The Many Faces of Garbled Circuits Vinod Vaikuntanathan
The Many Faces of Garbled Circuits Vinod Vaikuntanathan MIT
![Garbled Circuits [Yao’ 86, refined by BMR’ 90, AIK’ 04, BHR’ 12] Garble Circuit Garbled Circuits [Yao’ 86, refined by BMR’ 90, AIK’ 04, BHR’ 12] Garble Circuit](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-2.jpg)
Garbled Circuits [Yao’ 86, refined by BMR’ 90, AIK’ 04, BHR’ 12] Garble Circuit C: Garble(C; R) Encode Input x: Encode(x; R) Simplicity: Garbling and Encoding are “simple” (e. g. , Garble: small depth, Encode: affine)
![The Swiss-army Knife of Crypto (Constant Round) MPC [BMR 90, IK 00] Circuit-private Homomorphic The Swiss-army Knife of Crypto (Constant Round) MPC [BMR 90, IK 00] Circuit-private Homomorphic](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-3.jpg)
The Swiss-army Knife of Crypto (Constant Round) MPC [BMR 90, IK 00] Circuit-private Homomorphic Encryption [GHV 10] Secure Two-party Computation [Yao 86] Parallel Cryptography [AIK 05] Functional Encryption [SS 10, GVW 12] KDM-Security [BHHI 09, A 11] One-time Programs [GKR 08] Verifiable Outsourcing [GGP 10, AIK 10] And many others: [AF 90, FKN 94, NPS 99, KO 04, FM 06, AL 07, LP 07, GKR 08, GMS 08, BFK+09, PSS 09, BHHI 10, GGP 10, HS 10, KM 10, SS 10, A 11, KMR 11, LP 11, GVW 12, …]
![Powerful Theorems Theorem: [Yao’ 86, LP’ 04] Assuming one-way functions, there is a garbling Powerful Theorems Theorem: [Yao’ 86, LP’ 04] Assuming one-way functions, there is a garbling](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-4.jpg)
