CRYPTOGRAPHIC PROTOCOLS 2016 LECTURE 10 Garbled Circuits helger
CRYPTOGRAPHIC PROTOCOLS 2016, LECTURE 10 Garbled Circuits helger lipmaa, university of tartu
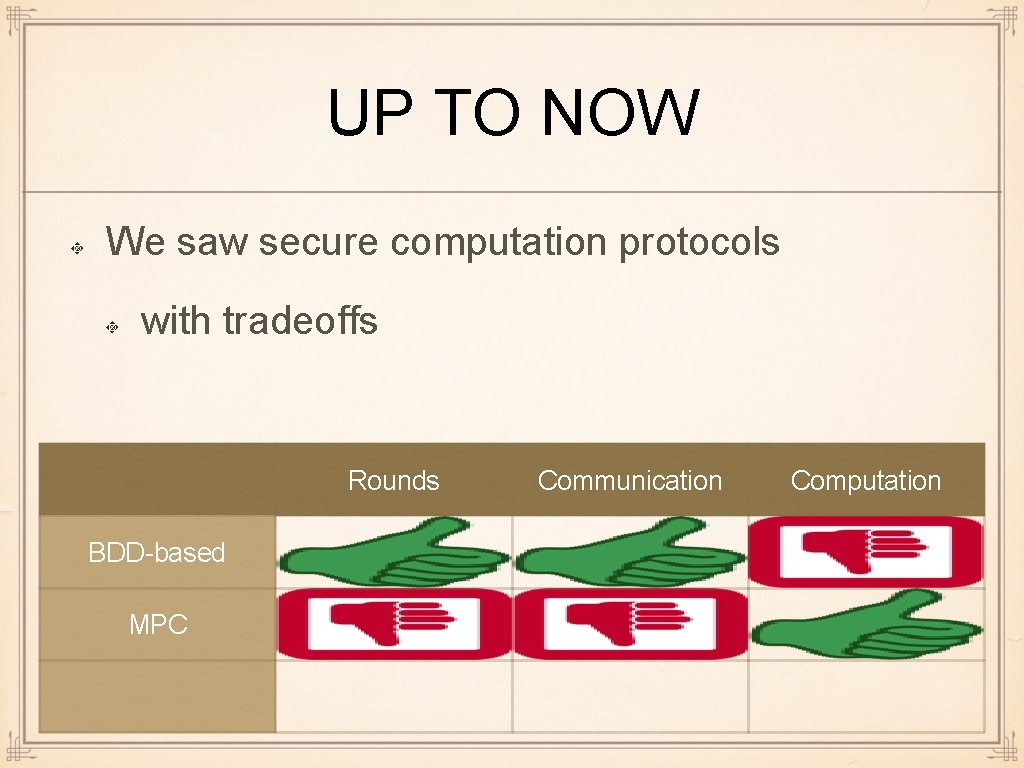
UP TO NOW We saw secure computation protocols with tradeoffs Rounds BDD-based MPC Communication Computation
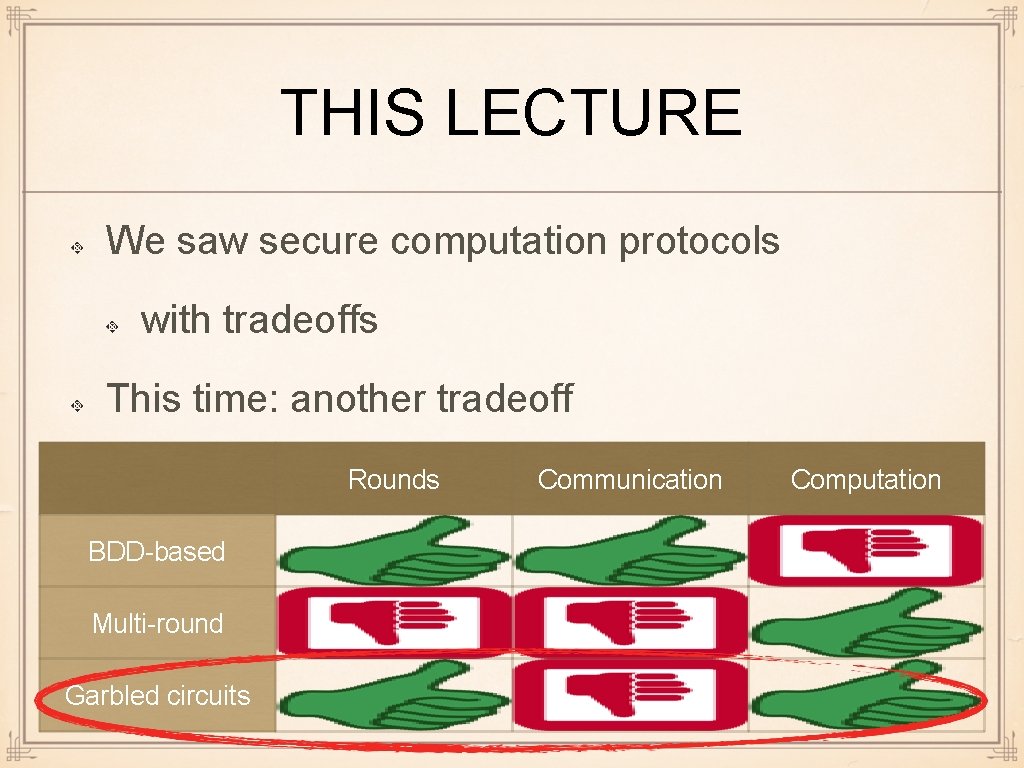
THIS LECTURE We saw secure computation protocols with tradeoffs This time: another tradeoff Rounds BDD-based Multi-round Garbled circuits Communication Computation
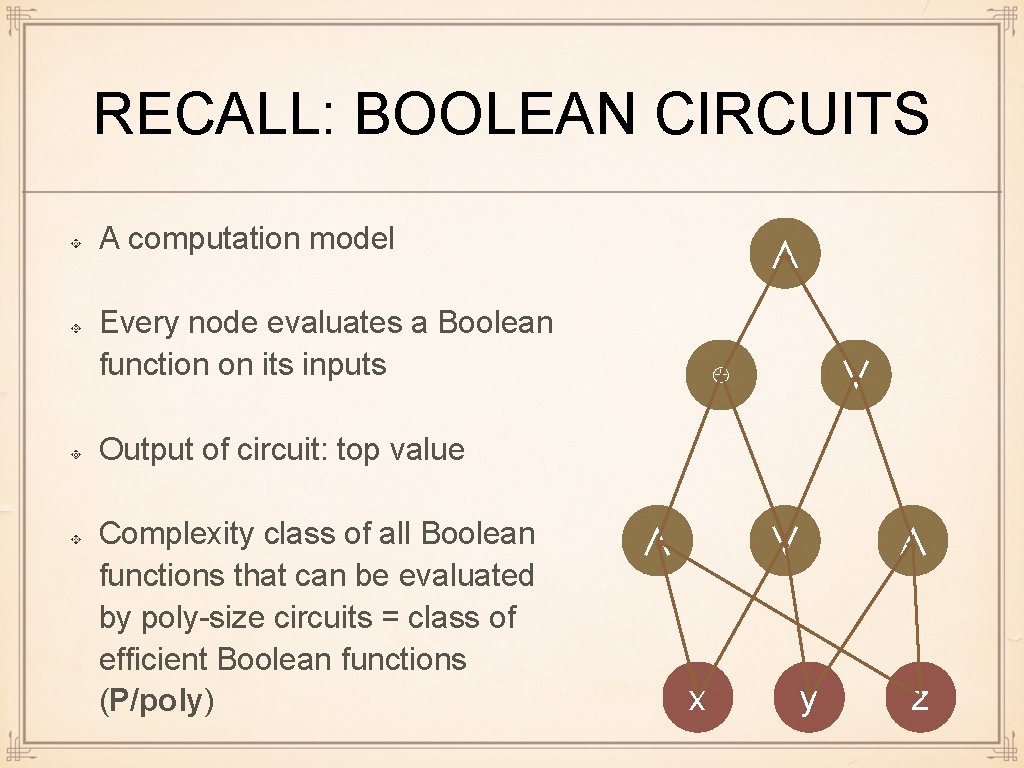
RECALL: BOOLEAN CIRCUITS A computation model ∧ Every node evaluates a Boolean function on its inputs ⊕ ∨ Output of circuit: top value Complexity class of all Boolean functions that can be evaluated by poly-size circuits = class of efficient Boolean functions (P/poly) ∧ ∨ x y ∧ z
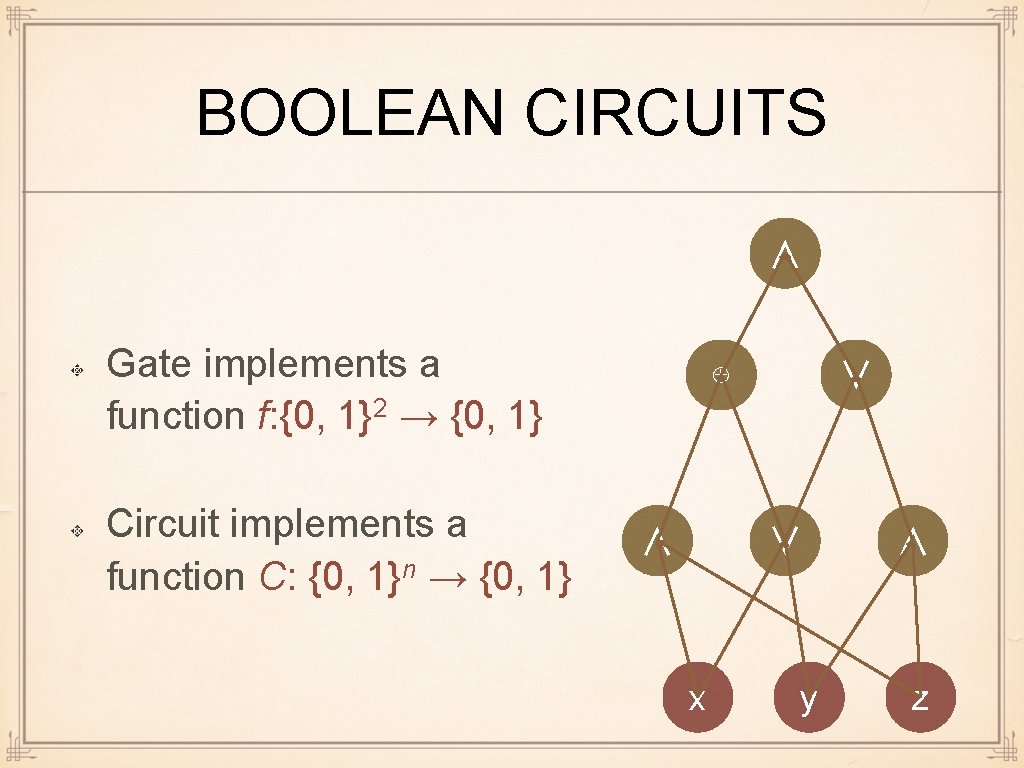
BOOLEAN CIRCUITS ∧ Gate implements a function f: {0, 1}2 → {0, 1} Circuit implements a function C: {0, 1}n → {0, 1} ⊕ ∧ ∨ ∨ x y ∧ z
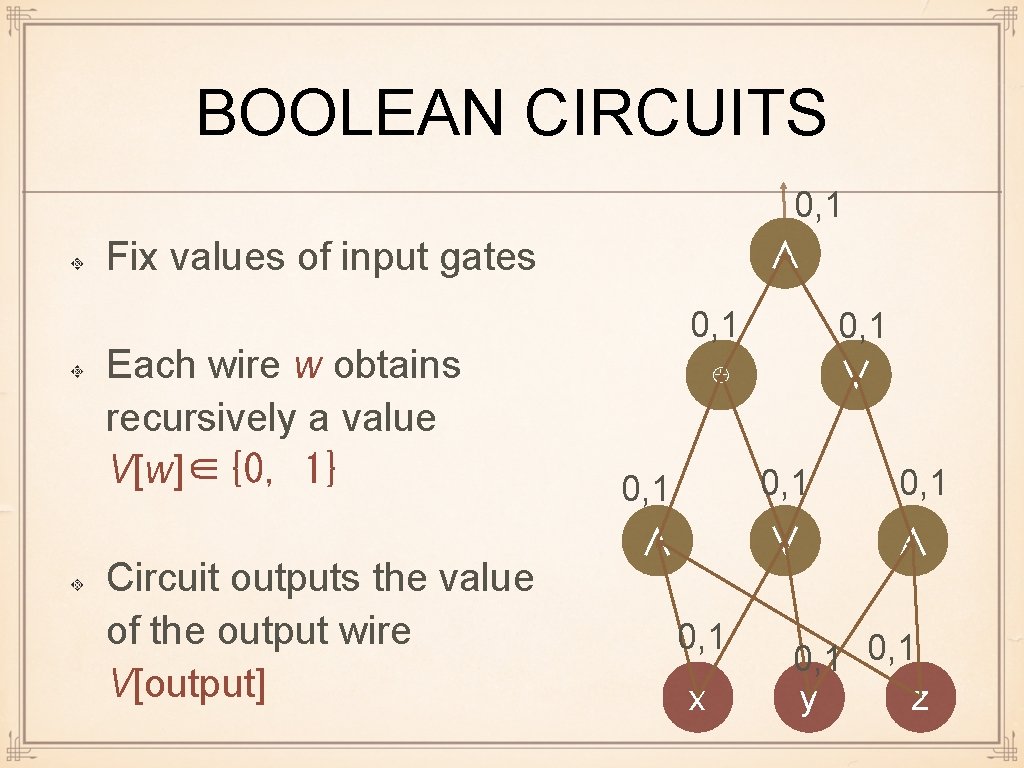
BOOLEAN CIRCUITS 0, 1 ∧ Fix values of input gates Each wire w obtains recursively a value V[w]∈{0, 1} Circuit outputs the value of the output wire V[output] 0, 1 ⊕ 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
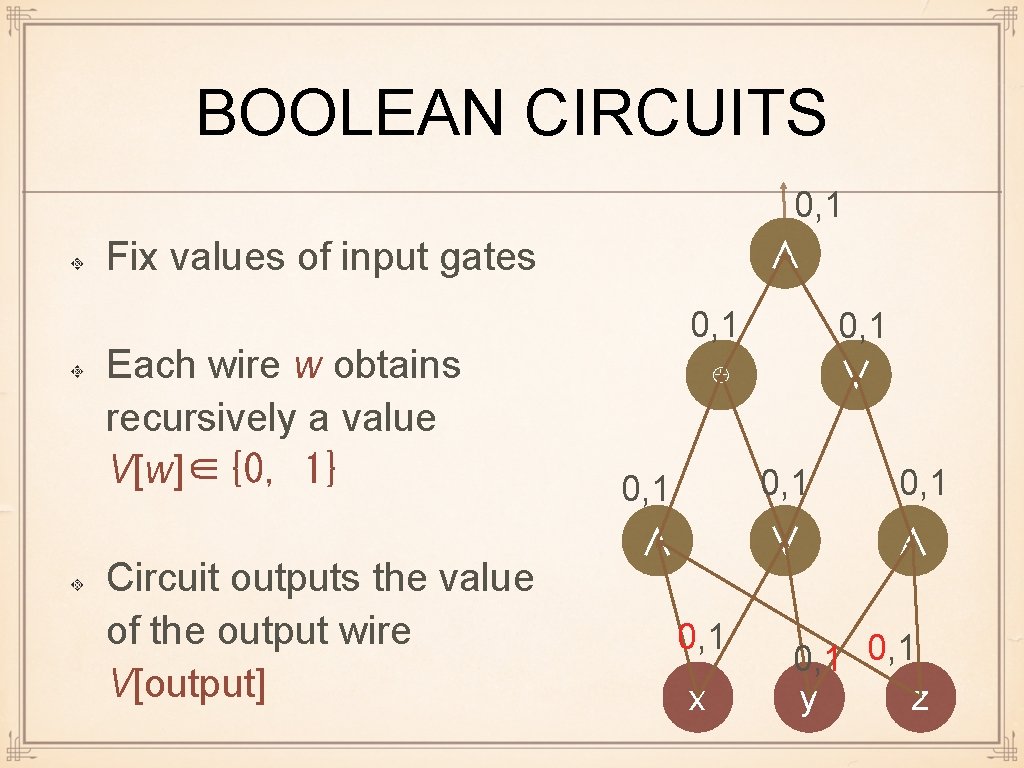
BOOLEAN CIRCUITS 0, 1 ∧ Fix values of input gates Each wire w obtains recursively a value V[w]∈{0, 1} Circuit outputs the value of the output wire V[output] 0, 1 ⊕ 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
