Computer Security Cryptography Basic Terminology Plaintext decrypted Ciphertext

Computer Security Cryptography
Basic. Terminology Plaintext (decrypted) Ciphertext (encrypted) Cryptography – keeping messages secure Cryptanalysis – breaking encrypted messages Cryptology – Cryptography + Cryptanalysis Cryptographic algorithm (a. k. a. cipher) – an algorithm for encryption
Goals of Secure Communication Channel Alice and Bob want to communicate securely Goals n n n No information/content leakage Only messages from Alice and Bob get delivered Messages are delivered in order, or not at all
Goals of Secure Communication Channel (2) What if Eve has access to the channel? Eve may be able to inspect, modify or drop any message Goals stand as before n n n No information/content leakage Only messages from Alice and Bob get delivered Messages are delivered in order or not at all
Alice, Bob and Eve
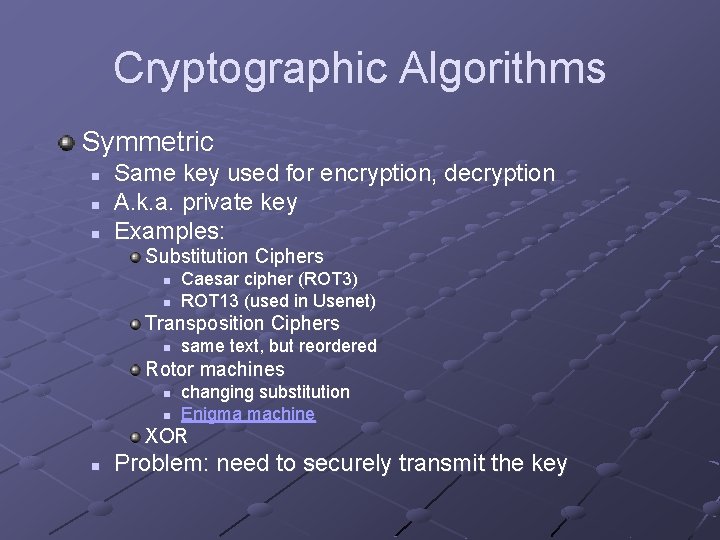
Cryptographic Algorithms Symmetric n n n Same key used for encryption, decryption A. k. a. private key Examples: Substitution Ciphers n n Caesar cipher (ROT 3) ROT 13 (used in Usenet) Transposition Ciphers n same text, but reordered Rotor machines n n changing substitution Enigma machine XOR n Problem: need to securely transmit the key
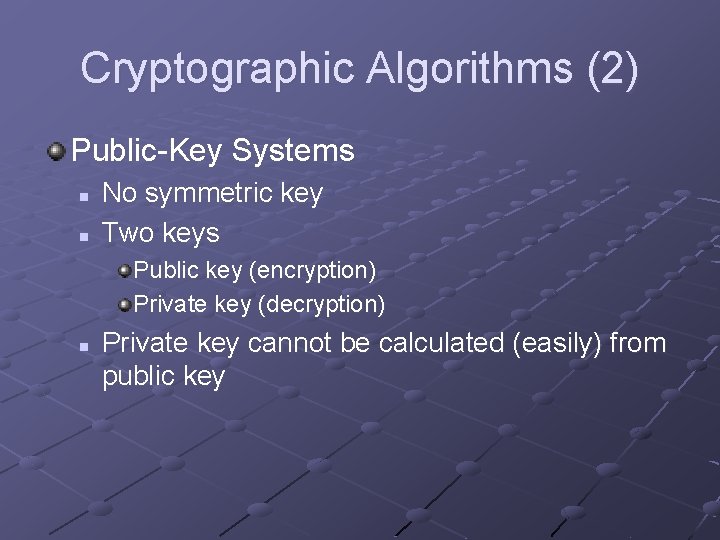
Cryptographic Algorithms (2) Public-Key Systems n n No symmetric key Two keys Public key (encryption) Private key (decryption) n Private key cannot be calculated (easily) from public key
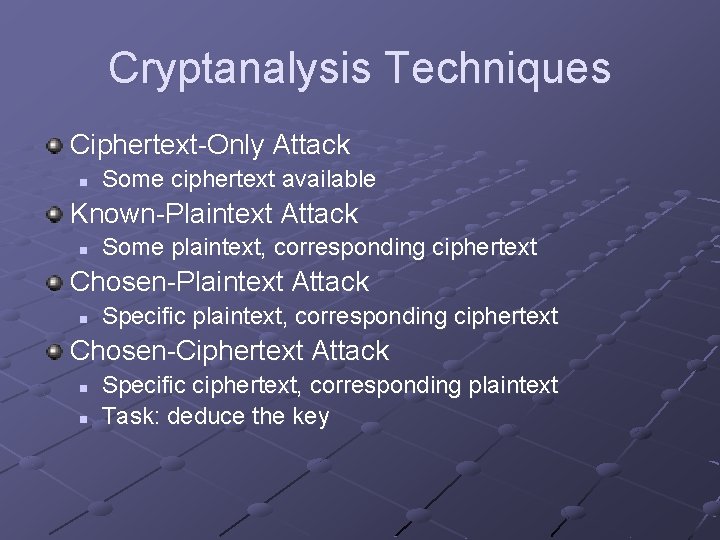
Cryptanalysis Techniques Ciphertext-Only Attack n Some ciphertext available Known-Plaintext Attack n Some plaintext, corresponding ciphertext Chosen-Plaintext Attack n Specific plaintext, corresponding ciphertext Chosen-Ciphertext Attack n n Specific ciphertext, corresponding plaintext Task: deduce the key