Powerful Theorems Theorem: [Yao’ 86, LP’ 04] Assuming one-way functions, there is a garbling scheme for the class of all poly-size circuits. Theorem: [IK’ 00, AIK’ 04] Assuming nothing, there is a garbling scheme for the class of logspace computable functions.
![Much Work, Many Constructions Better Efficiency: Variants [BMR 90, NPS 99] Free XOR [KS Much Work, Many Constructions Better Efficiency: Variants [BMR 90, NPS 99] Free XOR [KS](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-5.jpg)
Much Work, Many Constructions Better Efficiency: Variants [BMR 90, NPS 99] Free XOR [KS 08, CKKZ 12, A 13], Garbled Circuits with Short Input Encoding [AIKW 13] Several practical efficiency improvements [MNPS 04, BNP 08, HSEKS 11, KSS 12, BHKR 13] Better Security: Adaptive vs. Static Security [BHR 12 a, BHR 12 b, JSW 16] New Goals, New Models: Re-randomizable Garbled Circuits [GHV 10], Arithmetic Garbled Circuits [AIK 11], Garbling RAM machines [LO 13, GHLORW 14, GLOS 15, GLO 15] and so on…
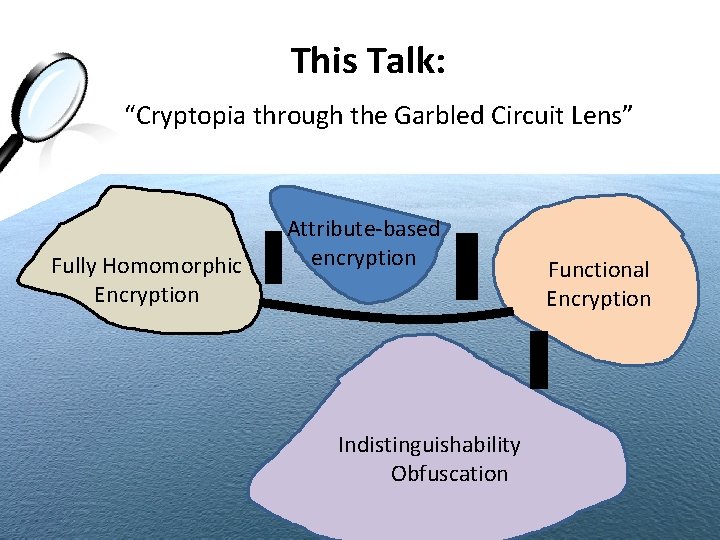
This Talk: “Cryptopia through the Garbled Circuit Lens” Fully Homomorphic Encryption Attribute-based encryption Indistinguishability Obfuscation Functional Encryption
![Yao’s Garbled Circuits [A. Yao 1986] AND-filter Yao’s Garbled Circuits [A. Yao 1986] AND-filter](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-7.jpg)
Yao’s Garbled Circuits [A. Yao 1986] AND-filter
![Yao’s Garbled Circuits [A. Yao 1986] garbled gate Yao’s Garbled Circuits [A. Yao 1986] garbled gate](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-8.jpg)