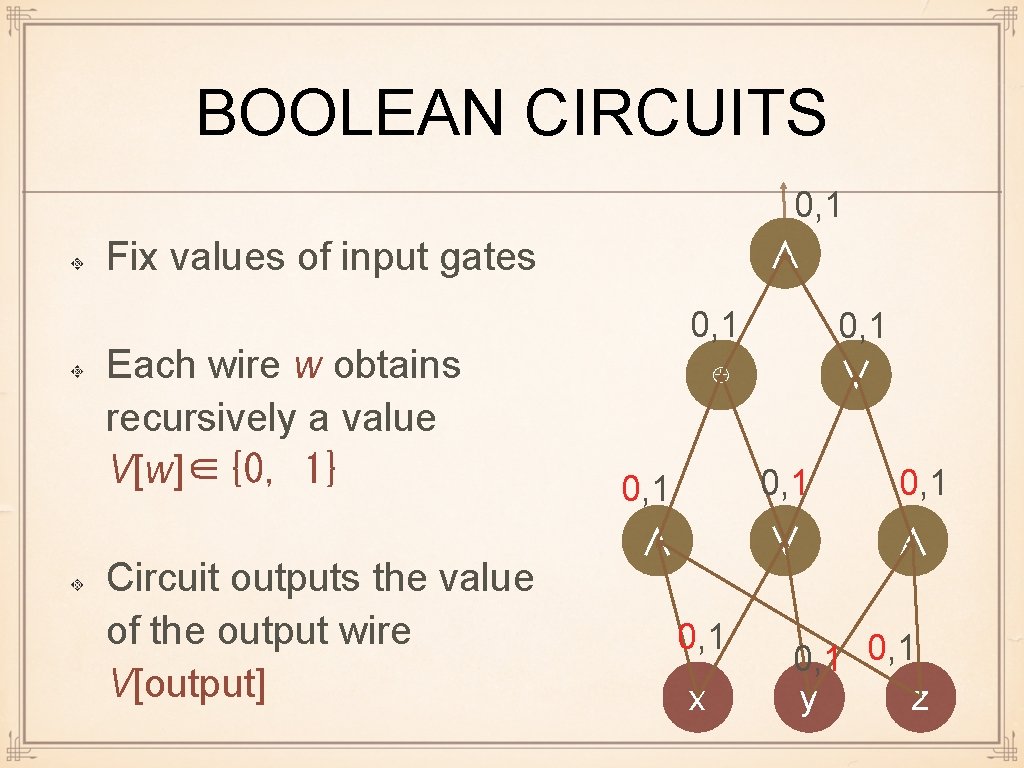
BOOLEAN CIRCUITS 0, 1 ∧ Fix values of input gates Each wire w obtains recursively a value V[w]∈{0, 1} Circuit outputs the value of the output wire V[output] 0, 1 ⊕ 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
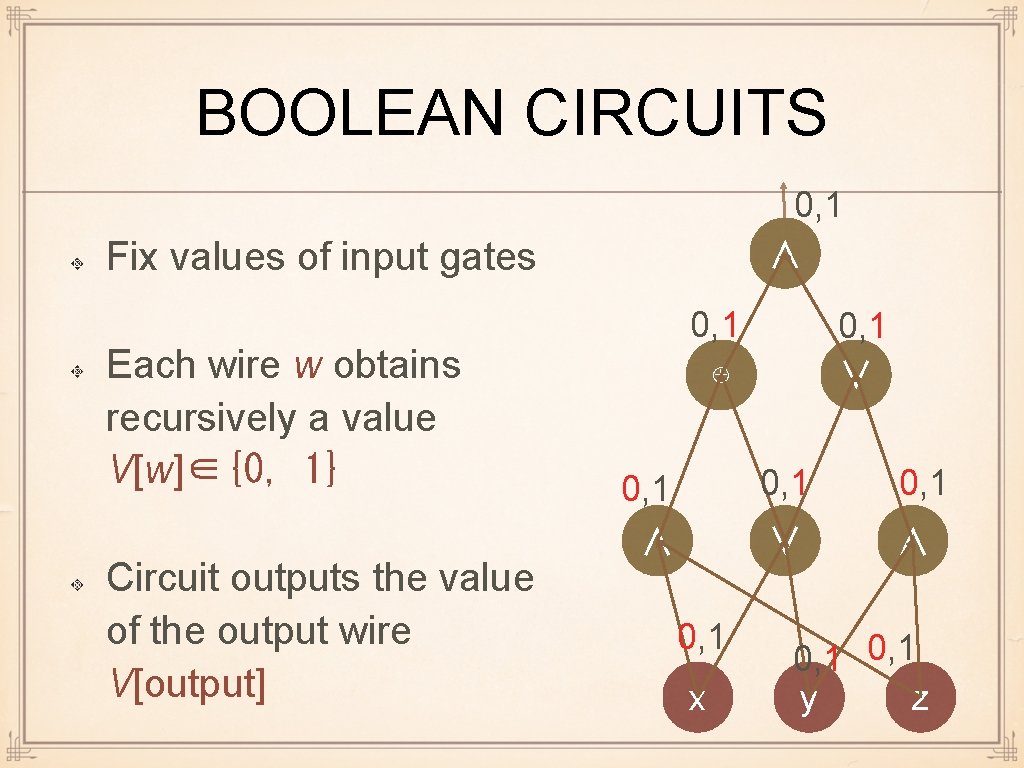
BOOLEAN CIRCUITS 0, 1 ∧ Fix values of input gates Each wire w obtains recursively a value V[w]∈{0, 1} Circuit outputs the value of the output wire V[output] 0, 1 ⊕ 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
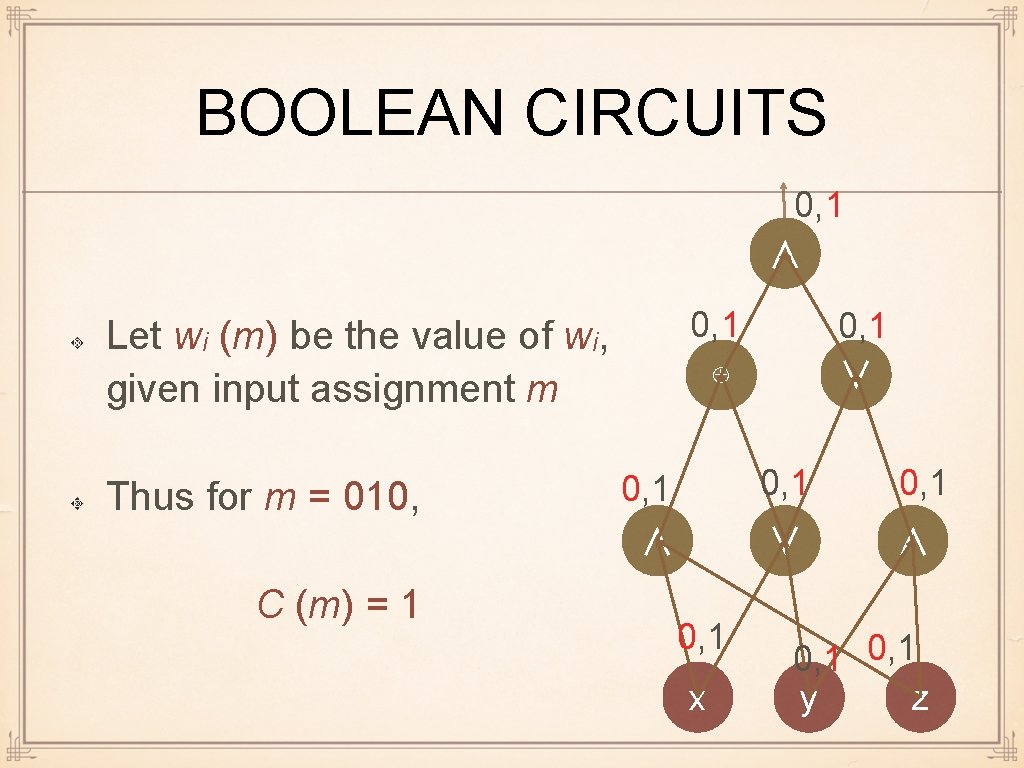
BOOLEAN CIRCUITS 0, 1 ∧ 0, 1 ⊕ Let wi (m) be the value of wi, given input assignment m Thus for m = 010, C (m) = 1 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
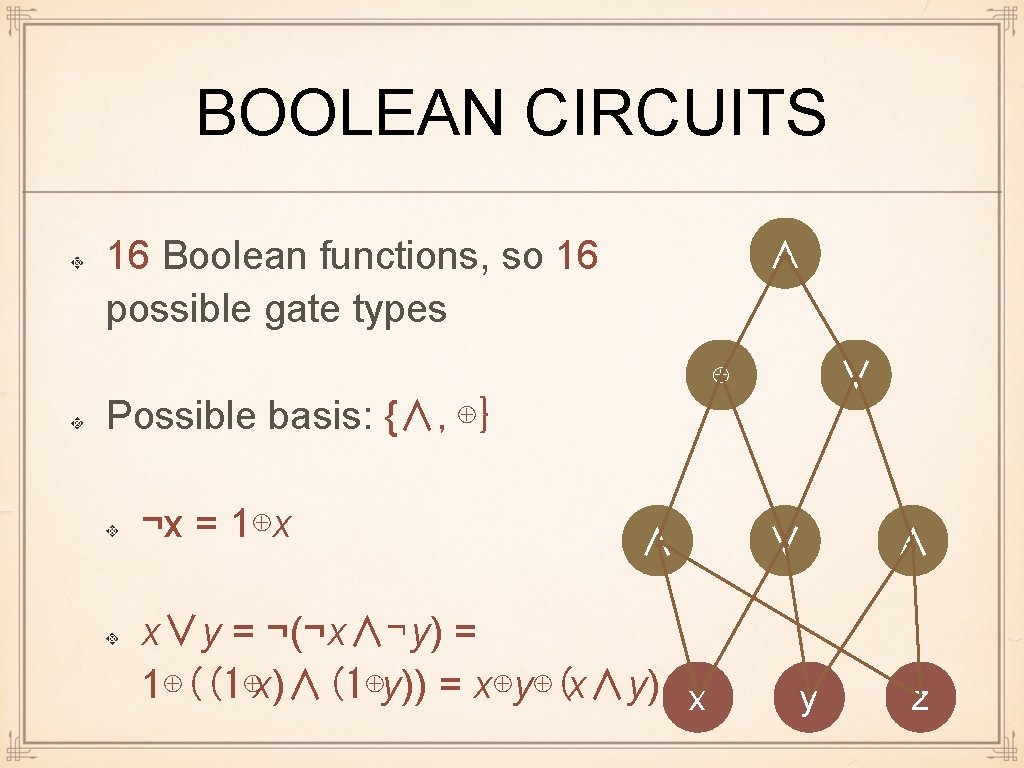
BOOLEAN CIRCUITS 16 Boolean functions, so 16 possible gate types ∧ ⊕ ∨ Possible basis: {∧, ⊕} ¬x = 1⊕x ∧ x∨y = ¬(¬x∧¬y) = 1⊕((1⊕x)∧(1⊕y)) = x⊕y⊕(x∧y) x ∨ y ∧ z
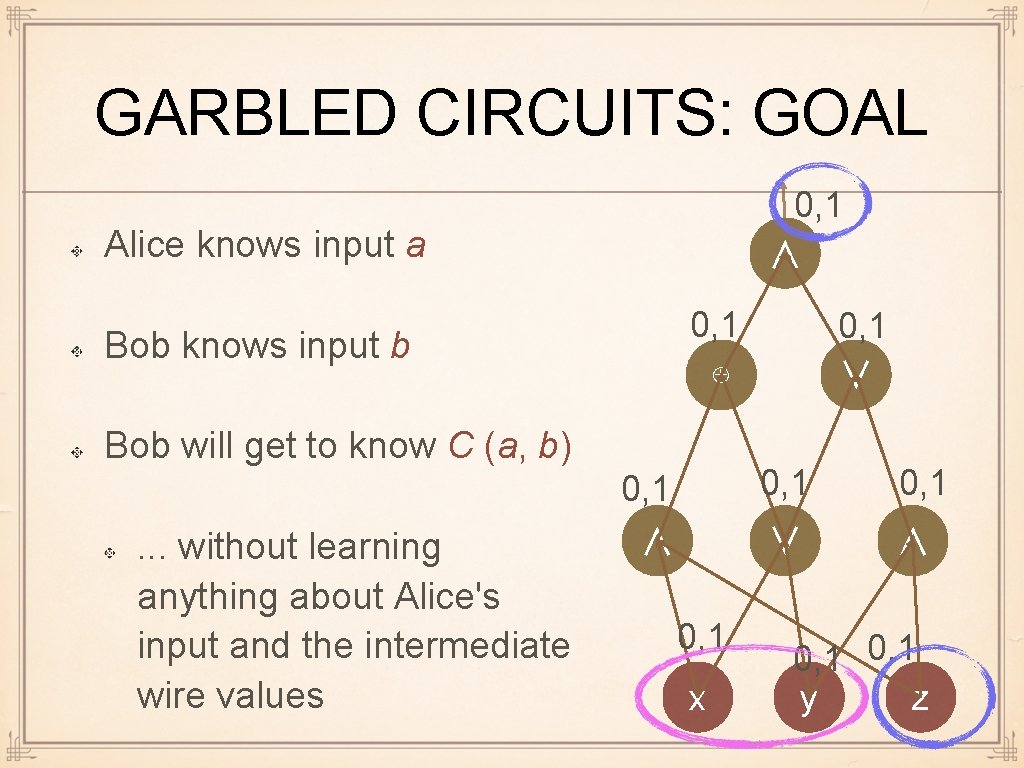
GARBLED CIRCUITS: GOAL 0, 1 ∧ Alice knows input a 0, 1 ⊕ Bob knows input b Bob will get to know C (a, b). . . without learning anything about Alice's input and the intermediate wire values 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
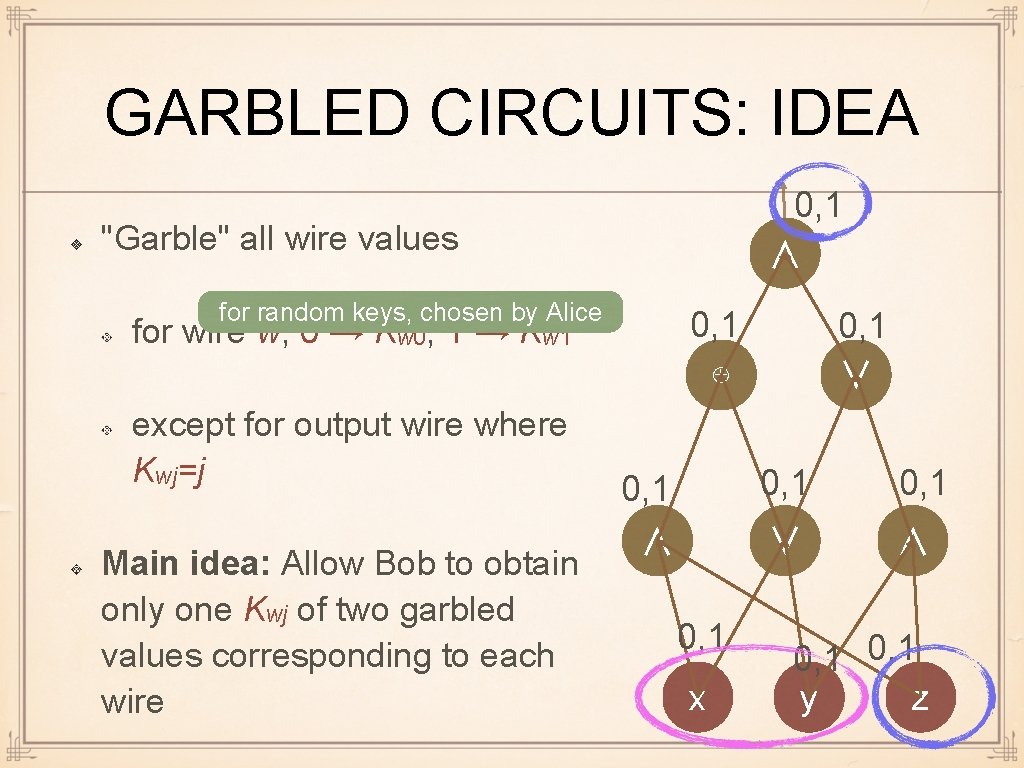
GARBLED CIRCUITS: IDEA 0, 1 ∧ "Garble" all wire values for random keys, chosen by Alice 0, 1 ⊕ for wire w, 0 → Kw 0, 1 → Kw 1 except for output wire where Kwj=j Main idea: Allow Bob to obtain only one Kwj of two garbled values corresponding to each wire 0, 1 ∧ 0, 1 x 0, 1 ∨ ∧ 0, 1 y z