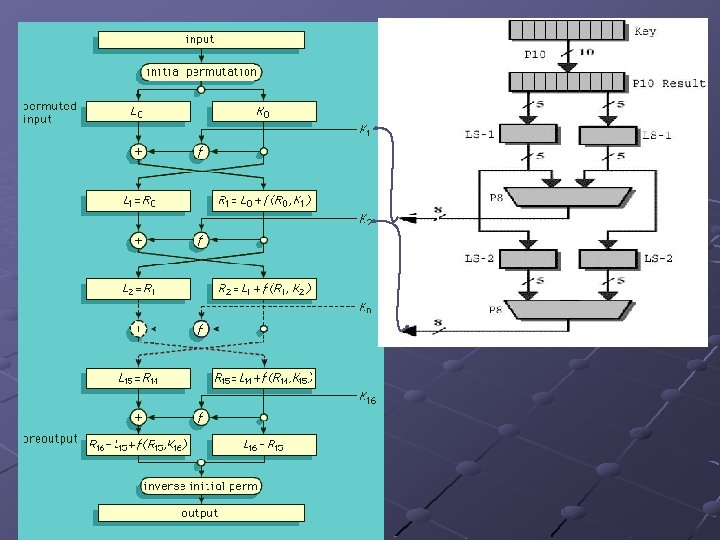
DES Data Encryption Standard (DES) Used since 1976 Combination of bit permutation, expansion, substitution
DES Information n n Applied Cryptography, Schneier http: //www. aci. net/kalliste/des. htm Simulations n http: //nsfsecurity. pr. erau. edu
Problems with DES Key length n n 56 bit key => 256 possible keys Brute force key attack on 56 bit keys Machine built in 1998, cracked in 56 hours Possible back doors n Unknown at this point
Improving DES Triple DES n Process Encrypt once with key-1 Decrypt with key-2 Encrypt again with key-1 n Benefits Search space now 2112 keys Brute force attack currently impossible
Next Generation Private Key Encryption DES is no longer secure for small keys Time will lessen its use with large keys Late 1990 s – NIST had contest to choose new algorithm n Many 15 5 1 Rijndael algorithm chosen as winner Renamed (Advanced Encryption Standard, AES), standard as of 2001
AES Similarities to DES n n Multiple cycles (“rounds”) Substitution, shifting, bit manipulations Differences n n n 128 bit key to start Can use 256 bit key Number of rounds not fixed to algorithm Can be increased for additional security
Goal: One-Way Function Definition n Function that is easily applied to some data to generate a result, but cannot (easily) be “unapplied” to get original data Application n Secure communication desires a one-way function with a trap door: easy access if know the secret key Examples n SHA-1, SHA-2, MD 4, MD 5
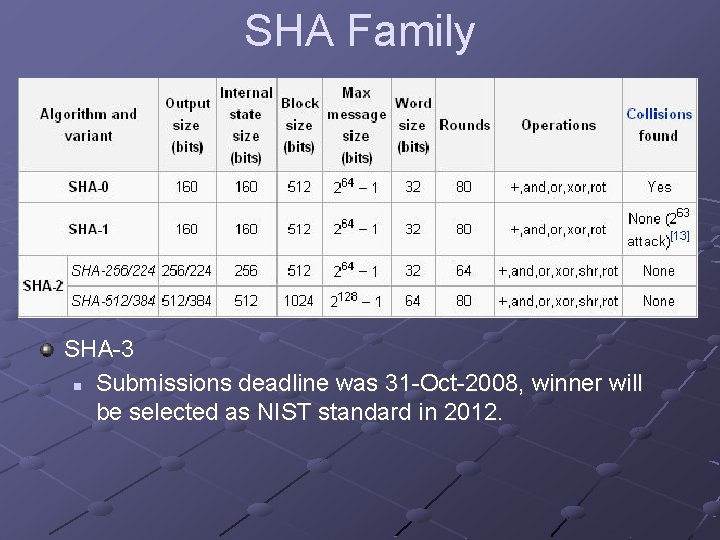
SHA Family SHA-3 n Submissions deadline was 31 -Oct-2008, winner will be selected as NIST standard in 2012.