Yao’s Garbled Circuits [A. Yao 1986] garbled gate
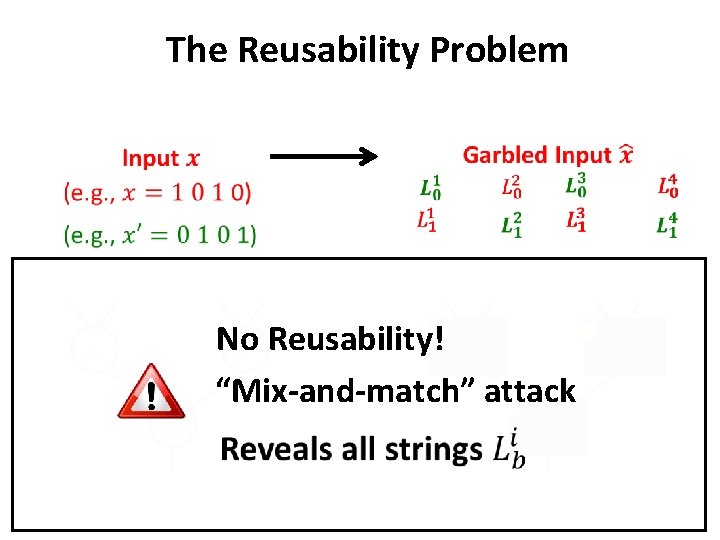
The Reusability Problem No Reusability! “Mix-and-match” attack
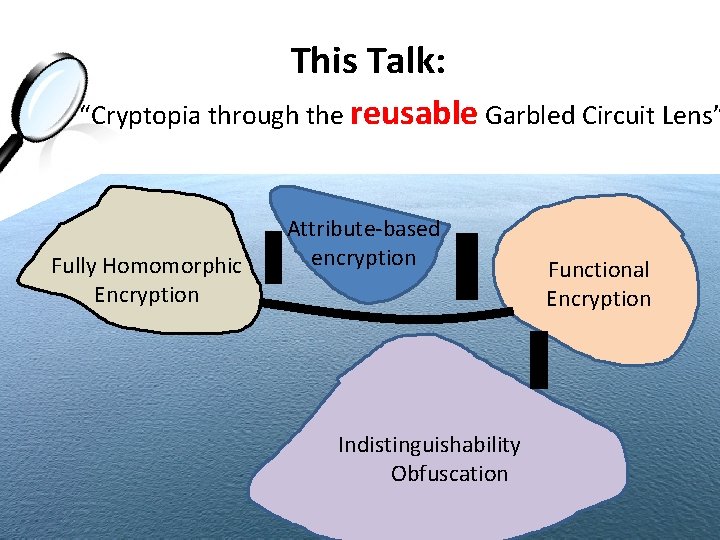
This Talk: “Cryptopia through the reusable Garbled Circuit Lens” Fully Homomorphic Encryption Attribute-based encryption Indistinguishability Obfuscation Functional Encryption
![Functional Encryption (FE) [Sahai-Waters’ 05, refined by BSW’ 12, O’neill’ 12] Secret Key for Functional Encryption (FE) [Sahai-Waters’ 05, refined by BSW’ 12, O’neill’ 12] Secret Key for](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-11.jpg)
Functional Encryption (FE) [Sahai-Waters’ 05, refined by BSW’ 12, O’neill’ 12] Secret Key for Circuit C: Key. Gen(SK, C) Encrypt Input x: Enc(PK, x) SKC Decrypt: SKC, C, CT → C(x) CT No circuit hiding: SKC does not hide the circuit C Public-key: many-input security for free Many-key Security: Can release many SKC_i revealing only Ci(x) Succinctness: Encryption time (and size) independent of |C|
![Attribute-based Encryption (ABE) [Sahai-Waters’ 05, Goyal-Pandey-Sahai-Waters’ 06] Secret Key for Circuit C: Key. Gen(SK, Attribute-based Encryption (ABE) [Sahai-Waters’ 05, Goyal-Pandey-Sahai-Waters’ 06] Secret Key for Circuit C: Key. Gen(SK,](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-12.jpg)