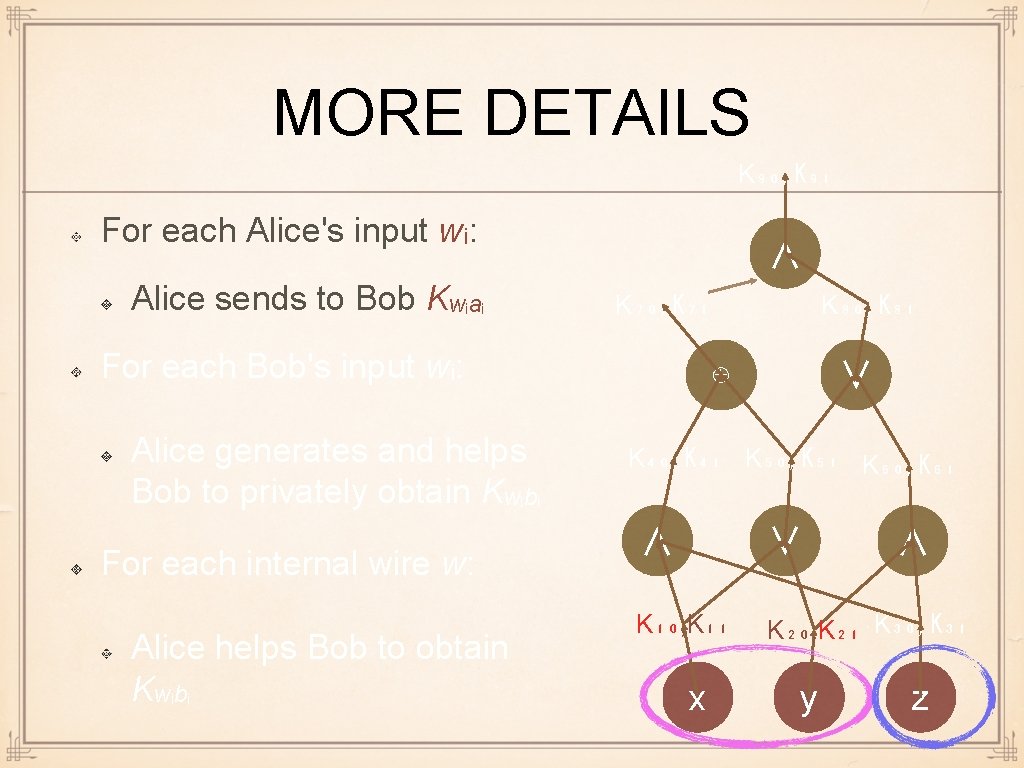
MORE DETAILS K₉₀, K₉₁ For each Alice's input wᵢ: Alice sends to Bob Kwᵢaᵢ ∧ K₇₀, K₇₁ For each Bob's input wᵢ: Alice generates and helps Bob to privately obtain Kwᵢbᵢ For each internal wire w: Alice helps Bob to obtain Kwᵢbᵢ K₈₀, K₈₁ ⊕ ∨ K₄₀, K₄₁ K₅₀, K₅₁ K₆₀, K₆₁ ∧ ∨ K₁₀, K₁₁ K₂₀, K₂₁ K₃₀, K₃₁ x y ∧ z
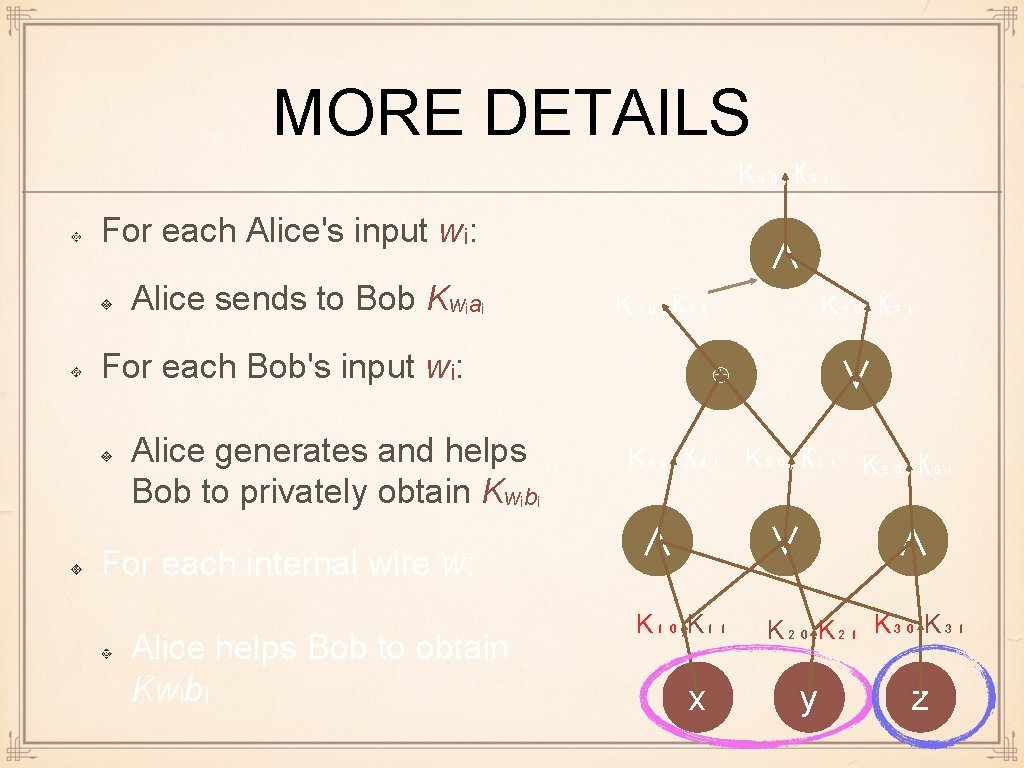
MORE DETAILS K₉₀, K₉₁ For each Alice's input wᵢ: Alice sends to Bob Kwᵢaᵢ ∧ K₇₀, K₇₁ For each Bob's input wᵢ: Alice generates and helps Bob to privately obtain Kwᵢbᵢ For each internal wire w: Alice helps Bob to obtain Kwᵢbᵢ K₈₀, K₈₁ ⊕ ∨ K₄₀, K₄₁ K₅₀, K₅₁ K₆₀, K₆₁ ∧ ∨ K₁₀, K₁₁ K₂₀, K₂₁ K₃₀, K₃₁ x y ∧ z
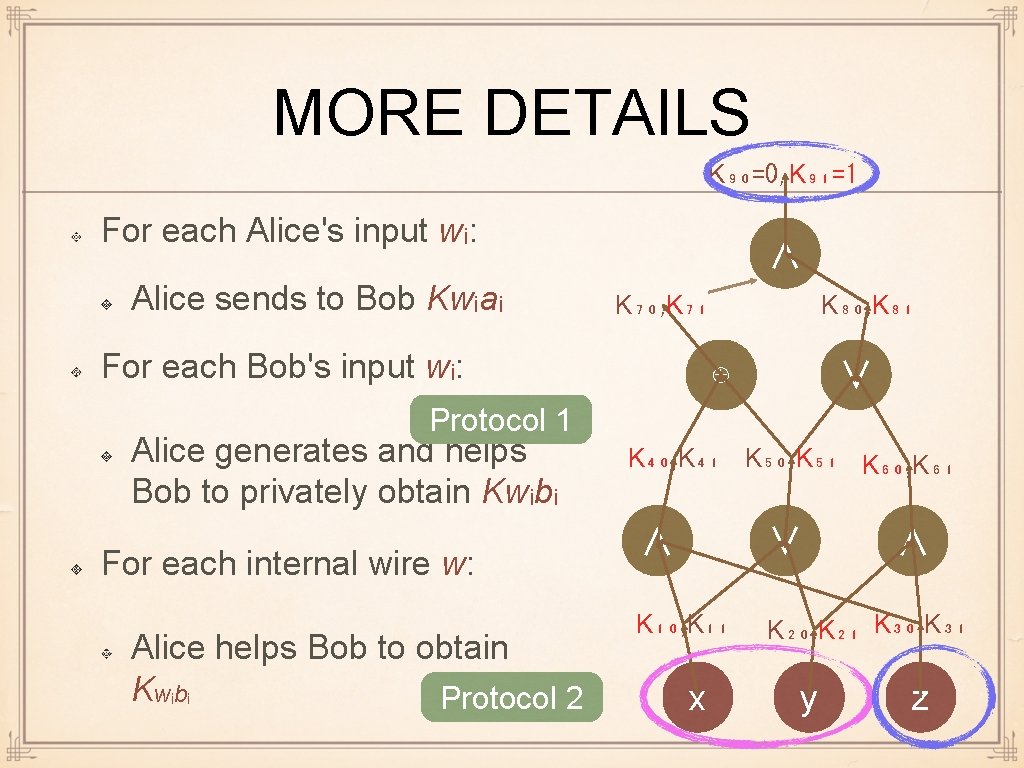
MORE DETAILS K₉₀=0, K₉₁=1 For each Alice's input wᵢ: Alice sends to Bob Kwᵢaᵢ ∧ K₇₀, K₇₁ For each Bob's input wᵢ: K₈₀, K₈₁ ⊕ ∨ Protocol 1 Alice generates and helps Bob to privately obtain Kwᵢbᵢ For each internal wire w: Alice helps Bob to obtain Kwᵢbᵢ Protocol 2 K₄₀, K₄₁ K₅₀, K₅₁ K₆₀, K₆₁ ∧ ∨ K₁₀, K₁₁ K₂₀, K₂₁ K₃₀, K₃₁ x y ∧ z
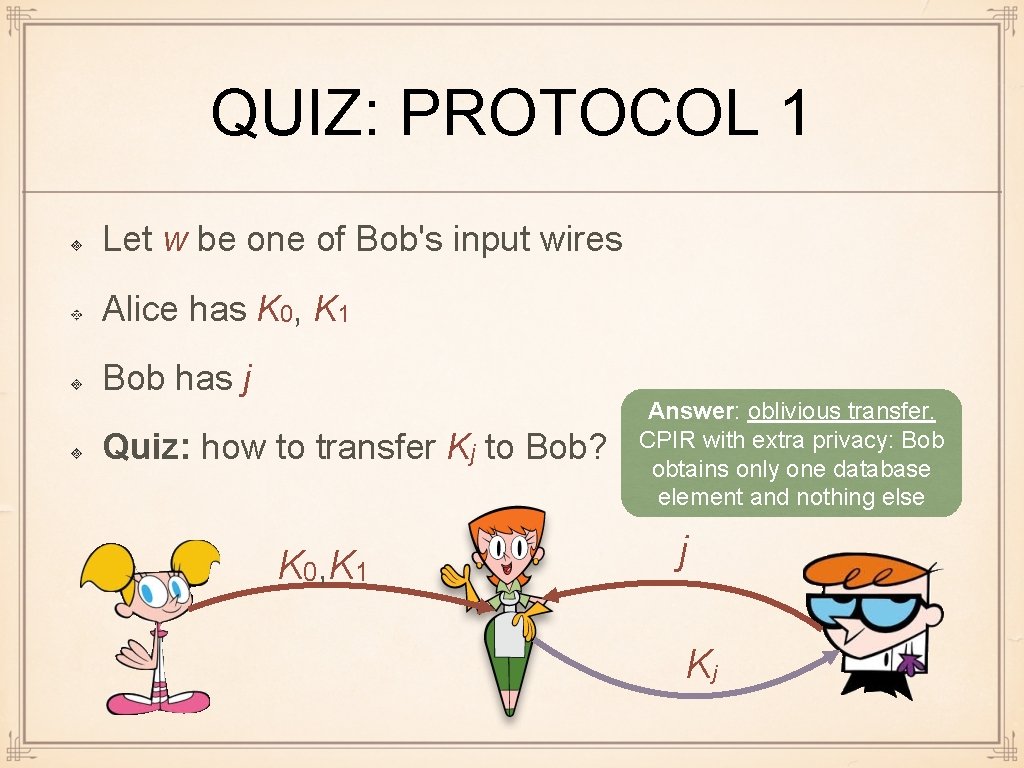
QUIZ: PROTOCOL 1 Let w be one of Bob's input wires Alice has K 0, K 1 Bob has j Quiz: how to transfer Kj to Bob? K 0, K 1 Answer: oblivious transfer. CPIR with extra privacy: Bob obtains only one database element and nothing else j Kj
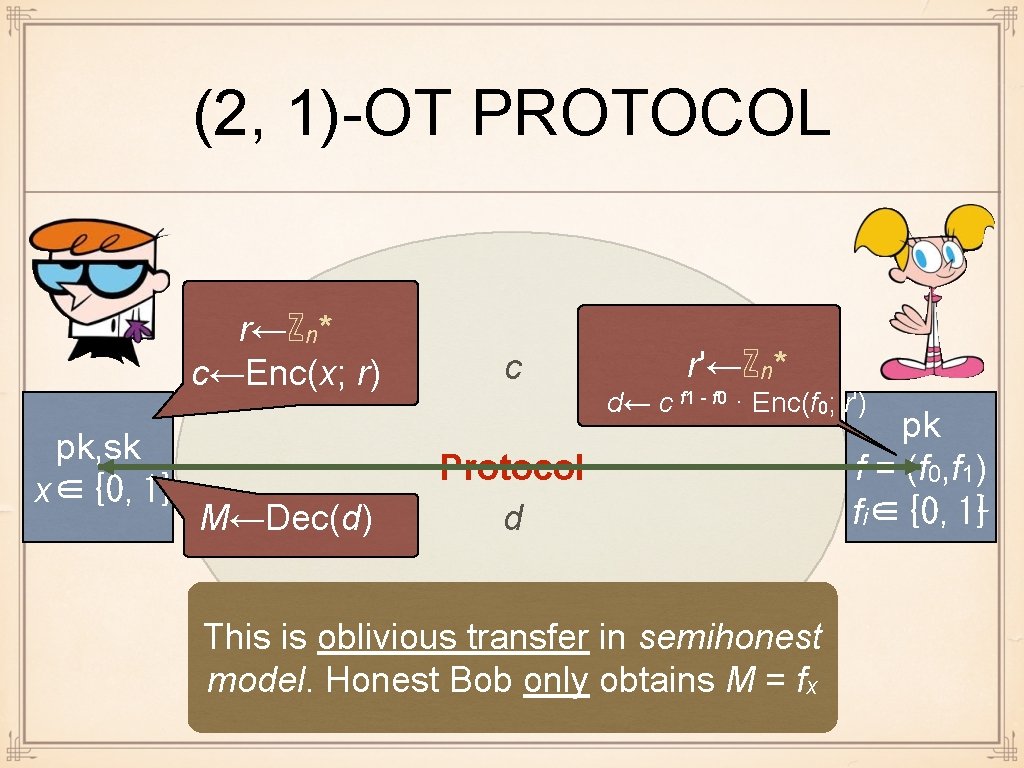