Public Key Cryptography Diffie/Hellman n 1976 – described public key cryptography RSA (Rivest, Shamir, Adelman) n n 1978 – introduced implementation algorithm based on difficulty of factoring products of large (100200 digit) prime numbers Idea: public and private key are related, but not in a way that’s easily discovered
Public-Key Cryptography - Basics Alice and Bob agree on a public-key system n Bob generates a public and private key pair Bob sends Alice (or publicizes) his public key Alice encrypts her message with Bob’s public key, sends it to Bob decrypts Alice’s message using his private key
Public-Key Crytography - Improved Alice gets Bob’s public key from a public database Alice encrypts her message with Bob’s public key and sends it Bob decrypts her message using his private key
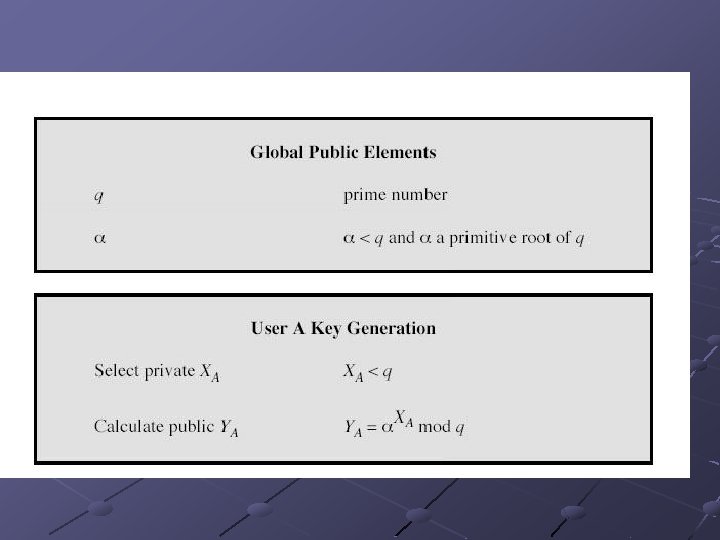
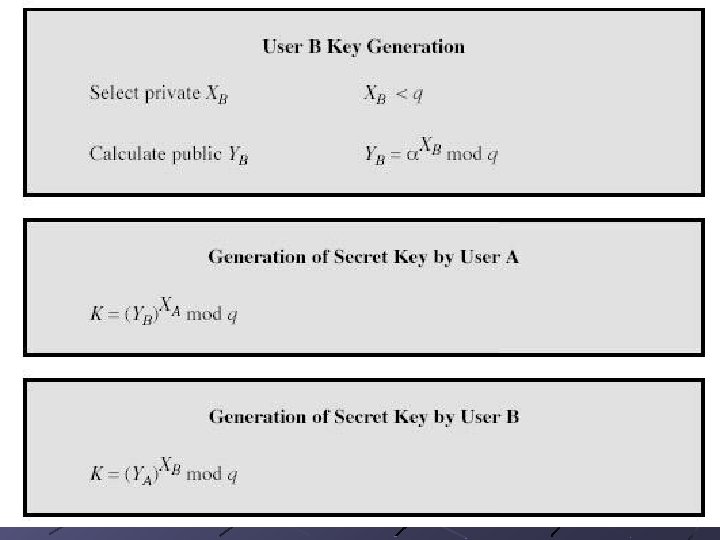
Diffie-Hellman Algorithm – Computing a secret key First public key algorithm invented Can only be used for secret key generation / distribution n Not for encryption and decryption Alice and Bob agree on g and n n n 1<g<n n should be prime (n-1)/2 should be prime g should be a primitive root mod n n should be at least 512 – 1024 bits
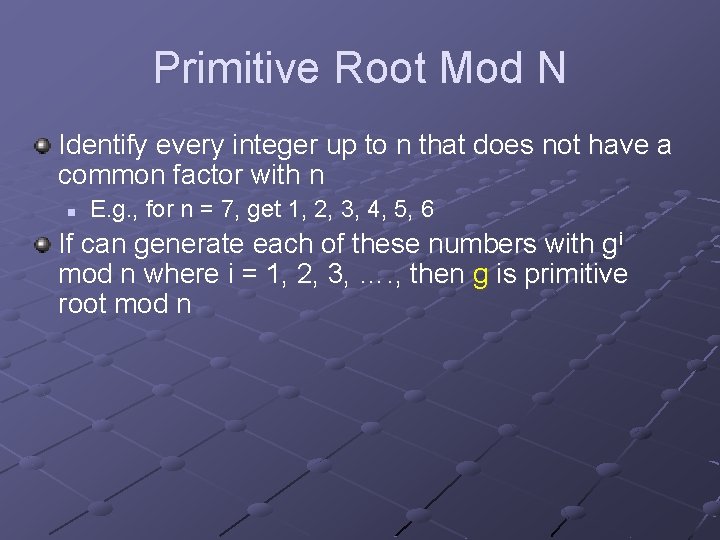
Primitive Root Mod N Identify every integer up to n that does not have a common factor with n n E. g. , for n = 7, get 1, 2, 3, 4, 5, 6 If can generate each of these numbers with gi mod n where i = 1, 2, 3, …. , then g is primitive root mod n
