Computer Science Introduction to Public Key Cryptography Lecture
Computer Science Introduction to Public Key Cryptography Lecture 4 CPSC 415 Biometrics and Cryptography 1
Outline Computer Science • Public Key Encryption • Public Key Cryptographic System • Public Key vs. Symmetric Key • Digital Signatures • Digital Envelope CPSC 415 Biometrics and Cryptography 2
Insufficiencies with Symmetric Encryption Computer Science • Symmetric encryption is not enough to address two key issues – key distribution – how to have secure communications in general without having to trust a KDC with your key? – digital signatures – how to verify that a received message really comes from the claimed sender? CPSC 415 Biometrics and Cryptography 3
Advent of Asymmetric Encryption Computer Science • Probably most significant advance in the 3000 year history of cryptography • Use two keys: a public key and a private key • Asymmetric since parties are not equal • Clever application of number theory concepts instead of merely substitution and permutation CPSC 415 Biometrics and Cryptography 4
How Asymmetric Encryption Works Computer Science • Asymmetric encryption uses two keys that are related to each other – a public key, which may be known to anybody, is used to encrypt messages, and verify signatures – a private key, known only to the owner, is used to decrypt messages encrypted by the matching public key, and create signatures – the key used to encrypt messages or verify signatures cannot decrypt messages or create signatures CPSC 415 Biometrics and Cryptography 5
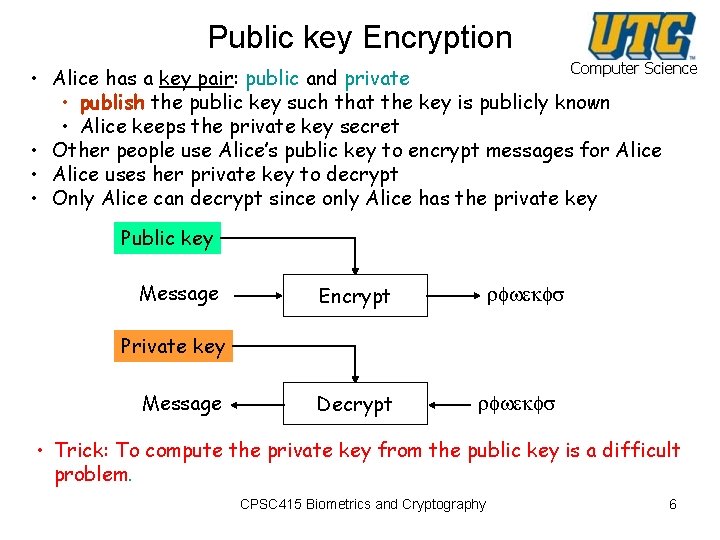