(2, 1)-OT PROTOCOL r←ℤn* c←Enc(x; r) pk, sk x∈{0, 1} M←Dec(d) c r'←ℤn* d← c f 1 - f 0 · Enc(f 0; r') Protocol d This is oblivious transfer in semihonest model. Honest Bob only obtains M = fx pk f = (f 0, f 1) fi∈{0, 1}L
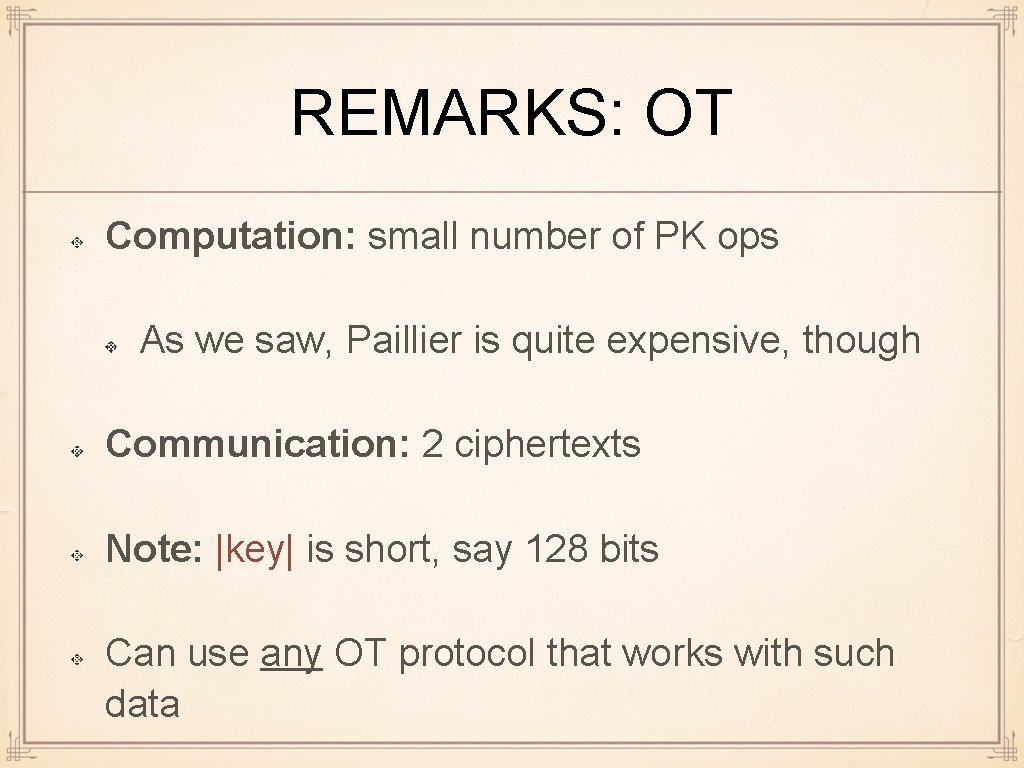
REMARKS: OT Computation: small number of PK ops As we saw, Paillier is quite expensive, though Communication: 2 ciphertexts Note: |key| is short, say 128 bits Can use any OT protocol that works with such data
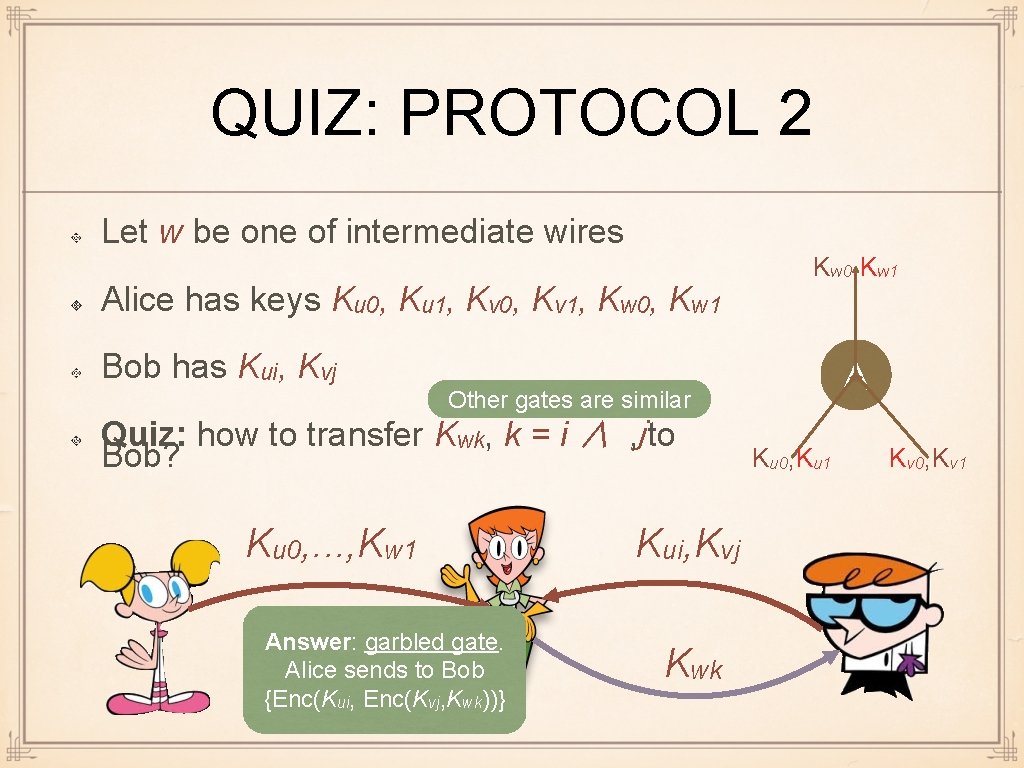
QUIZ: PROTOCOL 2 Let w be one of intermediate wires Alice has keys Ku 0, Ku 1, Kv 0, Kv 1, Kw 0, Kw 1 Bob has Kui, Kvj ∧ Other gates are similar Quiz: how to transfer Kwk, k = i ∧ , j to Bob? Ku 0, . . . , Kw 1 Answer: garbled gate. Alice sends to Bob {Enc(Kui, Enc(Kvj, Kwk))} Kui, Kvj Kwk Ku 0, Ku 1 Kv 0, Kv 1
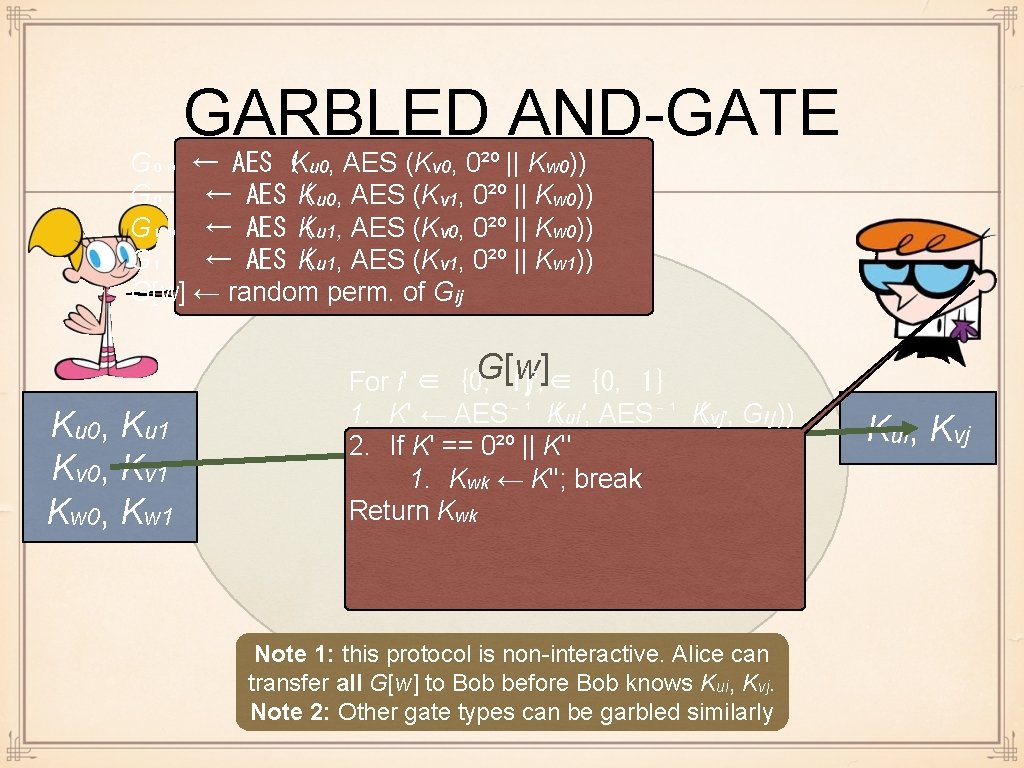
GARBLED AND-GATE G₀₀ ← AES (Ku 0, AES (Kv 0, 0²⁰ || Kw 0)) G₀₁ ← AES K ( u 0, AES (Kv 1, 0²⁰ || Kw 0)) G₁₀ ← AES K ( u 1, AES (Kv 0, 0²⁰ || Kw 0)) G₁₁ ← AES K ( u 1, AES (Kv 1, 0²⁰ || Kw 1)) G[w] ← random perm. of Gij Ku 0, Ku 1 Kv 0, Kv 1 Kw 0, Kw 1 G[w] For i' ∈ {0, 1}, j' ∈ {0, 1} 1. K' ← AES⁻¹ K ( ui', AES⁻¹ K ( vj', Gi'j')) 2. If K' == 0²⁰ || K'' 1. Protocol Kwk ← K''; break Return Kwk Note 1: this protocol is non-interactive. Alice can transfer all G[w] to Bob before Bob knows Kui, Kvj. Note 2: Other gate types can be garbled similarly Kui, Kvj
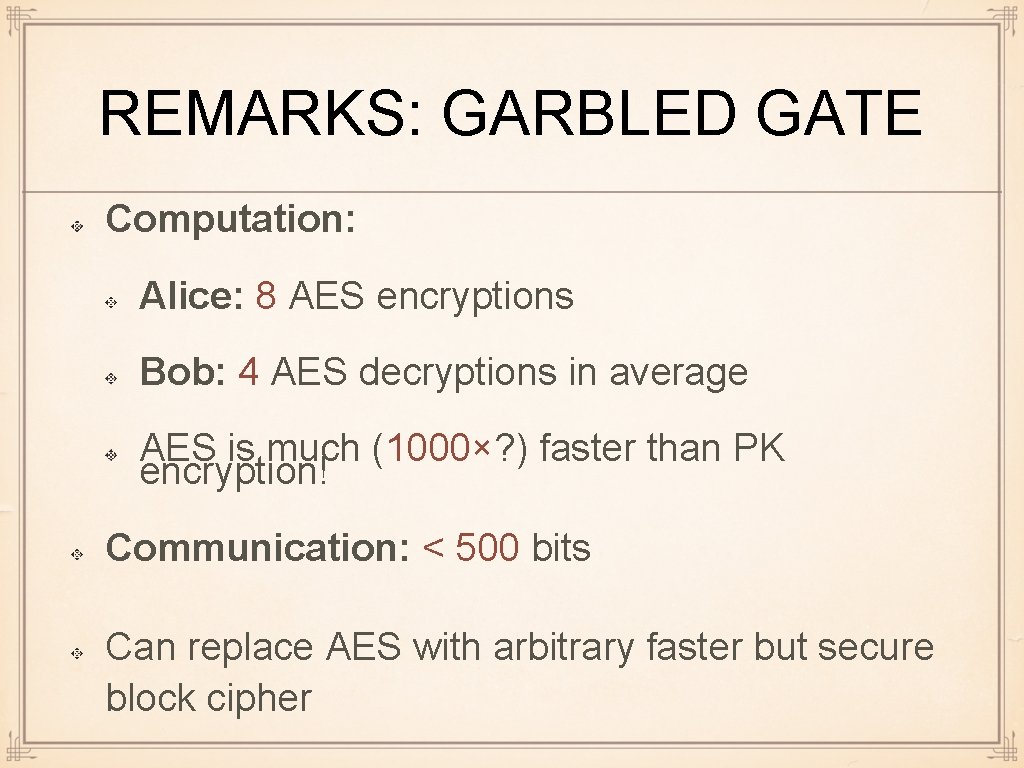