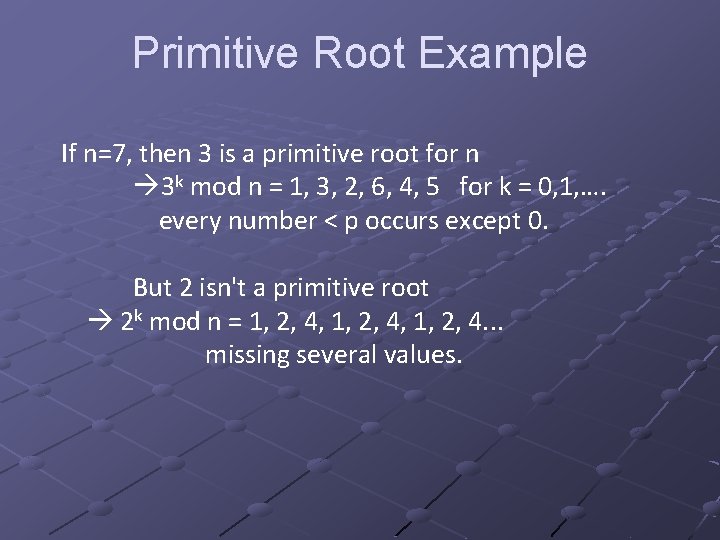
Primitive Root Example If n=7, then 3 is a primitive root for n 3 k mod n = 1, 3, 2, 6, 4, 5 for k = 0, 1, …. every number < p occurs except 0. But 2 isn't a primitive root 2 k mod n = 1, 2, 4, 1, 2, 4. . . missing several values.
from Nick Hopper
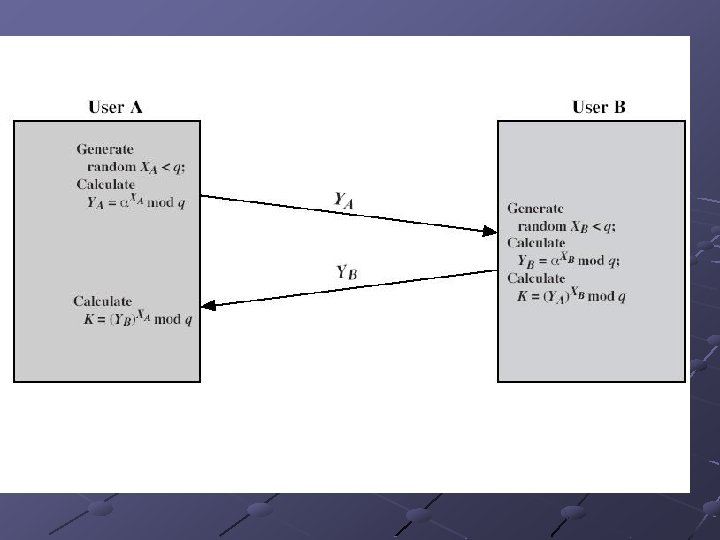
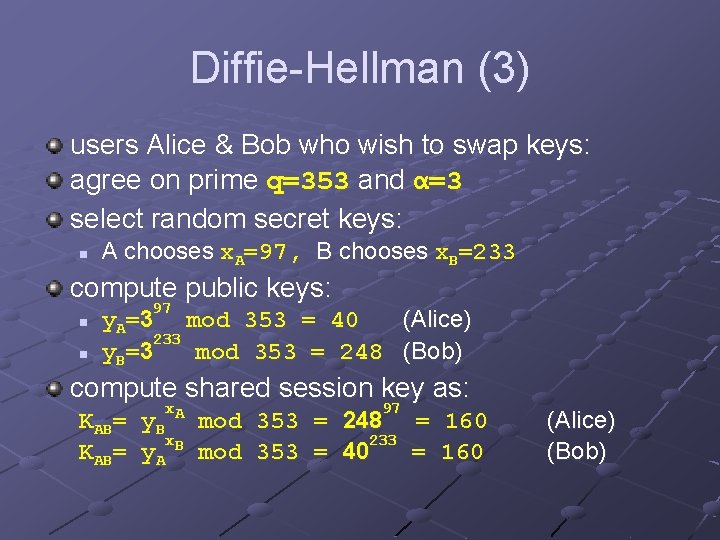
Diffie-Hellman (3) users Alice & Bob who wish to swap keys: agree on prime q=353 and α=3 select random secret keys: n A chooses x. A=97, B chooses x. B=233 compute public keys: n n 97 y. A=3 mod 353 = 40 (Alice) 233 y B= 3 mod 353 = 248 (Bob) compute shared session key as: KAB= x y. B A x y. A B mod 353 = = 97 248 233 40 = = 160 (Alice) (Bob)
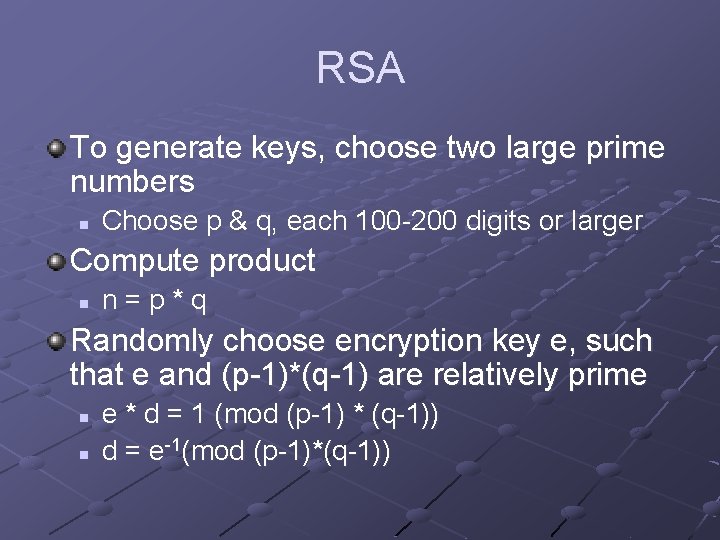
RSA To generate keys, choose two large prime numbers n Choose p & q, each 100 -200 digits or larger Compute product n n=p*q Randomly choose encryption key e, such that e and (p-1)*(q-1) are relatively prime n n e * d = 1 (mod (p-1) * (q-1)) d = e-1(mod (p-1)*(q-1))
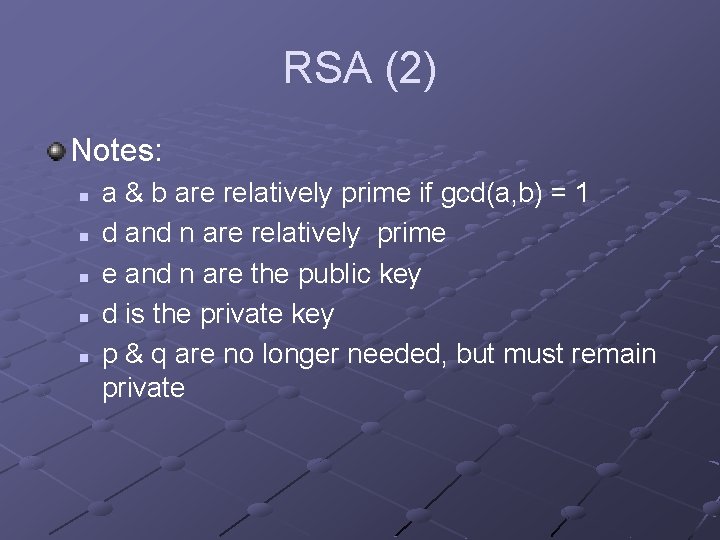
RSA (2) Notes: n n n a & b are relatively prime if gcd(a, b) = 1 d and n are relatively prime e and n are the public key d is the private key p & q are no longer needed, but must remain private
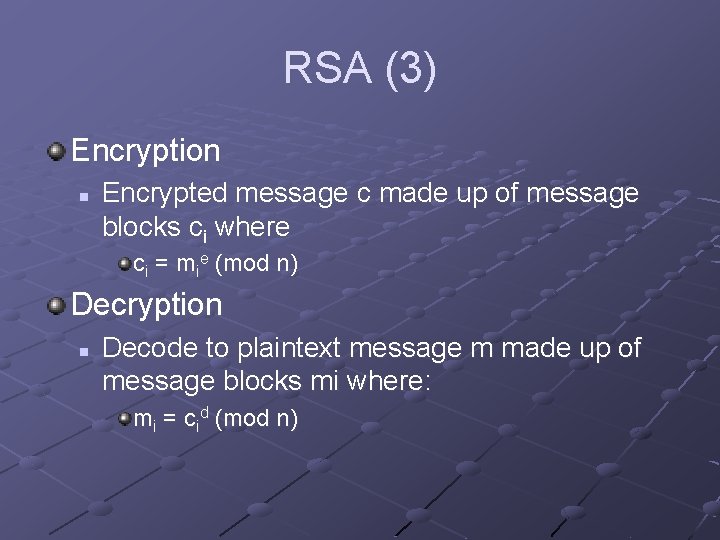
RSA (3) Encryption n Encrypted message c made up of message blocks ci where ci = mie (mod n) Decryption n Decode to plaintext message m made up of message blocks mi where: mi = cid (mod n)
