Garbled Circuits A Tutorial Benny Applebaum Tel Aviv
Garbled Circuits: A Tutorial Benny Applebaum Tel Aviv University Cryptography Boot Camp – Simons Institute, 2015
Plan • Definitions and Properties • Feasibility Results • Recent Efficiency Improvements – Skip practical advances • Applications ?
Garbled Circuit Powerful Cryptographic Tool with many Applications Constant-round secure computation [Yao 82, BMR 90, . . . ] Private Simultaneous Messages protocols [FKN 94, …] Computing on encrypted data [RAD 78, SYY 99, …] Parallel cryptography [AIK 05, …] One-time programs [GKR 08, …] KDM-secure encryption [BHHI 10, . . . ] Verifiable computation [GGP 10, …] Functional encryption [SS 10, …] Bootstrapping obfuscators [App 13] … Yao, 80’s
![Garbled Circuit “Encoding/Encryption of a function” What is a Garbled Circuit? [Yao 82] [FKN Garbled Circuit “Encoding/Encryption of a function” What is a Garbled Circuit? [Yao 82] [FKN](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-4.jpg)
Garbled Circuit “Encoding/Encryption of a function” What is a Garbled Circuit? [Yao 82] [FKN 94] [IK 00 -02] [AIK 04] [BHR 12] Yao, 80’s Secure 2 -party computation protocol Private Simultaneous Messages protocols Randomizing Polynomials representation Randomized Encoding of functions Garbling Scheme
![Randomized Encoding of Functions [IK 00, AIK 04] Input X f Output Y Decoder Randomized Encoding of Functions [IK 00, AIK 04] Input X f Output Y Decoder](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-5.jpg)
Randomized Encoding of Functions [IK 00, AIK 04] Input X f Output Y Decoder Random g Encoding(Y) Input X g(X; R) is a Randomized Encoding of f(X). • Correctness: (X, R), Decoder(g(X; R))=f(X) • Privacy: X Sim(f(X)) (g(X; R)) – flavors: perfect, statistical, computational Simulator
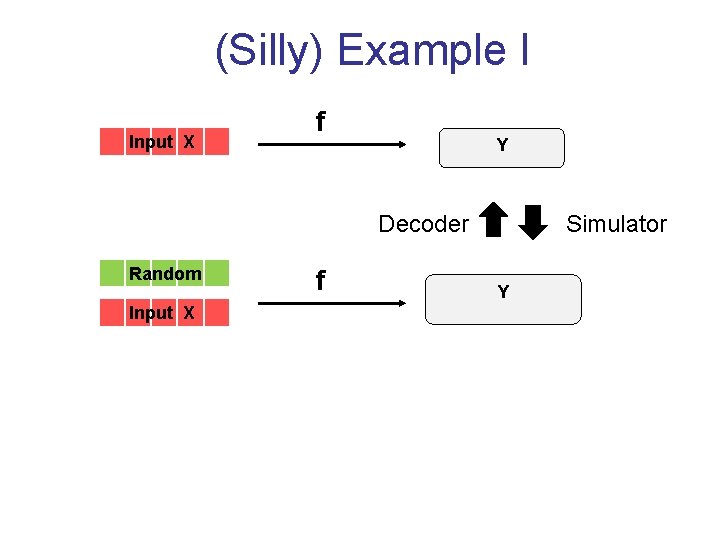
(Silly) Example I Input X f Y Decoder Random Input X f Simulator Y
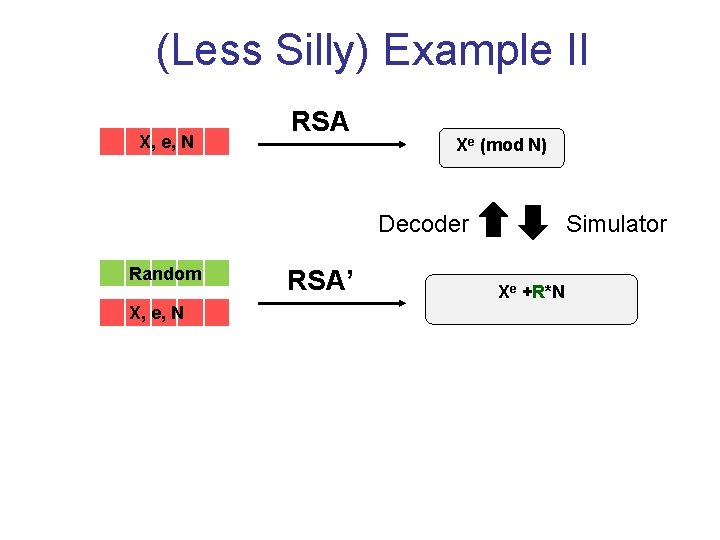
