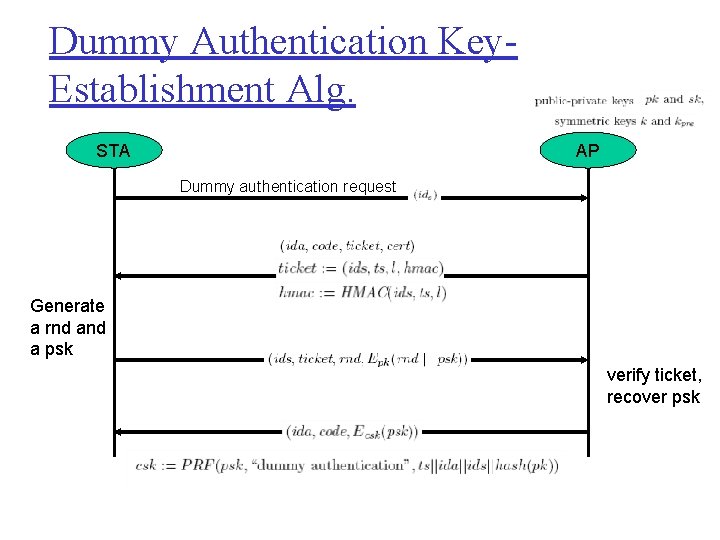
Dummy Authentication Key. Establishment Alg. STA AP Dummy authentication request Generate a rnd a psk verify ticket, recover psk
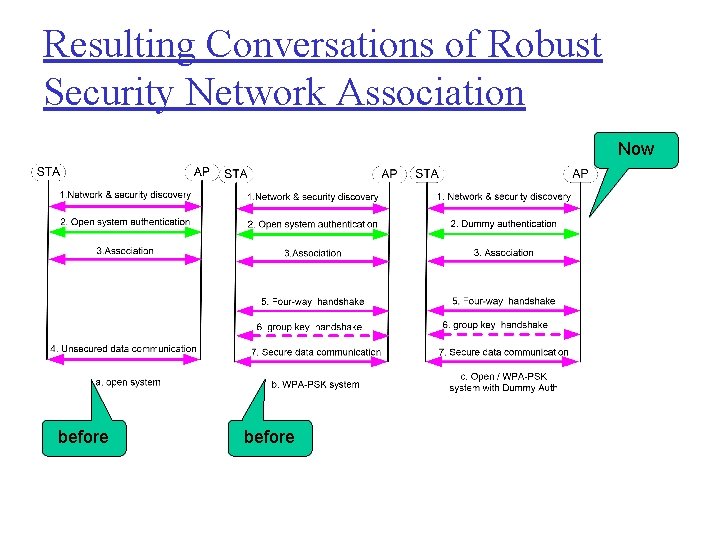
Resulting Conversations of Robust Security Network Association Now before
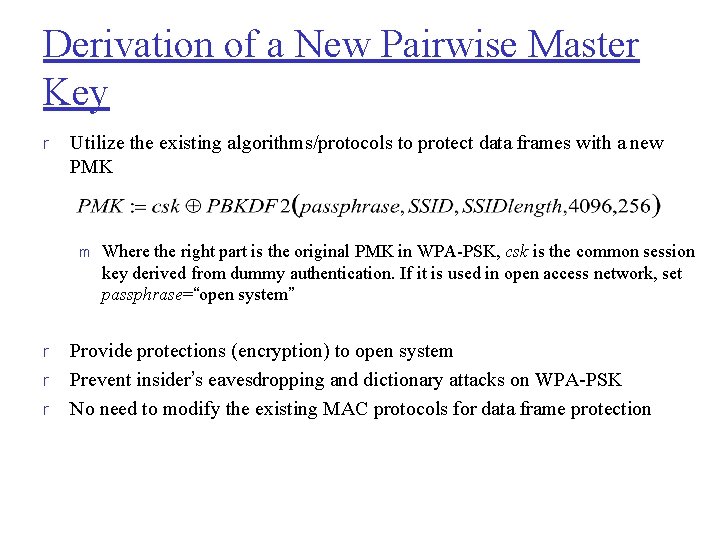
Derivation of a New Pairwise Master Key r Utilize the existing algorithms/protocols to protect data frames with a new PMK m r r r Where the right part is the original PMK in WPA-PSK, csk is the common session key derived from dummy authentication. If it is used in open access network, set passphrase=“open system” Provide protections (encryption) to open system Prevent insider’s eavesdropping and dictionary attacks on WPA-PSK No need to modify the existing MAC protocols for data frame protection
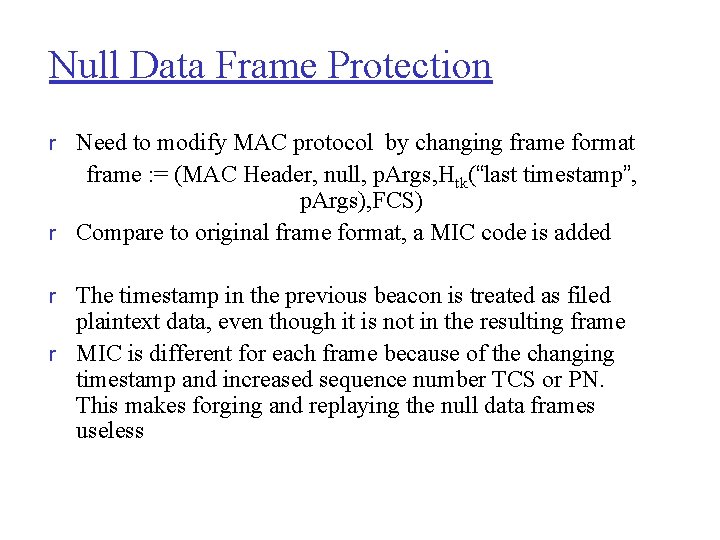
Null Data Frame Protection r Need to modify MAC protocol by changing frame format frame : = (MAC Header, null, p. Args, Htk(“last timestamp”, p. Args), FCS) r Compare to original frame format, a MIC code is added r The timestamp in the previous beacon is treated as filed plaintext data, even though it is not in the resulting frame r MIC is different for each frame because of the changing timestamp and increased sequence number TCS or PN. This makes forging and replaying the null data frames useless