Attribute-based Encryption (ABE) [Sahai-Waters’ 05, Goyal-Pandey-Sahai-Waters’ 06] Secret Key for Circuit C: Key. Gen(SK, C) Encrypt Input x, Message M: SKC Decrypt: SKC, C, CT, x → MC(x) (either M 0 or M 1 not both) CT Enc(PK, x, M 0, M 1) No circuit or input hiding: only messages M 0 and M 1 hidden Public-key: many-input security for free Many-key Security: If Ci(x) = b for all i, M 1 -b hidden Succinctness: Encryption time (and size) independent of |C|
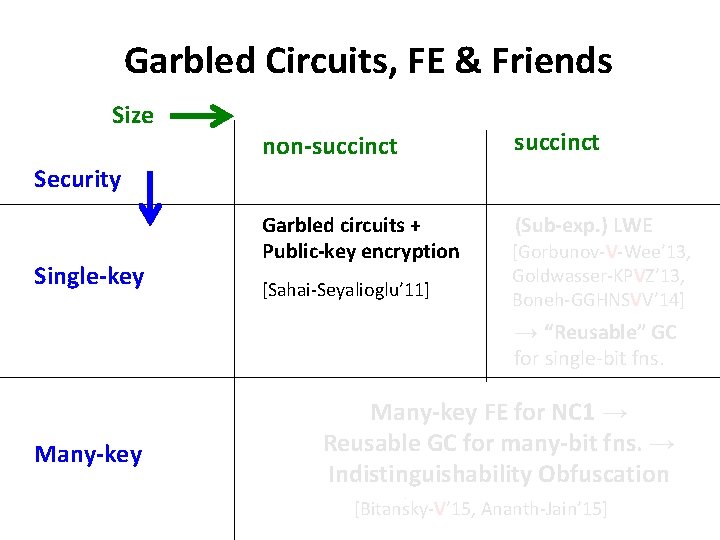
Garbled Circuits, FE & Friends Size non-succinct Garbled circuits + Public-key encryption (Sub-exp. ) LWE Security Single-key [Sahai-Seyalioglu’ 11] [Gorbunov-V-Wee’ 13, Goldwasser-KPVZ’ 13, Boneh-GGHNSVV’ 14] → “Reusable” GC for single-bit fns. Many-key = Many-key FE for NC 1 → Reusable GC for many-bit fns. → Indistinguishability Obfuscation [Bitansky-V’ 15, Ananth-Jain’ 15, Lin-Pass-Seth-Telang’ 16] [Bitansky-V’ 15, Ananth-Jain-Sahai’ 15] [Bitansky-V’ 15, Ananth-Jain’ 15]
![First Try: FE from Garbled Circuits [Sahai-Seyalioglu’ 11] Garbled Input for C Secret Key First Try: FE from Garbled Circuits [Sahai-Seyalioglu’ 11] Garbled Input for C Secret Key](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-14.jpg)
First Try: FE from Garbled Circuits [Sahai-Seyalioglu’ 11] Garbled Input for C Secret Key for Circuit C = SK i, Ci Many key, single input, secret key FE Many input, single key, secret key FE: use the universal circuit (and thus, lose succinctness) Single key (public key) FE: use public-key encryption and the “decomposability” of Yao’s garbled circuits
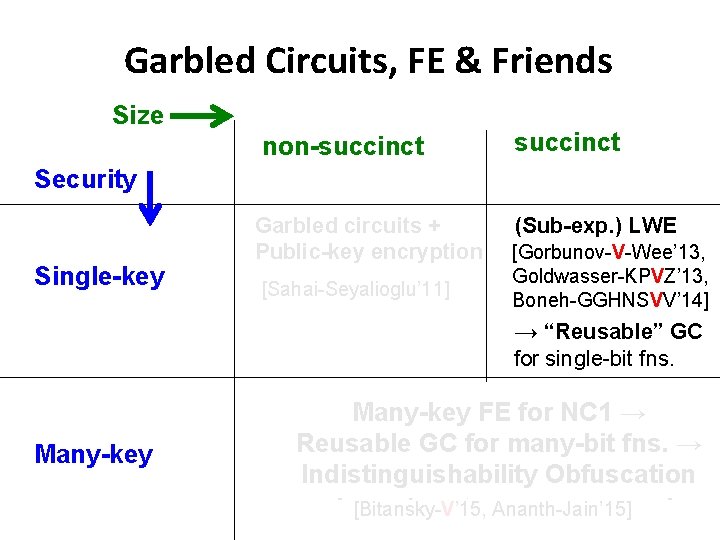