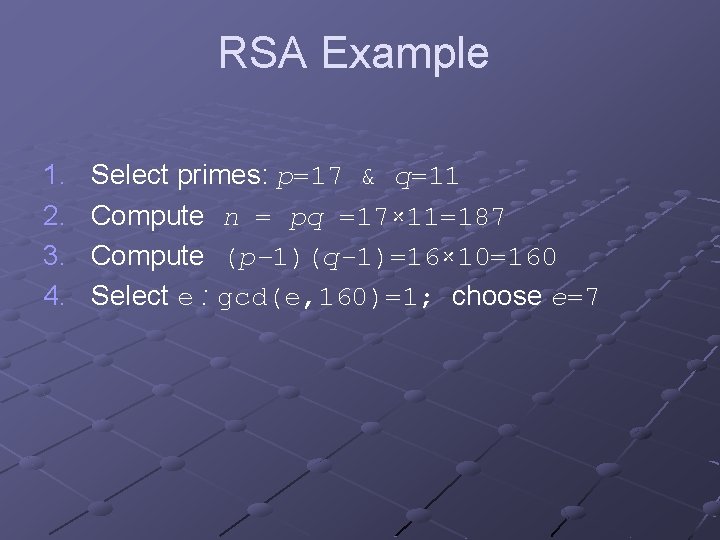
RSA Example 1. 2. 3. 4. Select primes: p=17 & q=11 Compute n = pq =17× 11=187 Compute (p– 1)(q-1)=16× 10=160 Select e : gcd(e, 160)=1; choose e=7
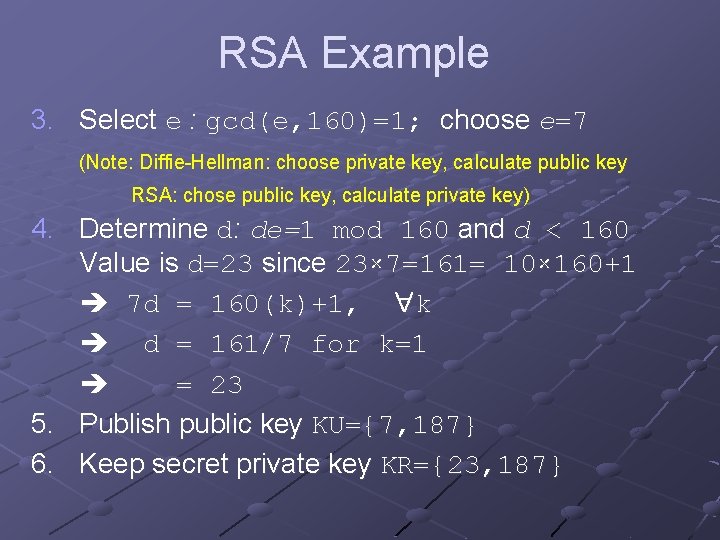
RSA Example 3. Select e : gcd(e, 160)=1; choose e=7 (Note: Diffie-Hellman: choose private key, calculate public key RSA: chose public key, calculate private key) 4. Determine d: de=1 mod 160 and d < 160 Value is d=23 since 23× 7=161= 10× 160+1 7 d = 160(k)+1, k d = 161/7 for k=1 = 23 5. Publish public key KU={7, 187} 6. Keep secret private key KR={23, 187}
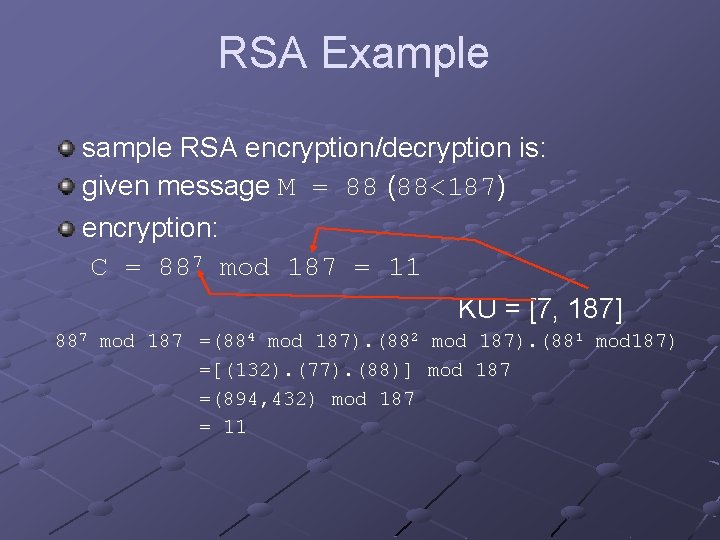
RSA Example sample RSA encryption/decryption is: given message M = 88 (88<187) encryption: C = 887 mod 187 = 11 KU = [7, 187] 887 mod 187 =(884 mod 187). (882 mod 187). (881 mod 187) =[(132). (77). (88)] mod 187 =(894, 432) mod 187 = 11
![RSA Example Decryption: M = 1123 mod 187 = 88 KR = [23, 187] RSA Example Decryption: M = 1123 mod 187 = 88 KR = [23, 187]](http://slidetodoc.com/presentation_image_h2/764eed92b8fc715c6e8a8d2c2eeecc8b/image-34.jpg)
RSA Example Decryption: M = 1123 mod 187 = 88 KR = [23, 187] 1123 mod 187 =(111 mod 187). (112 mod 187). (114 mod 187). (118 mod 187) = [(11). (121). (55). (33)] mod 187 = 79720245 mod 187 = 88
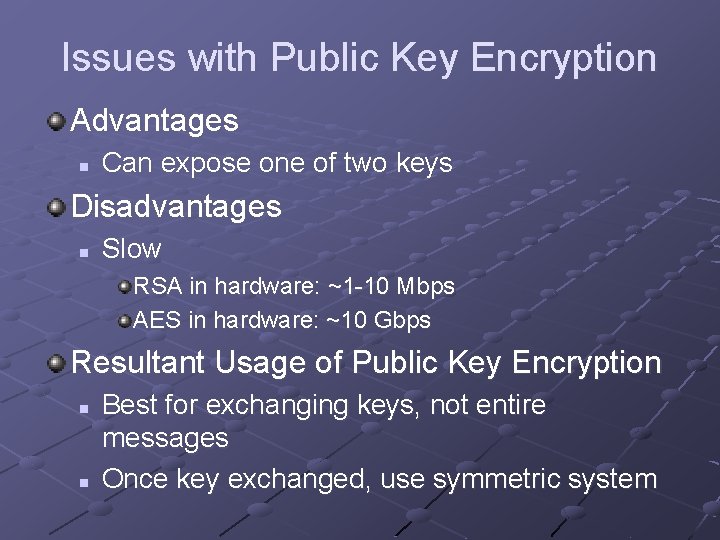
