Security Terminology TCP Wrapper Cryptography Kerberos 1 Terminology
Security Terminology TCP Wrapper Cryptography Kerberos 1
Terminology • Authentication: identifying someone (or something) reliably. Proving you are who you say you are. • Authorization: permission to access a resource. 2
Terminology • Encryption: Scramble data so that only someone with a secret can make sense of the data. • Decryption: Descrambling encrypted data. • DES: Data Encryption Standard: secret key cryptographic function standardized by NBS (NIST). 3
Terminology • Secret Key Cryptography: a cryptographic scheme where the same key is used to encrypt and decrypt. • Public Key Cryptography: a cryptographic scheme where different keys are used for encryption and decryption. 4
Terminology • Firewall: a network component that separates two networks and (typically) operates in the upper layers of the OSI reference model (Application layer). • Screening Router: a discriminating router that filters packets based on network layer (and sometimes transport layer) protocols and addresses. 5
TCP Wrapper • TCP wrapper is a simple system that provides some firewall-like functionality. • In this case a single host (really just a few services) is isolated from the rest of the world. • Functionality includes logging of requests for service and access control. 6
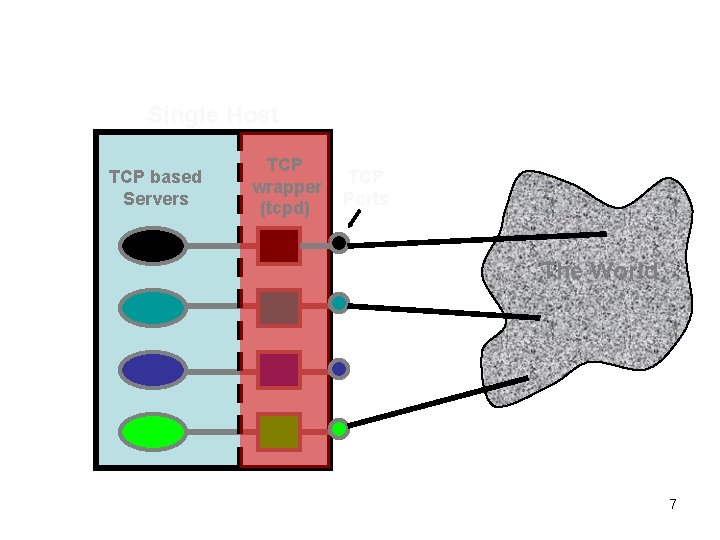
Single Host TCP based Servers TCP wrapper (tcpd) TCP Ports The World 7
tcpd • The tcpd daemon checks out incoming TCP connections before the real server gets the connection. • A log message can be generated indicating the service name, client address and time of connection. • tcpd can use client addresses to authorize each service request. 8
Typical tcpd setup • inetd (the ) is told to start tcpd instead of the real server. • tcpd checks out the client by calling getpeername on descriptor 0. • tcpd decides whether or not to start the real server (by calling exec). 9
tcpd configuration • The configuration files for tcpd specify which hosts are allowed/denied which services. • Entire domains or IP networks can be permitted or denied easily. • tcpd can be told to perform RFC 931 lookup to get a username. 10
- Slides: 10