(Less Silly) Example II X, e, N RSA Xe (mod N) Decoder Random X, e, N RSA’ Simulator Xe +R*N
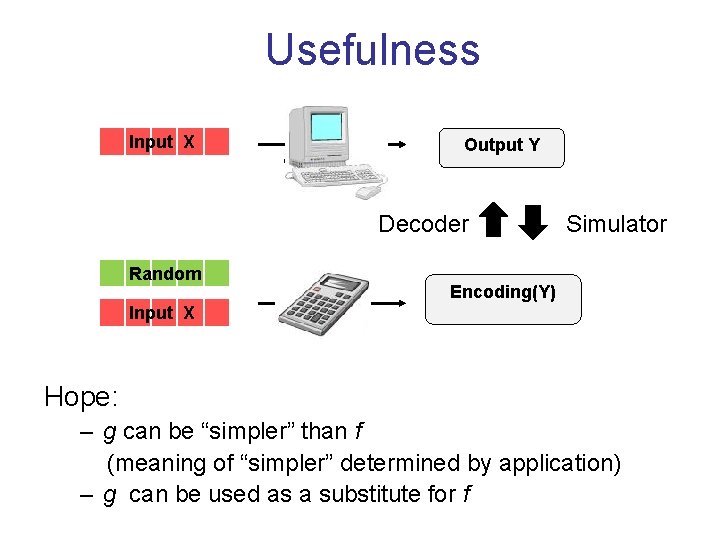
Usefulness Input X f “Complex” Output Y Decoder Random Input X g Simulator Encoding(Y) “Simple” Hope: – g can be “simpler” than f (meaning of “simpler” determined by application) – g can be used as a substitute for f
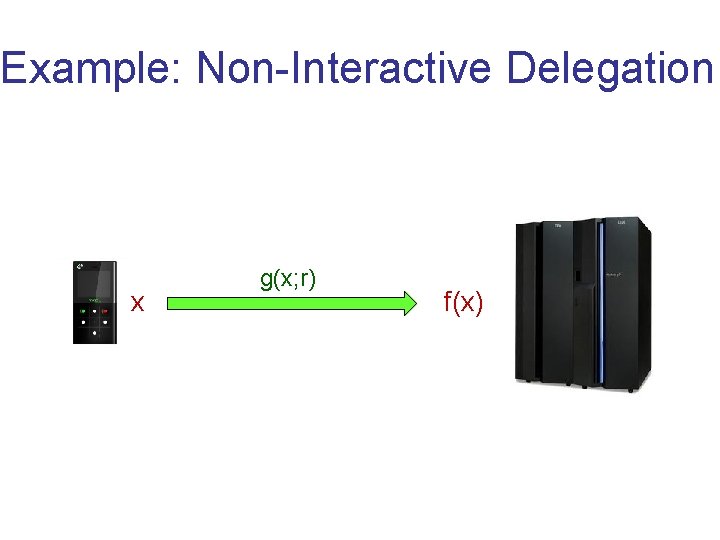
Example: Non-Interactive Delegation x g(x; r) f(x)
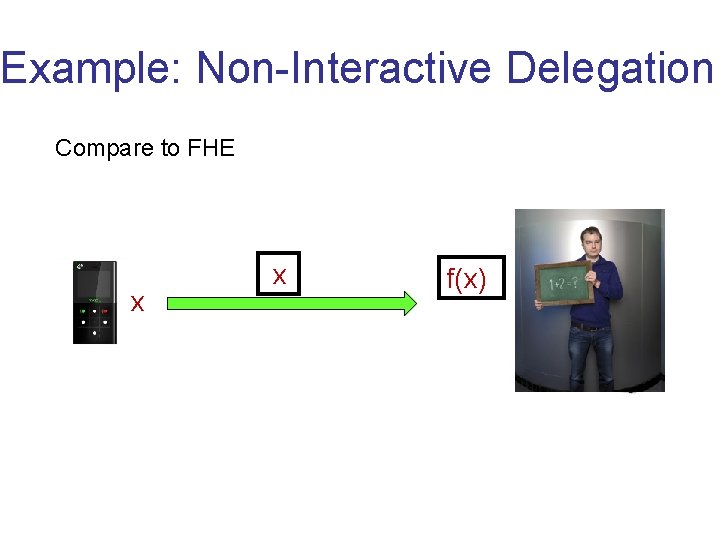
Example: Non-Interactive Delegation Compare to FHE x x f(x) x
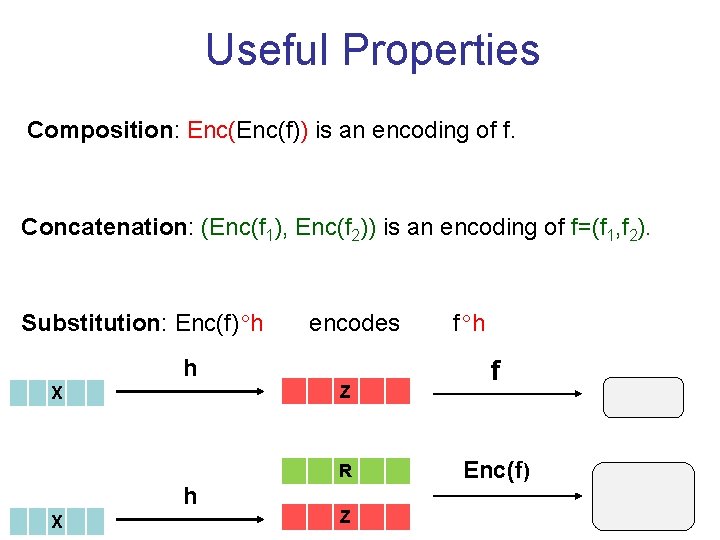
Useful Properties Composition: Enc(f)) is an encoding of f. Concatenation: (Enc(f 1), Enc(f 2)) is an encoding of f=(f 1, f 2). Substitution: Enc(f) h encodes h Z X R h X Z f h f Enc(f)
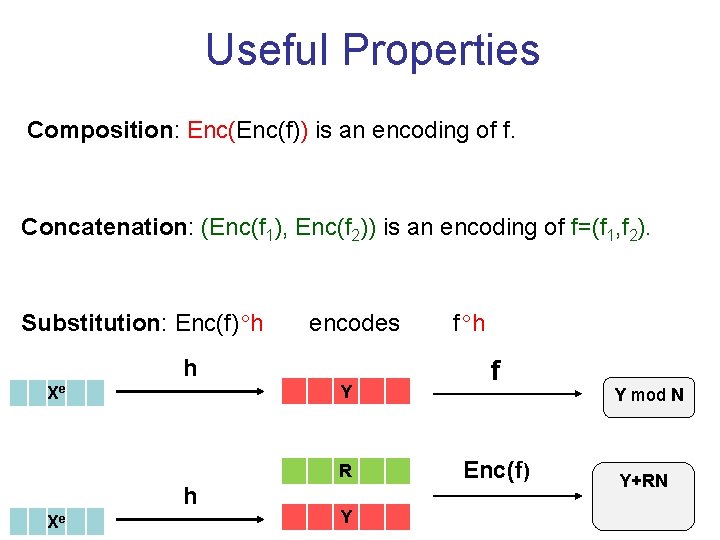
Useful Properties Composition: Enc(f)) is an encoding of f. Concatenation: (Enc(f 1), Enc(f 2)) is an encoding of f=(f 1, f 2). Substitution: Enc(f) h encodes h Y Xe R h Xe Y f h f Enc(f) Y mod N Y+RN
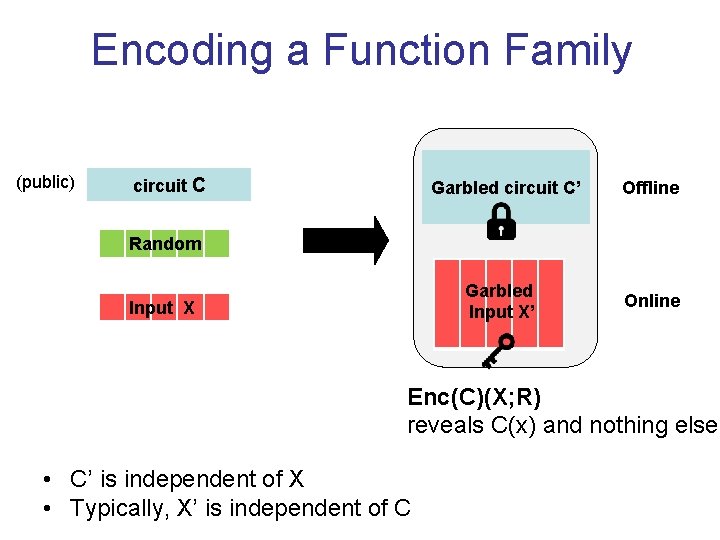
Encoding a Function Family (public) circuit C Garbled circuit C’ Offline Random Garbled Input X’ Input X Online Enc(C)(X; R) reveals C(x) and nothing else • C’ is independent of X • Typically, X’ is independent of C
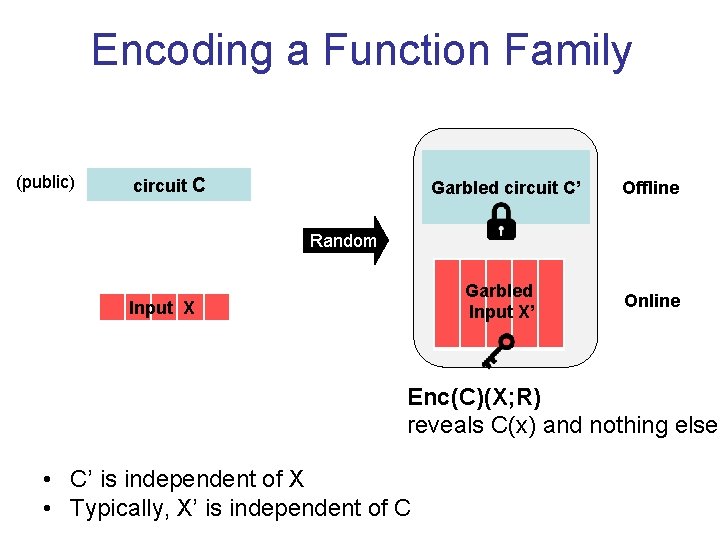
Encoding a Function Family (public) circuit C Garbled circuit C’ Offline Random Garbled Input X’ Input X Online Enc(C)(X; R) reveals C(x) and nothing else • C’ is independent of X • Typically, X’ is independent of C
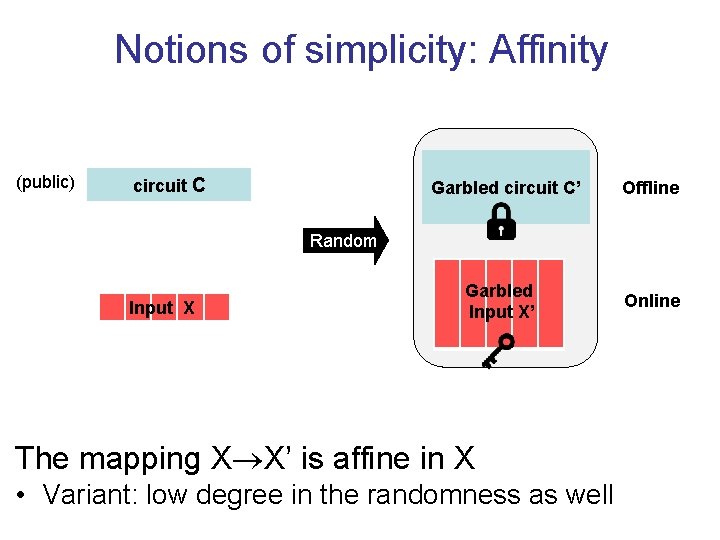
Notions of simplicity: Affinity (public) circuit C Garbled circuit C’ Offline Random Input X Garbled Input X’ The mapping X X’ is affine in X • Variant: low degree in the randomness as well Online
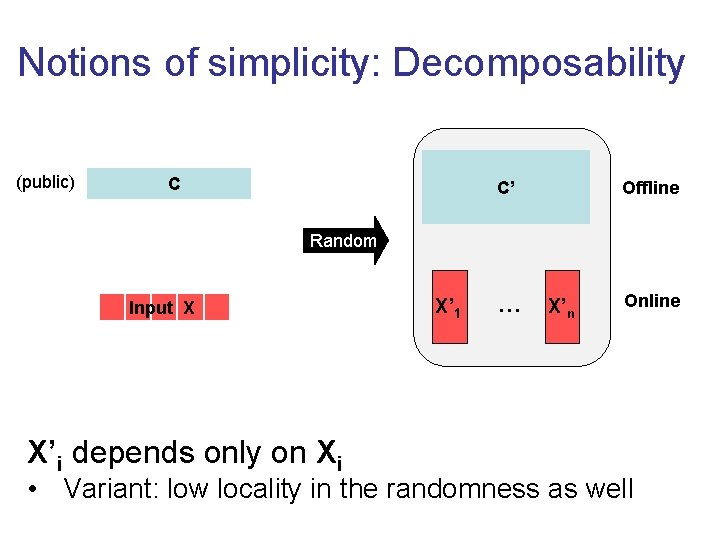
Notions of simplicity: Decomposability (public) C C’ Offline Random Input X X’i depends only on Xi X’ 1 … X’n Online • Variant: low locality in the randomness as well
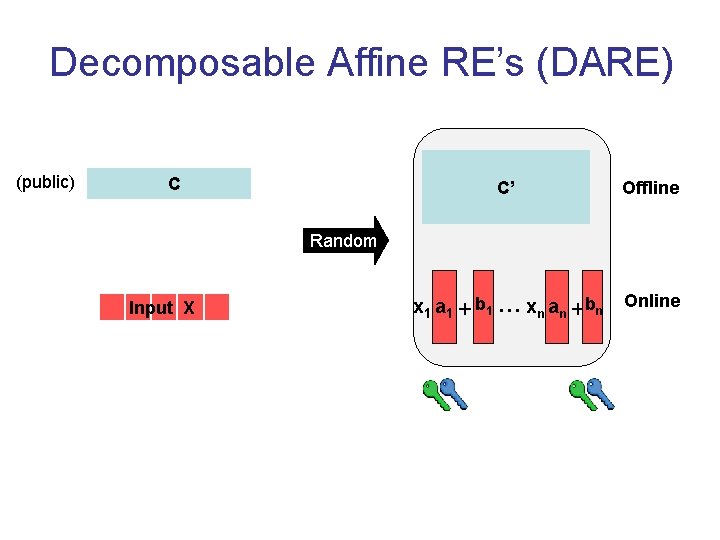