Public key Encryption Computer Science • Alice has a key pair: public and private • publish the public key such that the key is publicly known • Alice keeps the private key secret • Other people use Alice’s public key to encrypt messages for Alice • Alice uses her private key to decrypt • Only Alice can decrypt since only Alice has the private key Public key Message Encrypt rfwekfs Private key Message Decrypt rfwekfs • Trick: To compute the private key from the public key is a difficult problem. CPSC 415 Biometrics and Cryptography 6
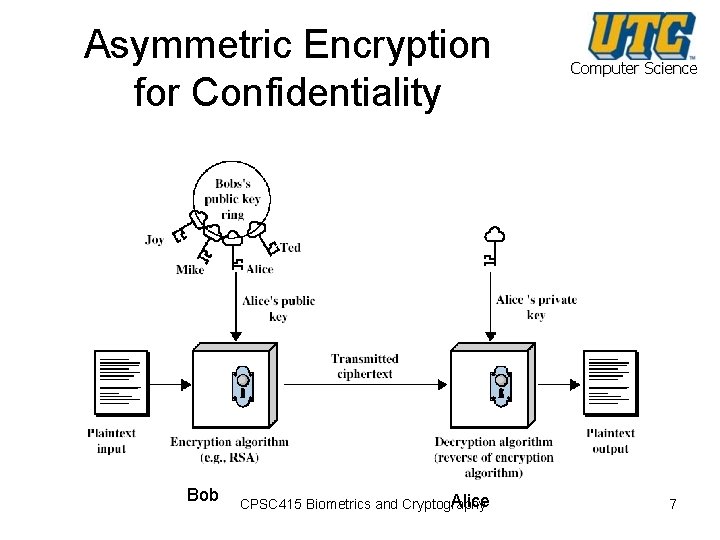
Asymmetric Encryption for Confidentiality Bob Alice CPSC 415 Biometrics and Cryptography Computer Science 7
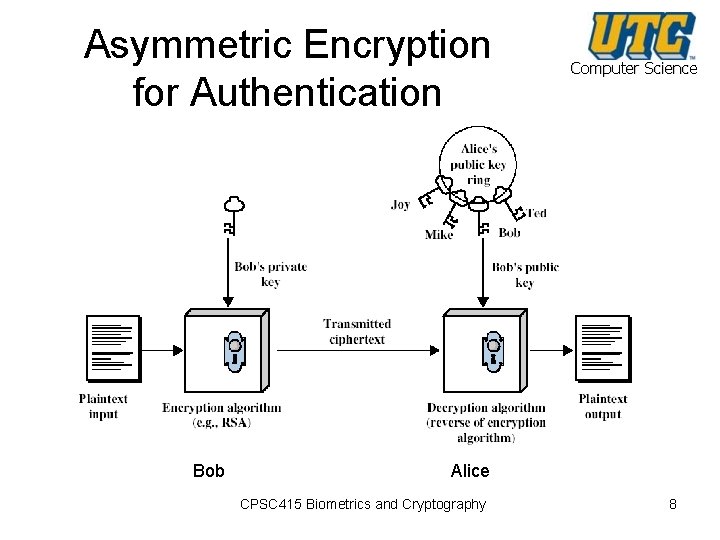
Asymmetric Encryption for Authentication Bob Computer Science Alice CPSC 415 Biometrics and Cryptography 8
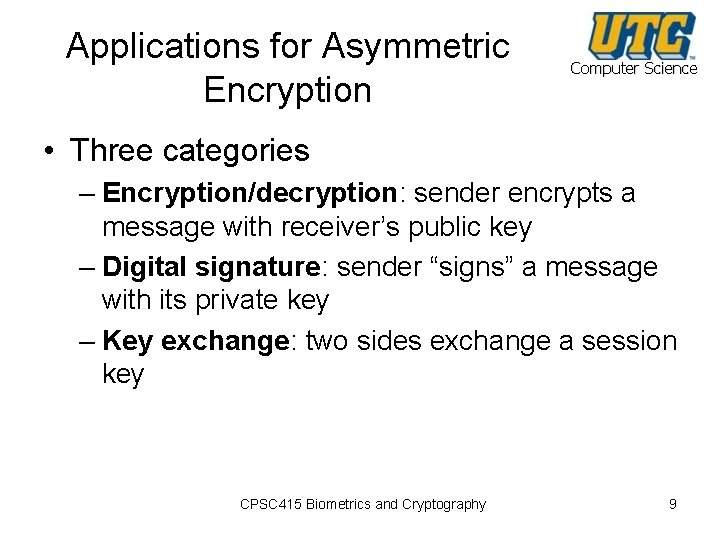
Applications for Asymmetric Encryption Computer Science • Three categories – Encryption/decryption: sender encrypts a message with receiver’s public key – Digital signature: sender “signs” a message with its private key – Key exchange: two sides exchange a session key CPSC 415 Biometrics and Cryptography 9
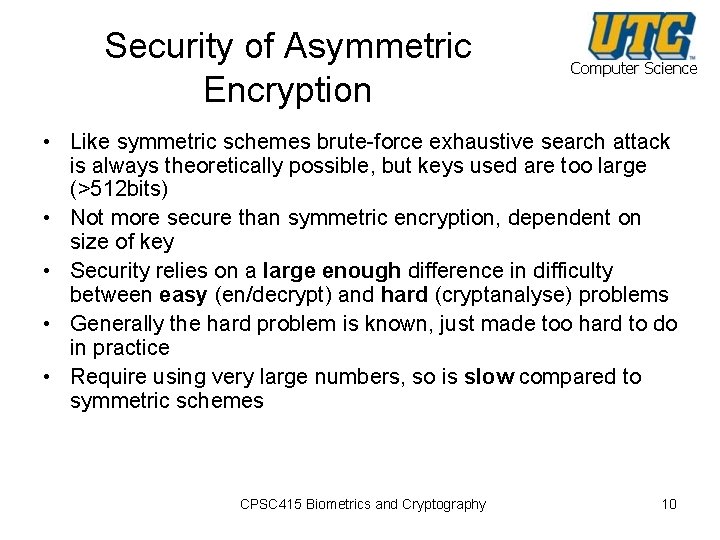
Security of Asymmetric Encryption Computer Science • Like symmetric schemes brute-force exhaustive search attack is always theoretically possible, but keys used are too large (>512 bits) • Not more secure than symmetric encryption, dependent on size of key • Security relies on a large enough difference in difficulty between easy (en/decrypt) and hard (cryptanalyse) problems • Generally the hard problem is known, just made too hard to do in practice • Require using very large numbers, so is slow compared to symmetric schemes CPSC 415 Biometrics and Cryptography 10