REMARKS: GARBLED GATE Computation: Alice: 8 AES encryptions Bob: 4 AES decryptions in average AES is much (1000×? ) faster than PK encryption! Communication: < 500 bits Can replace AES with arbitrary faster but secure block cipher
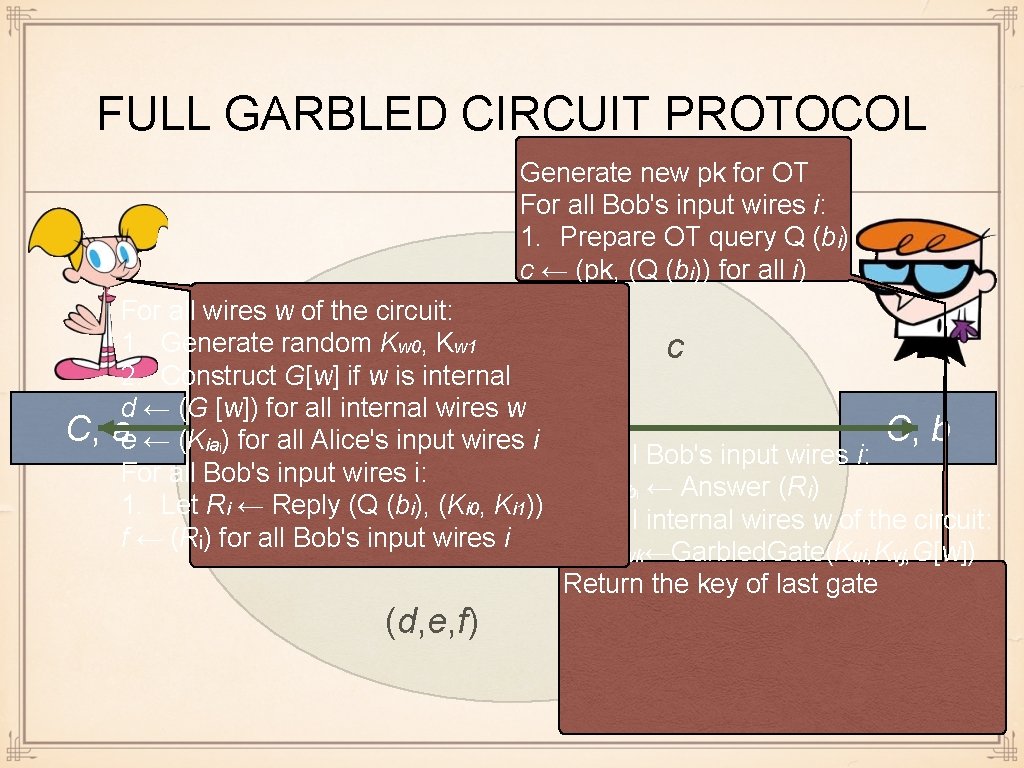
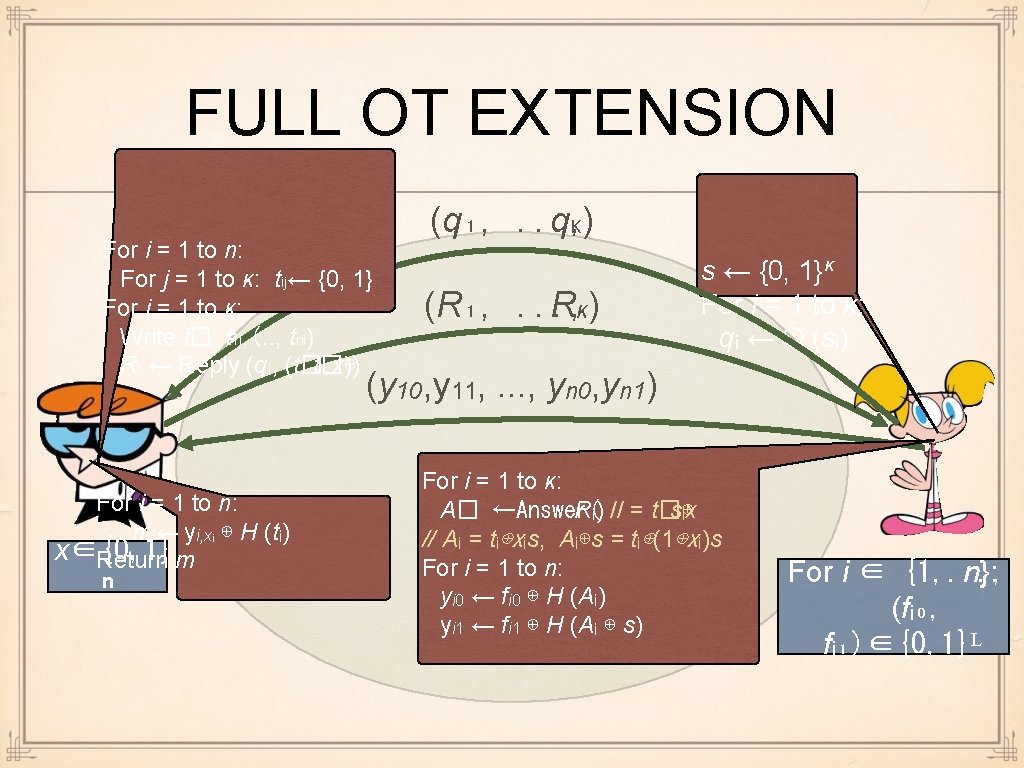
FULL GARBLED CIRCUIT PROTOCOL Generate new pk for OT For all Bob's input wires i: 1. Prepare OT query Q (bi) c ← (pk, (Q (bi)) for all i) C, For all wires w of the circuit: 1. Generate random Kw 0, Kw 1 c 2. Construct G[w] if w is internal d ← (G [w]) for all internal wires w ae ← (Kiaᵢ) for all Alice's input wires i C, b For all Bob's input wires i: Protocol 1. Kibᵢ ← Answer (Ri) 1. Let Ri ← Reply (Q (bi), (Ki 0, Ki 1)) For all internal wires w of the circuit: f ← (Rᵢ) for all Bob's input wires i 1. Kwk←Garbled. Gate(Kui, Kvj, G[w]) Return the key of last gate (d, e, f)
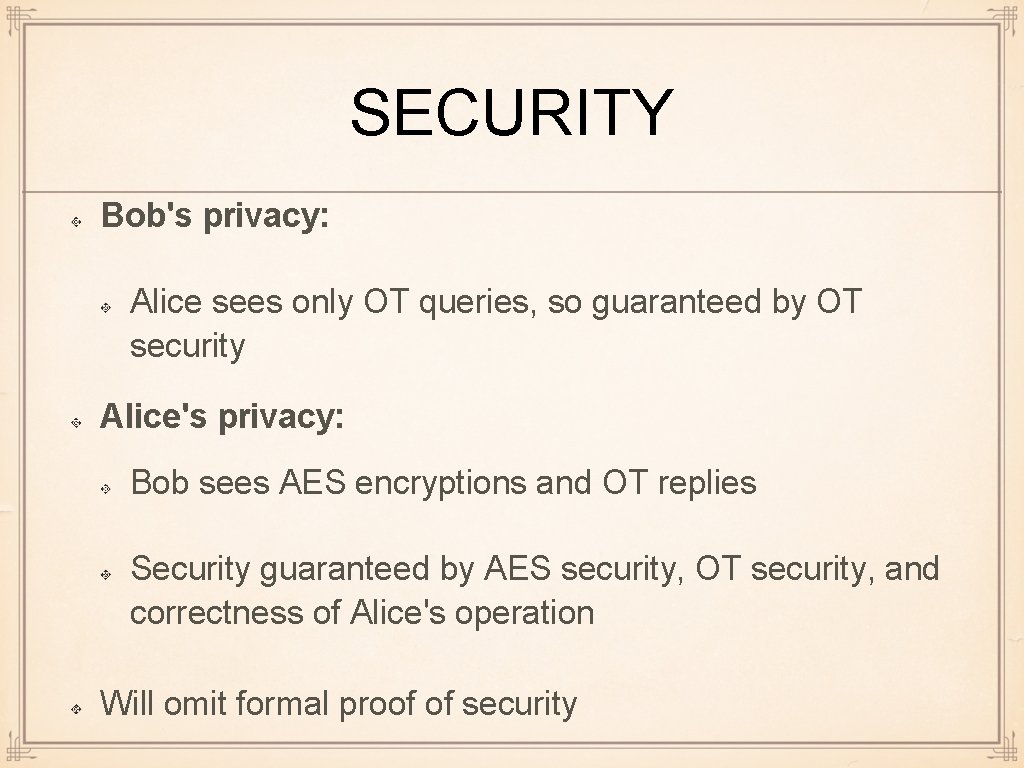
SECURITY Bob's privacy: Alice sees only OT queries, so guaranteed by OT security Alice's privacy: Bob sees AES encryptions and OT replies Security guaranteed by AES security, OT security, and correctness of Alice's operation Will omit formal proof of security
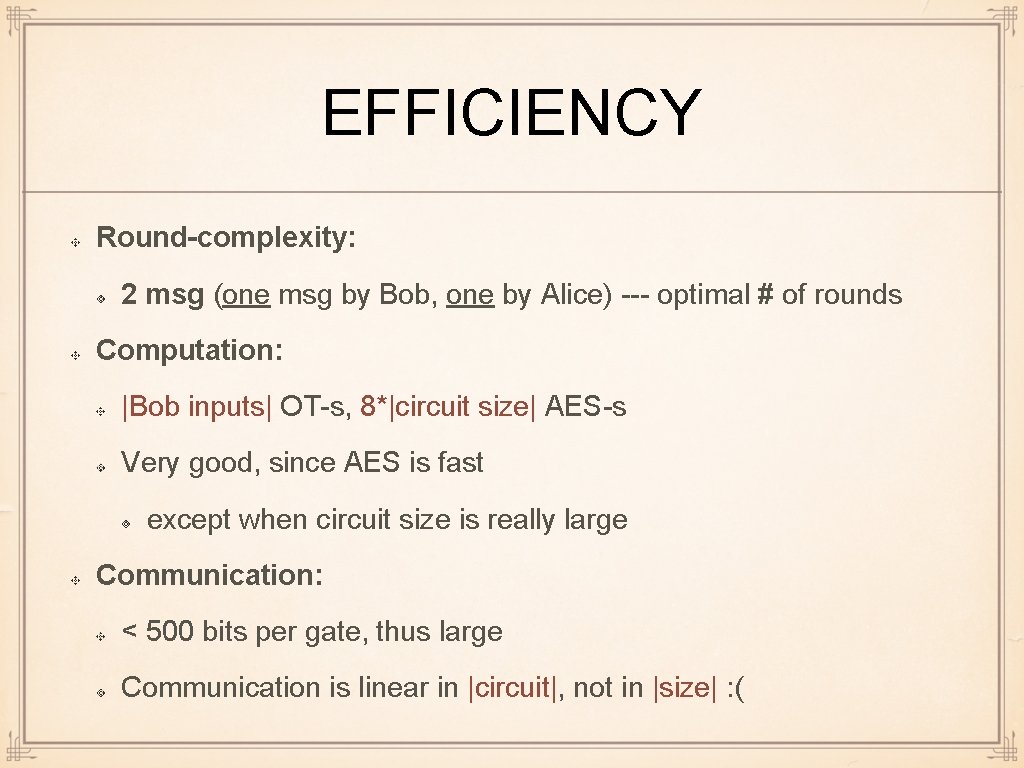
EFFICIENCY Round-complexity: 2 msg (one msg by Bob, one by Alice) --- optimal # of rounds Computation: |Bob inputs| OT-s, 8*|circuit size| AES-s Very good, since AES is fast except when circuit size is really large Communication: < 500 bits per gate, thus large Communication is linear in |circuit|, not in |size| : (
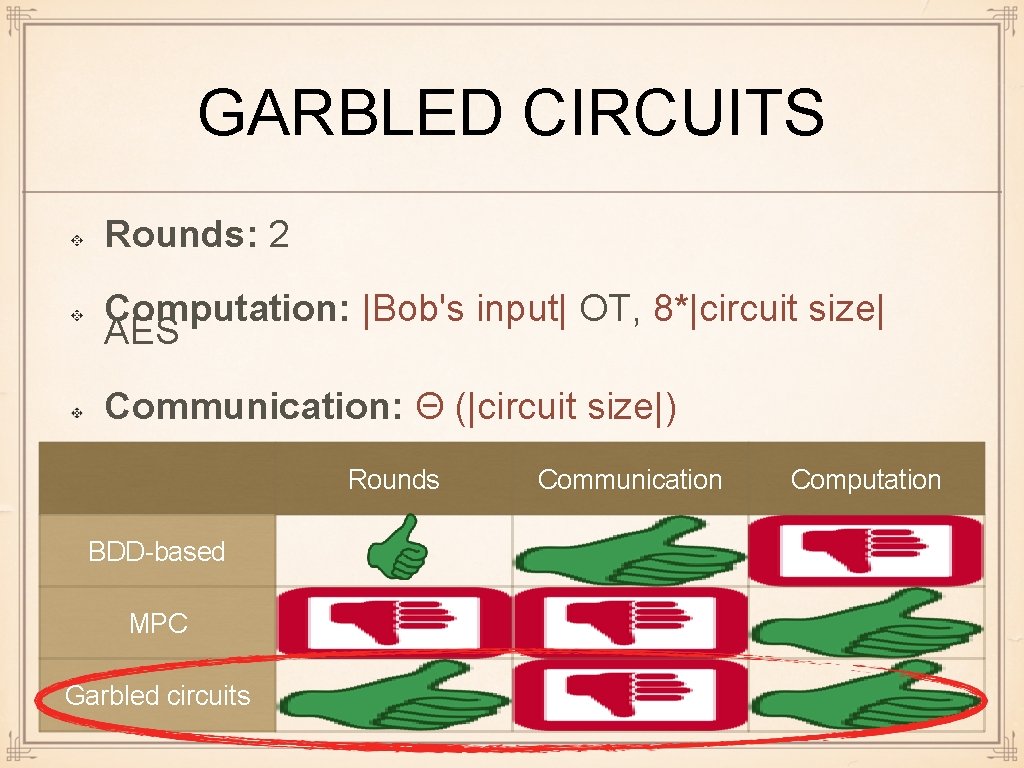