Issues with Public Key Encryption Advantages n Can expose one of two keys Disadvantages n Slow RSA in hardware: ~1 -10 Mbps AES in hardware: ~10 Gbps Resultant Usage of Public Key Encryption n n Best for exchanging keys, not entire messages Once key exchanged, use symmetric system
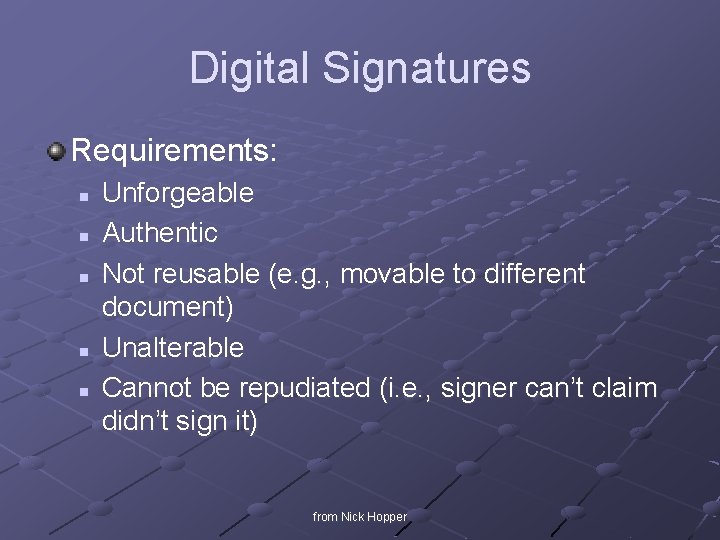
Digital Signatures Requirements: n n n Unforgeable Authentic Not reusable (e. g. , movable to different document) Unalterable Cannot be repudiated (i. e. , signer can’t claim didn’t sign it) from Nick Hopper
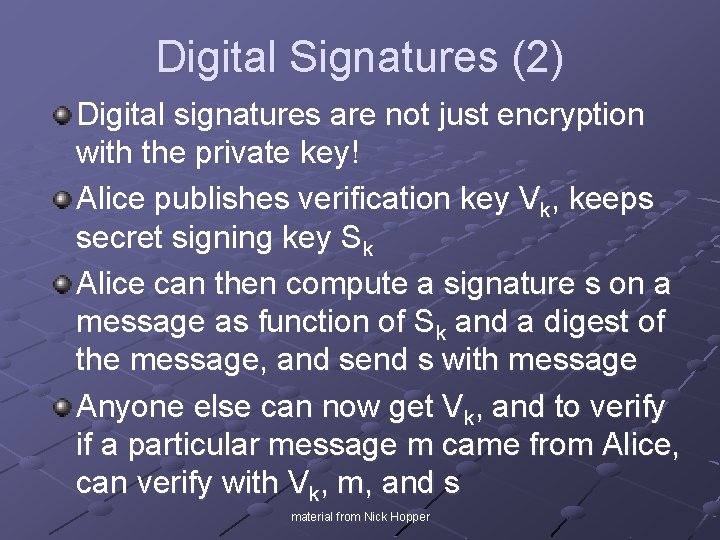
Digital Signatures (2) Digital signatures are not just encryption with the private key! Alice publishes verification key Vk, keeps secret signing key Sk Alice can then compute a signature s on a message as function of Sk and a digest of the message, and send s with message Anyone else can now get Vk, and to verify if a particular message m came from Alice, can verify with Vk, m, and s material from Nick Hopper
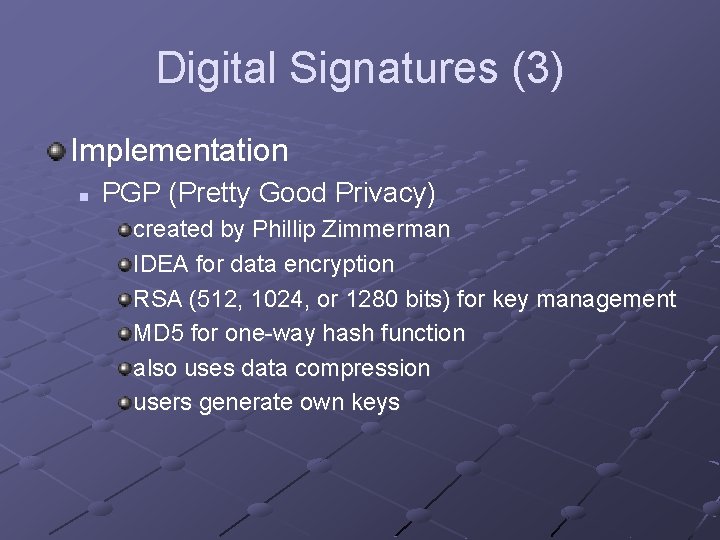
Digital Signatures (3) Implementation n PGP (Pretty Good Privacy) created by Phillip Zimmerman IDEA for data encryption RSA (512, 1024, or 1280 bits) for key management MD 5 for one-way hash function also uses data compression users generate own keys
Hashing and Integrity Need to determine integrity of message to show hasn’t been modified after sending Integrity: Eve cannot make new, valid message even after seeing Alice and Bob send many Process: reduce data and any meta-data (e. g. owner, timestamp) to a summary (digest) Hashing used for this n Example: SHA-1, SHA-256 Material from Nick Hopper