Decomposable Affine RE’s (DARE) (public) C C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random Input X
![Feasibility Results The [AIK 11] framework Feasibility Results The [AIK 11] framework](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-18.jpg)
Feasibility Results The [AIK 11] framework
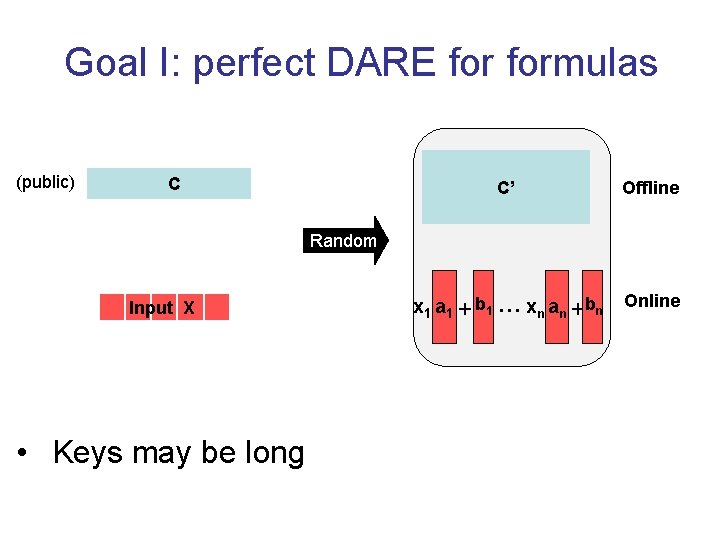
Goal I: perfect DARE formulas (public) C C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random Input X • Keys may be long
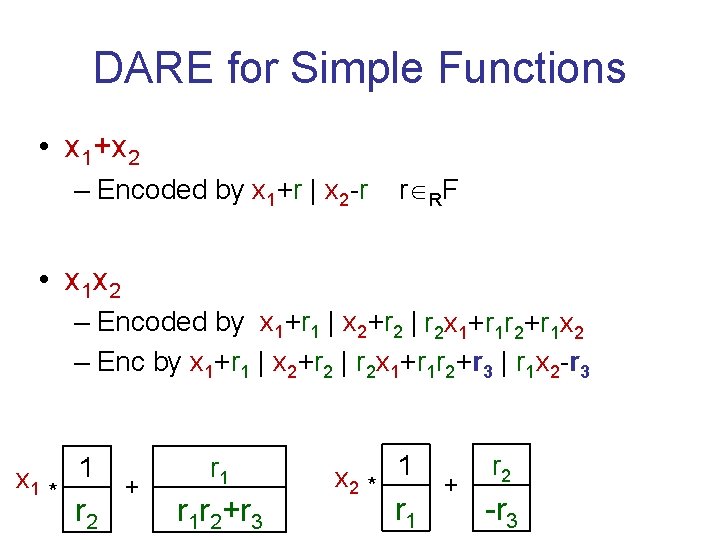
DARE for Simple Functions • x 1+x 2 – Encoded by x 1+r | x 2 -r r RF • x 1 x 2 – Encoded by x 1+r 1 | x 2+r 2 | ? r 2 x 1+r 1 r 2+r 1 x 2 – Enc by x 1+r 1 | x 2+r 2 | r 2 x 1+r 1 r 2+r 3 | r 1 x 2 -r 3 x 1 * 1 r 2 + r 1 r 2+r 3 x 2 * 1 r 1 + r 2 -r 3
DARE for Simple Functions • x 1 x 2+x 3 Affinization Gadget – Encoded by x 1 * 1 r 2 + r 1 r 2+r 3 x 2 * 1 r 1 + r 2 r 4 x 3 * -1 + -r 3 -r 4
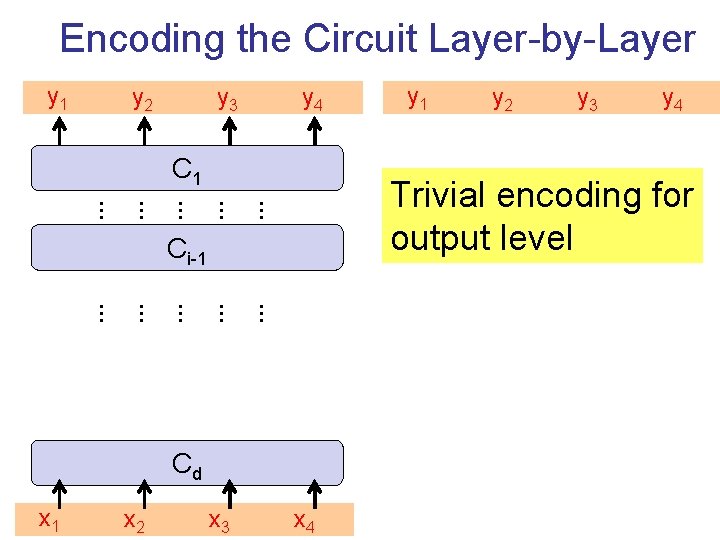
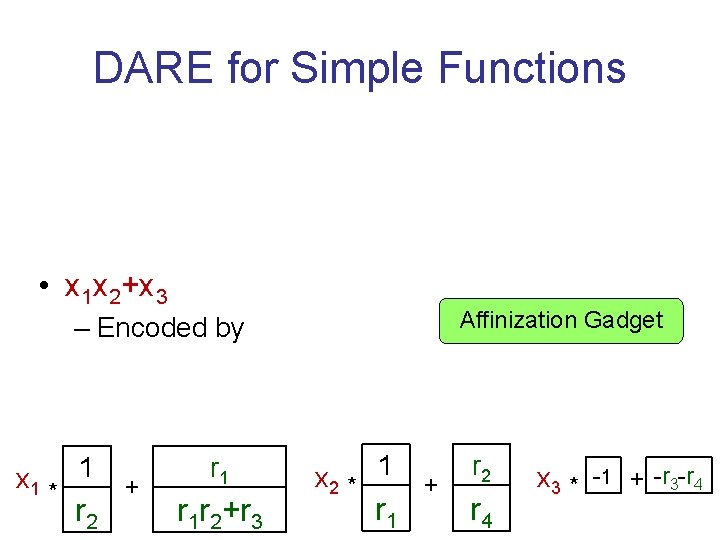
Encoding the Circuit Layer-by-Layer y 1 y 2 y 3 y 4 C 1 … … … … … Cd … x 3 … … x 2 y 3 y 4 Trivial encoding for output level Ci-1 x 1 y 1 x 4
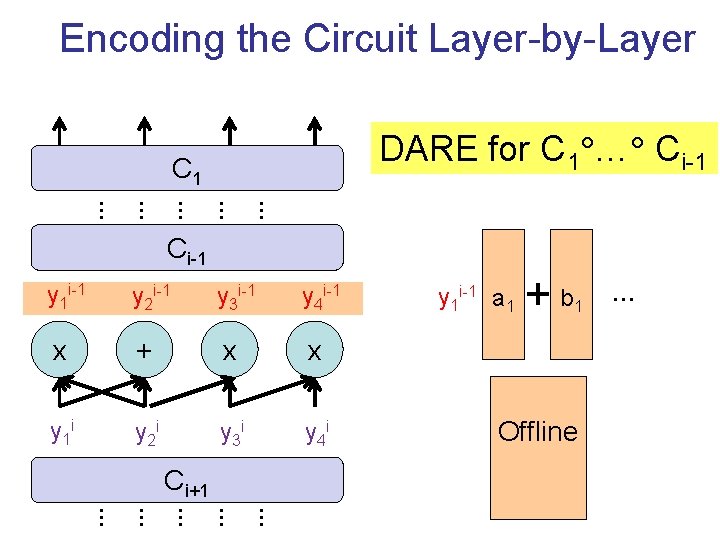
Encoding the Circuit Layer-by-Layer DARE for C 1 … Ci-1 C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 i-1 a 1 +b 1 Offline … … …
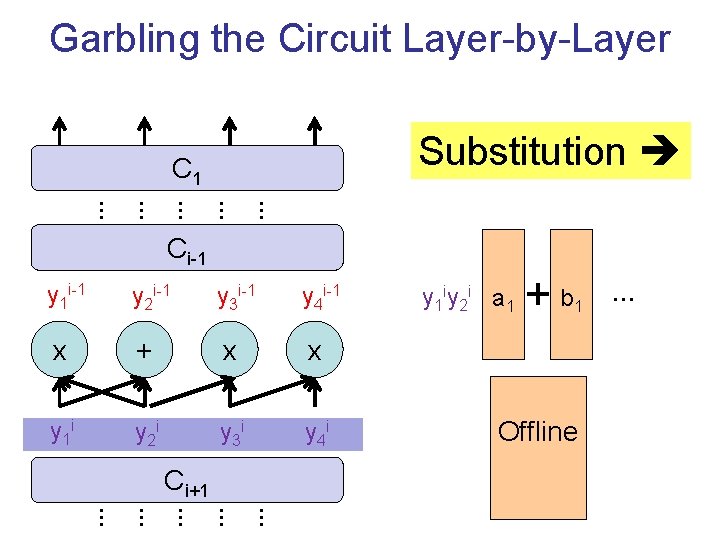
Garbling the Circuit Layer-by-Layer Substitution C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 iy 2 i a 1 +b 1 Offline … … …
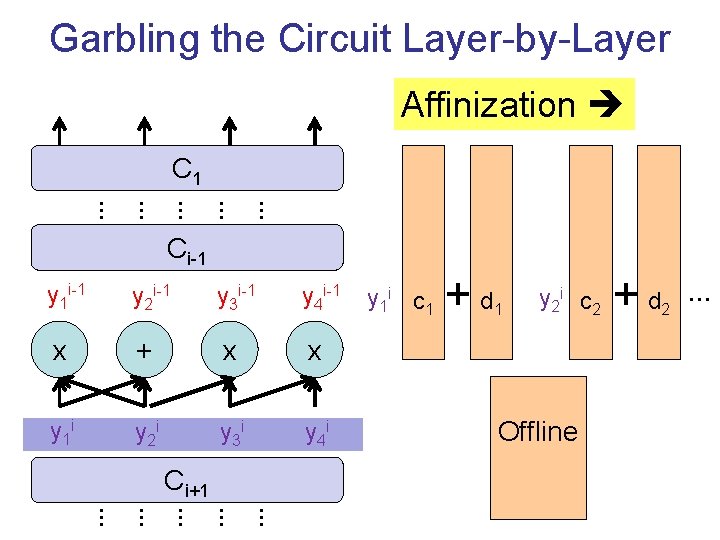
Garbling the Circuit Layer-by-Layer Affinization C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 i c 1 +d 1 y 2 i c 2 Offline +d 2 … … …
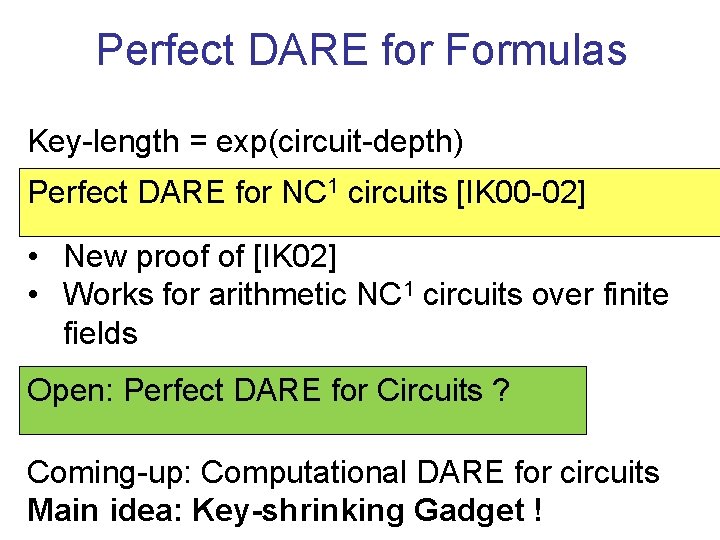
Perfect DARE for Formulas Key-length = exp(circuit-depth) Perfect DARE for NC 1 circuits [IK 00 -02] • New proof of [IK 02] • Works for arithmetic NC 1 circuits over finite fields Open: Perfect DARE for Circuits ? Coming-up: Computational DARE for circuits Main idea: Key-shrinking Gadget !