GARBLED CIRCUITS Rounds: 2 Computation: |Bob's input| OT, 8*|circuit size| AES Communication: Θ (|circuit size|) Rounds BDD-based MPC Garbled circuits Communication Computation
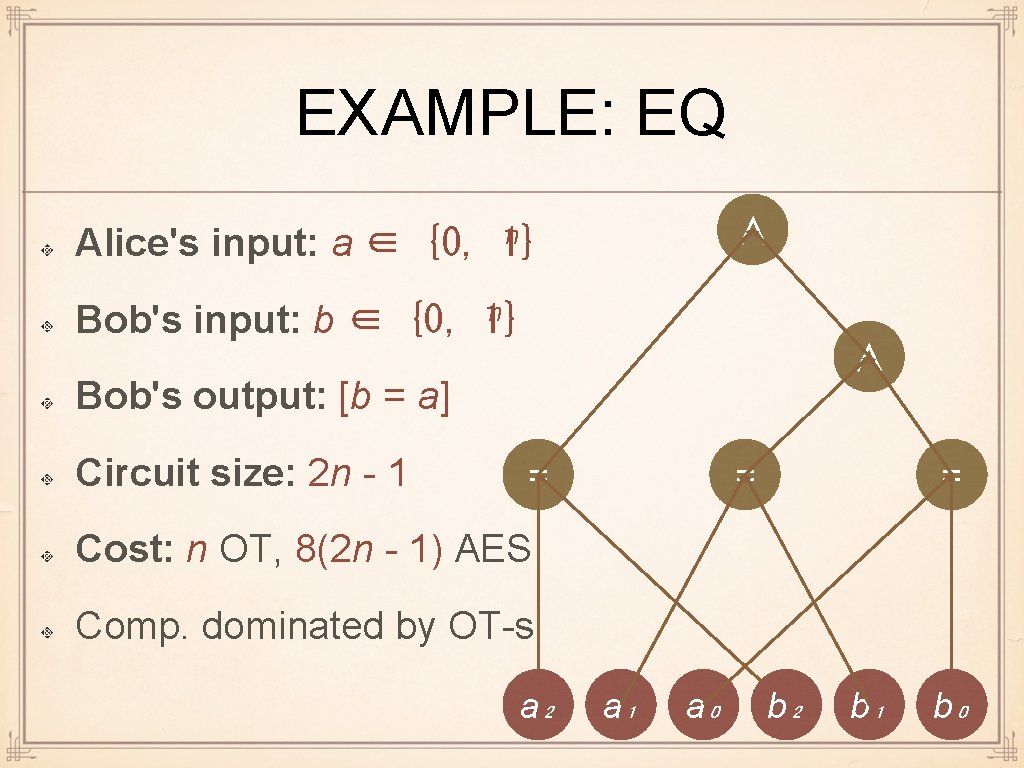
EXAMPLE: EQ Alice's input: a ∈ {0, ∧ n 1} n Bob's input: b ∈ {0, 1} ∧ Bob's output: [b = a] Circuit size: 2 n - 1 = = = Cost: n OT, 8(2 n - 1) AES Comp. dominated by OT-s a₂ a₁ a₀ b₂ b₁ b₀
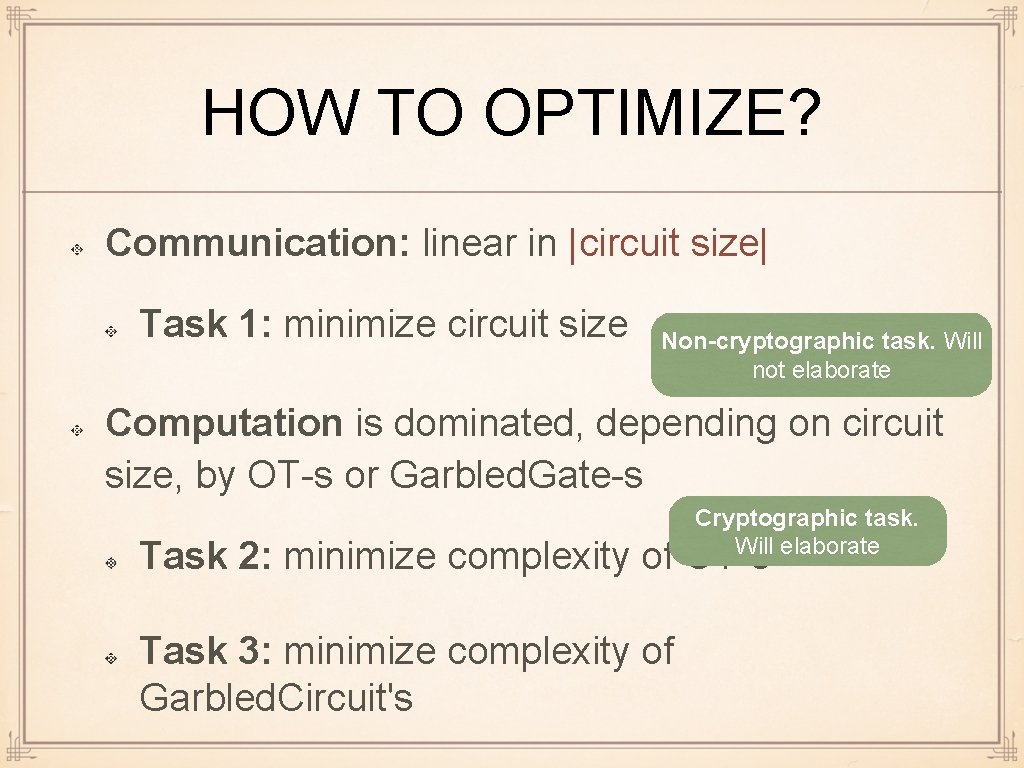
HOW TO OPTIMIZE? Communication: linear in |circuit size| Task 1: minimize circuit size Non-cryptographic task. Will not elaborate Computation is dominated, depending on circuit size, by OT-s or Garbled. Gate-s Cryptographic task. Will elaborate Task 2: minimize complexity of OT-s Task 3: minimize complexity of Garbled. Circuit's
OT COMPLEXITY MINIMIZATION Use more efficient (2, 1)-OT Paillier → Elgamal, but can't go much faster OT extension: we need many OT-s need to reduce the number expensive operations
OT EXTENSION If input length n is large: need to implement n >> κ OT-s Recall: κ is the security parameter Question: Can we implement n OT-s by using n "cheap operations" and << n OT-s?
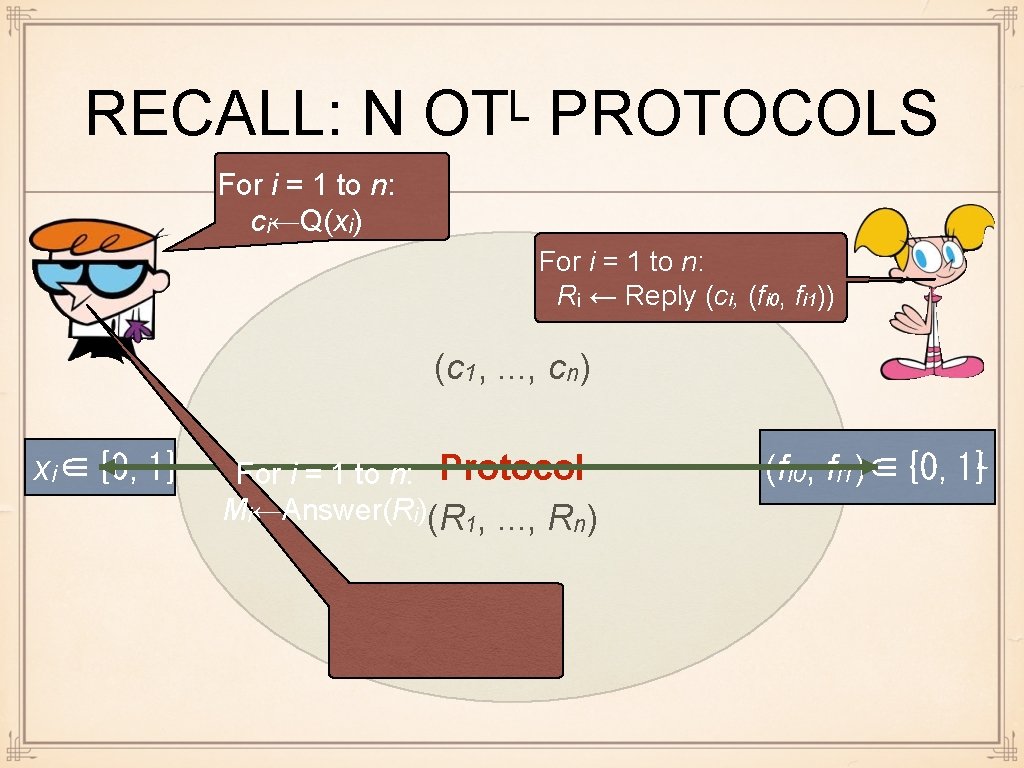
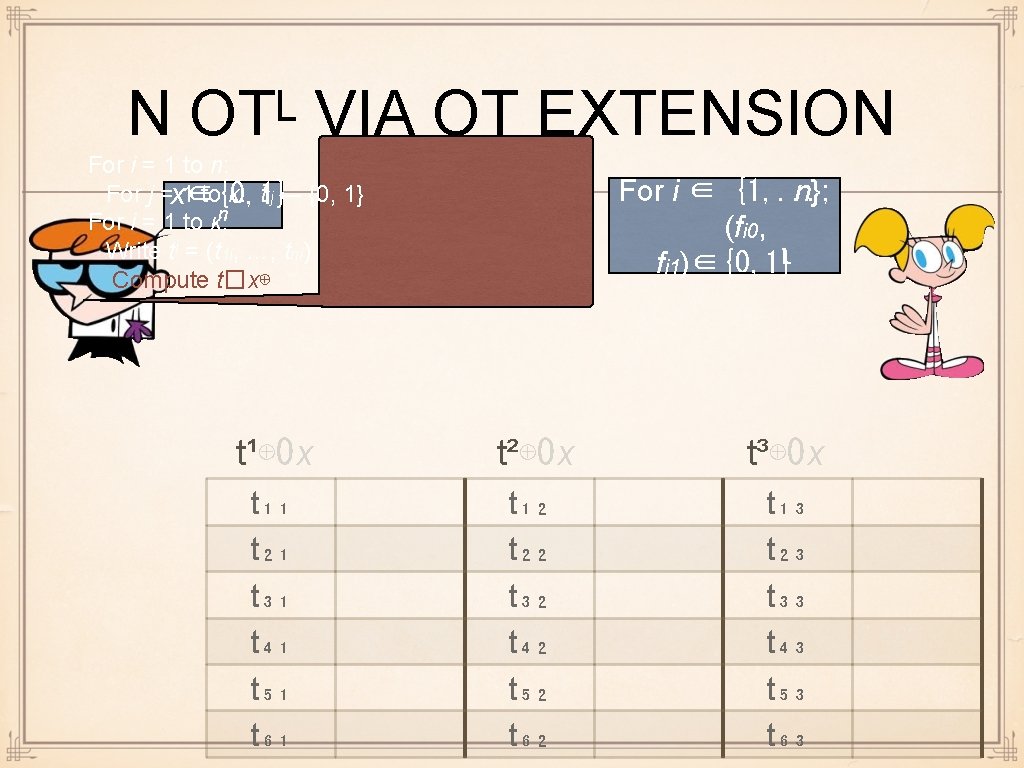
RECALL: N OTᴸ PROTOCOLS For i = 1 to n: ci←Q(xi) For i = 1 to n: Rᵢ ← Reply (ci, (fi 0, fi 1)) (c 1, . . . , cn) xi∈{0, 1} For i = 1 to n: Protocol Mi←Answer(Ri)(R 1, . . . , Rn) (fi 0, fi 1)∈{0, 1}L
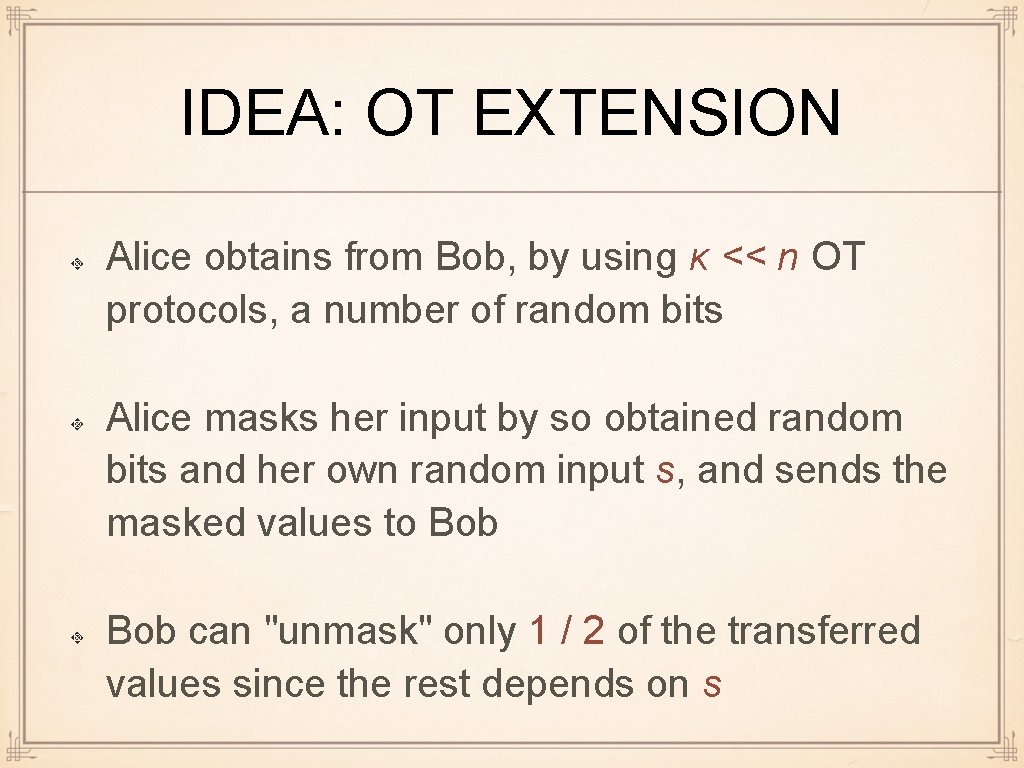