Hash Functions Map long strings to short strings Examples n n H(x, y, z) = x + y + z H(x) = x mod 65537 Hash functions may have a key n n E. g. Ha, b, p(x) = ax + b mod p When (a, b, p) are used only once, Ha, b, p(x) can be appended to x to prevent modification Material from Nick Hopper
Cryptographic Hash Functions Fixed hash functions with outputs that “look random” to an adversary A cryptographic hash function should resist attacks such as: n Inversion (Pre-image): given y, find any x so that H(x) =y n Targeted collisions: given x, H(x), find x’ != x where H(x’) = H(x) n Free collisions: find x’ != x where H(x) = H(x’) Material from Nick Hopper
Hash Function Strength For any function H with k-bit outputs, how long (at most) does it take to find: n n n Inversion/Pre-images: 2 k hashes Targeted collisions: 2 k hashes Free collisions: 2 k/2 hashes “Birthday Paradox” phenomena – even though 365 days in year, probability of finding two people with the same birthday is >50% with only 23 people in room Because of Birthday-based attacks, a k-bit hash function has at most k/2 bits of security against free collisions Material from Nick Hopper
Hash Function Weakness Even given a good hash function… Sending message with hash does not create a channel with integrity against adversaries Need something with a key: Message Authentication Code, or MAC Material from Nick Hopper
Message Authentication Code MAC input: a secret key and a message MAC output: a random-looking “tag” of fixed length Receiver can use key and verification function to check that received tag matches message and key Can build MAC out of block cipher, crypto hash function Issue: should be hard to find a new correct tag without knowing the key Material from Nick Hopper
Secure Socket Layer (SSL) Protocol for applying encryption to any TCP applications n n HTTPS Secure Shell Secure File Transfer (SFTP, Win. SCP) others…
SSL Process Client sends handshake to server Server sends its certificate (including public key, expiration, owner, fully qualified domain name) Client generates a challenge using the public key Server meets challenge using private key Client can now send data encrypted with public key
SSL Issues Is it a problem for server’s certificate to remain public? n Problem for attacker: need certificate plus private key to masquerade as the server But: n Attacker can present server’s certificate, then establish proxy connection to server (“man-inthe-middle”)
SSL Issues (2) Solution: Validate Certificates n n Client can keep list of valid certificates Better: Trusted 3 rd Party (Certification Authority) keeps list of valid certificates signs valid certificates with private key client can validate certification if can read signature with public key
Other Issues Implementations of SSL n Open. SSL Library Public domain n Commercial implementations Evolving n SSL => TLS (Transport Layer Security)
- Slides: 49