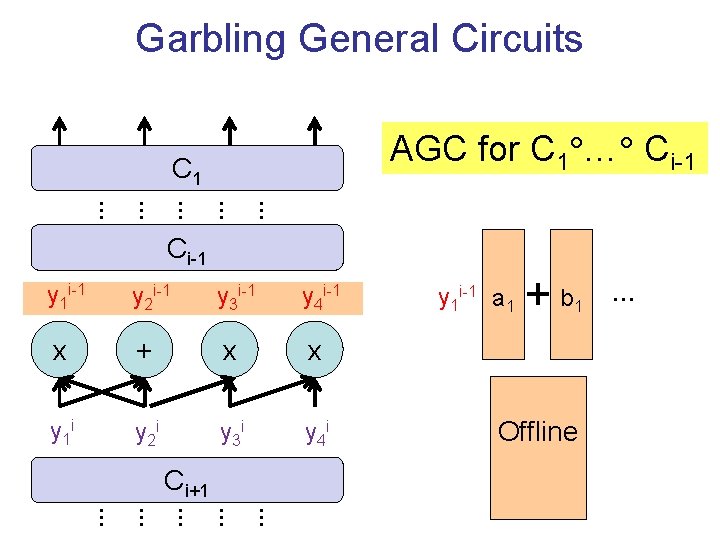
Garbling General Circuits AGC for C 1 … Ci-1 C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 i-1 a 1 +b 1 Offline … … …
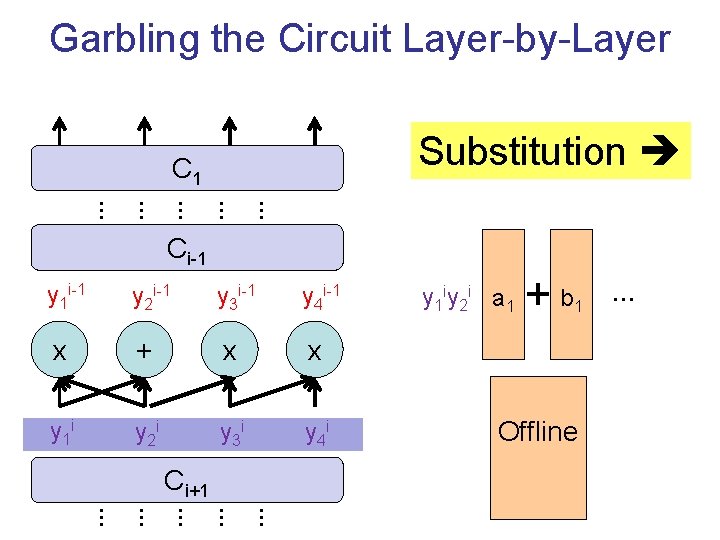
Garbling the Circuit Layer-by-Layer Substitution C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 iy 2 i a 1 +b 1 Offline … … …
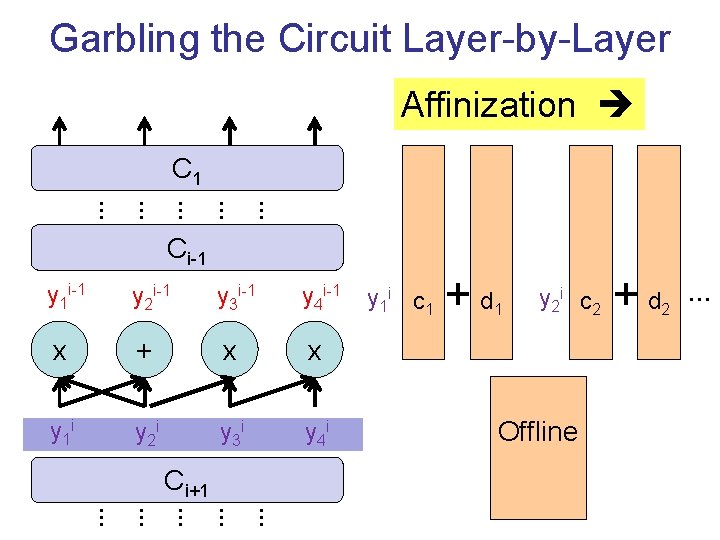
Garbling the Circuit Layer-by-Layer Affinization C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 i c 1 +d 1 y 2 i c 2 Offline +d 2 … … …
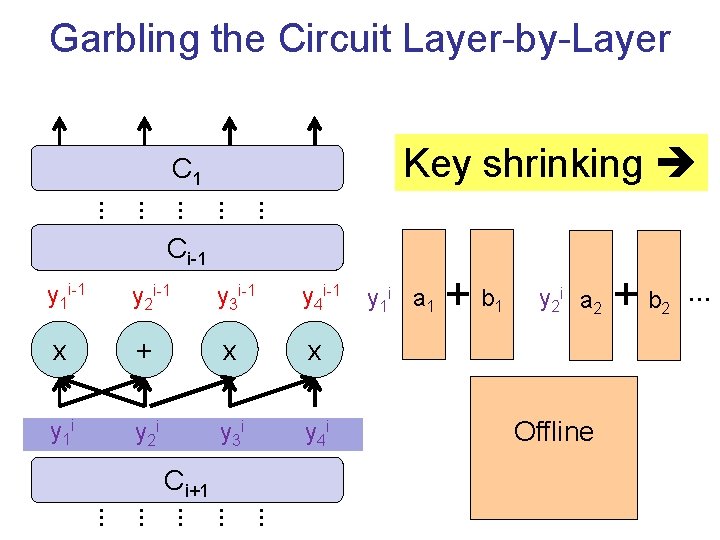
Garbling the Circuit Layer-by-Layer Key shrinking C 1 … … … Ci-1 y 1 i-1 y 2 i-1 y 3 i-1 y 4 i-1 x + x x y 1 i y 2 i y 3 i y 4 i Ci+1 y 1 i a 1 +b 1 y 2 i a 2 Offline +b 2 … … …
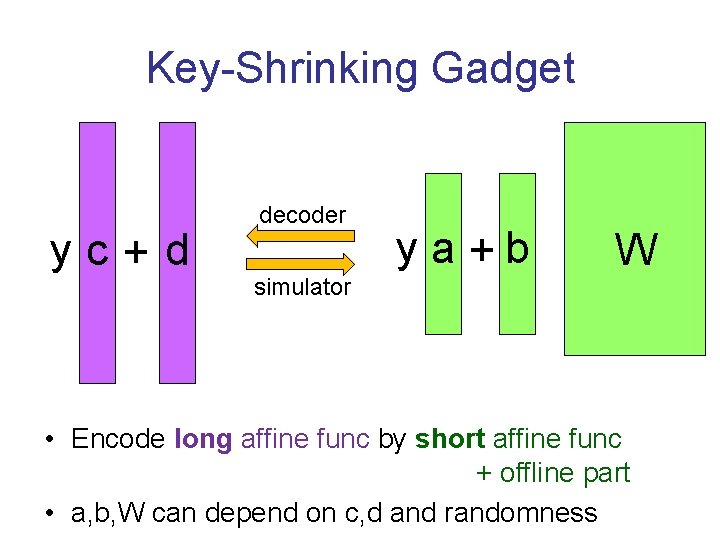
Key-Shrinking Gadget yc+d decoder simulator ya+b W • Encode long affine func by short affine func + offline part • a, b, W can depend on c, d and randomness
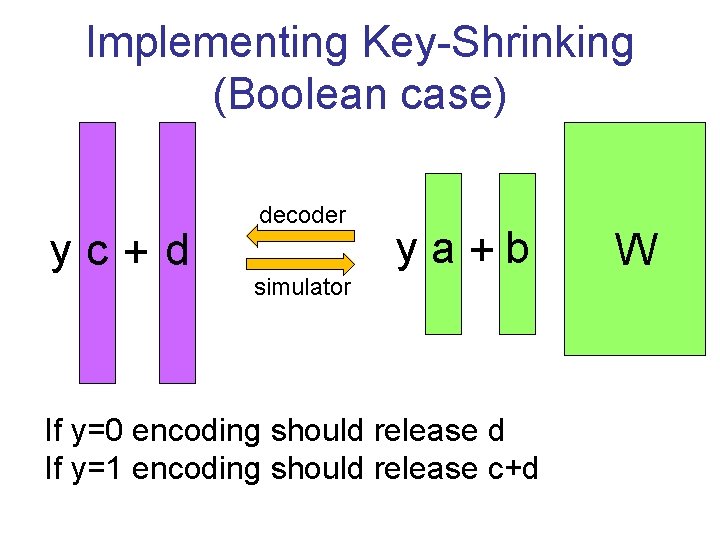
Implementing Key-Shrinking (Boolean case) yc+d decoder simulator ya+b If y=0 encoding should release d If y=1 encoding should release c+d W
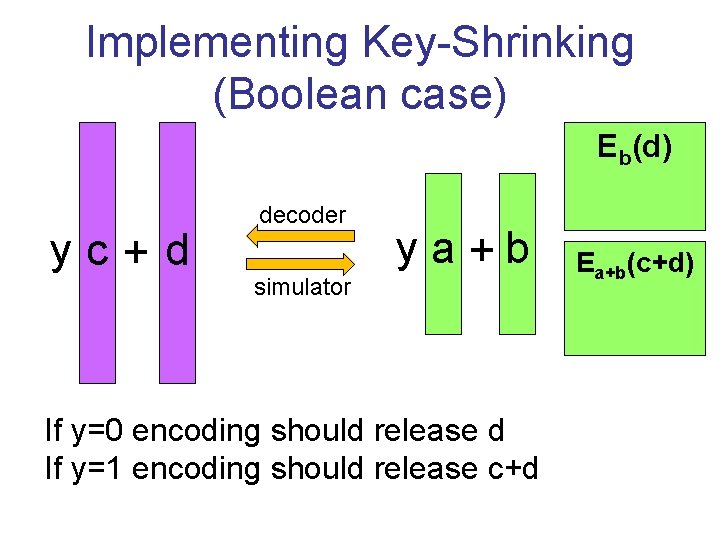
Implementing Key-Shrinking (Boolean case) Eb(d) yc+d decoder simulator ya+b If y=0 encoding should release d If y=1 encoding should release c+d Ea+b(c+d)
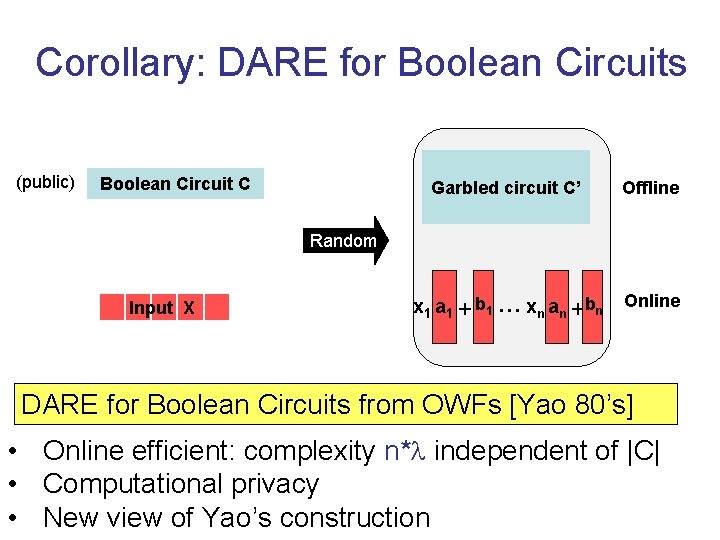
Corollary: DARE for Boolean Circuits (public) Boolean Circuit C Garbled circuit C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random Input X DARE for Boolean Circuits from OWFs [Yao 80’s] • Online efficient: complexity n* independent of |C| • Computational privacy • New view of Yao’s construction
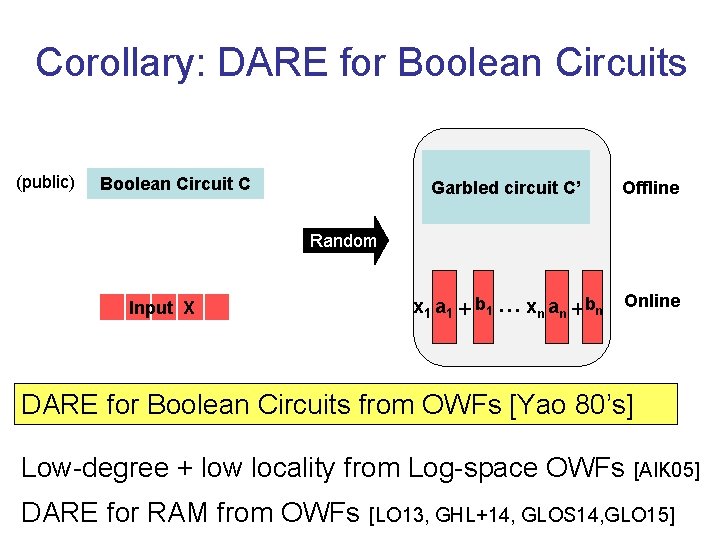
Corollary: DARE for Boolean Circuits (public) Boolean Circuit C Garbled circuit C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random Input X DARE for Boolean Circuits from OWFs [Yao 80’s] Low-degree + low locality from Log-space OWFs [AIK 05] DARE for RAM from OWFs [LO 13, GHL+14, GLOS 14, GLO 15]