IDEA: OT EXTENSION Alice obtains from Bob, by using κ << n OT protocols, a number of random bits Alice masks her input by so obtained random bits and her own random input s, and sends the masked values to Bob can "unmask" only 1 / 2 of the transferred values since the rest depends on s
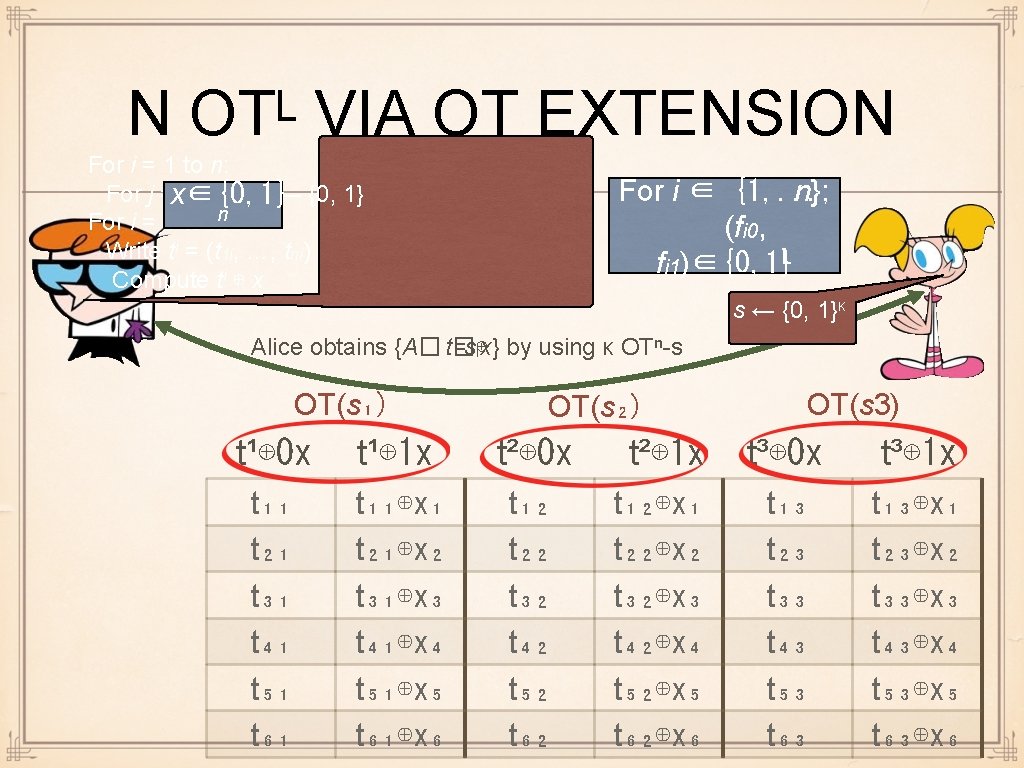
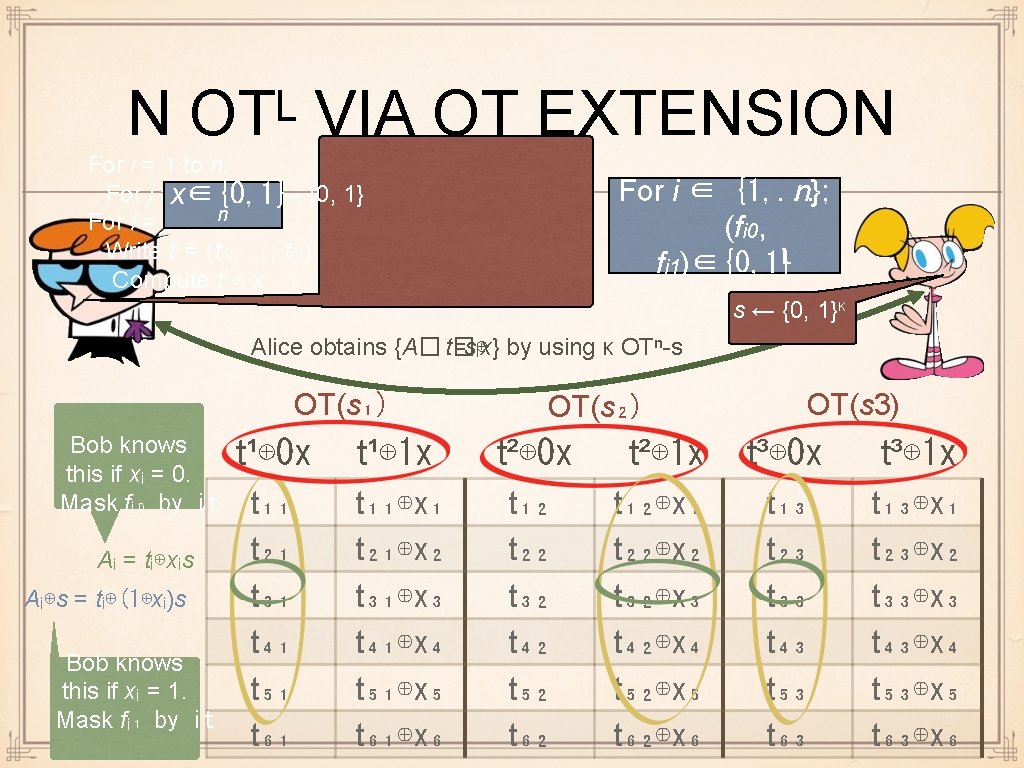
SECURITY Alice's privacy: Bob sees qi and mi =. . . + H (. . . ) Alice's privacy guaranteed by OT privacy and security of H (will not elaborate on the latter) Bob's privacy: Alice sees {ti ⊕ si x}i - no information revealed about x since ti is random
EFFICIENCY Alice: κ OT-s of n-bit strings, 2 n H-s Bob: κ OT-s of n-bit strings, n H-s If κ << n ≈ |circuit size| and Cost(H) << Cost(OT): huge benefit ⇒ OT dominates the cost of GC OT extension makes GC many times faster
G. GATE OPTIMIZATION, 1 Use a more efficient symmetric encryption scheme gives speedup, but not certain how much AES is implemented in Intel hardware Replace AES with a hash function use Bitcoin hardware
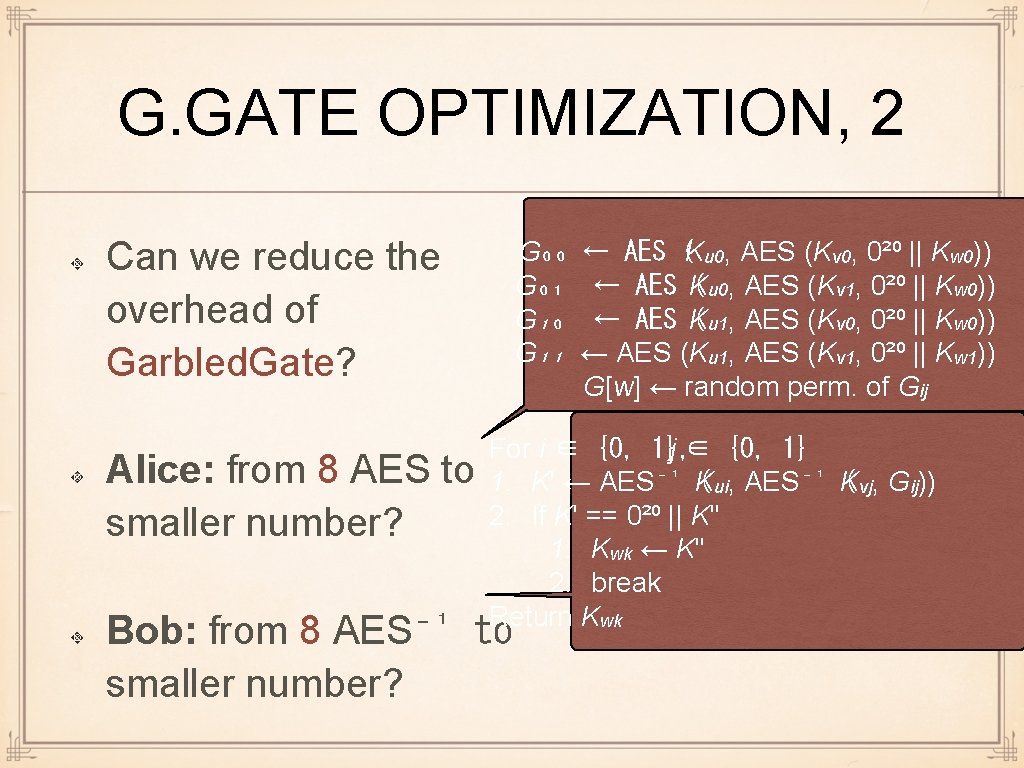
G. GATE OPTIMIZATION, 2 Can we reduce the overhead of Garbled. Gate? Alice: from 8 AES to smaller number? G₀₀ G₀₁ G₁₀ G₁₁ ← AES (Ku 0, AES (Kv 0, 0²⁰ || Kw 0)) ← AES K ( u 0, AES (Kv 1, 0²⁰ || Kw 0)) ← AES K ( u 1, AES (Kv 0, 0²⁰ || Kw 0)) ← AES (Ku 1, AES (Kv 1, 0²⁰ || Kw 1)) G[w] ← random perm. of Gij For i ∈ {0, 1}, j ∈ {0, 1} 1. K' ← AES⁻¹ K ( ui, AES⁻¹ K ( vj, Gij)) 2. If K' == 0²⁰ || K'' 1. Kwk ← K'' 2. break Return Kwk Bob: from 8 AES⁻¹ to smaller number?