Garbled Circuits, FE & Friends Size succinct non-succinct Security Single-key Garbled circuits + Public-key encryption [Sahai-Seyalioglu’ 11] (Sub-exp. ) LWE [Gorbunov-V-Wee’ 13, Goldwasser-KPVZ’ 13, Boneh-GGHNSVV’ 14] → “Reusable” GC for single-bit fns. Many-key = Many-key FE for NC 1 → Reusable GC for many-bit fns. → Indistinguishability Obfuscation [Bitansky-V’ 15, Ananth-Jain’ 15, Lin-Pass-Seth-Tela [Bitansky-V’ 15, Ananth-Jain-Sahai’ 15] [Bitansky-V’ 15, Ananth-Jain’ 15]
![Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-16.jpg)
Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there is an ABE scheme for the class of all poly-size circuits (of a-priori bounded depth). + Theorem 1. 2: [Goldwasser-Kalai-Popa-V. -Zeldovich’ 13] Compiler from ABE to (single key, succinct) FE 1. FHE for P 2. ABE for (bounded depth) P 3. (One-time) garbling FE for (bounded depth) P
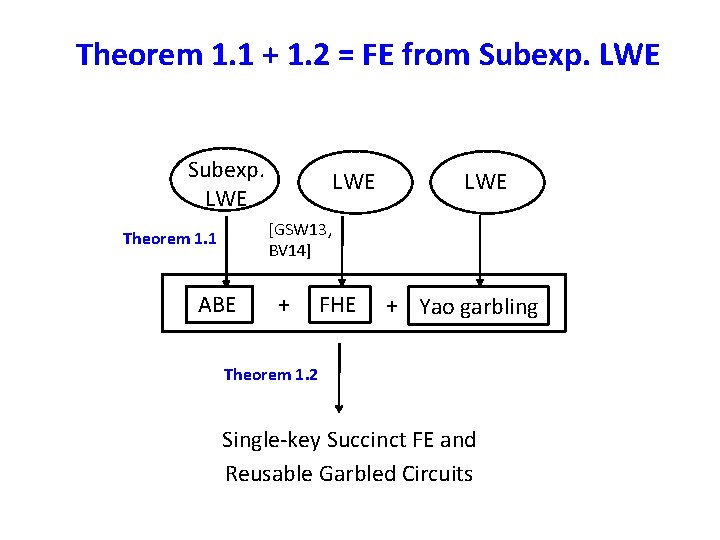
Theorem 1. 1 + 1. 2 = FE from Subexp. LWE Subexp. LWE [GSW 13, BV 14] Theorem 1. 1 ABE + FHE + Yao garbling Theorem 1. 2 Single-key Succinct FE and Reusable Garbled Circuits
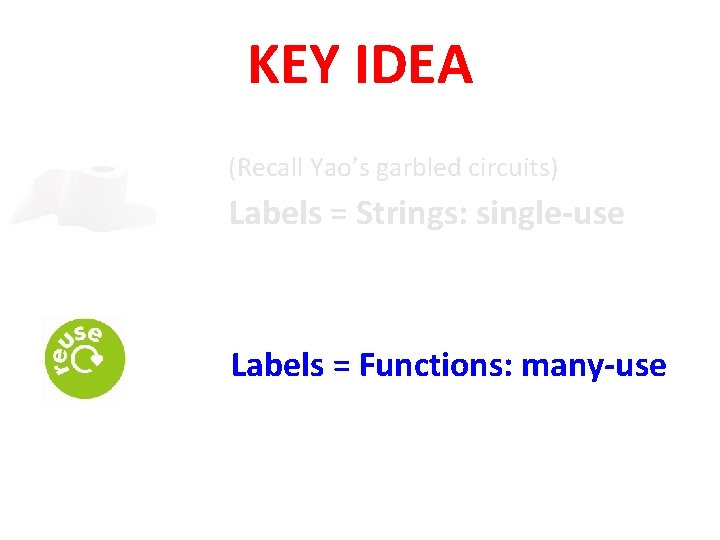
KEY IDEA (Recall Yao’s garbled circuits) Labels = Strings: single-use Labels = Functions: many-use
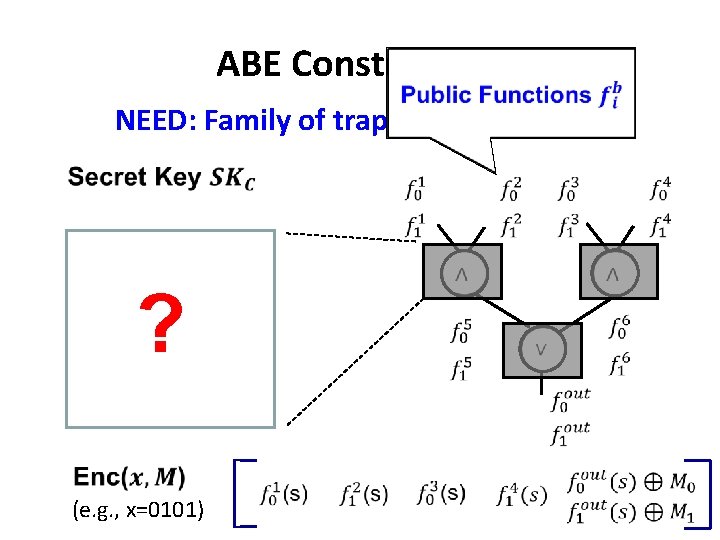
ABE Construction NEED: Family of trapdoor functions ? (e. g. , x=0101)
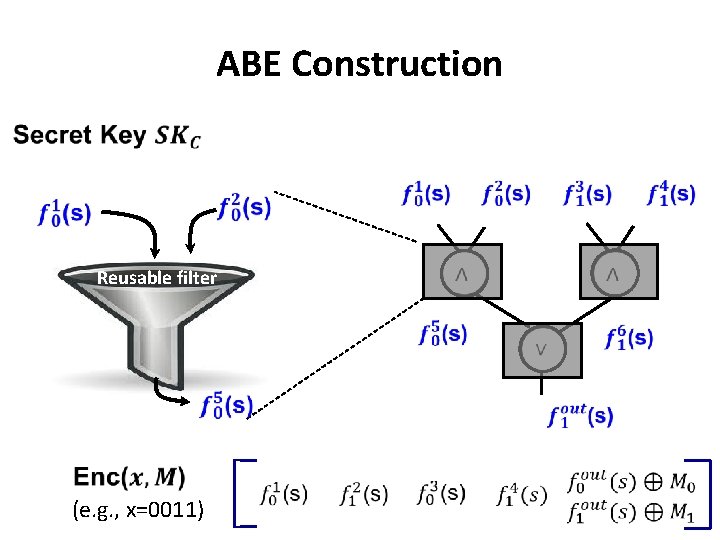
ABE Construction Reusable filter (e. g. , x=0011)
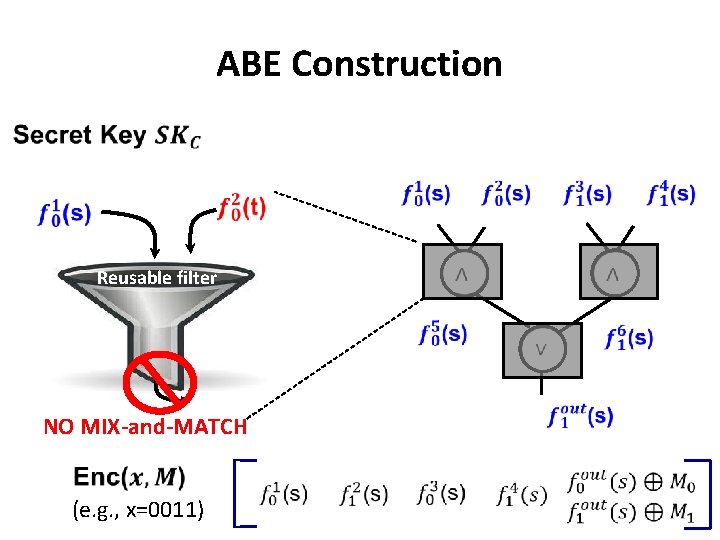
ABE Construction Reusable filter (e. g. , x=0011) NO MIX-and-MATCH
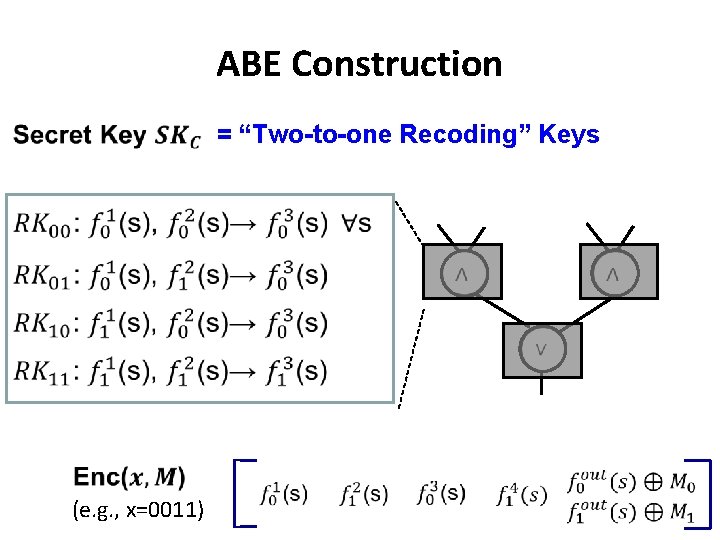
ABE Construction = “Two-to-one Recoding” Keys (e. g. , x=0011)