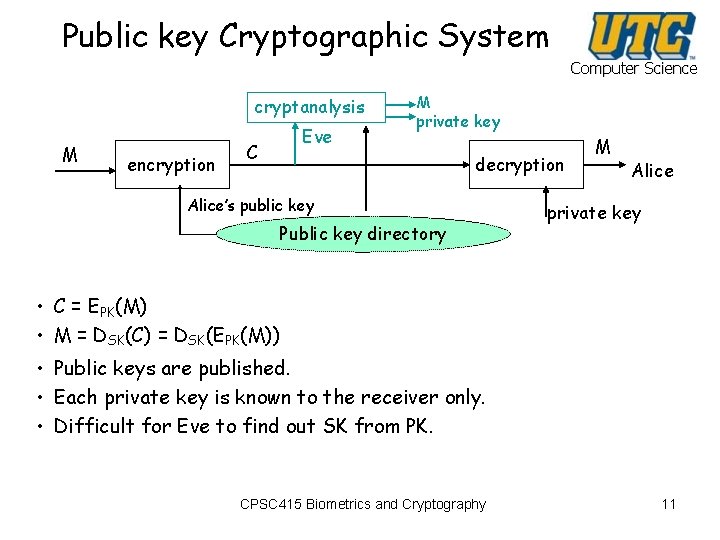
Public key Cryptographic System Computer Science cryptanalysis M encryption Eve C M private key decryption Alice’s public key Public key directory M Alice private key • C = EPK(M) • M = DSK(C) = DSK(EPK(M)) • Public keys are published. • Each private key is known to the receiver only. • Difficult for Eve to find out SK from PK. CPSC 415 Biometrics and Cryptography 11
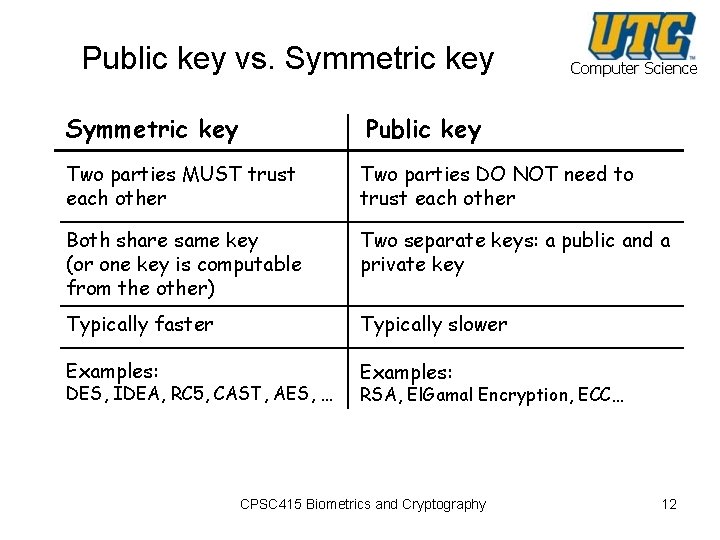
Public key vs. Symmetric key Computer Science Symmetric key Public key Two parties MUST trust each other Two parties DO NOT need to trust each other Both share same key (or one key is computable from the other) Two separate keys: a public and a private key Typically faster Typically slower Examples: DES, IDEA, RC 5, CAST, AES, … RSA, El. Gamal Encryption, ECC… CPSC 415 Biometrics and Cryptography 12
Digital signatures Computer Science • Is there a functional equivalent to a handwritten signature? – – Easy for legitimate user to sign But hard for anyone else to forge Easy for anyone to verify Dependent on message & signer (key) • Public key! – Sign: “invert” function using private key – Verify: compute function using public key CPSC 415 Biometrics and Cryptography 13
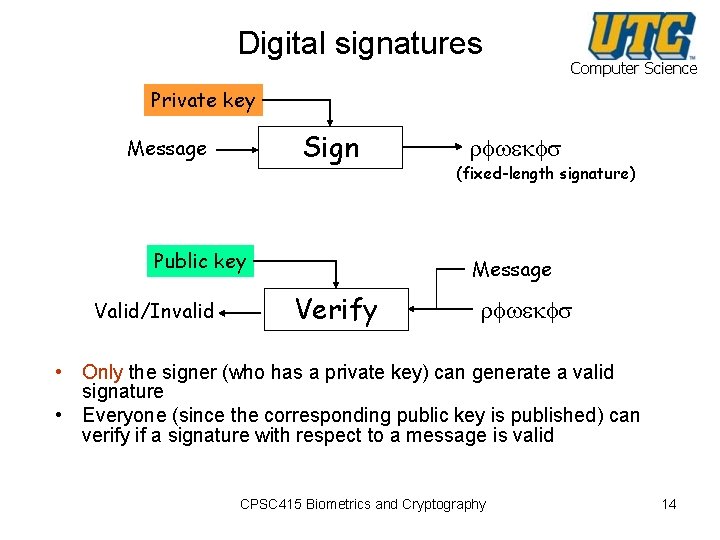
Digital signatures Computer Science Private key Sign Message Public key Valid/Invalid rfwekfs (fixed-length signature) Message Verify rfwekfs • Only the signer (who has a private key) can generate a valid signature • Everyone (since the corresponding public key is published) can verify if a signature with respect to a message is valid CPSC 415 Biometrics and Cryptography 14