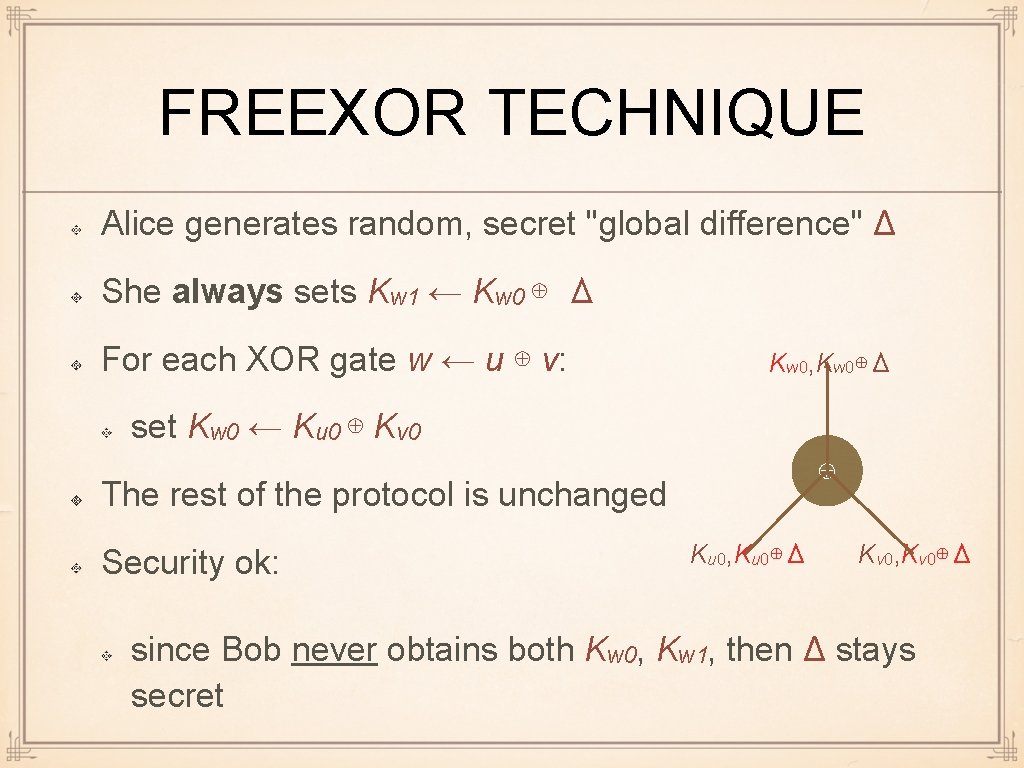
FREEXOR TECHNIQUE Alice generates random, secret "global difference" Δ She always sets Kw 1 ← Kw 0 ⊕ Δ For each XOR gate w ← u ⊕ v: Kw 0, Kw 0⊕Δ set Kw 0 ← Ku 0 ⊕ Kv 0 ⊕ The rest of the protocol is unchanged Security ok: Ku 0, Ku 0⊕Δ Kv 0, Kv 0⊕Δ since Bob never obtains both Kw 0, Kw 1, then Δ stays secret
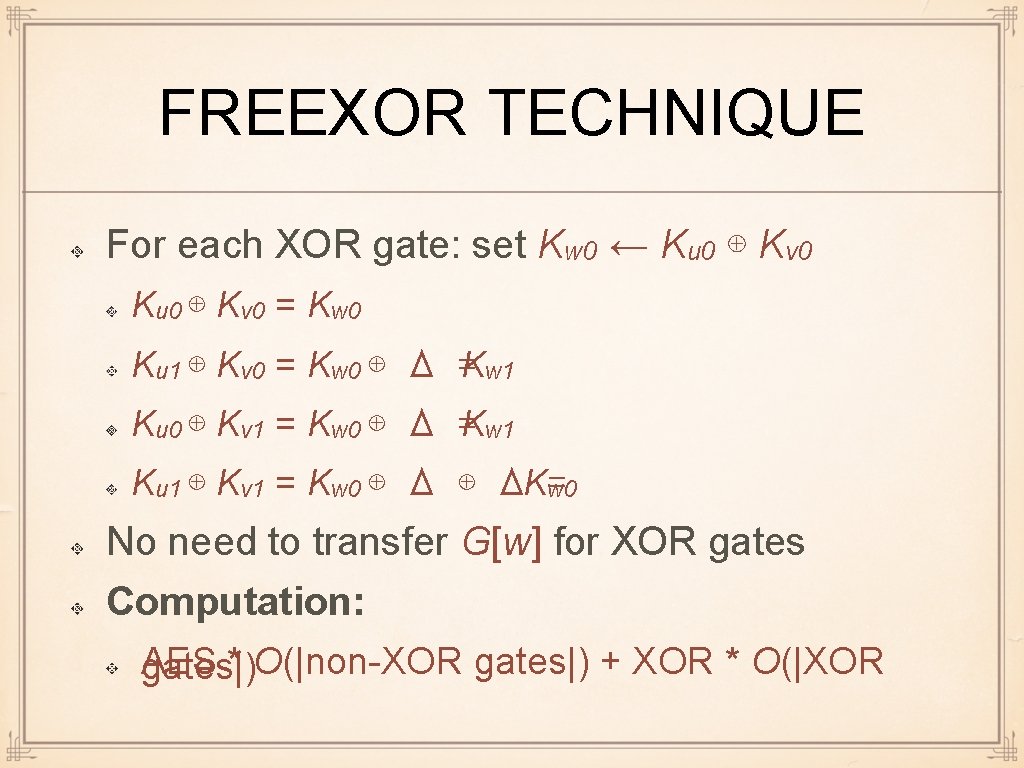
FREEXOR TECHNIQUE For each XOR gate: set Kw 0 ← Ku 0 ⊕ Kv 0 = Kw 0 Ku 1 ⊕ Kv 0 = Kw 0 ⊕ Δ =Kw 1 Ku 0 ⊕ Kv 1 = Kw 0 ⊕ Δ =Kw 1 Ku 1 ⊕ Kv 1 = Kw 0 ⊕ ΔKw 0 = No need to transfer G[w] for XOR gates Computation: AES * O(|non-XOR gates|) + XOR * O(|XOR gates|)
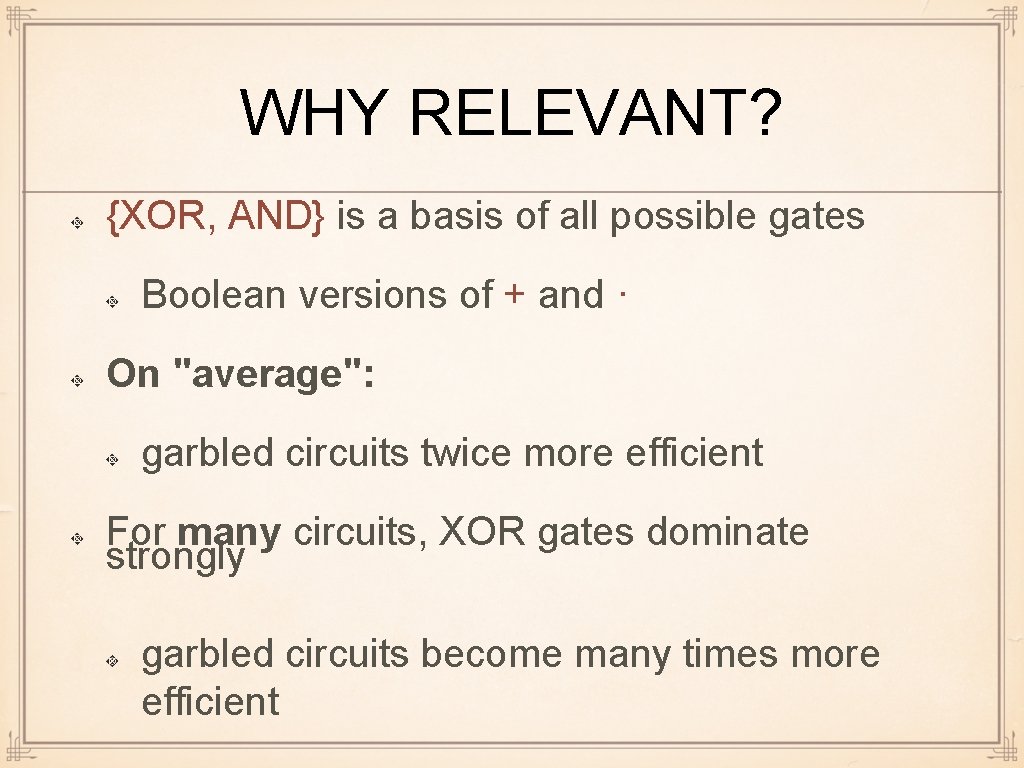
WHY RELEVANT? {XOR, AND} is a basis of all possible gates Boolean versions of + and · On "average": garbled circuits twice more efficient For many circuits, XOR gates dominate strongly garbled circuits become many times more efficient
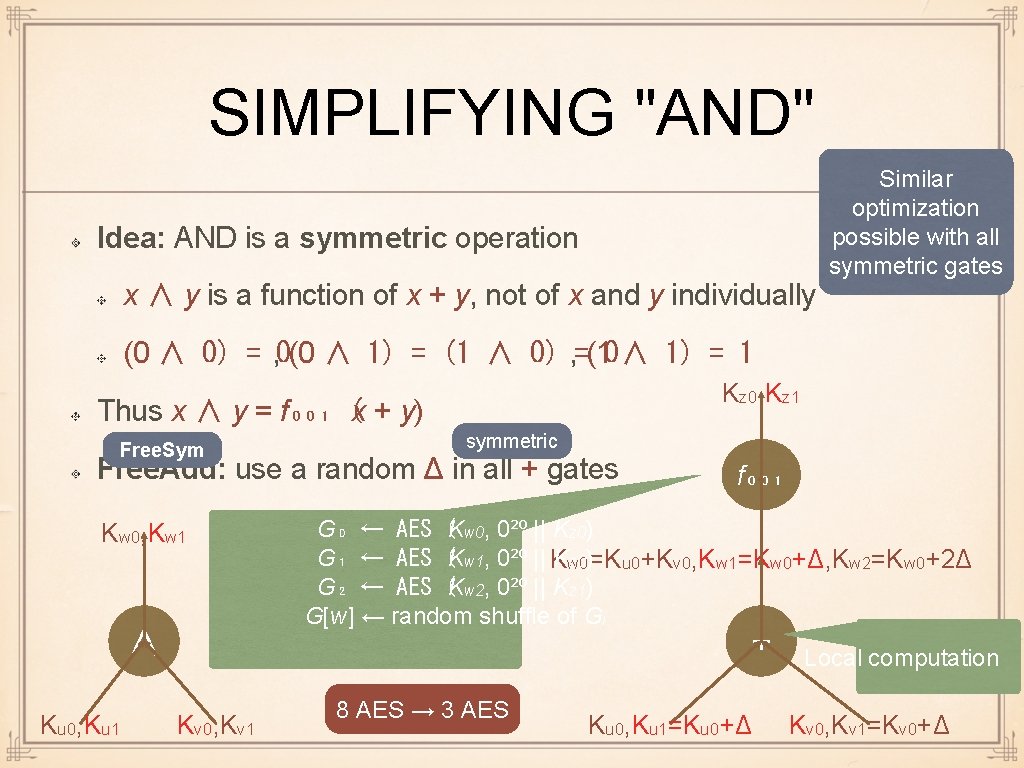
SIMPLIFYING "AND" Idea: AND is a symmetric operation x ∧ y is a function of x + y, not of x and y individually Similar optimization possible with all symmetric gates (0 ∧ 0) = , 0(0 ∧ 1) = (1 ∧ 0) , =(10 ∧ 1) = 1 Kz 0, Kz 1 Thus x ∧ y = f₀₀₁ (x + y) Free. Sym symmetric Free. Add: use a random Δ in all + gates Kw 0, Kw 1 G₀ ← AES (Kw 0, 0²⁰ || Kz 0) G₁ ← AES (Kw 1, 0²⁰ || K Kw 0 z 0)=Ku 0+Kv 0, Kw 1=Kw 0+Δ, Kw 2=Kw 0+2Δ G₂ ← AES (Kw 2, 0²⁰ || Kz 1) G[w] ← random shuffle of Gi + ∧ Ku 0, Ku 1 f₀₀₁ Kv 0, Kv 1 8 AES → 3 AES Ku 0, Ku 1=Ku 0+Δ Local computation Kv 0, Kv 1=Kv 0+Δ
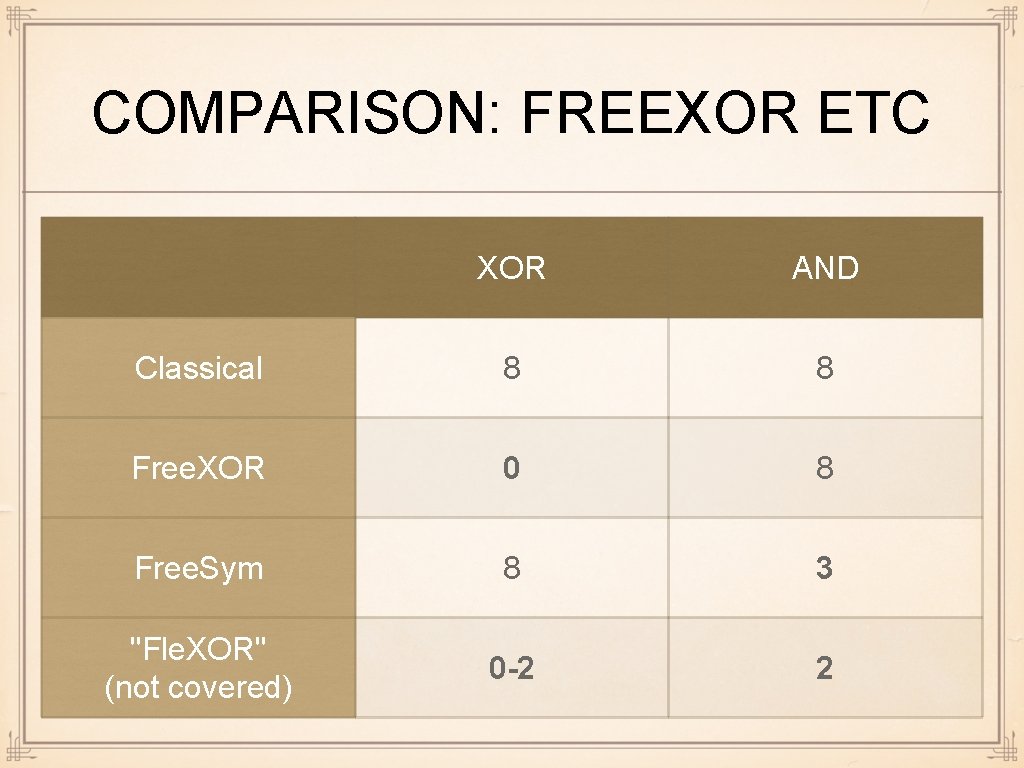
COMPARISON: FREEXOR ETC XOR AND Classical 8 8 Free. XOR 0 8 Free. Sym 8 3 "Fle. XOR" (not covered) 0 -2 2
AND MORE Highly parallel: A GPU implementation can process hundreds/thousands of gates in parallel after keys are computed, Alice can compute all garbled gates G [w] in parallel Many more optimizations than fit on the margins Very active research area especially active: not efficiency in malicious covering in this course - just not enough model time
GC: OUTRO Computationally very efficient Main problem: huge communication Another problem: circuit optimization In many cases, it is more natural to work in some other computational model For example: circuit for integer multiplication is large
WHAT NEXT? We showed how to compute almost anything securely in the semihonest model Starting from the next lecture: What to do when parties are malicious?
- Slides: 48