![What are these Trapdoor Functions? Learning with errors [BFKL’ 93, Regev’ 05] [Ajtai’ 99, What are these Trapdoor Functions? Learning with errors [BFKL’ 93, Regev’ 05] [Ajtai’ 99,](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-23.jpg)
What are these Trapdoor Functions? Learning with errors [BFKL’ 93, Regev’ 05] [Ajtai’ 99, Micciancio-Peikert’ 13] Trapdoor function (Sample uniformly random A with trapdoor)
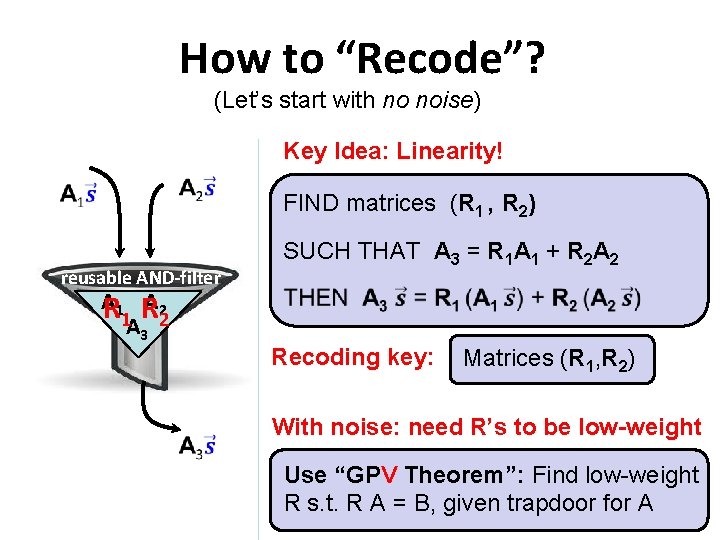
How to “Recode”? (Let’s start with no noise) Key Idea: Linearity! reusable AND-filter A R 11 RA 22 A 3 FIND matrices (R 1 , R 2) SUCH THAT A 3 = R 1 A 1 + R 2 A 2 Recoding key: Matrices (R 1, R 2) With noise: need R’s to be low-weight Use “GPV Theorem”: Find low-weight R s. t. R A = B, given trapdoor for A
![Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-25.jpg)
Theorem 1. 1: [Gorbunov-V. -Wee’ 13, Boneh-Gentry- Gorbunov-Halevi-Nikolaenko-Segev-V. -Vinayagamurthy’ 14]] Assuming “sub-exponential LWE”, there is an ABE scheme for the class of all poly-size circuits (of a-priori bounded depth). + Theorem 1. 2: [Goldwasser-Kalai-Popa-V. -Zeldovich’ 13] Compiler from ABE to (single key, succinct) FE 1. FHE for P 2. ABE for (bounded depth) P 3. (One-time) garbling FE for (bounded depth) P
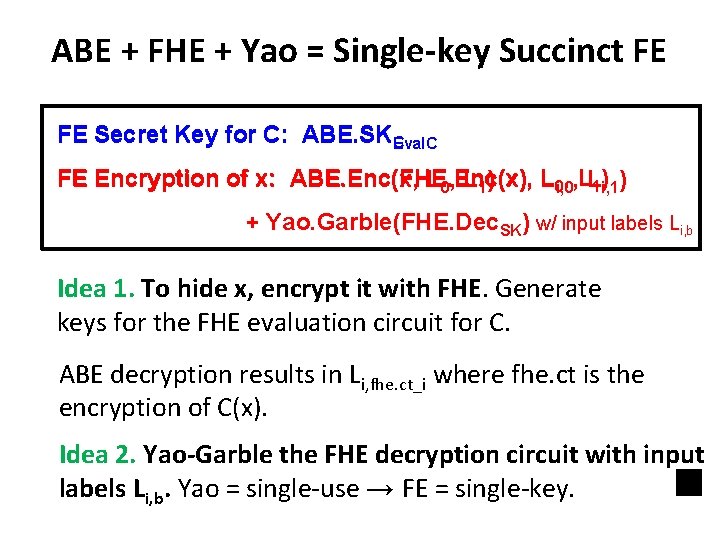
ABE + FHE + Yao = Single-key Succinct FE FE Secret Key for C: ABE. SKCEval. C FE Encryption of x: ABE. Enc(FHE. Enc(x), L 0 i, 0, , LL 1)i, 1) ABE. Enc(x, L 0, L 1) + Yao. Garble(FHE. Dec. SK) w/ input labels Li, b Idea 1. To hide x, encrypt it with FHE. Generate keys for the FHE evaluation circuit for C. ABE decryption results in Li, fhe. ct_i where fhe. ct is the encryption of C(x). Idea 2. Yao-Garble the FHE decryption circuit with input labels Li, b. Yao = single-use → FE = single-key.