Digital Envelopes -- Symmetric + Asymmetric Computer Science 1. Generate a secret key (session key) at random. 2. Encrypt the message using the session key and symmetric algorithm. 3. Encrypt the session key with the recipient’s public key. This becomes the “digital envelope”. 4. Send the encrypted message and the digital envelope to the recipient. • Figure … CPSC 415 Biometrics and Cryptography 15
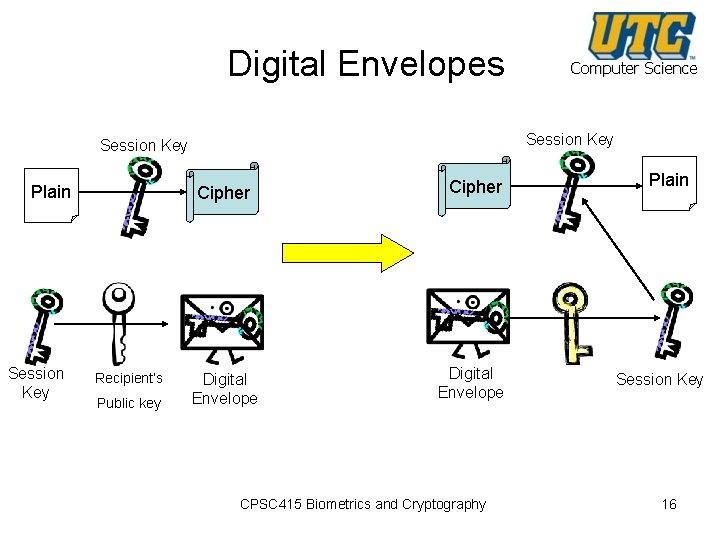
Digital Envelopes Session Key Plain Session Key Cipher Recipient’s Public key Computer Science Digital Envelope Cipher Digital Envelope CPSC 415 Biometrics and Cryptography Plain Session Key 16
RSA CPSC 415 Biometrics and Cryptography Computer Science 17
Motivation Computer Science Revision • One problem with symmetric key algorithms is that the sender needs a secure method of telling the receiver the key. • Plus, you need a separate key for everyone you might communicate with. • Public key algorithms use a public-key and privatekey pair to tackle key management problem. – Each receiver has a public key pair. – The public key is publicly known (published). – A sender uses the receiver’s public key to encrypt a message. – Only the receiver can decrypt it with the corresponding private key. CPSC 415 Biometrics and Cryptography 18
RSA Computer Science • Invented by Rivest, Shamir & Adleman of MIT in 1977 • Best known and widely used public-key scheme • Based on exponentiation in a finite (Galois) field over integers modulo a prime – exponentiation takes O((log n)3) operations (easy) • Use large integers (e. g. 1024 bits) • Security due to cost of factoring large numbers – factorization takes O(e log n) operations (hard) CPSC 415 Biometrics and Cryptography 19