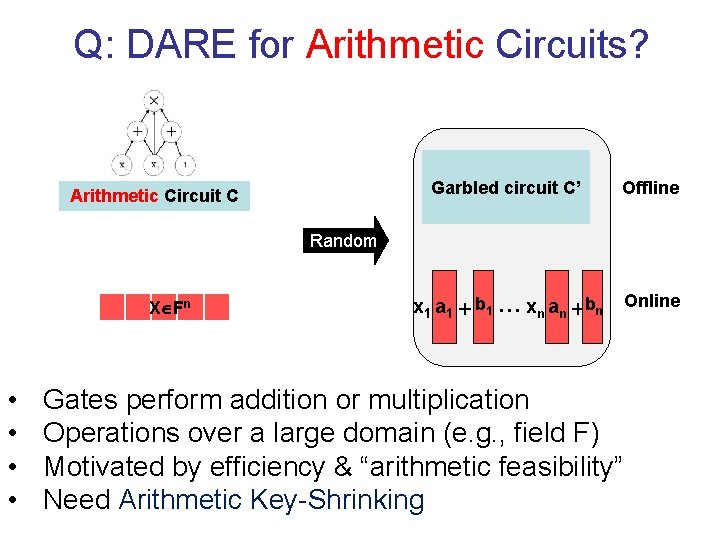
Q: DARE for Arithmetic Circuits? Arithmetic Circuit C Garbled circuit C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random X Fn • • Gates perform addition or multiplication Operations over a large domain (e. g. , field F) Motivated by efficiency & “arithmetic feasibility” Need Arithmetic Key-Shrinking
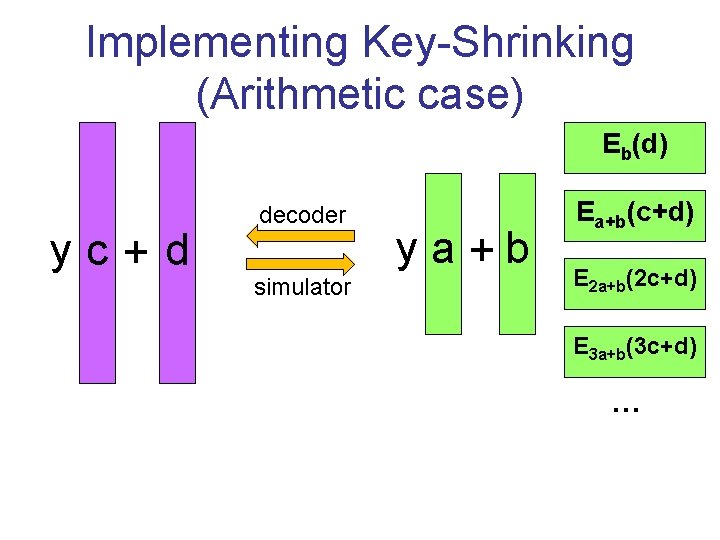
Implementing Key-Shrinking (Arithmetic case) Eb(d) yc+d decoder simulator ya+b Ea+b(c+d) E 2 a+b(2 c+d) E 3 a+b(3 c+d) …
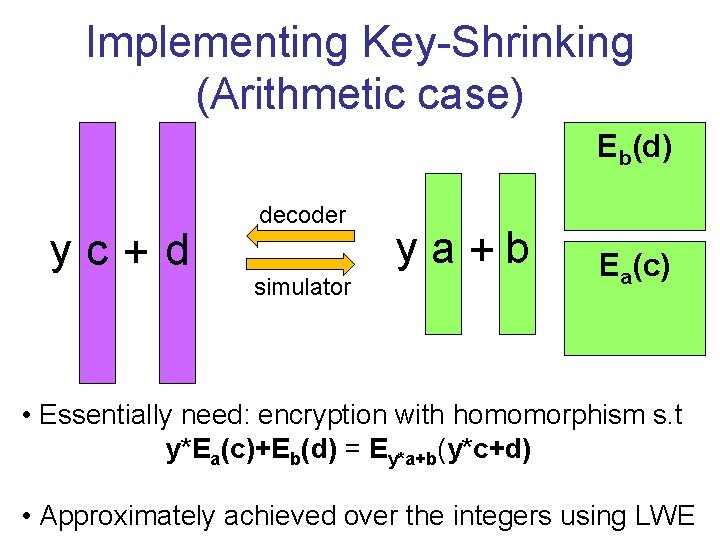
Implementing Key-Shrinking (Arithmetic case) Eb(d) yc+d decoder simulator ya+b Ea(c) • Essentially need: encryption with homomorphism s. t y*Ea(c)+Eb(d) = Ey*a+b(y*c+d) • Approximately achieved over the integers using LWE
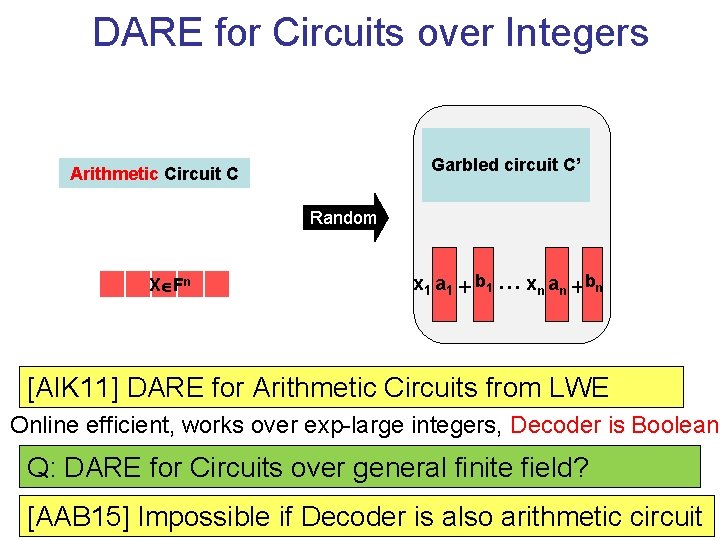
DARE for Circuits over Integers Garbled circuit C’ Arithmetic Circuit C Random X Fn x 1 a 1 + b 1 … xn an + b n [AIK 11] DARE for Arithmetic Circuits from LWE Online efficient, works over exp-large integers, Decoder is Boolean Q: DARE for Circuits over general finite field? [AAB 15] Impossible if Decoder is also arithmetic circuit
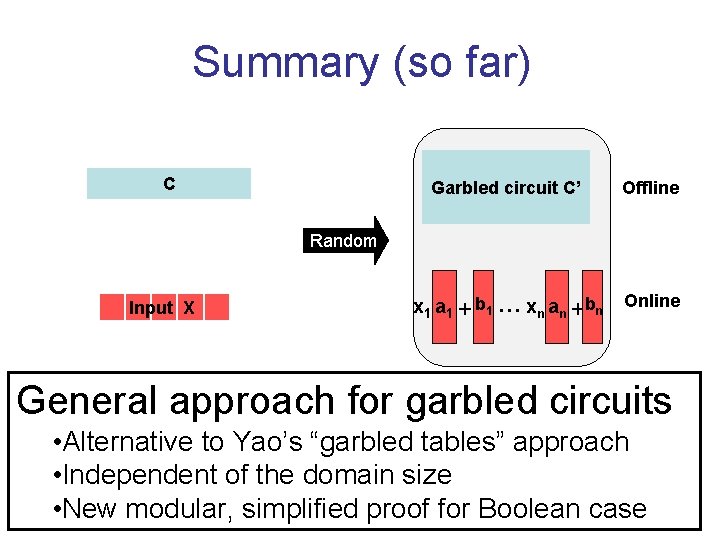
Summary (so far) C Garbled circuit C’ Offline x 1 a 1 + b 1 … xn an + b n Online Random Input X General approach for garbled circuits • Alternative to Yao’s “garbled tables” approach • Independent of the domain size • New modular, simplified proof for Boolean case

Efficiency Improvements
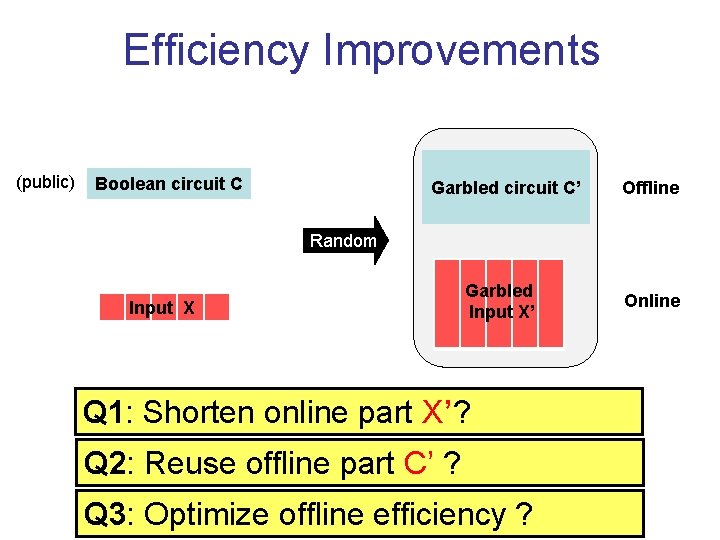
Efficiency Improvements (public) Boolean circuit C Garbled circuit C’ Offline Random Input X Garbled Input X’ Online Q 1: Shorten online part X’? Reveal C(x) and nothing else Q 2: Reuse offline part C’ ? Q 3: Optimize offline efficiency ?
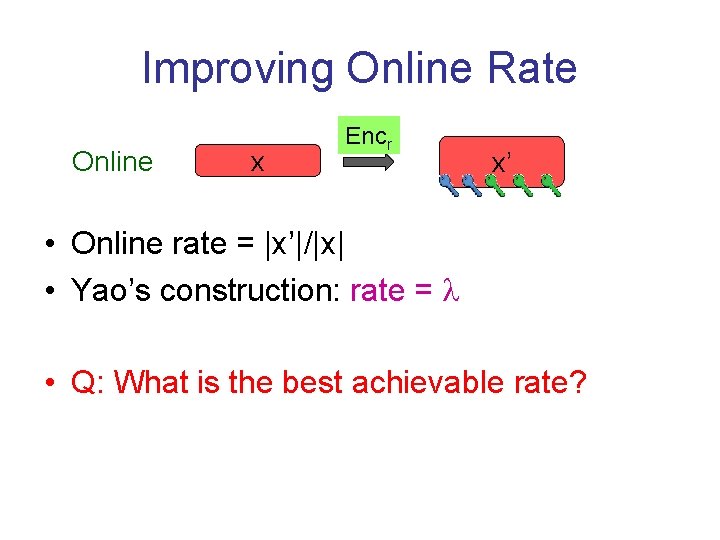
Improving Online Rate Online x Encr x’ • Online rate = |x’|/|x| • Yao’s construction: rate = • Q: What is the best achievable rate?
![Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-44.jpg)
Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or RSA, there is a Affine RE with online rate=1. • More precisely: |x’|=|x|+ • Quasi-linear online computational complexity • Decomposability is impossible
![Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-45.jpg)
Improving Online Rate Online x Encr x’ Thm [AIKW 13]: Assuming DDH, LWE, or RSA, there is a Affine RE with online rate=1. Outline: Key-Homomorphism Set Encryption Thm
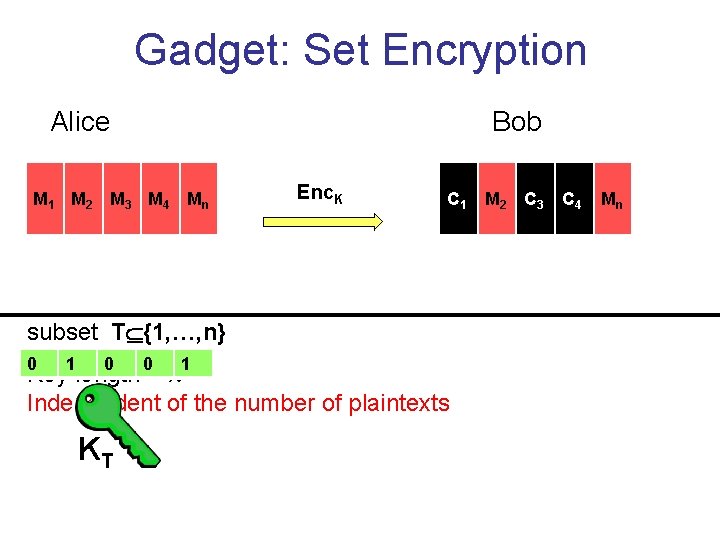
Gadget: Set Encryption Alice M 1 M 2 M 3 M 4 Mn Bob Enc. K C 1 subset T {1, …, n} 0 1 0 0 1 Key length = Independent of the number of plaintexts KT C 22 C 3 M C 4 Cnn M
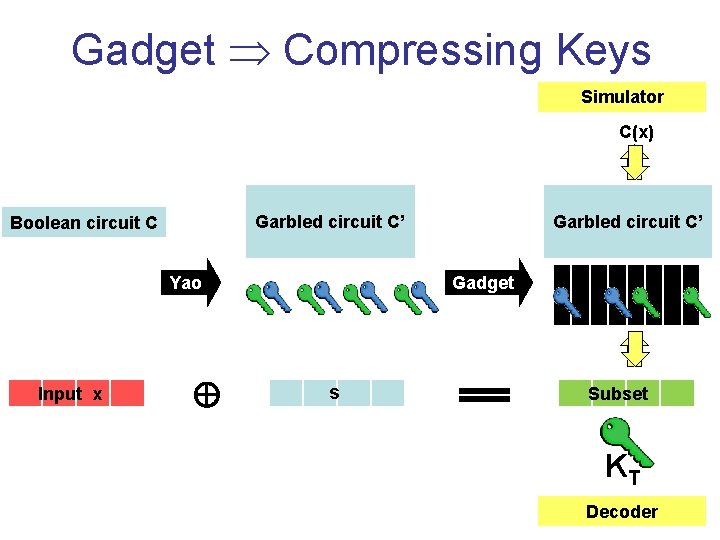
Gadget Compressing Keys Simulator C(x) Garbled circuit C’ Boolean circuit C Yao Input x Garbled circuit C’ Gadget s Subset KT Decoder
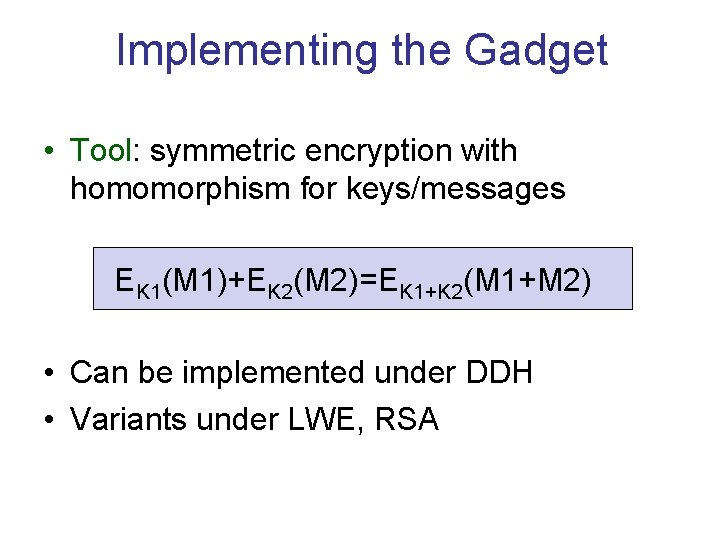
Implementing the Gadget • Tool: symmetric encryption with homomorphism for keys/messages EK 1(M 1)+EK 2(M 2)=EK 1+K 2(M 1+M 2) • Can be implemented under DDH • Variants under LWE, RSA
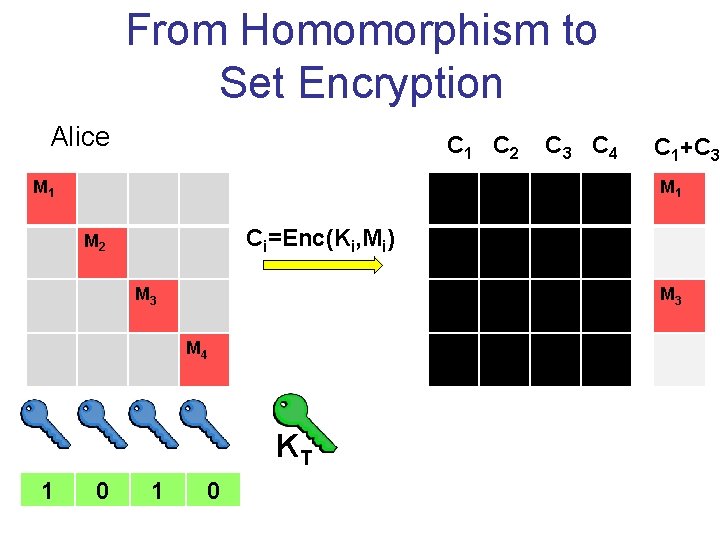
From Homomorphism to Set Encryption Alice C 1 C 2 M 1 C 1 MM 2 2 M 3 M 4 Mn Ci=Enc(Ki, Mi) M 3 0 1 C 2 0 M 3 C 4 KT C 1+C 3 M 1 C 3 M 4 1 C 3 C 4
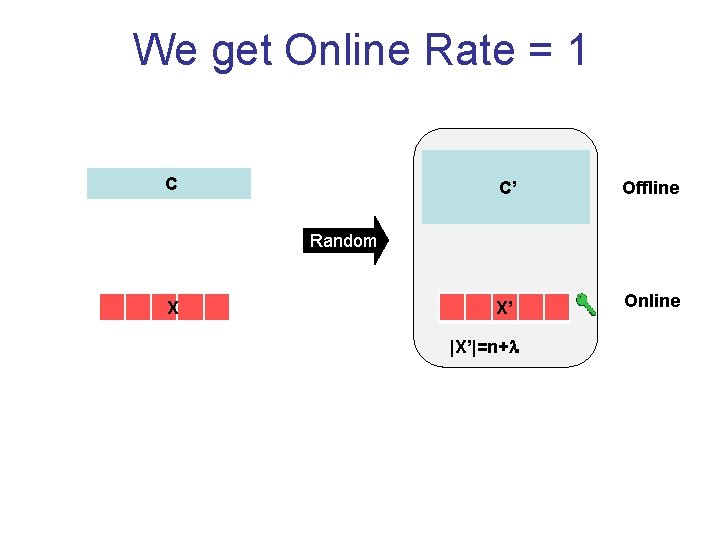
We get Online Rate = 1 C C’ Offline X’ Online Random X |X’|=n+
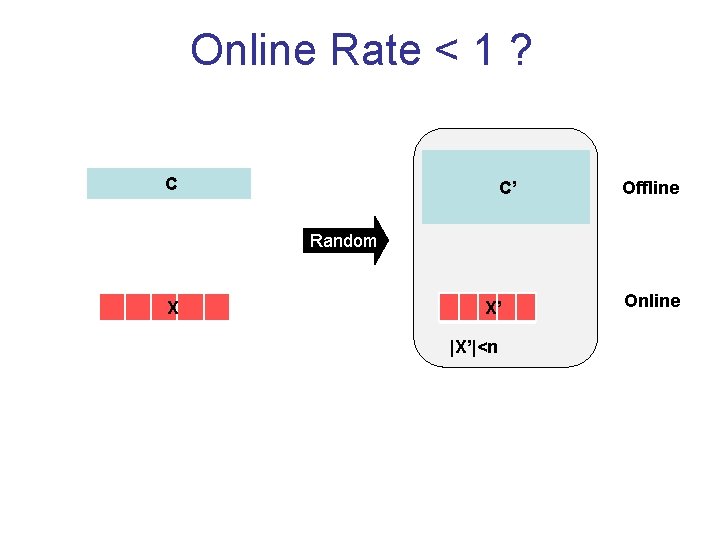
Online Rate < 1 ? C C’ Offline Random X X’ |X’|<n Online
Online Rate < 1 ? C X C’ Random X’ Offline Online |X’|<n Impossible if online part independent of C. • Consider C(X)=Xi
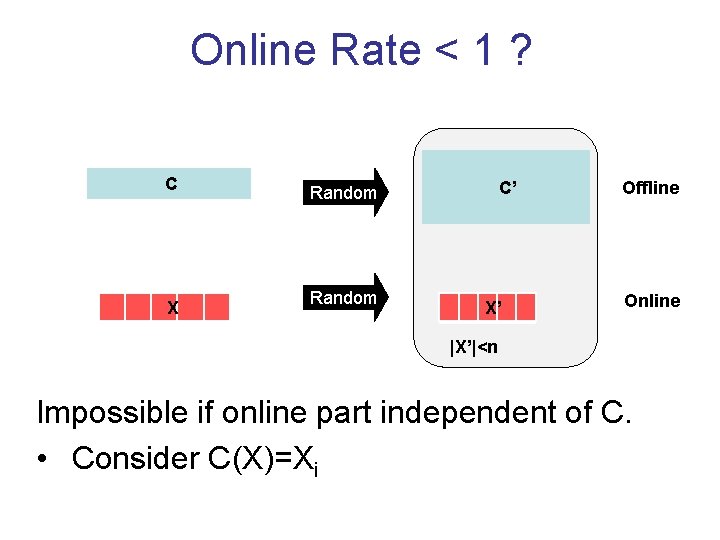
Online Rate < 1 for TM’s? Time n 3 Turing Machine C X C’ Time n 2 Time < Time(C) X’ Offline Online |X’|<n C is compressible function [DI 06, HN 10] [AEGS 15]: Incompressible functions likely to exist Unlikely to achieve online rate < 1
![Reusing the Offline Part [Gorbunov. Vaikuntanathan. Wee 13] [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Reusing the Offline Part [Gorbunov. Vaikuntanathan. Wee 13] [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13]](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-54.jpg)
Reusing the Offline Part [Gorbunov. Vaikuntanathan. Wee 13] [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13]
![Reusable Randomized Encoding Yao: expensive one-time secure offline part Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Amortize complexity Reusable Randomized Encoding Yao: expensive one-time secure offline part Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Amortize complexity](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-55.jpg)
Reusable Randomized Encoding Yao: expensive one-time secure offline part Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Amortize complexity by reusing the offline part? Reusable RE under sub-exp LWE • Online part grows with n, m, and circuit-depth • Succinct Functional Encryption Boolean circuit C Garbled circuit C’ Offline Random Input X Garbled Input X’ Online
![Reusable Randomized Encoding Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Reusable RE under sub-exp LWE Outline: Homomorphism Attribute Reusable Randomized Encoding Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Reusable RE under sub-exp LWE Outline: Homomorphism Attribute](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-56.jpg)
Reusable Randomized Encoding Thm. [Goldwasser-Kalai-Popa-Vaikuntanathan-Zeldovich 13] Reusable RE under sub-exp LWE Outline: Homomorphism Attribute Encryption Thm
![Gadget: Attribute Encryption [SW 05, GPSW 06] Reusable RE for the function: (T, s) Gadget: Attribute Encryption [SW 05, GPSW 06] Reusable RE for the function: (T, s)](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-57.jpg)