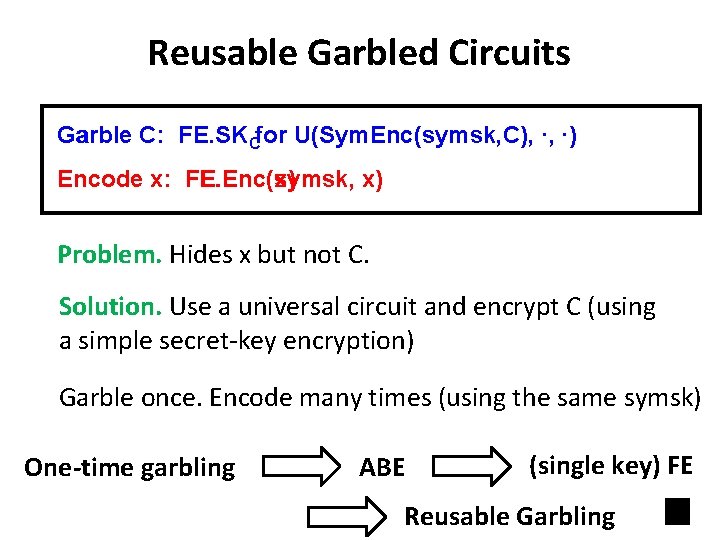
Reusable Garbled Circuits Garble C: FE. SKCfor U(Sym. Enc(symsk, C), ∙, ∙) Encode x: FE. Enc(symsk, FE. Enc(x) x) Problem. Hides x but not C. Solution. Use a universal circuit and encrypt C (using a simple secret-key encryption) Garble once. Encode many times (using the same symsk) One-time garbling ABE (single key) FE Reusable Garbling
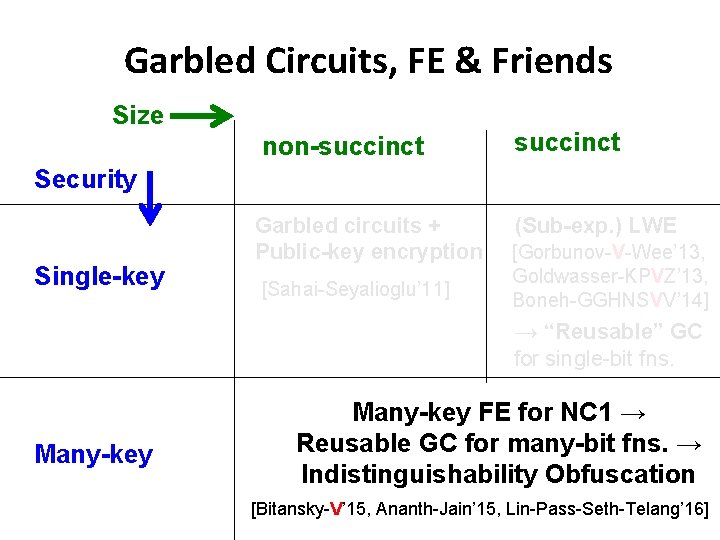
Garbled Circuits, FE & Friends Size non-succinct Security Single-key Garbled circuits + Public-key encryption [Sahai-Seyalioglu’ 11] (Sub-exp. ) LWE [Gorbunov-V-Wee’ 13, Goldwasser-KPVZ’ 13, Boneh-GGHNSVV’ 14] → “Reusable” GC for single-bit fns. Many-key FE for NC 1 → Reusable GC for many-bit fns. → Indistinguishability Obfuscation [Bitansky-V’ 15, Ananth-Jain’ 15, Lin-Pass-Seth-Telang’ 16]
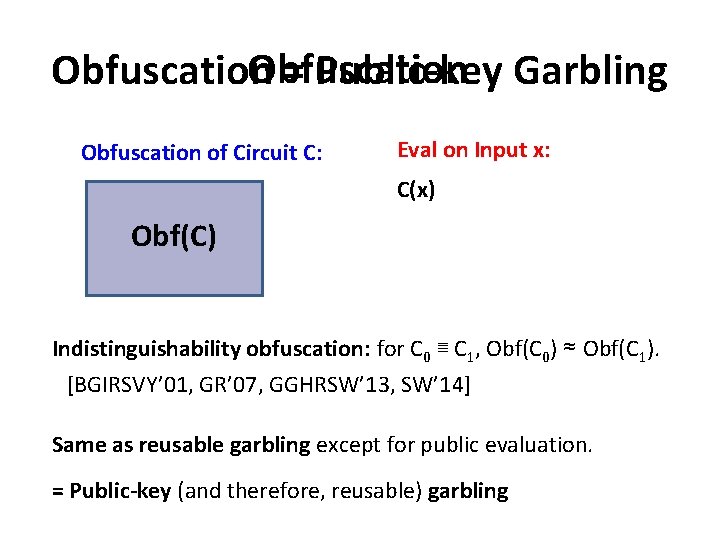
Obfuscation = Public-key Garbling Obfuscation of Circuit C: Eval on Input x: C(x) Obf(C) Indistinguishability obfuscation: for C 0 ≣ C 1, Obf(C 0) ≈ Obf(C 1). [BGIRSVY’ 01, GR’ 07, GGHRSW’ 13, SW’ 14] Same as reusable garbling except for public evaluation. = Public-key (and therefore, reusable) garbling
![Theorem: Reusable Garbling++ to IO [Bitansky-V. ’ 15, Ananth-Jain’ 15, simplified by Lin-Pass-Seth-Telang’ 16] Theorem: Reusable Garbling++ to IO [Bitansky-V. ’ 15, Ananth-Jain’ 15, simplified by Lin-Pass-Seth-Telang’ 16]](http://slidetodoc.com/presentation_image/25600071b3e7b1e1ed6635165cf4ff7d/image-30.jpg)