RSA Key Setup Computer Science • Each user generates a public/private key pair by – select two large primes at random: p, q – compute their system modulus n=p·q • note ø(n)=(p-1)(q-1) – select at random the encryption key e • where 1<e<ø(n), gcd(e, ø(n))=1 – solve following equation to find decryption key d • e·d=1 mod ø(n) and 0≤d≤n – publish their public encryption key: KU= {e, n} – keep secret private decryption key: KR= {d, n} CPSC 415 Biometrics and Cryptography 20
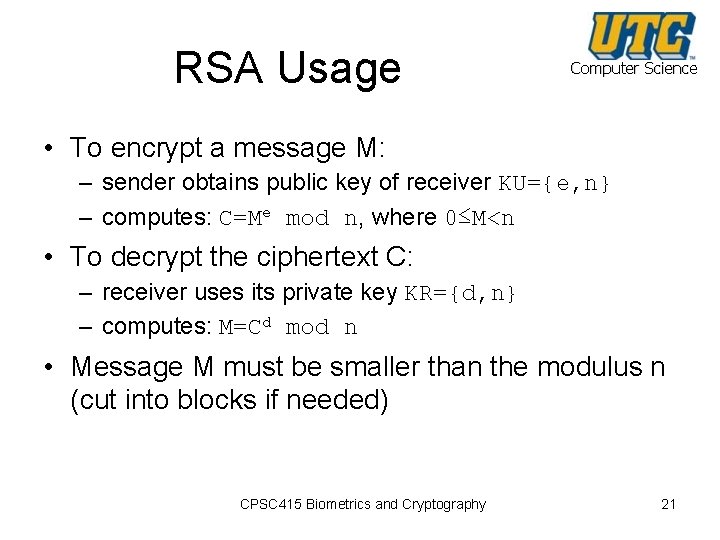
RSA Usage Computer Science • To encrypt a message M: – sender obtains public key of receiver KU={e, n} – computes: C=Me mod n, where 0≤M<n • To decrypt the ciphertext C: – receiver uses its private key KR={d, n} – computes: M=Cd mod n • Message M must be smaller than the modulus n (cut into blocks if needed) CPSC 415 Biometrics and Cryptography 21

RSA Example: Computing Keys 1. 2. 3. 4. Computer Science Select primes: p=17, q=11 Compute n=pq=17× 11=187 Compute ø(n)=(p– 1)(q-1)=16× 10=160 Select e: gcd(e, 160)=1 and e<160 § choose e=7 5. Determine d: de=1 mod 160 and d<160 § d=23 since 23× 7=161=10× 160+1 6. Publish public key KU={7, 187} 7. Keep secret private key KR={23, 187} CPSC 415 Biometrics and Cryptography 22
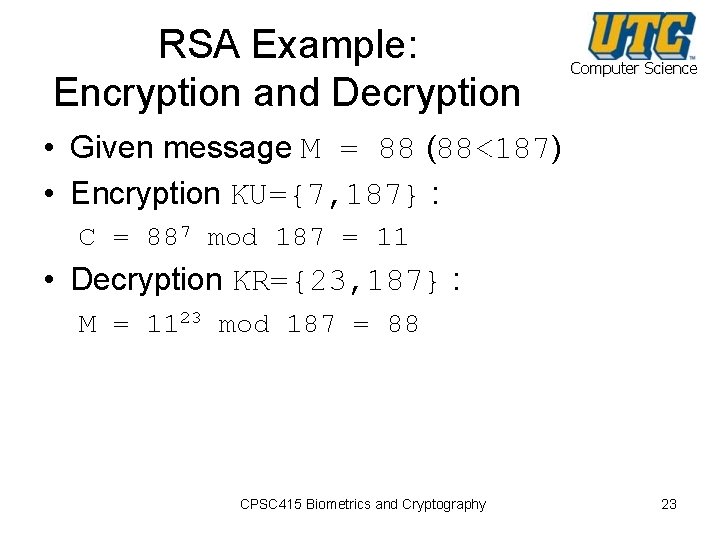
RSA Example: Encryption and Decryption Computer Science • Given message M = 88 (88<187) • Encryption KU={7, 187} : C = 887 mod 187 = 11 • Decryption KR={23, 187} : M = 1123 mod 187 = 88 CPSC 415 Biometrics and Cryptography 23
- Slides: 23