Gadget: Attribute Encryption [SW 05, GPSW 06] Reusable RE for the function: (T, s) if predicate P(T) holds (T, ) else AE(T, s)= Alice Bob Reusable Offline(P) T s if P(T) holds
FHE+ Attribute Enc Reusable-GC
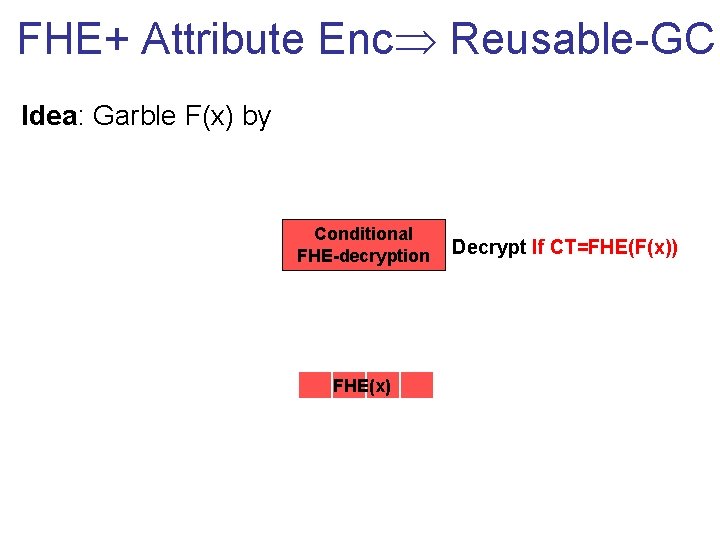
FHE+ Attribute Enc Reusable-GC Idea: Garble F(x) by Conditional F(x) FHE-decryption FHE(F(x)) FHE(x) Decrypt If CT=FHE(F(x))
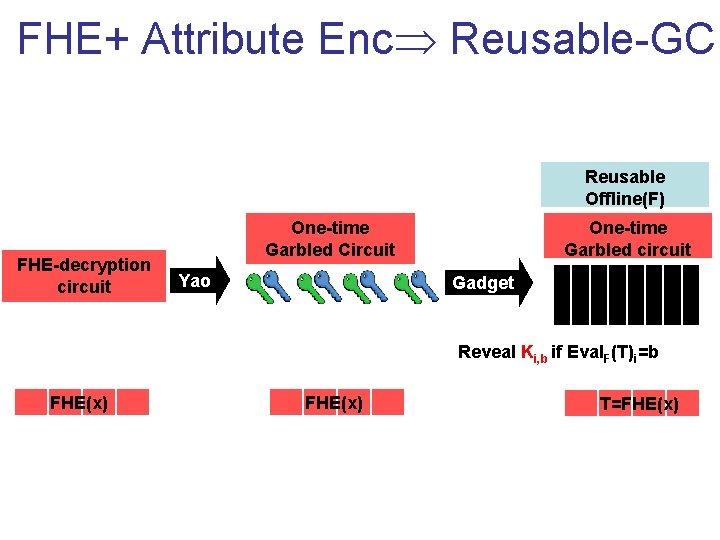
FHE+ Attribute Enc Reusable-GC Reusable Offline(F) FHE-decryption circuit One-time Garbled Circuit Yao One-time Garbled circuit Gadget Reveal Ki, b if Eval. F(T)i=b FHE(x) T=FHE(x)
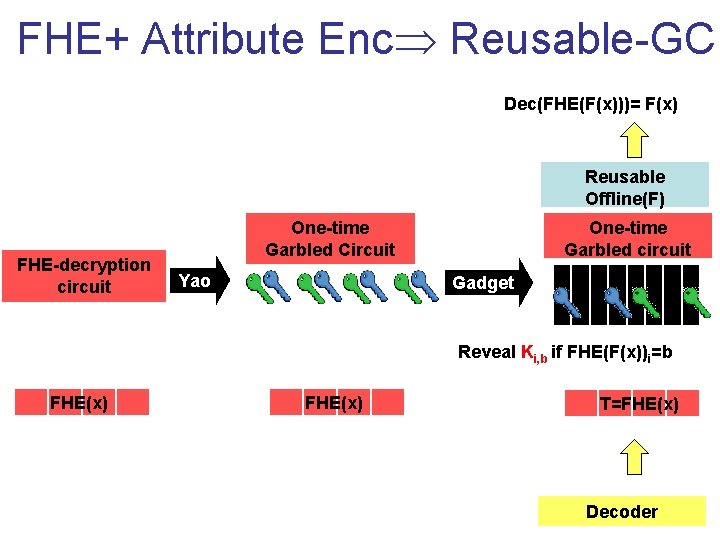
FHE+ Attribute Enc Reusable-GC Dec(FHE(F(x)))= F(x) Reusable Offline(F) FHE-decryption circuit One-time Garbled Circuit Yao One-time Garbled circuit Gadget Reveal Ki, b if FHE(F(x))i=b FHE(x) T=FHE(x) Decoder
![Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Tool: Public-Key Encryption with Re-Keying For every Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Tool: Public-Key Encryption with Re-Keying For every](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-62.jpg)
Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Tool: Public-Key Encryption with Re-Keying For every public-keys A, B, C, key TA, B C: EA(S), EB(S) EC(S) • Can be implemented under LWE
![Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 1 0 0 Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 1 0 0](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-63.jpg)
Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 1 0 0 Public input T Secret input s 0 1 s
![Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 s 1 0 Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 s 1 0](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-64.jpg)
Implementing Attribute Encryption [Gorbunov. Vaikuntanathan. Wee 13] Reveal s iff output(T)=1 s 1 0 0 Public input T Secret input s 0 1
![Succinct RE [GKPVZ 13 b, GHRW 14 b, BGLPT 15, KLW 15, CHJV 15] Succinct RE [GKPVZ 13 b, GHRW 14 b, BGLPT 15, KLW 15, CHJV 15]](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-65.jpg)
Succinct RE [GKPVZ 13 b, GHRW 14 b, BGLPT 15, KLW 15, CHJV 15]
![Complexity so far… [Yao]: Time(Enc(C)) Time(C) [GKPVZ 13]: Amortize. Time(Enc(C)) independent of Time(C) – Complexity so far… [Yao]: Time(Enc(C)) Time(C) [GKPVZ 13]: Amortize. Time(Enc(C)) independent of Time(C) –](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-66.jpg)
Complexity so far… [Yao]: Time(Enc(C)) Time(C) [GKPVZ 13]: Amortize. Time(Enc(C)) independent of Time(C) – poly(input, output, , depth(C)) Q: Time(Enc(C)) independent of Time(C)? • Assume that C has short description (Turing Machine). C’ C Random X X’
![Succinct RE Thm. [BGLPT 15, CHJV 15] Succinct RE under i. O+OWFs • Time(Enc(C))=poly(input, Succinct RE Thm. [BGLPT 15, CHJV 15] Succinct RE under i. O+OWFs • Time(Enc(C))=poly(input,](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-67.jpg)
Succinct RE Thm. [BGLPT 15, CHJV 15] Succinct RE under i. O+OWFs • Time(Enc(C))=poly(input, output, , space(C)) • Previously, [GKPVZ 13 b] under stronger assumption • Follow-up [KLW 15] eliminates dependency in space • Allows to transform i. O for circuits to i. O for TMs Turing Machine C’ C Random Input X Garbled Input X’
![Proof Idea (over-simplified) [BGLPT 15] View Turing Machine as a uniform circuit Y CT Proof Idea (over-simplified) [BGLPT 15] View Turing Machine as a uniform circuit Y CT](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-68.jpg)
Proof Idea (over-simplified) [BGLPT 15] View Turing Machine as a uniform circuit Y CT … … Program P Ci … … i C 1 … … X
![Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-69.jpg)
Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding is local Y CT … Enc(C 1) X’ … … Rand … … … X Enc(Ci) … … … Rand C 1 … Rand … Ci i Enc(CT) … … … Program P Rand
![Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-70.jpg)
Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding is local Enc(CT) … Rand X’ … … … Enc(C 1) … … … X … Enc(Ci) … i … Rand … … Program P’
![Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-71.jpg)
Proof Idea (over-simplified) [BGLPT 15] Encode the circuit via Yao’s construction Fact 1: encoding is local Enc(CT) … Rand X’ … … … Enc(C 1) … … … X … Enc(Ci) … i … PRFK … … Program P’ K
![Proof Idea (over-simplified) [BGLPT 15] Security: • Yao’s Simulation is local • Puncturing Encoding Proof Idea (over-simplified) [BGLPT 15] Security: • Yao’s Simulation is local • Puncturing Encoding](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-72.jpg)
Proof Idea (over-simplified) [BGLPT 15] Security: • Yao’s Simulation is local • Puncturing Encoding Program P’ K Program Obf(P’) i … … X Rand X’
![Take Home Message • Better Homomorphism Better encodings – – Rerandomizable GC’s [GHV 10] Take Home Message • Better Homomorphism Better encodings – – Rerandomizable GC’s [GHV 10]](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-73.jpg)
Take Home Message • Better Homomorphism Better encodings – – Rerandomizable GC’s [GHV 10] Free XOR gates [App 13] ABE for Arithmetic circuit [BNS 13] Simultaneous Compression of online/offline [GGHV 13]
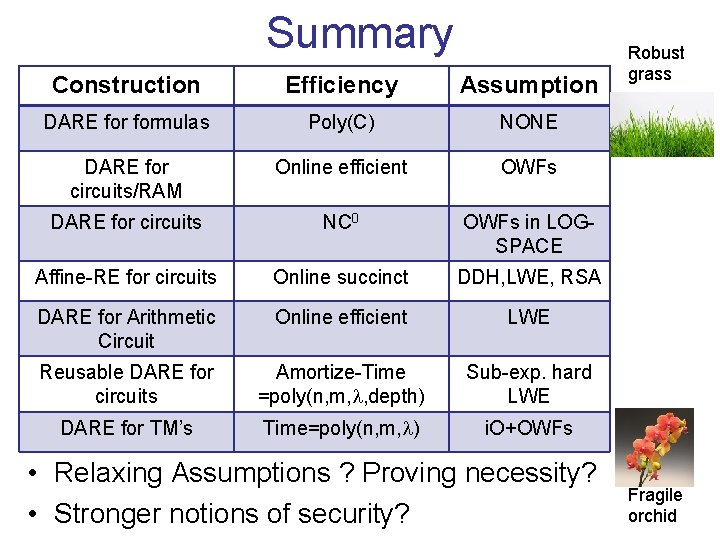
Summary Construction Efficiency Assumption DARE formulas Poly(C) NONE DARE for circuits/RAM Online efficient OWFs DARE for circuits NC 0 OWFs in LOGSPACE Affine-RE for circuits Online succinct DDH, LWE, RSA DARE for Arithmetic Circuit Online efficient LWE Reusable DARE for circuits Amortize-Time =poly(n, m, , depth) Sub-exp. hard LWE DARE for TM’s Time=poly(n, m, ) i. O+OWFs • Relaxing Assumptions ? Proving necessity? • Stronger notions of security? Robust grass Fragile orchid

Applications
The Archetypical Story Bob Adversary RE’s? Functionality Alice
Encoding the Functionality Bob Examples: • Secure Computation • Delegation • Program Checking • Verifiable Computation • Bootstrapping Obfuscation Adversary Functionality Alice
Encoding the Honest Parties Bob Adversary Examples: • Parallel Crypto • ECC with fast decoder Functionality Alice
![Encoding the Adversary Bob Adversary Examples: Key-Dependent Message Amplification [BHHI 10, App 11] Functionality Encoding the Adversary Bob Adversary Examples: Key-Dependent Message Amplification [BHHI 10, App 11] Functionality](http://slidetodoc.com/presentation_image_h/a3ac639269d413ce818c3d36aa83add5/image-79.jpg)
Encoding the Adversary Bob Adversary Examples: Key-Dependent Message Amplification [BHHI 10, App 11] Functionality Alice
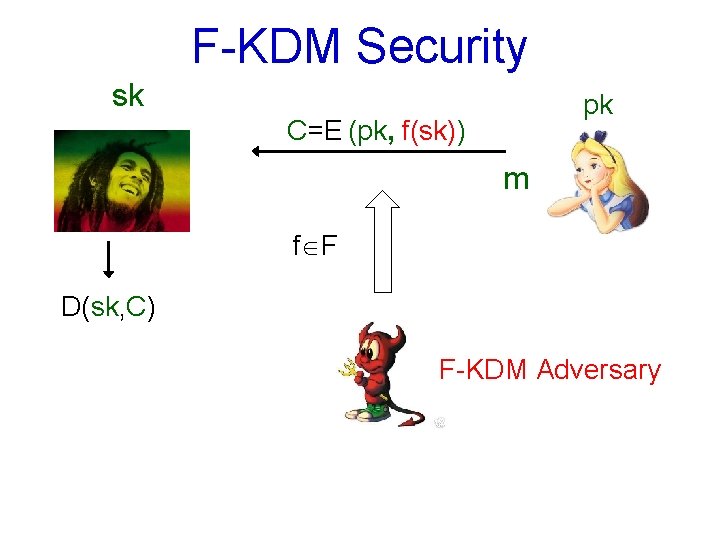
F-KDM Security sk pk C=E (pk, f(sk)) m f F D(sk, C) F-KDM Adversary
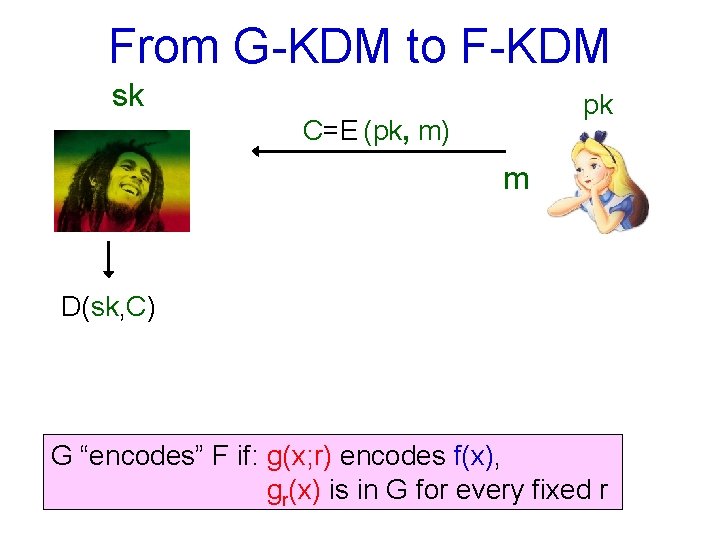
From G-KDM to F-KDM sk pk C=E (pk, m) m D(sk, C) G “encodes” F if: g(x; r) encodes f(x), gr(x) is in G for every fixed r
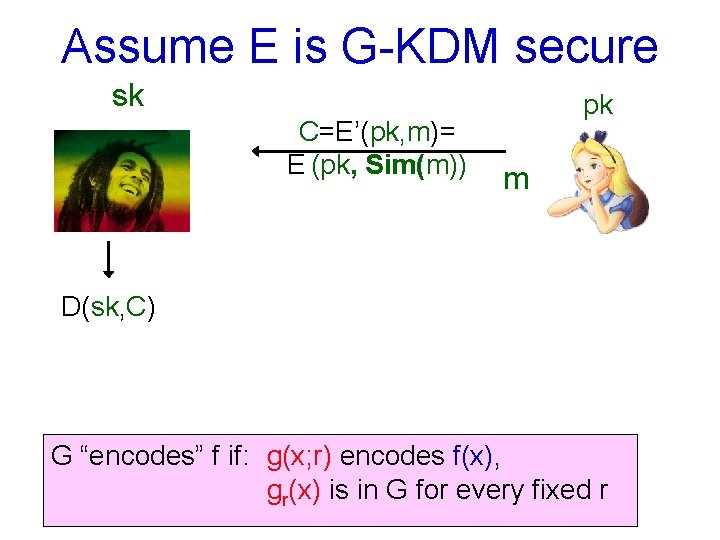
Assume E is G-KDM secure sk C=E’(pk, m)= E (pk, Sim(m)) pk m D(sk, C) G “encodes” f if: g(x; r) encodes f(x), gr(x) is in G for every fixed r
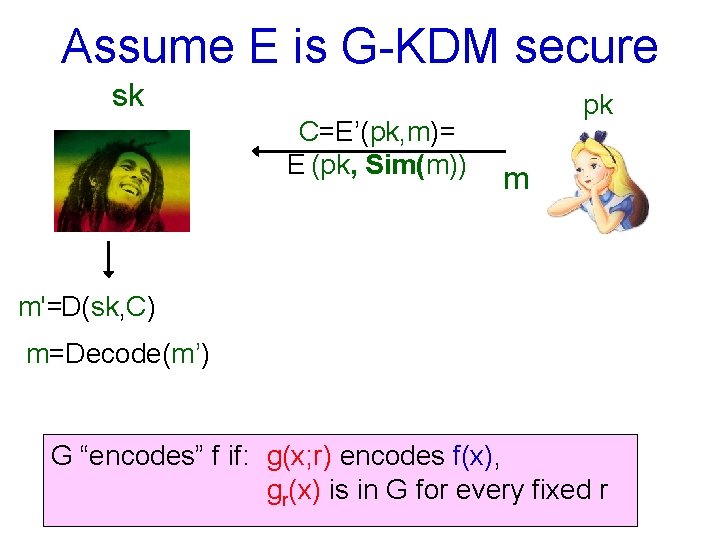
Assume E is G-KDM secure sk C=E’(pk, m)= E (pk, Sim(m)) pk m m'=D(sk, C) m=Decode(m’) G “encodes” f if: g(x; r) encodes f(x), gr(x) is in G for every fixed r
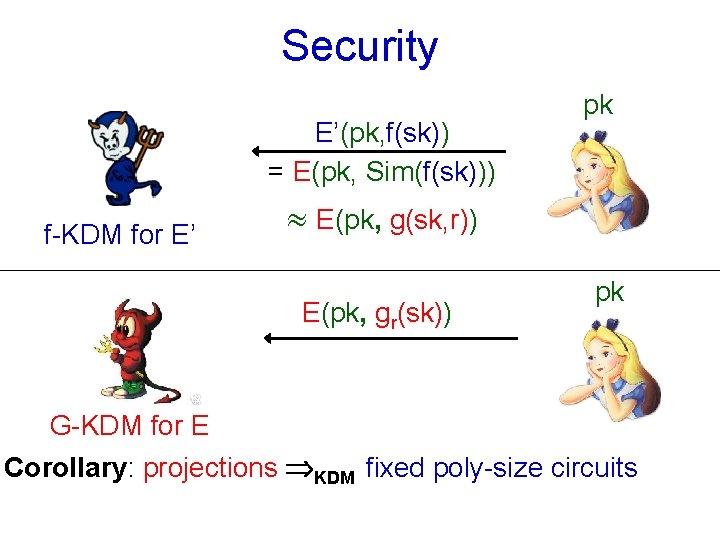
Security E’(pk, f(sk)) = E(pk, Sim(f(sk))) f-KDM for E’ pk E(pk, g(sk, r)) E(pk, gr(sk)) pk G-KDM for E Corollary: projections KDM fixed poly-size circuits
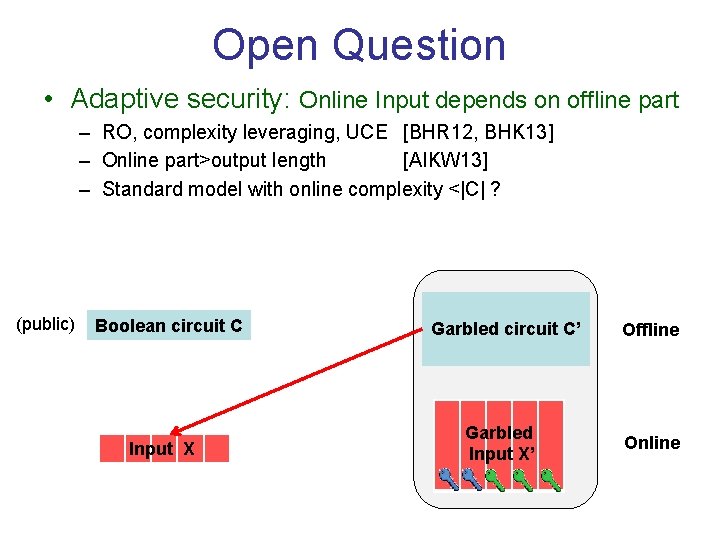
Open Question • Adaptive security: Online Input depends on offline part – RO, complexity leveraging, UCE [BHR 12, BHK 13] – Online part>output length [AIKW 13] – Standard model with online complexity <|C| ? (public) Boolean circuit C Input X Garbled circuit C’ Garbled Input X’ Offline Online

Thank You!
- Slides: 86