Theorem: Reusable Garbling++ to IO [Bitansky-V. ’ 15, Ananth-Jain’ 15, simplified by Lin-Pass-Seth-Telang’ 16] If there is a compact reusable garbled circuit + subexponentially secure OWF, then there is an IO scheme. Succinct: garbled input size ind. of |C| for one-bit functions ++ = Compact: garbled input size ind. of |C| for many-bit functions Compact Reusable GC th ea sy is Many-key FE [GGHRSW’ 13] th eo re m IO
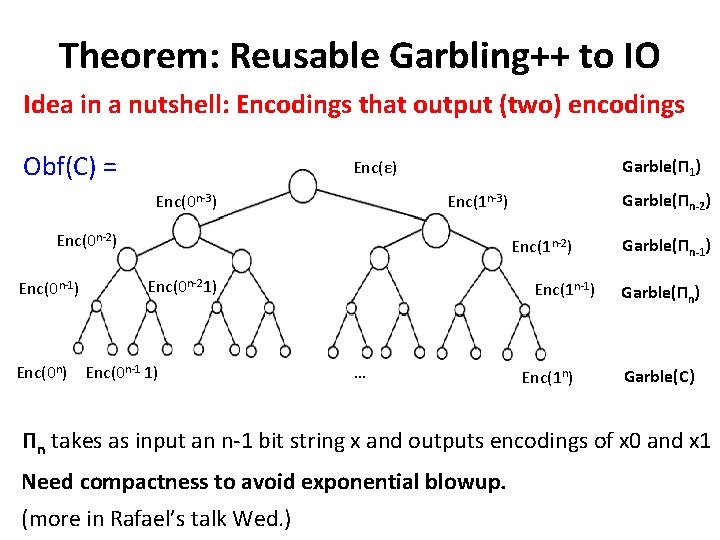
Theorem: Reusable Garbling++ to IO Idea in a nutshell: Encodings that output (two) encodings Obf(C) = Garble(П 1) Enc(ε) Enc(0 n-3) Enc(0 n-2) Enc(0 n-1) Garble(Пn-2) Enc(1 n-3) Enc(1 n-2) Enc(0 n-21) Enc(0 n-1 1) Enc(1 n-1) … Enc(1 n) Garble(Пn-1) Garble(Пn) Garble(C) Пn takes as input an n-1 bit string x and outputs encodings of x 0 and x 1 Need compactness to avoid exponential blowup. (more in Rafael’s talk Wed. )
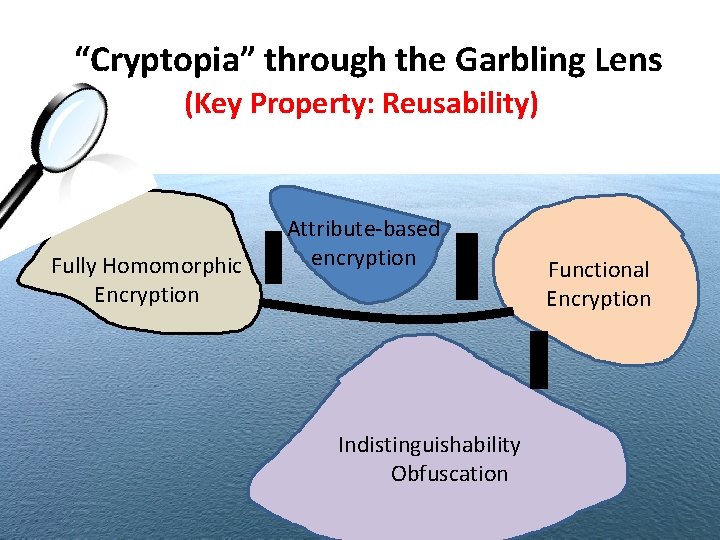
“Cryptopia” through the Garbling Lens (Key Property: Reusability) Fully Homomorphic Encryption Attribute-based encryption Indistinguishability Obfuscation Functional Encryption
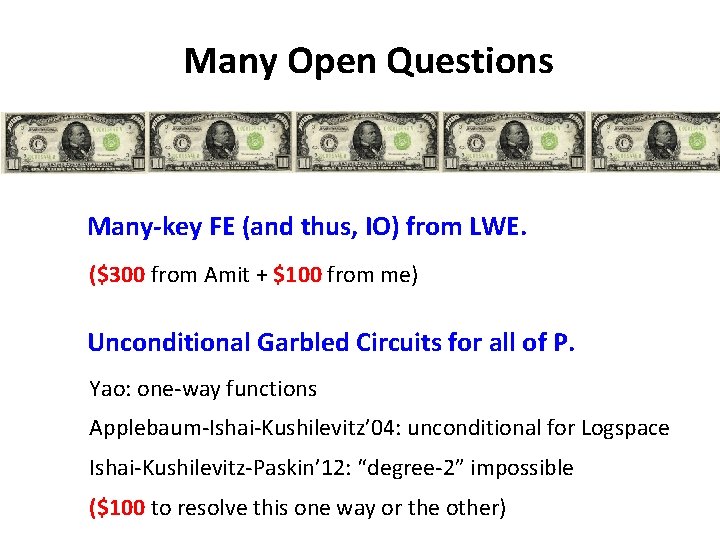
Many Open Questions Many-key FE (and thus, IO) from LWE. ($300 from Amit + $100 from me) Unconditional Garbled Circuits for all of P. Yao: one-way functions Applebaum-Ishai-Kushilevitz’ 04: unconditional for Logspace Ishai-Kushilevitz-Paskin’ 12: “degree-2” impossible ($100 to resolve this one way or the other)
Thank You!
- Slides: 34