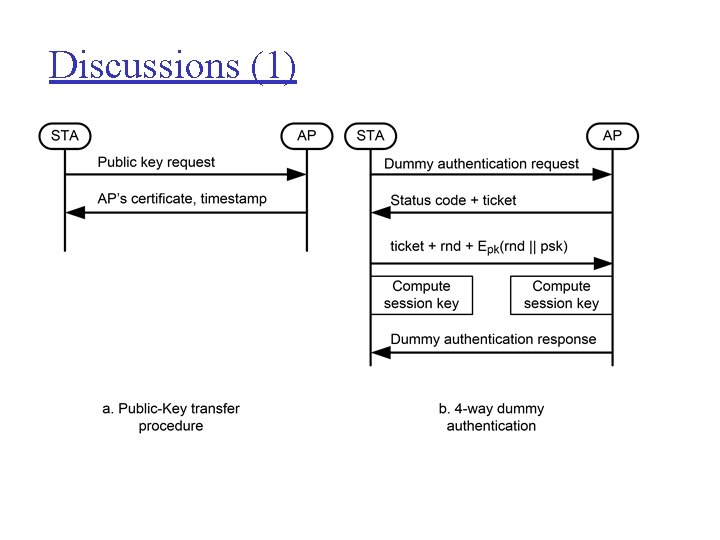
Discussions (1)
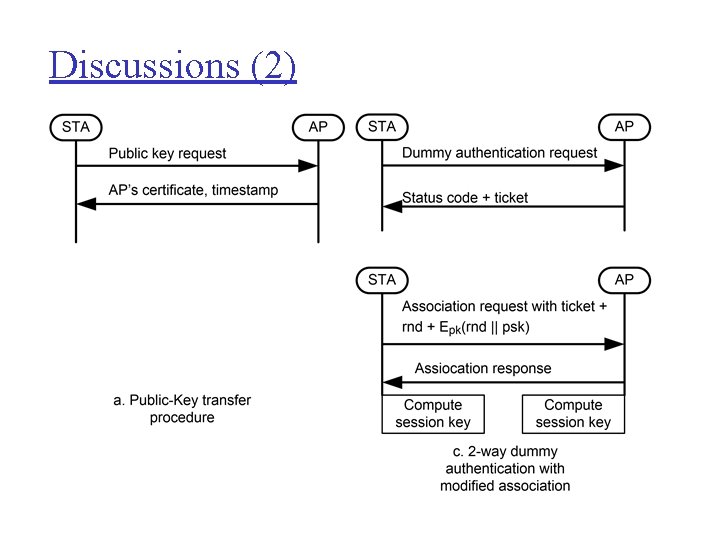
Discussions (2)
Final Remarks r MAC protocols control access to physical network r r resources for multiple clients (wired and wireless) Protocols not designed with security in mind Spoofing, flooding attacks possible against Ethernet, 802. 11 networks 802. 11 wireless security has improved considerably from WEP, but it is still not perfect Devices can be fingerprinted based on MAC layer characteristics 64
Thank You Questions & comments? 65
Acknowledgments This material is partially based on: Matthew Caesar’s slides on IP/Ethernet Security: http: //www. cs. illinois. edu/%7 Ecaesar/courses/CS 598. S 13/slides/lec_03_E thernet. pdf Slides for J. F. Kurose and K. W. Ross textbook Georg Carle’s slides on Link-Layer Security: http: //www. net. in. tum. de/fileadmin/TUM/teaching/netzsicherheit/ws 1011/ 06_Link. Layer. Security_1 up. pdf Zhimin Yang, Boxuan Gu, Adam Champion, Xiaole Bai and Dong Xuan, Link-Layer Protection in 802. 11 i WLANs with Dummy Authentication, in Proc. of ACM Conference on Wireless Network Security (Wi. Sec), March 2009 (short paper). 66
- Slides: 66